| File name: | 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b |
| Full analysis: | https://app.any.run/tasks/04fa0119-1230-49f6-926e-c1576c8c8112 |
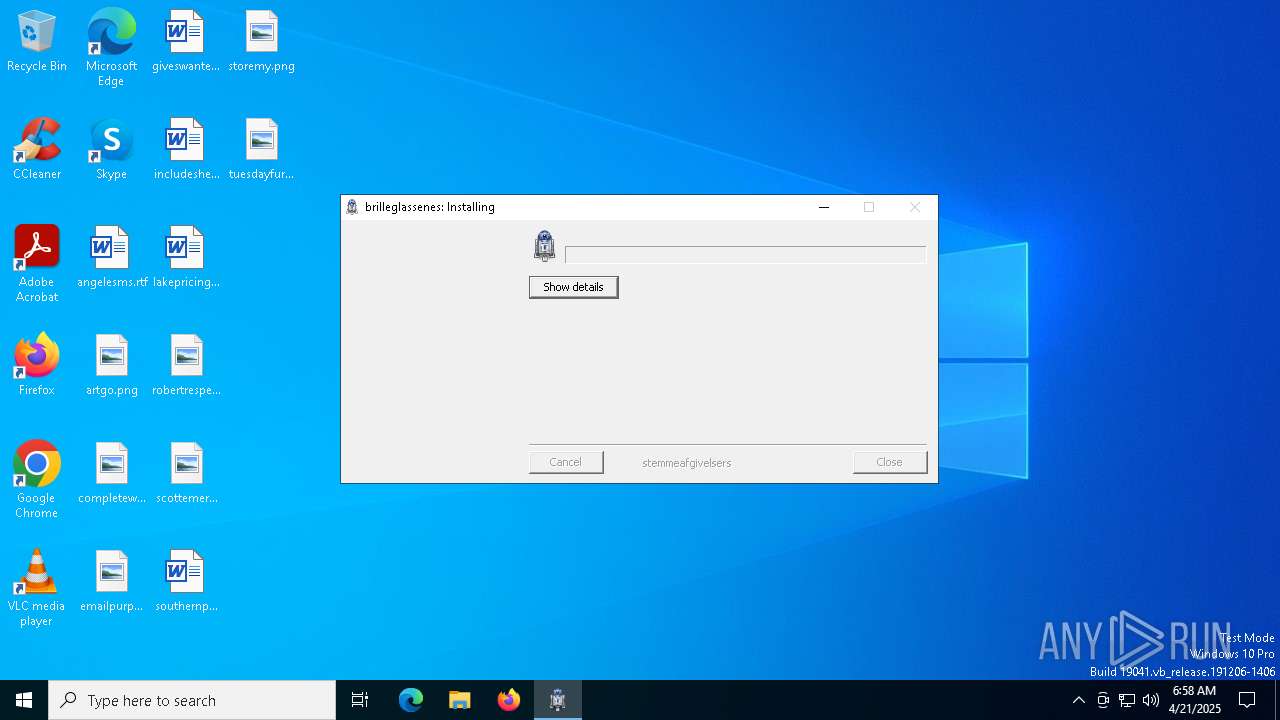
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | April 21, 2025, 06:58:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 25727BE97A9FF477EAF9F5EDE2517D4A |
| SHA1: | 66DE55B95E1F19B9C626E35126E9C6DBAC8680B0 |
| SHA256: | 037AFB04ECB79C472588E6F1B3571ABB8903AF2FC86F1A8CA2E2ACB63C14335B |
| SSDEEP: | 6144:2zgE3ixXUZZvUHOHYh0qfYNEP1Z5qhaiVptYFni0/Hz/fblOdr60VEZ0q568jX8h:28kZZvUuHmZYNEv5Mn8lT3be602Qjr |
MALICIOUS
GULOADER SHELLCODE has been detected (YARA)
- 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe (PID: 5280)
GULOADER has been detected (YARA)
- 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe (PID: 5280)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe (PID: 5280)
Executable content was dropped or overwritten
- 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe (PID: 5280)
The process creates files with name similar to system file names
- 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe (PID: 5280)
Malware-specific behavior (creating "System.dll" in Temp)
- 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe (PID: 5280)
INFO
Creates files or folders in the user directory
- 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe (PID: 5280)
Reads the computer name
- 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe (PID: 5280)
Checks supported languages
- 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe (PID: 5280)
Create files in a temporary directory
- 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe (PID: 5280)
The sample compiled with english language support
- 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe (PID: 5280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
guloader
(PID) Process(5280) 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe
C2 (1)https://cdn.discordapp.com/attachments/1232238430654562385/1235389222089785354/mOMLlKLVAqC185.bin?ex=6634315e&is=6632dfde&hm=f5cd118659d30c524ac64f127bbb36253100fb197f040cd3c339f2cbdc6872b4&
Strings (25)\Microsoft.NET\Framework\v4.0.30319\msbuild.exe
$_+
Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:121.0) Gecko/20100101 Firefox/121.0
wininet.dll
KERNELBASE.DLL
Msi.dll
psapi.dll
user32
advapi32
shell32
Publisher
windir=
TEMP=
mshtml.dll
SYSTEM\ControlSet001\Enum\ACPI\PNP0C0C
\system32\
\syswow64\
Startup key
Software\Microsoft\Windows\CurrentVersion\RunOnce
\subfolder1
C:\Program Files\qga\qga.exe
C:\Program Files\Qemu-ga\qemu-ga.exe
CONOUT$
CONIN$
\befstningers.exe
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:08:05 00:46:27+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 117760 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3217 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.0.0 |
| ProductVersionNumber: | 1.3.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileDescription: | intercident |
| InternalName: | oecodomical irisation.exe |
| LegalCopyright: | jackety funktionsanslagets |
| LegalTrademarks: | aalegaardsrettens |
Total processes
129
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5280 | "C:\Users\admin\AppData\Local\Temp\037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe" | C:\Users\admin\AppData\Local\Temp\037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: intercident Modules
guloader(PID) Process(5280) 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe C2 (1)https://cdn.discordapp.com/attachments/1232238430654562385/1235389222089785354/mOMLlKLVAqC185.bin?ex=6634315e&is=6632dfde&hm=f5cd118659d30c524ac64f127bbb36253100fb197f040cd3c339f2cbdc6872b4& Strings (25)\Microsoft.NET\Framework\v4.0.30319\msbuild.exe $_+ Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:121.0) Gecko/20100101 Firefox/121.0 wininet.dll KERNELBASE.DLL Msi.dll psapi.dll user32 advapi32 shell32 Publisher windir= TEMP= mshtml.dll SYSTEM\ControlSet001\Enum\ACPI\PNP0C0C \system32\ \syswow64\ Startup key Software\Microsoft\Windows\CurrentVersion\RunOnce \subfolder1 C:\Program Files\qga\qga.exe C:\Program Files\Qemu-ga\qemu-ga.exe CONOUT$ CONIN$ \befstningers.exe | |||||||||||||||
| 6040 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6456 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 251
Read events
265
Write events
986
Delete events
0
Modification events
| (PID) Process: | (5280) 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Subtilised229\Sankthansurters |
| Operation: | write | Name: | Gisela |
Value: %pentatriacontane%\forandrendes\graped.Ned | |||
| (PID) Process: | (5280) 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\unsonantal\Uninstall\Apollonistic |
| Operation: | write | Name: | Livspoint56 |
Value: 0 | |||
Executable files
1
Suspicious files
3
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5280 | 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe | C:\Users\admin\AppData\Roaming\ration\basketags\pelsberederiets\Bedmmelseskomite158\Weiselbergite153\delkorallen.txt | text | |
MD5:8A984F7616B446E3E097AAB82DC08B62 | SHA256:E81D10AEADC1D5E722479E467100BB1AB7D53853B54FA1C8D1753D0D0D058020 | |||
| 5280 | 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe | C:\Users\admin\AppData\Roaming\ration\basketags\pelsberederiets\Bedmmelseskomite158\Weiselbergite153\intellektualistiske.vol | binary | |
MD5:F9235913481923D5F4E6741CF81DFD31 | SHA256:AB7FD77D65E0C85E03E1249AAA42CCCA9A611B6A03EA8237BCA7460E87BCC999 | |||
| 5280 | 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe | C:\Users\admin\AppData\Local\Temp\nscC8D2.tmp\System.dll | executable | |
MD5:6F5257C0B8C0EF4D440F4F4FCE85FB1B | SHA256:B7CCB923387CC346731471B20FC3DF1EAD13EC8C2E3147353C71BB0BD59BC8B1 | |||
| 5280 | 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe | C:\Users\admin\AppData\Roaming\ration\basketags\pelsberederiets\Tlperagtigt\Relumining.brn | binary | |
MD5:396FB5CBEE90574CCAF95DDB324C05EC | SHA256:3943F9FF3B171C8F37DBCAD7138B0F7D725191D71C2755501880ABCB0CC81CFC | |||
| 5280 | 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe | C:\Users\admin\AppData\Roaming\ration\basketags\pelsberederiets\Bedmmelseskomite158\Weiselbergite153\Grundliniers.Bar | binary | |
MD5:95C5900744EB2A2AA1CE2B7BDA71D74C | SHA256:C0A0D07061DE3C5DE1279D0009C027DDBC9AC635F4301ED4FCCD8588FEB07805 | |||
| 5280 | 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe | C:\Users\admin\AppData\Local\Temp\tmc.ini | text | |
MD5:ECB33F100E1FCA0EB01B36757EF3CAC8 | SHA256:8734652A2A9E57B56D6CBD22FA9F305FC4691510606BCD2DFCA248D1BF9E79C7 | |||
| 5280 | 037afb04ecb79c472588e6f1b3571abb8903af2fc86f1a8ca2e2acb63c14335b.exe | C:\Users\admin\AppData\Local\Temp\App.ini | text | |
MD5:8669FF23B6E38D3F35902AB9FBB8104A | SHA256:17687D759D25C77DD94DB46570AD9C70EFE1B2C924B4E0A70BD18D8192ED592F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
20
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
— | — | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
6544 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
5200 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
5200 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 23.63.118.230:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |