| File name: | 04ccac472e7f9760a547e7bbb721c713f00021fcc74a59637c198f4bbee06c2d.exe |
| Full analysis: | https://app.any.run/tasks/beb56f90-e57d-4a44-9698-d0c520ec25ff |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
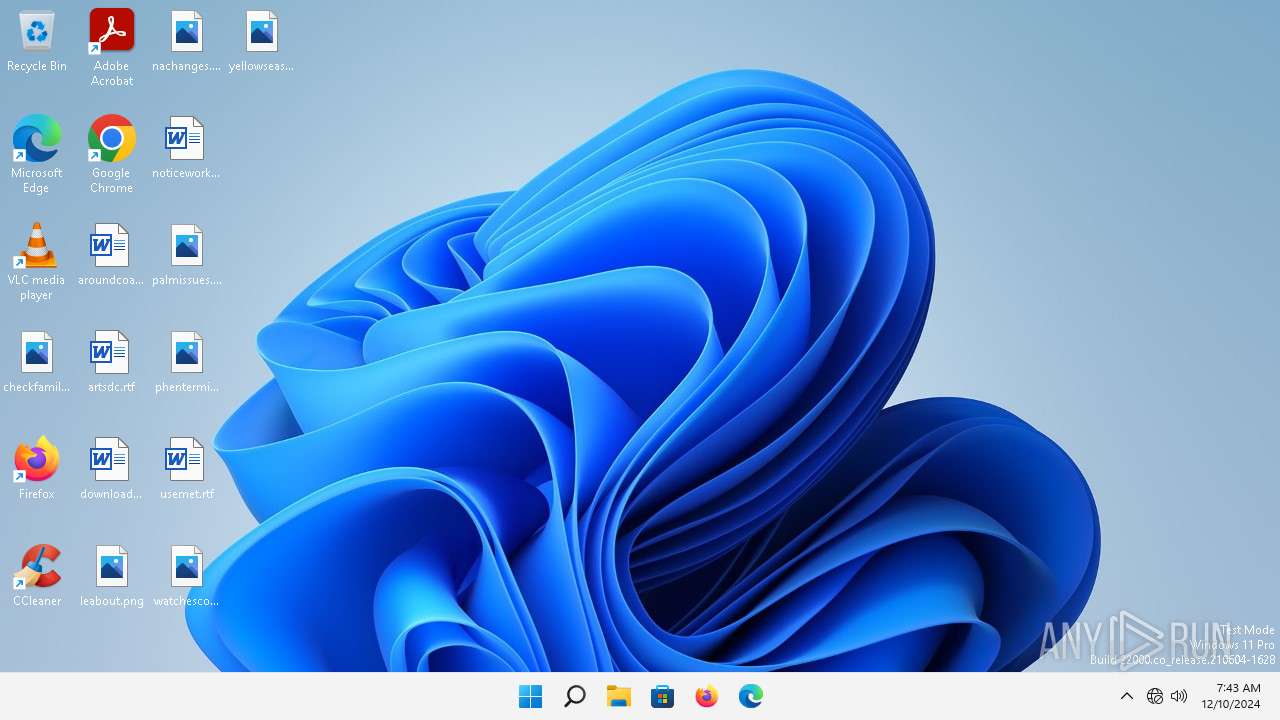
| Analysis date: | December 10, 2024, 07:43:27 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | FCC5C005C3CCBDDEE8BEE4DC5CA441E2 |
| SHA1: | D597F7EC6F9309AF338B0BBB2234F9A0A5CA1A92 |
| SHA256: | 04CCAC472E7F9760A547E7BBB721C713F00021FCC74A59637C198F4BBEE06C2D |
| SSDEEP: | 98304:gn2GNXZFit7VSPM591xQp288jeW7Wwyhu4CEW/kyA2i0NeVnnQafv25Wbnf+hKHW:xXIKlS65sHGf |
MALICIOUS
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 1656)
- 2U9131.exe (PID: 1408)
- 82cd910bdd.exe (PID: 1512)
Connects to the CnC server
- svchost.exe (PID: 1656)
- skotes.exe (PID: 2808)
- 4f5df52420.exe (PID: 2492)
Actions looks like stealing of personal data
- 2U9131.exe (PID: 1408)
- 82cd910bdd.exe (PID: 1512)
AMADEY has been detected (SURICATA)
- skotes.exe (PID: 2808)
Steals credentials from Web Browsers
- 82cd910bdd.exe (PID: 1512)
Changes the autorun value in the registry
- skotes.exe (PID: 2808)
STEALC has been detected (SURICATA)
- 4f5df52420.exe (PID: 2492)
Possible tool for stealing has been detected
- cc0a5239f0.exe (PID: 5776)
- firefox.exe (PID: 6120)
SUSPICIOUS
Process drops legitimate windows executable
- 04ccac472e7f9760a547e7bbb721c713f00021fcc74a59637c198f4bbee06c2d.exe (PID: 808)
- f4R43.exe (PID: 3688)
Starts a Microsoft application from unusual location
- 04ccac472e7f9760a547e7bbb721c713f00021fcc74a59637c198f4bbee06c2d.exe (PID: 808)
- f4R43.exe (PID: 3688)
- e0b81.exe (PID: 5452)
Reads the Internet Settings
- 1J17n3.exe (PID: 2812)
- skotes.exe (PID: 2808)
- 2U9131.exe (PID: 1408)
- 4f5df52420.exe (PID: 2492)
- 82cd910bdd.exe (PID: 1512)
Reads the BIOS version
- 1J17n3.exe (PID: 2812)
- skotes.exe (PID: 2808)
- 2U9131.exe (PID: 1408)
- 82cd910bdd.exe (PID: 1512)
- c7ac602eba.exe (PID: 5496)
Executable content was dropped or overwritten
- e0b81.exe (PID: 5452)
- f4R43.exe (PID: 3688)
- 04ccac472e7f9760a547e7bbb721c713f00021fcc74a59637c198f4bbee06c2d.exe (PID: 808)
- 1J17n3.exe (PID: 2812)
- skotes.exe (PID: 2808)
Reads security settings of Internet Explorer
- 1J17n3.exe (PID: 2812)
- skotes.exe (PID: 2808)
- 4f5df52420.exe (PID: 2492)
Starts itself from another location
- 1J17n3.exe (PID: 2812)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 1656)
- 2U9131.exe (PID: 1408)
- skotes.exe (PID: 2808)
- 82cd910bdd.exe (PID: 1512)
- 4f5df52420.exe (PID: 2492)
Reads settings of System Certificates
- 2U9131.exe (PID: 1408)
- 82cd910bdd.exe (PID: 1512)
Searches for installed software
- 2U9131.exe (PID: 1408)
Potential Corporate Privacy Violation
- skotes.exe (PID: 2808)
- 2U9131.exe (PID: 1408)
Process requests binary or script from the Internet
- skotes.exe (PID: 2808)
- 2U9131.exe (PID: 1408)
Windows Defender mutex has been found
- 4f5df52420.exe (PID: 2492)
Connects to the server without a host name
- 4f5df52420.exe (PID: 2492)
- skotes.exe (PID: 2808)
- 2U9131.exe (PID: 1408)
Uses TASKKILL.EXE to kill Browsers
- cc0a5239f0.exe (PID: 5776)
Uses TASKKILL.EXE to kill process
- cc0a5239f0.exe (PID: 5776)
The process executes via Task Scheduler
- skotes.exe (PID: 7456)
INFO
Checks supported languages
- 04ccac472e7f9760a547e7bbb721c713f00021fcc74a59637c198f4bbee06c2d.exe (PID: 808)
- f4R43.exe (PID: 3688)
- e0b81.exe (PID: 5452)
- 2U9131.exe (PID: 1408)
- skotes.exe (PID: 2808)
- 1J17n3.exe (PID: 2812)
- 82cd910bdd.exe (PID: 1512)
- 4f5df52420.exe (PID: 2492)
- cc0a5239f0.exe (PID: 5776)
- c7ac602eba.exe (PID: 5496)
Create files in a temporary directory
- e0b81.exe (PID: 5452)
- 1J17n3.exe (PID: 2812)
- f4R43.exe (PID: 3688)
- 04ccac472e7f9760a547e7bbb721c713f00021fcc74a59637c198f4bbee06c2d.exe (PID: 808)
- skotes.exe (PID: 2808)
Sends debugging messages
- 1J17n3.exe (PID: 2812)
- skotes.exe (PID: 2808)
- 2U9131.exe (PID: 1408)
- 82cd910bdd.exe (PID: 1512)
- 4f5df52420.exe (PID: 2492)
- c7ac602eba.exe (PID: 5496)
- skotes.exe (PID: 7456)
Reads the computer name
- 1J17n3.exe (PID: 2812)
- 2U9131.exe (PID: 1408)
- skotes.exe (PID: 2808)
- 82cd910bdd.exe (PID: 1512)
- 4f5df52420.exe (PID: 2492)
- cc0a5239f0.exe (PID: 5776)
- c7ac602eba.exe (PID: 5496)
Checks proxy server information
- skotes.exe (PID: 2808)
Reads the software policy settings
- 2U9131.exe (PID: 1408)
- 82cd910bdd.exe (PID: 1512)
Reads the machine GUID from the registry
- 2U9131.exe (PID: 1408)
- 82cd910bdd.exe (PID: 1512)
The process uses the downloaded file
- skotes.exe (PID: 2808)
Creates files or folders in the user directory
- 4f5df52420.exe (PID: 2492)
- skotes.exe (PID: 2808)
Application launched itself
- firefox.exe (PID: 6120)
- firefox.exe (PID: 5764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:05:24 22:49:06+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.13 |
| CodeSize: | 25600 |
| InitializedDataSize: | 7173120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6a60 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.0.17763.1 |
| ProductVersionNumber: | 11.0.17763.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 11.00.17763.1 (WinBuild.160101.0800) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE .MUI |
| ProductName: | Internet Explorer |
| ProductVersion: | 11.00.17763.1 |
Total processes
148
Monitored processes
33
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4820 -childID 4 -isForBrowser -prefsHandle 4896 -prefMapHandle 4892 -prefsLen 28383 -prefMapSize 243239 -jsInitHandle 1360 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {7c3f72bf-dad8-4a5b-845c-53000ce5c70c} 5764 "\\.\pipe\gecko-crash-server-pipe.5764" 139534cf4d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 808 | "C:\Users\admin\Desktop\04ccac472e7f9760a547e7bbb721c713f00021fcc74a59637c198f4bbee06c2d.exe" | C:\Users\admin\Desktop\04ccac472e7f9760a547e7bbb721c713f00021fcc74a59637c198f4bbee06c2d.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1408 | C:\Users\admin\AppData\Local\Temp\IXP002.TMP\2U9131.exe | C:\Users\admin\AppData\Local\Temp\IXP002.TMP\2U9131.exe | e0b81.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1512 | "C:\Users\admin\AppData\Local\Temp\1013650001\82cd910bdd.exe" | C:\Users\admin\AppData\Local\Temp\1013650001\82cd910bdd.exe | skotes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1656 | C:\Windows\system32\svchost.exe -k NetworkService -p | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1856 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2272 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2052 -parentBuildID 20240213221259 -prefsHandle 2040 -prefMapHandle 2036 -prefsLen 25692 -prefMapSize 243239 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {3db90a87-7cf5-48fa-8650-c5f986bf4092} 5764 "\\.\pipe\gecko-crash-server-pipe.5764" 1393cc83910 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1792 -parentBuildID 20240213221259 -prefsHandle 1732 -prefMapHandle 1724 -prefsLen 25692 -prefMapSize 243239 -appDir "C:\Program Files\Mozilla Firefox\browser" - {88328e5d-e0ff-4991-9303-d1d634d075f7} 5764 "\\.\pipe\gecko-crash-server-pipe.5764" 13948bd5e10 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2492 | "C:\Users\admin\AppData\Local\Temp\1013651001\4f5df52420.exe" | C:\Users\admin\AppData\Local\Temp\1013651001\4f5df52420.exe | skotes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2528 | taskkill /F /IM brave.exe /T | C:\Windows\SysWOW64\taskkill.exe | — | cc0a5239f0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
31 442
Read events
31 396
Write events
45
Delete events
1
Modification events
| (PID) Process: | (2812) 1J17n3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2812) 1J17n3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2812) 1J17n3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2812) 1J17n3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2808) skotes.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2808) skotes.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2808) skotes.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2808) skotes.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2808) skotes.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2808) skotes.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
16
Suspicious files
277
Text files
35
Unknown types
99
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 808 | 04ccac472e7f9760a547e7bbb721c713f00021fcc74a59637c198f4bbee06c2d.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\4U637G.exe | executable | |
MD5:99CFF6034A2010E18F19281AFA021AEC | SHA256:BDA24B571A92286E33963D7790A6CADA3B23B2D5B8C4099EB7F4922D41DF113E | |||
| 3688 | f4R43.exe | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\3w55K.exe | executable | |
MD5:82B70CB96DC208843A0380D75FF08F9B | SHA256:697D7F31A1D5ADAB597902CEB9228A77B6E84D776BE1F49A610B04DE25D87801 | |||
| 808 | 04ccac472e7f9760a547e7bbb721c713f00021fcc74a59637c198f4bbee06c2d.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\f4R43.exe | executable | |
MD5:777D6A67707876286FE17D655C830EBF | SHA256:4280ED645EF5B31060F54161C295196FC3EA72407FC1C466F43D21A96FFB133B | |||
| 5452 | e0b81.exe | C:\Users\admin\AppData\Local\Temp\IXP002.TMP\2U9131.exe | executable | |
MD5:FFBF4DAC7F1ED0ADE66186644F98132C | SHA256:EA3D6A813BFA00A6FE5888FDB841E24063E24BF7723AC233DF33D1E07129E23C | |||
| 3688 | f4R43.exe | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\e0b81.exe | executable | |
MD5:DEC11B3CC0EE1492FBF2C3F8F5E21497 | SHA256:9223019E435AC3DEB348E7AE211ABE23C5F7BBCCC4D2B9765A5CD1B7BE82C06B | |||
| 5452 | e0b81.exe | C:\Users\admin\AppData\Local\Temp\IXP002.TMP\1J17n3.exe | executable | |
MD5:11C23F104D7ECFCB5B535F22214C5DBE | SHA256:C5741977022E908FBE2C233DF25C5D5C6B0B88AF01A026ACC6085F30793708EF | |||
| 2808 | skotes.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\J0KBFYBW\random[1].exe | executable | |
MD5:5F300EBC0539EA54FD18FD8E52CA259A | SHA256:A85BCADBD84CAD34D13795EAF7A4A452FF99A7C4DF3C4E838CF623BAB52C32B8 | |||
| 2812 | 1J17n3.exe | C:\Users\admin\AppData\Local\Temp\abc3bc1985\skotes.exe | executable | |
MD5:11C23F104D7ECFCB5B535F22214C5DBE | SHA256:C5741977022E908FBE2C233DF25C5D5C6B0B88AF01A026ACC6085F30793708EF | |||
| 2808 | skotes.exe | C:\Users\admin\AppData\Local\Temp\1013650001\82cd910bdd.exe | executable | |
MD5:5F300EBC0539EA54FD18FD8E52CA259A | SHA256:A85BCADBD84CAD34D13795EAF7A4A452FF99A7C4DF3C4E838CF623BAB52C32B8 | |||
| 5764 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\8o2qovza.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
71
TCP/UDP connections
104
DNS requests
103
Threats
36
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2808 | skotes.exe | POST | 200 | 185.215.113.43:80 | http://185.215.113.43/Zu7JuNko/index.php | unknown | — | — | malicious |
— | — | POST | 200 | 104.21.32.1:443 | https://atten-supporse.biz/api | unknown | text | 2 b | malicious |
— | — | POST | 200 | 104.21.96.1:443 | https://atten-supporse.biz/api | unknown | text | 18.2 Kb | malicious |
— | — | POST | 200 | 34.120.208.123:443 | https://incoming.telemetry.mozilla.org/submit/firefox-desktop-background-defaultagent/baseline/1/c508b2a8-5db2-4170-bf4b-c1d02133e28e | unknown | — | — | whitelisted |
— | — | POST | 200 | 34.120.208.123:443 | https://incoming.telemetry.mozilla.org/submit/firefox-desktop-background-defaultagent/events/1/f3b4cb82-aec4-49d9-b7f7-83912f0fa8c8 | unknown | — | — | whitelisted |
— | — | POST | 200 | 34.120.208.123:443 | https://incoming.telemetry.mozilla.org/submit/firefox-desktop-background-defaultagent/events/1/4997ddbf-7674-4321-8925-ea1ae748f288 | unknown | — | — | whitelisted |
— | — | POST | 200 | 34.120.208.123:443 | https://incoming.telemetry.mozilla.org/submit/firefox-desktop-background-defaultagent/baseline/1/b06e4ce9-fb91-418e-a90a-98488f8662c7 | unknown | — | — | whitelisted |
— | — | POST | 200 | 104.21.48.1:443 | https://atten-supporse.biz/api | unknown | text | 18.2 Kb | malicious |
— | — | POST | 200 | 104.21.112.1:443 | https://atten-supporse.biz/api | unknown | text | 2 b | malicious |
— | — | POST | 200 | 104.21.16.1:443 | https://atten-supporse.biz/api | unknown | text | 16 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
6700 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
6700 | firefox.exe | 34.120.208.123:443 | incoming.telemetry.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
1296 | svchost.exe | 2.18.64.212:80 | — | Administracion Nacional de Telecomunicaciones | UY | unknown |
3820 | rundll32.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3484 | OfficeC2RClient.exe | 52.109.32.97:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | GB | unknown |
5552 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1408 | 2U9131.exe | 104.21.64.1:443 | atten-supporse.biz | CLOUDFLARENET | — | malicious |
2808 | skotes.exe | 185.215.113.43:80 | — | 1337team Limited | SC | malicious |
2808 | skotes.exe | 185.215.113.16:80 | — | 1337team Limited | SC | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
incoming.telemetry.mozilla.org |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
prod.remote-settings.prod.webservices.mozgcp.net |
| whitelisted |
telemetry-incoming.r53-2.services.mozilla.com |
| whitelisted |
google.com |
| whitelisted |
atten-supporse.biz |
| malicious |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ecs.office.com |
| whitelisted |
mrodevicemgr.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1656 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (atten-supporse .biz) |
1408 | 2U9131.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (atten-supporse .biz in TLS SNI) |
2808 | skotes.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 33 |
2808 | skotes.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
1408 | 2U9131.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (atten-supporse .biz in TLS SNI) |
1408 | 2U9131.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (atten-supporse .biz in TLS SNI) |
2808 | skotes.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
2808 | skotes.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2808 | skotes.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 33 |
2808 | skotes.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
1J17n3.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
skotes.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
2U9131.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
82cd910bdd.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
4f5df52420.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
c7ac602eba.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
skotes.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
2U9131.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|