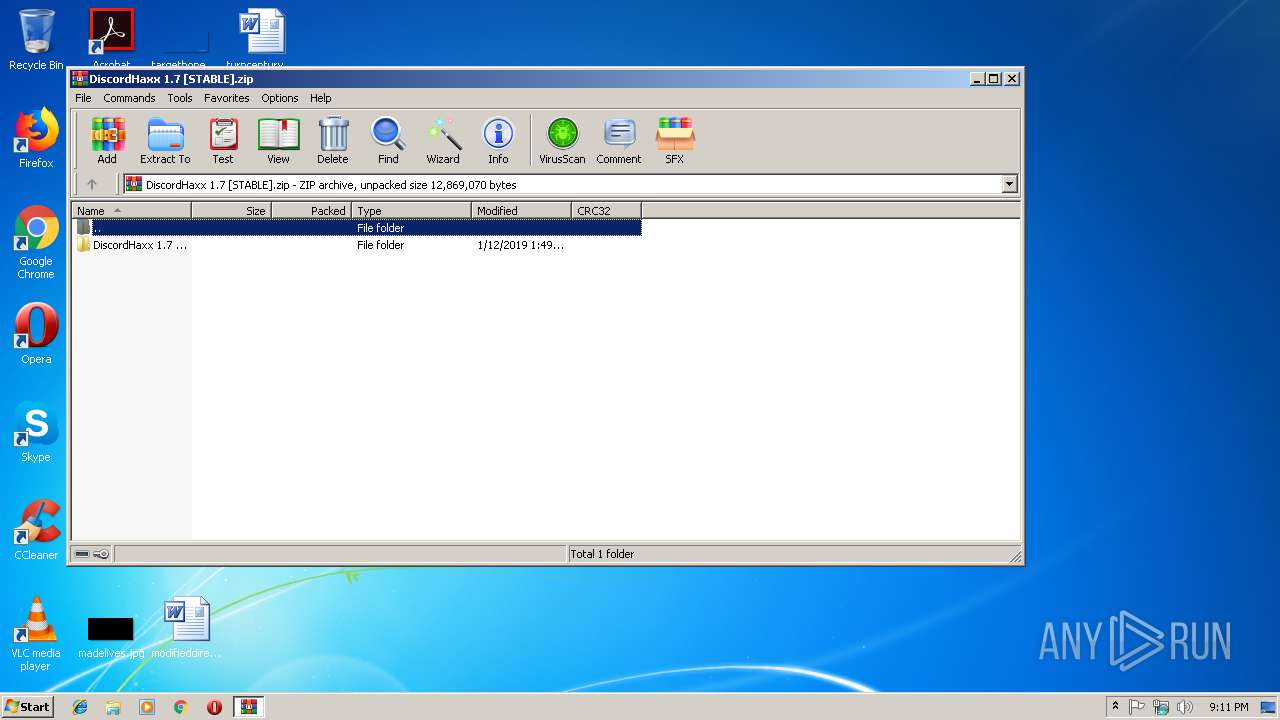
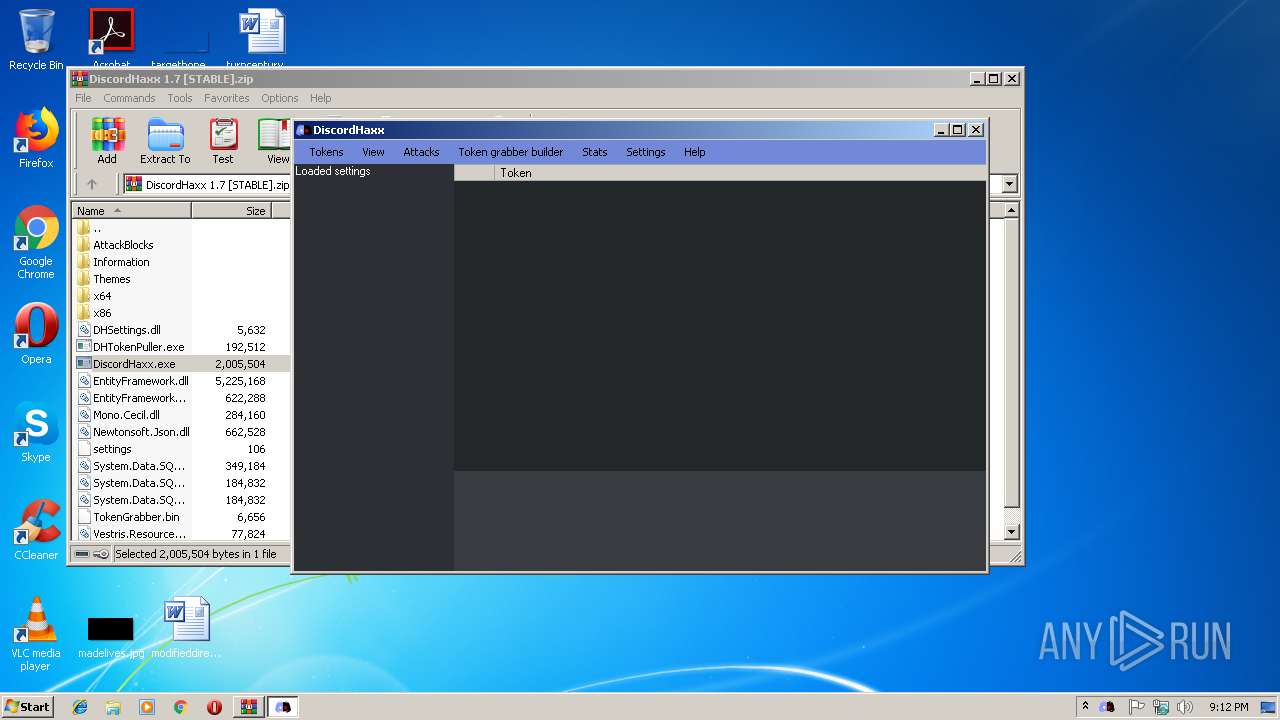
| File name: | DiscordHaxx 1.7 [STABLE].zip |
| Full analysis: | https://app.any.run/tasks/ee1ca949-e6fe-452a-85a4-0ae44180af61 |
| Verdict: | Malicious activity |
| Analysis date: | January 30, 2019, 21:11:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 04177571A30D2E98DABB656C2FB6BBA9 |
| SHA1: | 6496F1F684D3A92EC29D5FC008C628520F39789D |
| SHA256: | FFC74C87BEAA2405BF892B22D92907B17DCCF40A240DCB4C72D24A108D718DE5 |
| SSDEEP: | 98304:1wDQH+R7dEN9A3oFwEhzhnrddURitafQSM9QuLRZYlRot/R+TVj2yP5EOHyh1nau:ODx5dEN9conPnrrTSqQG3YlOt/4TF2Ye |
MALICIOUS
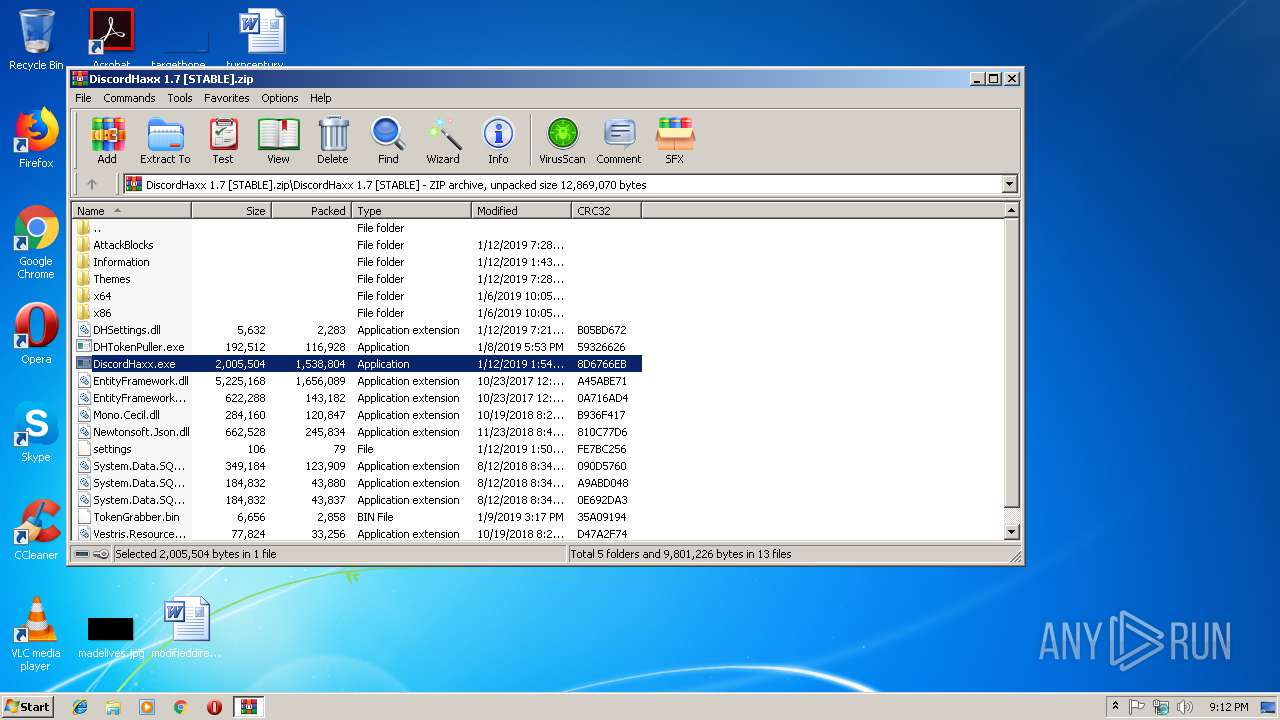
Loads dropped or rewritten executable
- DiscordHaxx.exe (PID: 4000)
Application was dropped or rewritten from another process
- DHTokenPuller.exe (PID: 2620)
- DiscordHaxx.exe (PID: 4000)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3100)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
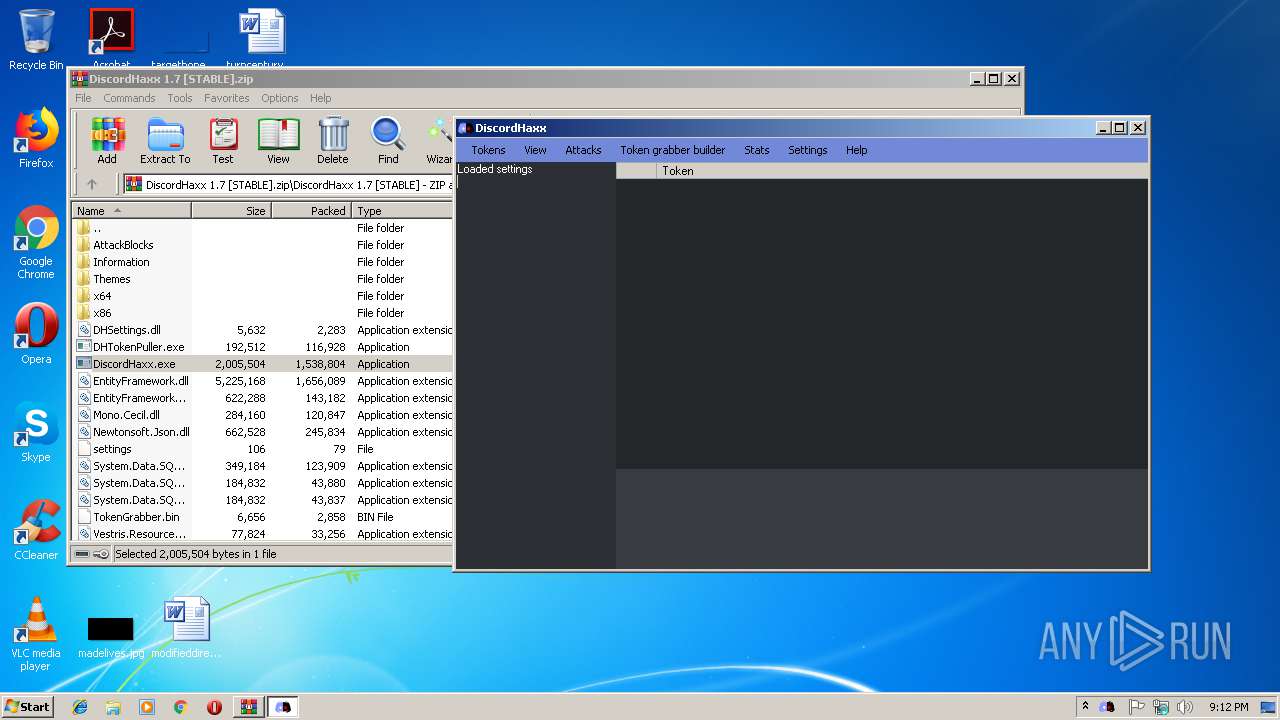
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:01:12 14:49:22 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | DiscordHaxx 1.7 [STABLE]/ |
Total processes
33
Monitored processes
3
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
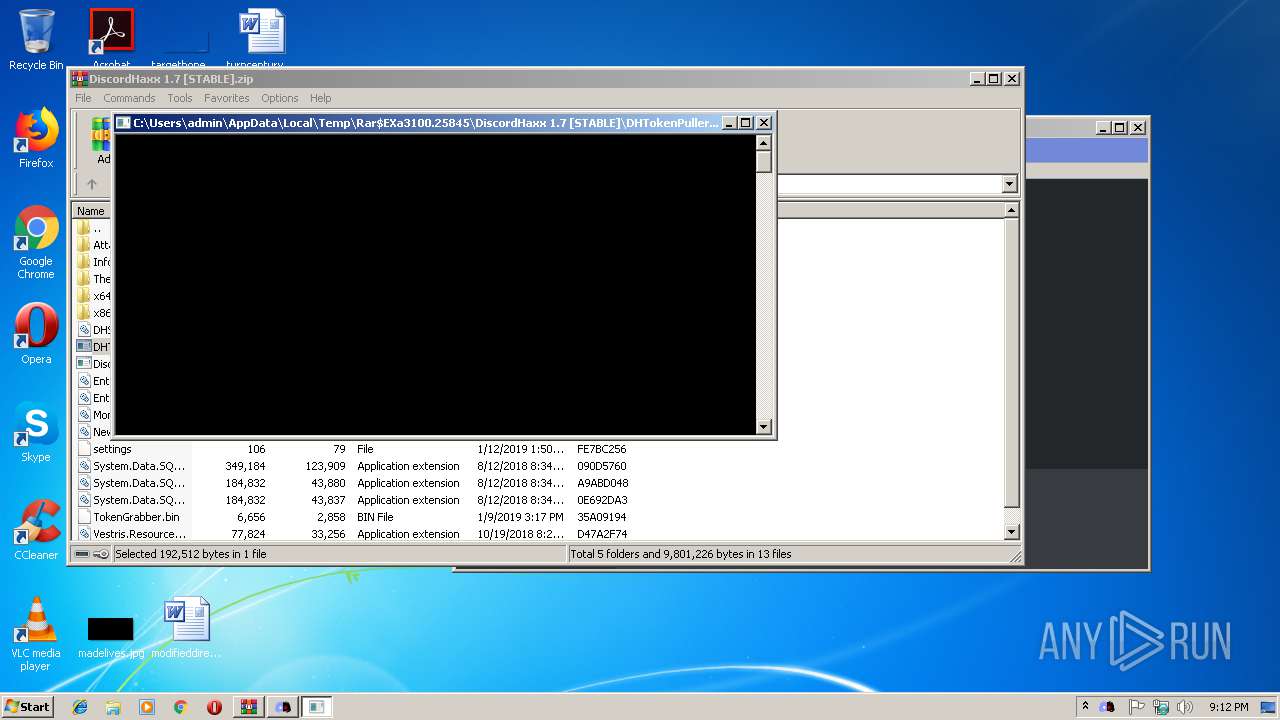
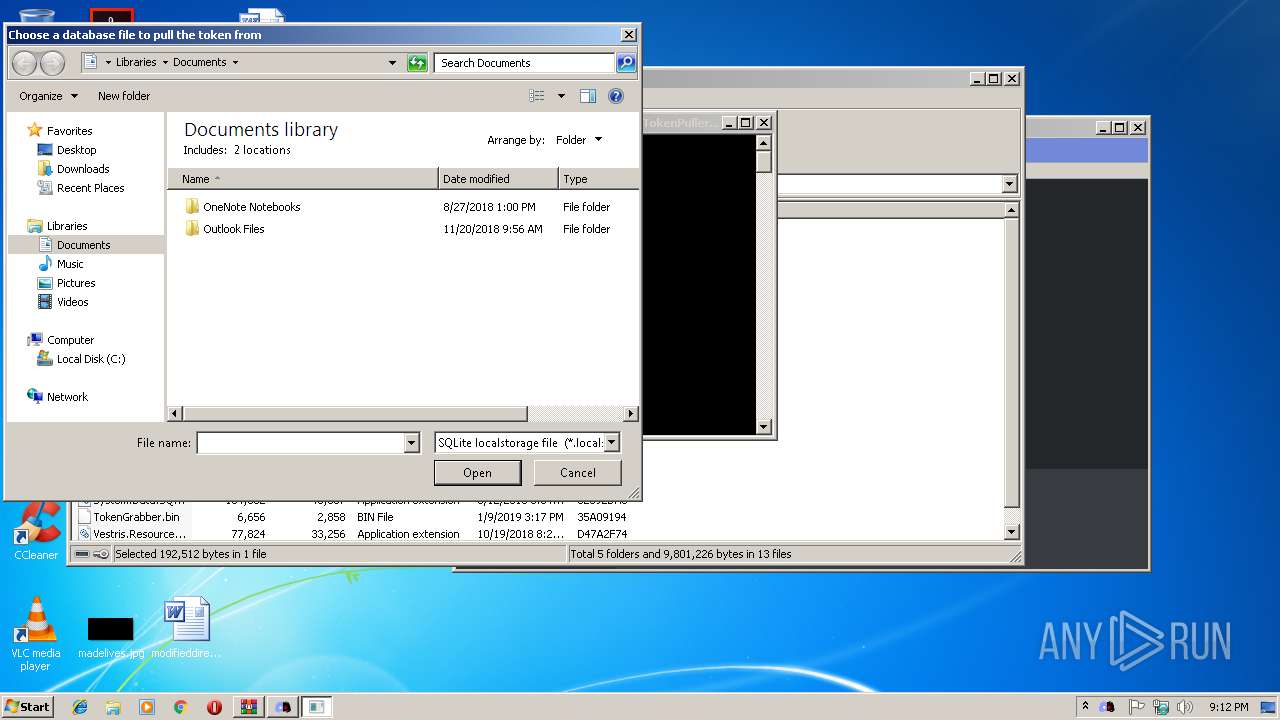
| 2620 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.25845\DiscordHaxx 1.7 [STABLE]\DHTokenPuller.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.25845\DiscordHaxx 1.7 [STABLE]\DHTokenPuller.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DHTokenPuller Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3100 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\DiscordHaxx 1.7 [STABLE].zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 4000 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.23731\DiscordHaxx 1.7 [STABLE]\DiscordHaxx.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.23731\DiscordHaxx 1.7 [STABLE]\DiscordHaxx.exe | WinRAR.exe | ||||||||||||
User: admin Company: iLinked Software Integrity Level: MEDIUM Description: DiscordHaxx Exit code: 0 Version: 1.7.0.0 Modules
| |||||||||||||||
Total events
992
Read events
938
Write events
53
Delete events
1
Modification events
| (PID) Process: | (3100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3100) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\DiscordHaxx 1.7 [STABLE].zip | |||
| (PID) Process: | (3100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3100) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
28
Suspicious files
0
Text files
30
Unknown types
0
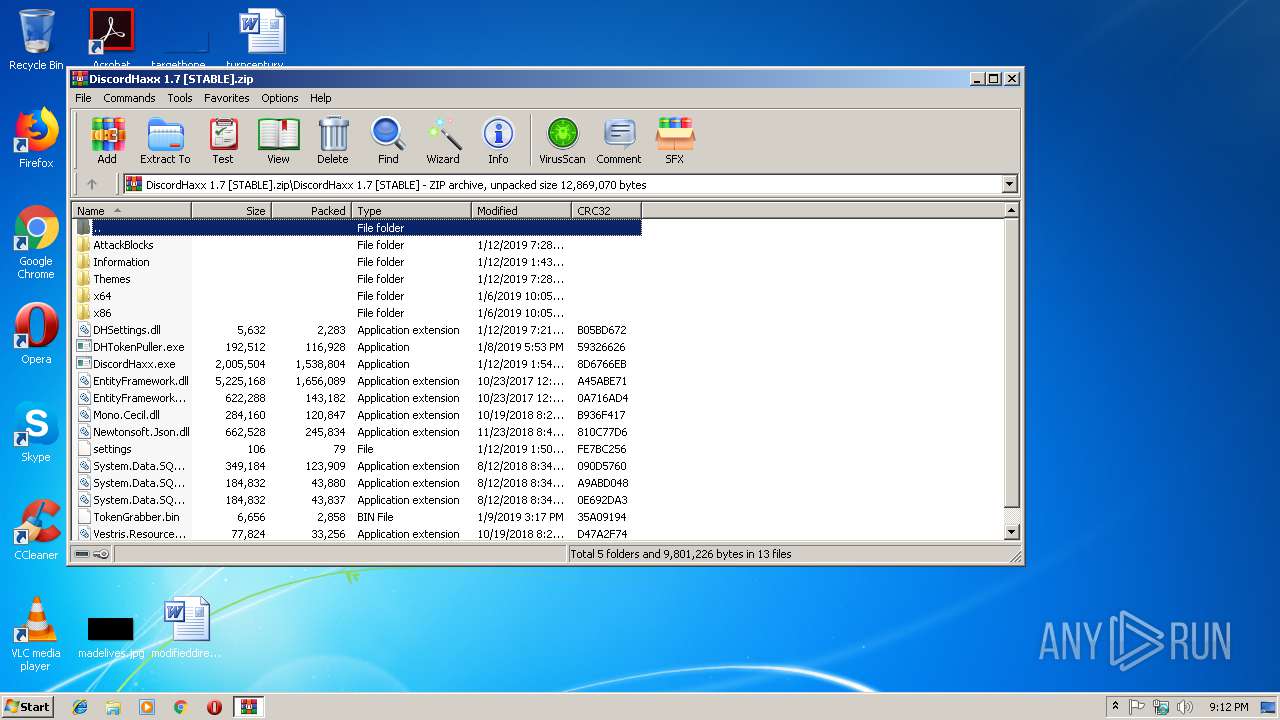
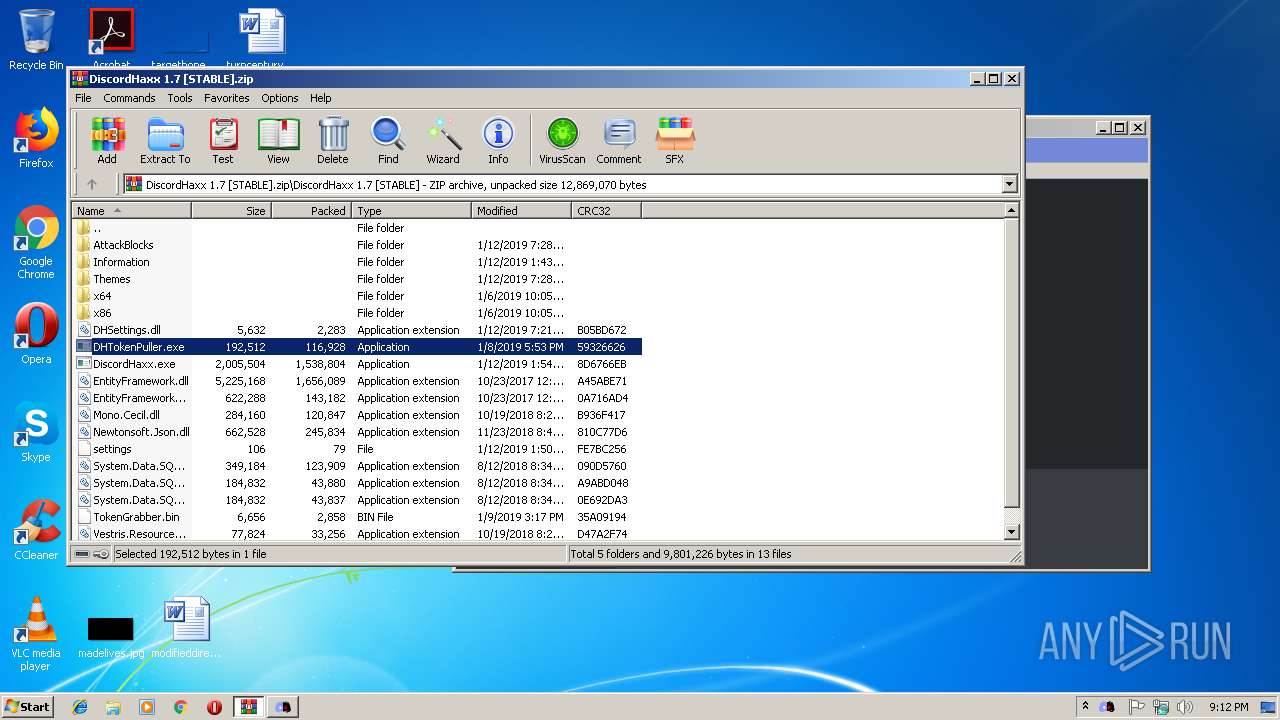
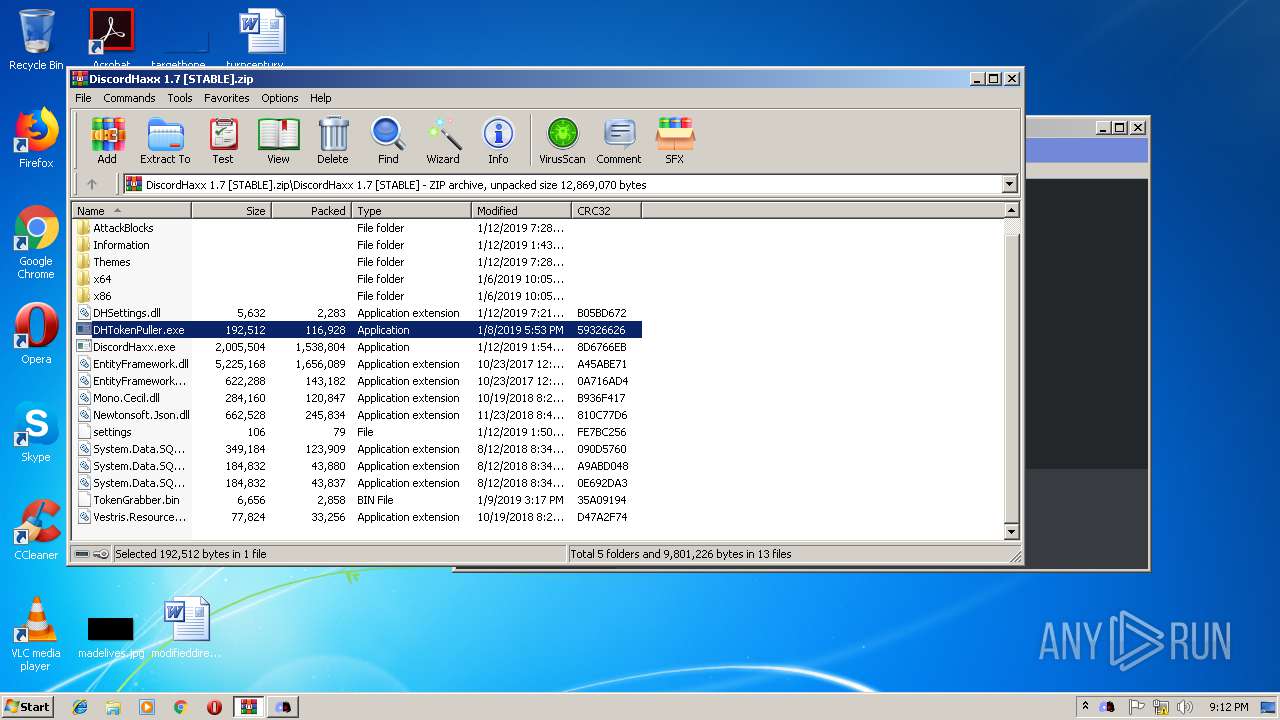
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.23731\DiscordHaxx 1.7 [STABLE]\DiscordHaxx.exe | executable | |
MD5:— | SHA256:— | |||
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.23731\DiscordHaxx 1.7 [STABLE]\DHSettings.dll | executable | |
MD5:— | SHA256:— | |||
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.23731\DiscordHaxx 1.7 [STABLE]\DHTokenPuller.exe | executable | |
MD5:— | SHA256:— | |||
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.23731\DiscordHaxx 1.7 [STABLE]\AttackBlocks\Leaver.dhb | text | |
MD5:C01676932973069181EDEC6B62EDA8F4 | SHA256:C1056D8DE27F441FC32D7598C6E558259934D7F23A32337A00943457025AD214 | |||
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.23731\DiscordHaxx 1.7 [STABLE]\AttackBlocks\Flooder.dhb | text | |
MD5:1CF8927B78F1A1D9CD09360A543E6D3F | SHA256:A8C48CC63E2C07189E39D0E5705BCD4354185F5653DD3DE637994CAED51EB708 | |||
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.23731\DiscordHaxx 1.7 [STABLE]\AttackBlocks\Reaction bomber.dhb | text | |
MD5:4AC0846853BEEBD336A6932772E48AEB | SHA256:FF719E458A4AAA37DA7C93D079F917C92247A67EE78EE6271163622BC242EAC4 | |||
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.23731\DiscordHaxx 1.7 [STABLE]\AttackBlocks\Webhook spammer.dhb | text | |
MD5:1421294A14AAE2B5364CF4BF4A22178A | SHA256:4F5D42C6597EC74D05471AD6D1CF52D12F52E850672560953D862DAF39C41F5F | |||
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.23731\DiscordHaxx 1.7 [STABLE]\EntityFramework.dll | executable | |
MD5:806D33A8300E885C3C1A00C6107AF8EB | SHA256:9C20FB2AD86A760B0C6AEBD9301C9009891D02AE14720A93926C0B535B8AD09B | |||
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.23731\DiscordHaxx 1.7 [STABLE]\settings | text | |
MD5:— | SHA256:— | |||
| 3100 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3100.23731\DiscordHaxx 1.7 [STABLE]\AttackBlocks\DM flooder.dhb | text | |
MD5:F063CC82549B5C3AE7C6CACBDFBFD74B | SHA256:62A912D265C75D4E492B753742E388A979C5B5396DADED3D58B38FC244F11779 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4000 | DiscordHaxx.exe | 104.20.209.21:443 | pastebin.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |