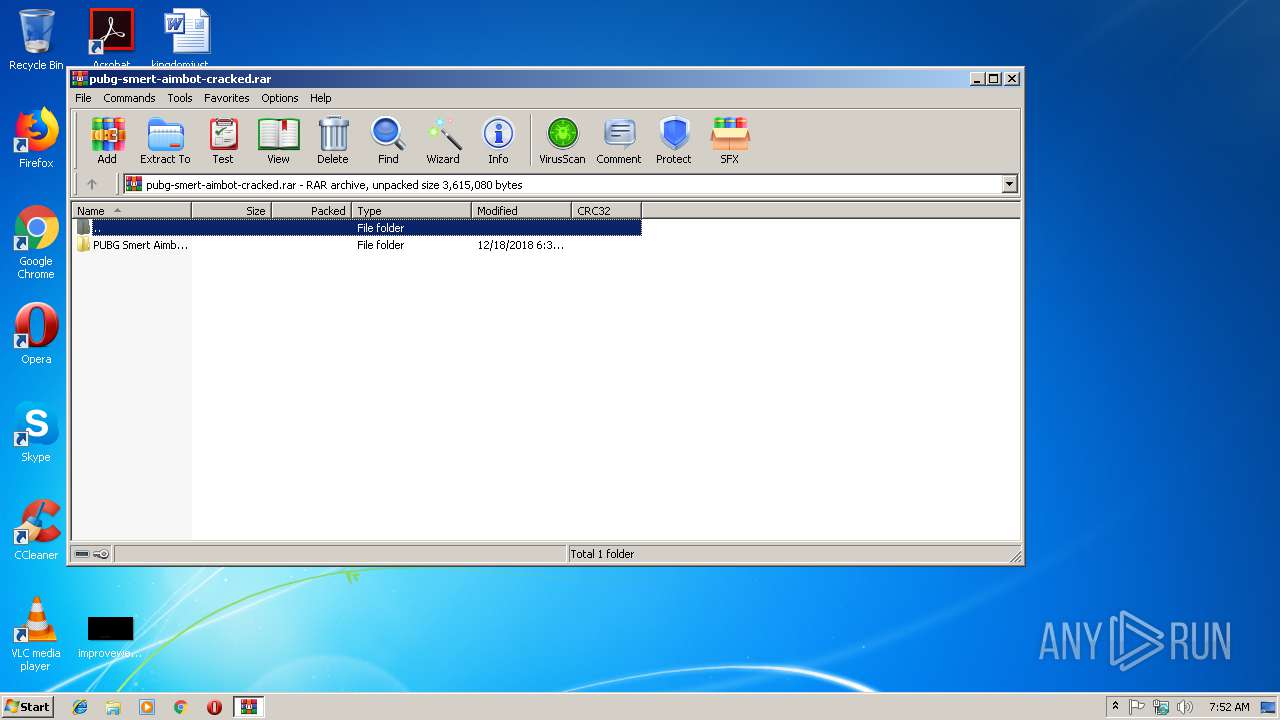
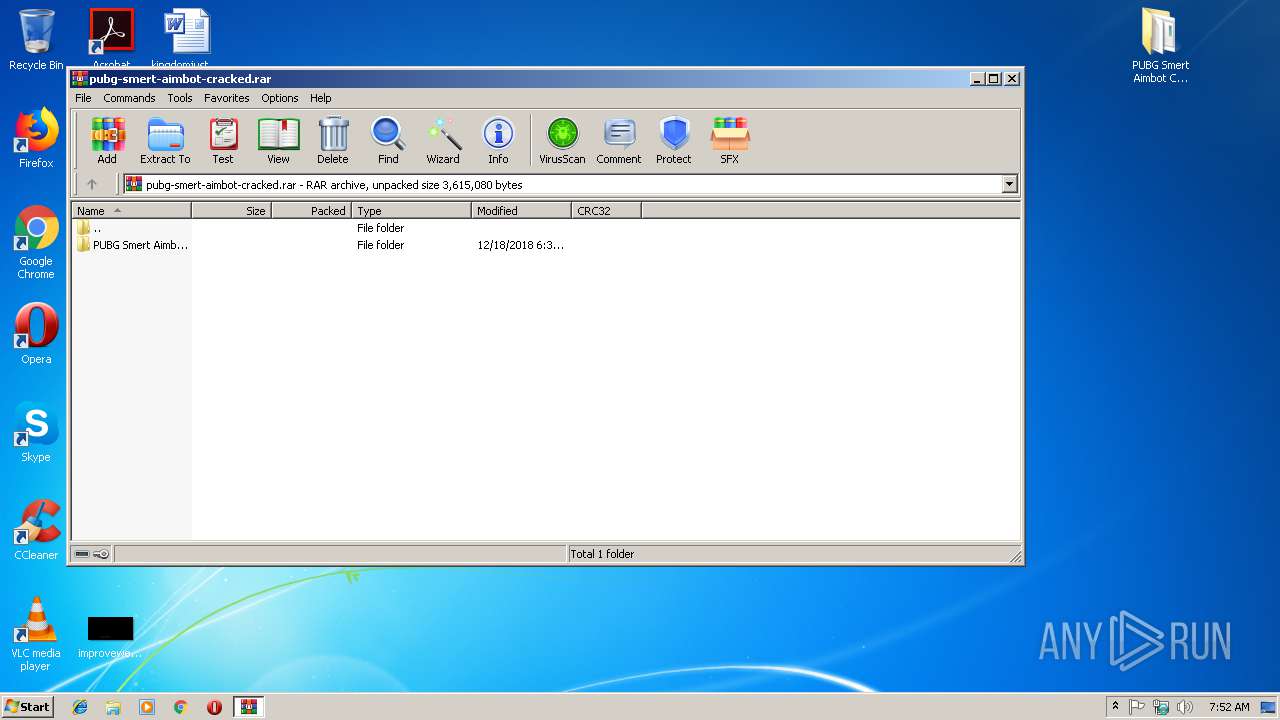
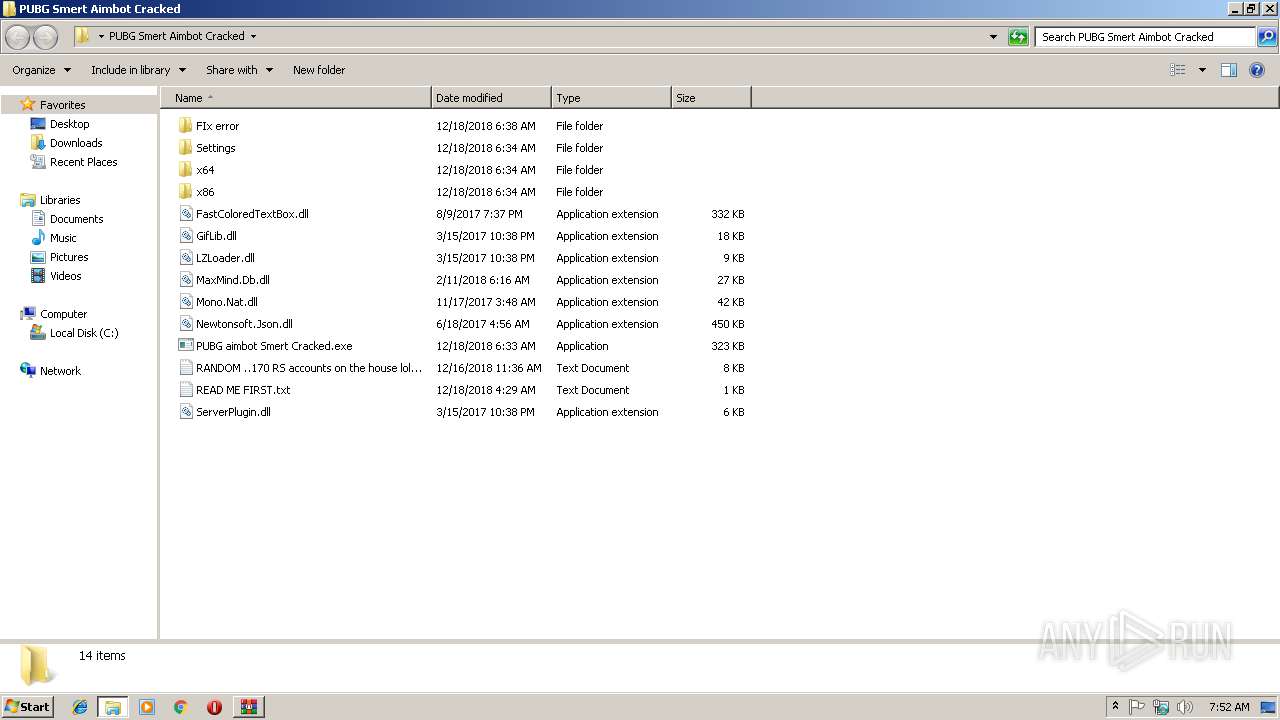
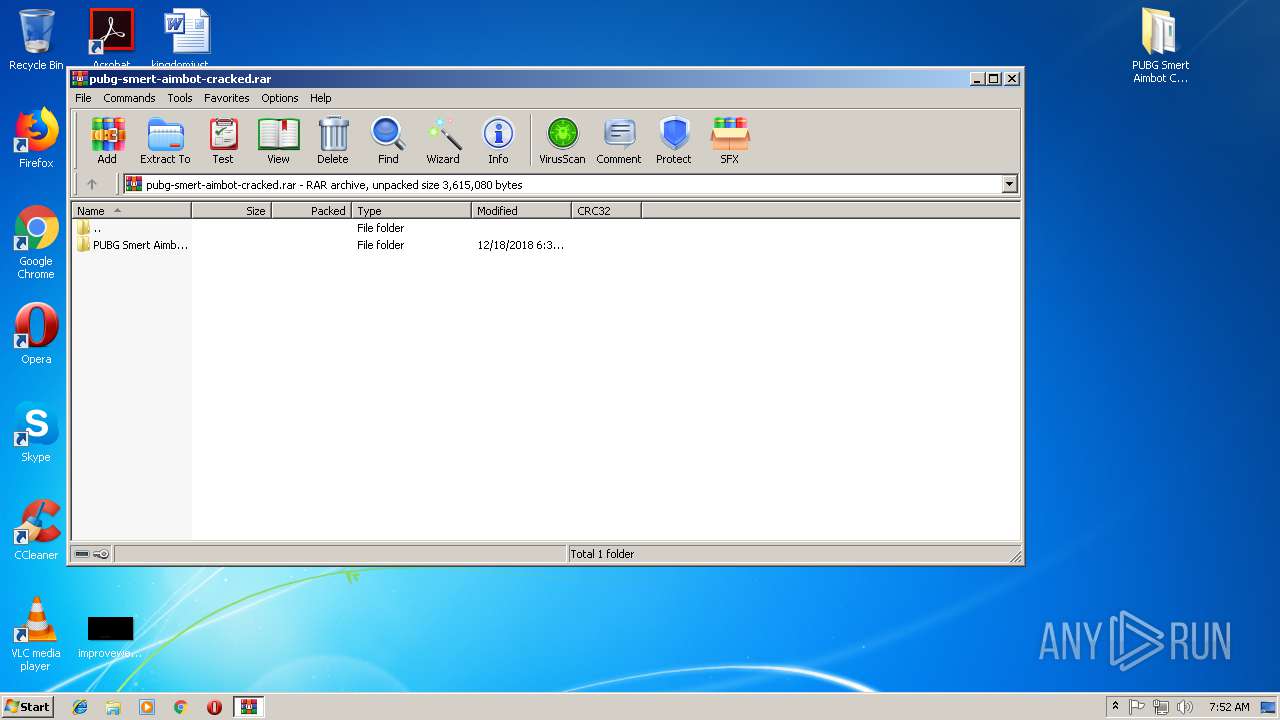
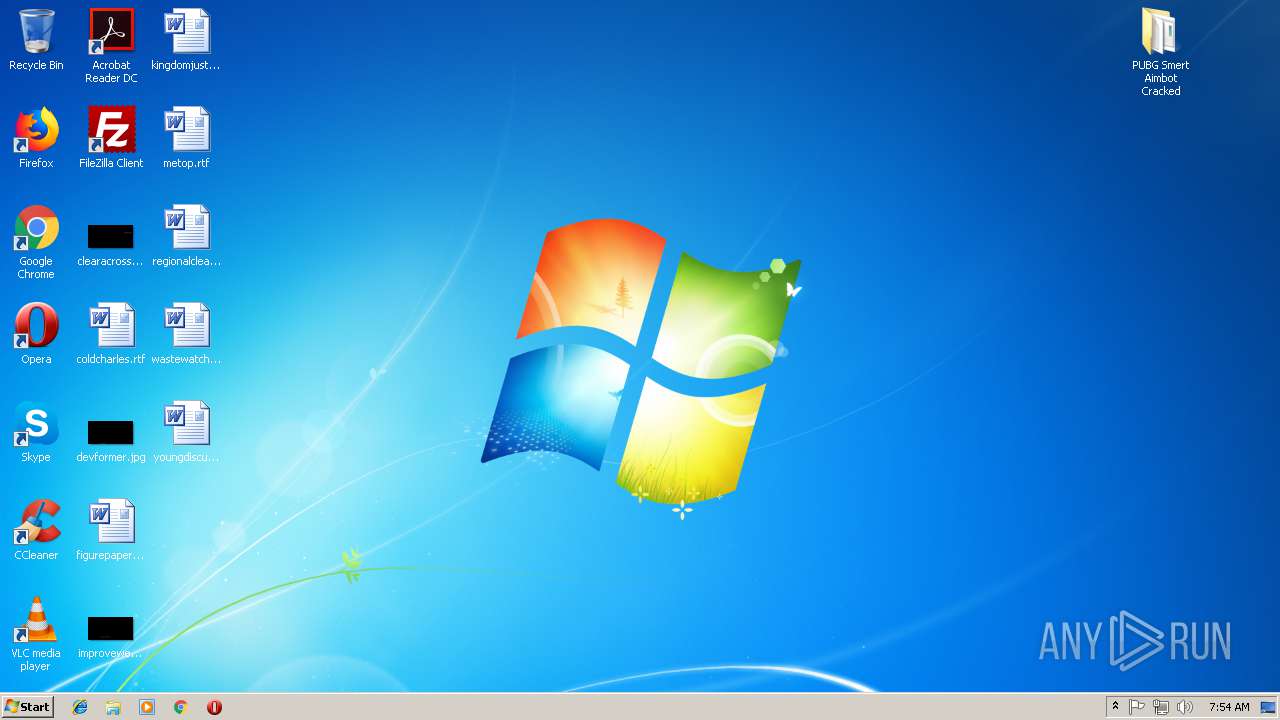
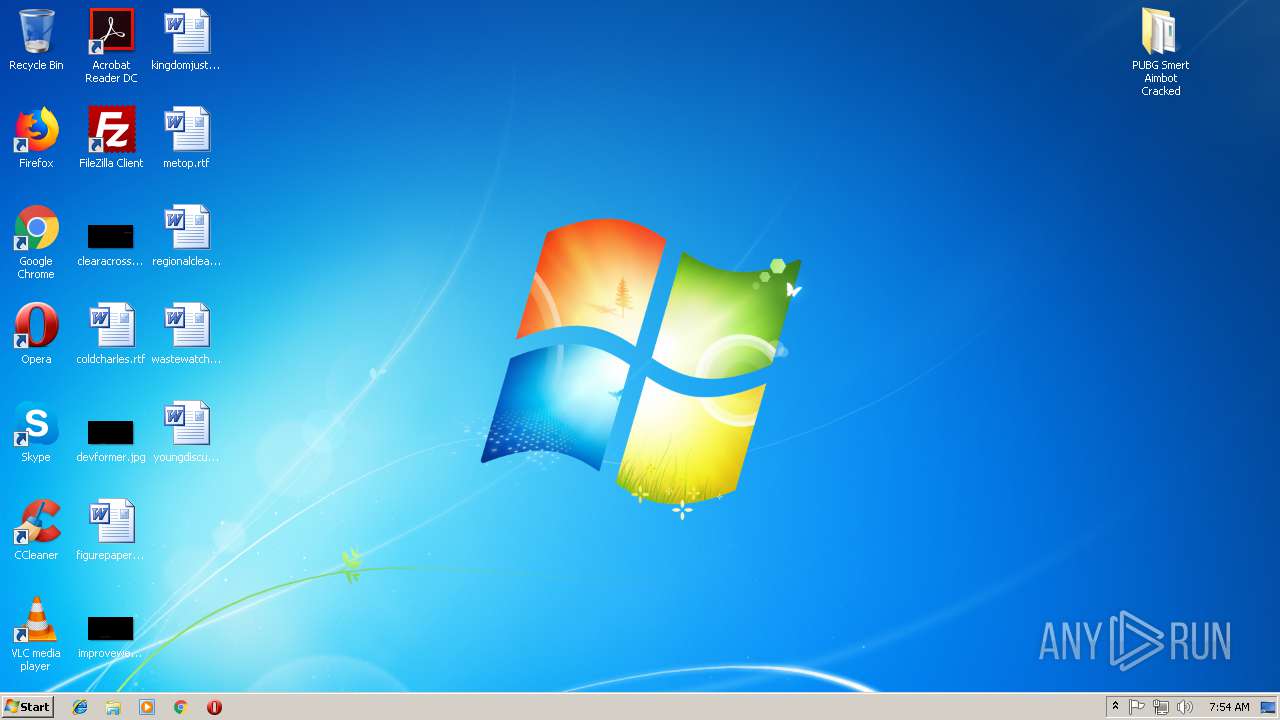
| File name: | pubg-smert-aimbot-cracked.rar |
| Full analysis: | https://app.any.run/tasks/846a4ed9-635b-431e-a893-74848caadc74 |
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | December 18, 2018, 07:52:11 |
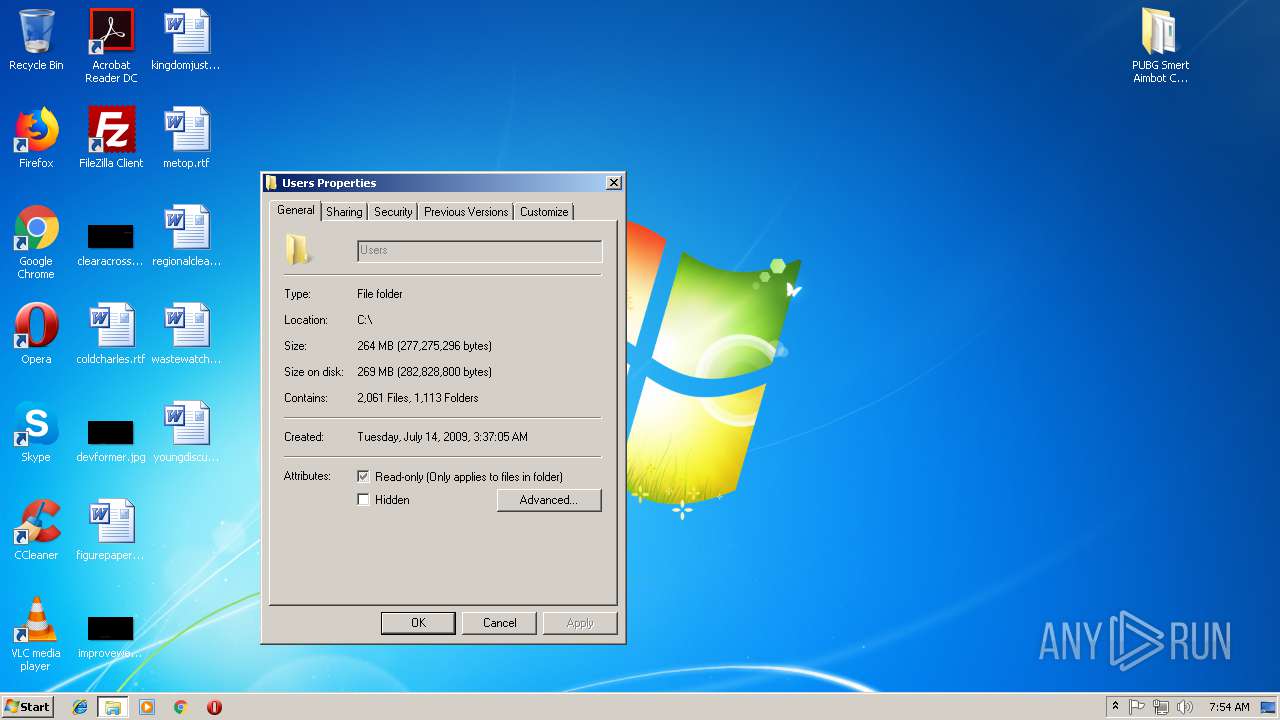
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | EC02608CF26A47FDE38AC7E154BCE15C |
| SHA1: | 2350B372CB6FAB596B2328B5A9979962B3416A25 |
| SHA256: | 03C228BD741F0671D866475CC042C8BFFC49D5F6E69552051ADB64454001F508 |
| SSDEEP: | 49152:tGHpCastwNwJxLCFPA/FqBiZUHNpBaxxun8Fd5ttrQZd+9:tGHyw2PkAQBiZWNyxwq5ttrR9 |
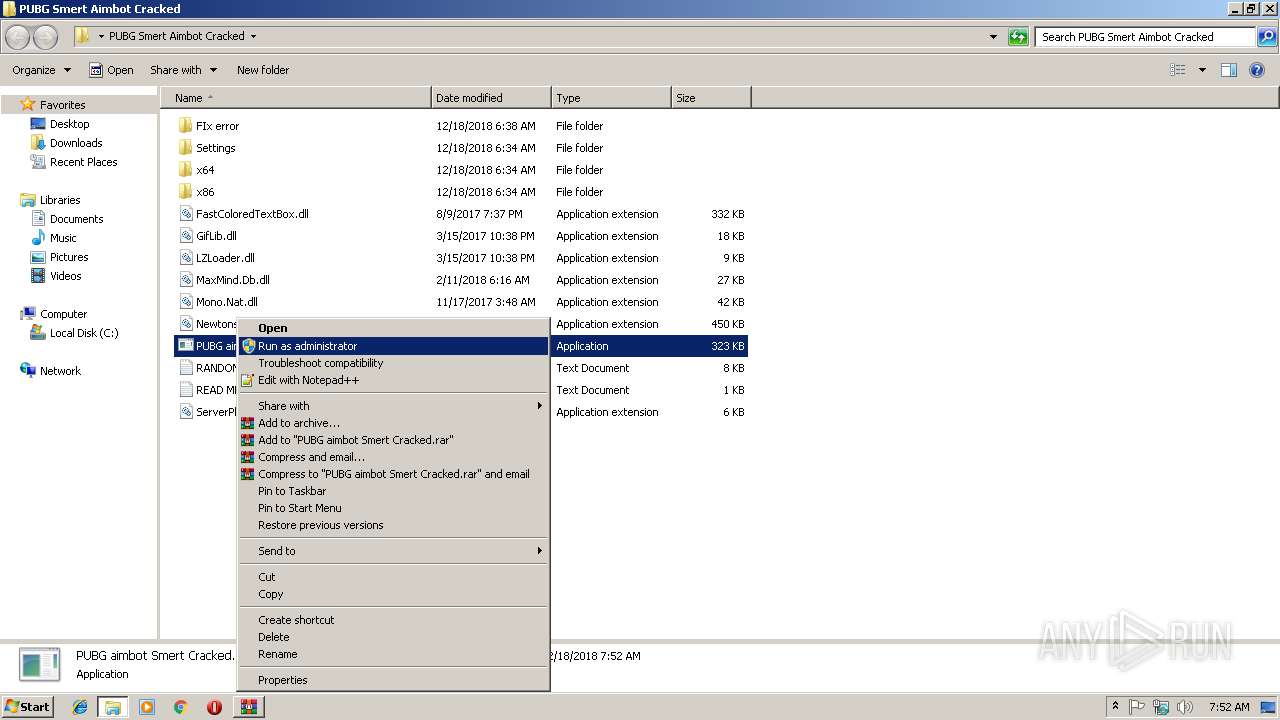
MALICIOUS
Application was dropped or rewritten from another process
- PUBG aimbot Smert Cracked.exe (PID: 2952)
Detected Imminent RAT
- PUBG aimbot Smert Cracked.exe (PID: 2952)
Connects to CnC server
- PUBG aimbot Smert Cracked.exe (PID: 2952)
Changes settings of System certificates
- PUBG aimbot Smert Cracked.exe (PID: 2952)
Actions looks like stealing of personal data
- PUBG aimbot Smert Cracked.exe (PID: 2952)
Runs app for hidden code execution
- PUBG aimbot Smert Cracked.exe (PID: 2952)
Executes PowerShell scripts
- cmd.exe (PID: 612)
- cmd.exe (PID: 2676)
Changes the autorun value in the registry
- PUBG aimbot Smert Cracked.exe (PID: 2952)
SUSPICIOUS
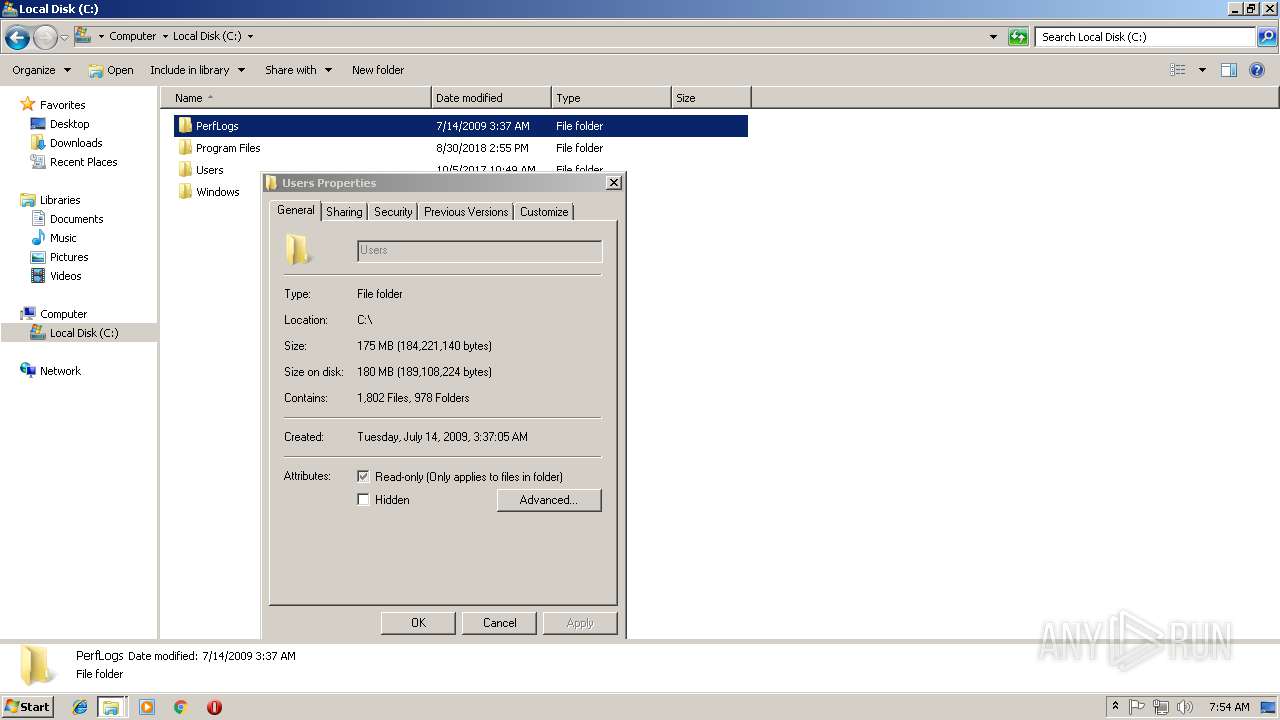
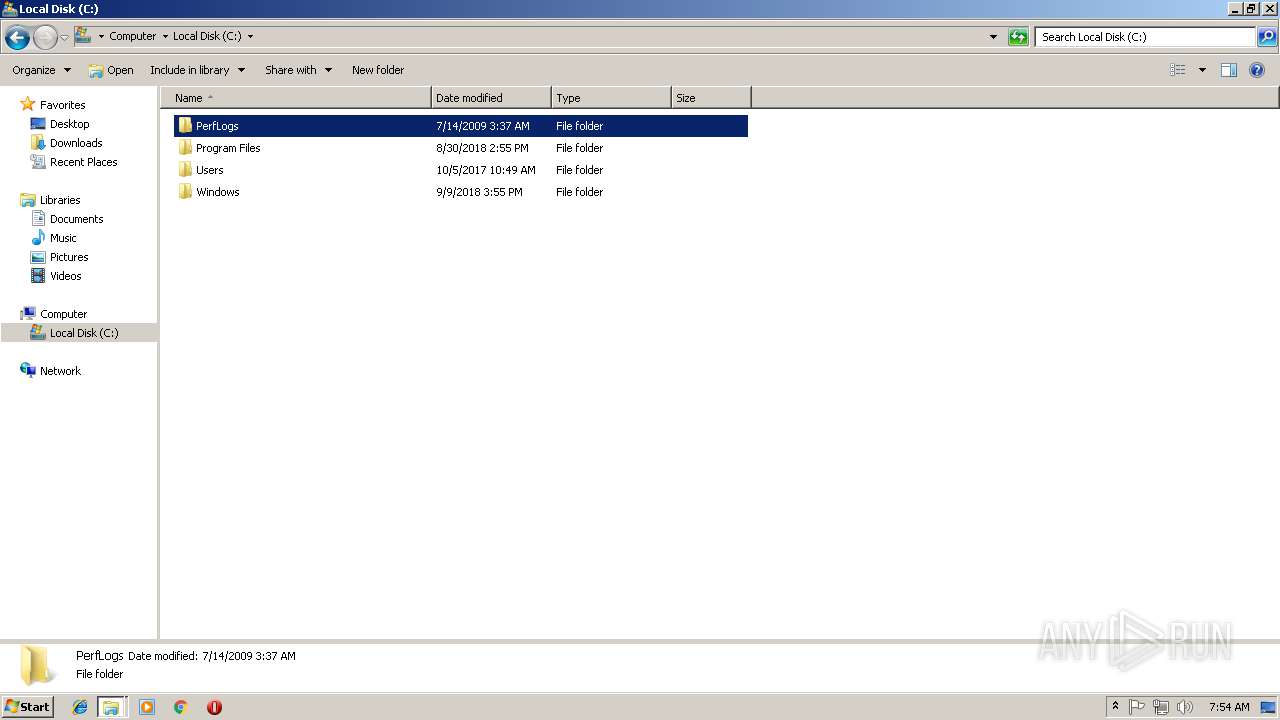
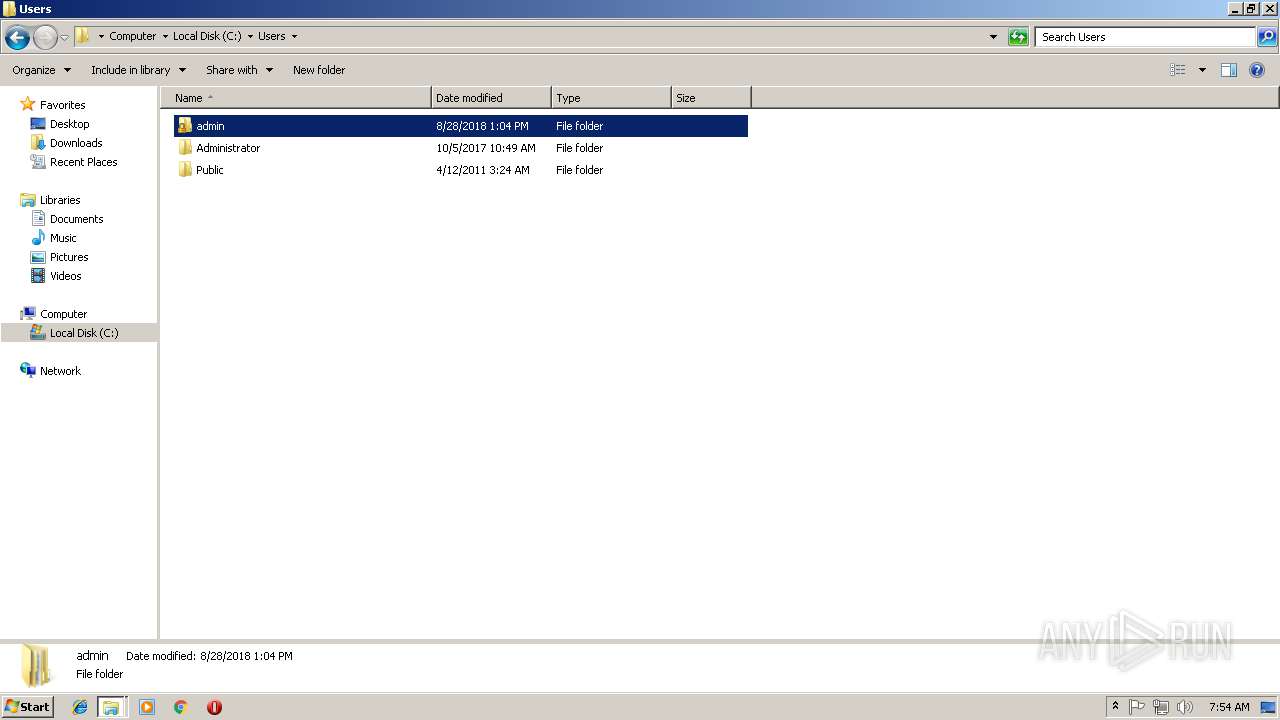
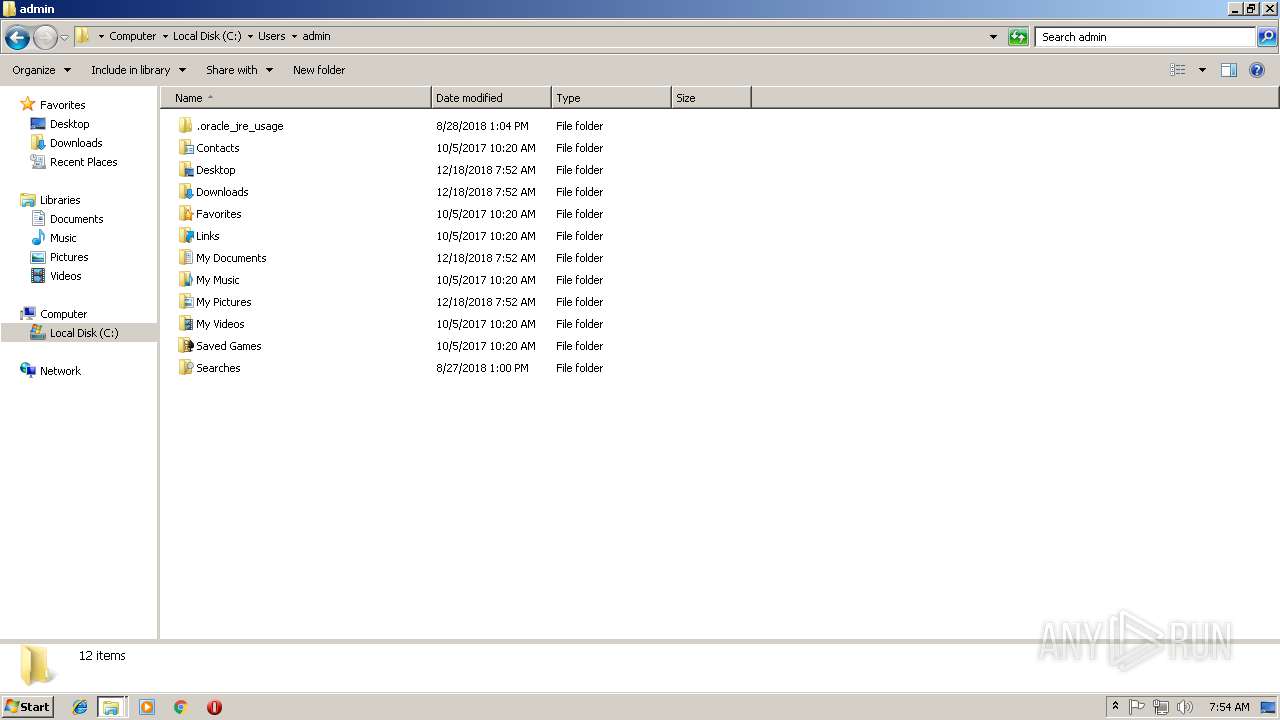
Creates files in the user directory
- PUBG aimbot Smert Cracked.exe (PID: 2952)
- powershell.exe (PID: 2712)
- powershell.exe (PID: 2736)
Connects to unusual port
- PUBG aimbot Smert Cracked.exe (PID: 2952)
Executable content was dropped or overwritten
- PUBG aimbot Smert Cracked.exe (PID: 2952)
Adds / modifies Windows certificates
- PUBG aimbot Smert Cracked.exe (PID: 2952)
Starts CMD.EXE for commands execution
- PUBG aimbot Smert Cracked.exe (PID: 2952)
INFO
Application launched itself
- chrome.exe (PID: 2788)
- iexplore.exe (PID: 960)
Reads settings of System Certificates
- chrome.exe (PID: 2788)
Changes internet zones settings
- iexplore.exe (PID: 960)
Creates files in the user directory
- opera.exe (PID: 4076)
Reads Internet Cache Settings
- iexplore.exe (PID: 2212)
Reads internet explorer settings
- iexplore.exe (PID: 2212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
66
Monitored processes
23
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=924,6797910326150638326,5275441728870264966,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4F5DB95582A7CA59110DBB13395D0ECD --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4F5DB95582A7CA59110DBB13395D0ECD --renderer-client-id=8 --mojo-platform-channel-handle=3948 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2608 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 612 | "cmd.exe" | C:\Windows\system32\cmd.exe | — | PUBG aimbot Smert Cracked.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 4294967295 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 792 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 960 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=924,6797910326150638326,5275441728870264966,131072 --enable-features=PasswordImport --service-pipe-token=268F0814BC18F7DE22E9E85AC710968D --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=268F0814BC18F7DE22E9E85AC710968D --renderer-client-id=5 --mojo-platform-channel-handle=1880 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:960 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2264 | C:\Windows\system32\wbem\WmiApSrv.exe | C:\Windows\system32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=924,6797910326150638326,5275441728870264966,131072 --enable-features=PasswordImport --service-pipe-token=DD4618867364008CAD93ED67A3E75927 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=DD4618867364008CAD93ED67A3E75927 --renderer-client-id=3 --mojo-platform-channel-handle=2096 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
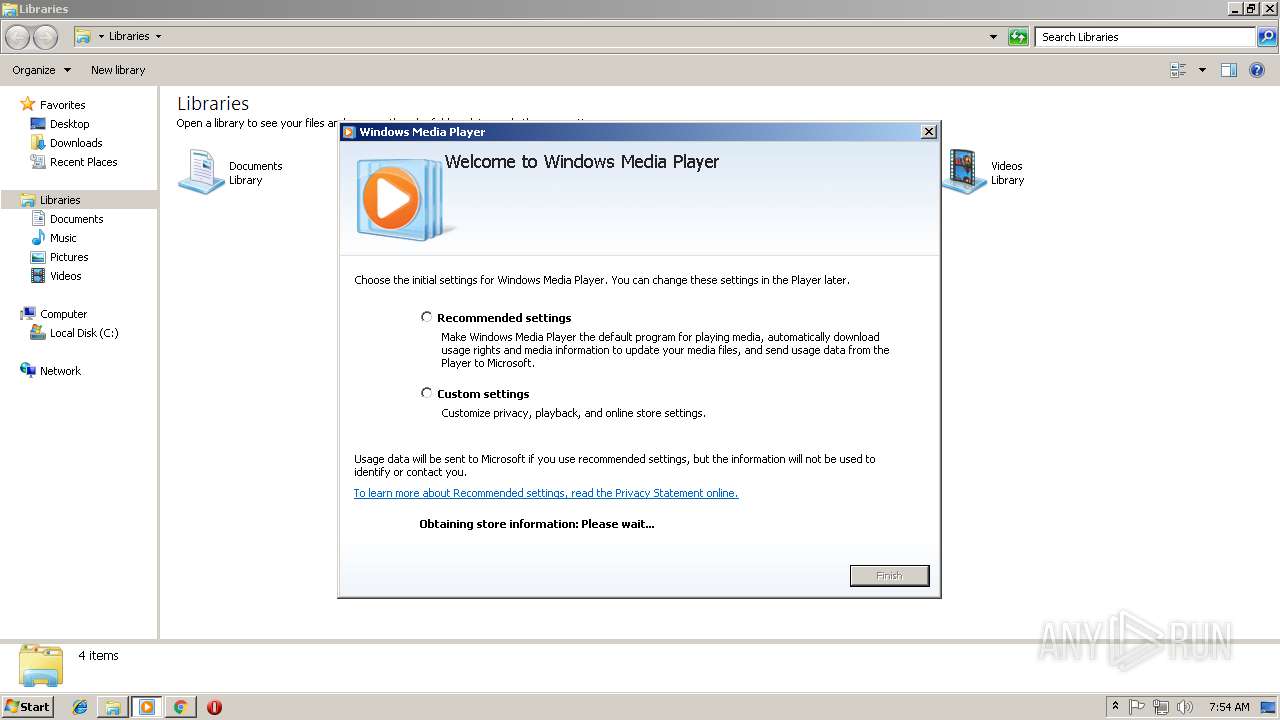
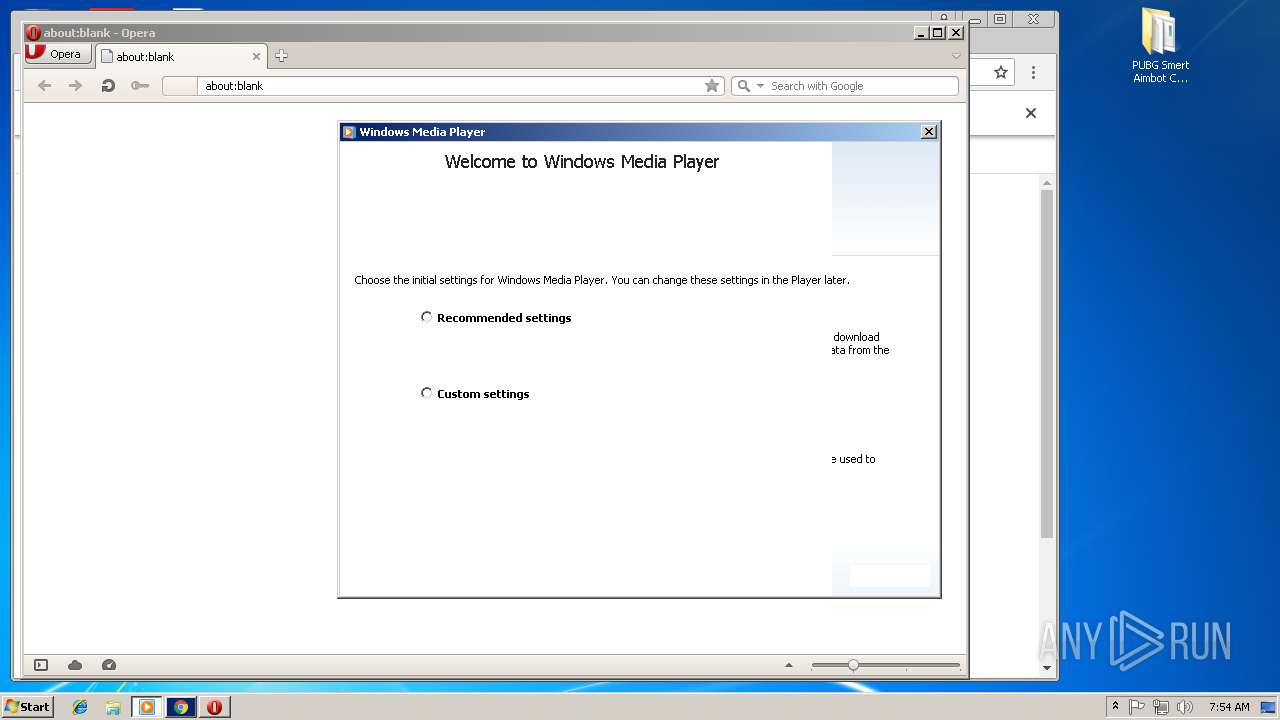
| 2392 | "C:\Program Files\Windows Media Player\setup_wm.exe" /RunOnce:"C:\Program Files\Windows Media Player\wmplayer.exe" /prefetch:1 | C:\Program Files\Windows Media Player\setup_wm.exe | wmplayer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Media Configuration Utility Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 232
Read events
1 573
Write events
655
Delete events
4
Modification events
| (PID) Process: | (3404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3404) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\pubg-smert-aimbot-cracked.rar | |||
| (PID) Process: | (3404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2952) PUBG aimbot Smert Cracked.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | system |
Value: C:\Users\admin\AppData\Roaming\system\system.exe | |||
| (PID) Process: | (2952) PUBG aimbot Smert Cracked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\PUBG aimbot Smert Cracked_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
1
Suspicious files
114
Text files
75
Unknown types
7
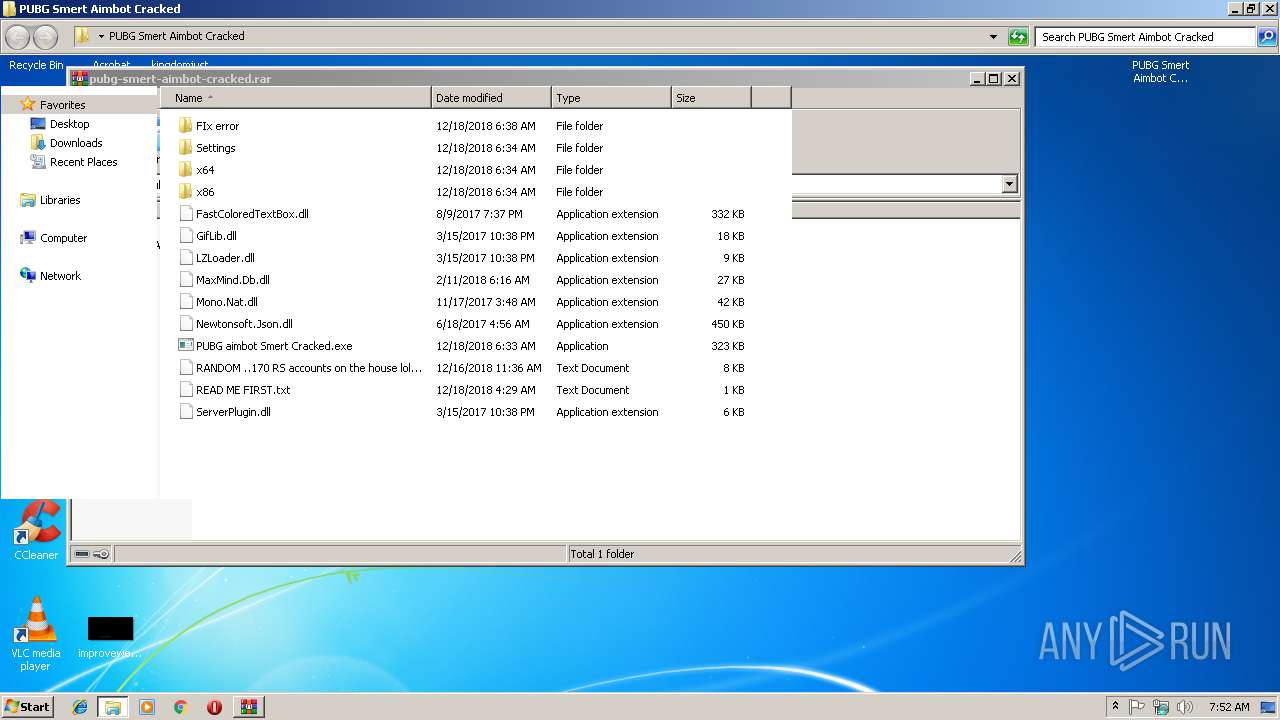
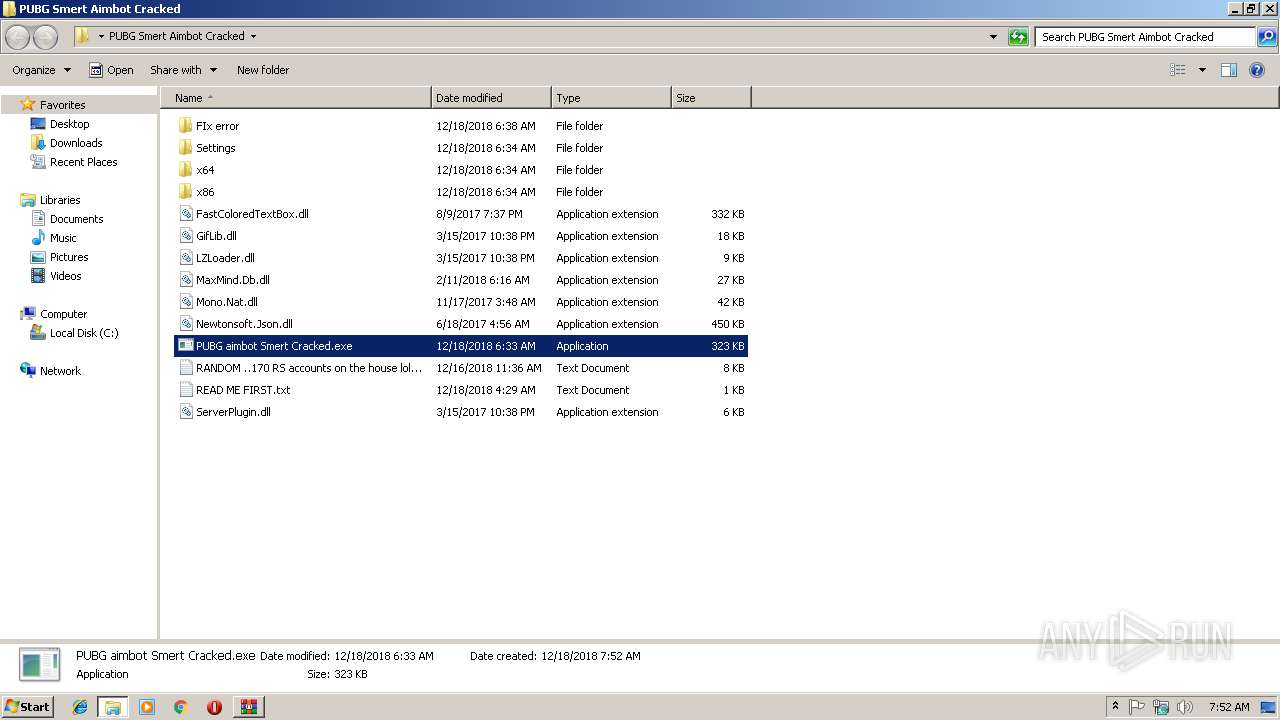
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3404 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3404.5052\PUBG Smert Aimbot Cracked\FastColoredTextBox.dll | — | |
MD5:— | SHA256:— | |||
| 3404 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3404.5052\PUBG Smert Aimbot Cracked\FIx error\Fix.html | — | |
MD5:— | SHA256:— | |||
| 3404 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3404.5052\PUBG Smert Aimbot Cracked\GifLib.dll | — | |
MD5:— | SHA256:— | |||
| 3404 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3404.5052\PUBG Smert Aimbot Cracked\LZLoader.dll | — | |
MD5:— | SHA256:— | |||
| 3404 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3404.5052\PUBG Smert Aimbot Cracked\MaxMind.Db.dll | — | |
MD5:— | SHA256:— | |||
| 3404 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3404.5052\PUBG Smert Aimbot Cracked\Mono.Nat.dll | — | |
MD5:— | SHA256:— | |||
| 3404 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3404.5052\PUBG Smert Aimbot Cracked\Newtonsoft.Json.dll | — | |
MD5:— | SHA256:— | |||
| 3404 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3404.5052\PUBG Smert Aimbot Cracked\PUBG aimbot Smert Cracked.exe | — | |
MD5:— | SHA256:— | |||
| 3404 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3404.5052\PUBG Smert Aimbot Cracked\RANDOM ..170 RS accounts on the house lol.txt | — | |
MD5:— | SHA256:— | |||
| 3404 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3404.5052\PUBG Smert Aimbot Cracked\READ ME FIRST.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
23
DNS requests
19
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2392 | setup_wm.exe | GET | 302 | 2.16.186.41:80 | http://redir.metaservices.microsoft.com/redir/allservices/?sv=5&version=12.0.7601.17514&locale=409&userlocale=409&geoid=f4&parch=x86&arch=x86 | unknown | — | — | whitelisted |
4076 | opera.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAOXQPQlVpLtFek%2BmcpabOk%3D | US | der | 471 b | whitelisted |
4076 | opera.exe | GET | 200 | 66.225.197.197:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 543 b | whitelisted |
2392 | setup_wm.exe | GET | 200 | 2.16.186.98:80 | http://onlinestores.metaservices.microsoft.com/serviceswitching/AllServices.aspx?sv=5&version=12.0.7601.17514&locale=409&userlocale=409&geoid=f4&parch=x86&arch=x86 | unknown | xml | 546 b | whitelisted |
2392 | setup_wm.exe | GET | 200 | 2.16.186.98:80 | http://onlinestores.metaservices.microsoft.com/bing/bing.xml | unknown | text | 523 b | whitelisted |
960 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2952 | PUBG aimbot Smert Cracked.exe | 45.55.57.244:443 | www.iptrackeronline.com | Digital Ocean, Inc. | US | malicious |
2788 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2788 | chrome.exe | 172.217.16.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2788 | chrome.exe | 172.217.16.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
2392 | setup_wm.exe | 2.16.186.98:80 | onlinestores.metaservices.microsoft.com | Akamai International B.V. | — | whitelisted |
2392 | setup_wm.exe | 2.16.186.41:80 | redir.metaservices.microsoft.com | Akamai International B.V. | — | whitelisted |
4076 | opera.exe | 82.145.215.40:443 | certs.opera.com | Opera Software AS | — | whitelisted |
4076 | opera.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
960 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4076 | opera.exe | 66.225.197.197:80 | crl4.digicert.com | CacheNetworks, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
lol1342343.ddns.net |
| malicious |
www.iptrackeronline.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
redir.metaservices.microsoft.com |
| whitelisted |
onlinestores.metaservices.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2952 | PUBG aimbot Smert Cracked.exe | A Network Trojan was detected | MALWARE [PTsecurity] Imminent Monitor RAT (outbound) |
2952 | PUBG aimbot Smert Cracked.exe | A Network Trojan was detected | MALWARE [PTsecurity] Imminent Monitor RAT (outbound) |
2 ETPRO signatures available at the full report