| File name: | injector2.exe |
| Full analysis: | https://app.any.run/tasks/747f4dff-205a-4593-8ef9-2df4f587c076 |
| Verdict: | Malicious activity |
| Threats: | Orcus is a modular Remote Access Trojan with some unusual functions. This RAT enables attackers to create plugins using a custom development library and offers a robust core feature set that makes it one of the most dangerous malicious programs in its class. |
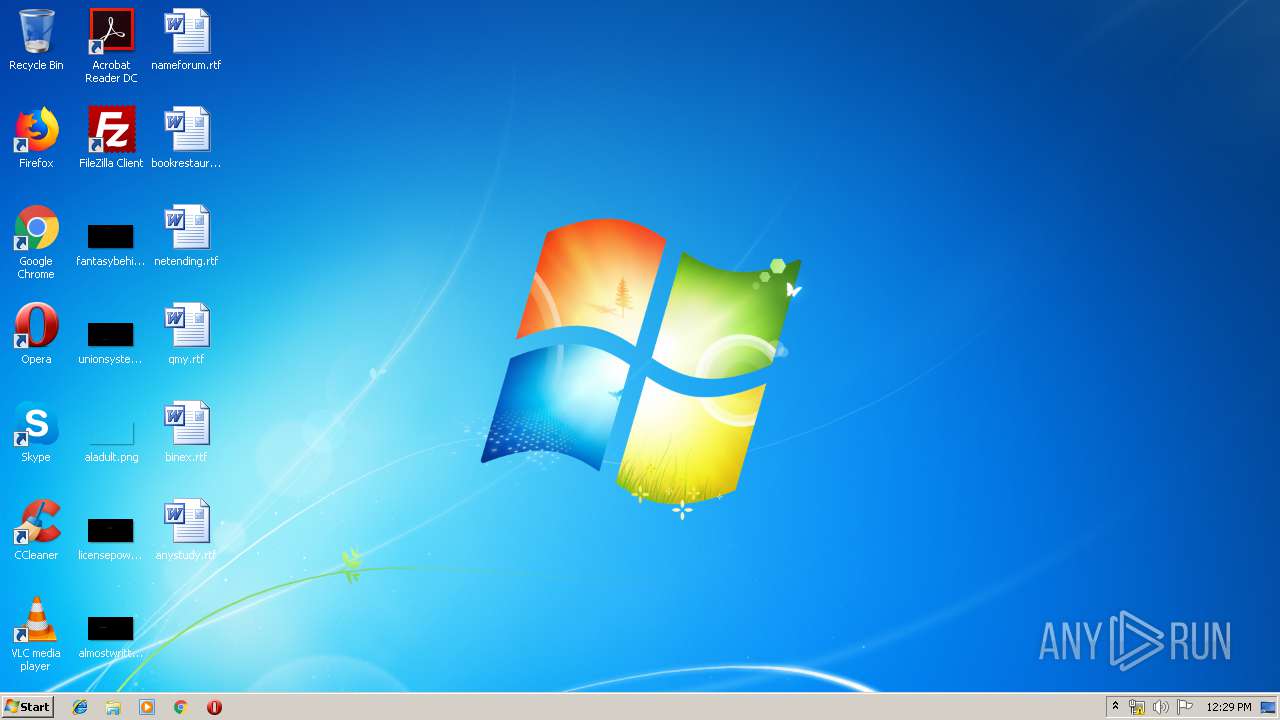
| Analysis date: | March 21, 2019, 12:29:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4C073CD92C5A4C3B6BD40FB55423AD0B |
| SHA1: | A3B16DB9197DB98E2A3344FEFF379EFDB74DBBFE |
| SHA256: | 0242EC15A75E7567186F9B6936CAEE53A9A7C24D5B3302D541D44790AC716693 |
| SSDEEP: | 24576:NedrDOQzXK0st3/7UxN/jm90TtfM8I7P7gM9gcQ4PcHg/BG12+A9pNj5zb:NeJn6T/7Uzu0T9M77zg22aG12x/j5P |
MALICIOUS
Orcus was detected
- regasm.exe (PID: 2456)
- regasm.exe (PID: 3544)
- regasm.exe (PID: 1272)
Changes the autorun value in the registry
- injector2.exe (PID: 2380)
SUSPICIOUS
Executable content was dropped or overwritten
- injector2.exe (PID: 2380)
- sewinup.exe (PID: 604)
- csc.exe (PID: 2708)
- sewinup.exe (PID: 2148)
Starts itself from another location
- injector2.exe (PID: 2380)
Application launched itself
- sewinup.exe (PID: 604)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (68.8) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 6 (27.2) |
| .exe | | | Win32 Executable Delphi generic (1.4) |
| .scr | | | Windows screen saver (1.3) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 419328 |
| InitializedDataSize: | 488960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6755c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | heLixv2 |
| FileVersion: | 1.0.0.0 |
| InternalName: | heLixv2.exe |
| LegalCopyright: | Copyright © 2017 |
| LegalTrademarks: | - |
| OriginalFileName: | heLixv2.exe |
| ProductName: | heLixv2 |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | heLixv2 |
| FileVersion: | 1.0.0.0 |
| InternalName: | heLixv2.exe |
| LegalCopyright: | Copyright © 2017 |
| LegalTrademarks: | - |
| OriginalFilename: | heLixv2.exe |
| ProductName: | heLixv2 |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000665A4 | 0x00066600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48567 |
DATA | 0x00068000 | 0x0000146C | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.61766 |
BSS | 0x0006A000 | 0x000037B1 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0006E000 | 0x00002124 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.97093 |
.tls | 0x00071000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00072000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.199108 |
.reloc | 0x00073000 | 0x00005E8C | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.64657 |
.rsrc | 0x00079000 | 0x0006DC00 | 0x0006DC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 3.96501 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.2748 | 780 | UNKNOWN | UNKNOWN | RT_VERSION |
2 | 3.93679 | 67624 | UNKNOWN | Spanish - Spain (International sort) | RT_ICON |
3 | 4.26182 | 38056 | UNKNOWN | Spanish - Spain (International sort) | RT_ICON |
4 | 4.30071 | 21640 | UNKNOWN | Spanish - Spain (International sort) | RT_ICON |
5 | 4.23586 | 16936 | UNKNOWN | Spanish - Spain (International sort) | RT_ICON |
6 | 4.49579 | 9640 | UNKNOWN | Spanish - Spain (International sort) | RT_ICON |
7 | 4.58105 | 4264 | UNKNOWN | Spanish - Spain (International sort) | RT_ICON |
8 | 4.813 | 2440 | UNKNOWN | Spanish - Spain (International sort) | RT_ICON |
9 | 4.78042 | 1128 | UNKNOWN | Spanish - Spain (International sort) | RT_ICON |
4081 | 2.6696 | 136 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Total processes
43
Monitored processes
12
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | C:\Users\admin\AppData\Local\Temp\sewinup.exe | C:\Users\admin\AppData\Local\Temp\sewinup.exe | injector2.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: heLixv2 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1272 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\regasm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\regasm.exe | sewinup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 1472 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESA139.tmp" "c:\Users\admin\AppData\Local\Temp\CSCA128.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 1624 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\osqe6tf8.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | — | regasm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2148 | C:\Users\admin\AppData\Local\Temp\sewinup.exe | C:\Users\admin\AppData\Local\Temp\sewinup.exe | sewinup.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: heLixv2 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2380 | "C:\Users\admin\AppData\Local\Temp\injector2.exe" | C:\Users\admin\AppData\Local\Temp\injector2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: heLixv2 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2456 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\regasm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\regasm.exe | sewinup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2676 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\btdvdb6e.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | — | regasm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2708 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\smnqjt-u.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | regasm.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 3028 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES6208.tmp" "c:\Users\admin\AppData\Local\Temp\CSC6207.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
Total events
32
Read events
31
Write events
1
Delete events
0
Modification events
| (PID) Process: | (2380) injector2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | server\ |
Value: C:\Users\admin\server\server.exe | |||
Executable files
5
Suspicious files
0
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2676 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCA128.tmp | — | |
MD5:— | SHA256:— | |||
| 1472 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESA139.tmp | — | |
MD5:— | SHA256:— | |||
| 2676 | csc.exe | C:\Users\admin\AppData\Local\Temp\btdvdb6e.dll | — | |
MD5:— | SHA256:— | |||
| 2676 | csc.exe | C:\Users\admin\AppData\Local\Temp\btdvdb6e.out | — | |
MD5:— | SHA256:— | |||
| 2456 | regasm.exe | C:\Users\admin\AppData\Local\Temp\smnqjt-u.0.cs | — | |
MD5:— | SHA256:— | |||
| 2708 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCFFD3.tmp | — | |
MD5:— | SHA256:— | |||
| 4012 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESFFD4.tmp | — | |
MD5:— | SHA256:— | |||
| 2708 | csc.exe | C:\Users\admin\AppData\Local\Temp\smnqjt-u.out | — | |
MD5:— | SHA256:— | |||
| 1624 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC6207.tmp | — | |
MD5:— | SHA256:— | |||
| 3028 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES6208.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report