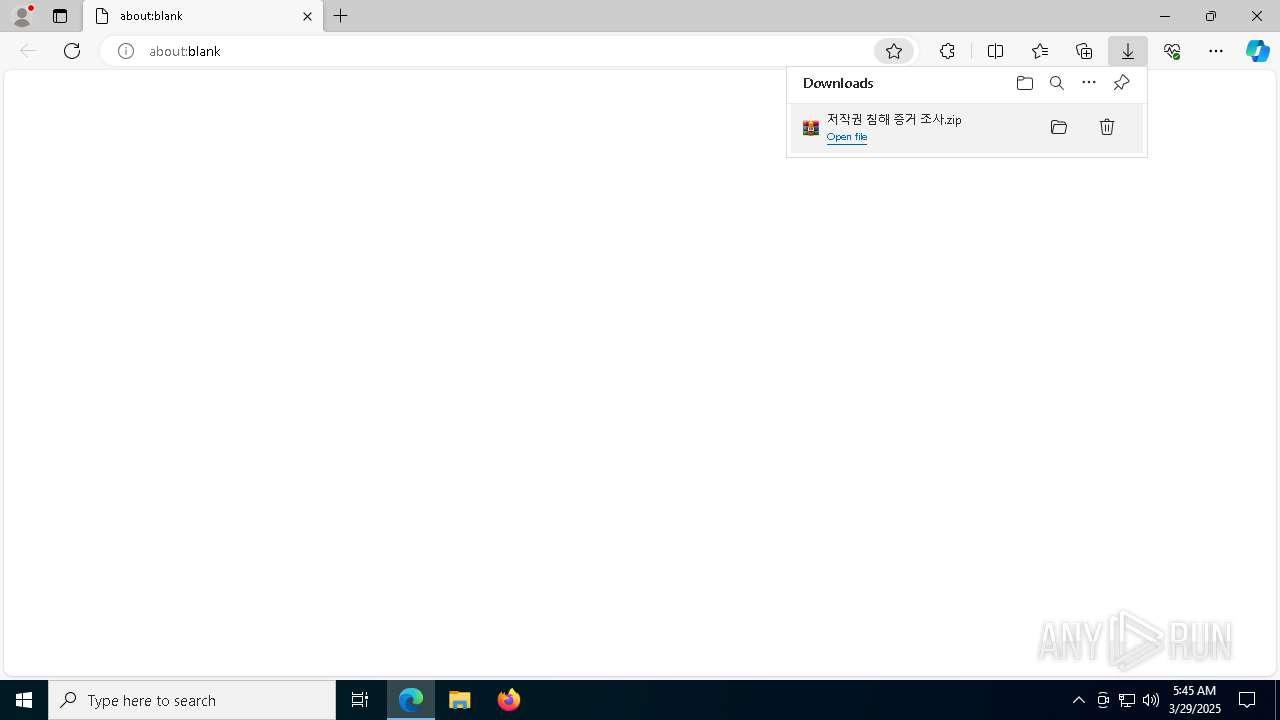
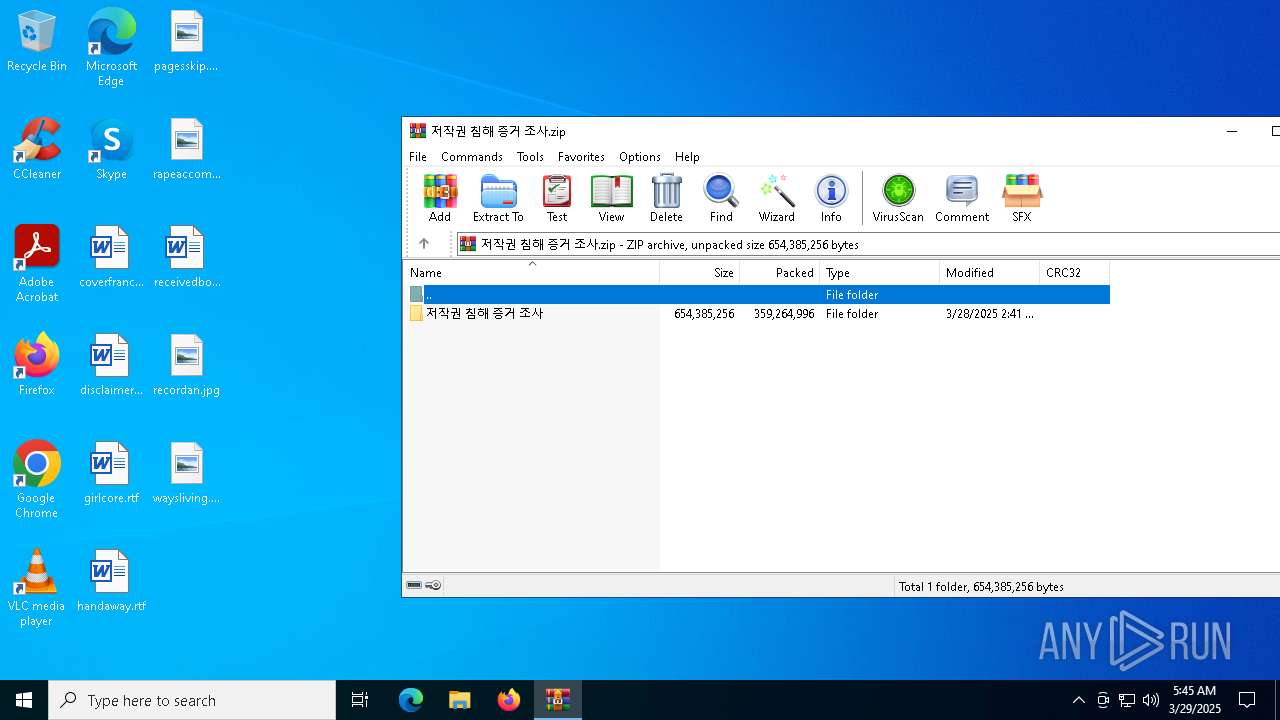
| URL: | https://tranedg.com/?u=https://www.mediafire.com/file_premium/mw0f6wp0p0uc8a3/%25EC%25A0%2580%25EC%259E%2591%25EA%25B6%258C_%25EC%25B9%25A8%25ED%2595%25B4_%25EC%25A6%259D%25EA%25B1%25B0_%25EC%25A1%25B0%25EC%2582%25AC.zip/file |
| Full analysis: | https://app.any.run/tasks/a8fcbc41-ed89-4732-9bfd-04a4bceccffb |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | March 29, 2025, 05:43:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 524C30DC642D7DBE251827CAC38B3941 |
| SHA1: | E04EBC8D68D261B69B63FF2D0FD0842AE24260F9 |
| SHA256: | 03C3B0211FB5F92D3D4ACDB15F604C34F0352FAEADB45FC3BE6E53B33B8386C1 |
| SSDEEP: | 6:24FGLw3eGBOd/gDXKy/sKkuAKqA0pDVAXhef1:2S3e2OEoxAqRAXq1 |
MALICIOUS
RHADAMANTHYS mutex has been found
- svchost.exe (PID: 1328)
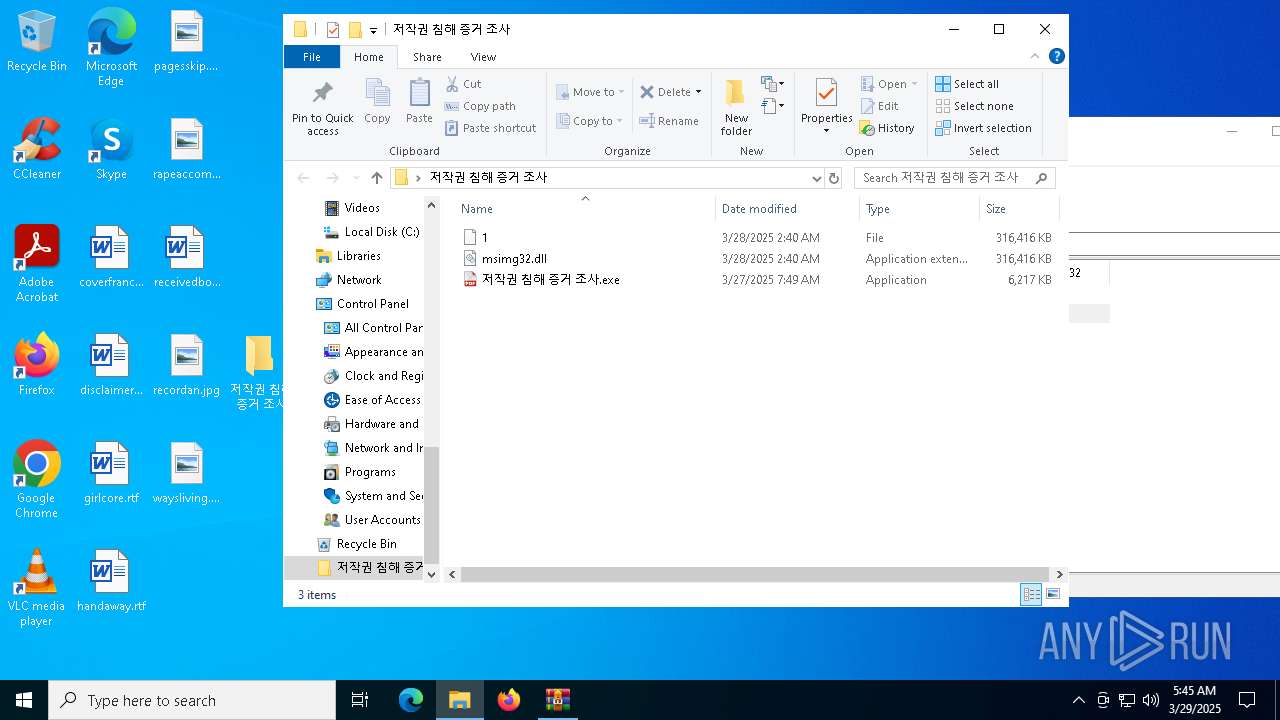
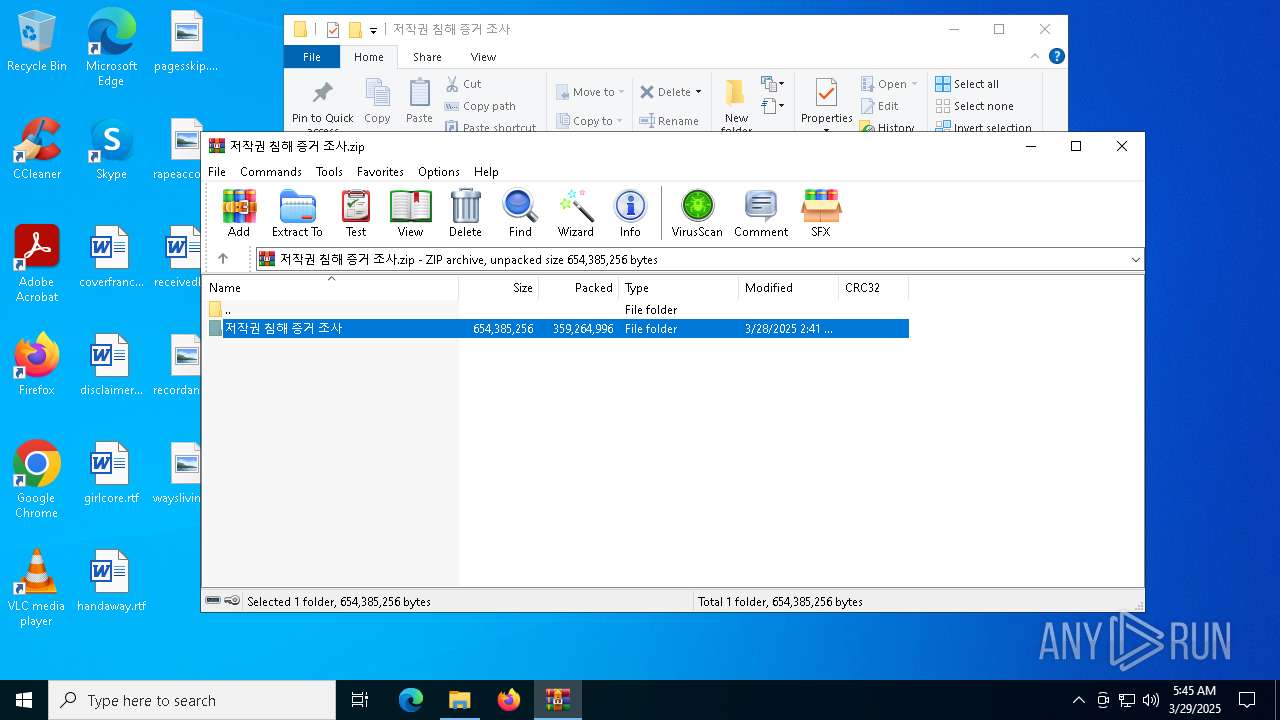
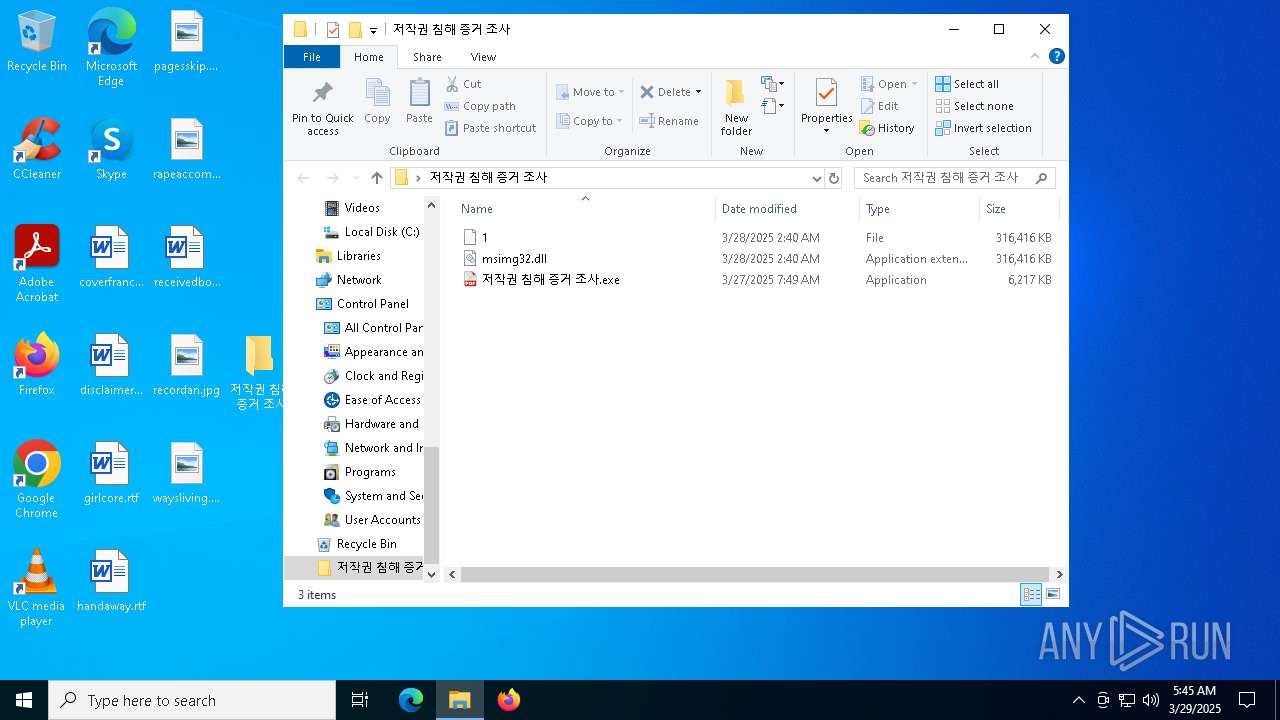
- 저작권 침해 증거 조사.exe (PID: 6156)
Actions looks like stealing of personal data
- chrome.exe (PID: 7692)
- msedge.exe (PID: 7972)
- csc.exe (PID: 7492)
RHADAMANTHYS has been detected (YARA)
- svchost.exe (PID: 2040)
Steals credentials from Web Browsers
- msedge.exe (PID: 7972)
RHADAMANTHYS has been detected (SURICATA)
- svchost.exe (PID: 2040)
ASYNCRAT mutex has been found
- csc.exe (PID: 7492)
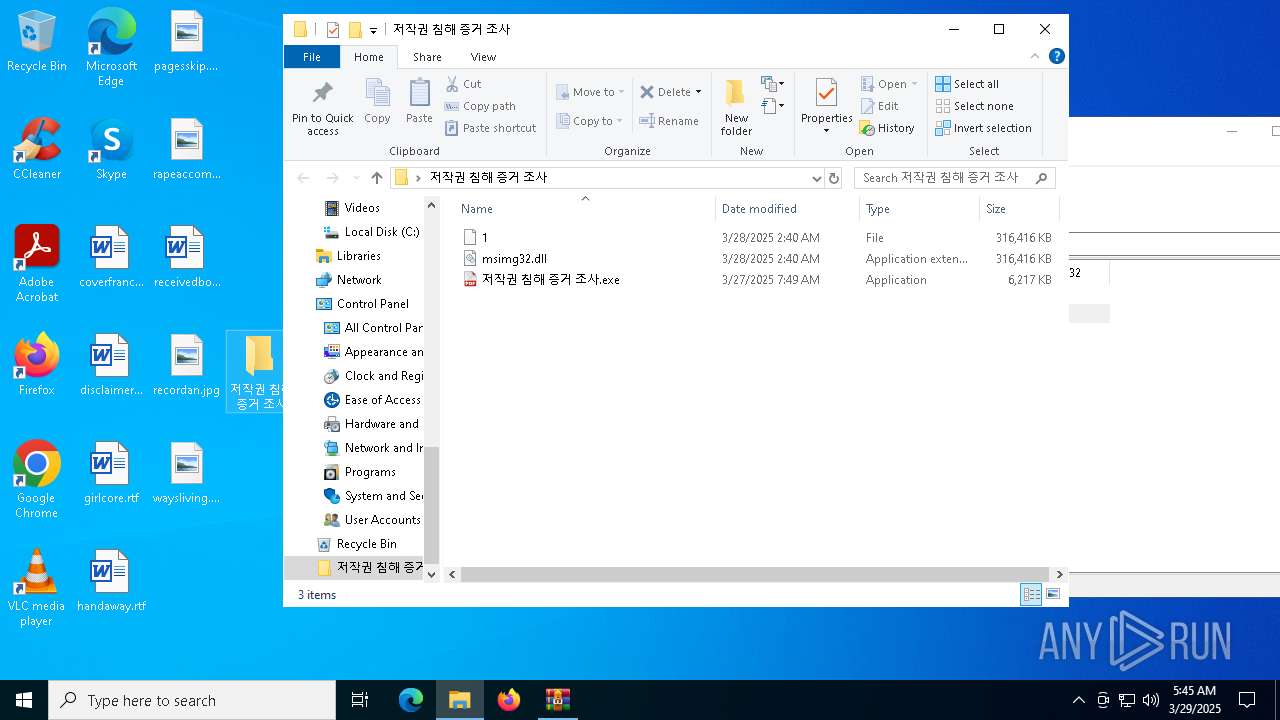
Starts Visual C# compiler
- uS6c~g.exe (PID: 7344)
ASYNCRAT has been detected (SURICATA)
- csc.exe (PID: 7492)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- 저작권 침해 증거 조사.exe (PID: 872)
- uS6c~g.exe (PID: 7344)
Application launched itself
- 저작권 침해 증거 조사.exe (PID: 872)
- chrome.exe (PID: 7692)
- msedge.exe (PID: 7972)
The process checks if it is being run in the virtual environment
- svchost.exe (PID: 1328)
Executes application which crashes
- 저작권 침해 증거 조사.exe (PID: 6156)
- uS6c~g.exe (PID: 7344)
Connects to unusual port
- svchost.exe (PID: 1328)
- svchost.exe (PID: 2040)
- csc.exe (PID: 7492)
Multiple wallet extension IDs have been found
- svchost.exe (PID: 2040)
Reads security settings of Internet Explorer
- msedge.exe (PID: 7972)
Reads Mozilla Firefox installation path
- msedge.exe (PID: 7972)
Loads DLL from Mozilla Firefox
- svchost.exe (PID: 2040)
Executable content was dropped or overwritten
- wmlaunch.exe (PID: 7828)
- svchost.exe (PID: 2040)
Searches for installed software
- svchost.exe (PID: 2040)
Contacting a server suspected of hosting an CnC
- csc.exe (PID: 7492)
INFO
Application launched itself
- msedge.exe (PID: 4996)
- msedge.exe (PID: 5156)
Reads the computer name
- identity_helper.exe (PID: 2088)
- identity_helper.exe (PID: 8916)
- chrome.exe (PID: 7692)
- msedge.exe (PID: 7972)
- wmlaunch.exe (PID: 7828)
- csc.exe (PID: 7492)
Checks supported languages
- identity_helper.exe (PID: 8916)
- identity_helper.exe (PID: 2088)
- 저작권 침해 증거 조사.exe (PID: 872)
- 저작권 침해 증거 조사.exe (PID: 6156)
- chrome.exe (PID: 7692)
- msedge.exe (PID: 7972)
- uS6c~g.exe (PID: 7344)
- wmlaunch.exe (PID: 7828)
- csc.exe (PID: 7492)
Reads Environment values
- identity_helper.exe (PID: 8916)
- identity_helper.exe (PID: 2088)
- msedge.exe (PID: 7972)
- chrome.exe (PID: 7692)
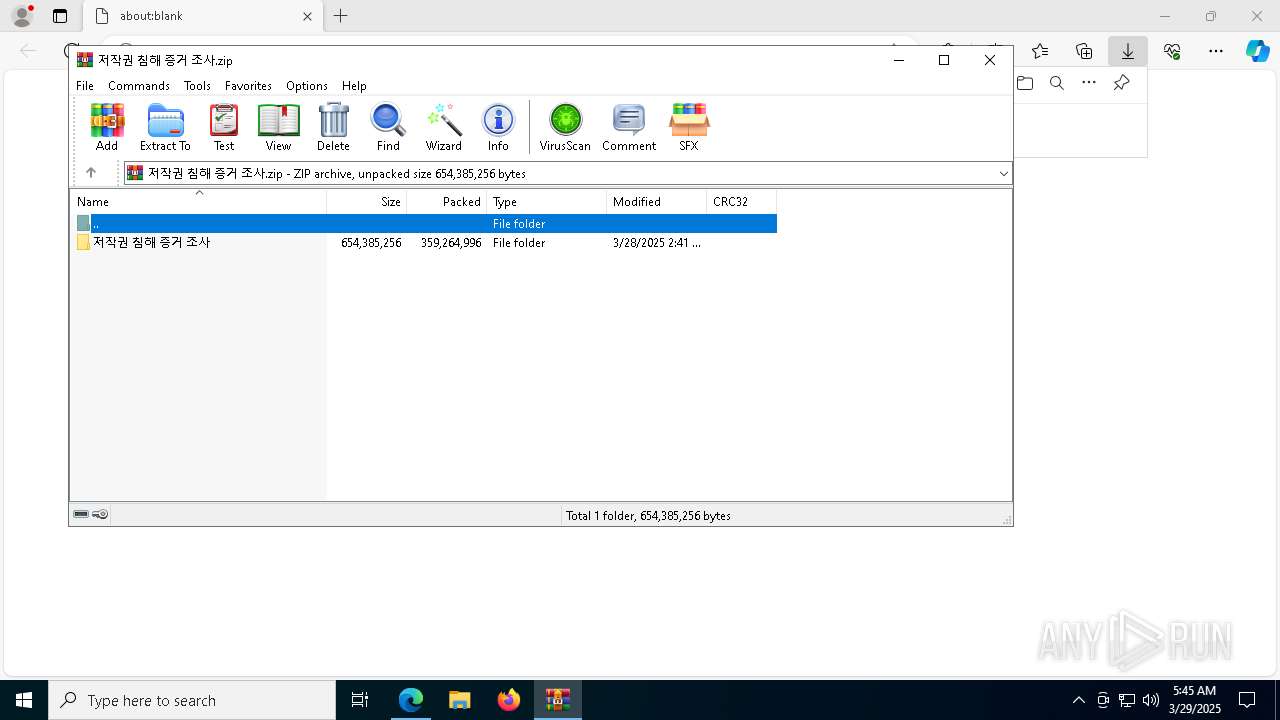
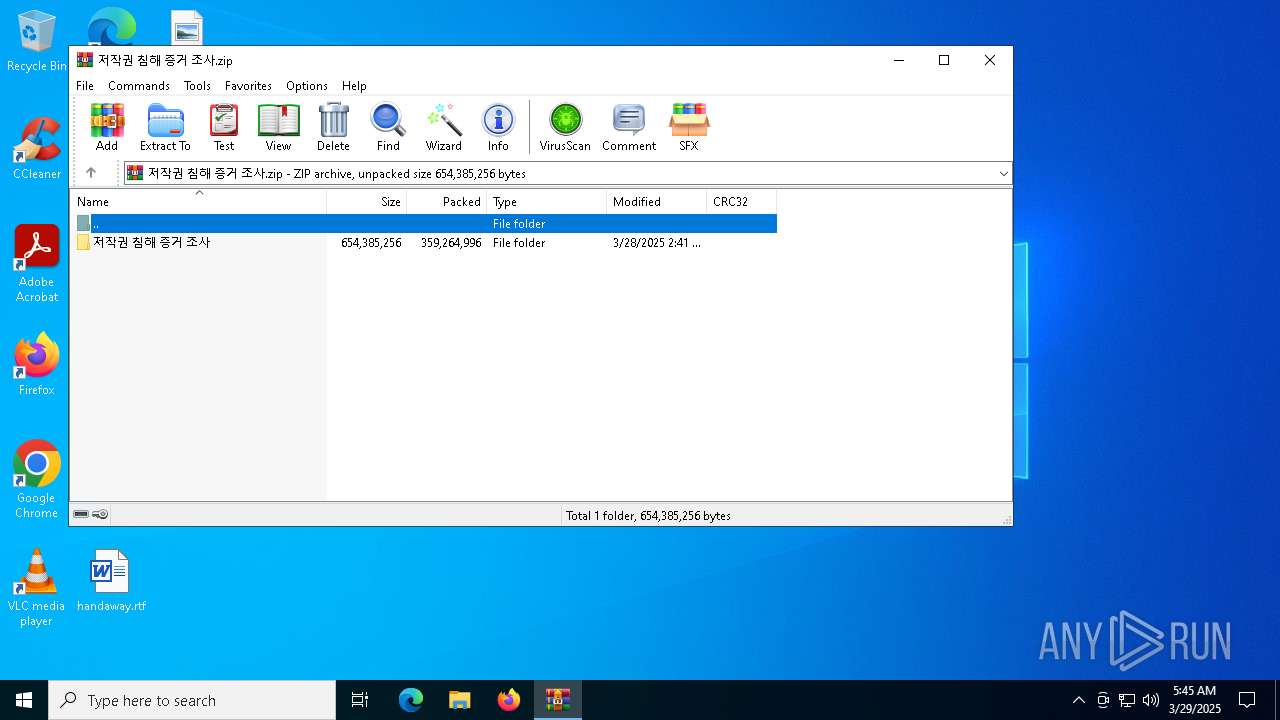
Manual execution by a user
- 저작권 침해 증거 조사.exe (PID: 872)
- svchost.exe (PID: 1328)
- svchost.exe (PID: 2040)
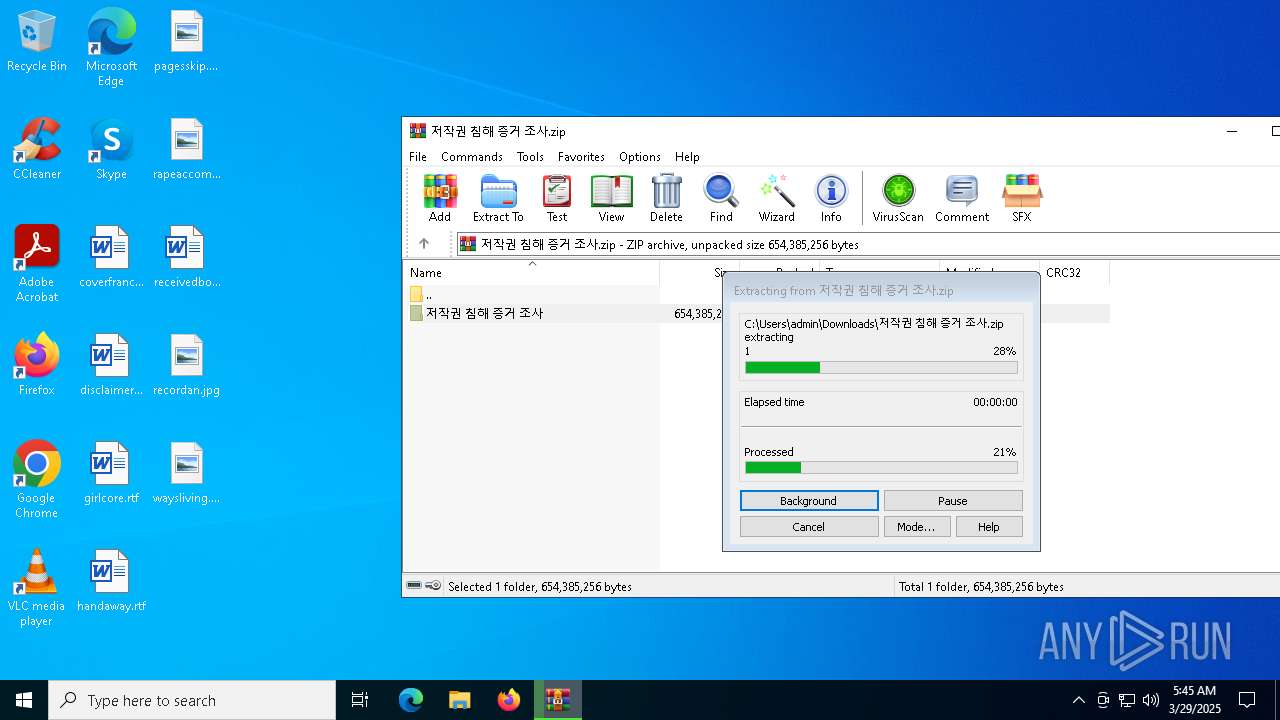
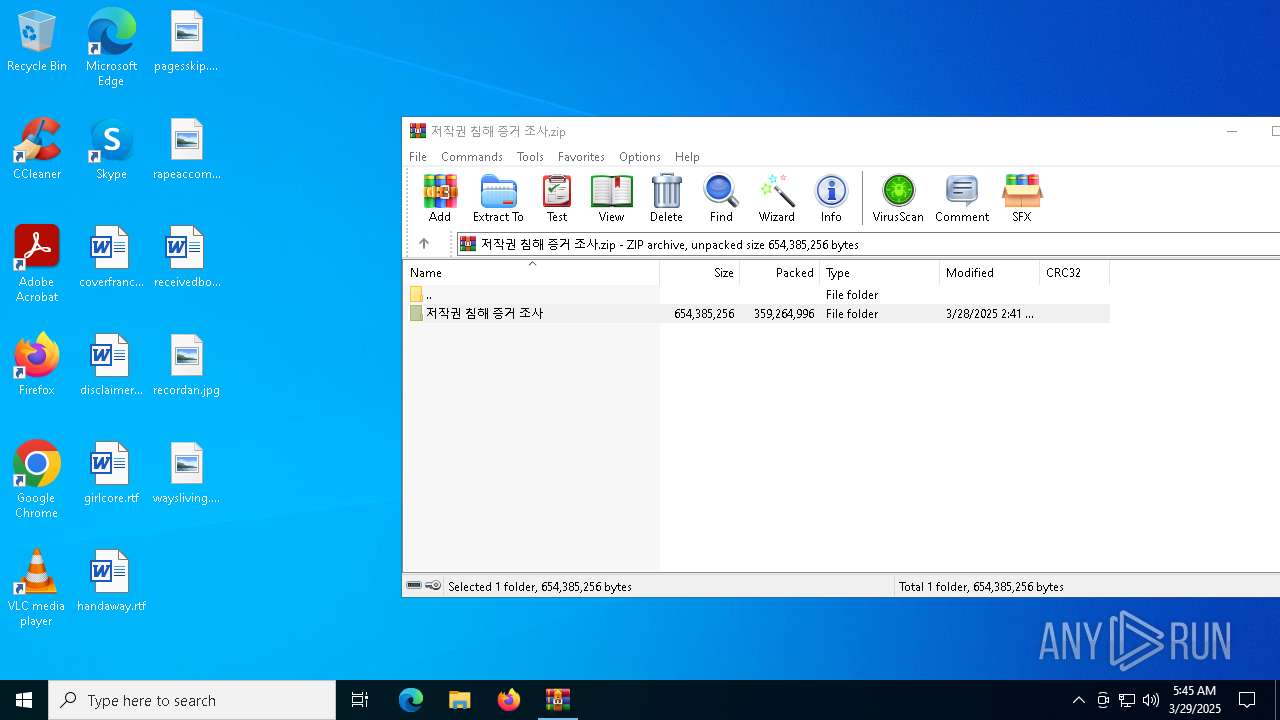
The sample compiled with english language support
- WinRAR.exe (PID: 8484)
- svchost.exe (PID: 2040)
- wmlaunch.exe (PID: 7828)
- msedge.exe (PID: 4276)
Reads Microsoft Office registry keys
- msedge.exe (PID: 4996)
Checks proxy server information
- slui.exe (PID: 8380)
- chrome.exe (PID: 7692)
- msedge.exe (PID: 7972)
Reads the software policy settings
- slui.exe (PID: 8380)
- slui.exe (PID: 896)
- csc.exe (PID: 7492)
Create files in a temporary directory
- svchost.exe (PID: 2040)
- chrome.exe (PID: 7692)
- msedge.exe (PID: 7972)
Autorun file from Downloads
- msedge.exe (PID: 1012)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8484)
- msedge.exe (PID: 4276)
Reads the machine GUID from the registry
- chrome.exe (PID: 7692)
- msedge.exe (PID: 7972)
- wmlaunch.exe (PID: 7828)
- csc.exe (PID: 7492)
Process checks computer location settings
- chrome.exe (PID: 7692)
- msedge.exe (PID: 7972)
Process checks whether UAC notifications are on
- msedge.exe (PID: 7972)
Compiled with Borland Delphi (YARA)
- uS6c~g.exe (PID: 7344)
Creates files or folders in the user directory
- wmlaunch.exe (PID: 7828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
252
Monitored processes
110
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5776 --field-trial-handle=2352,i,13011834736275688685,821821235607298987,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2672 --field-trial-handle=2352,i,13011834736275688685,821821235607298987,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 540 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --mojo-platform-channel-handle=4676 --field-trial-handle=2392,i,14383711459531400544,9814558425678010725,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 728 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7344 -s 156 | C:\Windows\SysWOW64\WerFault.exe | — | uS6c~g.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | "C:\Users\admin\Desktop\저작권 침해 증거 조사\저작권 침해 증거 조사.exe" | C:\Users\admin\Desktop\저작권 침해 증거 조사\저작권 침해 증거 조사.exe | — | explorer.exe | |||||||||||
User: admin Company: Haihaisoft Limited Integrity Level: MEDIUM Description: Haihaisoft PDF Reader Exit code: 269382723 Version: 1.5.7.0 Modules
| |||||||||||||||
| 896 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=4848 --field-trial-handle=2392,i,14383711459531400544,9814558425678010725,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 924 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5332 --field-trial-handle=2352,i,13011834736275688685,821821235607298987,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2640 --field-trial-handle=1880,i,4480183641166802577,487544727340569817,262144 --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1004 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5248 --field-trial-handle=2352,i,13011834736275688685,821821235607298987,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
20 353
Read events
20 293
Write events
59
Delete events
1
Modification events
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CB66DCF30A902F00 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328530 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A22BCA97-E3E1-4953-8362-80B92364E791} | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328530 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1F9E6495-0A13-4D84-BF3B-5437CA074C5F} | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9947E4F30A902F00 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E99B34F40A902F00 | |||
| (PID) Process: | (4996) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
31
Suspicious files
732
Text files
183
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b519.TMP | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b519.TMP | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b538.TMP | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b538.TMP | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b538.TMP | — | |
MD5:— | SHA256:— | |||
| 4996 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
93
DNS requests
109
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4244 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8708 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8708 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8412 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1743588628&P2=404&P3=2&P4=WFcav8PPx2E%2brULH835RSiiIhDuGSyh99tWcFhOHYBafu3WPnE%2fuQuW6LnjEUHlbsSfOlhs4zsA27c3MnyNamA%3d%3d | unknown | — | — | whitelisted |
8412 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1743588628&P2=404&P3=2&P4=WFcav8PPx2E%2brULH835RSiiIhDuGSyh99tWcFhOHYBafu3WPnE%2fuQuW6LnjEUHlbsSfOlhs4zsA27c3MnyNamA%3d%3d | unknown | — | — | whitelisted |
8412 | svchost.exe | HEAD | 200 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1743588628&P2=404&P3=2&P4=WFcav8PPx2E%2brULH835RSiiIhDuGSyh99tWcFhOHYBafu3WPnE%2fuQuW6LnjEUHlbsSfOlhs4zsA27c3MnyNamA%3d%3d | unknown | — | — | whitelisted |
8412 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1743588628&P2=404&P3=2&P4=WFcav8PPx2E%2brULH835RSiiIhDuGSyh99tWcFhOHYBafu3WPnE%2fuQuW6LnjEUHlbsSfOlhs4zsA27c3MnyNamA%3d%3d | unknown | — | — | whitelisted |
8412 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1743588628&P2=404&P3=2&P4=WFcav8PPx2E%2brULH835RSiiIhDuGSyh99tWcFhOHYBafu3WPnE%2fuQuW6LnjEUHlbsSfOlhs4zsA27c3MnyNamA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
7332 | msedge.exe | 104.17.151.117:443 | www.mediafire.com | — | — | whitelisted |
4996 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7332 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7332 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
tranedg.com |
| unknown |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7332 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7332 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7332 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
7332 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2040 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
2040 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
7492 | csc.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
7492 | csc.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |