| File name: | PO.exe |
| Full analysis: | https://app.any.run/tasks/5b5f03b0-5a4f-4d74-a22c-3465baccb577 |
| Verdict: | Malicious activity |
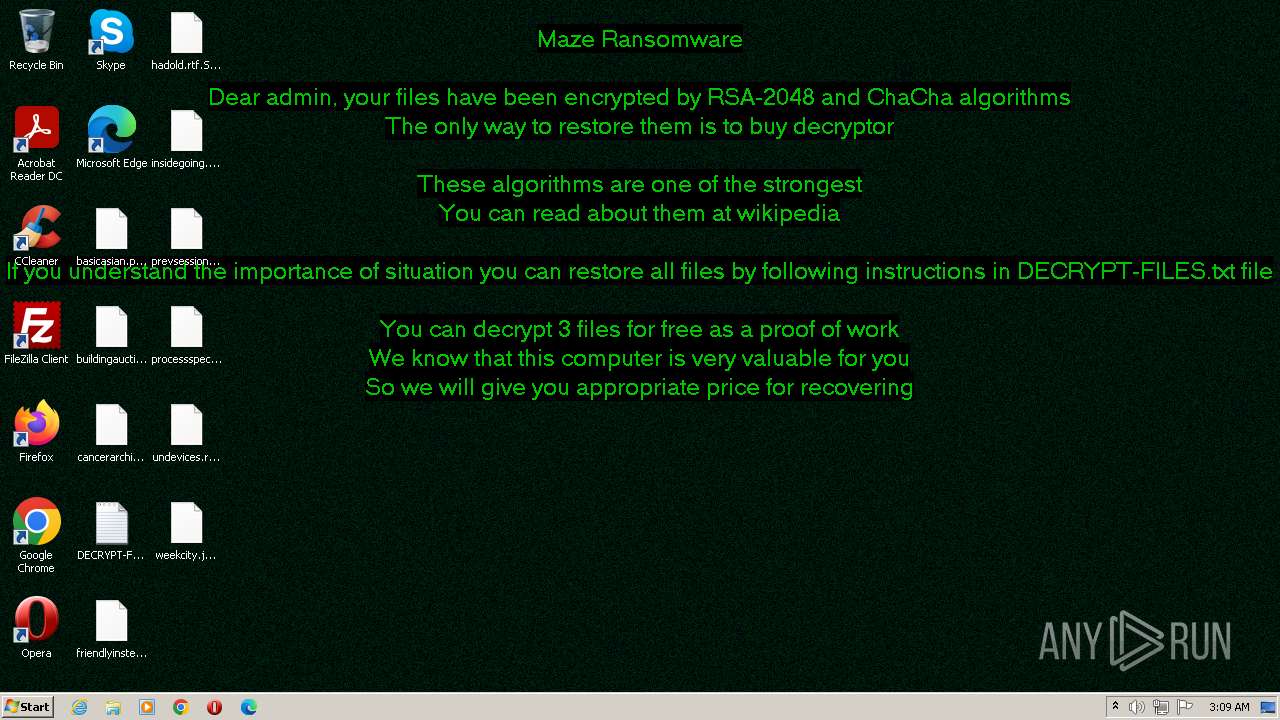
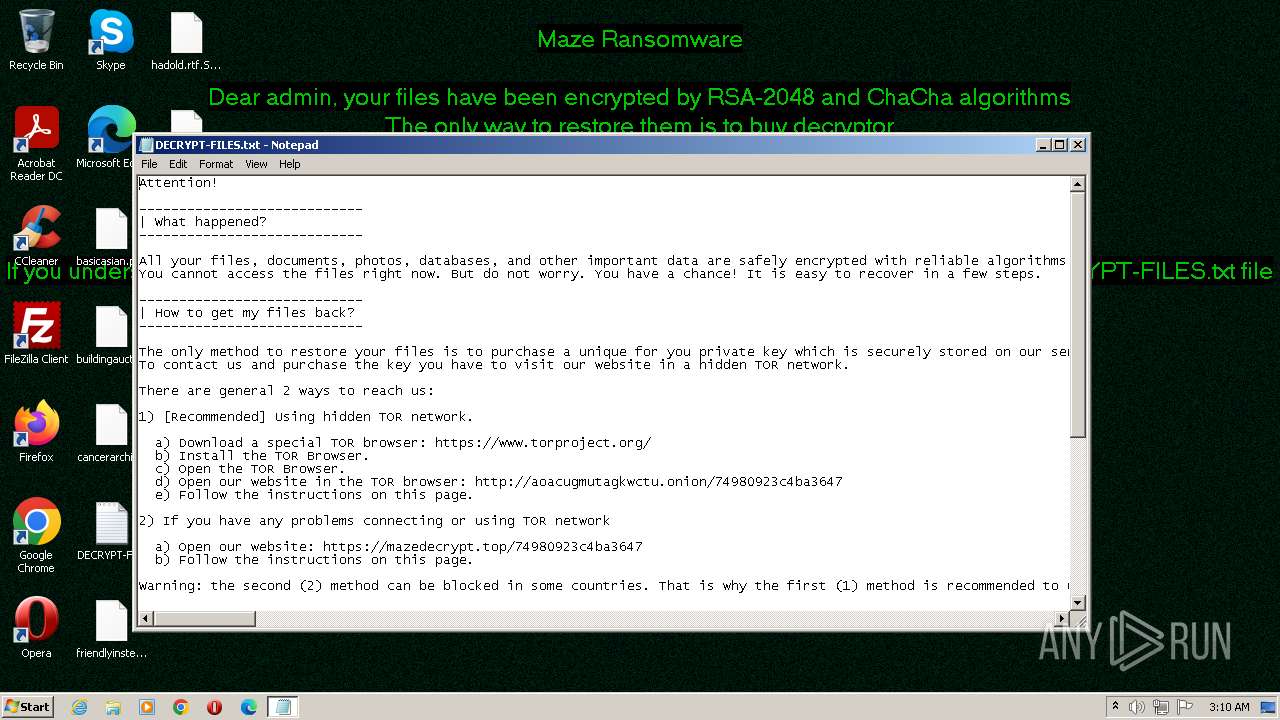
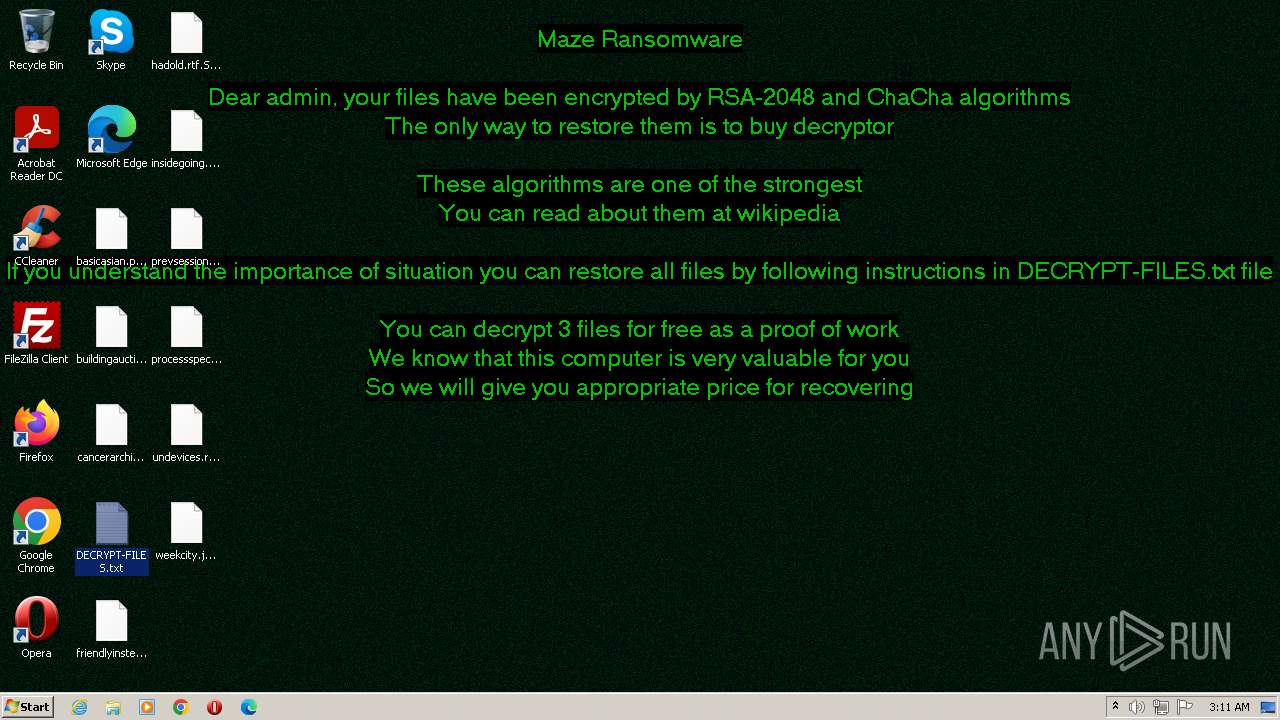
| Threats: | Maze is ransomware — a malware type that encrypts the victim’s files and restores the data in exchange for a ransom payment. One of the most distinguishable features of Maze is that it is one of the first malware of the kind to publicly release stolen data. |
| Analysis date: | August 31, 2023, 02:07:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 58B70BE83F9735F4E626054DE966CC94 |
| SHA1: | 153A8273173896DB4F035B113312D8F1A0B2D93E |
| SHA256: | 02D881E51D79ACE66F90EAF66628ED94617D25D18E301470995102A299EE2A03 |
| SSDEEP: | 12288:V/UOijhLB4ONL1Oa+iJBPWhbvULrJ6Bti3ERXxlcWdh9dLz6k7:V/UOa9hEYsbvULrwC+Xxlc+h9dLz6k7 |
MALICIOUS
Writes a file to the Word startup folder
- PO.exe (PID: 3488)
Create files in the Startup directory
- PO.exe (PID: 3488)
Steals credentials from Web Browsers
- PO.exe (PID: 3488)
Deletes shadow copies
- PO.exe (PID: 3488)
Renames files like ransomware
- PO.exe (PID: 3488)
Actions looks like stealing of personal data
- PO.exe (PID: 3488)
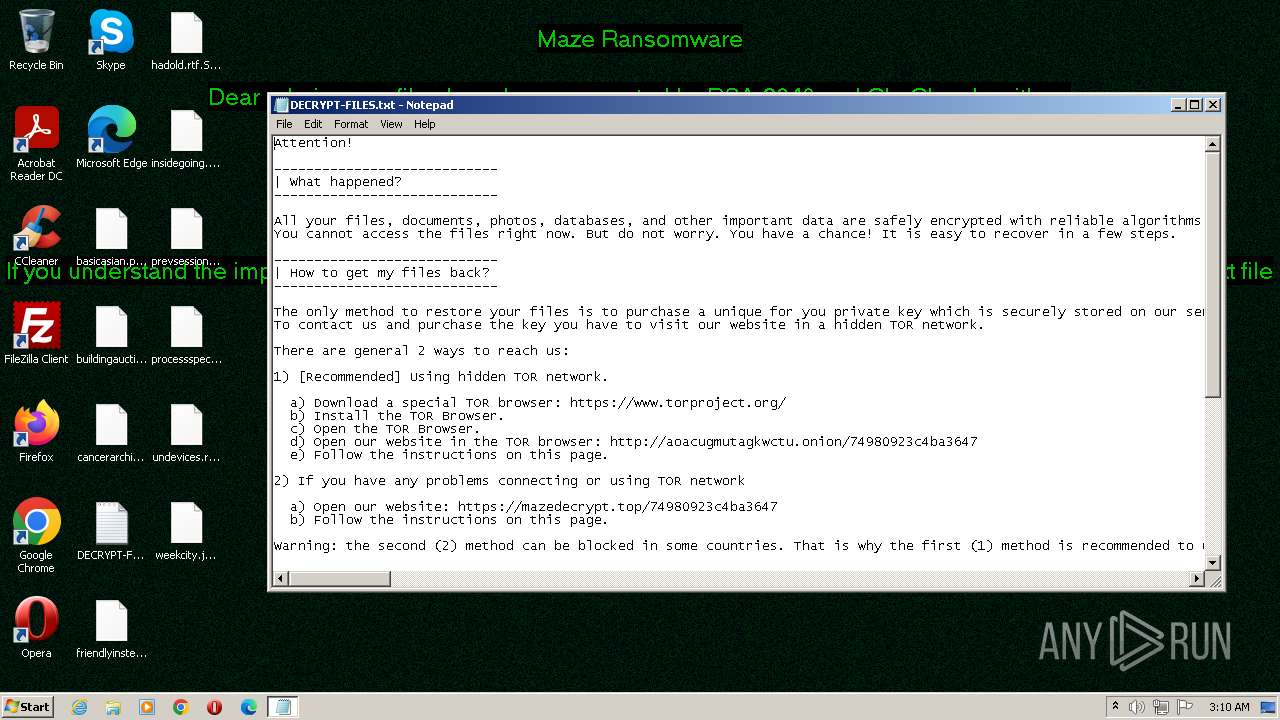
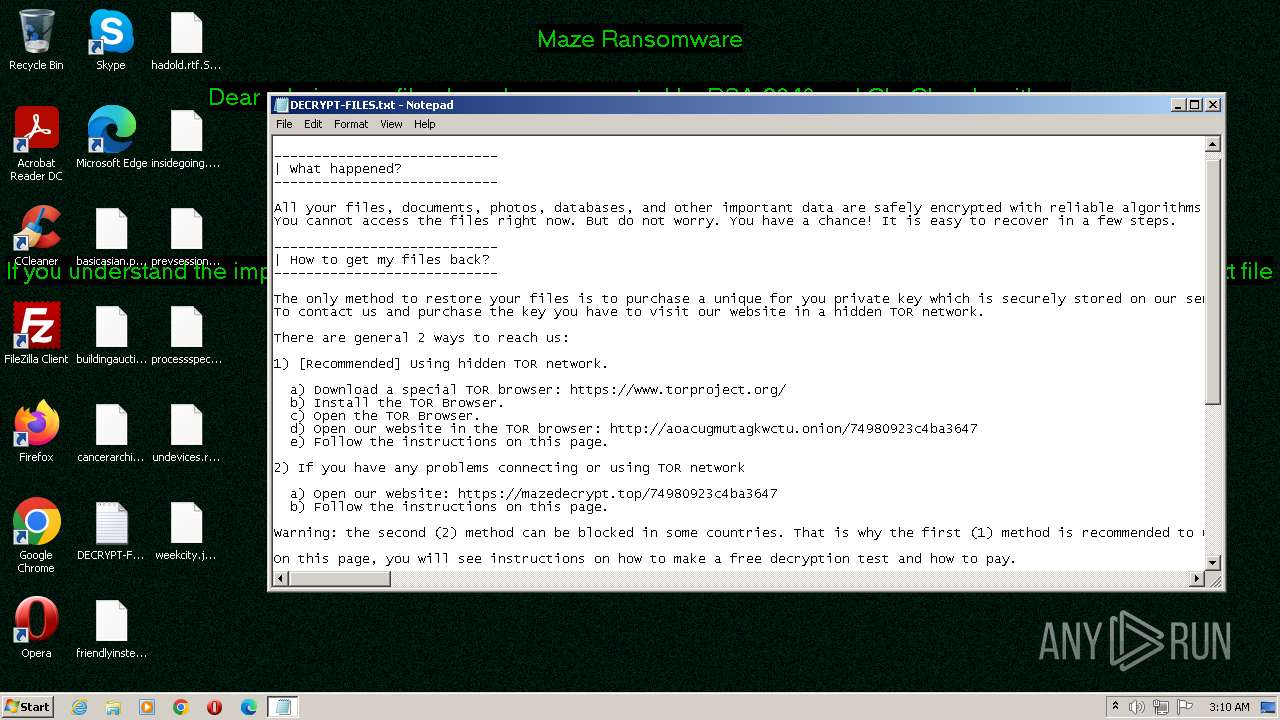
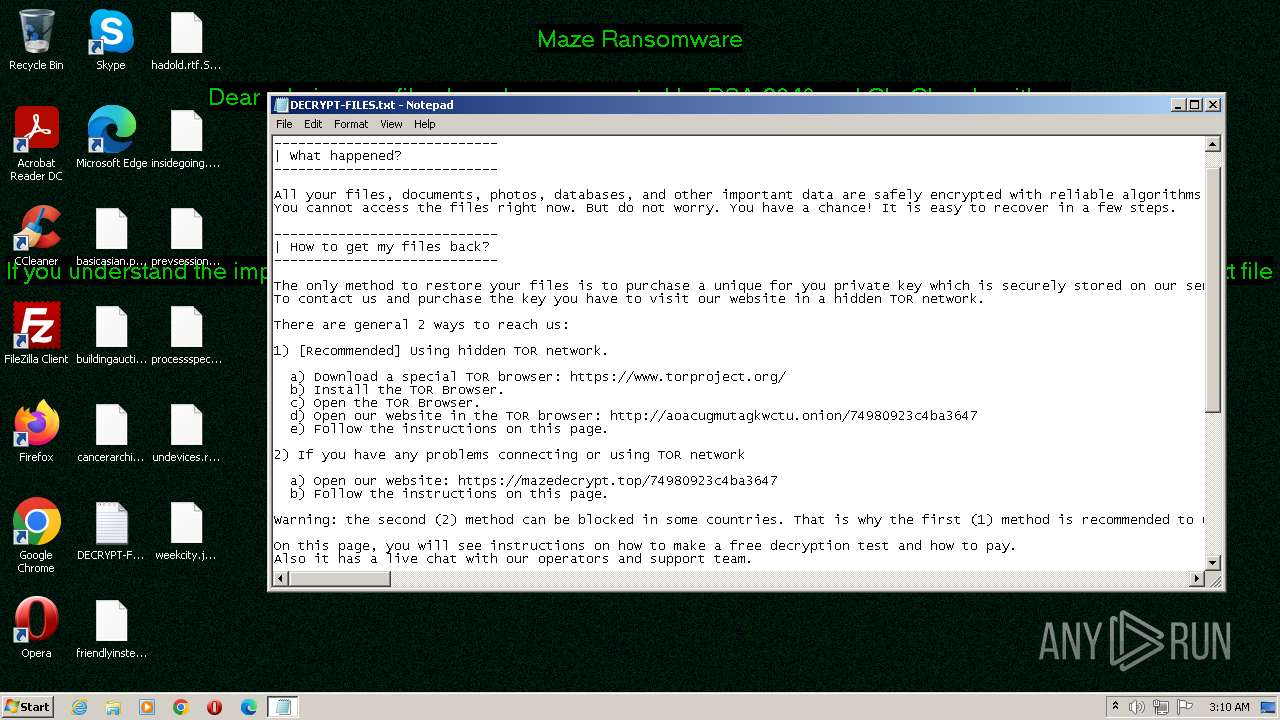
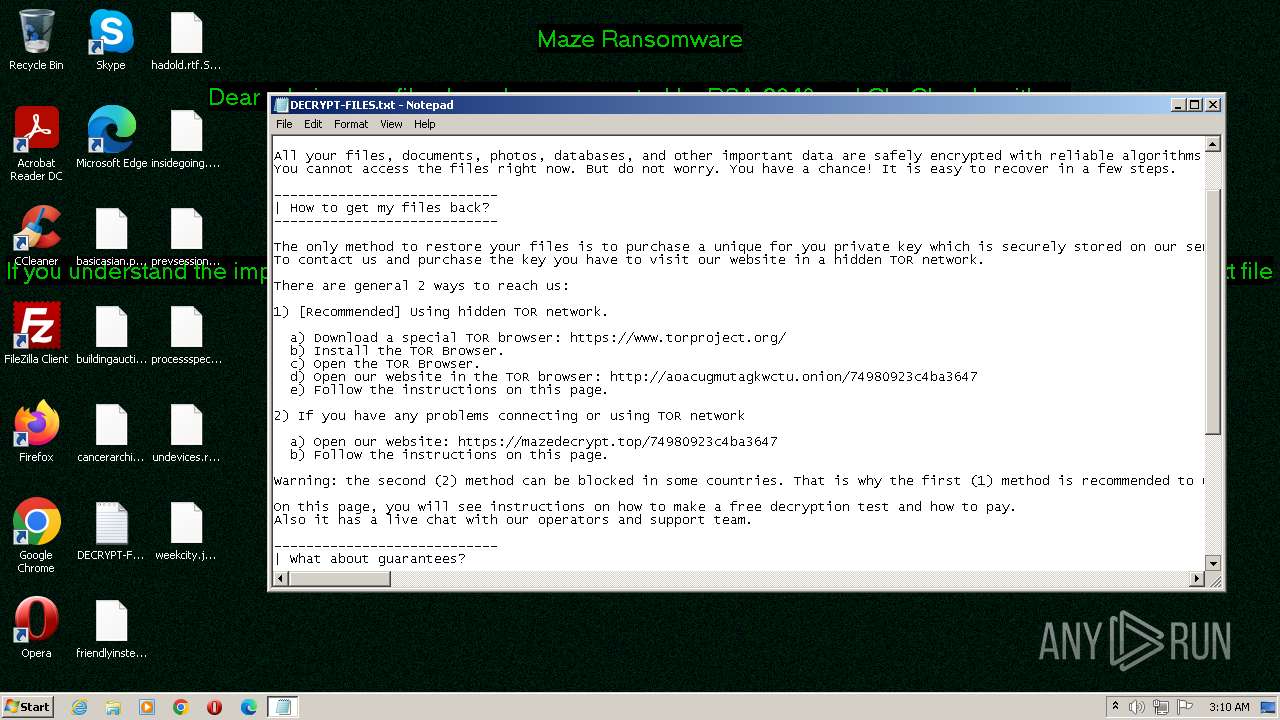
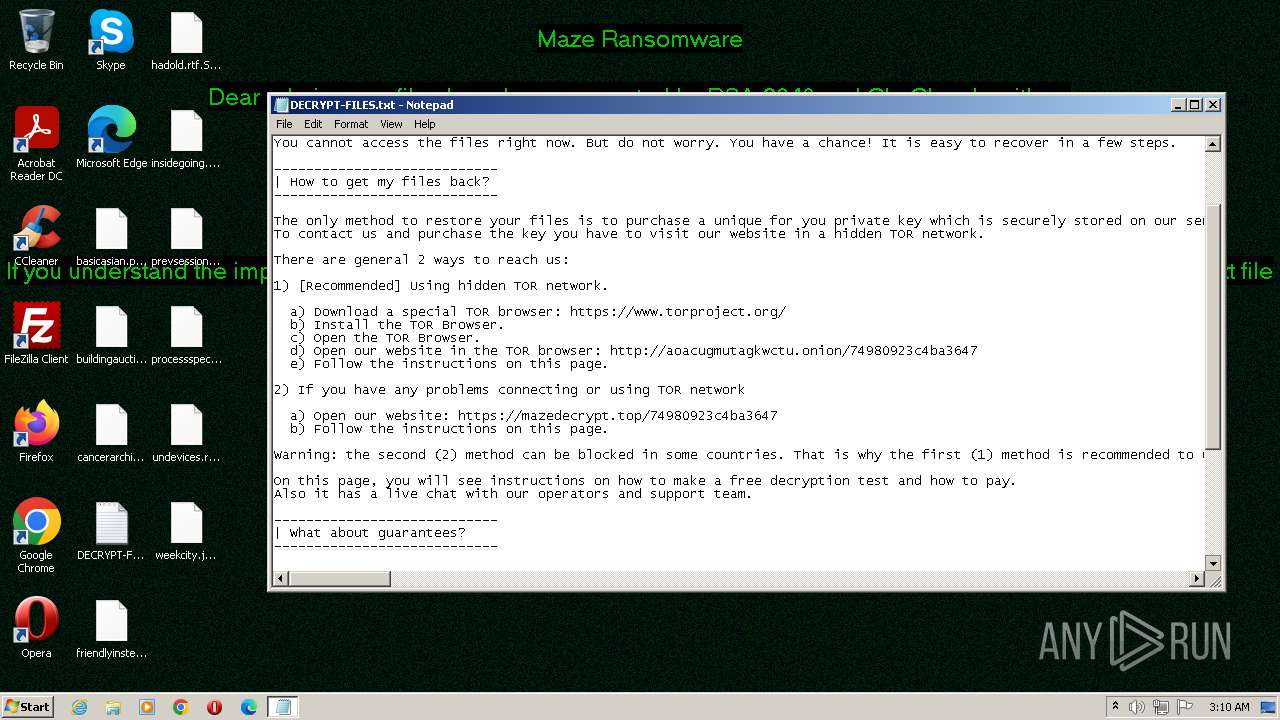
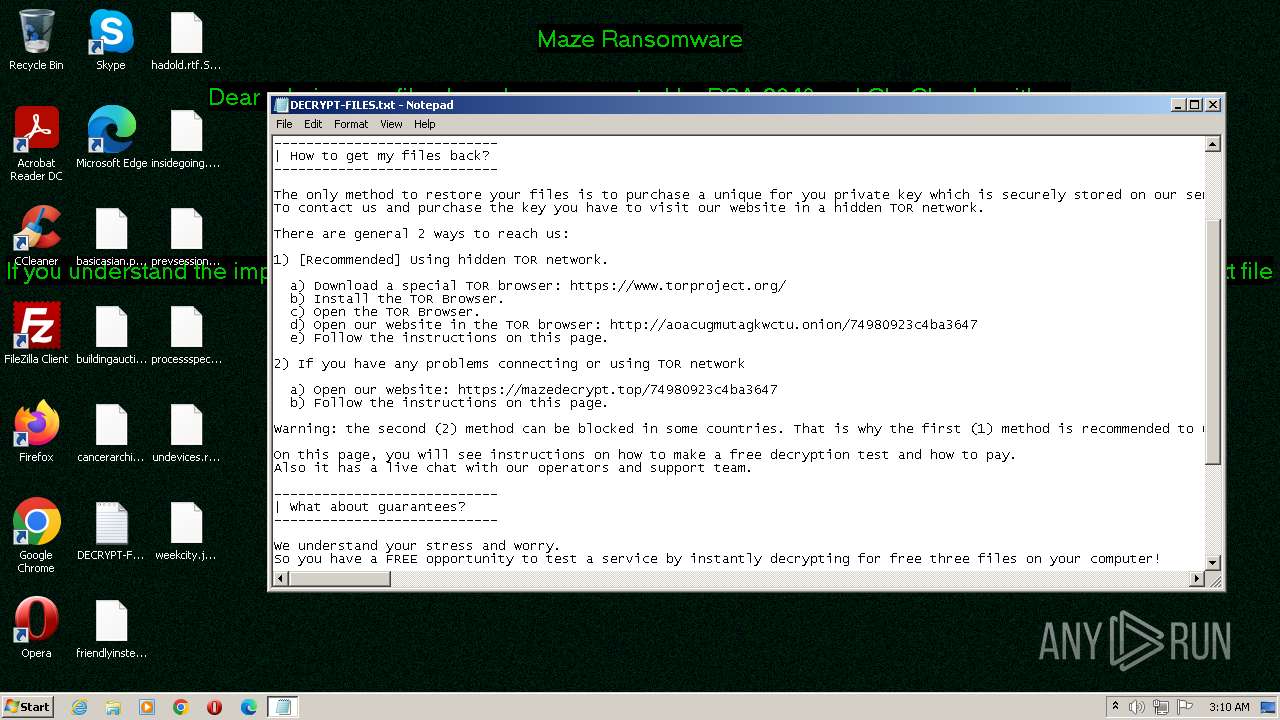
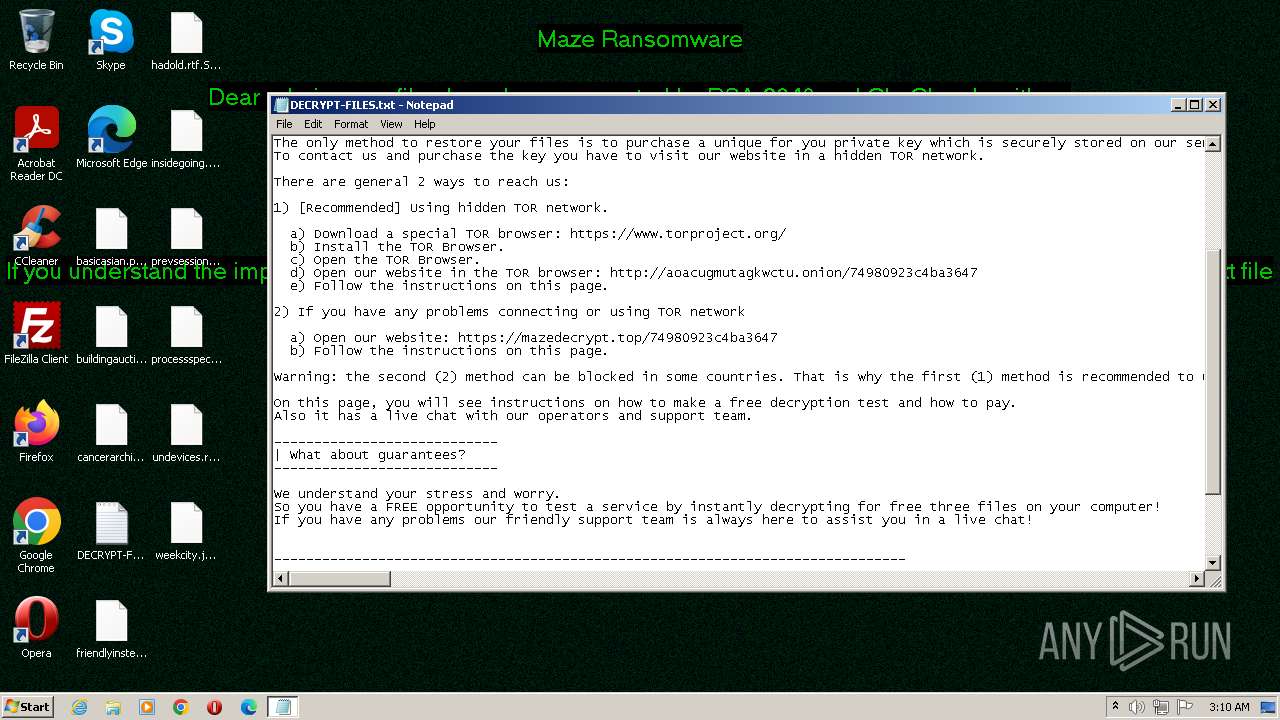
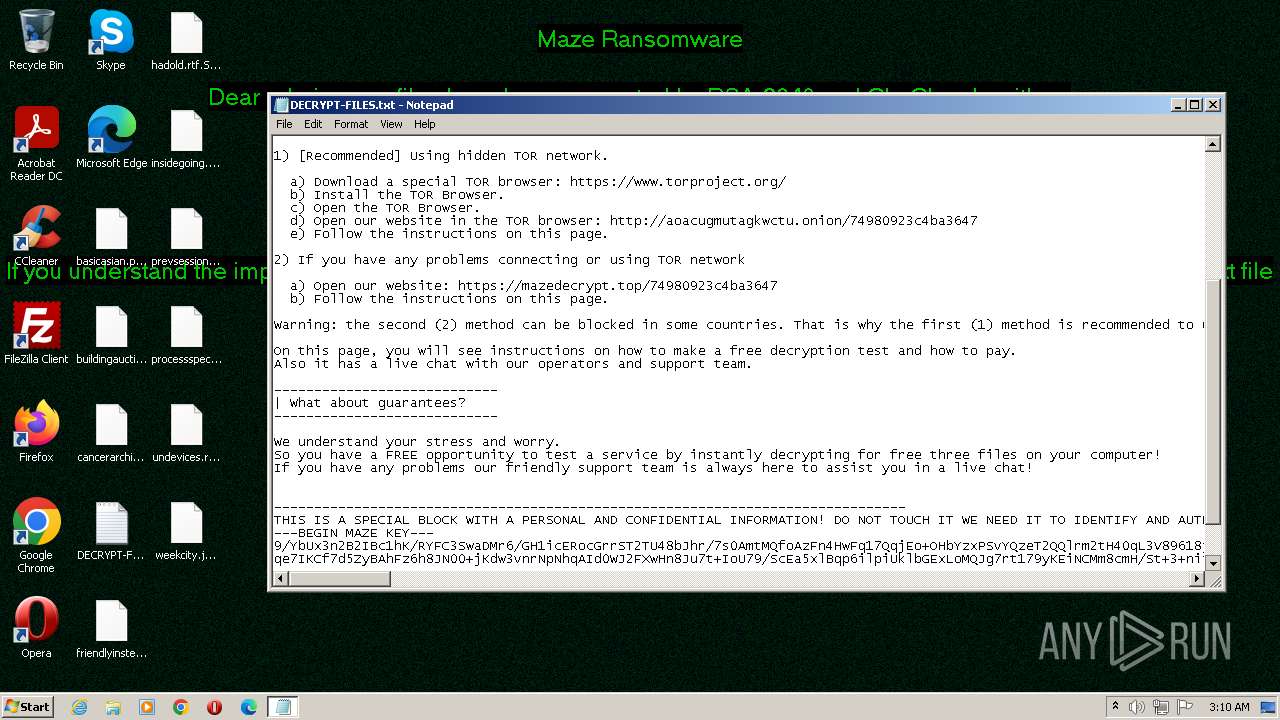
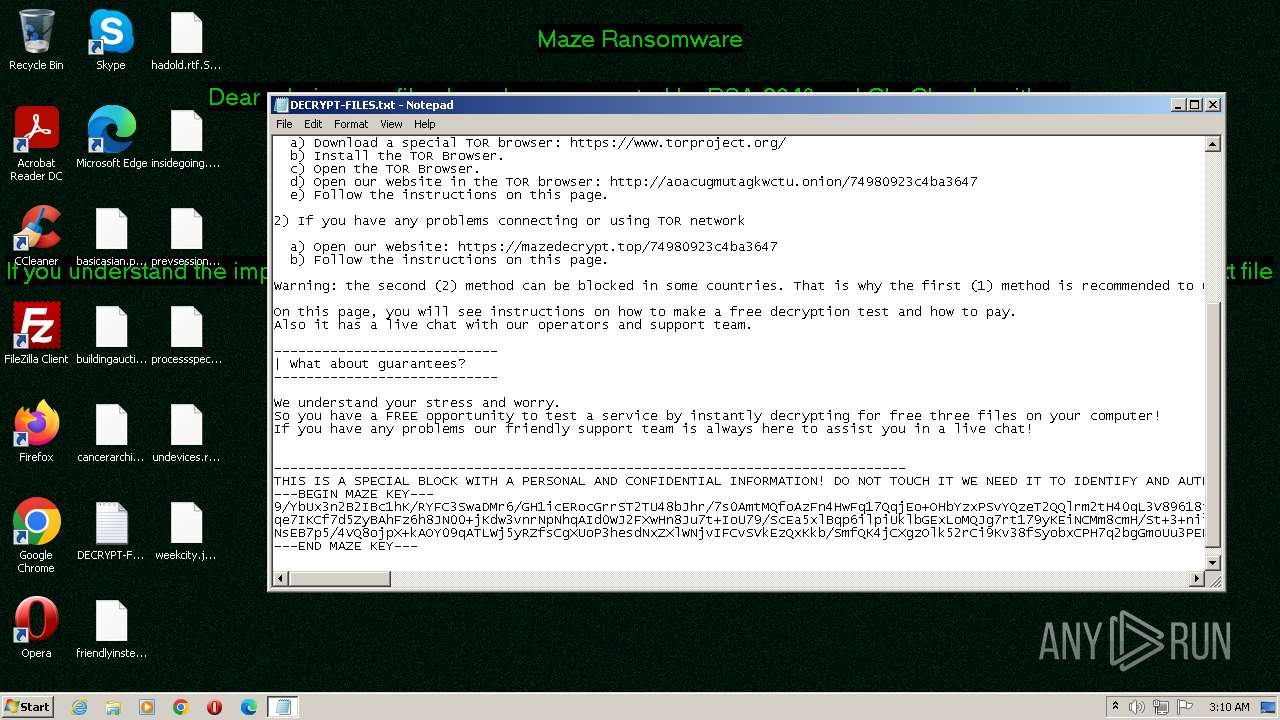
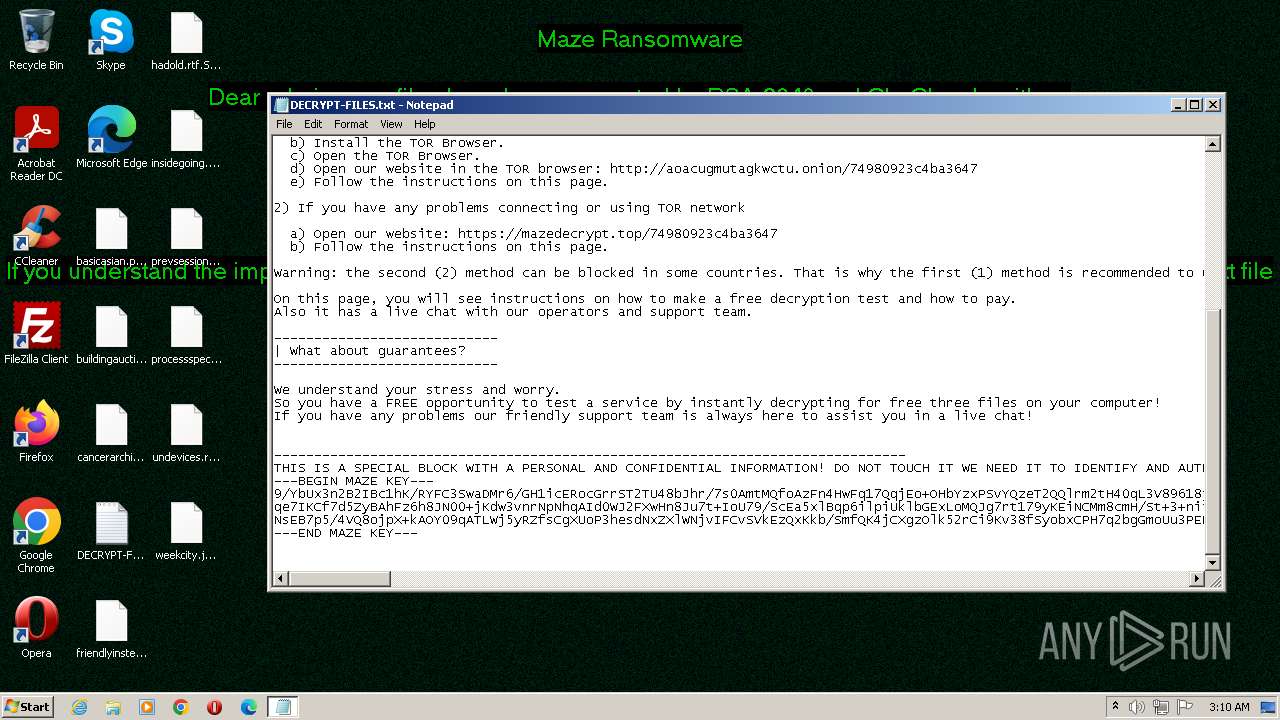
Maze ransom note is found
- PO.exe (PID: 3488)
SUSPICIOUS
Connects to the server without a host name
- PO.exe (PID: 3488)
Reads the Internet Settings
- WMIC.exe (PID: 2364)
- WMIC.exe (PID: 3928)
- PO.exe (PID: 3488)
Creates files like ransomware instruction
- PO.exe (PID: 3488)
INFO
Checks supported languages
- PO.exe (PID: 3488)
Creates files in the program directory
- PO.exe (PID: 3488)
Reads product name
- PO.exe (PID: 3488)
Reads Environment values
- PO.exe (PID: 3488)
Reads the computer name
- PO.exe (PID: 3488)
Creates files or folders in the user directory
- PO.exe (PID: 3488)
Reads the machine GUID from the registry
- PO.exe (PID: 3488)
Create files in a temporary directory
- PO.exe (PID: 3488)
Checks proxy server information
- PO.exe (PID: 3488)
Manual execution by a user
- notepad.exe (PID: 2540)
Dropped object may contain TOR URL's
- PO.exe (PID: 3488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.3) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x6ebe |
| UninitializedDataSize: | 3584 |
| InitializedDataSize: | 114176 |
| CodeSize: | 649728 |
| LinkerVersion: | 6.6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2019:11:18 11:12:10+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Nov-2019 11:12:10 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 18-Nov-2019 11:12:10 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0009E94C | 0x0009EA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.74388 |
.data | 0x000A0000 | 0x00000C3E | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.83262 |
.rdata | 0x000A1000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.rsrc | 0x000A2000 | 0x00019EB0 | 0x0001A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.46344 |
0x000BD000 | 0x00000344 | 0x00000400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 0 | 33 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
2 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
3 | 0 | 17 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
4 | 0 | 12 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
5 | 0 | 48 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
comctl32.dll |
gdiplus.dll |
kernel32.dll |
oleacc.dll |
oledlg.dll |
Total processes
43
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2364 | "C:\isoa\gr\..\..\Windows\eelux\ongm\xovn\..\..\..\system32\b\sa\fb\..\..\..\wbem\cicty\is\..\..\wmic.exe" shadowcopy delete | C:\Windows\System32\wbem\WMIC.exe | — | PO.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2540 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\DECRYPT-FILES.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3488 | "C:\Users\admin\AppData\Local\Temp\PO.exe" | C:\Users\admin\AppData\Local\Temp\PO.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3928 | "C:\sa\b\..\..\Windows\lb\..\system32\grx\wbut\..\..\wbem\ftgdi\e\sfoii\..\..\..\wmic.exe" shadowcopy delete | C:\Windows\System32\wbem\WMIC.exe | — | PO.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 216
Read events
1 131
Write events
85
Delete events
0
Modification events
| (PID) Process: | (3488) PO.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\AudioOutput\TokenEnums\MMAudioOut\{0.0.0.00000000}.{e602c5a2-9378-42f9-9806-a74c065977f6} |
| Operation: | write | Name: | CLSID |
Value: {A8C680EB-3D32-11D2-9EE7-00C04F797396} | |||
| (PID) Process: | (3488) PO.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\AudioOutput\TokenEnums\MMAudioOut\{0.0.0.00000000}.{e602c5a2-9378-42f9-9806-a74c065977f6} |
| Operation: | write | Name: | DeviceName |
Value: Speakers (Realtek AC'97 Audio) | |||
| (PID) Process: | (3488) PO.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\AudioOutput\TokenEnums\MMAudioOut\{0.0.0.00000000}.{e602c5a2-9378-42f9-9806-a74c065977f6} |
| Operation: | write | Name: | DeviceId |
Value: {0.0.0.00000000}.{e602c5a2-9378-42f9-9806-a74c065977f6} | |||
| (PID) Process: | (3488) PO.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\AudioOutput\TokenEnums\MMAudioOut\{0.0.0.00000000}.{e602c5a2-9378-42f9-9806-a74c065977f6}\Attributes |
| Operation: | write | Name: | Vendor |
Value: Microsoft | |||
| (PID) Process: | (3488) PO.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\AudioOutput\TokenEnums\MMAudioOut\{0.0.0.00000000}.{e602c5a2-9378-42f9-9806-a74c065977f6}\Attributes |
| Operation: | write | Name: | Technology |
Value: MMSys | |||
| (PID) Process: | (3488) PO.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\CurrentUserLexicon |
| Operation: | write | Name: | CLSID |
Value: {C9E37C15-DF92-4727-85D6-72E5EEB6995A} | |||
| (PID) Process: | (3488) PO.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3488) PO.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3488) PO.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3488) PO.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000004F010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
3
Suspicious files
887
Text files
313
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3488 | PO.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | binary | |
MD5:F76EA9C494B2C068969C07A04FDE82C4 | SHA256:65BE8208FA40FC9603A89DD07C4FF450D8EE2C26D438EB6DB3592B53725C7620 | |||
| 3488 | PO.exe | C:\Users\admin\DECRYPT-FILES.txt | text | |
MD5:28BB073B8C38A5B2CB566313F42743A6 | SHA256:EB8596AD8964284DCBF8623209601577A1C818E305E11EC93CC48408814DD887 | |||
| 3488 | PO.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Collab\DECRYPT-FILES.txt | text | |
MD5:28BB073B8C38A5B2CB566313F42743A6 | SHA256:EB8596AD8964284DCBF8623209601577A1C818E305E11EC93CC48408814DD887 | |||
| 3488 | PO.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DECRYPT-FILES.txt | text | |
MD5:28BB073B8C38A5B2CB566313F42743A6 | SHA256:EB8596AD8964284DCBF8623209601577A1C818E305E11EC93CC48408814DD887 | |||
| 3488 | PO.exe | C:\Users\admin\AppData\DECRYPT-FILES.txt | text | |
MD5:28BB073B8C38A5B2CB566313F42743A6 | SHA256:EB8596AD8964284DCBF8623209601577A1C818E305E11EC93CC48408814DD887 | |||
| 3488 | PO.exe | C:\Users\admin\.oracle_jre_usage\DECRYPT-FILES.txt | text | |
MD5:28BB073B8C38A5B2CB566313F42743A6 | SHA256:EB8596AD8964284DCBF8623209601577A1C818E305E11EC93CC48408814DD887 | |||
| 3488 | PO.exe | C:\ProgramData\data1.tmp | gmc | |
MD5:76F8F28BD51EFA03AB992FDB050C8382 | SHA256:5470F0644589685000154CB7D3F60280ACB16E39CA961CCE2C016078B303BC1B | |||
| 3488 | PO.exe | C:\Users\admin\AppData\Roaming\Adobe\DECRYPT-FILES.txt | text | |
MD5:28BB073B8C38A5B2CB566313F42743A6 | SHA256:EB8596AD8964284DCBF8623209601577A1C818E305E11EC93CC48408814DD887 | |||
| 3488 | PO.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\DECRYPT-FILES.txt | text | |
MD5:28BB073B8C38A5B2CB566313F42743A6 | SHA256:EB8596AD8964284DCBF8623209601577A1C818E305E11EC93CC48408814DD887 | |||
| 3488 | PO.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\DECRYPT-FILES.txt | text | |
MD5:28BB073B8C38A5B2CB566313F42743A6 | SHA256:EB8596AD8964284DCBF8623209601577A1C818E305E11EC93CC48408814DD887 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
9
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3488 | PO.exe | POST | — | 91.218.114.4:80 | http://91.218.114.4/webauth/archive/gtbnevqhk.shtml | unknown | — | — | unknown |
3488 | PO.exe | POST | — | 91.218.114.4:80 | http://91.218.114.4/transfer/yxo.jspx?hhta=qu1w7e5&y=1&hmb=03x1k6 | unknown | — | — | unknown |
3488 | PO.exe | POST | — | 91.218.114.4:80 | http://91.218.114.4/transfer/yxo.jspx?hhta=qu1w7e5&y=1&hmb=03x1k6 | unknown | — | — | unknown |
3488 | PO.exe | POST | — | 91.218.114.4:80 | http://91.218.114.4/webauth/archive/gtbnevqhk.shtml | unknown | — | — | unknown |
3488 | PO.exe | POST | — | 91.218.114.11:80 | http://91.218.114.11/aofa.aspx?oitr=v16w177i&wm=ipddvot7&w=10 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3284 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3488 | PO.exe | 91.218.114.4:80 | — | Hostkey B.v. | RU | malicious |
3488 | PO.exe | 91.218.114.11:80 | — | Hostkey B.v. | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3488 | PO.exe | A Network Trojan was detected | ET MALWARE Maze/ID Ransomware Activity |
3488 | PO.exe | A Network Trojan was detected | ET MALWARE Maze/ID Ransomware Activity |
3488 | PO.exe | A Network Trojan was detected | ET MALWARE Maze/ID Ransomware Activity |