| File name: | FivemCheat.exe |
| Full analysis: | https://app.any.run/tasks/8697a4f1-c73b-4f8a-bfaf-6ac4d97206db |
| Verdict: | Malicious activity |
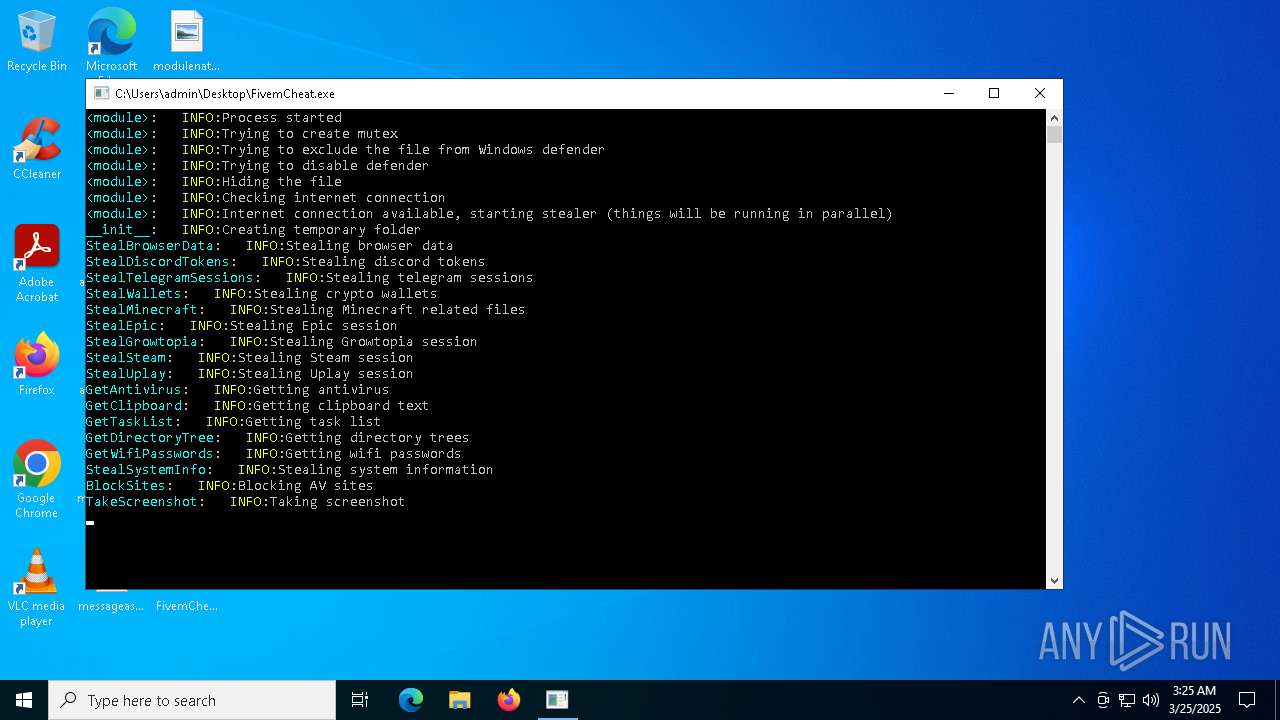
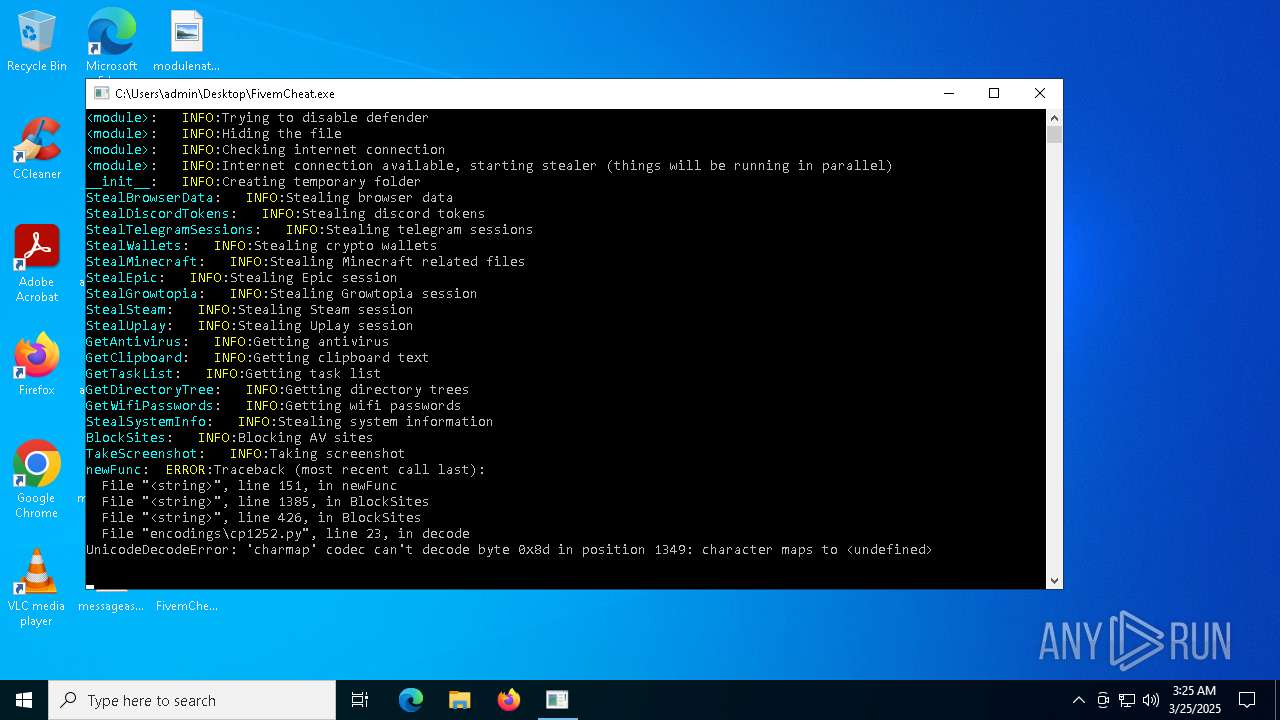
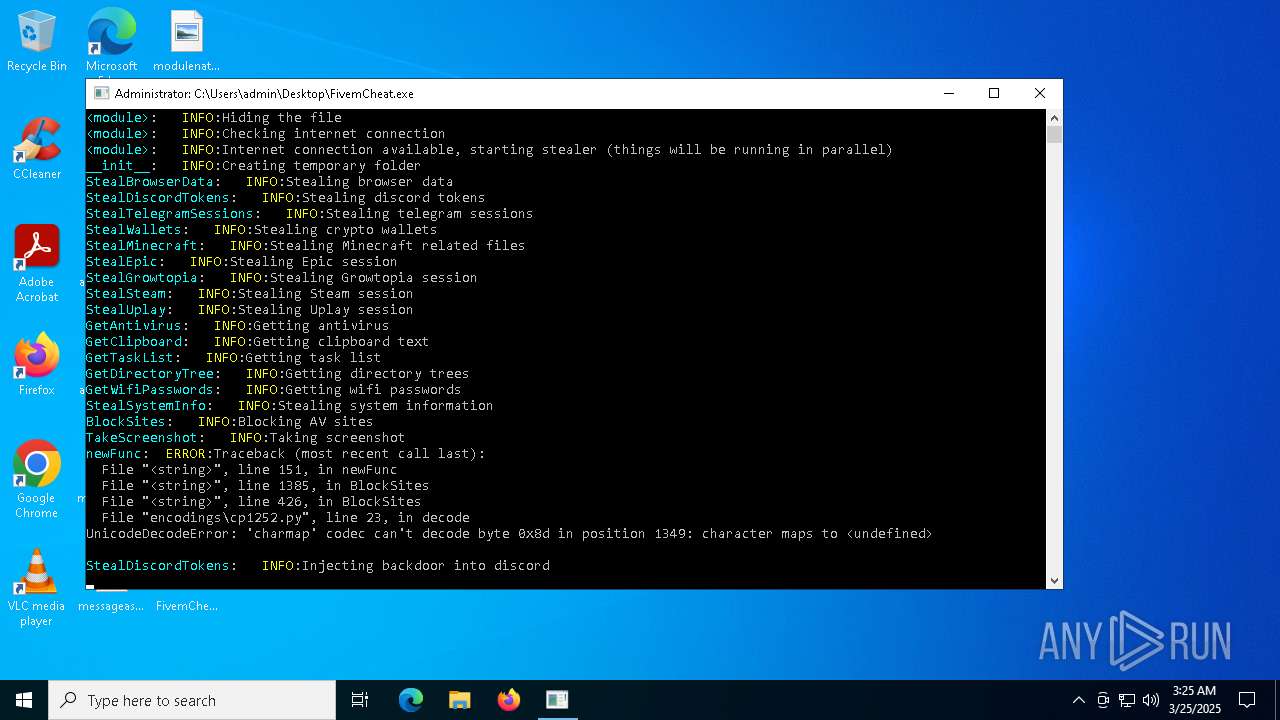
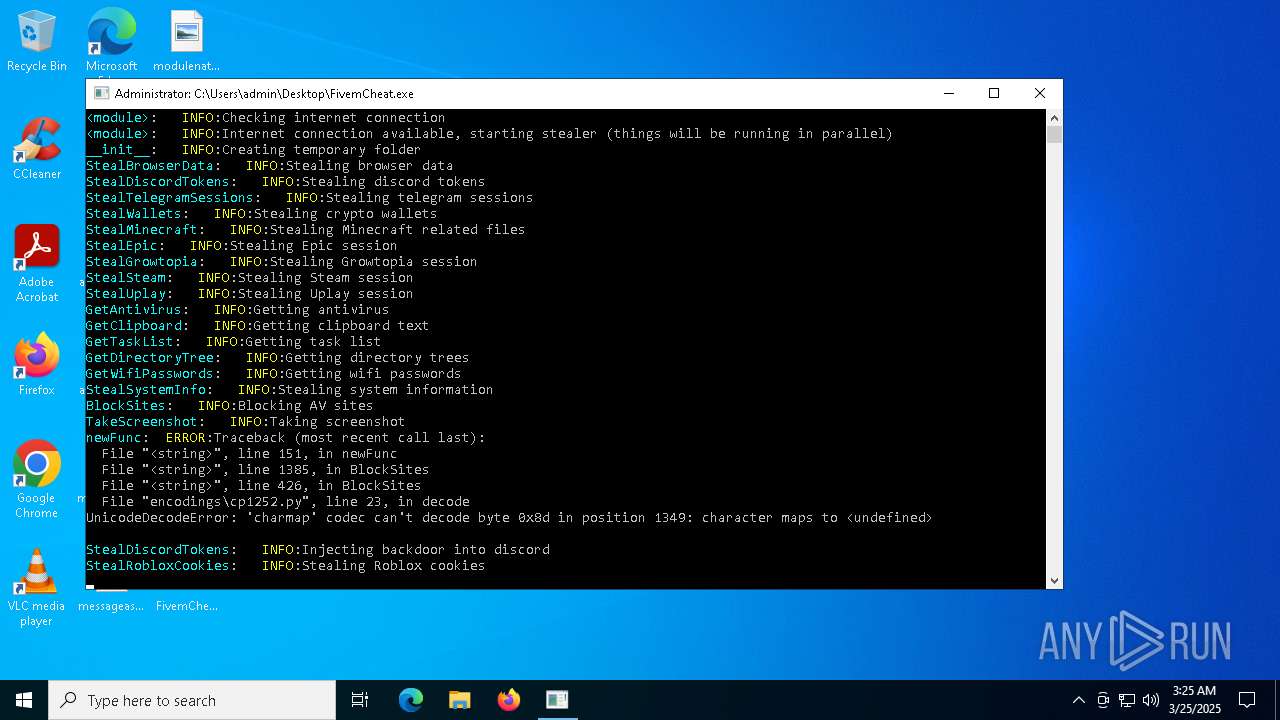
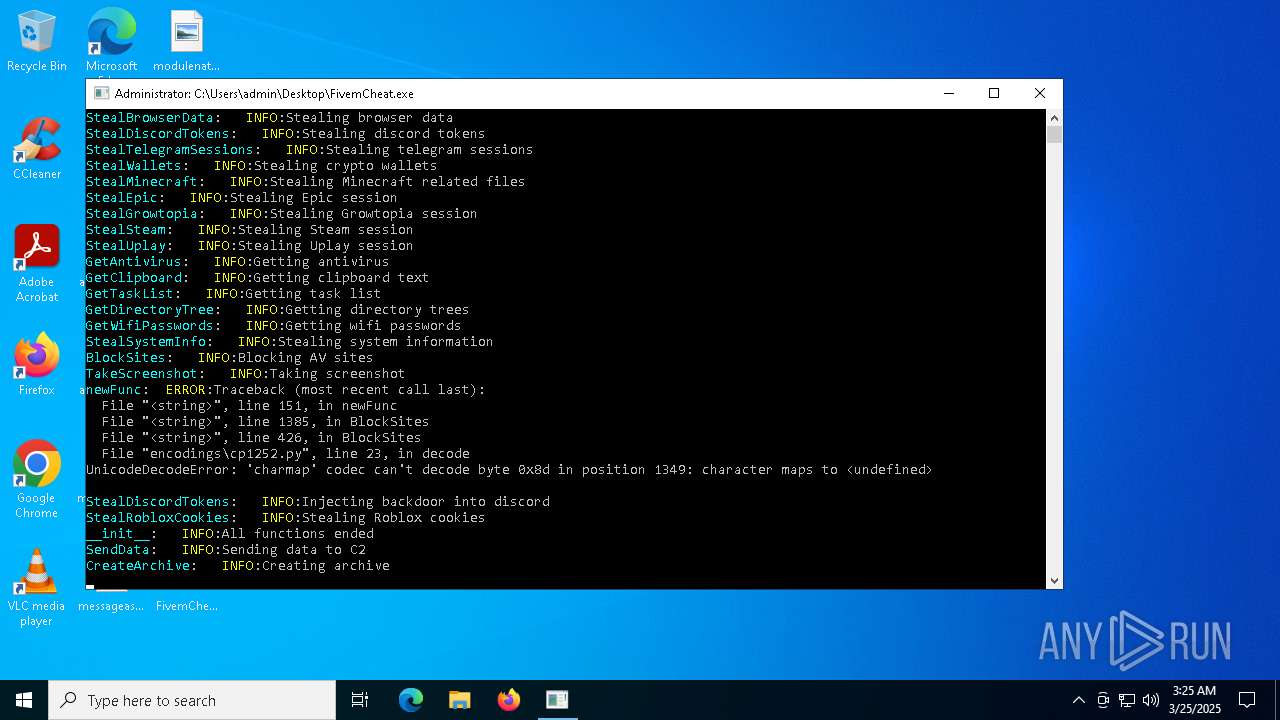
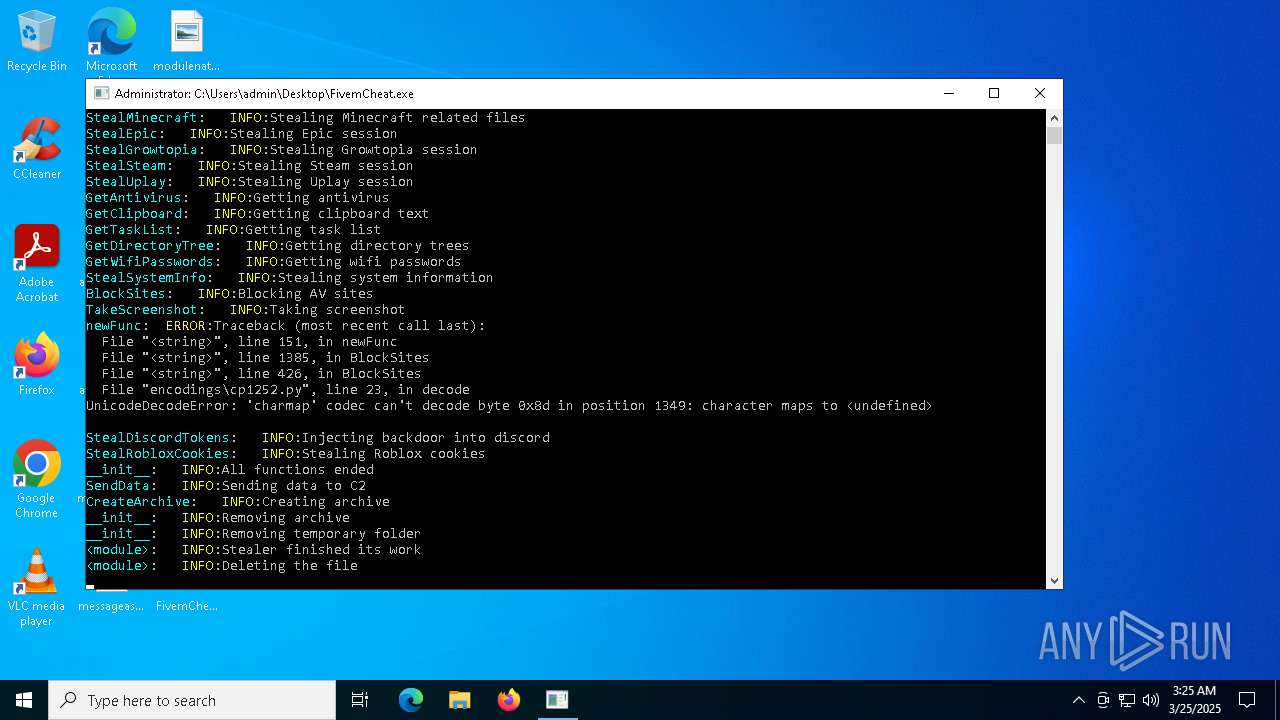
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
| Analysis date: | March 25, 2025, 03:24:53 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | A48EDA18E6D377AA7F61472D2522CAE5 |
| SHA1: | 2865A89C5492CCD1E79C75A4D44DDB0C90FE12E9 |
| SHA256: | 00B8176ED414597F955681A8DFA4BB9D45E0832469FD5EFE876C625E13F67B8A |
| SSDEEP: | 98304:1xb28yxcXL+aw10YPfpqt3/bqpuzXC5Zo4m0IN3fUtfqqQVH68DcDo0nkPle2dx2:ZO44a+nw29ekdN18E |
MALICIOUS
Executing a file with an untrusted certificate
- FivemCheat.exe (PID: 6068)
- FivemCheat.exe (PID: 5548)
- FivemCheat.exe (PID: 3192)
BlankGrabber has been detected
- FivemCheat.exe (PID: 6068)
- FivemCheat.exe (PID: 5548)
Bypass User Account Control (Modify registry)
- reg.exe (PID: 1348)
Bypass User Account Control (ComputerDefaults)
- ComputerDefaults.exe (PID: 960)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 6488)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 5392)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 2432)
- FivemCheat.exe (PID: 3192)
Changes Windows Defender settings
- cmd.exe (PID: 2432)
- cmd.exe (PID: 6488)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 5392)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 5392)
Changes Controlled Folder Access settings
- powershell.exe (PID: 5392)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 5392)
Changes settings for real-time protection
- powershell.exe (PID: 5392)
Steals credentials from Web Browsers
- FivemCheat.exe (PID: 3192)
Actions looks like stealing of personal data
- FivemCheat.exe (PID: 3192)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 5392)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 3240)
Bypass execution policy to execute commands
- powershell.exe (PID: 7368)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 7620)
UMBRALSTEALER has been detected (YARA)
- FivemCheat.exe (PID: 3192)
BLANKGRABBER has been detected (SURICATA)
- FivemCheat.exe (PID: 3192)
Starts CMD.EXE for self-deleting
- FivemCheat.exe (PID: 3192)
DISCORDGRABBER has been detected (YARA)
- FivemCheat.exe (PID: 3192)
GROWTOPIA has been detected (YARA)
- FivemCheat.exe (PID: 3192)
SUSPICIOUS
Starts a Microsoft application from unusual location
- FivemCheat.exe (PID: 6068)
- FivemCheat.exe (PID: 6712)
- FivemCheat.exe (PID: 5548)
- FivemCheat.exe (PID: 3192)
Process drops legitimate windows executable
- FivemCheat.exe (PID: 6068)
- FivemCheat.exe (PID: 5548)
Executable content was dropped or overwritten
- FivemCheat.exe (PID: 6068)
- FivemCheat.exe (PID: 5548)
- csc.exe (PID: 8036)
The process drops C-runtime libraries
- FivemCheat.exe (PID: 6068)
- FivemCheat.exe (PID: 5548)
Process drops python dynamic module
- FivemCheat.exe (PID: 6068)
- FivemCheat.exe (PID: 5548)
Application launched itself
- FivemCheat.exe (PID: 6068)
- FivemCheat.exe (PID: 5548)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2432)
- cmd.exe (PID: 7020)
- cmd.exe (PID: 1012)
Changes default file association
- reg.exe (PID: 1348)
Starts CMD.EXE for commands execution
- FivemCheat.exe (PID: 6712)
- FivemCheat.exe (PID: 3192)
Uses WEVTUTIL.EXE to query events from a log or log file
- cmd.exe (PID: 5544)
- cmd.exe (PID: 6676)
Found strings related to reading or modifying Windows Defender settings
- FivemCheat.exe (PID: 6712)
- FivemCheat.exe (PID: 3192)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2432)
- cmd.exe (PID: 6488)
- cmd.exe (PID: 2284)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 7508)
- cmd.exe (PID: 7840)
- cmd.exe (PID: 7528)
- cmd.exe (PID: 7288)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 2432)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 6488)
Script disables Windows Defender's IPS
- cmd.exe (PID: 6488)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 5244)
Get information on the list of running processes
- cmd.exe (PID: 5984)
- cmd.exe (PID: 6592)
- cmd.exe (PID: 5640)
- FivemCheat.exe (PID: 3192)
Starts application with an unusual extension
- cmd.exe (PID: 1324)
- cmd.exe (PID: 7492)
- cmd.exe (PID: 7632)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 7700)
- cmd.exe (PID: 7880)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 732)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 5400)
- cmd.exe (PID: 8040)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 5972)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 3240)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 3240)
Base64-obfuscated command line is found
- cmd.exe (PID: 3240)
Accesses antivirus product name via WMI (SCRIPT)
- WMIC.exe (PID: 7280)
CSC.EXE is used to compile C# code
- csc.exe (PID: 8036)
Captures screenshot (POWERSHELL)
- powershell.exe (PID: 7368)
The executable file from the user directory is run by the CMD process
- rar.exe (PID: 7892)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 7380)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 7388)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 1280)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 7488)
Possible usage of Discord/Telegram API has been detected (YARA)
- FivemCheat.exe (PID: 3192)
Checks for external IP
- FivemCheat.exe (PID: 3192)
- svchost.exe (PID: 2196)
Hides command output
- cmd.exe (PID: 4008)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 4008)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 6048)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 1300)
INFO
Checks supported languages
- FivemCheat.exe (PID: 6068)
- FivemCheat.exe (PID: 6712)
- FivemCheat.exe (PID: 5548)
- FivemCheat.exe (PID: 3192)
- tree.com (PID: 7200)
- tree.com (PID: 7540)
- tree.com (PID: 7664)
- tree.com (PID: 7744)
- tree.com (PID: 7836)
- tree.com (PID: 7896)
- csc.exe (PID: 8036)
- cvtres.exe (PID: 8100)
- MpCmdRun.exe (PID: 7620)
- rar.exe (PID: 7892)
Reads the computer name
- FivemCheat.exe (PID: 6068)
- FivemCheat.exe (PID: 5548)
- FivemCheat.exe (PID: 3192)
- MpCmdRun.exe (PID: 7620)
The sample compiled with english language support
- FivemCheat.exe (PID: 6068)
- FivemCheat.exe (PID: 5548)
Create files in a temporary directory
- FivemCheat.exe (PID: 6068)
- FivemCheat.exe (PID: 6712)
- FivemCheat.exe (PID: 5548)
- FivemCheat.exe (PID: 3192)
- cvtres.exe (PID: 8100)
- csc.exe (PID: 8036)
- MpCmdRun.exe (PID: 7620)
- rar.exe (PID: 7892)
Reads security settings of Internet Explorer
- ComputerDefaults.exe (PID: 960)
- WMIC.exe (PID: 7280)
- WMIC.exe (PID: 7488)
- WMIC.exe (PID: 7388)
- WMIC.exe (PID: 4224)
- WMIC.exe (PID: 1300)
The Powershell gets current clipboard
- powershell.exe (PID: 4628)
Checks the directory tree
- tree.com (PID: 7200)
- tree.com (PID: 7540)
- tree.com (PID: 7664)
- tree.com (PID: 7744)
- tree.com (PID: 7836)
- tree.com (PID: 7896)
Reads the machine GUID from the registry
- csc.exe (PID: 8036)
- rar.exe (PID: 7892)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 5552)
- powershell.exe (PID: 5392)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5392)
- powershell.exe (PID: 5552)
- powershell.exe (PID: 7584)
- powershell.exe (PID: 7828)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 7696)
PyInstaller has been detected (YARA)
- FivemCheat.exe (PID: 5548)
Checks proxy server information
- slui.exe (PID: 4172)
Reads the software policy settings
- slui.exe (PID: 4172)
Found Base64 encoded reflection usage via PowerShell (YARA)
- FivemCheat.exe (PID: 3192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(3192) FivemCheat.exe
Discord-Webhook-Tokens (1)1353098549339881534/Q9EDN6LH_Zn0jH2JLWKlygSsTWZwlTiaw5zkl4oeiwgHbBFHn5I3Rs4WuThgG7ERDA69
Discord-Info-Links
1353098549339881534/Q9EDN6LH_Zn0jH2JLWKlygSsTWZwlTiaw5zkl4oeiwgHbBFHn5I3Rs4WuThgG7ERDA69
Get Webhook Infohttps://discord.com/api/webhooks/1353098549339881534/Q9EDN6LH_Zn0jH2JLWKlygSsTWZwlTiaw5zkl4oeiwgHbBFHn5I3Rs4WuThgG7ERDA69
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:03:24 14:05:58+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 178688 |
| InitializedDataSize: | 94720 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc380 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 10.0.26100.3323 |
| ProductVersionNumber: | 10.0.26100.3323 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Family Safety Token Auth |
| FileVersion: | 10.0.26100.3323 (WinBuild.160101.0800) |
| InternalName: | WpcTok.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WpcTok.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 10.0.26100.3323 |
Total processes
212
Monitored processes
88
Malicious processes
10
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | tasklist /FO LIST | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | C:\WINDOWS\system32\cmd.exe /c "netsh wlan show profile" | C:\Windows\System32\cmd.exe | — | FivemCheat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | "C:\WINDOWS\system32\ComputerDefaults.exe" --nouacbypass | C:\Windows\System32\ComputerDefaults.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Set Program Access and Computer Defaults Control Panel Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | C:\WINDOWS\system32\cmd.exe /c "reg delete hkcu\Software\Classes\ms-settings /f" | C:\Windows\System32\cmd.exe | — | FivemCheat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | C:\WINDOWS\system32\cmd.exe /c "wmic computersystem get totalphysicalmemory" | C:\Windows\System32\cmd.exe | — | FivemCheat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | wmic path win32_VideoController get name | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | C:\WINDOWS\system32\cmd.exe /c "tree /A /F" | C:\Windows\System32\cmd.exe | — | FivemCheat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | powershell Get-ItemPropertyValue -Path 'HKLM:SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform' -Name BackupProductKeyDefault | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | reg add hkcu\Software\Classes\ms-settings\shell\open\command /v "DelegateExecute" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
57 278
Read events
57 265
Write events
9
Delete events
4
Modification events
| (PID) Process: | (1348) reg.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\shell\open\command |
| Operation: | write | Name: | DelegateExecute |
Value: | |||
| (PID) Process: | (960) ComputerDefaults.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (960) ComputerDefaults.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (960) ComputerDefaults.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (960) ComputerDefaults.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2552) reg.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\shell\open\command |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2552) reg.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\shell\open |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2552) reg.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\shell |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2552) reg.exe | Key: | HKEY_CLASSES_ROOT\ms-settings |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3192) FivemCheat.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Multimedia\DrawDib |
| Operation: | write | Name: | 1280x720x32(BGR 0) |
Value: 31,31,31,31 | |||
Executable files
37
Suspicious files
35
Text files
35
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6068 | FivemCheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI60682\_bz2.pyd | executable | |
MD5:94309558EB827E8315D0F201BBE7F2B1 | SHA256:7857736CEFD36B645191871F7D7C9256E1C940788CC1978609248B562E8B40D4 | |||
| 6068 | FivemCheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI60682\VCRUNTIME140.dll | executable | |
MD5:862F820C3251E4CA6FC0AC00E4092239 | SHA256:36585912E5EAF83BA9FEA0631534F690CCDC2D7BA91537166FE53E56C221E153 | |||
| 6068 | FivemCheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI60682\blank.aes | binary | |
MD5:B4CF54761BE1A2EF123CF063F2CC6B5D | SHA256:73DB28BFA52F6BCF53FB7F045993EC342B2277BB49688AAD833A4D32454FC994 | |||
| 6068 | FivemCheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI60682\libcrypto-3.dll | executable | |
MD5:8377FE5949527DD7BE7B827CB1FFD324 | SHA256:88E8AA1C816E9F03A3B589C7028319EF456F72ADB86C9DDCA346258B6B30402D | |||
| 6068 | FivemCheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI60682\_ctypes.pyd | executable | |
MD5:FC40D41AFF12417142C0256E536B4A1A | SHA256:1846030E35037D8CBAACB640FA9AC99AF5D26C0AADC09E3C2AF04DB7CA7909DC | |||
| 6068 | FivemCheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI60682\python313.dll | executable | |
MD5:2A4AAD7818D527BBEA76E9E81077CC21 | SHA256:4712A6BB81B862FC292FCD857CEF931CA8E4C142E70EAA4FD7A8D0A96AFF5E7E | |||
| 6068 | FivemCheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI60682\rar.exe | executable | |
MD5:9C223575AE5B9544BC3D69AC6364F75E | SHA256:90341AC8DCC9EC5F9EFE89945A381EB701FE15C3196F594D9D9F0F67B4FC2213 | |||
| 6068 | FivemCheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI60682\libssl-3.dll | executable | |
MD5:B2E766F5CF6F9D4DCBE8537BC5BDED2F | SHA256:3CC6828E7047C6A7EFF517AA434403EA42128C8595BF44126765B38200B87CE4 | |||
| 6068 | FivemCheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI60682\_lzma.pyd | executable | |
MD5:042AC1B18A7F6FFF8ED09EC9EFA9E724 | SHA256:0F44F360662DAAC7DB8ACBCE44557035E7E170B1309A4931DDE07CFAAD6019A0 | |||
| 6068 | FivemCheat.exe | C:\Users\admin\AppData\Local\Temp\_MEI60682\rarreg.key | text | |
MD5:4531984CAD7DACF24C086830068C4ABE | SHA256:58209C8AB4191E834FFE2ECD003FD7A830D3650F0FD1355A74EB8A47C61D4211 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
26
DNS requests
8
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 204 | 142.250.185.67:443 | https://gstatic.com/generate_204 | unknown | — | — | unknown |
3192 | FivemCheat.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/?fields=225545 | unknown | — | — | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 404 | 162.159.136.232:443 | https://discord.com/api/webhooks/1353098549339881534/Q9EDN6LH_Zn0jH2JLWKlygSsTWZwlTiaw5zkl4oeiwgHbBFHn5I3Rs4WuThgG7ERDA69 | unknown | binary | 45 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
3192 | FivemCheat.exe | 172.217.16.195:443 | gstatic.com | GOOGLE | US | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3192 | FivemCheat.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | whitelisted |
3192 | FivemCheat.exe | 162.159.136.232:443 | discord.com | CLOUDFLARENET | — | whitelisted |
6728 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4172 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
gstatic.com |
| whitelisted |
ip-api.com |
| whitelisted |
discord.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
3192 | FivemCheat.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
3192 | FivemCheat.exe | A Network Trojan was detected | STEALER [ANY.RUN] BlankGrabber (SkochGrabber) Generic External IP Check |
2196 | svchost.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
2196 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
3192 | FivemCheat.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
3192 | FivemCheat.exe | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |