| File name: | Hamsta Injector.exe |
| Full analysis: | https://app.any.run/tasks/851a3df6-e94e-4b8c-91cf-5c53e355b4fc |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | July 13, 2020, 03:11:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 0994E96E5CB4CEDDD4ECBE0A5F58BDBC |
| SHA1: | 8A5D48EC78C34477E7B58FA22FDF9560B9EB8B1A |
| SHA256: | 035E8E0106FE825128316B46835D0EA34E3E1691146E0303EE67A00C1C8A166A |
| SSDEEP: | 12288:c0fXbP+ifUt1Jgscq5Ionzr8yThb3bKWmHHVd7O8hxkdKdk27mOmyyXTta:c0/iUULDz//DTZlmnz7pxkCk2i7pTE |
MALICIOUS
HAWKEYE was detected
- Hamsta Injector.exe (PID: 3192)
Uses NirSoft utilities to collect credentials
- vbc.exe (PID: 2664)
Actions looks like stealing of personal data
- vbc.exe (PID: 2664)
- vbc.exe (PID: 2752)
Changes the autorun value in the registry
- reg.exe (PID: 2536)
Stealing of credential data
- vbc.exe (PID: 2664)
Changes settings of System certificates
- Hamsta Injector.exe (PID: 3192)
SUSPICIOUS
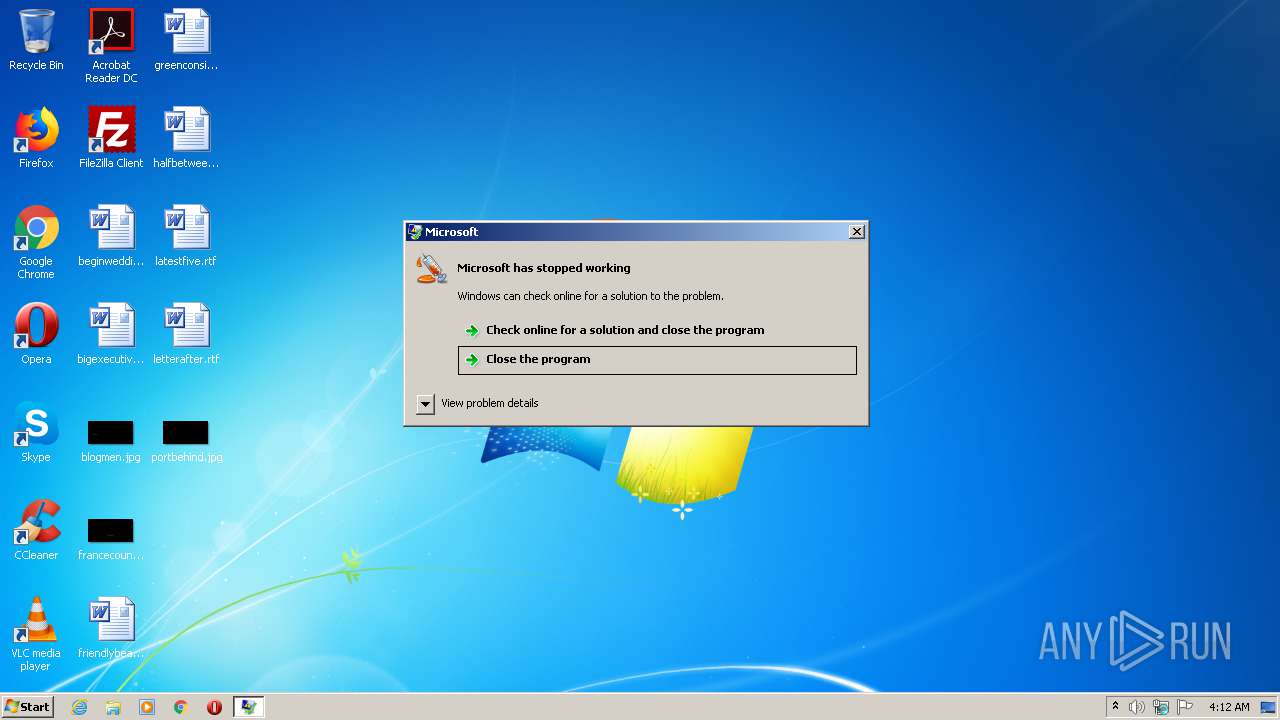
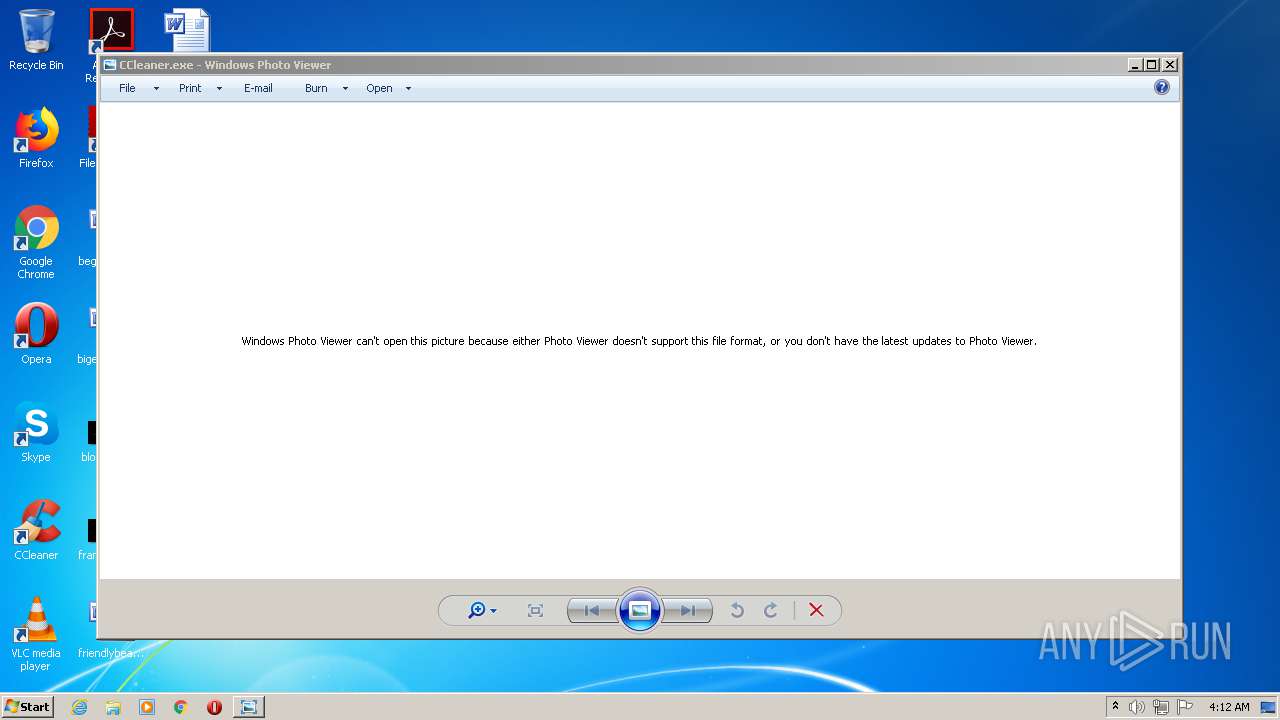
Creates files in the program directory
- dw20.exe (PID: 3252)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 2664)
Application launched itself
- Hamsta Injector.exe (PID: 688)
- Skype.exe (PID: 2816)
- Skype.exe (PID: 1248)
- Skype.exe (PID: 2744)
- Skype.exe (PID: 2504)
- Skype.exe (PID: 3052)
Checks for external IP
- Hamsta Injector.exe (PID: 3192)
Executes scripts
- Hamsta Injector.exe (PID: 3192)
Creates files in the user directory
- Skype.exe (PID: 2816)
- Skype.exe (PID: 1248)
- Hamsta Injector.exe (PID: 3192)
Uses REG.EXE to modify Windows registry
- Skype.exe (PID: 2816)
Modifies the open verb of a shell class
- Skype.exe (PID: 2816)
Reads CPU info
- Skype.exe (PID: 2504)
- Skype.exe (PID: 2816)
- Skype.exe (PID: 2744)
- Skype.exe (PID: 3052)
Executed via COM
- DllHost.exe (PID: 752)
Adds / modifies Windows certificates
- Hamsta Injector.exe (PID: 3192)
INFO
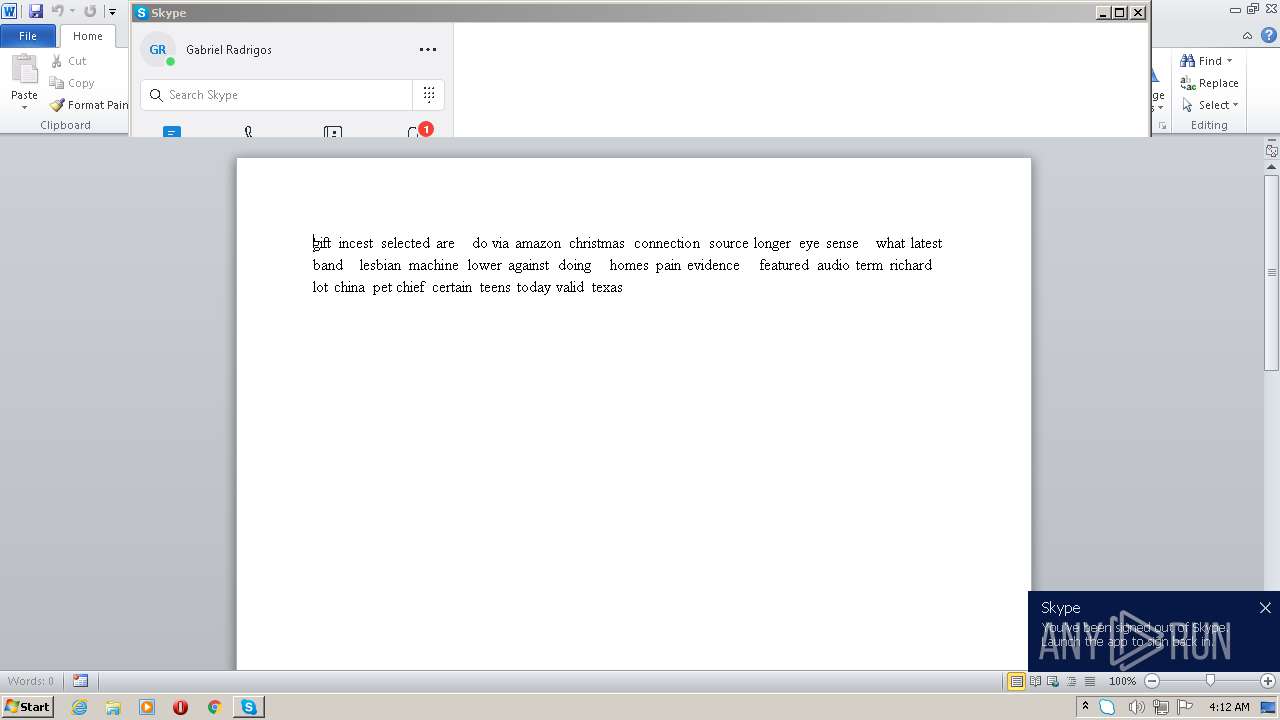
Manual execution by user
- WINWORD.EXE (PID: 3228)
- opera.exe (PID: 3500)
- Skype.exe (PID: 2744)
- Skype.exe (PID: 2504)
- WINWORD.EXE (PID: 2784)
- Skype.exe (PID: 3052)
- WINWORD.EXE (PID: 2372)
- WINWORD.EXE (PID: 3652)
- WINWORD.EXE (PID: 2632)
- WINWORD.EXE (PID: 3560)
- Skype.exe (PID: 2816)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3228)
- WINWORD.EXE (PID: 2784)
- WINWORD.EXE (PID: 2372)
- WINWORD.EXE (PID: 3652)
- WINWORD.EXE (PID: 3560)
- WINWORD.EXE (PID: 2632)
Creates files in the user directory
- WINWORD.EXE (PID: 3228)
- opera.exe (PID: 3500)
- WINWORD.EXE (PID: 2784)
Reads the hosts file
- Skype.exe (PID: 2816)
- Skype.exe (PID: 2744)
- Skype.exe (PID: 2504)
- Skype.exe (PID: 3052)
Reads settings of System Certificates
- Skype.exe (PID: 2816)
- Hamsta Injector.exe (PID: 3192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (64.5) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (13.6) |
| .exe | | | Win32 Executable (generic) (9.3) |
| .exe | | | Win16/32 Executable Delphi generic (4.2) |
| .exe | | | Generic Win/DOS Executable (4.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:07:07 19:29:44+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 660480 |
| InitializedDataSize: | 143872 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa332e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
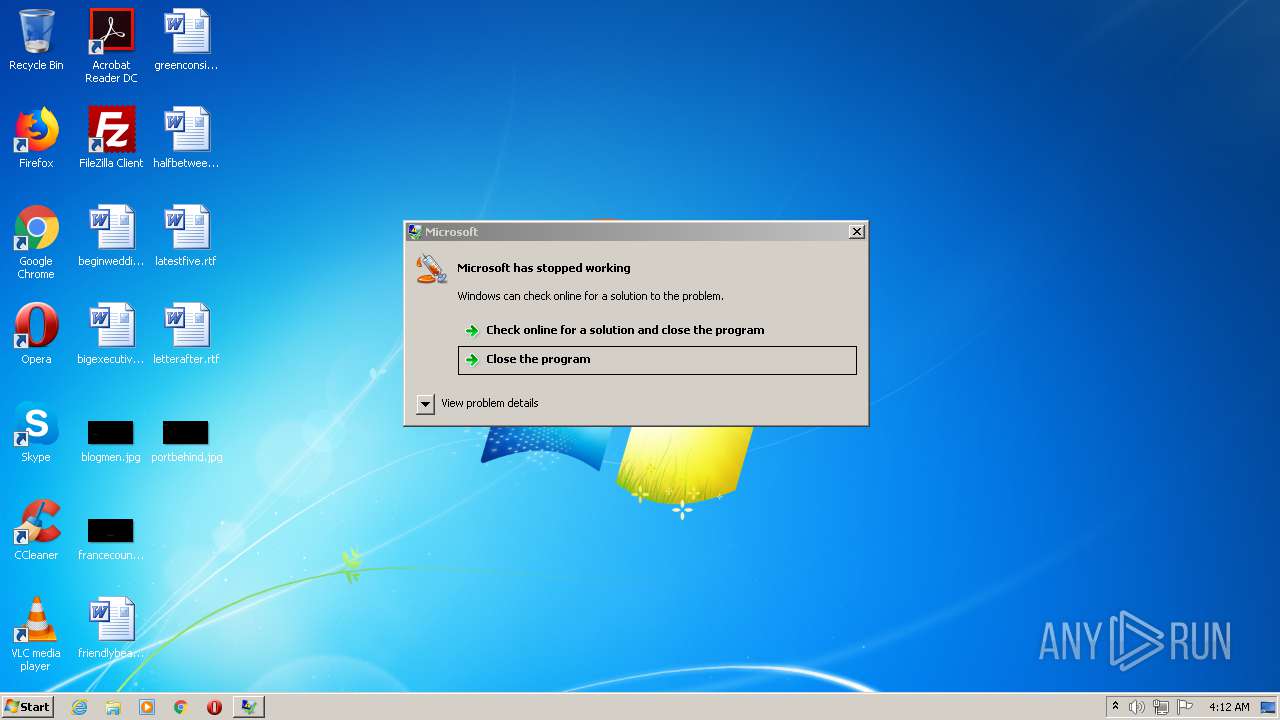
| FileDescription: | Microsoft |
| FileVersion: | 1.0.0.0 |
| InternalName: | Microsoft.exe |
| LegalCopyright: | Copyright © 2013 |
| OriginalFileName: | Microsoft.exe |
| ProductName: | Microsoft |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Jul-2016 17:29:44 |
| FileDescription: | Microsoft |
| FileVersion: | 1.0.0.0 |
| InternalName: | Microsoft.exe |
| LegalCopyright: | Copyright © 2013 |
| OriginalFilename: | Microsoft.exe |
| ProductName: | Microsoft |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 07-Jul-2016 17:29:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000A1334 | 0x000A1400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.72202 |
.rsrc | 0x000A4000 | 0x00004A00 | 0x00004A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.05285 |
.reloc | 0x000AA000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
kMxO7i8Q(\xe5\x01 | 0x000AC000 | 0x0001E528 | 0x0001E600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.84739 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94474 | 2259 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 4.75208 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 4.48935 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
32512 | 2.47702 | 34 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
68
Monitored processes
26
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 688 | "C:\Users\admin\AppData\Local\Temp\Hamsta Injector.exe" | C:\Users\admin\AppData\Local\Temp\Hamsta Injector.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Microsoft Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 752 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --type=renderer --ms-disable-indexeddb-transaction-timeout --no-sandbox --service-pipe-token=79AFCBD7A3D411CE5CE287A22CD23796 --lang=en-US --app-user-model-id=Microsoft.Skype.SkypeDesktop --app-path="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar" --node-integration=false --webview-tag=true --no-sandbox --preload="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar\Preload.js" --context-id=2 --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=79AFCBD7A3D411CE5CE287A22CD23796 --renderer-client-id=3 --mojo-platform-channel-handle=1576 /prefetch:1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | — | Skype.exe | |||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | Skype.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 2 Version: 8.29.0.50 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\beginwedding.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2448 | C:\Windows\system32\reg.exe QUERY HKCU\Software\Microsoft\Skype /v RestartForUpdate | C:\Windows\system32\reg.exe | — | Skype.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2504 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | explorer.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 2536 | C:\Windows\system32\reg.exe ADD HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v "Skype for Desktop" /t REG_SZ /d "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" /f | C:\Windows\system32\reg.exe | Skype.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2572 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | Skype.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --type=renderer --ms-disable-indexeddb-transaction-timeout --no-sandbox --service-pipe-token=96F3296E512C2696106A7410BE5652E4 --lang=en-US --app-user-model-id=Microsoft.Skype.SkypeDesktop --app-path="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar" --node-integration=false --webview-tag=true --no-sandbox --preload="C:\Program Files\Microsoft\Skype for Desktop\resources\app.asar\Preload.js" --context-id=1 --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=96F3296E512C2696106A7410BE5652E4 --renderer-client-id=4 --mojo-platform-channel-handle=2320 /prefetch:1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | — | Skype.exe | |||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
Total events
4 790
Read events
2 873
Write events
1 702
Delete events
215
Modification events
| (PID) Process: | (688) Hamsta Injector.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (688) Hamsta Injector.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3192) Hamsta Injector.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hamsta Injector_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3192) Hamsta Injector.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hamsta Injector_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3192) Hamsta Injector.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hamsta Injector_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3192) Hamsta Injector.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hamsta Injector_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3192) Hamsta Injector.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hamsta Injector_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3192) Hamsta Injector.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hamsta Injector_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3192) Hamsta Injector.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hamsta Injector_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3192) Hamsta Injector.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hamsta Injector_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
37
Text files
29
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2752 | vbc.exe | C:\Users\admin\AppData\Local\Temp\holdermail.txt | — | |
MD5:— | SHA256:— | |||
| 3228 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR3AA5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3500 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr4D42.tmp | — | |
MD5:— | SHA256:— | |||
| 3500 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr4D82.tmp | — | |
MD5:— | SHA256:— | |||
| 3500 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 3500 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RI3MKBEG1CBF65QA2YTQ.temp | — | |
MD5:— | SHA256:— | |||
| 3500 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JRO8Z16C3BRI3XIONXWT.temp | — | |
MD5:— | SHA256:— | |||
| 3192 | Hamsta Injector.exe | C:\Users\admin\AppData\Roaming\pidloc.txt | text | |
MD5:— | SHA256:— | |||
| 3500 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr66F6.tmp | — | |
MD5:— | SHA256:— | |||
| 3228 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
16
DNS requests
10
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3192 | Hamsta Injector.exe | GET | 301 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | — | — | shared |
3500 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 564 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3192 | Hamsta Injector.exe | 74.208.5.15:587 | smtp.mail.com | 1&1 Internet SE | US | malicious |
— | — | 52.174.193.75:443 | get.skype.com | Microsoft Corporation | NL | whitelisted |
3192 | Hamsta Injector.exe | 104.16.155.36:80 | whatismyipaddress.com | Cloudflare Inc | US | shared |
— | — | 13.107.42.23:443 | a.config.skype.com | Microsoft Corporation | US | suspicious |
3192 | Hamsta Injector.exe | 104.16.155.36:443 | whatismyipaddress.com | Cloudflare Inc | US | shared |
— | — | 104.16.155.36:443 | whatismyipaddress.com | Cloudflare Inc | US | shared |
3500 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2816 | Skype.exe | 152.199.19.160:443 | bot-framework.azureedge.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3500 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2816 | Skype.exe | 2.18.233.81:443 | download.skype.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
whatismyipaddress.com |
| shared |
smtp.mail.com |
| shared |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
get.skype.com |
| whitelisted |
a.config.skype.com |
| whitelisted |
download.skype.com |
| whitelisted |
pipe.skype.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
bot-framework.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3192 | Hamsta Injector.exe | Potential Corporate Privacy Violation | ET POLICY Known External IP Lookup Service Domain in SNI |
3192 | Hamsta Injector.exe | Potential Corporate Privacy Violation | ET POLICY Known External IP Lookup Service Domain in SNI |
3192 | Hamsta Injector.exe | A Network Trojan was detected | SPYWARE [PTsecurity] HawkEye / Predator Pain (IP Chck) |
3192 | Hamsta Injector.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
Skype.exe | [2572:3088:0713/041247.172:VERBOSE1:crash_service.cc(304)] checkpoint is C:\Users\admin\AppData\Local\Temp\skype-preview Crashes\crash_checkpoint.txt
server is https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload
maximum 128 reports/day
reporter is electron-crash-service
|
Skype.exe | [2572:3048:0713/041247.172:VERBOSE1:crash_service.cc(333)] client start. pid = 2816
|
Skype.exe | [2572:3088:0713/041247.172:VERBOSE1:crash_service.cc(304)] checkpoint is C:\Users\admin\AppData\Local\Temp\skype-preview Crashes\crash_checkpoint.txt
server is https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload
maximum 128 reports/day
reporter is electron-crash-service
|
Skype.exe | [2572:3088:0713/041247.172:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [2572:3088:0713/041247.172:VERBOSE1:crash_service_main.cc(94)] Ready to process crash requests
|
Skype.exe | [2572:3088:0713/041247.172:VERBOSE1:crash_service.cc(145)] window handle is 000201A4
|
Skype.exe | [2572:3048:0713/041249.021:VERBOSE1:crash_service.cc(333)] client start. pid = 1248
|
Skype.exe | [2356:2200:0713/041249.334:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [2356:2200:0713/041249.336:VERBOSE1:crash_service.cc(145)] window handle is 000201BE
|
Skype.exe | [2356:2200:0713/041249.337:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\skype-preview Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\skype-preview Crashes
|