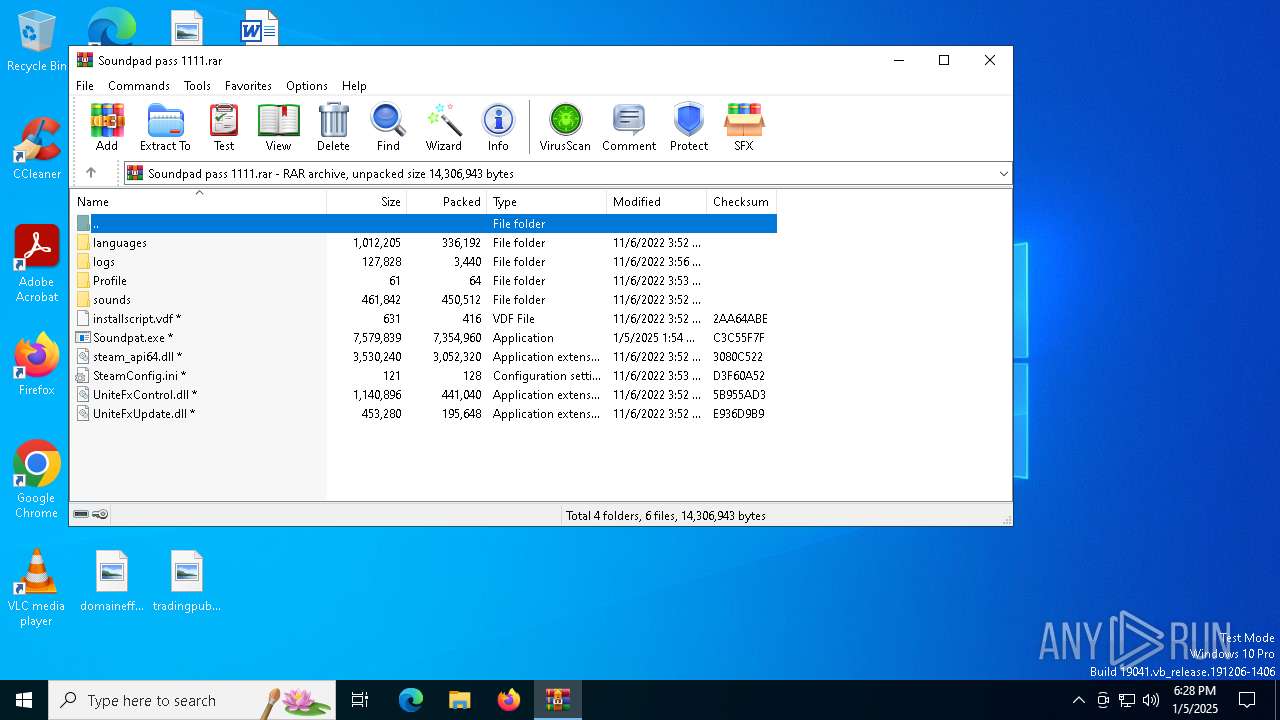
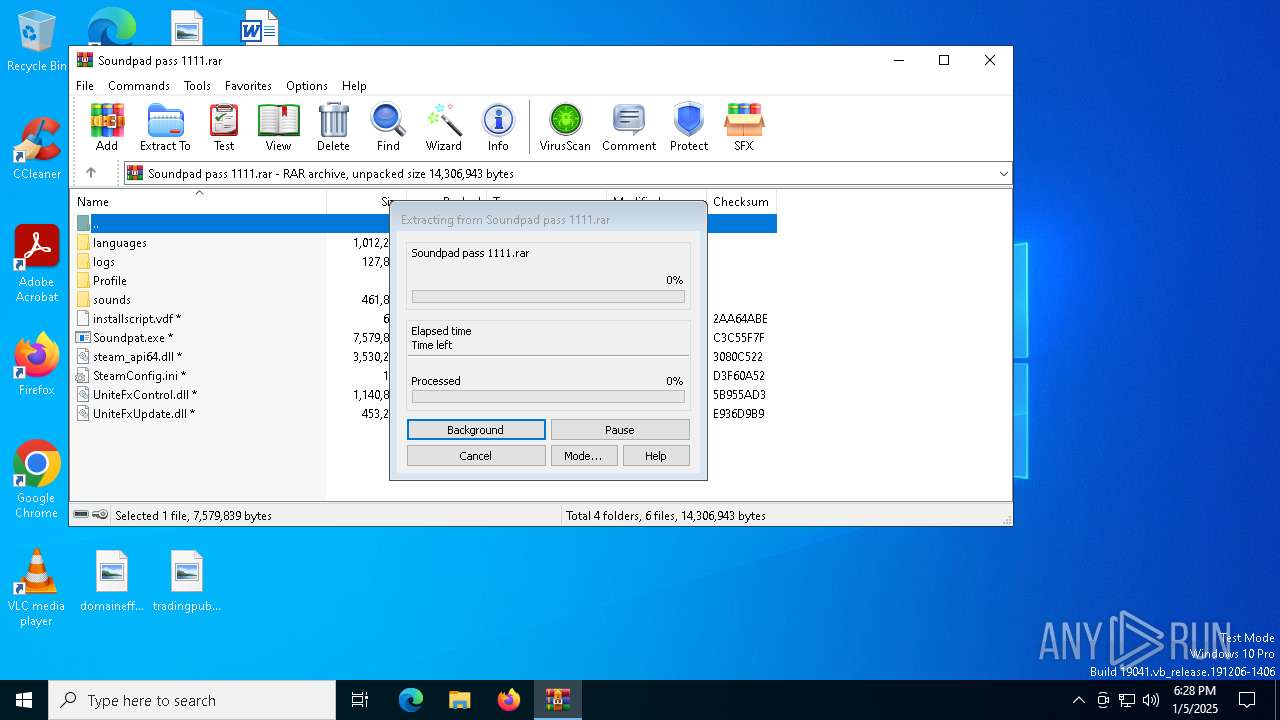
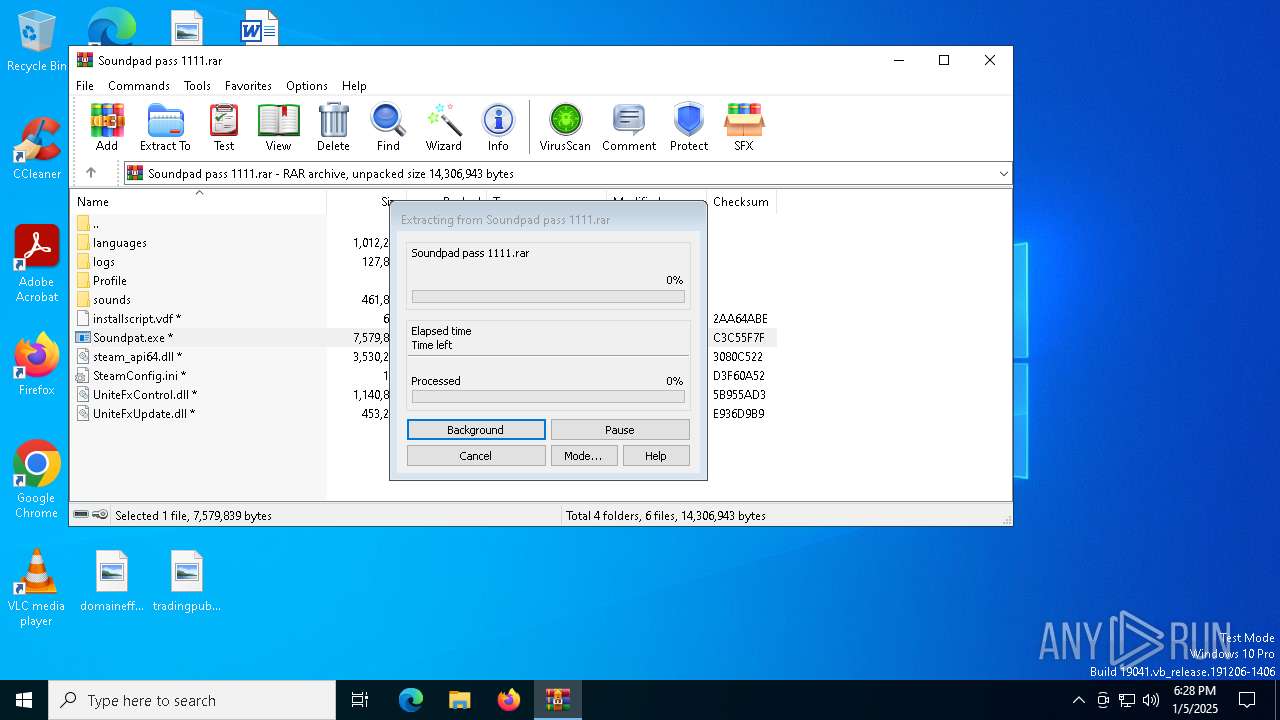
| File name: | Soundpad pass 1111.rar |
| Full analysis: | https://app.any.run/tasks/1e04b4b6-292f-42c7-8dc1-9f833106c6ed |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | January 05, 2025, 18:27:56 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 093392DF5B45FC759A5B8049F26CBB10 |
| SHA1: | D53E9A83EF2C33129AAF8DA4AFFDE7CBE64000CD |
| SHA256: | 013FB3A81634CFABBD3C3C74BB9EEC58200B96E9AD513C73C19C4A5100151A27 |
| SSDEEP: | 98304:kkoHp+JXyoU9egOa0jmkWZRdoXvxdkchuWKcqhTbeMM4rcrgMI5zokwFez3wA2nl:YyIu6Uu57HckEvWbW6zAR5 |
MALICIOUS
Orcus is detected
- RunTimeBroker.exe (PID: 5728)
- RunTimeBroker.exe (PID: 4968)
- svchost.exe (PID: 1296)
- svchost.exe (PID: 3680)
- RegAsm.exe (PID: 3664)
- svchost.exe (PID: 1144)
- InstallUtil.exe (PID: 1544)
- svchost.exe (PID: 6336)
- InstallUtil.exe (PID: 6352)
- svchost.exe (PID: 6440)
- MSBuild.exe (PID: 6476)
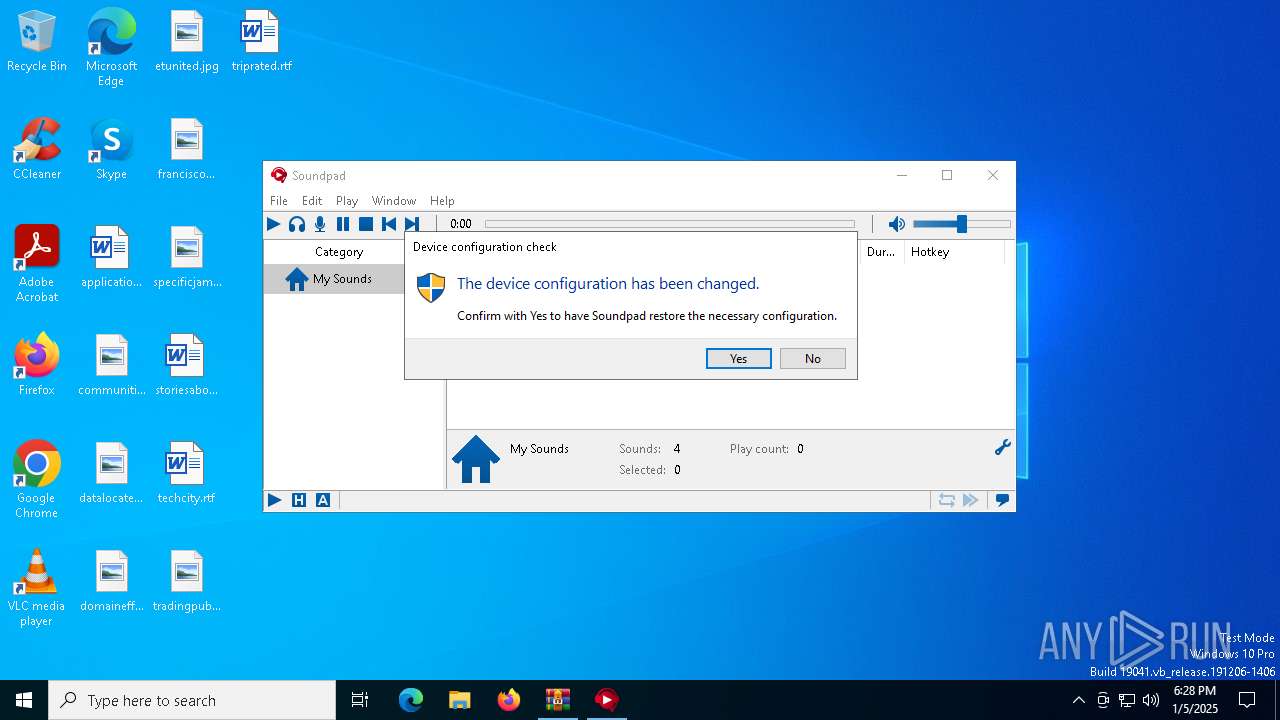
Registers / Runs the DLL via REGSVR32.EXE
- Soundpad.exe (PID: 900)
ASYNCRAT has been detected (SURICATA)
- InstallUtil.exe (PID: 1544)
Steals credentials from Web Browsers
- InstallUtil.exe (PID: 1544)
Actions looks like stealing of personal data
- InstallUtil.exe (PID: 1544)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5968)
- RunTimeBroker.exe (PID: 5728)
- Soundpad.exe (PID: 1684)
- Soundpat.exe (PID: 1224)
- RunTimeBroker.exe (PID: 4968)
- Soundpad.exe (PID: 900)
- InstallUtil.exe (PID: 1544)
Executable content was dropped or overwritten
- Soundpat.exe (PID: 1224)
- RunTimeBroker.exe (PID: 4968)
- Soundpad.exe (PID: 900)
- InstallUtil.exe (PID: 1544)
Reads Microsoft Outlook installation path
- Soundpat.exe (PID: 1224)
Reads Internet Explorer settings
- Soundpat.exe (PID: 1224)
Reads the date of Windows installation
- Soundpat.exe (PID: 1224)
- Soundpad.exe (PID: 1684)
- Soundpad.exe (PID: 900)
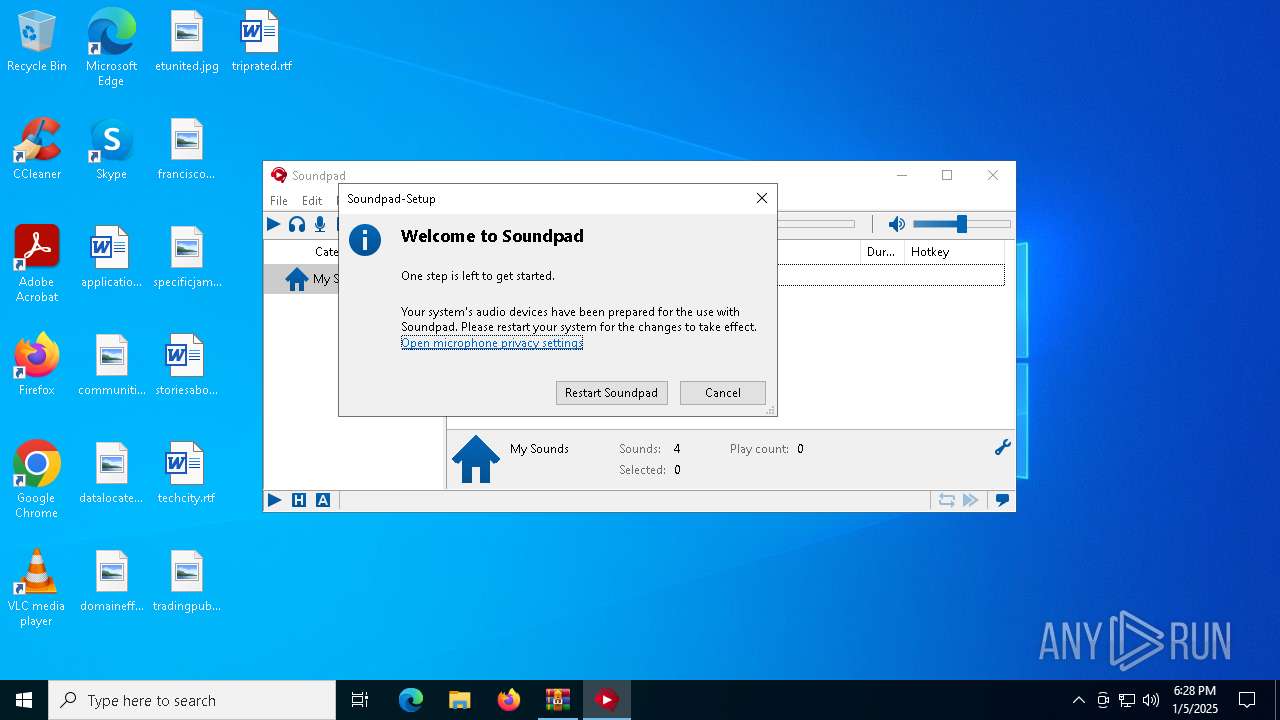
Application launched itself
- RunTimeBroker.exe (PID: 5728)
- Soundpad.exe (PID: 1684)
The process creates files with name similar to system file names
- RunTimeBroker.exe (PID: 4968)
Starts itself from another location
- RunTimeBroker.exe (PID: 4968)
The process executes via Task Scheduler
- svchost.exe (PID: 3680)
- svchost.exe (PID: 1144)
- svchost.exe (PID: 6336)
- svchost.exe (PID: 6440)
Creates/Modifies COM task schedule object
- Soundpad.exe (PID: 900)
Contacting a server suspected of hosting an CnC
- InstallUtil.exe (PID: 1544)
Connects to unusual port
- InstallUtil.exe (PID: 1544)
INFO
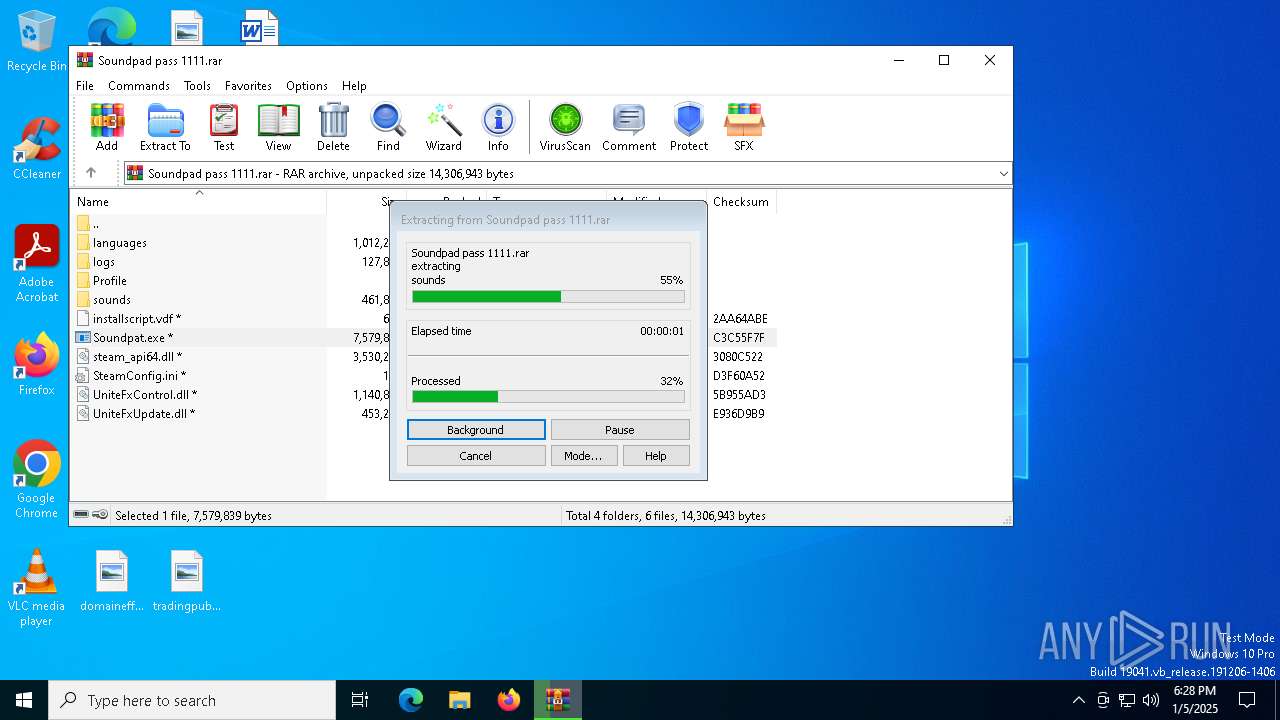
The sample compiled with chinese language support
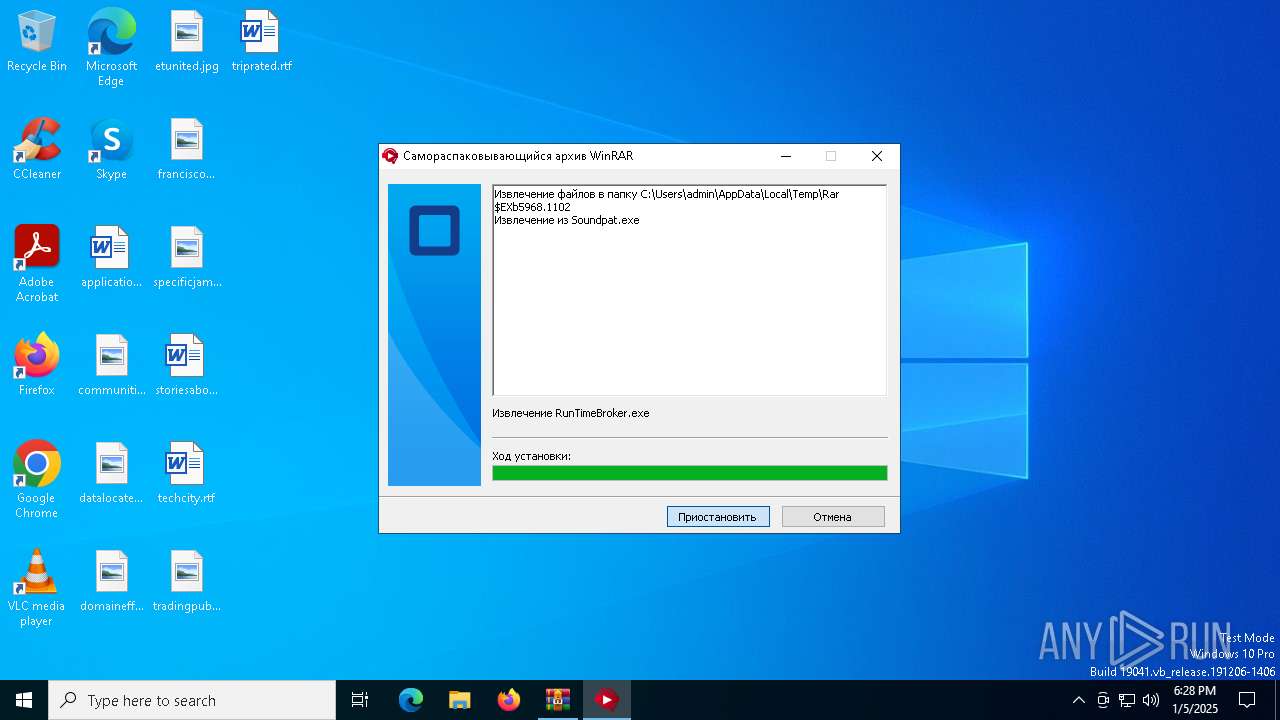
- WinRAR.exe (PID: 5968)
The process uses the downloaded file
- WinRAR.exe (PID: 5968)
- RunTimeBroker.exe (PID: 5728)
- Soundpad.exe (PID: 1684)
- Soundpat.exe (PID: 1224)
- RunTimeBroker.exe (PID: 4968)
- Soundpad.exe (PID: 900)
The sample compiled with english language support
- WinRAR.exe (PID: 5968)
- Soundpat.exe (PID: 1224)
- Soundpad.exe (PID: 900)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5968)
Reads the computer name
- Soundpat.exe (PID: 1224)
- RunTimeBroker.exe (PID: 5728)
- Soundpad.exe (PID: 1684)
- RunTimeBroker.exe (PID: 4968)
- svchost.exe (PID: 1296)
- svchost.exe (PID: 3680)
- RegAsm.exe (PID: 3664)
- Soundpad.exe (PID: 900)
- svchost.exe (PID: 1144)
- InstallUtil.exe (PID: 1544)
- svchost.exe (PID: 6336)
- MSBuild.exe (PID: 6476)
- InstallUtil.exe (PID: 6352)
- svchost.exe (PID: 6440)
Checks proxy server information
- Soundpat.exe (PID: 1224)
Checks supported languages
- Soundpat.exe (PID: 1224)
- RunTimeBroker.exe (PID: 5728)
- Soundpad.exe (PID: 1684)
- RunTimeBroker.exe (PID: 4968)
- svchost.exe (PID: 1296)
- RegAsm.exe (PID: 3664)
- svchost.exe (PID: 3680)
- svchost.exe (PID: 1144)
- InstallUtil.exe (PID: 1544)
- Soundpad.exe (PID: 900)
- svchost.exe (PID: 6336)
- InstallUtil.exe (PID: 6352)
- MSBuild.exe (PID: 6476)
- svchost.exe (PID: 6440)
Create files in a temporary directory
- Soundpat.exe (PID: 1224)
Process checks computer location settings
- Soundpat.exe (PID: 1224)
- RunTimeBroker.exe (PID: 5728)
- Soundpad.exe (PID: 1684)
- RunTimeBroker.exe (PID: 4968)
- Soundpad.exe (PID: 900)
Reads the machine GUID from the registry
- RunTimeBroker.exe (PID: 5728)
- RunTimeBroker.exe (PID: 4968)
- svchost.exe (PID: 1296)
- svchost.exe (PID: 3680)
- RegAsm.exe (PID: 3664)
- InstallUtil.exe (PID: 1544)
- svchost.exe (PID: 1144)
- svchost.exe (PID: 6336)
- InstallUtil.exe (PID: 6352)
- svchost.exe (PID: 6440)
- MSBuild.exe (PID: 6476)
Creates files or folders in the user directory
- RunTimeBroker.exe (PID: 4968)
- InstallUtil.exe (PID: 1544)
Reads the software policy settings
- InstallUtil.exe (PID: 1544)
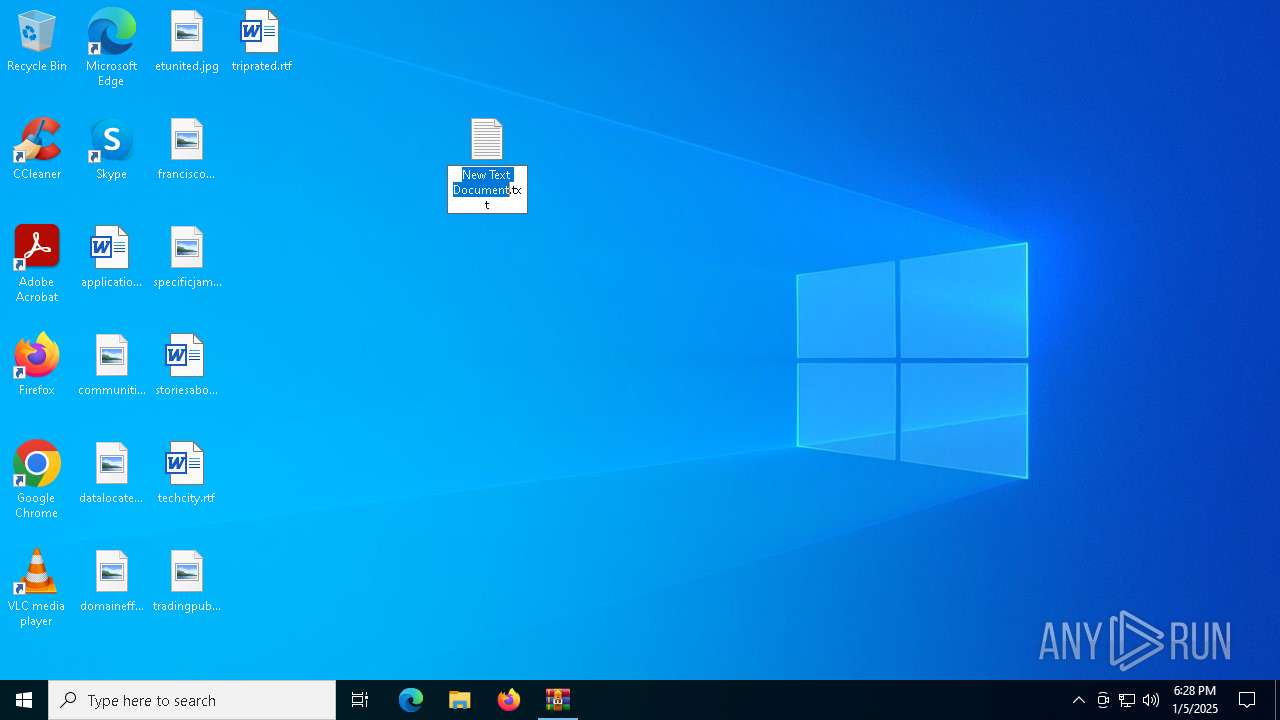
Manual execution by a user
- notepad.exe (PID: 6688)
- notepad.exe (PID: 6724)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 17712 |
| UncompressedSize: | 49942 |
| OperatingSystem: | Win32 |
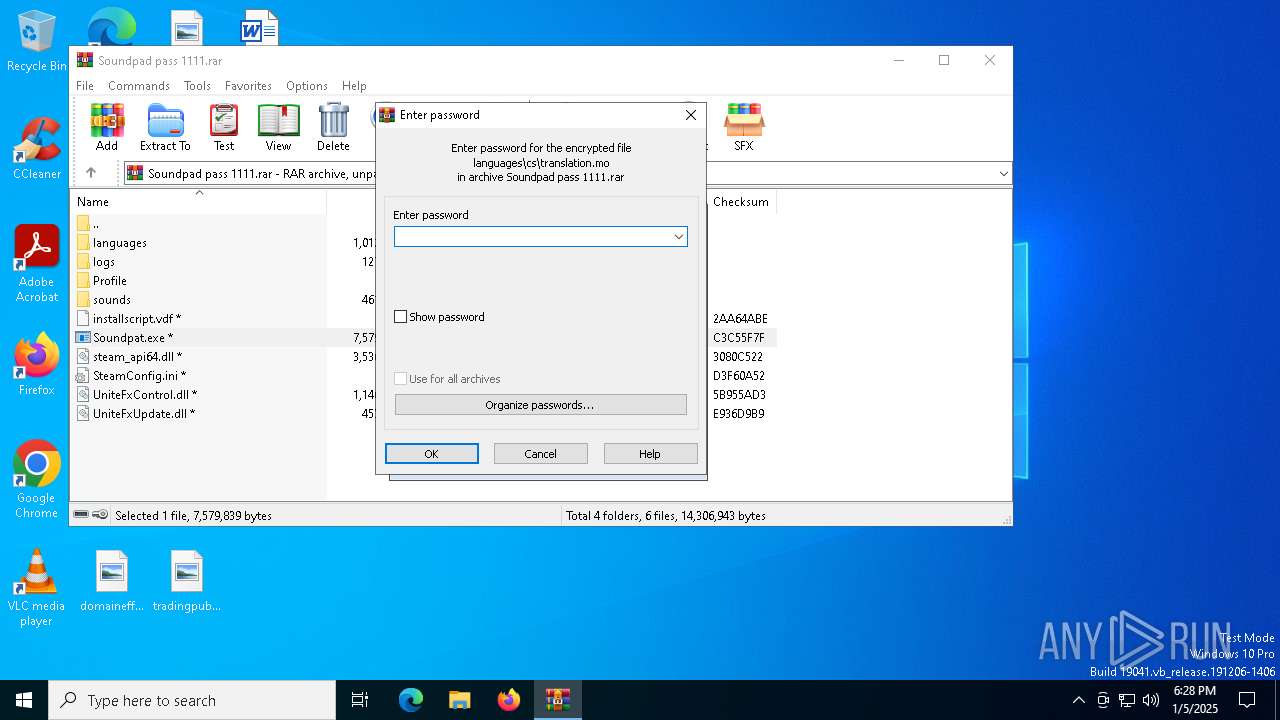
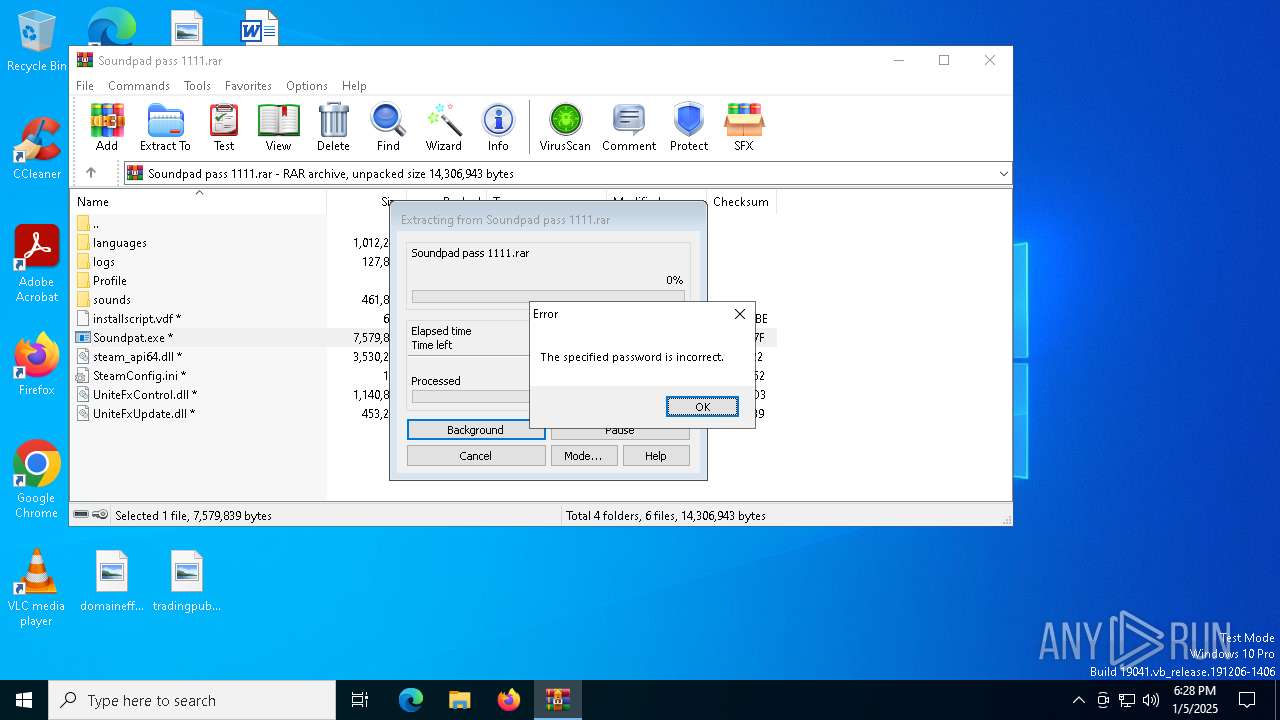
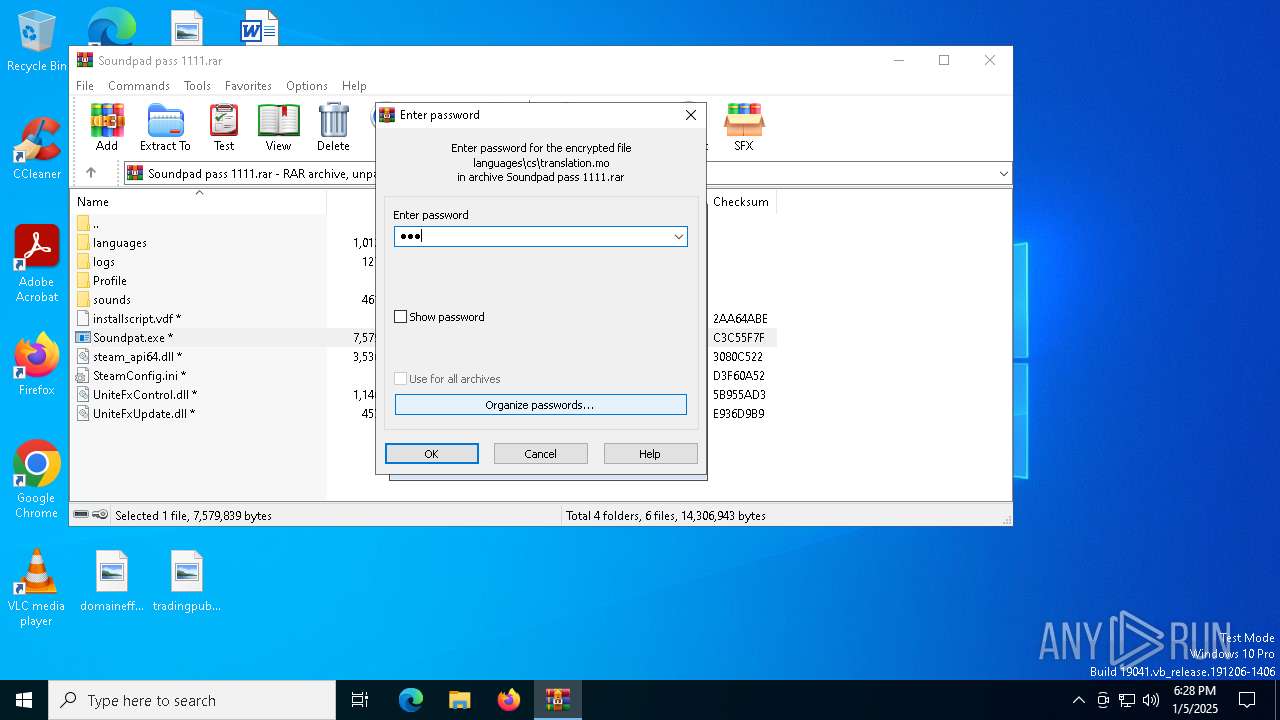
| ArchivedFileName: | languages/cs/translation.mo |
Total processes
142
Monitored processes
21
Malicious processes
14
Suspicious processes
1
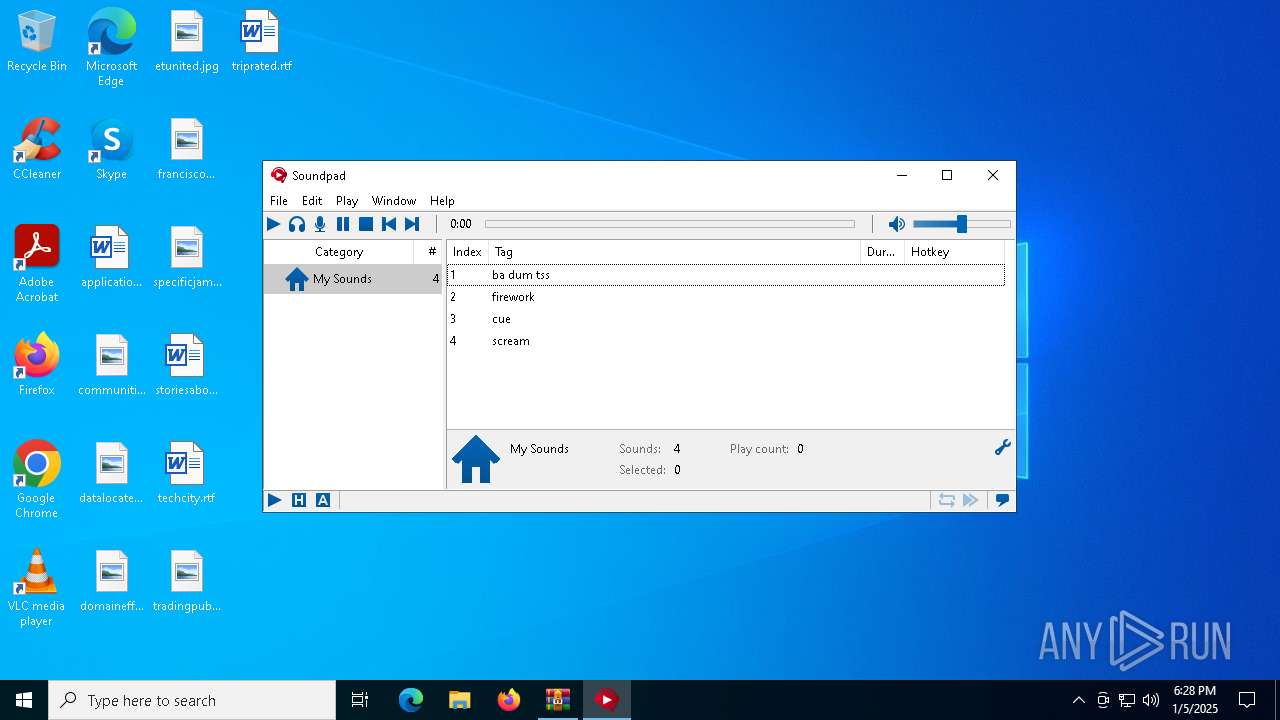
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
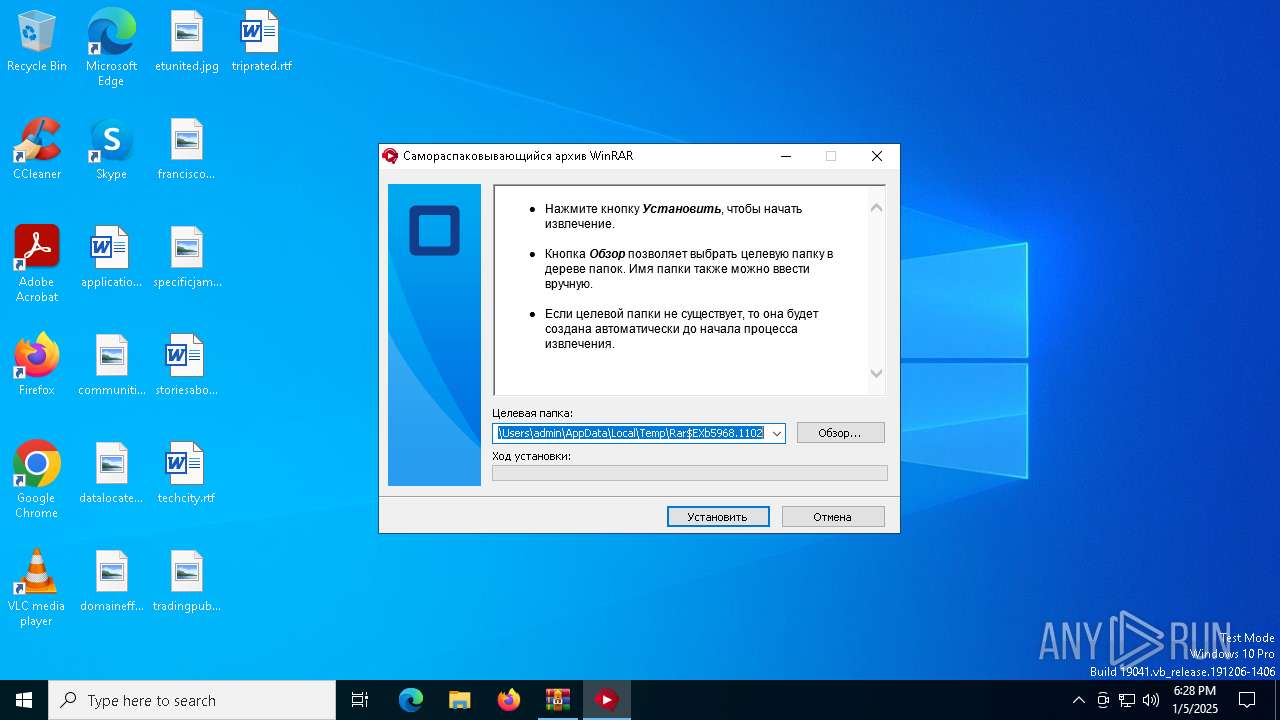
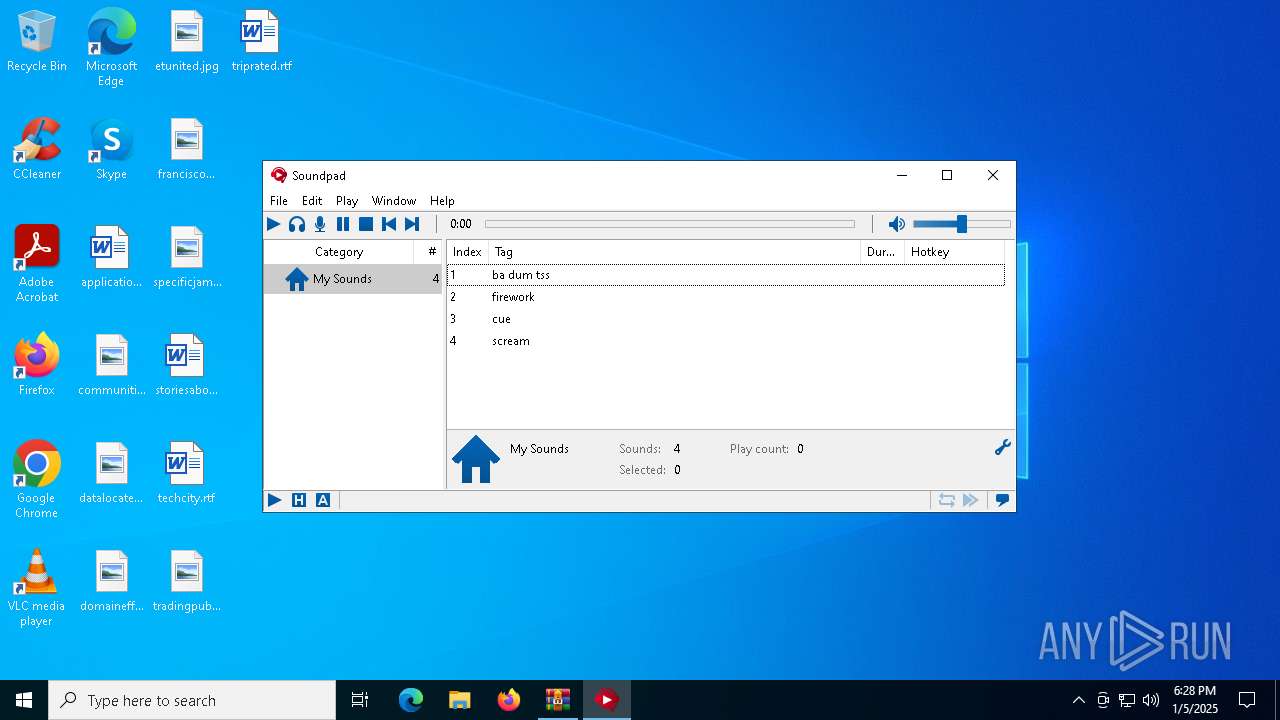
| 900 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb5968.1102\Soundpad.exe" -r | C:\Users\admin\AppData\Local\Temp\Rar$EXb5968.1102\Soundpad.exe | Soundpad.exe | ||||||||||||
User: admin Company: Leppsoft Integrity Level: HIGH Description: Soundpad Exit code: 0 Version: 3.1.8 Modules
| |||||||||||||||
| 1144 | "C:\Users\admin\AppData\Roaming\uploadsdatalife\svchost.exe" | C:\Users\admin\AppData\Roaming\uploadsdatalife\svchost.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1224 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb5968.1102\Soundpat.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb5968.1102\Soundpat.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1296 | "C:\Users\admin\AppData\Roaming\uploadsdatalife\svchost.exe" | C:\Users\admin\AppData\Roaming\uploadsdatalife\svchost.exe | RunTimeBroker.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1544 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\installutil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Framework installation utility Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1684 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb5968.1102\Soundpad.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb5968.1102\Soundpad.exe | — | Soundpat.exe | |||||||||||
User: admin Company: Leppsoft Integrity Level: MEDIUM Description: Soundpad Exit code: 0 Version: 3.1.8 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3664 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\regasm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 3680 | "C:\Users\admin\AppData\Roaming\uploadsdatalife\svchost.exe" | C:\Users\admin\AppData\Roaming\uploadsdatalife\svchost.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4968 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb5968.1102\RunTimeBroker.exe" /wait | C:\Users\admin\AppData\Local\Temp\Rar$EXb5968.1102\RunTimeBroker.exe | RunTimeBroker.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
14 822
Read events
14 639
Write events
162
Delete events
21
Modification events
| (PID) Process: | (5968) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5968) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5968) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5968) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Soundpad pass 1111.rar | |||
| (PID) Process: | (5968) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5968) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5968) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5968) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5968) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (1224) Soundpat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
9
Suspicious files
35
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb5968.1102\languages\fi\translation.mo | binary | |
MD5:05561F37A16002C2CA8F65FAEF7D1749 | SHA256:8DCF58474FC5AB1514461E1F9B8E336EF0C13B49F26F7BCEB14D477DA7A85B6A | |||
| 5968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb5968.1102\languages\ko\translation.mo | binary | |
MD5:9F0282E5E1E42E196A48261F57247637 | SHA256:DD6D1DACEF96225413043914FB7AE5BEABAFC72969B6312E47DCE033896C32FC | |||
| 5968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb5968.1102\languages\it\translation.mo | binary | |
MD5:896A7D5D126E4473CEDF237B76DBFAE6 | SHA256:9E5FB77ABBC5B636CCA97637A07C9D40E03AF74981AFA2835900E3B65BEEAF38 | |||
| 5968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb5968.1102\logs\UniteFxControl.log | text | |
MD5:C61DEE4F422258AFF6B560FCF8ECC4D8 | SHA256:DAA9616B4DE8C30B553973C9A17EE141F219C1EC4A405A36366F75EAA5D1A88D | |||
| 5968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb5968.1102\languages\tr\translation.mo | binary | |
MD5:8496AD5A2C4CC1506772F1CFF085058A | SHA256:9FF0671E01612351D1B27C169FB70A8D8D822457E31E75BB273256495602A165 | |||
| 5968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb5968.1102\languages\pt_BR\translation.mo | binary | |
MD5:CFB7405E3C064B7B0EE1F044E625E29B | SHA256:408EF183013258F151C70A5F030A35E2459F7E420D94DC7BA185144B64BD7A63 | |||
| 5968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb5968.1102\languages\nb_NO\translation.mo | binary | |
MD5:EF80EC397A53A886F298D7C65143908A | SHA256:75097F60B9D5D8CD3609C809CE4B28ADC4C42A508345D2F34C1D25F2000D6919 | |||
| 5968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb5968.1102\languages\nl\translation.mo | binary | |
MD5:0046EA807DC7DF2742C6C932EBE71E84 | SHA256:E57B67E9989D3D86D835CB7164E7B9704638509C60E6E89170829F26915BBEC5 | |||
| 5968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb5968.1102\languages\zh_CN\translation.mo | binary | |
MD5:F6F021FAC65FBFC2BD6FE9E8FD5F2741 | SHA256:5AA409AC1DF27F494FF0E4447D6F8DA9D589033583D33CB5641CB5BA73CE77BC | |||
| 5968 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb5968.1102\languages\de\translation.mo | binary | |
MD5:6FF1D323C51C2ED88F05EE7FF468900F | SHA256:5220672F99B439B1DB77479AB170A5A0F2B65B4B14416B72447DED6F1EBCD40E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
34
DNS requests
16
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | svchost.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
372 | SIHClient.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
372 | SIHClient.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3820 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.21.110.146:443 | www.bing.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | svchost.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.21.110.139:443 | www.bing.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
1 ETPRO signatures available at the full report