| File name: | 2019 Repeat Purchase Order. PDF File.exe |
| Full analysis: | https://app.any.run/tasks/5ded2851-08b2-4fe1-a34c-45daf448e8e2 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | December 06, 2019, 18:30:47 |
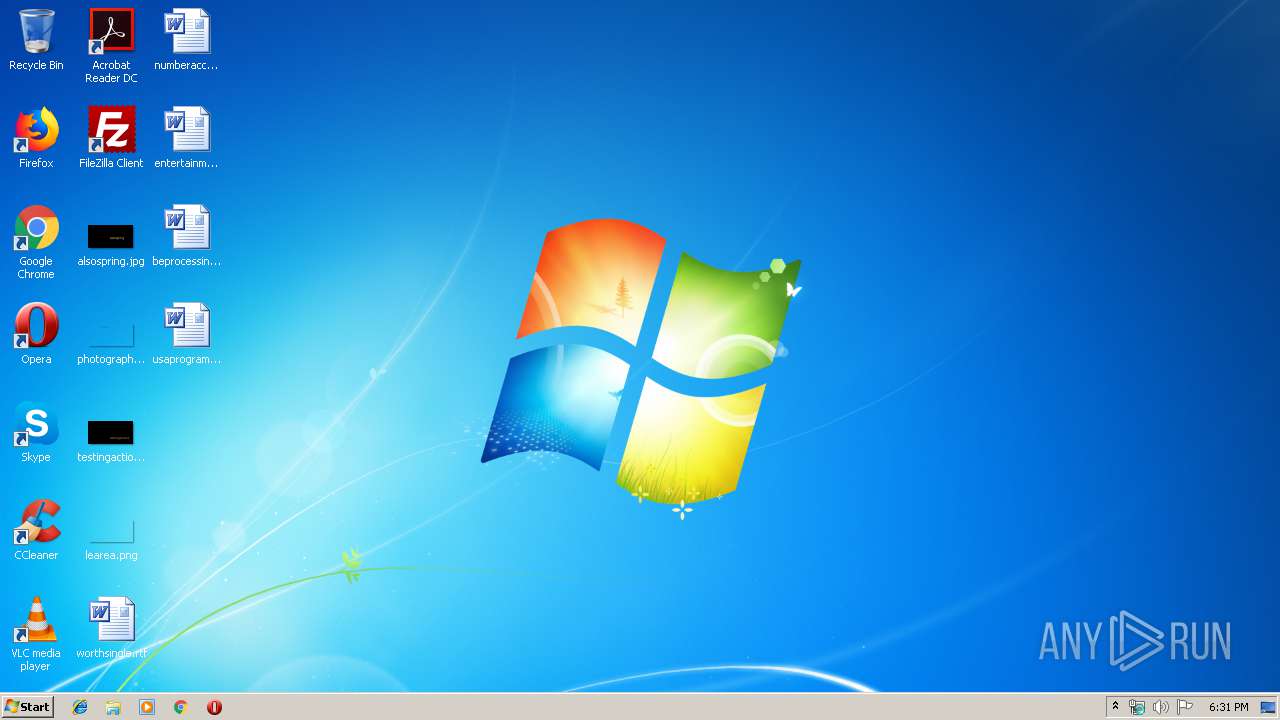
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | F16CE338142165A1372C55FACEC92E7D |
| SHA1: | 4055A50516853E9CDFDC78A97580F3759C39C055 |
| SHA256: | 0029B8B2061568C14A08325B1AB5CC526DE497FC517314E545BA174FD14BF19C |
| SSDEEP: | 12288:Ri56pDYRJ9DjqywrcShrRpLfop5WopL1wVwJNYVesXpb5o:Ru6pDejnaOOVlpl |
MALICIOUS
FORMBOOK was detected
- explorer.exe (PID: 352)
- colorcpl.exe (PID: 1728)
- Firefox.exe (PID: 2724)
Connects to CnC server
- explorer.exe (PID: 352)
Actions looks like stealing of personal data
- colorcpl.exe (PID: 1728)
Application was dropped or rewritten from another process
- RegAsm.exe (PID: 3376)
- gdimhlhwz.exe (PID: 920)
Starts Visual C# compiler
- 2019 Repeat Purchase Order. PDF File.exe (PID: 2092)
Changes the autorun value in the registry
- colorcpl.exe (PID: 1728)
Stealing of credential data
- colorcpl.exe (PID: 1728)
SUSPICIOUS
Creates files in the user directory
- colorcpl.exe (PID: 1728)
Starts CMD.EXE for commands execution
- colorcpl.exe (PID: 1728)
Executable content was dropped or overwritten
- explorer.exe (PID: 352)
- DllHost.exe (PID: 2552)
Creates files in the program directory
- DllHost.exe (PID: 2552)
Loads DLL from Mozilla Firefox
- colorcpl.exe (PID: 1728)
Executed via COM
- DllHost.exe (PID: 2552)
INFO
Manual execution by user
- colorcpl.exe (PID: 1728)
Reads the hosts file
- colorcpl.exe (PID: 1728)
Creates files in the user directory
- Firefox.exe (PID: 2724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (62) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.5) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Win16/32 Executable Delphi generic (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:20 14:27:24+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 938496 |
| InitializedDataSize: | 1024 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xe718e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Oct-2019 12:27:24 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 20-Oct-2019 12:27:24 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000E5194 | 0x000E5200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.48427 |
.rsrc | 0x000E8000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.0203931 |
.reloc | 0x000EA000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Imports
mscoree.dll |
Total processes
46
Monitored processes
10
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 920 | "C:\Program Files\Izn3du\gdimhlhwz.exe" | C:\Program Files\Izn3du\gdimhlhwz.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 1728 | "C:\Windows\System32\colorcpl.exe" | C:\Windows\System32\colorcpl.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Color Control Panel Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2092 | "C:\Users\admin\AppData\Local\Temp\2019 Repeat Purchase Order. PDF File.exe" | C:\Users\admin\AppData\Local\Temp\2019 Repeat Purchase Order. PDF File.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2192 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESB5ED.tmp" "c:\Users\admin\AppData\Local\Temp\CSC57E36C6FA845492BA4259509EA1D8F0.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 12.00.52519.0 built by: VSWINSERVICING Modules
| |||||||||||||||
| 2552 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2724 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | colorcpl.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3356 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\3in5h3ha.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | — | 2019 Repeat Purchase Order. PDF File.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 3376 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | 2019 Repeat Purchase Order. PDF File.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 3784 | /c del "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" | C:\Windows\System32\cmd.exe | — | colorcpl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
73
Read events
70
Write events
3
Delete events
0
Modification events
| (PID) Process: | (1728) colorcpl.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | ZNOPDRBPAZ |
Value: C:\Program Files\Izn3du\gdimhlhwz.exe | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {7P5N40RS-N0SO-4OSP-874N-P0S2R0O9SN8R}\Vma3qh\tqvzuyujm.rkr |
Value: 000000000000000000000000AC000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000003200000037000000DEE61200090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101090000000D000000CC19050033003000380030003400360042003000410046003400410033003900430042000000460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C0049006E007400650072006E006500740020004500780070006C006F007200650072005C0051007500690063006B0020004C00610075006E00630068005C0055007300650072002000500069006E006E006500000000000034FF01F832FF01D4E3E1013DA94A7600000000FBFFFF7FF8E3E101987880574F8C6244BB6371042380B1090000000001100211FFFFFFFF000000000000000000000000534275066D42750653427506000000000000000000000000080000002E006C00E72F0A77A48EF37600000000AC032E0000002E00E72F0A77B08EF37603005B019604010000002E005B148D23020000006CE4E101B07F0A7744E5E1010000000058005A0044E5E1010200000010E5E101F2700A7791830A771C8FF37611000000B8453100B045310078192F00F8FD580600E500008F148D23B0E4E10182914A7600E5E101B4E4E10127954A7600000000CC90FF01DCE4E101CD944A76CC90FF0188E5E101408CFF01E1944A7600000000408CFF0188E5E101E4E4E101 | |||
Executable files
2
Suspicious files
82
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3356 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC57E36C6FA845492BA4259509EA1D8F0.TMP | — | |
MD5:— | SHA256:— | |||
| 2192 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESB5ED.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | csc.exe | C:\Users\admin\AppData\Local\Temp\3in5h3ha.dll | — | |
MD5:— | SHA256:— | |||
| 3356 | csc.exe | C:\Users\admin\AppData\Local\Temp\3in5h3ha.out | — | |
MD5:— | SHA256:— | |||
| 2092 | 2019 Repeat Purchase Order. PDF File.exe | C:\Users\admin\AppData\Local\Temp\3in5h3ha.0.cs | text | |
MD5:— | SHA256:— | |||
| 1728 | colorcpl.exe | C:\Users\admin\AppData\Roaming\380AN8QE\380logrc.ini | binary | |
MD5:— | SHA256:— | |||
| 1728 | colorcpl.exe | C:\Users\admin\AppData\Roaming\380AN8QE\380logri.ini | binary | |
MD5:D63A82E5D81E02E399090AF26DB0B9CB | SHA256:EAECE2EBA6310253249603033C744DD5914089B0BB26BDE6685EC9813611BAAE | |||
| 2724 | Firefox.exe | C:\Users\admin\AppData\Roaming\380AN8QE\380logrf.ini | binary | |
MD5:— | SHA256:— | |||
| 1728 | colorcpl.exe | C:\Users\admin\AppData\Roaming\380AN8QE\380logrv.ini | binary | |
MD5:BA3B6BC807D4F76794C4B81B09BB9BA5 | SHA256:6EEBF968962745B2E9DE2CA969AF7C424916D4E3FE3CC0BB9B3D414ABFCE9507 | |||
| 1728 | colorcpl.exe | C:\Users\admin\AppData\Roaming\380AN8QE\380logim.jpeg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
33
DNS requests
15
Threats
69
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
352 | explorer.exe | GET | — | 203.78.142.55:80 | http://www.sluas.com/kc/?FtI0wNF=mi4038ihx+EBCMftOGd/7aeU81+2QXwKa7qAnFYyhcPnYDEF7+L3JR21C9/Neu1PXdhvGg==&0D=Zb8Dbz9hu2jt | HK | — | — | malicious |
352 | explorer.exe | GET | 301 | 35.242.251.130:80 | http://www.institutdebeautechablis.com/kc/?FtI0wNF=Wdr074qZuKjFW+jrH4Vbb99OD9mQldEj7WrY+jgGrmLijJJuiK+CVTV5rlIhEADQRq3KEw==&0D=Zb8Dbz9hu2jt | US | — | — | malicious |
352 | explorer.exe | POST | 404 | 68.65.121.23:80 | http://www.jevmod.com/kc/ | US | html | 290 b | malicious |
352 | explorer.exe | GET | — | 76.164.193.43:80 | http://www.insidereaganmanx.com/kc/?FtI0wNF=CBaHmLEbO9L8H1kSCefjbBETOcnwPEWbfIvUPdYIr8fUsOVRLRTv0bIdNfGcRVGpael3tQ==&0D=Zb8Dbz9hu2jt | US | — | — | malicious |
352 | explorer.exe | GET | 404 | 217.160.223.227:80 | http://www.artgrowth.fund/kc/?FtI0wNF=Im9yJgvbz29s6zGPOuwgkbi4+r2G8MiqRmHnGbPhFGUMDqQ/R9s2oJ9me4Y0lccyRAZJtA==&0D=Zb8Dbz9hu2jt | DE | html | 1.33 Kb | malicious |
352 | explorer.exe | GET | 404 | 195.142.1.93:80 | http://www.fixref4.com/kc/?FtI0wNF=RqgdagcEHBmQFRqOjykKgxnbdt3k5OAjcTC5V9uf5/yxHiMRKur6rB2XsODJZqUFFM3OeQ==&0D=Zb8Dbz9hu2jt | TR | html | 282 b | malicious |
352 | explorer.exe | GET | — | 213.186.33.5:80 | http://www.presence-digitale.net/kc/?FtI0wNF=NMKRLht3HPcQnqJScc60oEsMx8fiJ7ic/mlFpm1I/m3pHc3MJfeXHpqYe7lZPmQbNrpsrA==&0D=Zb8Dbz9hu2jt | FR | — | — | malicious |
352 | explorer.exe | POST | — | 68.65.121.23:80 | http://www.jevmod.com/kc/ | US | — | — | malicious |
352 | explorer.exe | POST | — | 195.142.1.93:80 | http://www.fixref4.com/kc/ | TR | — | — | malicious |
352 | explorer.exe | POST | — | 195.142.1.93:80 | http://www.fixref4.com/kc/ | TR | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
352 | explorer.exe | 217.160.223.227:80 | www.artgrowth.fund | 1&1 Internet SE | DE | malicious |
352 | explorer.exe | 68.65.121.23:80 | www.jevmod.com | Namecheap, Inc. | US | malicious |
352 | explorer.exe | 195.142.1.93:80 | www.fixref4.com | SAGLAYICI Teknoloji Bilisim Yayincilik Hiz. Ticaret Ltd. Sti. | TR | malicious |
— | — | 35.242.251.130:80 | www.institutdebeautechablis.com | — | US | malicious |
352 | explorer.exe | 23.227.38.64:80 | www.shopforbabys.com | Shopify, Inc. | CA | malicious |
352 | explorer.exe | 35.242.251.130:80 | www.institutdebeautechablis.com | — | US | malicious |
352 | explorer.exe | 207.148.248.143:80 | www.hotrugged.com | The Endurance International Group, Inc. | US | malicious |
352 | explorer.exe | 213.186.33.5:80 | www.presence-digitale.net | OVH SAS | FR | malicious |
352 | explorer.exe | 203.78.142.55:80 | www.sluas.com | LinkChina Telecom Global Limited. | HK | malicious |
352 | explorer.exe | 76.164.193.43:80 | www.insidereaganmanx.com | Versaweb, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.artgrowth.fund |
| unknown |
www.jevmod.com |
| malicious |
www.fixref4.com |
| malicious |
www.smprimeholdings.com |
| unknown |
www.sluas.com |
| malicious |
www.wwwgmanetwork.com |
| unknown |
www.insidereaganmanx.com |
| malicious |
www.institutdebeautechablis.com |
| malicious |
www.m5644.com |
| unknown |
www.presence-digitale.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
24 ETPRO signatures available at the full report