| File name: | logs.exe |
| Full analysis: | https://app.any.run/tasks/5f61bc2d-c556-4557-b980-14e5a88d185e |
| Verdict: | Malicious activity |
| Threats: | Meduza Stealer is an information-stealing malware primarily targeting Windows systems, designed to harvest sensitive data such as login credentials, browsing histories, cookies, cryptocurrency wallets, and password manager data. It has advanced anti-detection mechanisms, allowing it to evade many antivirus programs. The malware is distributed through various means, including phishing emails and malicious links. It’s marketed on underground forums and Telegram channels. |
| Analysis date: | July 08, 2025, 16:13:52 |
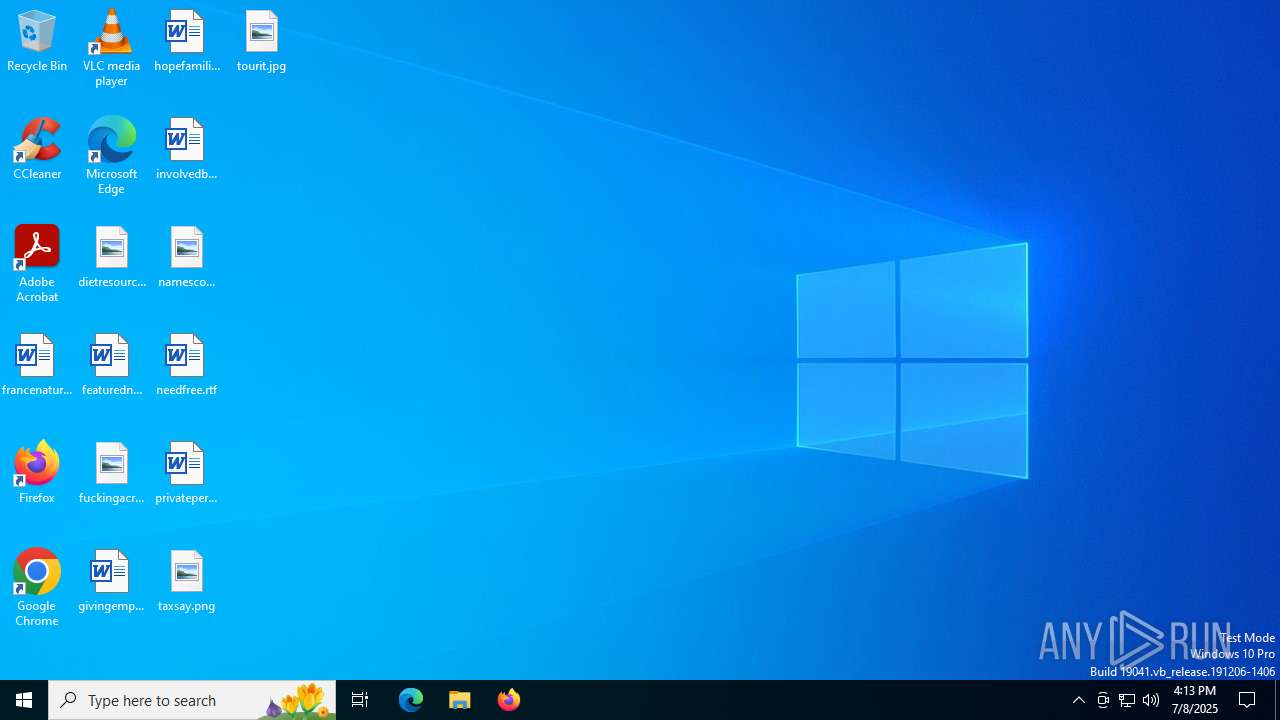
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | C575968B3DF5F0A8B2A022D14FAB01F6 |
| SHA1: | F2C4138136C3BB7227D652CE8A17BD966E5C2477 |
| SHA256: | 035F7FE000669479A182EF61034DC4B4DD89D15C47F830FD9C2E28F68F40C466 |
| SSDEEP: | 24576:d6AJLxI59fFXmVlo1wdMjmhR1MxlZ5rWoDkeQIHYnEPuJBXiDGLIZahks6:kAJLxI59fFXmVlo1wdMjm31MzZ5KoDkV |
MALICIOUS
Scans artifacts that could help determine the target
- logs.exe (PID: 2604)
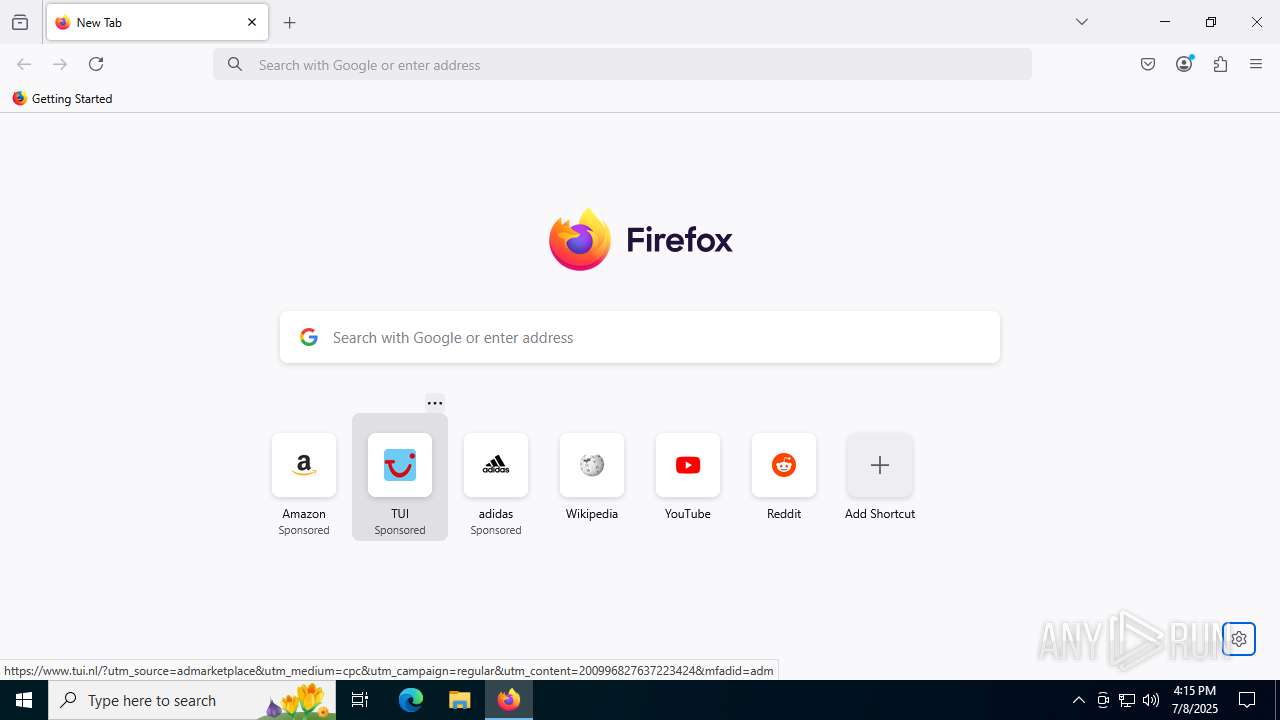
Steals credentials from Web Browsers
- logs.exe (PID: 2604)
PUREHVNC has been detected (YARA)
- logs.exe (PID: 2604)
PURELOGS has been detected (SURICATA)
- logs.exe (PID: 2604)
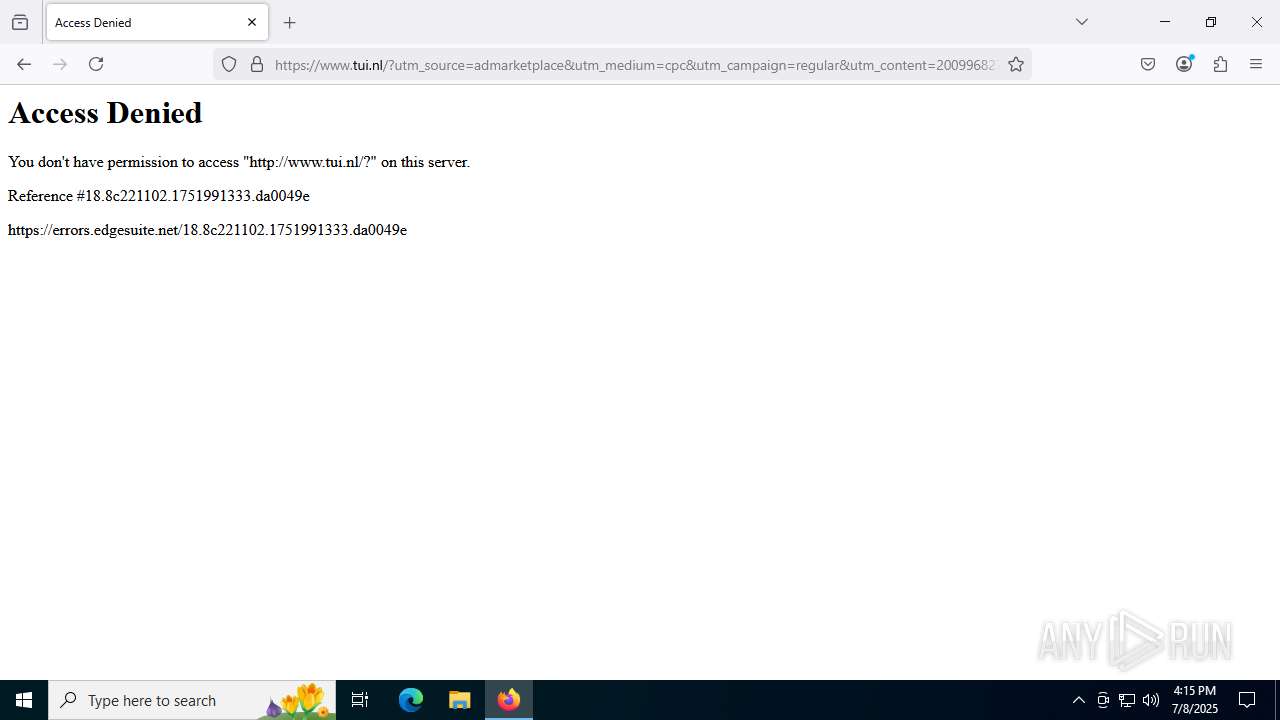
Connects to the CnC server
- logs.exe (PID: 2604)
MEDUZA has been detected (YARA)
- logs.exe (PID: 2604)
Actions looks like stealing of personal data
- logs.exe (PID: 2604)
SUSPICIOUS
Connects to unusual port
- logs.exe (PID: 2604)
Multiple wallet extension IDs have been found
- logs.exe (PID: 2604)
INFO
Checks supported languages
- logs.exe (PID: 2604)
Reads Environment values
- logs.exe (PID: 2604)
Reads the machine GUID from the registry
- logs.exe (PID: 2604)
Reads the computer name
- logs.exe (PID: 2604)
Reads Microsoft Office registry keys
- logs.exe (PID: 2604)
- firefox.exe (PID: 4676)
Application launched itself
- msedge.exe (PID: 2764)
- msedge.exe (PID: 2320)
- firefox.exe (PID: 4100)
- firefox.exe (PID: 4676)
- chrome.exe (PID: 420)
Manual execution by a user
- firefox.exe (PID: 4100)
Reads the software policy settings
- slui.exe (PID: 8184)
Checks proxy server information
- slui.exe (PID: 8184)
.NET Reactor protector has been detected
- logs.exe (PID: 2604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2100:12:22 04:22:54+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 562176 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8b3ae |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | Mcekk.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | Mcekk.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
184
Monitored processes
44
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disable-fre --no-default-browser-check --no-first-run --no-sandbox --allow-no-sandbox-job --disable-gpu --mute-audio --disable-audio --user-data-dir="C:\Users\admin\AppData\Local\Temp\vszq5wsv.ese" | C:\Program Files\Google\Chrome\Application\chrome.exe | logs.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-sandbox --mute-audio --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\vszq5wsv.ese" --field-trial-handle=2220,i,8112870976113181554,3068393653443554139,262144 --variations-seed-version --mojo-platform-channel-handle=2408 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\vszq5wsv.ese" --extension-process --enable-dinosaur-easter-egg-alt-images --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=3644,i,8112870976113181554,3068393653443554139,262144 --variations-seed-version --mojo-platform-channel-handle=3672 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\vszq5wsv.ese" --enable-dinosaur-easter-egg-alt-images --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=3156,i,8112870976113181554,3068393653443554139,262144 --variations-seed-version --mojo-platform-channel-handle=3168 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\4stpnvlo.ebj" --extension-process --renderer-sub-type=extension --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --always-read-main-dll --field-trial-handle=4280,i,2154801811120607649,6713586082121509237,262144 --variations-seed-version --mojo-platform-channel-handle=4260 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1156 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-sandbox --mute-audio --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\4stpnvlo.ebj" --always-read-main-dll --field-trial-handle=2308,i,2154801811120607649,6713586082121509237,262144 --variations-seed-version --mojo-platform-channel-handle=2732 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\vszq5wsv.ese" --enable-dinosaur-easter-egg-alt-images --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=3176,i,8112870976113181554,3068393653443554139,262144 --variations-seed-version --mojo-platform-channel-handle=3184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\vszq5wsv.ese" --enable-dinosaur-easter-egg-alt-images --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=3604,i,8112870976113181554,3068393653443554139,262144 --variations-seed-version --mojo-platform-channel-handle=3612 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1332 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\4stpnvlo.ebj" --extension-process --renderer-sub-type=extension --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=4180,i,2154801811120607649,6713586082121509237,262144 --variations-seed-version --mojo-platform-channel-handle=4136 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 5256 -prefsLen 39068 -prefMapHandle 5260 -prefMapSize 272997 -jsInitHandle 5264 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5272 -initialChannelId {fbdd8cab-0c00-482c-8284-8766abd64bd4} -parentPid 4676 -crashReporter "\\.\pipe\gecko-crash-server-pipe.4676" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 9 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
Total events
15 795
Read events
15 779
Write events
15
Delete events
1
Modification events
| (PID) Process: | (420) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (420) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (420) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (420) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (420) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (420) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2320) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2764) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 1 | |||
| (PID) Process: | (2764) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
Executable files
0
Suspicious files
209
Text files
77
Unknown types
310
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 420 | chrome.exe | C:\Users\admin\AppData\Local\Temp\vszq5wsv.ese\Default\Code Cache\wasm\index-dir\temp-index | binary | |
MD5:FD0CBDC3BDF8C582AA5951712407DA9B | SHA256:5AAB1A440F337FC6CD467B5E62942B041239DFF3B5DC2D61D1632A1715724E78 | |||
| 420 | chrome.exe | C:\Users\admin\AppData\Local\Temp\vszq5wsv.ese\Default\Extension Rules\000001.dbtmp | text | |
MD5:46295CAC801E5D4857D09837238A6394 | SHA256:0F1BAD70C7BD1E0A69562853EC529355462FCD0423263A3D39D6D0D70B780443 | |||
| 420 | chrome.exe | C:\Users\admin\AppData\Local\Temp\vszq5wsv.ese\Default\Code Cache\wasm\index | binary | |
MD5:54CB446F628B2EA4A5BCE5769910512E | SHA256:FBCFE23A2ECB82B7100C50811691DDE0A33AA3DA8D176BE9882A9DB485DC0F2D | |||
| 420 | chrome.exe | C:\Users\admin\AppData\Local\Temp\vszq5wsv.ese\Default\Site Characteristics Database\000001.dbtmp | text | |
MD5:46295CAC801E5D4857D09837238A6394 | SHA256:0F1BAD70C7BD1E0A69562853EC529355462FCD0423263A3D39D6D0D70B780443 | |||
| 420 | chrome.exe | C:\Users\admin\AppData\Local\Temp\vszq5wsv.ese\Default\Code Cache\wasm\index-dir\the-real-index | binary | |
MD5:FD0CBDC3BDF8C582AA5951712407DA9B | SHA256:5AAB1A440F337FC6CD467B5E62942B041239DFF3B5DC2D61D1632A1715724E78 | |||
| 420 | chrome.exe | C:\Users\admin\AppData\Local\Temp\vszq5wsv.ese\Default\1155180a-277b-4d30-b1fb-e30cb0e98ebd.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 420 | chrome.exe | C:\Users\admin\AppData\Local\Temp\vszq5wsv.ese\Default\Extension Rules\MANIFEST-000001 | binary | |
MD5:5AF87DFD673BA2115E2FCF5CFDB727AB | SHA256:F9D31B278E215EB0D0E9CD709EDFA037E828F36214AB7906F612160FEAD4B2B4 | |||
| 420 | chrome.exe | C:\Users\admin\AppData\Local\Temp\vszq5wsv.ese\Default\Site Characteristics Database\MANIFEST-000001 | binary | |
MD5:5AF87DFD673BA2115E2FCF5CFDB727AB | SHA256:F9D31B278E215EB0D0E9CD709EDFA037E828F36214AB7906F612160FEAD4B2B4 | |||
| 420 | chrome.exe | C:\Users\admin\AppData\Local\Temp\vszq5wsv.ese\Default\History-journal | — | |
MD5:— | SHA256:— | |||
| 420 | chrome.exe | C:\Users\admin\AppData\Local\Temp\vszq5wsv.ese\Default\Code Cache\js\index-dir\temp-index | binary | |
MD5:FD0CBDC3BDF8C582AA5951712407DA9B | SHA256:5AAB1A440F337FC6CD467B5E62942B041239DFF3B5DC2D61D1632A1715724E78 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
61
DNS requests
96
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1156 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:H4AnNdmeZwdPZYywaipqEfqLNowDJHGumcY5D68txVw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
4528 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.19.198.194:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8076 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8076 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 2.16.252.233:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
4676 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
4676 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
4676 | firefox.exe | POST | 200 | 142.250.186.35:80 | http://o.pki.goog/s/wr3/azY | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7136 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2604 | logs.exe | 212.56.35.232:7705 | — | — | GB | malicious |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4528 | svchost.exe | 20.190.160.66:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4528 | svchost.exe | 23.63.118.230:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
620 | chrome.exe | 142.250.186.163:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
620 | chrome.exe | 172.217.16.206:80 | clients2.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
ntp.msn.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2604 | logs.exe | A Network Trojan was detected | ET MALWARE PureLogs C2 Server Connection M3 |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\vszq5wsv.ese directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\4stpnvlo.ebj directory exists )
|