| URL: | https://zippyshare.day/FRZjYTWMSAxdNLP/file |
| Full analysis: | https://app.any.run/tasks/df201696-ed35-41d9-a25e-befbb3a25e3e |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | August 21, 2024, 11:29:11 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 61007876C912AED90EF793272EADF7AA |
| SHA1: | 5B23D59CB948E992283EF3A420A5F5E07E23590A |
| SHA256: | 018C217CFAA9701110B1DD42F24A1661640D9C931A0AE8D71B3674710625B62B |
| SSDEEP: | 3:N8mhBEn3g7DD9S:2Gy3g7NS |
MALICIOUS
Adds extension to the Windows Defender exclusion list
- RegistryHost.exe (PID: 7200)
- rkduajedzcrd.exe (PID: 8016)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2256)
- explorer.exe (PID: 7736)
AMADEY has been detected (SURICATA)
- explorer.exe (PID: 7736)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7276)
Changes image file execution options
- KMSELDI.exe (PID: 8064)
- AutoPico.exe (PID: 3696)
XORed URL has been found (YARA)
- explorer.exe (PID: 7736)
SILENTCRYPTOMINER has been detected (SURICATA)
- explorer.exe (PID: 7736)
Connects to the CnC server
- explorer.exe (PID: 7736)
SUSPICIOUS
Reads security settings of Internet Explorer
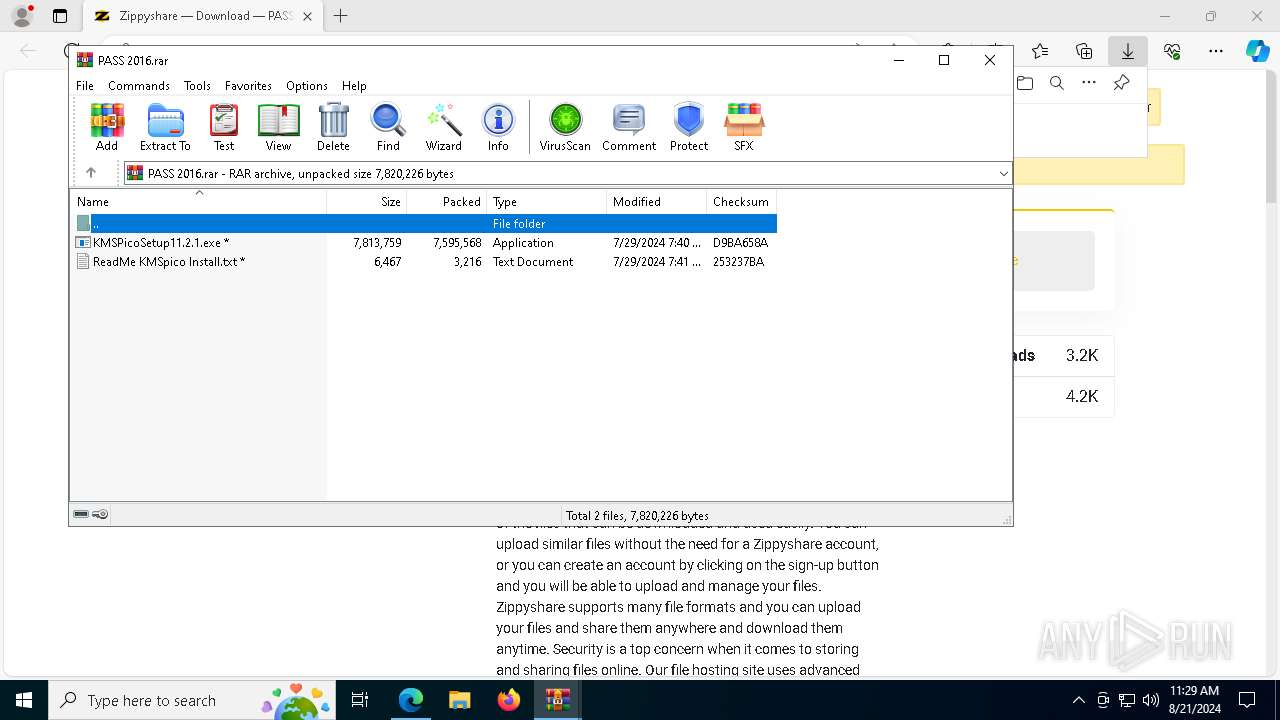
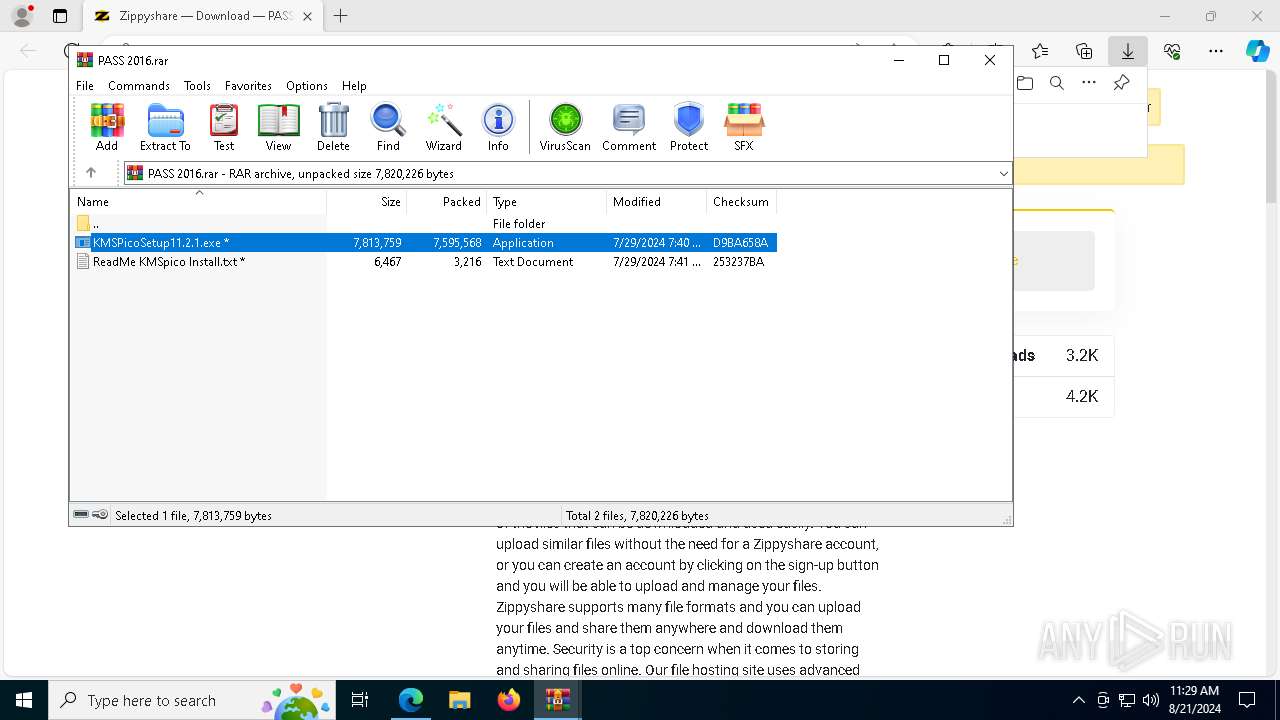
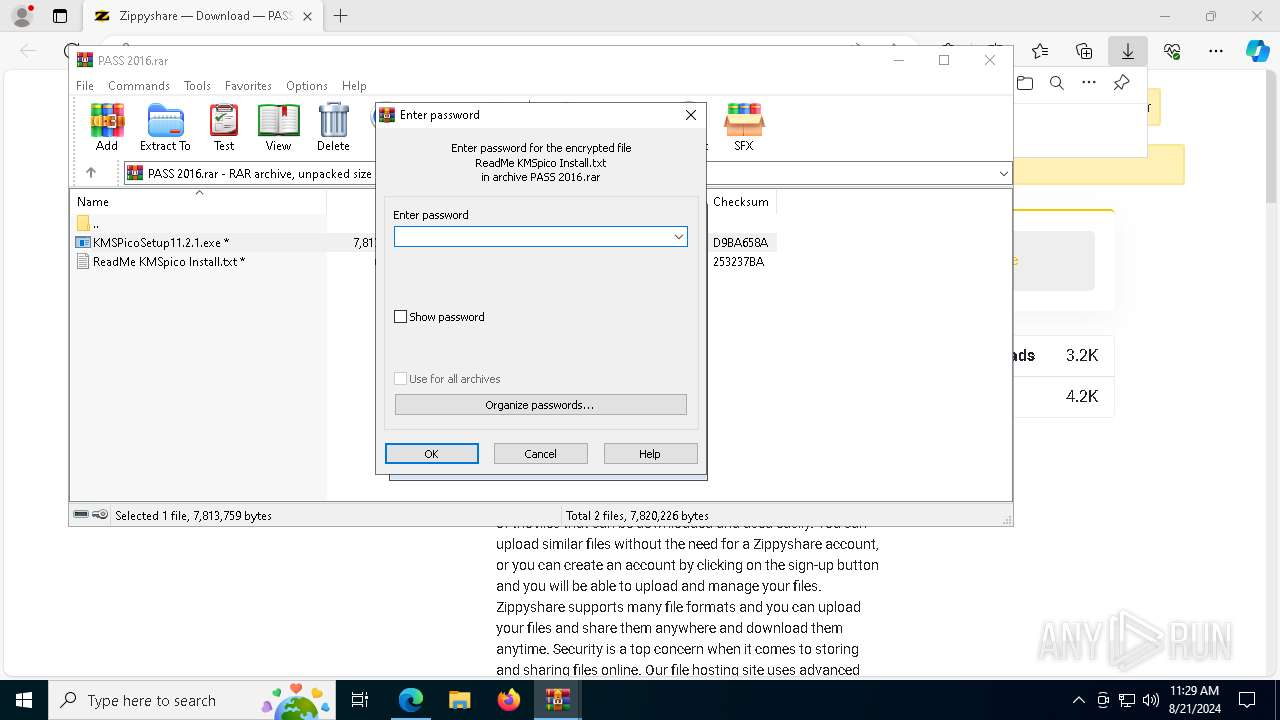
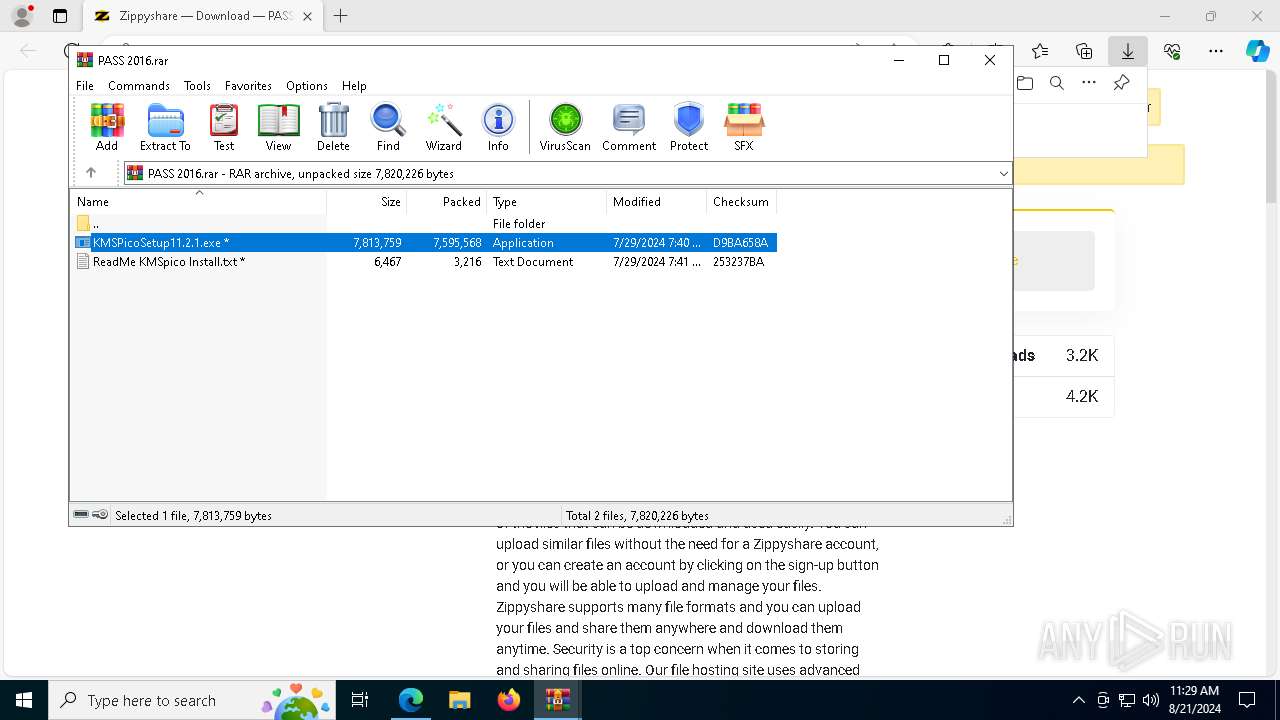
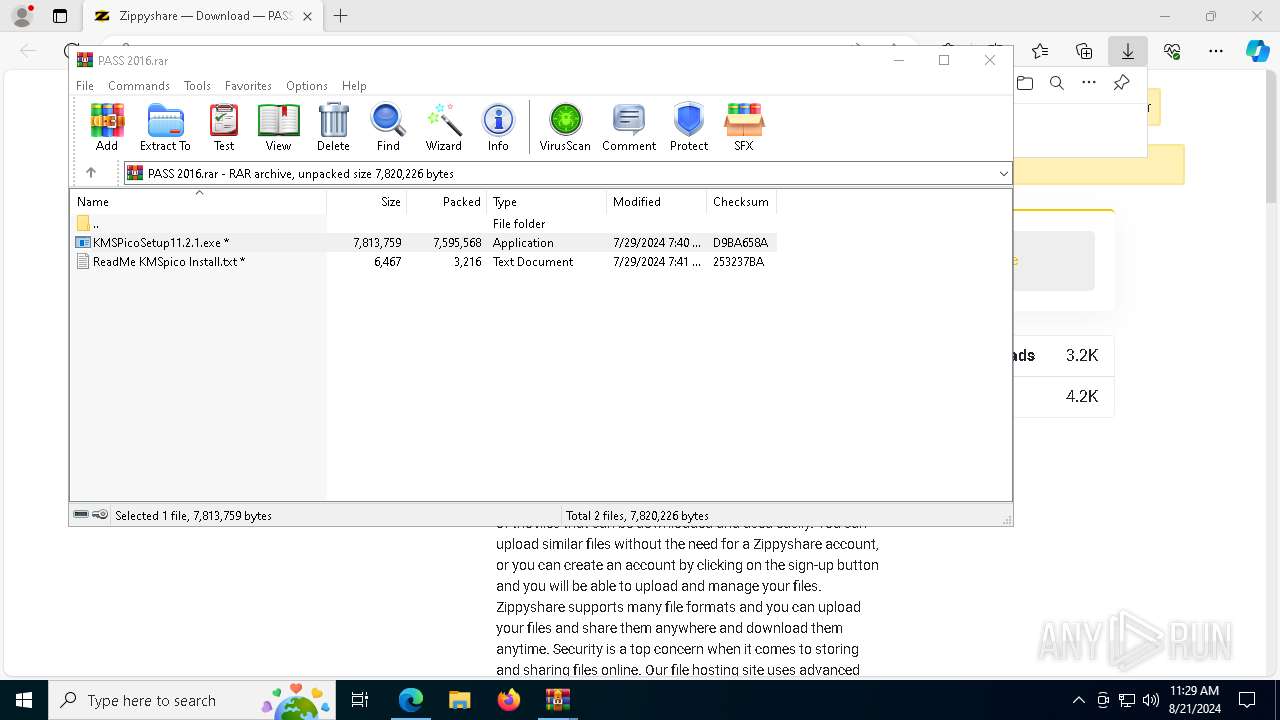
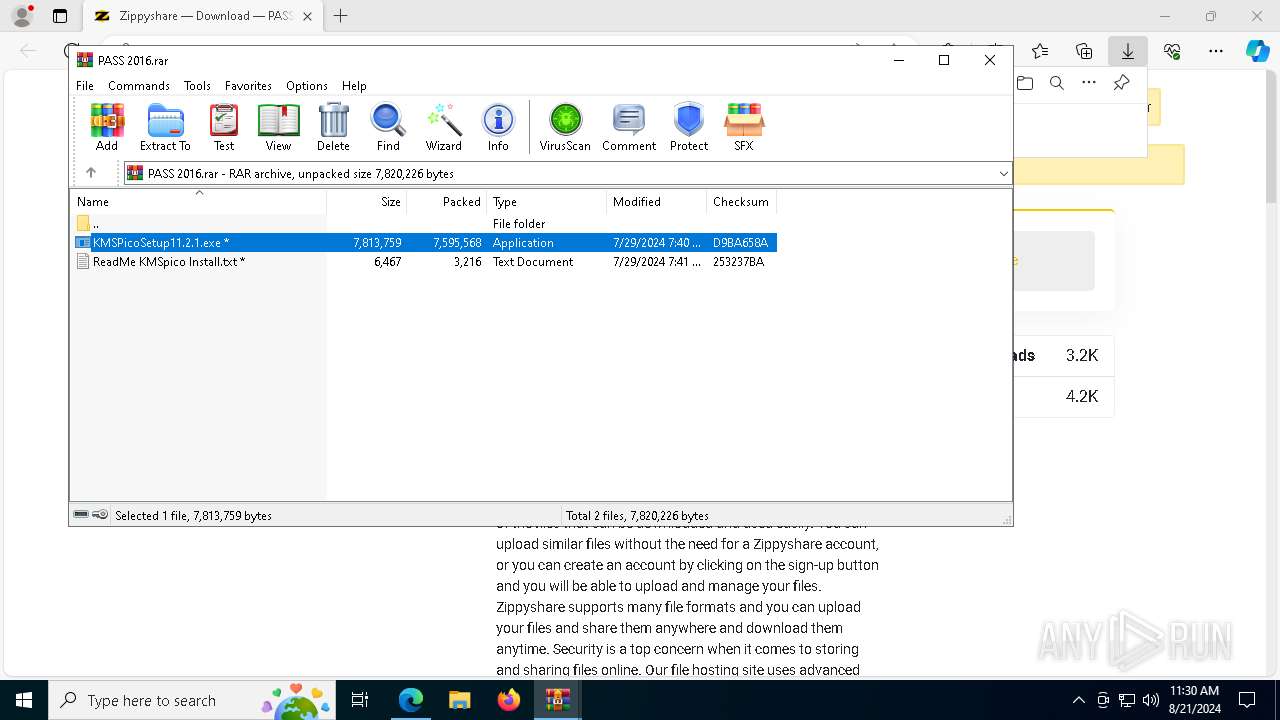
- WinRAR.exe (PID: 7360)
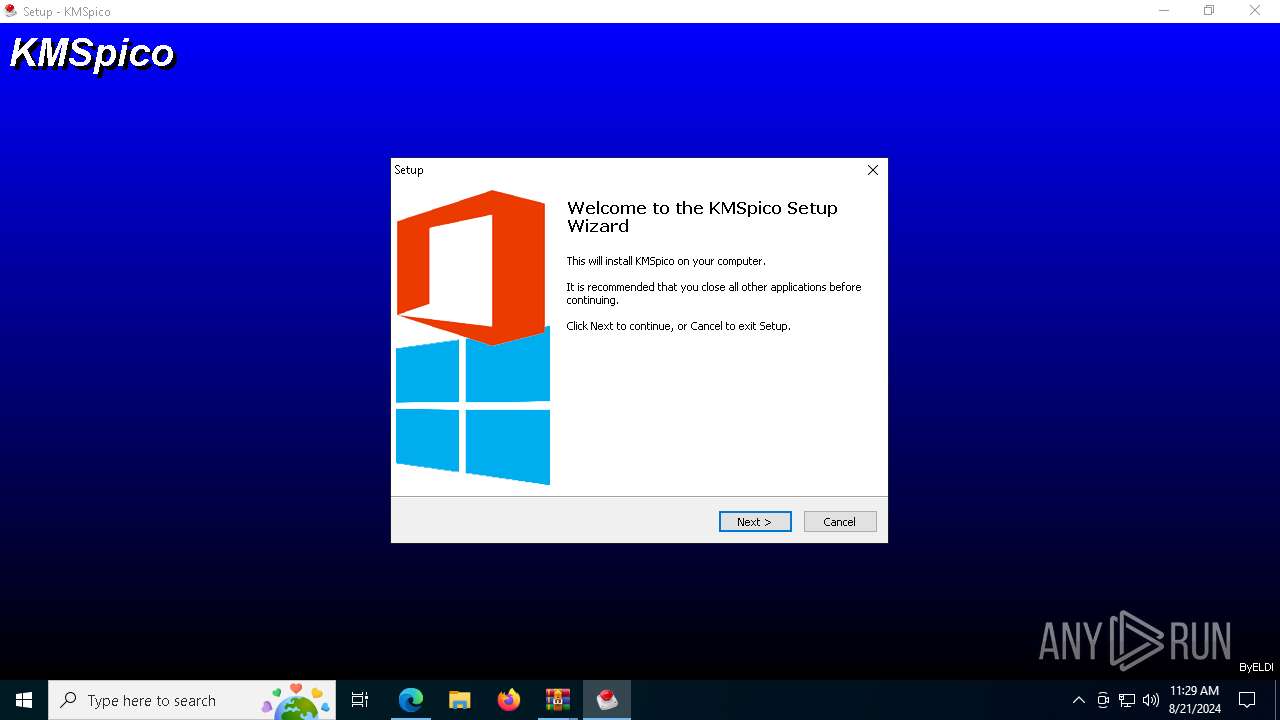
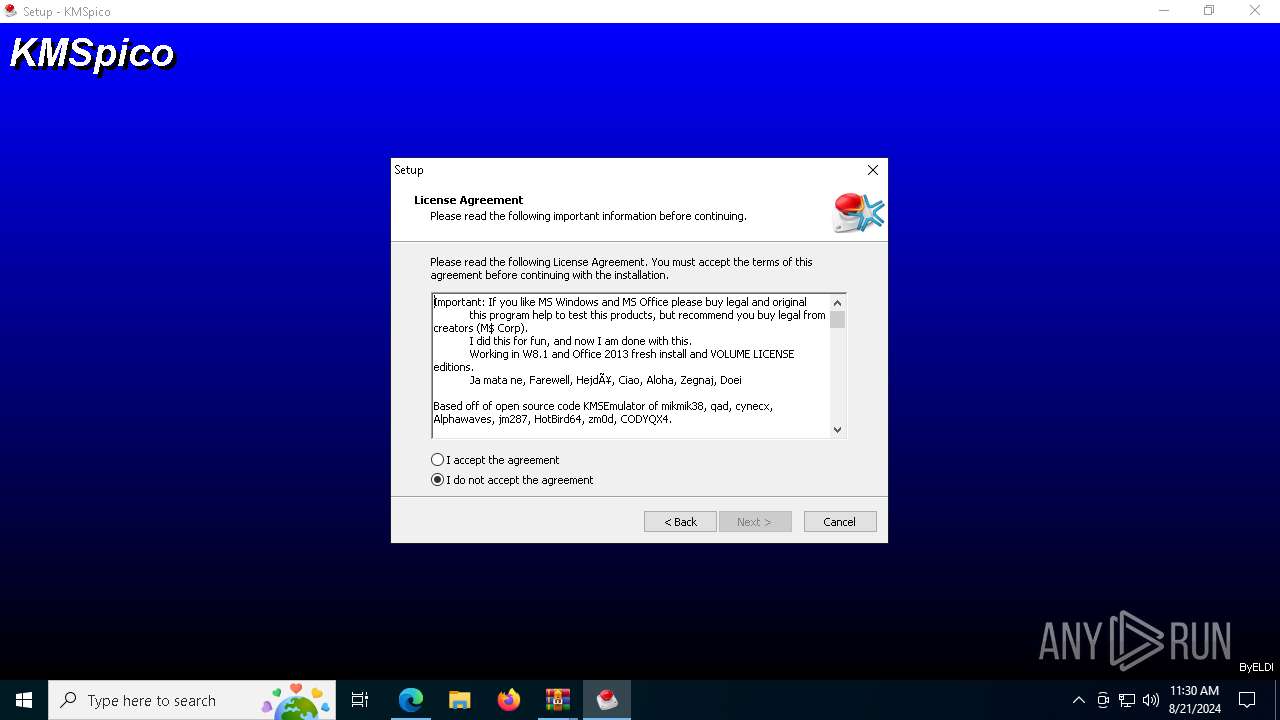
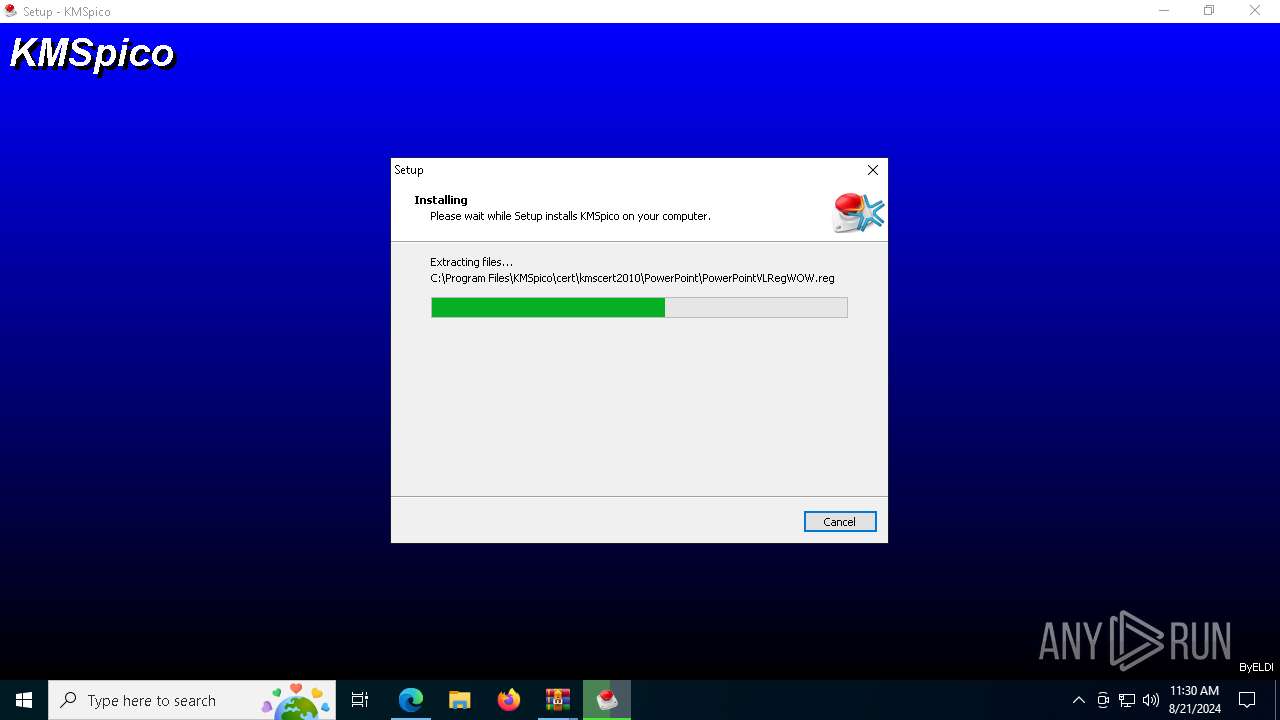
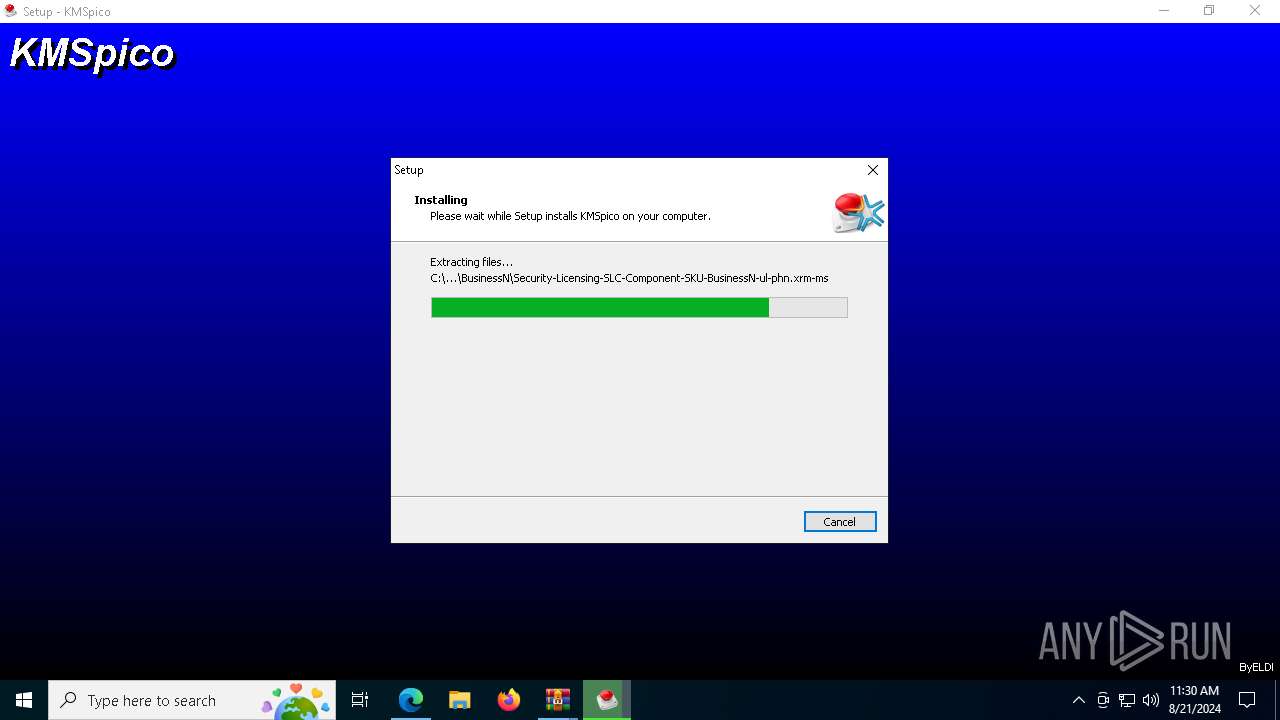
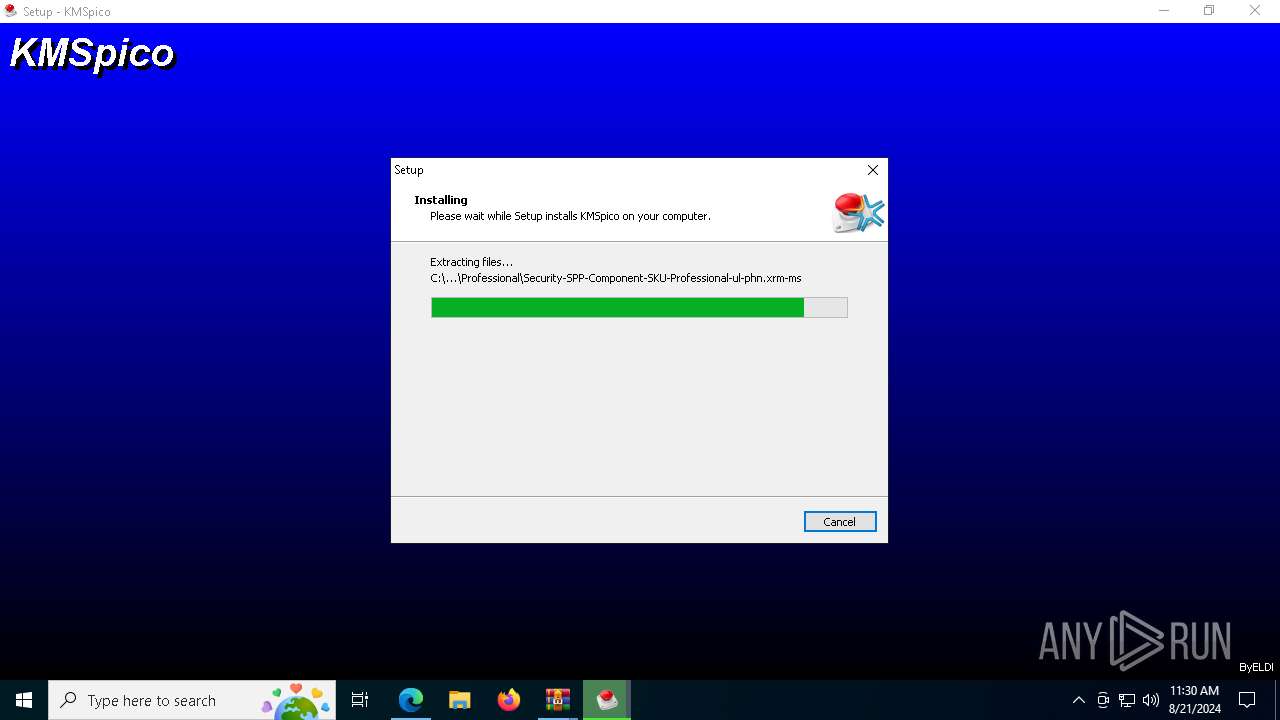
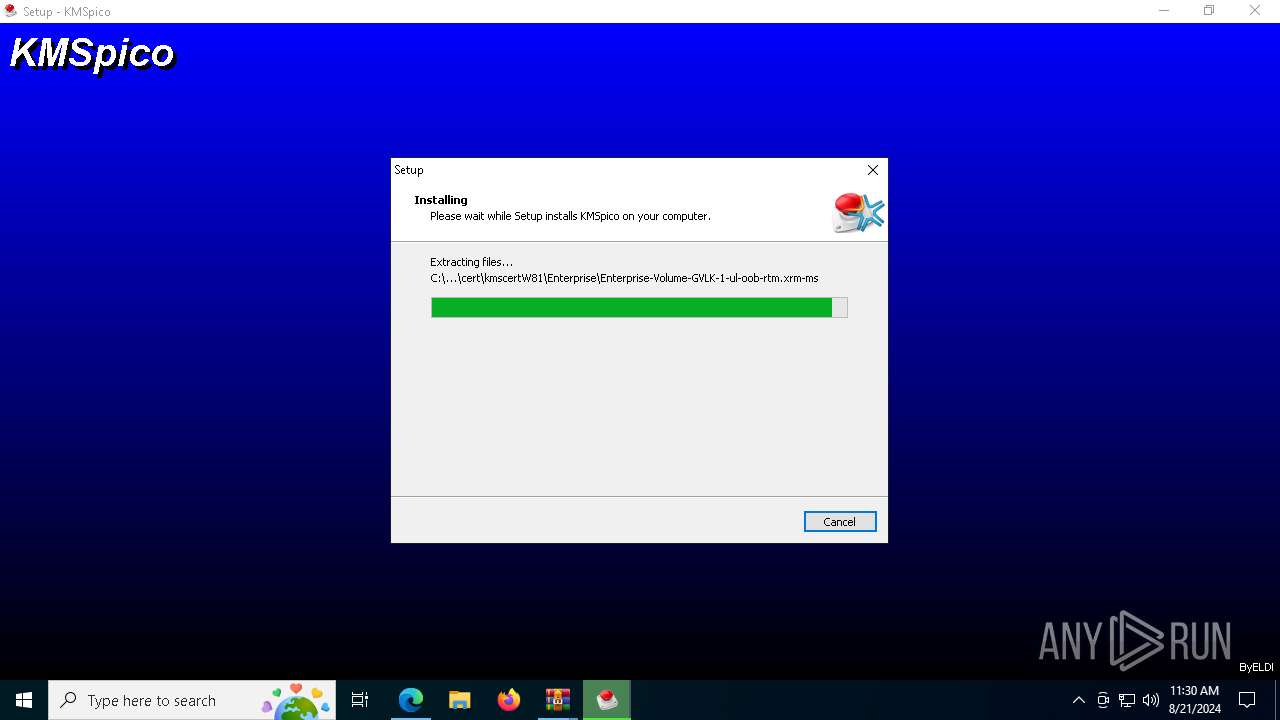
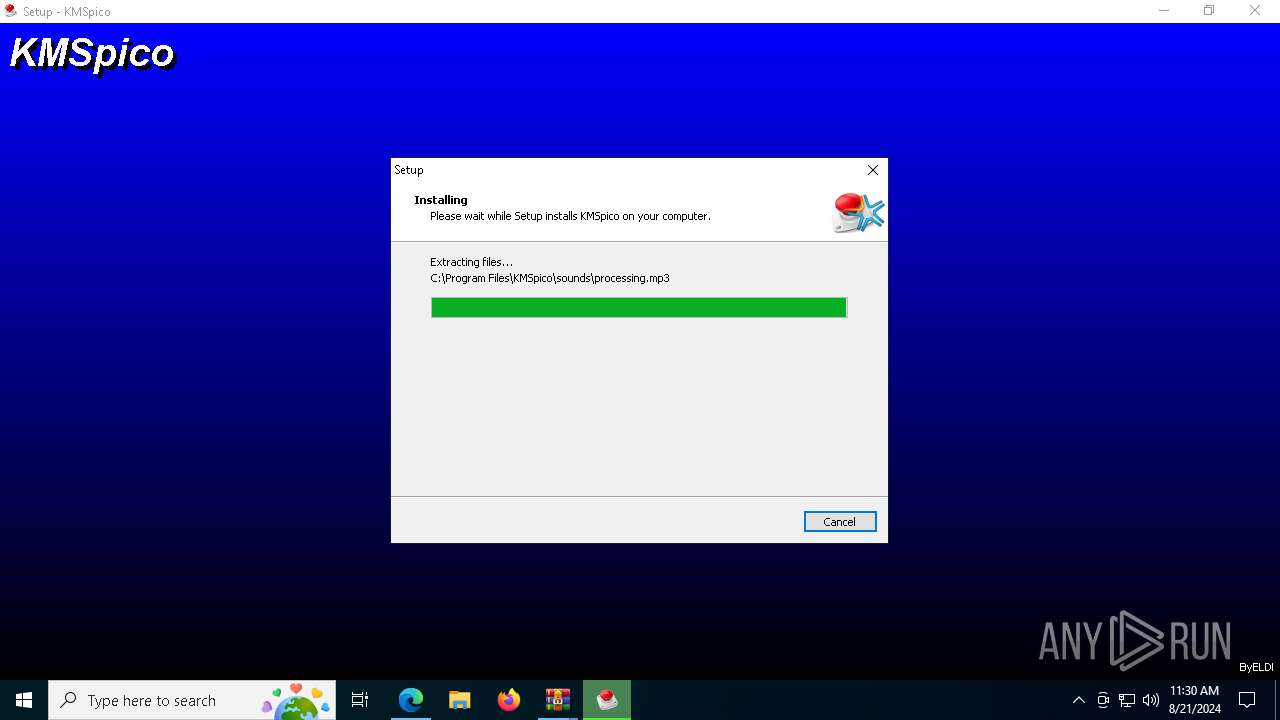
- KMSPicoSetup11.2.1.exe (PID: 7804)
- KMSpicosetup.tmp (PID: 7996)
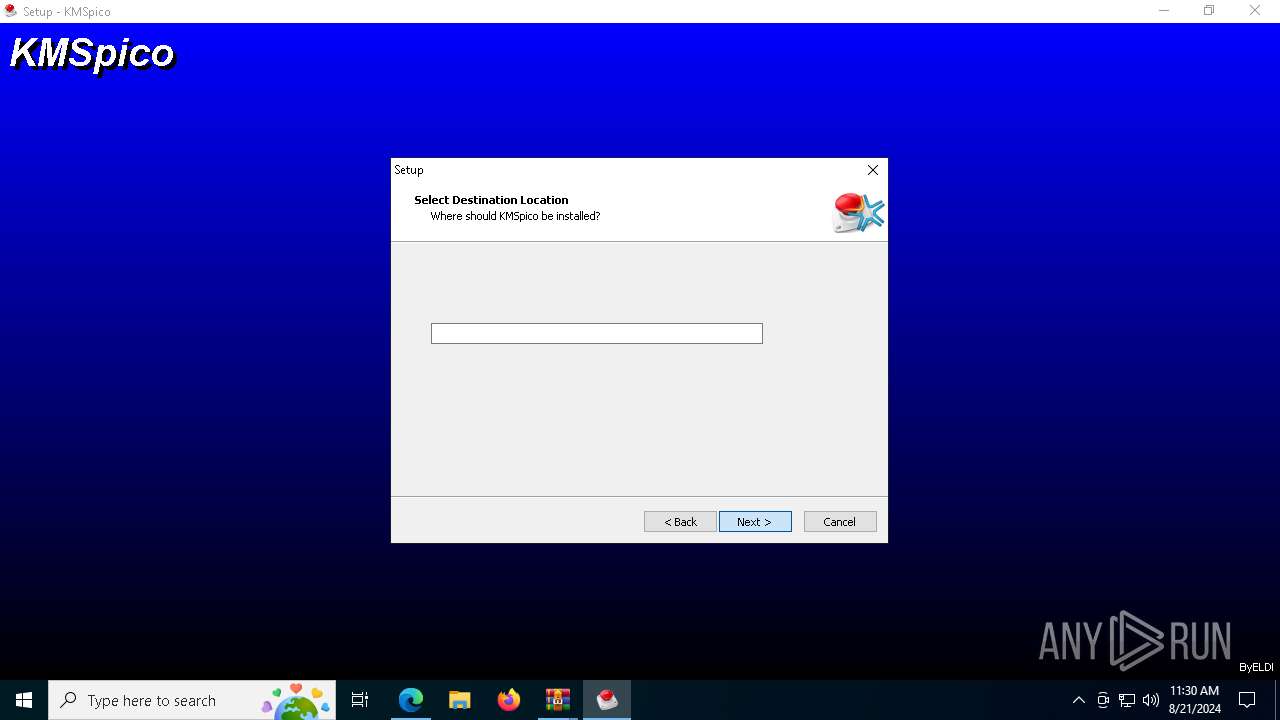
The process creates files with name similar to system file names
- KMSPicoSetup11.2.1.exe (PID: 7804)
Drops the executable file immediately after the start
- KMSPicoSetup11.2.1.exe (PID: 7804)
- KMSpicosetup.exe (PID: 4084)
- KMSpicosetup.exe (PID: 7652)
- KMSpicosetup.tmp (PID: 7684)
- RegistryHost.exe (PID: 7200)
- rkduajedzcrd.exe (PID: 8016)
- KMSELDI.exe (PID: 8064)
Executable content was dropped or overwritten
- KMSPicoSetup11.2.1.exe (PID: 7804)
- KMSpicosetup.tmp (PID: 7684)
- KMSpicosetup.exe (PID: 4084)
- KMSpicosetup.exe (PID: 7652)
- RegistryHost.exe (PID: 7200)
- rkduajedzcrd.exe (PID: 8016)
- KMSELDI.exe (PID: 8064)
Reads the date of Windows installation
- KMSPicoSetup11.2.1.exe (PID: 7804)
- KMSpicosetup.tmp (PID: 7996)
Starts POWERSHELL.EXE for commands execution
- RegistryHost.exe (PID: 7888)
- RegistryHost.exe (PID: 7200)
- rkduajedzcrd.exe (PID: 8016)
Powershell scripting: start process
- RegistryHost.exe (PID: 7888)
Reads the Windows owner or organization settings
- KMSpicosetup.tmp (PID: 7684)
Script adds exclusion path to Windows Defender
- RegistryHost.exe (PID: 7200)
- rkduajedzcrd.exe (PID: 8016)
Script adds exclusion extension to Windows Defender
- RegistryHost.exe (PID: 7200)
- rkduajedzcrd.exe (PID: 8016)
Process uninstalls Windows update
- wusa.exe (PID: 4008)
- wusa.exe (PID: 7216)
Starts CMD.EXE for commands execution
- RegistryHost.exe (PID: 7200)
- rkduajedzcrd.exe (PID: 8016)
- KMSpicosetup.tmp (PID: 7684)
Starts SC.EXE for service management
- RegistryHost.exe (PID: 7200)
- cmd.exe (PID: 6356)
Executes as Windows Service
- rkduajedzcrd.exe (PID: 8016)
Process drops legitimate windows executable
- KMSpicosetup.tmp (PID: 7684)
Drops a system driver (possible attempt to evade defenses)
- rkduajedzcrd.exe (PID: 8016)
Modifies the phishing filter of IE
- KMSpicosetup.tmp (PID: 7684)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2256)
- explorer.exe (PID: 7736)
Connects to unusual port
- explorer.exe (PID: 7736)
Executing commands from ".cmd" file
- KMSpicosetup.tmp (PID: 7684)
Crypto Currency Mining Activity Detected
- explorer.exe (PID: 7736)
INFO
Application launched itself
- msedge.exe (PID: 6600)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6600)
- KMSELDI.exe (PID: 8064)
- AutoPico.exe (PID: 3696)
Checks supported languages
- identity_helper.exe (PID: 3256)
- KMSPicoSetup11.2.1.exe (PID: 7804)
- RegistryHost.exe (PID: 7888)
- KMSpicosetup.tmp (PID: 7996)
- KMSpicosetup.exe (PID: 7652)
- KMSpicosetup.tmp (PID: 7684)
- KMSpicosetup.exe (PID: 4084)
- rkduajedzcrd.exe (PID: 8016)
- RegistryHost.exe (PID: 7200)
- AutoPico.exe (PID: 3696)
- UninsHs.exe (PID: 6180)
- KMSELDI.exe (PID: 8064)
- SECOH-QAD.exe (PID: 7716)
Reads Environment values
- identity_helper.exe (PID: 3256)
- KMSELDI.exe (PID: 8064)
- AutoPico.exe (PID: 3696)
The process uses the downloaded file
- WinRAR.exe (PID: 7360)
- msedge.exe (PID: 6492)
- msedge.exe (PID: 6600)
Reads the computer name
- identity_helper.exe (PID: 3256)
- KMSPicoSetup11.2.1.exe (PID: 7804)
- KMSpicosetup.tmp (PID: 7996)
- KMSpicosetup.tmp (PID: 7684)
- KMSELDI.exe (PID: 8064)
- AutoPico.exe (PID: 3696)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7360)
Create files in a temporary directory
- KMSPicoSetup11.2.1.exe (PID: 7804)
- KMSpicosetup.exe (PID: 4084)
- KMSpicosetup.exe (PID: 7652)
- KMSpicosetup.tmp (PID: 7684)
Process checks computer location settings
- KMSPicoSetup11.2.1.exe (PID: 7804)
- KMSpicosetup.tmp (PID: 7996)
The executable file from the user directory is run by the Powershell process
- RegistryHost.exe (PID: 7200)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6208)
- powershell.exe (PID: 8020)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6208)
- powershell.exe (PID: 8020)
Creates files in the program directory
- RegistryHost.exe (PID: 7200)
- KMSpicosetup.tmp (PID: 7684)
- KMSELDI.exe (PID: 8064)
- AutoPico.exe (PID: 3696)
Creates a software uninstall entry
- KMSpicosetup.tmp (PID: 7684)
Reads product name
- KMSELDI.exe (PID: 8064)
- AutoPico.exe (PID: 3696)
UPX packer has been detected
- explorer.exe (PID: 7736)
Reads the machine GUID from the registry
- KMSELDI.exe (PID: 8064)
- AutoPico.exe (PID: 3696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(7736) explorer.exe
Decrypted-URLs (1)https://206.12
Total processes
236
Monitored processes
93
Malicious processes
9
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 964 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5456 --field-trial-handle=2404,i,14738368979915644630,18076518174764241718,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1564 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5856 --field-trial-handle=2404,i,14738368979915644630,18076518174764241718,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1752 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4560 --field-trial-handle=2404,i,14738368979915644630,18076518174764241718,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2388 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2400 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2508 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4328 --field-trial-handle=2404,i,14738368979915644630,18076518174764241718,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3104 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
59 133
Read events
58 911
Write events
208
Delete events
14
Modification events
| (PID) Process: | (6600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (6600) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6600) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
31
Suspicious files
320
Text files
841
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11d9e2.TMP | — | |
MD5:— | SHA256:— | |||
| 6600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11d9e2.TMP | — | |
MD5:— | SHA256:— | |||
| 6600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF11d9e2.TMP | — | |
MD5:— | SHA256:— | |||
| 6600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF11d9e2.TMP | — | |
MD5:— | SHA256:— | |||
| 6600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF11d9e2.TMP | — | |
MD5:— | SHA256:— | |||
| 6600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
140
DNS requests
106
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5740 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7452 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3992 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7fc05444-f914-468e-ba6d-4e4860ab2bdc?P1=1724830353&P2=404&P3=2&P4=lJA6E1Qmkh%2fbz0obn64Um4Q3NVwtZ9HEurmP6Ql9l1K%2ftN1eJ%2bqQYdHSIbjT7NLHtoMnbc1gbA56EGzNvZh4%2fg%3d%3d | unknown | — | — | whitelisted |
8184 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3992 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7fc05444-f914-468e-ba6d-4e4860ab2bdc?P1=1724830353&P2=404&P3=2&P4=lJA6E1Qmkh%2fbz0obn64Um4Q3NVwtZ9HEurmP6Ql9l1K%2ftN1eJ%2bqQYdHSIbjT7NLHtoMnbc1gbA56EGzNvZh4%2fg%3d%3d | unknown | — | — | whitelisted |
3992 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7fc05444-f914-468e-ba6d-4e4860ab2bdc?P1=1724830353&P2=404&P3=2&P4=lJA6E1Qmkh%2fbz0obn64Um4Q3NVwtZ9HEurmP6Ql9l1K%2ftN1eJ%2bqQYdHSIbjT7NLHtoMnbc1gbA56EGzNvZh4%2fg%3d%3d | unknown | — | — | whitelisted |
3992 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7fc05444-f914-468e-ba6d-4e4860ab2bdc?P1=1724830353&P2=404&P3=2&P4=lJA6E1Qmkh%2fbz0obn64Um4Q3NVwtZ9HEurmP6Ql9l1K%2ftN1eJ%2bqQYdHSIbjT7NLHtoMnbc1gbA56EGzNvZh4%2fg%3d%3d | unknown | — | — | whitelisted |
3992 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7fc05444-f914-468e-ba6d-4e4860ab2bdc?P1=1724830353&P2=404&P3=2&P4=lJA6E1Qmkh%2fbz0obn64Um4Q3NVwtZ9HEurmP6Ql9l1K%2ftN1eJ%2bqQYdHSIbjT7NLHtoMnbc1gbA56EGzNvZh4%2fg%3d%3d | unknown | — | — | whitelisted |
7736 | explorer.exe | POST | 200 | 50.87.175.234:80 | http://webserverupdate.com/api/endpoint.php | unknown | — | — | unknown |
3992 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7fc05444-f914-468e-ba6d-4e4860ab2bdc?P1=1724830353&P2=404&P3=2&P4=lJA6E1Qmkh%2fbz0obn64Um4Q3NVwtZ9HEurmP6Ql9l1K%2ftN1eJ%2bqQYdHSIbjT7NLHtoMnbc1gbA56EGzNvZh4%2fg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
368 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3164 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6600 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6884 | msedge.exe | 52.123.243.66:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | DE | unknown |
6884 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6884 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6884 | msedge.exe | 13.107.246.60:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6884 | msedge.exe | 217.196.52.196:443 | zippyshare.day | BRDY AS | NO | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
zippyshare.day |
| unknown |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6884 | msedge.exe | Misc activity | ET INFO Commonly Abused File Sharing Domain (wasabisys .com) in DNS Lookup |
6884 | msedge.exe | Misc activity | ET INFO Commonly Abused File Sharing Domain (wasabisys .com) in DNS Lookup |
6884 | msedge.exe | Misc activity | ET INFO Commonly Abused File Sharing Domain (wasabisys .com) in DNS Lookup |
6884 | msedge.exe | Misc activity | ET INFO Commonly Abused File Sharing Domain (wasabisys .com) in TLS SNI |
2256 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY Observed DNS Query to Coin Mining Domain (nanopool .org) |
7736 | explorer.exe | A Network Trojan was detected | ET MALWARE Win32/Amadey Host Fingerprint Exfil (POST) M3 |
7736 | explorer.exe | A Network Trojan was detected | ET MALWARE Win32/Amadey Host Fingerprint Exfil (POST) M3 |
7736 | explorer.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
7736 | explorer.exe | A Network Trojan was detected | ET MALWARE SilentCryptoMiner Agent Config Inbound |
7736 | explorer.exe | Crypto Currency Mining Activity Detected | ET MALWARE [ANY.RUN] SilentCryptoMiner Check-in POST Request |
1 ETPRO signatures available at the full report