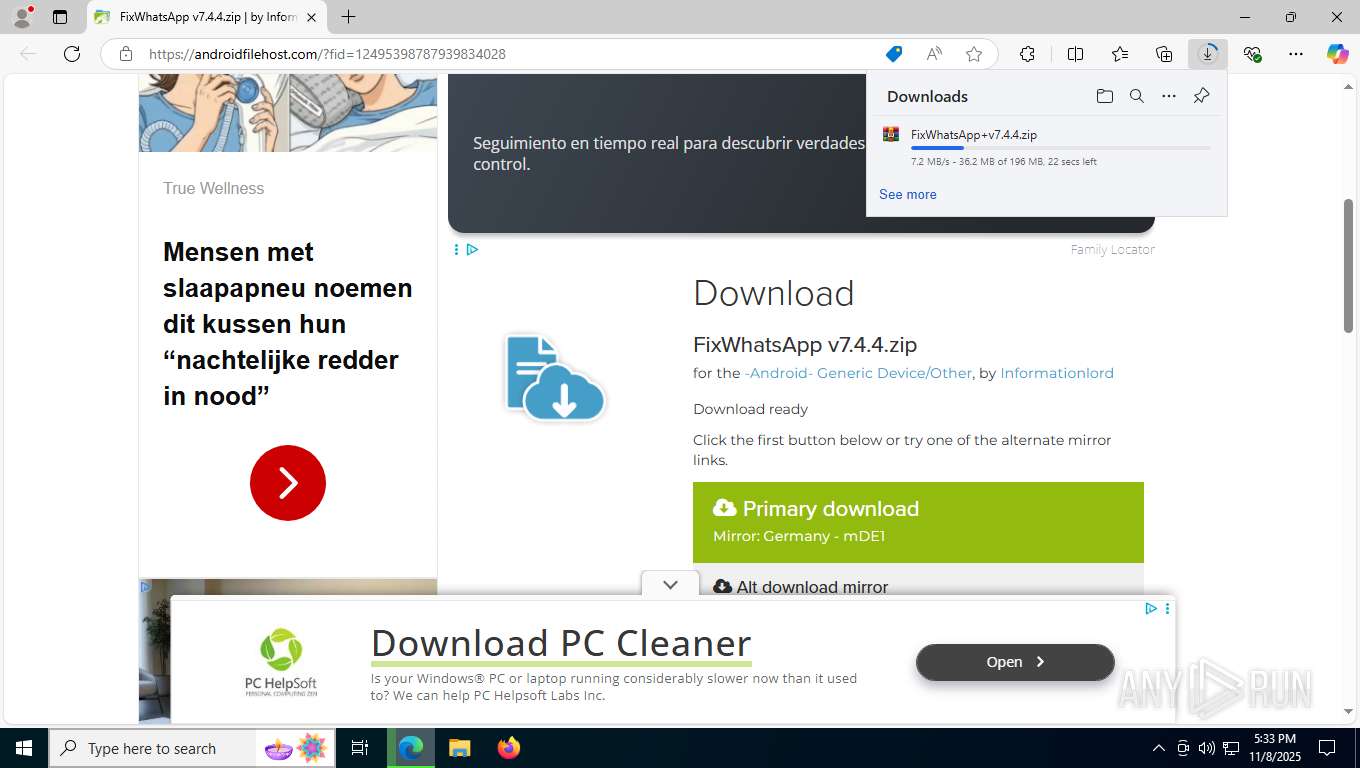
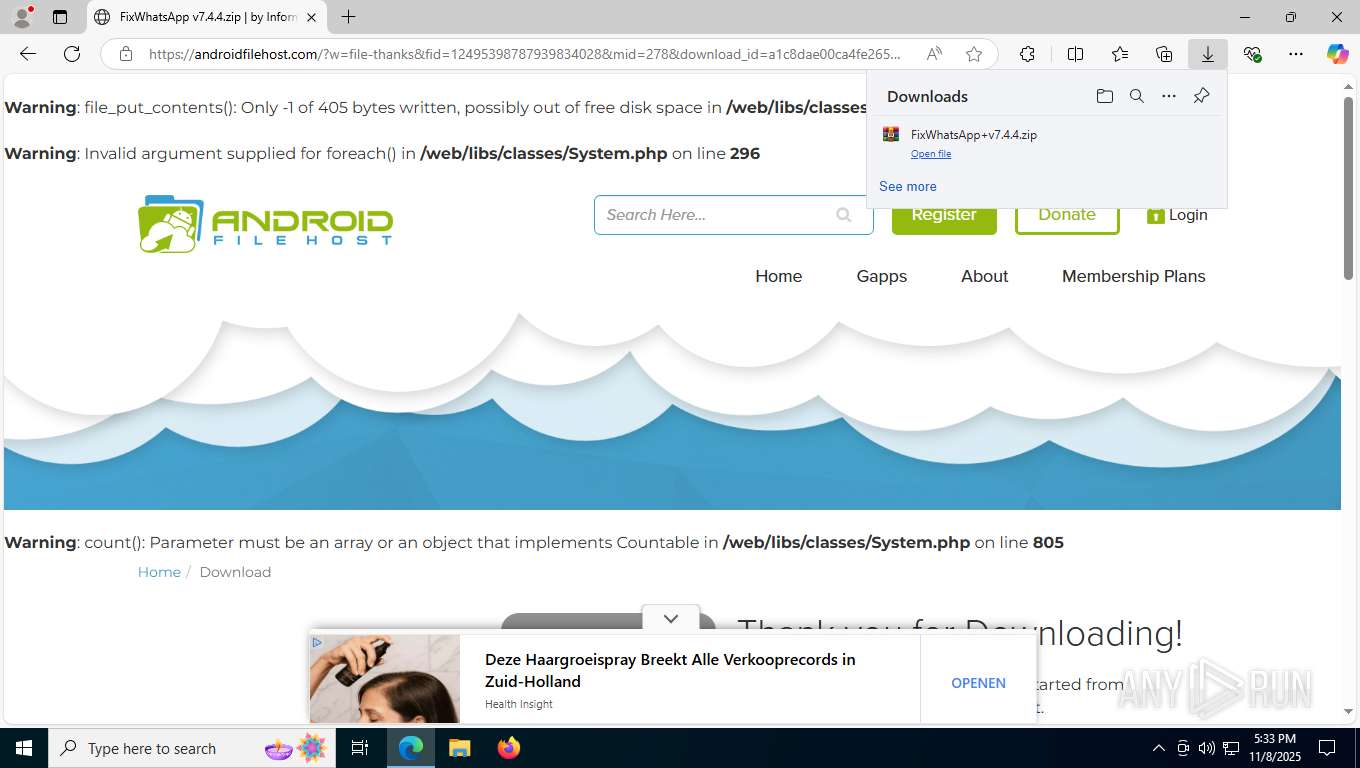
| URL: | https://androidfilehost.com/?fid=12495398787939834028 |
| Full analysis: | https://app.any.run/tasks/668769c6-fed0-4bab-beba-ba7137c16984 |
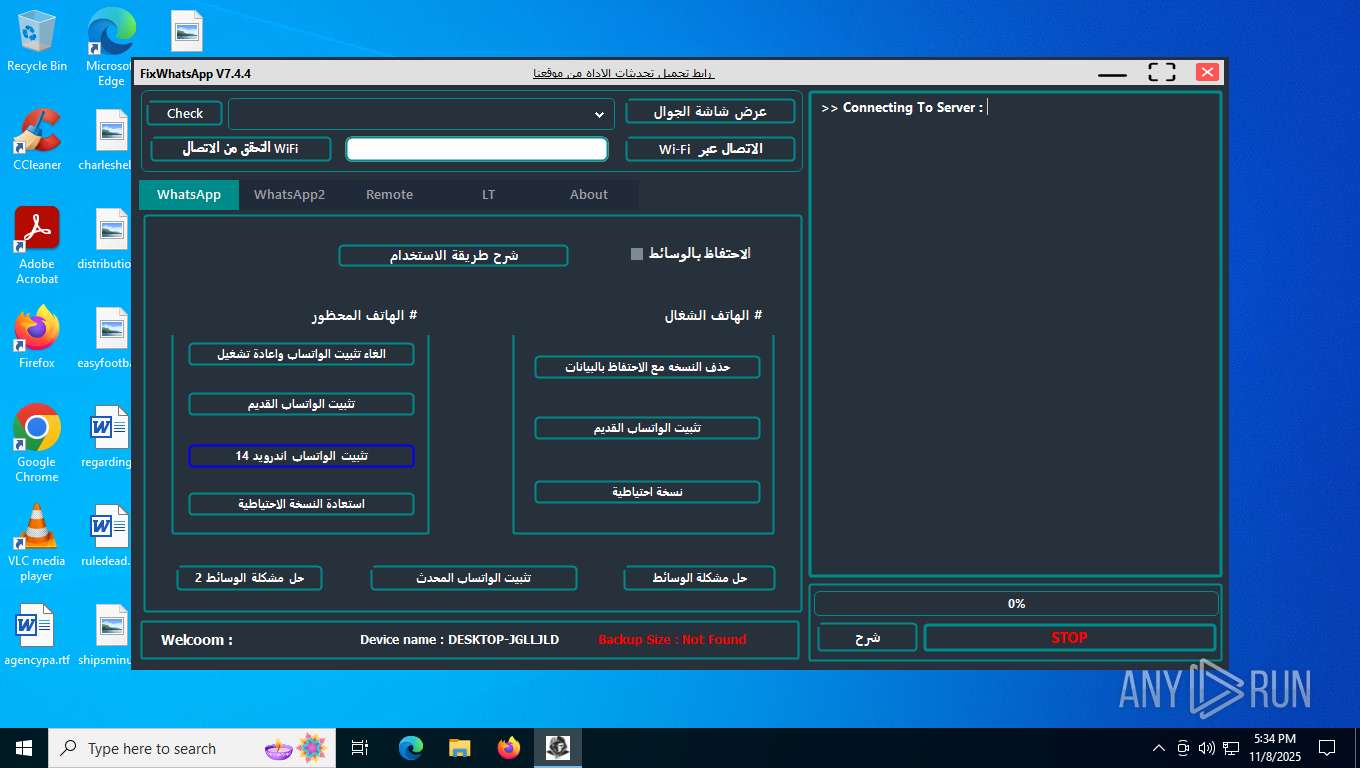
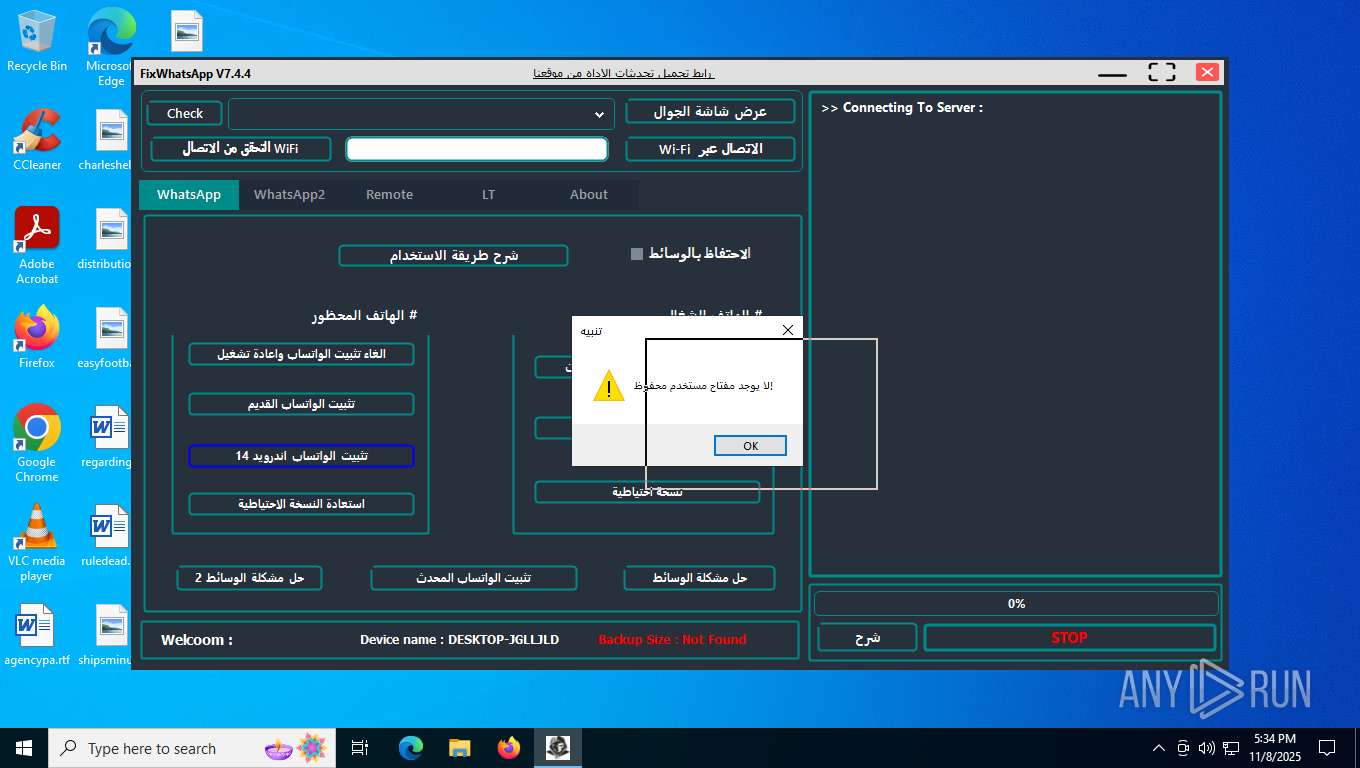
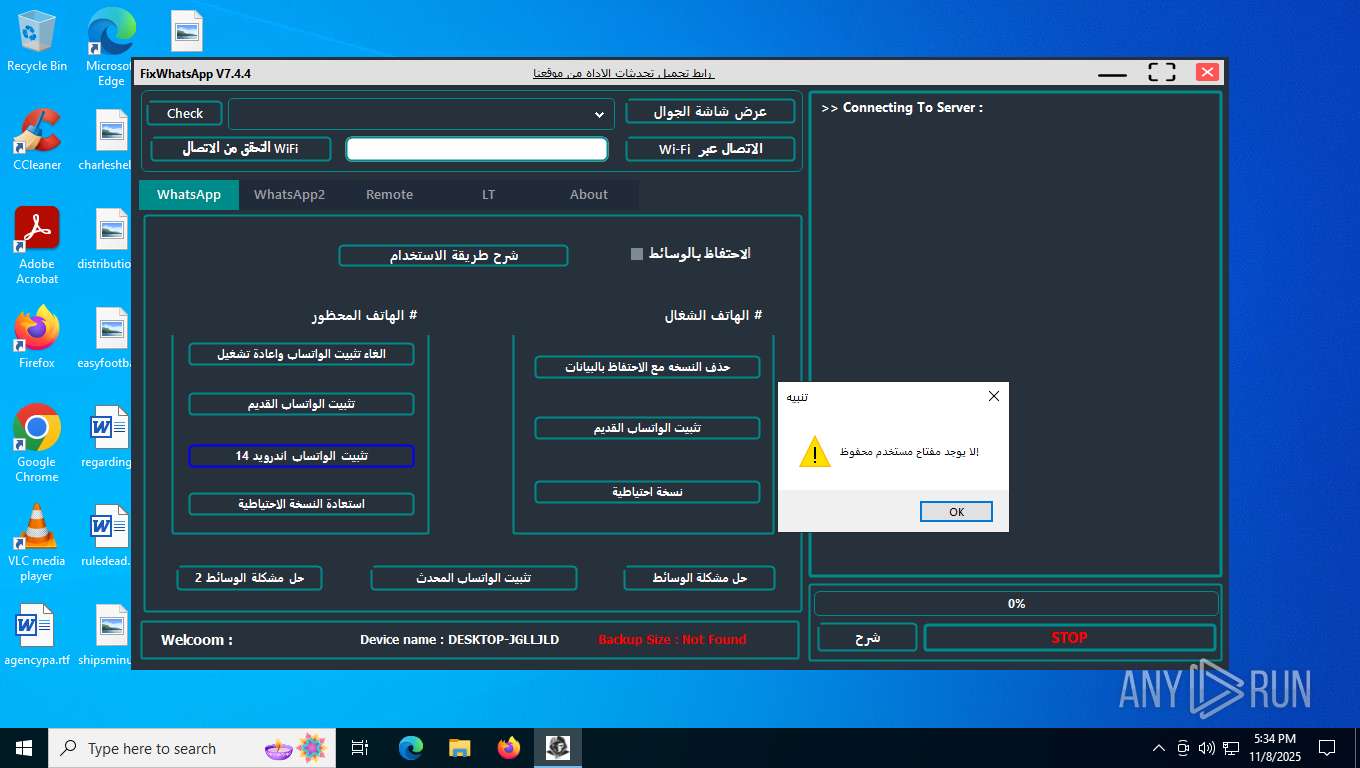
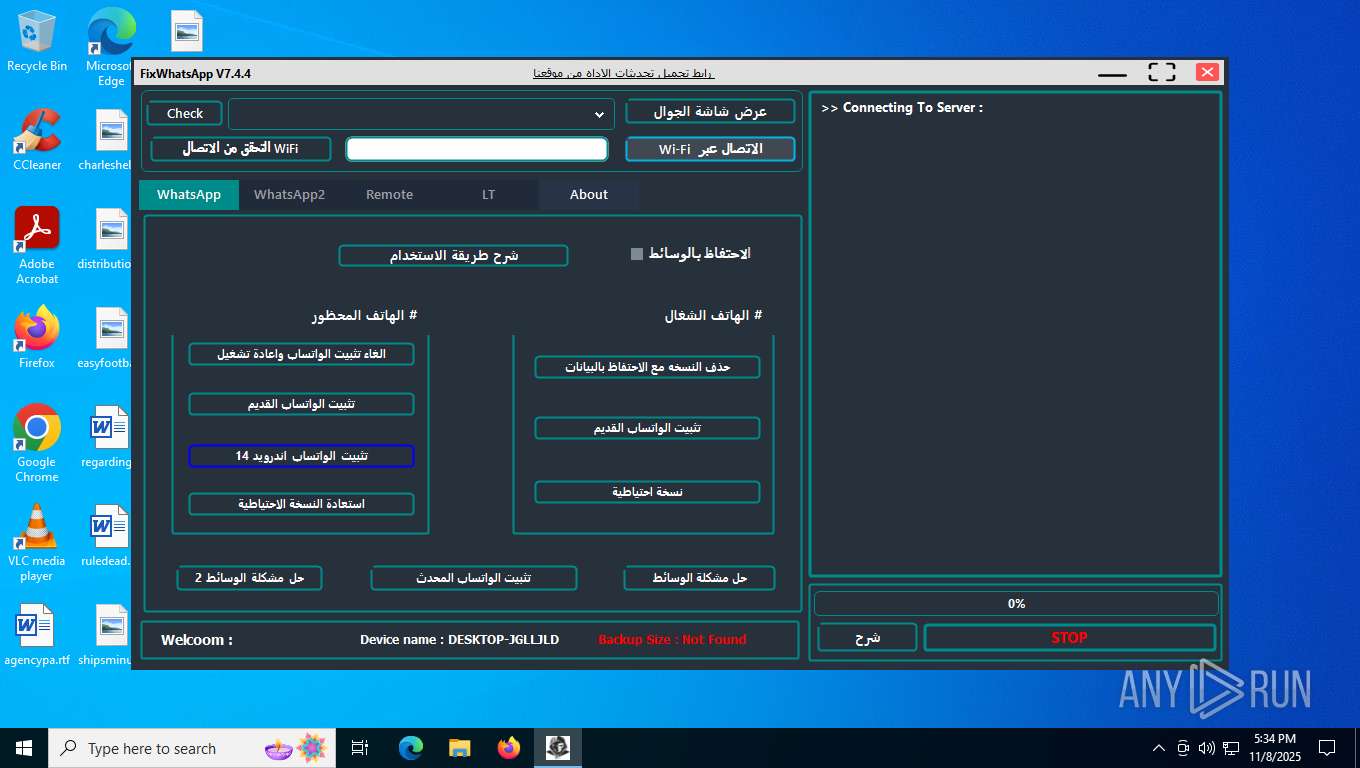
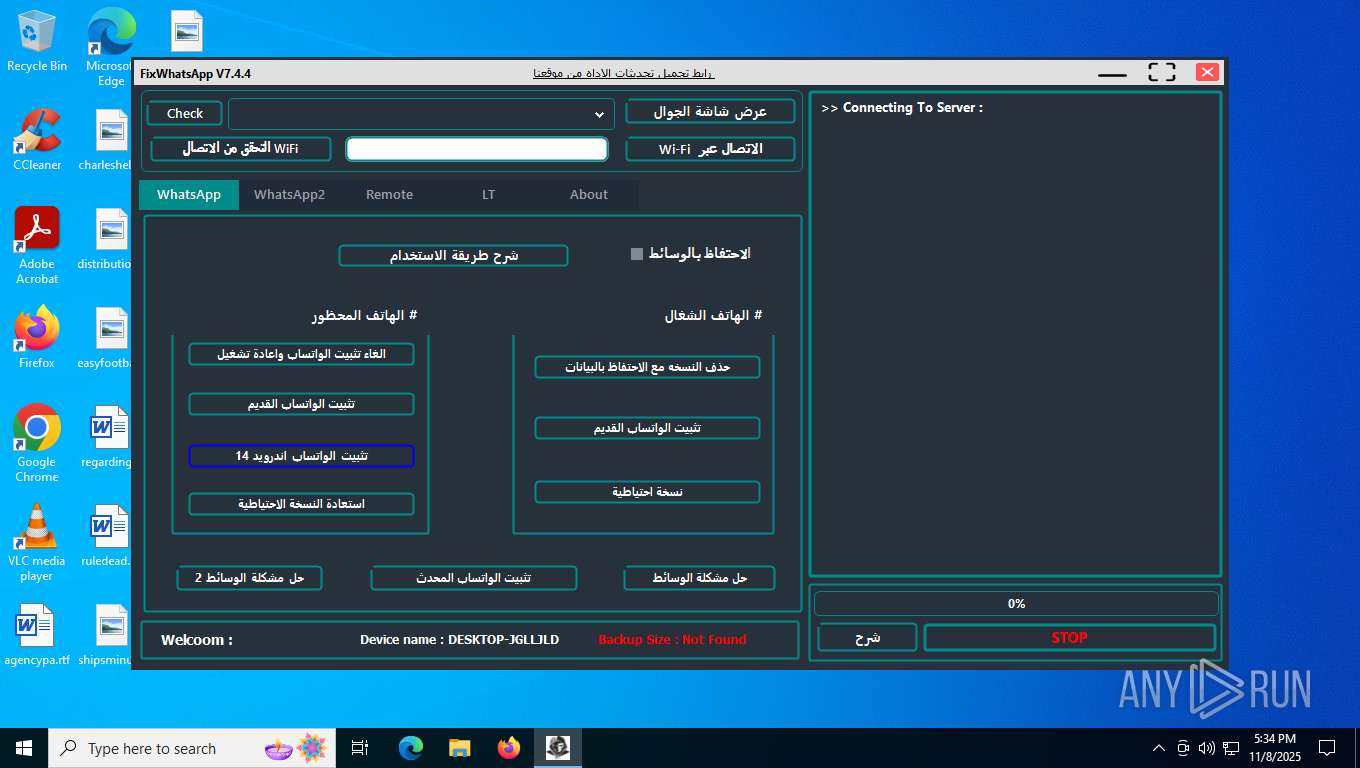
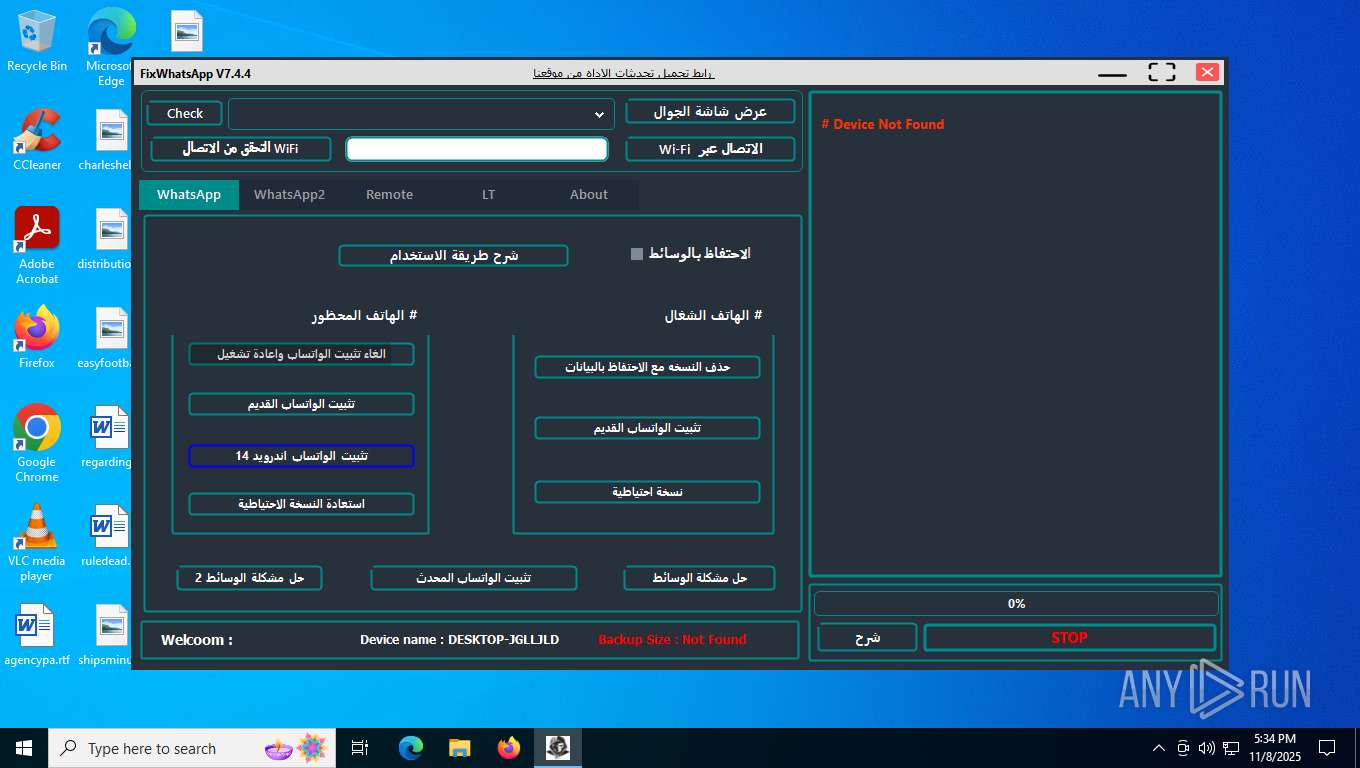
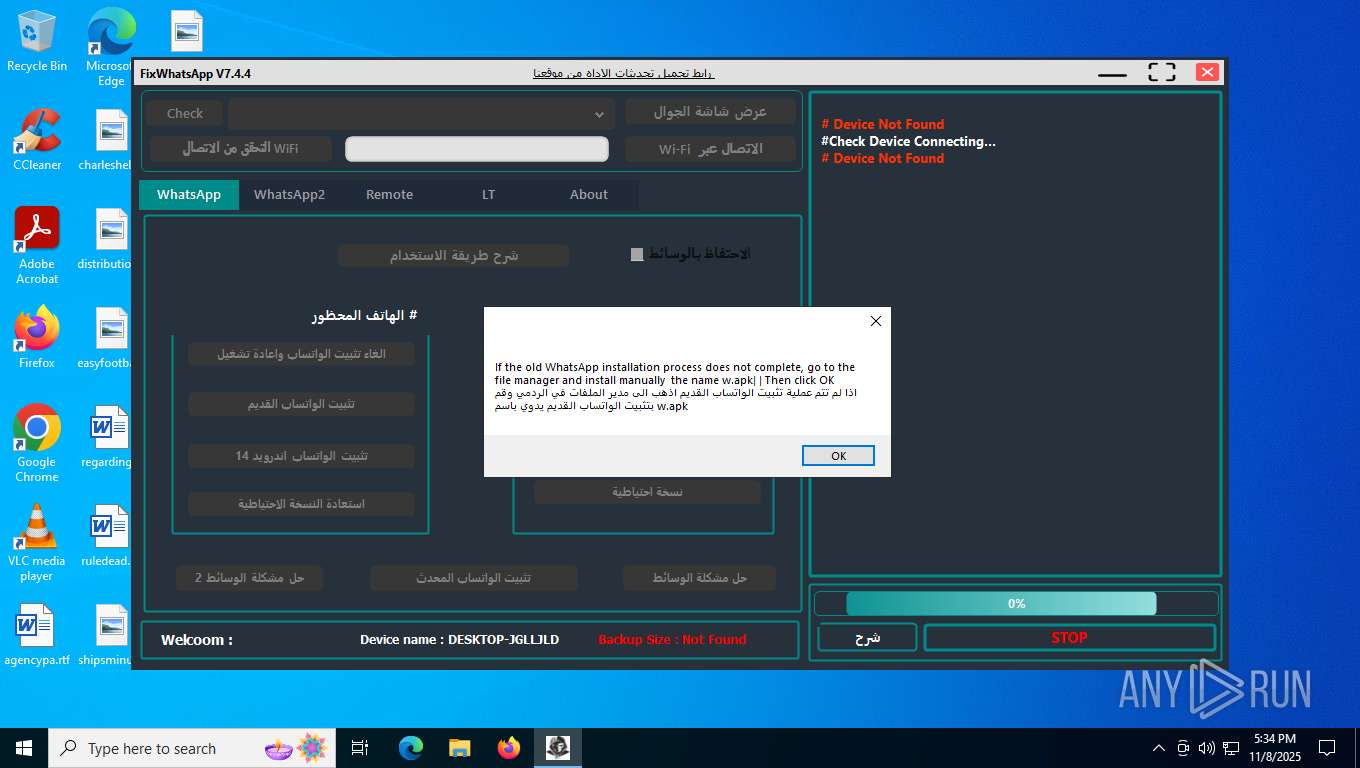
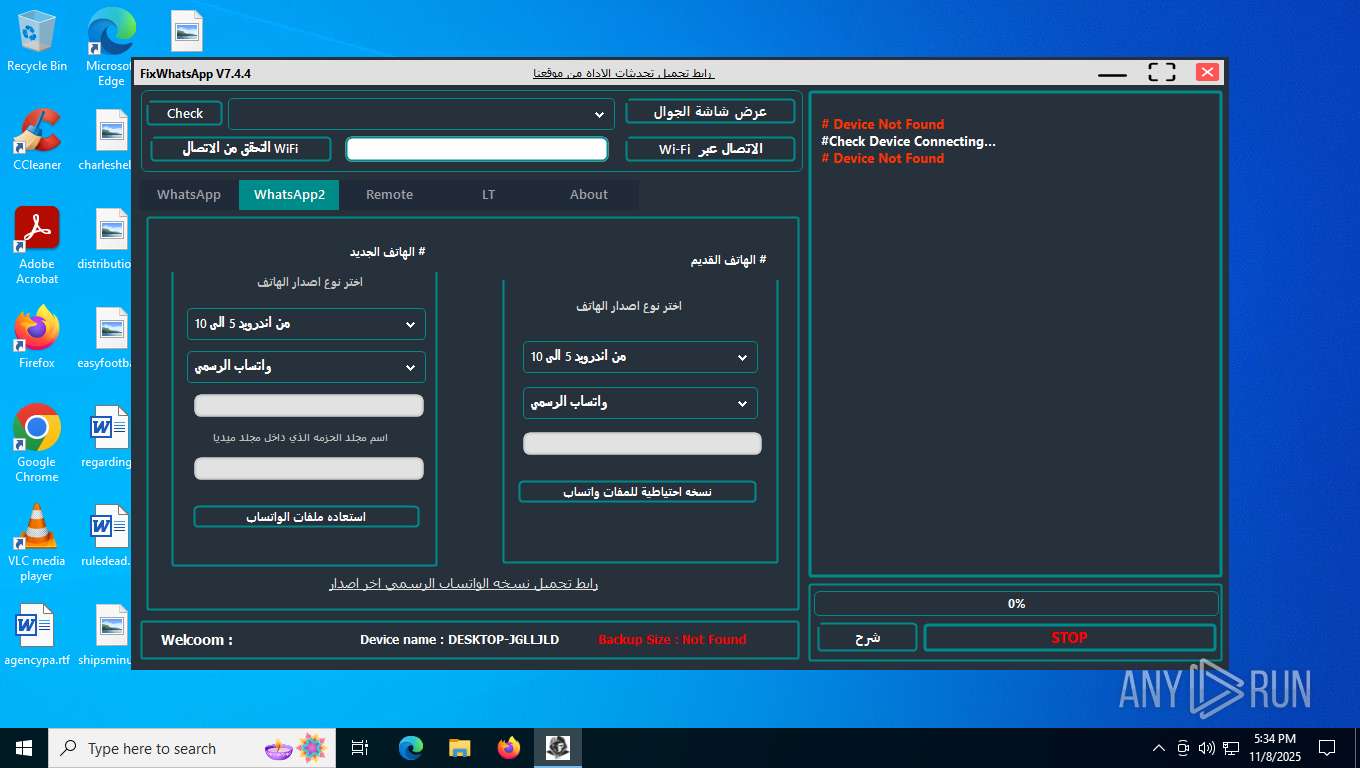
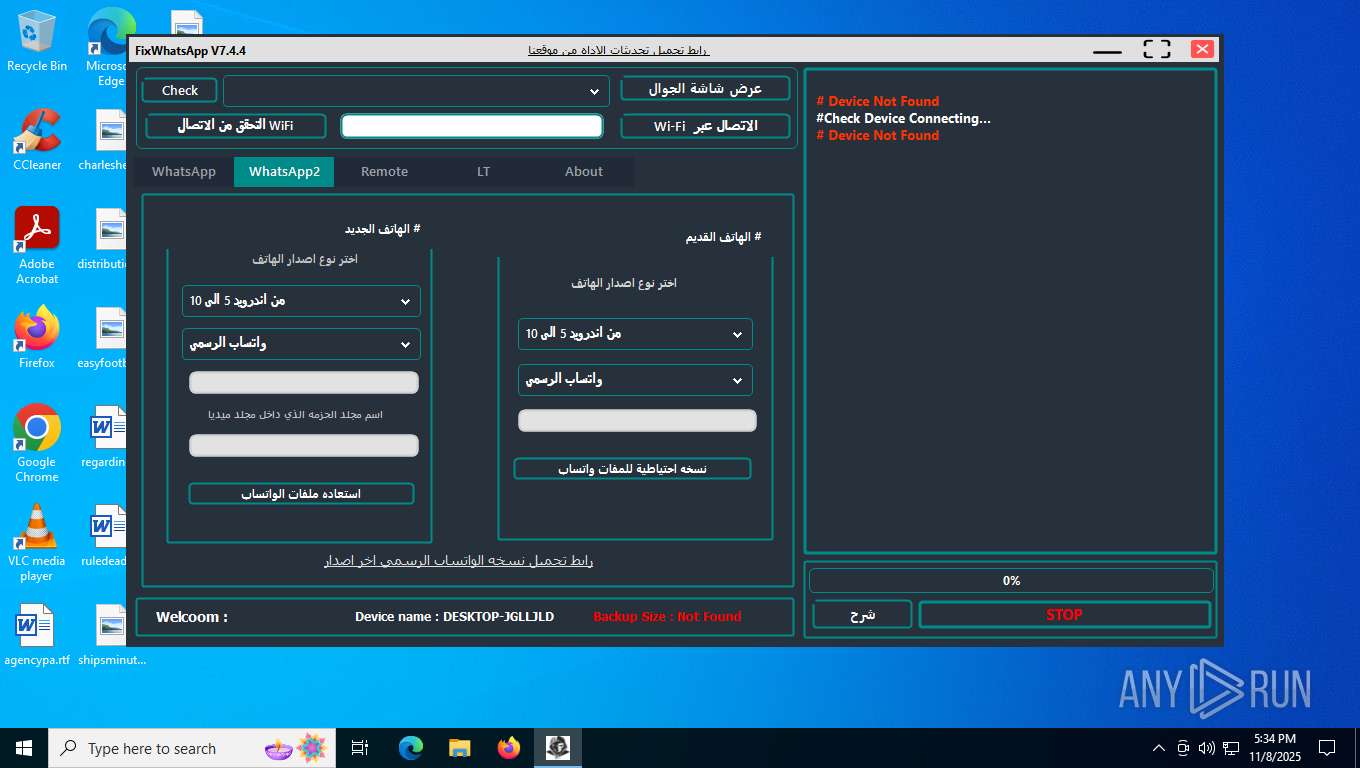
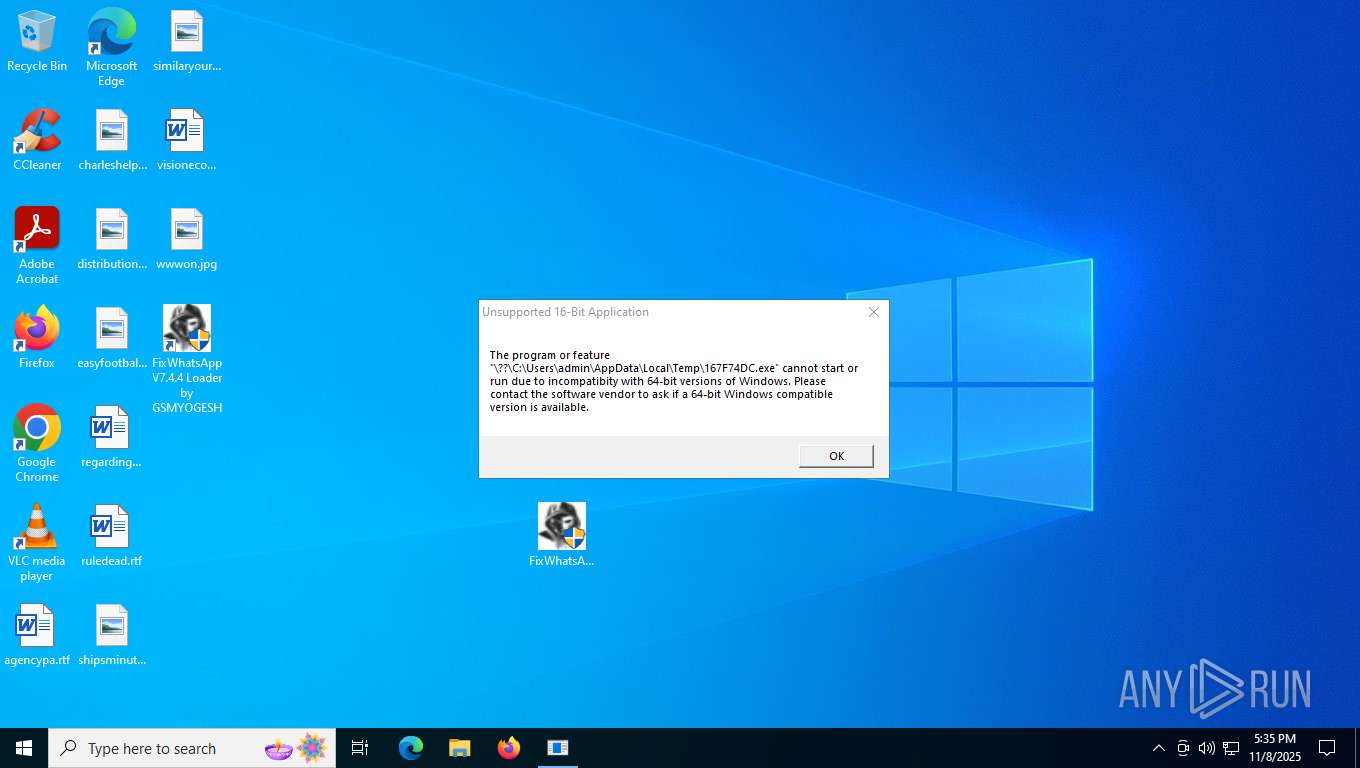
| Verdict: | Malicious activity |
| Threats: | A backdoor is a type of cybersecurity threat that allows attackers to secretly compromise a system and conduct malicious activities, such as stealing data and modifying files. Backdoors can be difficult to detect, as they often use legitimate system applications to evade defense mechanisms. Threat actors often utilize special malware, such as PlugX, to establish backdoors on target devices. |
| Analysis date: | November 08, 2025, 17:33:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
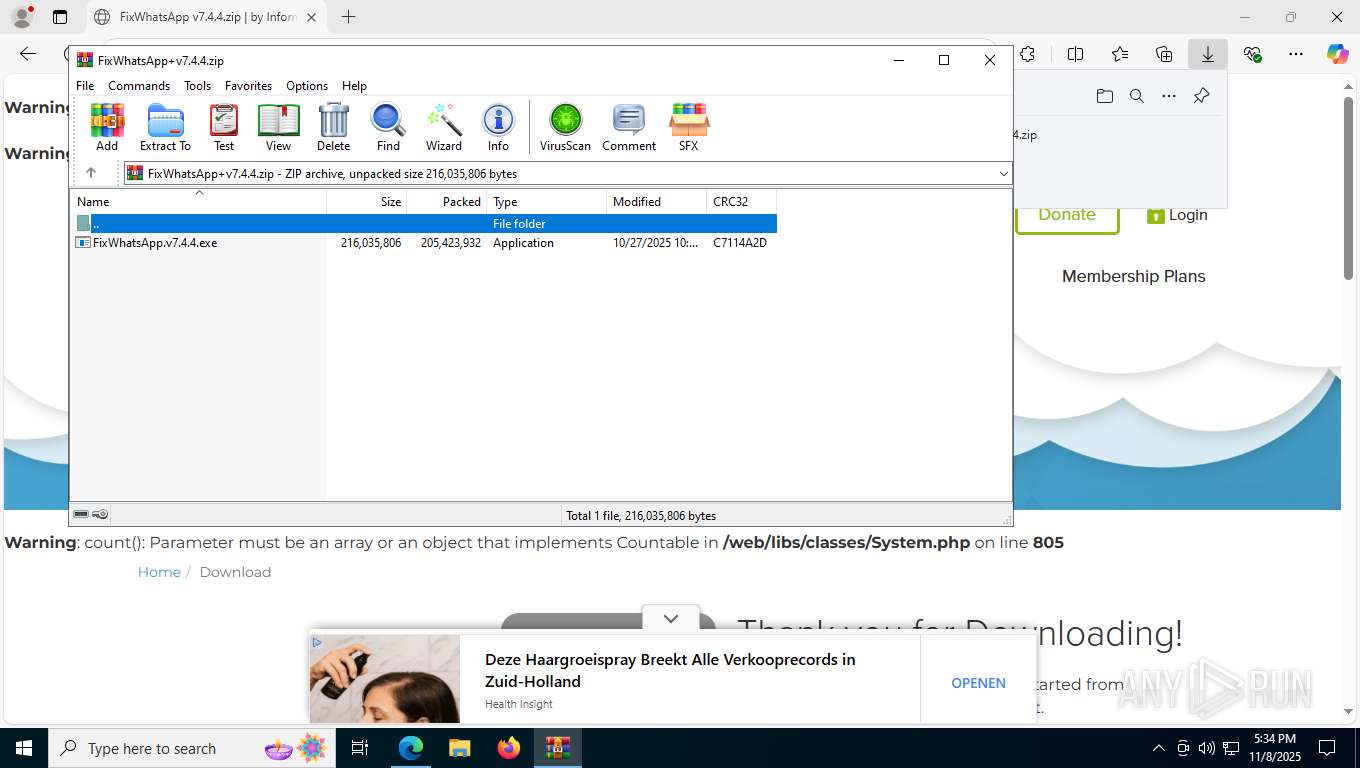
| MD5: | C2C70FE0453D1494FC7453EC03DB8425 |
| SHA1: | C5E3606F296DFFCD07B222754BA194937147685E |
| SHA256: | 0284167108CE553E4AAFC8761387F918BDA5321E1D3F8B7BF0E6555F0B4FE298 |
| SSDEEP: | 3:N8FMBDGKIBQvbE0Nn:22BBIBQvbrN |
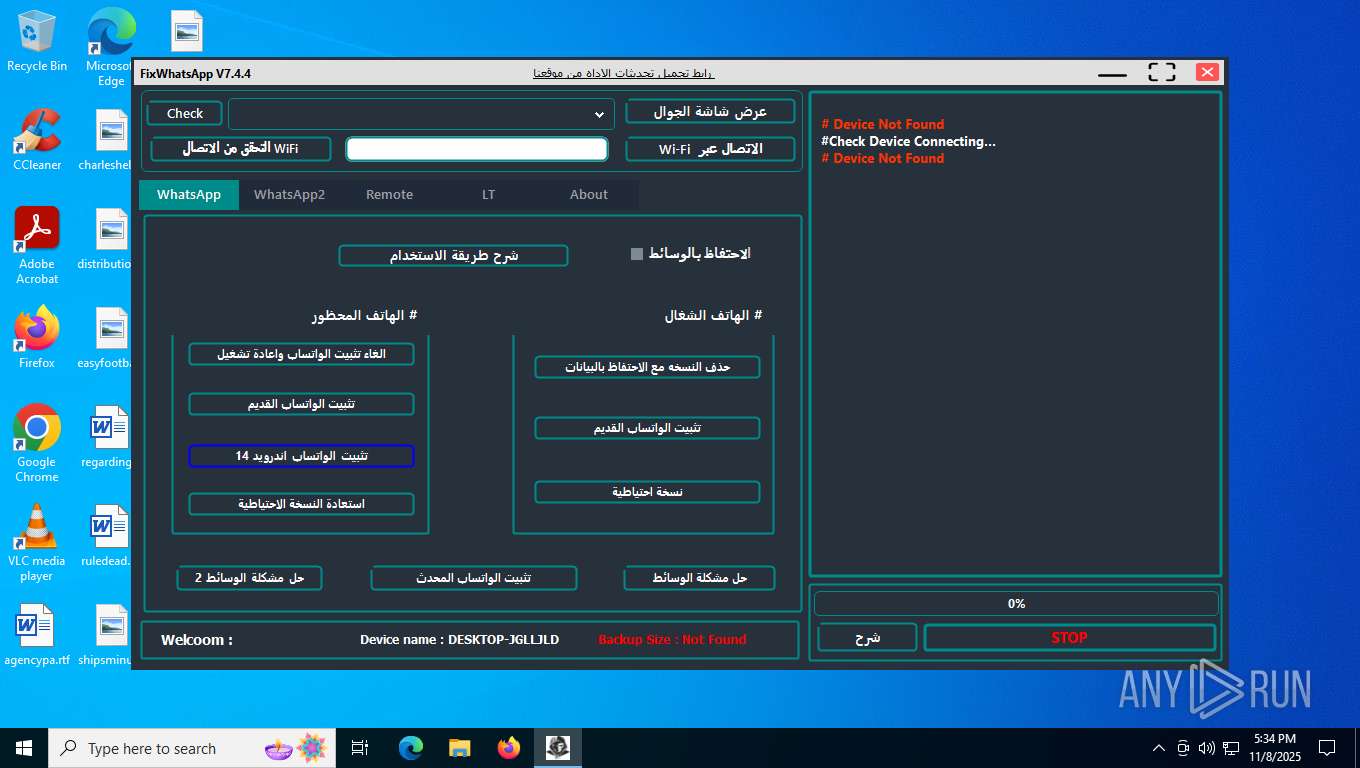
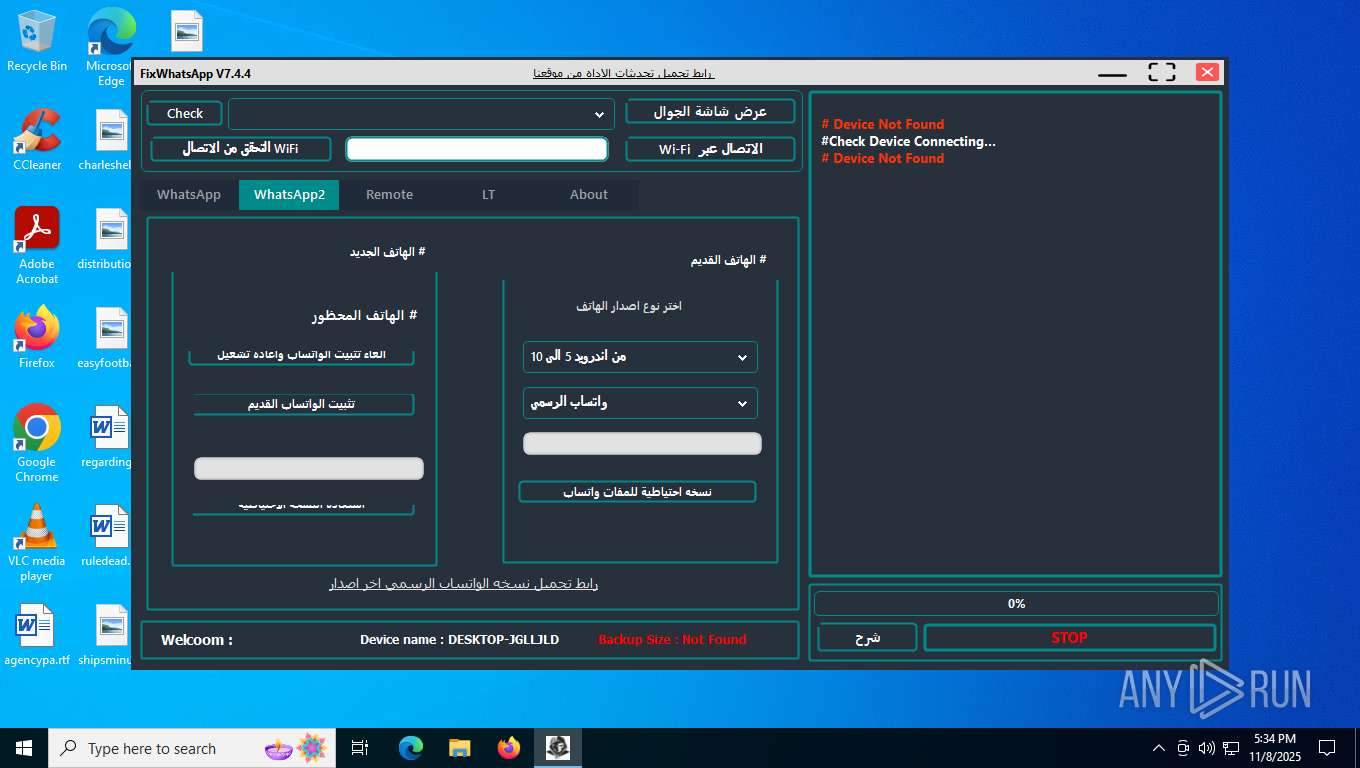
MALICIOUS
Changes the autorun value in the registry
- FixWhatsApp.v7.4.4.exe (PID: 2028)
Reads a specific registry key of the VM
- FixWhatsApp.exe (PID: 9052)
Changes settings of System certificates
- dcagentregister.exe (PID: 5304)
- dcconfig.exe (PID: 3500)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7372)
BDAEJEC has been detected
- gsDRUf.exe (PID: 3272)
Changes the Windows auto-update feature
- meaaphelper.exe (PID: 6836)
- bmagent.exe (PID: 8332)
Actions looks like stealing of personal data
- bmagent.exe (PID: 8332)
SUSPICIOUS
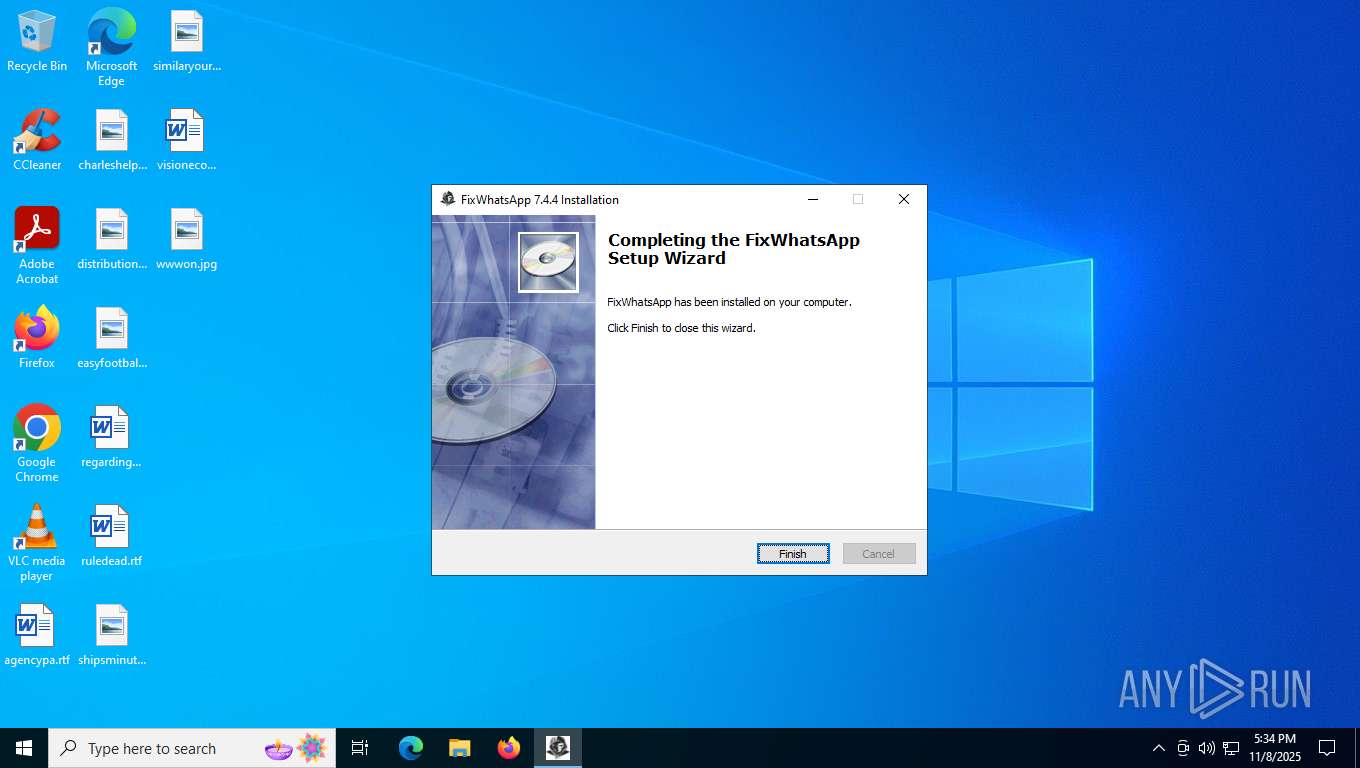
ADVANCEDINSTALLER mutex has been found
- FixWhatsApp.v7.4.4.exe (PID: 2028)
Reads the Windows owner or organization settings
- FixWhatsApp.v7.4.4.exe (PID: 2028)
- msiexec.exe (PID: 7648)
Process drops legitimate windows executable
- FixWhatsApp.v7.4.4.exe (PID: 2028)
- FixWhatsApp_V7.4.4.exe (PID: 1664)
- msiexec.exe (PID: 7648)
- 7za.exe (PID: 4064)
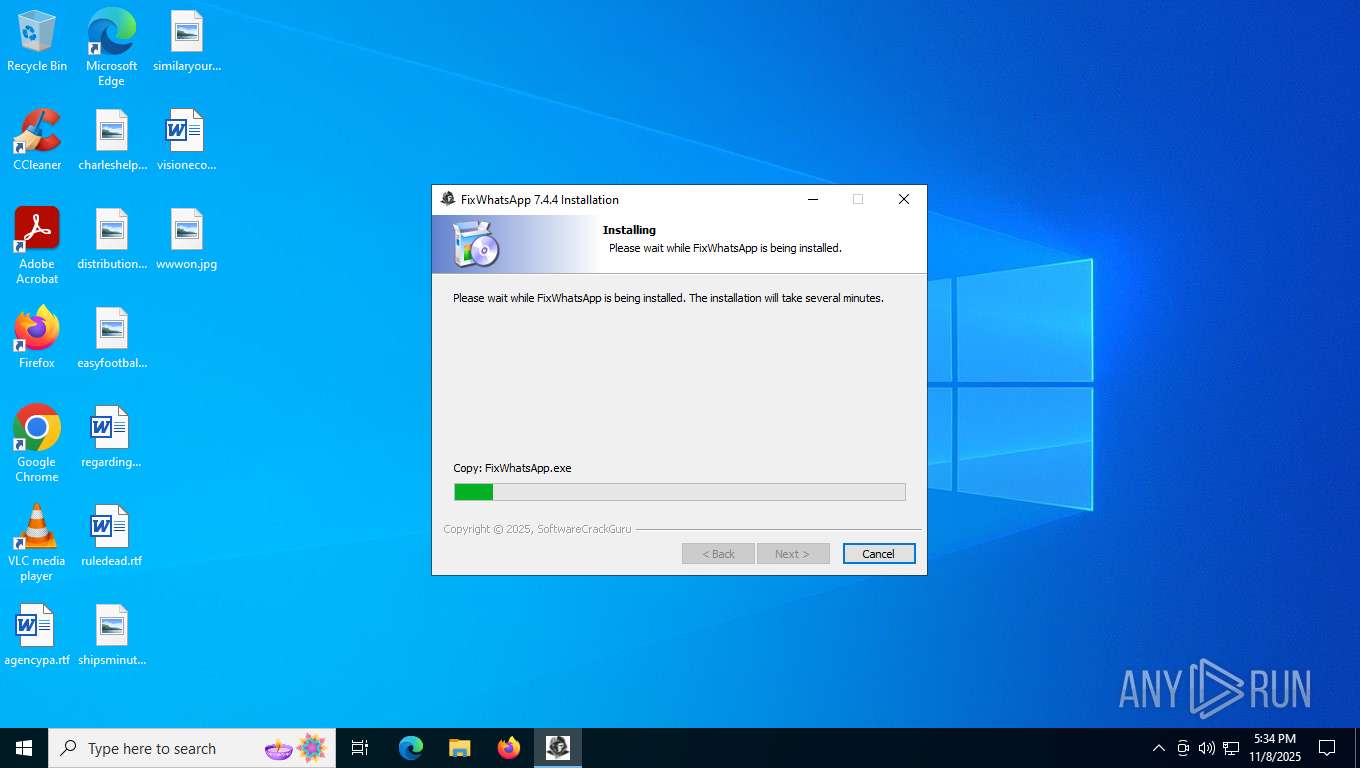
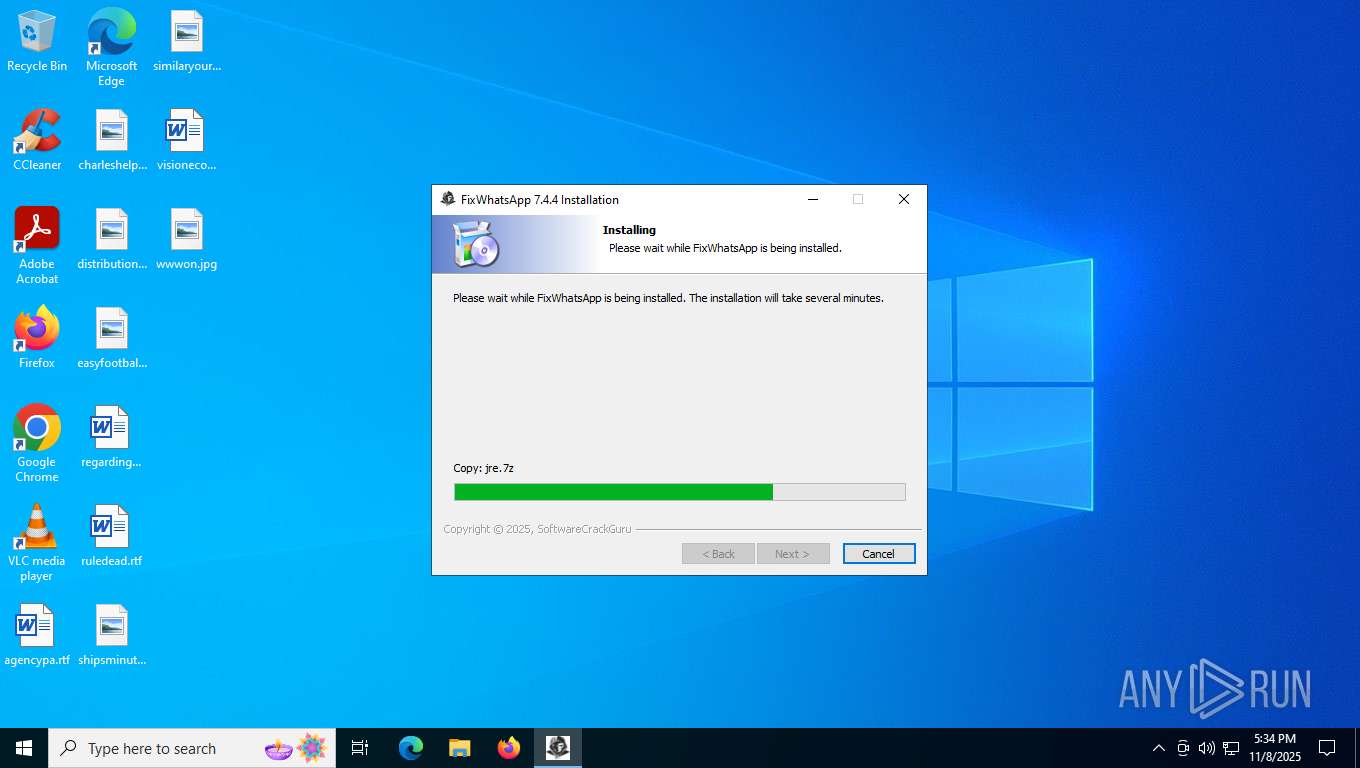
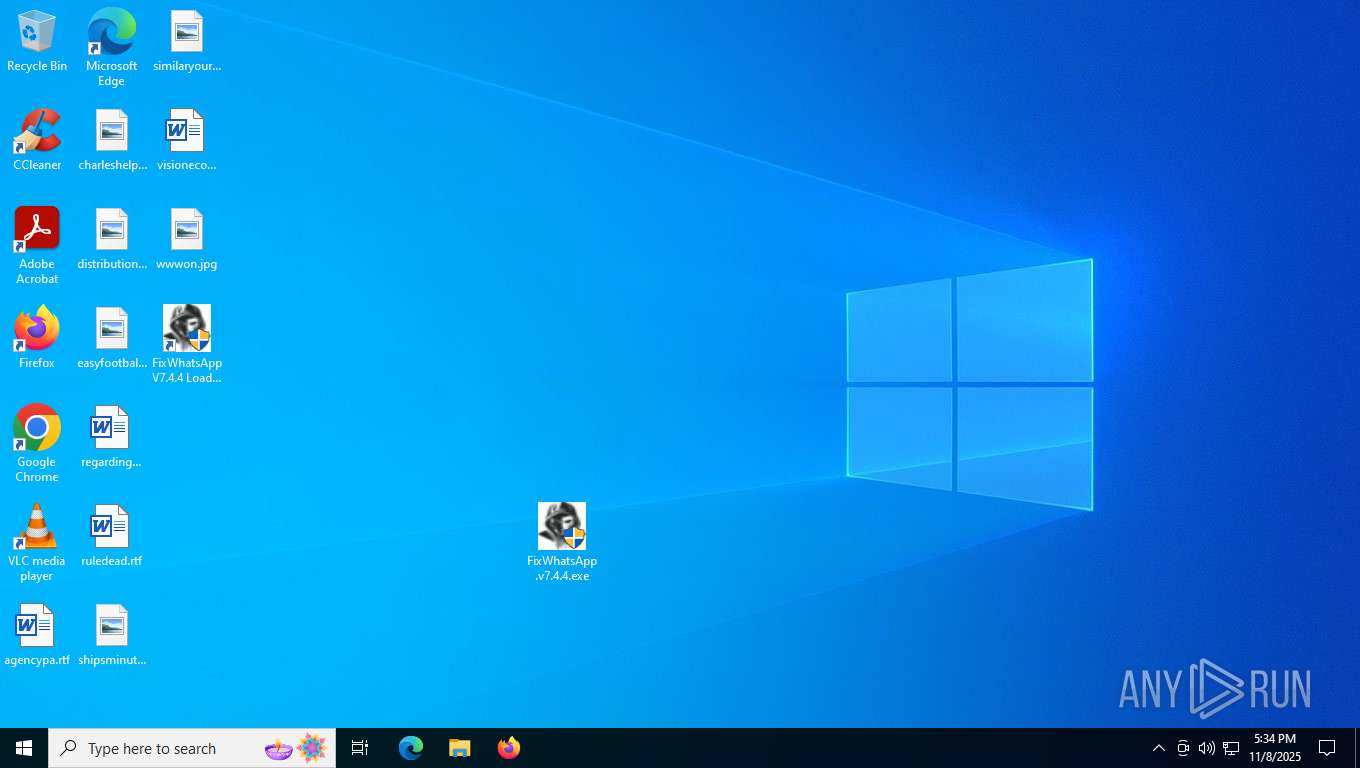
Executable content was dropped or overwritten
- FixWhatsApp.v7.4.4.exe (PID: 2564)
- FixWhatsApp_V7.4.4.exe (PID: 1664)
- FixWhatsApp.v7.4.4.exe (PID: 2028)
- 7za.exe (PID: 4064)
- FixWhatsApp.v7.4.4.exe (PID: 7216)
- 7zr.exe (PID: 8796)
- meaaphelper.exe (PID: 3420)
- 7za.exe (PID: 7672)
- 7za.exe (PID: 2436)
- 7za.exe (PID: 5376)
Reads security settings of Internet Explorer
- FixWhatsApp.v7.4.4.exe (PID: 2028)
- msiexec.exe (PID: 8840)
- FixWhatsApp.exe (PID: 9052)
- MSI617.tmp (PID: 7208)
- gsDRUf.exe (PID: 3272)
- JpLTCC.exe (PID: 7300)
Drops 7-zip archiver for unpacking
- FixWhatsApp_V7.4.4.exe (PID: 1664)
- msiexec.exe (PID: 7648)
There is functionality for taking screenshot (YARA)
- FixWhatsApp.v7.4.4.exe (PID: 2028)
- FixWhatsApp.exe (PID: 9052)
Detects AdvancedInstaller (YARA)
- FixWhatsApp.v7.4.4.exe (PID: 2028)
Reads the BIOS version
- FixWhatsApp.exe (PID: 9052)
The process drops C-runtime libraries
- FixWhatsApp_V7.4.4.exe (PID: 1664)
- 7za.exe (PID: 4064)
Adds/modifies Windows certificates
- dcagentregister.exe (PID: 5304)
- dcconfig.exe (PID: 3500)
Connects to unusual port
- dcagentregister.exe (PID: 5304)
- dcstatusutil.exe (PID: 7688)
- dcstatusutil.exe (PID: 7944)
- dcconfig.exe (PID: 3364)
- dcinventory.exe (PID: 7772)
- dcondemand.exe (PID: 6716)
- dcinventory.exe (PID: 7776)
- gsDRUf.exe (PID: 3272)
- dcconfig.exe (PID: 3500)
- JpLTCC.exe (PID: 7300)
- meaap.exe (PID: 9120)
- bmagent.exe (PID: 8332)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 1196)
Starts CMD.EXE for commands execution
- dcagentregister.exe (PID: 5304)
- MSI617.tmp (PID: 7208)
- gsDRUf.exe (PID: 3272)
- JpLTCC.exe (PID: 7300)
Executes as Windows Service
- dcagentservice.exe (PID: 7964)
- VSSVC.exe (PID: 2612)
- WmiApSrv.exe (PID: 1928)
Non windows owned service launched
- dcagentservice.exe (PID: 7964)
Searches for installed software
- dcinventory.exe (PID: 7772)
- dcconfig.exe (PID: 3500)
- EdgeWebView2.exe (PID: 8372)
Lists all scheduled tasks
- schtasks.exe (PID: 1128)
- schtasks.exe (PID: 7812)
- schtasks.exe (PID: 932)
Executing commands from a ".bat" file
- MSI617.tmp (PID: 7208)
- gsDRUf.exe (PID: 3272)
- JpLTCC.exe (PID: 7300)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 7372)
- net.exe (PID: 2312)
- net.exe (PID: 6884)
- cmd.exe (PID: 7192)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 3404)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7372)
Get information on the list of running processes
- cmd.exe (PID: 7372)
Starts POWERSHELL.EXE for commands execution
- EdgeWebView2.exe (PID: 8372)
Checks for external IP
- svchost.exe (PID: 2276)
- EdgeWebView2.exe (PID: 8372)
The process bypasses the loading of PowerShell profile settings
- EdgeWebView2.exe (PID: 8372)
Suspicious use of NETSH.EXE
- EdgeWebView2.exe (PID: 8372)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 3420)
The process creates files with name similar to system file names
- 7za.exe (PID: 5376)
INFO
Checks supported languages
- identity_helper.exe (PID: 2008)
- FixWhatsApp.v7.4.4.exe (PID: 2028)
- msiexec.exe (PID: 7648)
- msiexec.exe (PID: 8840)
- FixWhatsApp.v7.4.4.exe (PID: 2564)
- FixWhatsApp_V7.4.4.exe (PID: 1664)
- msiexec.exe (PID: 4912)
- FixWhatsApp.exe (PID: 9052)
- dcagentregister.exe (PID: 5304)
- adb.exe (PID: 404)
- adb.exe (PID: 1276)
- 7za.exe (PID: 4064)
- identity_helper.exe (PID: 8208)
- dcstatusutil.exe (PID: 7688)
- dcagentservice.exe (PID: 7964)
- dcusbsummary.exe (PID: 4792)
- dcconfig.exe (PID: 3364)
- dcusb64.exe (PID: 2616)
- CRU_Reporter.exe (PID: 5376)
- dcswmeter.exe (PID: 8048)
- dcinventory.exe (PID: 7772)
- dcstatusutil.exe (PID: 7944)
- dcondemand.exe (PID: 6716)
- dcconfig.exe (PID: 3500)
- dcnacprocess.exe (PID: 5456)
- msiexec.exe (PID: 2036)
- msiexec.exe (PID: 8608)
- MSI617.tmp (PID: 7208)
- FixWhatsApp.v7.4.4.exe (PID: 7216)
- EdgeWebView2.exe (PID: 8372)
- dcinventory.exe (PID: 7776)
- 7zr.exe (PID: 8796)
- gsDRUf.exe (PID: 3272)
- 7za.exe (PID: 7672)
- DCProcessMonitor.exe (PID: 2328)
- JpLTCC.exe (PID: 7300)
- meaap.exe (PID: 9120)
- meaaphelper.exe (PID: 3420)
- 7za.exe (PID: 688)
- 7za.exe (PID: 2436)
- meaaphelper.exe (PID: 6836)
- 7za.exe (PID: 5376)
- 7za.exe (PID: 7100)
- bmagent.exe (PID: 8332)
- meaaphelper.exe (PID: 8996)
- meaaphelper.exe (PID: 8828)
- meaaphelper.exe (PID: 8448)
Application launched itself
- msedge.exe (PID: 7492)
- msedge.exe (PID: 8744)
- msedge.exe (PID: 8224)
- msedge.exe (PID: 1664)
- msedge.exe (PID: 8272)
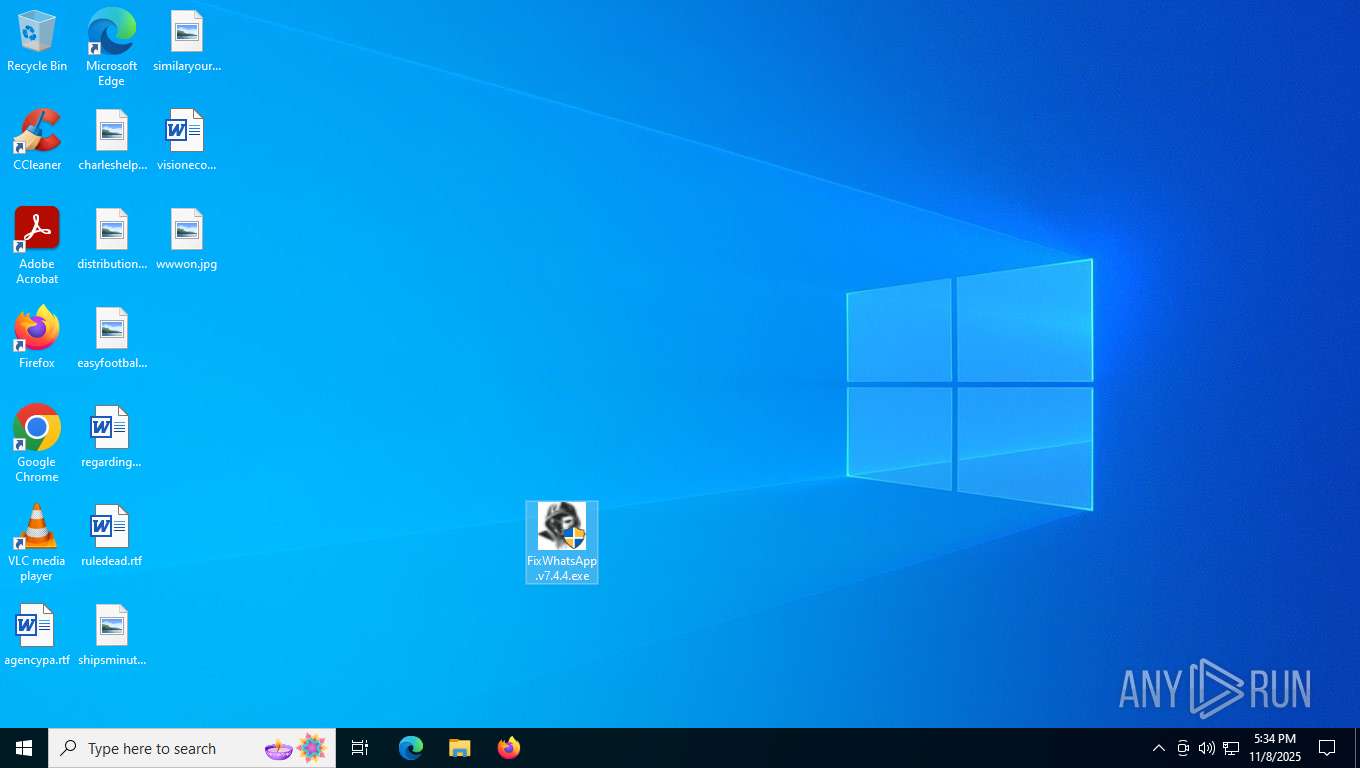
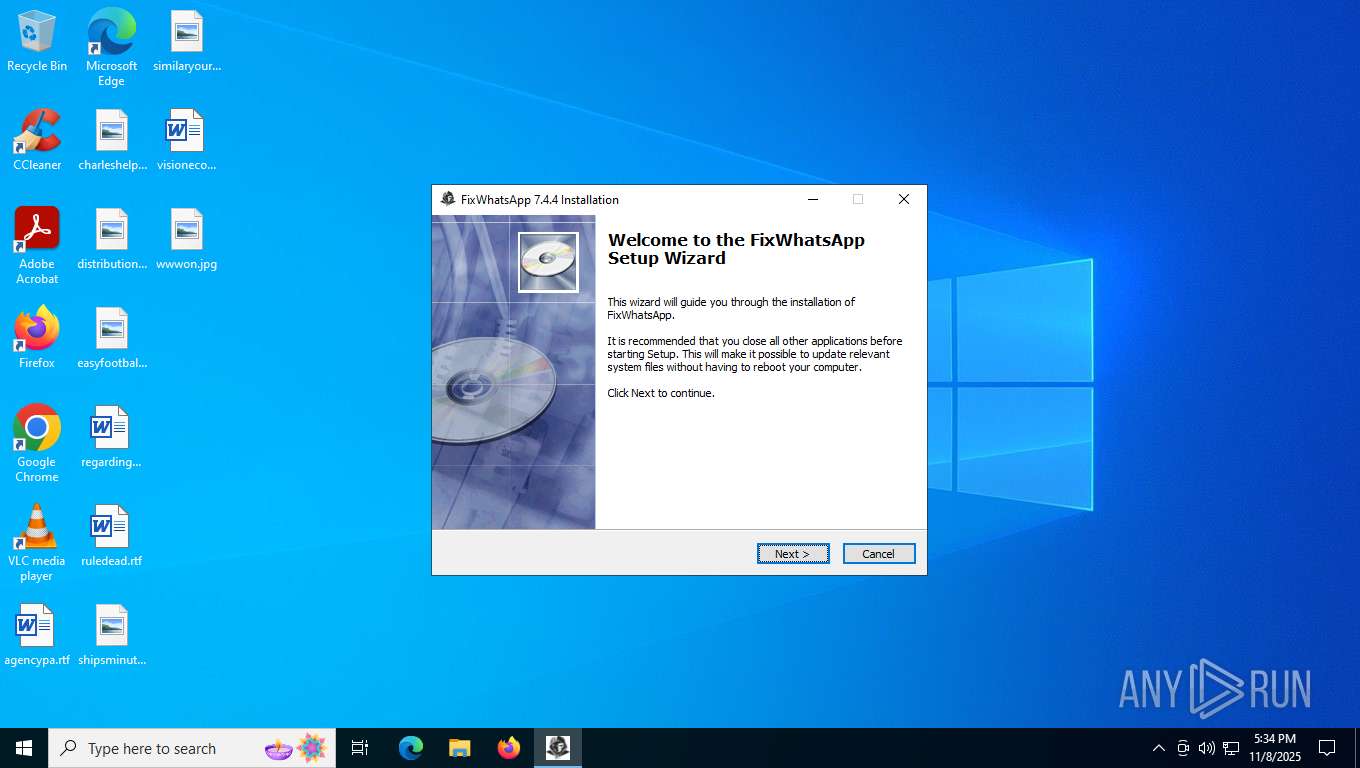
Manual execution by a user
- FixWhatsApp.v7.4.4.exe (PID: 4784)
- FixWhatsApp.v7.4.4.exe (PID: 2028)
- FixWhatsApp.exe (PID: 4712)
- FixWhatsApp.exe (PID: 9052)
- msedge.exe (PID: 8744)
- FixWhatsApp.v7.4.4.exe (PID: 592)
- cmd.exe (PID: 7192)
Reads the computer name
- identity_helper.exe (PID: 2008)
- FixWhatsApp.v7.4.4.exe (PID: 2028)
- msiexec.exe (PID: 7648)
- msiexec.exe (PID: 8840)
- FixWhatsApp_V7.4.4.exe (PID: 1664)
- msiexec.exe (PID: 4912)
- FixWhatsApp.exe (PID: 9052)
- 7za.exe (PID: 4064)
- dcagentregister.exe (PID: 5304)
- identity_helper.exe (PID: 8208)
- dcstatusutil.exe (PID: 7688)
- dcagentservice.exe (PID: 7964)
- dcusbsummary.exe (PID: 4792)
- dcusb64.exe (PID: 2616)
- dcconfig.exe (PID: 3364)
- dcstatusutil.exe (PID: 7944)
- dcswmeter.exe (PID: 8048)
- dcinventory.exe (PID: 7772)
- dcondemand.exe (PID: 6716)
- dcnacprocess.exe (PID: 5456)
- msiexec.exe (PID: 2036)
- msiexec.exe (PID: 8608)
- MSI617.tmp (PID: 7208)
- EdgeWebView2.exe (PID: 8372)
- dcconfig.exe (PID: 3500)
- dcinventory.exe (PID: 7776)
- gsDRUf.exe (PID: 3272)
- 7zr.exe (PID: 8796)
- DCProcessMonitor.exe (PID: 2328)
- JpLTCC.exe (PID: 7300)
- 7za.exe (PID: 7672)
- meaap.exe (PID: 9120)
- 7za.exe (PID: 688)
- 7za.exe (PID: 2436)
- 7za.exe (PID: 7100)
- 7za.exe (PID: 5376)
- meaaphelper.exe (PID: 6836)
- bmagent.exe (PID: 8332)
- meaaphelper.exe (PID: 8828)
Reads Environment values
- identity_helper.exe (PID: 2008)
- FixWhatsApp.v7.4.4.exe (PID: 2028)
- msiexec.exe (PID: 8840)
- identity_helper.exe (PID: 8208)
- msiexec.exe (PID: 2036)
- msiexec.exe (PID: 8608)
Create files in a temporary directory
- FixWhatsApp.v7.4.4.exe (PID: 2028)
- FixWhatsApp_V7.4.4.exe (PID: 1664)
- dcagentregister.exe (PID: 5304)
- dcstatusutil.exe (PID: 7688)
- msiexec.exe (PID: 3956)
- msiexec.exe (PID: 2036)
- 7zr.exe (PID: 8796)
- gsDRUf.exe (PID: 3272)
Creates files or folders in the user directory
- FixWhatsApp.v7.4.4.exe (PID: 2028)
- FixWhatsApp.v7.4.4.exe (PID: 2564)
- msiexec.exe (PID: 7648)
- FixWhatsApp.v7.4.4.exe (PID: 7216)
- gsDRUf.exe (PID: 3272)
The sample compiled with english language support
- FixWhatsApp.v7.4.4.exe (PID: 2028)
- FixWhatsApp_V7.4.4.exe (PID: 1664)
- msiexec.exe (PID: 7648)
- 7za.exe (PID: 4064)
- 7zr.exe (PID: 8796)
- meaap.exe (PID: 9120)
- 7za.exe (PID: 5376)
Process checks computer location settings
- FixWhatsApp.v7.4.4.exe (PID: 2028)
- msiexec.exe (PID: 8840)
- MSI617.tmp (PID: 7208)
- gsDRUf.exe (PID: 3272)
Launching a file from a Registry key
- FixWhatsApp.v7.4.4.exe (PID: 2028)
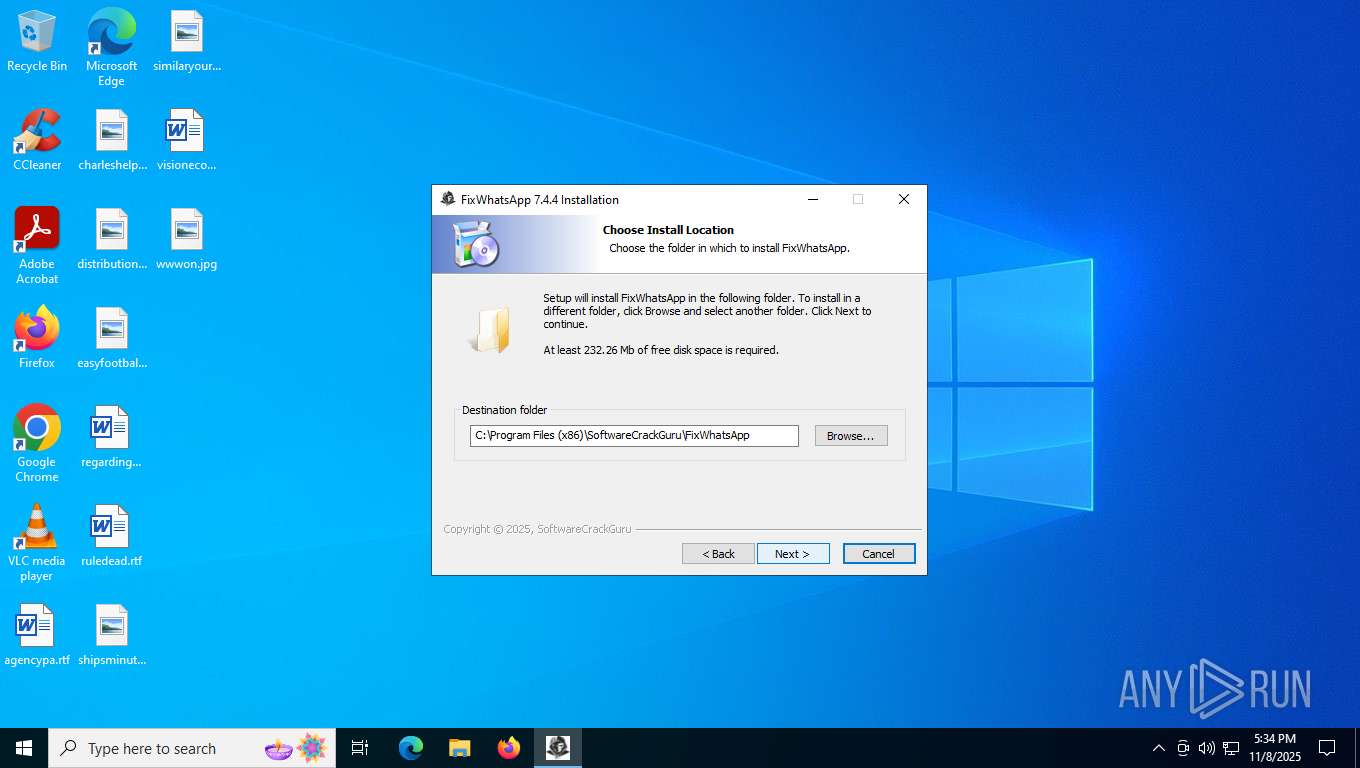
Creates files in the program directory
- FixWhatsApp_V7.4.4.exe (PID: 1664)
- 7za.exe (PID: 4064)
- dcagentregister.exe (PID: 5304)
- cmd.exe (PID: 1196)
- dcstatusutil.exe (PID: 7688)
- dcagentservice.exe (PID: 7964)
- CRU_Reporter.exe (PID: 5376)
- dcconfig.exe (PID: 3364)
- dcusbsummary.exe (PID: 4792)
- dcusb64.exe (PID: 2616)
- dcstatusutil.exe (PID: 7944)
- dcondemand.exe (PID: 6716)
- dcinventory.exe (PID: 7772)
- dcswmeter.exe (PID: 8048)
- dcnacprocess.exe (PID: 5456)
- dcinventory.exe (PID: 7776)
- 7zr.exe (PID: 8796)
- DCProcessMonitor.exe (PID: 2328)
- dcconfig.exe (PID: 3500)
- 7za.exe (PID: 7672)
- meaap.exe (PID: 9120)
- meaaphelper.exe (PID: 3420)
- 7za.exe (PID: 2436)
- 7za.exe (PID: 5376)
- meaaphelper.exe (PID: 6836)
- bmagent.exe (PID: 8332)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7648)
Reads the machine GUID from the registry
- FixWhatsApp.exe (PID: 9052)
- dcagentregister.exe (PID: 5304)
- dcstatusutil.exe (PID: 7688)
- dcondemand.exe (PID: 6716)
- dcconfig.exe (PID: 3364)
- dcinventory.exe (PID: 7772)
- dcstatusutil.exe (PID: 7944)
- EdgeWebView2.exe (PID: 8372)
- dcinventory.exe (PID: 7776)
- dcagentservice.exe (PID: 7964)
- dcconfig.exe (PID: 3500)
- meaap.exe (PID: 9120)
- bmagent.exe (PID: 8332)
Creates a software uninstall entry
- FixWhatsApp_V7.4.4.exe (PID: 1664)
- msiexec.exe (PID: 7648)
- dcconfig.exe (PID: 3500)
Reads the software policy settings
- FixWhatsApp.exe (PID: 9052)
- dcagentregister.exe (PID: 5304)
- dcstatusutil.exe (PID: 7688)
- slui.exe (PID: 6108)
- dcstatusutil.exe (PID: 7944)
- dcondemand.exe (PID: 6716)
- dcconfig.exe (PID: 3364)
- dcinventory.exe (PID: 7772)
- EdgeWebView2.exe (PID: 8372)
- dcconfig.exe (PID: 3500)
- dcinventory.exe (PID: 7776)
- meaap.exe (PID: 9120)
- bmagent.exe (PID: 8332)
Disables trace logs
- FixWhatsApp.exe (PID: 9052)
- netsh.exe (PID: 9008)
Checks proxy server information
- FixWhatsApp.exe (PID: 9052)
- slui.exe (PID: 6108)
- gsDRUf.exe (PID: 3272)
- bmagent.exe (PID: 8332)
The sample compiled with arabic language support
- 7za.exe (PID: 4064)
.NET Reactor protector has been detected
- FixWhatsApp.exe (PID: 9052)
Manages system restore points
- SrTasks.exe (PID: 1564)
Starts application with an unusual extension
- msiexec.exe (PID: 7648)
Launching a file from Task Scheduler
- cmd.exe (PID: 7372)
Drops encrypted JS script (Microsoft Script Encoder)
- EdgeWebView2.exe (PID: 8372)
Reads Windows Product ID
- powershell.exe (PID: 7732)
- powershell.exe (PID: 7748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
369
Monitored processes
190
Malicious processes
3
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | "adb.exe" -s push w.apk /sdcard/ | C:\Program Files (x86)\SoftwareCrackGuru\FixWhatsApp\adb.exe | — | FixWhatsApp.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 580 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 592 | "C:\Users\admin\Desktop\FixWhatsApp.v7.4.4.exe" /cmdloc "HKCU\Software\WhatsApp AiTemp\{EC7F0C48-F369-4A02-8F5C-E6BDE792372D}" | C:\Users\admin\Desktop\FixWhatsApp.v7.4.4.exe | — | explorer.exe | |||||||||||
User: admin Company: SoftwareCrackGuru Integrity Level: MEDIUM Description: Fix WhatsApp 7.4.4 installation Exit code: 3221226540 Version: 7.4.4 Modules
| |||||||||||||||
| 660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 7za.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 688 | "C:\Program Files (x86)\EdgeWebView\UEMS_Agent\bin\7za.exe" x -y "C:\Program Files (x86)\EdgeWebView\UEMS_Agent\temp\BitLockerMgmt.zip" bin\dccomponentregister.dll | C:\Program Files (x86)\EdgeWebView\UEMS_Agent\bin\7za.exe | — | meaaphelper.exe | |||||||||||
User: SYSTEM Company: Igor Pavlov Integrity Level: SYSTEM Description: 7-Zip Standalone Console Exit code: 0 Version: 23.01 Modules
| |||||||||||||||
| 692 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | meaaphelper.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 744 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 752 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | dcinventory.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 828 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 7zr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4420,i,17786576647853139069,12072968081933764025,262144 --variations-seed-version --mojo-platform-channel-handle=4432 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
90 070
Read events
88 050
Write events
1 801
Delete events
219
Modification events
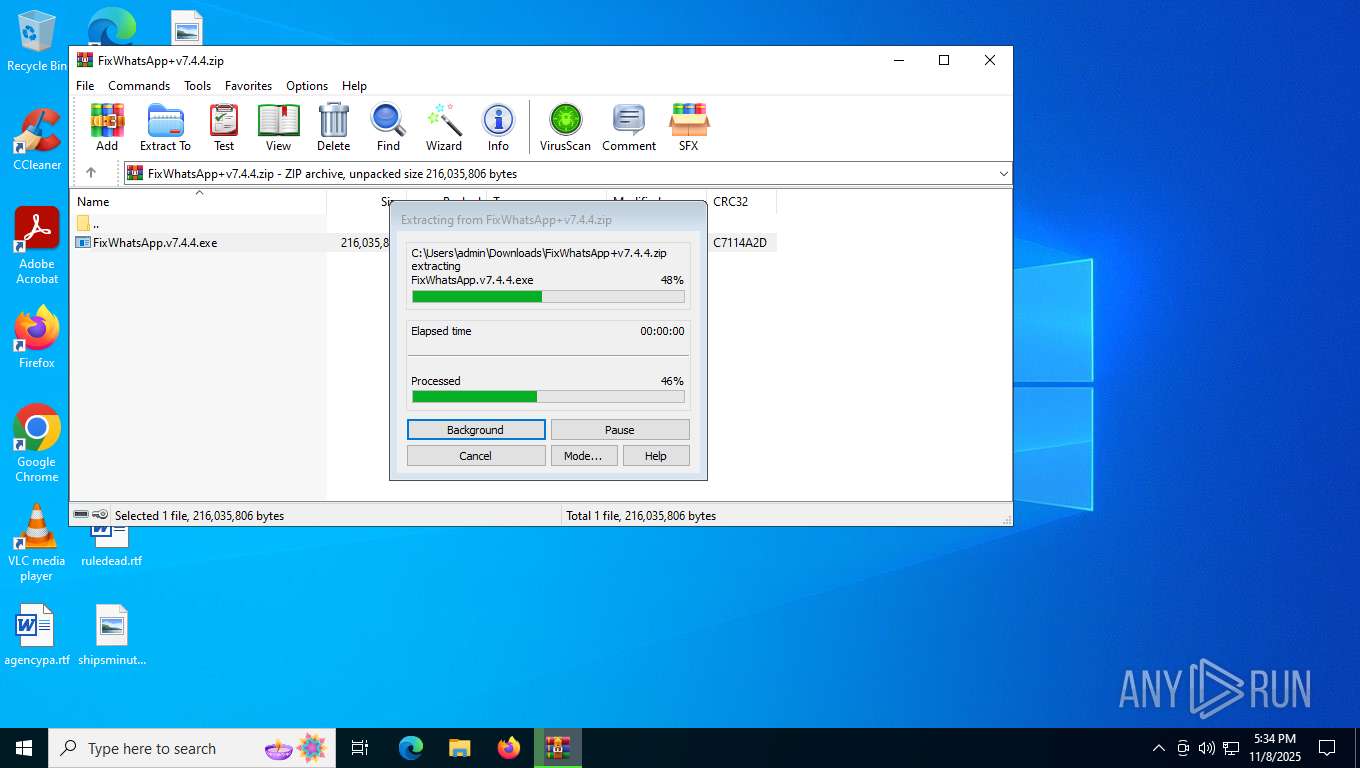
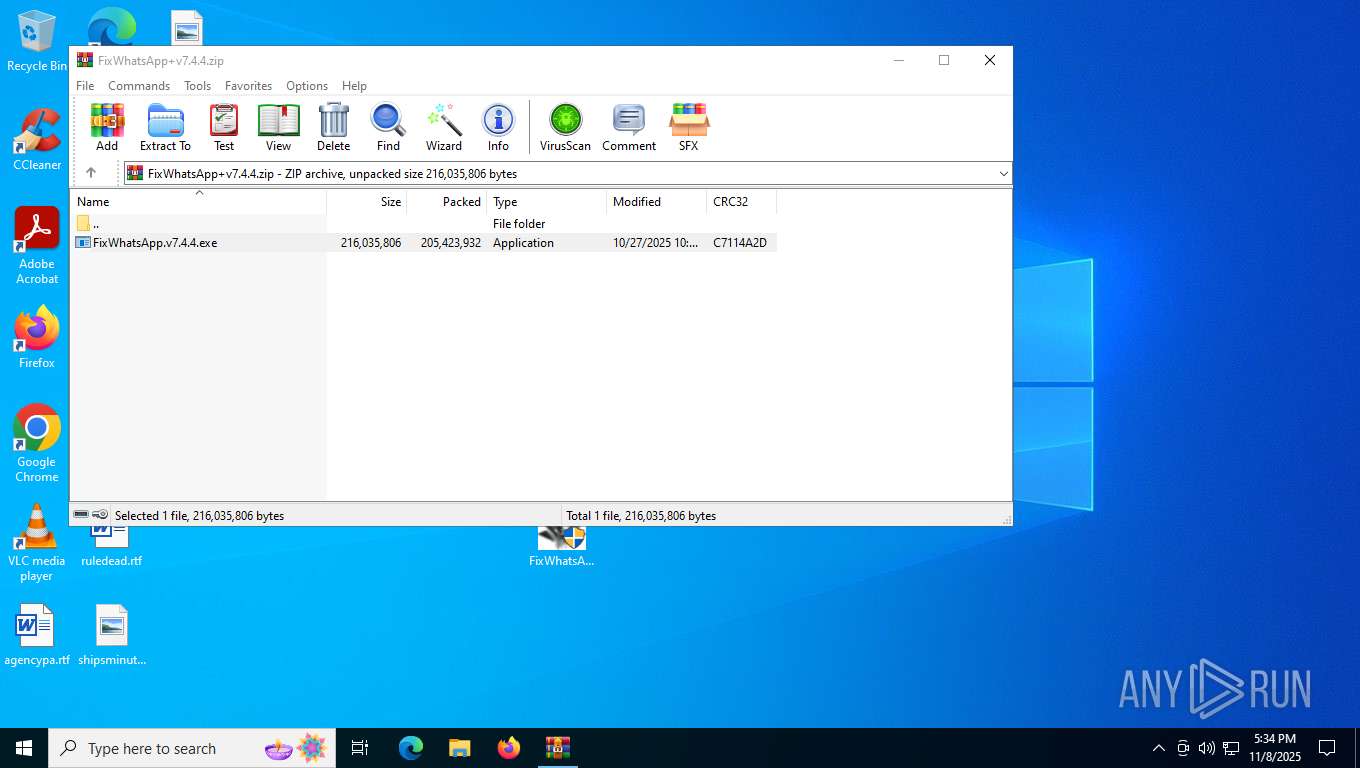
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\FixWhatsApp+v7.4.4.zip | |||
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (3028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
366
Suspicious files
770
Text files
501
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1621a6.TMP | — | |
MD5:— | SHA256:— | |||
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1621b5.TMP | — | |
MD5:— | SHA256:— | |||
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1621b5.TMP | — | |
MD5:— | SHA256:— | |||
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1621b5.TMP | — | |
MD5:— | SHA256:— | |||
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1621b5.TMP | — | |
MD5:— | SHA256:— | |||
| 7492 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1621f4.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
334
DNS requests
199
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7832 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:wUgGJGZfCT41RHybDV6JoFV7S9F453TewBB-CvTtsLM&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
5732 | svchost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
9168 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | NL | binary | 813 b | whitelisted |
5596 | MoUsoCoreWorker.exe | GET | 200 | 95.101.35.8:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
9168 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | NL | binary | 814 b | whitelisted |
3272 | gsDRUf.exe | GET | — | 3.229.117.57:799 | http://ddos.dnsnb8.net:799/cj//k1.rar | US | — | — | malicious |
9168 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | NL | binary | 401 b | whitelisted |
3272 | gsDRUf.exe | GET | — | 3.229.117.57:799 | http://ddos.dnsnb8.net:799/cj//k2.rar | US | — | — | malicious |
8304 | svchost.exe | HEAD | 200 | 2.16.168.202:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ddbf4492-d475-4fe4-bcde-6cbac56f6034?P1=1762967634&P2=404&P3=2&P4=fXoe%2fRFN6JxWGSfvCfjtJgaoBQMDQJOj%2fGppwExGYEFjt7Tp8tPqwovG1FLUxKp%2fL8sIppid1v4Yd0P%2bsk45lg%3d%3d | RU | — | — | whitelisted |
8304 | svchost.exe | GET | 206 | 2.16.168.202:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ddbf4492-d475-4fe4-bcde-6cbac56f6034?P1=1762967634&P2=404&P3=2&P4=fXoe%2fRFN6JxWGSfvCfjtJgaoBQMDQJOj%2fGppwExGYEFjt7Tp8tPqwovG1FLUxKp%2fL8sIppid1v4Yd0P%2bsk45lg%3d%3d | RU | binary | 1.09 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5732 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
224 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7088 | SearchApp.exe | 2.16.204.142:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7832 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7832 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7832 | msedge.exe | 172.66.40.195:443 | androidfilehost.com | CLOUDFLARENET | US | whitelisted |
7832 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
androidfilehost.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
use.typekit.net |
| whitelisted |
use.fontawesome.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7832 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7832 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7832 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7832 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7832 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7832 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7832 | msedge.exe | Misc activity | INFO [ANY.RUN] .cc TLD domain request |
2276 | svchost.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain in DNS Lookup (keyauth .win) |
9052 | FixWhatsApp.exe | Not Suspicious Traffic | INFO [ANY.RUN] Firebase Web App Development Platform (firebaseio .com) |
Process | Message |
|---|---|
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |