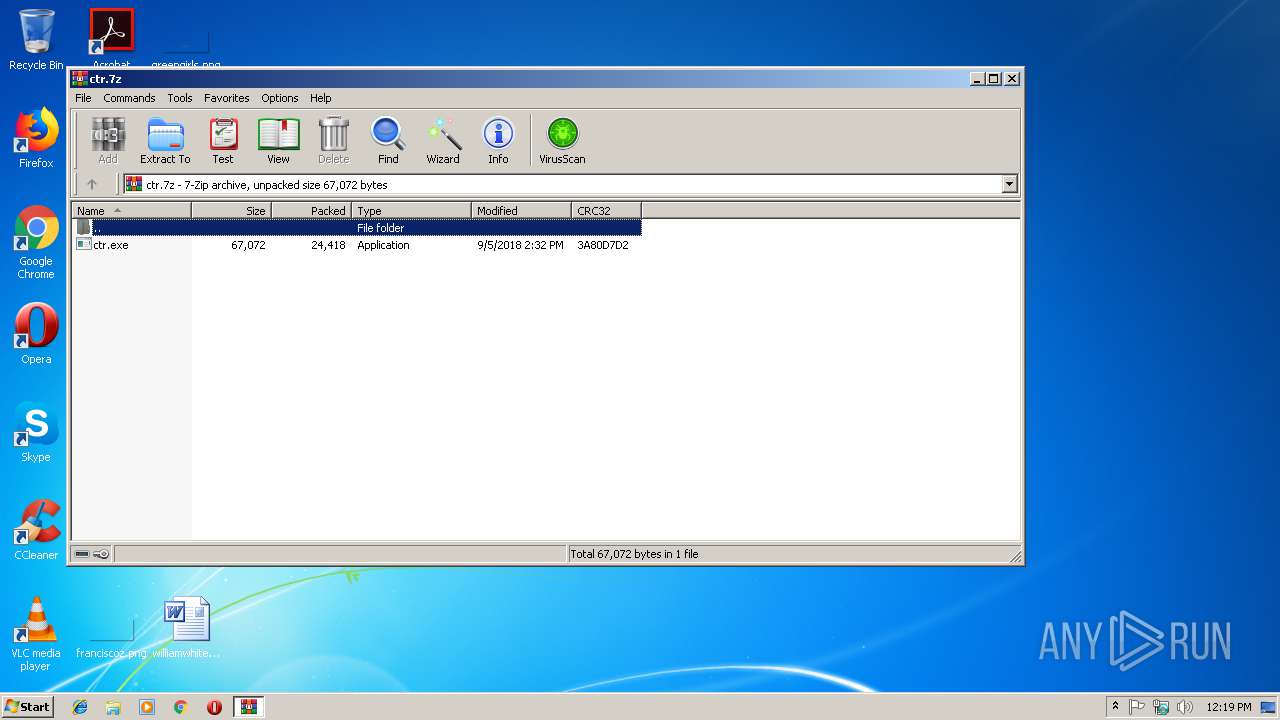
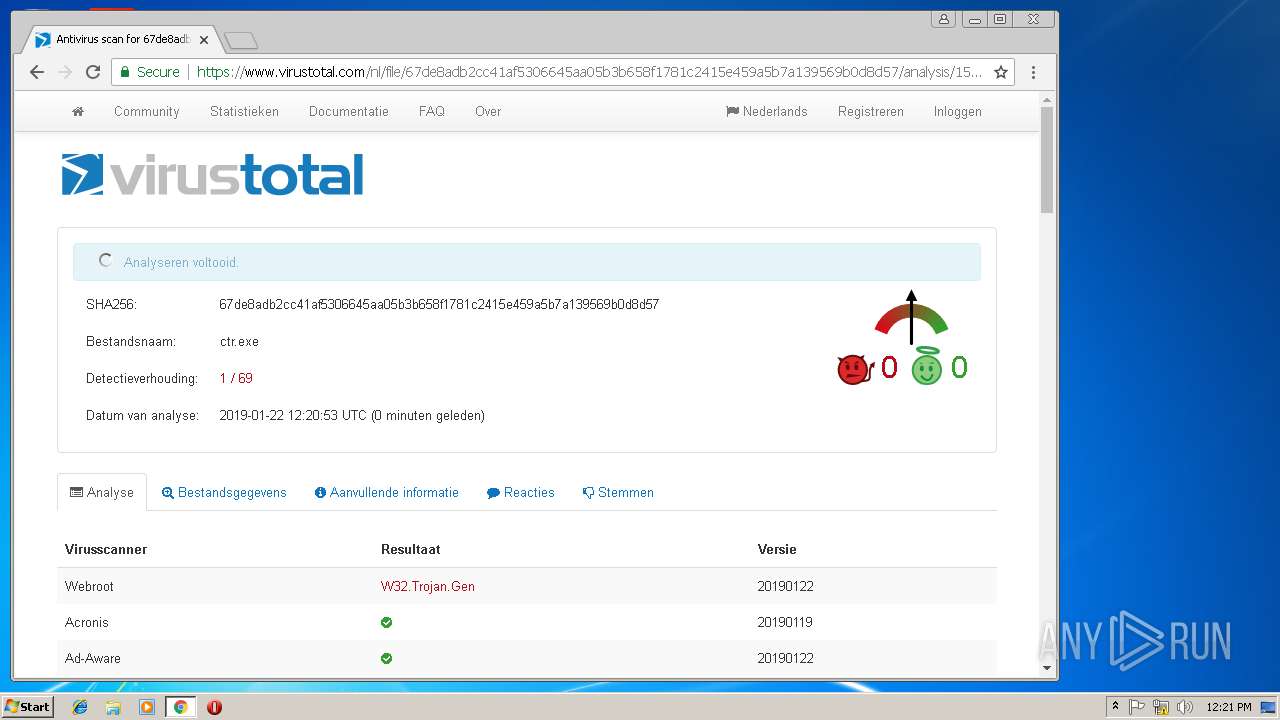
| File name: | ctr.7z |
| Full analysis: | https://app.any.run/tasks/887f7659-a412-472a-abb6-9fa3c7c45689 |
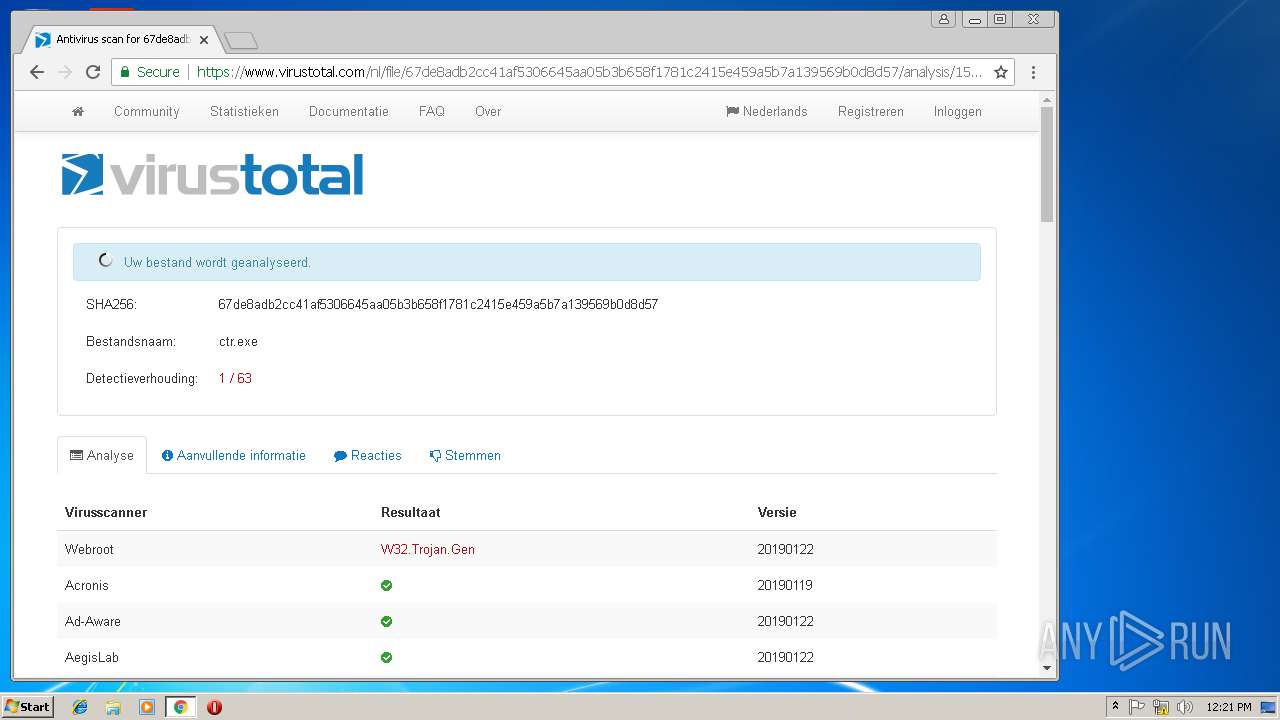
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 12:18:49 |
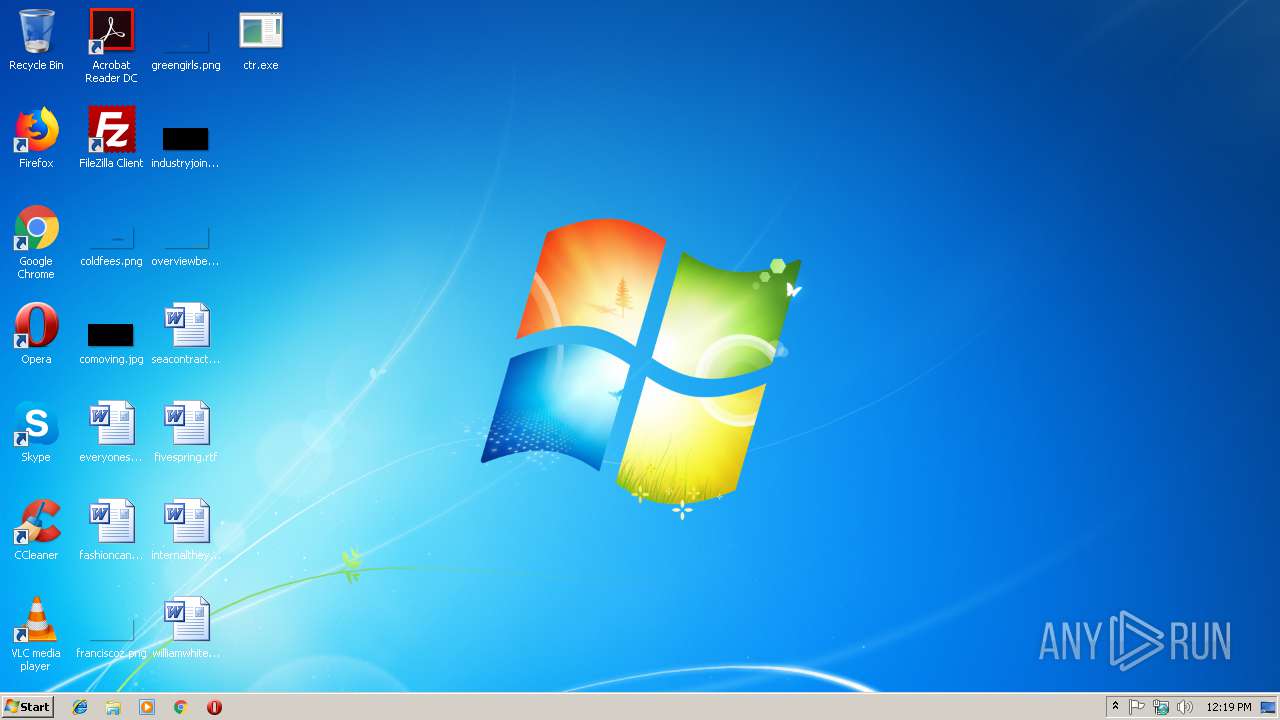
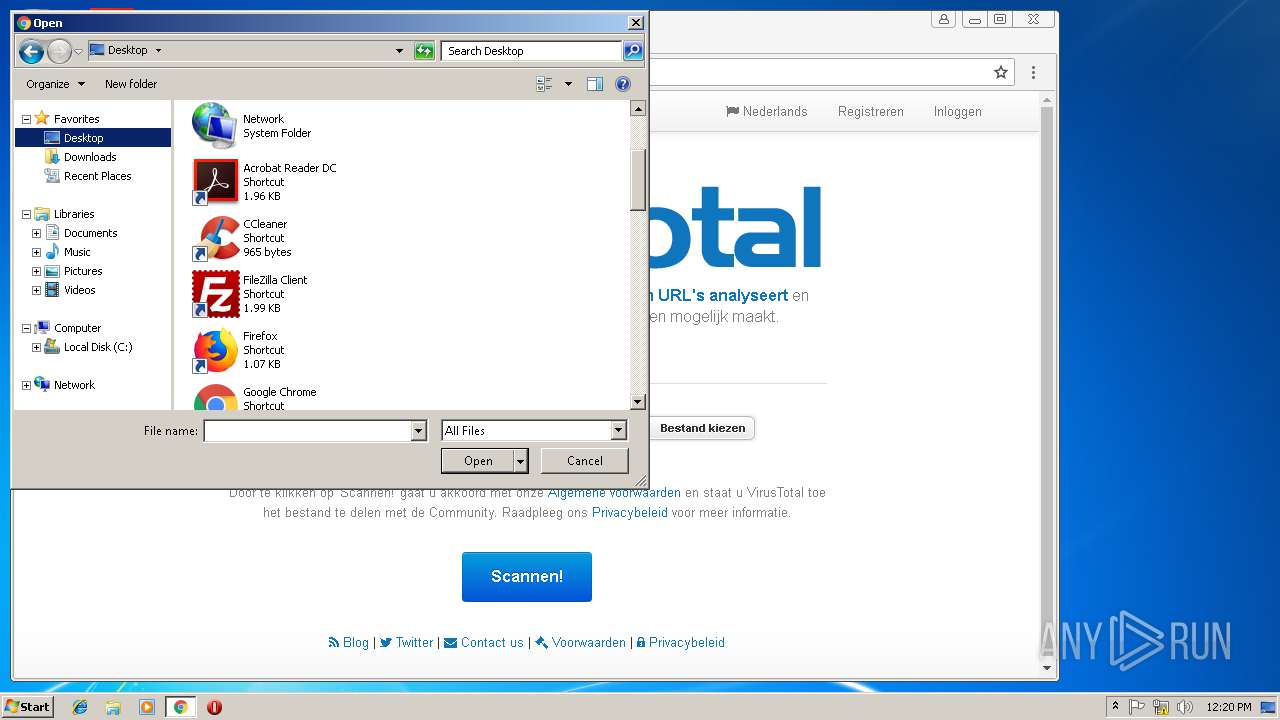
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 7B9D93B7C791E74C203B68E5A4DD6C50 |
| SHA1: | 21616A79E729816557DB0701E18D2DB01978E0DD |
| SHA256: | FFD9A2C899CD1BF6AF8A16C0E9991CE481CB2C94A9BE3E36E28FD97F4F948133 |
| SSDEEP: | 384:EgEinsZZKM/I/EdrVlbwDMA5nOIE8t6aZPEY6orvWa/3ayrz7fsVwlZUujkedWkC:TDZ/EV8fcct6aZX7rBjrz7fsVUUVGy |
MALICIOUS
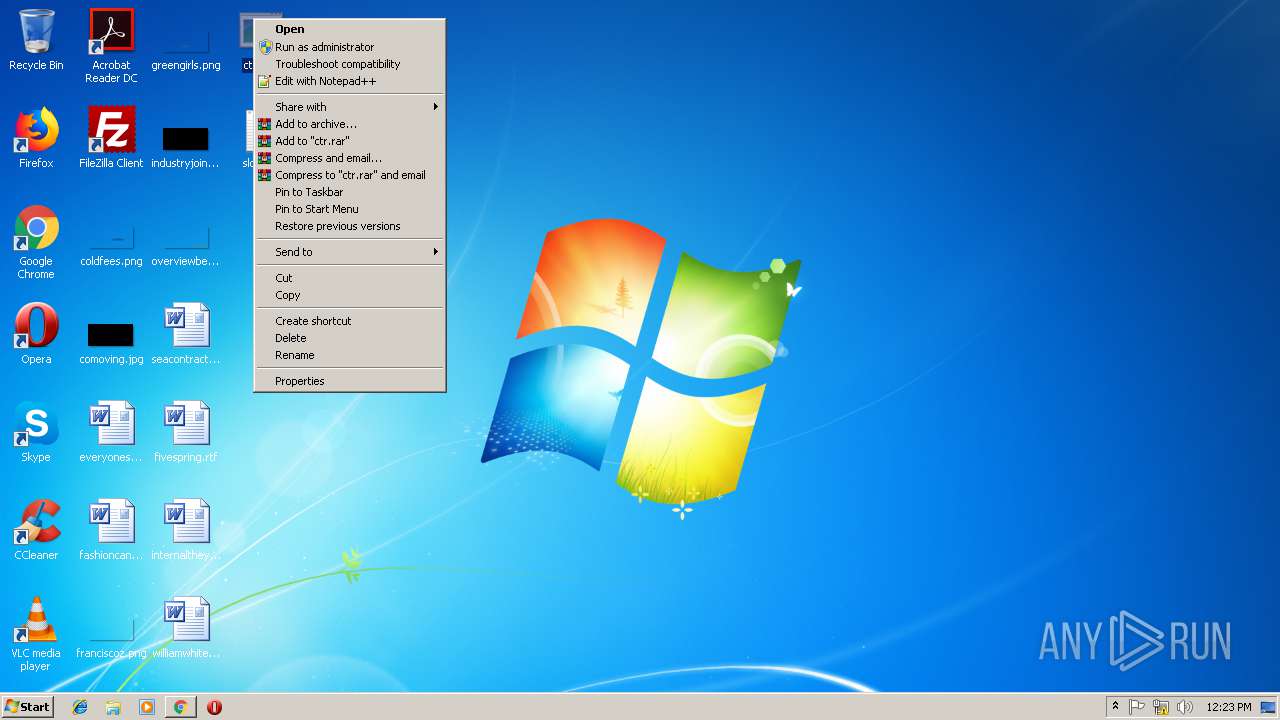
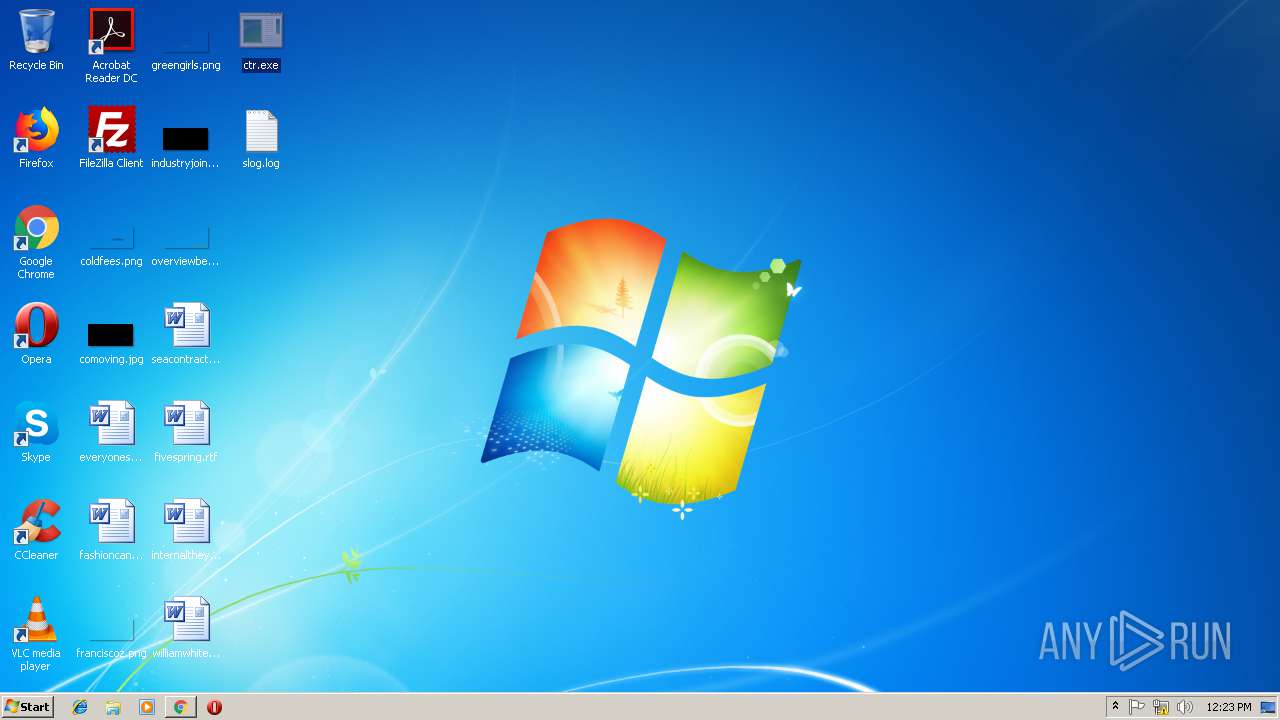
Application was dropped or rewritten from another process
- ctr.exe (PID: 2780)
- ctr.exe (PID: 1028)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2980)
INFO
Application launched itself
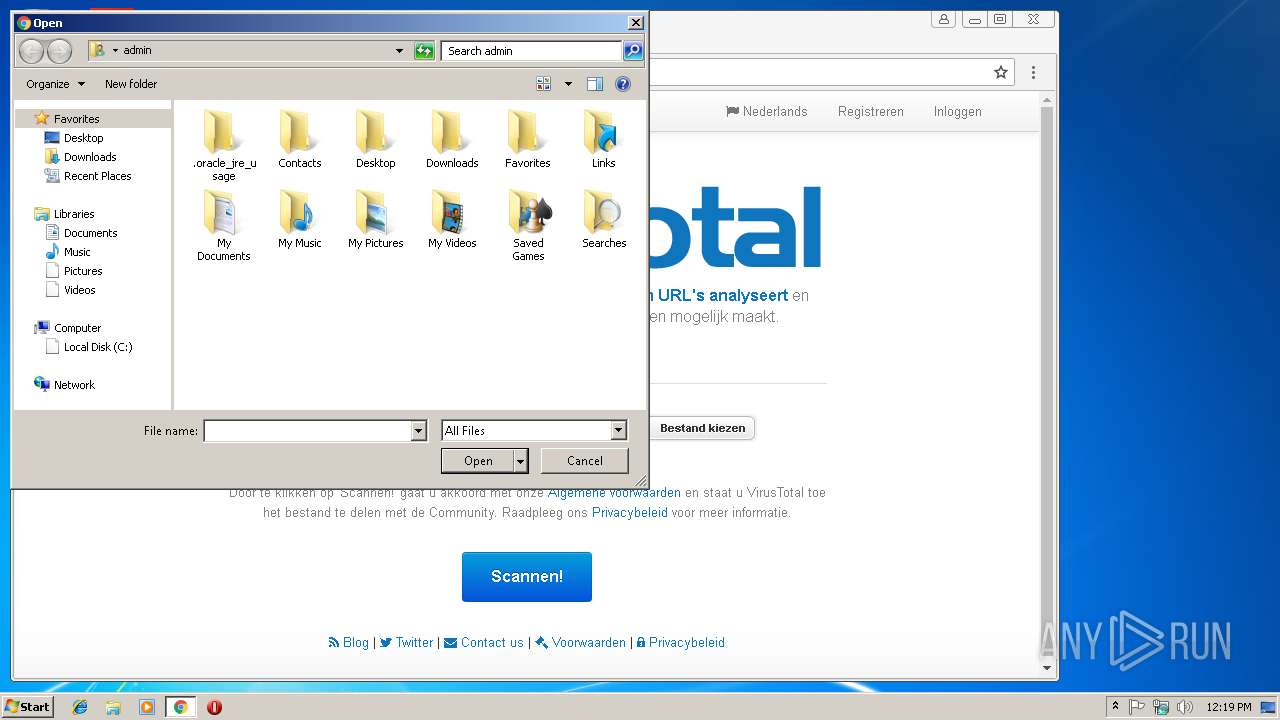
- chrome.exe (PID: 3344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
58
Monitored processes
17
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,8422805637082179802,10775811641080249010,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=813D744AB2F607019597DEEB8F410A42 --mojo-platform-channel-handle=4112 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
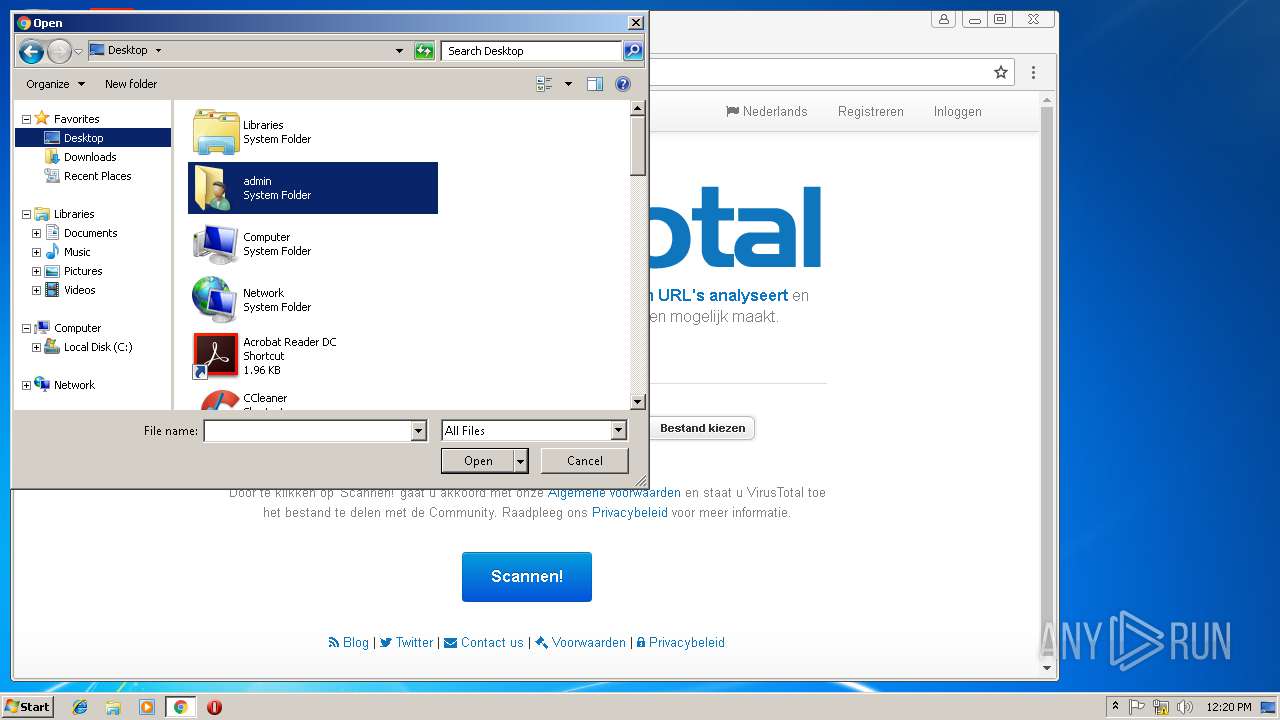
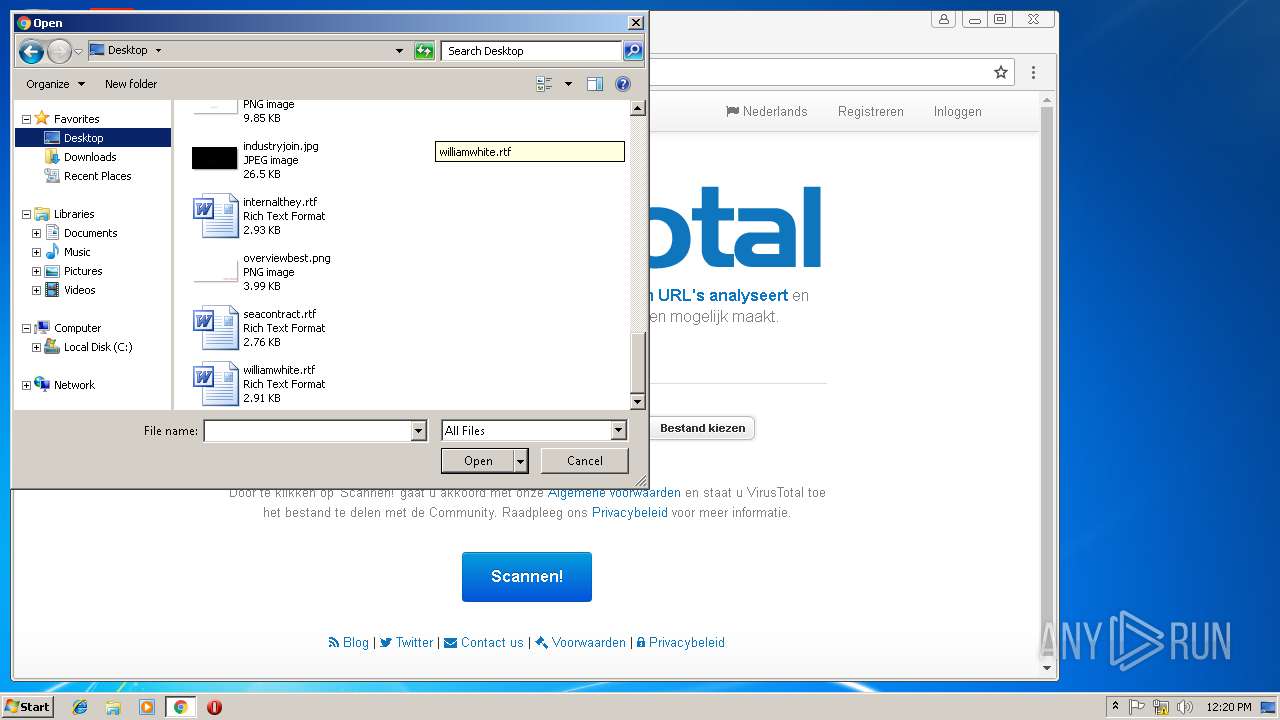
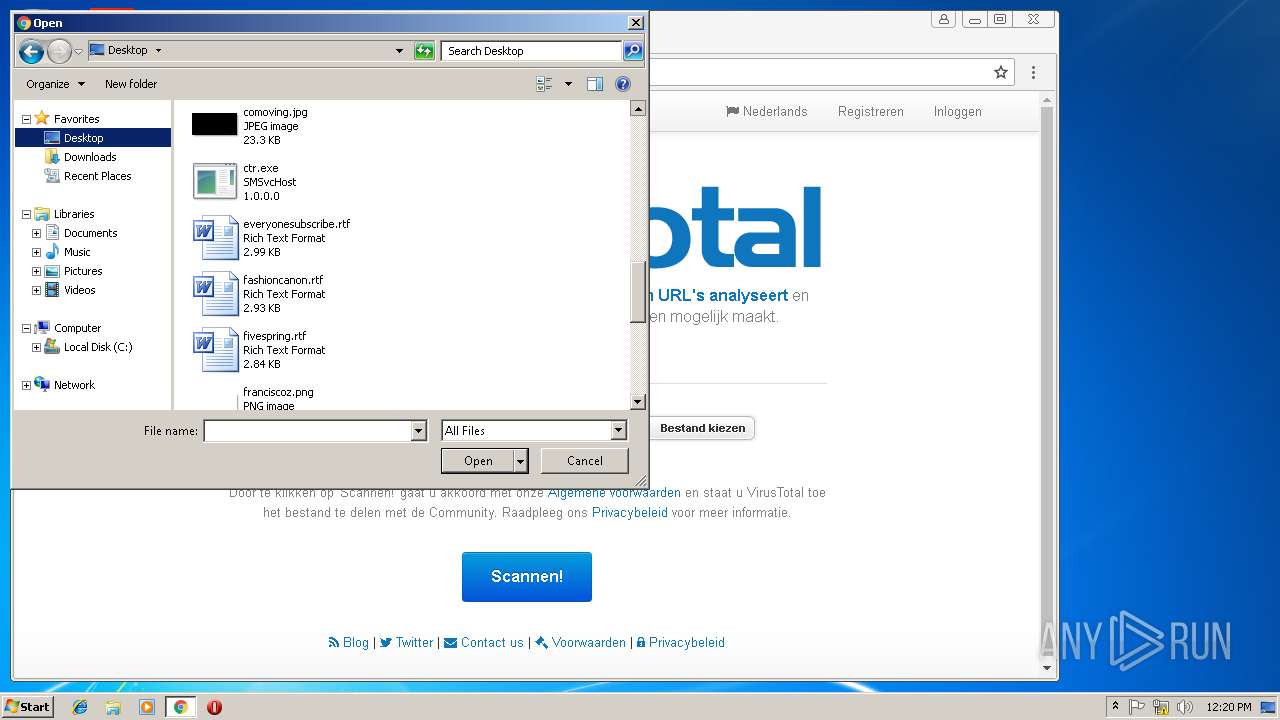
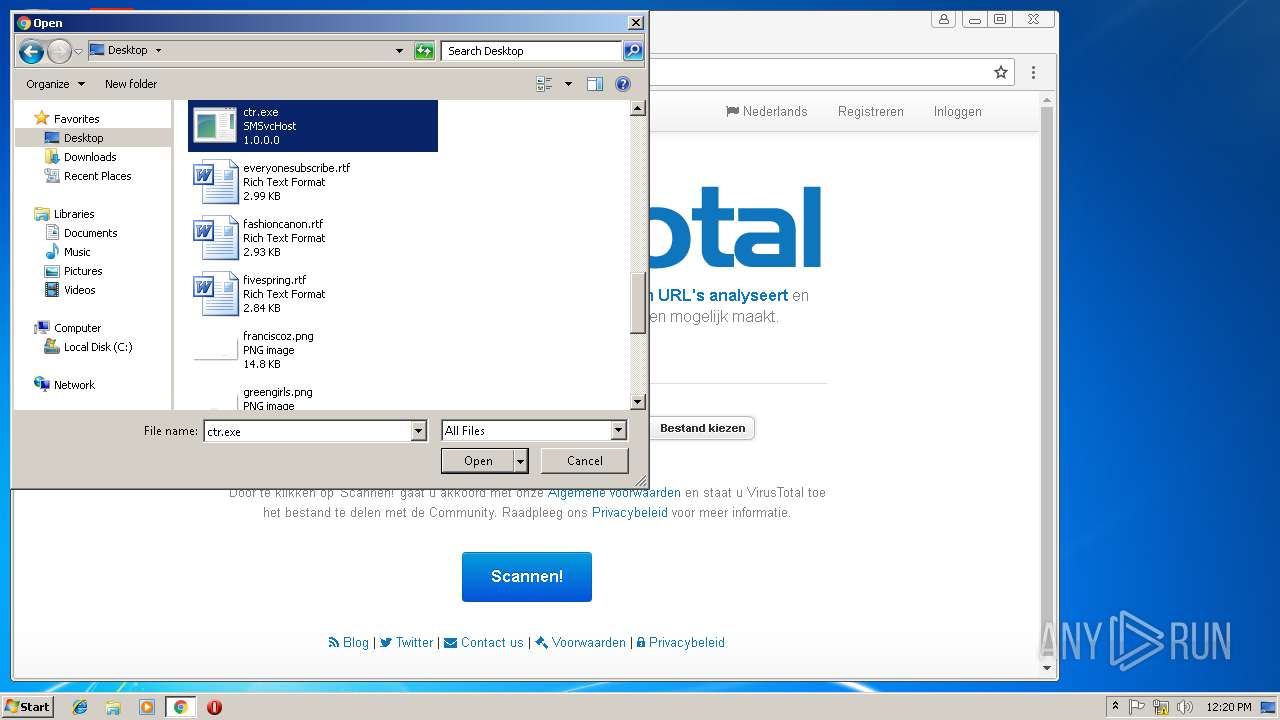
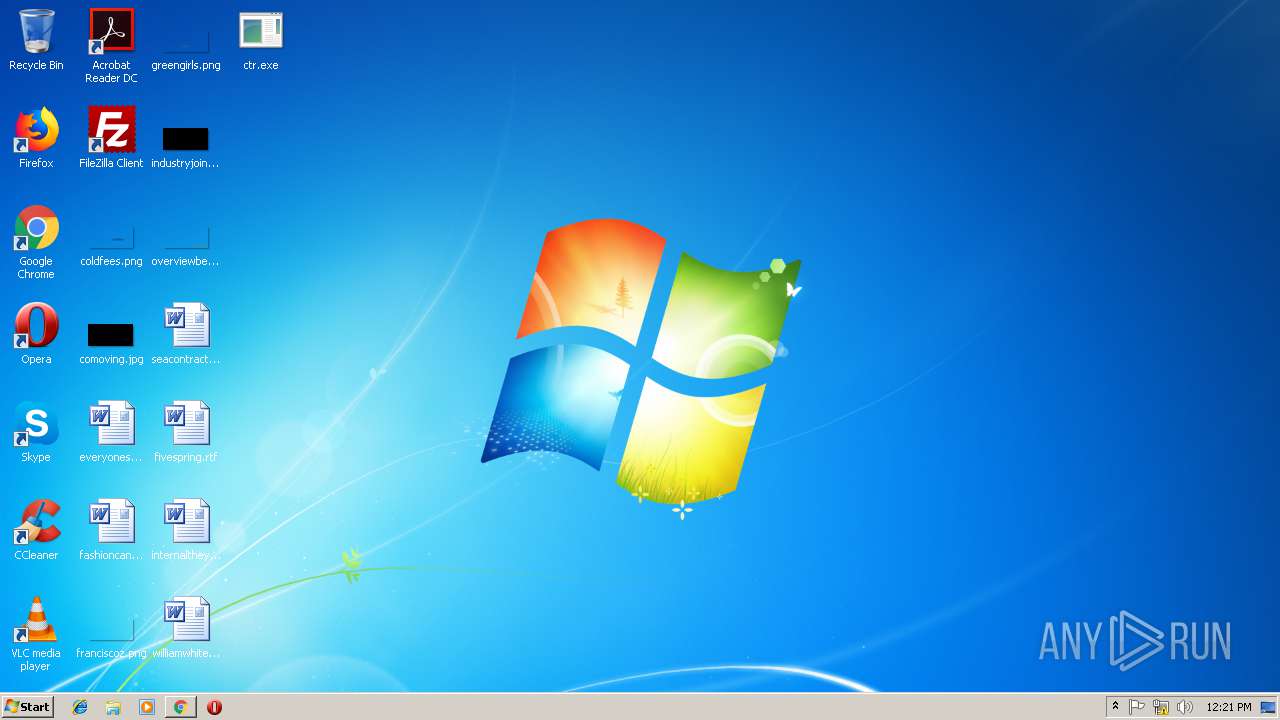
| 1028 | "C:\Users\admin\Desktop\ctr.exe" | C:\Users\admin\Desktop\ctr.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: SMSvcHost Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,8422805637082179802,10775811641080249010,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=569E4A56E561E62DFB313C7C1068AB47 --mojo-platform-channel-handle=3580 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x701500b0,0x701500c0,0x701500cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,8422805637082179802,10775811641080249010,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=CD658F54605C58203A73E2D847770AEA --mojo-platform-channel-handle=3800 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,8422805637082179802,10775811641080249010,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=402CE9C77501B2C194BDC5C42C69F73D --mojo-platform-channel-handle=1028 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2780 | "C:\Users\admin\Desktop\ctr.exe" | C:\Users\admin\Desktop\ctr.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: SMSvcHost Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
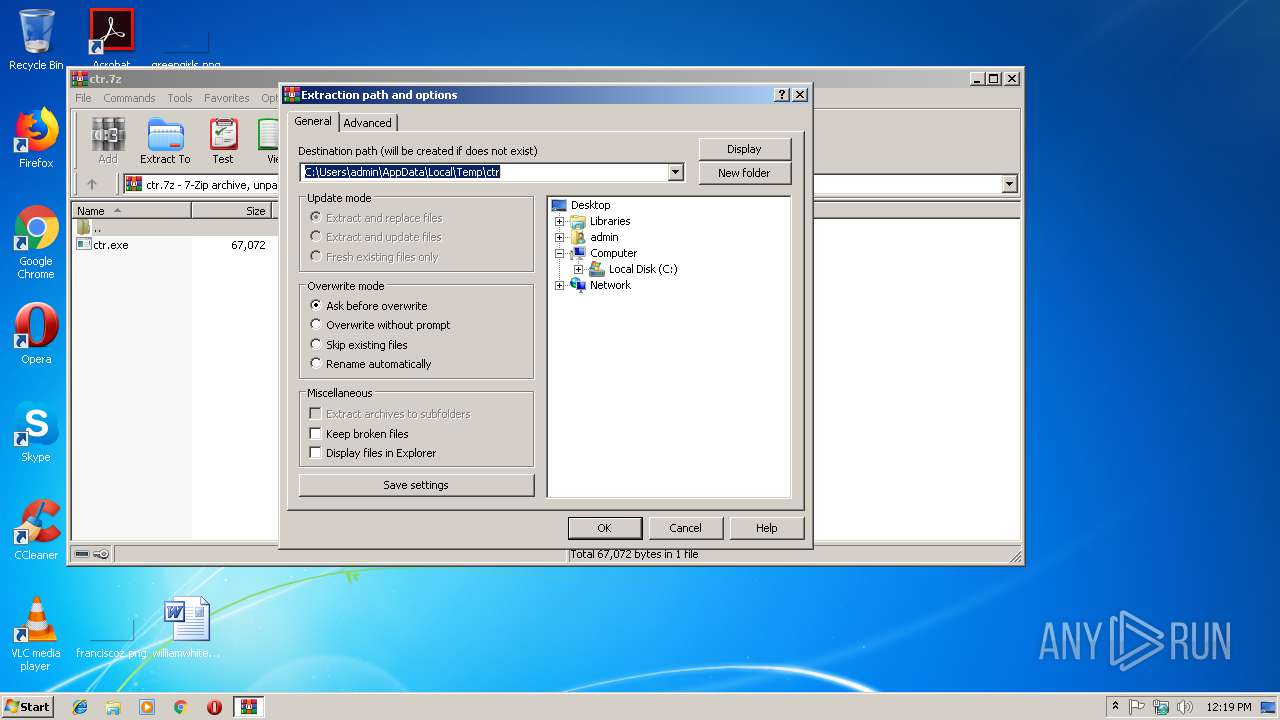
| 2980 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\ctr.7z" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,8422805637082179802,10775811641080249010,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=001D537CD85B2D6A7F0187FA00FE68AF --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=001D537CD85B2D6A7F0187FA00FE68AF --renderer-client-id=8 --mojo-platform-channel-handle=3852 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,8422805637082179802,10775811641080249010,131072 --enable-features=PasswordImport --service-pipe-token=8E8DAB089E60631FBFB4097EA1DBDC89 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8E8DAB089E60631FBFB4097EA1DBDC89 --renderer-client-id=5 --mojo-platform-channel-handle=1900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 523
Read events
1 359
Write events
159
Delete events
5
Modification events
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ctr.7z | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
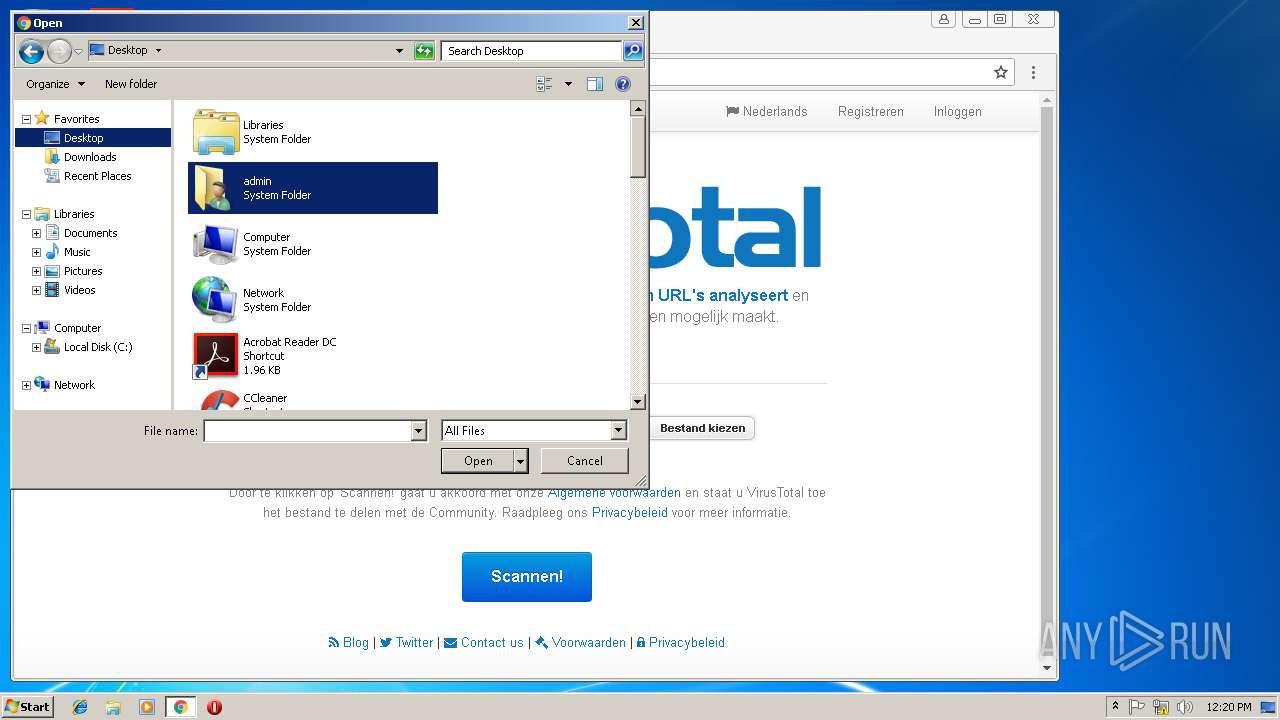
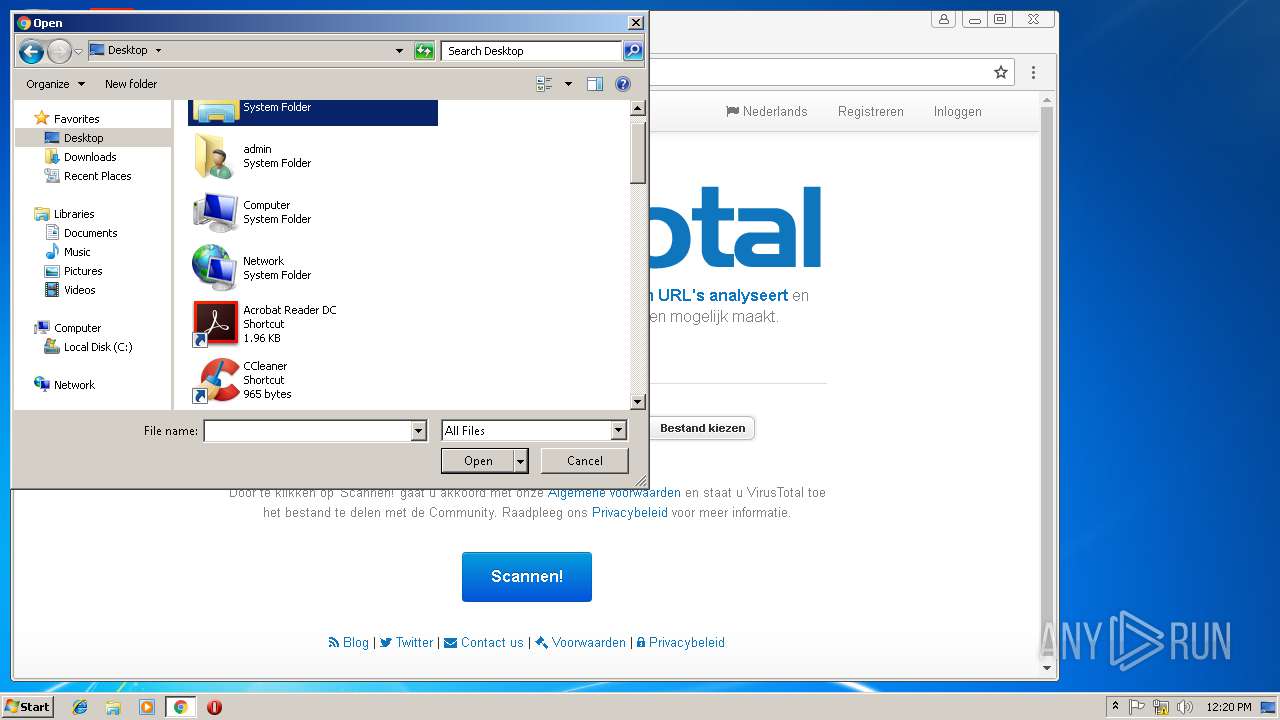
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2980) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
1
Suspicious files
70
Text files
96
Unknown types
1
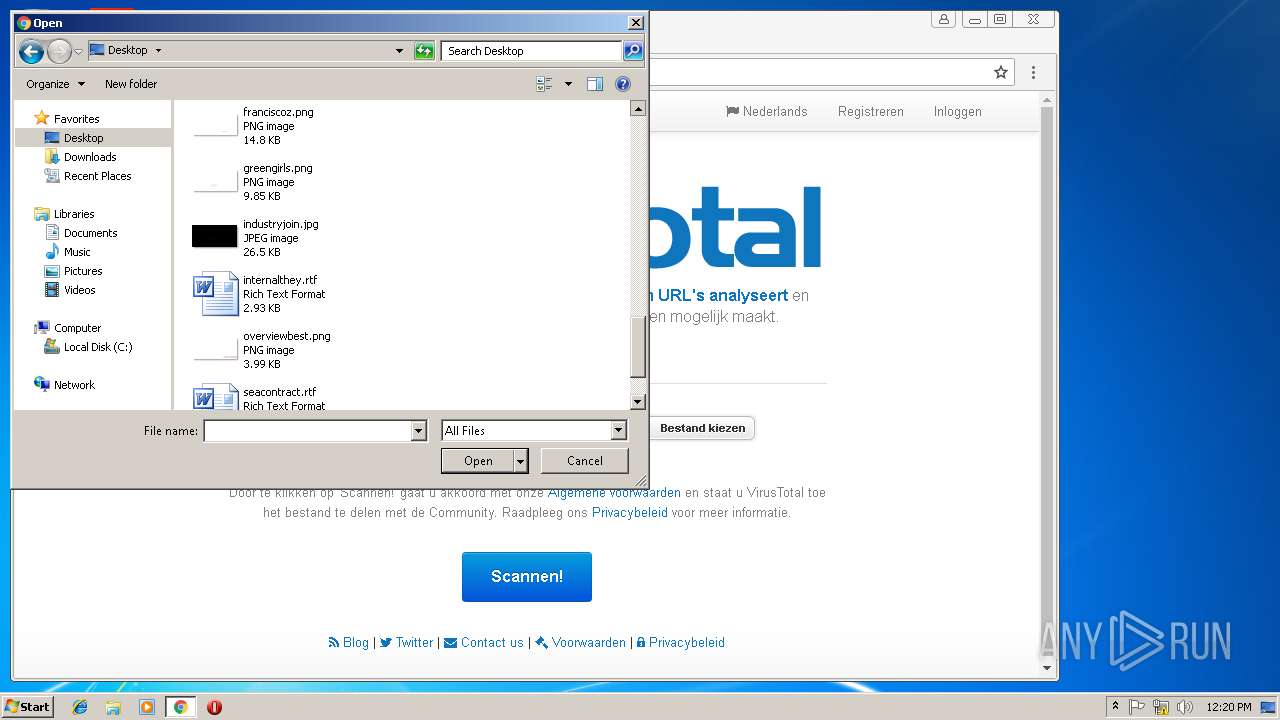
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\22f7c8e8-6648-462f-85ce-3dd02c3be9d4.tmp | — | |
MD5:— | SHA256:— | |||
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a64d3e6a-63ab-48d6-a52f-d9bf08772c89.tmp | — | |
MD5:— | SHA256:— | |||
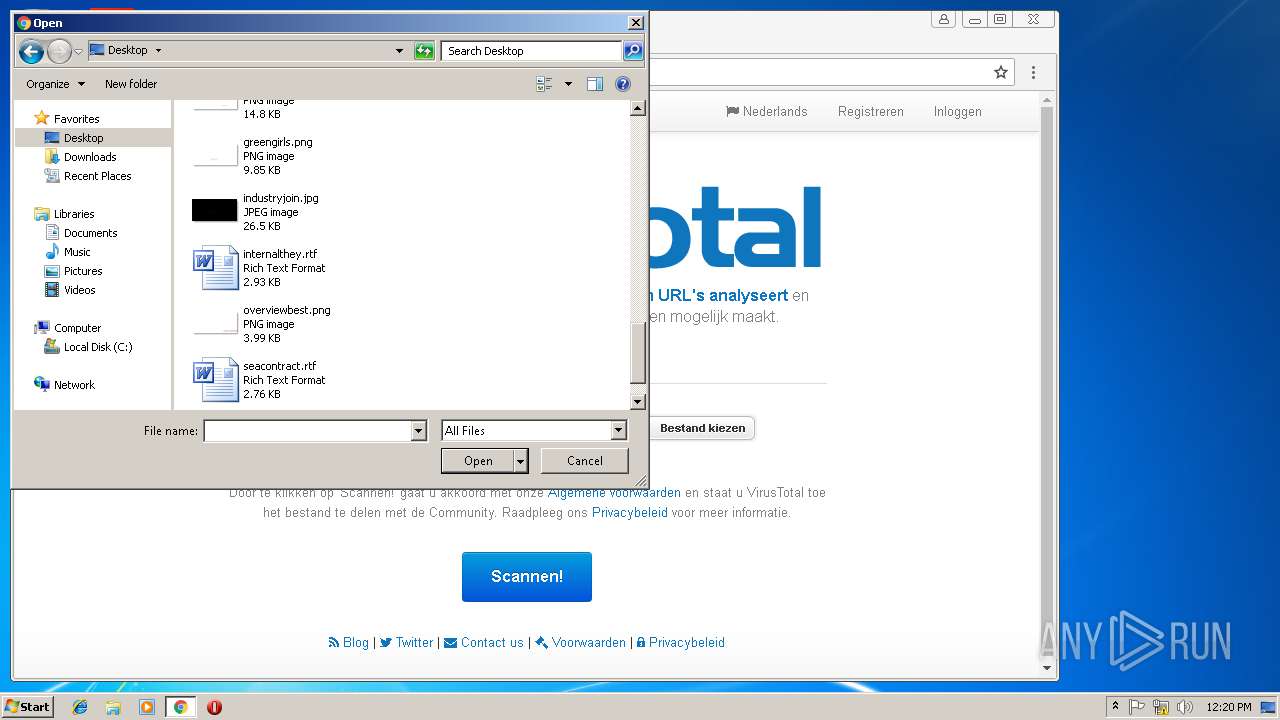
| 2980 | WinRAR.exe | C:\Users\admin\Desktop\ctr.exe | executable | |
MD5:— | SHA256:— | |||
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF215090.TMP | text | |
MD5:— | SHA256:— | |||
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old~RF215071.TMP | text | |
MD5:— | SHA256:— | |||
| 3344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
34
DNS requests
22
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2780 | ctr.exe | CONNECT | — | 10.24.126.176:8080 | http://10.24.126.176:808084.38.133.22:53 | unknown | — | — | unknown |
1028 | ctr.exe | CONNECT | — | 10.24.126.176:8080 | http://10.24.126.176:808084.38.133.22:53 | unknown | — | — | unknown |
1028 | ctr.exe | CONNECT | — | 10.24.126.176:8080 | http://10.24.126.176:808084.38.133.22:53 | unknown | — | — | unknown |
1028 | ctr.exe | CONNECT | — | 10.24.126.176:8080 | http://10.24.126.176:808084.38.133.22:53 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
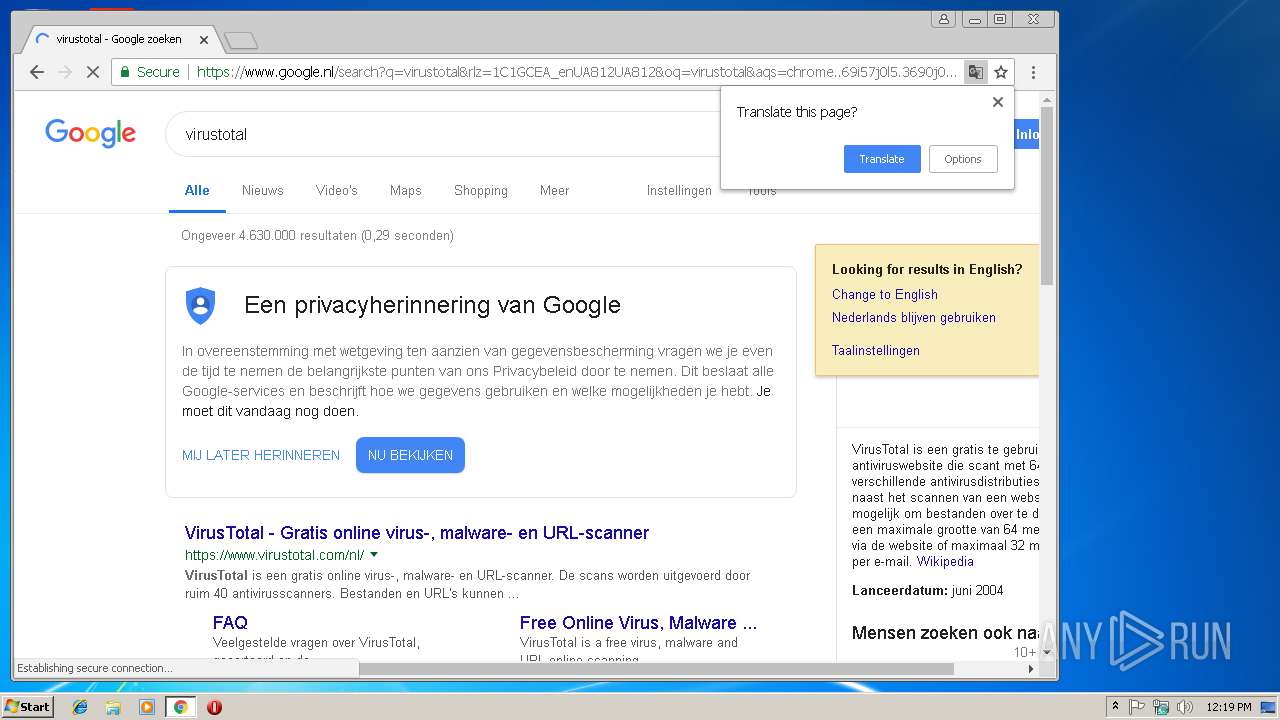
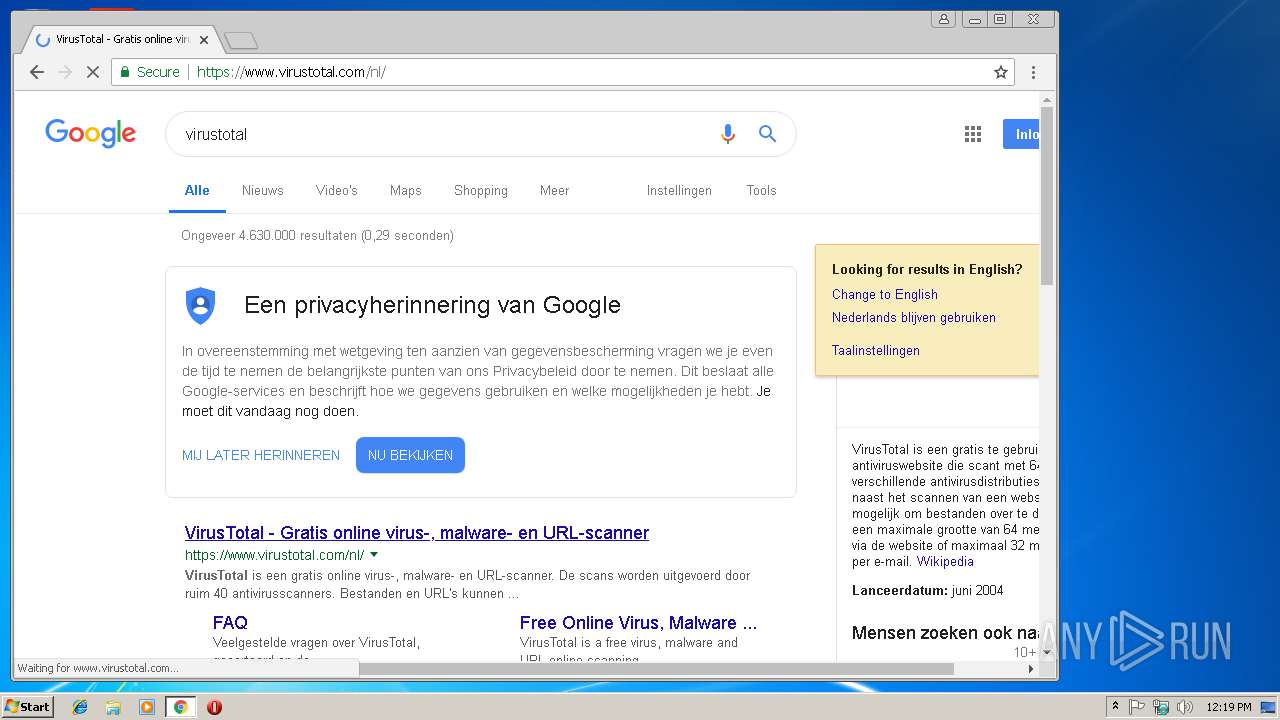
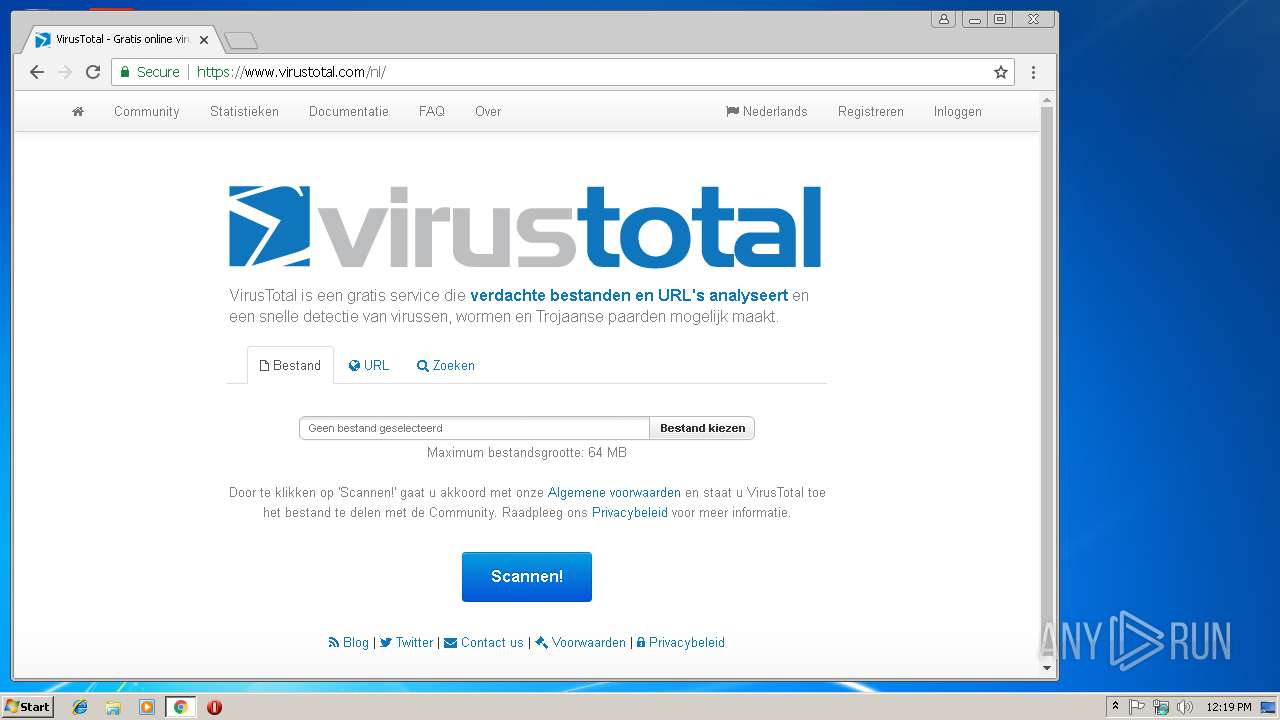
3344 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3344 | chrome.exe | 172.217.22.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3344 | chrome.exe | 216.58.207.46:443 | apis.google.com | Google Inc. | US | whitelisted |
3344 | chrome.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
3344 | chrome.exe | 172.217.18.3:443 | www.google.nl | Google Inc. | US | whitelisted |
3344 | chrome.exe | 172.217.22.14:443 | consent.google.com | Google Inc. | US | whitelisted |
3344 | chrome.exe | 172.217.16.138:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
3344 | chrome.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3344 | chrome.exe | 172.217.22.34:443 | adservice.google.nl | Google Inc. | US | whitelisted |
3344 | chrome.exe | 216.58.205.234:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.nl |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2780 | ctr.exe | Generic Protocol Command Decode | SURICATA HTTP missing Host header |