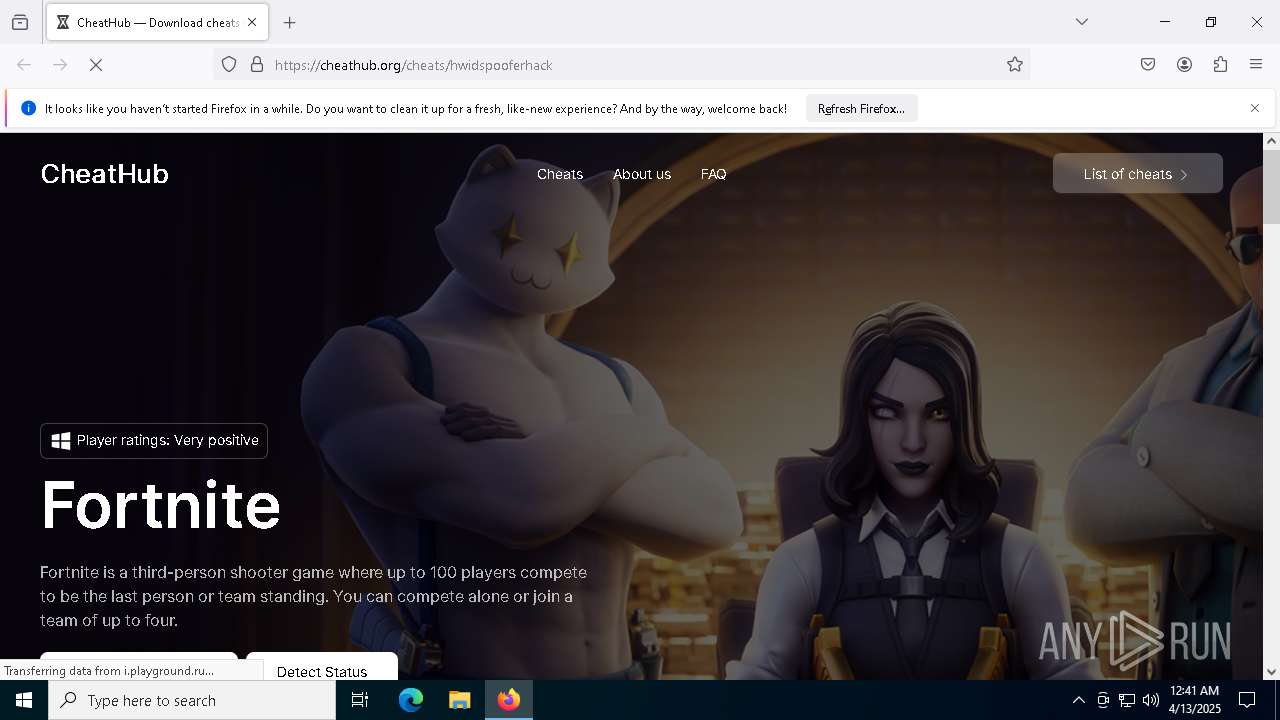
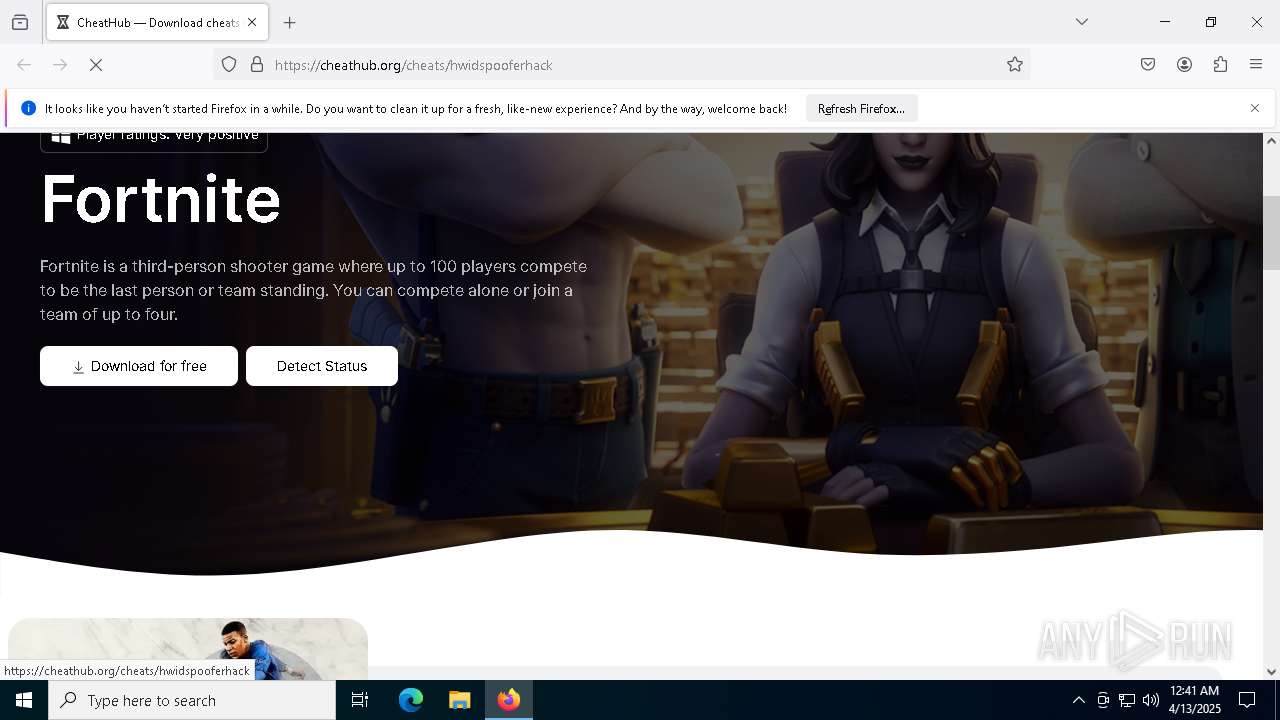
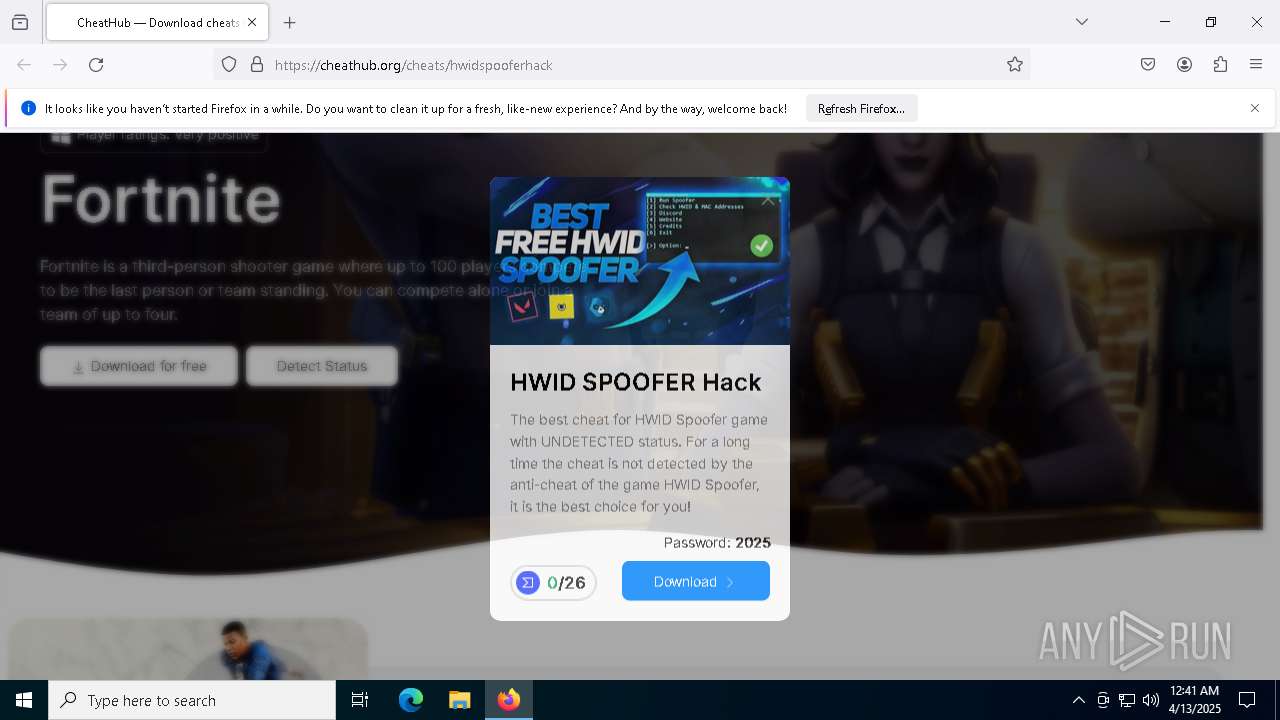
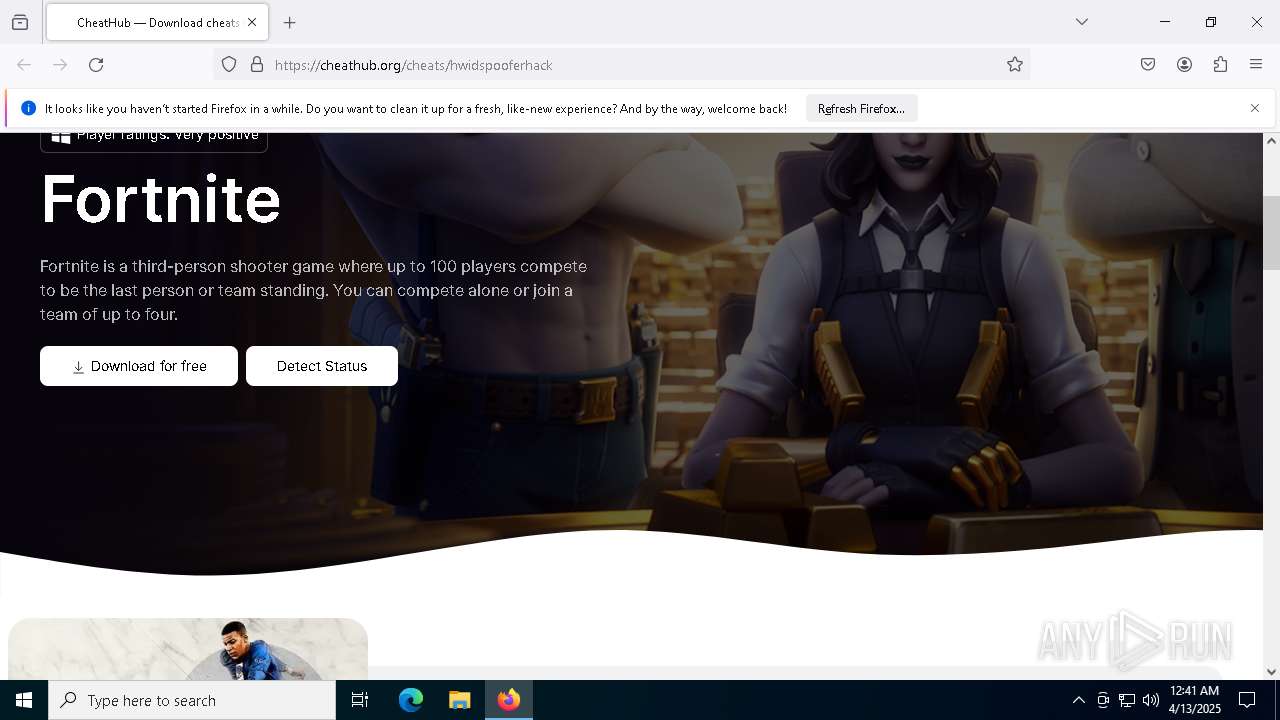
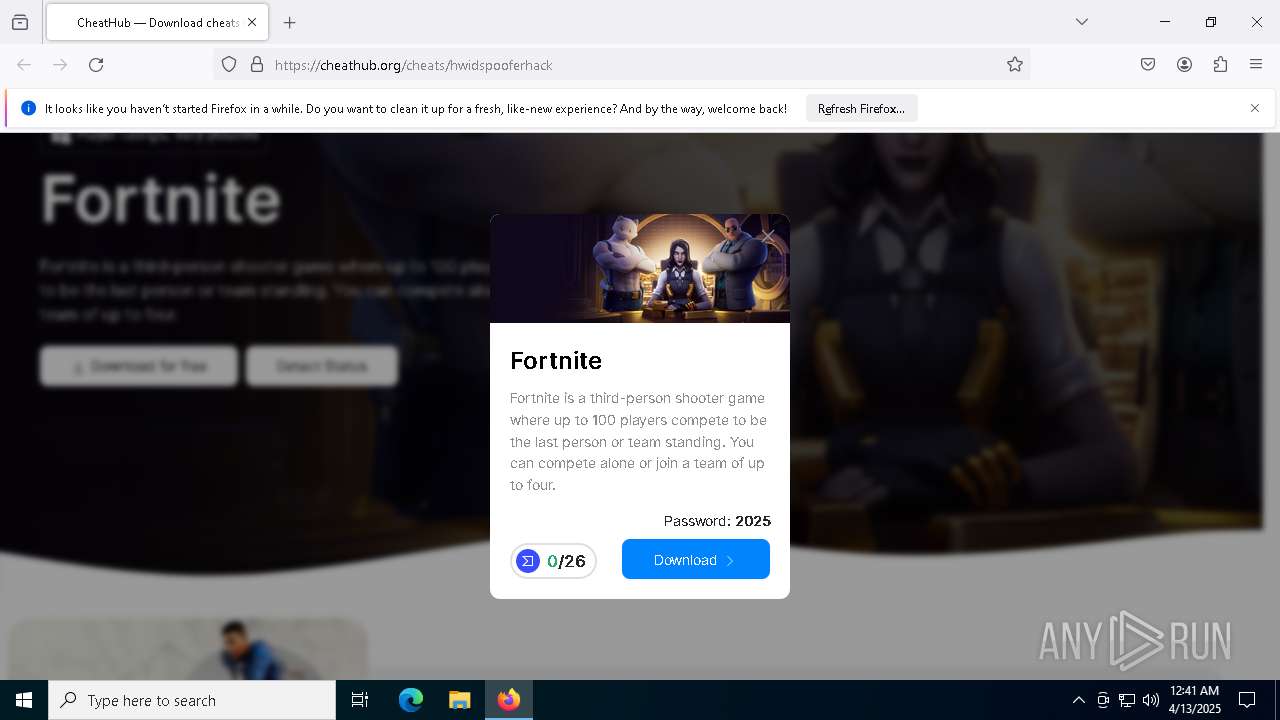
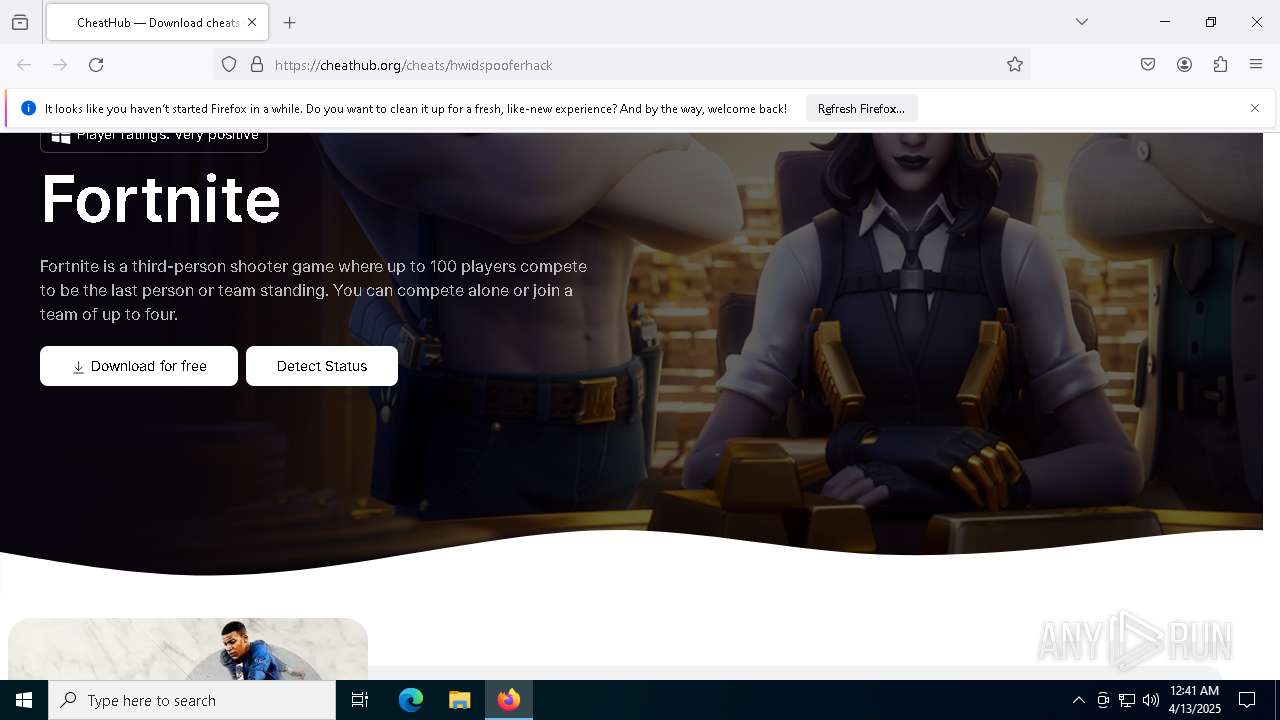
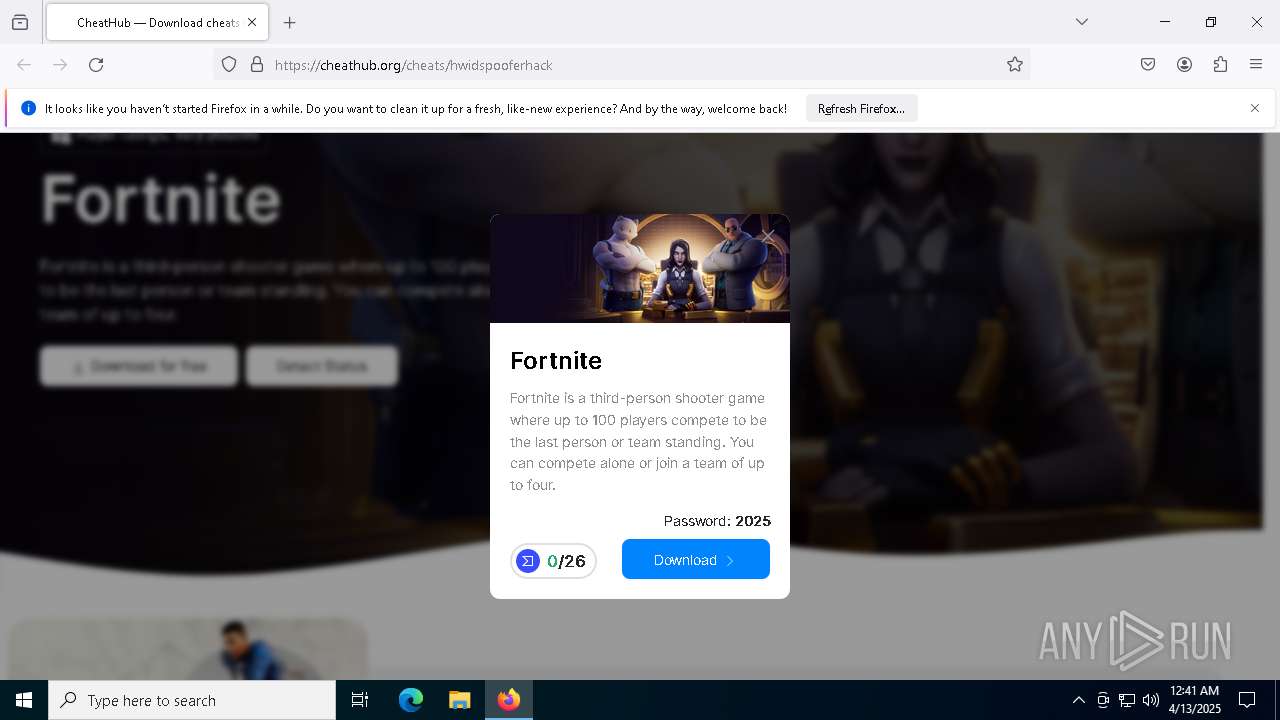
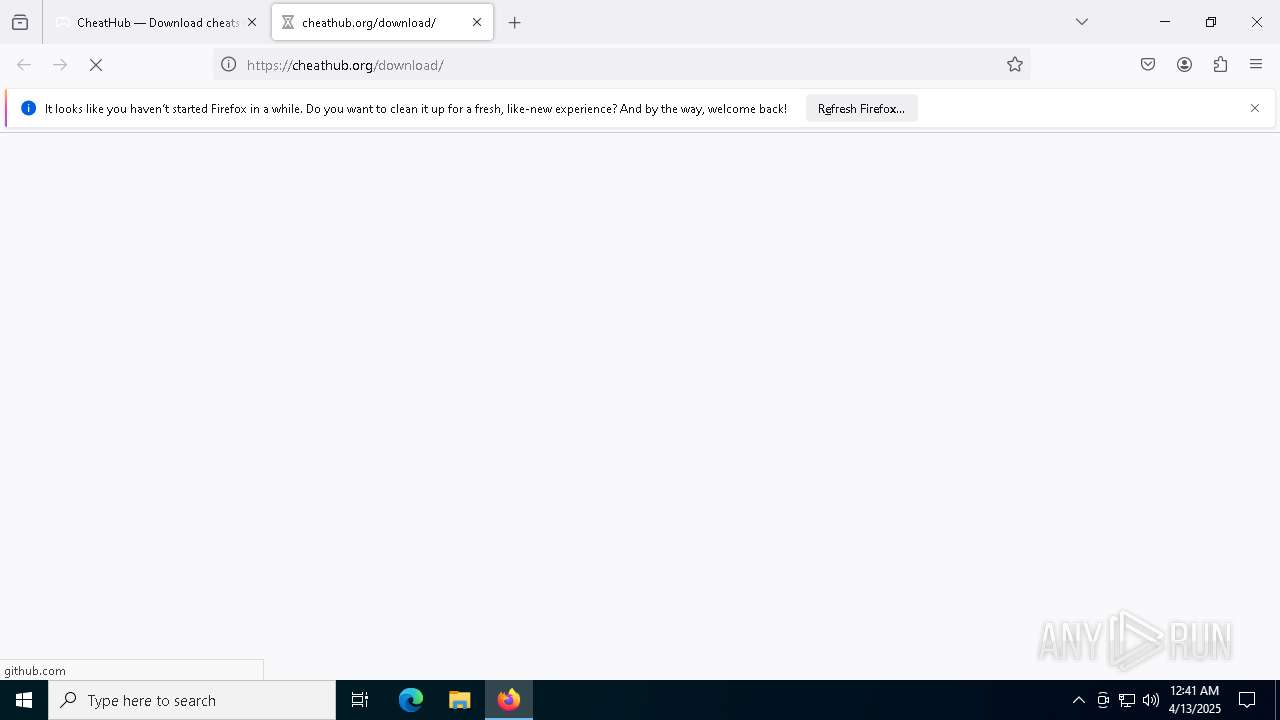
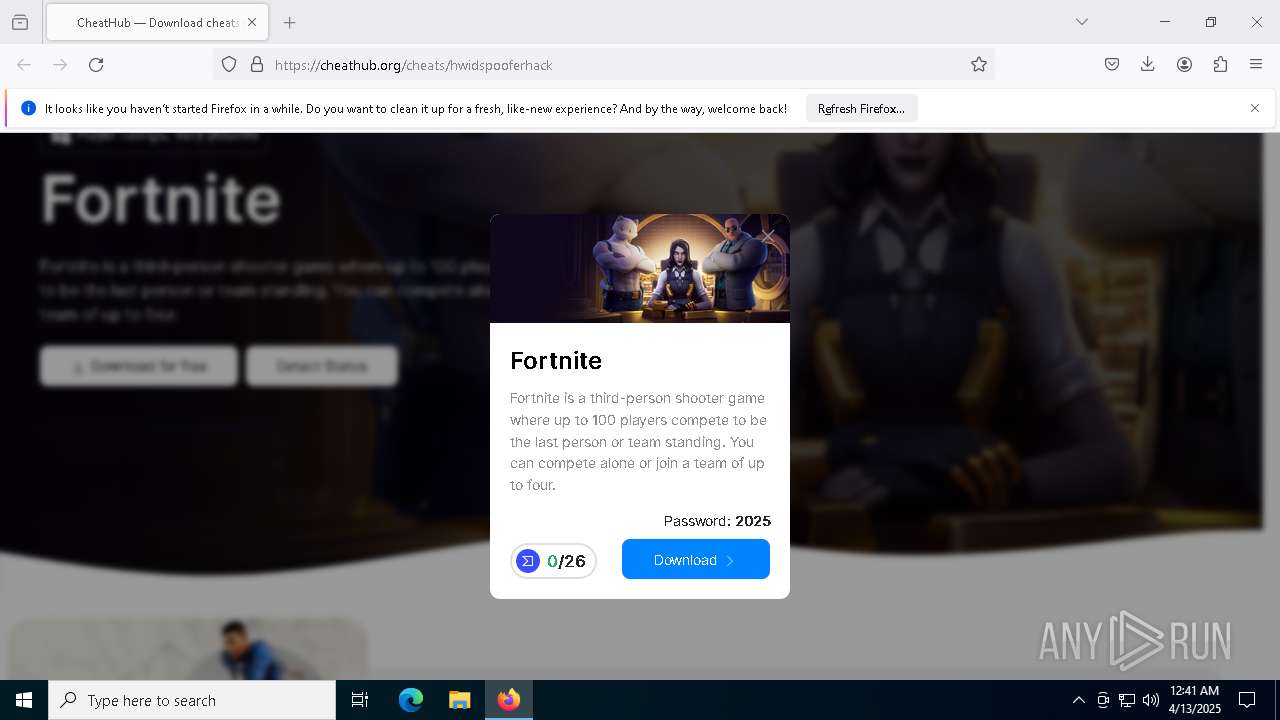
| URL: | https://cheathub.org/cheats/hwidspooferhack |
| Full analysis: | https://app.any.run/tasks/6e0e5ff2-e314-47f7-9caa-87ac4c5edad3 |
| Verdict: | Malicious activity |
| Analysis date: | April 13, 2025, 00:40:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6E16C34914CCE05C5CD773761FDD9CCF |
| SHA1: | 39BC7D699C46B26F5CBB9567E5CBBD04F0092158 |
| SHA256: | FFE06688571076D2409B9F1C9613517645AECBD82BE79FAB79AA487BE140E28B |
| SSDEEP: | 3:N8QtQrKXJkWWYglWGO:2QCMJfxXZ |
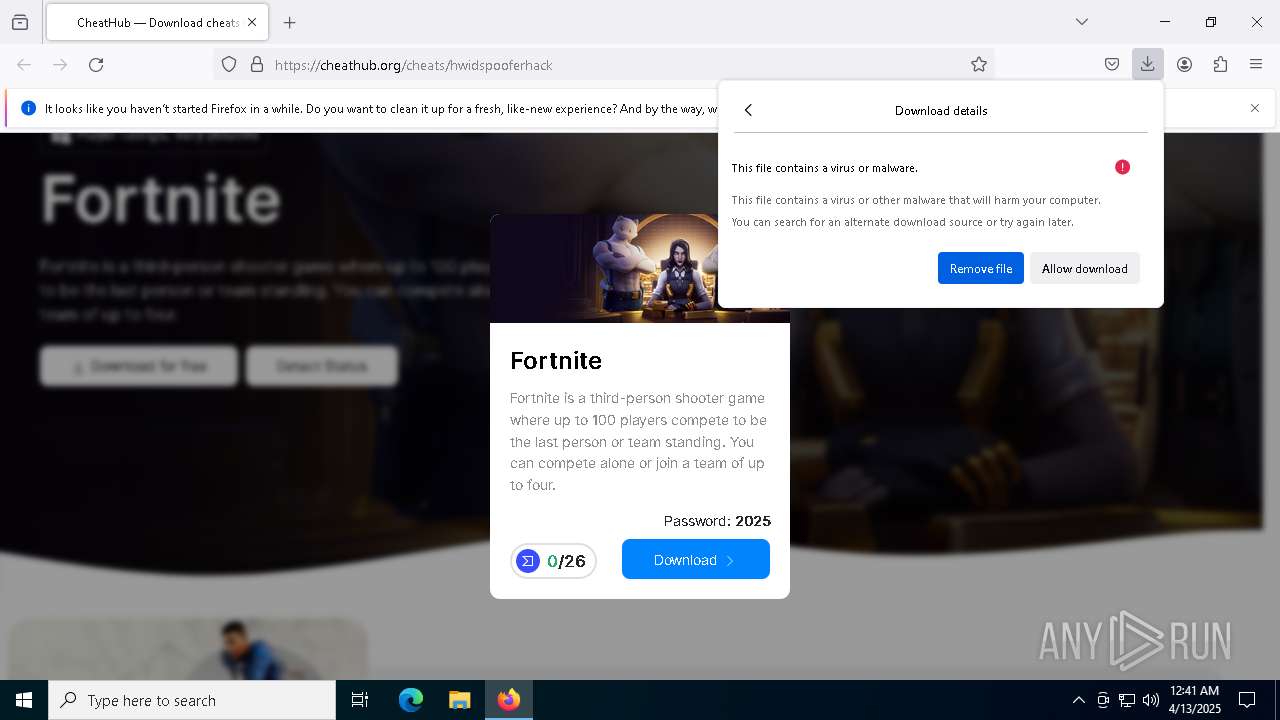
MALICIOUS
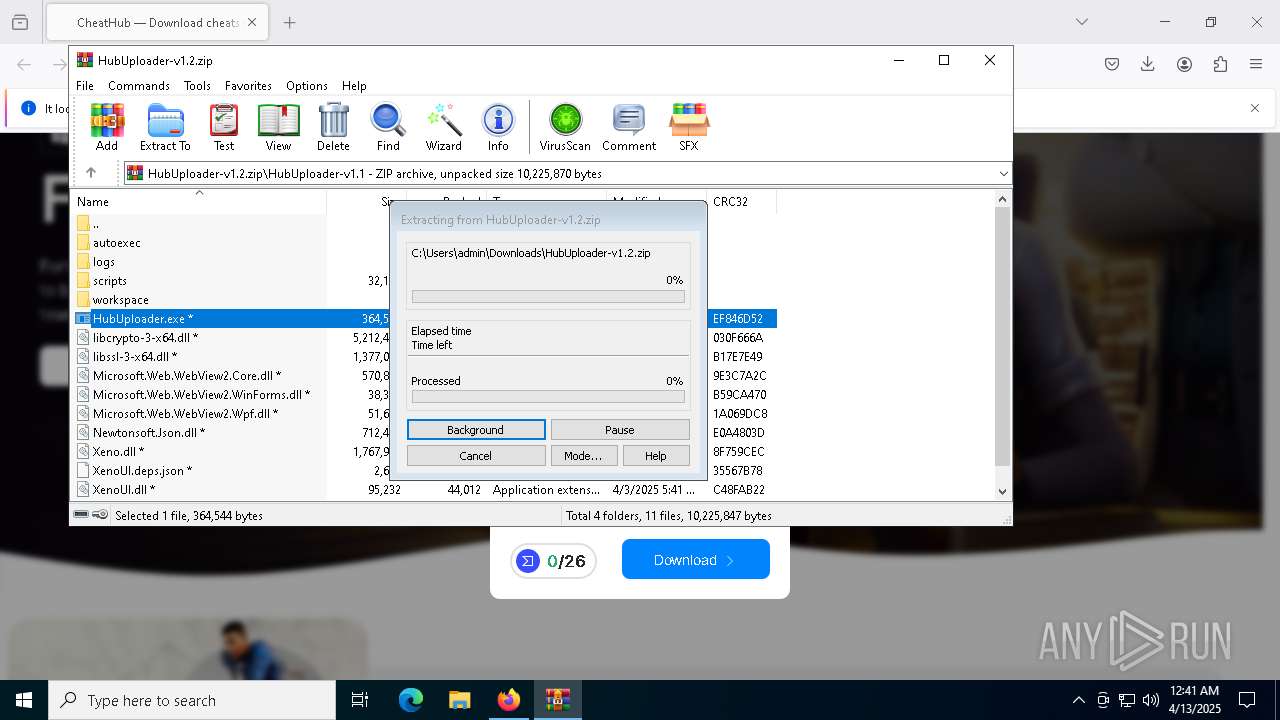
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 6828)
- HubUploader.exe (PID: 2504)
Changes Windows Defender settings
- cmd.exe (PID: 6828)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 856)
- HubUploader.exe (PID: 5328)
Starts CMD.EXE for commands execution
- HubUploader.exe (PID: 2504)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 6828)
Application launched itself
- HubUploader.exe (PID: 5328)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6828)
- cmd.exe (PID: 7488)
Downloads file from URI via Powershell
- powershell.exe (PID: 7748)
Reads the date of Windows installation
- HubUploader.exe (PID: 5328)
INFO
Application launched itself
- firefox.exe (PID: 2140)
- firefox.exe (PID: 3332)
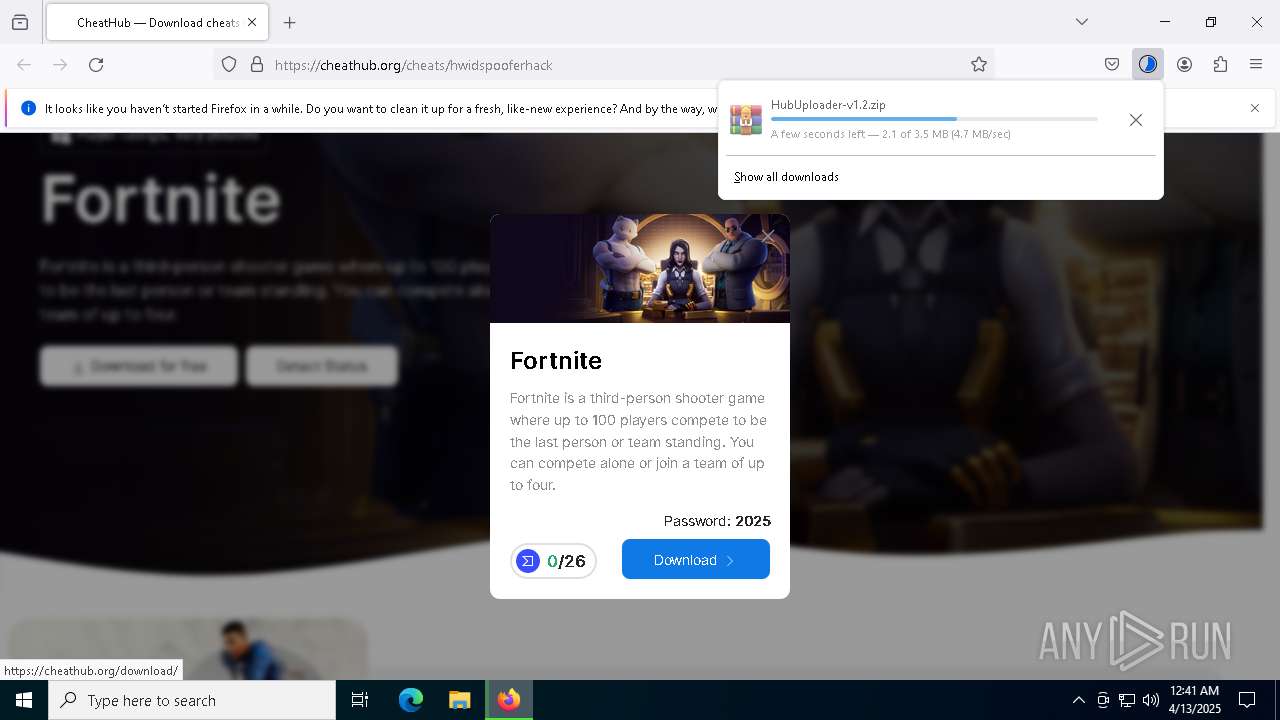
Autorun file from Downloads
- firefox.exe (PID: 3332)
Manual execution by a user
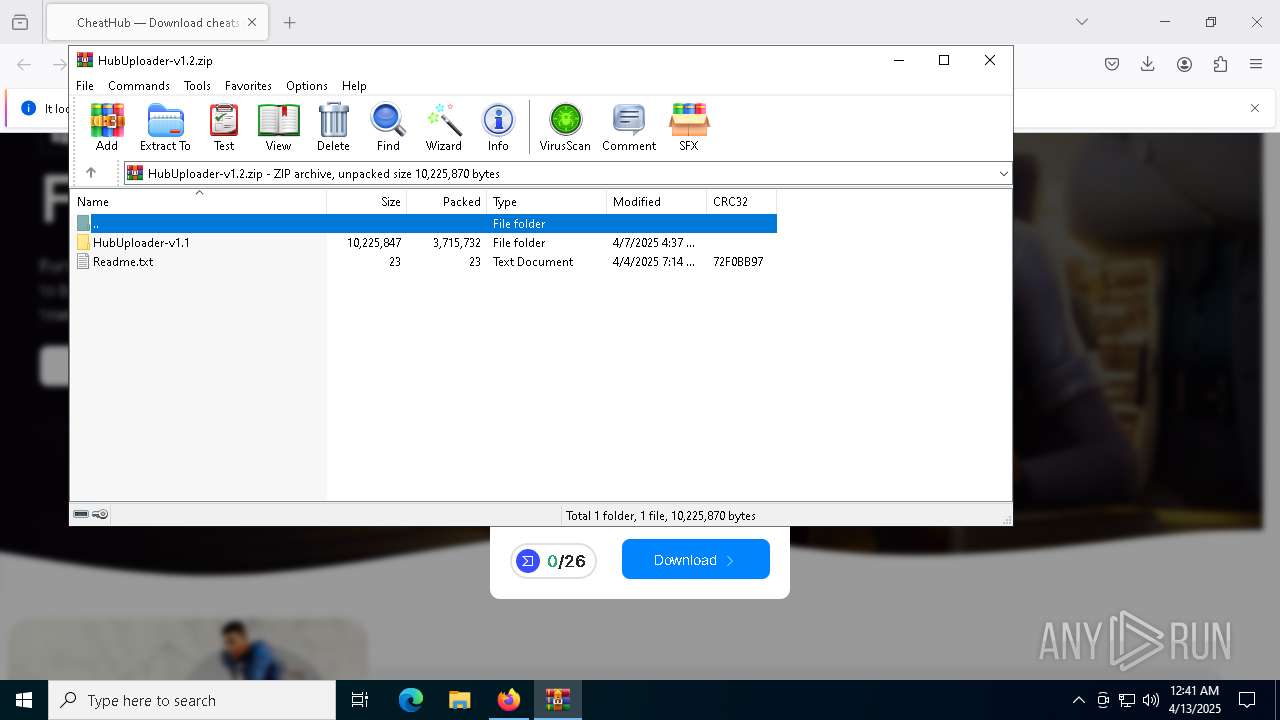
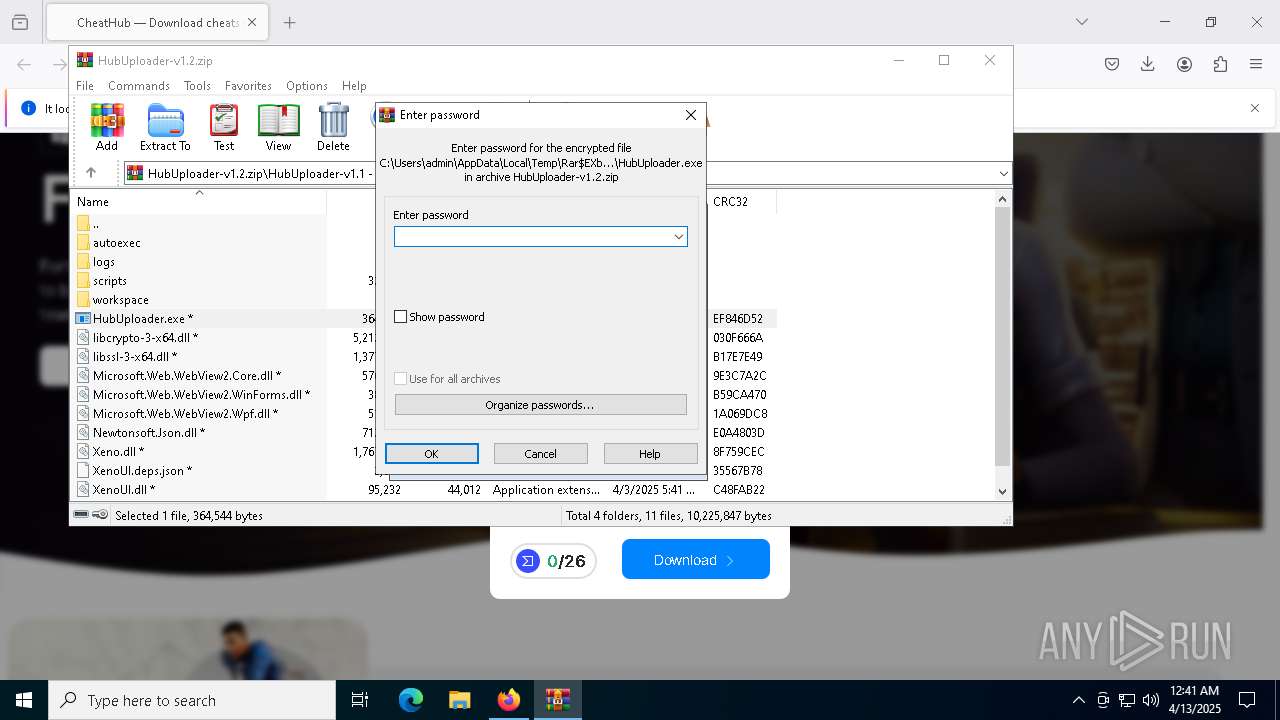
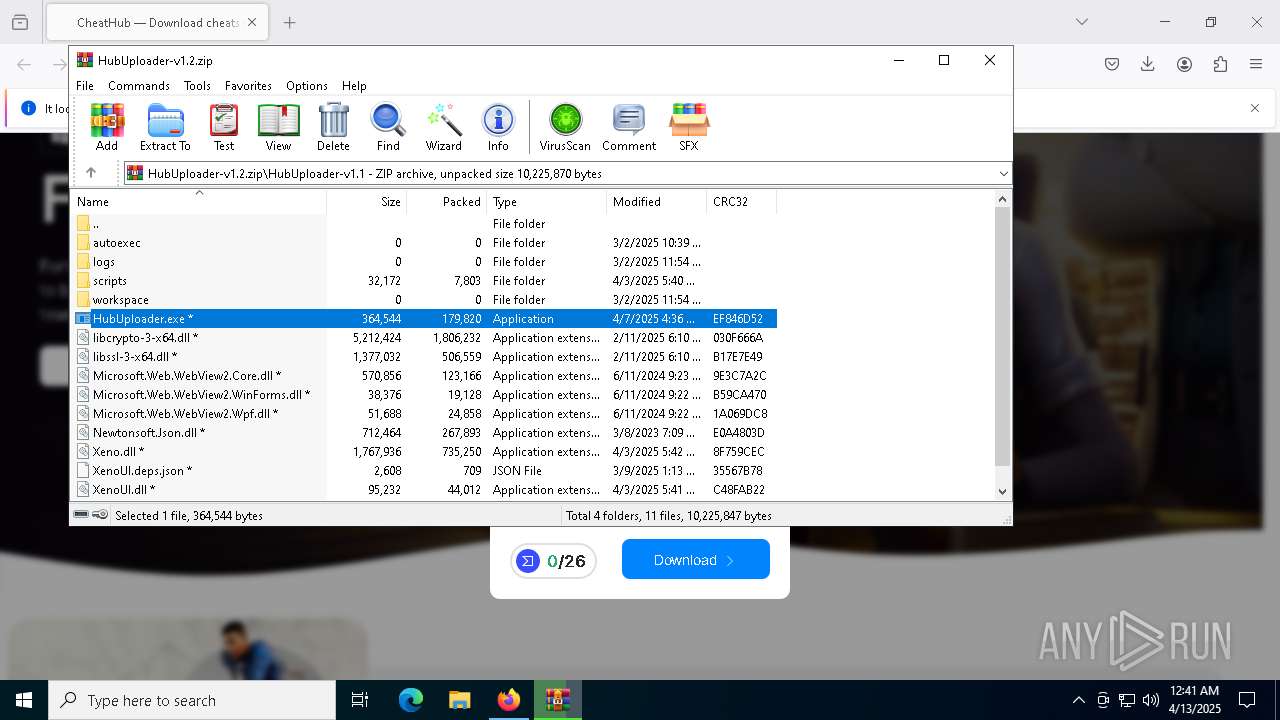
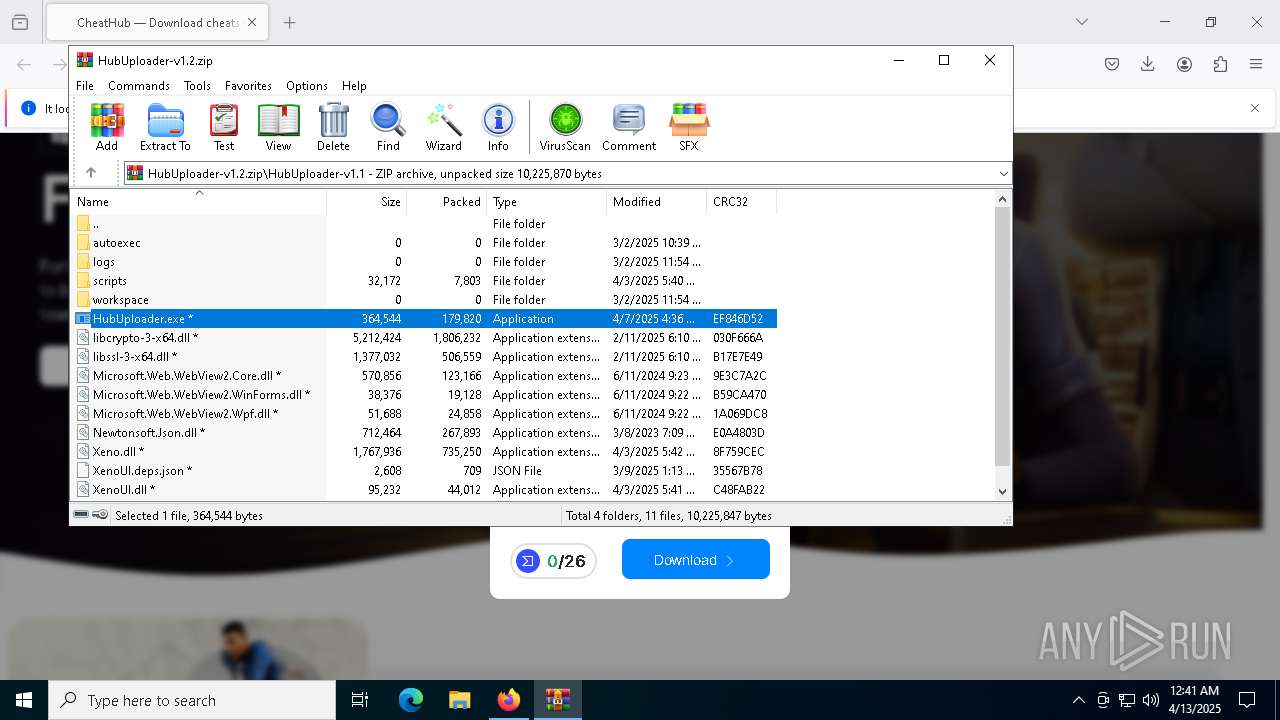
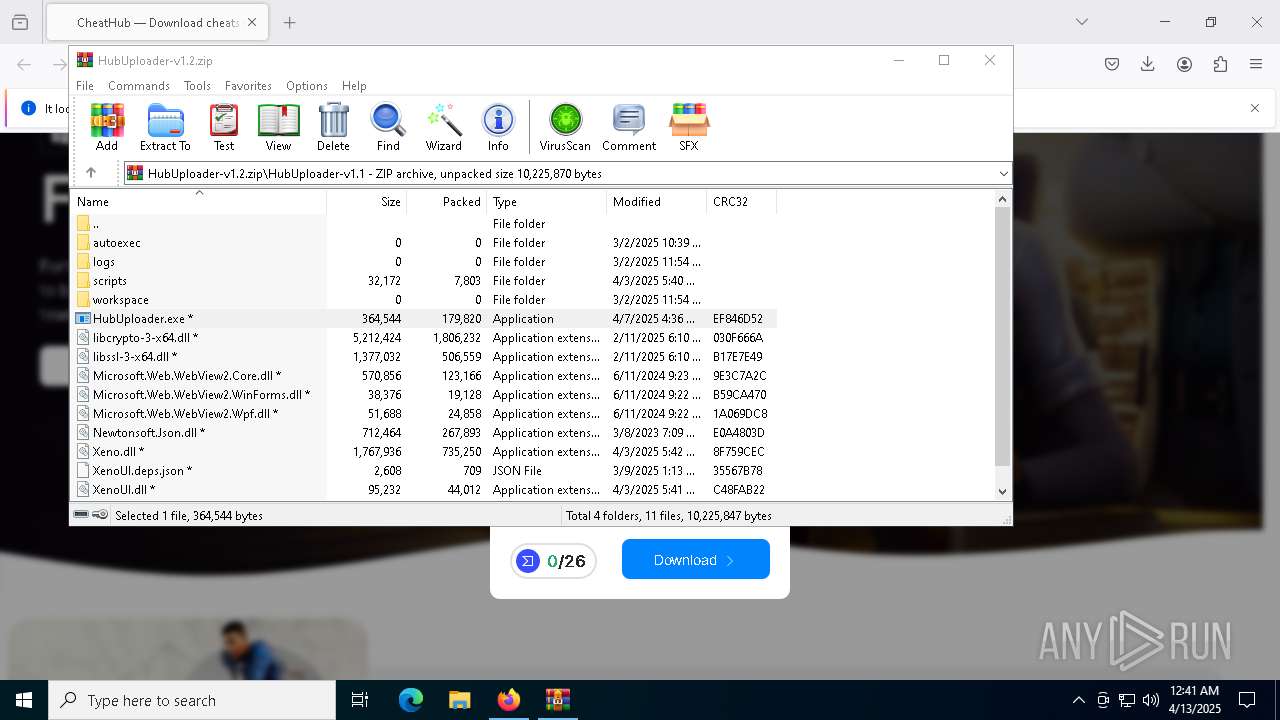
- WinRAR.exe (PID: 856)
The sample compiled with english language support
- WinRAR.exe (PID: 856)
Reads the computer name
- HubUploader.exe (PID: 5328)
- HubUploader.exe (PID: 2504)
Checks supported languages
- HubUploader.exe (PID: 5328)
- HubUploader.exe (PID: 2504)
Process checks computer location settings
- HubUploader.exe (PID: 5328)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 856)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4728)
- powershell.exe (PID: 7748)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4728)
Disables trace logs
- powershell.exe (PID: 7748)
Checks proxy server information
- powershell.exe (PID: 7748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
150
Monitored processes
22
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\HubUploader-v1.2.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://cheathub.org/cheats/hwidspooferhack" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
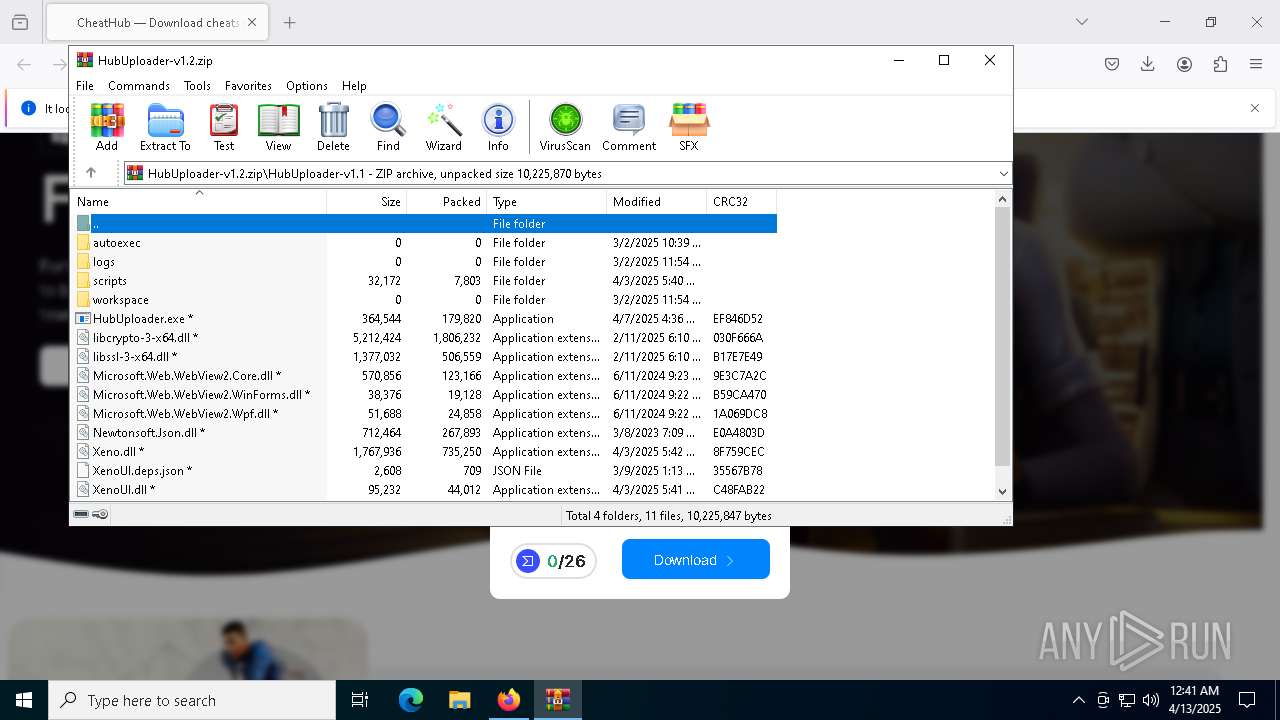
| 2504 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb856.21861\HubUploader-v1.1\HubUploader.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb856.21861\HubUploader-v1.1\HubUploader.exe | HubUploader.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 3100 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3332 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://cheathub.org/cheats/hwidspooferhack | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 4728 | powershell -Command "Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\uilgdogy', 'C:\Users', 'C:\ProgramData'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5328 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb856.21861\HubUploader-v1.1\HubUploader.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb856.21861\HubUploader-v1.1\HubUploader.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5376 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5252 -childID 6 -isForBrowser -prefsHandle 5500 -prefMapHandle 5496 -prefsLen 38217 -prefMapSize 244583 -jsInitHandle 1308 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {2e4b87de-568c-4c61-88dd-2a7b3f368437} 3332 "\\.\pipe\gecko-crash-server-pipe.3332" 2e521348850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 6388 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6828 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\uilgdogy', 'C:\Users', 'C:\ProgramData'" | C:\Windows\System32\cmd.exe | — | HubUploader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 519
Read events
25 509
Write events
10
Delete events
0
Modification events
| (PID) Process: | (3332) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\HubUploader-v1.2.zip | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (856) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
9
Suspicious files
154
Text files
30
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3332 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:AADE8C264BC2949C09F23251F94F0F7D | SHA256:AA07E227121171B851F7202696A0C00ACB3390A7B8FC222EC81D44FAAD5B9F2C | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.tmp | binary | |
MD5:4006DDC2918B16C7EF5516C58373842B | SHA256:269EA23B77EDE0874628BD8611BCC5A3E87E0C44CA8A821C0D028B929D4F468F | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db | binary | |
MD5:44756E5EBC76617DF37743E2607EDE71 | SHA256:A730B656DBC3944049739C3397609910537387E553574B12F8319262AF564683 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
107
DNS requests
154
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3332 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
3332 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://o.pki.goog/wr2 | unknown | — | — | whitelisted |
3332 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://o.pki.goog/s/wr3/cgo | unknown | — | — | whitelisted |
3332 | firefox.exe | POST | 200 | 2.23.82.9:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
3332 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
3332 | firefox.exe | POST | 200 | 2.23.82.9:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
3332 | firefox.exe | POST | 200 | 2.23.82.9:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
3332 | firefox.exe | POST | 200 | 2.23.82.57:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
3332 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://o.pki.goog/wr2 | unknown | — | — | whitelisted |
3332 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://o.pki.goog/s/wr3/UTA | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3332 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
3332 | firefox.exe | 34.107.243.93:443 | push.services.mozilla.com | GOOGLE | US | whitelisted |
3332 | firefox.exe | 216.58.212.170:443 | safebrowsing.googleapis.com | — | — | whitelisted |
3332 | firefox.exe | 188.114.96.3:443 | cheathub.org | CLOUDFLARENET | NL | malicious |
3332 | firefox.exe | 34.107.152.202:443 | firefox-settings-attachments.cdn.mozilla.net | GOOGLE | US | whitelisted |
3332 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
cheathub.org |
| malicious |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |