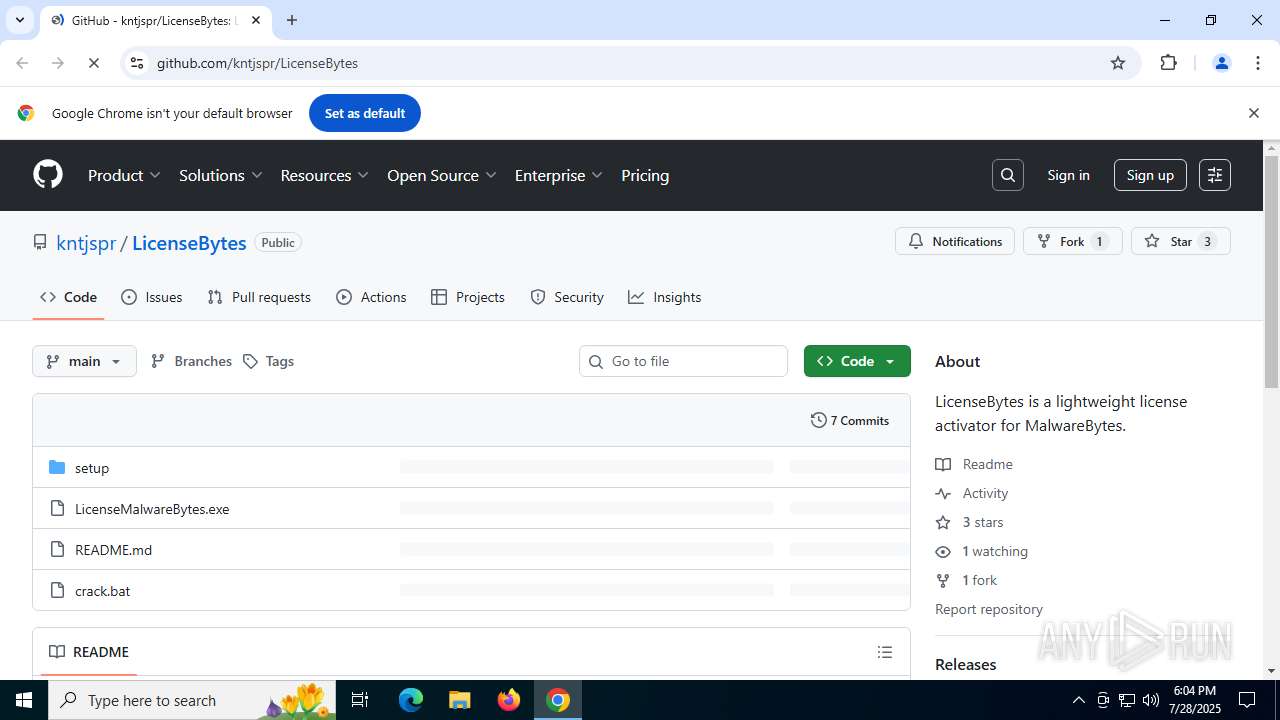
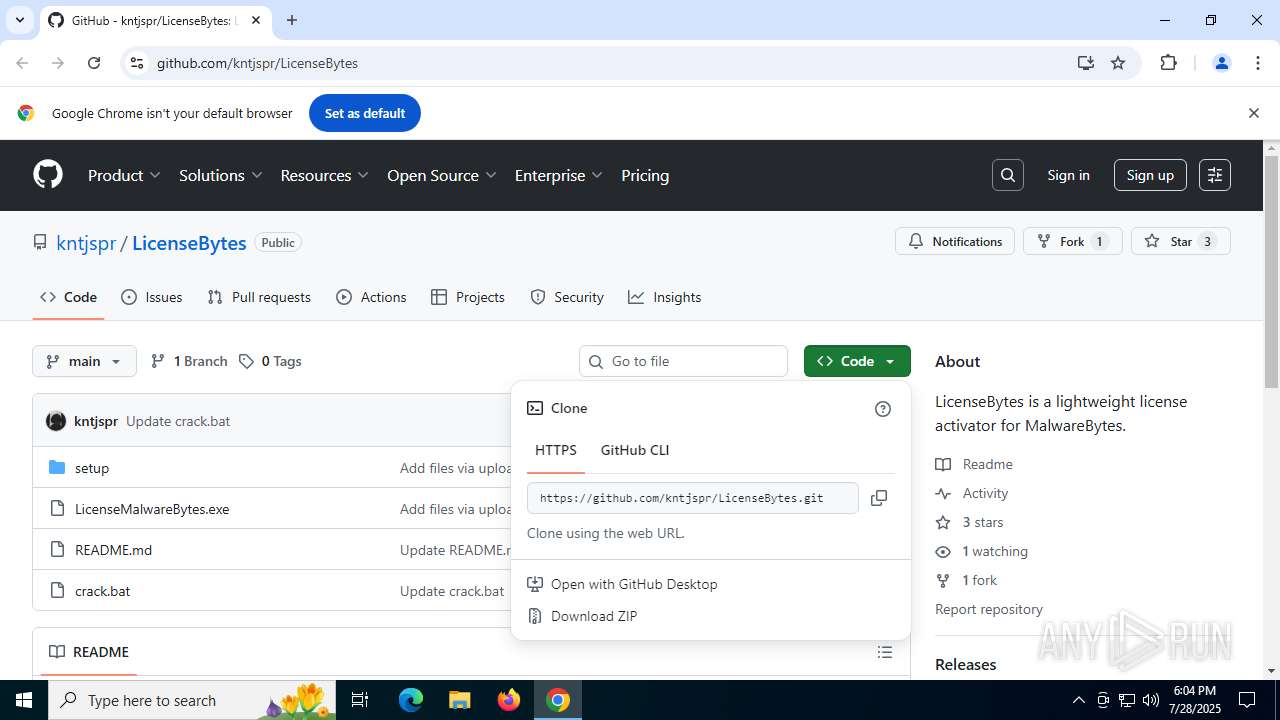
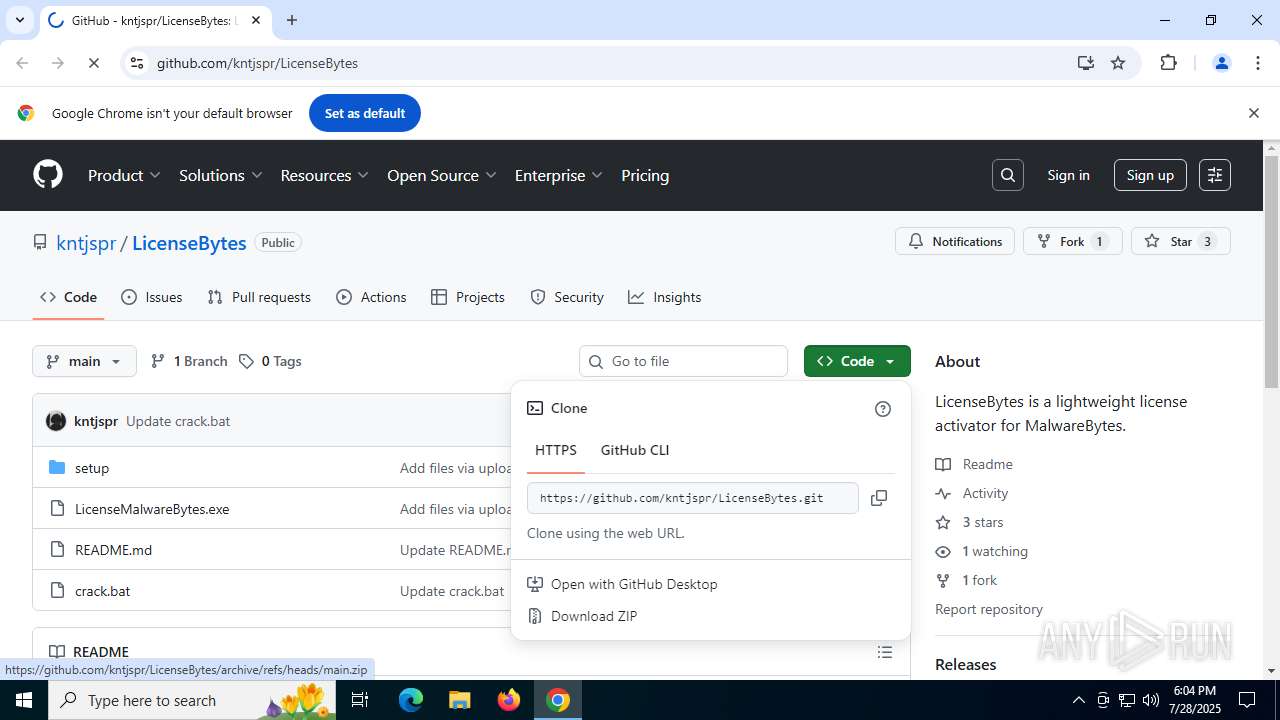
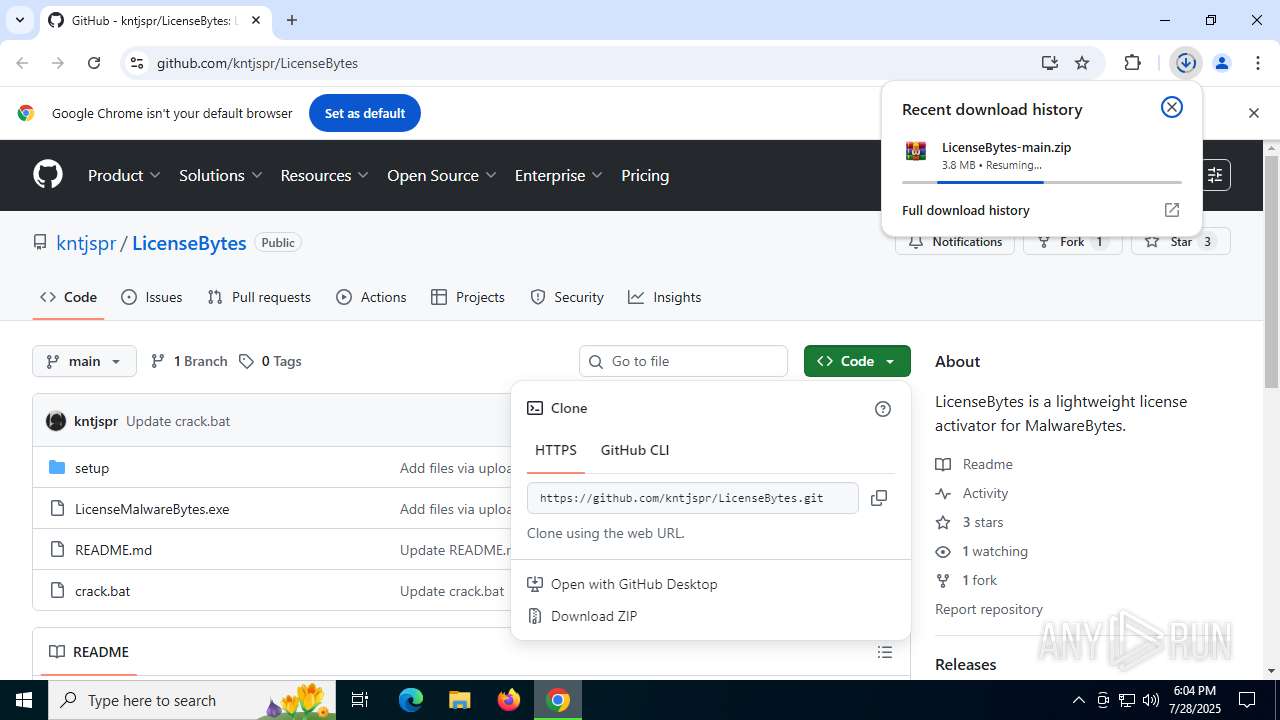
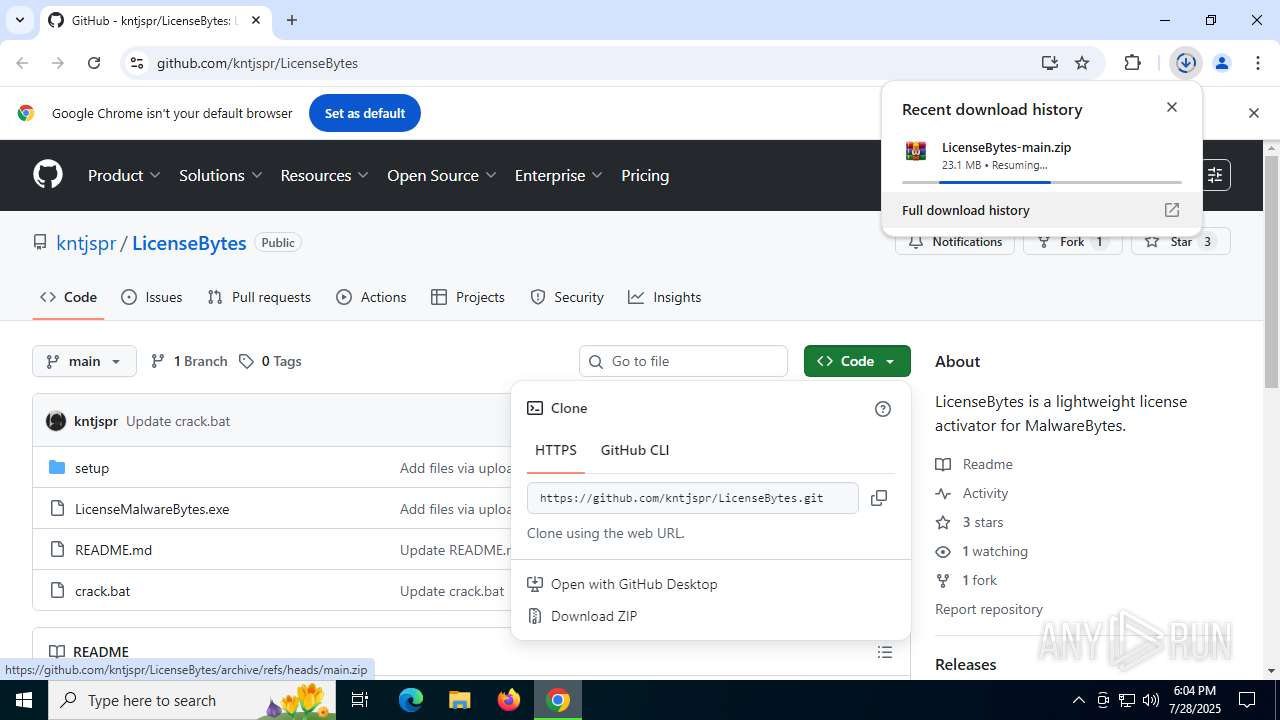
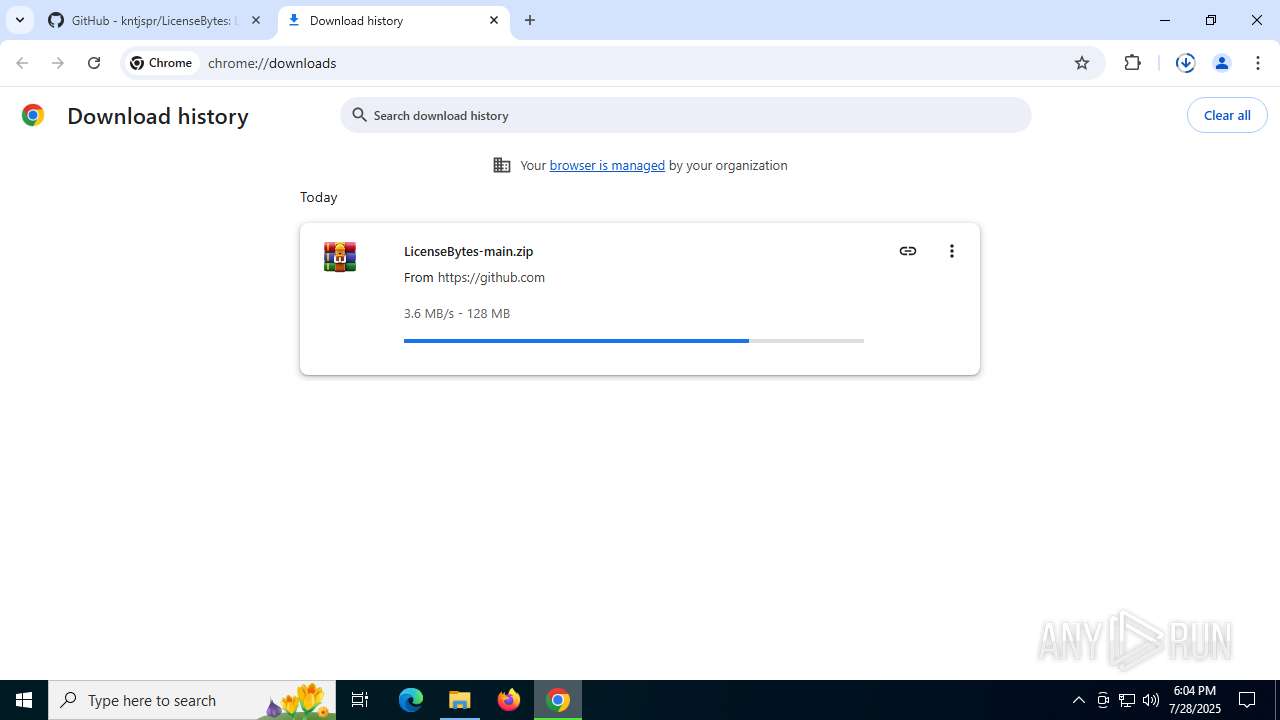
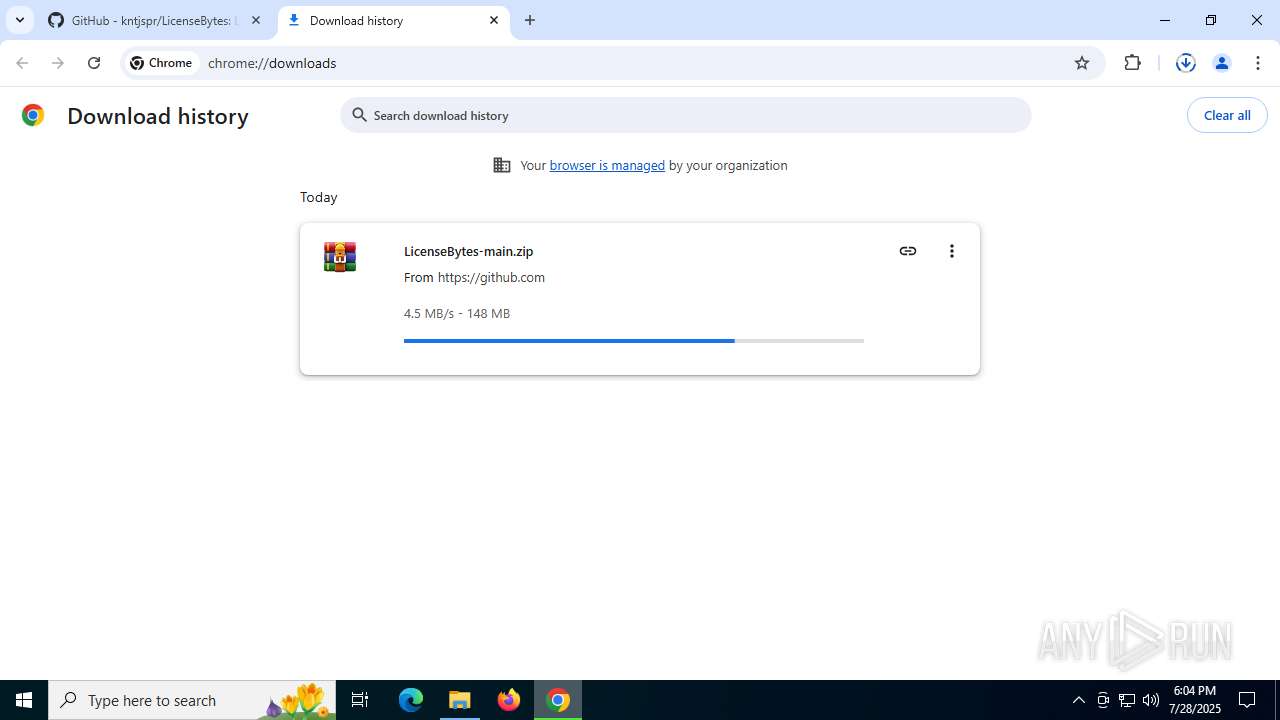
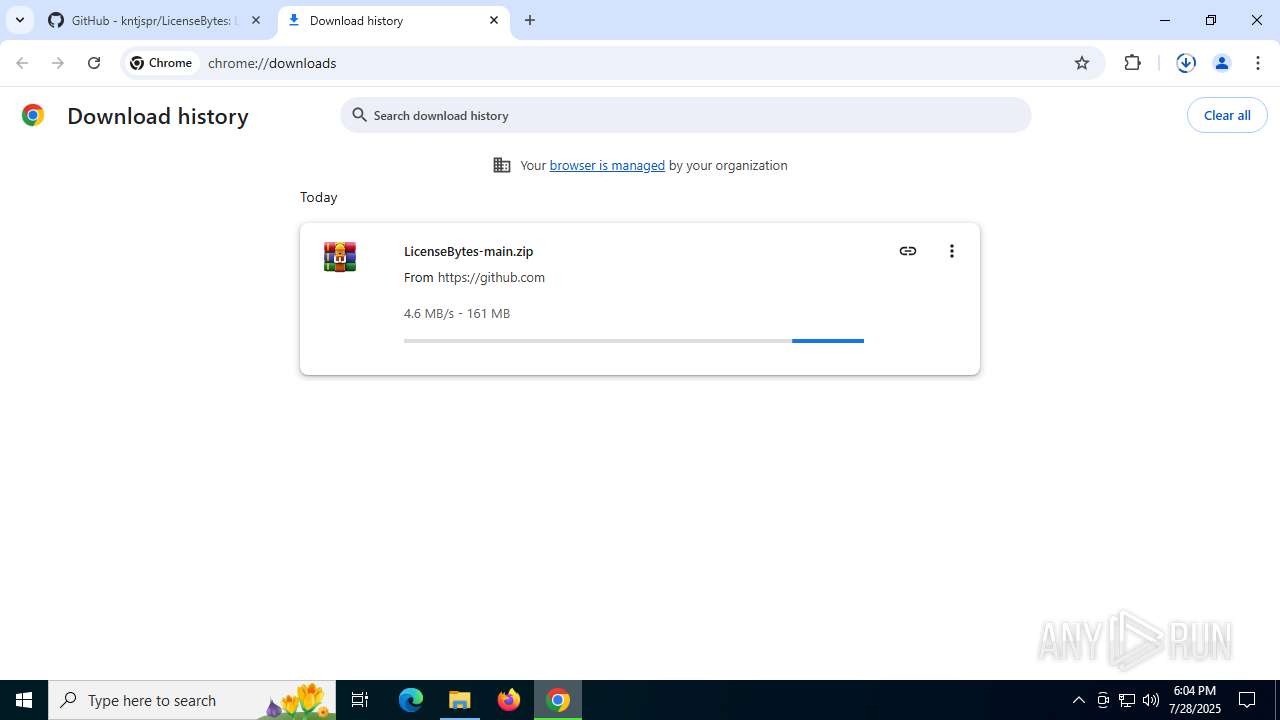
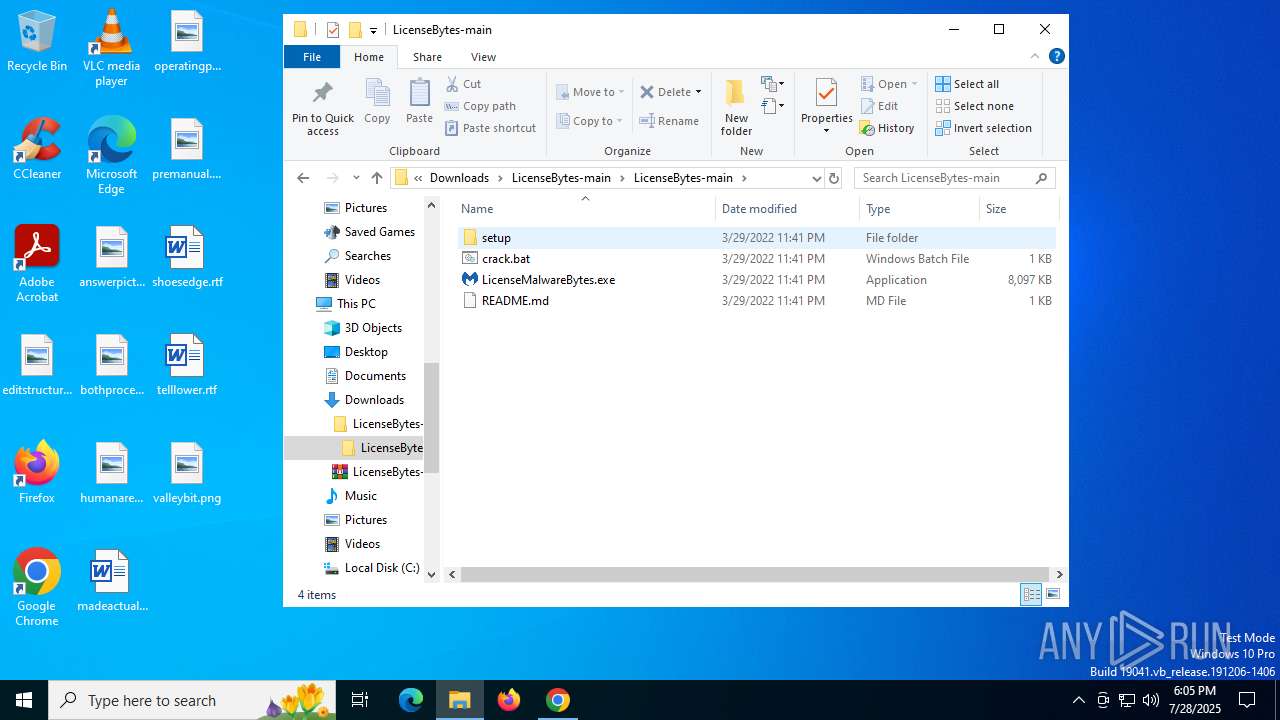
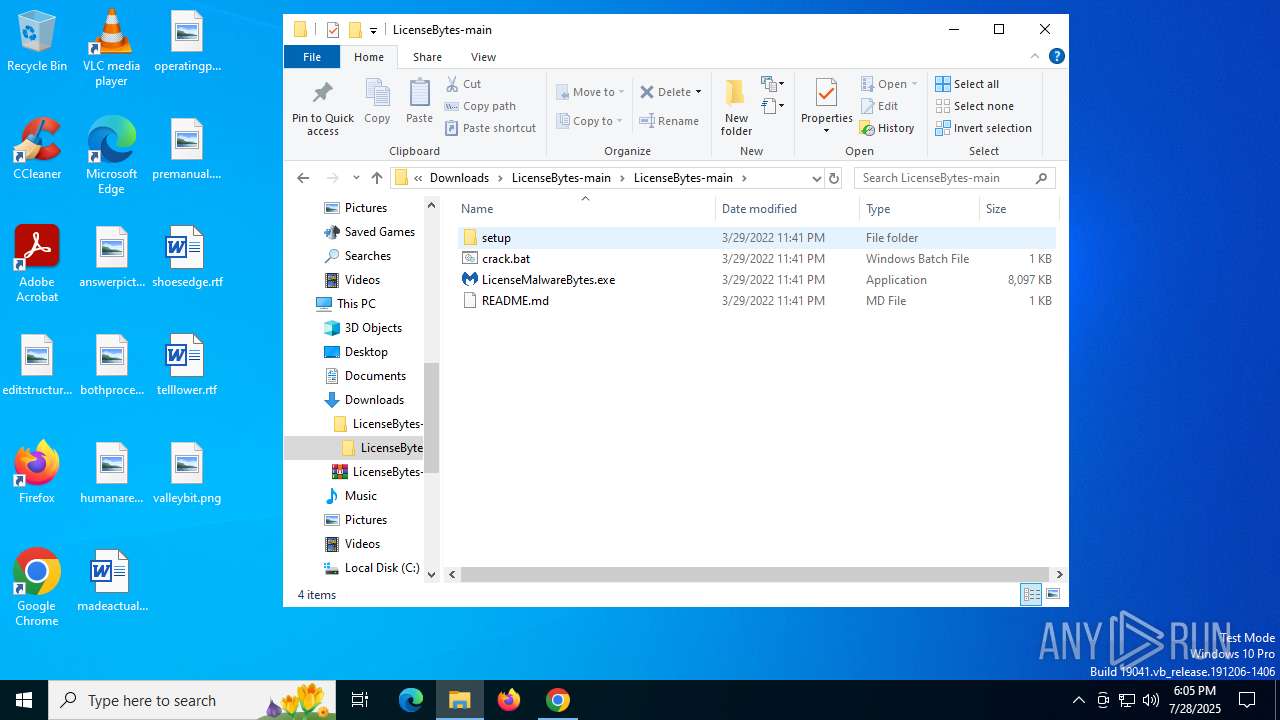
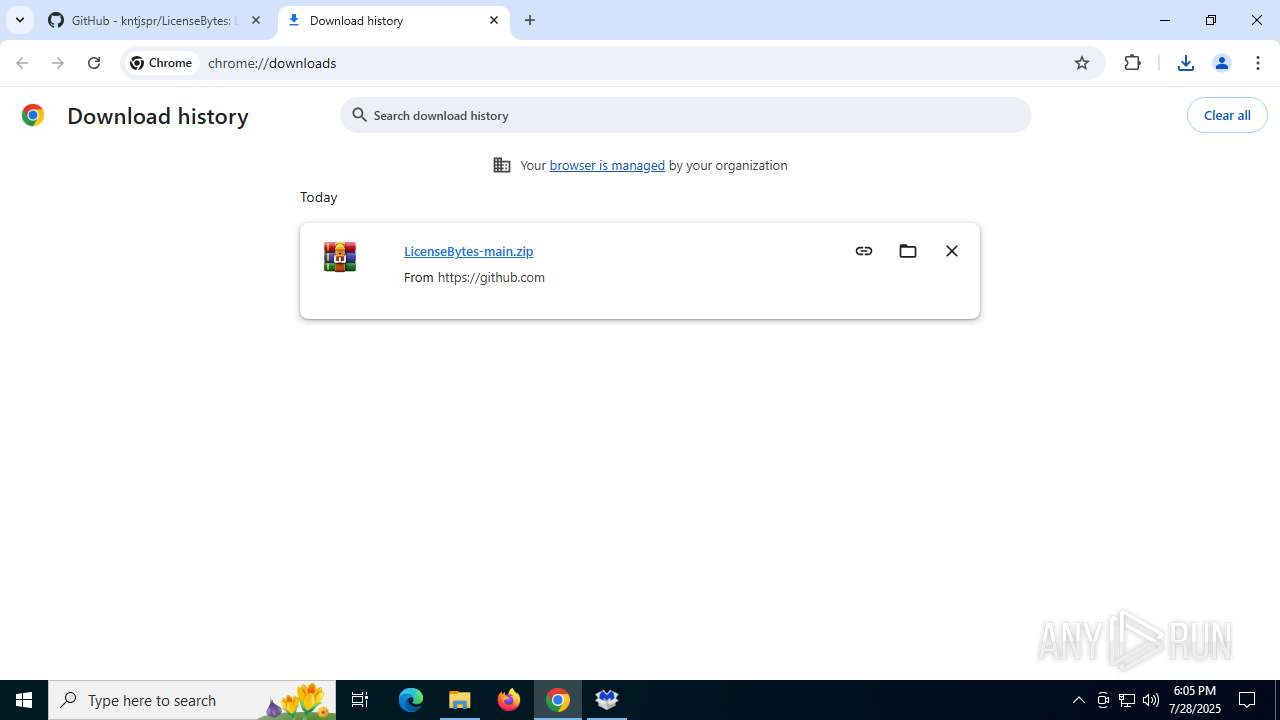
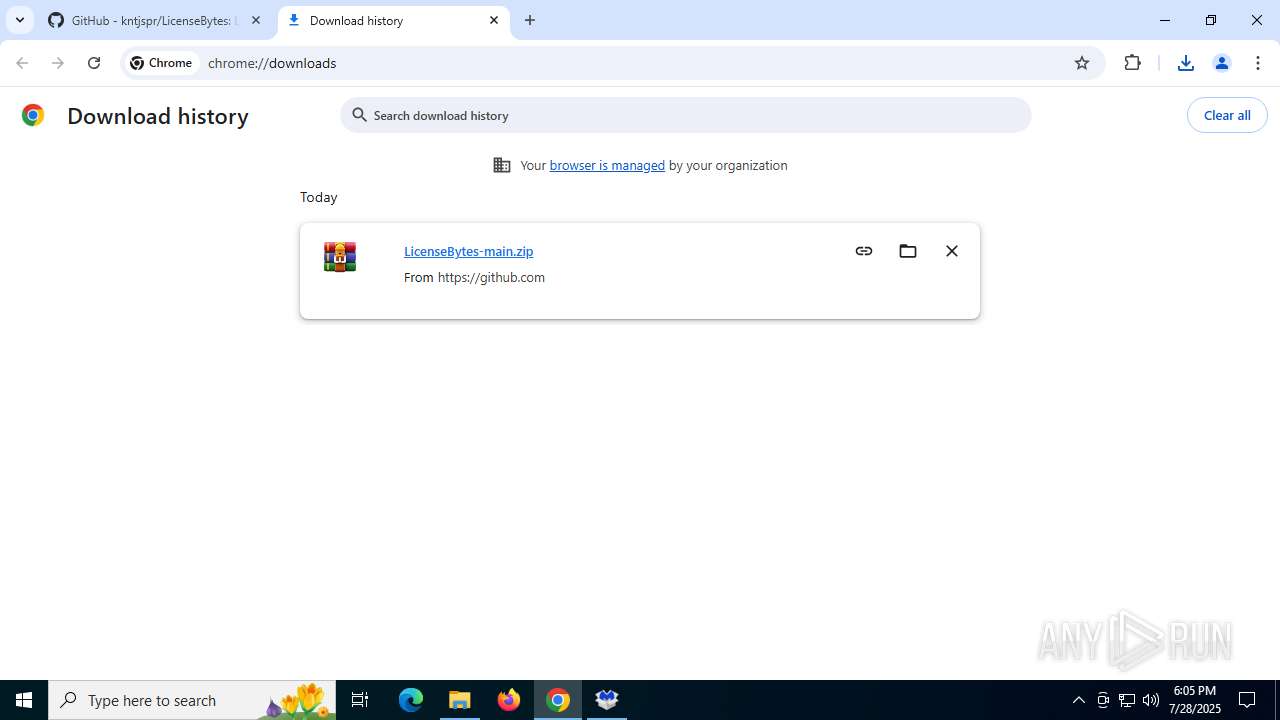
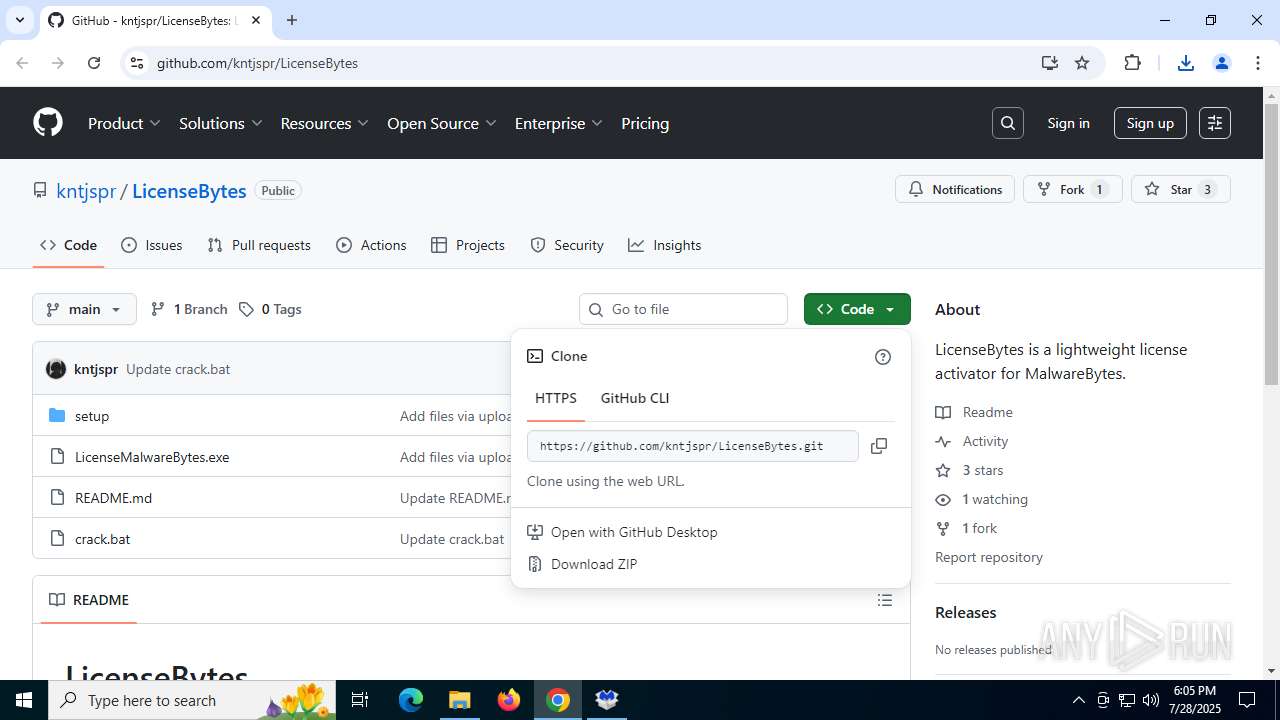
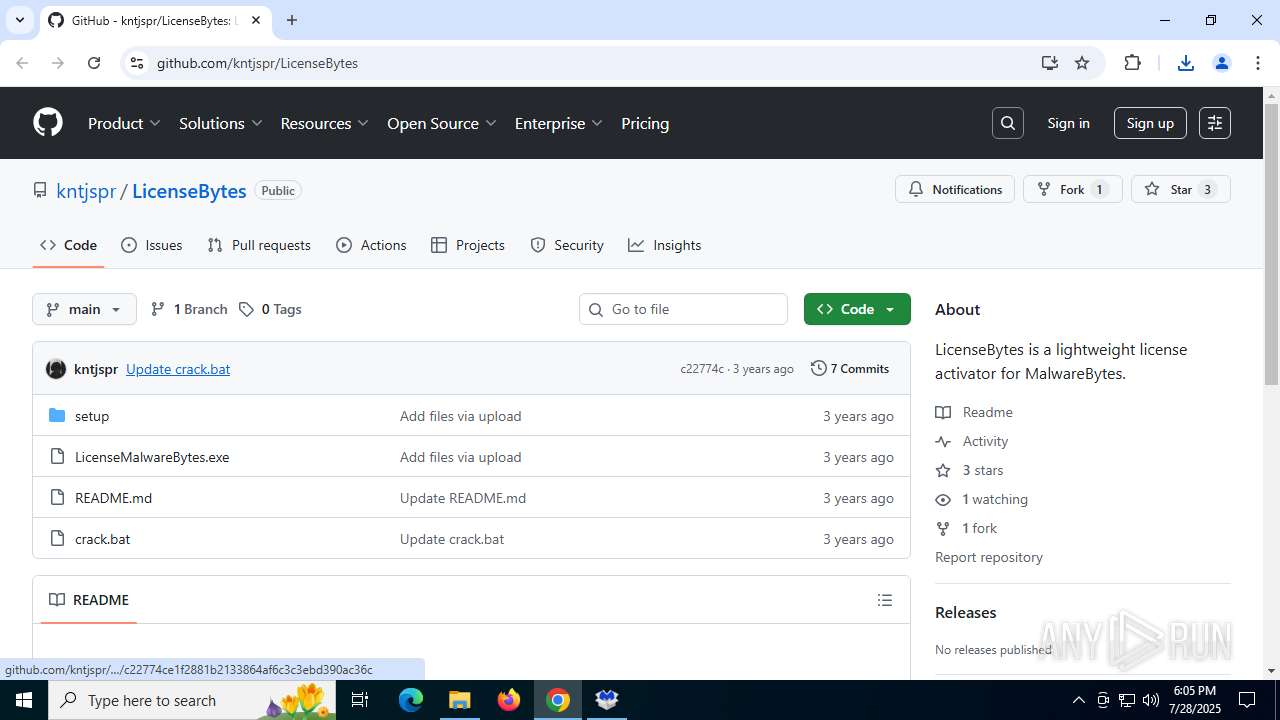
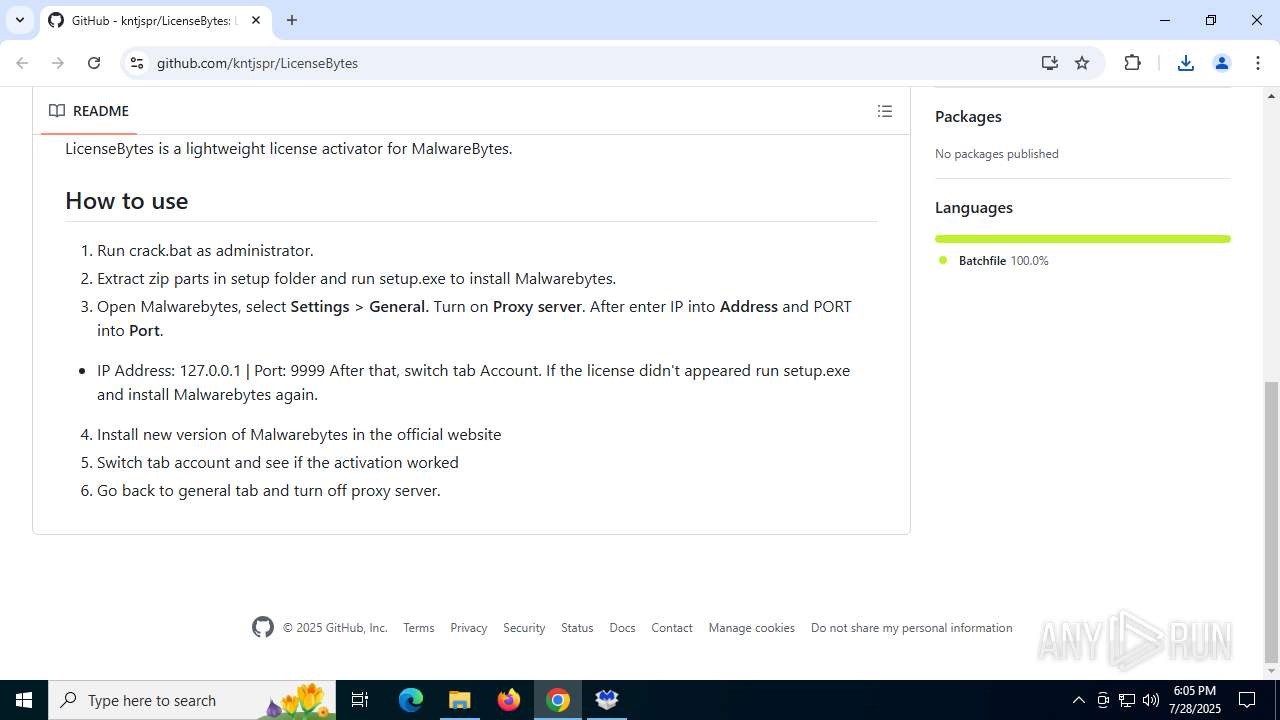
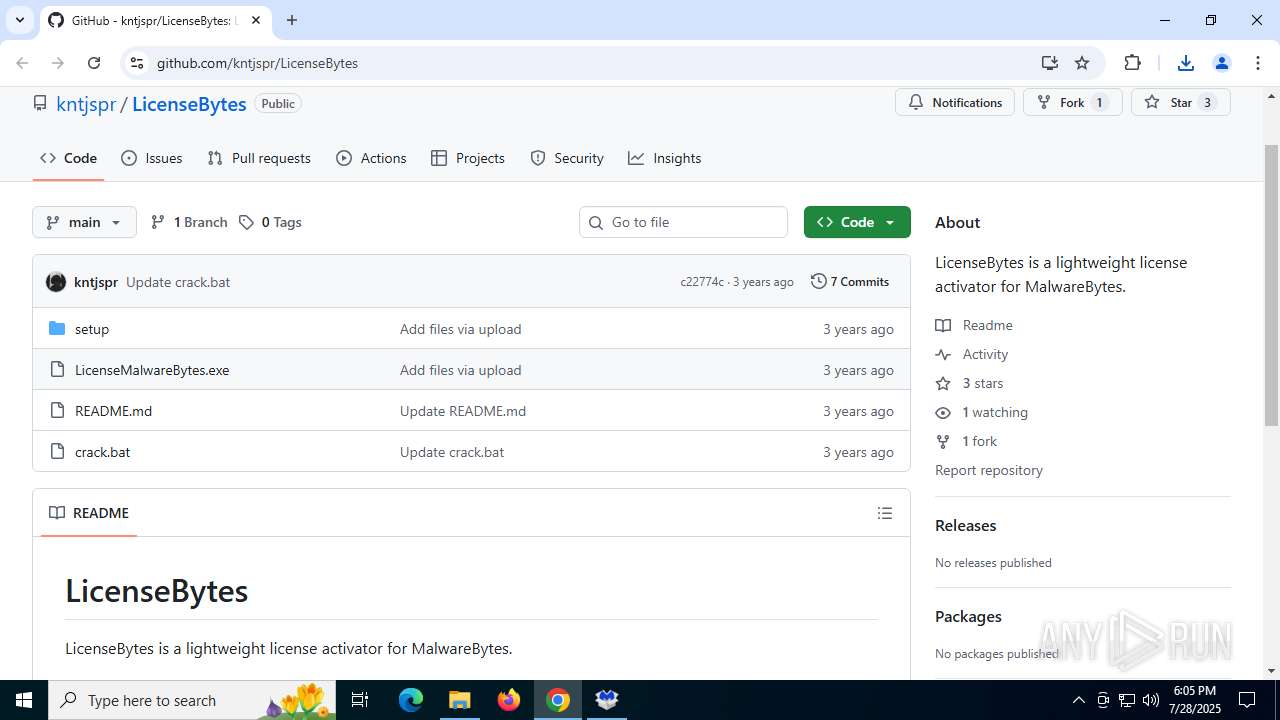
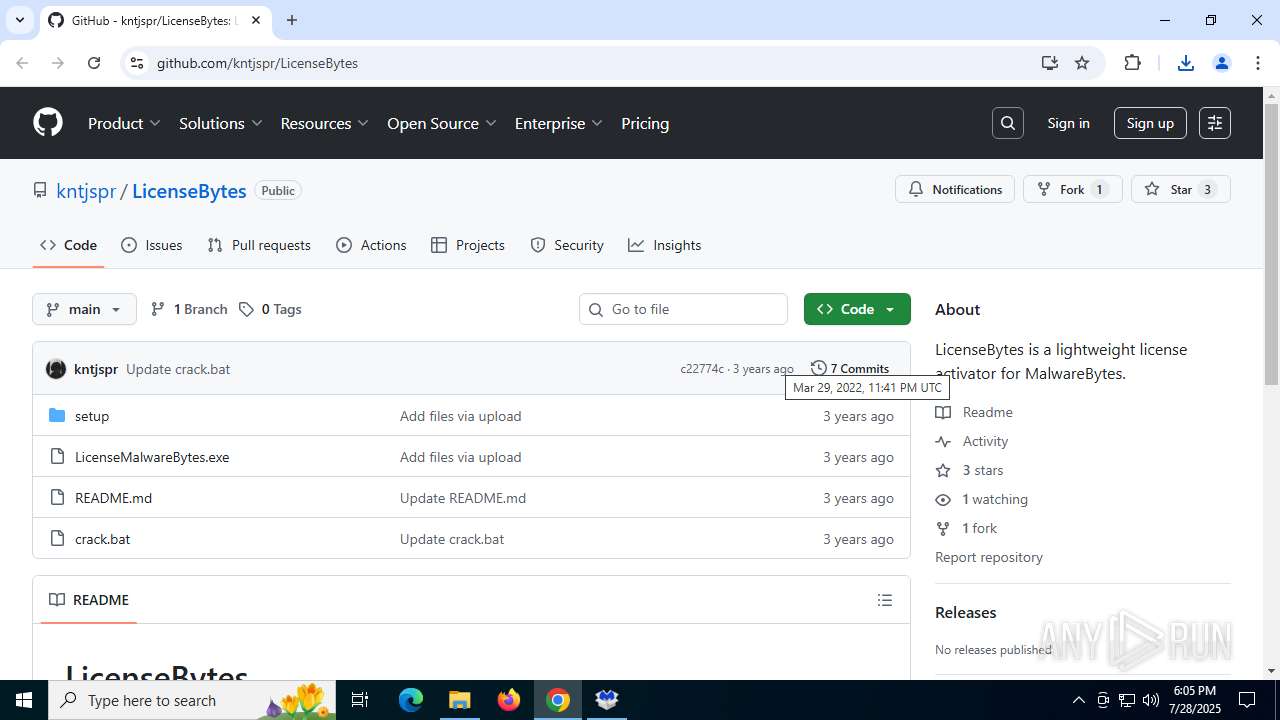
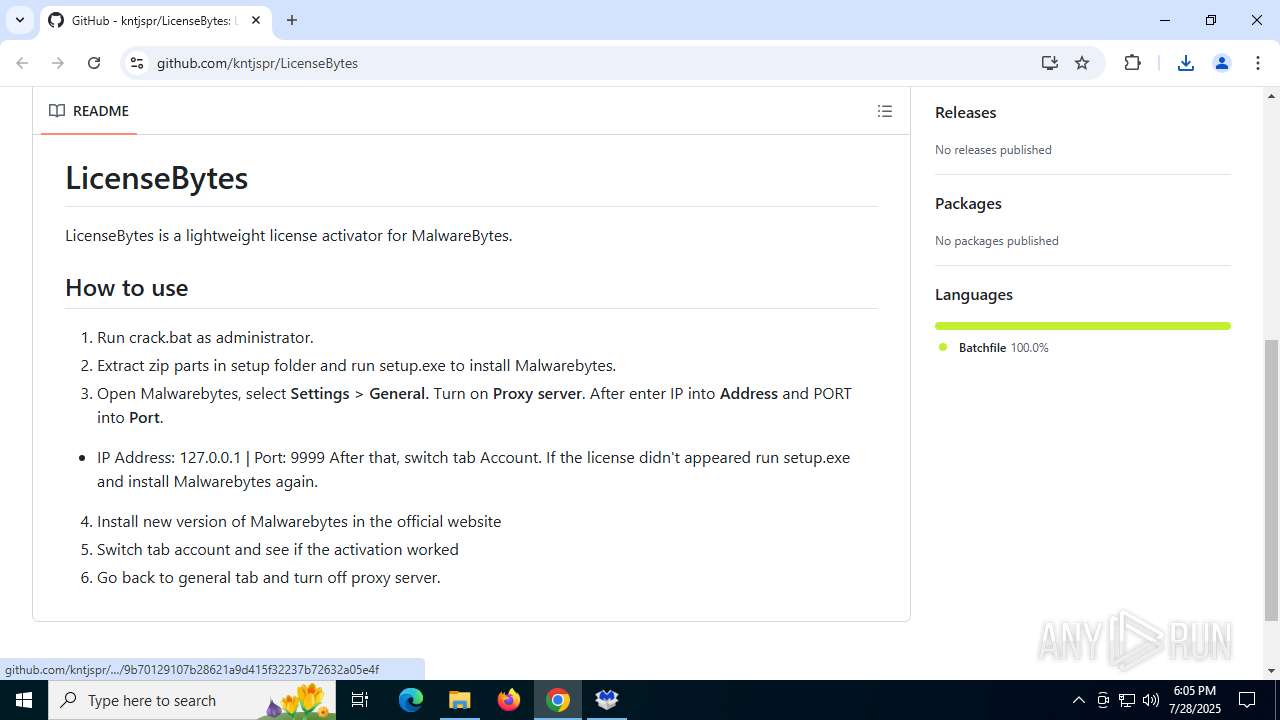
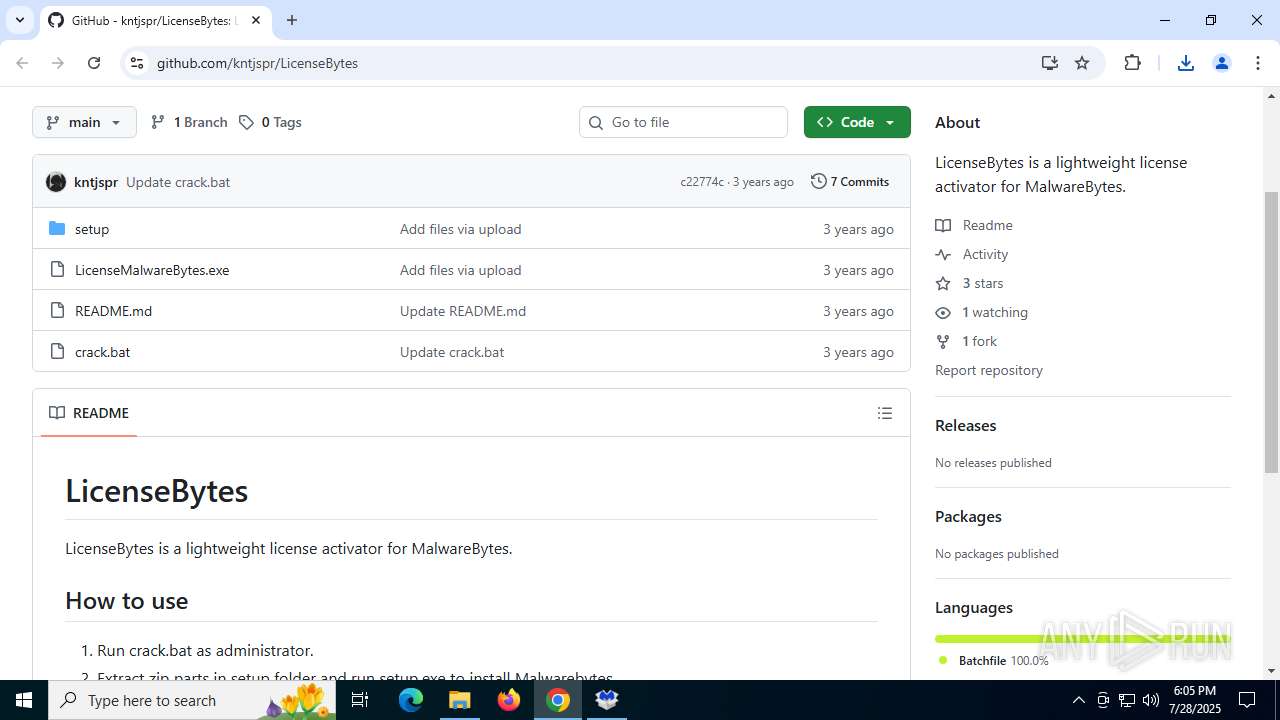
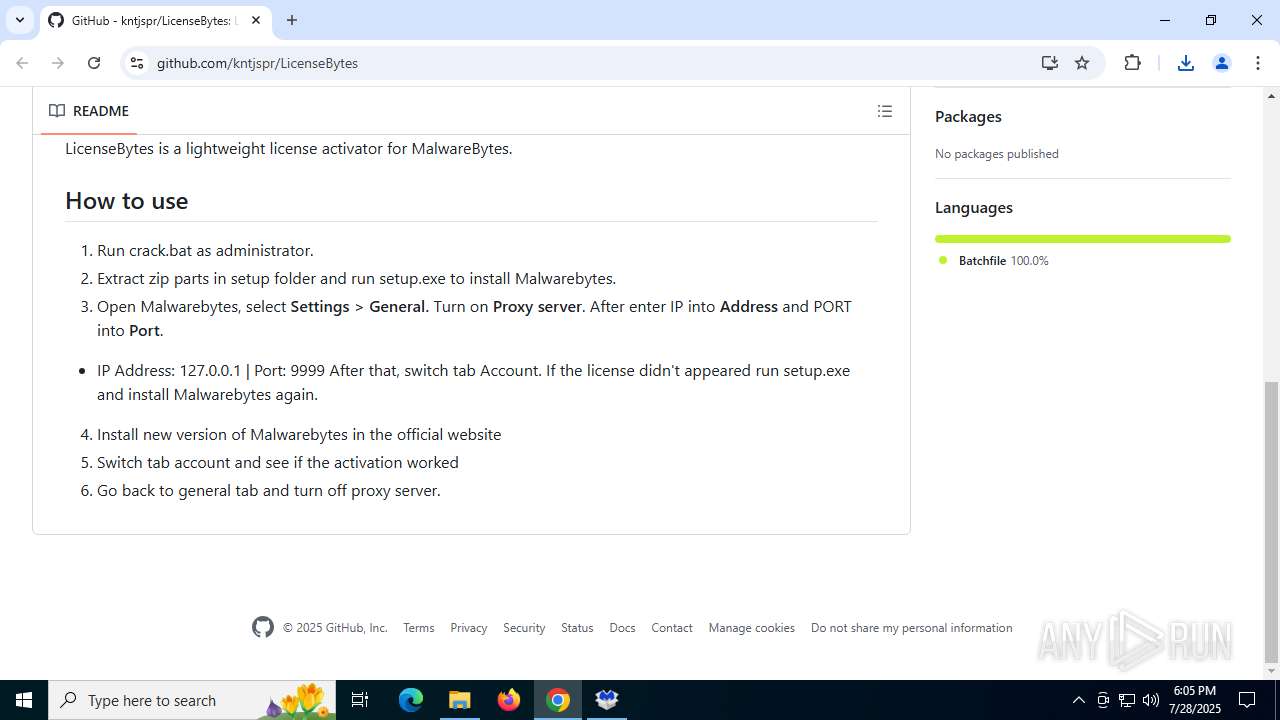
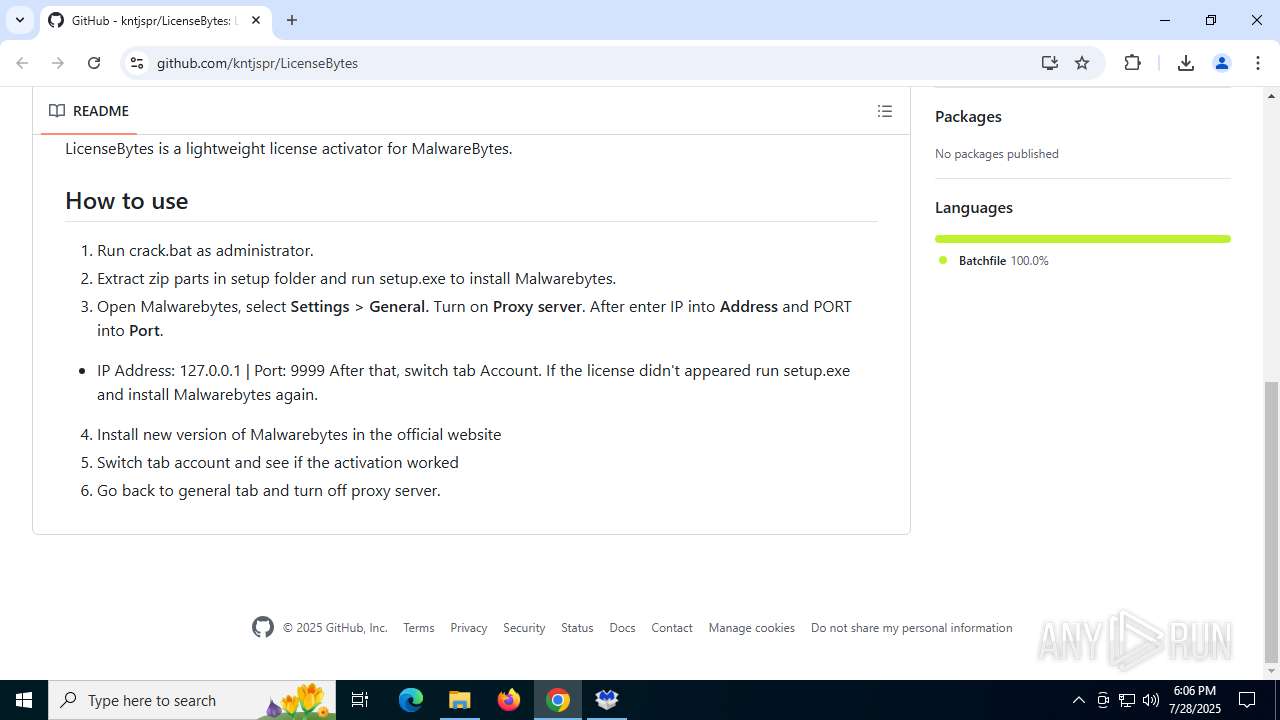
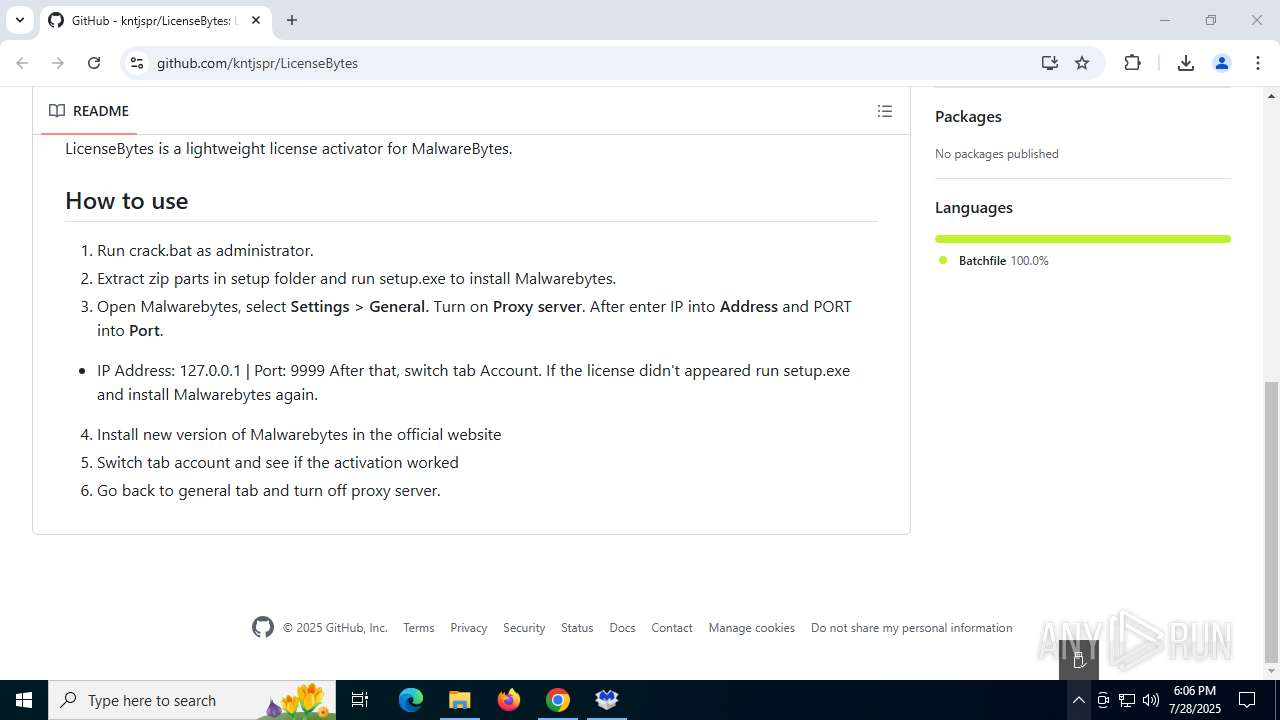
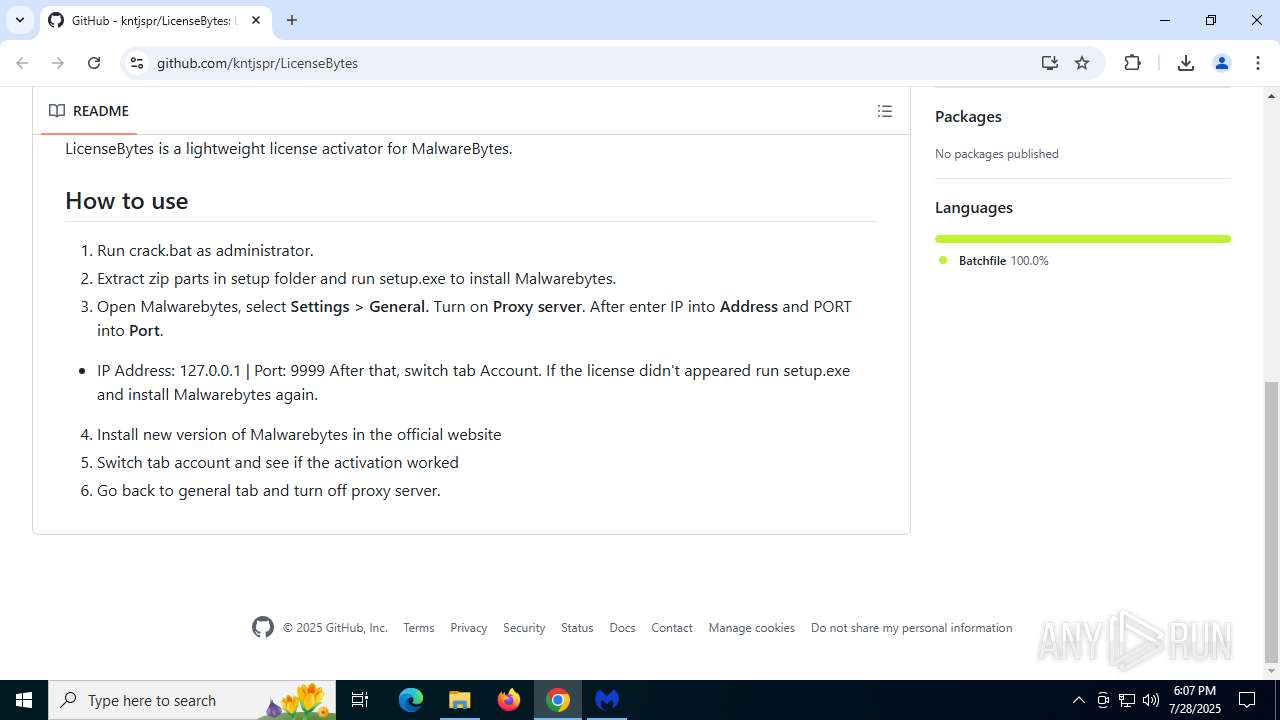
| URL: | https://github.com/kntjspr/LicenseBytes |
| Full analysis: | https://app.any.run/tasks/5627120d-35b3-4ffe-9fd7-68e0e4b77f6d |
| Verdict: | Malicious activity |
| Analysis date: | July 28, 2025, 18:03:59 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 196BED252F6E6673FE0D0F0054FFE689 |
| SHA1: | AFAD15710275ACF0AB10E87CB6C8CD8FD016D9DC |
| SHA256: | FFEF7B9F24D5A5A35667DC7D212595CF95202DB71518A691A82BD1092677BF86 |
| SSDEEP: | 3:N8tEd+LRP1MrFW:2uoL/j |
MALICIOUS
Antivirus name has been found in the command line (generic signature)
- mbam.exe (PID: 3460)
SUSPICIOUS
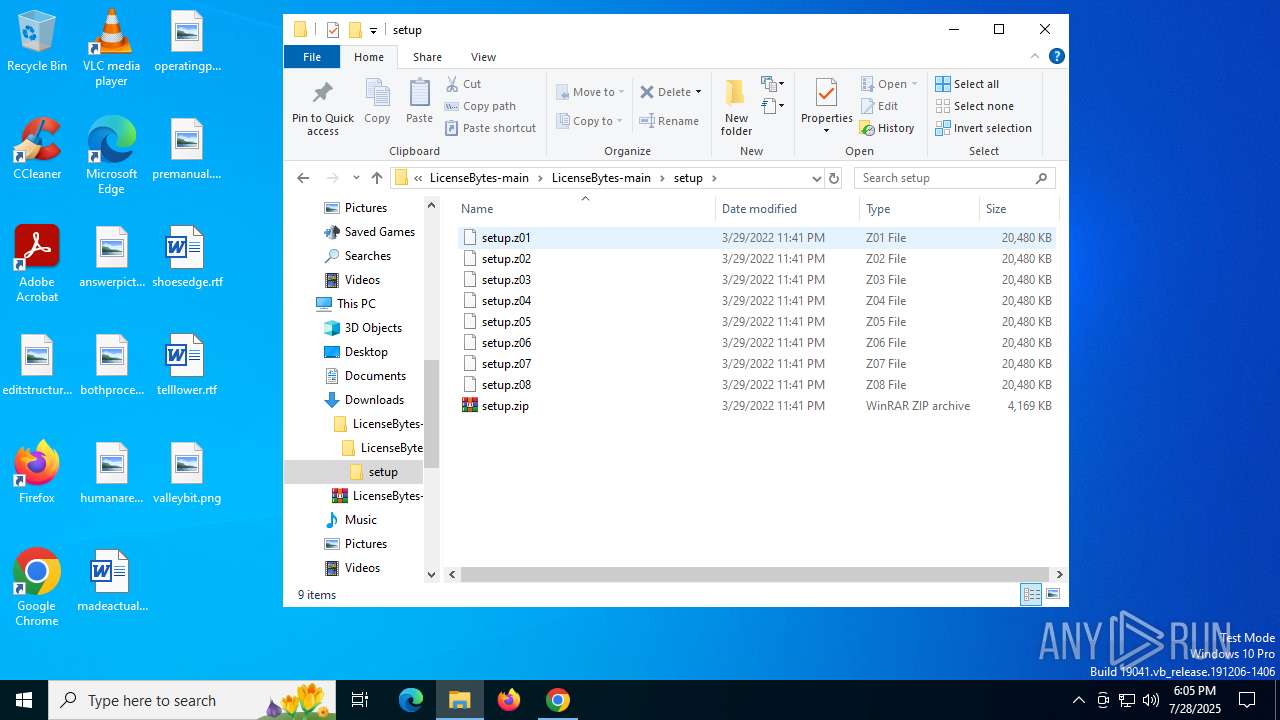
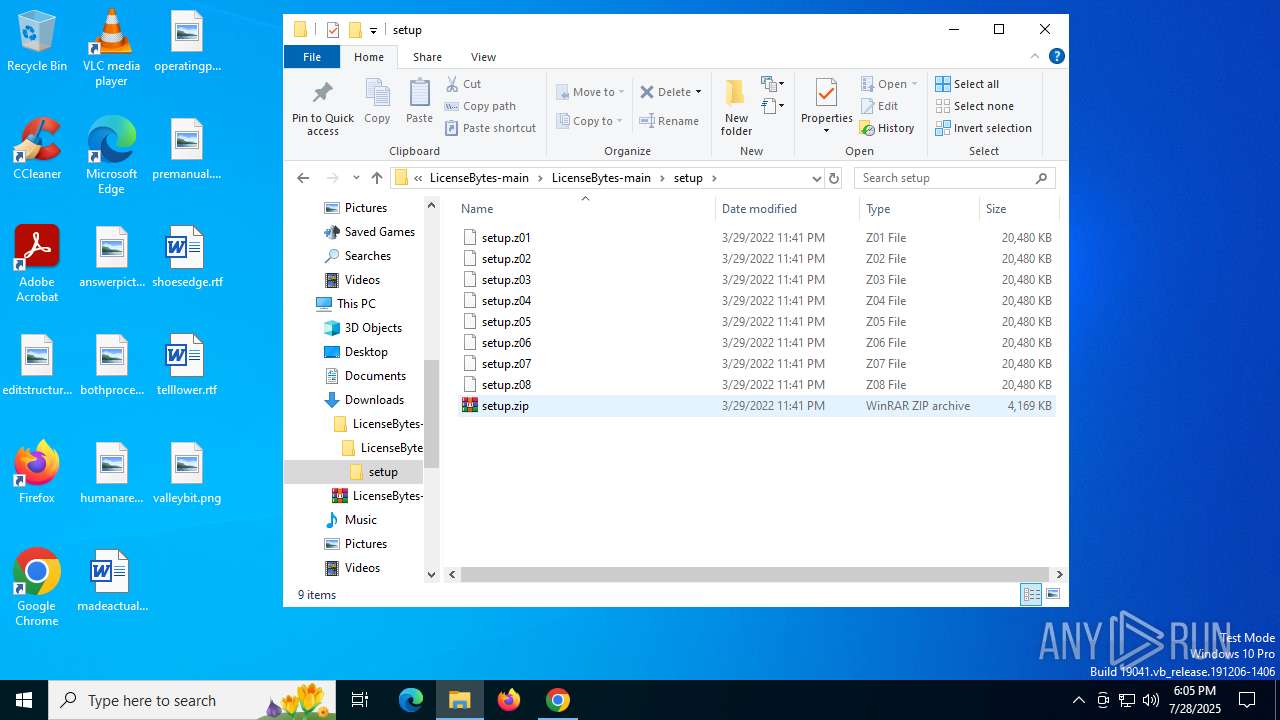
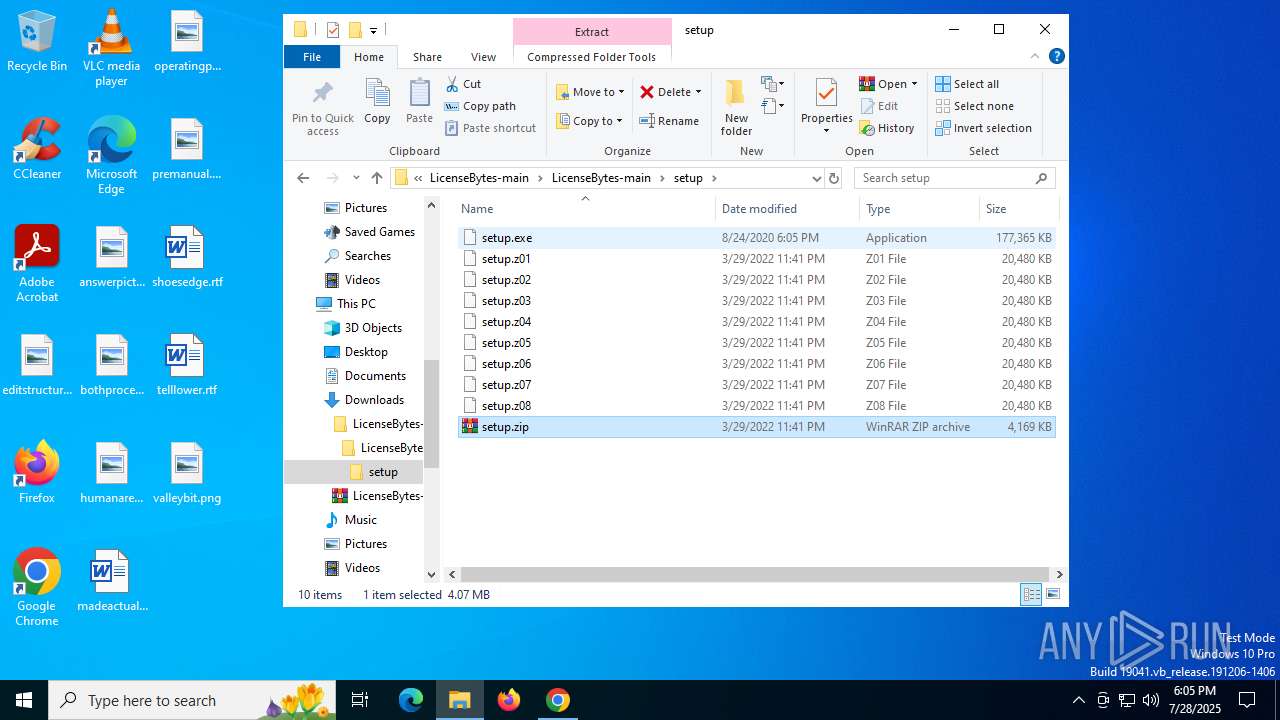
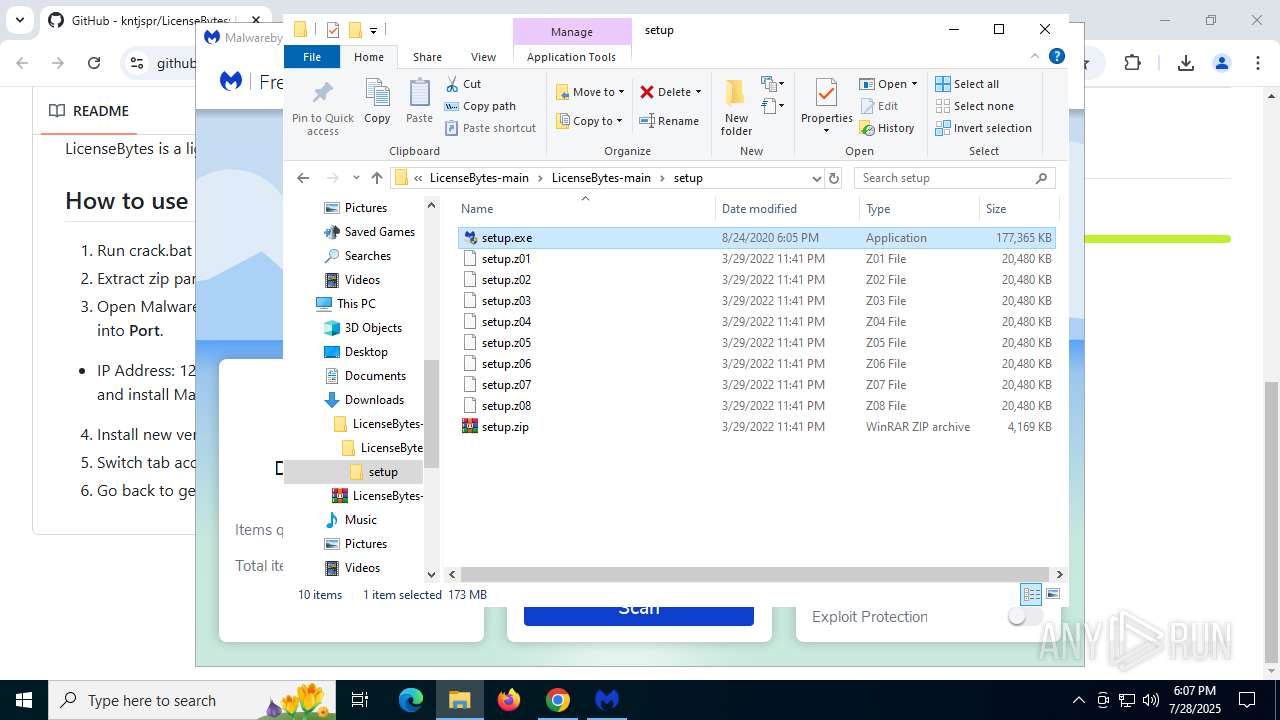
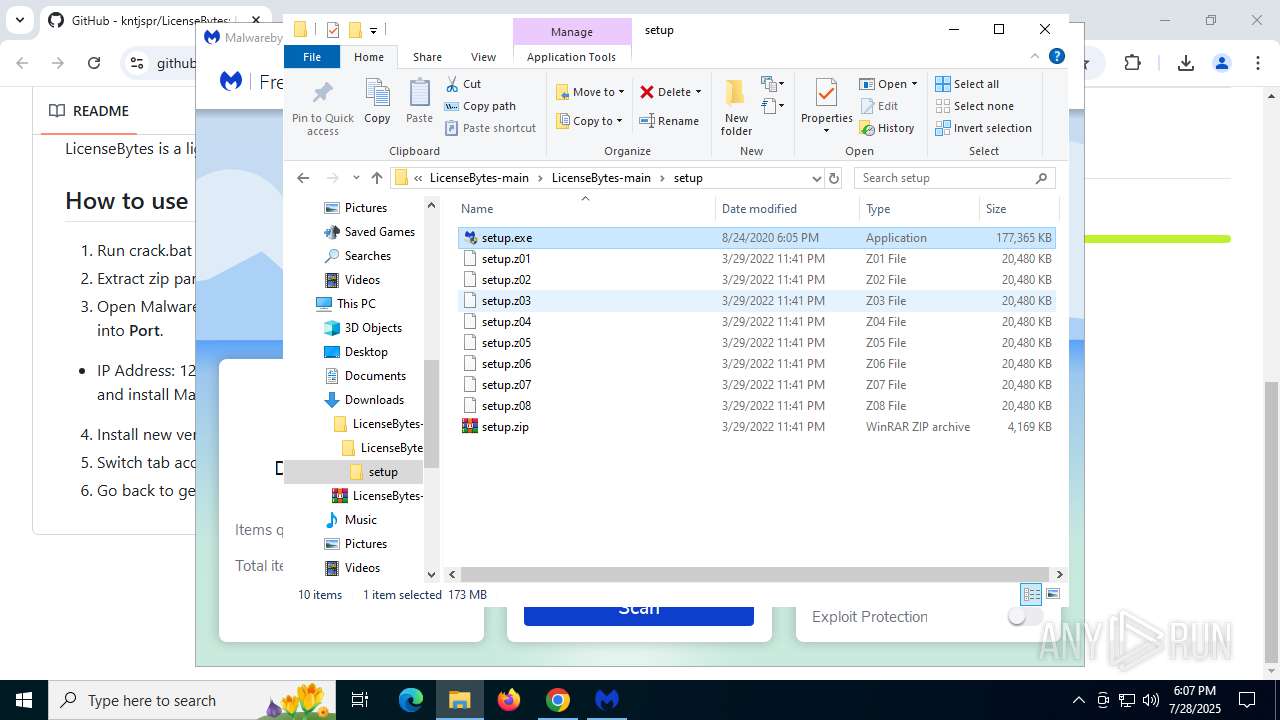
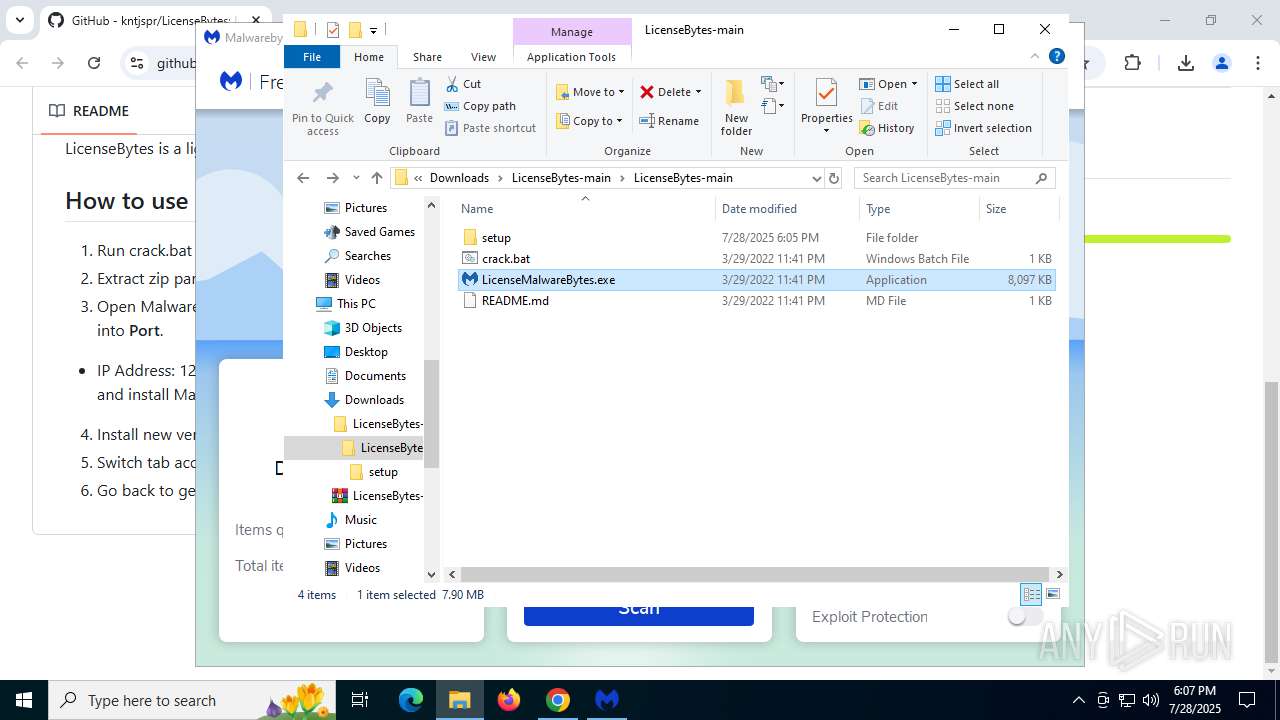
Executable content was dropped or overwritten
- setup.exe (PID: 6400)
- MBAMInstallerService.exe (PID: 7888)
- MBAMService.exe (PID: 2192)
- MBAMService.exe (PID: 984)
- LicenseMalwareBytes.exe (PID: 7776)
- LicenseMalwareBytes.exe (PID: 3876)
Searches for installed software
- setup.exe (PID: 6400)
- MBAMInstallerService.exe (PID: 7888)
Executes as Windows Service
- MBAMInstallerService.exe (PID: 7888)
- MBAMService.exe (PID: 2192)
Drops a system driver (possible attempt to evade defenses)
- MBAMInstallerService.exe (PID: 7888)
- MBAMService.exe (PID: 984)
- MBAMService.exe (PID: 2192)
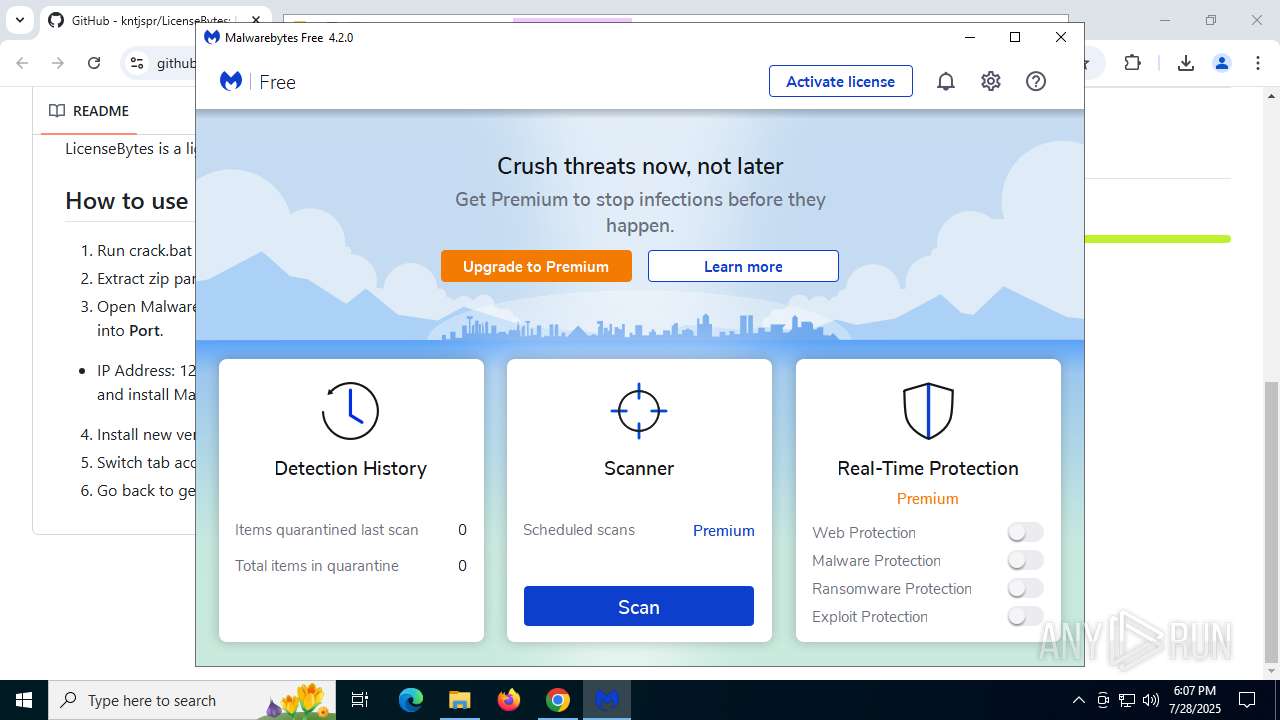
The process verifies whether the antivirus software is installed
- MBAMInstallerService.exe (PID: 7888)
- setup.exe (PID: 6400)
- MBAMService.exe (PID: 984)
- MBAMService.exe (PID: 2192)
- mbamtray.exe (PID: 7404)
- mbam.exe (PID: 3460)
There is functionality for taking screenshot (YARA)
- setup.exe (PID: 6400)
- mbamtray.exe (PID: 7404)
- mbam.exe (PID: 3460)
The process drops C-runtime libraries
- MBAMInstallerService.exe (PID: 7888)
- LicenseMalwareBytes.exe (PID: 7776)
- LicenseMalwareBytes.exe (PID: 3876)
Drops 7-zip archiver for unpacking
- MBAMInstallerService.exe (PID: 7888)
Process drops legitimate windows executable
- MBAMInstallerService.exe (PID: 7888)
- LicenseMalwareBytes.exe (PID: 7776)
- LicenseMalwareBytes.exe (PID: 3876)
The process creates files with name similar to system file names
- setup.exe (PID: 6400)
Changes Internet Explorer settings (feature browser emulation)
- MBAMInstallerService.exe (PID: 7888)
- MBAMService.exe (PID: 2192)
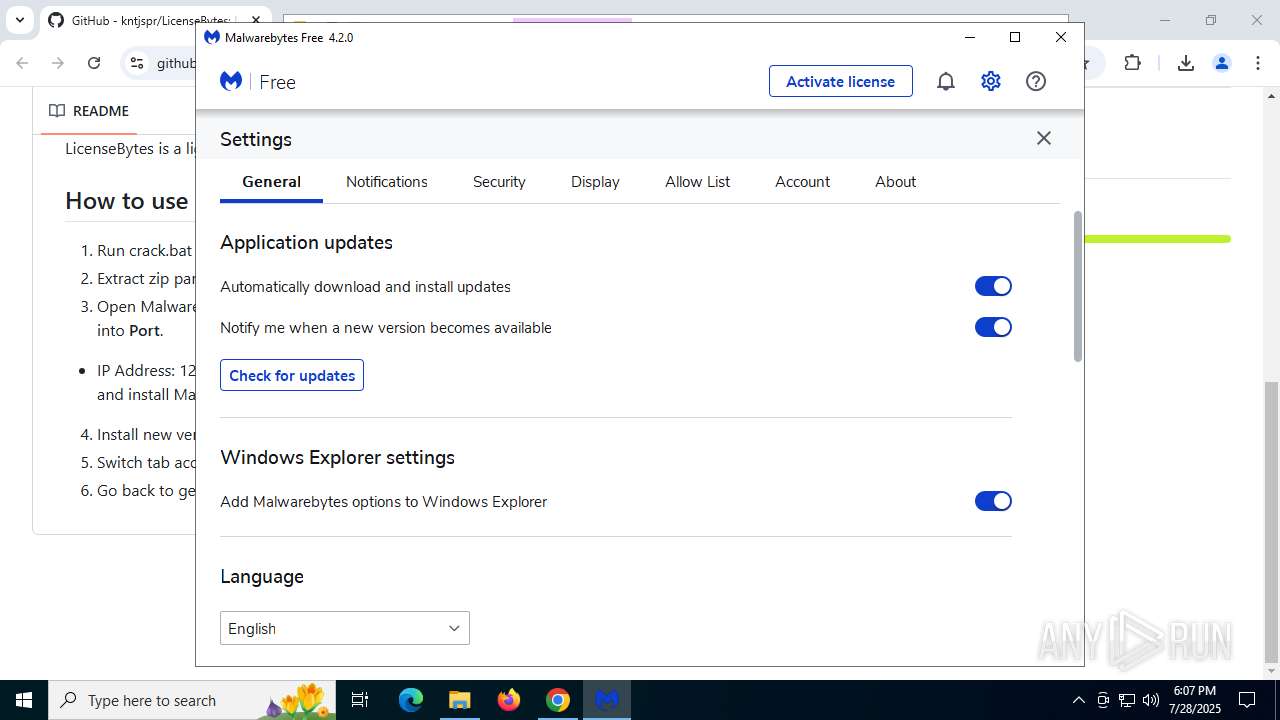
Creates or modifies Windows services
- MBAMService.exe (PID: 984)
- MBAMService.exe (PID: 2192)
Creates files in the driver directory
- MBAMService.exe (PID: 984)
- MBAMInstallerService.exe (PID: 7888)
- MBAMService.exe (PID: 2192)
Creates/Modifies COM task schedule object
- MBAMService.exe (PID: 2192)
Adds/modifies Windows certificates
- certutil.exe (PID: 3880)
- certutil.exe (PID: 7952)
Reads security settings of Internet Explorer
- mbamtray.exe (PID: 7404)
- mbam.exe (PID: 3460)
Creates a software uninstall entry
- MBAMInstallerService.exe (PID: 7888)
Reads the date of Windows installation
- mbam.exe (PID: 3460)
Process drops python dynamic module
- LicenseMalwareBytes.exe (PID: 7776)
- LicenseMalwareBytes.exe (PID: 3876)
Detected use of alternative data streams (AltDS)
- mbam.exe (PID: 3460)
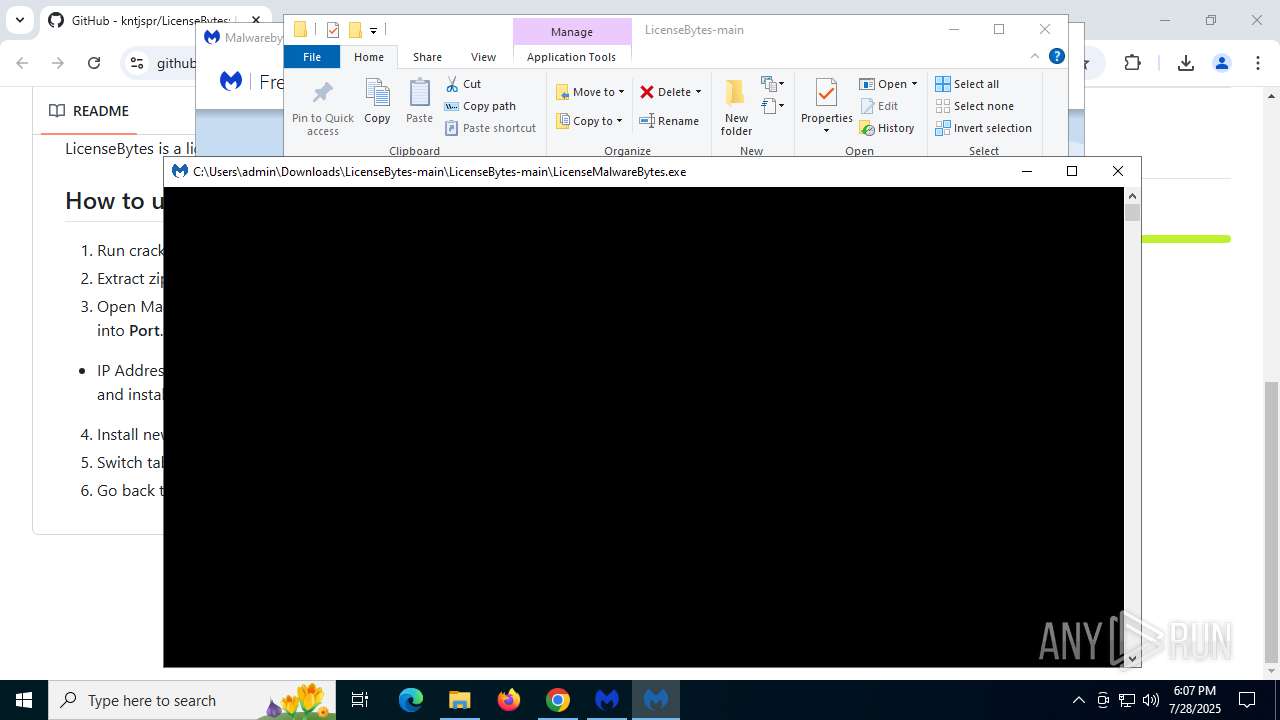
Application launched itself
- LicenseMalwareBytes.exe (PID: 7776)
- LicenseMalwareBytes.exe (PID: 3876)
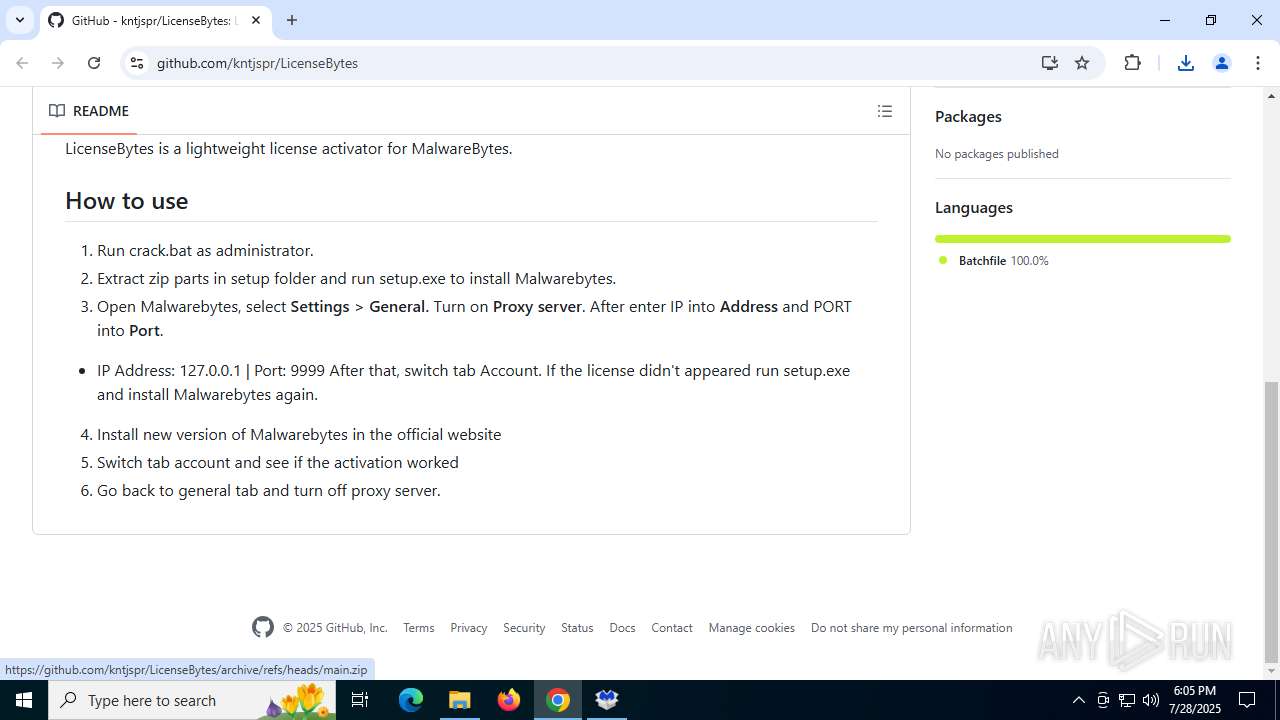
Modifies hosts file to alter network resolution
- LicenseMalwareBytes.exe (PID: 7748)
- LicenseMalwareBytes.exe (PID: 620)
Reads the BIOS version
- MBAMService.exe (PID: 2192)
Loads Python modules
- LicenseMalwareBytes.exe (PID: 7748)
- LicenseMalwareBytes.exe (PID: 620)
INFO
Application launched itself
- chrome.exe (PID: 2228)
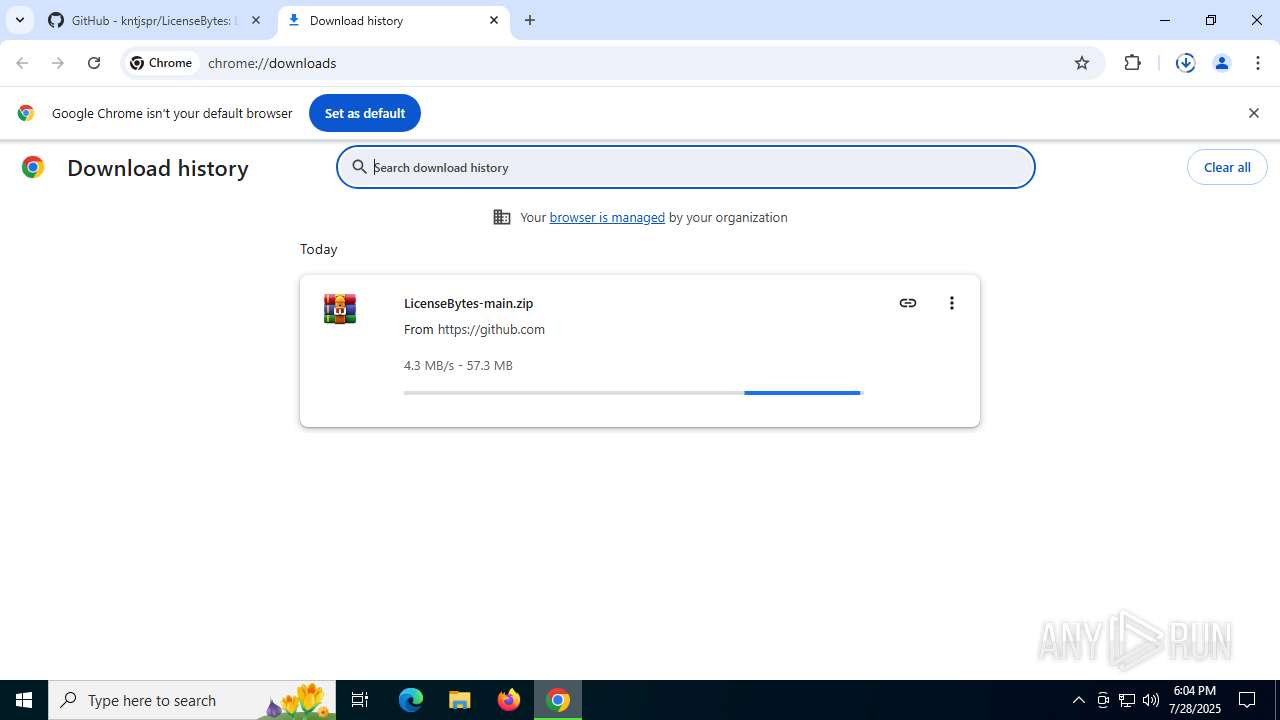
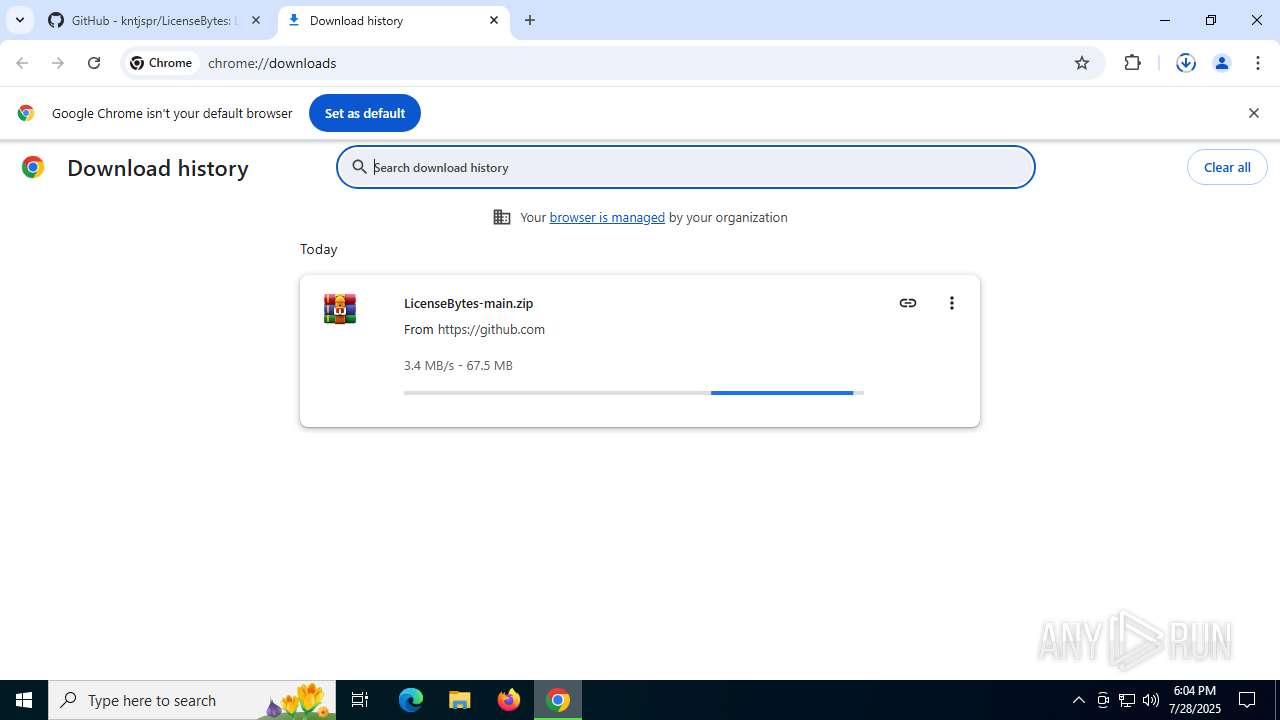
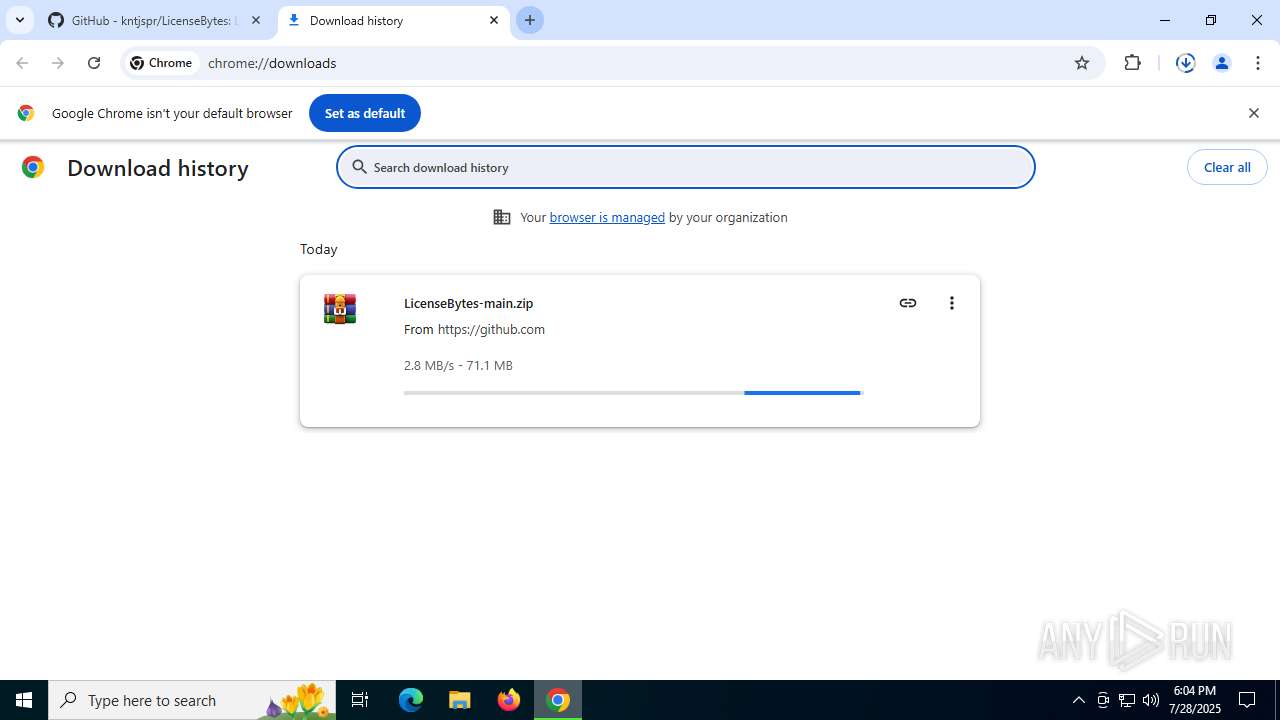
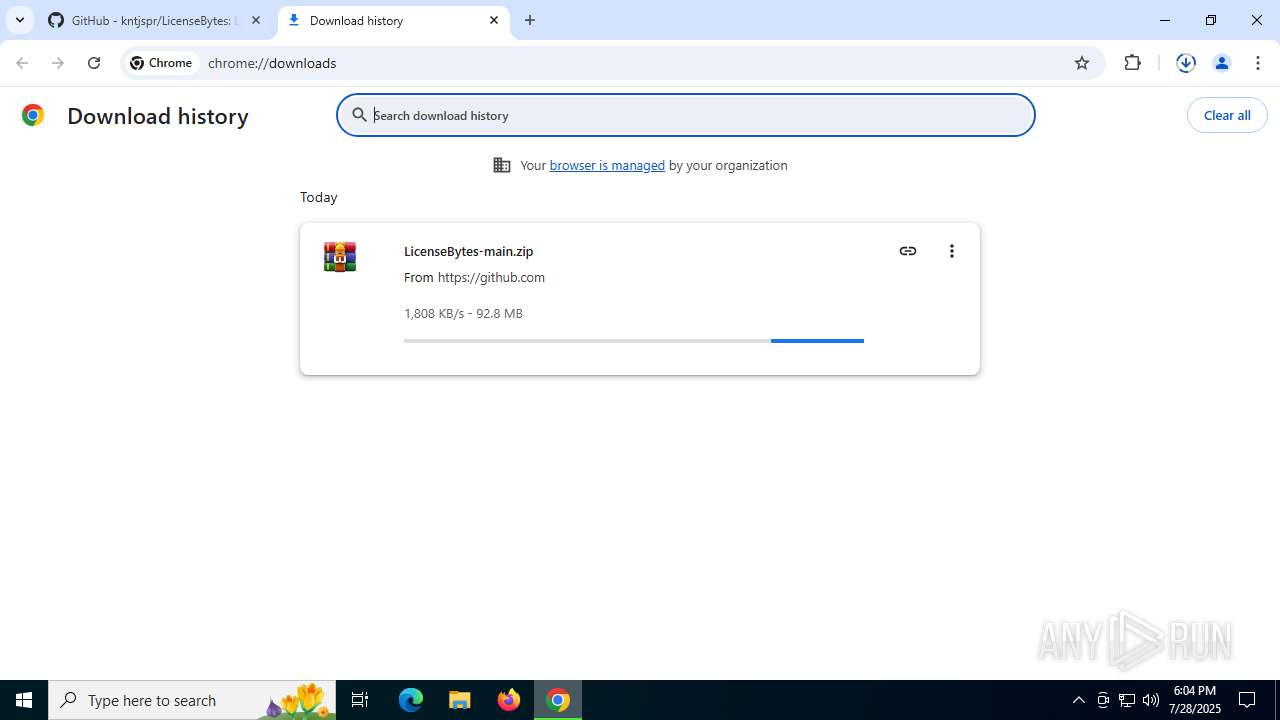
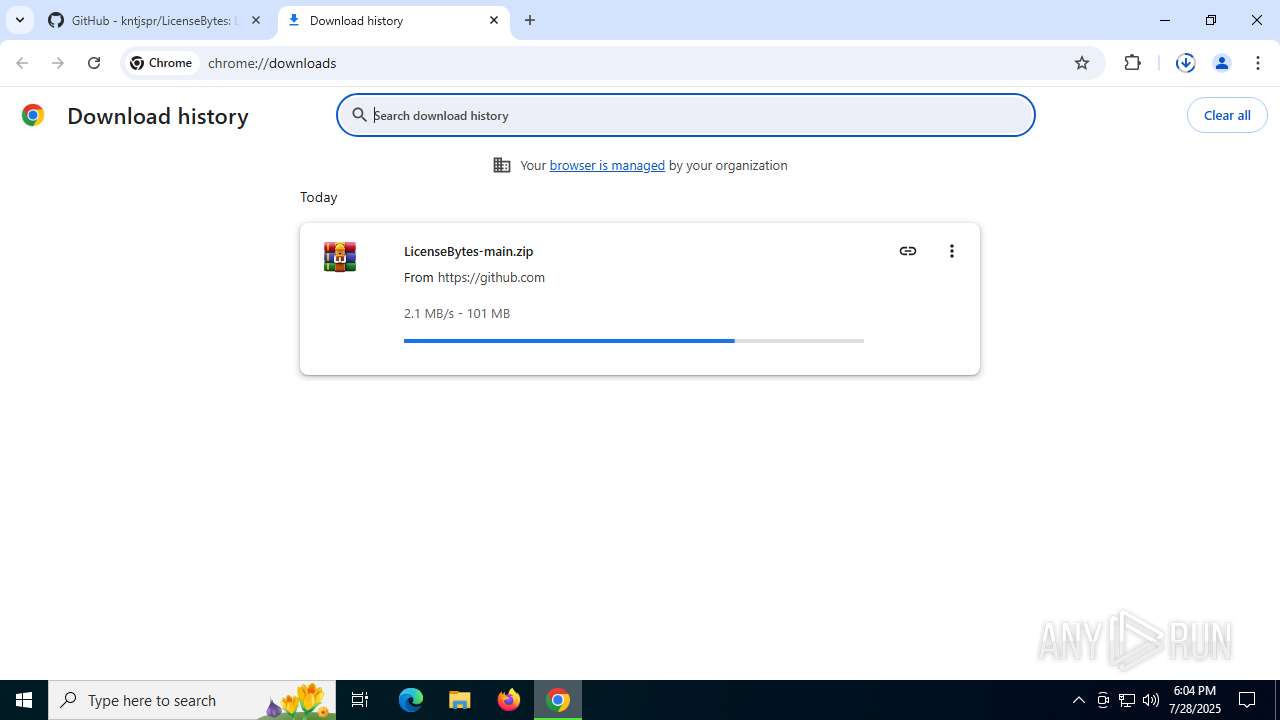
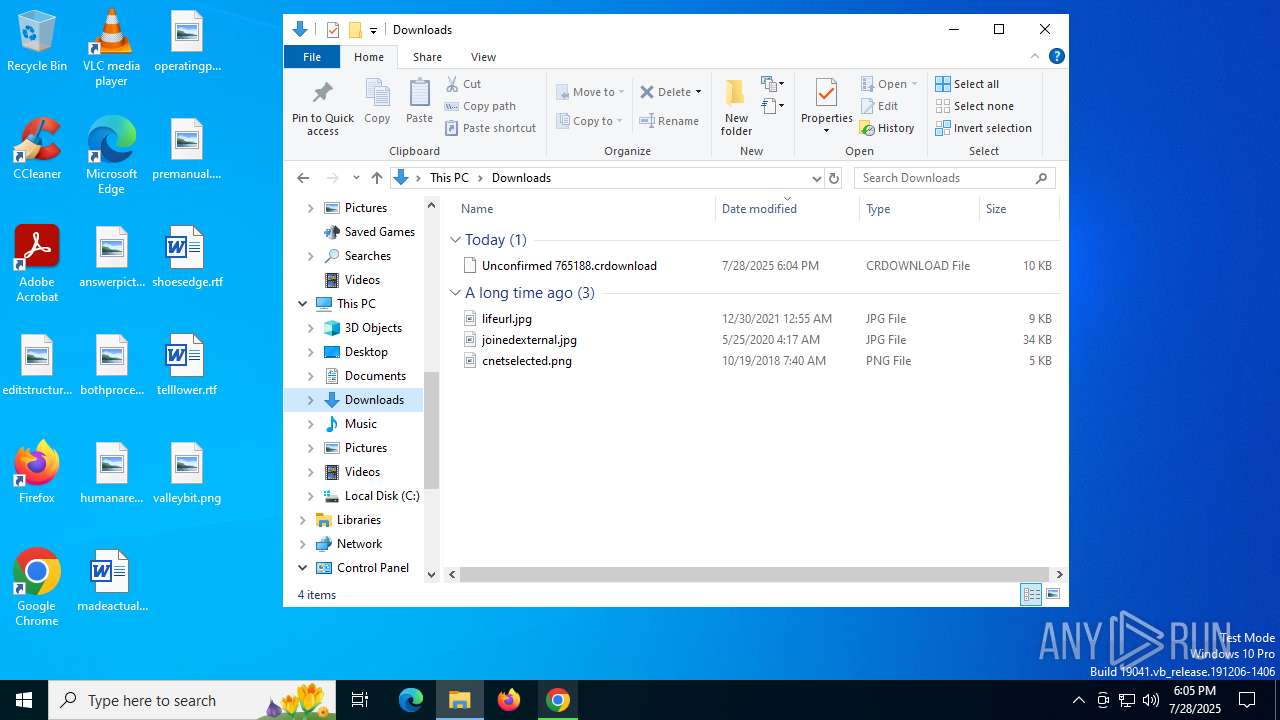
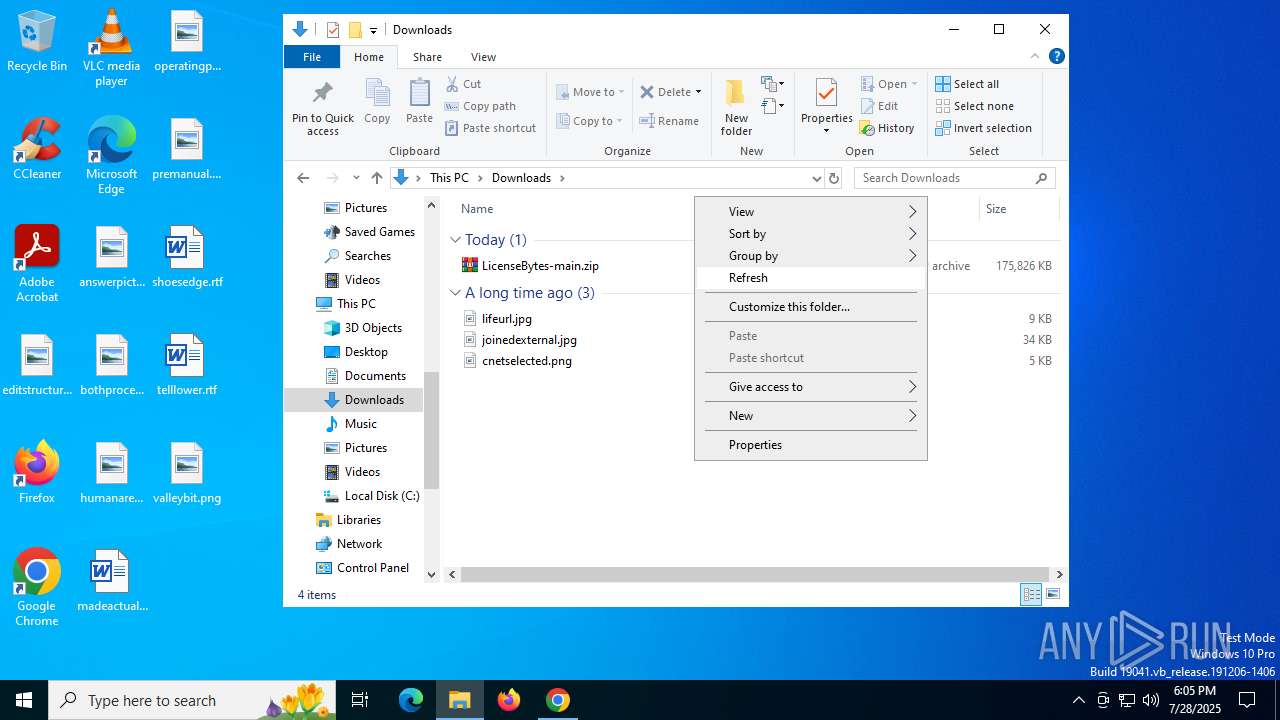
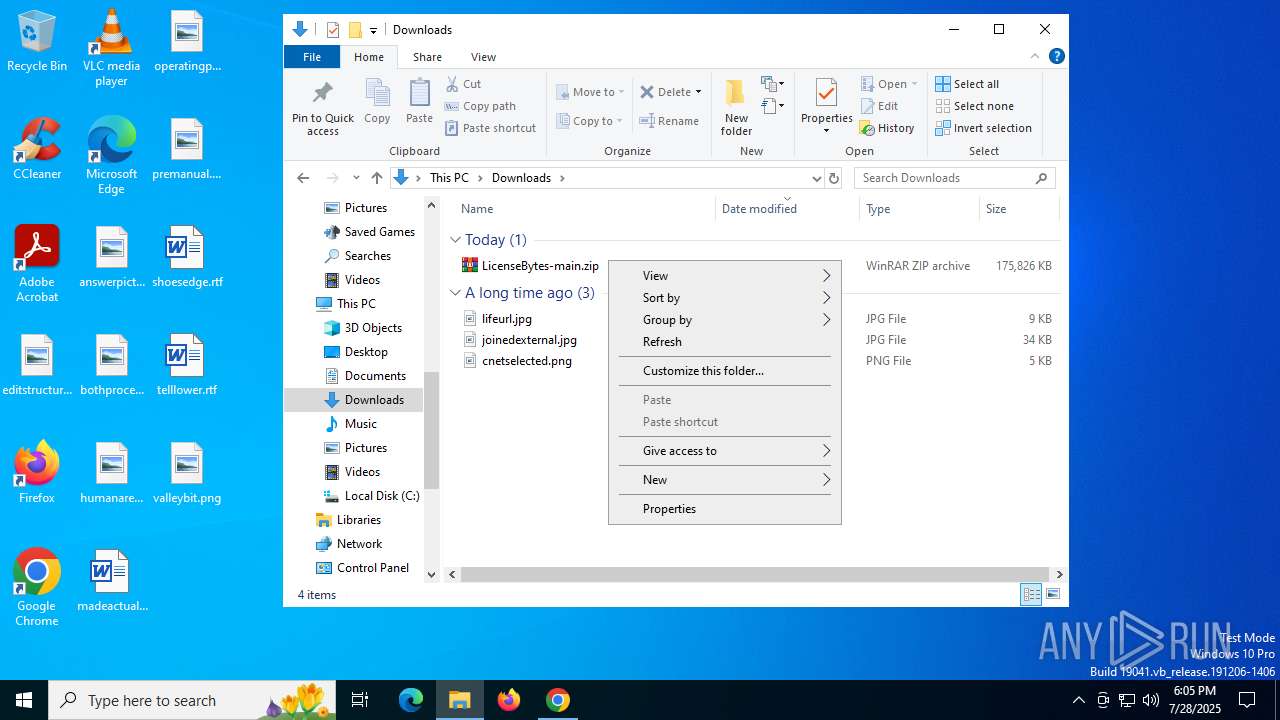
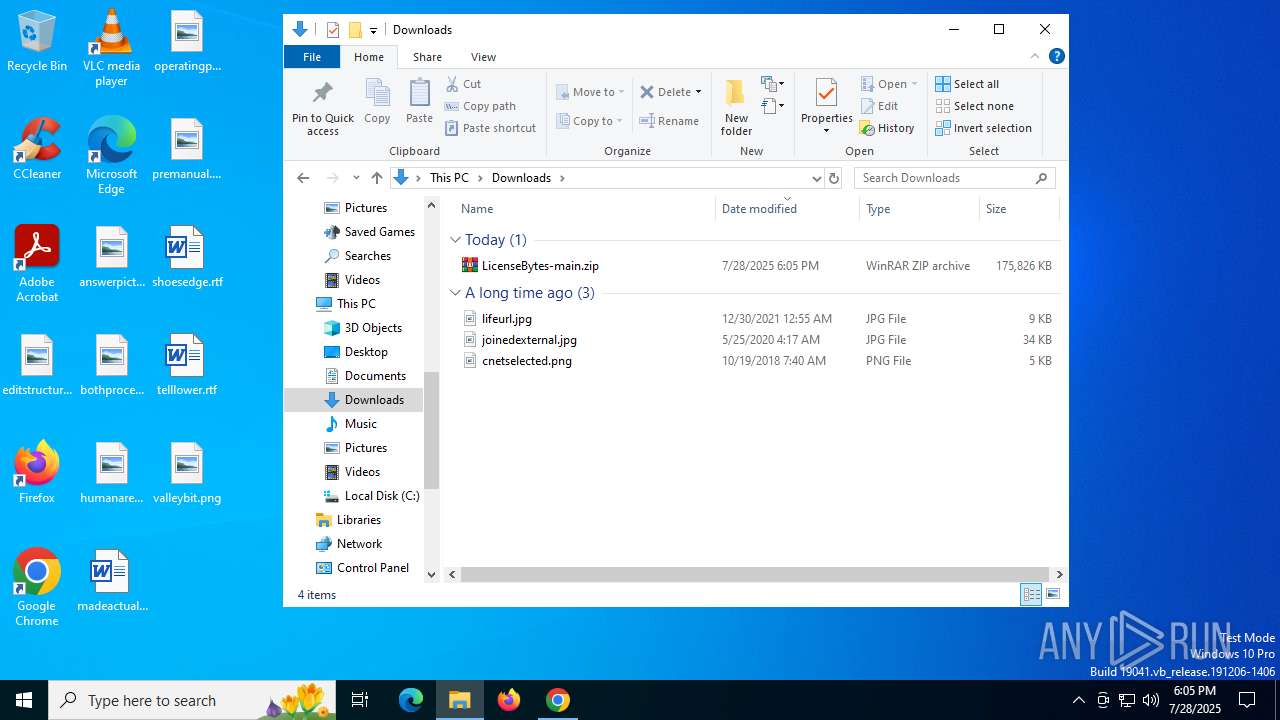
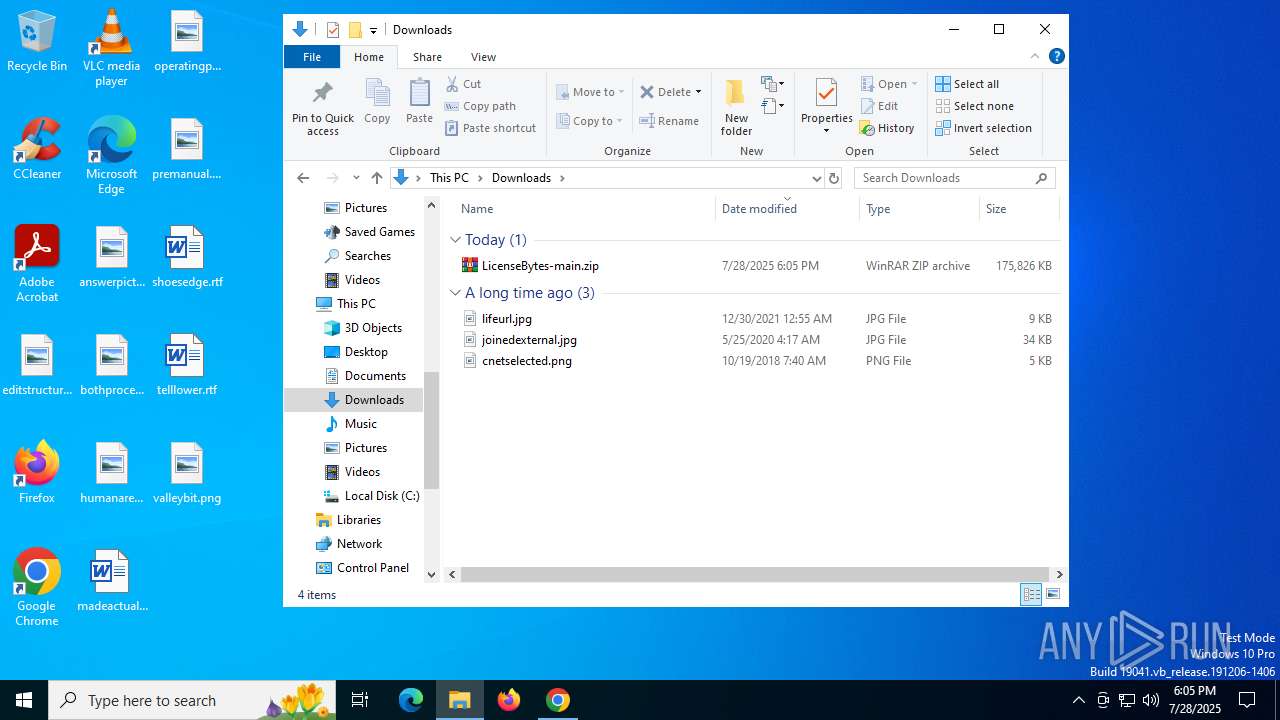
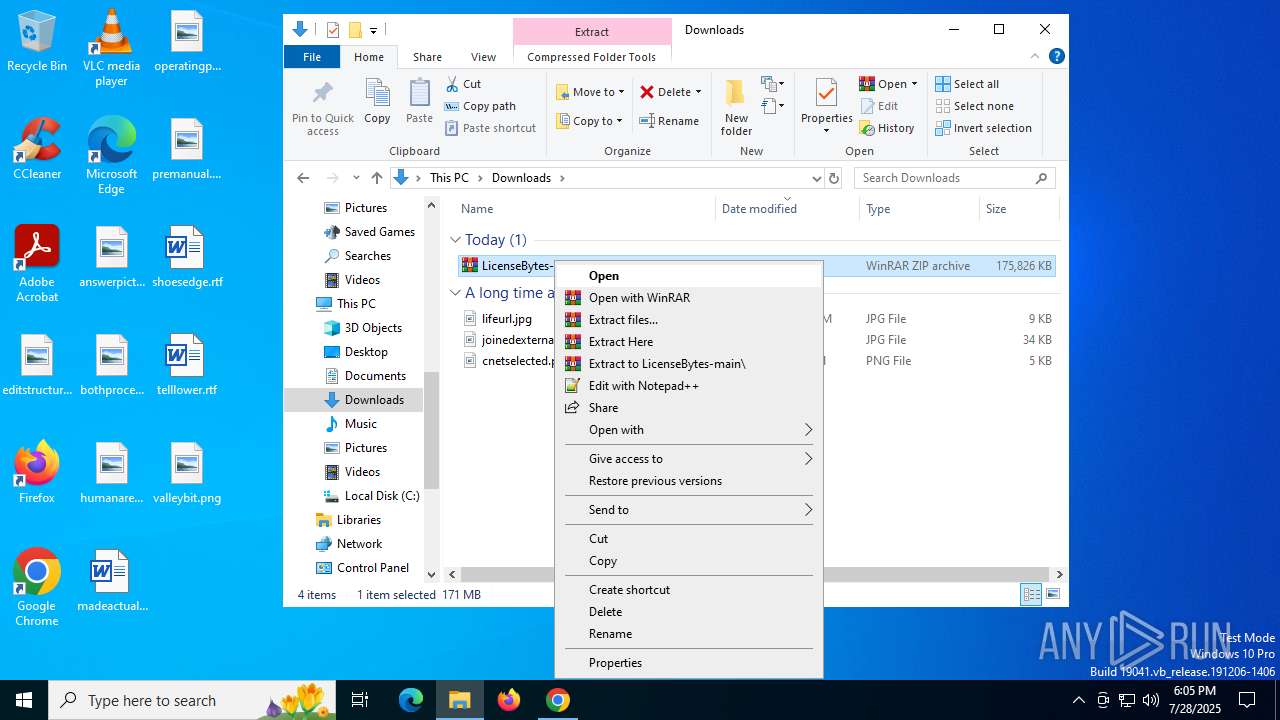
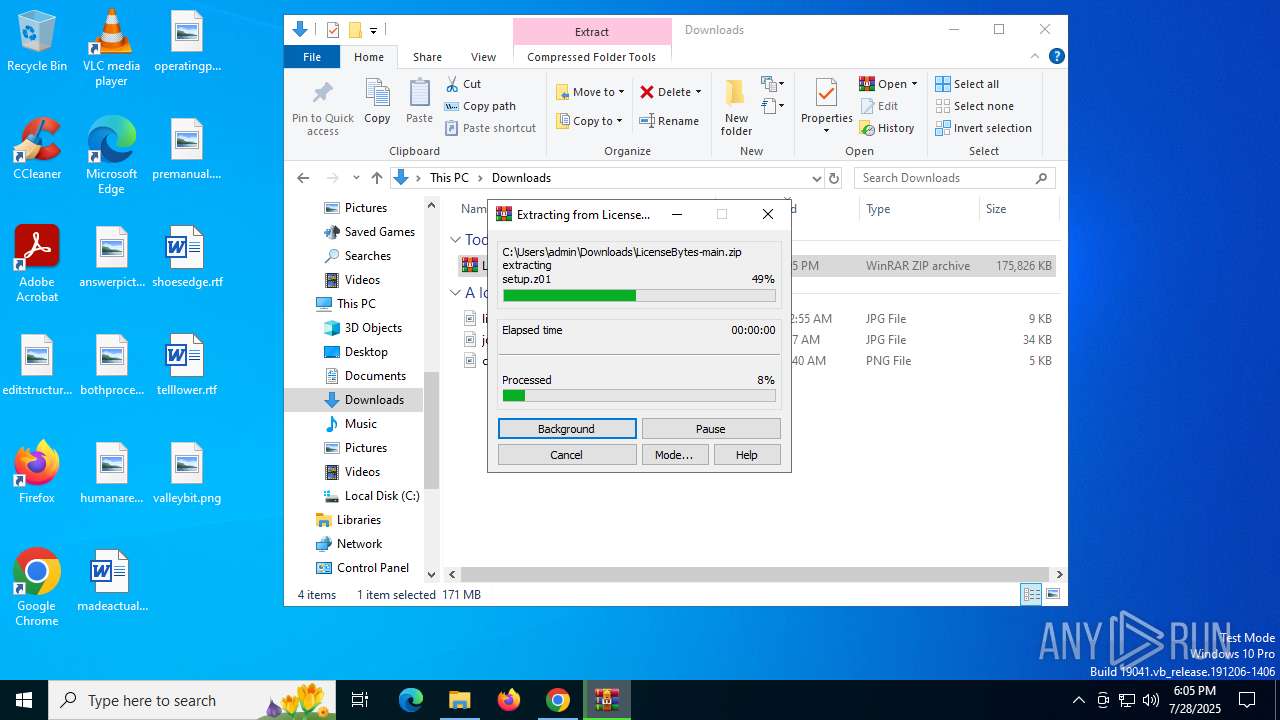
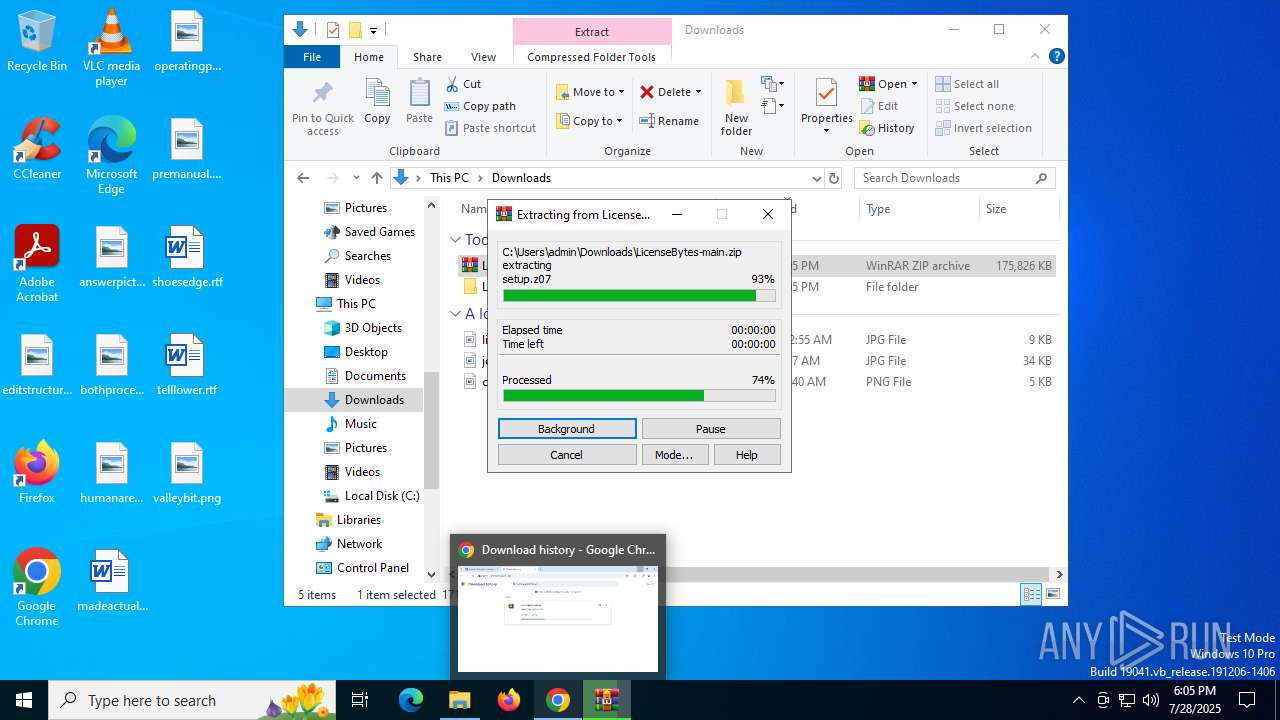
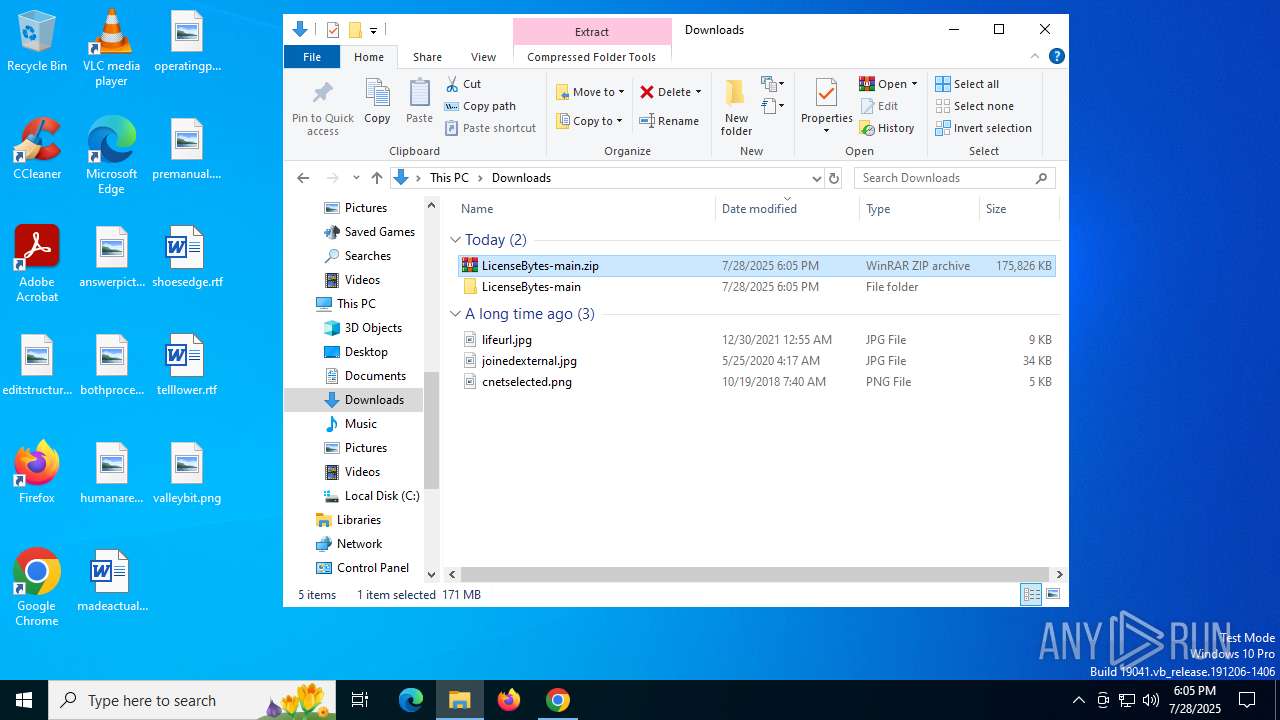
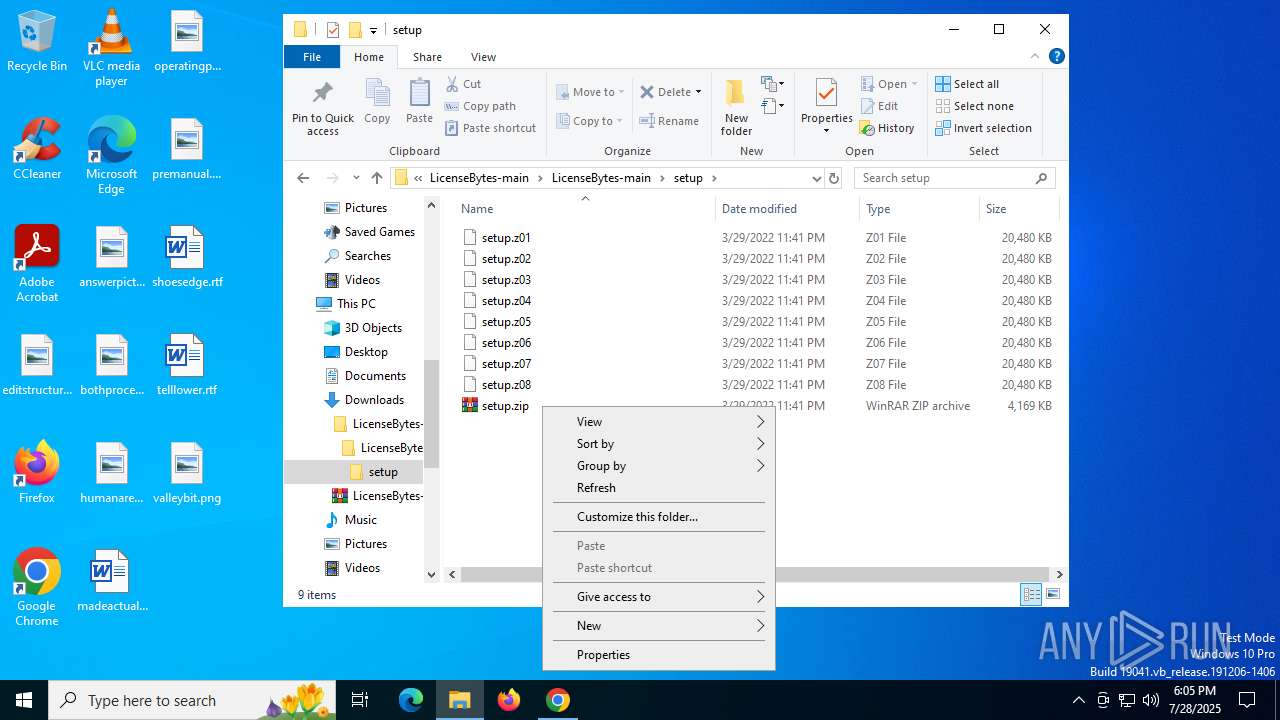
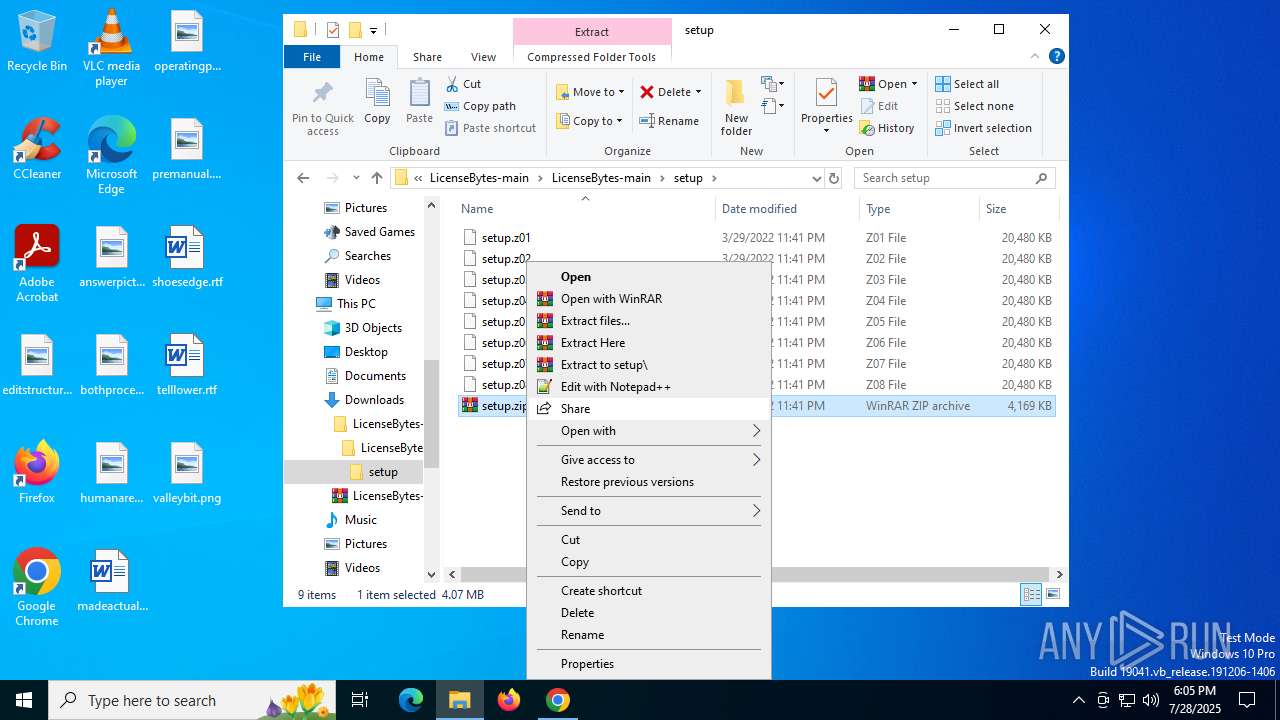
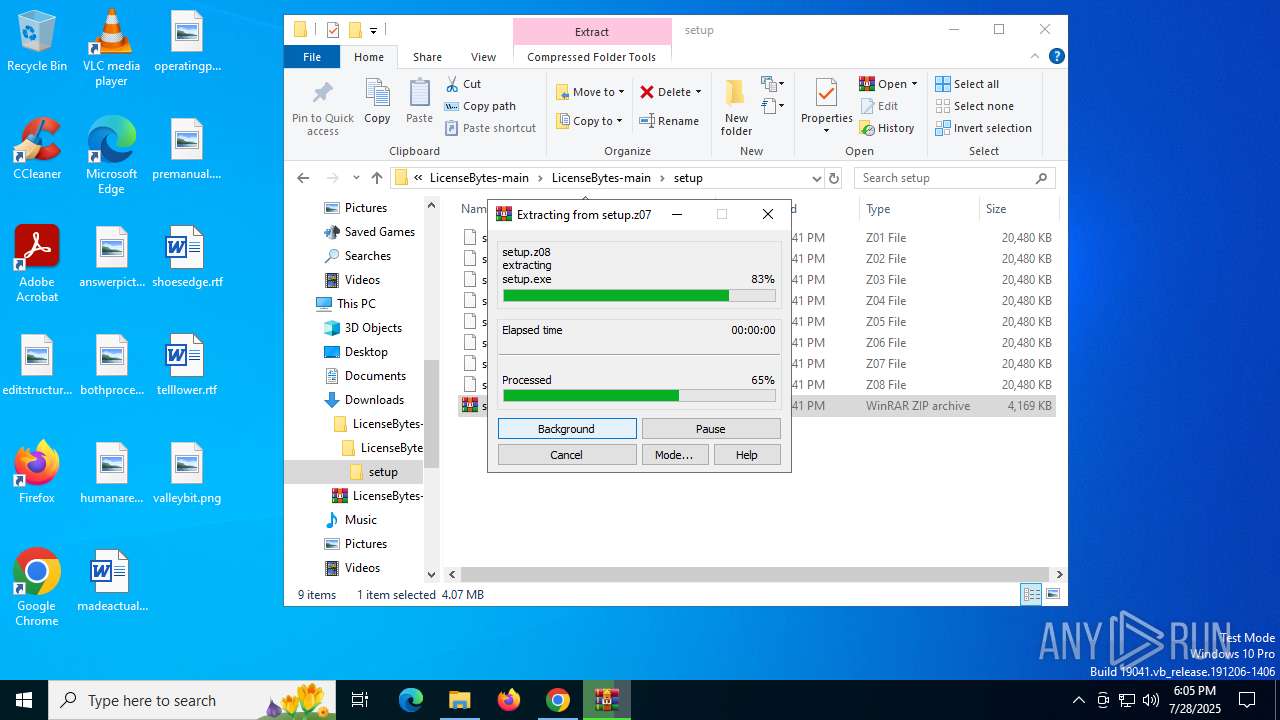
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1352)
- chrome.exe (PID: 5600)
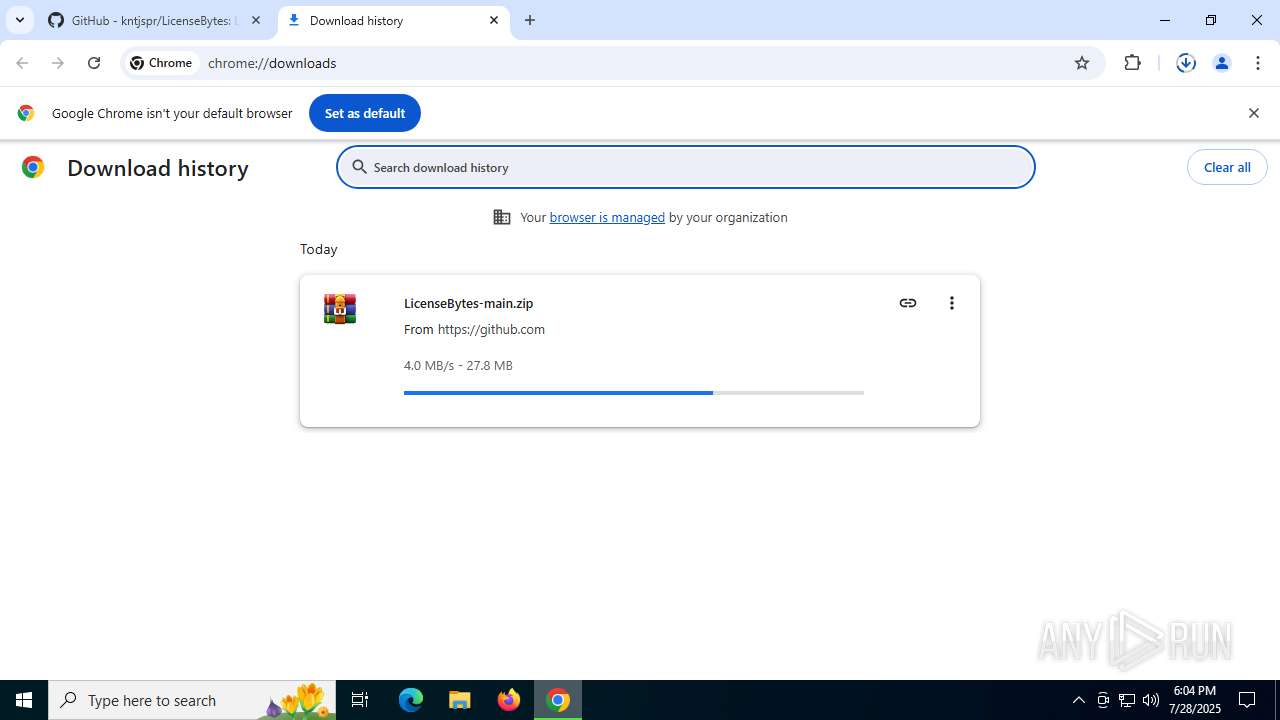
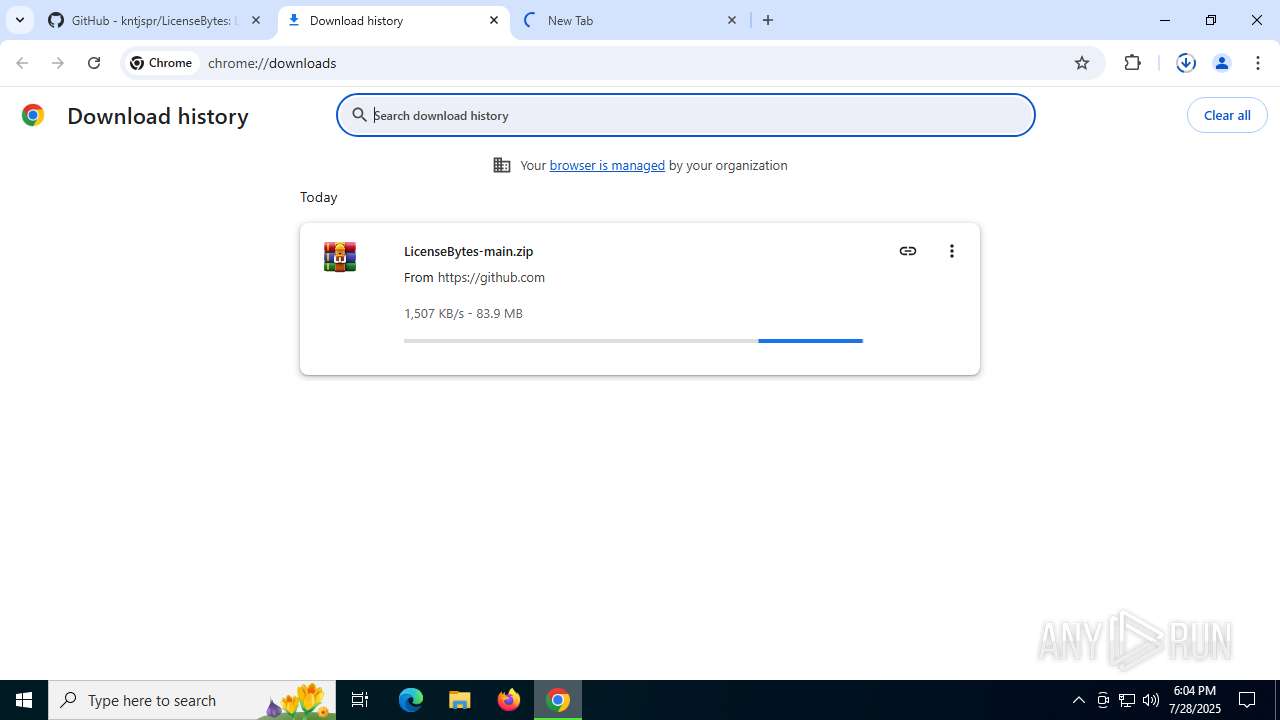
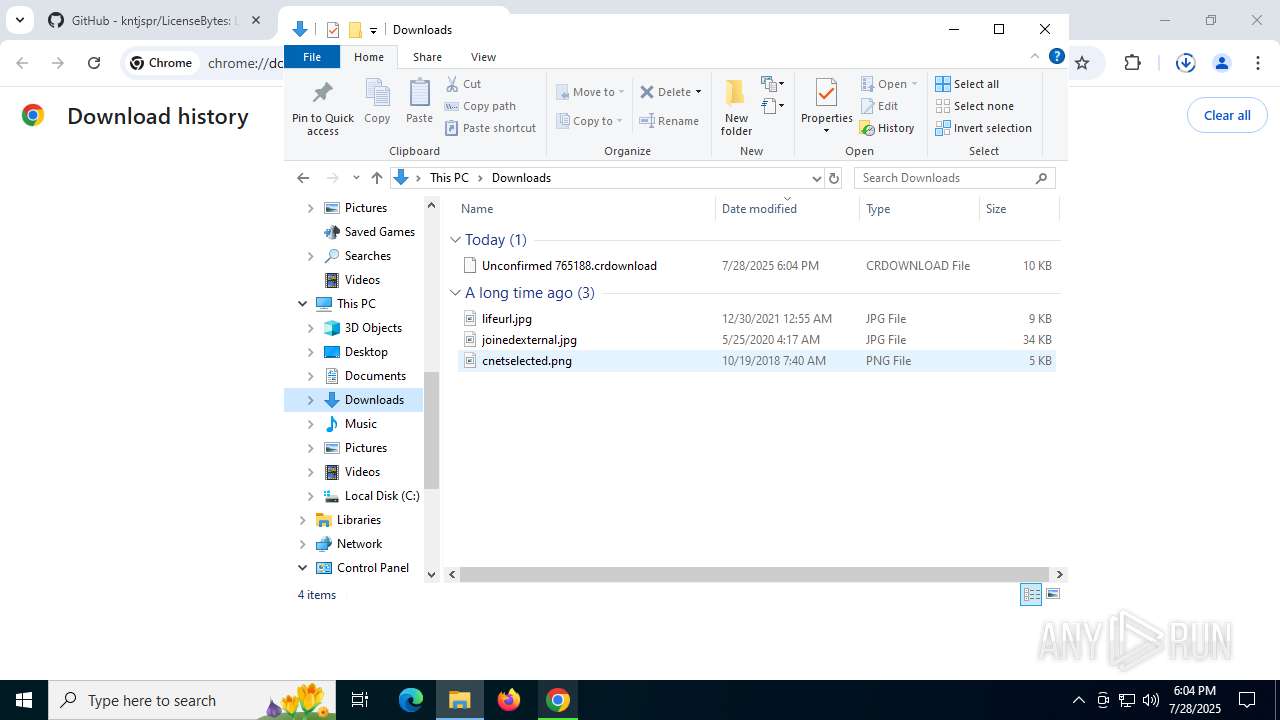
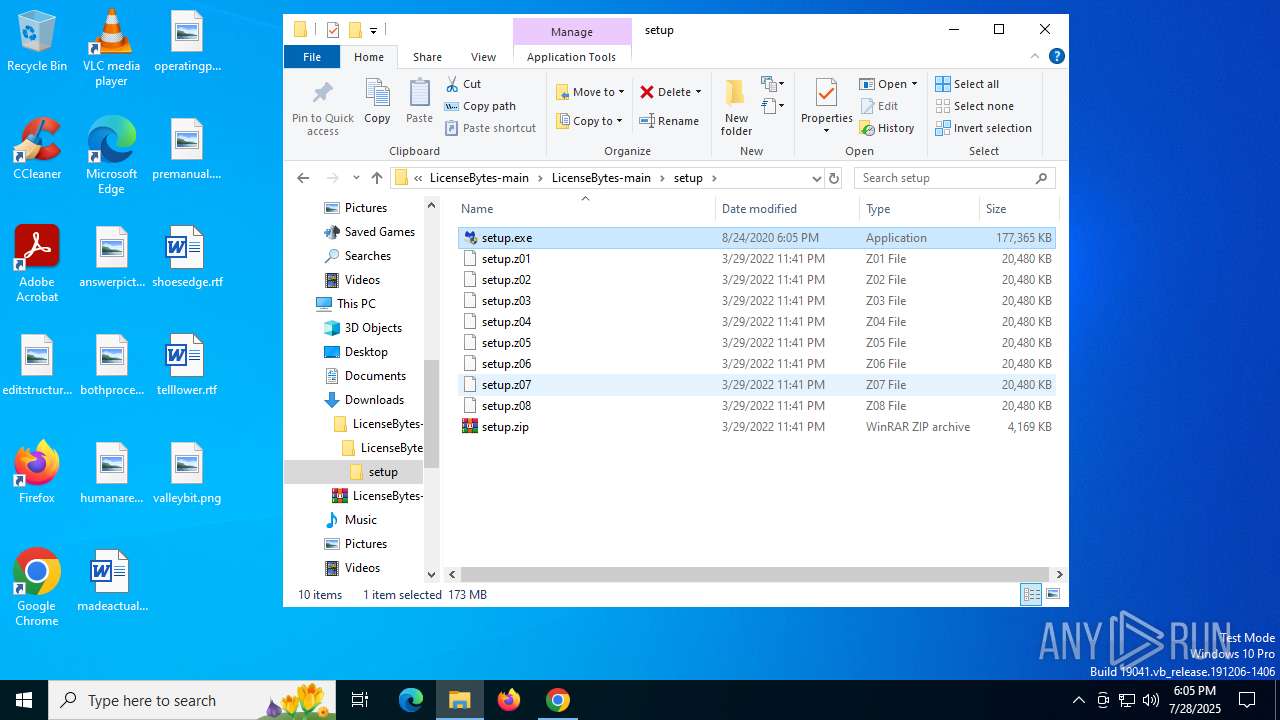
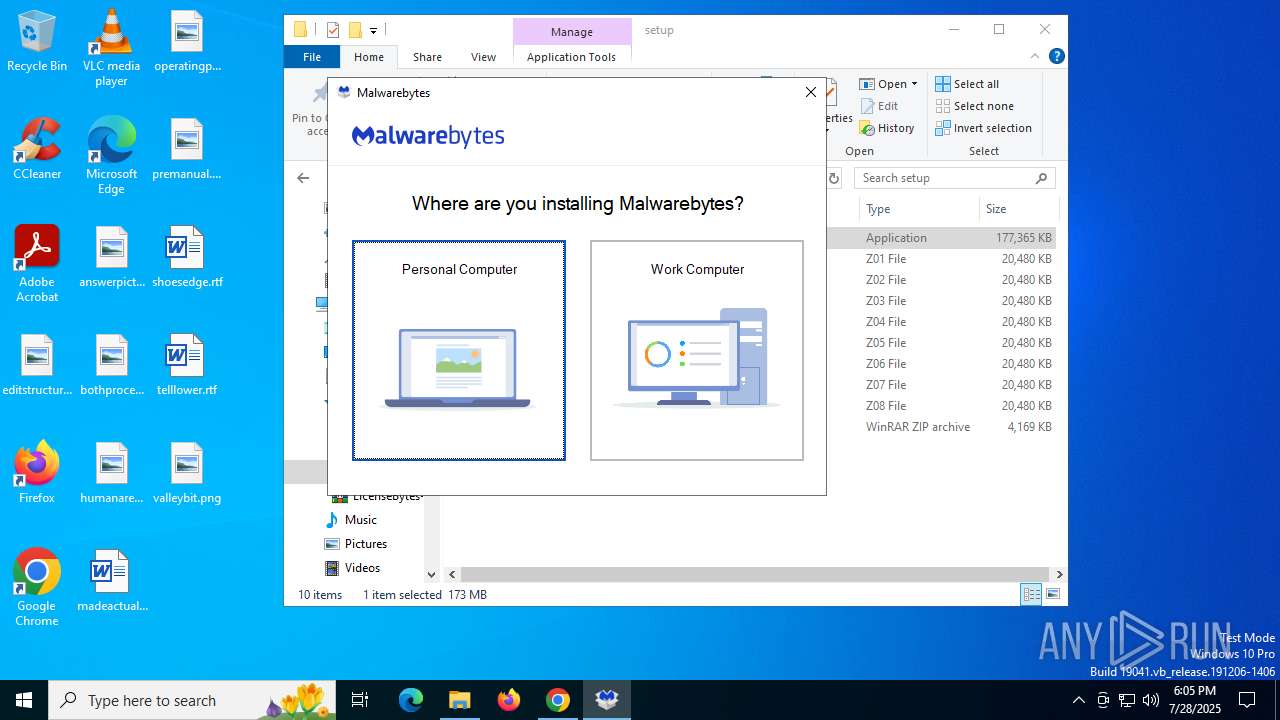
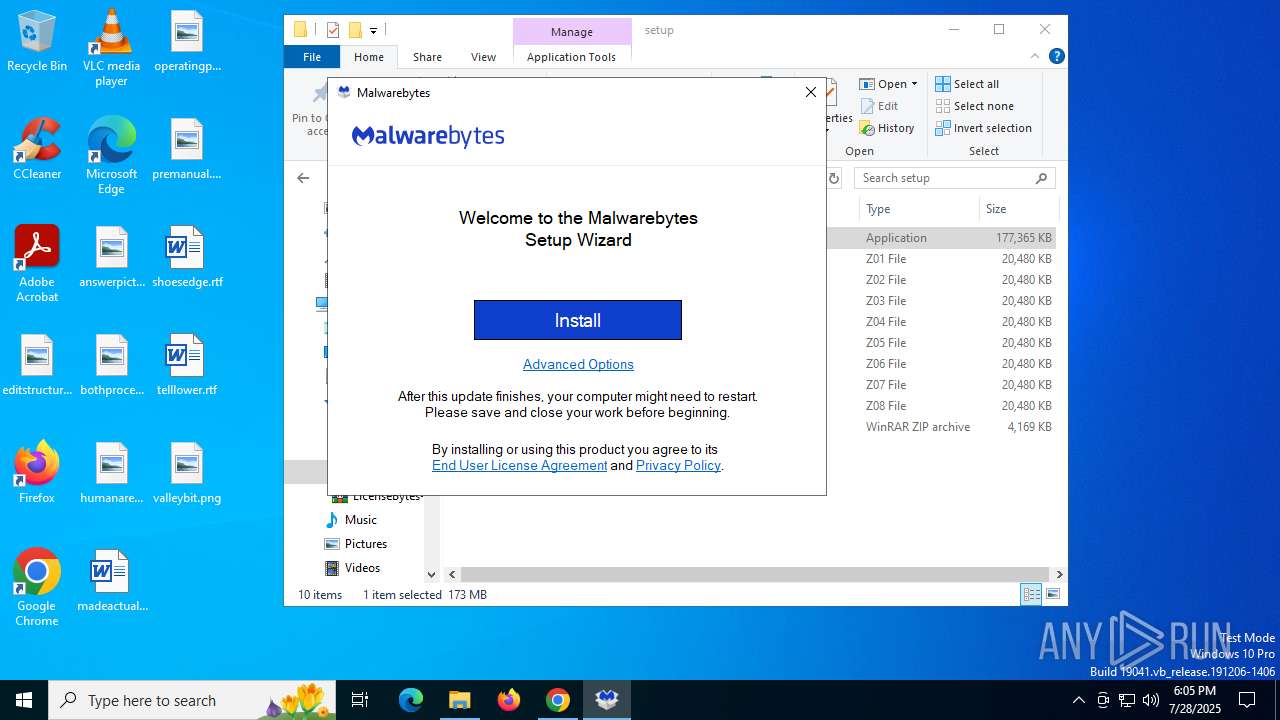
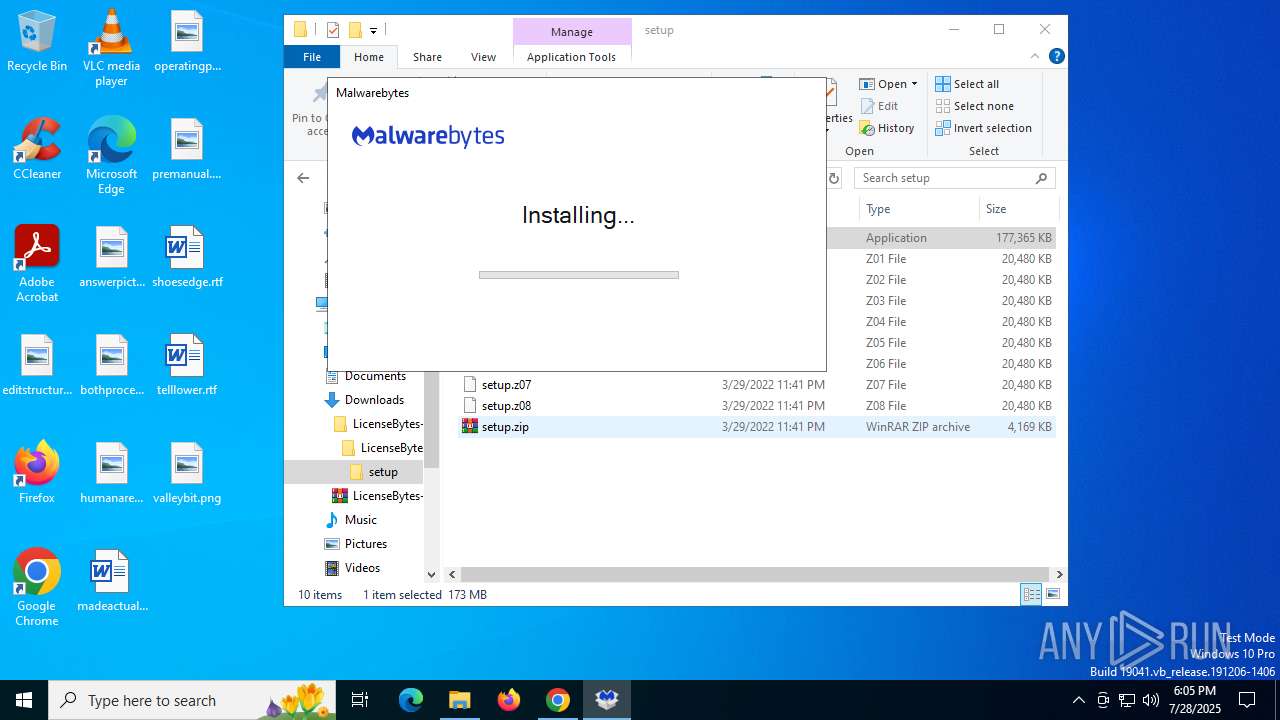
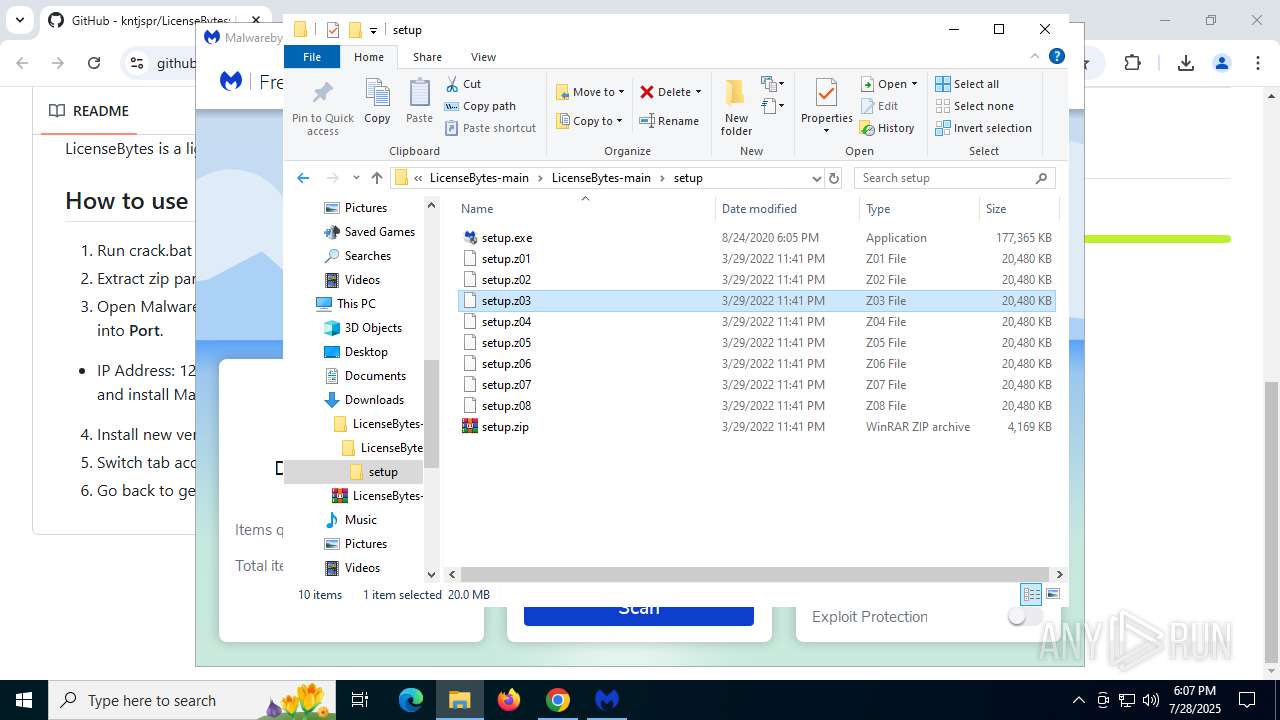
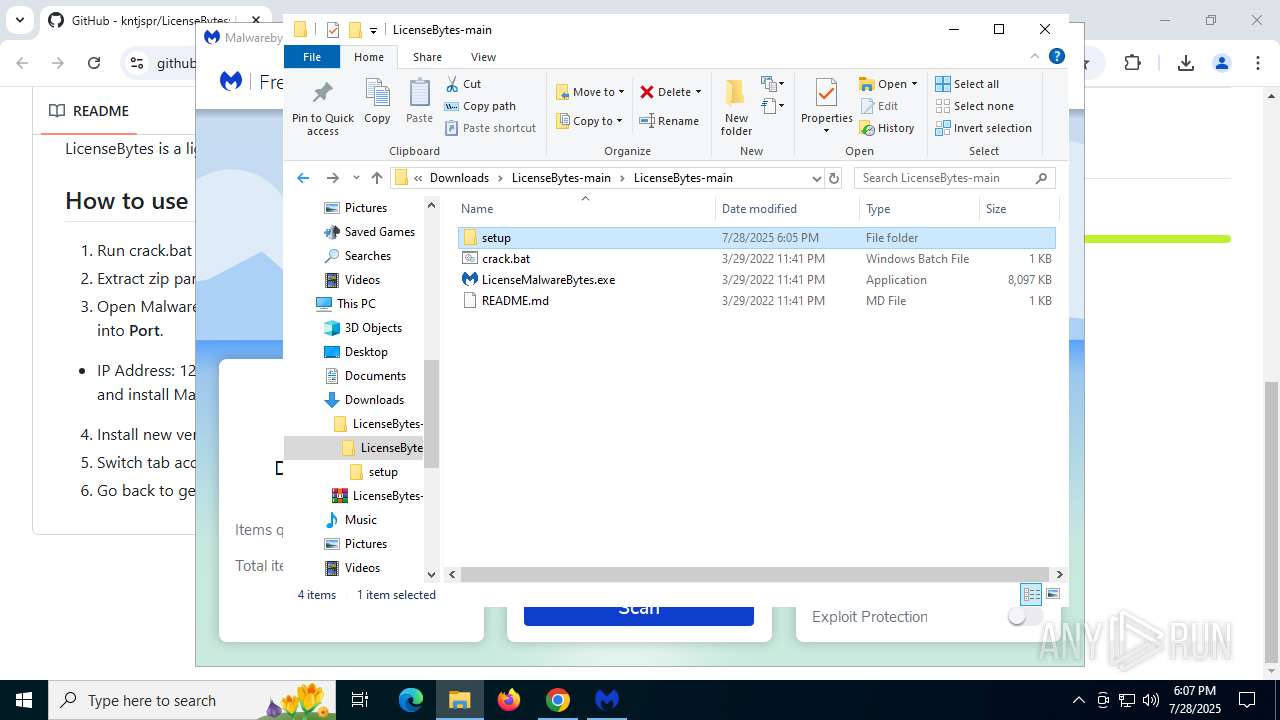
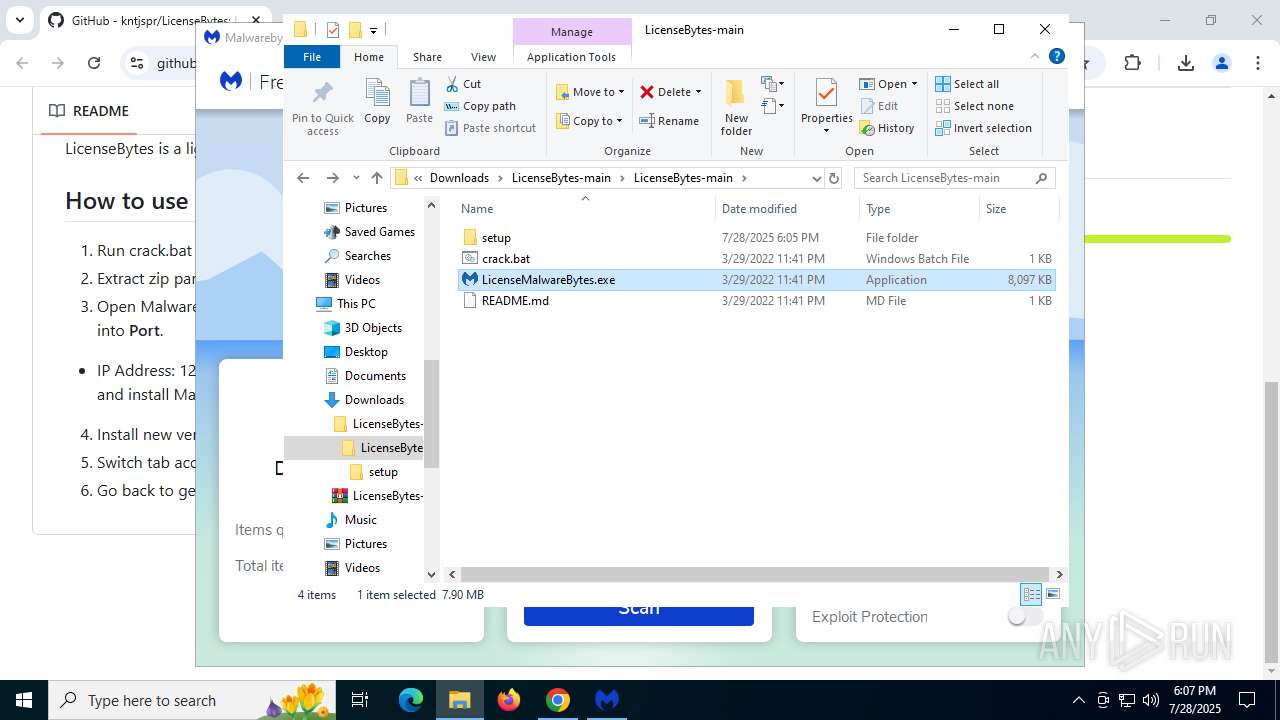
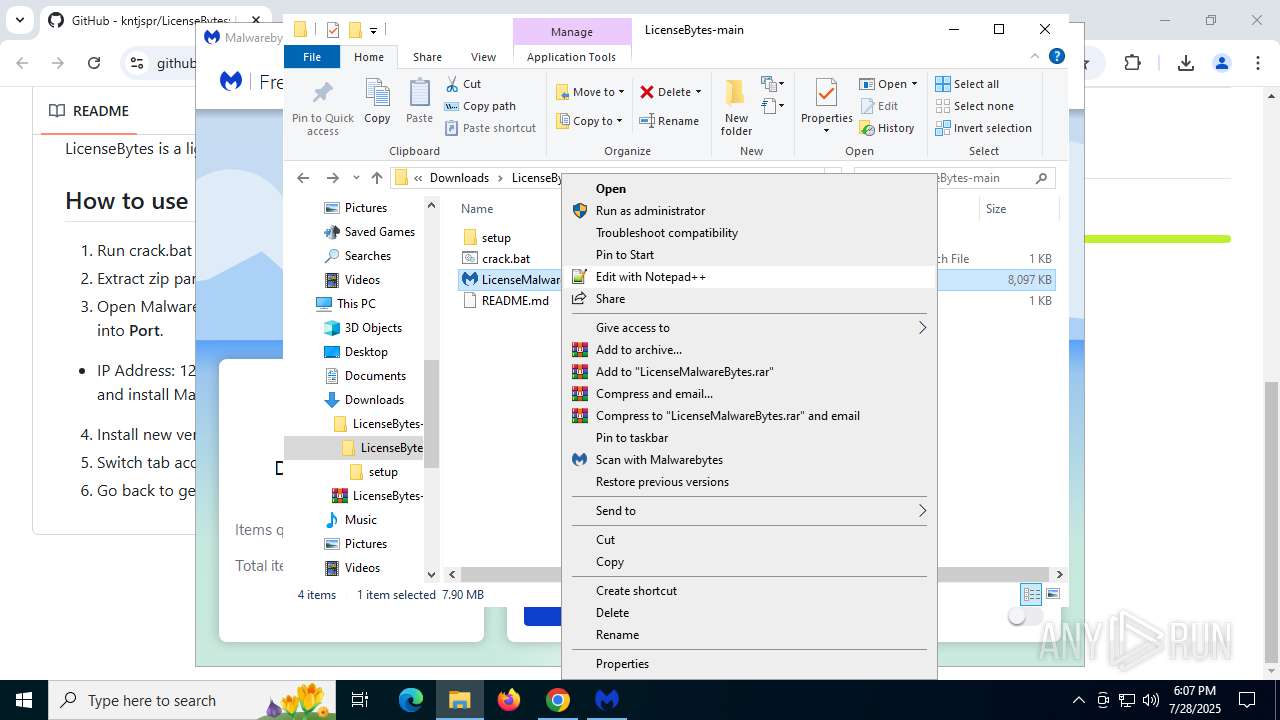
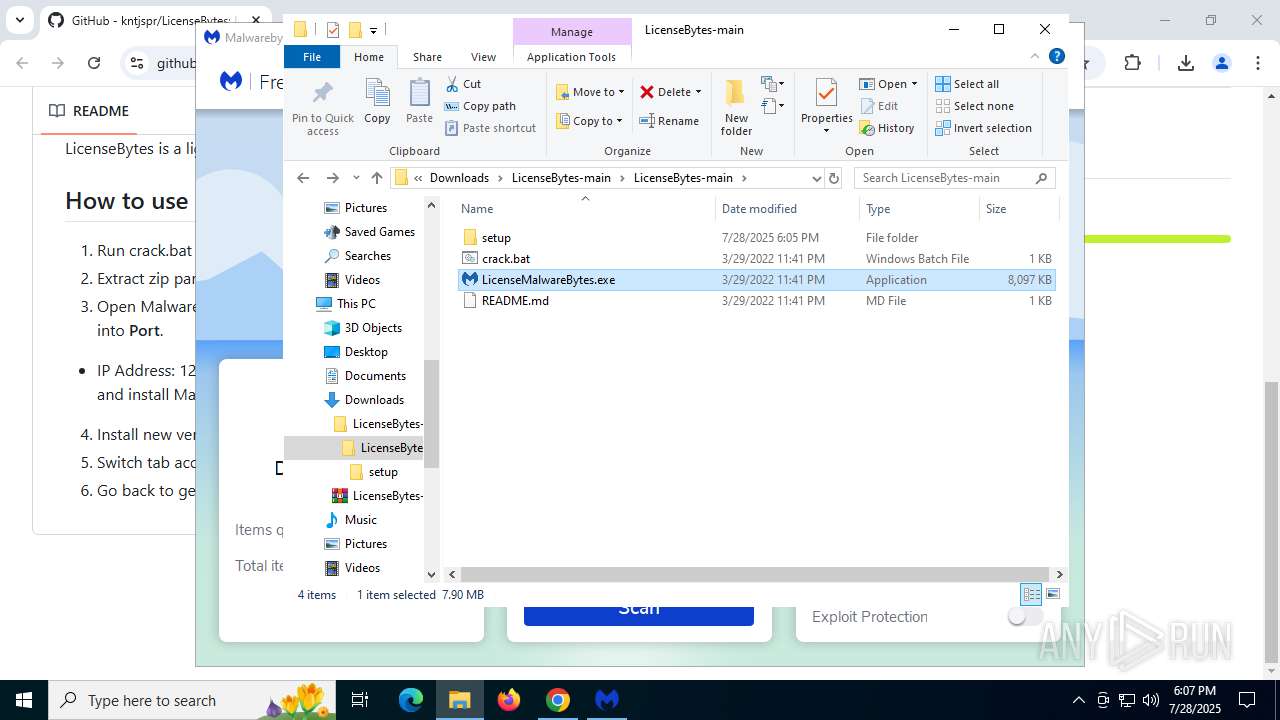
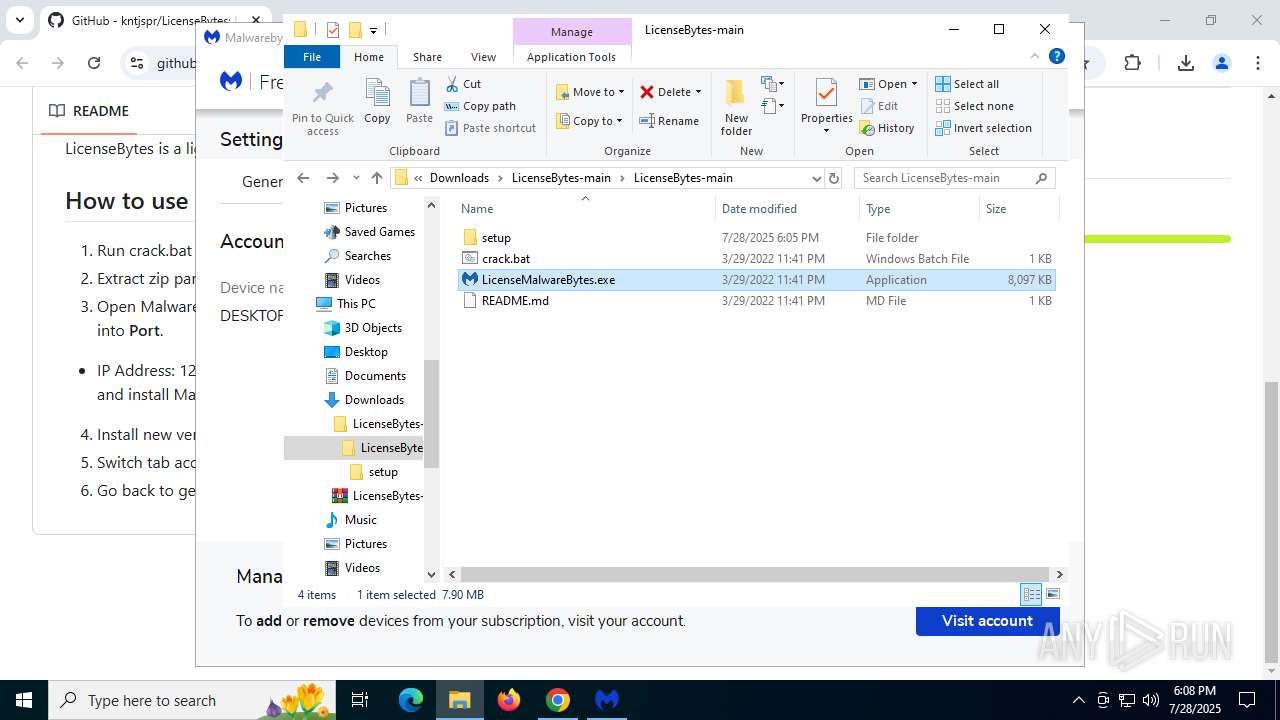
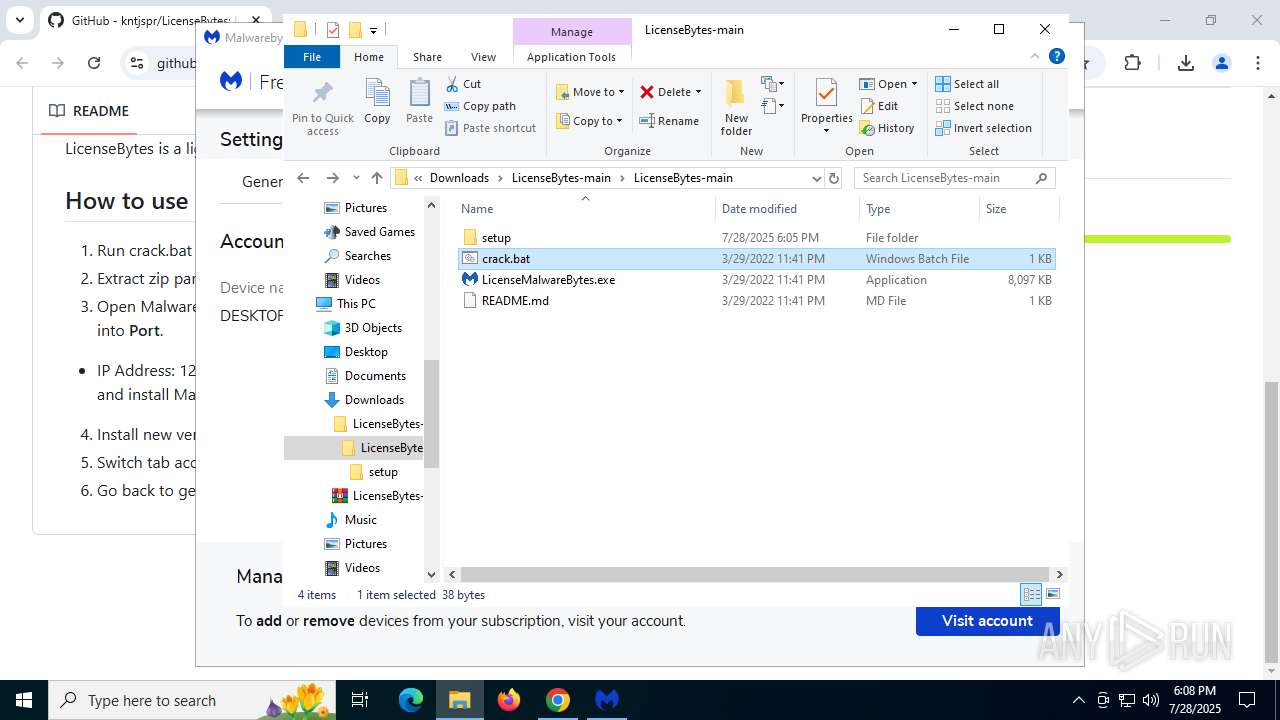
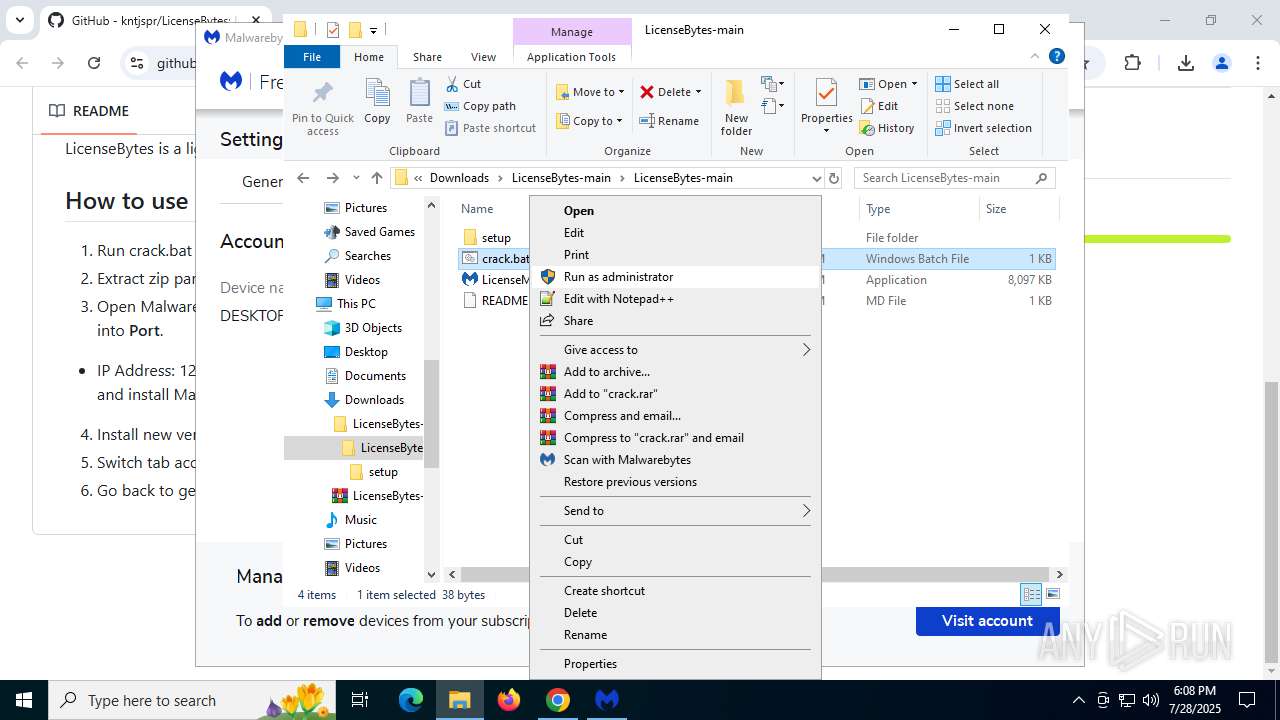
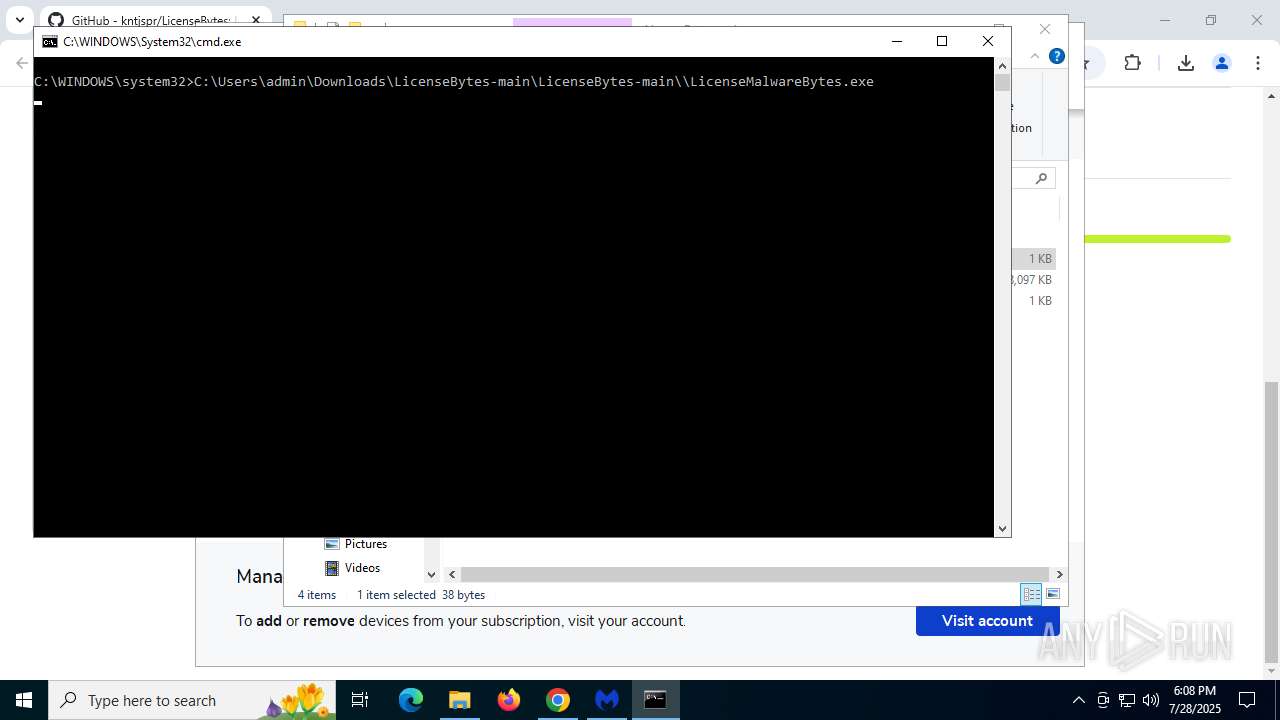
Manual execution by a user
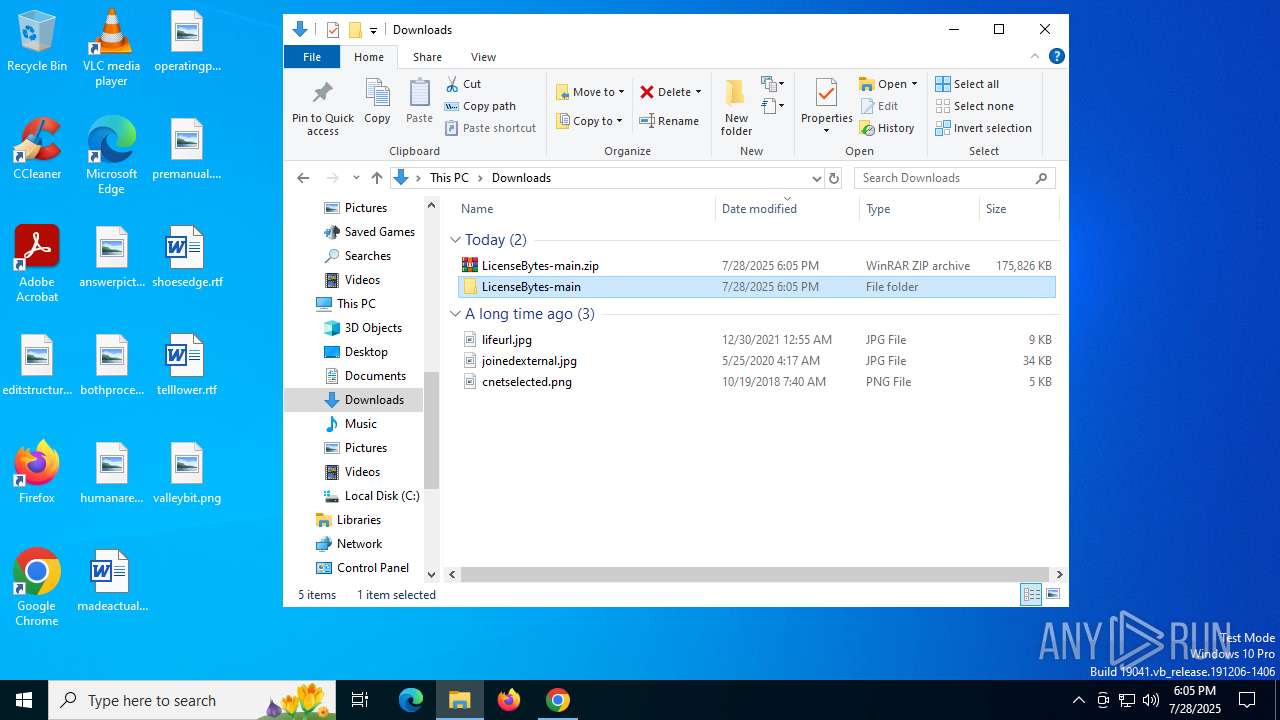
- WinRAR.exe (PID: 6472)
- setup.exe (PID: 3480)
- WinRAR.exe (PID: 1352)
- setup.exe (PID: 6400)
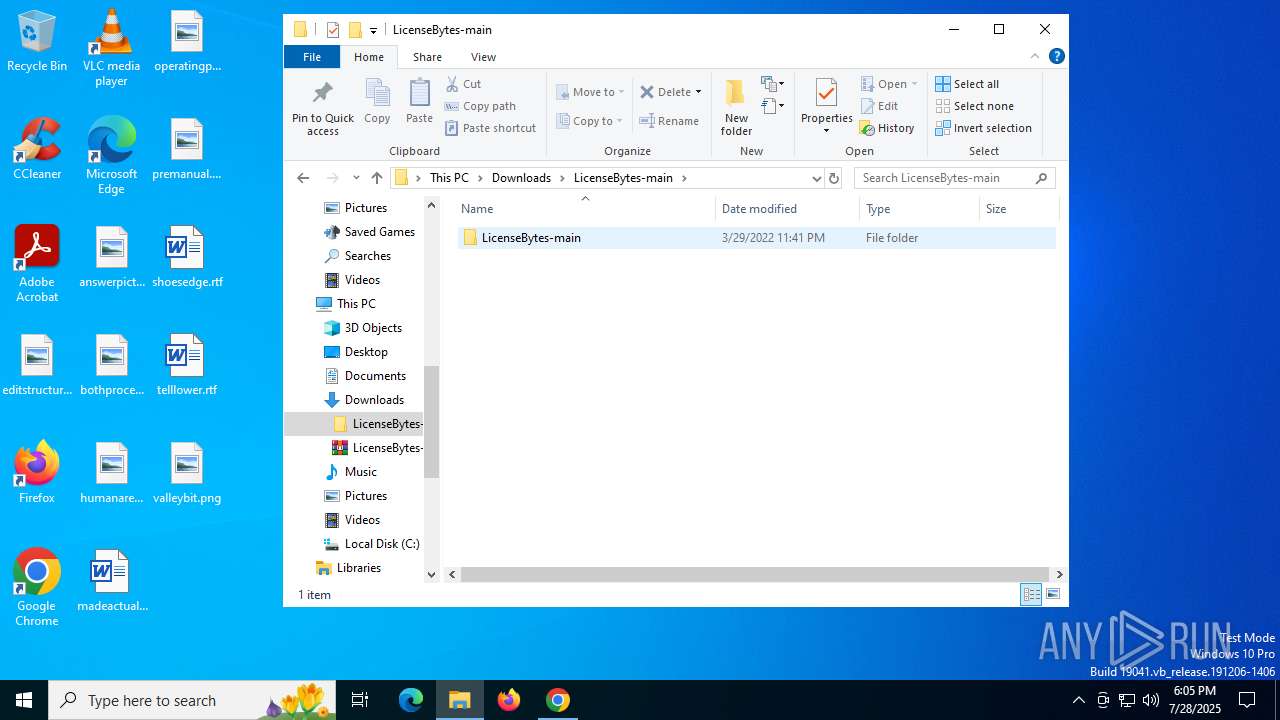
- LicenseMalwareBytes.exe (PID: 7776)
- cmd.exe (PID: 6980)
Create files in a temporary directory
- setup.exe (PID: 6400)
- mbam.exe (PID: 3460)
- LicenseMalwareBytes.exe (PID: 7776)
- LicenseMalwareBytes.exe (PID: 3876)
Checks supported languages
- setup.exe (PID: 6400)
- MBAMInstallerService.exe (PID: 7888)
- MBAMService.exe (PID: 984)
- MBAMService.exe (PID: 2192)
- mbamtray.exe (PID: 7404)
- mbam.exe (PID: 3460)
- LicenseMalwareBytes.exe (PID: 7776)
- LicenseMalwareBytes.exe (PID: 7748)
- LicenseMalwareBytes.exe (PID: 3876)
- LicenseMalwareBytes.exe (PID: 620)
The sample compiled with english language support
- setup.exe (PID: 6400)
- MBAMInstallerService.exe (PID: 7888)
- MBAMService.exe (PID: 984)
- MBAMService.exe (PID: 2192)
- LicenseMalwareBytes.exe (PID: 7776)
- chrome.exe (PID: 5600)
- LicenseMalwareBytes.exe (PID: 3876)
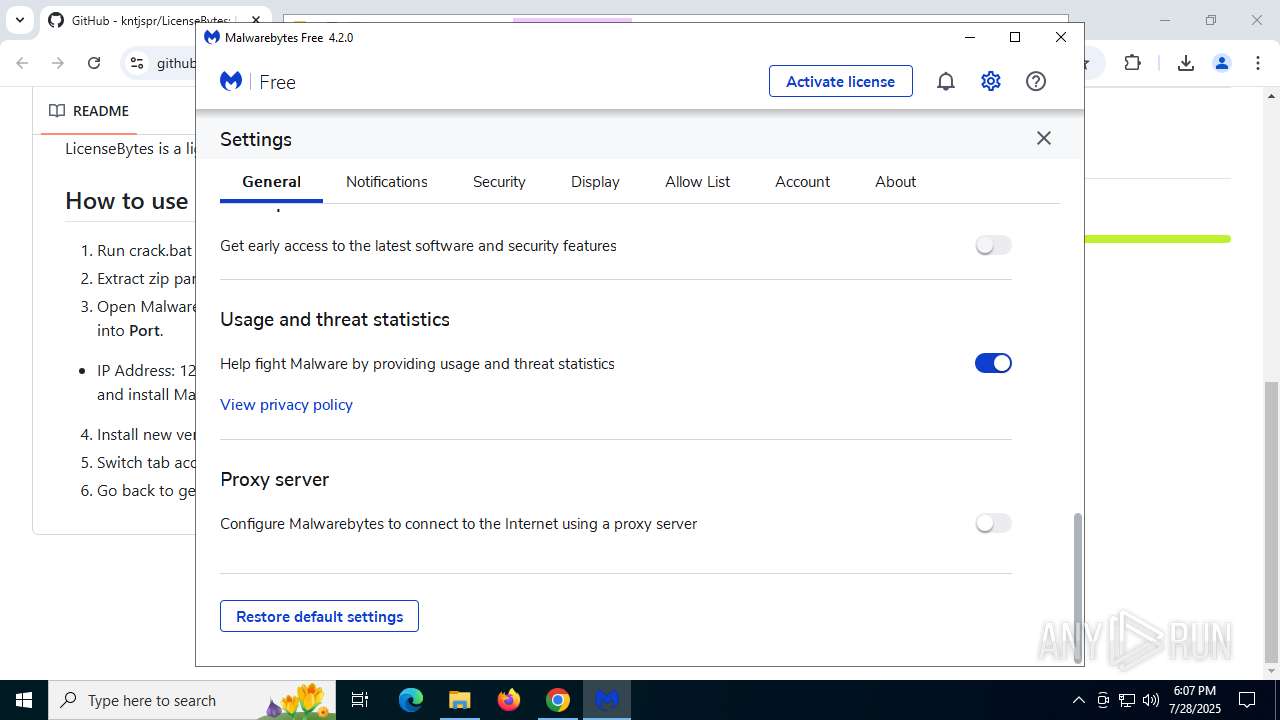
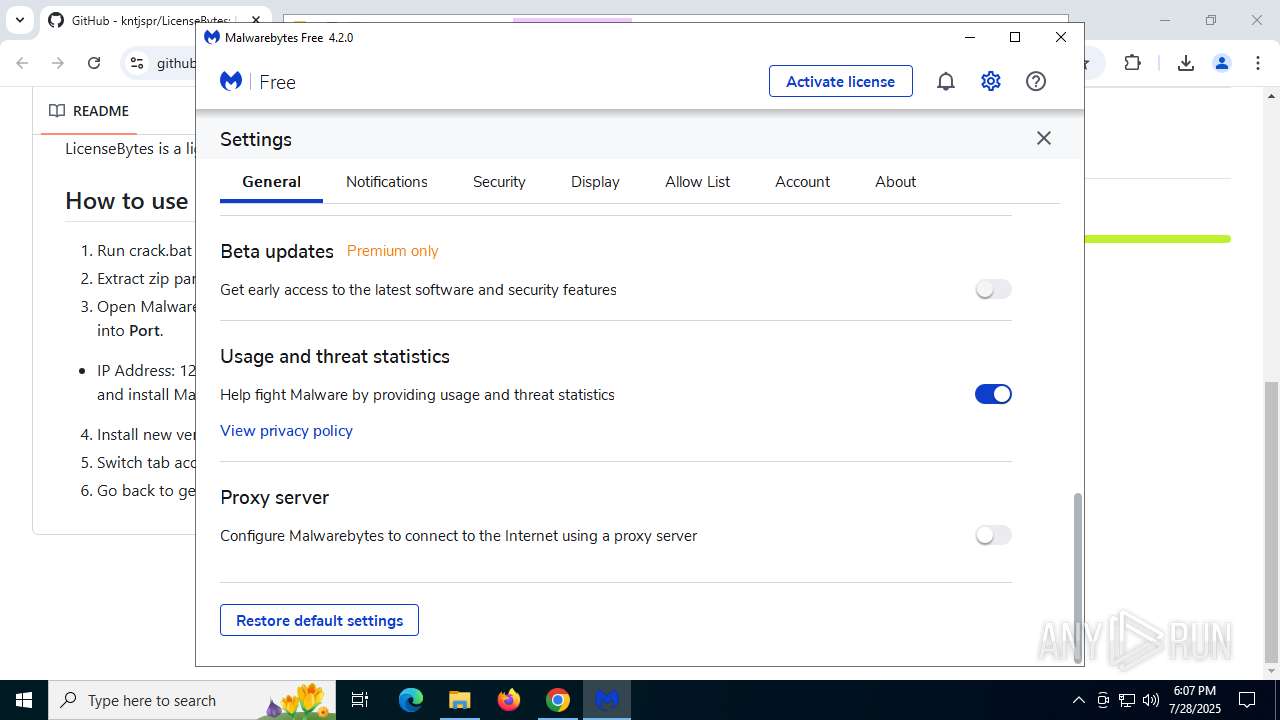
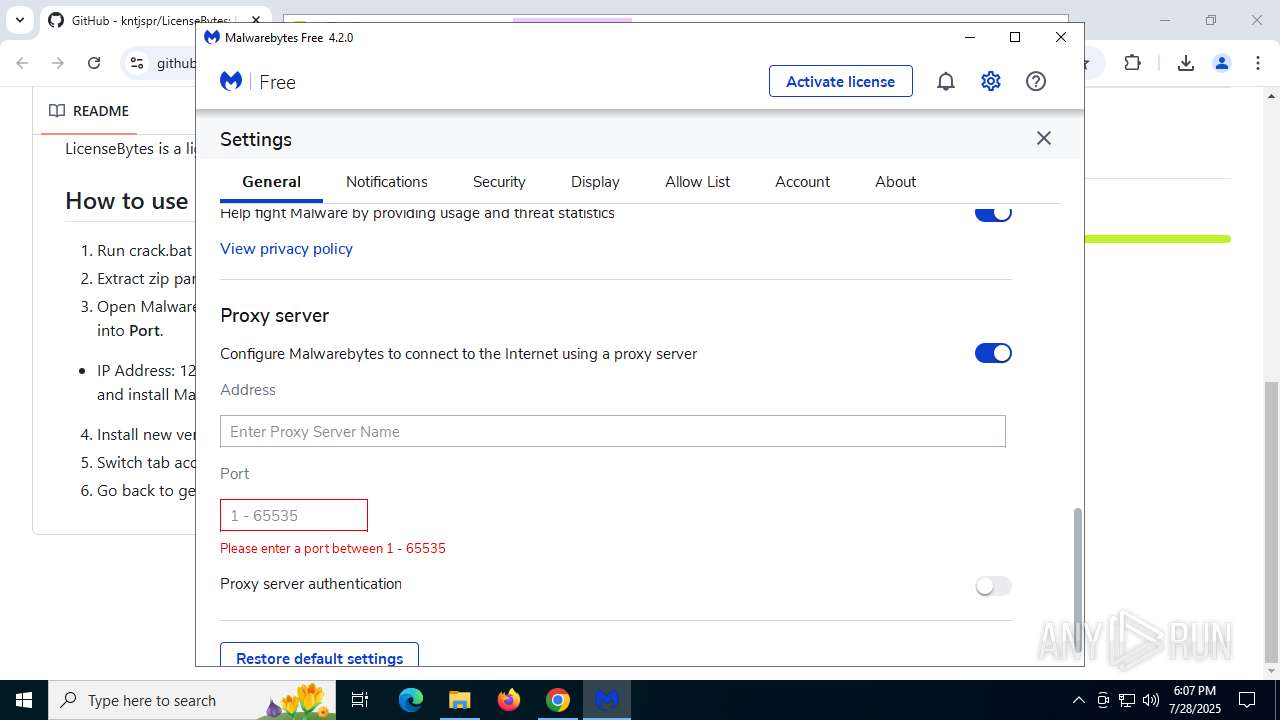
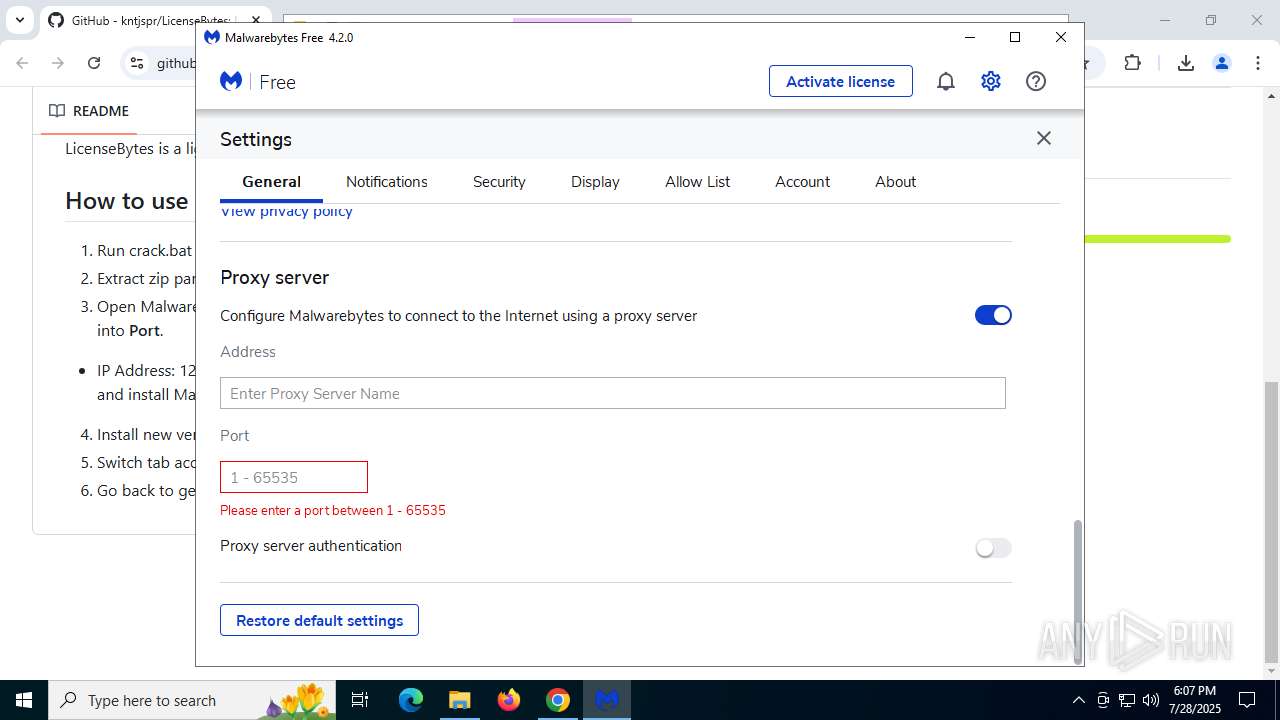
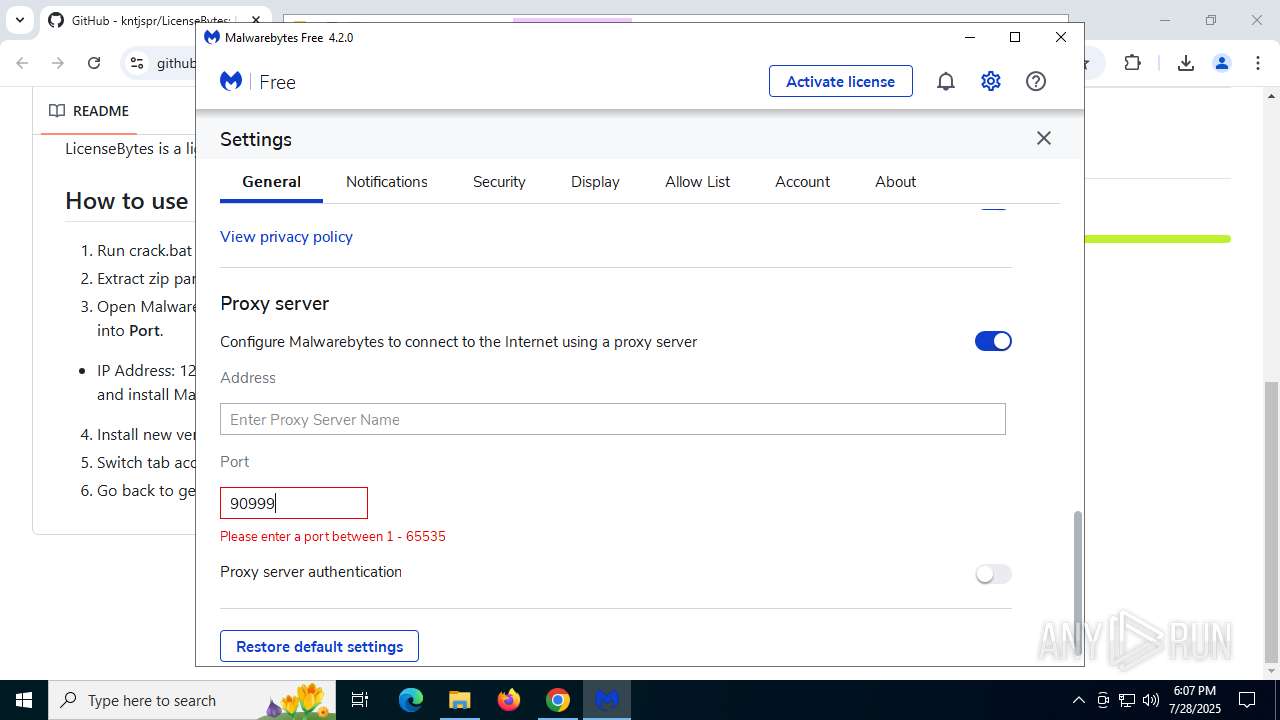
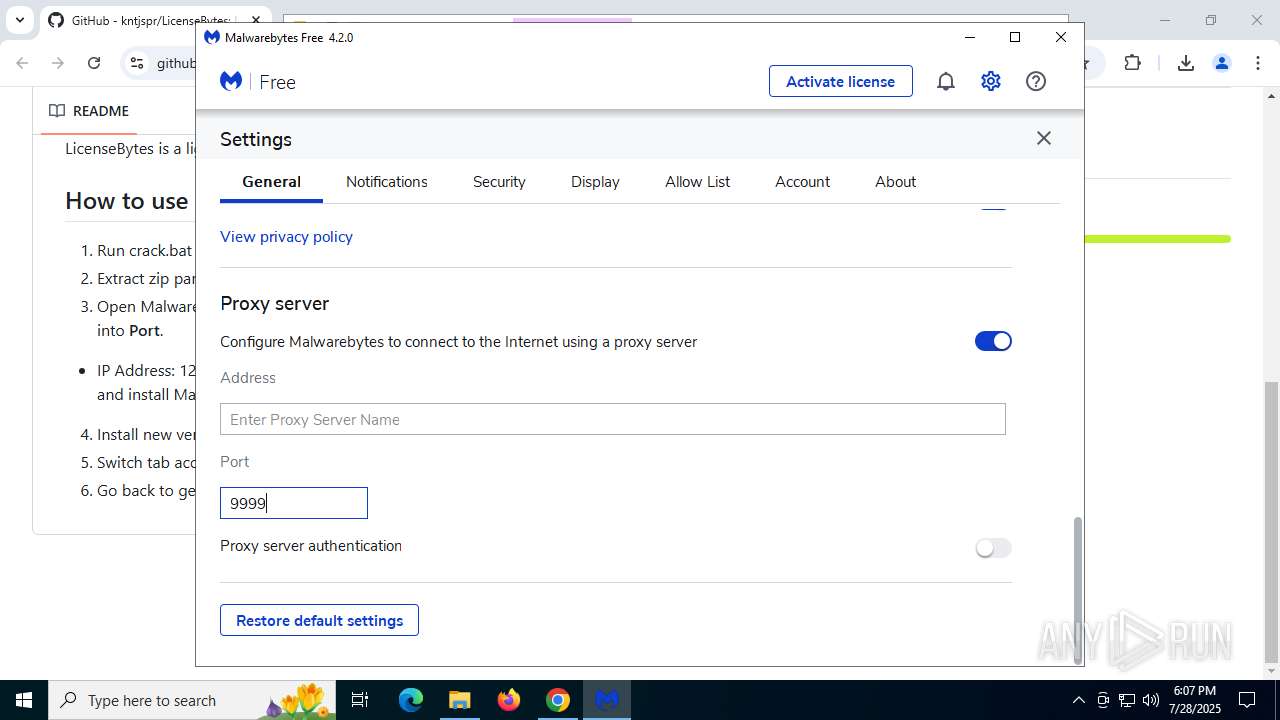
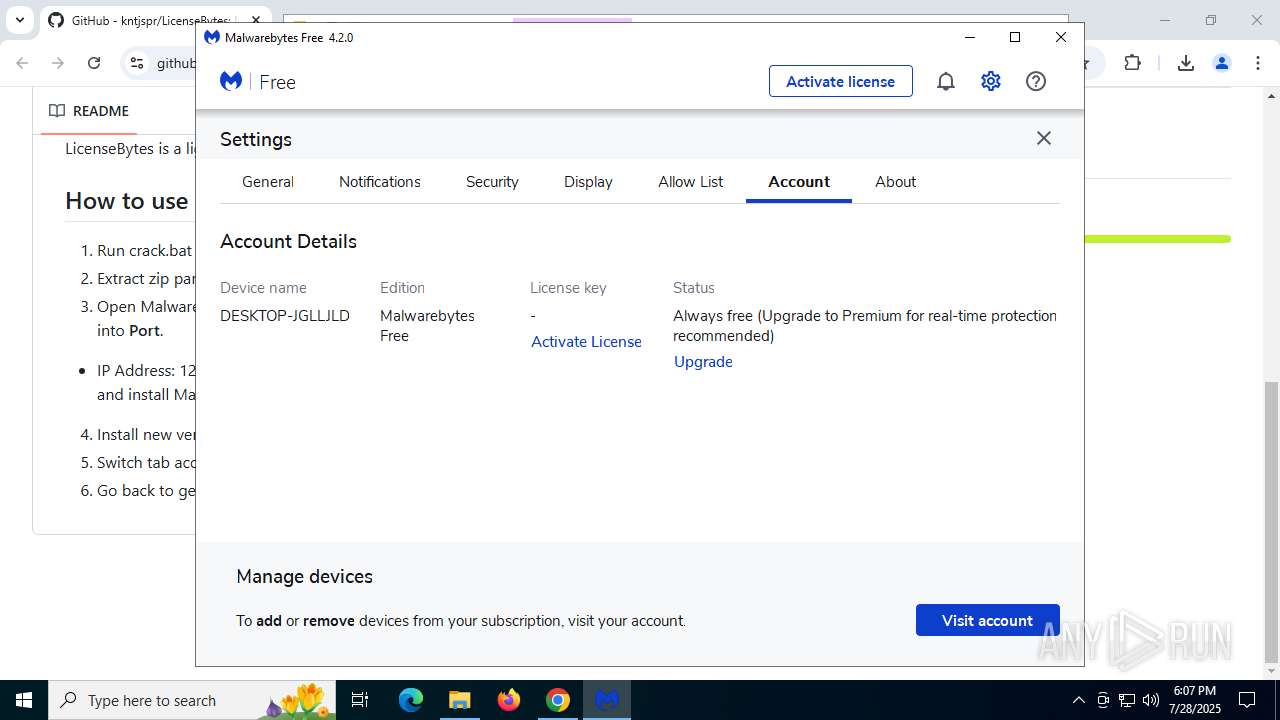
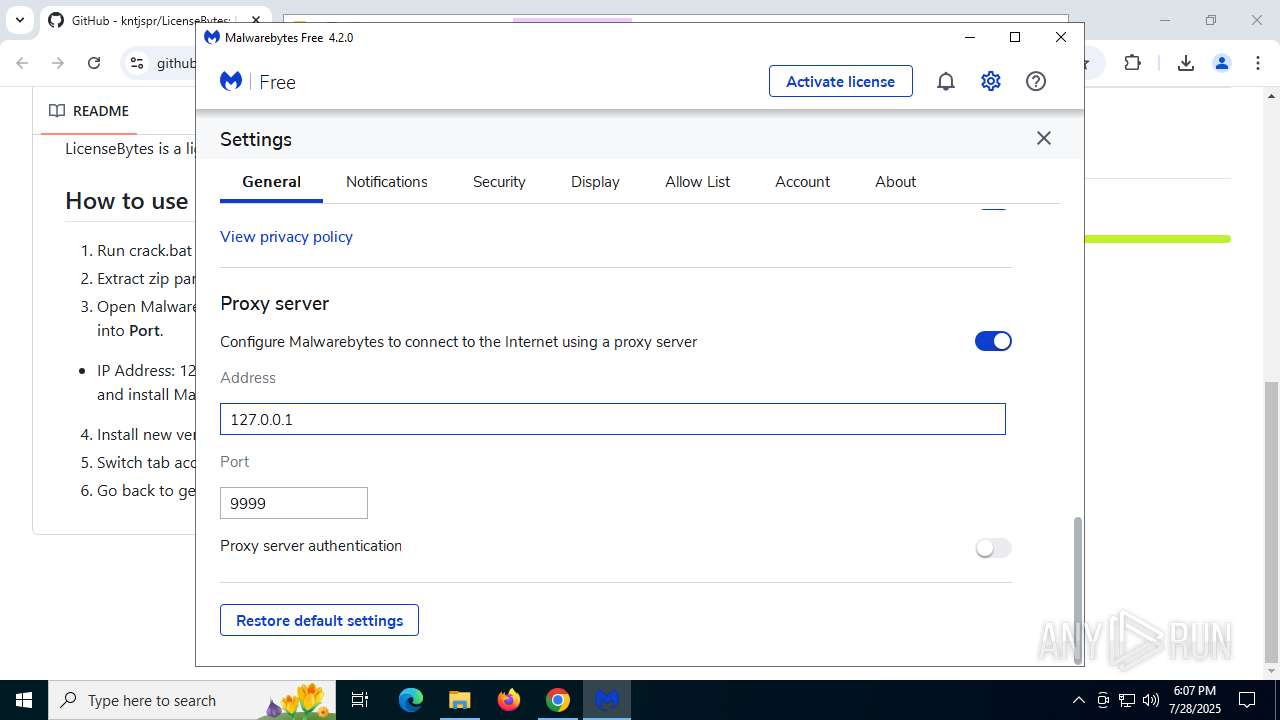
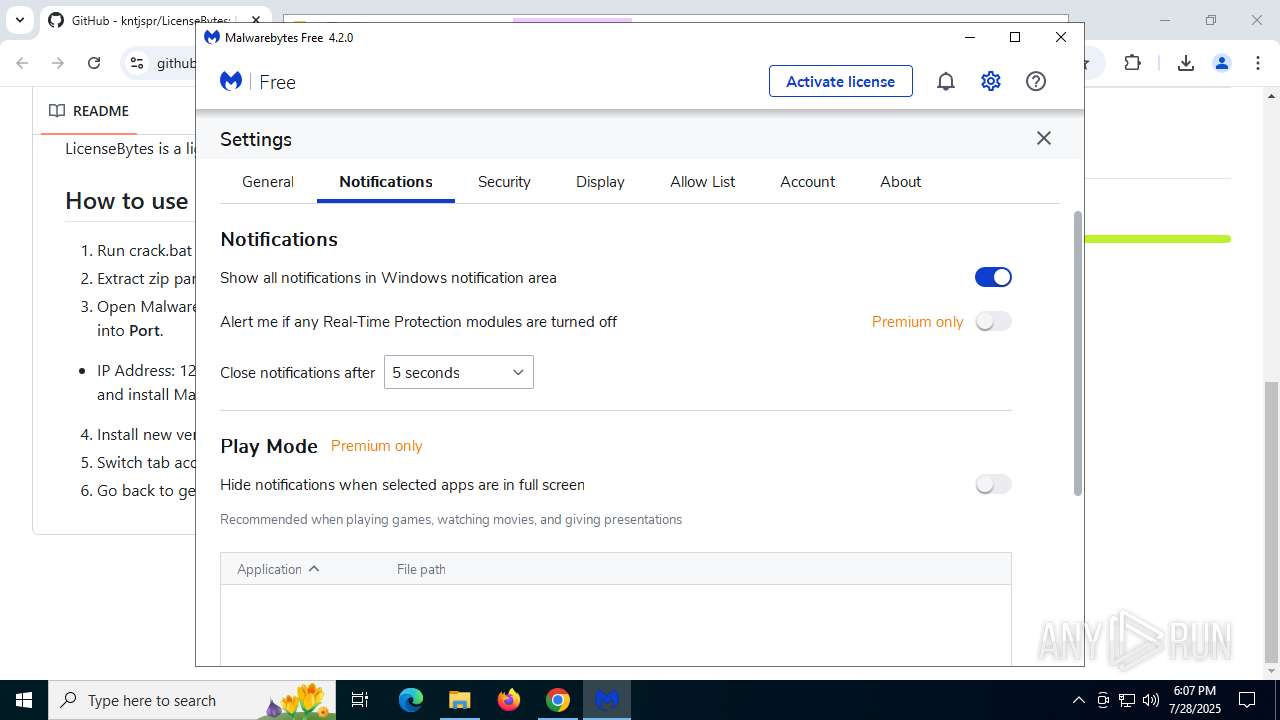
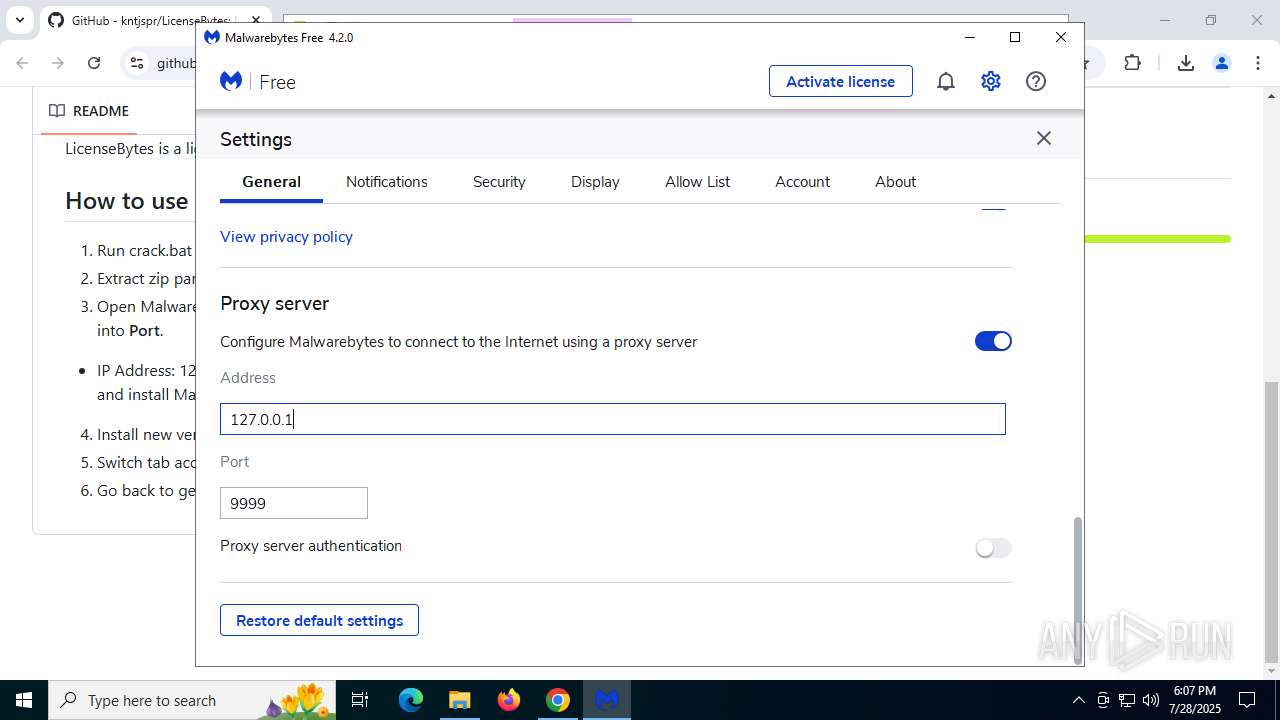
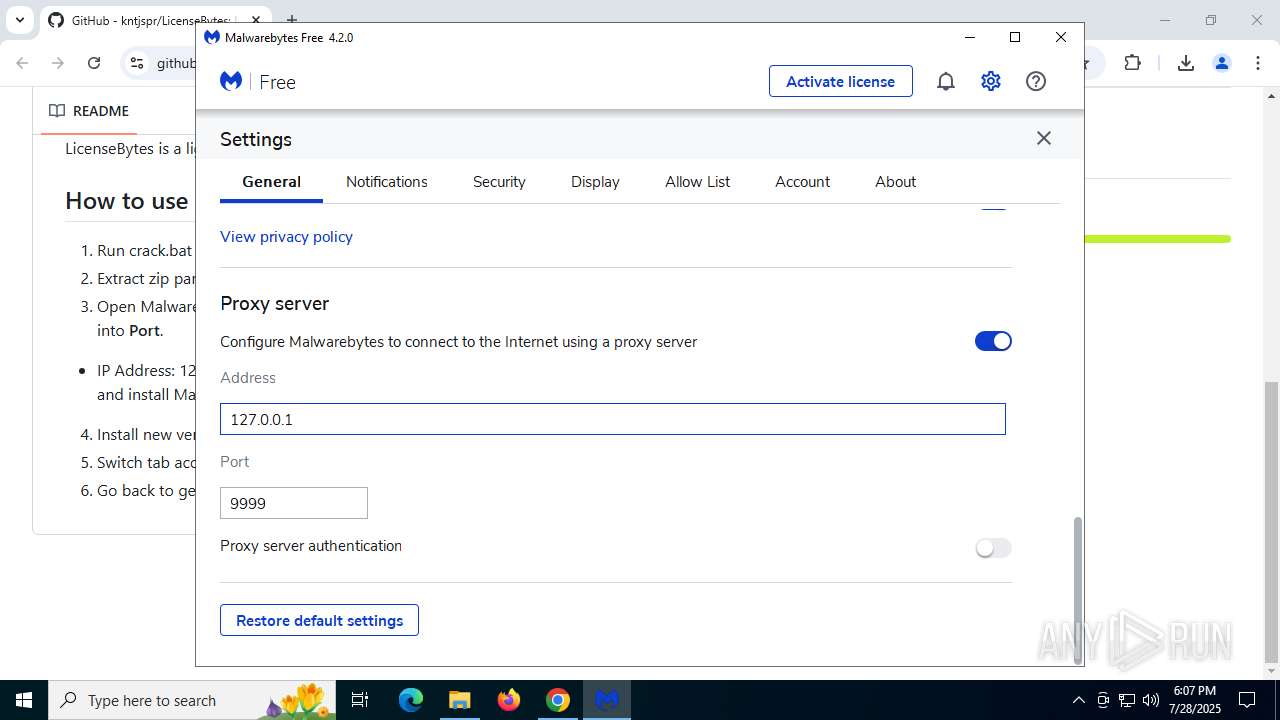
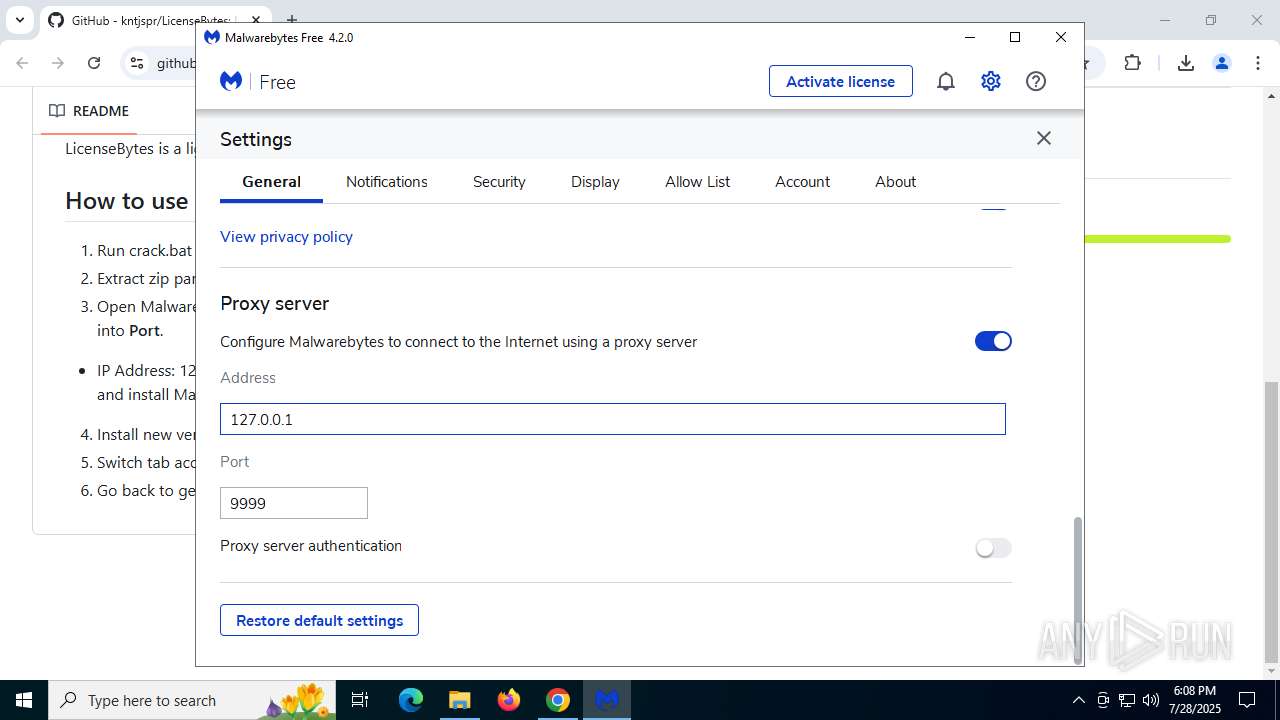
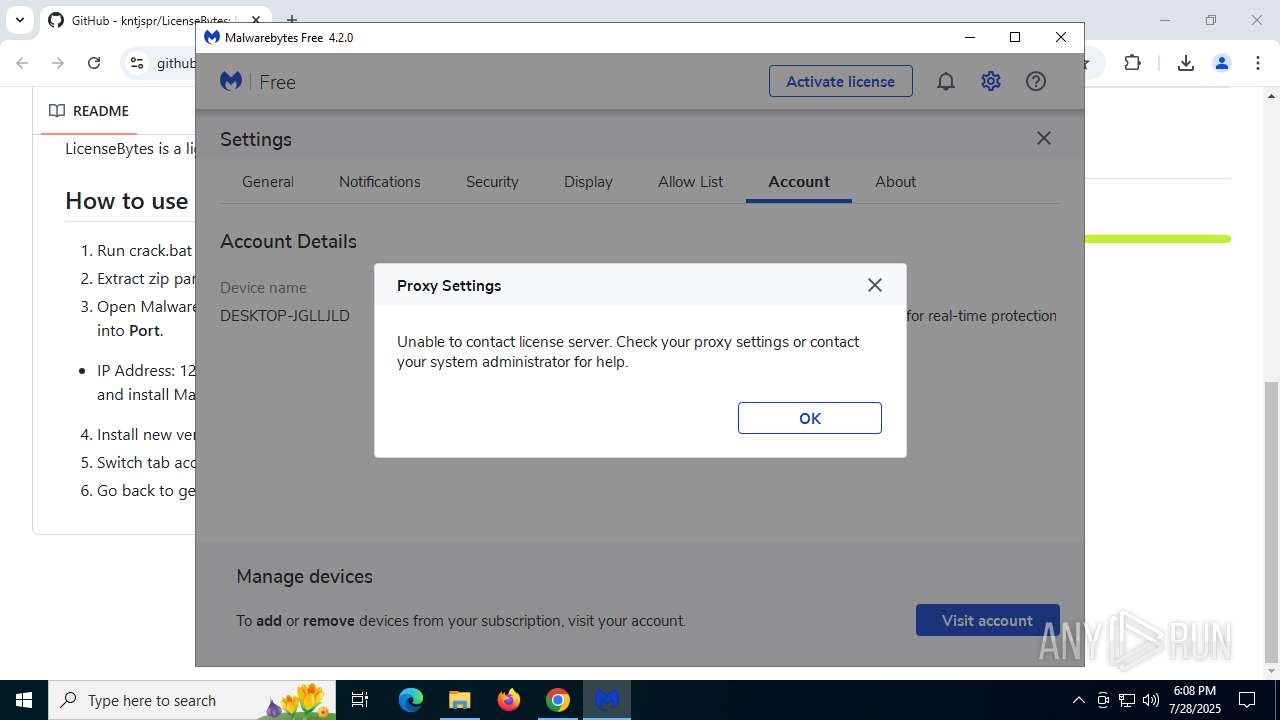
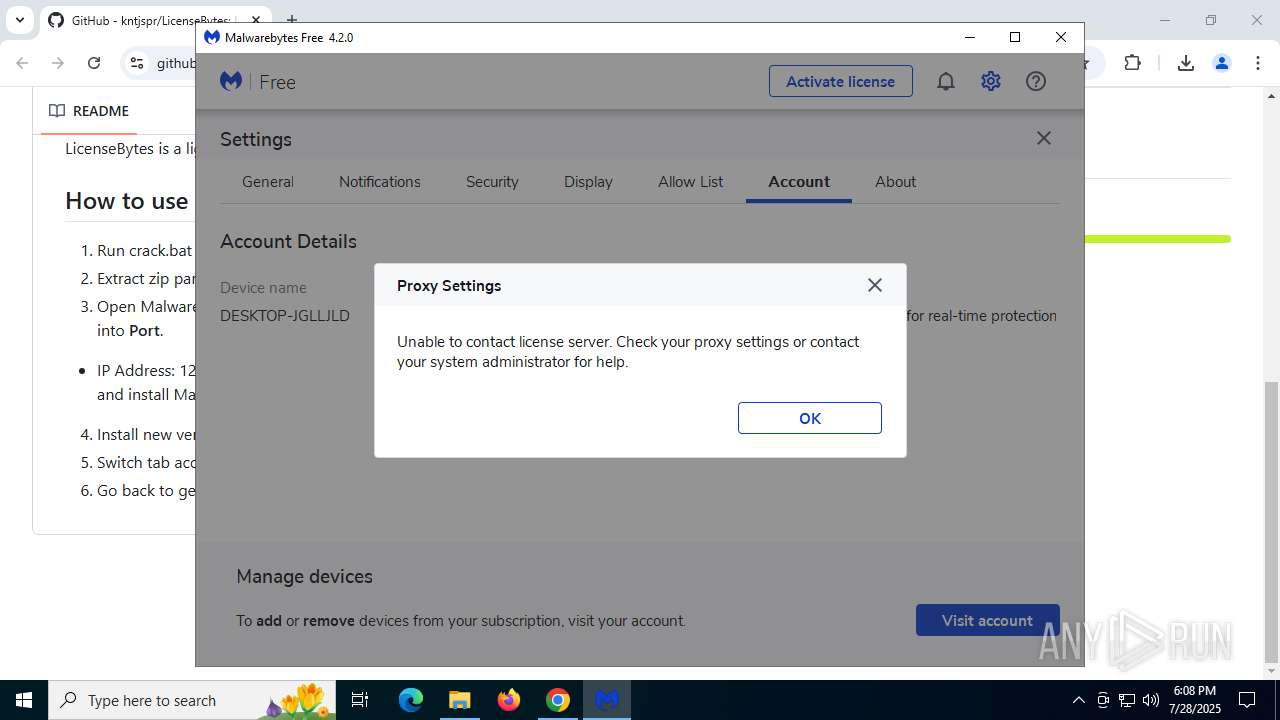
Checks proxy server information
- setup.exe (PID: 6400)
- slui.exe (PID: 6756)
- mbamtray.exe (PID: 7404)
- mbam.exe (PID: 3460)
Reads the computer name
- MBAMInstallerService.exe (PID: 7888)
- setup.exe (PID: 6400)
- MBAMService.exe (PID: 984)
- MBAMService.exe (PID: 2192)
- mbamtray.exe (PID: 7404)
- mbam.exe (PID: 3460)
- LicenseMalwareBytes.exe (PID: 7748)
- LicenseMalwareBytes.exe (PID: 620)
Creates files in the program directory
- MBAMInstallerService.exe (PID: 7888)
- setup.exe (PID: 6400)
- MBAMService.exe (PID: 2192)
The sample compiled with spanish language support
- MBAMInstallerService.exe (PID: 7888)
Reads the software policy settings
- slui.exe (PID: 6756)
Reads the machine GUID from the registry
- MBAMInstallerService.exe (PID: 7888)
- MBAMService.exe (PID: 2192)
- LicenseMalwareBytes.exe (PID: 7748)
- LicenseMalwareBytes.exe (PID: 620)
Reads CPU info
- MBAMService.exe (PID: 2192)
Reads the time zone
- MBAMService.exe (PID: 2192)
CONNECTWISE has been detected
- MBAMService.exe (PID: 2192)
Reads Environment values
- MBAMService.exe (PID: 2192)
Creates files or folders in the user directory
- mbam.exe (PID: 3460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
201
Monitored processes
51
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 72 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 620 | C:\Users\admin\Downloads\LicenseBytes-main\LicenseBytes-main\\LicenseMalwareBytes.exe | C:\Users\admin\Downloads\LicenseBytes-main\LicenseBytes-main\LicenseMalwareBytes.exe | — | LicenseMalwareBytes.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 4294967295 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Malwarebytes\Anti-Malware\MBAMService.exe" /Service /Protected | C:\Program Files\Malwarebytes\Anti-Malware\MBAMService.exe | MBAMInstallerService.exe | ||||||||||||
User: SYSTEM Company: Malwarebytes Integrity Level: SYSTEM Description: Malwarebytes Service Exit code: 0 Version: 3.2.0.912 Modules
| |||||||||||||||
| 1056 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=2160,i,12222627713126744744,9138246616778997415,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2152 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\LicenseBytes-main.zip" C:\Users\admin\Downloads\LicenseBytes-main\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Malwarebytes\Anti-Malware\MBAMService.exe" | C:\Program Files\Malwarebytes\Anti-Malware\MBAMService.exe | services.exe | ||||||||||||
User: SYSTEM Company: Malwarebytes Integrity Level: SYSTEM Description: Malwarebytes Service Version: 3.2.0.912 Modules
| |||||||||||||||
| 2228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://github.com/kntjspr/LicenseBytes" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5804,i,12222627713126744744,9138246616778997415,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=6272 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgABAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1896,i,12222627713126744744,9138246616778997415,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=1892 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
44 025
Read events
43 434
Write events
572
Delete events
19
Modification events
| (PID) Process: | (2228) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2228) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2228) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2228) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2228) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2228) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1F |
Value: 1 | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1352) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
421
Suspicious files
407
Text files
1 135
Unknown types
297
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF18d9e0.TMP | — | |
MD5:— | SHA256:— | |||
| 2228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF18d9e0.TMP | — | |
MD5:— | SHA256:— | |||
| 2228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF18d9f0.TMP | — | |
MD5:— | SHA256:— | |||
| 2228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF18d9ff.TMP | — | |
MD5:— | SHA256:— | |||
| 2228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF18d9ff.TMP | — | |
MD5:— | SHA256:— | |||
| 2228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2228 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF18da0f.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
87
DNS requests
84
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1212 | chrome.exe | GET | 200 | 142.250.185.142:80 | http://clients2.google.com/time/1/current?cup2key=8:T_nUAquG6GXXgJng6p1ZvdXsm1Q_6UeKxulyYJul03s&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
4520 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.36:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8172 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8172 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2528 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | unknown | — | — | whitelisted |
2528 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | unknown | — | — | whitelisted |
2528 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | unknown | — | — | whitelisted |
2528 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2288 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1212 | chrome.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
1212 | chrome.exe | 142.250.185.142:80 | clients2.google.com | GOOGLE | US | whitelisted |
1212 | chrome.exe | 142.250.186.106:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
1212 | chrome.exe | 142.250.27.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
1212 | chrome.exe | 185.199.111.154:443 | github.githubassets.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
github.com |
| whitelisted |
accounts.google.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
user-images.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
mbamtray.exe | QAxBase::setControl: requested control {F36AD0D0-B5F0-4C69-AF08-603D177FEF0E} could not be instantiated
|
mbamtray.exe | QAxBase: Error calling IDispatch member GetLastActiveScanner: Exception thrown by server
|
mbamtray.exe | Code : -2147467259
|
mbamtray.exe | Source :
|
mbamtray.exe | Description:
|
mbamtray.exe | Help :
|
mbamtray.exe | Connect to the exception(int,QString,QString,QString) signal to catch this exception
|
mbamtray.exe | qt.scenegraph.general: Loading backend software
|
mbamtray.exe |
class QSharedPointer<class QPluginLoader> __cdecl FindAndActivatePlugin(const class QString &,const class QString &) Plugin found, activating: "TrayPlugin.dll"
|
mbamtray.exe | void __cdecl PageStatusMonitor::OnRequestFinished(class QNetworkReply *) "Page: https://links.malwarebytes.com/link/3x_cart?affiliate=&uuid=&x-source=trial-avail&x-action=comparison_chart&x-token_secret=jgQTeomKKCX-ohzCvjCx3hwcIVtPY30kwsHoc_3VxIWF8YGGbcdCrb_PFmTgtVcdO-QRWiOwdVTGsLwA3breug==&ADDITIONAL_x-token_secret=jgQTeomKKCX-ohzCvjCx3hwcIVtPY30kwsHoc_3VxIWF8YGGbcdCrb_PFmTgtVcdO-QRWiOwdVTGsLwA3breug==&x-prodcode=MBAM-C&lang=en&version=4.2.0.82&ptb=0 received code: 307"
|