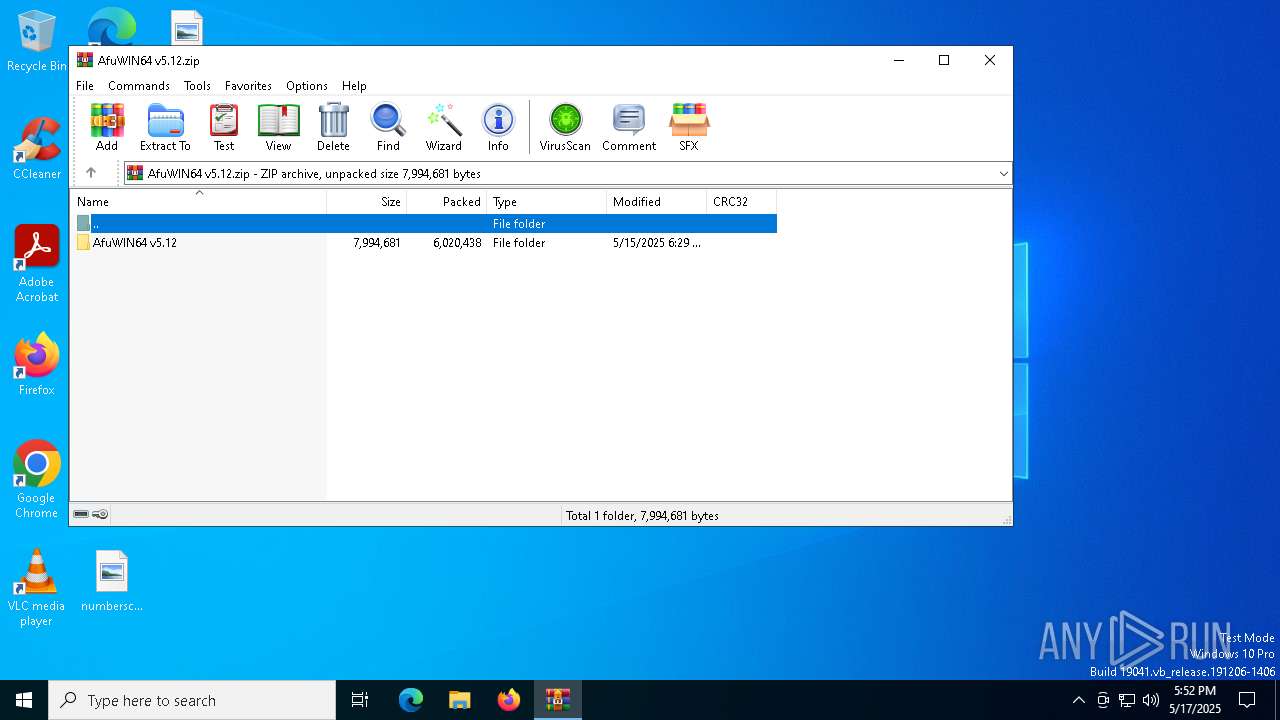
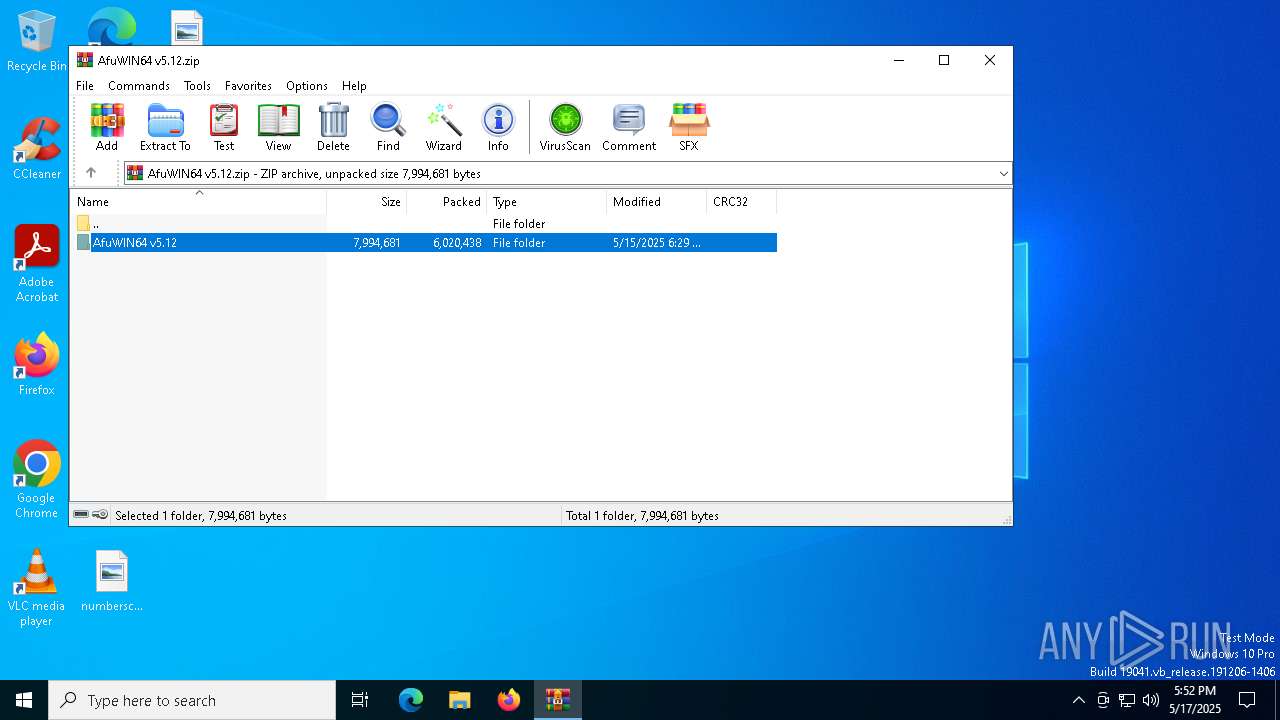
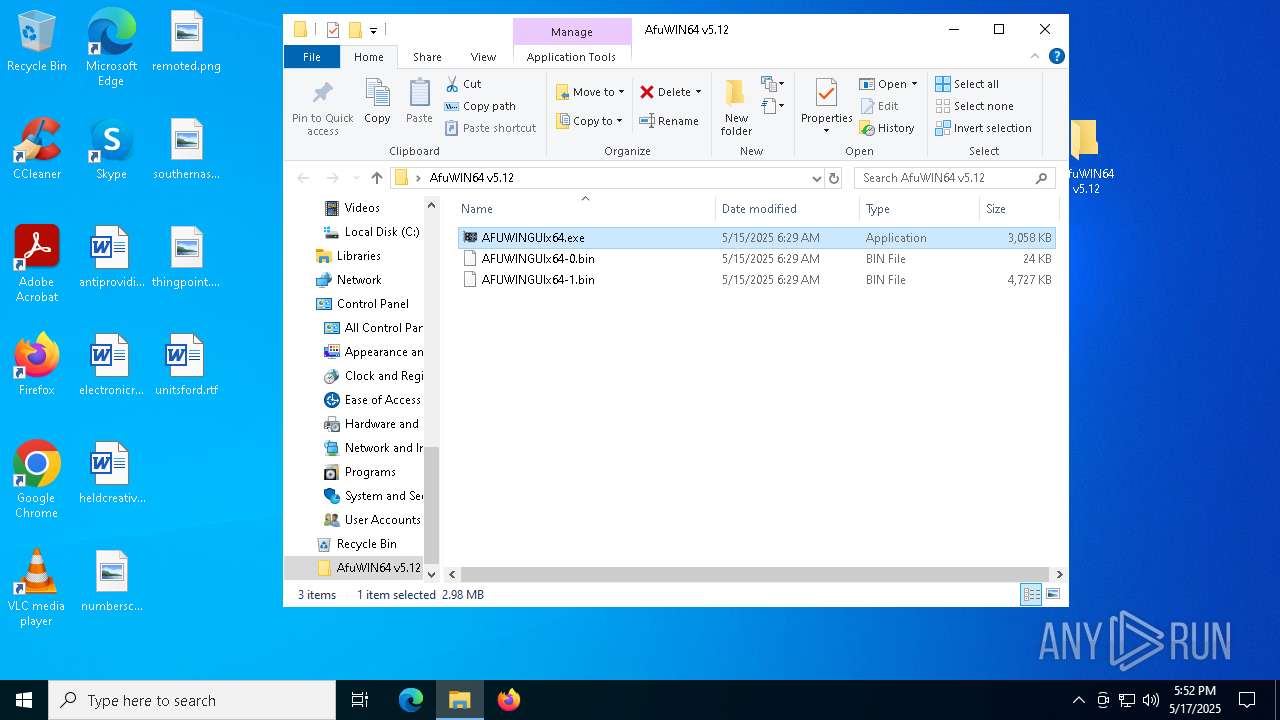
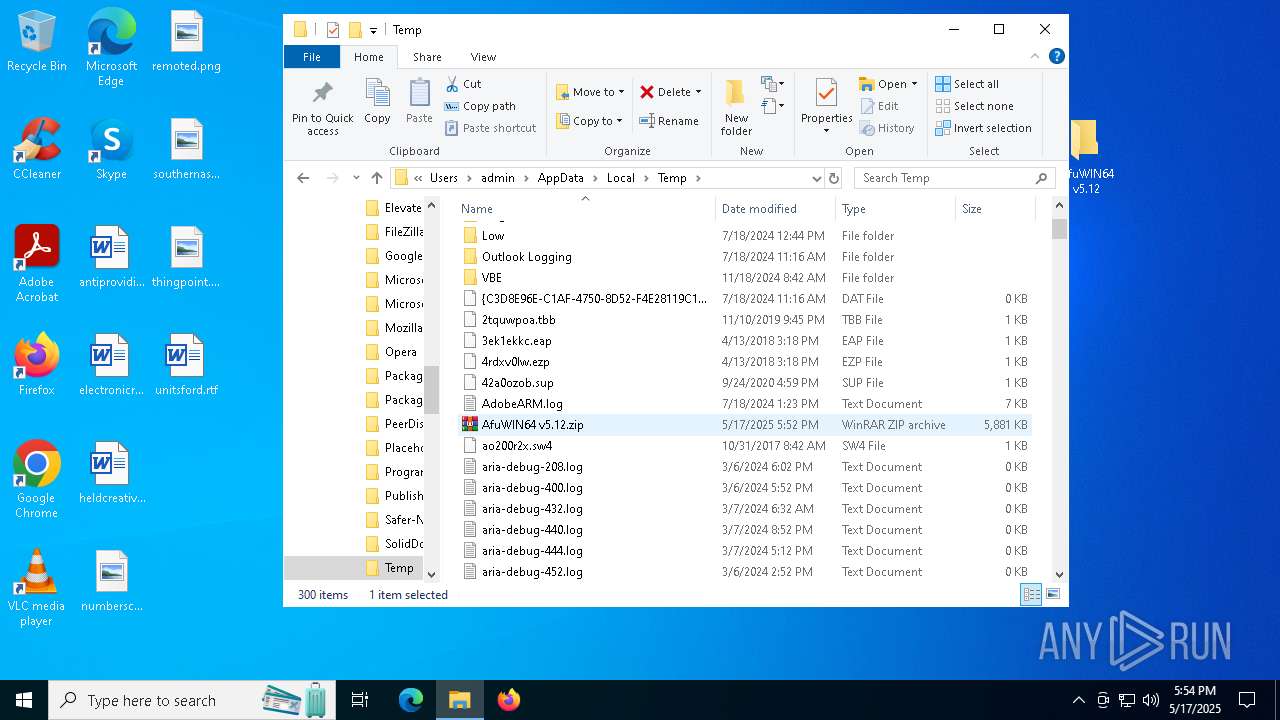
| File name: | AfuWIN64 v5.12.zip |
| Full analysis: | https://app.any.run/tasks/ebf0d497-11ce-4b53-8c3c-eb2f0449d40d |
| Verdict: | Malicious activity |
| Threats: | HijackLoader is a modular malware acting as a vehicle for distributing different types of malicious software on compromised systems. It gained prominence during the summer of 2023 and has since been used in multiple attacks against organizations from various sectors, including hospitality businesses. |
| Analysis date: | May 17, 2025, 17:52:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 5DBE6CF2F221DB0F77220A45258E4EC0 |
| SHA1: | D7796E66AD11A61EE2BA1017E27945B1C6BC9189 |
| SHA256: | 02514E445A8E6177D853203748CDD0F0A55835FE4E00F7EAB40BFD4EDDE23E51 |
| SSDEEP: | 98304:i7OMgzkPwb6njsfiJLOGYThI+0ShydC9A0aAA05v/Drs0NaCEZWYsikWzU0/AjYB:9ULnYXXa |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 5408)
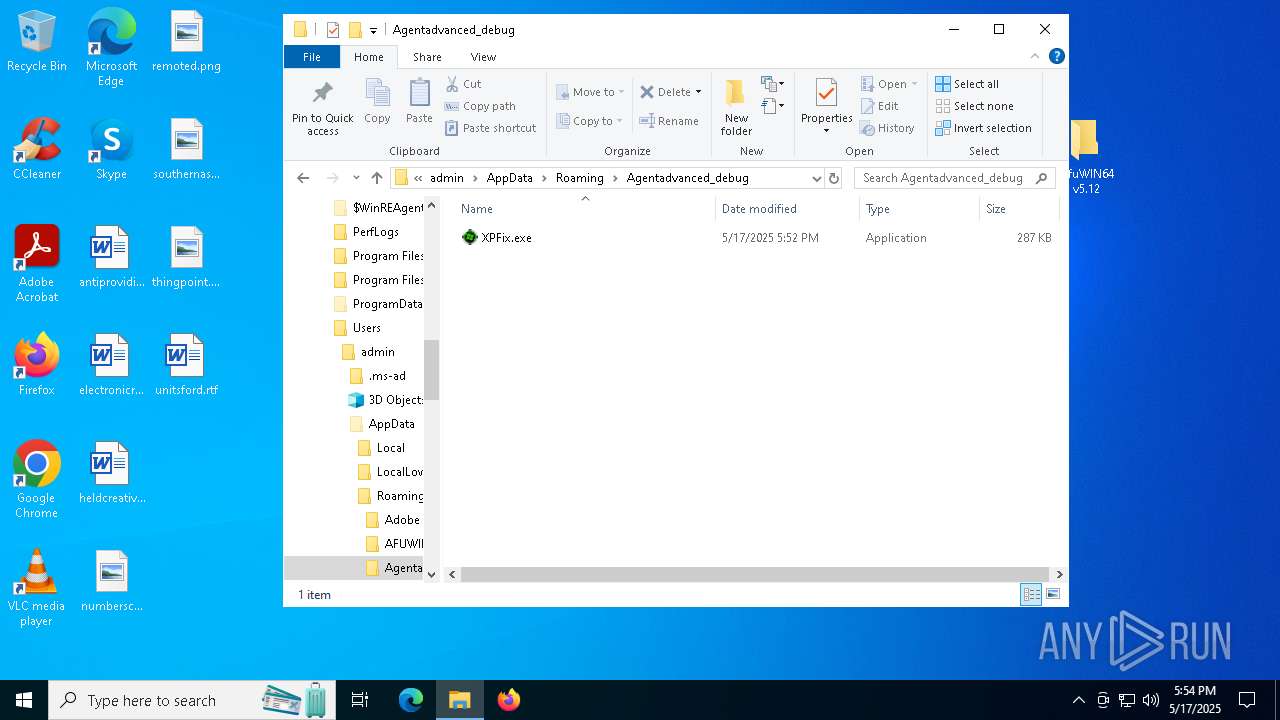
Executing a file with an untrusted certificate
- InspectorConfig.exe (PID: 7904)
- XPFix.exe (PID: 7452)
- InspectorConfig.exe (PID: 7996)
REMCOS has been detected (YARA)
- ParallelFab.exe (PID: 1348)
HIJACKLOADER has been detected (YARA)
- InspectorConfig.exe (PID: 7996)
SUSPICIOUS
Reads security settings of Internet Explorer
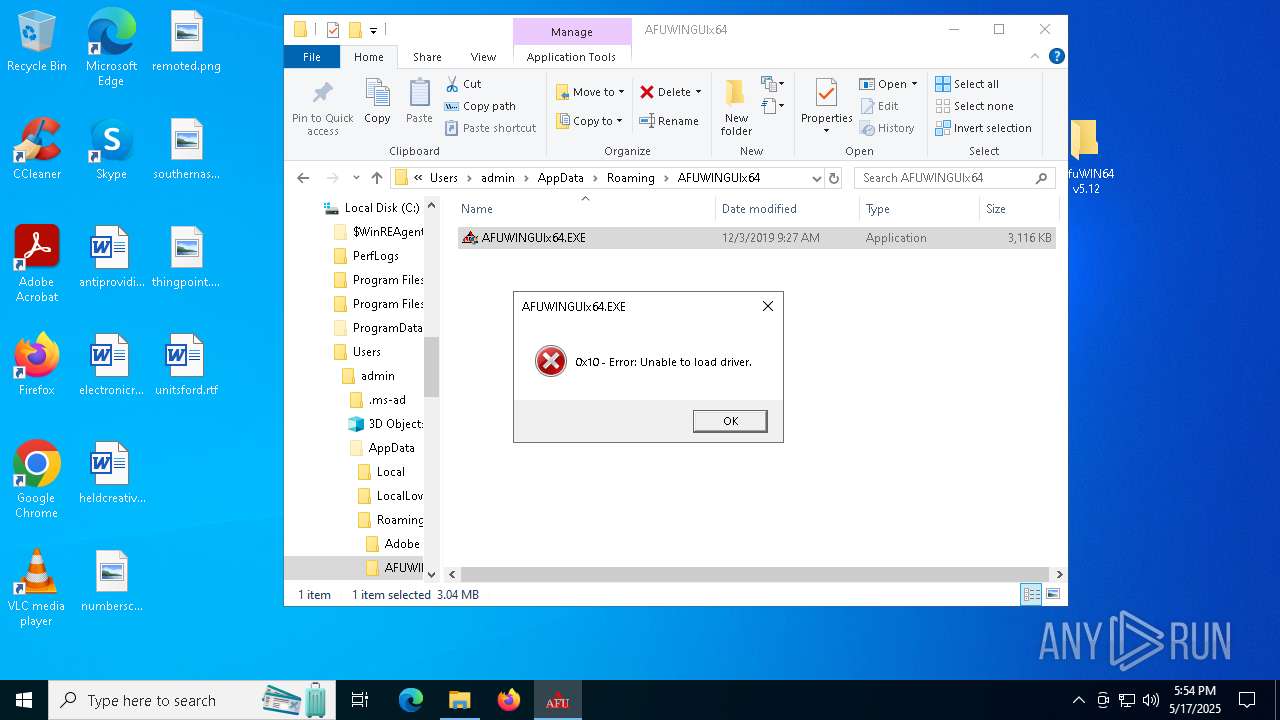
- AFUWINGUIx64.exe (PID: 7732)
- AFUWINGUIx64.exe (PID: 7816)
Reads the Windows owner or organization settings
- AFUWINGUIx64.exe (PID: 7816)
- AFUWINGUIx64.exe (PID: 7856)
Application launched itself
- AFUWINGUIx64.exe (PID: 7732)
- AFUWINGUIx64.exe (PID: 7816)
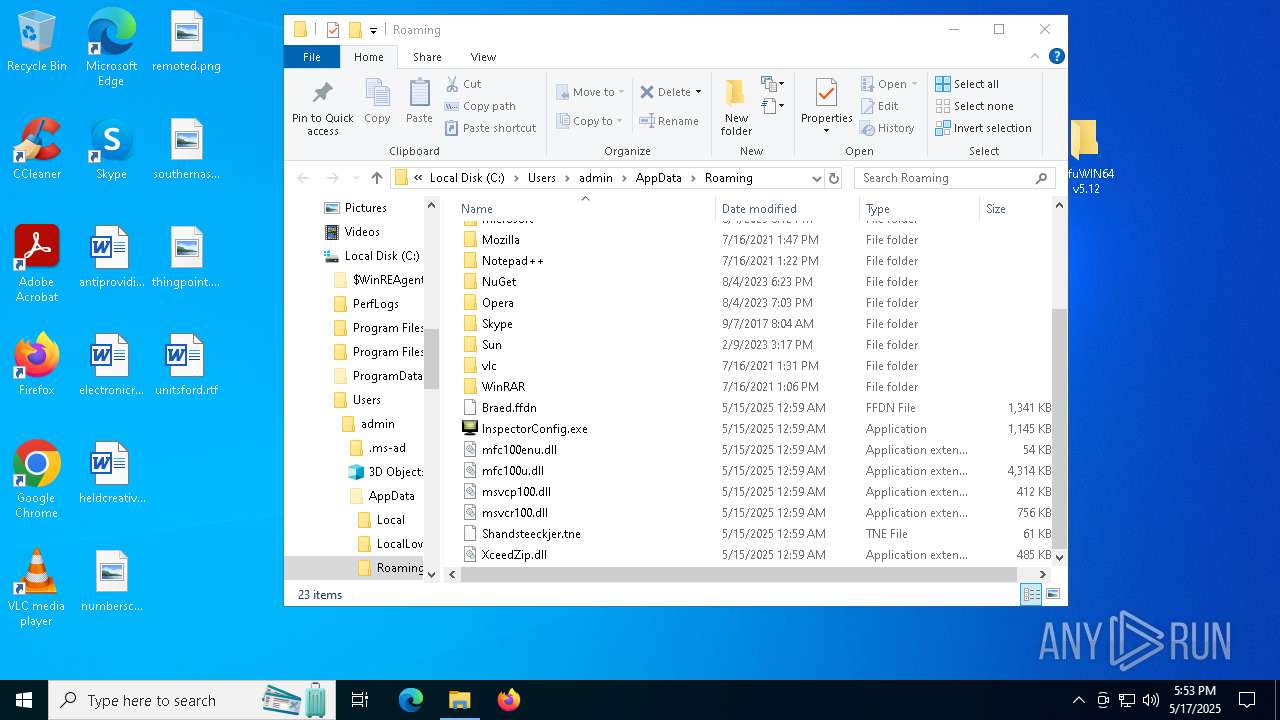
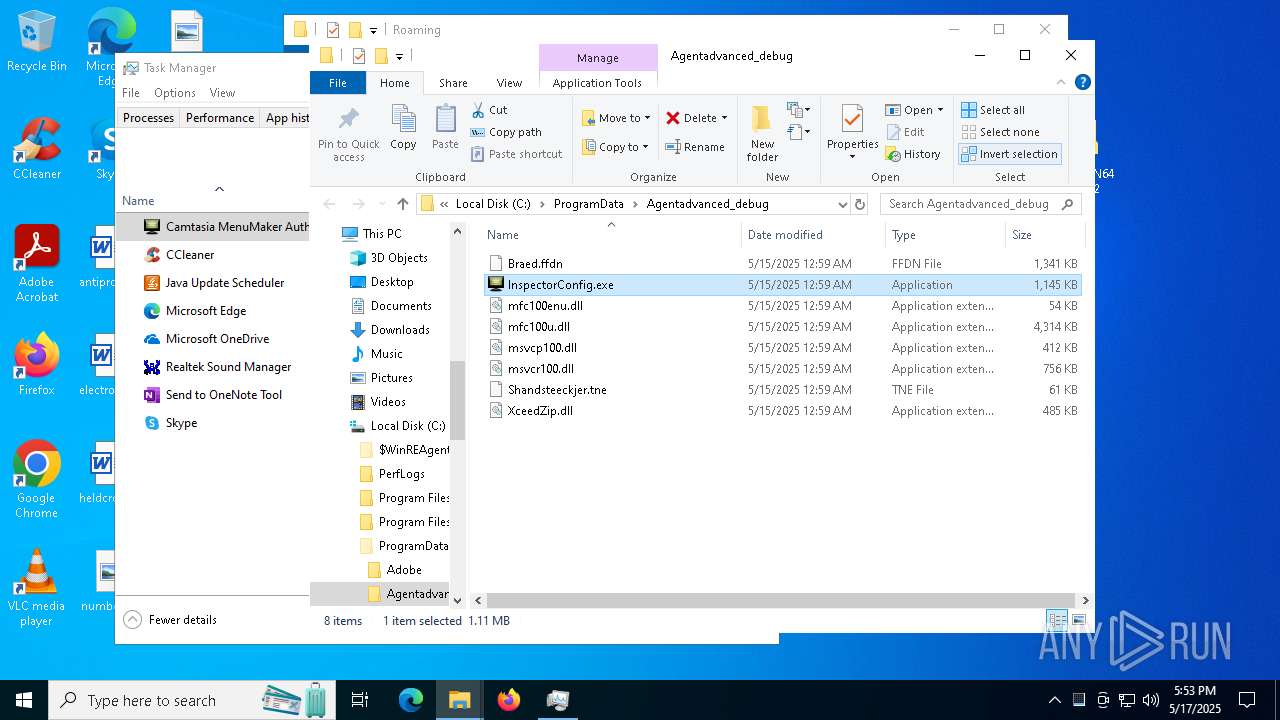
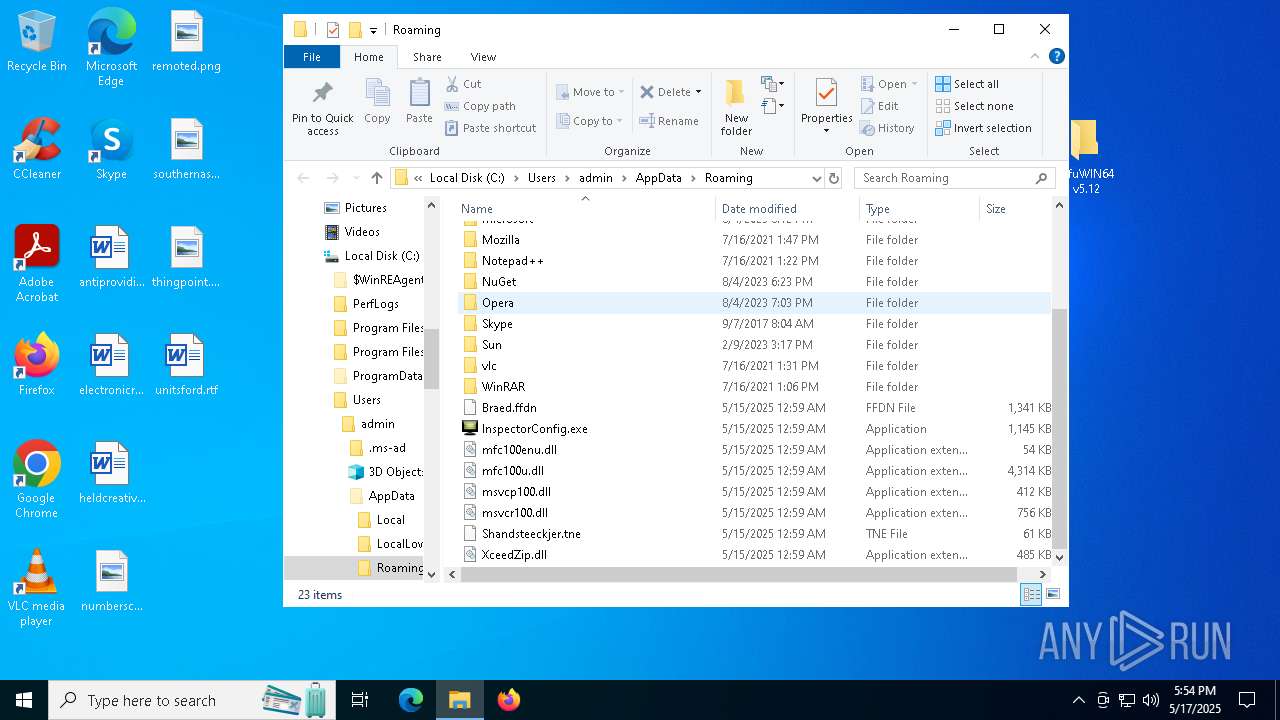
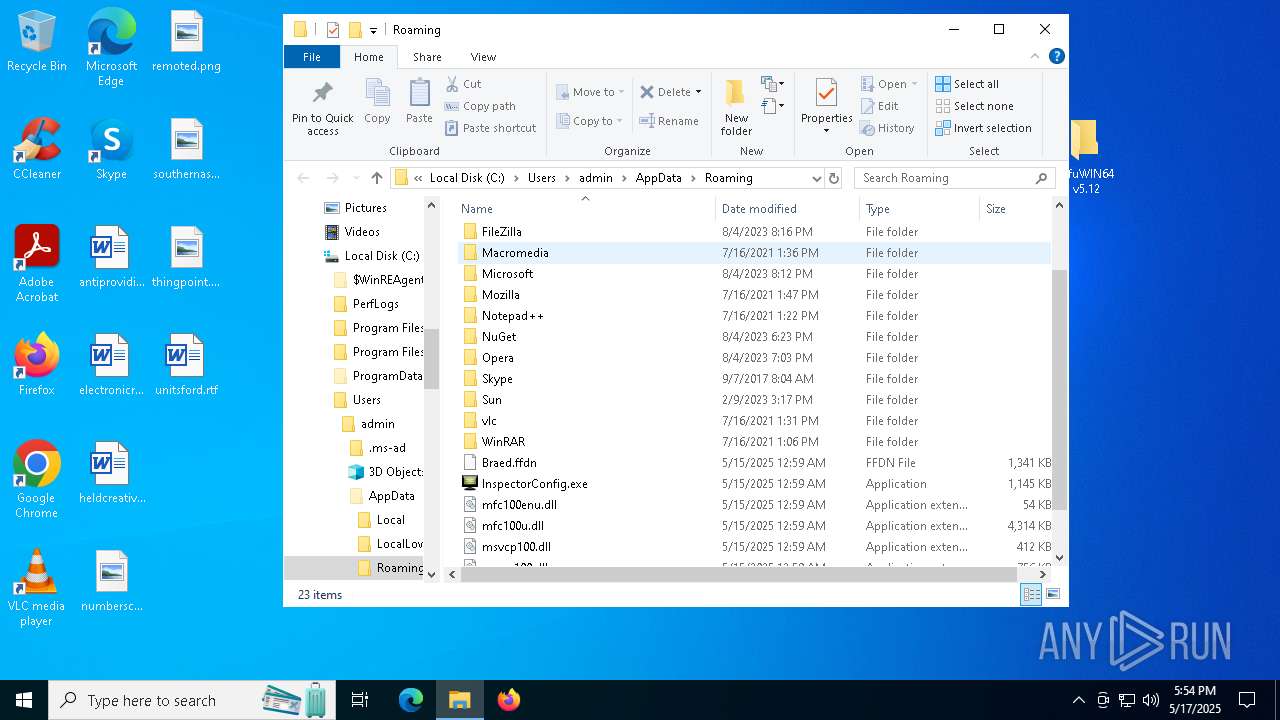
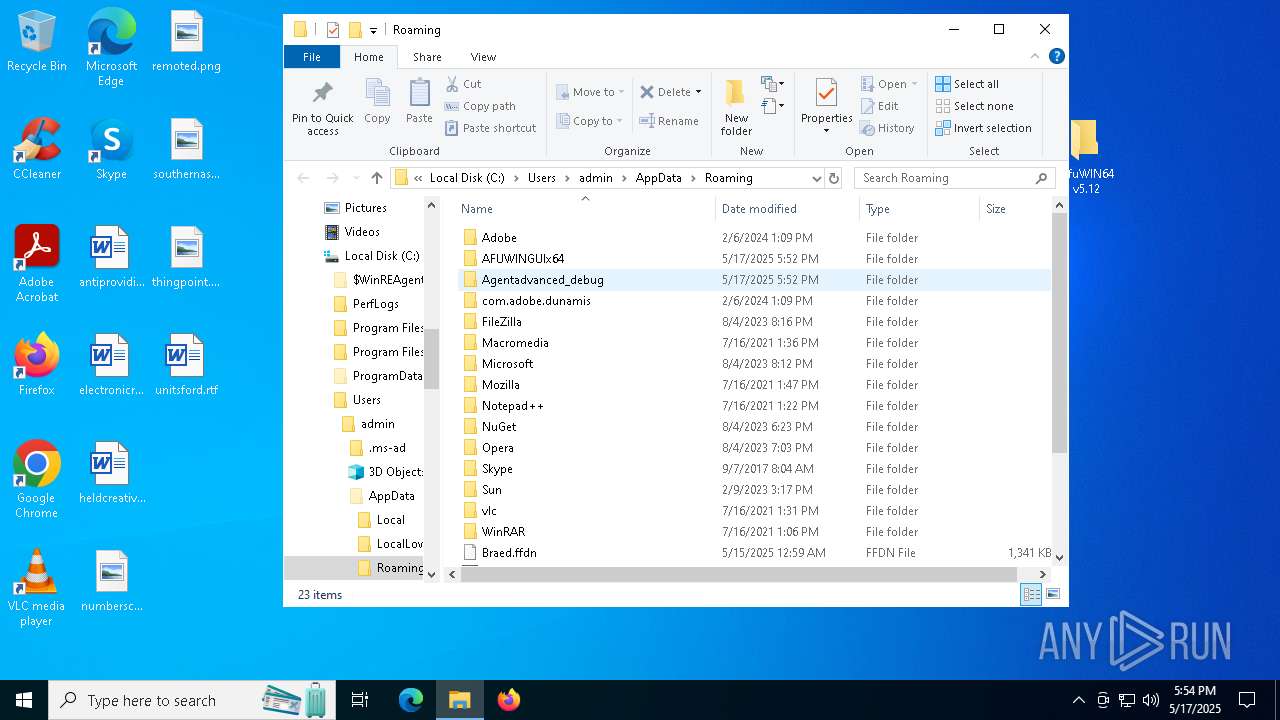
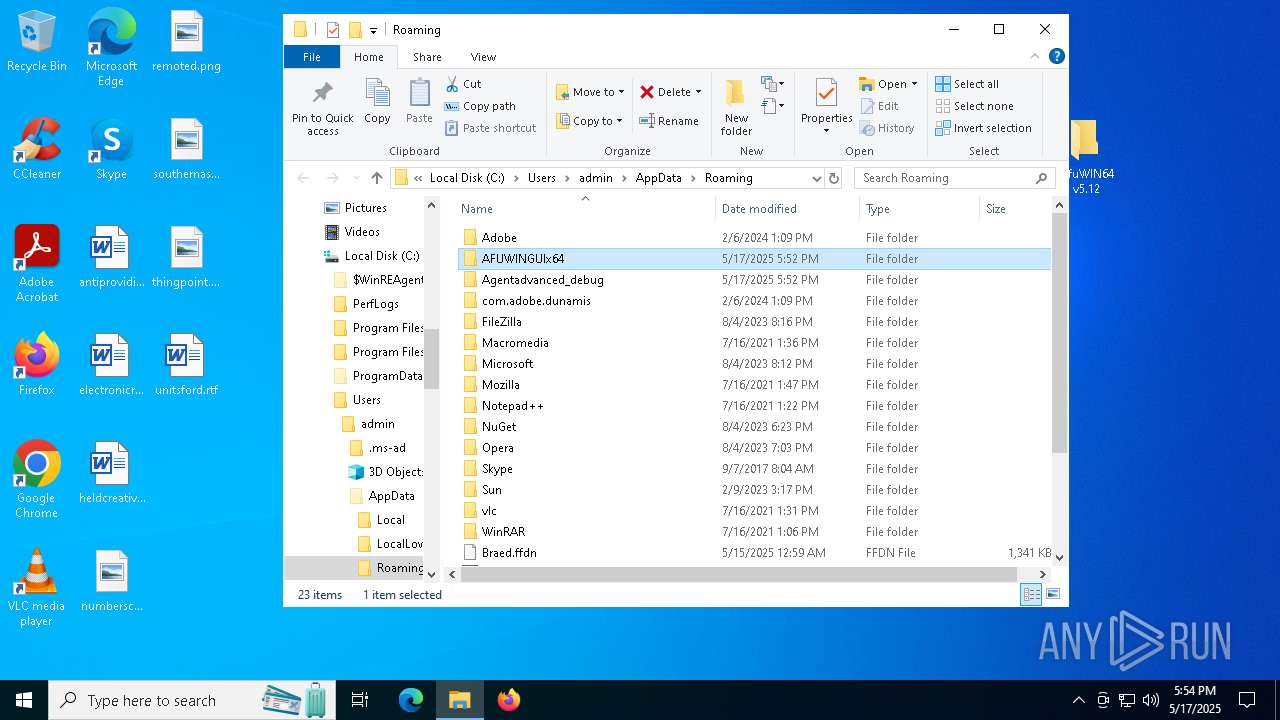
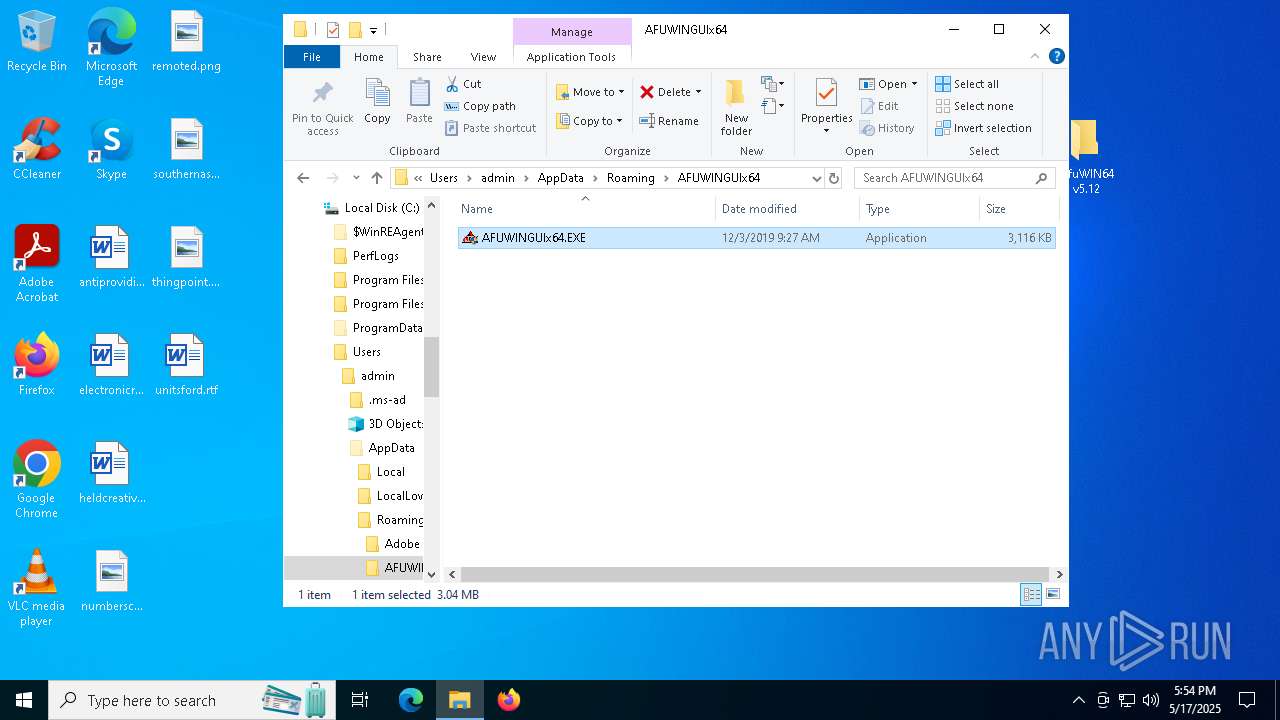
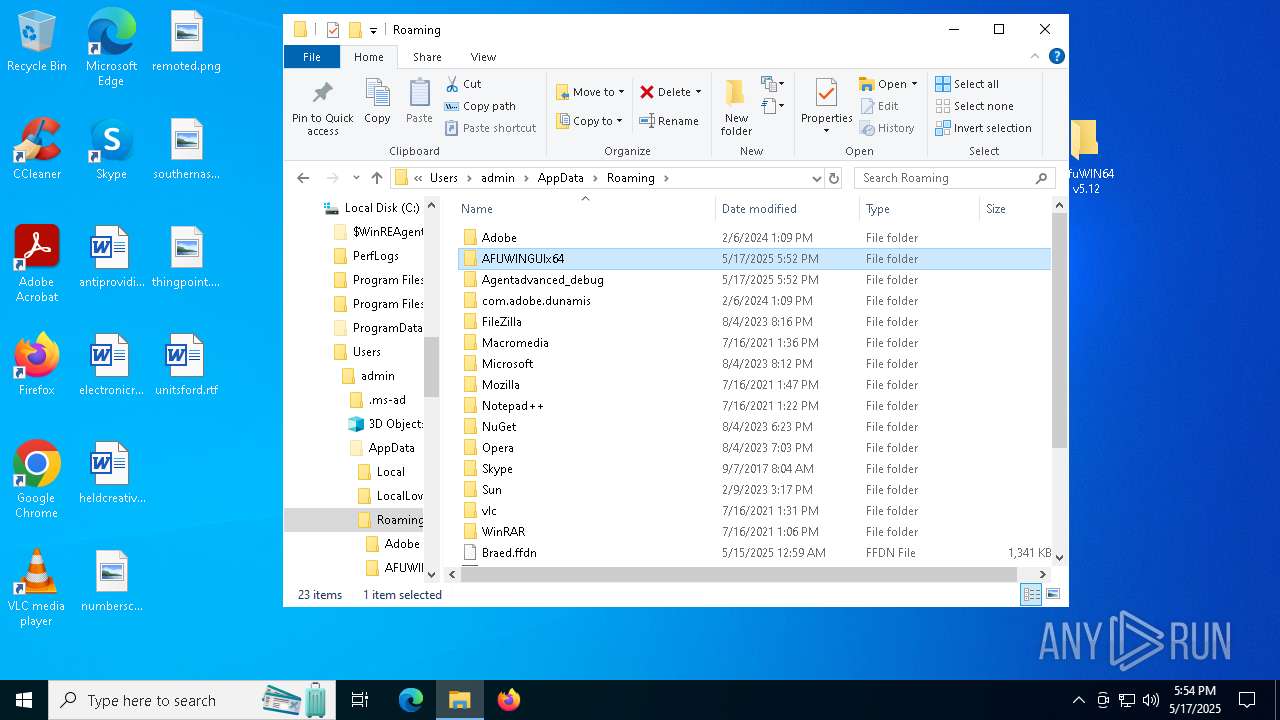
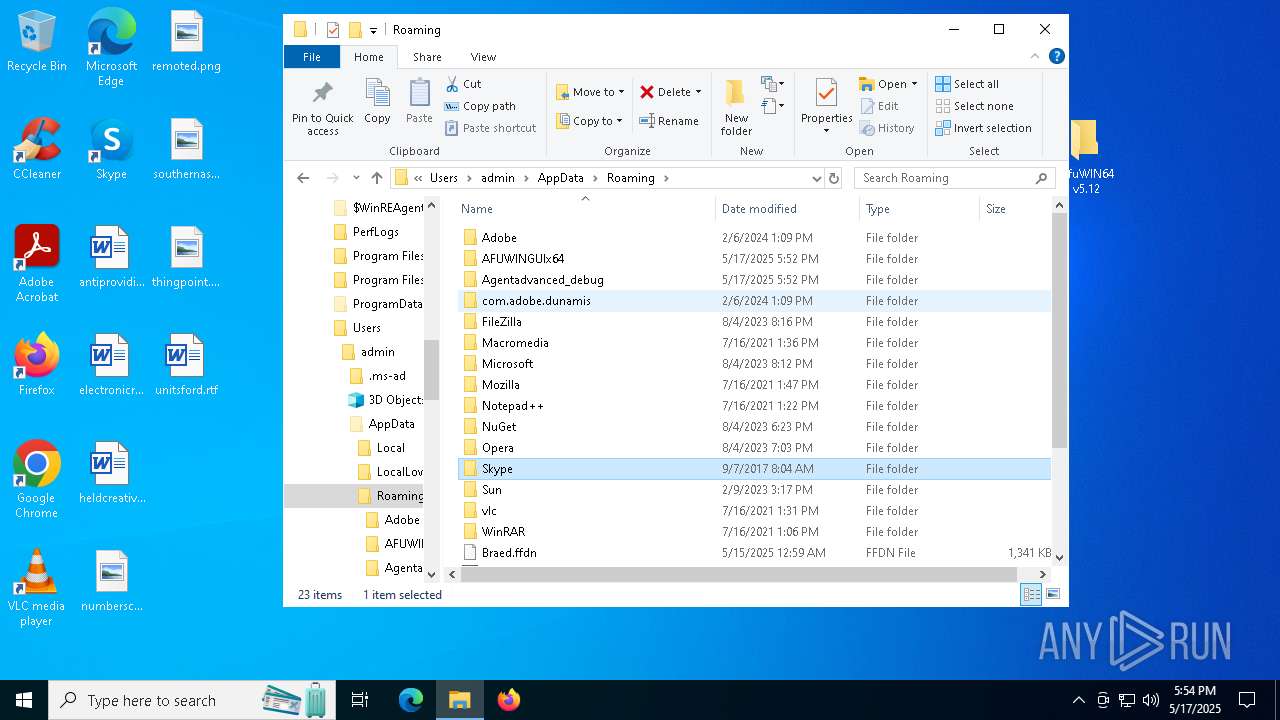
Executable content was dropped or overwritten
- AFUWINGUIx64.exe (PID: 7816)
- AFUWINGUIx64.exe (PID: 7856)
- InspectorConfig.exe (PID: 7904)
- InspectorConfig.exe (PID: 7996)
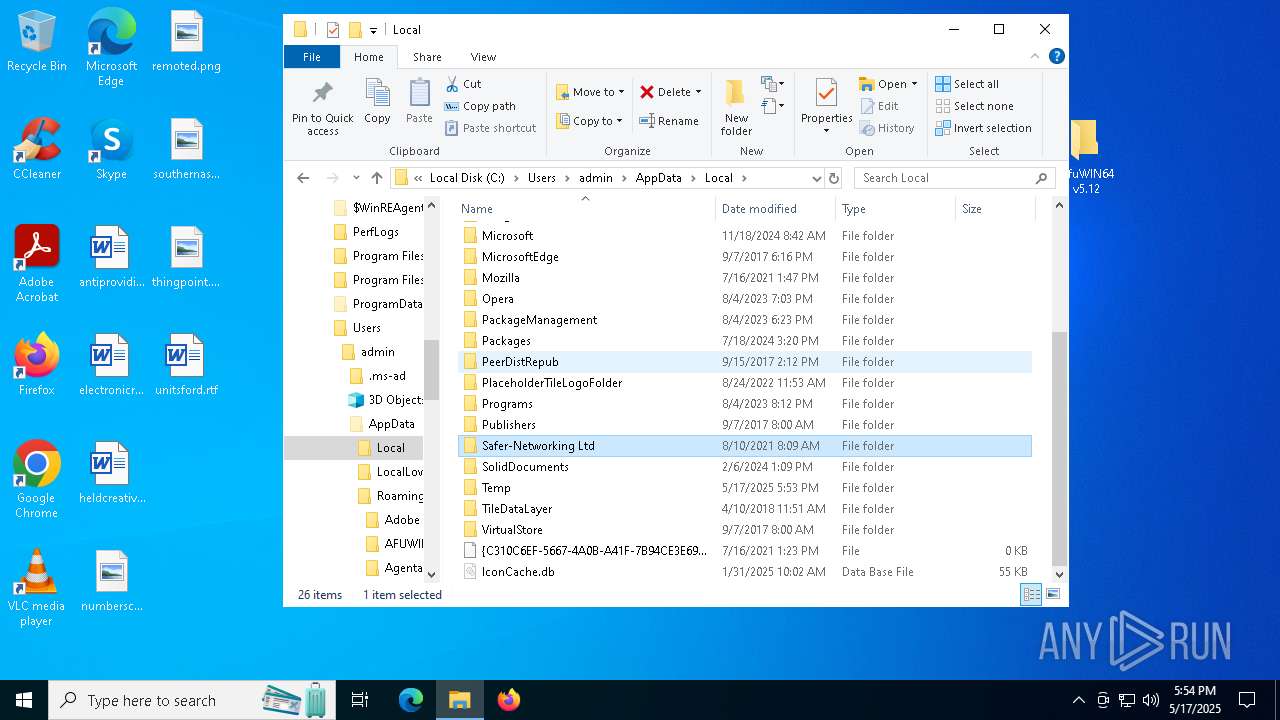
Process drops legitimate windows executable
- AFUWINGUIx64.exe (PID: 7856)
- InspectorConfig.exe (PID: 7904)
The process drops C-runtime libraries
- AFUWINGUIx64.exe (PID: 7856)
- InspectorConfig.exe (PID: 7904)
Starts itself from another location
- InspectorConfig.exe (PID: 7904)
There is functionality for taking screenshot (YARA)
- ParallelFab.exe (PID: 1348)
Connects to unusual port
- ParallelFab.exe (PID: 1348)
INFO
Checks supported languages
- AFUWINGUIx64.exe (PID: 7732)
- AFUWINGUIx64.exe (PID: 7816)
- AFUWINGUIx64.exe (PID: 7856)
- AFUWINGUIx64.EXE (PID: 7896)
- InspectorConfig.exe (PID: 7904)
- ParallelFab.exe (PID: 1348)
- InspectorConfig.exe (PID: 7996)
Reads the computer name
- AFUWINGUIx64.exe (PID: 7732)
- AFUWINGUIx64.exe (PID: 7816)
- AFUWINGUIx64.exe (PID: 7856)
- AFUWINGUIx64.EXE (PID: 7896)
- InspectorConfig.exe (PID: 7904)
- ParallelFab.exe (PID: 1348)
- InspectorConfig.exe (PID: 7996)
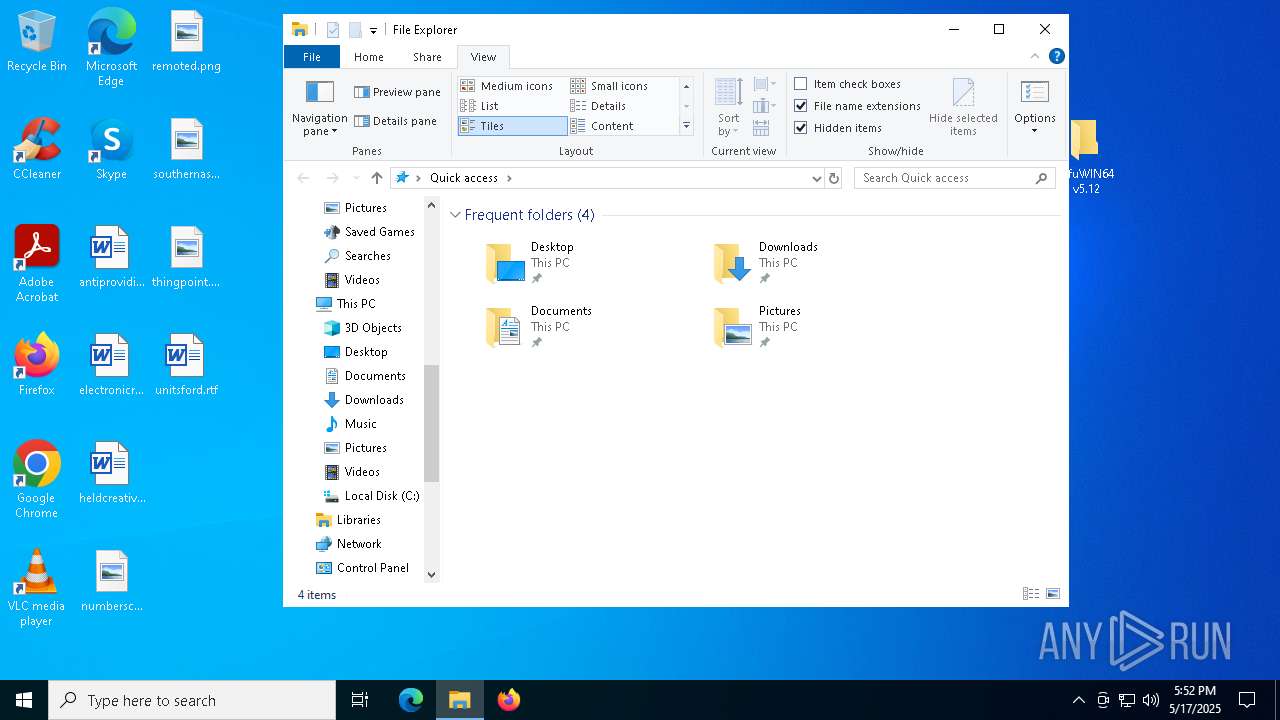
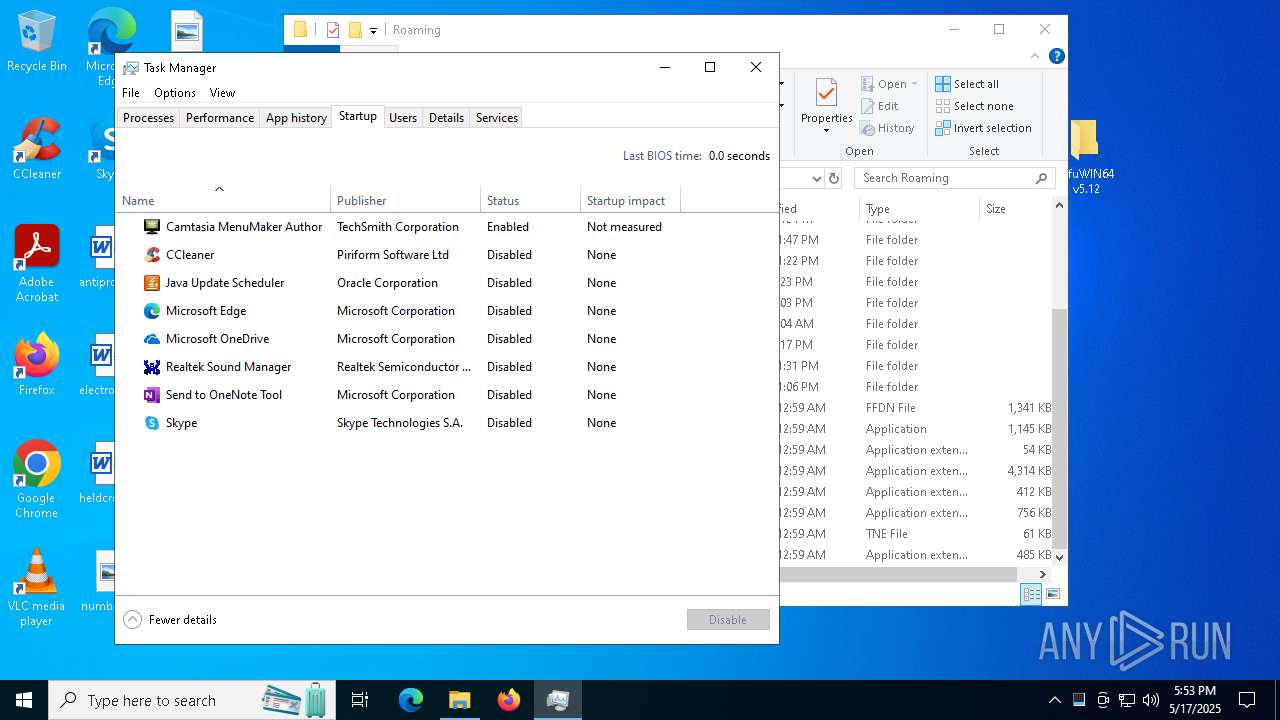
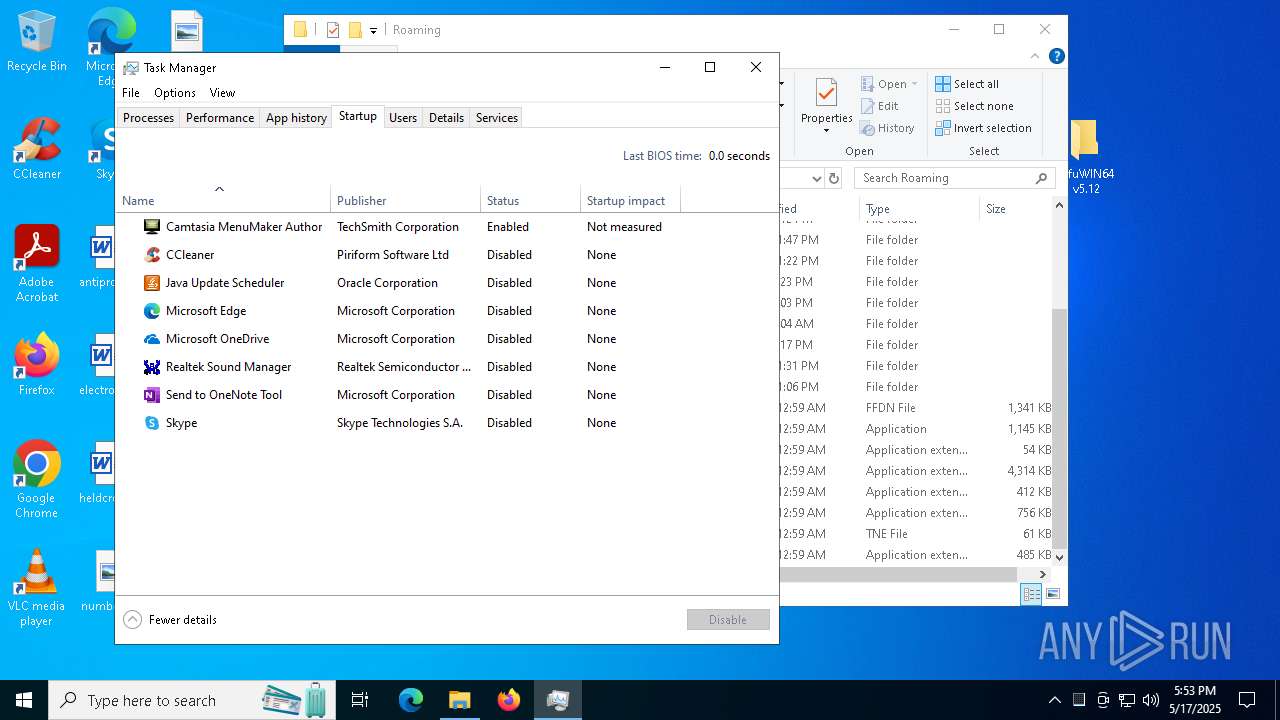
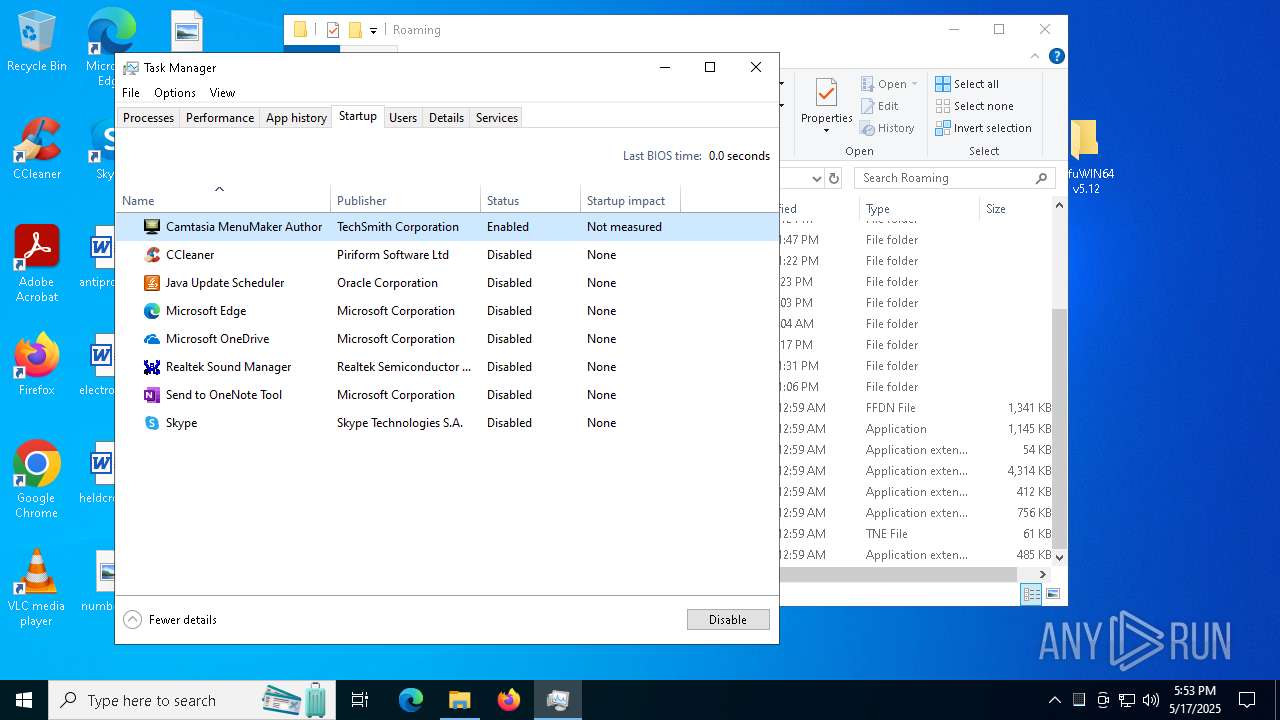
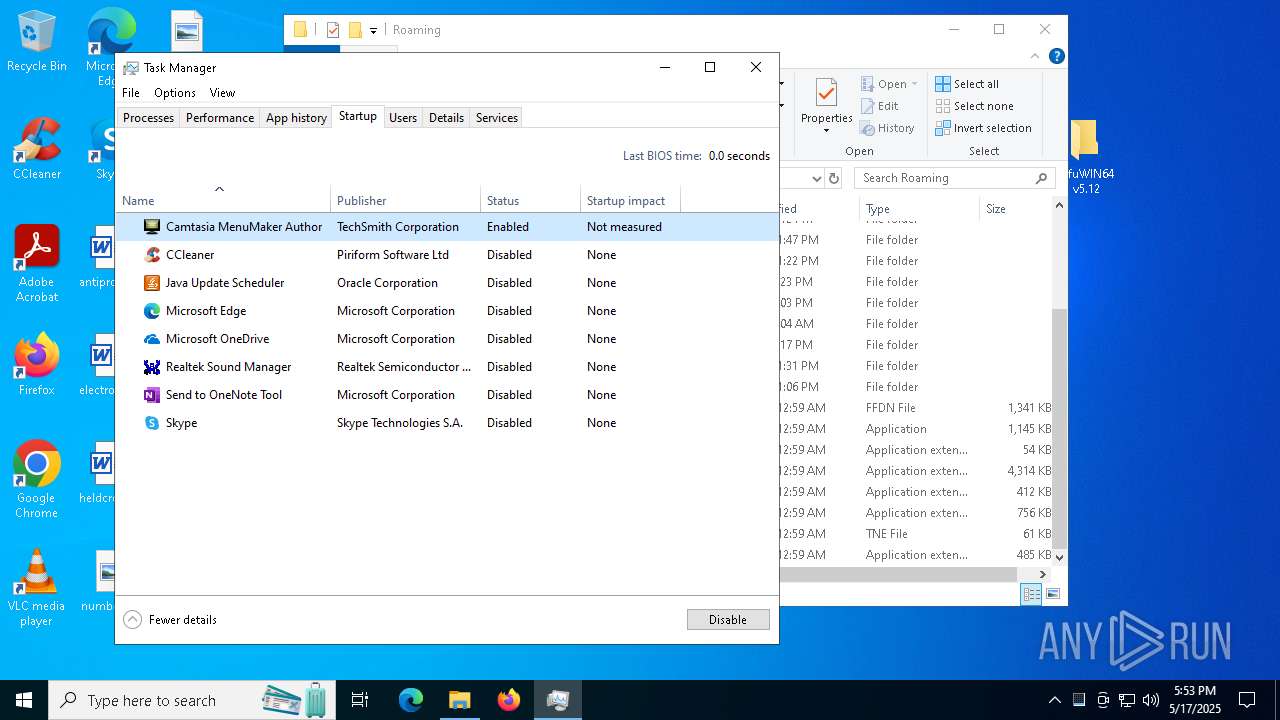
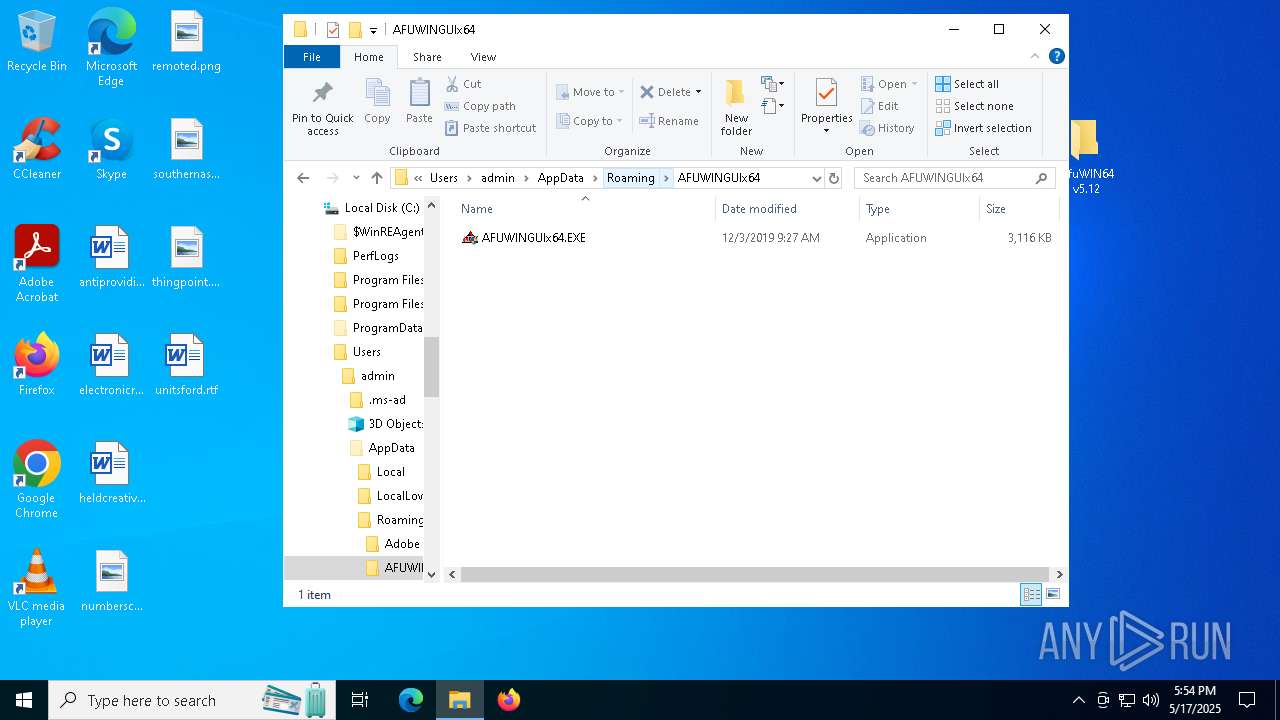
Manual execution by a user
- AFUWINGUIx64.exe (PID: 7732)
- Taskmgr.exe (PID: 7576)
- Taskmgr.exe (PID: 7560)
- AFUWINGUIx64.EXE (PID: 7748)
- AFUWINGUIx64.EXE (PID: 7848)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5408)
Process checks computer location settings
- AFUWINGUIx64.exe (PID: 7732)
- AFUWINGUIx64.exe (PID: 7816)
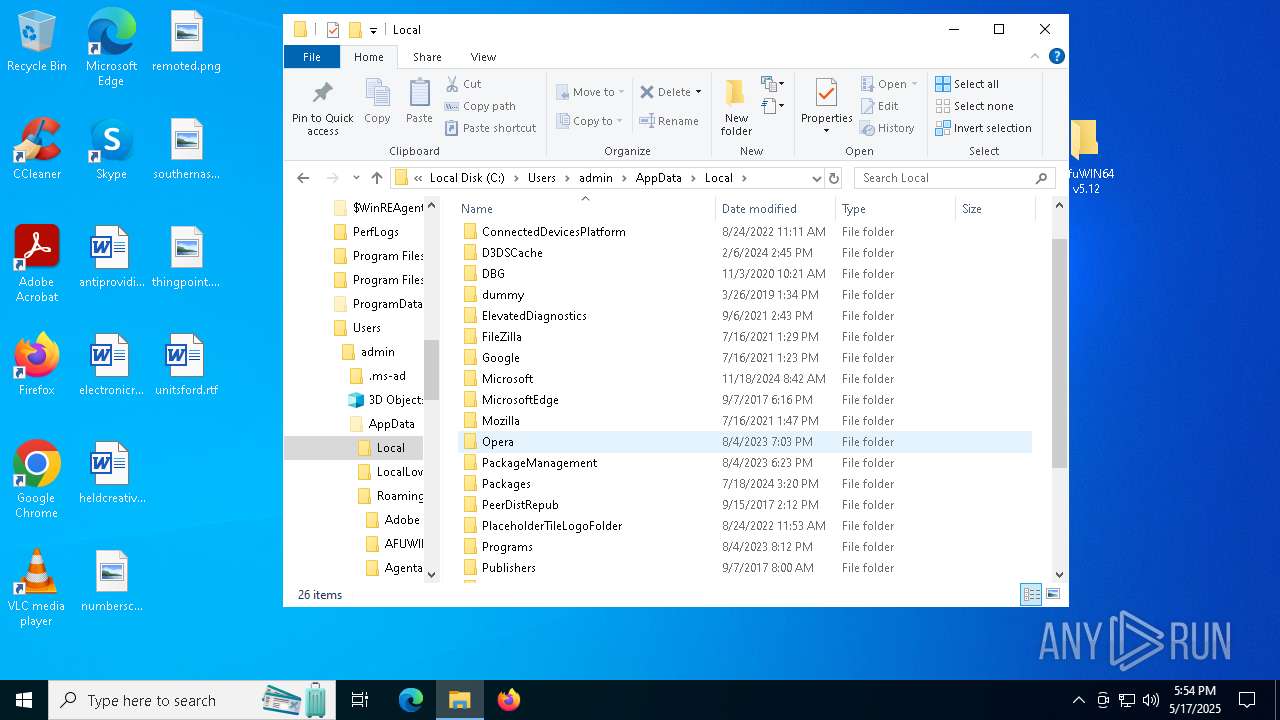
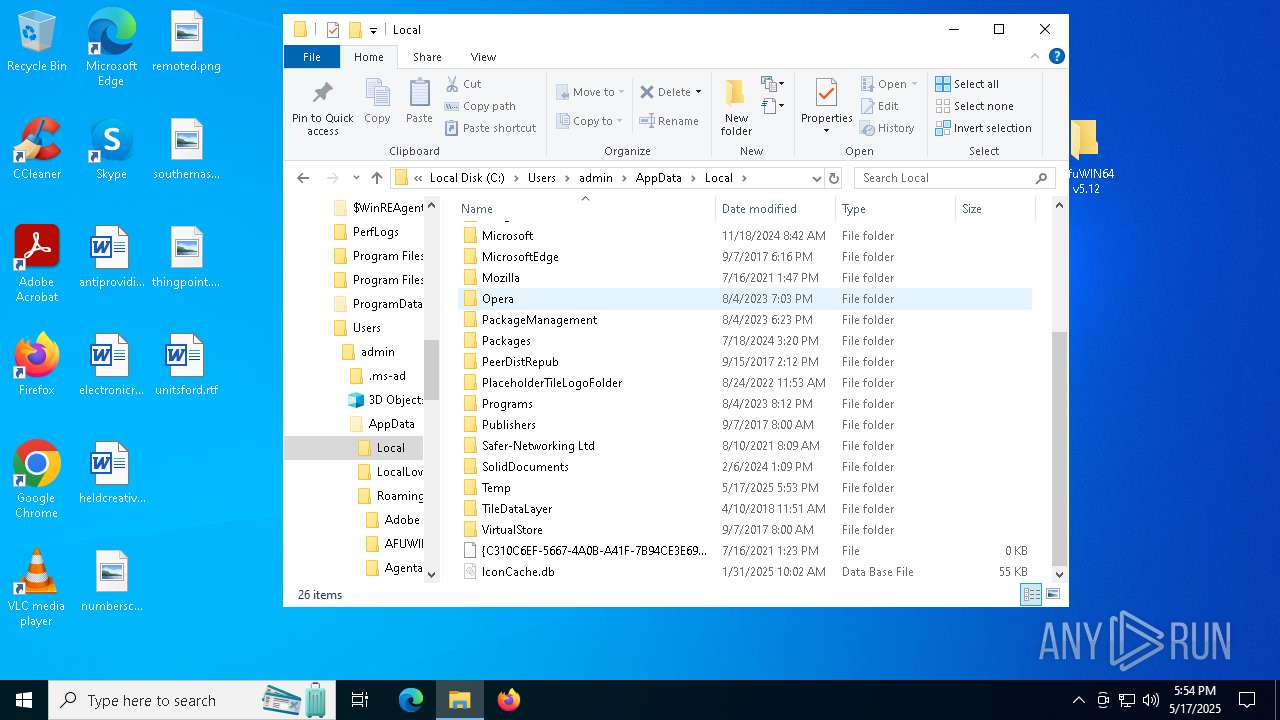
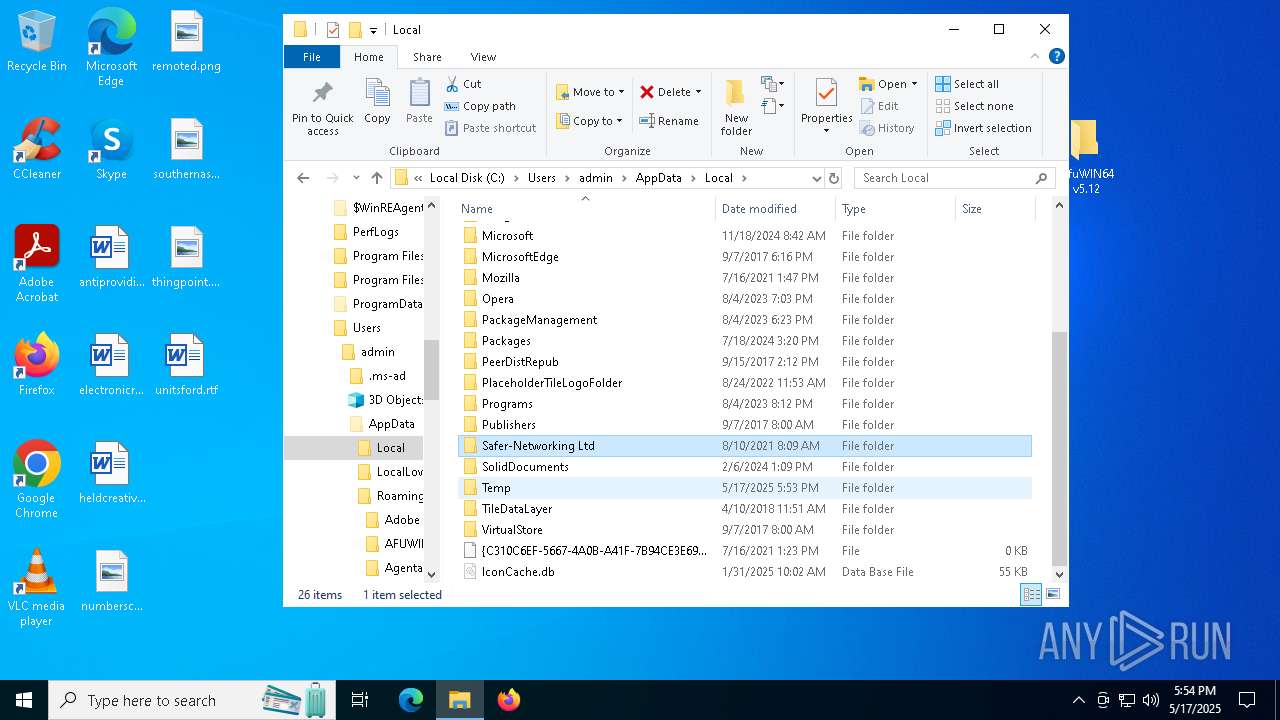
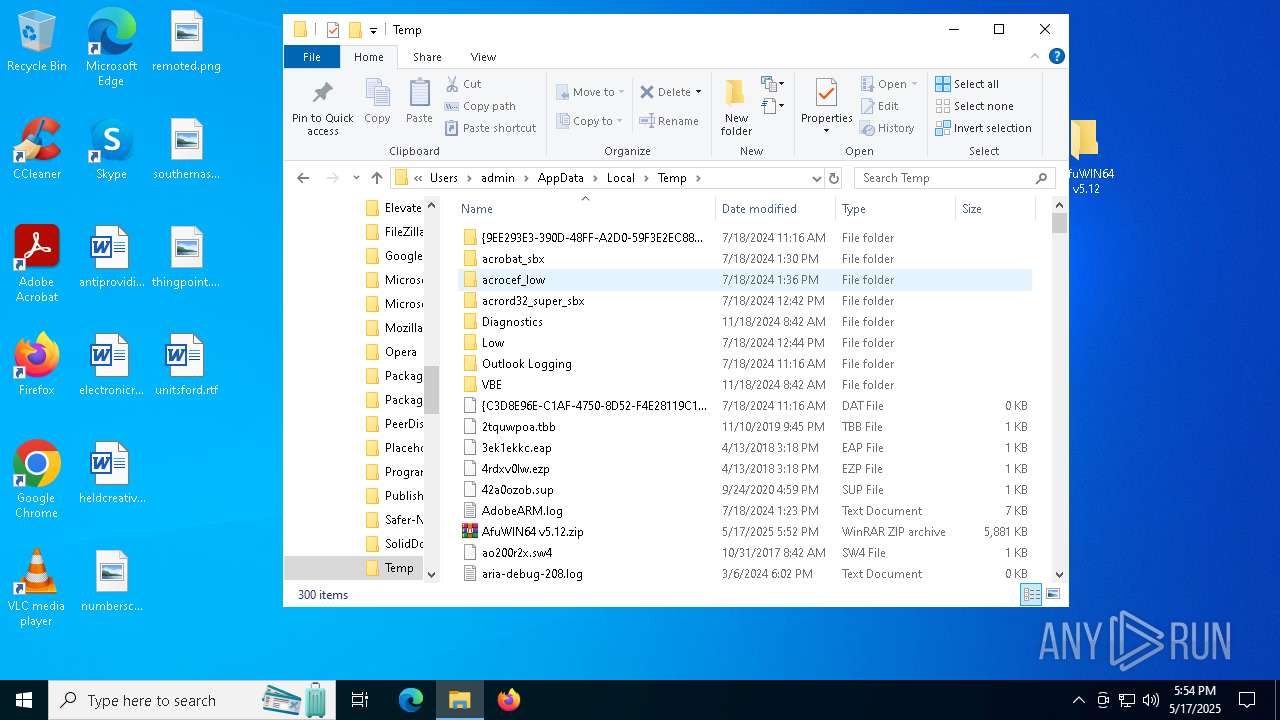
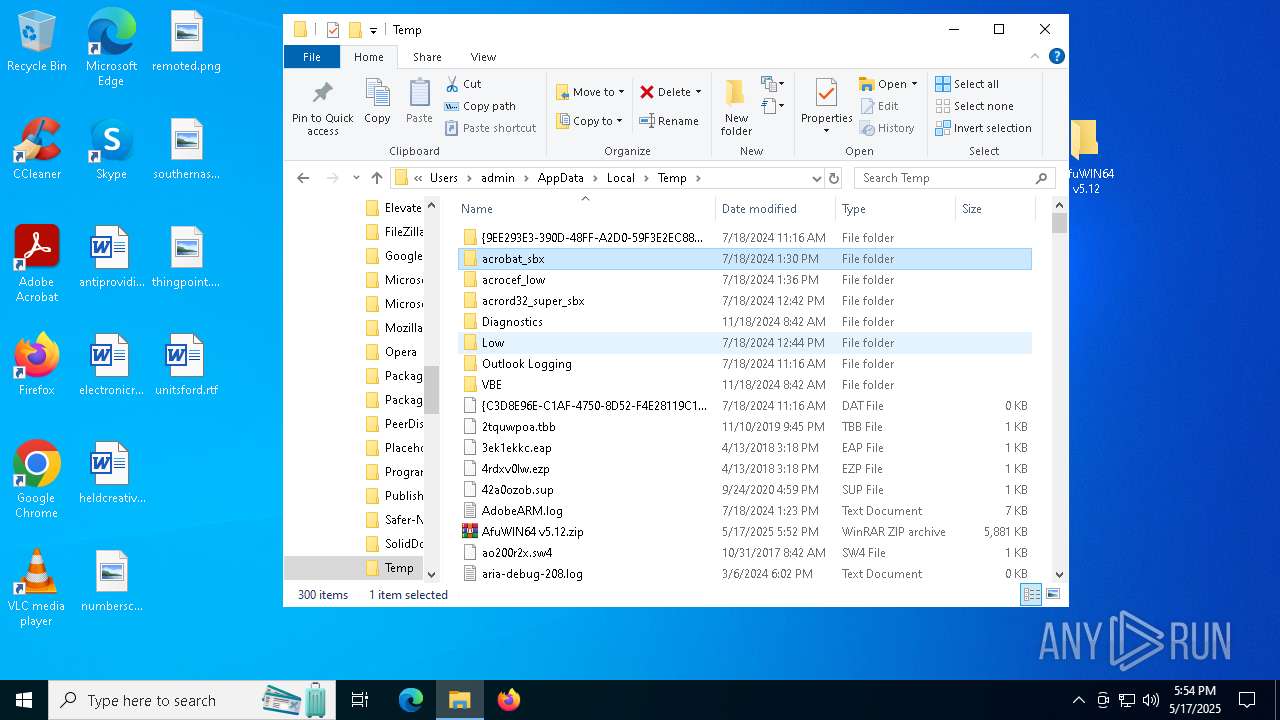
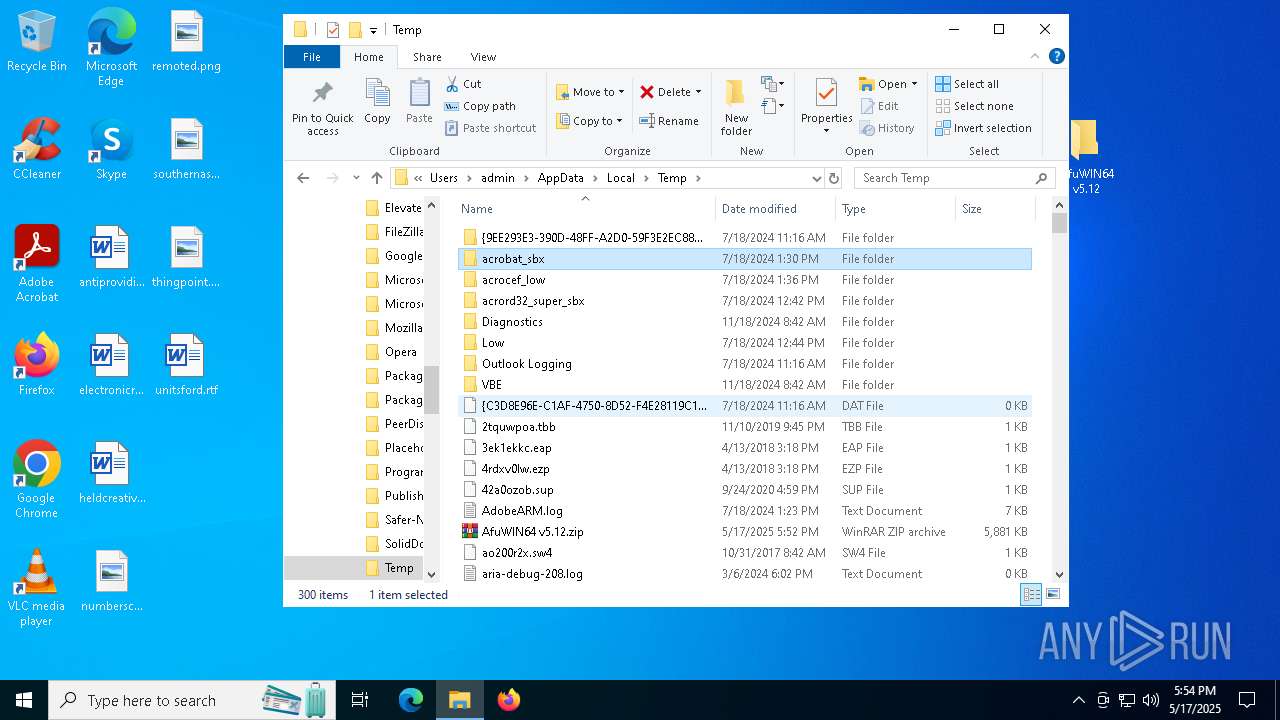
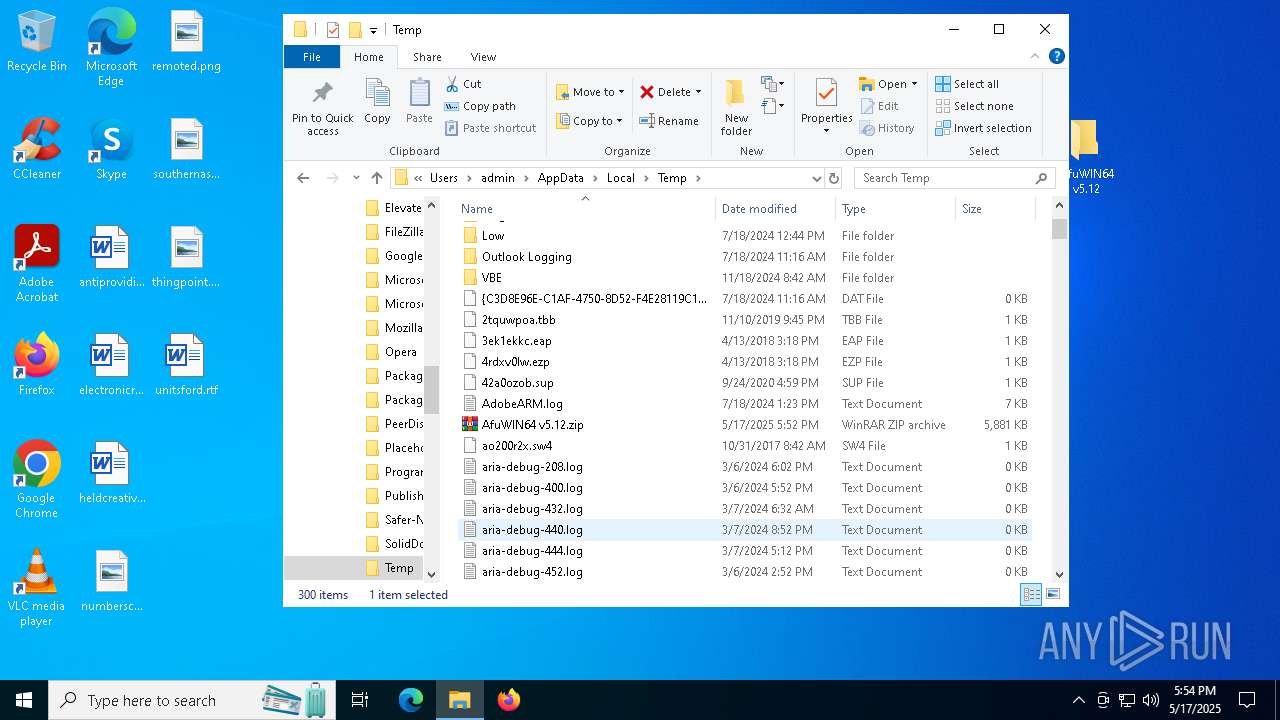
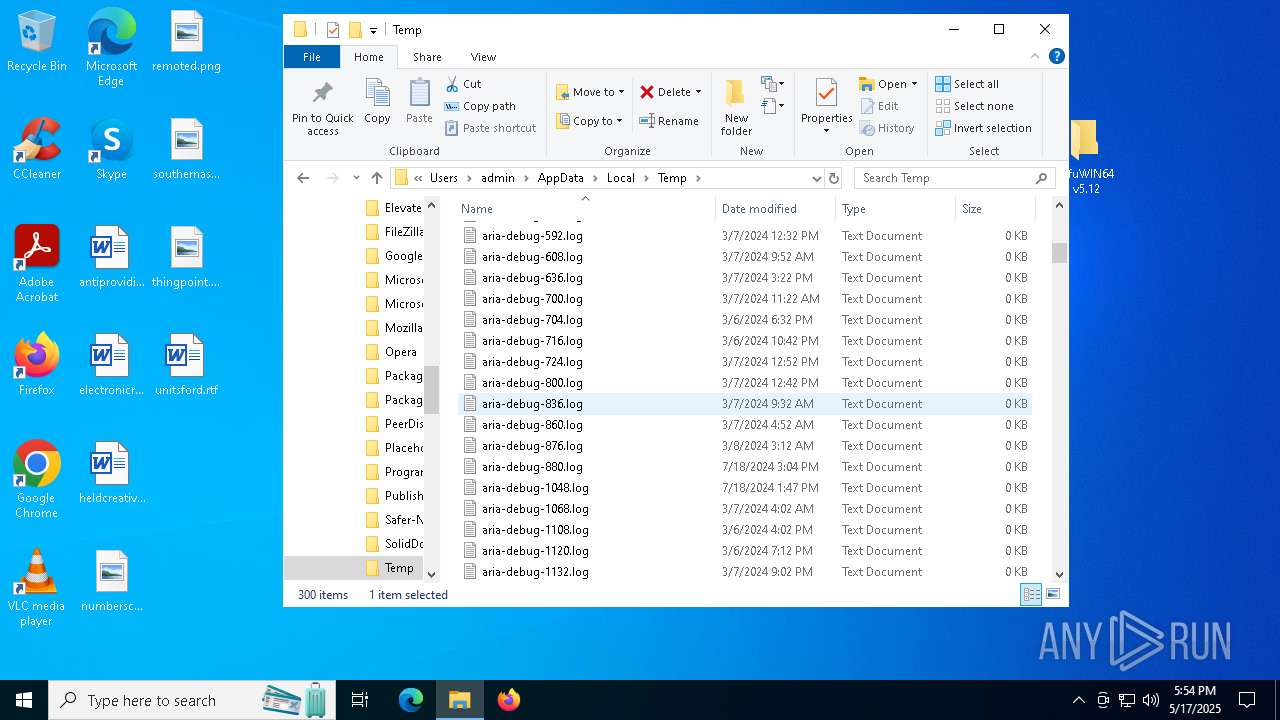
Create files in a temporary directory
- AFUWINGUIx64.exe (PID: 7816)
- AFUWINGUIx64.exe (PID: 7856)
- InspectorConfig.exe (PID: 7996)
The sample compiled with english language support
- AFUWINGUIx64.exe (PID: 7856)
- InspectorConfig.exe (PID: 7904)
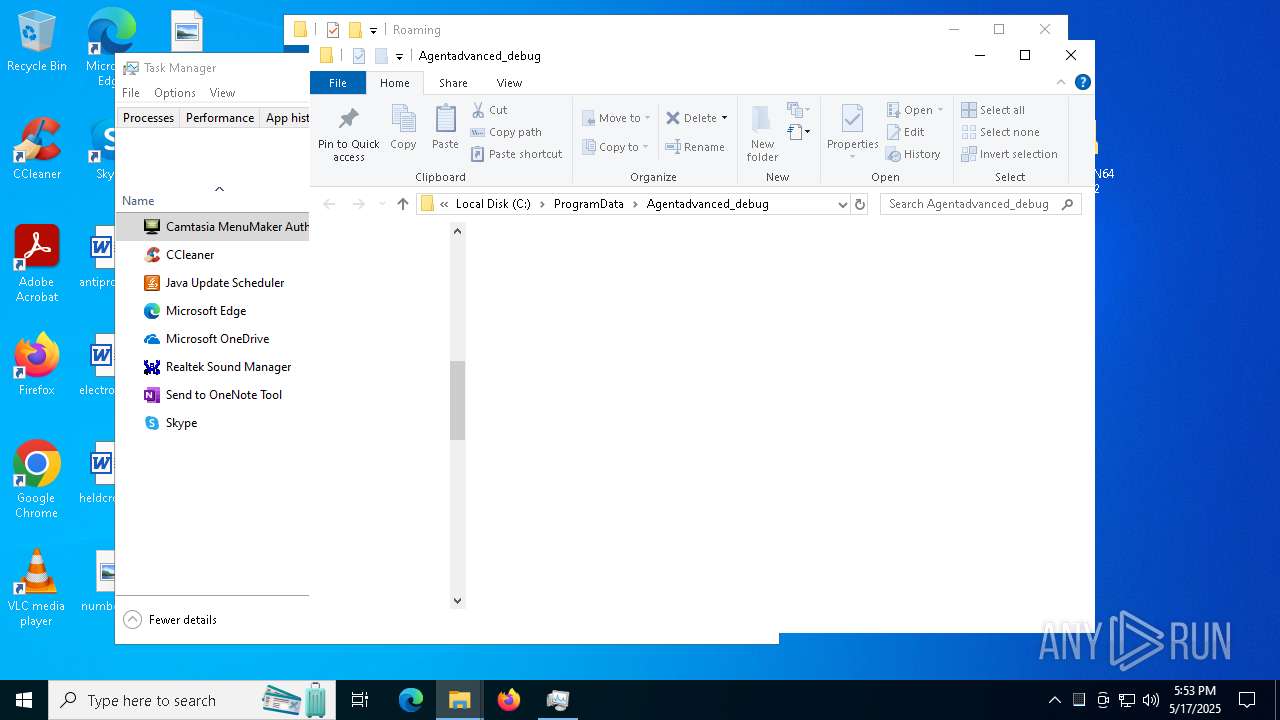
Creates files in the program directory
- AFUWINGUIx64.exe (PID: 7856)
- InspectorConfig.exe (PID: 7904)
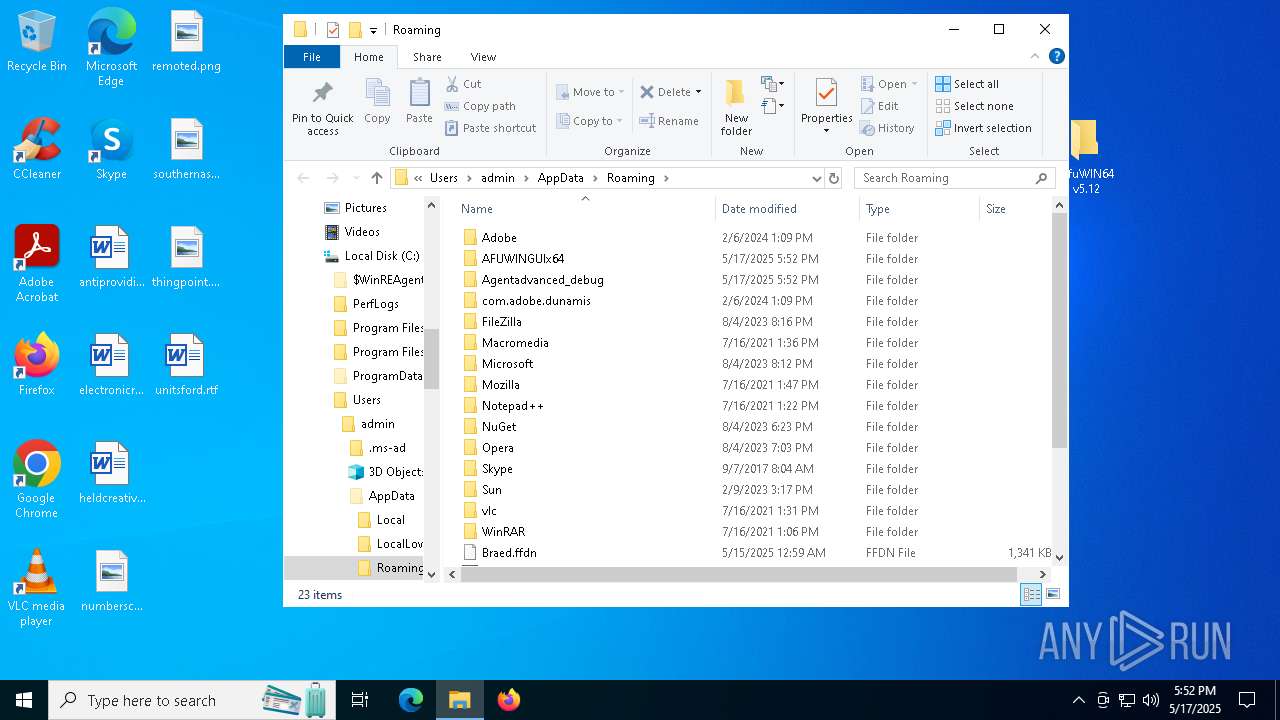
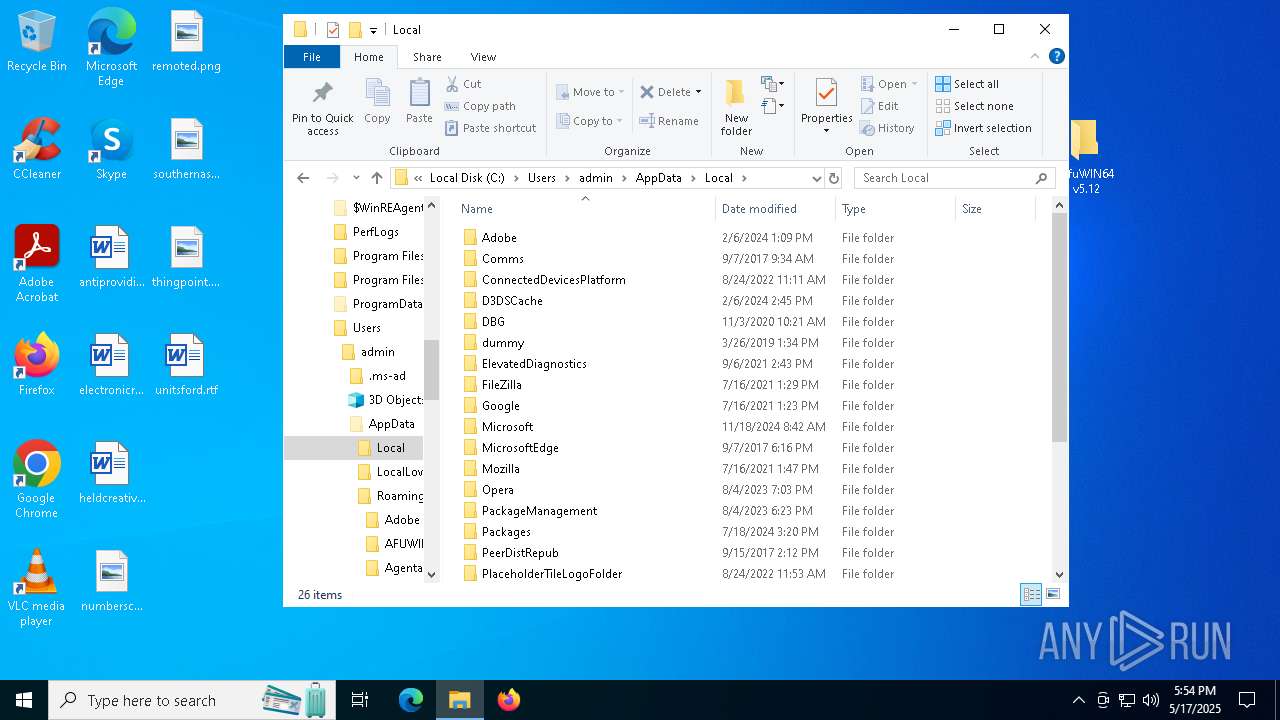
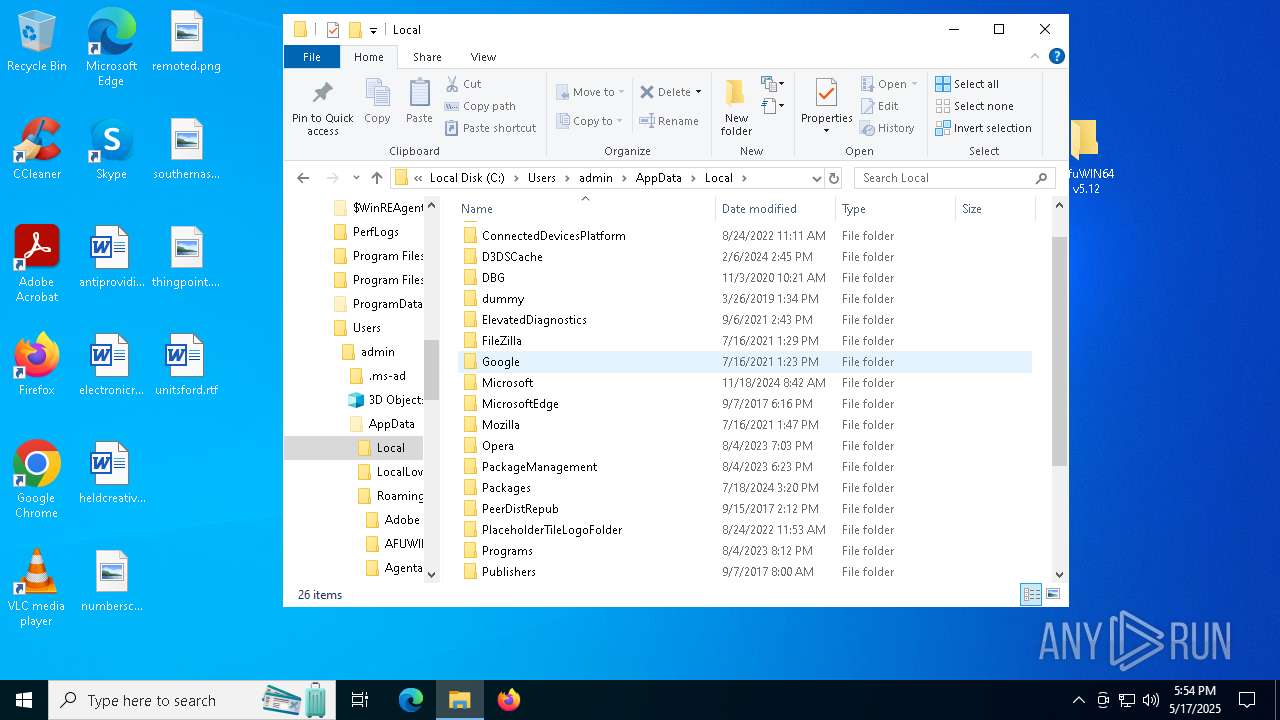
Creates files or folders in the user directory
- AFUWINGUIx64.exe (PID: 7856)
- InspectorConfig.exe (PID: 7996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Remcos
(PID) Process(1348) ParallelFab.exe
C2 (1)38.180.91.87:4545
BotnetNOV
Options
Connect_interval1
Install_flagFalse
Install_HKCU\RunTrue
Install_HKLM\RunTrue
Install_HKLM\Explorer\Run1
Install_HKLM\Winlogon\Shell100000
Setup_path%LOCALAPPDATA%
Copy_fileremcos.exe
Startup_valueFalse
Hide_fileFalse
Mutex_namevrtrtvrtvvrt-YHR3NT
Keylog_flag0
Keylog_path%LOCALAPPDATA%
Keylog_filelogs.dat
Keylog_cryptFalse
Hide_keylogFalse
Screenshot_flagFalse
Screenshot_time5
Take_ScreenshotFalse
Screenshot_path%APPDATA%
Screenshot_fileScreenshots
Screenshot_cryptFalse
Mouse_optionFalse
Delete_fileFalse
Audio_record_time5
Audio_path1
Audio_dirMicRecords
Connect_delay0
Copy_dirRemcos
Keylog_dirremcos
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:05:15 09:29:50 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | AfuWIN64 v5.12/ |
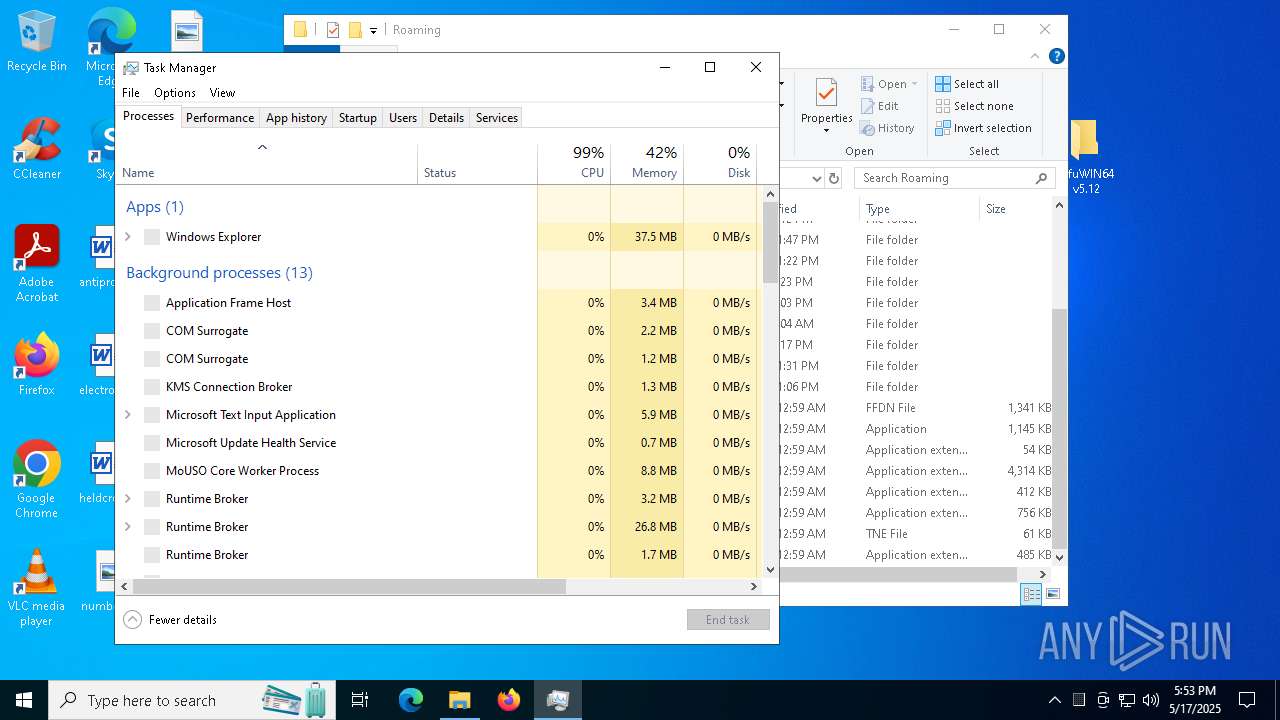
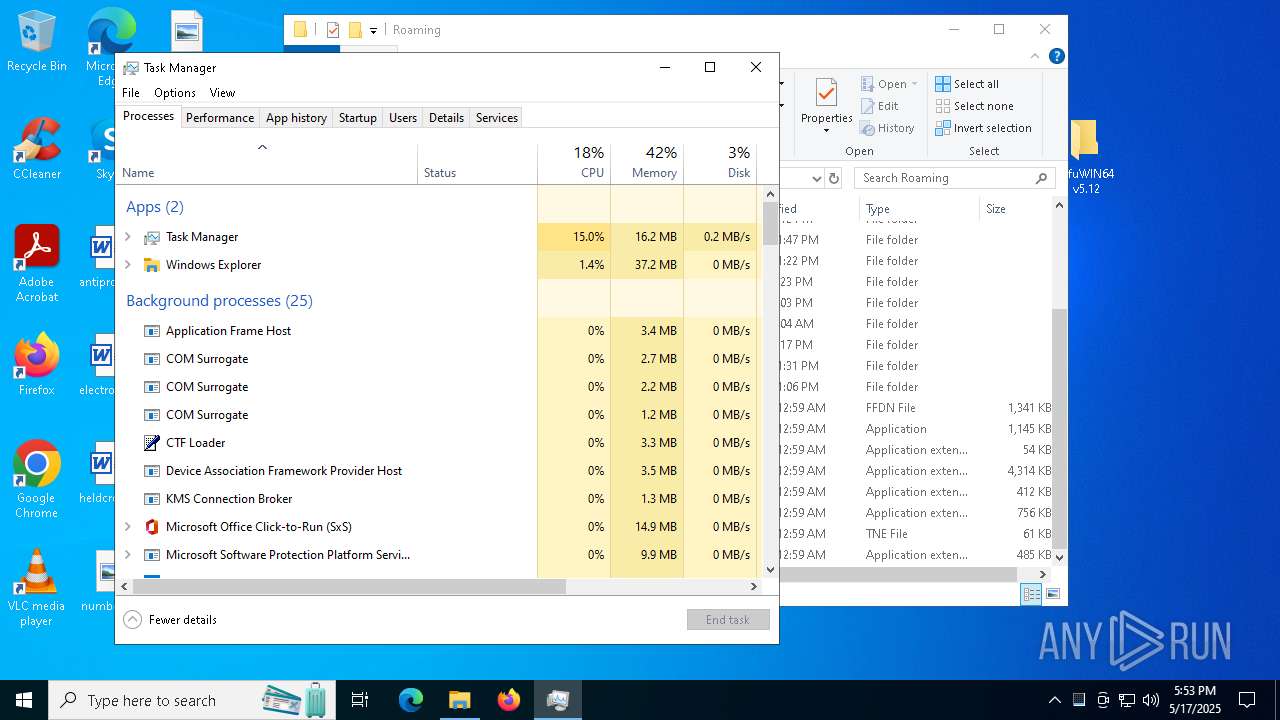
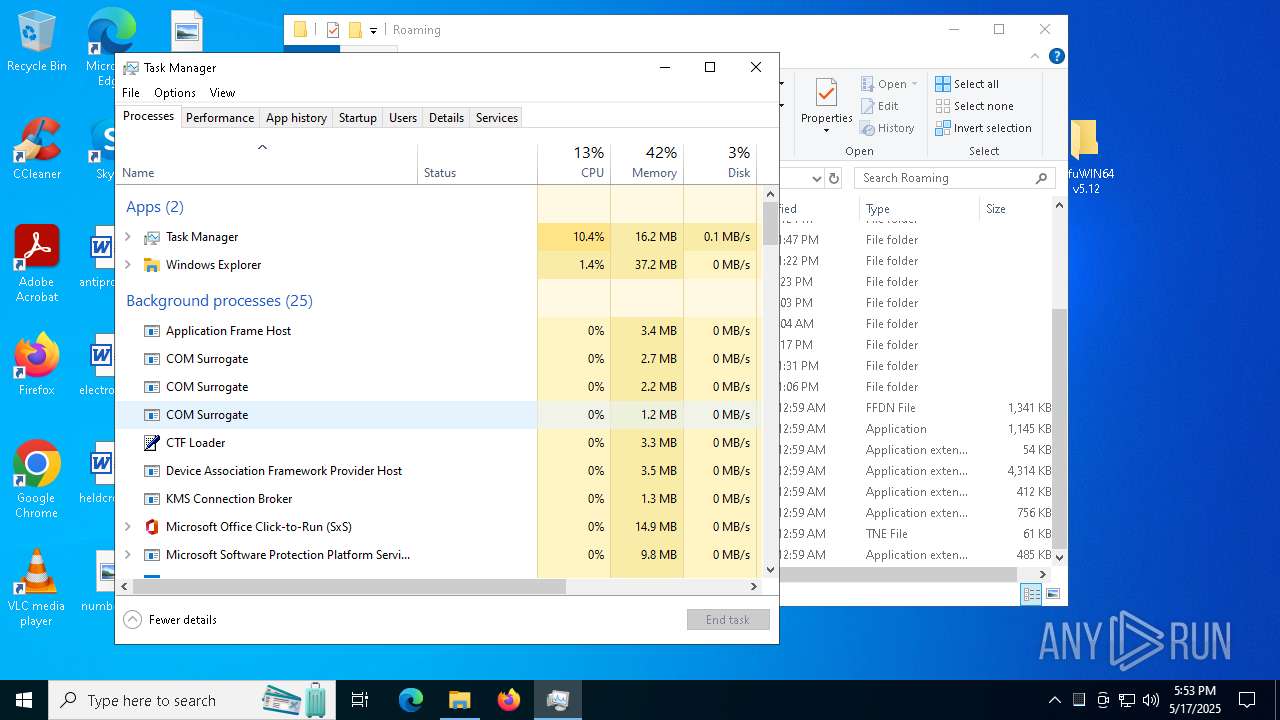
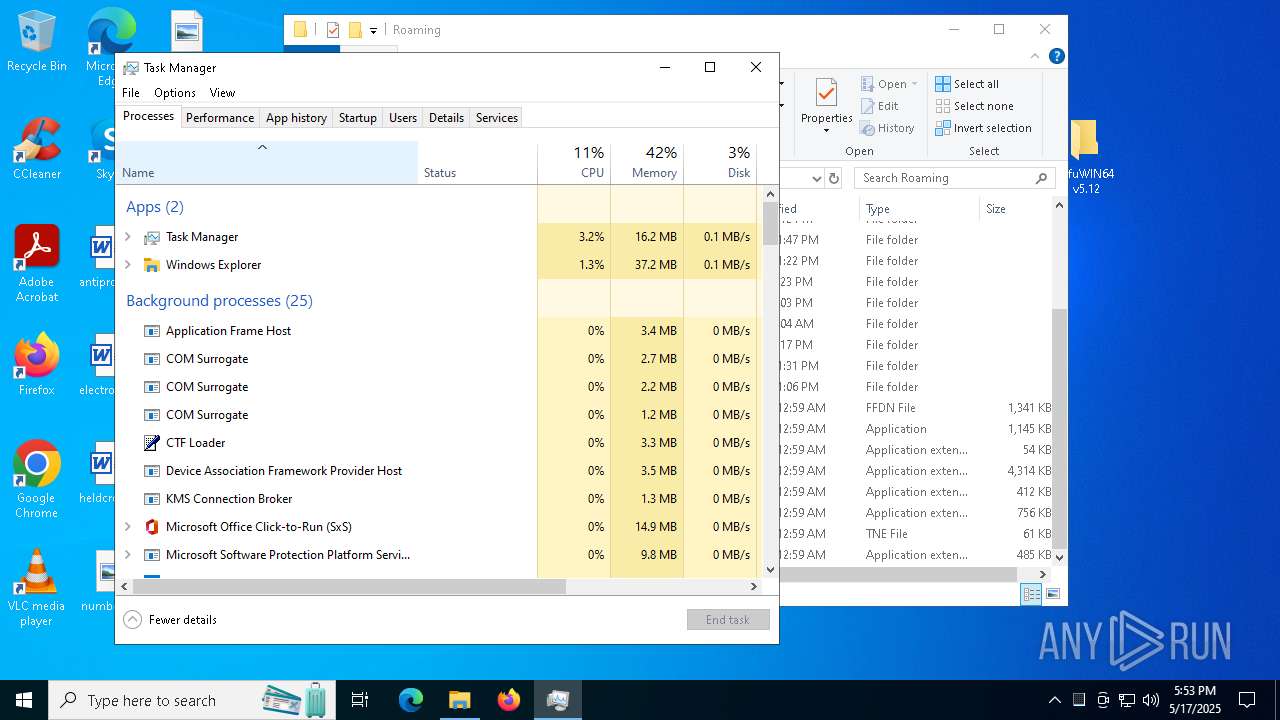
Total processes
155
Monitored processes
17
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1348 | C:\Users\admin\AppData\Local\Temp\ParallelFab.exe | C:\Users\admin\AppData\Local\Temp\ParallelFab.exe | InspectorConfig.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
Remcos(PID) Process(1348) ParallelFab.exe C2 (1)38.180.91.87:4545 BotnetNOV Options Connect_interval1 Install_flagFalse Install_HKCU\RunTrue Install_HKLM\RunTrue Install_HKLM\Explorer\Run1 Install_HKLM\Winlogon\Shell100000 Setup_path%LOCALAPPDATA% Copy_fileremcos.exe Startup_valueFalse Hide_fileFalse Mutex_namevrtrtvrtvvrt-YHR3NT Keylog_flag0 Keylog_path%LOCALAPPDATA% Keylog_filelogs.dat Keylog_cryptFalse Hide_keylogFalse Screenshot_flagFalse Screenshot_time5 Take_ScreenshotFalse Screenshot_path%APPDATA% Screenshot_fileScreenshots Screenshot_cryptFalse Mouse_optionFalse Delete_fileFalse Audio_record_time5 Audio_path1 Audio_dirMicRecords Connect_delay0 Copy_dirRemcos Keylog_dirremcos | |||||||||||||||
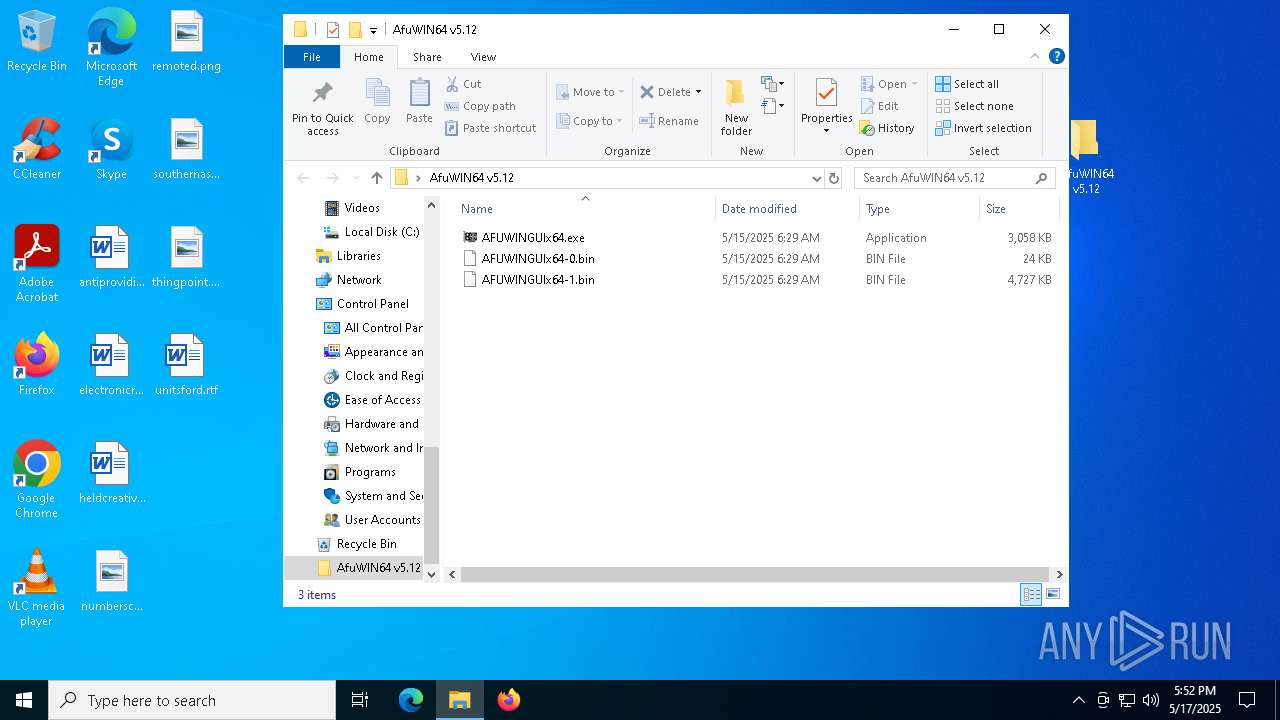
| 5408 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\AfuWIN64 v5.12.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6592 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7216 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7248 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7452 | "C:\Users\admin\AppData\Roaming\Agentadvanced_debug\XPFix.exe" "C:\Users\admin\AppData\Roaming\Agentadvanced_debug\XPFix.exe" /update | C:\Users\admin\AppData\Roaming\Agentadvanced_debug\XPFix.exe | — | InspectorConfig.exe | |||||||||||
User: admin Company: 360.cn Integrity Level: HIGH Description: 360安全卫士 安全防护中心模块 Exit code: 0 Version: 1, 0, 0, 1013 Modules
| |||||||||||||||
| 7560 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7576 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7672 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7732 | "C:\Users\admin\Desktop\AfuWIN64 v5.12\AFUWINGUIx64.exe" | C:\Users\admin\Desktop\AfuWIN64 v5.12\AFUWINGUIx64.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
5 718
Read events
5 685
Write events
32
Delete events
1
Modification events
| (PID) Process: | (5408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\AfuWIN64 v5.12.zip | |||
| (PID) Process: | (5408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (5408) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
25
Suspicious files
12
Text files
1
Unknown types
0
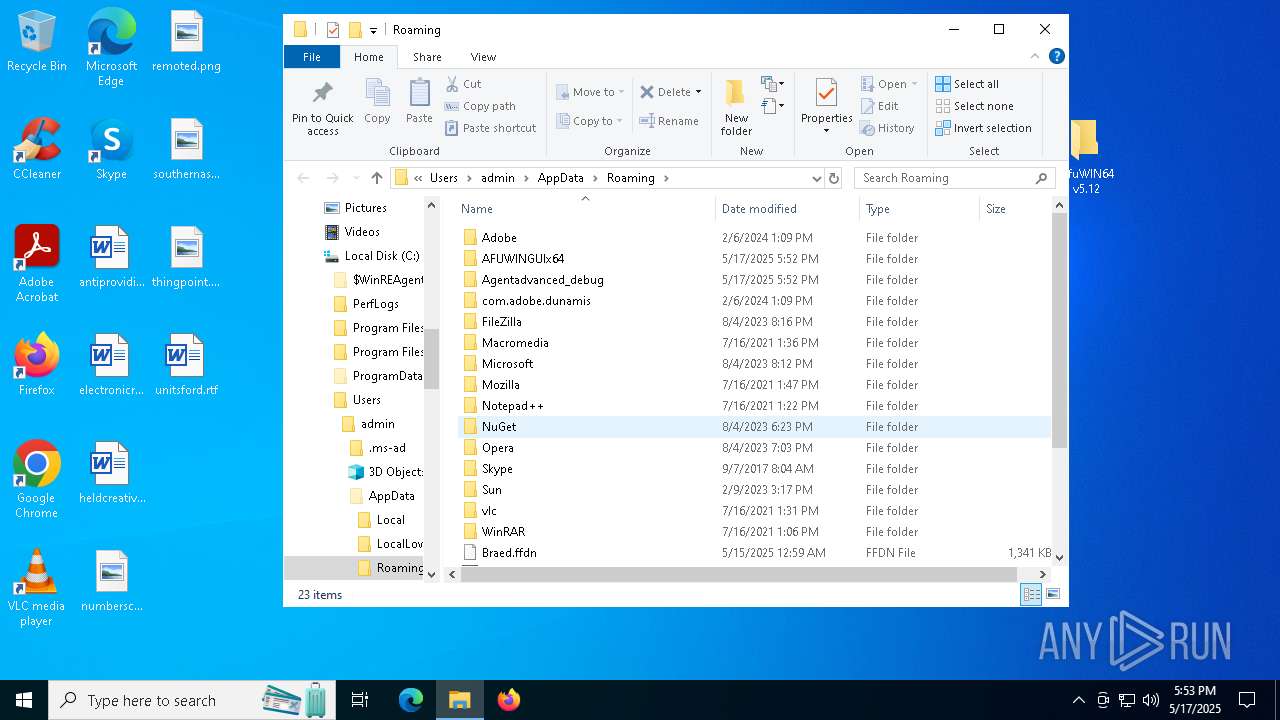
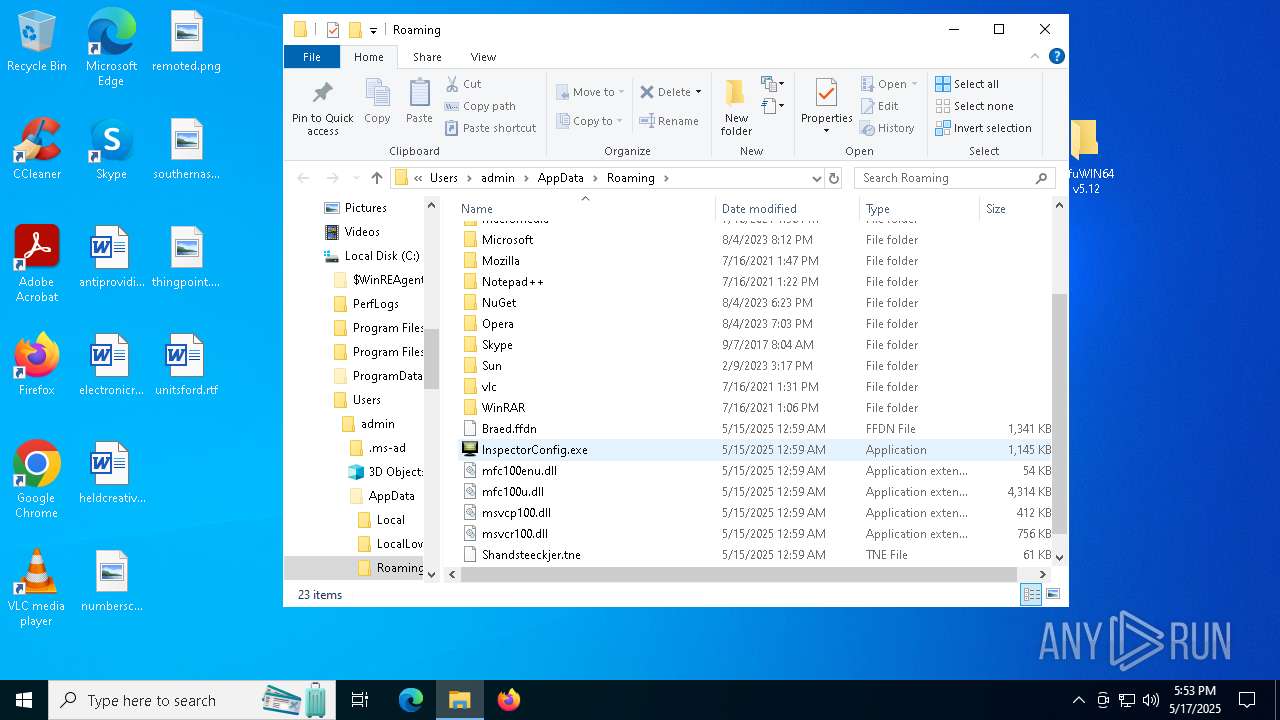
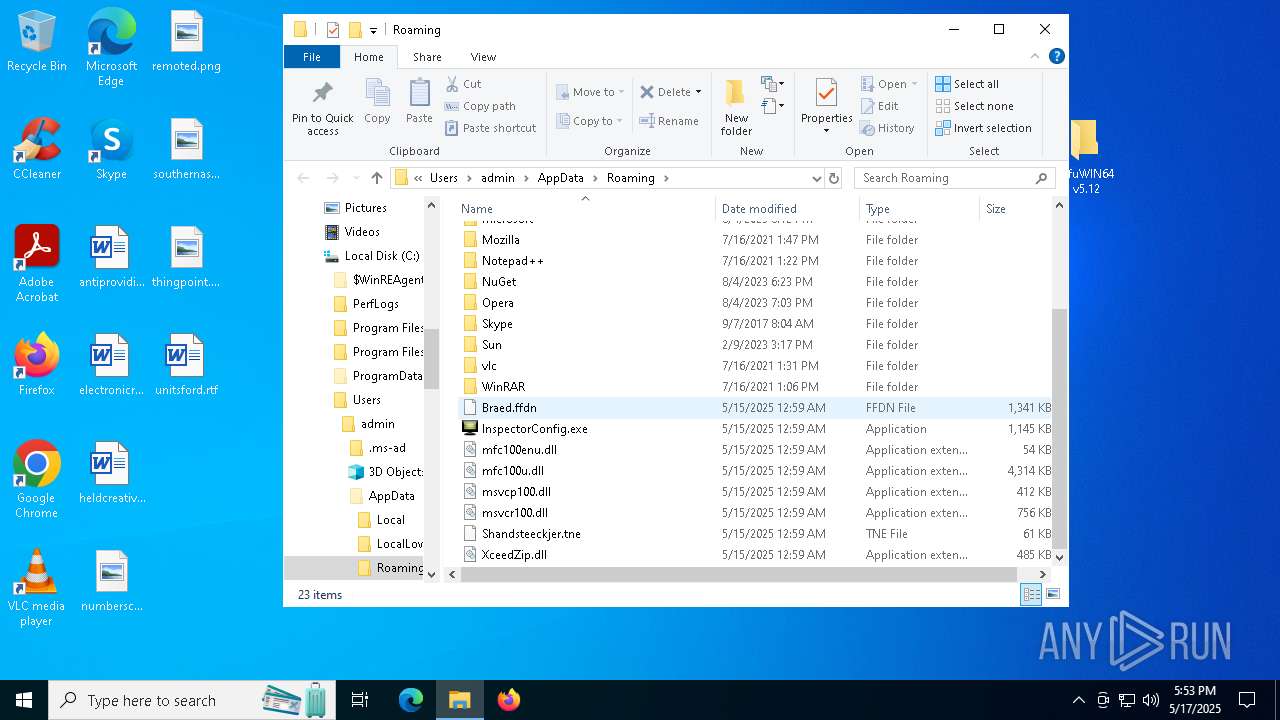
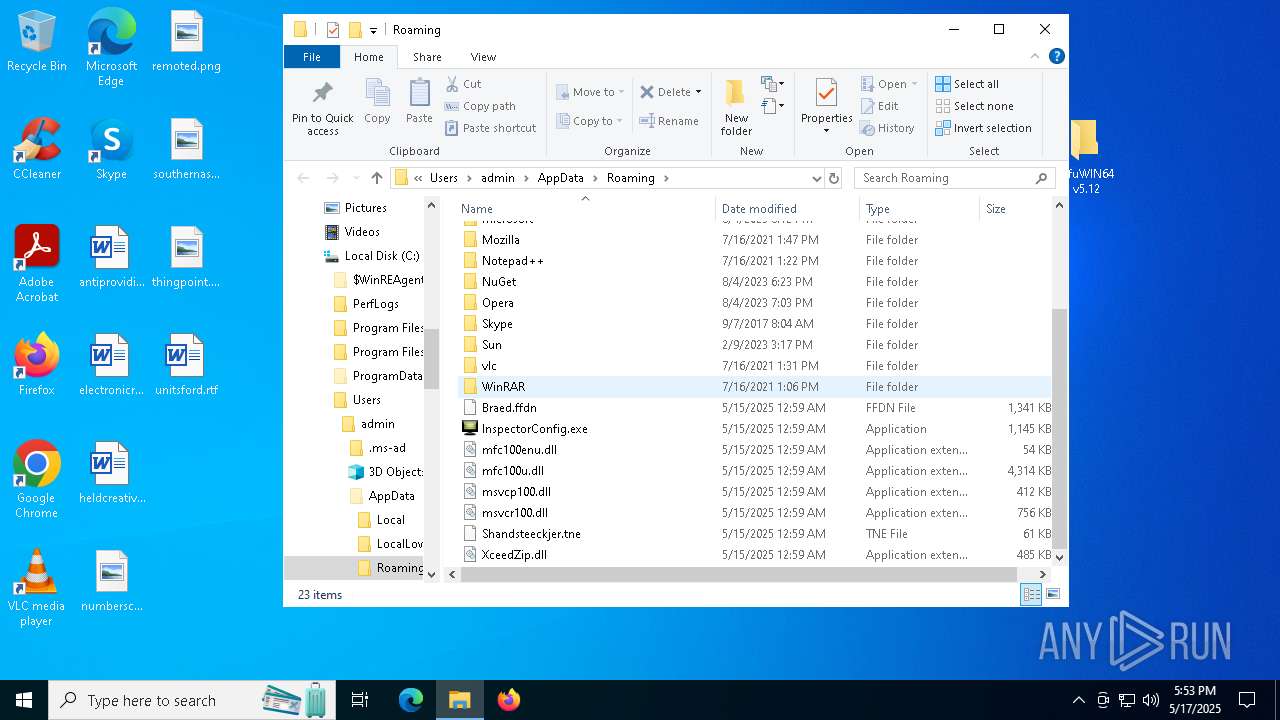
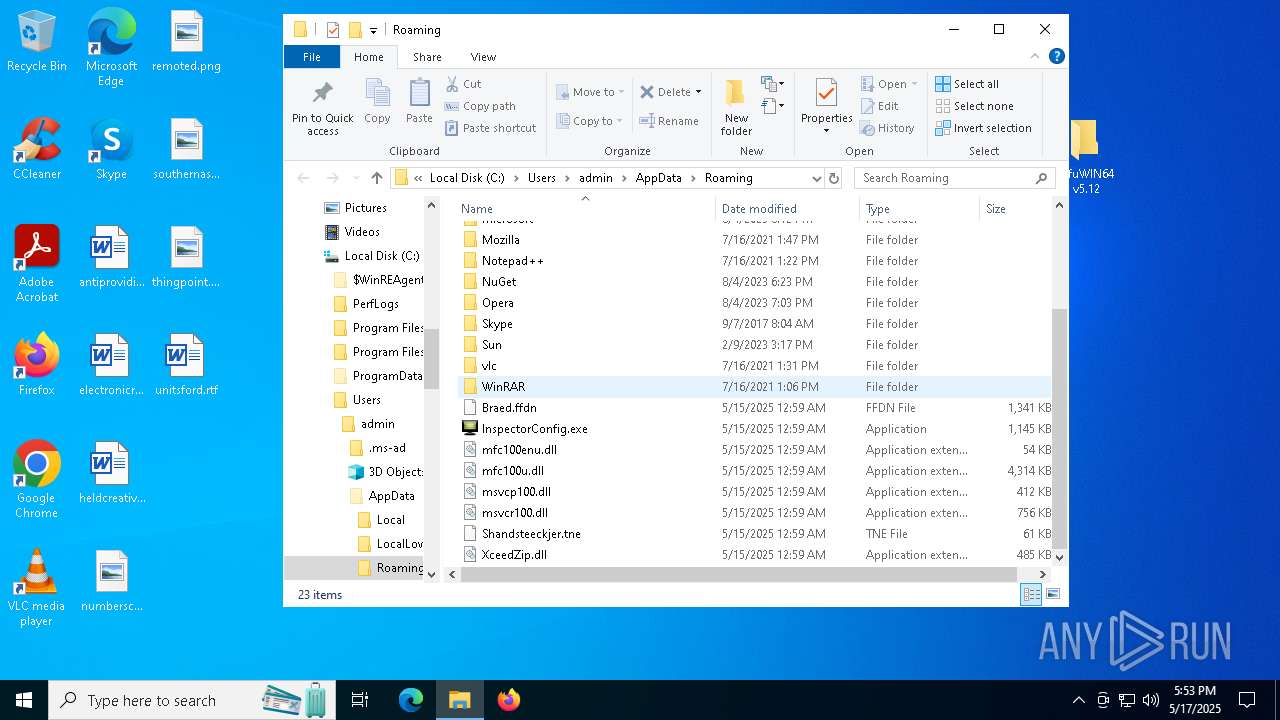
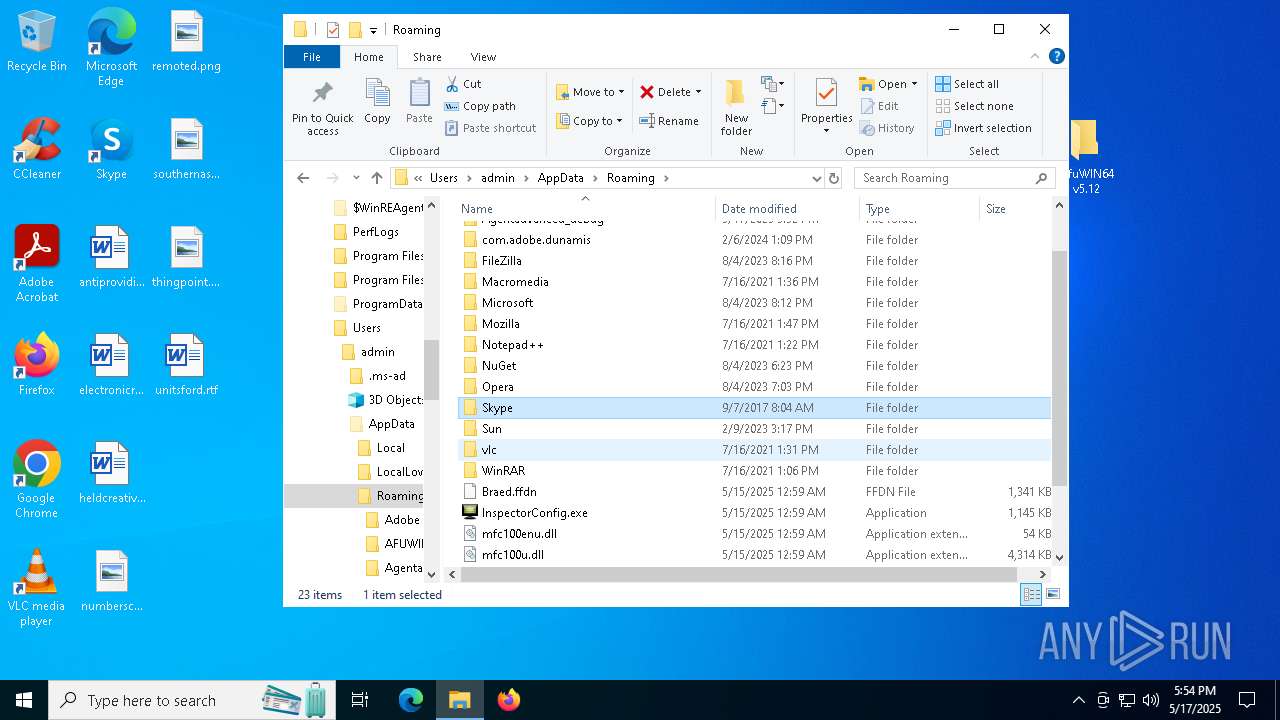
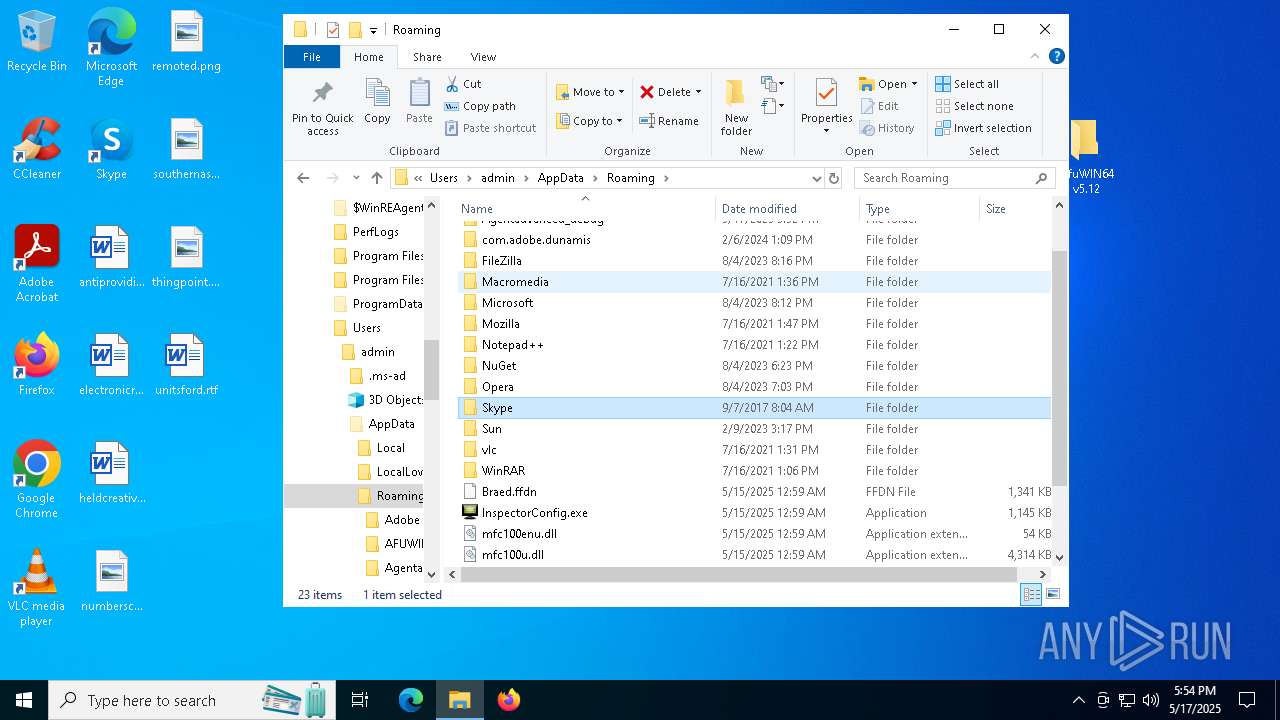
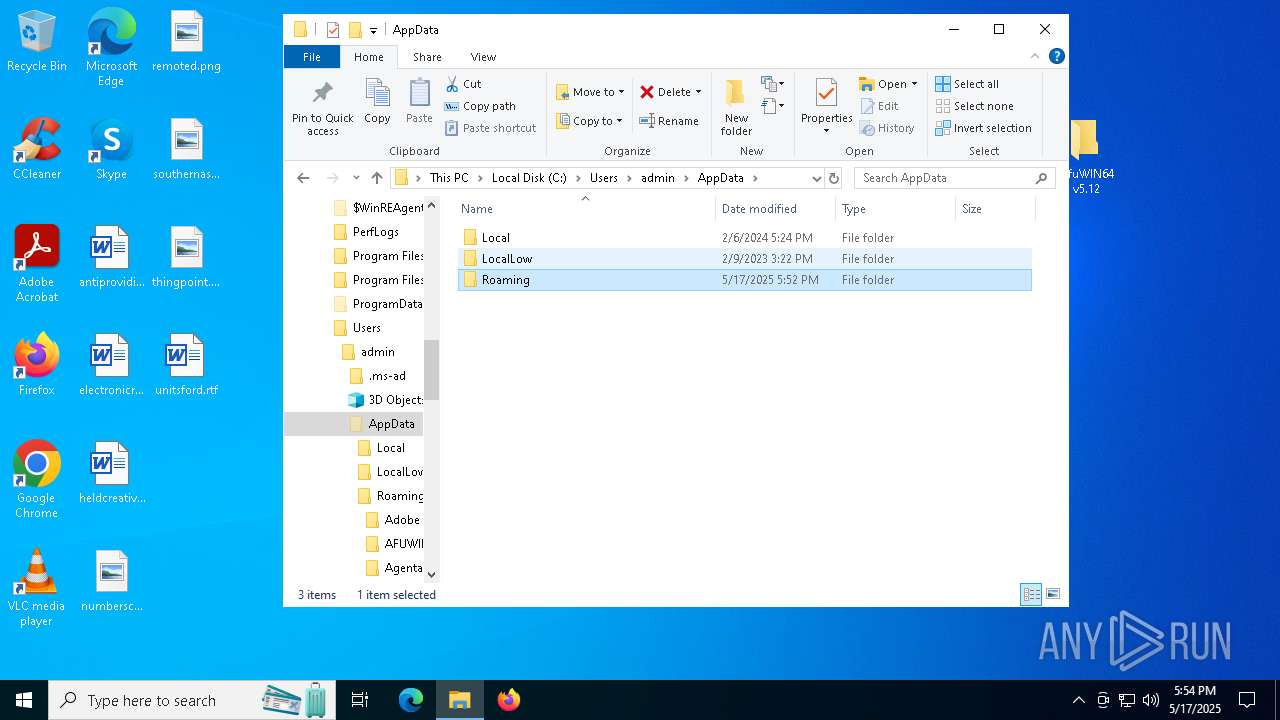
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5408 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5408.16561\AfuWIN64 v5.12\AFUWINGUIx64-1.bin | — | |
MD5:— | SHA256:— | |||
| 7856 | AFUWINGUIx64.exe | C:\Users\admin\AppData\Roaming\is-C1NU0.tmp | executable | |
MD5:2A2C442F00B45E01D4C882EEA69A01BC | SHA256:D71DB839DE0BC1FCC01A125D57CED2AAEA3F444A992426C316CE18C267C33A8C | |||
| 7816 | AFUWINGUIx64.exe | C:\Users\admin\AppData\Local\Temp\is-BCHKJ.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 7856 | AFUWINGUIx64.exe | C:\Users\admin\AppData\Roaming\is-LPCU1.tmp | binary | |
MD5:E2C853E4BD996D7C6175A3F6B84744A7 | SHA256:2C6CDBF3B7D3442C8D2171E7431D0AEB4C7709F6BC8B5D6D04EB84339BAD253A | |||
| 7856 | AFUWINGUIx64.exe | C:\Users\admin\AppData\Roaming\is-20FJI.tmp | executable | |
MD5:BC83108B18756547013ED443B8CDB31B | SHA256:B2AD109C15EAA92079582787B7772BA0A2F034F7D075907FF87028DF0EAEA671 | |||
| 7856 | AFUWINGUIx64.exe | C:\Users\admin\AppData\Roaming\AFUWINGUIx64\AFUWINGUIx64.EXE | executable | |
MD5:DAB11F6CE6D53BF01168B4F8A8850BBA | SHA256:1D59A561AC7EC00AC68C1ABFC1D6C7E6D76208805727A8AE1EAF71350D19FCAA | |||
| 7856 | AFUWINGUIx64.exe | C:\Users\admin\AppData\Roaming\AFUWINGUIx64\is-19G8C.tmp | executable | |
MD5:DAB11F6CE6D53BF01168B4F8A8850BBA | SHA256:1D59A561AC7EC00AC68C1ABFC1D6C7E6D76208805727A8AE1EAF71350D19FCAA | |||
| 7856 | AFUWINGUIx64.exe | C:\Users\admin\AppData\Roaming\is-ECN3L.tmp | executable | |
MD5:0AA5410C7565C20AEBBB56A317E578DA | SHA256:88A1F9A40EB7ECE8999092B2872B6AFDE0FB3776E29384C5B00631BB0FCA34D1 | |||
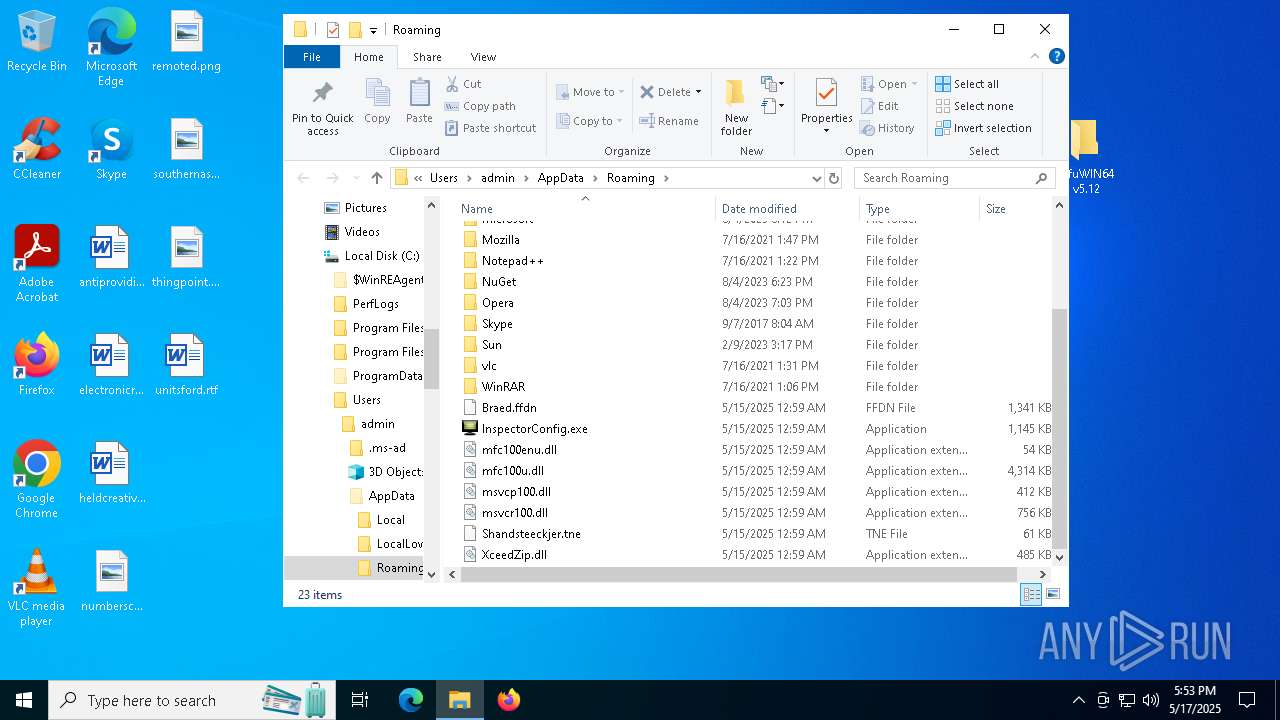
| 7856 | AFUWINGUIx64.exe | C:\Users\admin\AppData\Roaming\Braed.ffdn | binary | |
MD5:E2C853E4BD996D7C6175A3F6B84744A7 | SHA256:2C6CDBF3B7D3442C8D2171E7431D0AEB4C7709F6BC8B5D6D04EB84339BAD253A | |||
| 7856 | AFUWINGUIx64.exe | C:\Users\admin\AppData\Roaming\InspectorConfig.exe | executable | |
MD5:0AA5410C7565C20AEBBB56A317E578DA | SHA256:88A1F9A40EB7ECE8999092B2872B6AFDE0FB3776E29384C5B00631BB0FCA34D1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
395
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2908 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2908 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |