| File name: | cd.doc |
| Full analysis: | https://app.any.run/tasks/4fa60f83-4e8d-4ce1-9180-3b5e131e097f |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | December 19, 2018, 04:31:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
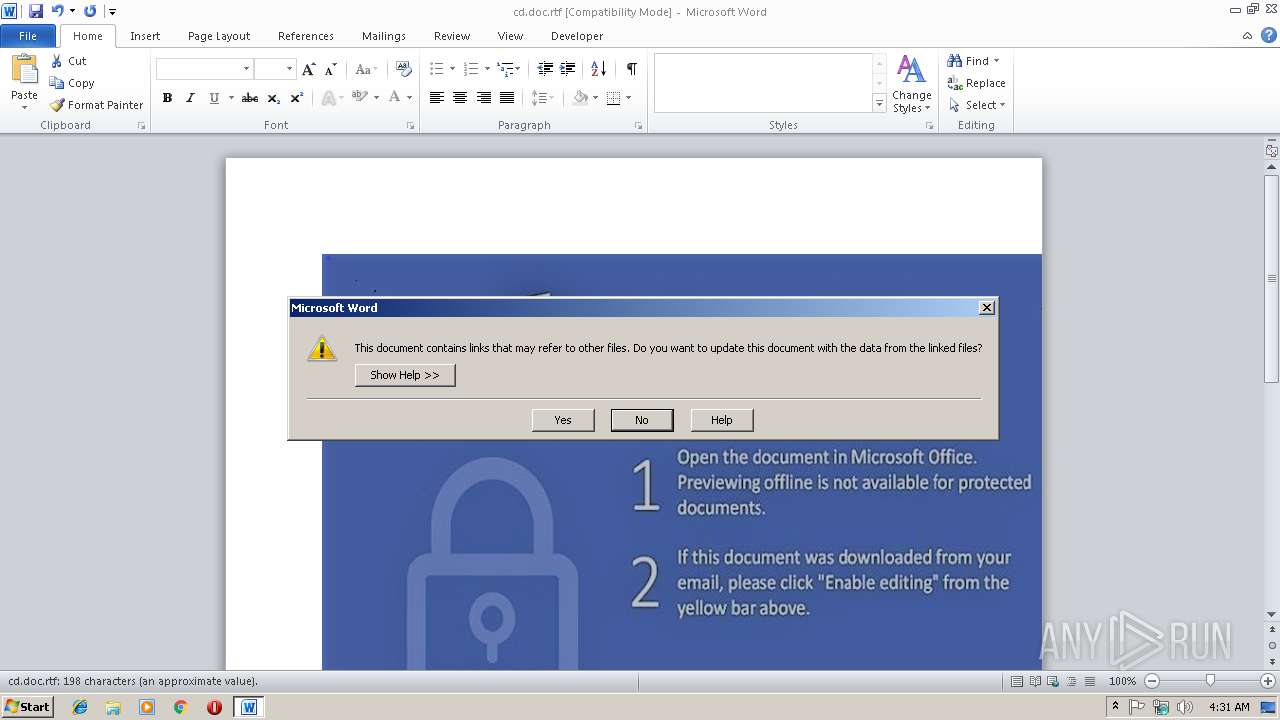
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | 550814CA4B9C3C4982EB8B6CF96D6D32 |
| SHA1: | C9140C710735BCE20F43ED942A915CBEEF9F231E |
| SHA256: | 01759673B06D831750C8F4B92690BF252344E64702220DCF3425B84E013C4BA3 |
| SSDEEP: | 12288:LZ6WO/LYDIIrPJcZMY5a8iSb0jmZVrxpwLi5C1etVGPLuKIv7w+t7+gSd:LMWMYDRCSYRomZVlGOC8ULuREwEd |
MALICIOUS
Runs app for hidden code execution
- cmd.exe (PID: 2744)
- cmd.exe (PID: 2272)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2932)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2932)
Changes the autorun value in the registry
- saver.scr (PID: 2440)
- cxdwjg4bvx8.exe (PID: 4028)
- cmmon32.exe (PID: 3008)
Loads dropped or rewritten executable
- saver.scr (PID: 2440)
- cxdwjg4bvx8.exe (PID: 4028)
- cmmon32.exe (PID: 3008)
Application was dropped or rewritten from another process
- saver.scr (PID: 2440)
- cxdwjg4bvx8.exe (PID: 4028)
- saver.scr (PID: 3124)
- cxdwjg4bvx8.exe (PID: 2532)
FORMBOOK was detected
- explorer.exe (PID: 236)
Connects to CnC server
- explorer.exe (PID: 236)
Formbook was detected
- cmmon32.exe (PID: 3008)
- Firefox.exe (PID: 3100)
Actions looks like stealing of personal data
- cmmon32.exe (PID: 3008)
Stealing of credential data
- cmd.exe (PID: 4032)
- cmmon32.exe (PID: 3008)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2740)
- cmd.exe (PID: 2272)
- cmd.exe (PID: 2744)
- cmd.exe (PID: 3032)
- cmmon32.exe (PID: 3008)
Executable content was dropped or overwritten
- cscript.exe (PID: 4080)
- saver.scr (PID: 2440)
- DllHost.exe (PID: 3440)
- explorer.exe (PID: 236)
- cxdwjg4bvx8.exe (PID: 4028)
- cmmon32.exe (PID: 3008)
Application launched itself
- cmd.exe (PID: 3032)
- saver.scr (PID: 2440)
- cxdwjg4bvx8.exe (PID: 4028)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3116)
- cmd.exe (PID: 3008)
- cmd.exe (PID: 4020)
- cmd.exe (PID: 3032)
- cmd.exe (PID: 2744)
- cmd.exe (PID: 2928)
- cmd.exe (PID: 3536)
Executes scripts
- cmd.exe (PID: 3032)
Uses TASKKILL.EXE to kill Office Apps
- cmd.exe (PID: 3032)
Starts application with an unusual extension
- cmd.exe (PID: 3032)
- saver.scr (PID: 2440)
Creates files in the user directory
- saver.scr (PID: 2440)
- cmmon32.exe (PID: 3008)
Creates files in the program directory
- DllHost.exe (PID: 3440)
Loads DLL from Mozilla Firefox
- cmmon32.exe (PID: 3008)
Uses NETSTAT.EXE to discover network connections
- explorer.exe (PID: 236)
INFO
Starts Microsoft Office Application
- explorer.exe (PID: 236)
Creates files in the user directory
- WINWORD.EXE (PID: 2932)
- Firefox.exe (PID: 3100)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
75
Monitored processes
39
Malicious processes
11
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 856 | REG QUERY "HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Word\File MRU" /v "Item 1" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2160 | /c del "C:\Users\admin\AppData\Local\Temp\saver.scr" | C:\Windows\System32\cmd.exe | — | cmmon32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2192 | TASkKILL /F /IM winword.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2272 | "C:\Windows\System32\cmd.exe" /C CmD < "C:\Users\admin\AppData\Local\Temp\ufFm.cMD" | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2384 | reg delete HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\11.0\Word\Resiliency /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2440 | "C:\Users\admin\AppData\Local\Temp\saver.scr" | C:\Users\admin\AppData\Local\Temp\saver.scr | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2508 | reg delete HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\15.0\Word\Resiliency /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Mibcd\cxdwjg4bvx8.exe" | C:\Program Files\Mibcd\cxdwjg4bvx8.exe | — | cxdwjg4bvx8.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2588 | reg delete HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\13.0\Word\Resiliency /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 924
Read events
1 878
Write events
43
Delete events
3
Modification events
| (PID) Process: | (236) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000B565F6B699A72142B34A423D67ADEB4000000000020000000000106600000001000020000000B27796CAE837387EF052DE02365DA38D41F8CA5C18713725B31672BD33CE0BD5000000000E8000000002000020000000A44D09587B1F9D9E2D708DDCF285B19C3D7FAEF89EFB4F02EA836AF3D729D6583000000067B4B06C5E3F3D3F212672F44A51325BF2D07B529CD9F82194B7537F15D1FA0D6488079E9024CA5E8F96C15C629E973140000000D67EDC05D35CD75C31930E0AFCB55DBF9C03727F724D9A35B205F2332C8709B68A4F88AF905488CC4B9C4E30E09B59D5E8A45D03183951FB63DCA4866CE07924 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | w=? |
Value: 773D3F00740B0000010000000000000000000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1301479447 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1301479568 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1301479569 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 740B000042019BB55397D40100000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 1?? |
Value: 313F3F00740B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 1?? |
Value: 313F3F00740B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
Executable files
10
Suspicious files
85
Text files
28
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA5F7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$cd.doc.rtf | pgc | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\a.ScT | xml | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\1.zip | compressed | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\itnqknf5.cmd | text | |
MD5:— | SHA256:— | |||
| 3032 | cmd.exe | C:\Users\admin\AppData\Local\Temp\_.vbs | text | |
MD5:— | SHA256:— | |||
| 4080 | cscript.exe | C:\Users\admin\AppData\Local\Temp\saver.scr | executable | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{C57A47B7-FCB2-45DA-B94F-E069594DB968}.tmp | binary | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\uffm.cmd | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
19
DNS requests
6
Threats
46
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
236 | explorer.exe | GET | — | 198.54.117.211:80 | http://www.bolavita.download/we/?_8yL2v_=BrqvsvuRj6U73QtwHd9yVlRmBSa+ONb6iZQ1cEuVGE8mL7Bn1yffz/LEymz+bSlCV37Wrw==&mfqxz=U6Ql | US | — | — | malicious |
236 | explorer.exe | GET | — | 104.24.120.221:80 | http://www.dw591.com/we/?_8yL2v_=F39vZ10doz5Og+6Zx+4d25j+TNc/tqxEbEjJTlC0g0/5CzAZi470N+XaJvtTLXW5x+LjNA==&mfqxz=U6Ql | US | — | — | malicious |
236 | explorer.exe | GET | 200 | 192.64.114.224:80 | http://www.cravlop.com/we/?_8yL2v_=wTmcjo91+zBok5inC8oUfxpssPSx6OXgLNMKUqegHYAO5/ocGOpXO1mFVoGHqgoJ1vwSdg==&mfqxz=U6Ql&sql=1 | US | binary | 323 Kb | malicious |
236 | explorer.exe | POST | 404 | 192.64.114.224:80 | http://www.cravlop.com/we/ | US | html | 289 b | malicious |
236 | explorer.exe | POST | — | 198.13.123.182:80 | http://www.alphacomplexextremee.com/we/ | US | — | — | malicious |
236 | explorer.exe | POST | — | 198.13.123.182:80 | http://www.alphacomplexextremee.com/we/ | US | — | — | malicious |
236 | explorer.exe | POST | — | 23.20.239.12:80 | http://www.blockdossier.com/we/ | US | — | — | shared |
236 | explorer.exe | POST | — | 192.64.114.224:80 | http://www.cravlop.com/we/ | US | — | — | malicious |
236 | explorer.exe | POST | 404 | 192.64.114.224:80 | http://www.cravlop.com/we/ | US | html | 289 b | malicious |
236 | explorer.exe | POST | — | 198.13.123.182:80 | http://www.alphacomplexextremee.com/we/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
236 | explorer.exe | 198.54.117.211:80 | www.bolavita.download | Namecheap, Inc. | US | malicious |
236 | explorer.exe | 198.13.123.182:80 | www.alphacomplexextremee.com | Psychz Networks | US | malicious |
236 | explorer.exe | 104.24.120.221:80 | www.dw591.com | Cloudflare Inc | US | shared |
236 | explorer.exe | 192.64.114.224:80 | www.cravlop.com | Namecheap, Inc. | US | malicious |
236 | explorer.exe | 23.20.239.12:80 | www.blockdossier.com | Amazon.com, Inc. | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bolavita.download |
| malicious |
www.alphacomplexextremee.com |
| malicious |
www.cravlop.com |
| malicious |
www.ul0higuwn6.com |
| unknown |
www.dw591.com |
| malicious |
www.blockdossier.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
236 | explorer.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious HTTP-GET request with body and minimal header |
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
236 | explorer.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious HTTP-GET request with body and minimal header |
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
236 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
236 | explorer.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious HTTP-GET request with body and minimal header |
13 ETPRO signatures available at the full report