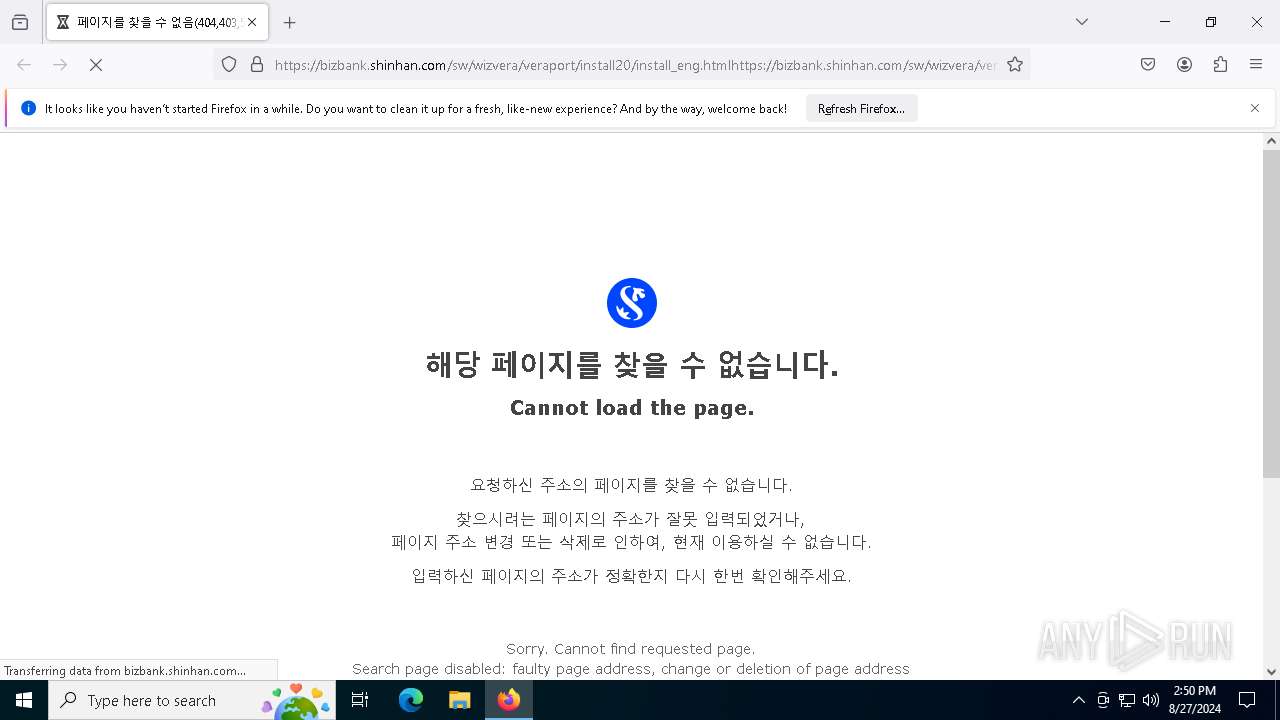
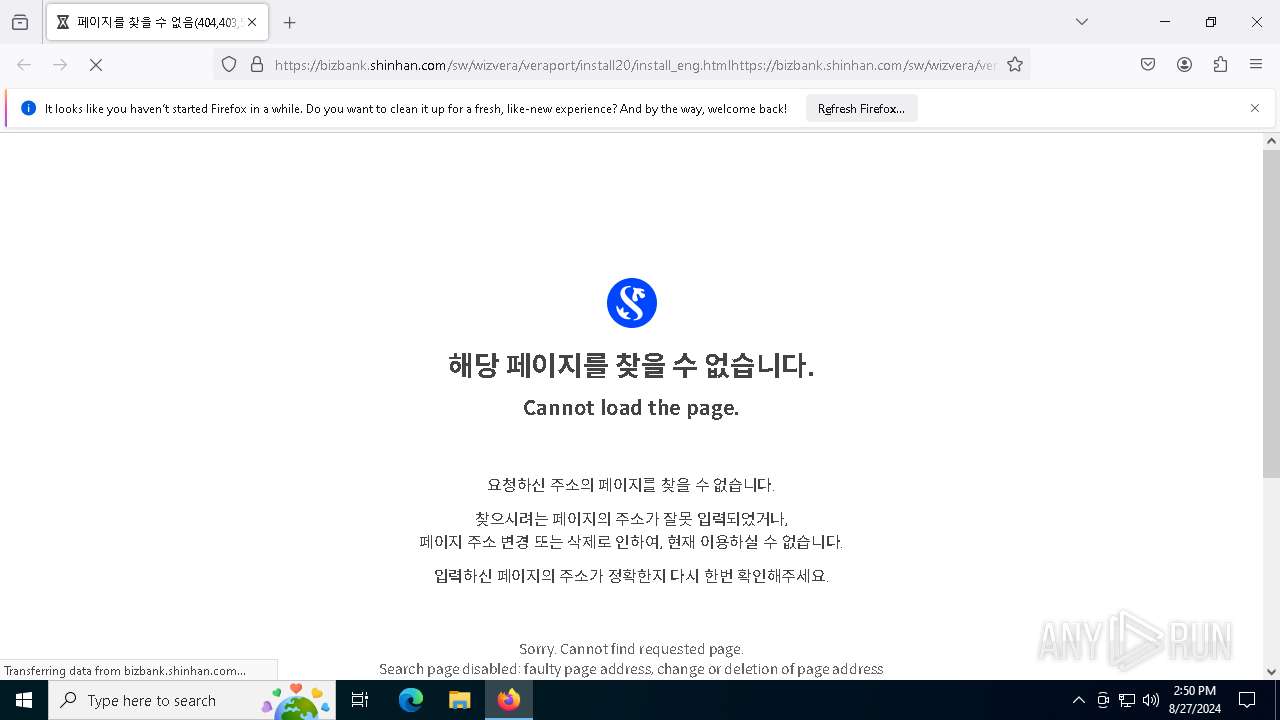
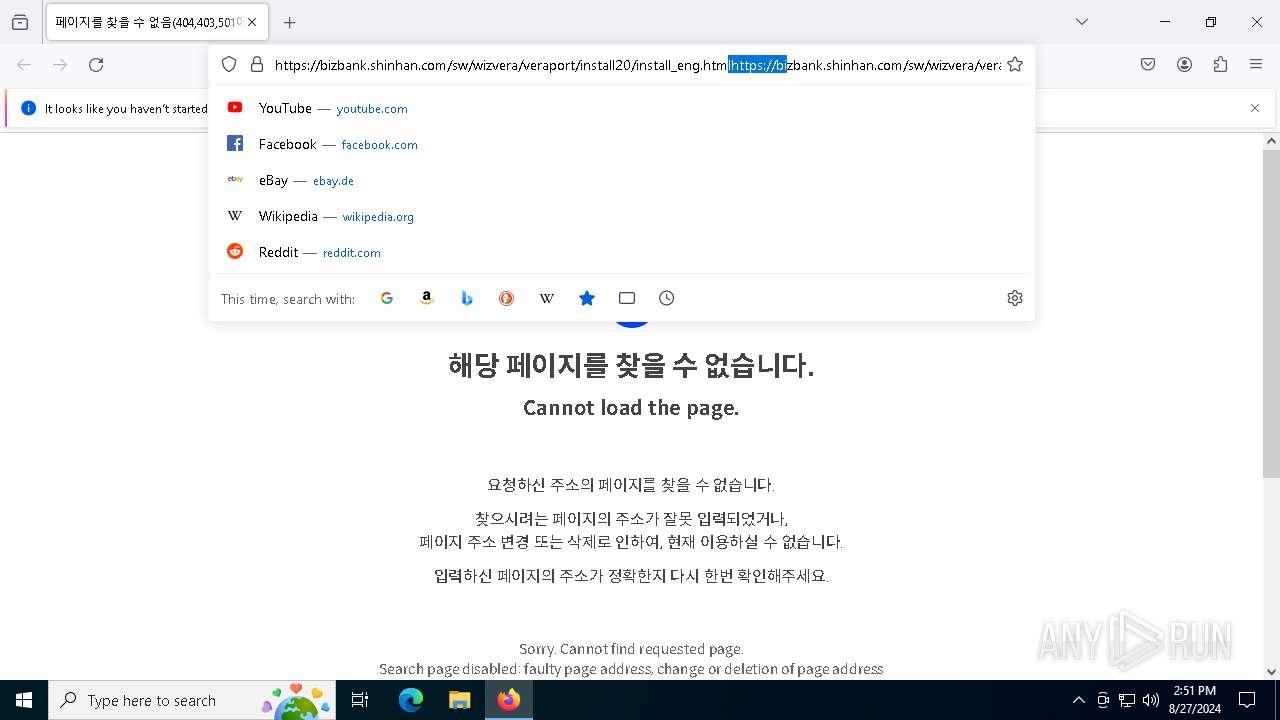
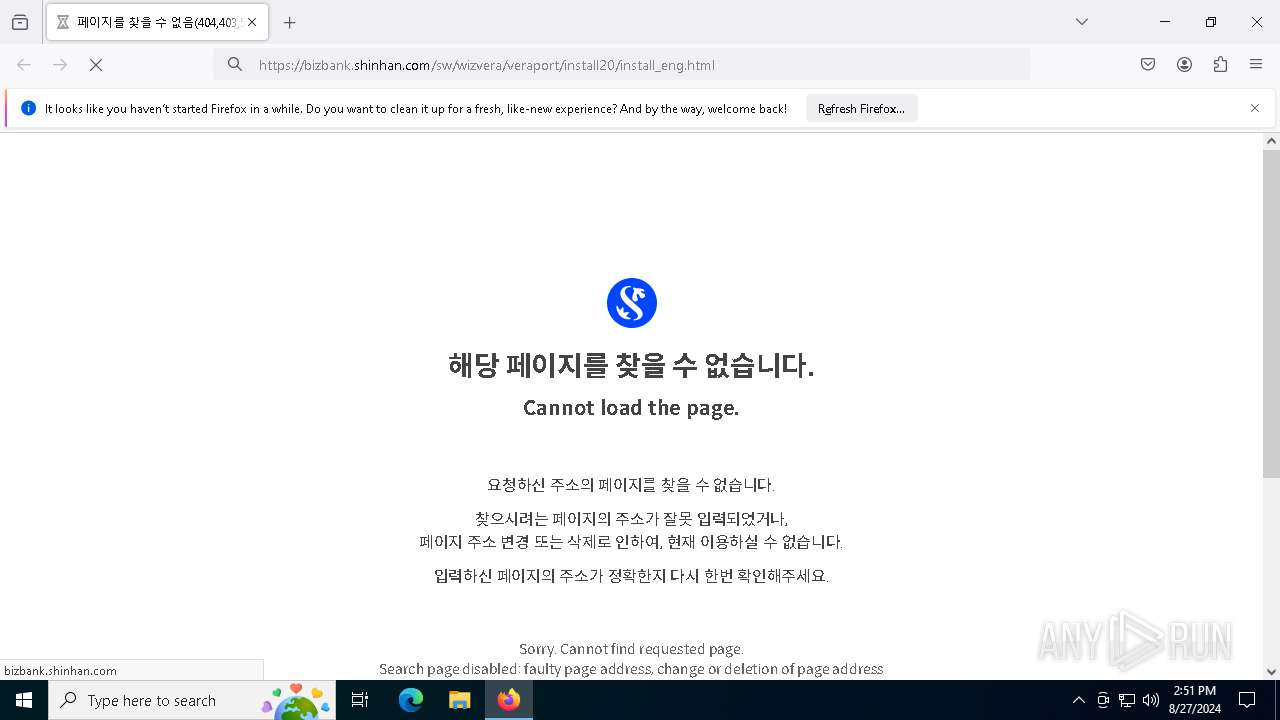
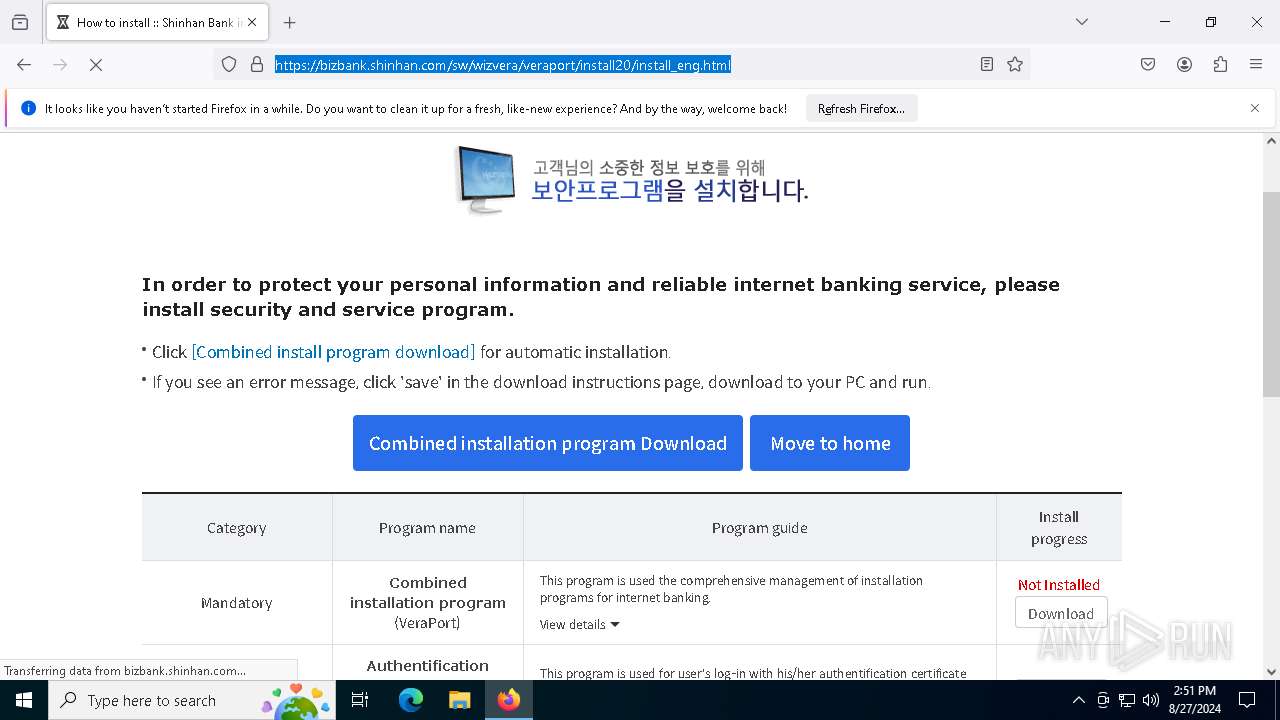
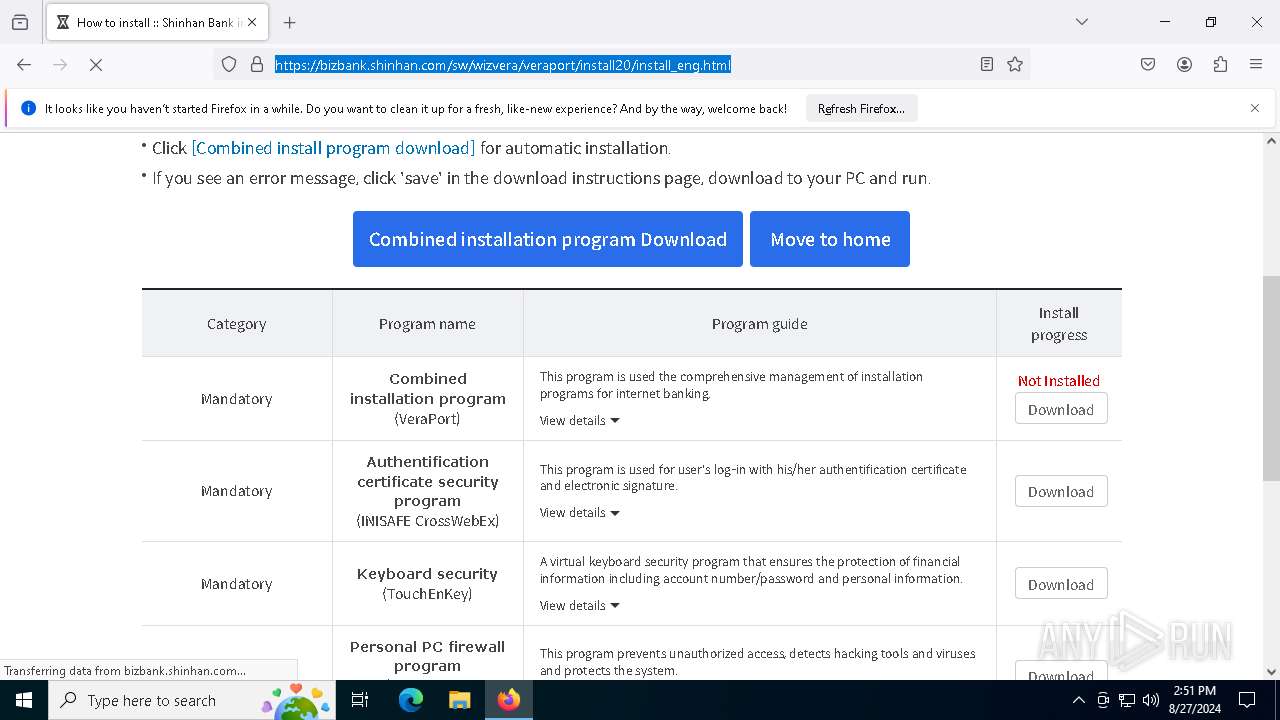
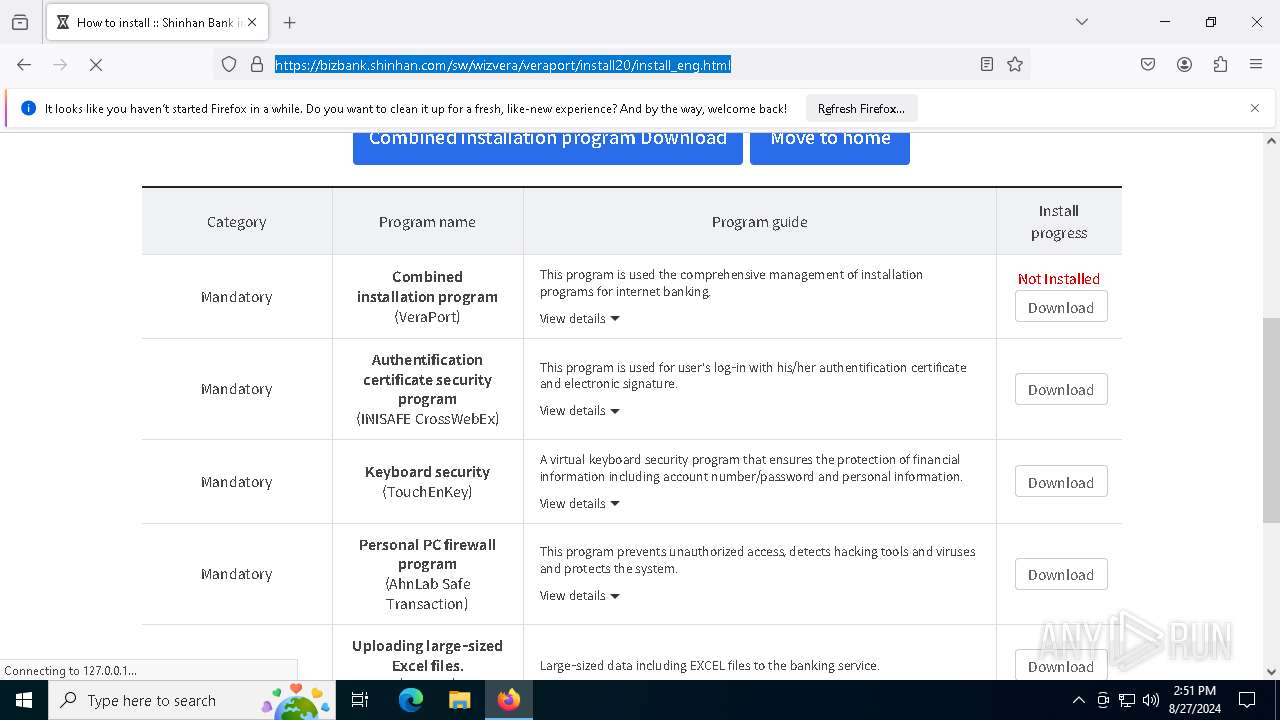
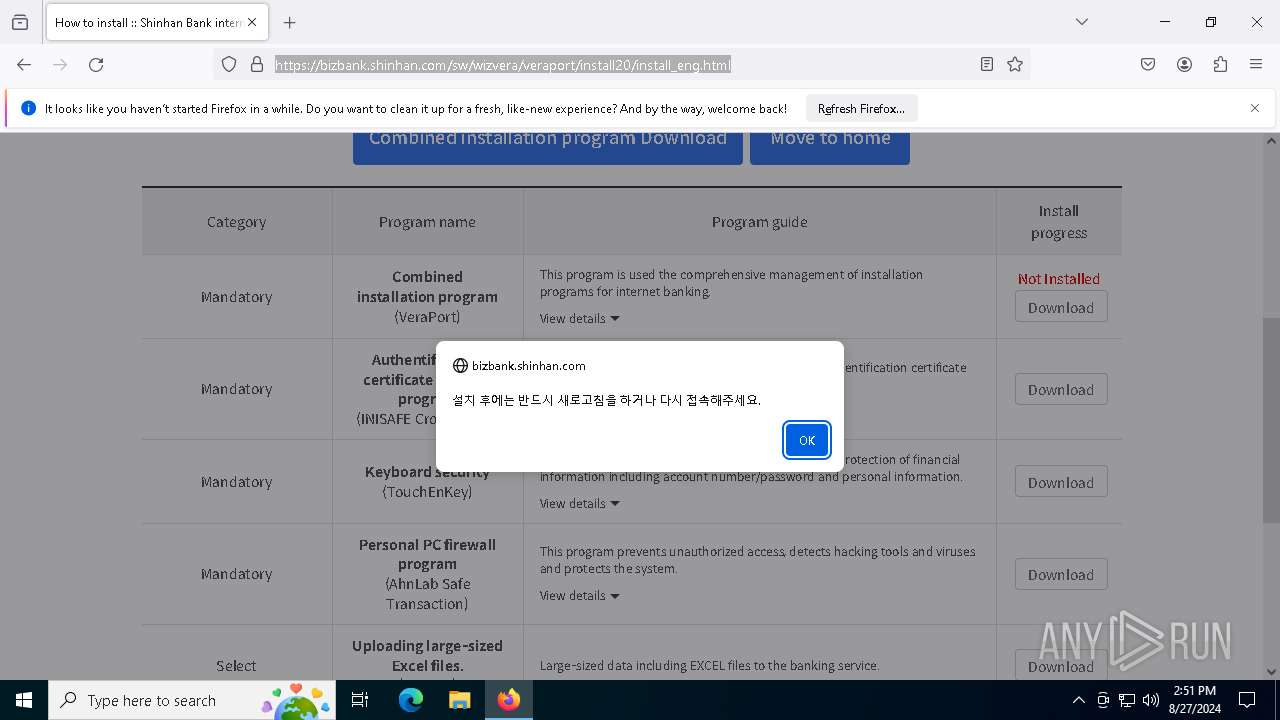
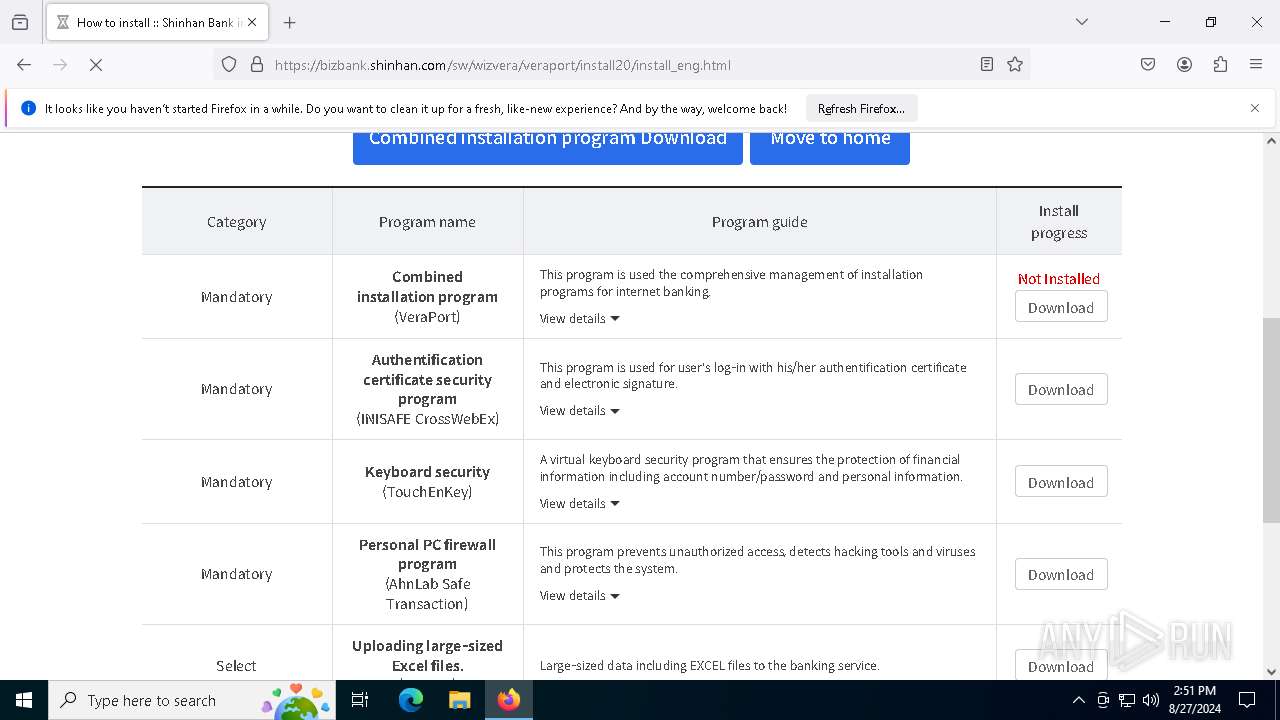
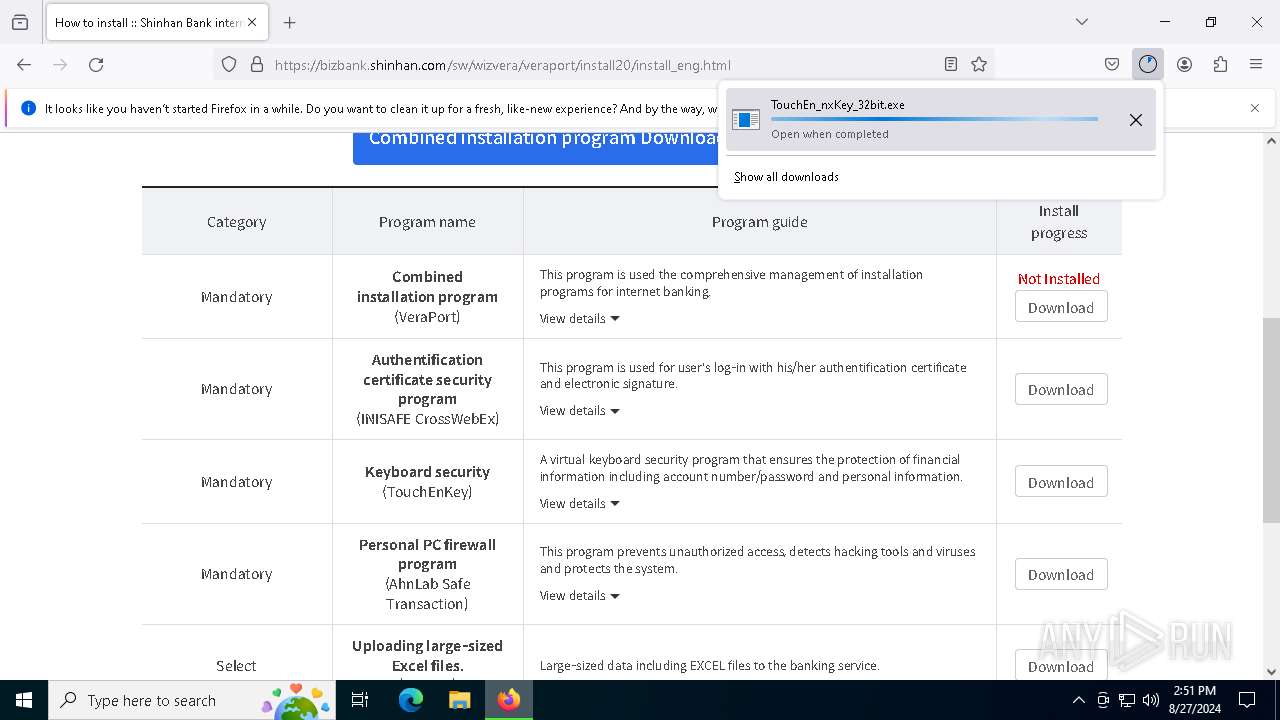
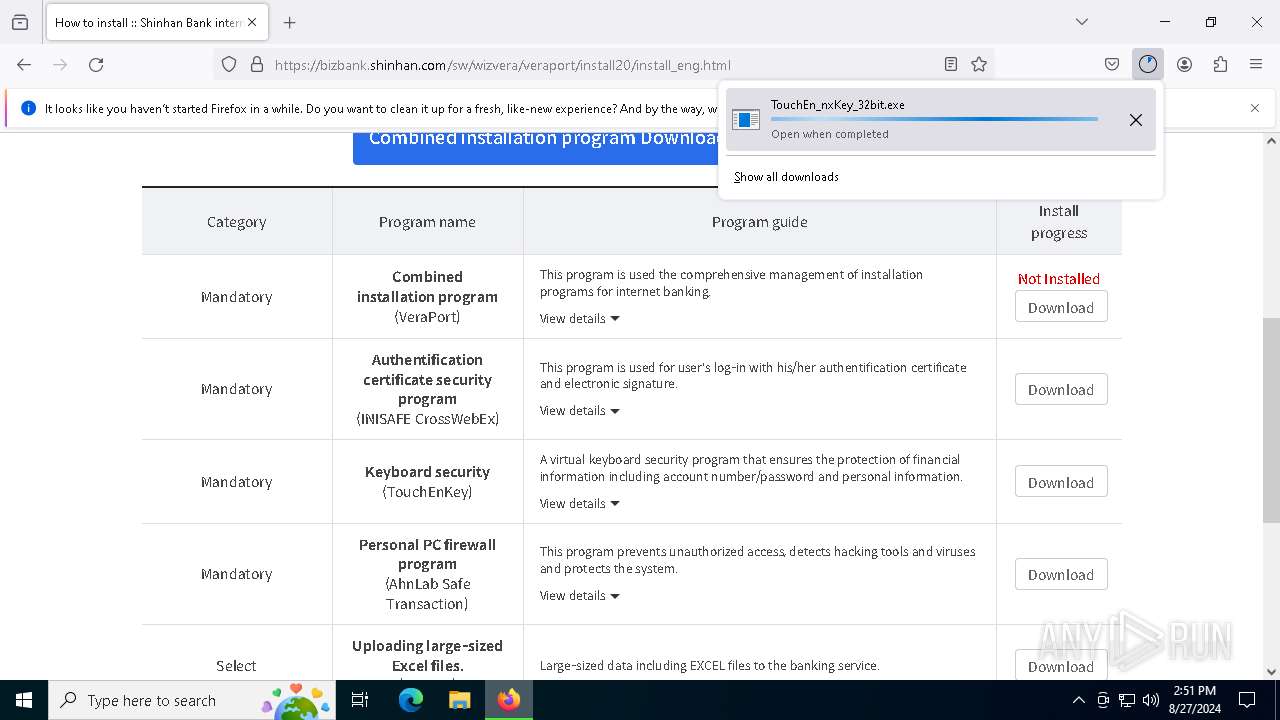
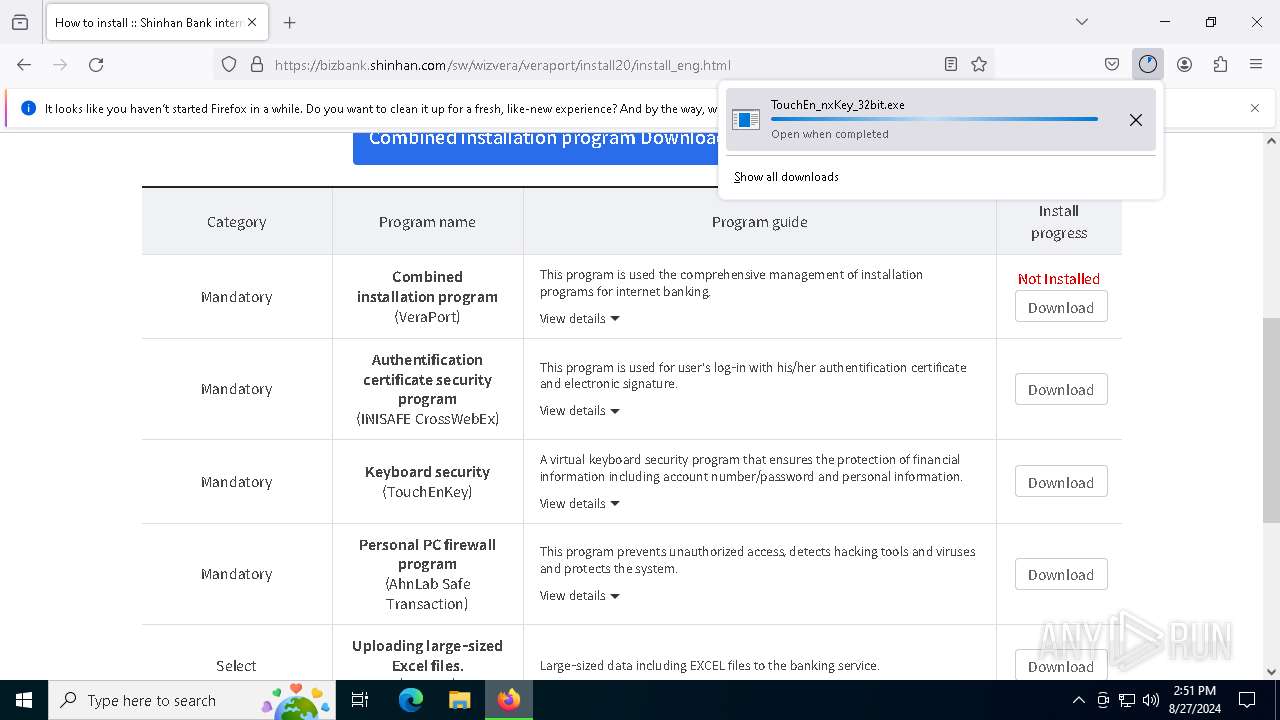
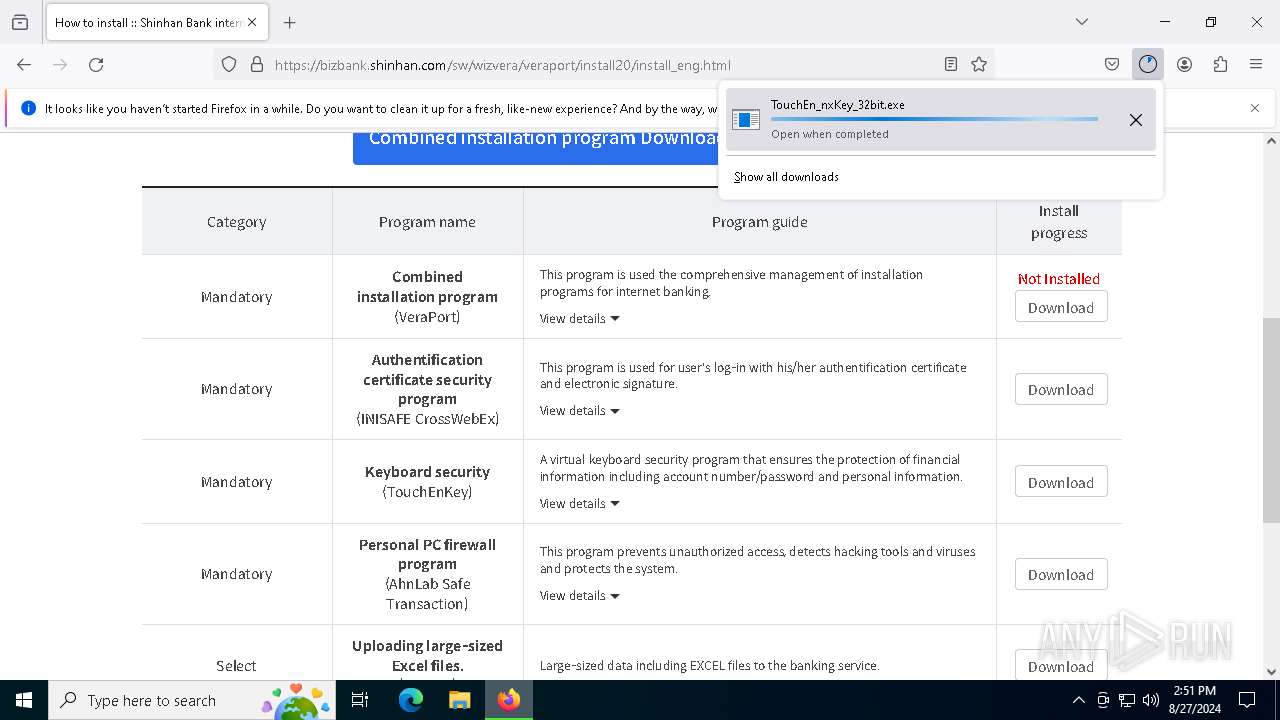
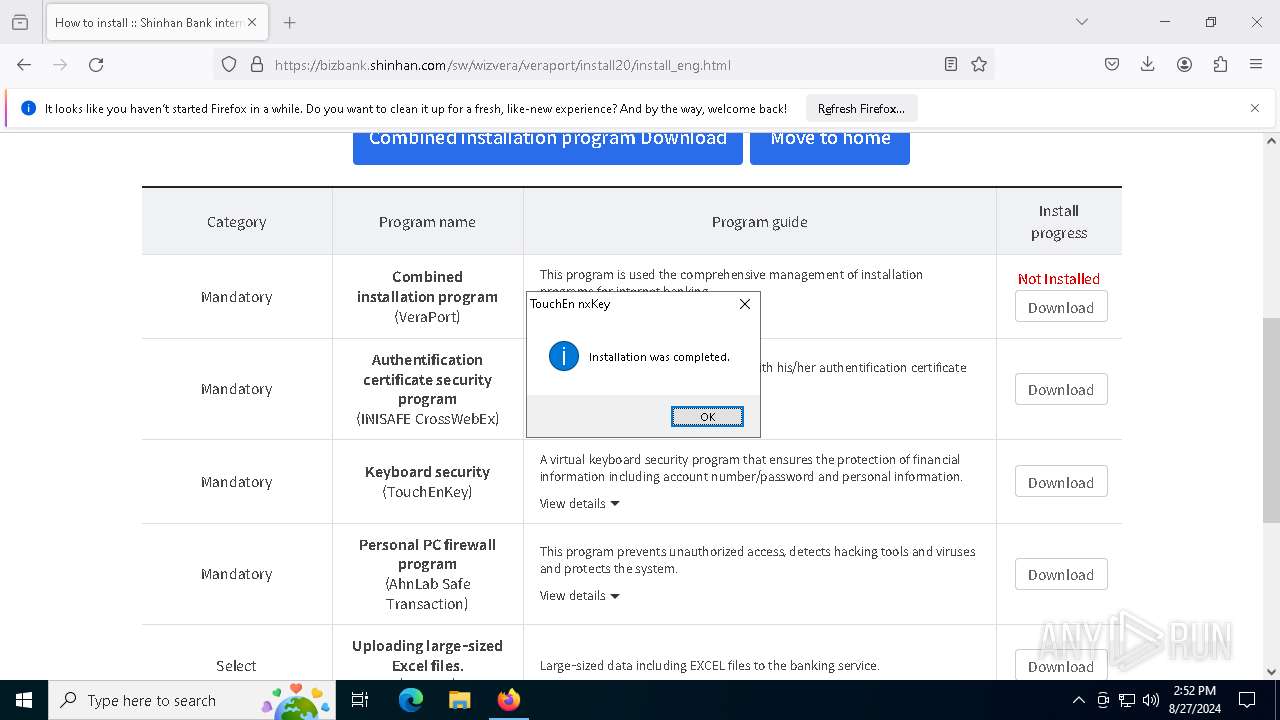
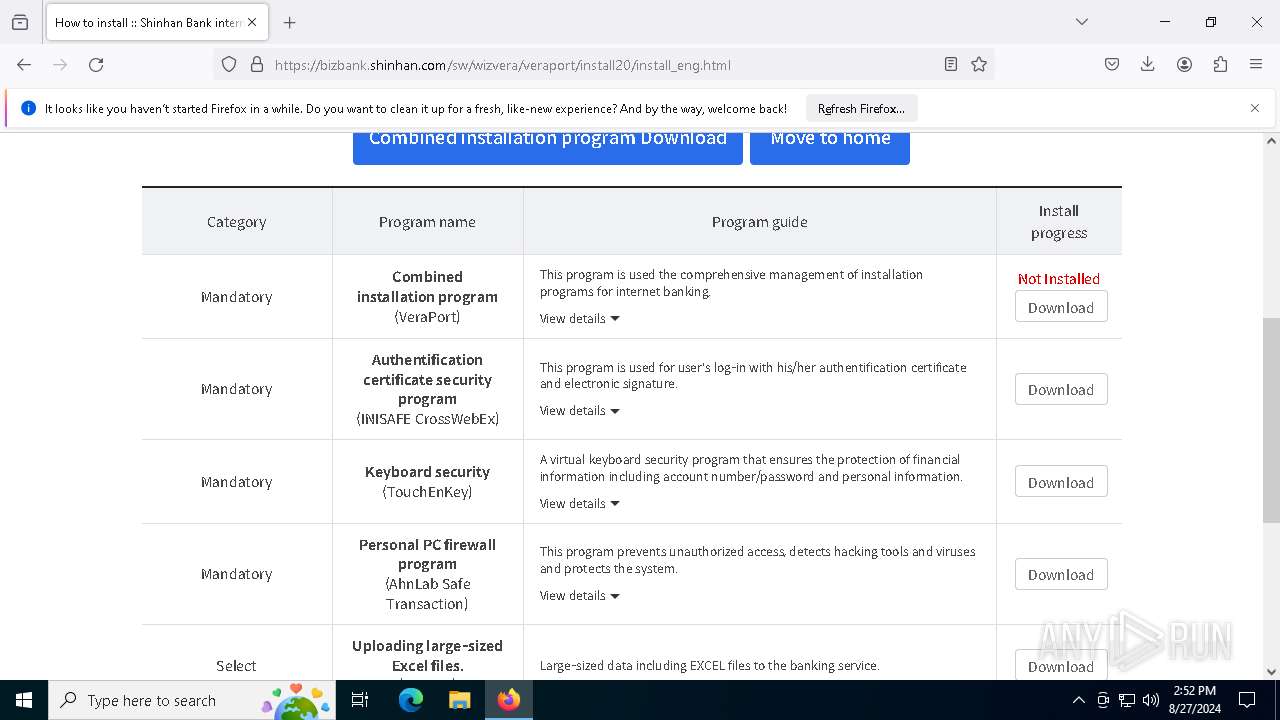
| URL: | https://bizbank.shinhan.com/sw/wizvera/veraport/install20/install_eng.htmlhttps://bizbank.shinhan.com/sw/wizvera/veraport/install20/install_eng.html |
| Full analysis: | https://app.any.run/tasks/fa0dde18-e92e-4e20-a28e-3bedcfaefdfd |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | August 27, 2024, 14:50:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F9E80F97C427AE300CAF1C1E15164280 |
| SHA1: | CF15D5C665CBC66C2FA4026BCF687B70C8F1BE29 |
| SHA256: | FFC46EF2FF480EFC799A329721FF7DF4D63ED20C07B7A13E21FC4CE3CCFBCD5D |
| SSDEEP: | 3:N8PeLNiyKIKWSKXMXYX8sZFWq0ZYRWeLNiyKIKWSKXMXYX8sZFWq0ZQ:2PeLM2KWNMoMsHV0OWeLM2KWNMoMsHVF |
MALICIOUS
Changes the autorun value in the registry
- CrossEX_LocalService_Install.exe (PID: 6180)
Actions looks like stealing of personal data
- Firefox_CertUtil.exe (PID: 4936)
- certutil.exe (PID: 4084)
- certutil.exe (PID: 3004)
XORed URL has been found (YARA)
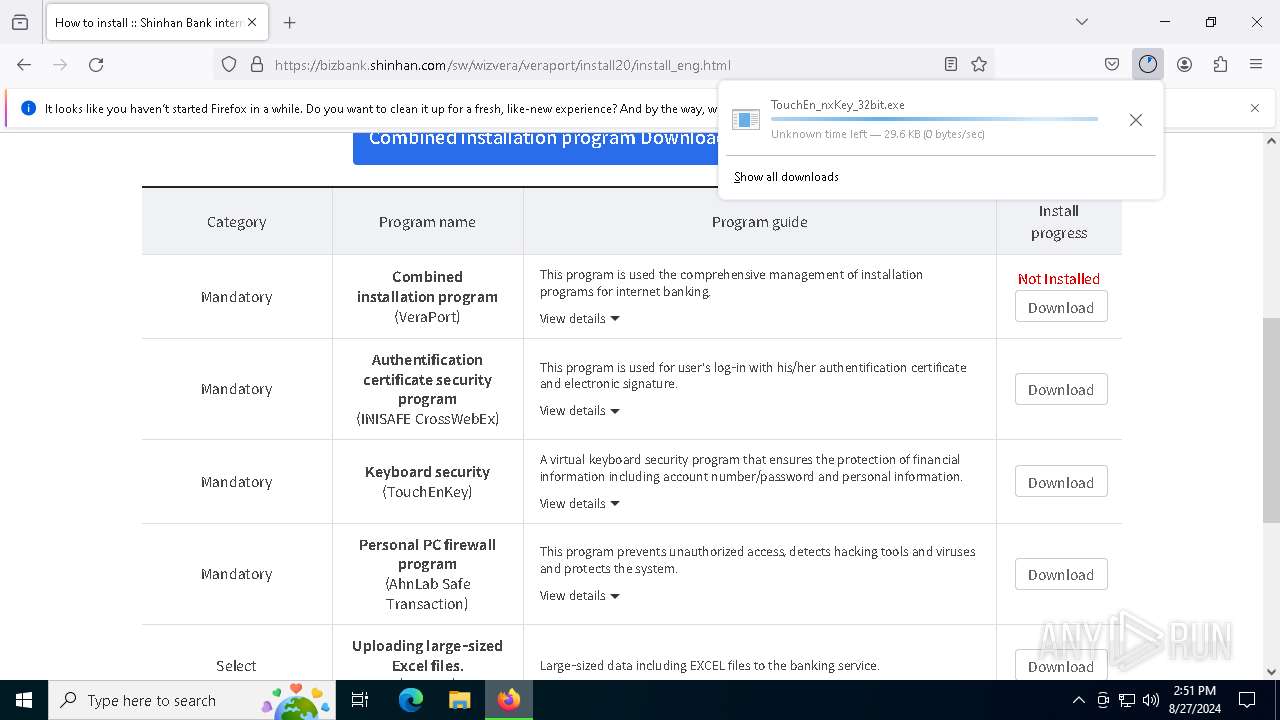
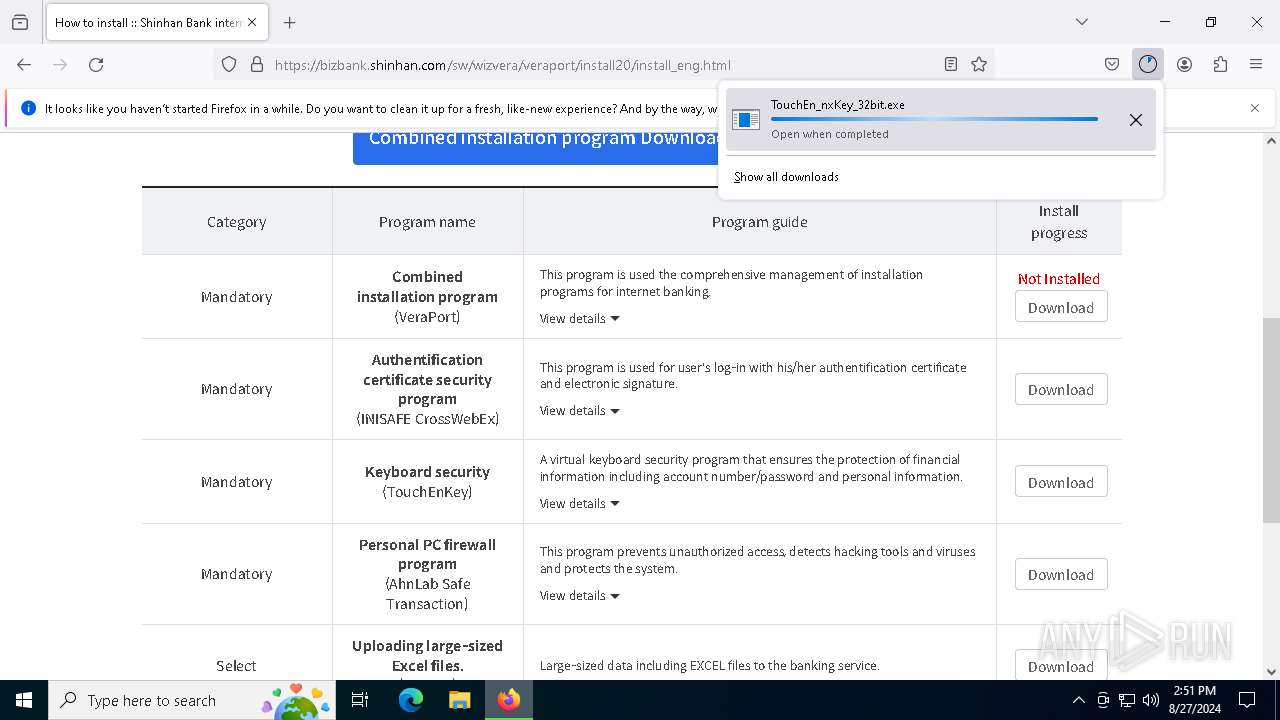
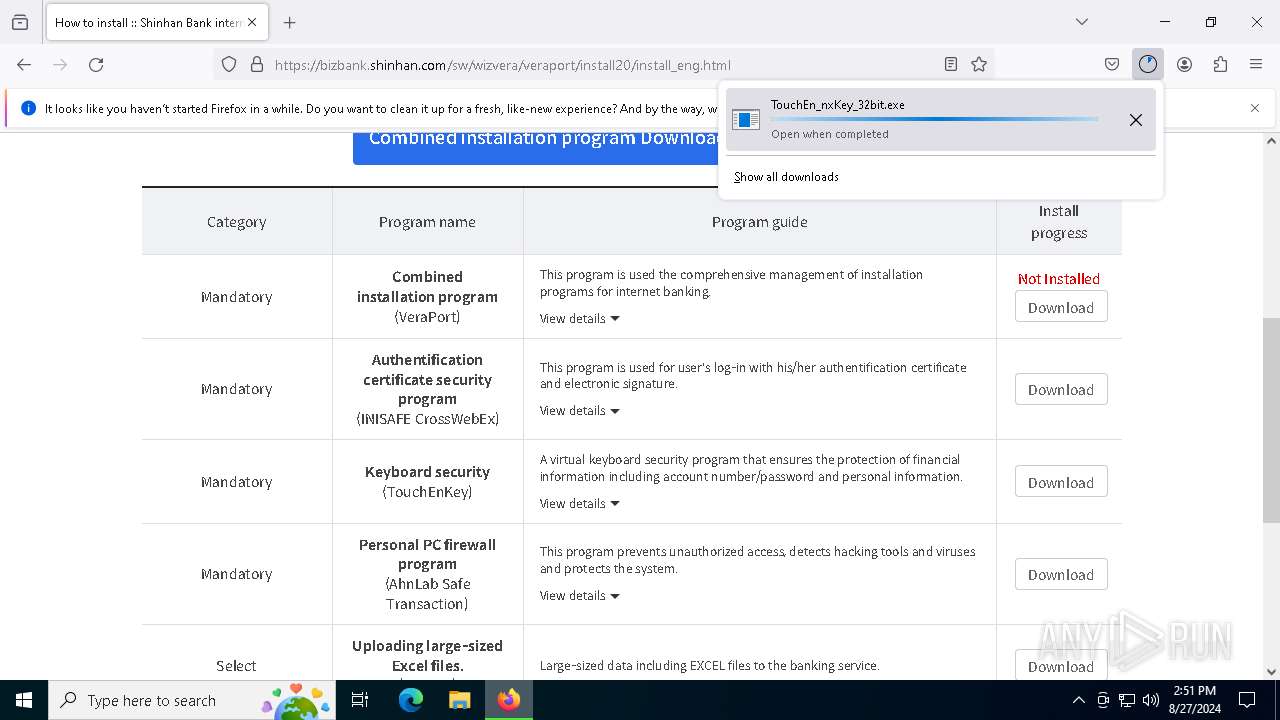
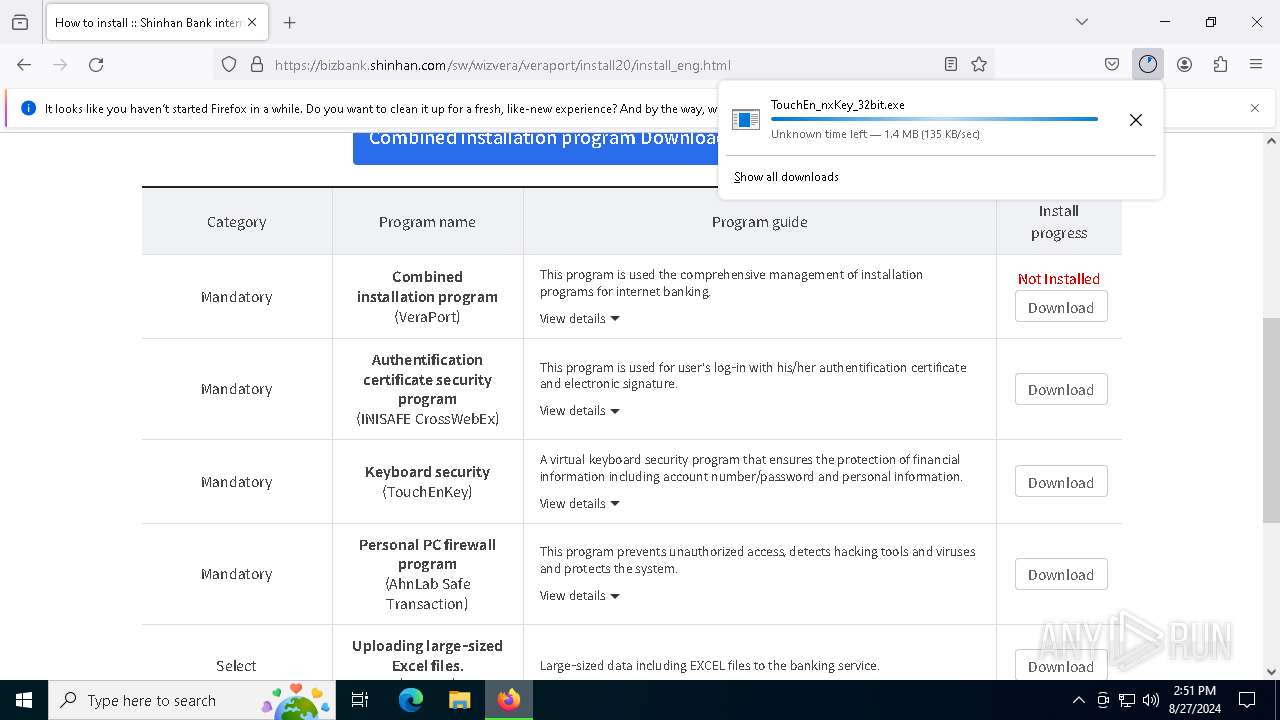
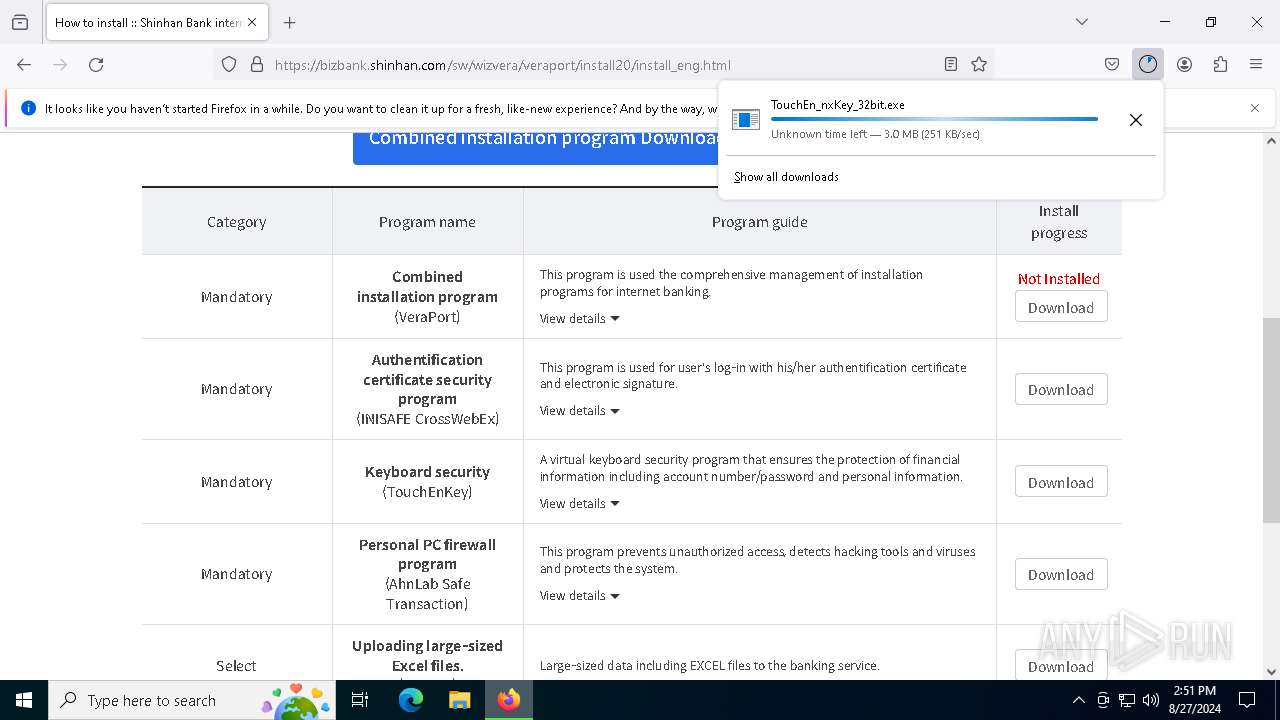
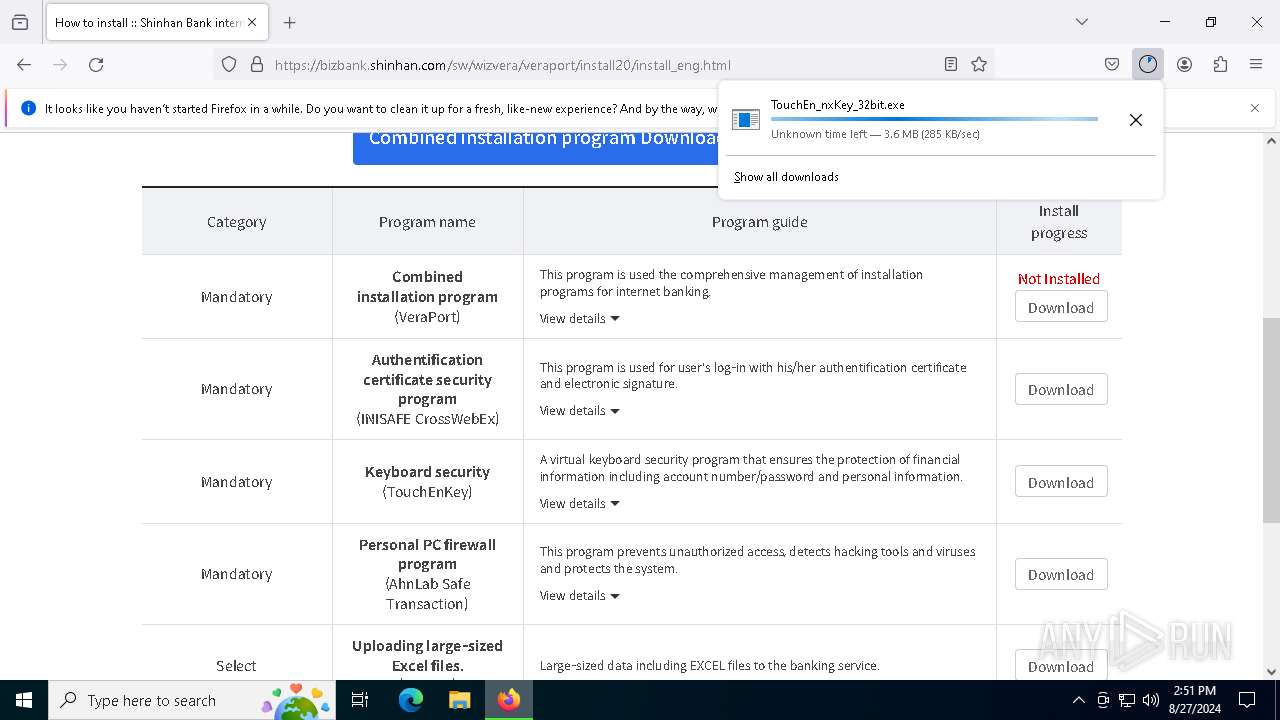
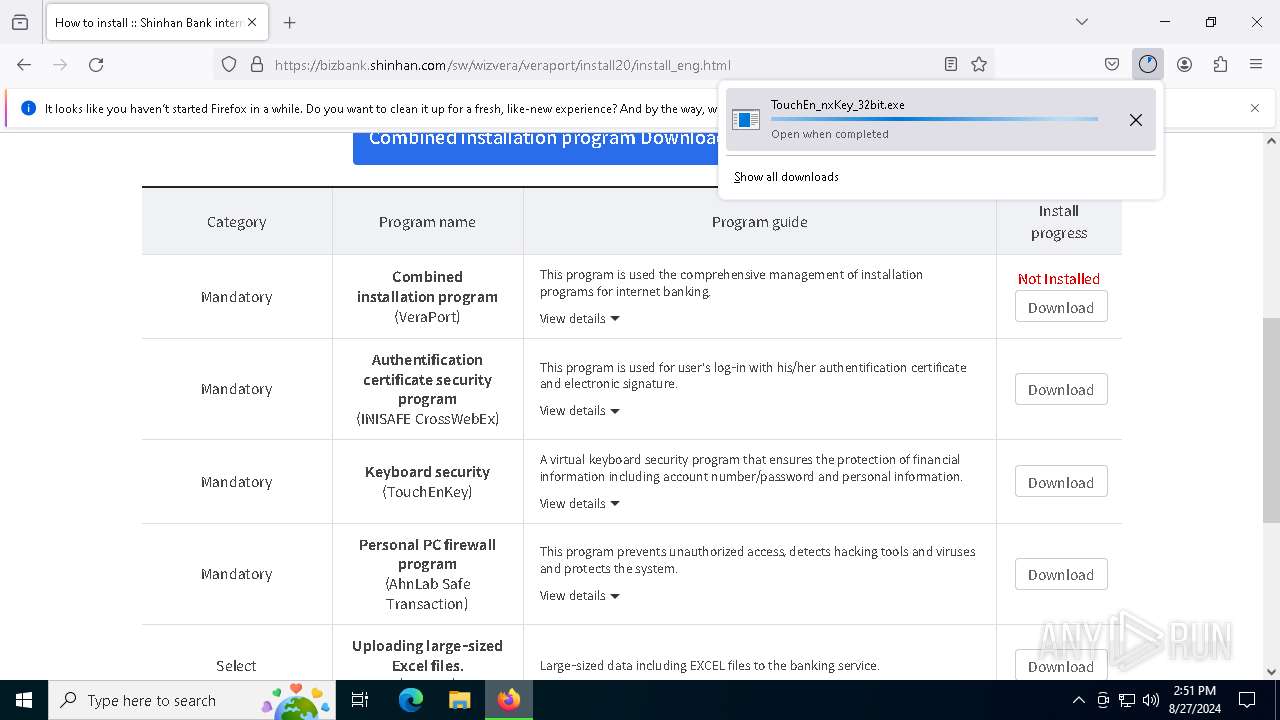
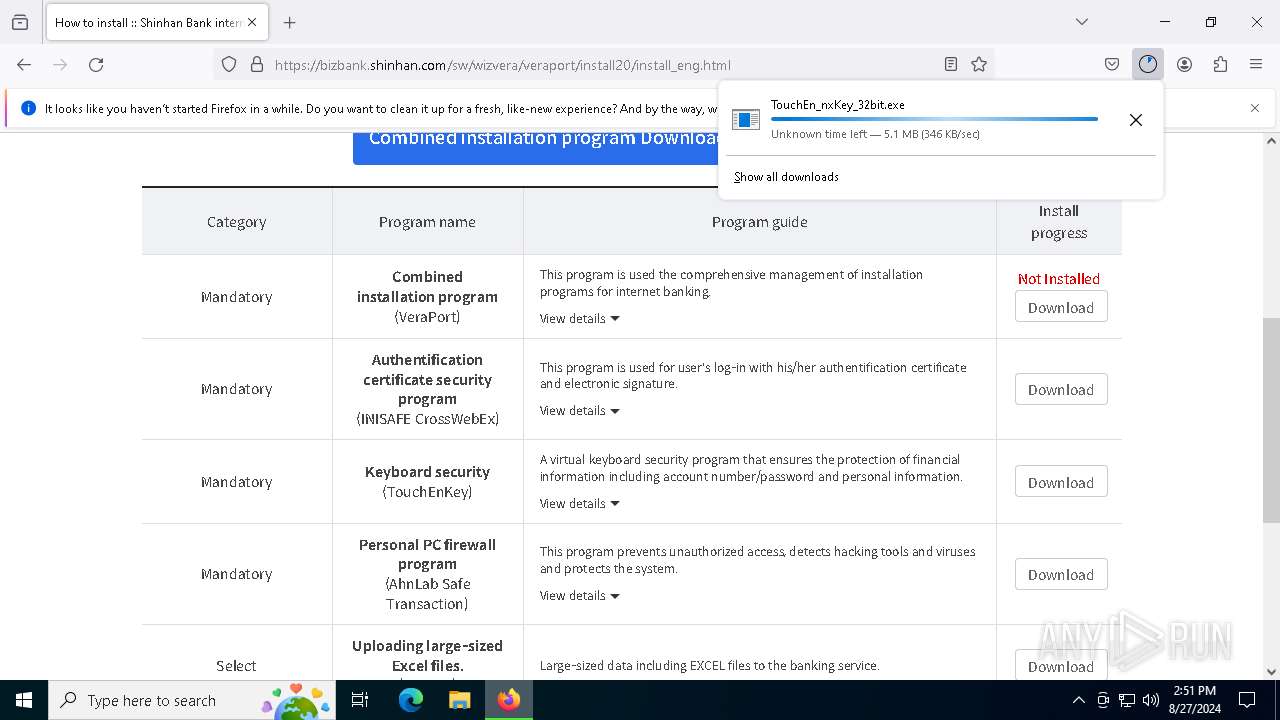
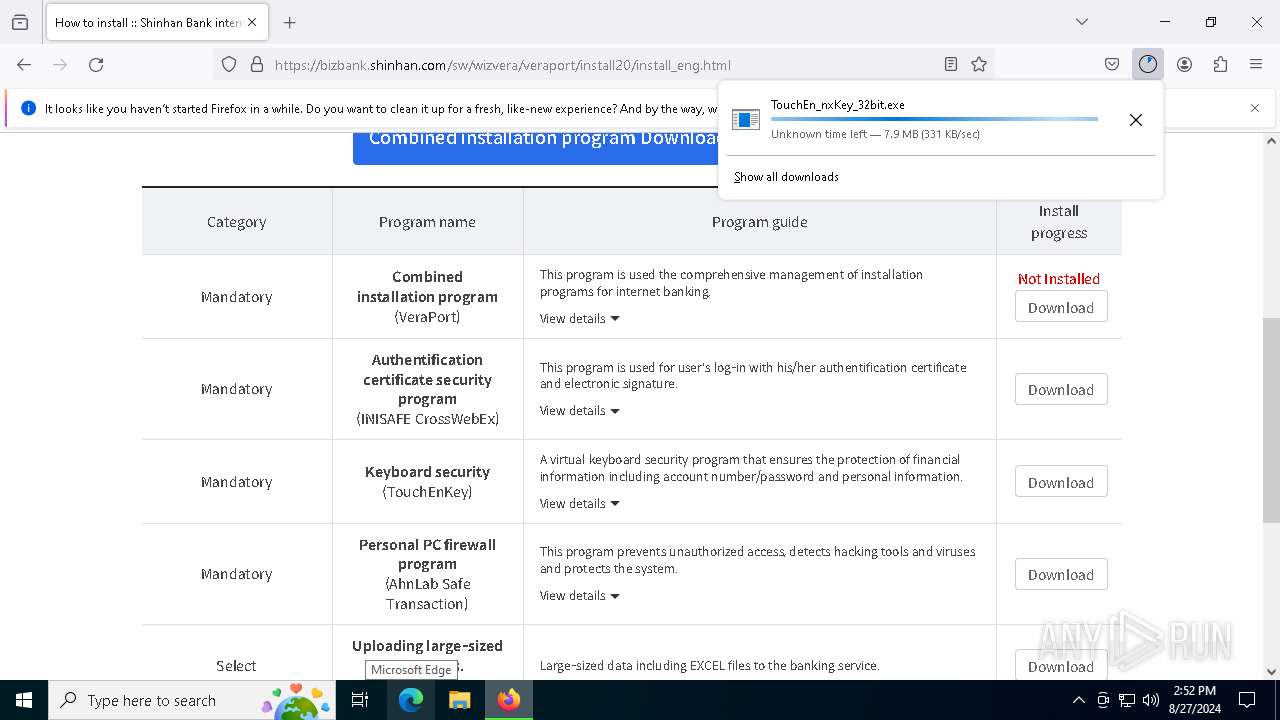
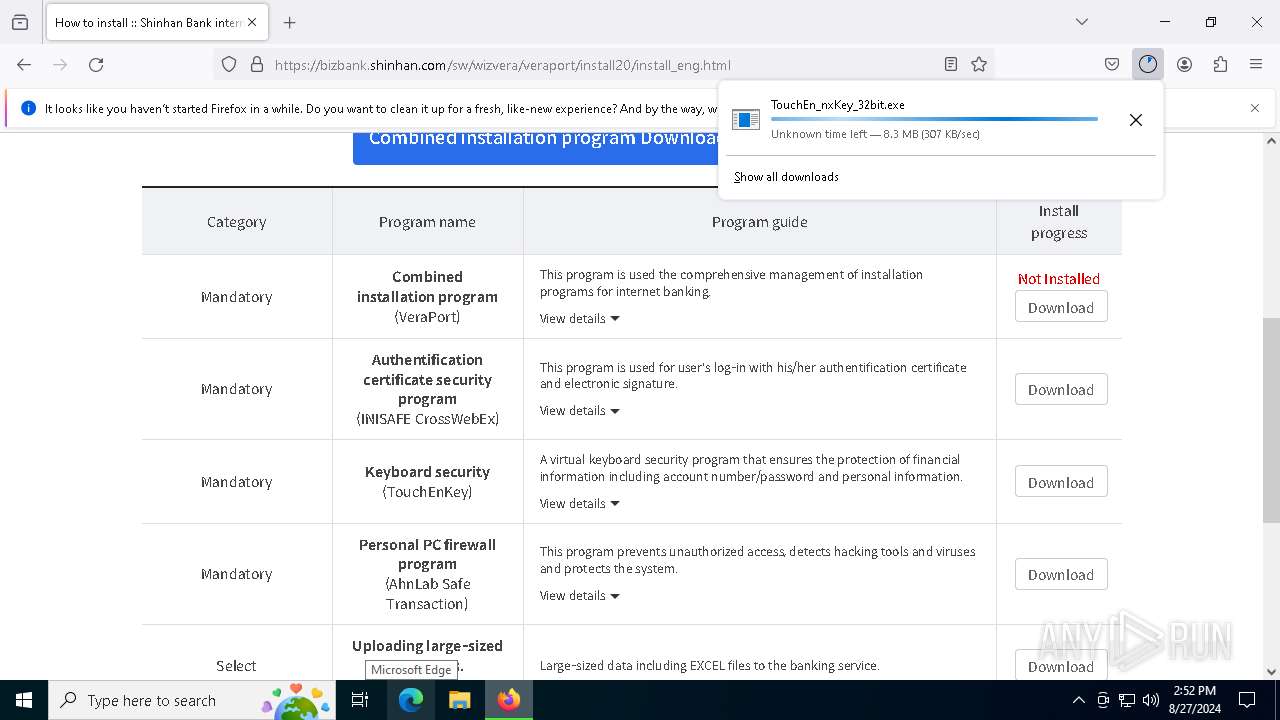
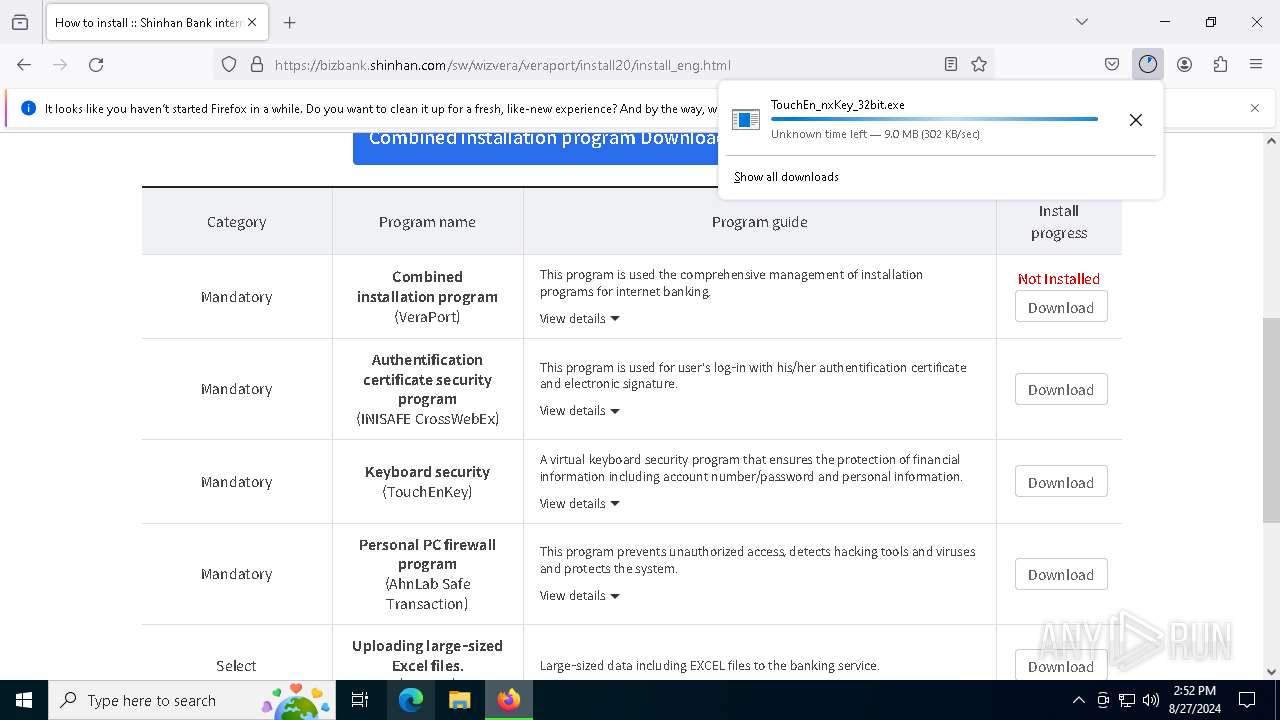
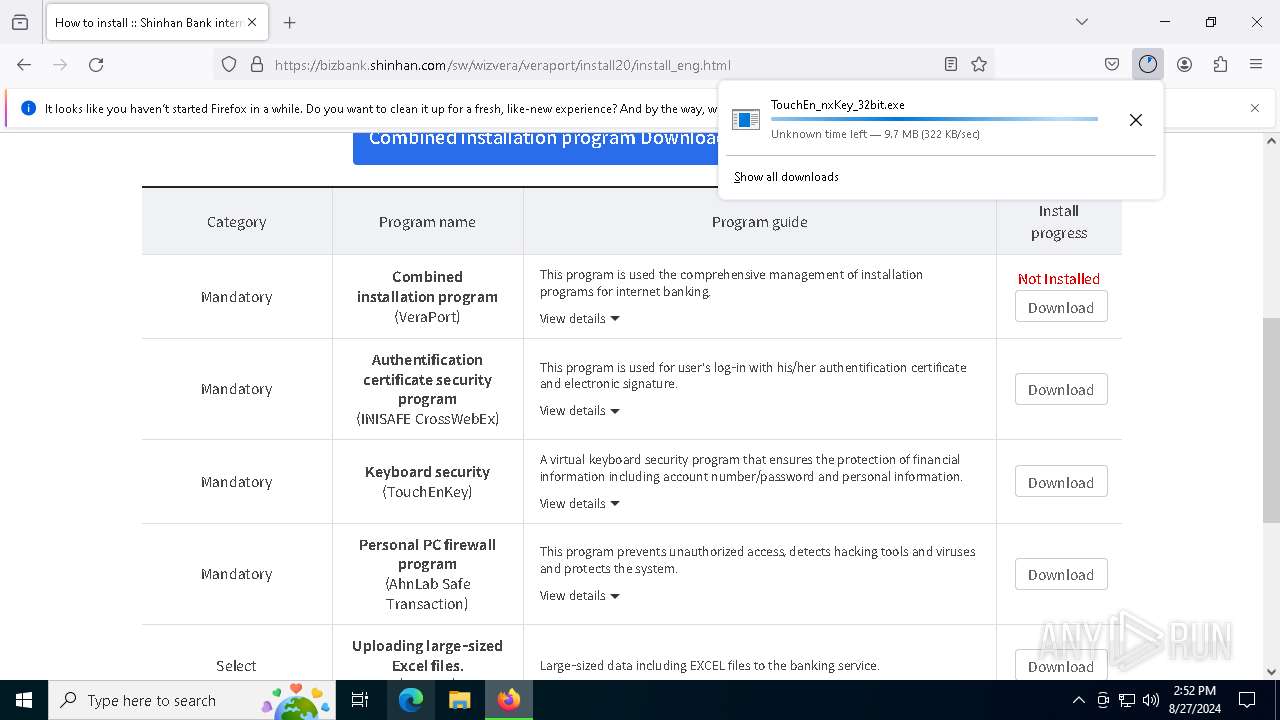
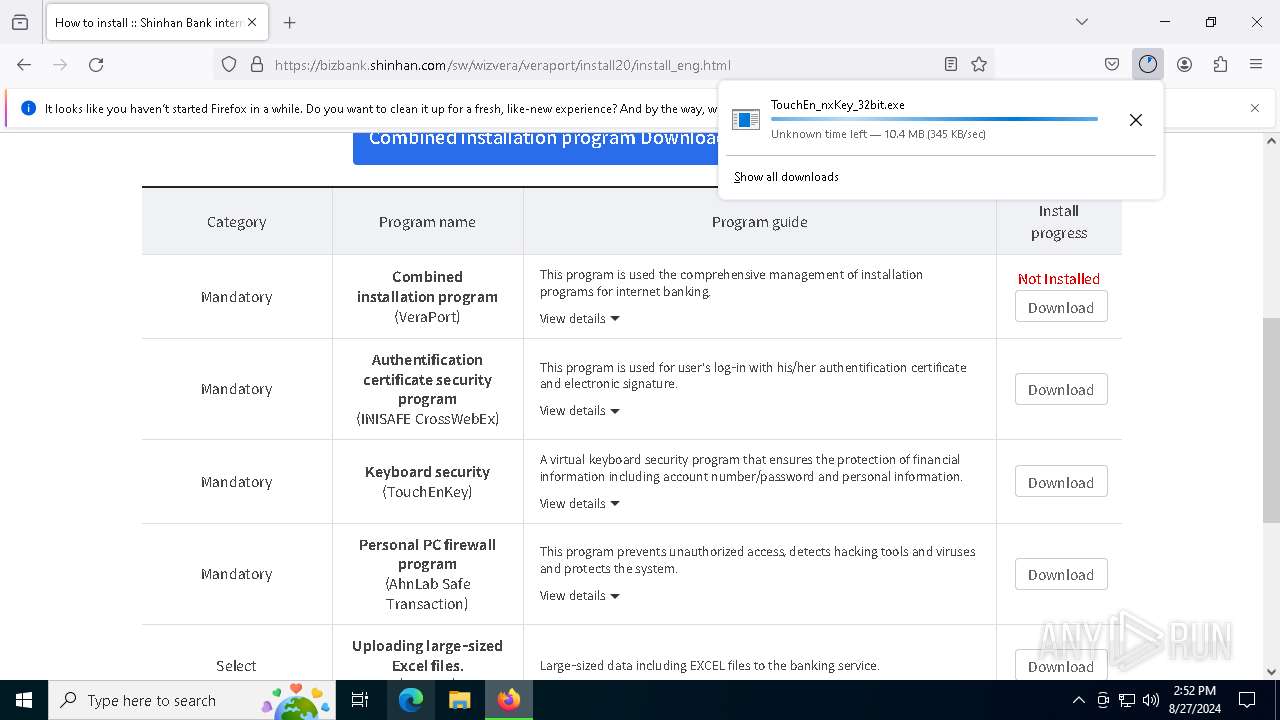
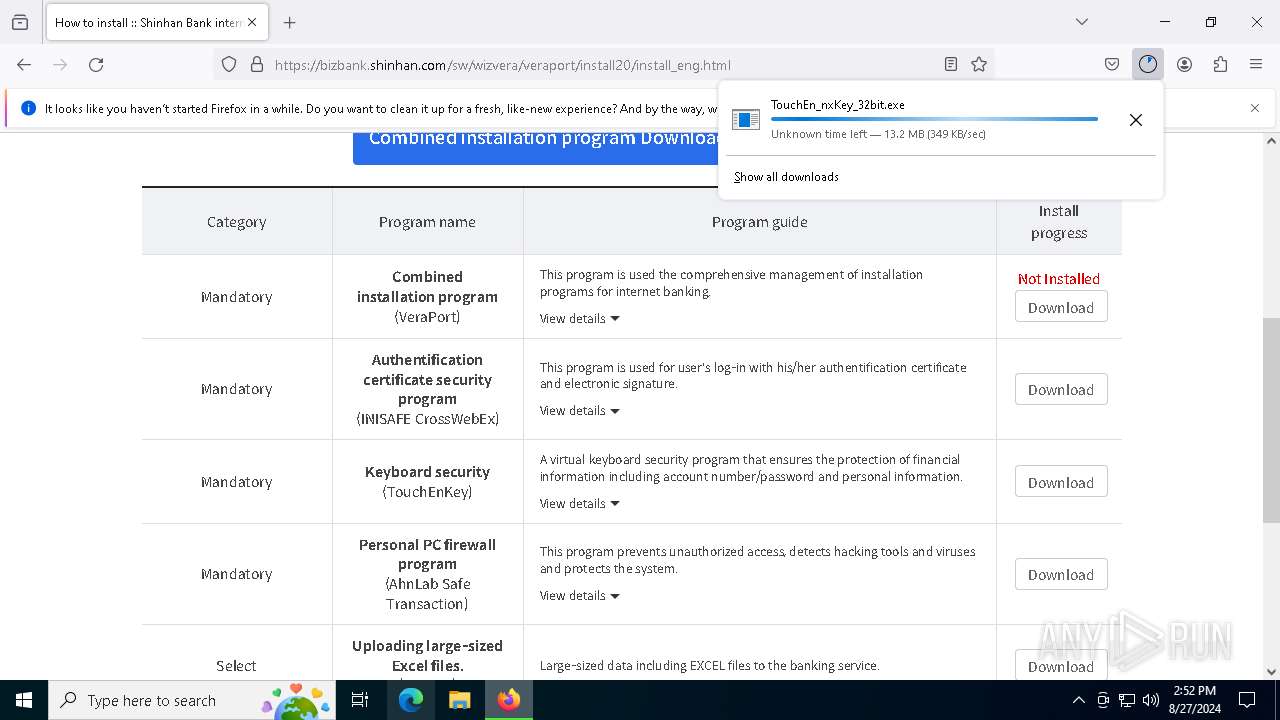
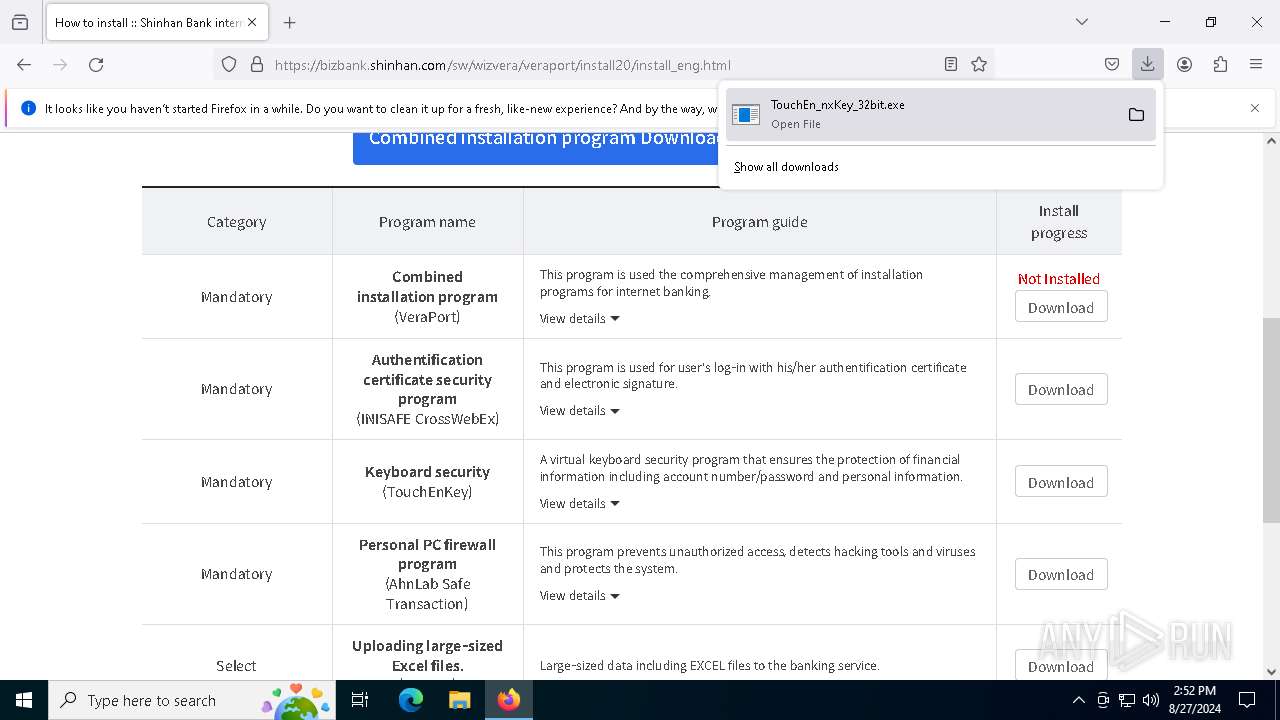
- TouchEn_nxKey_32bit.exe (PID: 6340)
SUSPICIOUS
Drops the executable file immediately after the start
- CKSetup32.exe (PID: 6520)
- CKSetup64.exe (PID: 5072)
- CKSetup64.exe (PID: 3116)
- TouchEn_nxKey_32bit.exe (PID: 6340)
- raon_touchenex_Install.exe (PID: 2904)
- CrossEX_LocalService_Install.exe (PID: 6180)
- FFCert.exe (PID: 4316)
Executable content was dropped or overwritten
- CKSetup32.exe (PID: 6520)
- CKSetup64.exe (PID: 5072)
- CKSetup64.exe (PID: 3116)
- raon_touchenex_Install.exe (PID: 2904)
- TouchEn_nxKey_32bit.exe (PID: 6340)
- CrossEX_LocalService_Install.exe (PID: 6180)
- FFCert.exe (PID: 4316)
Drops a system driver (possible attempt to evade defenses)
- CKSetup64.exe (PID: 5072)
Creates a software uninstall entry
- CKSetup32.exe (PID: 6520)
- CrossEX_LocalService_Install.exe (PID: 6180)
- TouchEn_nxKey_32bit.exe (PID: 6340)
Reads the date of Windows installation
- TouchEn_nxKey_32bit.exe (PID: 6340)
Malware-specific behavior (creating "System.dll" in Temp)
- raon_touchenex_Install.exe (PID: 2904)
- CrossEX_LocalService_Install.exe (PID: 6180)
Adds/modifies Windows certificates
- raon_touchenex_Install.exe (PID: 2904)
- CrossEX_LocalService_Install.exe (PID: 6180)
The process creates files with name similar to system file names
- raon_touchenex_Install.exe (PID: 2904)
- CrossEX_LocalService_Install.exe (PID: 6180)
- FFCert.exe (PID: 4316)
Creates/Modifies COM task schedule object
- raon_touchenex_Install.exe (PID: 2904)
- TouchEn_nxKey_32bit.exe (PID: 6340)
Executes as Windows Service
- ObCrossEXService.exe (PID: 6740)
Process drops legitimate windows executable
- FFCert.exe (PID: 4316)
The process drops C-runtime libraries
- FFCert.exe (PID: 4316)
Reads security settings of Internet Explorer
- CKSetup32.exe (PID: 6520)
- TouchEn_nxKey_32bit.exe (PID: 6340)
INFO
Application launched itself
- firefox.exe (PID: 5000)
- firefox.exe (PID: 6684)
Reads Microsoft Office registry keys
- firefox.exe (PID: 5000)
Reads the computer name
- CKSetup32.exe (PID: 6520)
- CKSetup64.exe (PID: 5072)
- raon_touchenex_Install.exe (PID: 2904)
- CrossEXService.exe (PID: 1992)
- ObCrossEXService.exe (PID: 6740)
- certutil.exe (PID: 4084)
- certutil.exe (PID: 3004)
- TouchEn_nxKey_32bit.exe (PID: 6340)
Checks supported languages
- CKSetup64.exe (PID: 5072)
- CKSetup64.exe (PID: 3116)
- raon_touchenex_Install.exe (PID: 2904)
- CrossEXService.exe (PID: 1992)
- CrossEX_LocalService_Install.exe (PID: 6180)
- ObCrossEXService.exe (PID: 6740)
- FFCert.exe (PID: 4316)
- Firefox_CertUtil.exe (PID: 4936)
- certutil.exe (PID: 4084)
- certutil.exe (PID: 3004)
- TouchEn_nxKey_32bit.exe (PID: 6340)
- CKSetup32.exe (PID: 6520)
Creates files in the program directory
- TouchEn_nxKey_32bit.exe (PID: 6340)
- raon_touchenex_Install.exe (PID: 2904)
- CrossEX_LocalService_Install.exe (PID: 6180)
Create files in a temporary directory
- raon_touchenex_Install.exe (PID: 2904)
- CrossEX_LocalService_Install.exe (PID: 6180)
- FFCert.exe (PID: 4316)
- certutil.exe (PID: 4084)
- certutil.exe (PID: 3004)
- TouchEn_nxKey_32bit.exe (PID: 6340)
Process checks computer location settings
- TouchEn_nxKey_32bit.exe (PID: 6340)
Reads the machine GUID from the registry
- CrossEX_LocalService_Install.exe (PID: 6180)
- CrossEXService.exe (PID: 1992)
Creates files or folders in the user directory
- certutil.exe (PID: 4084)
UPX packer has been detected
- TouchEn_nxKey_32bit.exe (PID: 6340)
Executable content was dropped or overwritten
- firefox.exe (PID: 5000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
163
Monitored processes
32
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 872 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1232 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | certutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5636 -childID 4 -isForBrowser -prefsHandle 5784 -prefMapHandle 5780 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1488 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {ae96a388-2563-48f0-a57d-80f88743c4c0} 5000 "\\.\pipe\gecko-crash-server-pipe.5000" 16508d4d310 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1992 | "C:\Program Files (x86)\iniLINE\CrossEX\crossex\CrossEXService.exe" | C:\Program Files (x86)\iniLINE\CrossEX\crossex\CrossEXService.exe | — | CrossEX_LocalService_Install.exe | |||||||||||
User: admin Company: iniLINE Co., Ltd. Integrity Level: HIGH Description: CrossEX Service Version: 1.0.2.14 Modules
| |||||||||||||||
| 2252 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2968 -childID 1 -isForBrowser -prefsHandle 2964 -prefMapHandle 2960 -prefsLen 26706 -prefMapSize 244343 -jsInitHandle 1488 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {73d56296-36d6-4eed-af40-13fdeac56730} 5000 "\\.\pipe\gecko-crash-server-pipe.5000" 1650302d150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2324 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1920 -parentBuildID 20240213221259 -prefsHandle 1860 -prefMapHandle 1852 -prefsLen 30537 -prefMapSize 244343 -appDir "C:\Program Files\Mozilla Firefox\browser" - {8f6ca727-3d92-4c2a-9fea-f5dcc34565d8} 5000 "\\.\pipe\gecko-crash-server-pipe.5000" 1657e0c4110 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2480 | sc start "CrossEX Live Checker" | C:\Windows\SysWOW64\sc.exe | — | CrossEX_LocalService_Install.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2900 | sc description "CrossEX Live Checker" "checking live status of CrossEXService" | C:\Windows\SysWOW64\sc.exe | — | CrossEX_LocalService_Install.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2904 | "C:\Users\admin\AppData\Local\Temp\~RAPack1341484\raon_touchenex_Install.exe" /S | C:\Users\admin\AppData\Local\Temp\~RAPack1341484\raon_touchenex_Install.exe | TouchEn_nxKey_32bit.exe | ||||||||||||
User: admin Company: iniLINE Co., Ltd. Integrity Level: HIGH Description: iniLINE CrossEX 32bit Exit code: 0 Version: 1.0.1.1547 Modules
| |||||||||||||||
| 3004 | "C:\Users\admin\AppData\Local\Temp\ffcert_raon\bin\certutil.exe" -L -d sql:"C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release" | C:\Users\admin\AppData\Local\Temp\ffcert_raon\bin\certutil.exe | Firefox_CertUtil.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
37 755
Read events
37 654
Write events
90
Delete events
11
Modification events
| (PID) Process: | (6684) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: D279620501000000 | |||
| (PID) Process: | (5000) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 07FC640501000000 | |||
| (PID) Process: | (5000) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 0 | |||
| (PID) Process: | (5000) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 1 | |||
| (PID) Process: | (5000) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Installer\308046B0AF4A39CB |
| Operation: | delete value | Name: | installer.taskbarpin.win10.enabled |
Value: | |||
| (PID) Process: | (5000) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (5000) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (5000) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Theme |
Value: 1 | |||
| (PID) Process: | (5000) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (5000) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
Executable files
59
Suspicious files
177
Text files
40
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5000 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5000 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5000 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5000 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 5000 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5000 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 5000 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5000 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:7A97B8DBC4F98D175F958C00F463A52A | SHA256:92074D2ED1AA1FD621287E35DB9EF1AE3DC04777EFAE5F09E7A3B4534C201548 | |||
| 5000 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\AlternateServices.bin | binary | |
MD5:5D5AA72303D26D1DDFA9AB5619FDFF95 | SHA256:8415ABDC72BA95B918676048890495E1285CAD054FBAE33DBE184B808017230A | |||
| 5000 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:7A97B8DBC4F98D175F958C00F463A52A | SHA256:92074D2ED1AA1FD621287E35DB9EF1AE3DC04777EFAE5F09E7A3B4534C201548 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
95
DNS requests
123
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5000 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
5000 | firefox.exe | POST | 200 | 184.24.77.48:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
5000 | firefox.exe | POST | 200 | 184.24.77.48:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
5000 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
5000 | firefox.exe | POST | 200 | 184.24.77.79:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
5000 | firefox.exe | POST | — | 142.250.184.195:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
5000 | firefox.exe | POST | 200 | 184.24.77.79:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
5000 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://status.thawte.com/ | unknown | — | — | unknown |
5000 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
5000 | firefox.exe | POST | 200 | 184.24.77.79:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
892 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6652 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
5000 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
5000 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
5000 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
5000 | firefox.exe | 59.7.252.102:443 | bizbank.shinhan.com | Shinhan Bank | KR | whitelisted |
5000 | firefox.exe | 184.24.77.48:80 | r11.o.lencr.org | Akamai International B.V. | DE | whitelisted |
5000 | firefox.exe | 34.107.243.93:443 | push.services.mozilla.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
bizbank.shinhan.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
prod.ads.prod.webservices.mozgcp.net |
| unknown |
Threats
Process | Message |
|---|---|
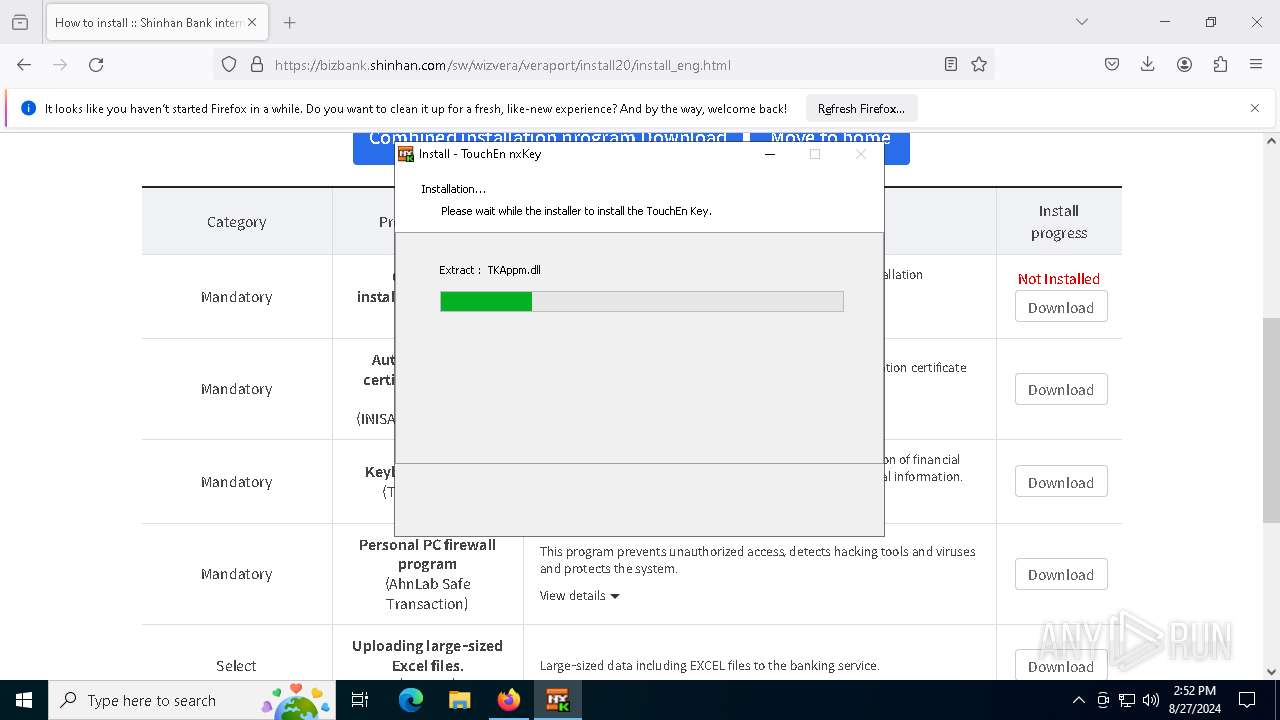
TouchEn_nxKey_32bit.exe | 20141130 fn : C:\Users\admin\AppData\Local\Temp\~RAPack1341484\_Chunk.zip, C:\Users\admin\AppData\Local\Temp\~RAPack1341484 333
|
TouchEn_nxKey_32bit.exe | 20141211 1.szResVersion : 3,1,2,61
|
TouchEn_nxKey_32bit.exe | 20141130 fn : C:\WINDOWS\system32\CKSetup32.exe, C:\WINDOWS\system32(size=3176944) 577
|
TouchEn_nxKey_32bit.exe | 20141130 1304_.\TouchEn_nxKey_Installer.cpp
|
TouchEn_nxKey_32bit.exe | C:\WINDOWS\system32\CKSetup32.exe /install appm
|
CKSetup64.exe | update CKAgentNXE |
CKSetup64.exe | update CKAgent |
TouchEn_nxKey_32bit.exe | 20141130 GetExitCode.0
|
TouchEn_nxKey_32bit.exe | 20141130 fn : C:\Users\admin\AppData\Local\Temp\~RAPack1341484\raon_touchenex_Install.exe, C:\Users\admin\AppData\Local\Temp\~RAPack1341484(size=2114936) 577
|
TouchEn_nxKey_32bit.exe | 20230405 KillProcessByProcessId pid : 0
|