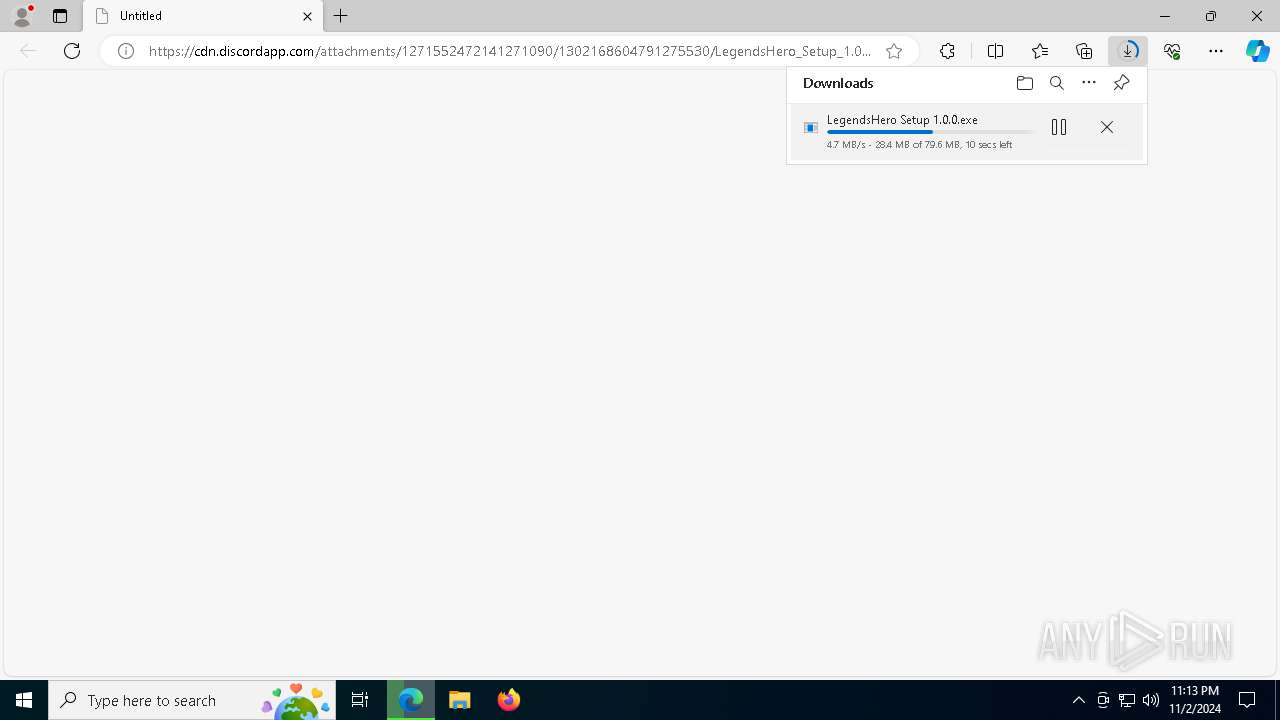
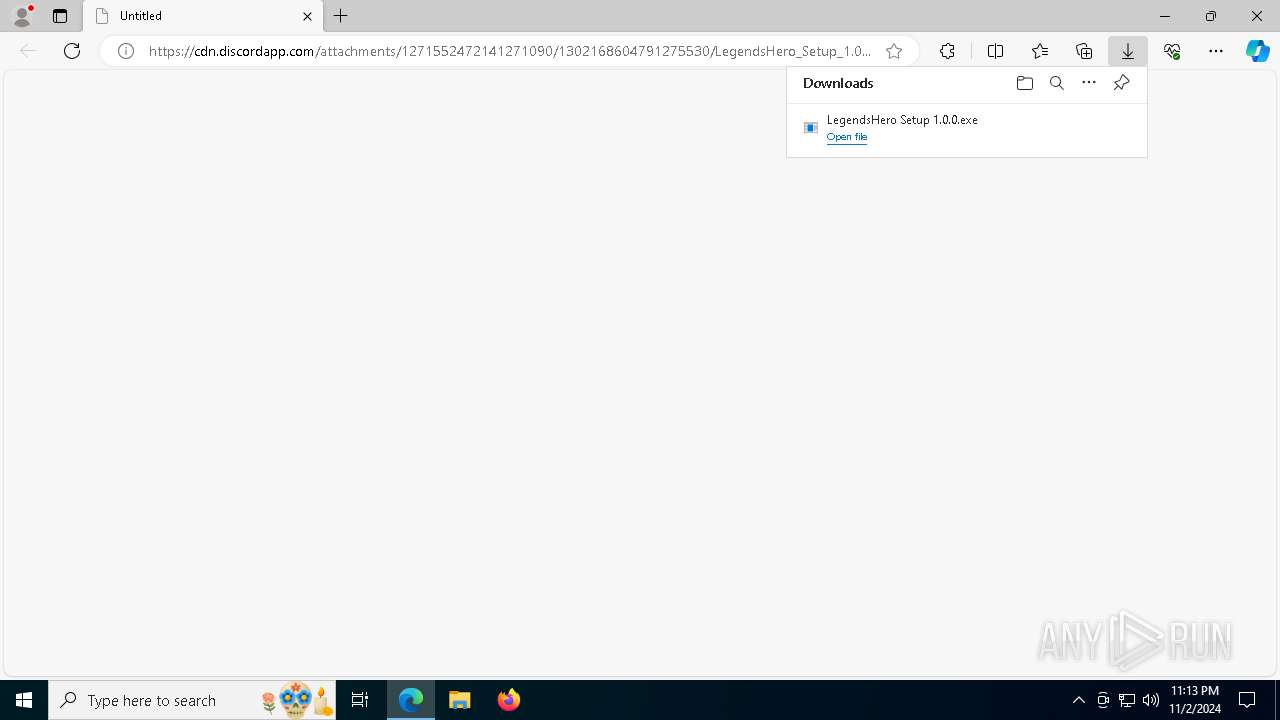
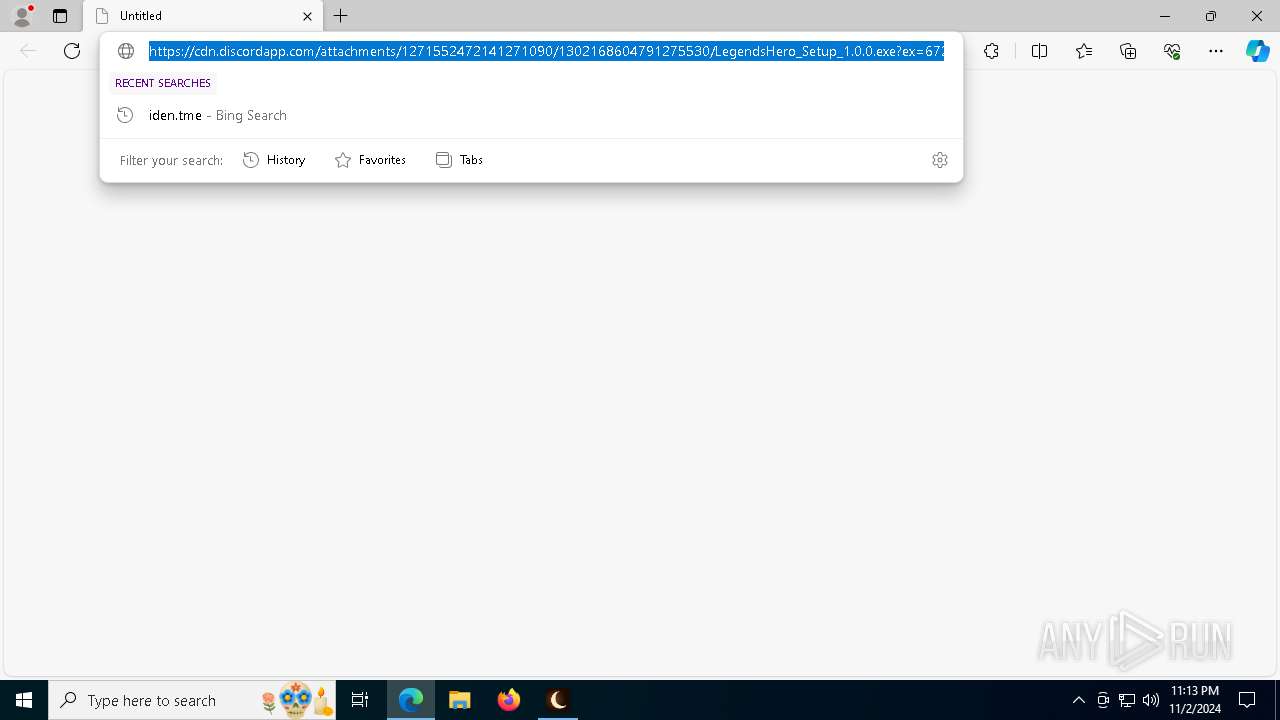
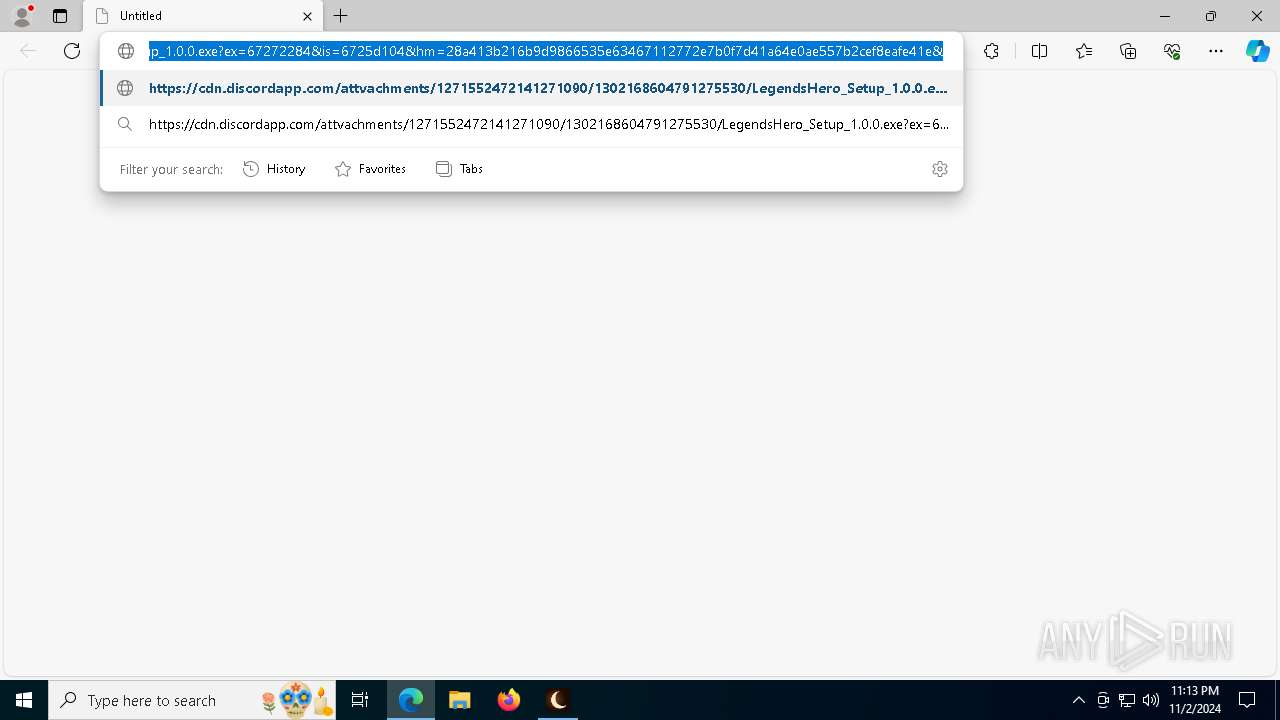
| URL: | https://cdn.discordapp.com/attachments/1271552472141271090/1302168604791275530/LegendsHero_Setup_1.0.0.exe?ex=67272284&is=6725d104&hm=28a413b216b9d9866535e63467112772e7b0f7d41a64e0ae557b2cef8eafe41e& |
| Full analysis: | https://app.any.run/tasks/80b60136-ba40-492d-960d-e60daa1c45f1 |
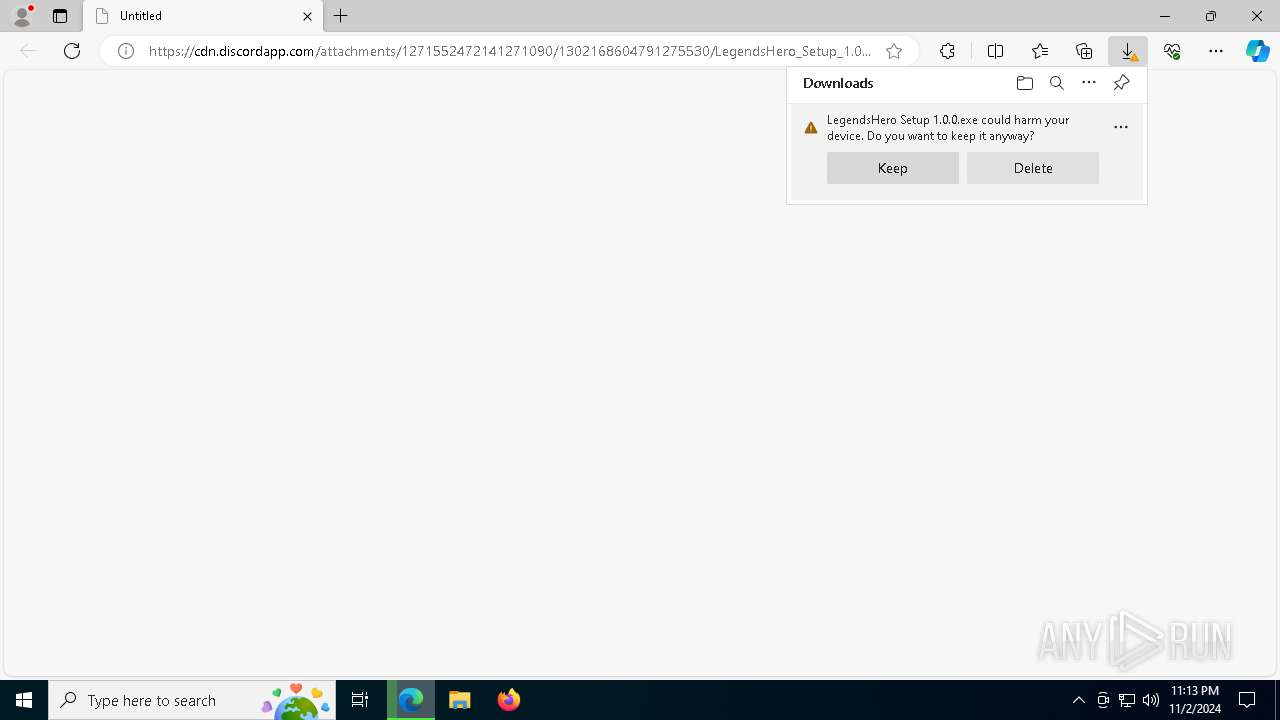
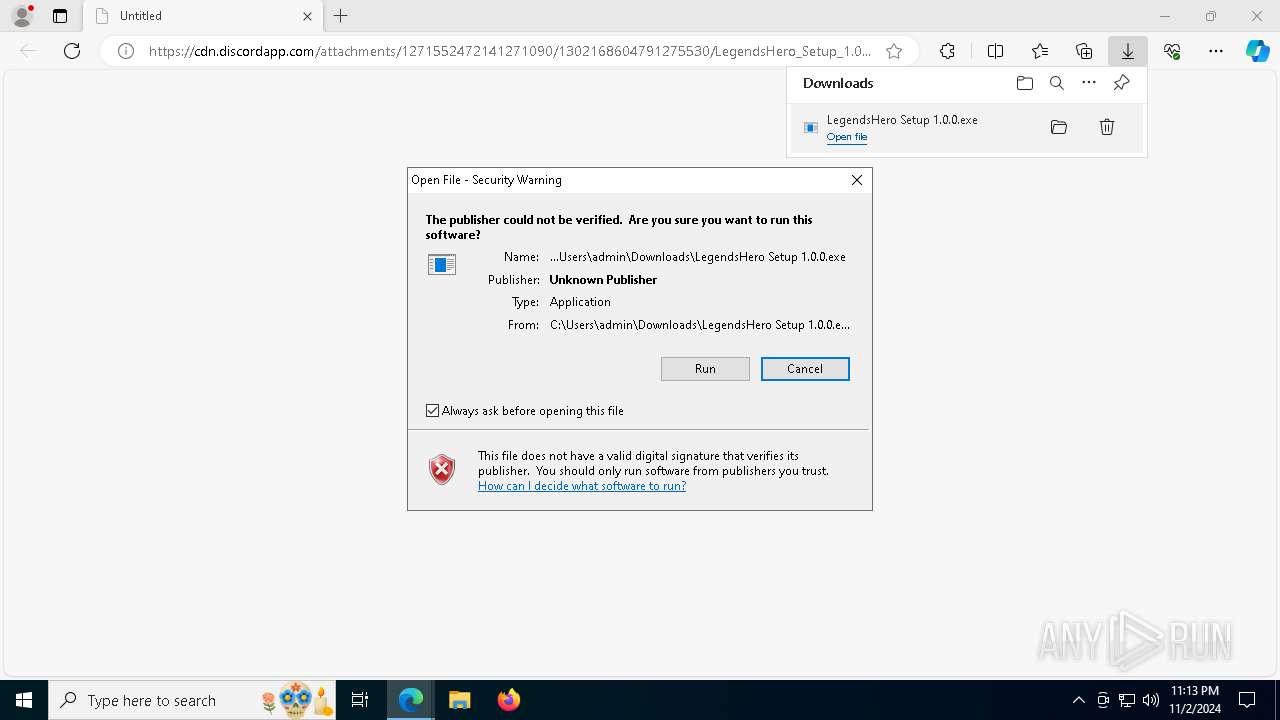
| Verdict: | Malicious activity |
| Analysis date: | November 02, 2024, 23:13:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 287F90D0D3EB1D6635B43FC688BF8E99 |
| SHA1: | D50A66D5E2A8227891FAE1459AA37C6C9898F1DA |
| SHA256: | FFF3D41670D60D9E0F524A4E102FA959FC6C7D65FCA10E373E7CBFC31C838D97 |
| SSDEEP: | 3:N8cCWdy6//OnFBkLUkUTRW1QSKpACALVuVCd/AaISXXTeBMla6GR8vTTMATDd6RY:2cry6X3U1Wa5pu4Qd/WSXCMdl34nj0 |
MALICIOUS
Starts Visual C# compiler
- cmd.exe (PID: 5644)
SUSPICIOUS
Discord domain found in command line (probably downloading payload)
- msedge.exe (PID: 6644)
Malware-specific behavior (creating "System.dll" in Temp)
- LegendsHero Setup 1.0.0.exe (PID: 7628)
Get information on the list of running processes
- cmd.exe (PID: 7624)
- LegendsHero Setup 1.0.0.exe (PID: 7628)
- LegendsHero.exe (PID: 6404)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 6768)
- cmd.exe (PID: 1748)
- cmd.exe (PID: 7876)
- cmd.exe (PID: 6128)
- LegendsHero.exe (PID: 7596)
- cmd.exe (PID: 692)
- cmd.exe (PID: 1768)
- cmd.exe (PID: 6688)
- cmd.exe (PID: 6752)
- cmd.exe (PID: 6136)
- cmd.exe (PID: 512)
- cmd.exe (PID: 7436)
- cmd.exe (PID: 1084)
- LegendsHero.exe (PID: 4548)
- cmd.exe (PID: 8096)
- cmd.exe (PID: 8136)
- cmd.exe (PID: 2784)
- cmd.exe (PID: 7036)
- cmd.exe (PID: 7452)
Executable content was dropped or overwritten
- LegendsHero Setup 1.0.0.exe (PID: 7628)
- LegendsHero.exe (PID: 6404)
- LegendsHero.exe (PID: 7596)
- LegendsHero.exe (PID: 4548)
- hexon_8e2c2d9da1038898.exe (PID: 7392)
- csc.exe (PID: 8028)
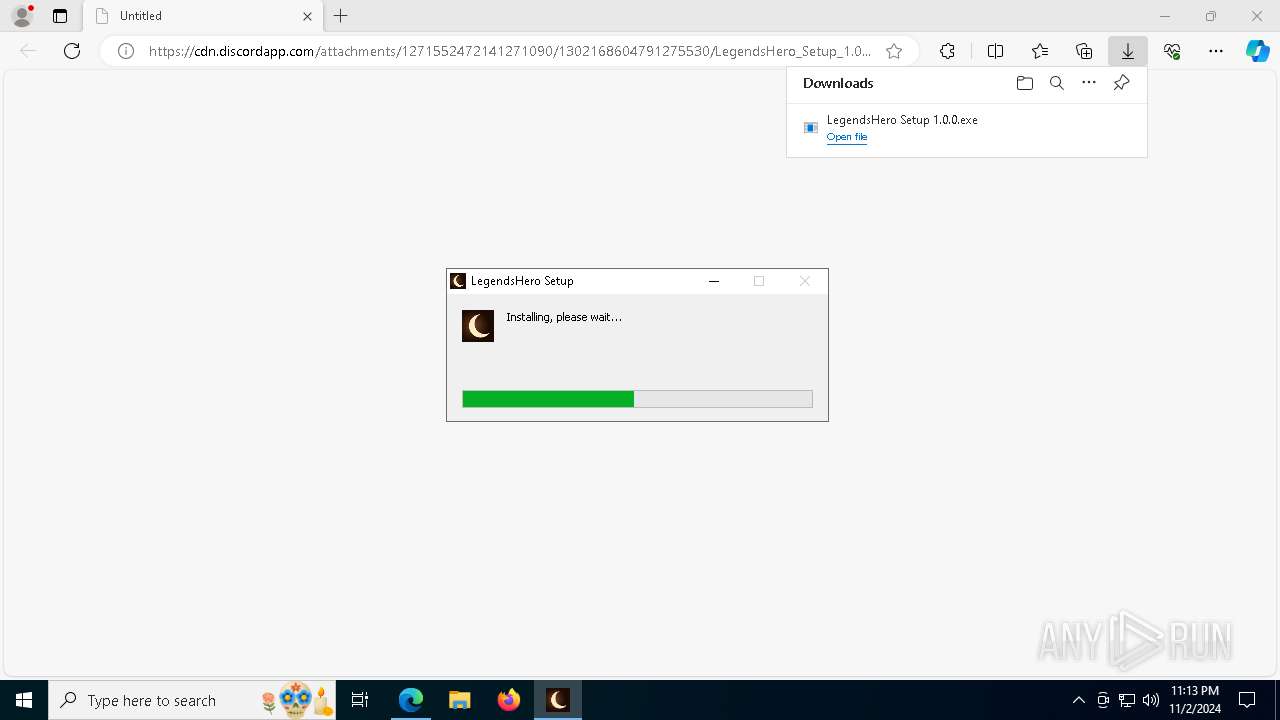
Drops 7-zip archiver for unpacking
- LegendsHero Setup 1.0.0.exe (PID: 7628)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 7196)
- cmd.exe (PID: 1884)
- cmd.exe (PID: 6244)
Process drops legitimate windows executable
- LegendsHero Setup 1.0.0.exe (PID: 7628)
Application launched itself
- LegendsHero.exe (PID: 6404)
- chrome.exe (PID: 2780)
- msedge.exe (PID: 6408)
- LegendsHero.exe (PID: 7596)
- chrome.exe (PID: 6448)
- msedge.exe (PID: 7476)
- LegendsHero.exe (PID: 4548)
- msedge.exe (PID: 7640)
- chrome.exe (PID: 6152)
Starts CMD.EXE for commands execution
- LegendsHero.exe (PID: 6404)
- LegendsHero Setup 1.0.0.exe (PID: 7628)
- LegendsHero.exe (PID: 7596)
- LegendsHero.exe (PID: 4548)
- hexon_8e2c2d9da1038898.exe (PID: 7392)
- hexon_6f152f993eb2aab6.exe (PID: 7056)
- hexon_6259cd23aa559925.exe (PID: 2056)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 7336)
- cmd.exe (PID: 7644)
- cmd.exe (PID: 7536)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 2816)
- cmd.exe (PID: 4060)
- cmd.exe (PID: 1748)
- cmd.exe (PID: 6444)
- cmd.exe (PID: 5284)
- cmd.exe (PID: 1712)
- cmd.exe (PID: 512)
- cmd.exe (PID: 2648)
MS Edge headless start
- msedge.exe (PID: 7292)
- msedge.exe (PID: 6408)
- msedge.exe (PID: 7476)
- msedge.exe (PID: 7348)
- msedge.exe (PID: 7640)
- msedge.exe (PID: 3508)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6344)
- cmd.exe (PID: 7888)
- cmd.exe (PID: 5616)
- cmd.exe (PID: 7860)
- cmd.exe (PID: 6740)
- cmd.exe (PID: 7272)
- cmd.exe (PID: 6884)
- cmd.exe (PID: 1572)
- cmd.exe (PID: 6492)
The process executes VB scripts
- cmd.exe (PID: 7464)
- cmd.exe (PID: 6884)
- cmd.exe (PID: 6212)
Executing commands from a ".bat" file
- hexon_8e2c2d9da1038898.exe (PID: 7392)
- hexon_6259cd23aa559925.exe (PID: 2056)
- hexon_6f152f993eb2aab6.exe (PID: 7056)
The executable file from the user directory is run by the CMD process
- screenCapture_1.3.2.exe (PID: 8004)
- screenCapture_1.3.2.exe (PID: 2196)
- screenCapture_1.3.2.exe (PID: 7736)
INFO
Application launched itself
- msedge.exe (PID: 6644)
- msedge.exe (PID: 5604)
Checks supported languages
- identity_helper.exe (PID: 8032)
Reads the computer name
- identity_helper.exe (PID: 8032)
Reads Environment values
- identity_helper.exe (PID: 8032)
Executable content was dropped or overwritten
- msedge.exe (PID: 6644)
Attempting to use instant messaging service
- msedge.exe (PID: 204)
Manual execution by a user
- LegendsHero.exe (PID: 6404)
- msedge.exe (PID: 7756)
- LegendsHero.exe (PID: 7596)
- LegendsHero.exe (PID: 4548)
- msedge.exe (PID: 5604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
487
Monitored processes
346
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 204 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2588 --field-trial-handle=2404,i,5944559452064293915,2923334953478220627,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 1 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 512 | taskkill /IM msedge.exe /F | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-sandbox --mute-audio --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --no-appcompat-clear --mojo-platform-channel-handle=4816 --field-trial-handle=2288,i,694486827913148207,13061358303188593042,262144 --enable-features=PdfOopif,msMetricsLogFastStartup,msSendMetricsLogOnClose --disable-features=AcceptCHFrame,IsolateSandboxedIframes,MediaRouter,OptimizationHints,PaintHolding,ProcessPerSiteUpToMainFrameThreshold,Translate --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 512 | C:\WINDOWS\system32\cmd.exe /d /s /c "tasklist" | C:\Windows\System32\cmd.exe | — | LegendsHero.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 512 | C:\WINDOWS\system32\cmd.exe /d /s /c "taskkill /IM msedge.exe /F" | C:\Windows\System32\cmd.exe | — | LegendsHero.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 616 | taskkill /IM chrome.exe /F | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 692 | C:\WINDOWS\system32\cmd.exe /d /s /c "tasklist" | C:\Windows\System32\cmd.exe | — | LegendsHero.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\Google\Chrome\User Data" --no-appcompat-clear --no-sandbox --disable-background-timer-throttling --disable-breakpad --enable-automation --force-color-profile=srgb --remote-debugging-port=0 --allow-pre-commit-input --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3712 --field-trial-handle=1864,i,5429096356953901977,3259517631303882712,262144 --enable-features=PdfOopif --disable-features=AcceptCHFrame,IsolateSandboxedIframes,MediaRouter,OptimizationHints,PaintHolding,ProcessPerSiteUpToMainFrameThreshold,Translate --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | |||||||||||||||
| 696 | taskkill /IM chrome.exe /F | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | wmic csproduct get uuid | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 573
Read events
21 433
Write events
67
Delete events
73
Modification events
| (PID) Process: | (6644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6644) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D293057B8C842F00 | |||
| (PID) Process: | (6644) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: ADBA0C7B8C842F00 | |||
| (PID) Process: | (6644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262732 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {50C82CCE-5014-483A-B884-383439355E53} | |||
| (PID) Process: | (6644) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BB32417B8C842F00 | |||
| (PID) Process: | (6644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (6644) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
62
Suspicious files
1 015
Text files
375
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF8b697.TMP | — | |
MD5:— | SHA256:— | |||
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF8b697.TMP | — | |
MD5:— | SHA256:— | |||
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF8b6a6.TMP | — | |
MD5:— | SHA256:— | |||
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF8b6a6.TMP | — | |
MD5:— | SHA256:— | |||
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF8b6b6.TMP | — | |
MD5:— | SHA256:— | |||
| 6644 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
233
DNS requests
210
Threats
53
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7088 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6384 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7884 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7884 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.151.152.98:1337 | http://20.151.152.98:1337/socket.io/?EIO=4&transport=polling&t=s6pvdfjv&sid=eu-8MOjKBNN1mEFjAAQa | unknown | — | — | unknown |
— | — | GET | 101 | 20.151.152.98:1337 | http://20.151.152.98:1337/socket.io/?EIO=4&transport=websocket&sid=eu-8MOjKBNN1mEFjAAQa | unknown | — | — | unknown |
— | — | GET | 200 | 20.151.152.98:1337 | http://20.151.152.98:1337/socket.io/?EIO=4&transport=polling&t=s6ppa0r0 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4292 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 104.126.37.137:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
204 | msedge.exe | 162.159.134.233:443 | cdn.discordapp.com | — | — | shared |
6644 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
204 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
cdn.discordapp.com |
| shared |
business.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
204 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
204 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
2172 | svchost.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
2172 | svchost.exe | Potentially Bad Traffic | ET INFO Online File Storage Domain in DNS Lookup (gofile .io) |
6404 | LegendsHero.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |
6404 | LegendsHero.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |
6404 | LegendsHero.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |
6404 | LegendsHero.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |
6404 | LegendsHero.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |
6404 | LegendsHero.exe | Misc activity | ET INFO File Sharing Related Domain in TLS SNI (gofile .io) |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Google\Chrome\User Data directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Microsoft\Edge\User Data directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Google\Chrome\User Data directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Microsoft\Edge\User Data directory exists )
|