| File name: | Order_1536753G_KO 0203 AC - KO 5946 AB.iso |
| Full analysis: | https://app.any.run/tasks/0438dfd9-ca4b-44c1-9e2c-32629b612d4c |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | March 14, 2019, 13:50:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-iso9660-image |
| File info: | ISO 9660 CD-ROM filesystem data 'Order_1536753G_KO 0203 AC - KO 5' |
| MD5: | 257DEDC02CA764C734D6BBA9ED71CD7B |
| SHA1: | B19C90C530CD514D640BEBCF6F1C004B58394E65 |
| SHA256: | 0461BAFC801CC3329EC977E06CB48BDA257447EBEA46EF09F31C948D5CD4FF85 |
| SSDEEP: | 6144:FKzHvL2qE+YPsyjkNgyUvQ2JiLeLyoWLPMMOaSc/:FIHvCFoNg9DcL4yoWLXSc |
MALICIOUS
Application was dropped or rewritten from another process
- Order_1536753G_KO 0203 AC - KO 5946 AB.exe (PID: 2544)
- Order_1536753G_KO 0203 AC - KO 5946 AB.exe (PID: 3136)
- objectMOSELOVENE.exe (PID: 2652)
- objectMOSELOVENE.exe (PID: 3360)
- objectMOSELOVENE.exe (PID: 2096)
Changes the autorun value in the registry
- objectMOSELOVENE.exe (PID: 2652)
LOKIBOT was detected
- objectMOSELOVENE.exe (PID: 2096)
Detected artifacts of LokiBot
- objectMOSELOVENE.exe (PID: 2096)
Connects to CnC server
- objectMOSELOVENE.exe (PID: 2096)
Actions looks like stealing of personal data
- objectMOSELOVENE.exe (PID: 2096)
SUSPICIOUS
Application launched itself
- Order_1536753G_KO 0203 AC - KO 5946 AB.exe (PID: 2544)
- objectMOSELOVENE.exe (PID: 3360)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3080)
- Order_1536753G_KO 0203 AC - KO 5946 AB.exe (PID: 3136)
- objectMOSELOVENE.exe (PID: 2096)
Loads DLL from Mozilla Firefox
- objectMOSELOVENE.exe (PID: 2096)
Creates files in the user directory
- objectMOSELOVENE.exe (PID: 2096)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .iso | | | ISO 9660 CD image (27.6) |
|---|---|---|
| .atn | | | Photoshop Action (27.1) |
| .gmc | | | Game Music Creator Music (6.1) |
EXIF
ISO
| System: | Win32 |
|---|---|
| VolumeName: | Order_1536753G_KO 0203 AC - KO 5 |
| VolumeBlockCount: | 244 |
| VolumeBlockSize: | 2048 |
| RootDirectoryCreateDate: | 2019:03:13 08:57:18+01:00 |
| Software: | PowerISO |
| VolumeCreateDate: | 2019:03:13 08:57:18.00+01:00 |
| VolumeModifyDate: | 2019:03:13 08:57:18.00+01:00 |
Composite
| VolumeSize: | 488 kB |
|---|
Total processes
36
Monitored processes
7
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2096 | "C:\Users\admin\AppData\Local\Temp\objectMOSELOVENE.exe" | C:\Users\admin\AppData\Local\Temp\objectMOSELOVENE.exe | objectMOSELOVENE.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2544 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3080.410\Order_1536753G_KO 0203 AC - KO 5946 AB.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3080.410\Order_1536753G_KO 0203 AC - KO 5946 AB.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2652 | "C:\Users\admin\AppData\Local\Temp\objectMOSELOVENE.exe" | C:\Users\admin\AppData\Local\Temp\objectMOSELOVENE.exe | Order_1536753G_KO 0203 AC - KO 5946 AB.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
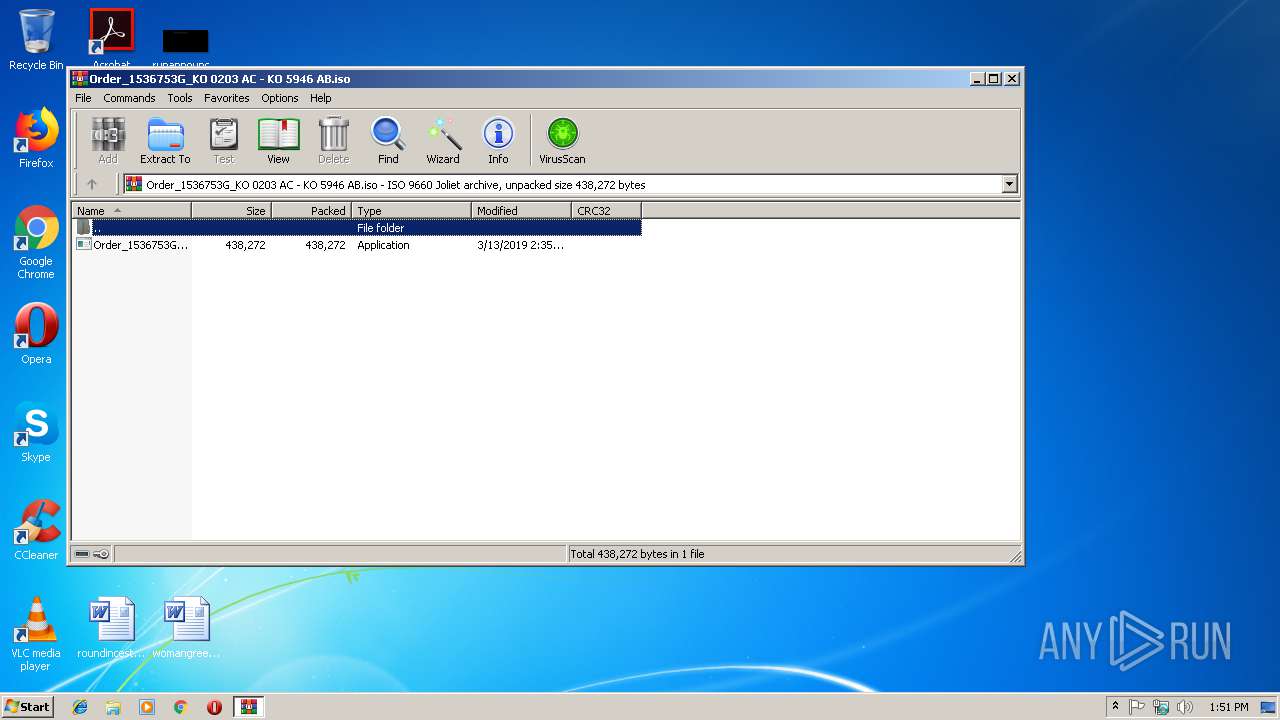
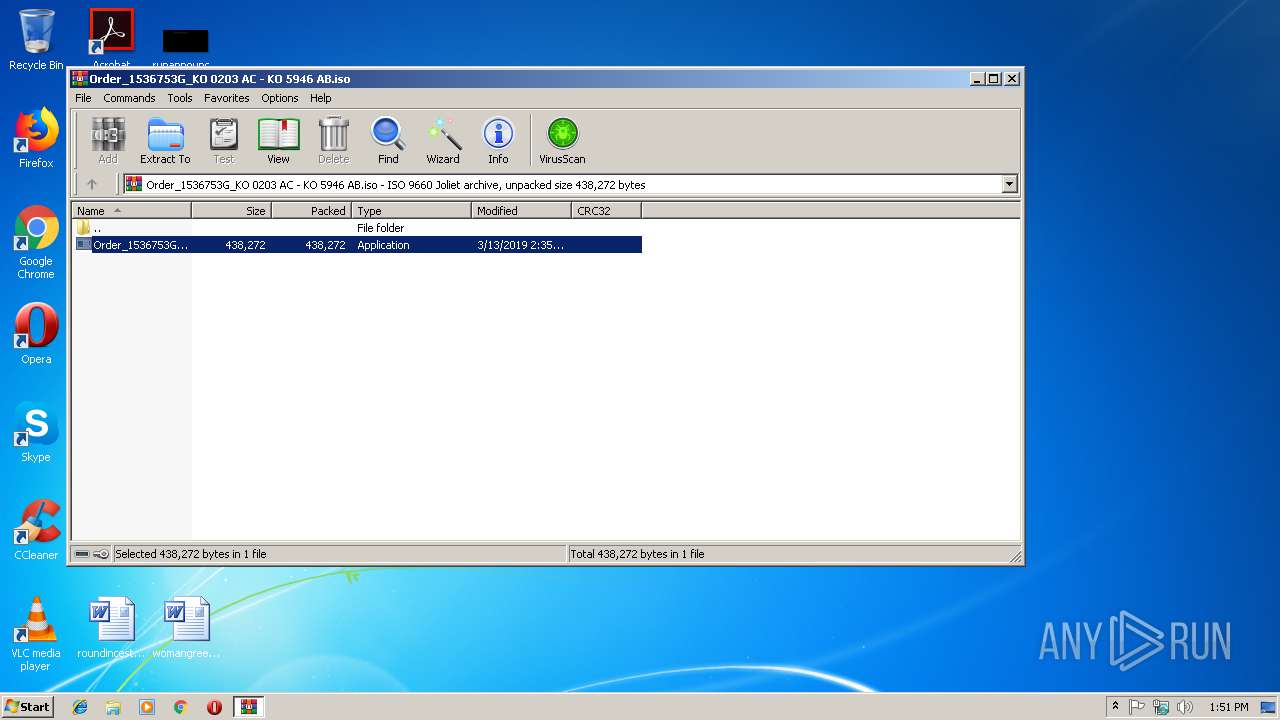
| 2844 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Order_1536753G_KO 0203 AC - KO 5946 AB.iso | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3080 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Order_1536753G_KO 0203 AC - KO 5946 AB.iso" | C:\Program Files\WinRAR\WinRAR.exe | rundll32.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3136 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3080.410\Order_1536753G_KO 0203 AC - KO 5946 AB.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3080.410\Order_1536753G_KO 0203 AC - KO 5946 AB.exe | Order_1536753G_KO 0203 AC - KO 5946 AB.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3360 | "C:\Users\admin\AppData\Local\Temp\objectMOSELOVENE.exe" | C:\Users\admin\AppData\Local\Temp\objectMOSELOVENE.exe | — | objectMOSELOVENE.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
1 052
Read events
957
Write events
95
Delete events
0
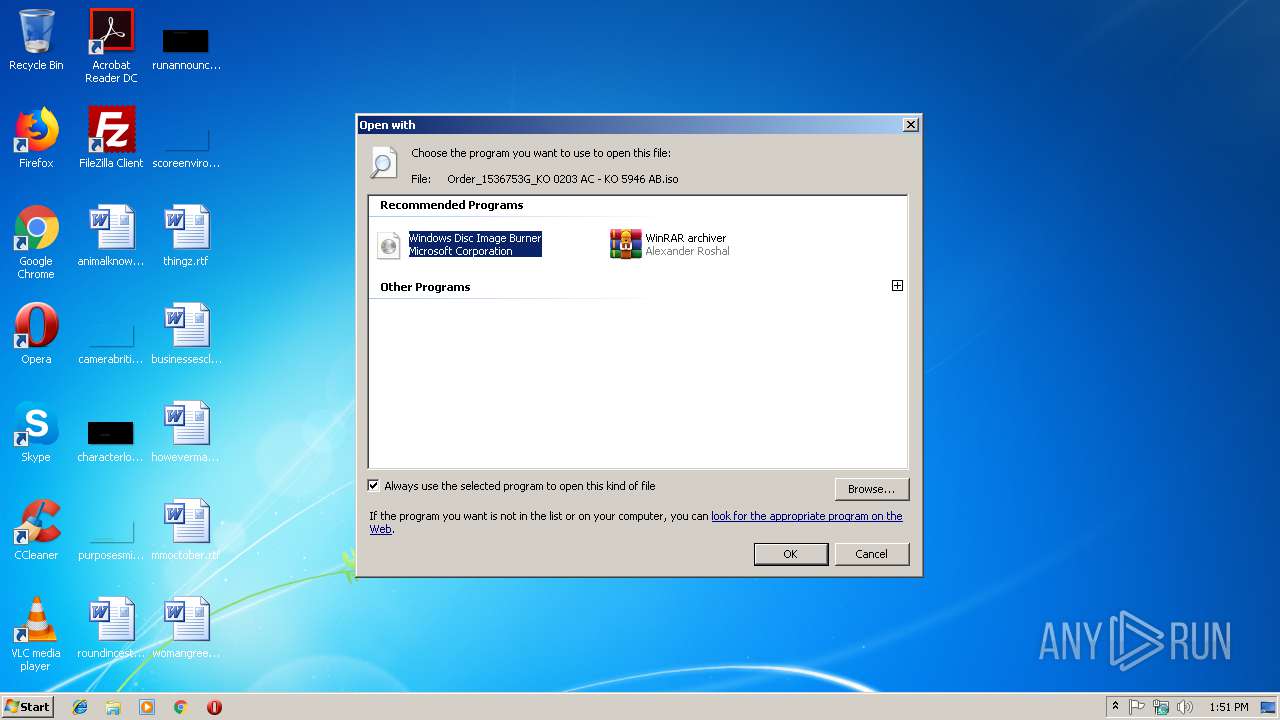
Modification events
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\isoburn.exe,-350 |
Value: Disc Image File | |||
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.iso\OpenWithProgids |
| Operation: | write | Name: | Windows.IsoFile |
Value: | |||
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\isoburn.exe,-352 |
Value: Windows Disc Image Burner | |||
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\System32\isoburn.exe |
Value: Windows Disc Image Burner | |||
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\WinRAR\WinRAR.exe |
Value: WinRAR archiver | |||
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (2844) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
Executable files
3
Suspicious files
0
Text files
7
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2096 | objectMOSELOVENE.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.lck | — | |
MD5:— | SHA256:— | |||
| 3136 | Order_1536753G_KO 0203 AC - KO 5946 AB.exe | C:\Users\admin\AppData\Local\Temp\objectMOSELOVENE.exe | executable | |
MD5:— | SHA256:— | |||
| 3080 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3080.410\Order_1536753G_KO 0203 AC - KO 5946 AB.exe | executable | |
MD5:— | SHA256:— | |||
| 3136 | Order_1536753G_KO 0203 AC - KO 5946 AB.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\win.ini | text | |
MD5:D2A2412BDDBA16D60EC63BD9550D933F | SHA256:79FF2254E38192BE1626D05BEC6C82E10C85E1CF91DF7440C4C443380A1E877A | |||
| 2096 | objectMOSELOVENE.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.hdb | text | |
MD5:— | SHA256:— | |||
| 2544 | Order_1536753G_KO 0203 AC - KO 5946 AB.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\win.ini | text | |
MD5:D2A2412BDDBA16D60EC63BD9550D933F | SHA256:79FF2254E38192BE1626D05BEC6C82E10C85E1CF91DF7440C4C443380A1E877A | |||
| 2096 | objectMOSELOVENE.exe | C:\Users\admin\AppData\Roaming\F63AAA\A71D80.exe | executable | |
MD5:— | SHA256:— | |||
| 2096 | objectMOSELOVENE.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\0f5007522459c86e95ffcc62f32308f1_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:18B8CFC0185C50383AAC0A4F30A9DAC8 | SHA256:913E8CED6A447FE791954D382ABA52D490513C5D2F689B391866C7E561F89A03 | |||
| 3136 | Order_1536753G_KO 0203 AC - KO 5946 AB.exe | C:\Users\admin\AppData\Local\Temp\objectMOSELOVENE.vbs | text | |
MD5:091BB60664FFF77D4F1BF60123AB0FF4 | SHA256:A5D3C1C188E001A239D98F59286DDDD1E62BE07B7E3B9E74AC768A730671B35F | |||
| 2652 | objectMOSELOVENE.exe | C:\Users\admin\AppData\Local\VirtualStore\Windows\win.ini | text | |
MD5:D2A2412BDDBA16D60EC63BD9550D933F | SHA256:79FF2254E38192BE1626D05BEC6C82E10C85E1CF91DF7440C4C443380A1E877A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
1
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2096 | objectMOSELOVENE.exe | POST | — | 104.27.169.144:80 | http://honduraz.gq/raphael/fre.php | US | — | — | malicious |
2096 | objectMOSELOVENE.exe | POST | — | 104.27.169.144:80 | http://honduraz.gq/raphael/fre.php | US | — | — | malicious |
2096 | objectMOSELOVENE.exe | POST | — | 104.27.169.144:80 | http://honduraz.gq/raphael/fre.php | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2096 | objectMOSELOVENE.exe | 104.27.169.144:80 | honduraz.gq | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
honduraz.gq |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gq Domain |
2096 | objectMOSELOVENE.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
2096 | objectMOSELOVENE.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
2096 | objectMOSELOVENE.exe | Potentially Bad Traffic | ET INFO HTTP POST Request to Suspicious *.gq domain |
2096 | objectMOSELOVENE.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M1 |
2096 | objectMOSELOVENE.exe | A Network Trojan was detected | ET TROJAN LokiBot Application/Credential Data Exfiltration Detected M2 |
2096 | objectMOSELOVENE.exe | A Network Trojan was detected | MALWARE [PTsecurity] Loki Bot Check-in M2 |
2096 | objectMOSELOVENE.exe | A Network Trojan was detected | ET TROJAN LokiBot User-Agent (Charon/Inferno) |
2096 | objectMOSELOVENE.exe | A Network Trojan was detected | ET TROJAN LokiBot Checkin |
2096 | objectMOSELOVENE.exe | Potentially Bad Traffic | ET INFO HTTP POST Request to Suspicious *.gq domain |
3 ETPRO signatures available at the full report