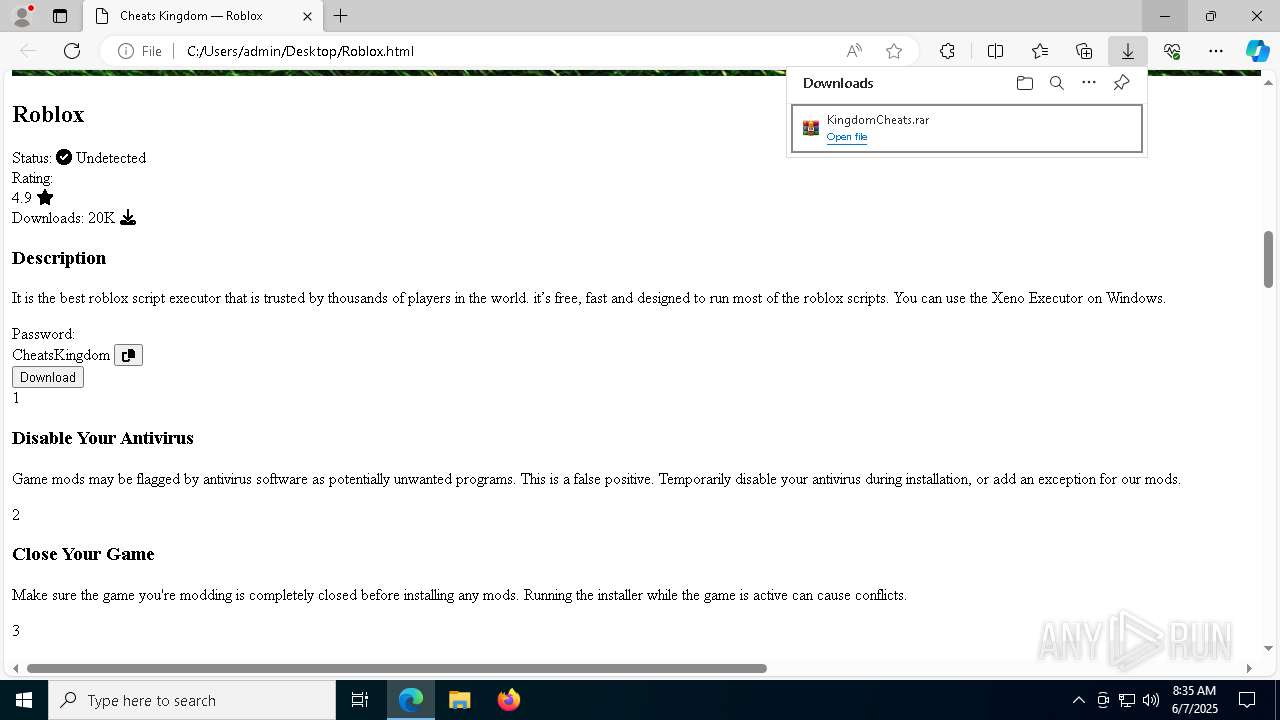
| download: | /download/Roblox.html |
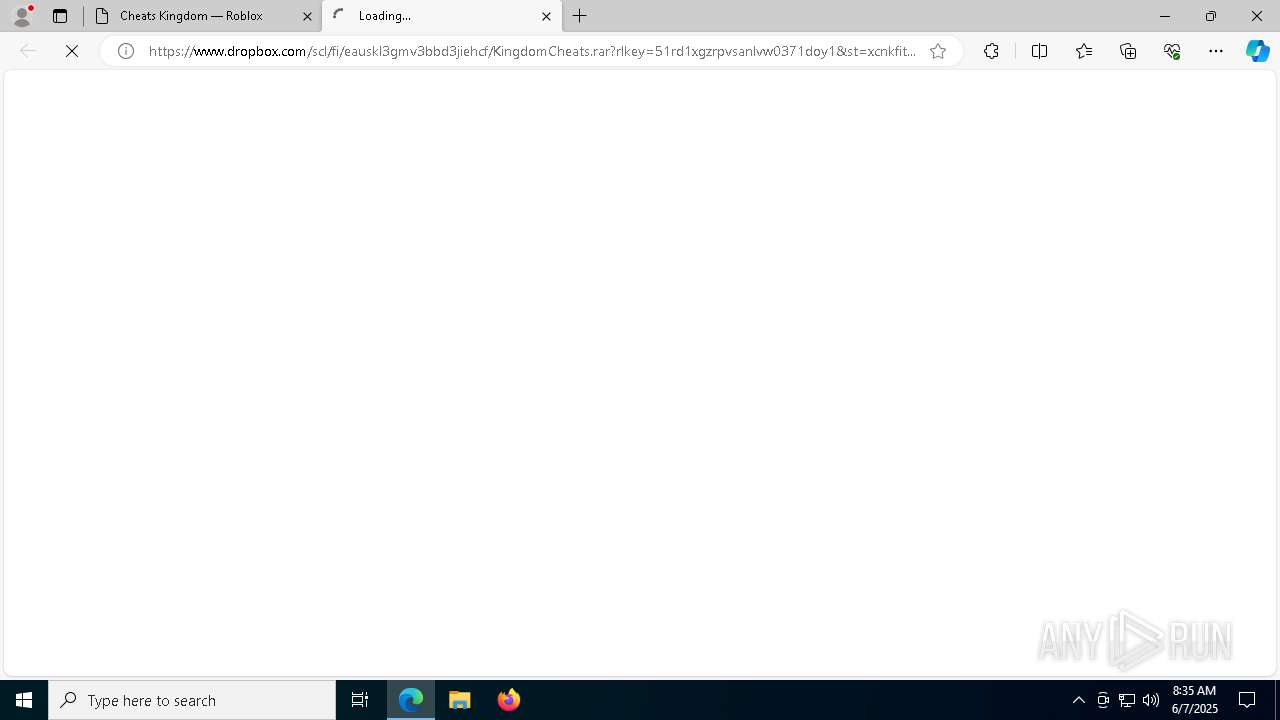
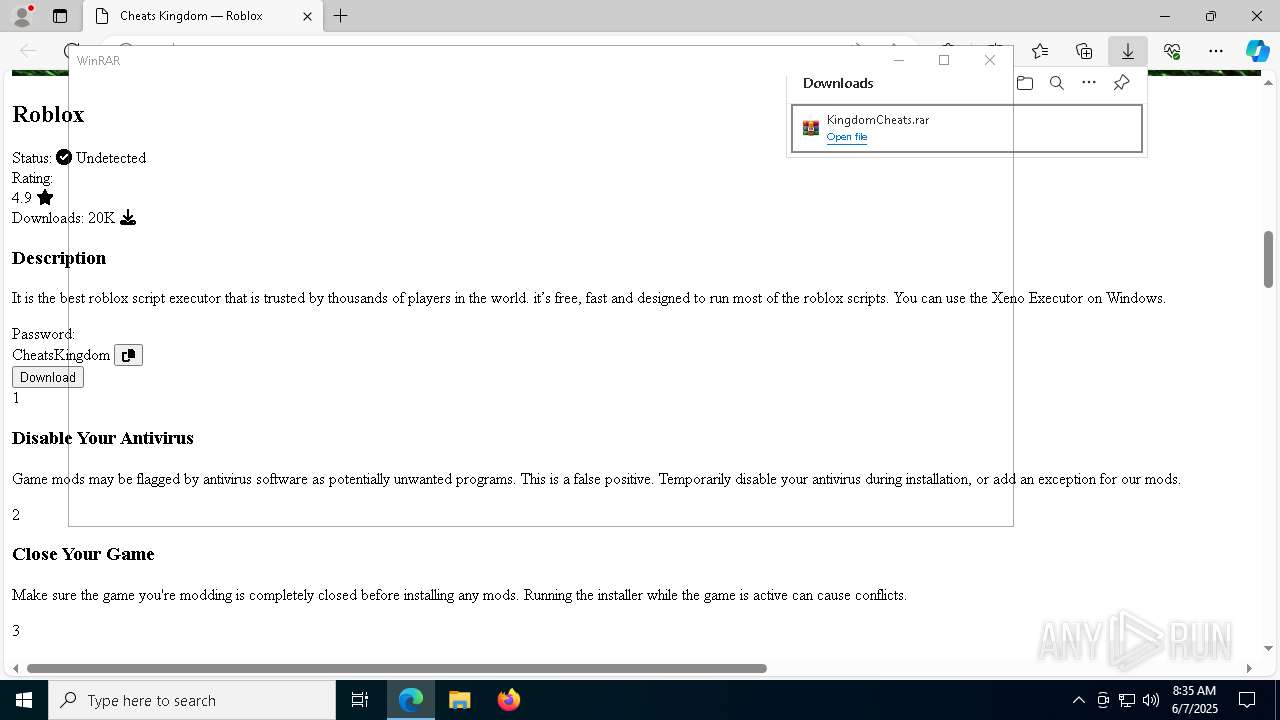
| Full analysis: | https://app.any.run/tasks/5aa6d651-999a-473a-97e6-14ab61b4938b |
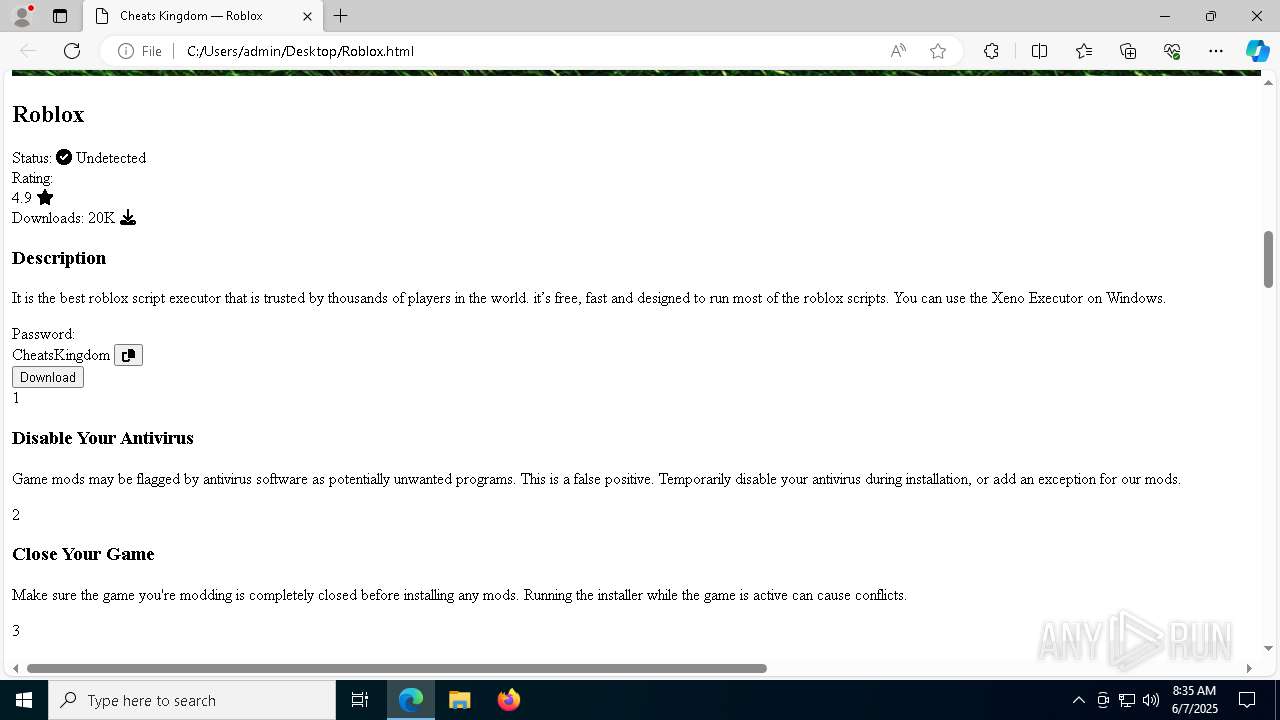
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | June 07, 2025, 08:34:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, Unicode text, UTF-8 text, with CRLF line terminators |
| MD5: | 6FA8507AFB364BACC2F5B827840E1334 |
| SHA1: | ABDE08A3639884C82BBD29196EC9ACB60E7AA31F |
| SHA256: | 03FD55158290FE9384440859C31237C30740F77A570F869A0F6235DD9582BC4B |
| SSDEEP: | 96:VAkkVWE9ELT/TdT39NJM6OvtySASASYjHymSgll/xVI1dG47oN8nLhQwCnNK+l1k:akkVWE9ELThj455NHgll/cG47r2a1V |
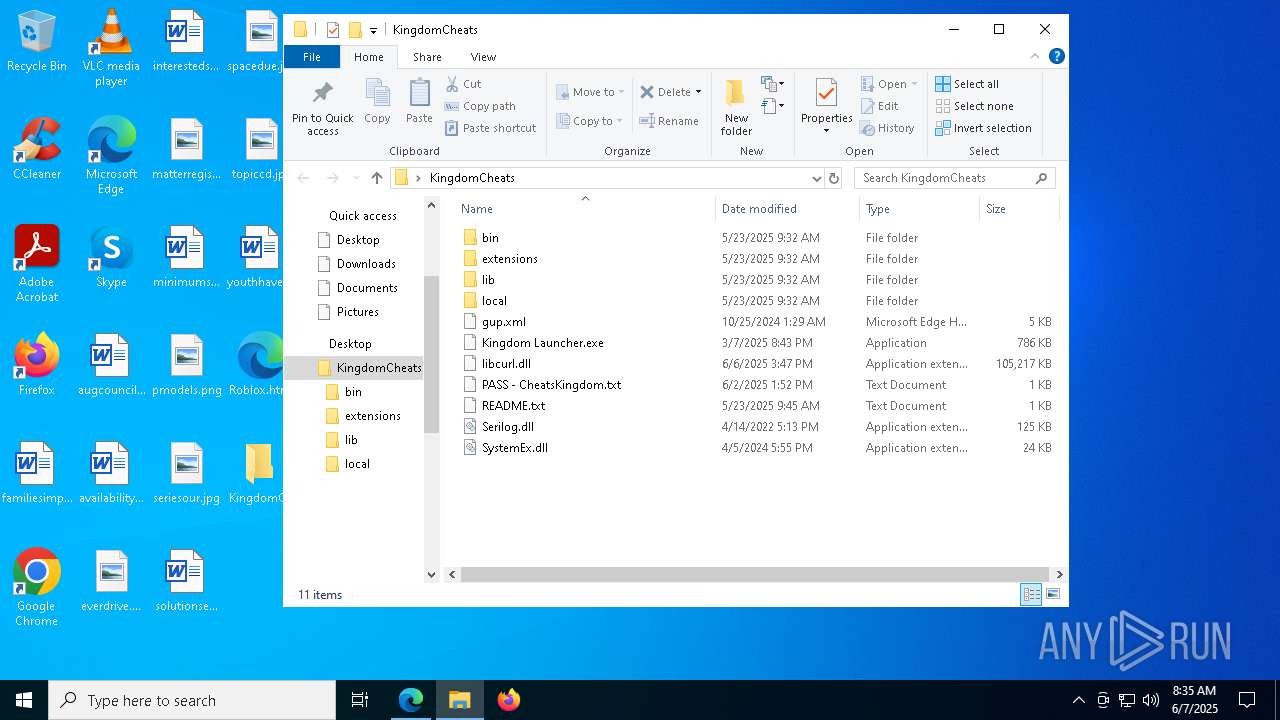
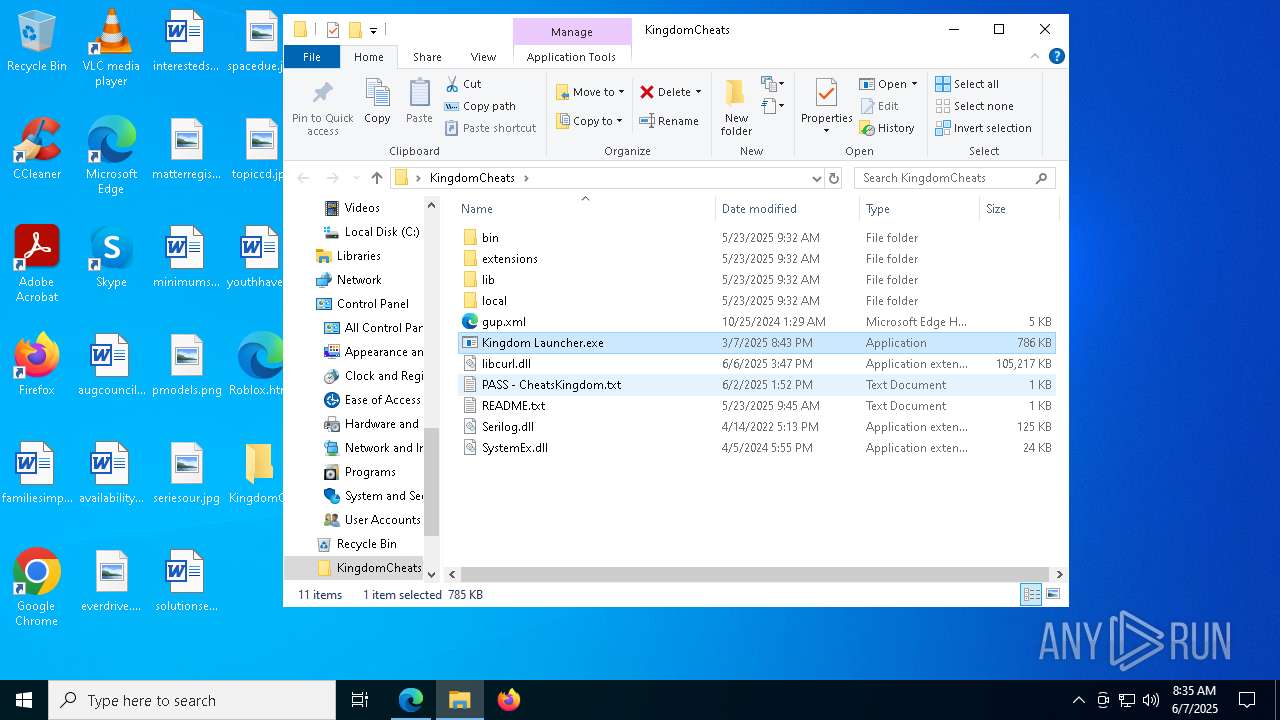
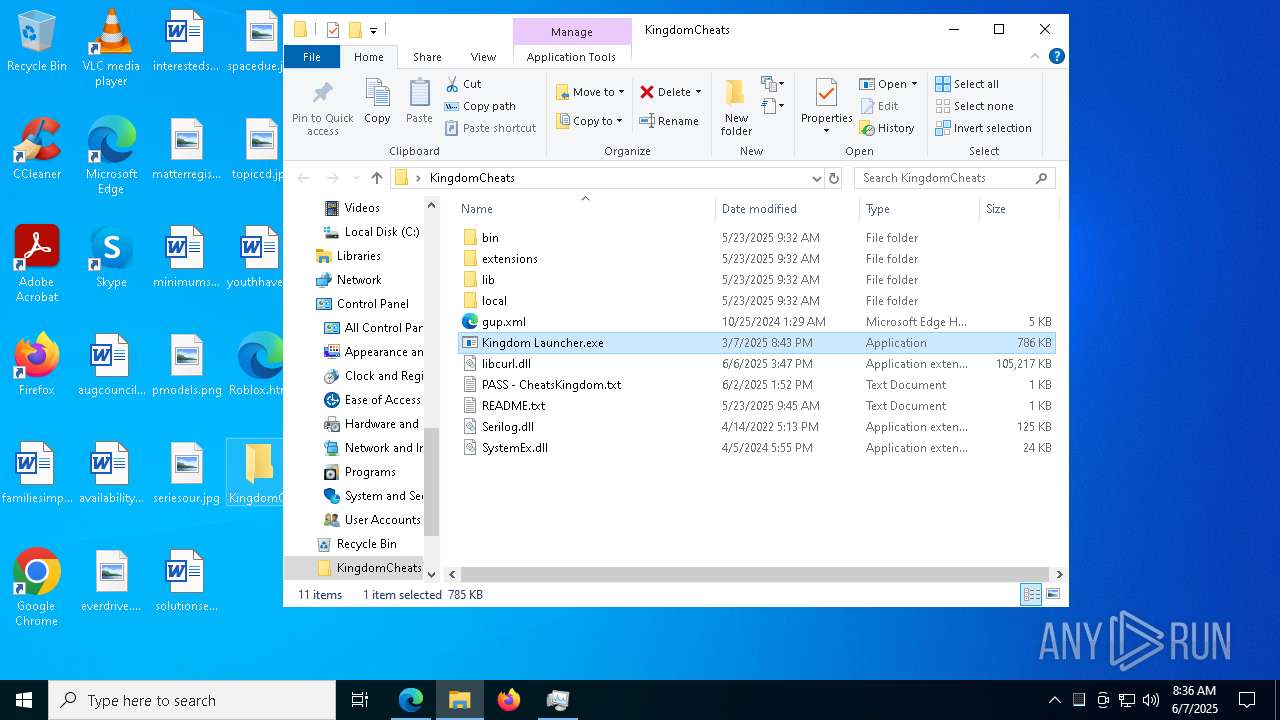
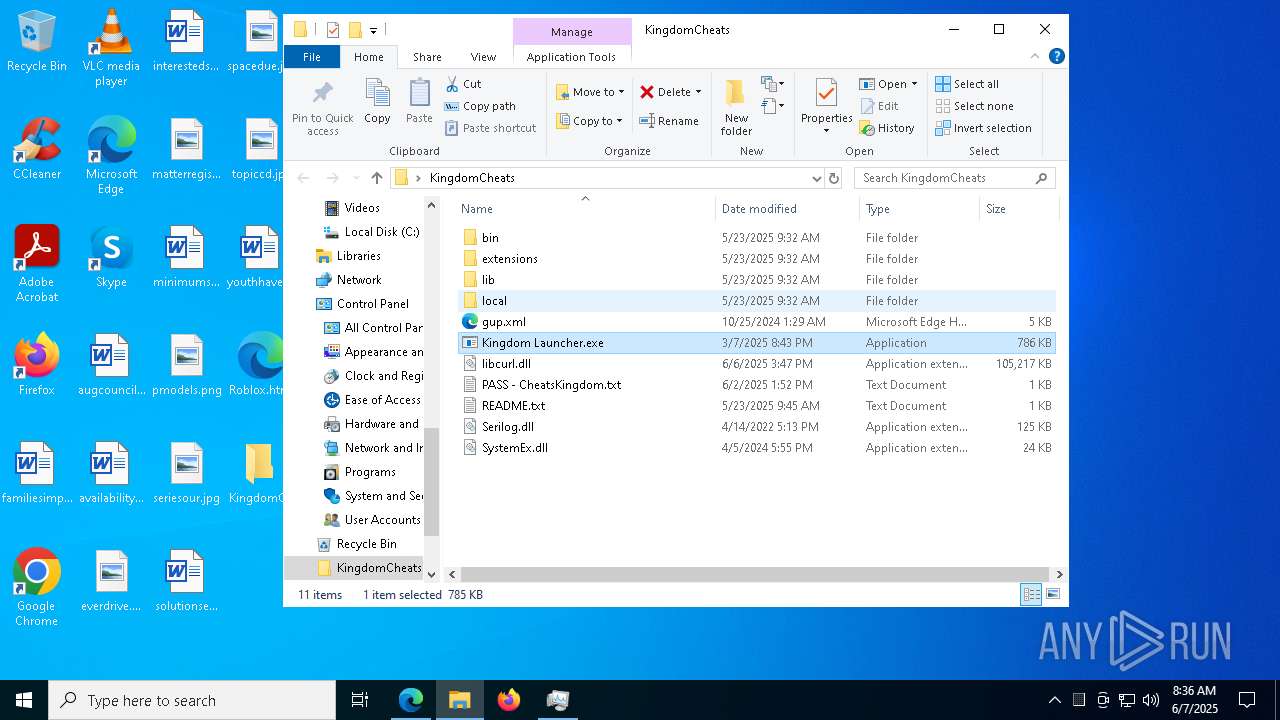
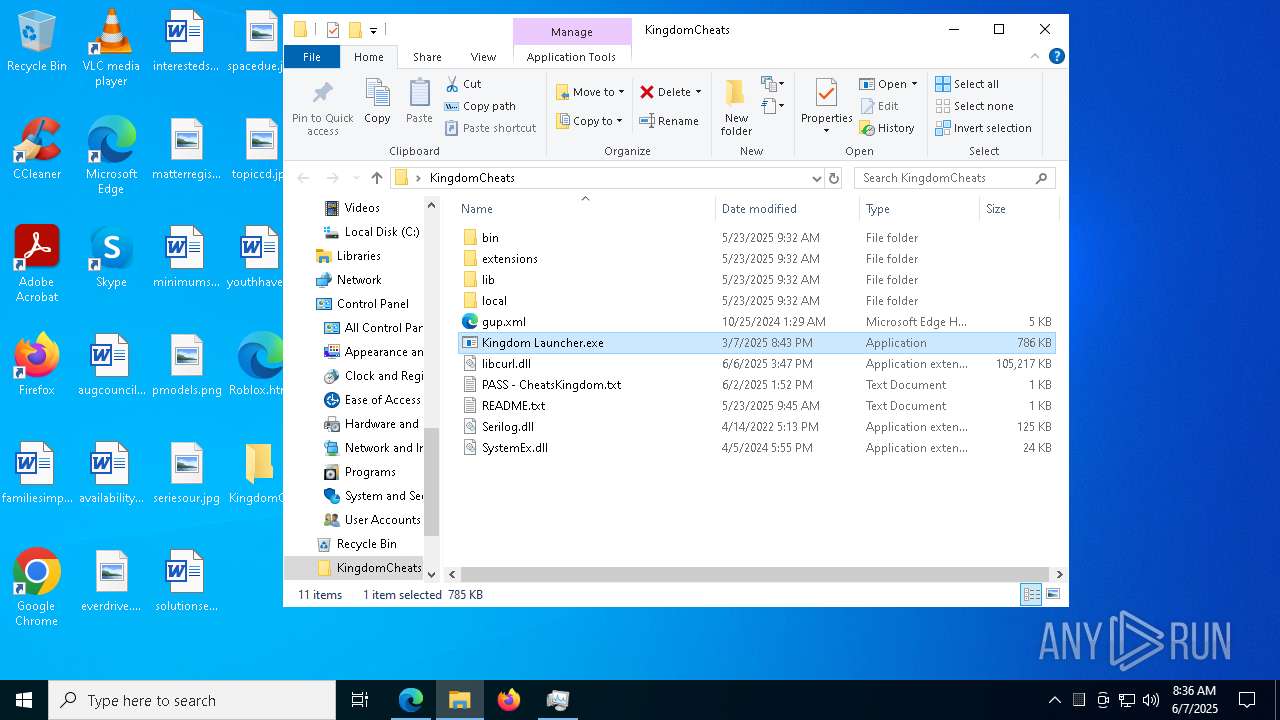
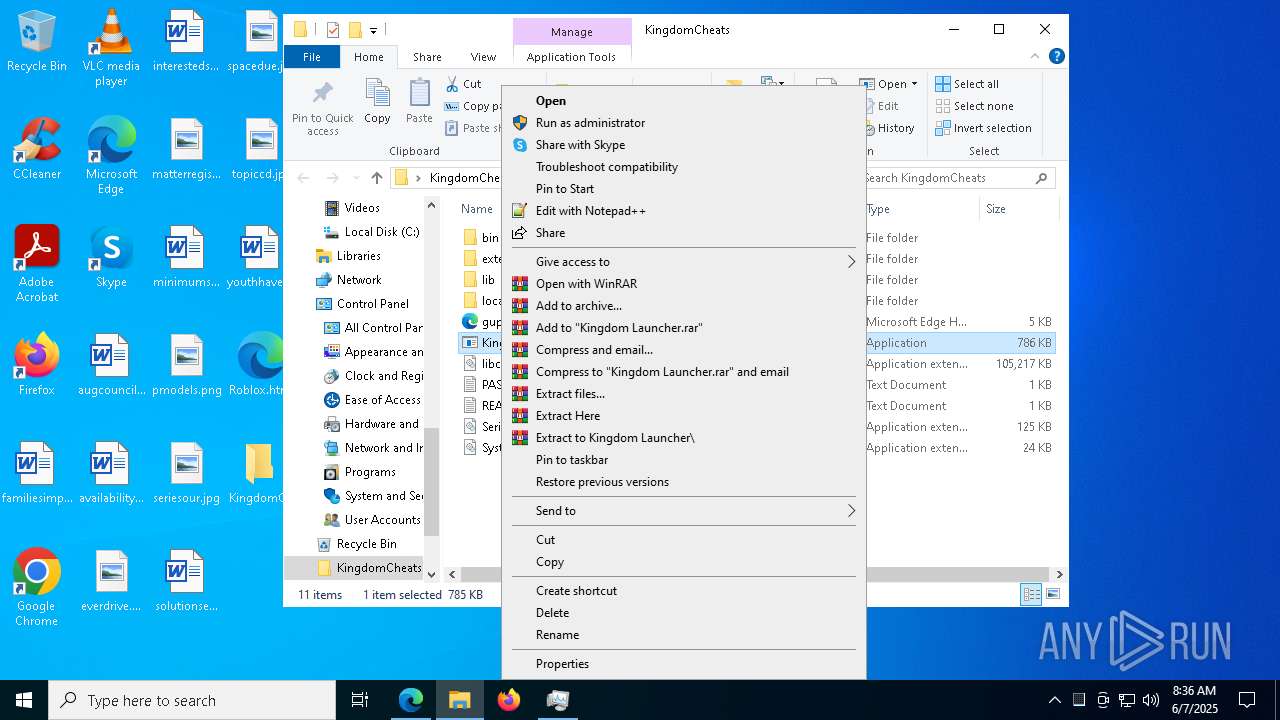
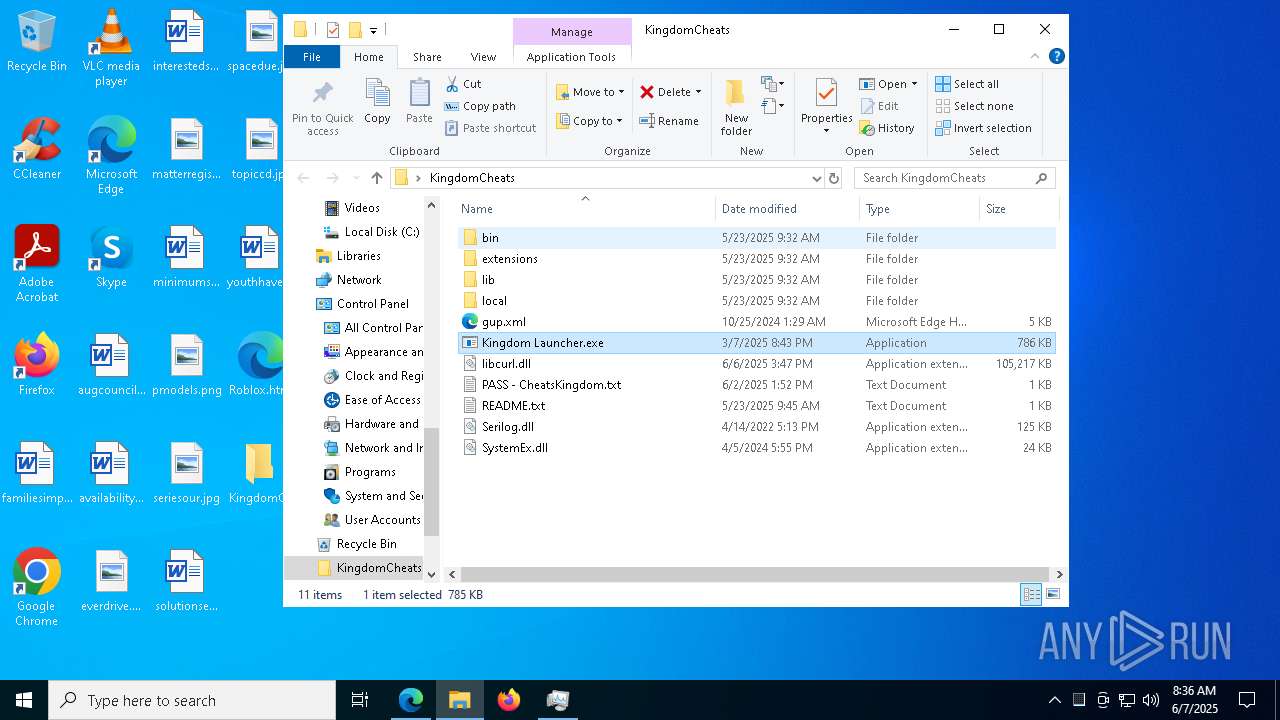
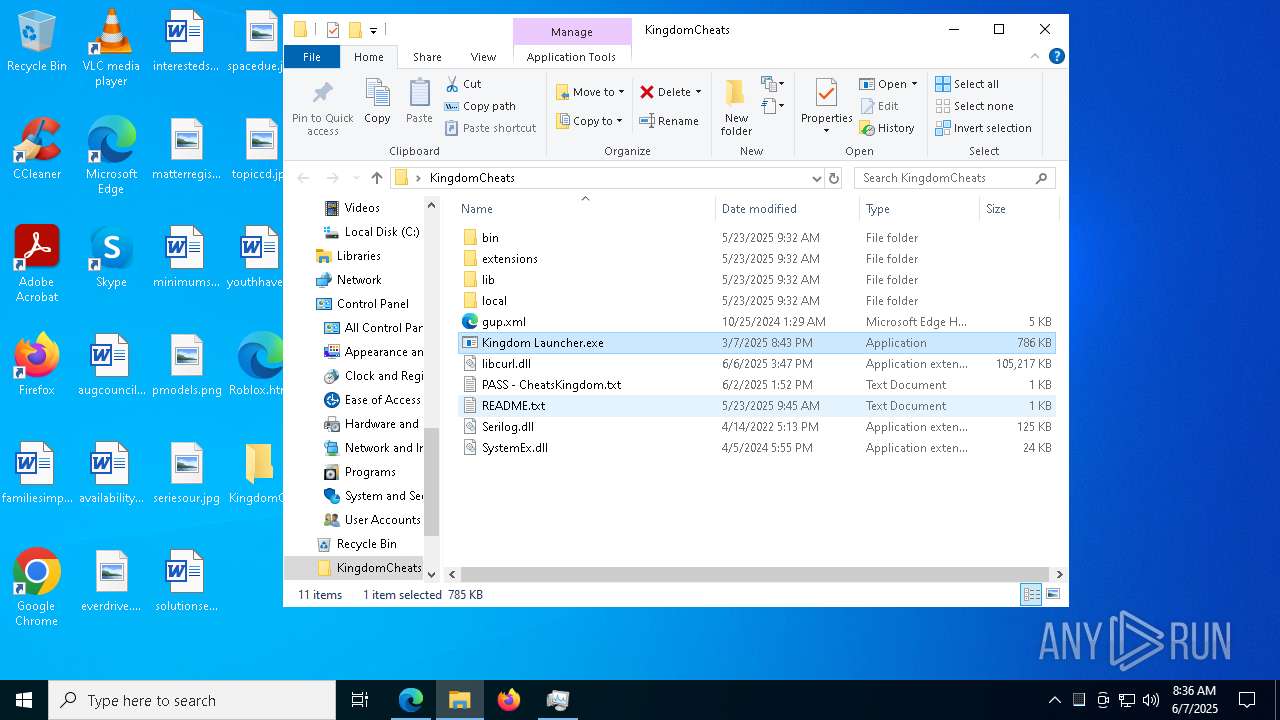
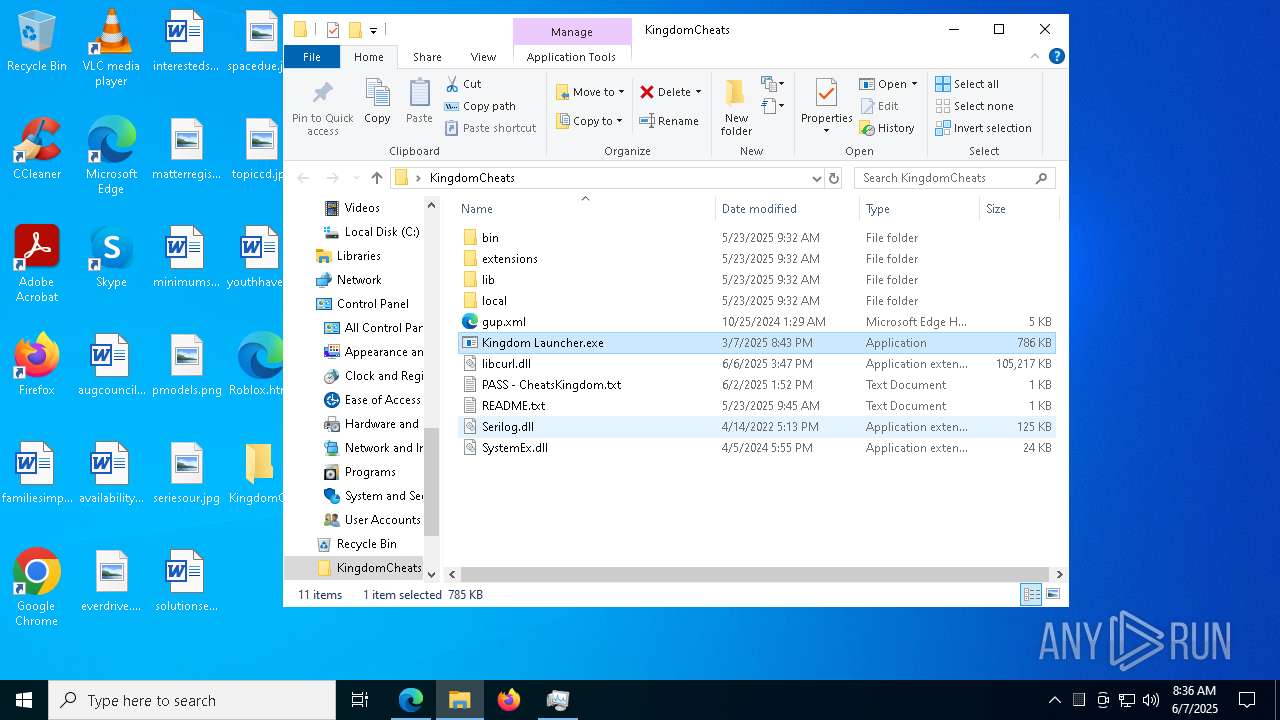
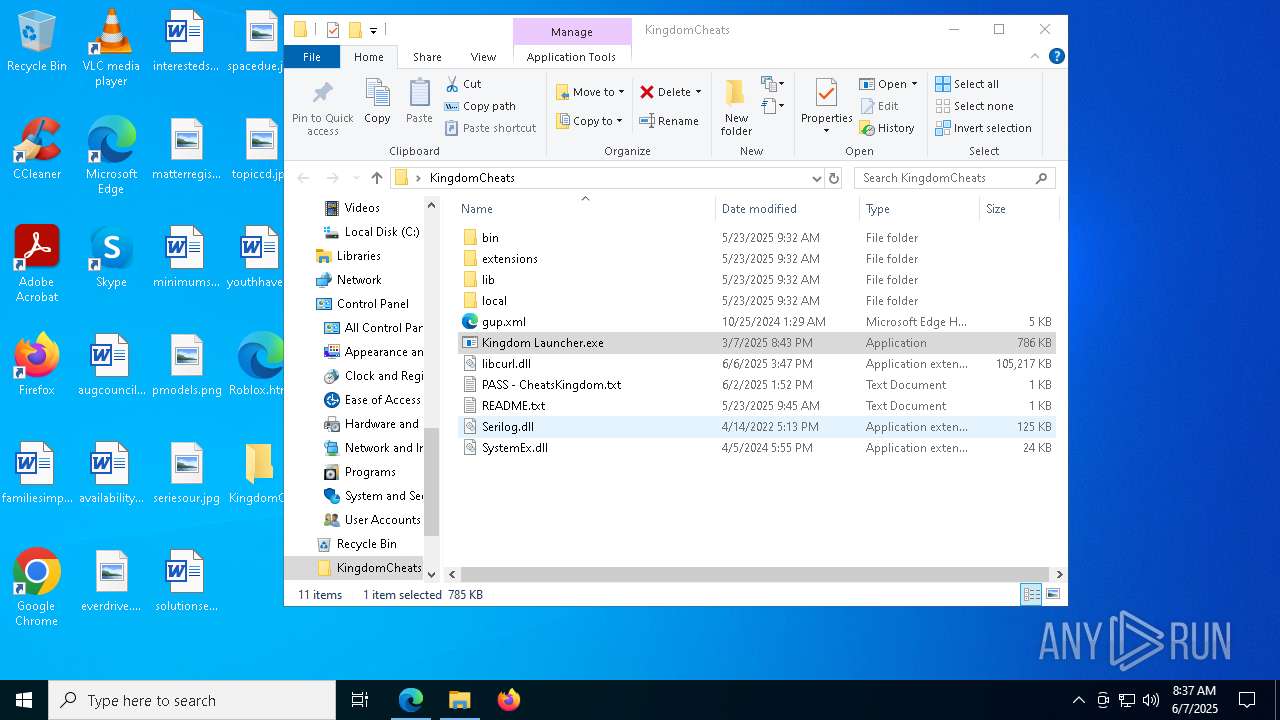
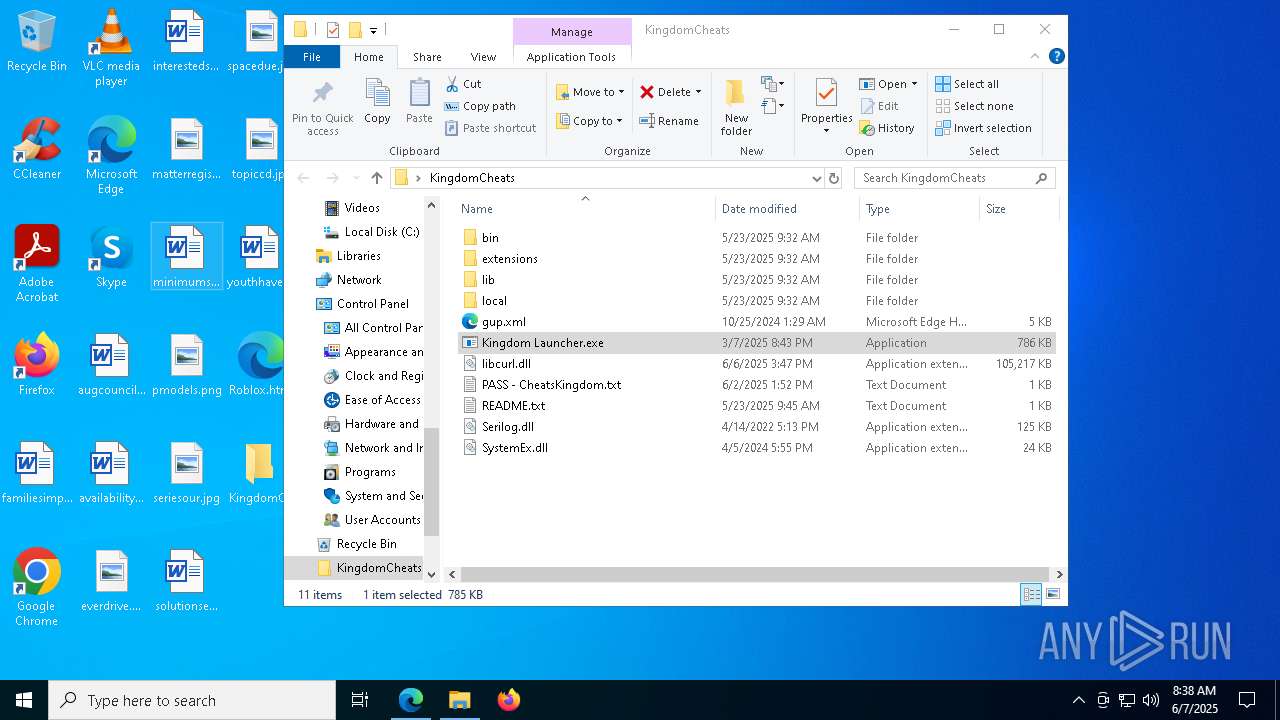
MALICIOUS
Changes Windows Defender settings
- Kingdom Launcher.exe (PID: 2796)
Adds path to the Windows Defender exclusion list
- Kingdom Launcher.exe (PID: 2796)
Adds process to the Windows Defender exclusion list
- Kingdom Launcher.exe (PID: 2796)
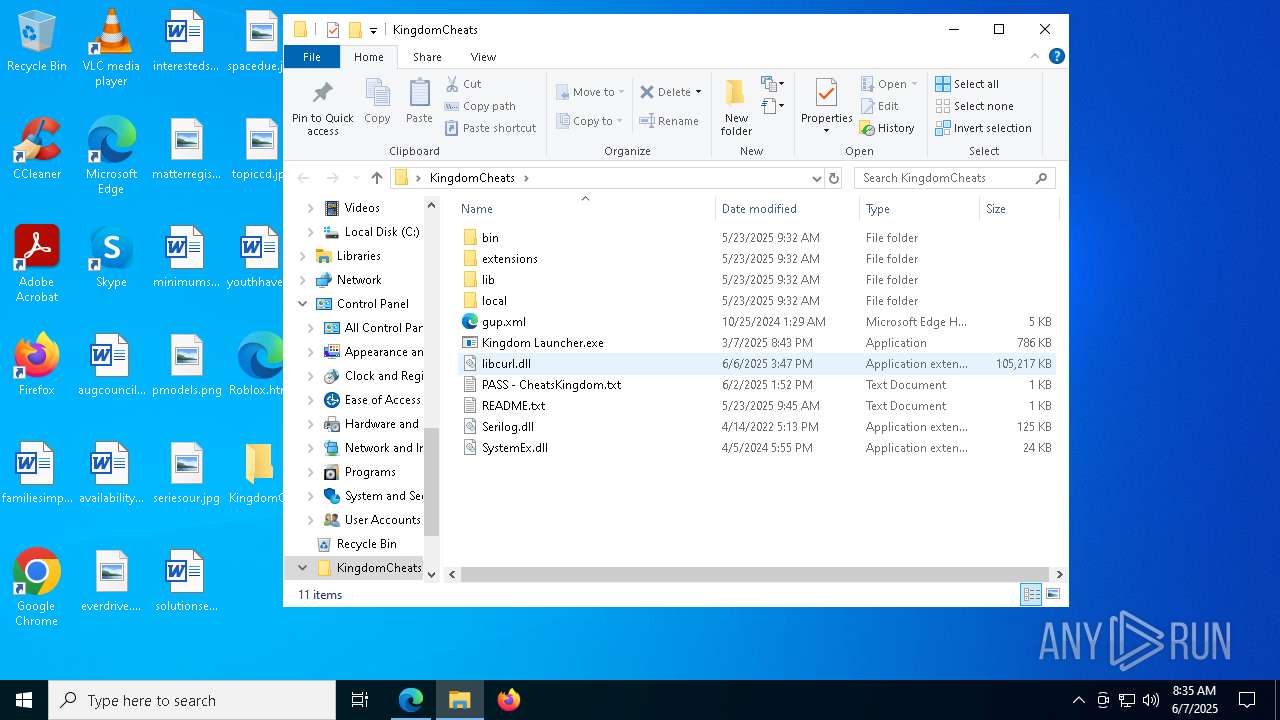
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- downloaded_0.exe (PID: 7128)
Connects to the CnC server
- svchost.exe (PID: 2196)
LUMMA has been detected (YARA)
- downloaded_0.exe (PID: 7128)
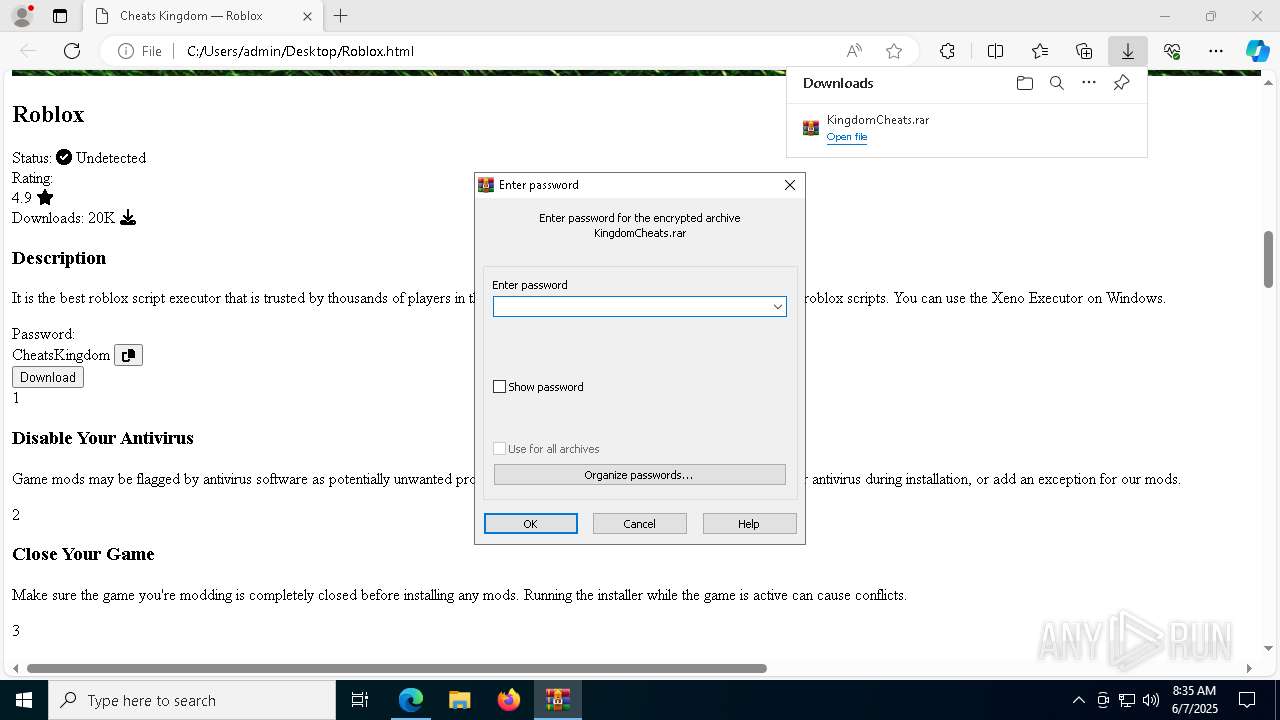
SUSPICIOUS
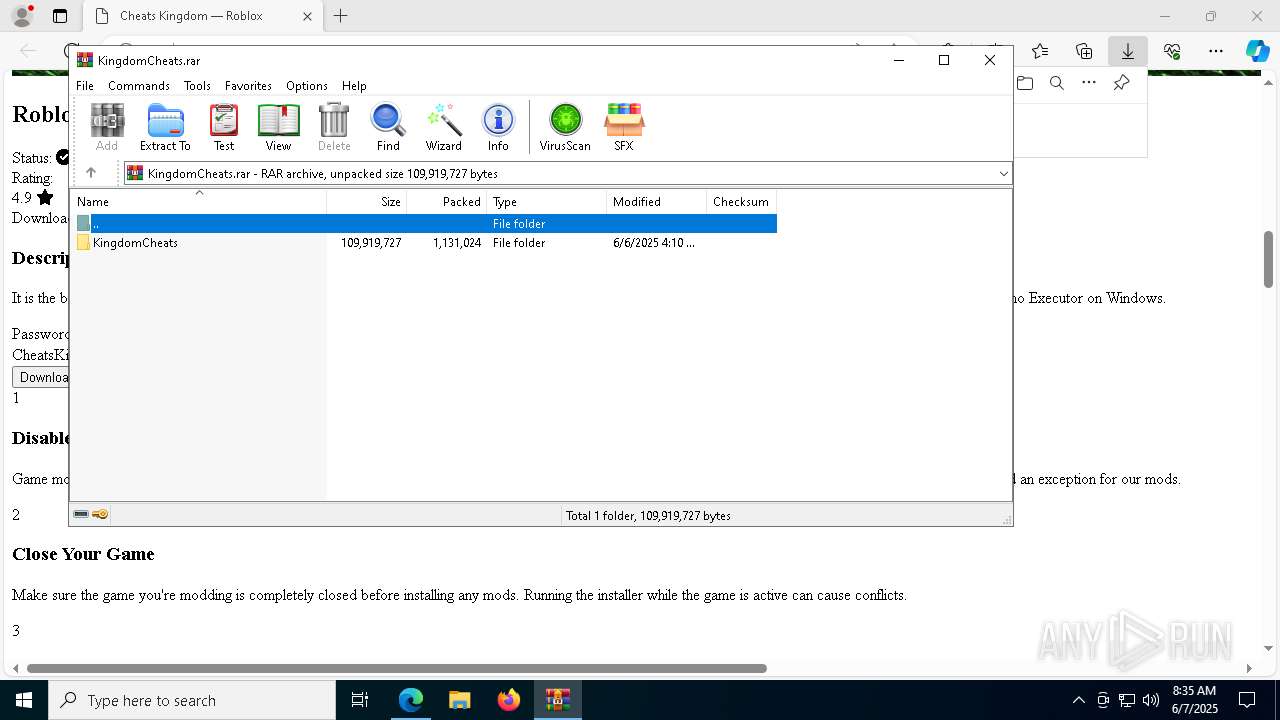
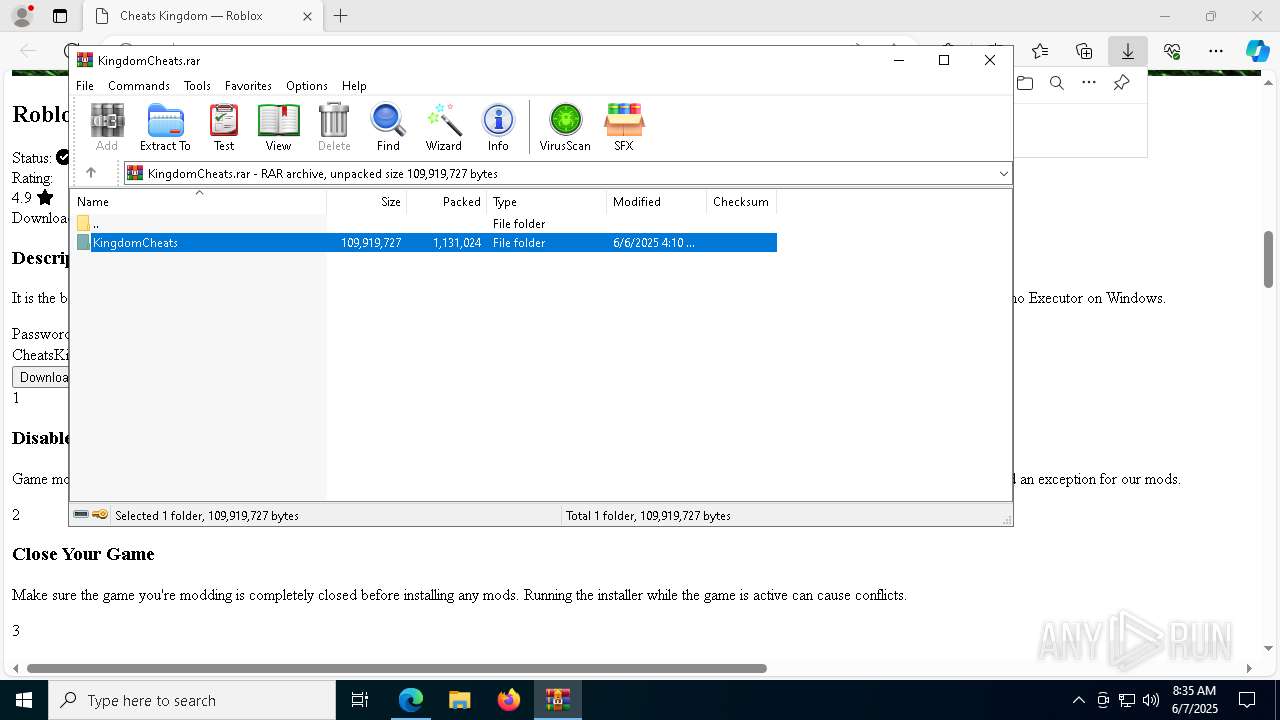
The process creates files with name similar to system file names
- WinRAR.exe (PID: 7304)
Process drops legitimate windows executable
- WinRAR.exe (PID: 7304)
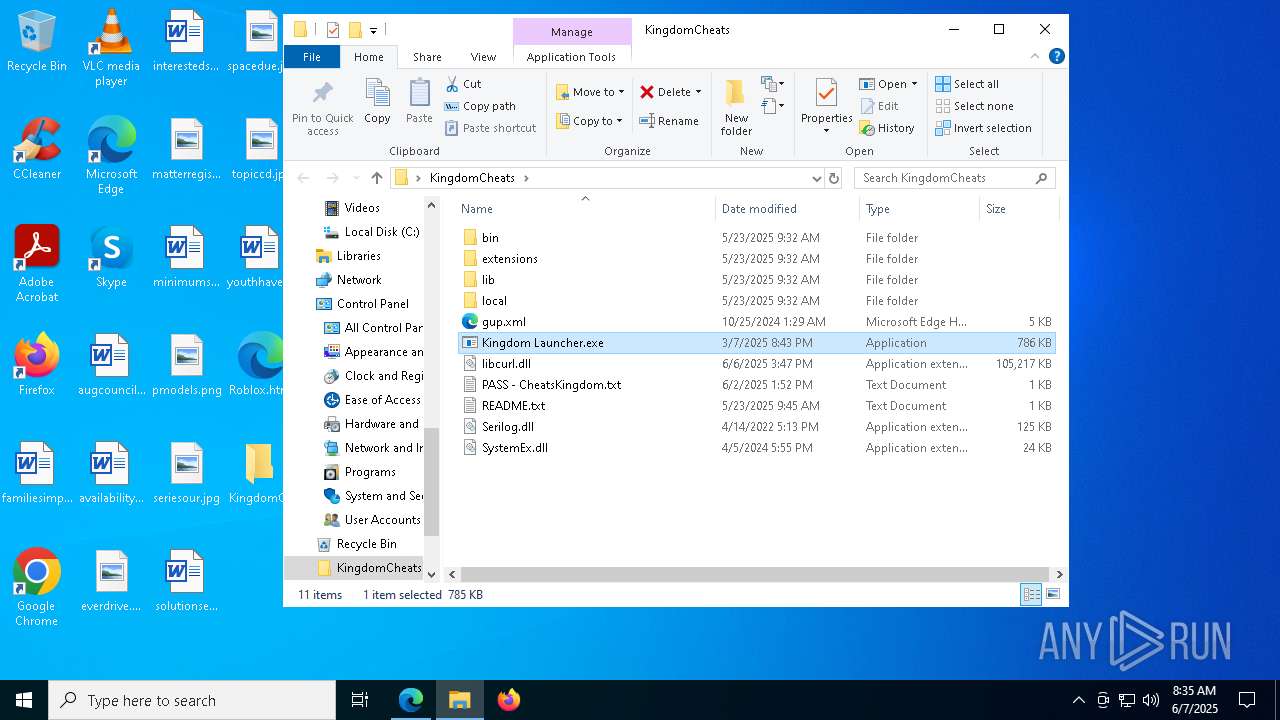
Executable content was dropped or overwritten
- Kingdom Launcher.exe (PID: 7752)
- Kingdom Launcher.exe (PID: 2796)
Reads security settings of Internet Explorer
- Kingdom Launcher.exe (PID: 7752)
- Kingdom Launcher.exe (PID: 2796)
Reads the date of Windows installation
- Kingdom Launcher.exe (PID: 7752)
Starts POWERSHELL.EXE for commands execution
- Kingdom Launcher.exe (PID: 2796)
Script adds exclusion path to Windows Defender
- Kingdom Launcher.exe (PID: 2796)
There is functionality for taking screenshot (YARA)
- Kingdom Launcher.exe (PID: 2796)
- downloaded_0.exe (PID: 7128)
Starts itself from another location
- Kingdom Launcher.exe (PID: 7752)
Script adds exclusion process to Windows Defender
- Kingdom Launcher.exe (PID: 2796)
Application launched itself
- downloaded_0.exe (PID: 2560)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- downloaded_0.exe (PID: 7128)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- downloaded_0.exe (PID: 7128)
INFO
Checks supported languages
- identity_helper.exe (PID: 8080)
- Kingdom Launcher.exe (PID: 7752)
- Kingdom Launcher.exe (PID: 2796)
Application launched itself
- msedge.exe (PID: 2104)
Reads Environment values
- identity_helper.exe (PID: 8080)
Reads the computer name
- identity_helper.exe (PID: 8080)
- Kingdom Launcher.exe (PID: 7752)
- Kingdom Launcher.exe (PID: 2796)
Reads Microsoft Office registry keys
- msedge.exe (PID: 2104)
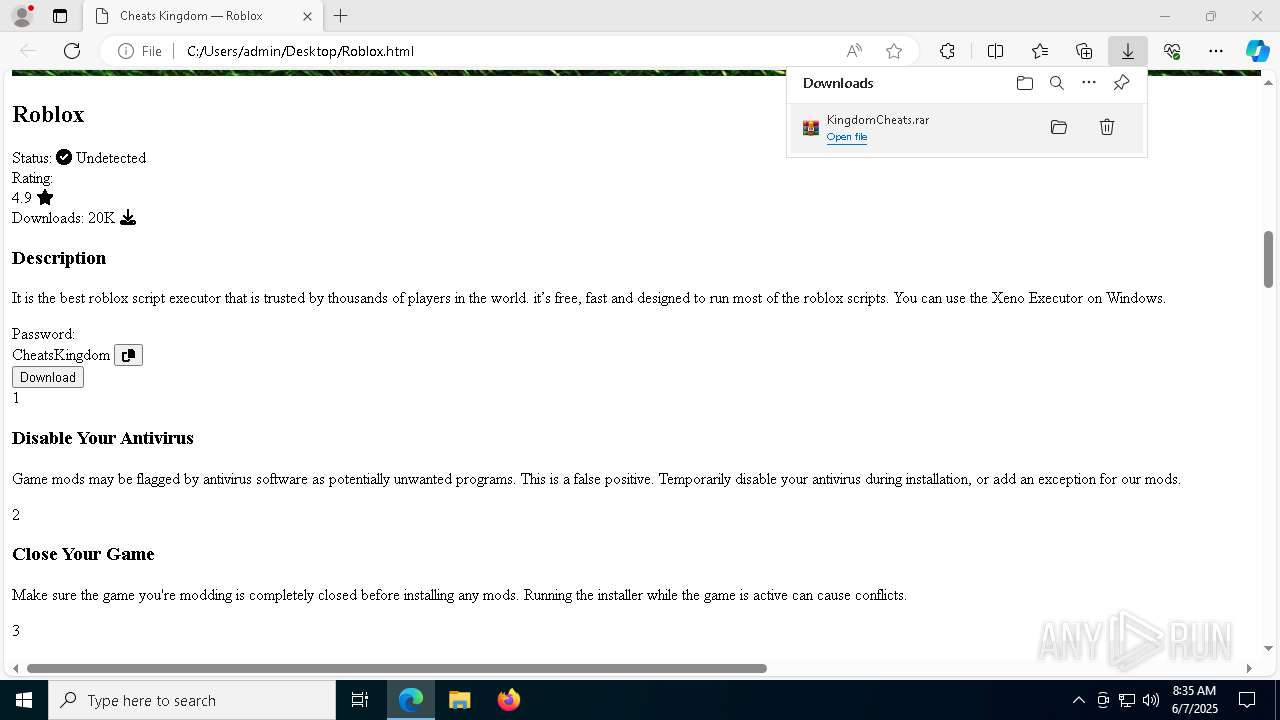
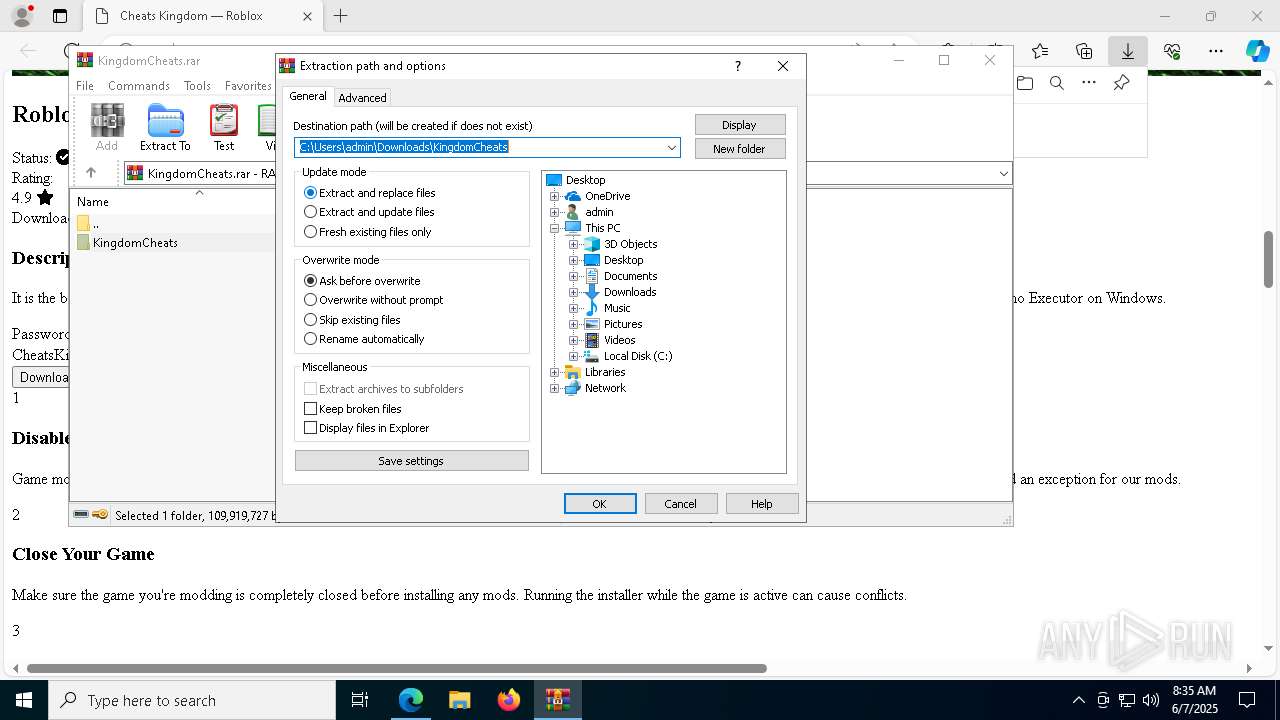
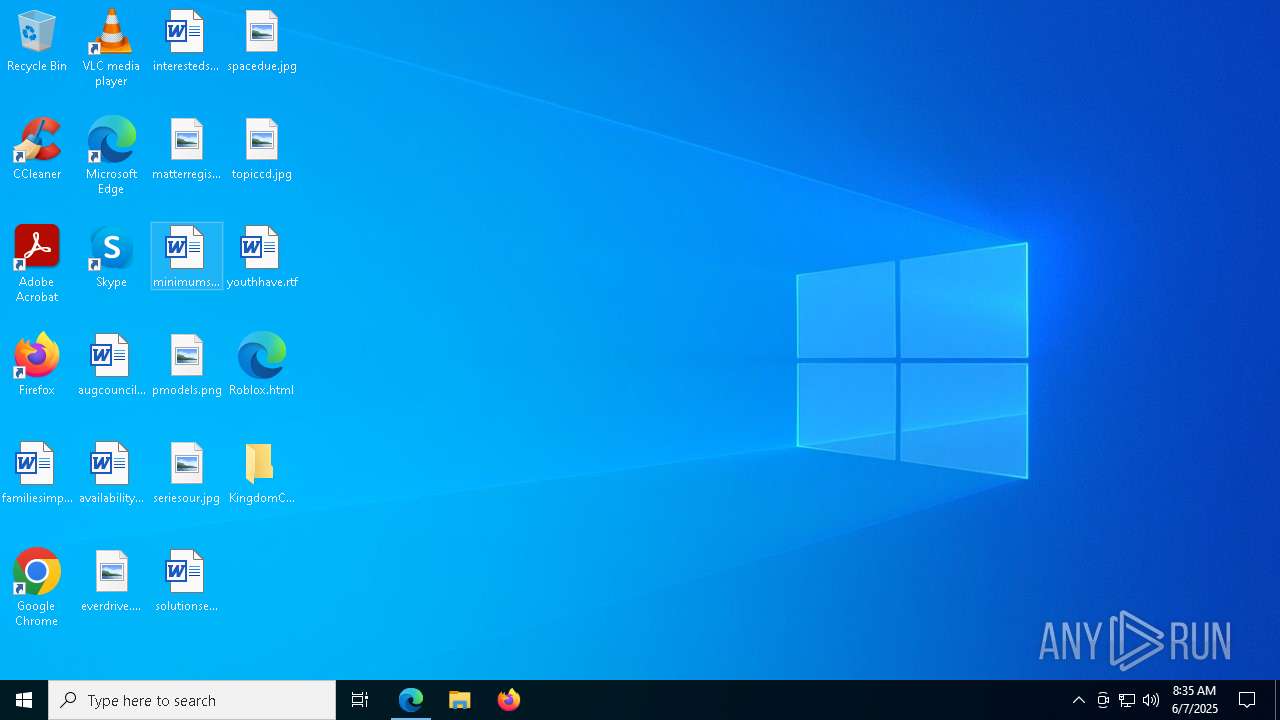
Launching a file from the Downloads directory
- msedge.exe (PID: 2104)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7304)
- msedge.exe (PID: 7484)
The sample compiled with russian language support
- WinRAR.exe (PID: 7304)
- Kingdom Launcher.exe (PID: 2796)
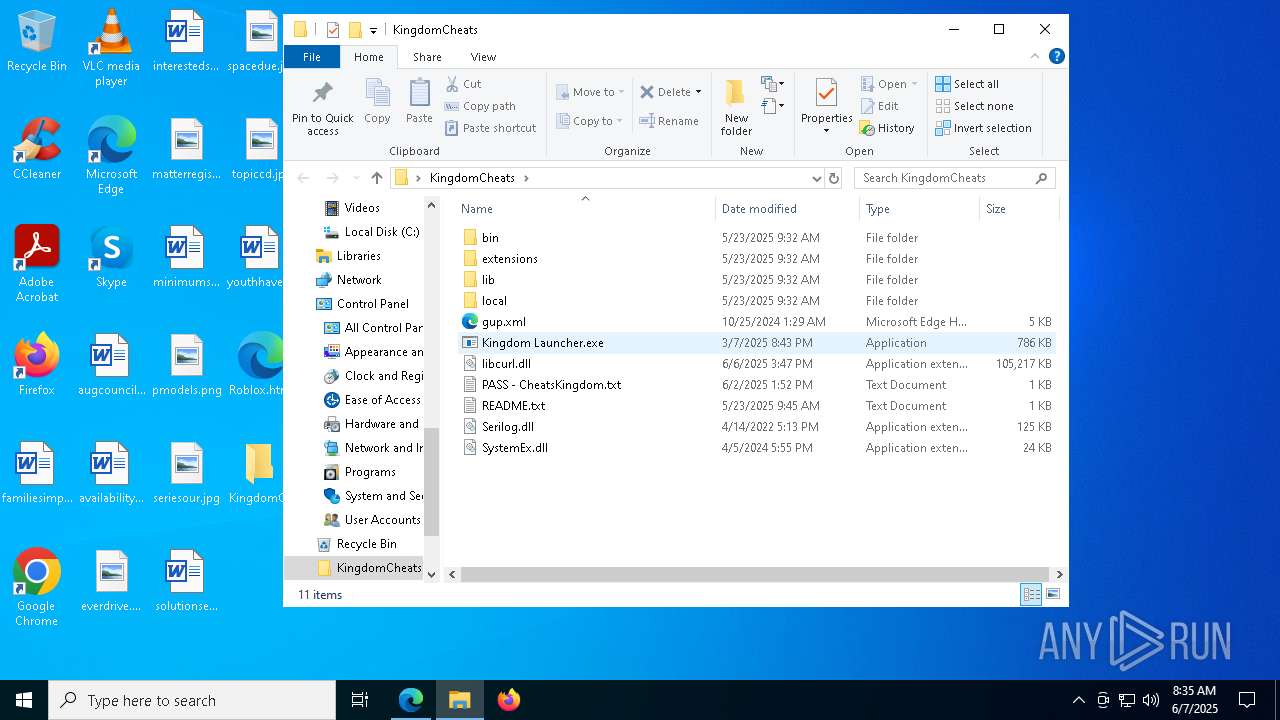
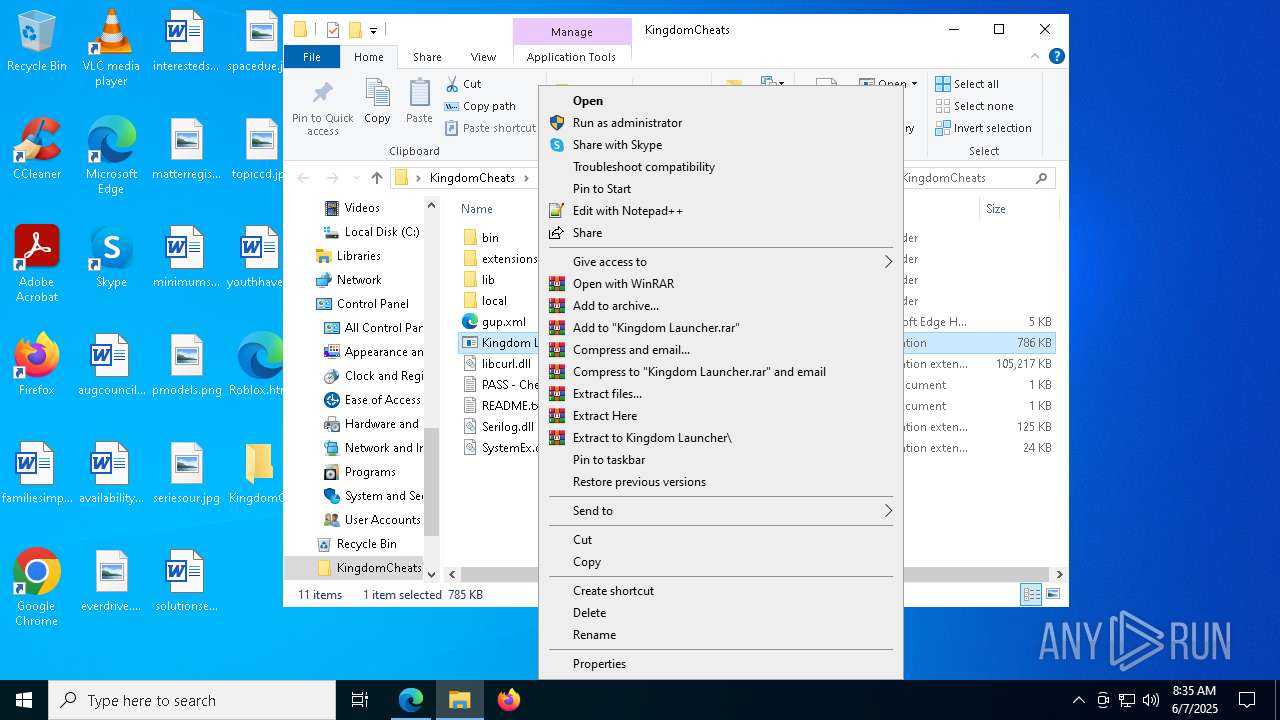
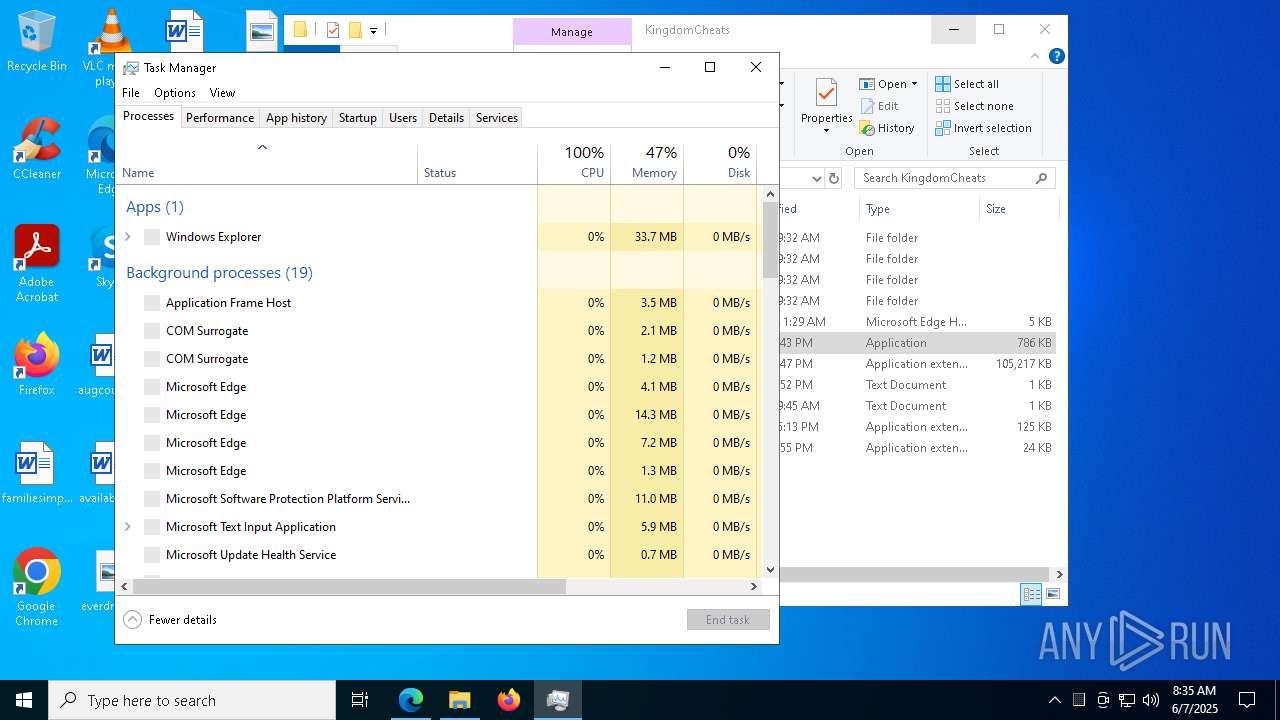
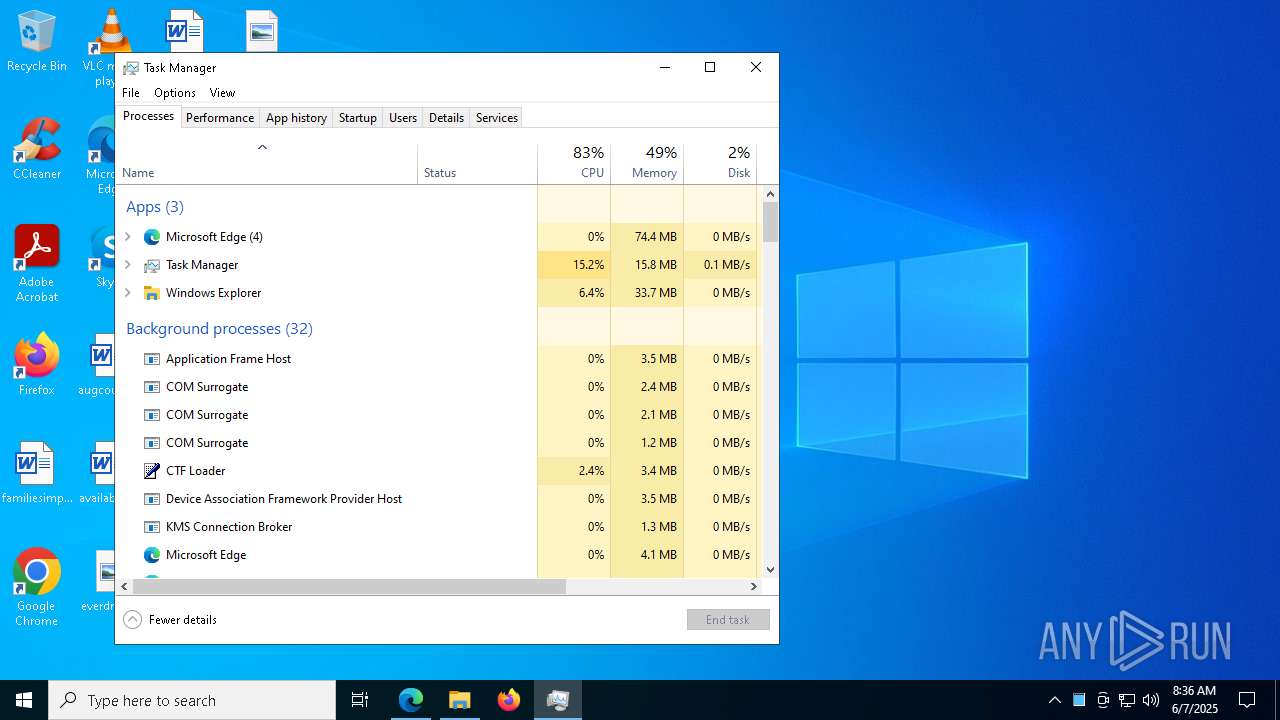
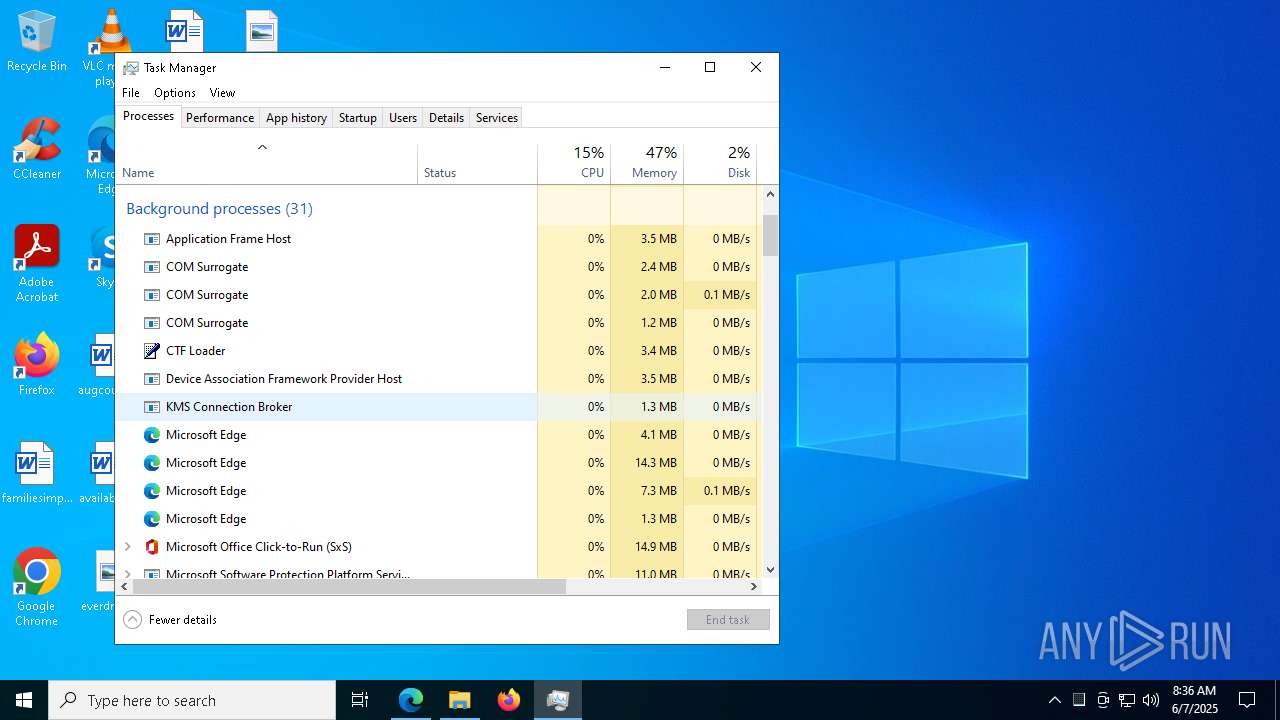
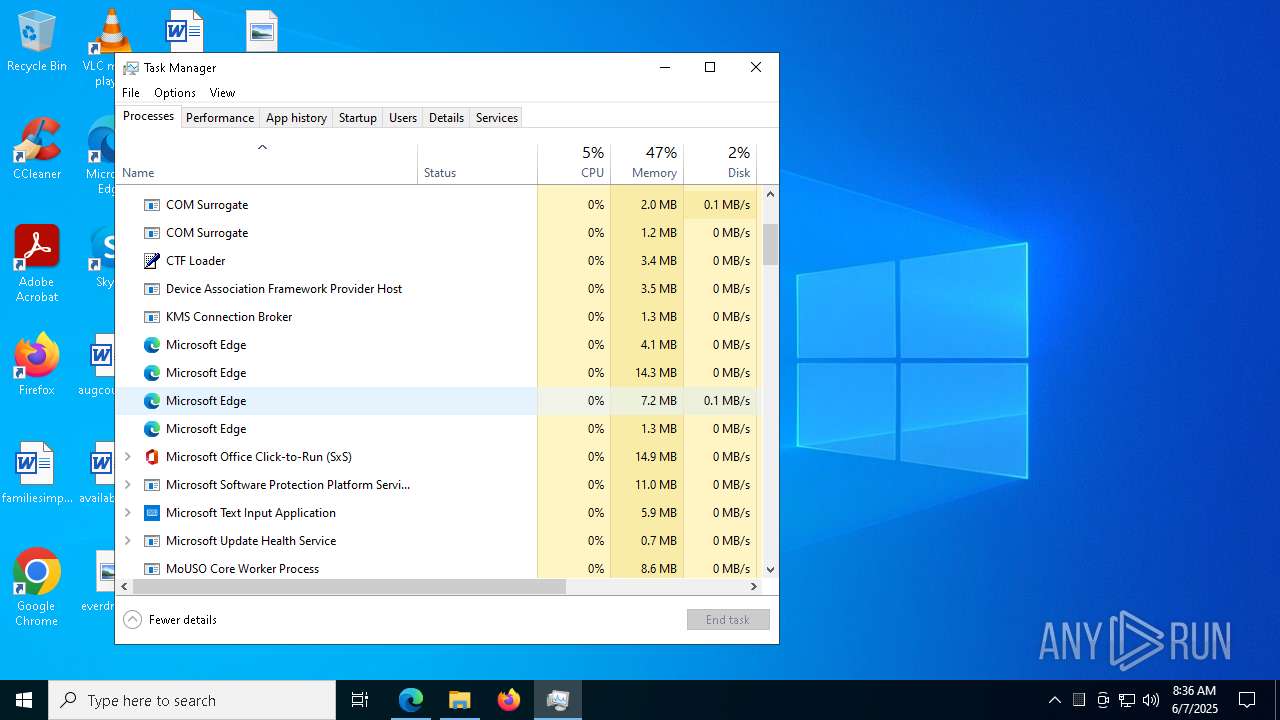
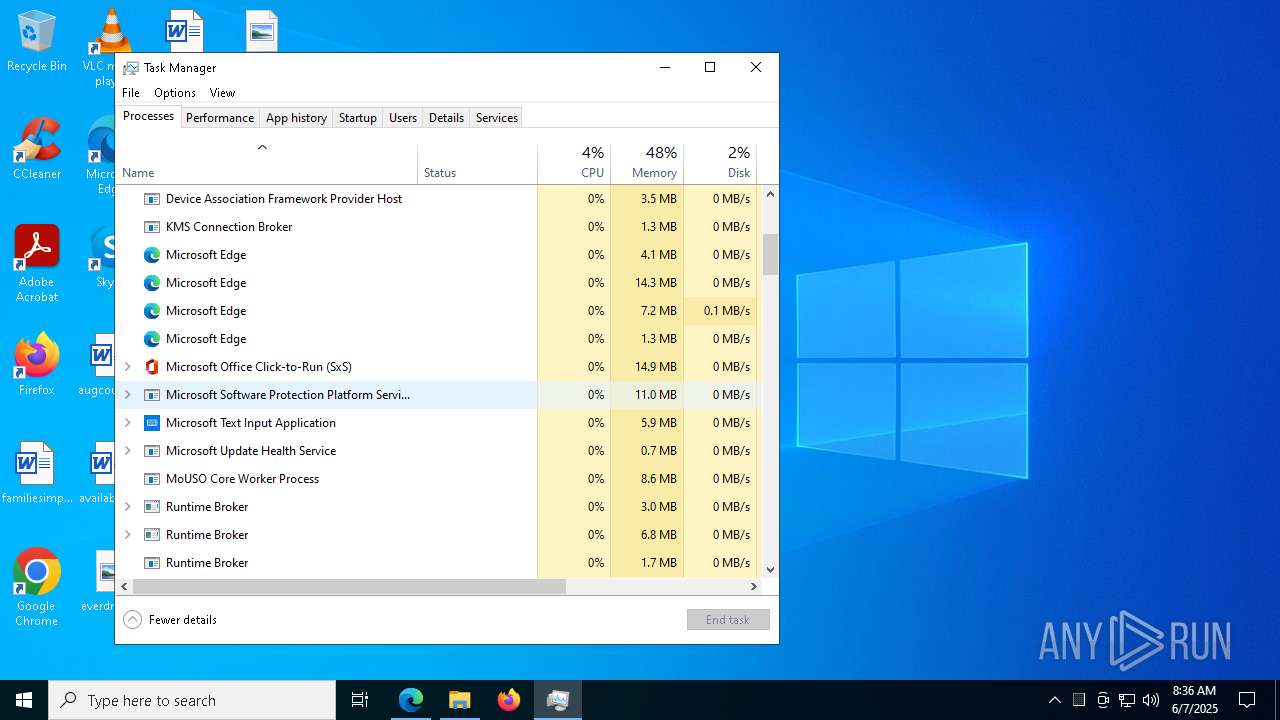
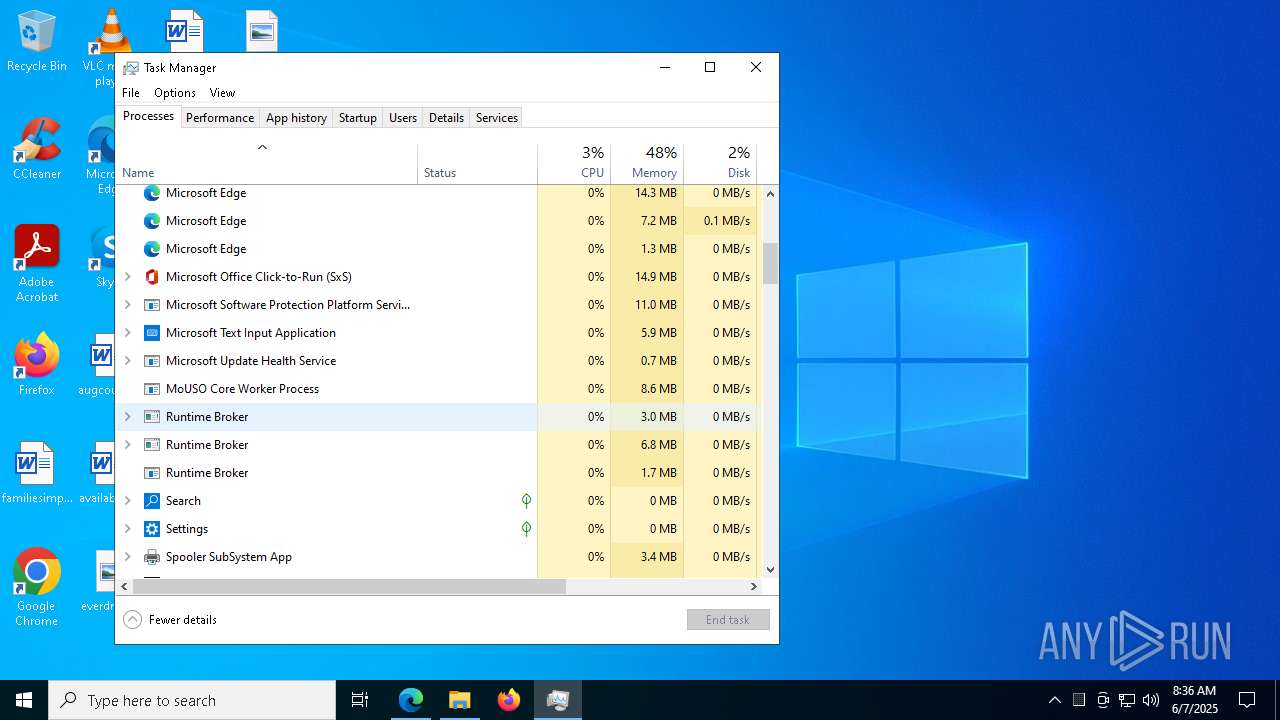
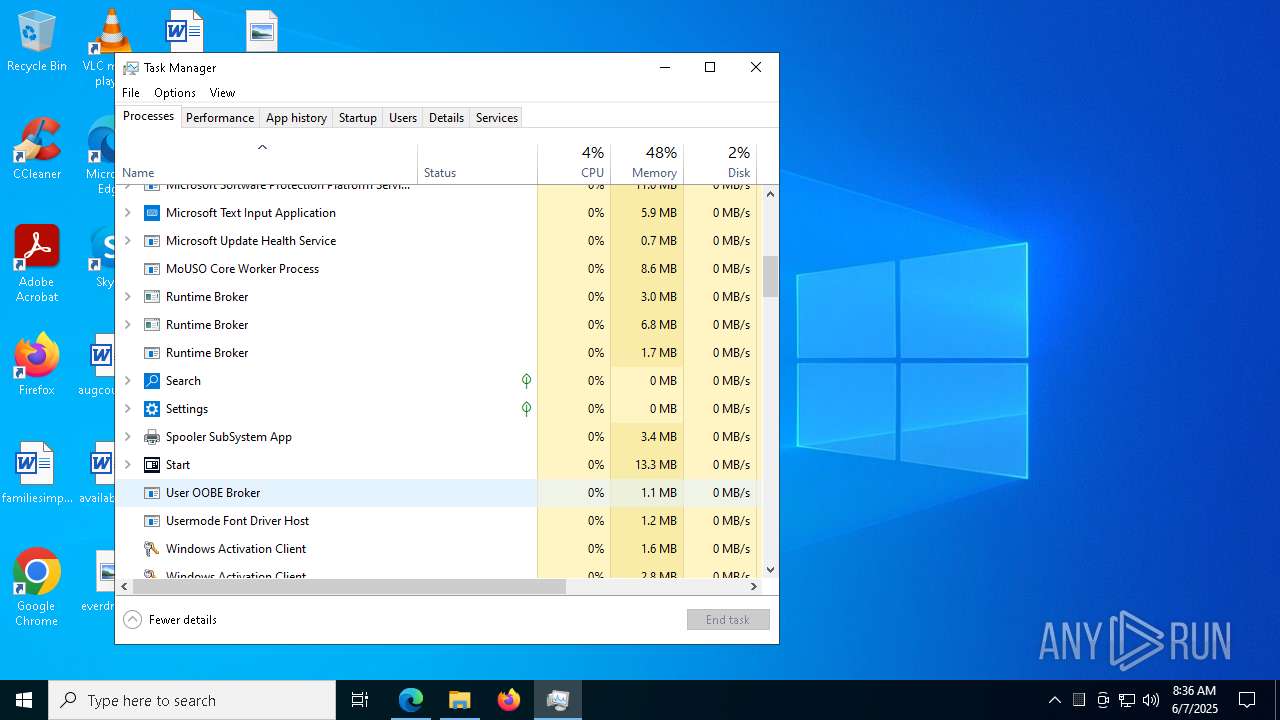
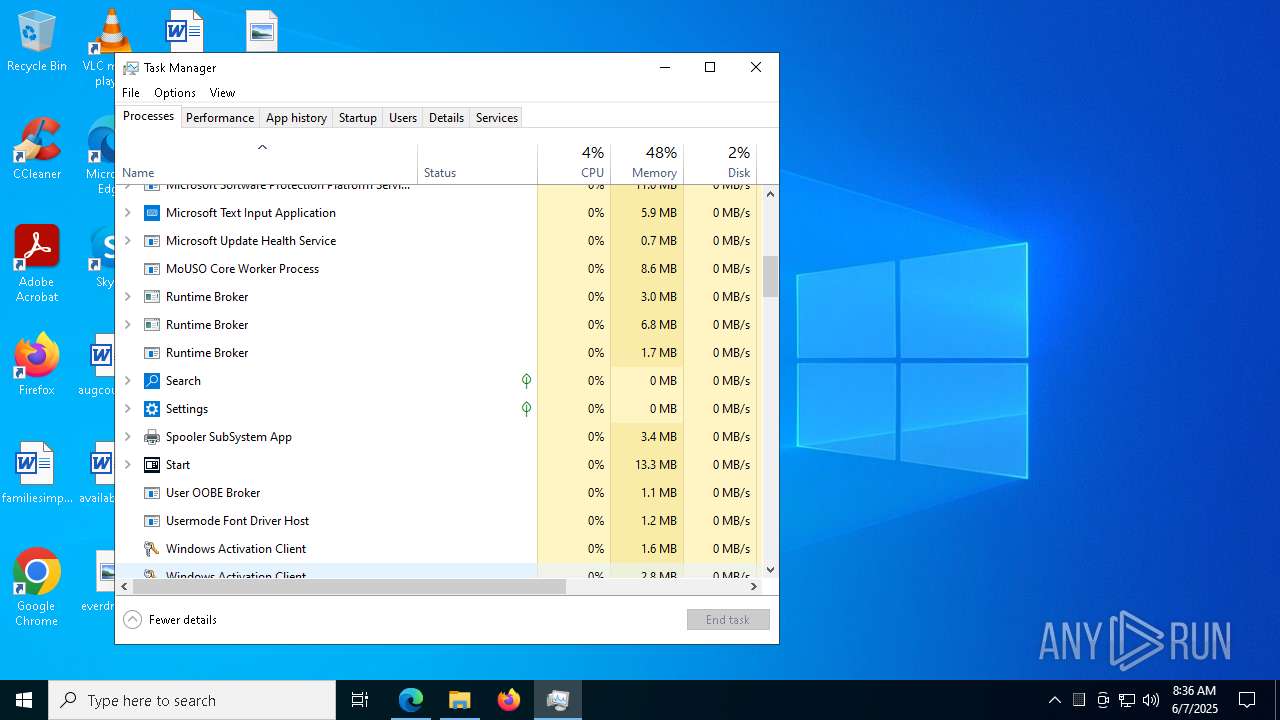
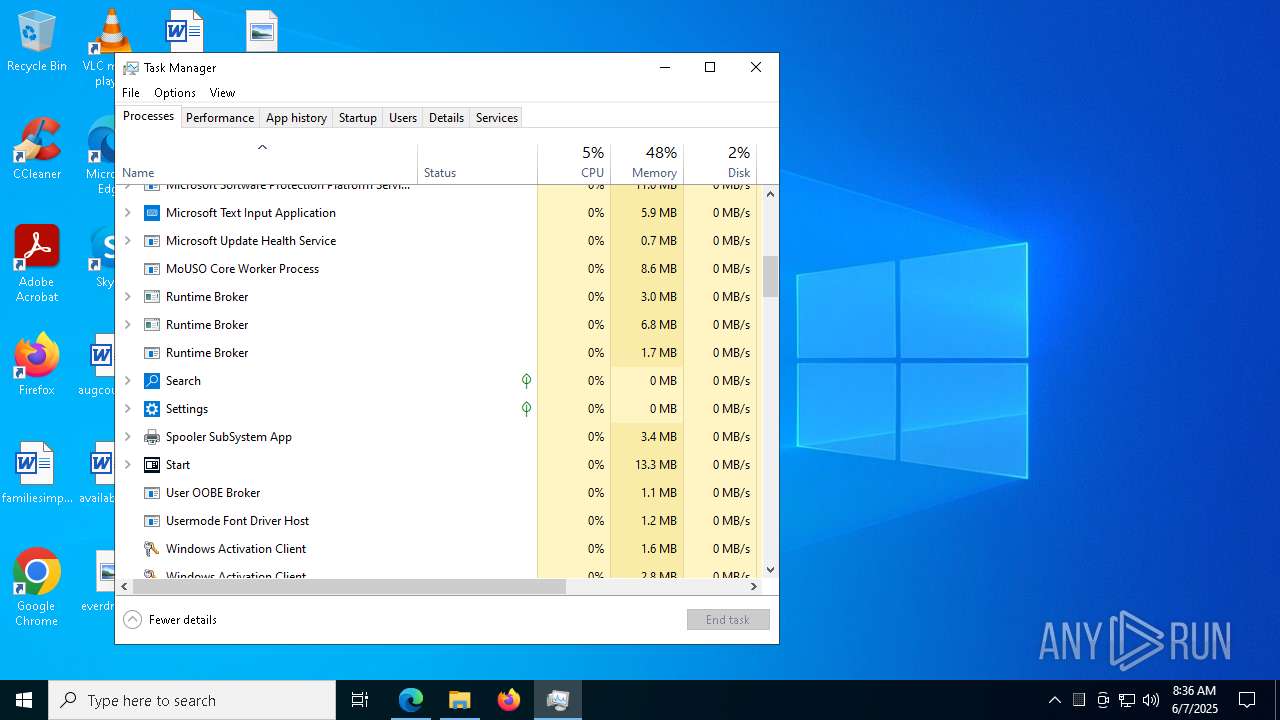
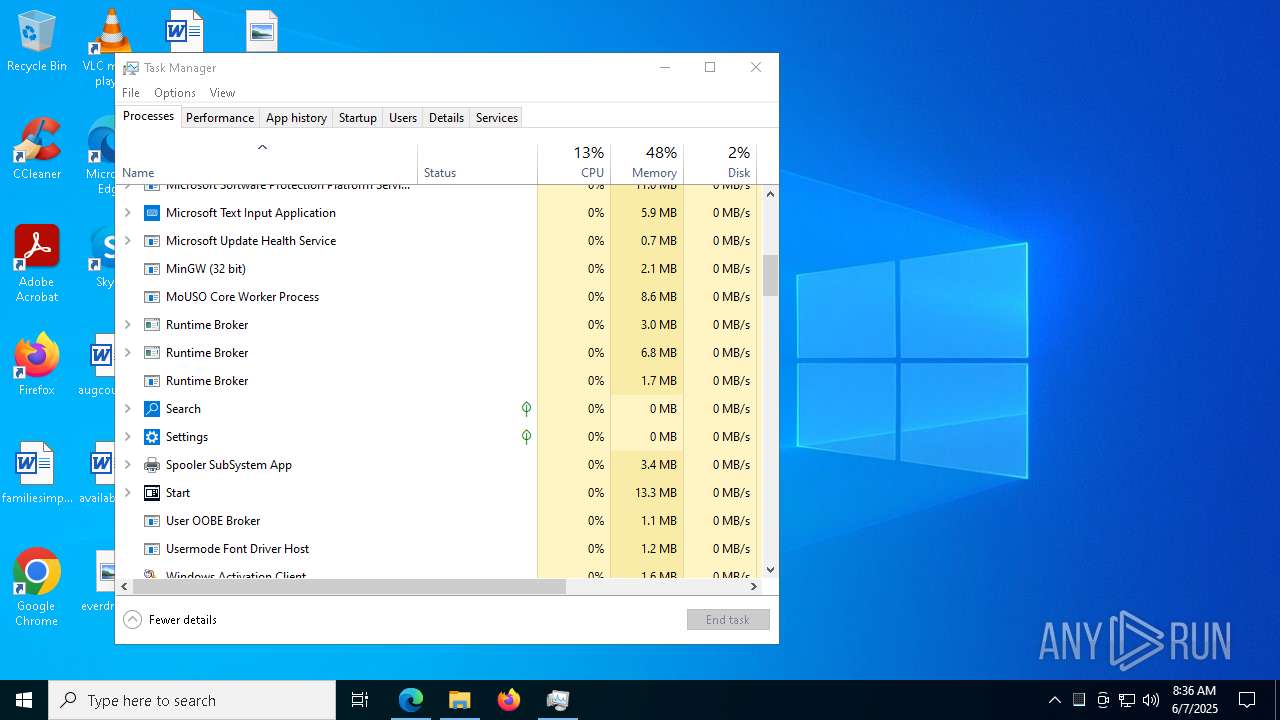
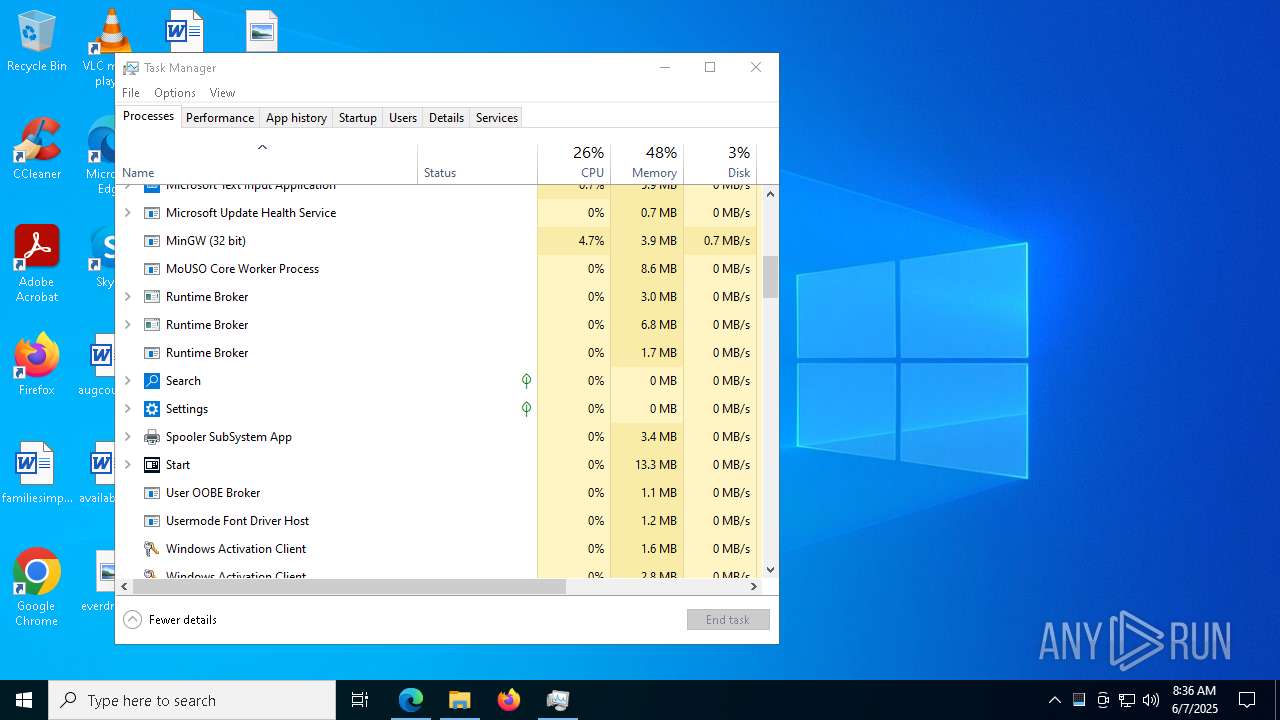
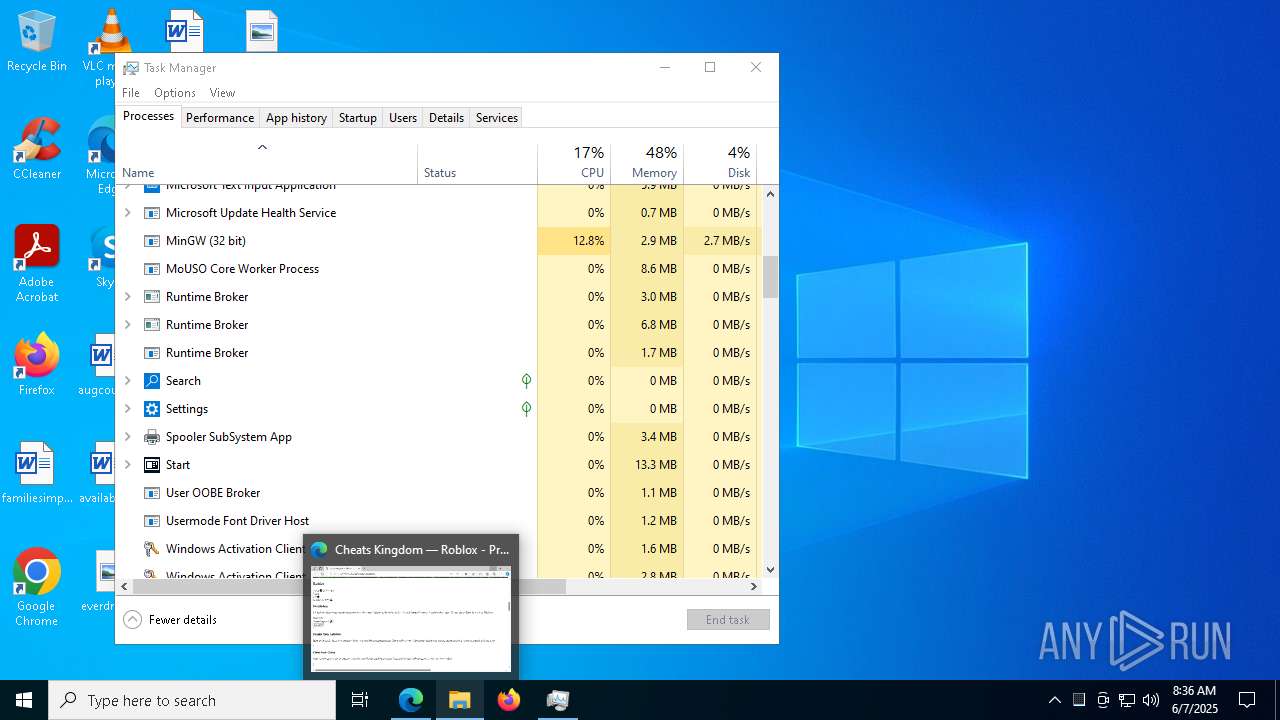
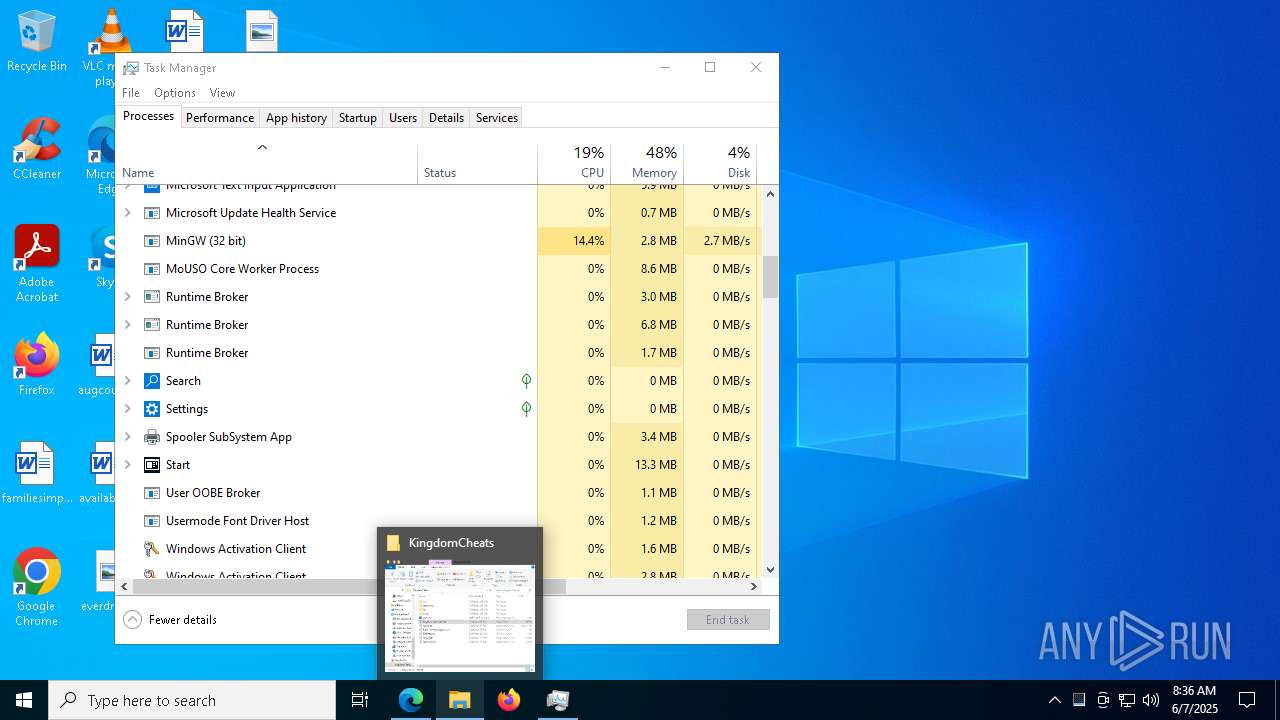
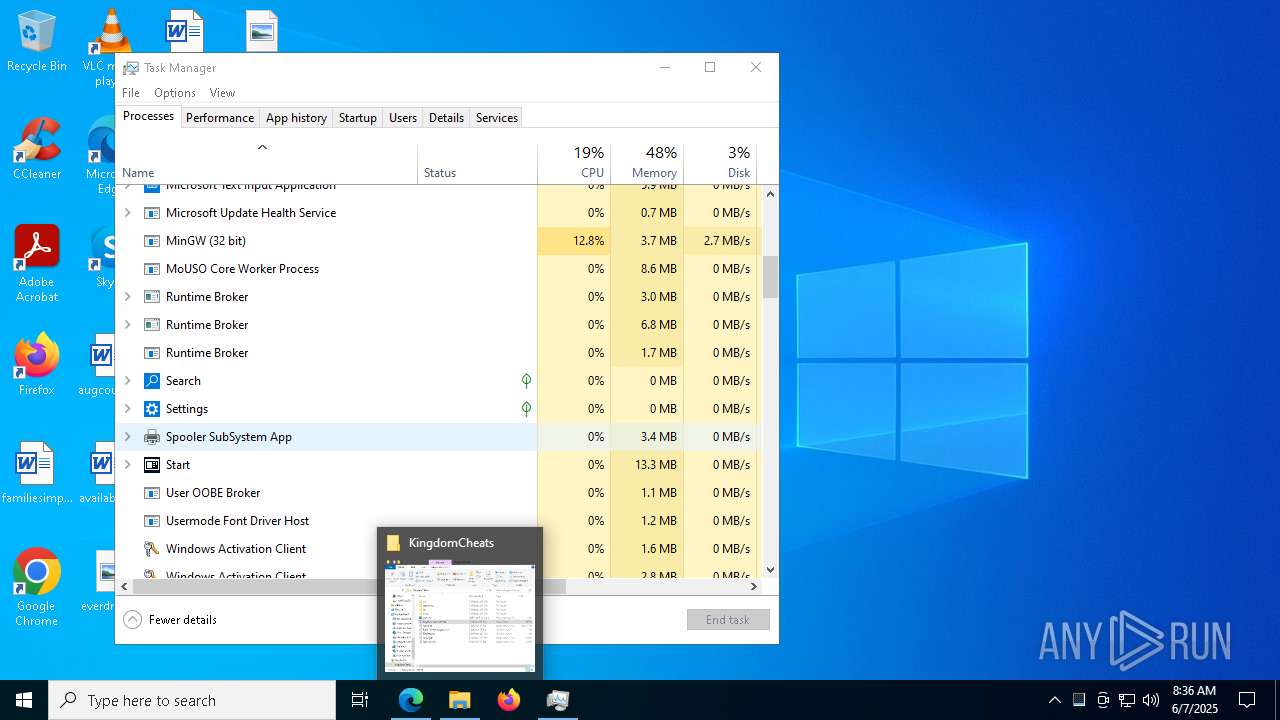
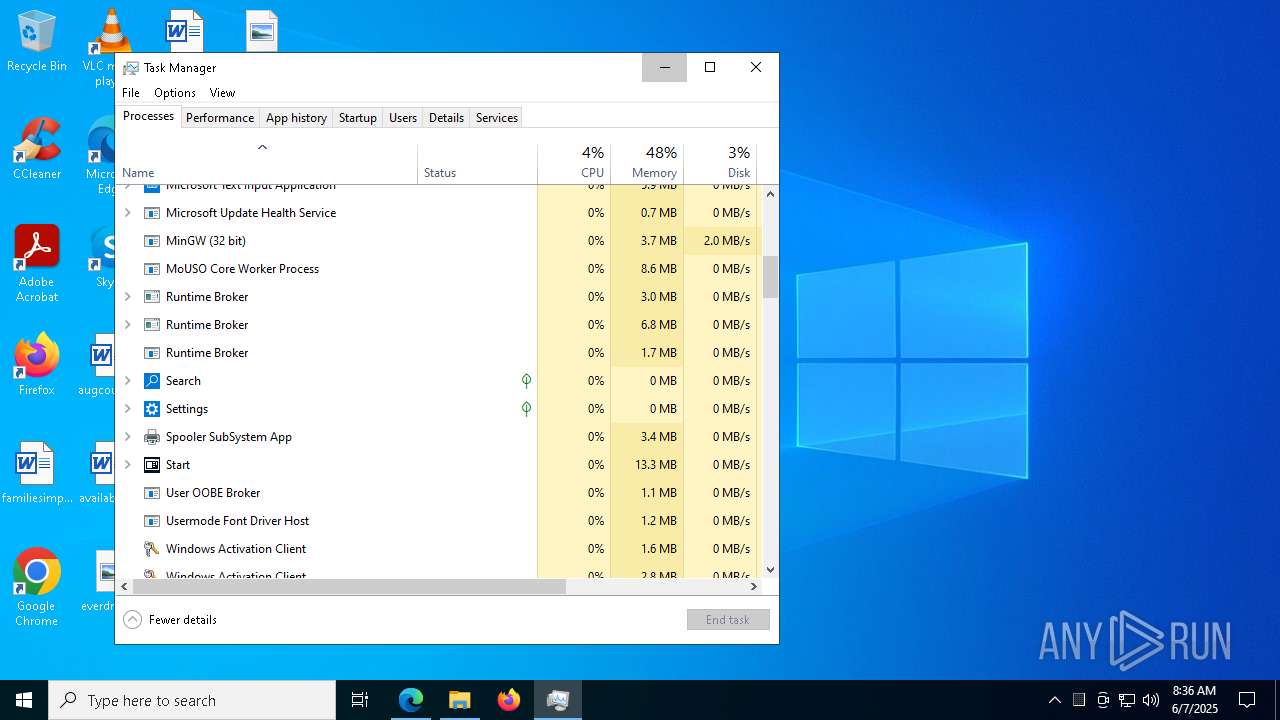
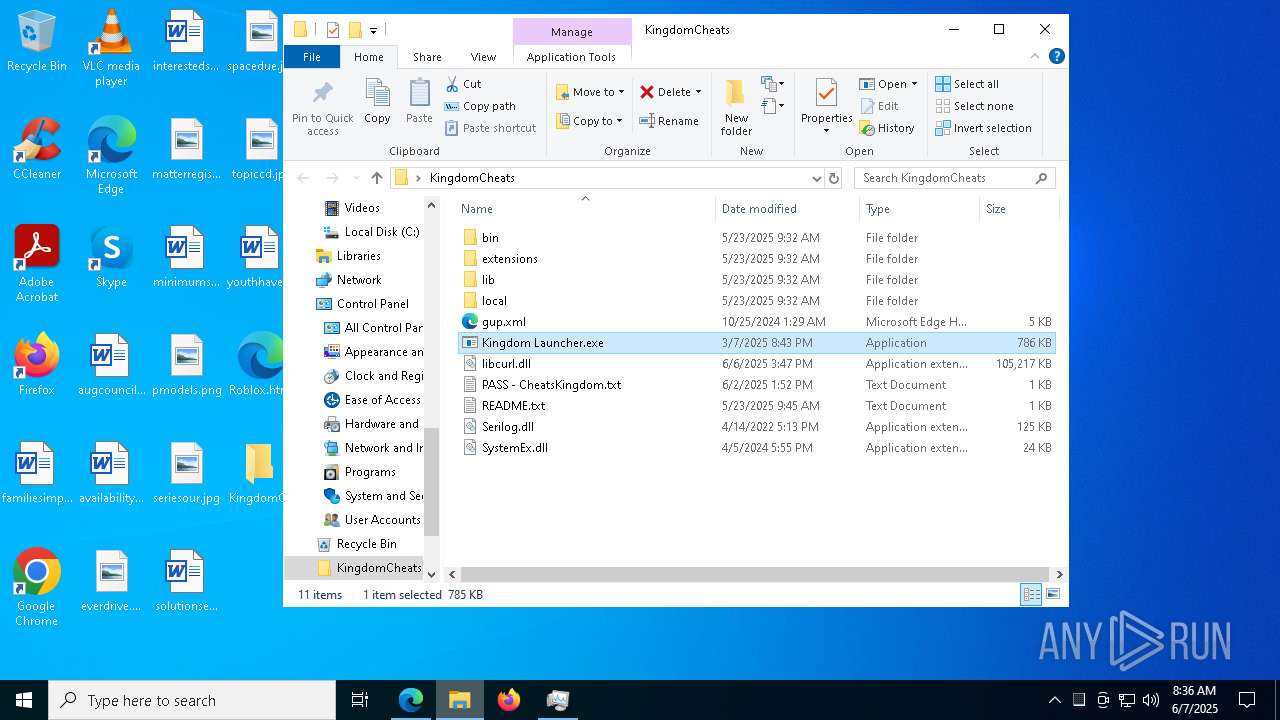
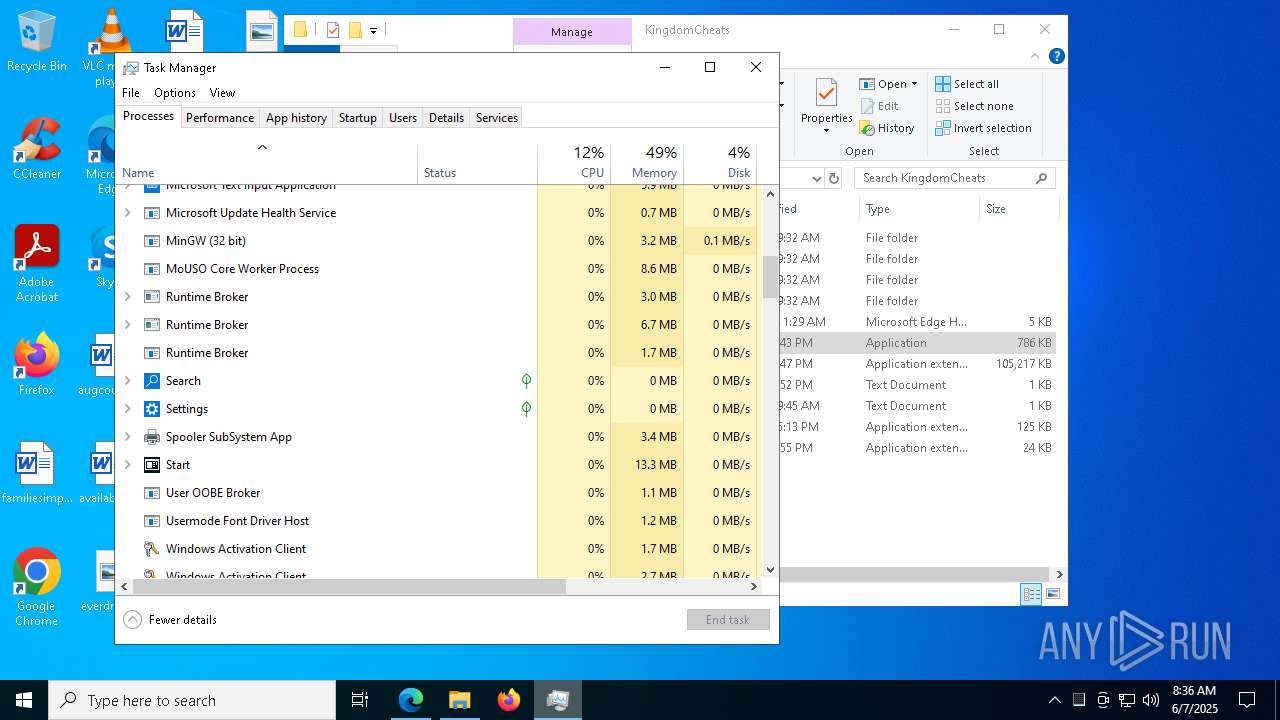
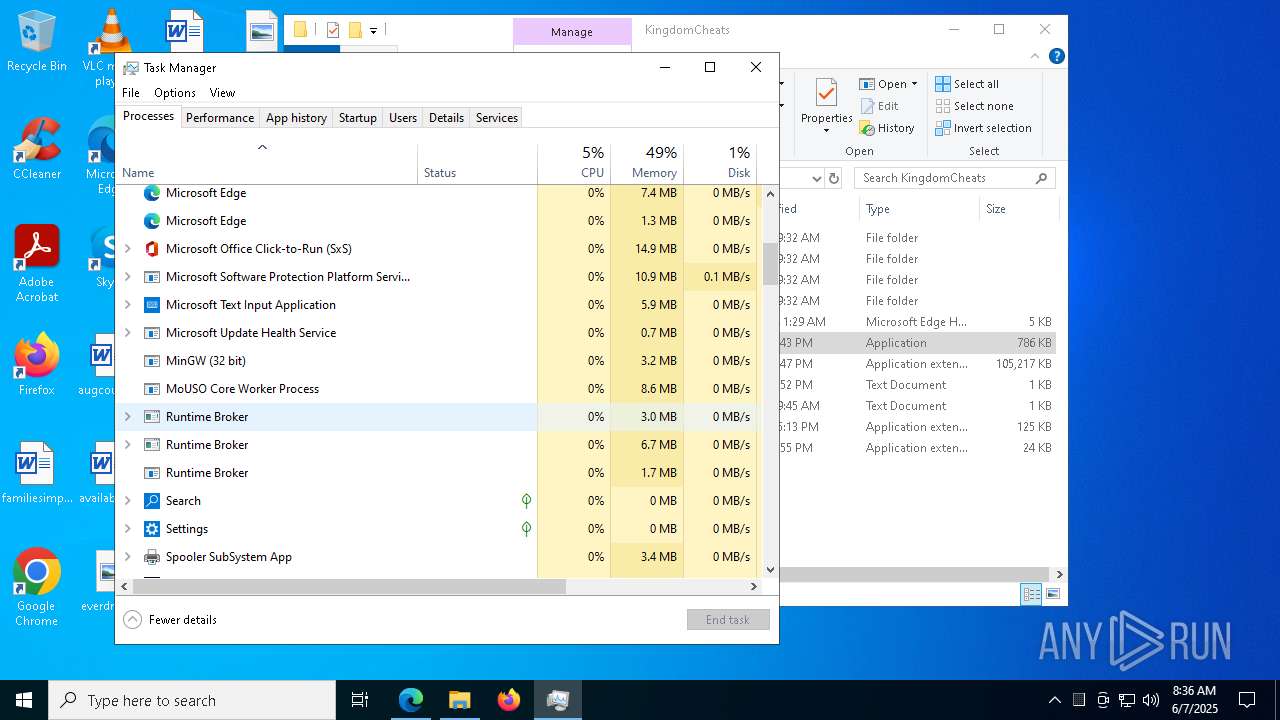
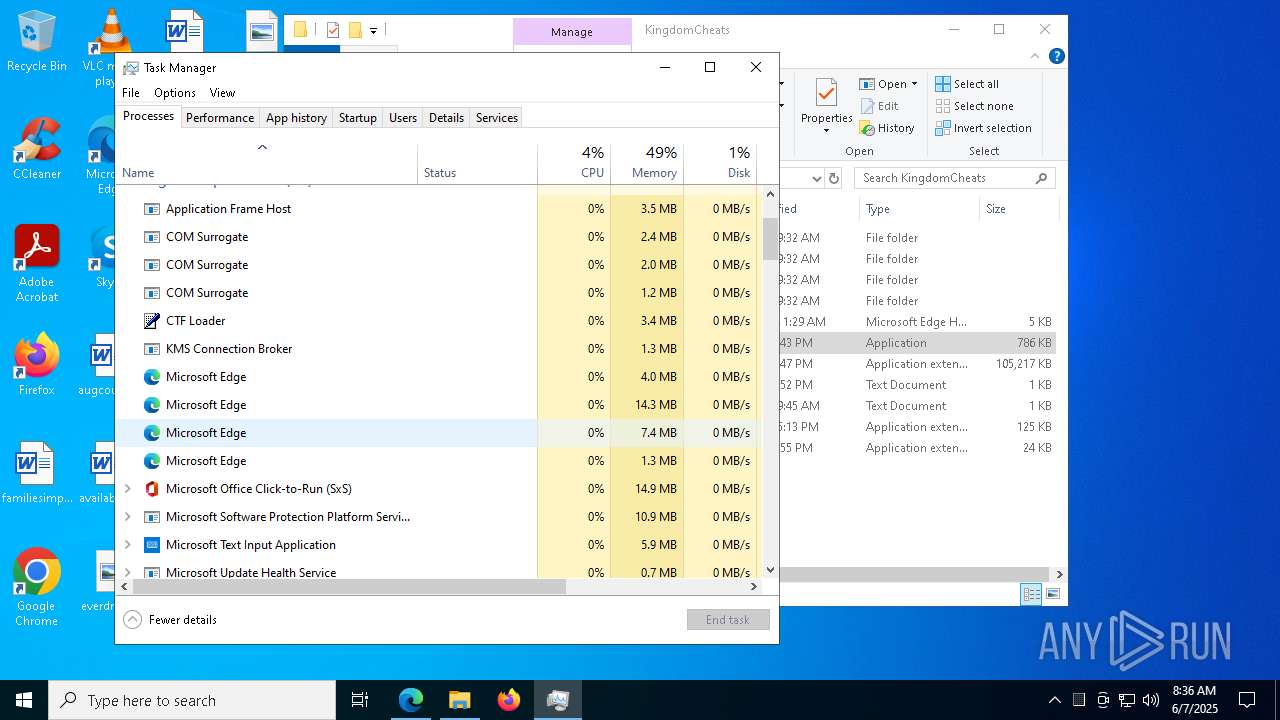
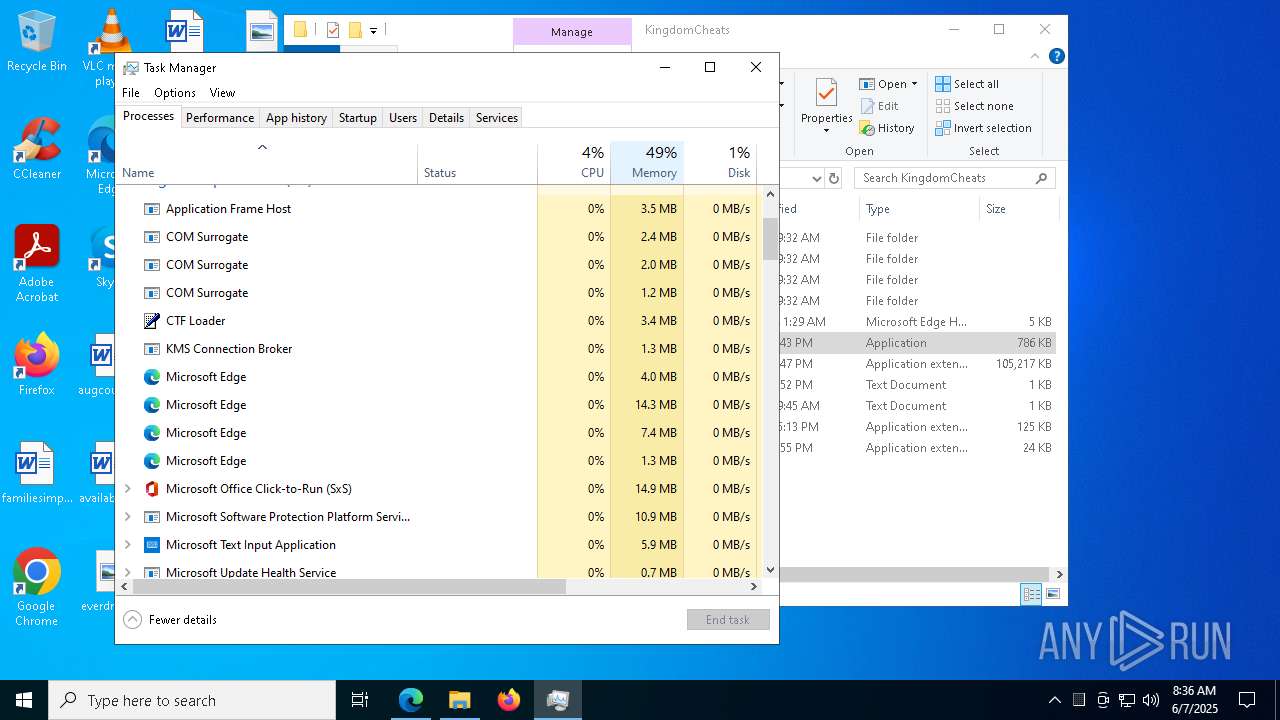
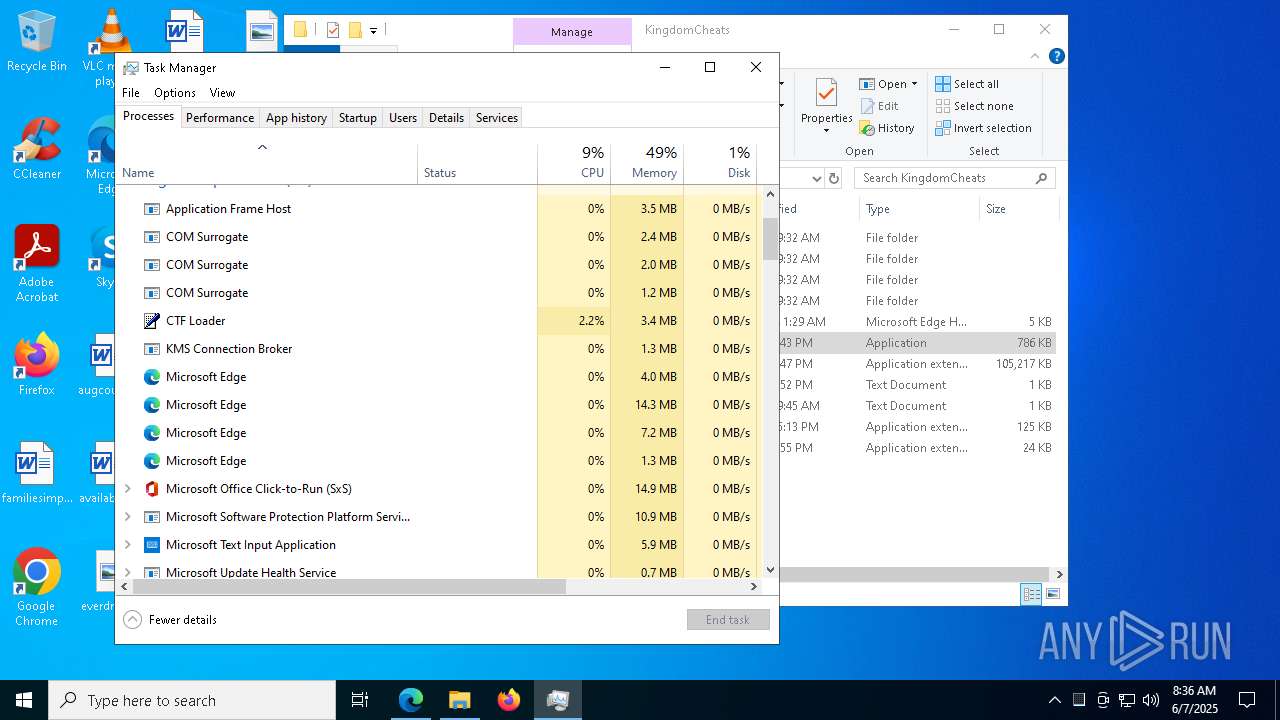
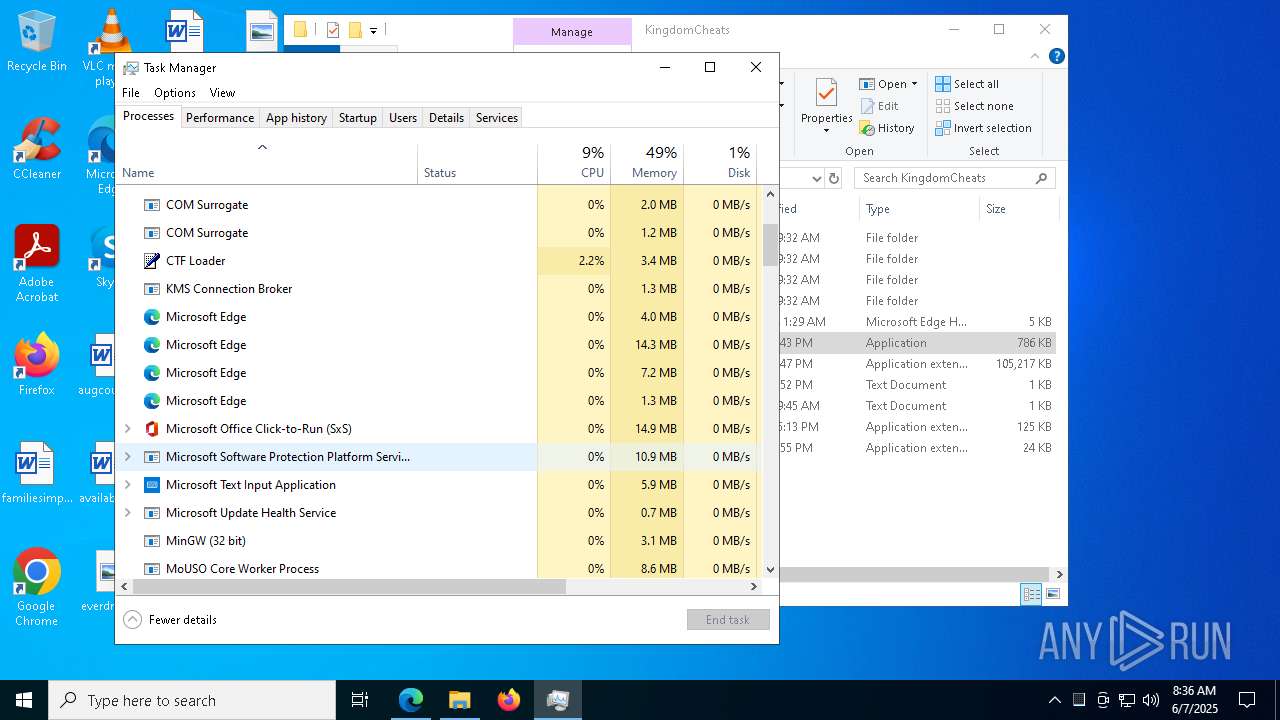
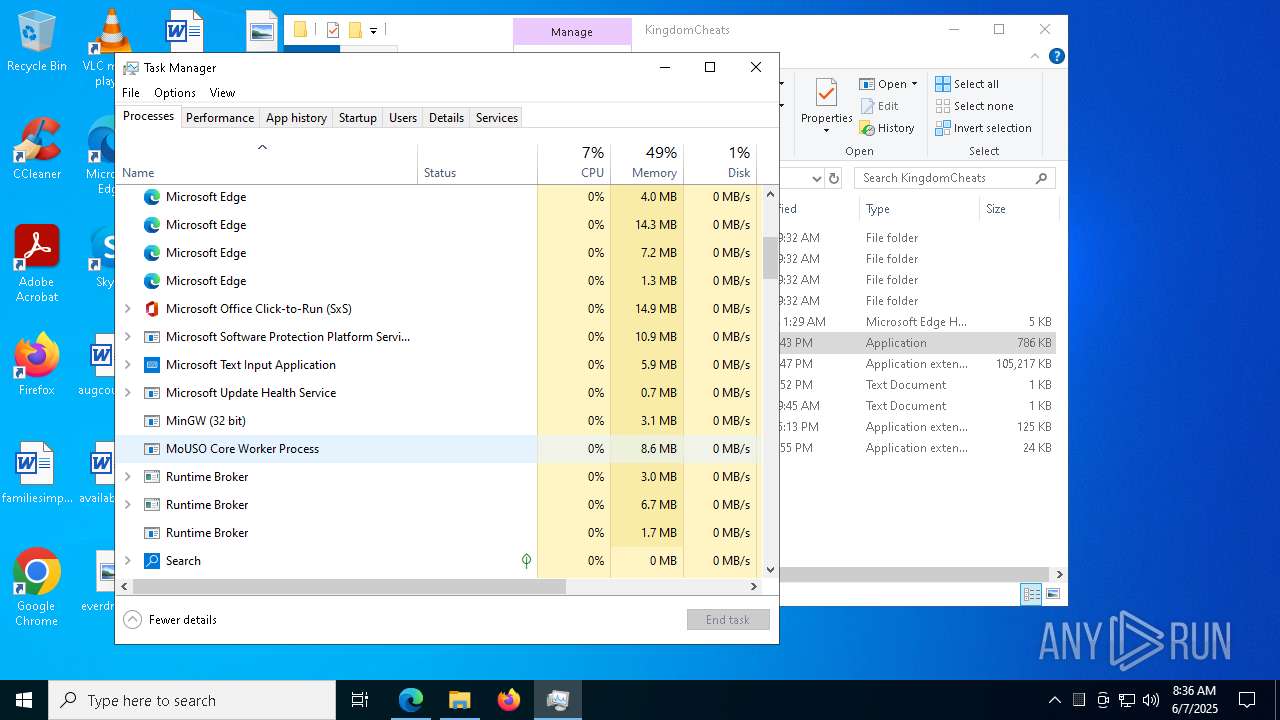
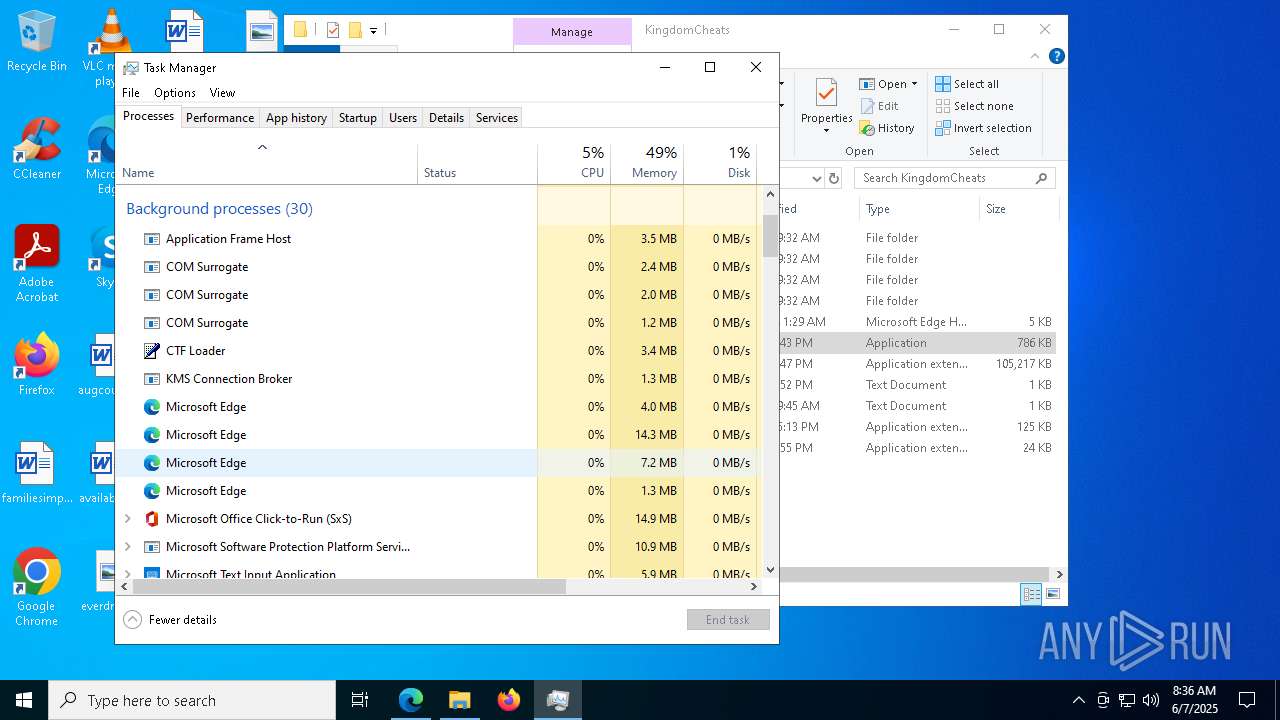
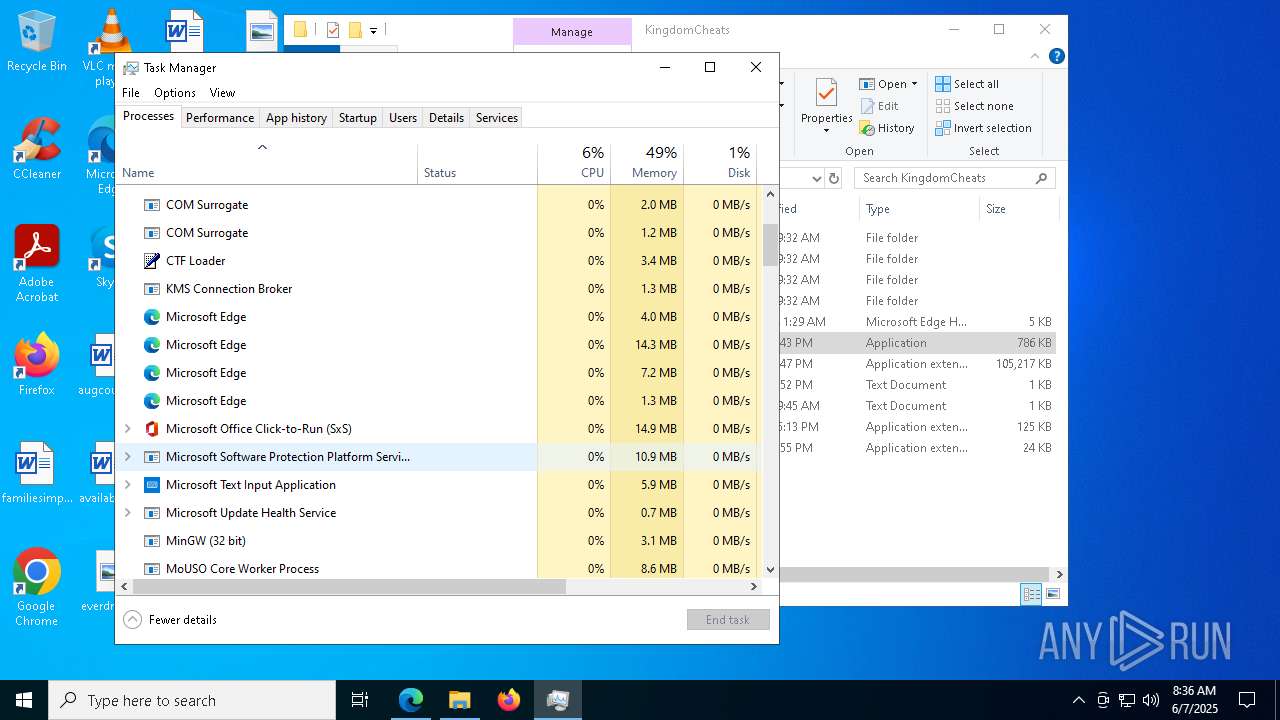
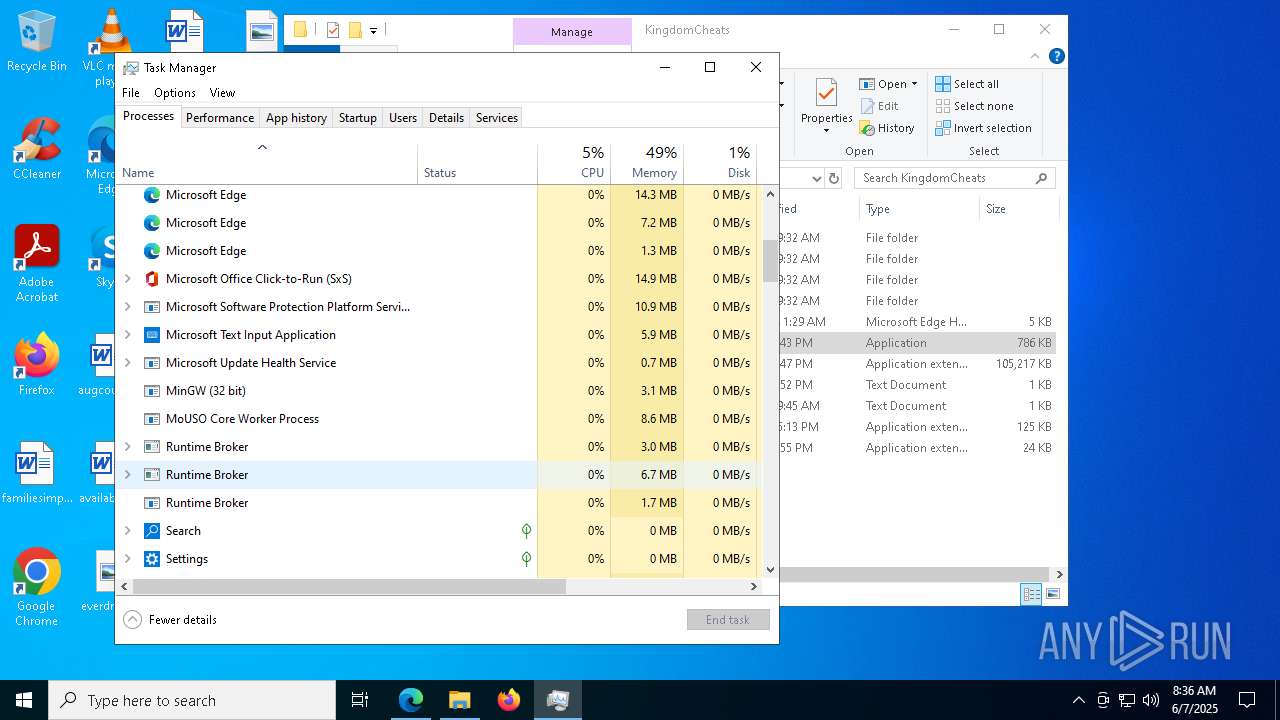
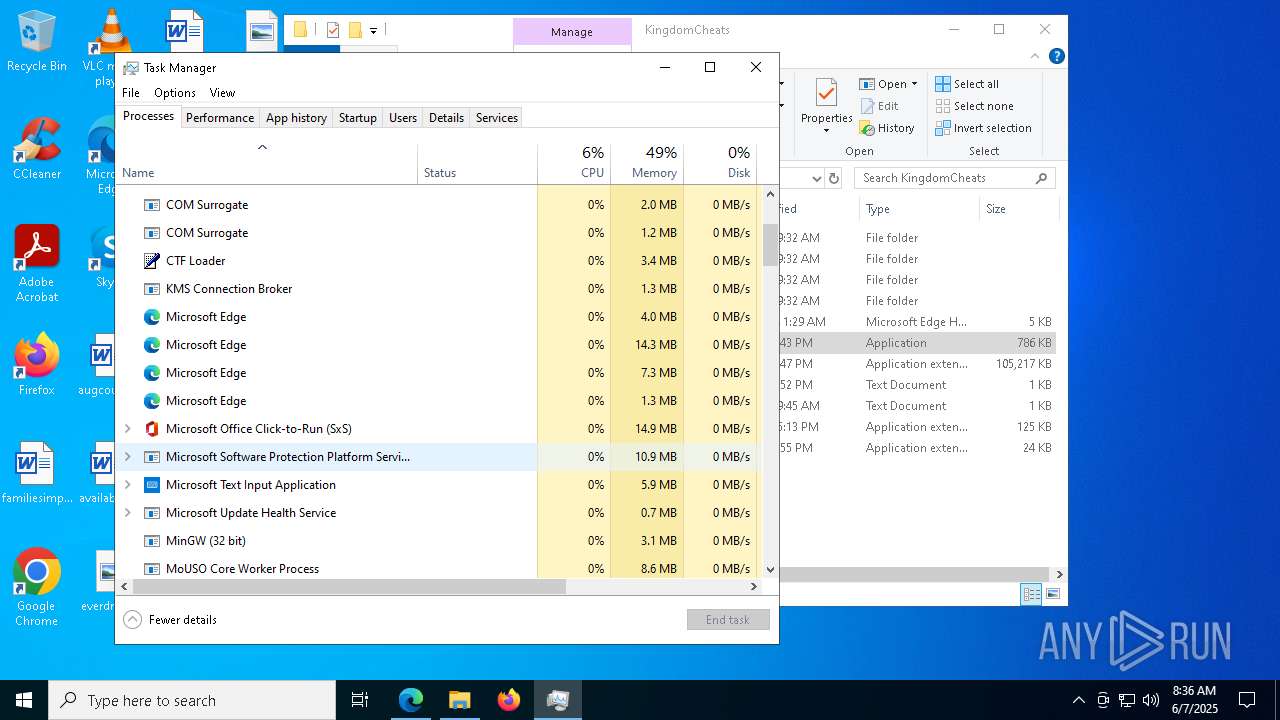
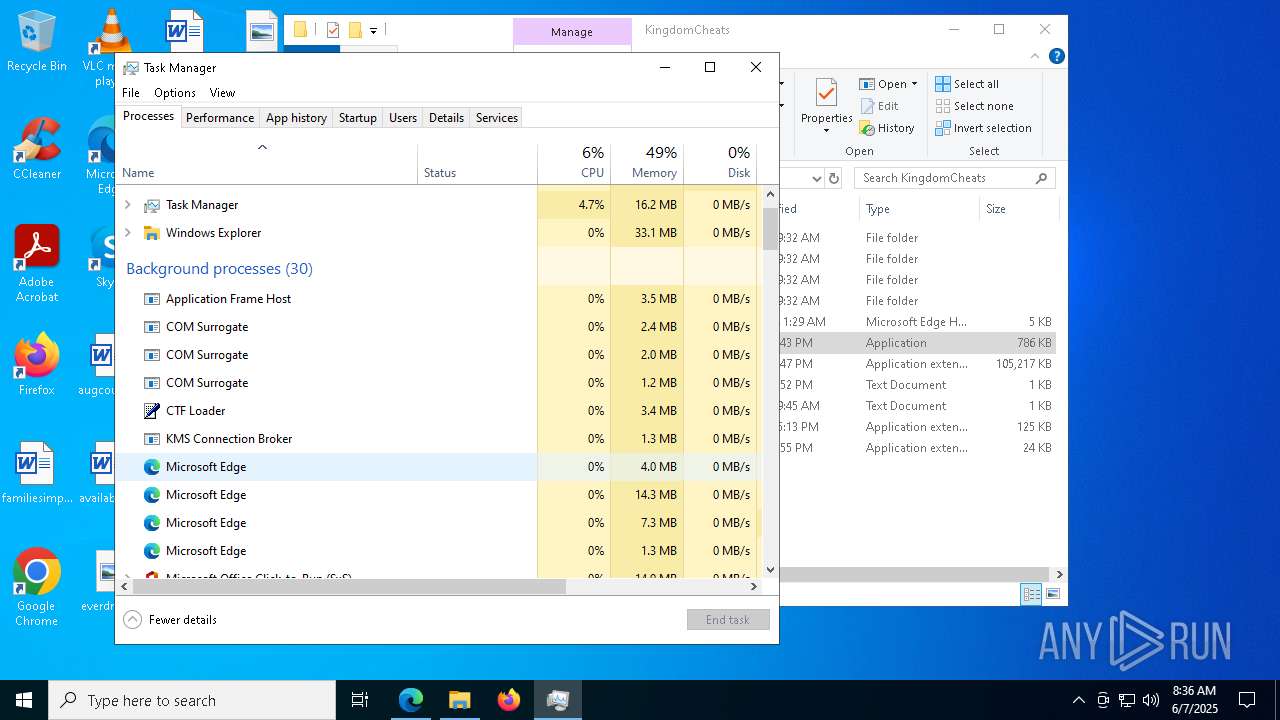
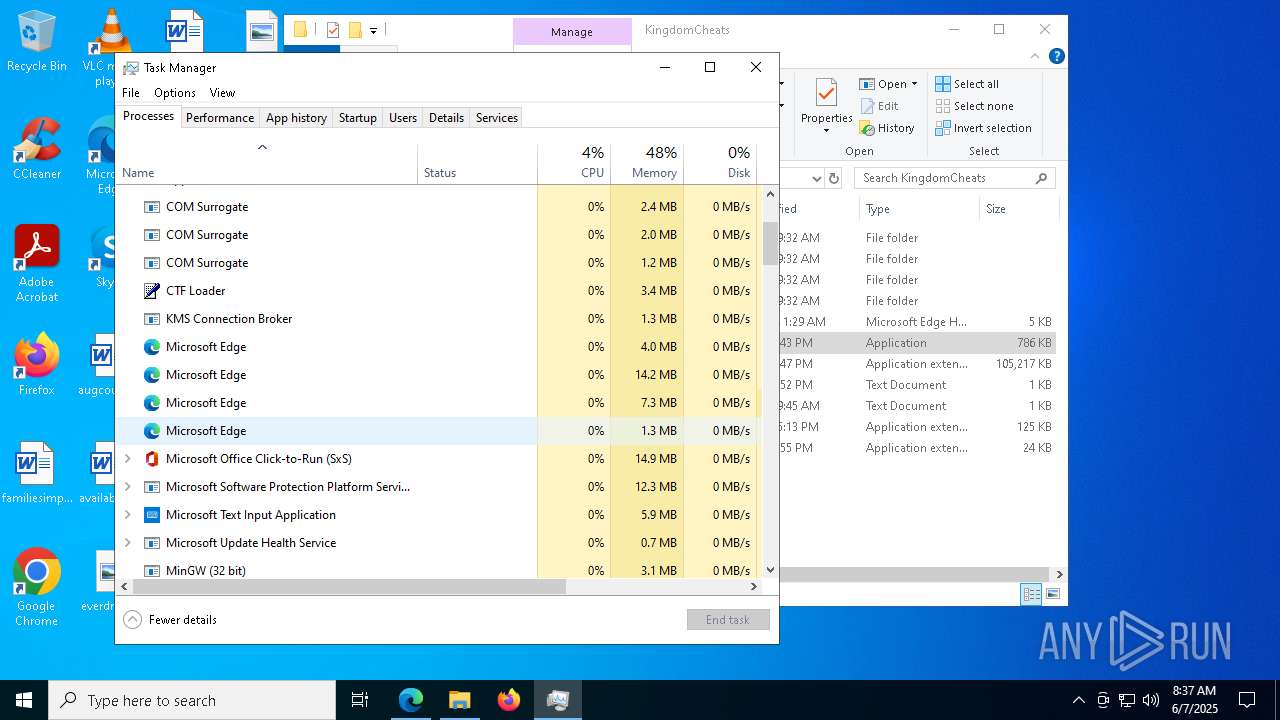
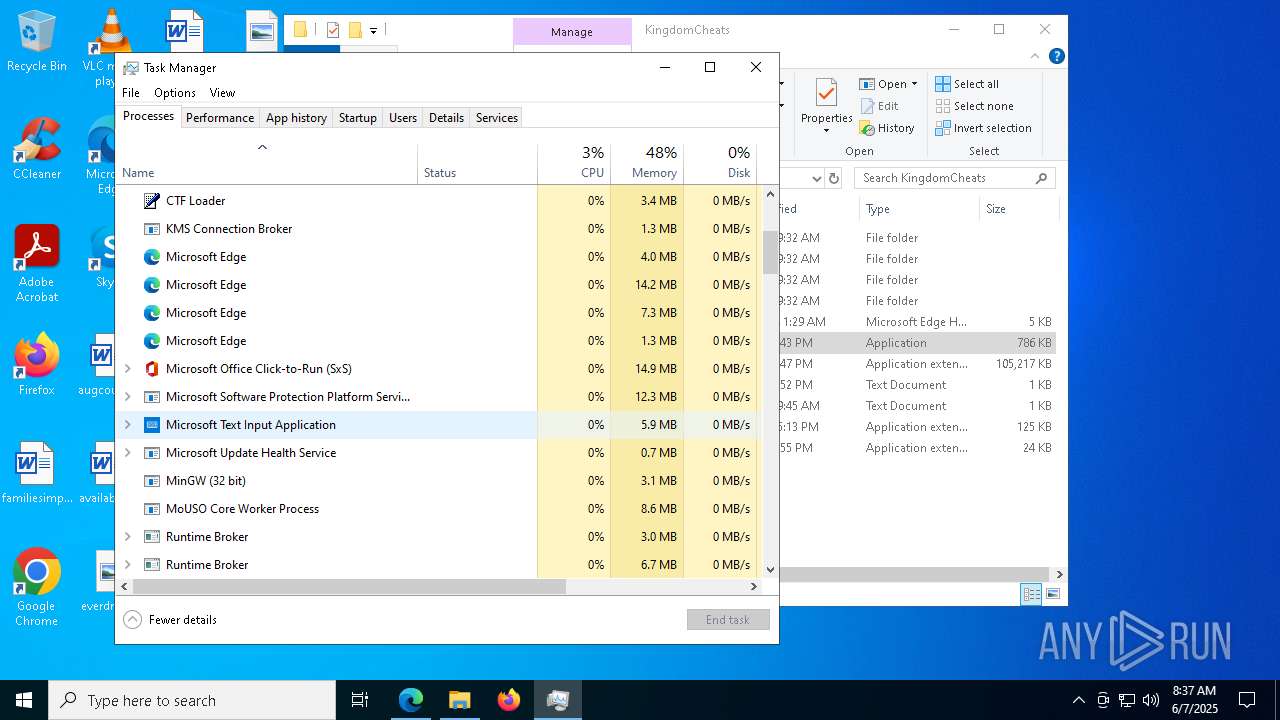
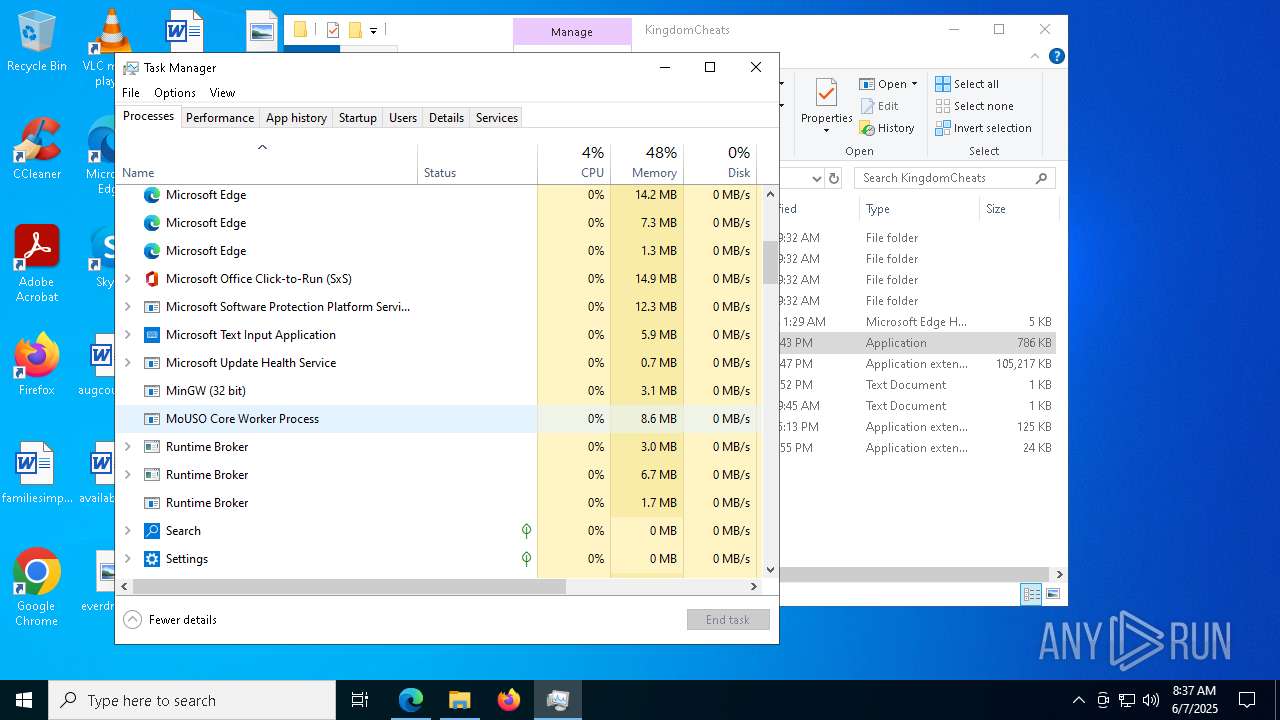
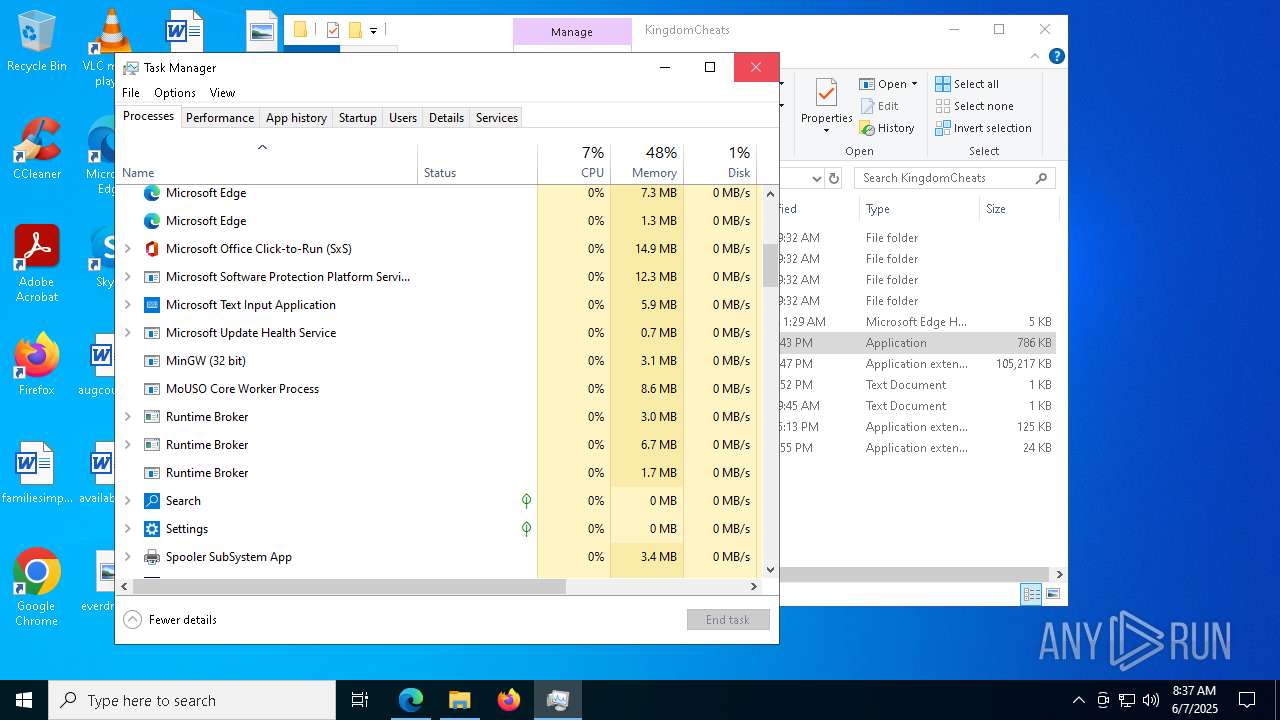
Manual execution by a user
- Kingdom Launcher.exe (PID: 7752)
- Taskmgr.exe (PID: 8172)
- Taskmgr.exe (PID: 7796)
- Kingdom Launcher.exe (PID: 5328)
The sample compiled with english language support
- WinRAR.exe (PID: 7304)
- Kingdom Launcher.exe (PID: 7752)
- msedge.exe (PID: 7484)
Create files in a temporary directory
- Kingdom Launcher.exe (PID: 7752)
- Kingdom Launcher.exe (PID: 2796)
Process checks computer location settings
- Kingdom Launcher.exe (PID: 7752)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2140)
- powershell.exe (PID: 4728)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2140)
- powershell.exe (PID: 4728)
Creates files or folders in the user directory
- Kingdom Launcher.exe (PID: 2796)
Reads the software policy settings
- slui.exe (PID: 6712)
- Kingdom Launcher.exe (PID: 2796)
Reads the machine GUID from the registry
- Kingdom Launcher.exe (PID: 2796)
Checks proxy server information
- Kingdom Launcher.exe (PID: 2796)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 7796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(7128) downloaded_0.exe
C2 (10)narrathfpt.top/tekq
witchdbhy.run/pzal
lepidobdkn.digital/taj
citellcagt.top/gjtu
tinklertjp.bet/nzaf
korxddl.top/qidz
https://t.me/pizdenka202020
localixbiw.top/zlpa
diecam.top/laur
escczlv.top/bufi
EXIF
HTML
| Viewport: | width=device-width, initial-scale=1.0 |
|---|---|
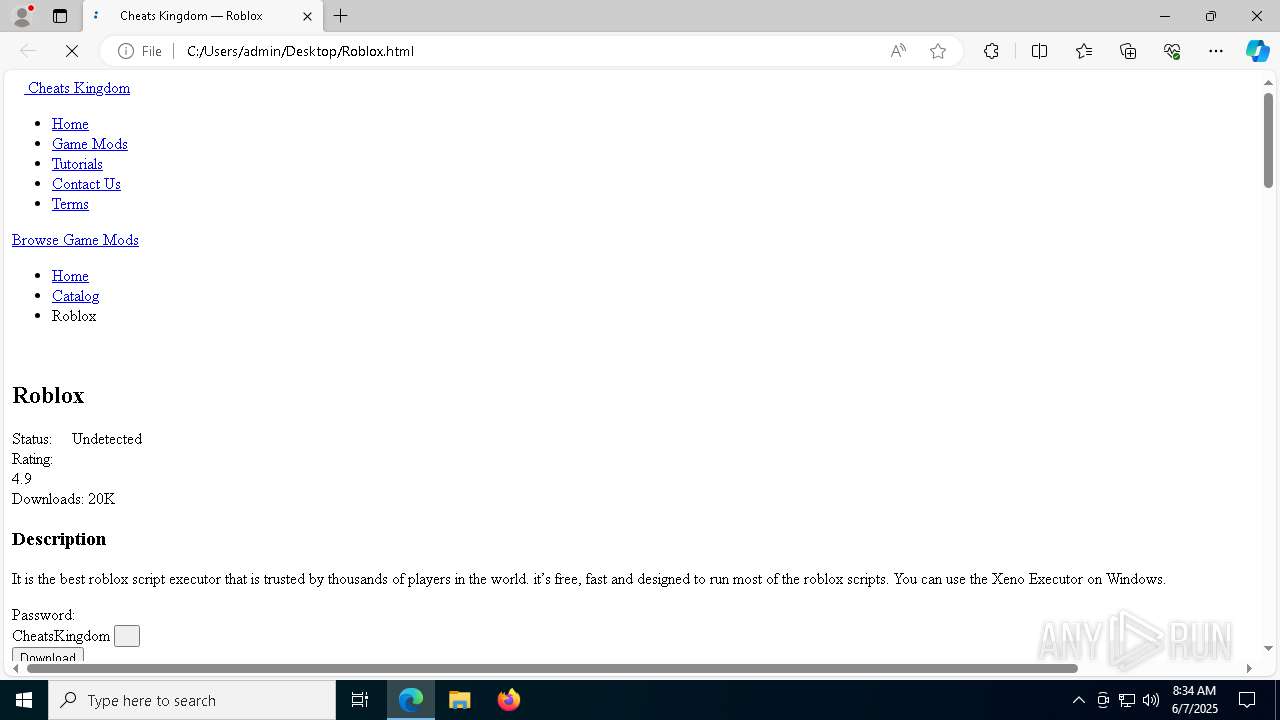
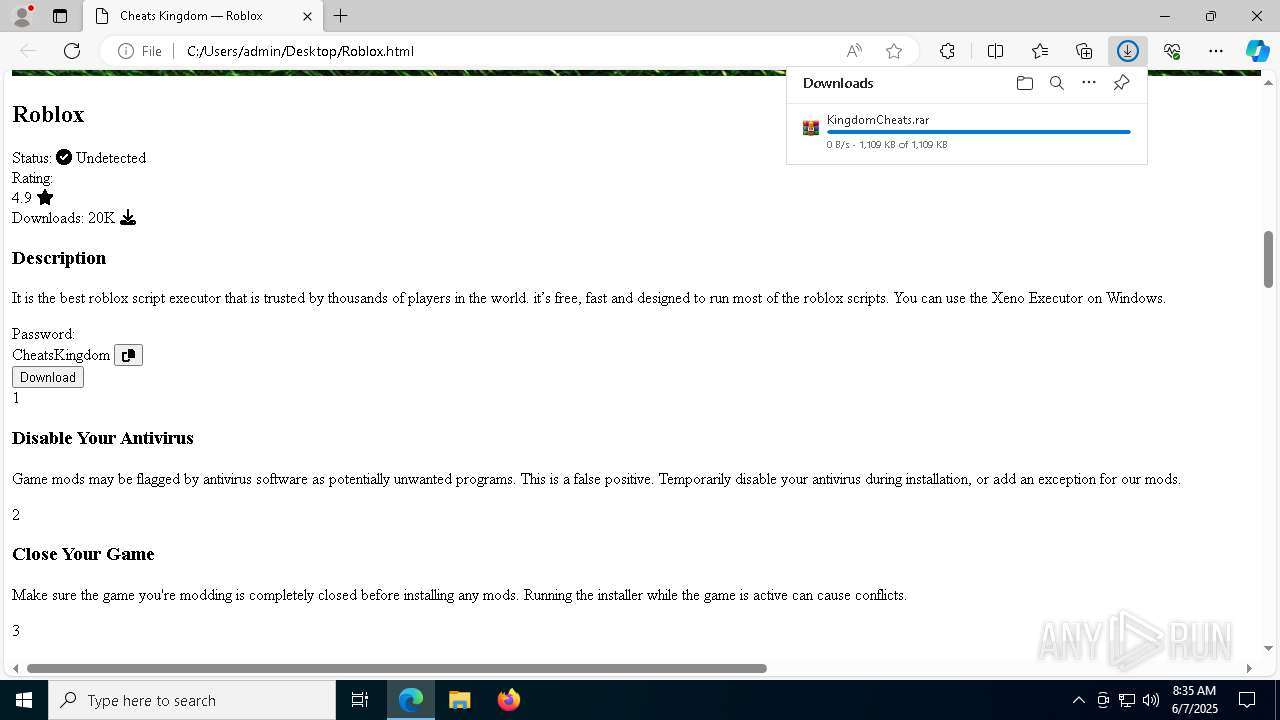
| Keywords: | game mods, game software, game cheat, download cheat, fortnite cheat, cs2 cheat, free hacks, download hack for game, steam hack, steam cheat, free cheats, roblox cheat |
| Description: | Download any cheats for your favorite games! Constant updates and replenishment of the catalog. |
| AppleMobileWebAppTitle: | Game Mods |
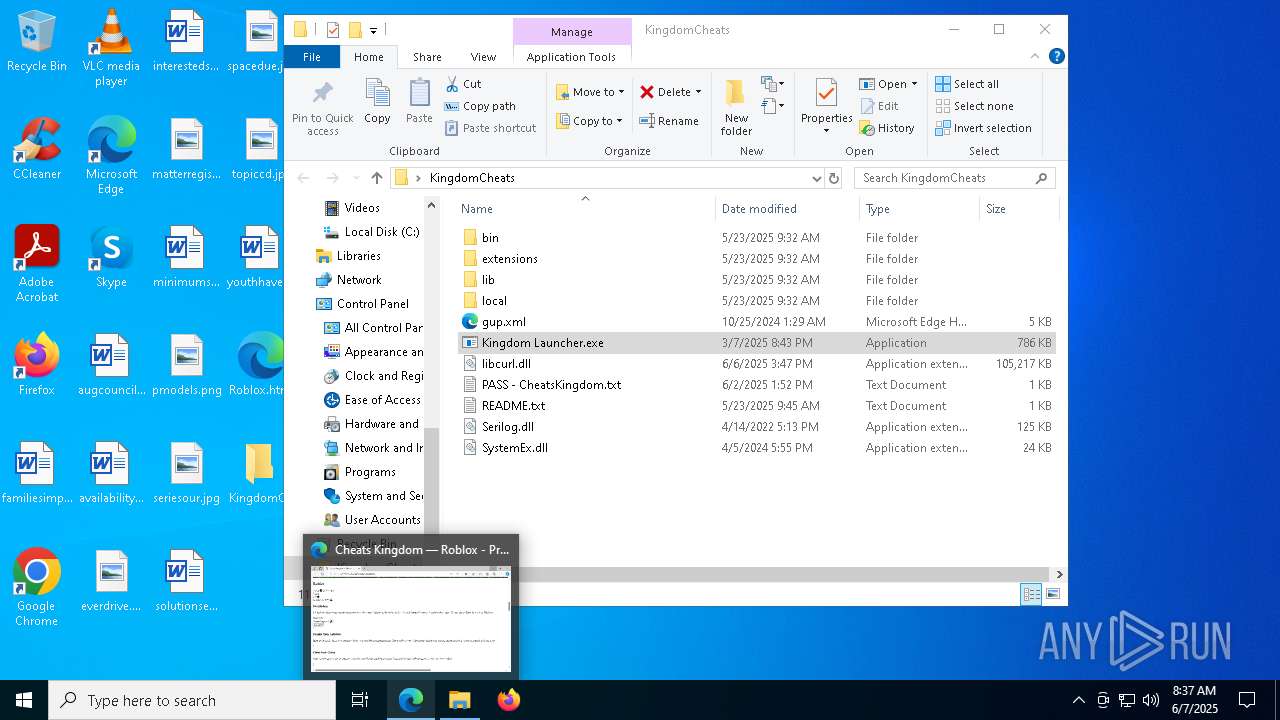
| Title: | Cheats Kingdom — Roblox |
Total processes
197
Monitored processes
65
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --mojo-platform-channel-handle=3808 --field-trial-handle=2380,i,15621312852283936856,10160587989270983273,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 760 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 772 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6700 --field-trial-handle=2380,i,15621312852283936856,10160587989270983273,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1012 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4500 --field-trial-handle=2380,i,15621312852283936856,10160587989270983273,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1012 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6688 --field-trial-handle=2380,i,15621312852283936856,10160587989270983273,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6068 --field-trial-handle=2380,i,15621312852283936856,10160587989270983273,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1176 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5416 --field-trial-handle=2380,i,15621312852283936856,10160587989270983273,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3852 --field-trial-handle=2380,i,15621312852283936856,10160587989270983273,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1284 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6700 --field-trial-handle=2380,i,15621312852283936856,10160587989270983273,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1328 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6192 --field-trial-handle=2380,i,15621312852283936856,10160587989270983273,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
25 608
Read events
25 516
Write events
74
Delete events
18
Modification events
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 468321562 | |||
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31184775 | |||
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1696) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
27
Suspicious files
357
Text files
62
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF11f7ea.TMP | — | |
MD5:— | SHA256:— | |||
| 2104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF11f7f9.TMP | — | |
MD5:— | SHA256:— | |||
| 2104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old~RF11f7f9.TMP | — | |
MD5:— | SHA256:— | |||
| 2104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old~RF11f809.TMP | — | |
MD5:— | SHA256:— | |||
| 2104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF11f809.TMP | — | |
MD5:— | SHA256:— | |||
| 2104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11f809.TMP | — | |
MD5:— | SHA256:— | |||
| 2104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2104 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
79
DNS requests
84
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
7196 | svchost.exe | HEAD | 200 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1749575113&P2=404&P3=2&P4=Oh6OUp5wRAmbYKUM7pTv6x22hb%2b7q4nrQS5kayB75fP5DRgVvDvhsVW34VW%2fXGTYCTSk2EVAl5xHpYlL6IW9hQ%3d%3d | US | — | — | whitelisted |
236 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
236 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
7196 | svchost.exe | GET | 206 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1749575113&P2=404&P3=2&P4=Oh6OUp5wRAmbYKUM7pTv6x22hb%2b7q4nrQS5kayB75fP5DRgVvDvhsVW34VW%2fXGTYCTSk2EVAl5xHpYlL6IW9hQ%3d%3d | US | binary | 1.09 Kb | whitelisted |
2796 | Kingdom Launcher.exe | GET | 200 | 5.101.153.129:80 | http://lena255f.beget.tech/rblinks.txt | RU | text | 68 b | whitelisted |
2796 | Kingdom Launcher.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | US | binary | 1.42 Kb | whitelisted |
7196 | svchost.exe | GET | 206 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1749575113&P2=404&P3=2&P4=Oh6OUp5wRAmbYKUM7pTv6x22hb%2b7q4nrQS5kayB75fP5DRgVvDvhsVW34VW%2fXGTYCTSk2EVAl5xHpYlL6IW9hQ%3d%3d | US | compressed | 764 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7868 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5344 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5344 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5344 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5344 | msedge.exe | 199.232.192.193:443 | i.imgur.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5344 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image Sharing Service (imgur.com) |
5344 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5344 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5344 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image Sharing Service (imgur.com) |
5344 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5344 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5344 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image Sharing Service (imgur.com) |
5344 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image Sharing Service (imgur.com) |
7128 | downloaded_0.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (lepidobdkn .digital) |