| File name: | 2.44 Classic_acdsee244.exe |
| Full analysis: | https://app.any.run/tasks/26c47ffc-47f6-4756-931e-9fbcdace3819 |
| Verdict: | Malicious activity |
| Analysis date: | October 21, 2020, 16:00:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E2F01BFC60CEDDF89FF62D802C41FC8C |
| SHA1: | 167392FE10245399EC00777381F463AA768DB510 |
| SHA256: | FF9CF8B6260A460746C85BFD540DAF880DBBB0FE62AB4E26BE940A78D56A46EA |
| SSDEEP: | 49152:zkyHWciXUB2dy2G074VC6FX9QguOrh3Sboqh14kfsvU+OSCj4lS8xiqGyIKQOcv/:Y9cIaa7OC64ON9uQvVhIM8yFiTIbH |
MALICIOUS
Application was dropped or rewritten from another process
- ACDSee32.exe (PID: 3052)
- ACDSee32.exe (PID: 2876)
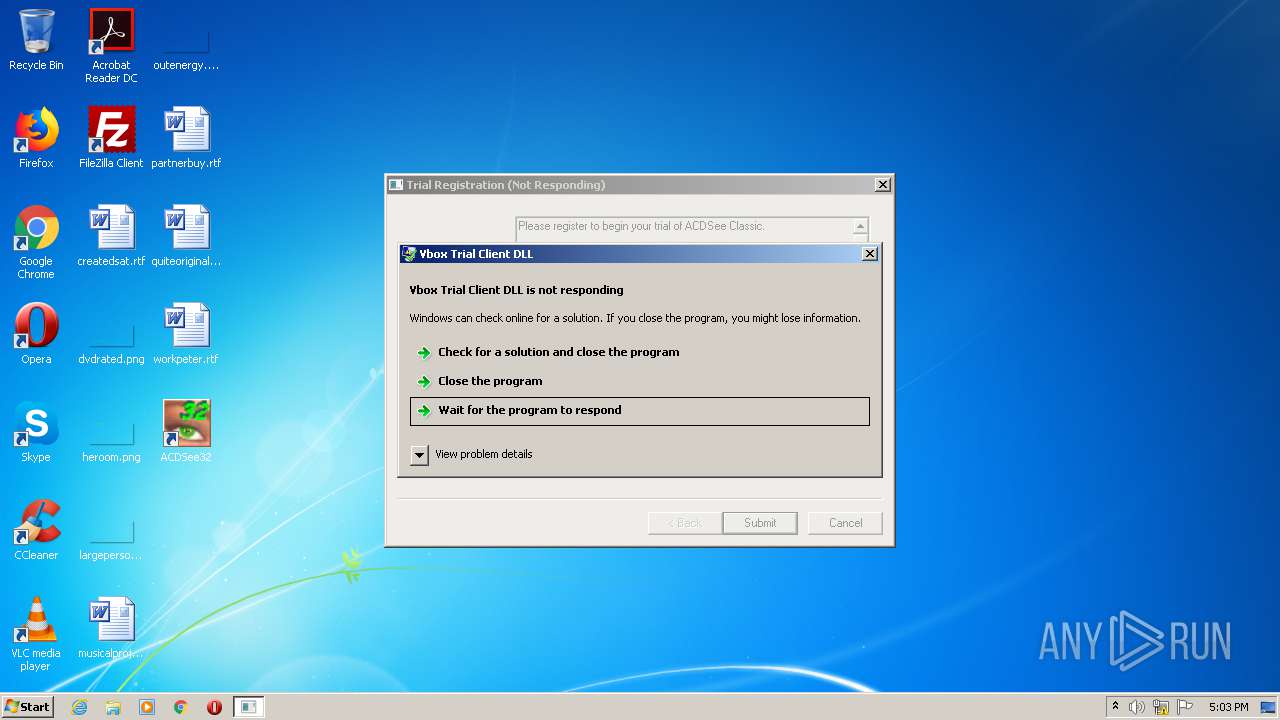
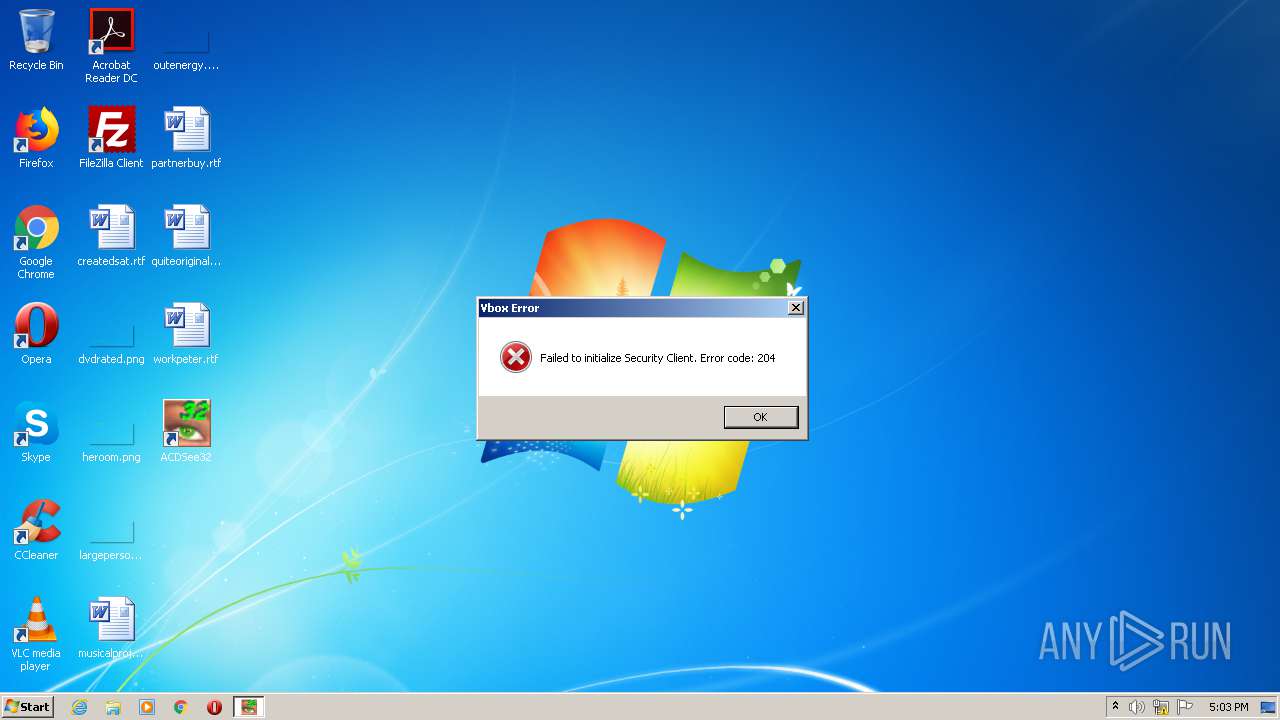
- vboxm.dll (PID: 2480)
- vboxm.dll (PID: 1092)
Loads dropped or rewritten executable
- ACDSee32.exe (PID: 3052)
- vboxm.dll (PID: 1092)
- explorer.exe (PID: 392)
- RUNDLL32.exe (PID: 1936)
- svchost.exe (PID: 2700)
- RUNDLL32.exe (PID: 2656)
- werfault.exe (PID: 3816)
- ACDSee32.exe (PID: 2876)
- vboxm.dll (PID: 2480)
- svchost.exe (PID: 872)
SUSPICIOUS
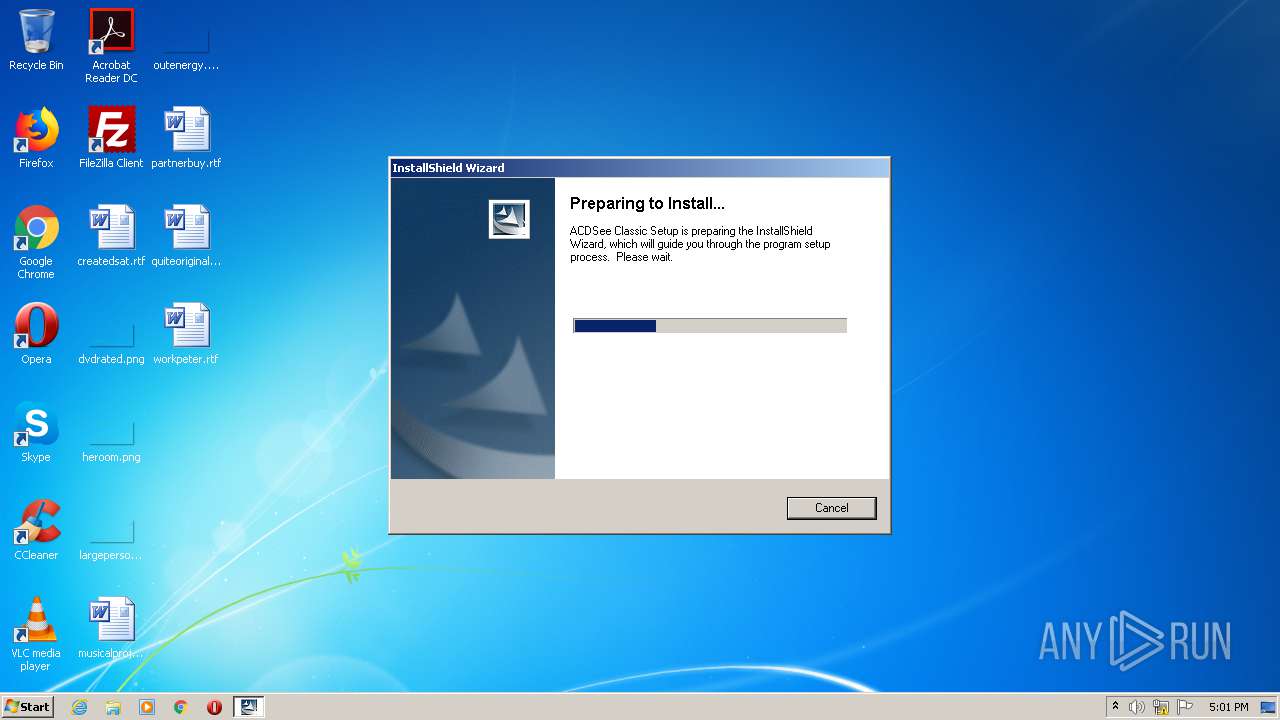
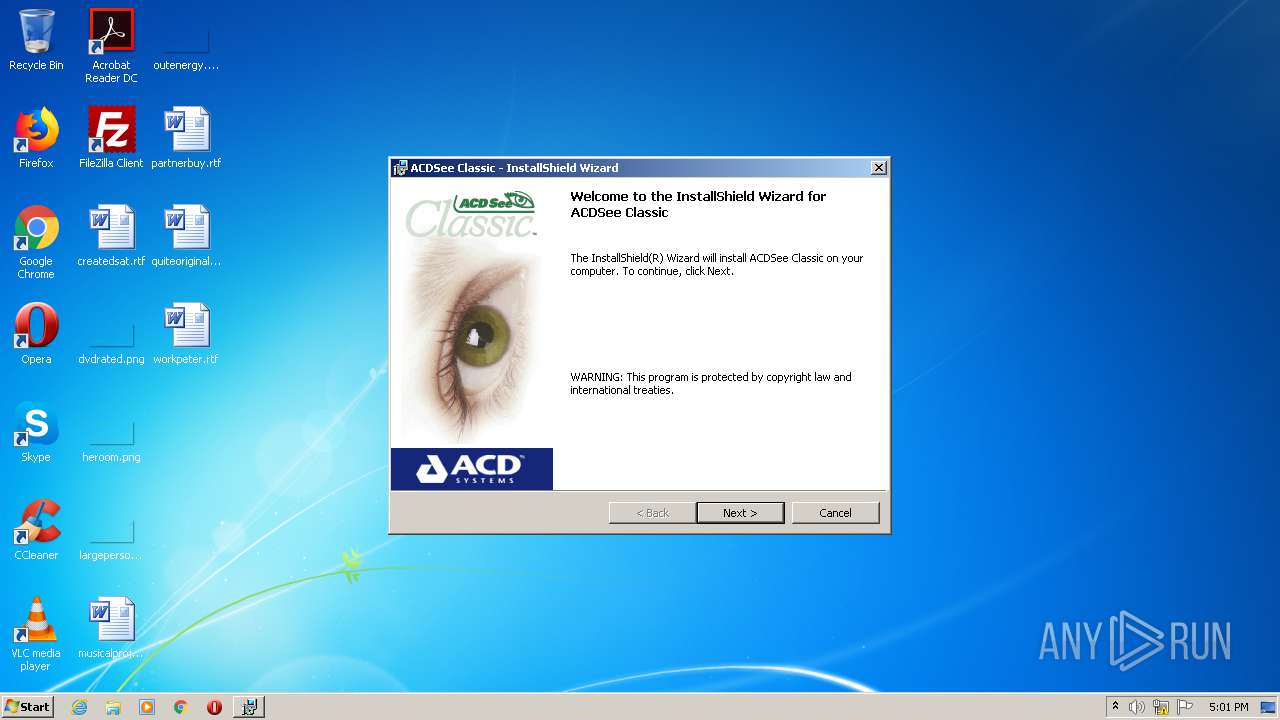
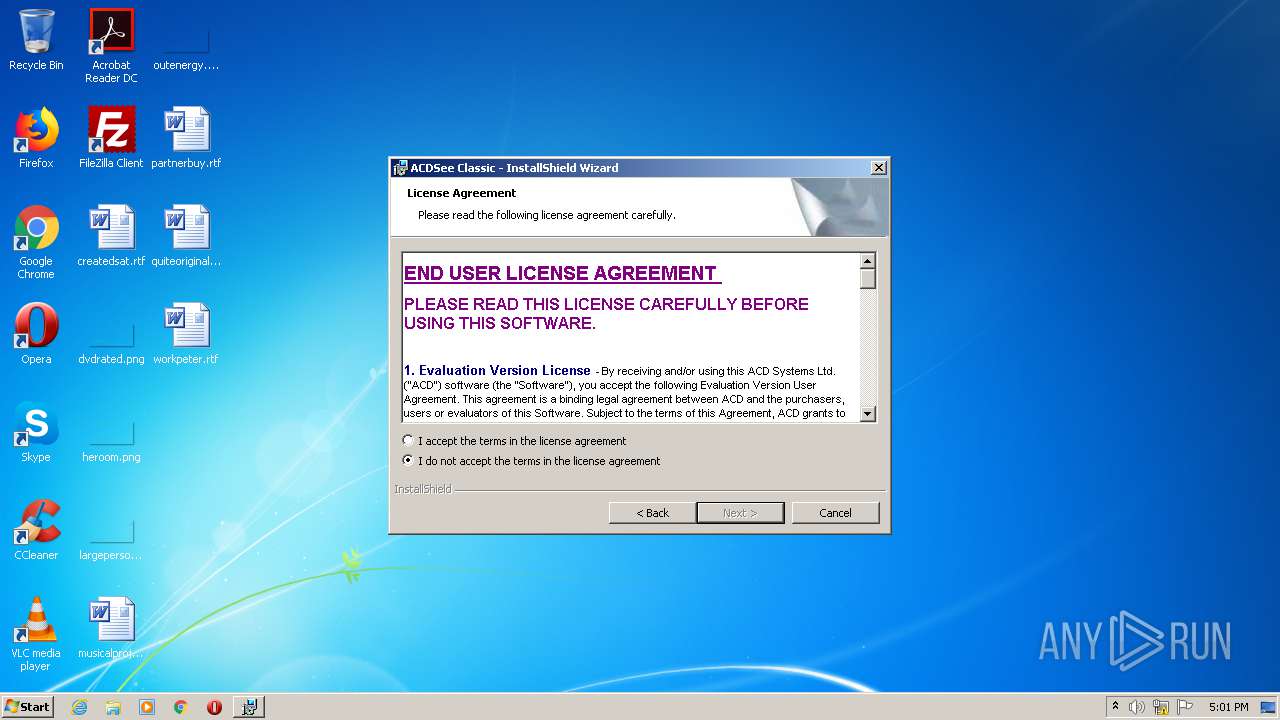
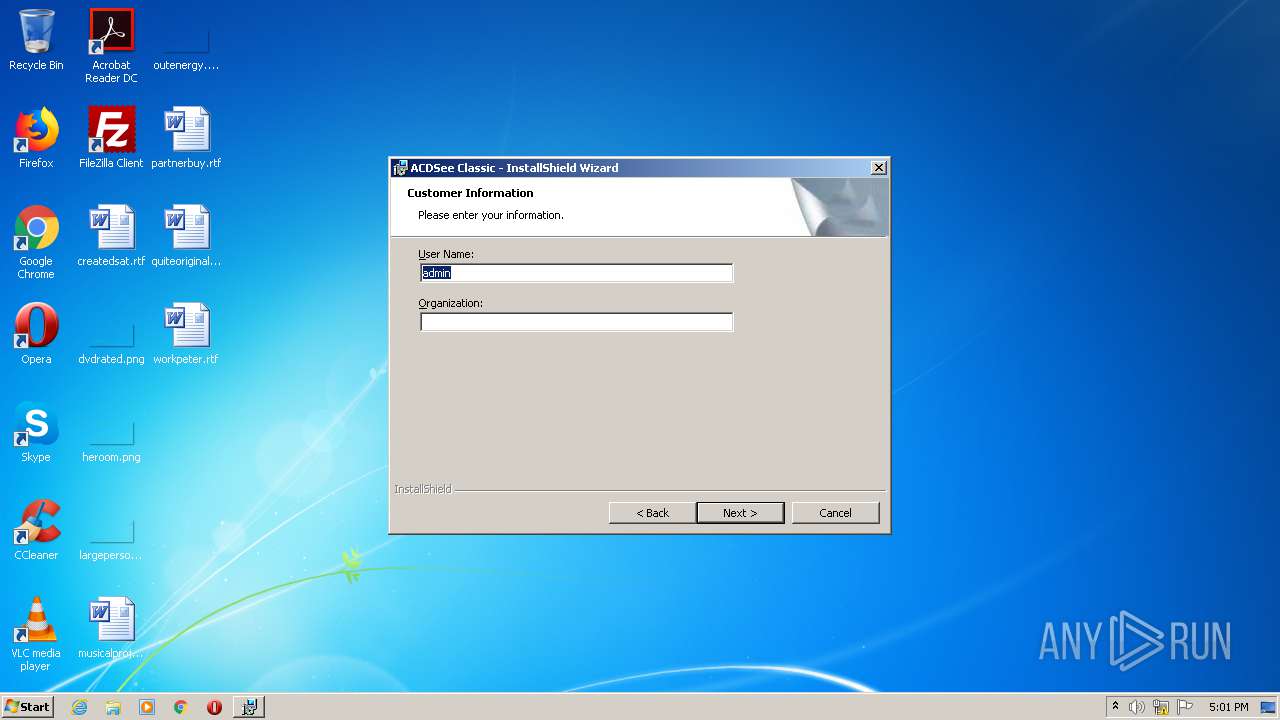
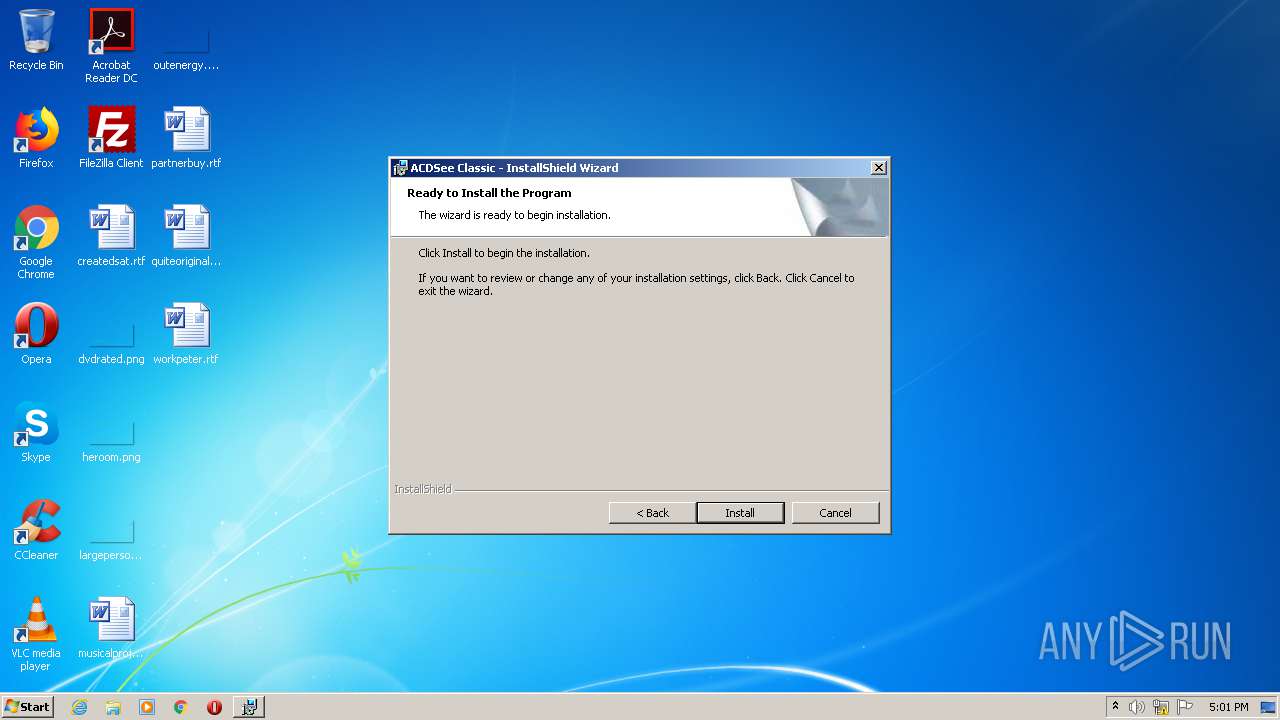
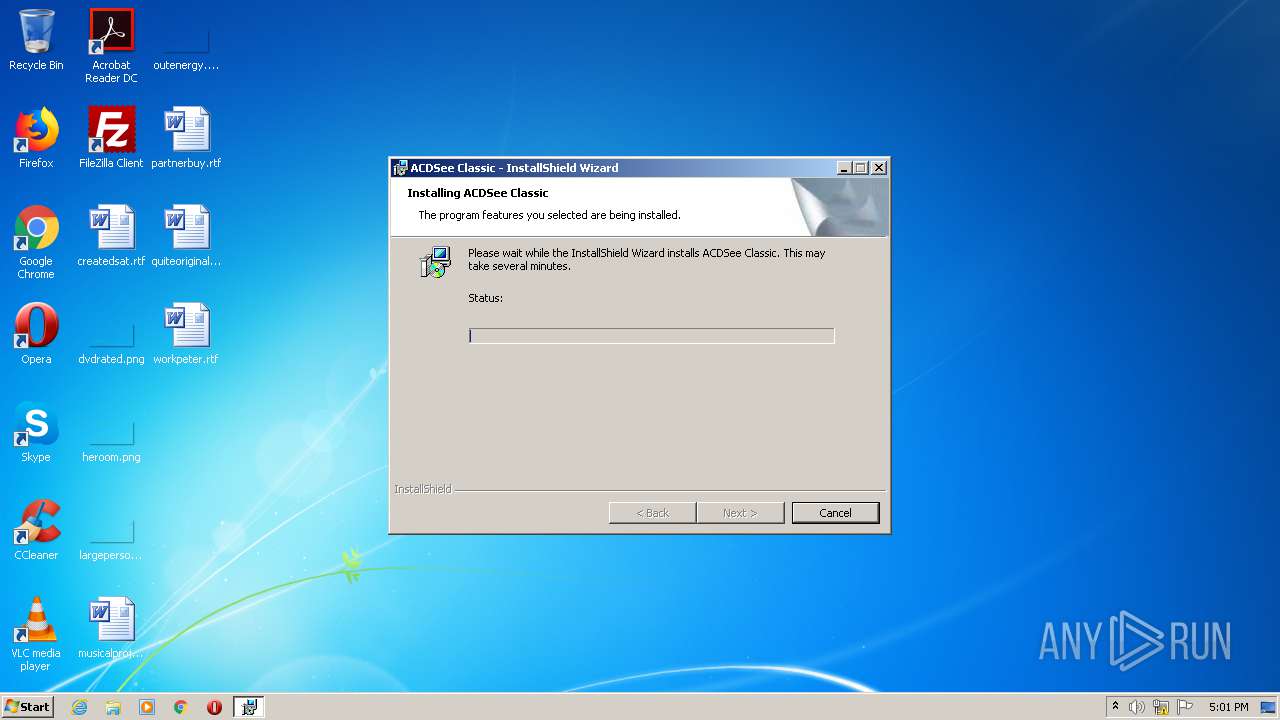
Starts Microsoft Installer
- 2.44 Classic_acdsee244.exe (PID: 3208)
Creates files in the Windows directory
- 2.44 Classic_acdsee244.exe (PID: 3208)
Executable content was dropped or overwritten
- 2.44 Classic_acdsee244.exe (PID: 3208)
- MSI8AD.tmp (PID: 2544)
- msiexec.exe (PID: 2136)
Executed as Windows Service
- vssvc.exe (PID: 3536)
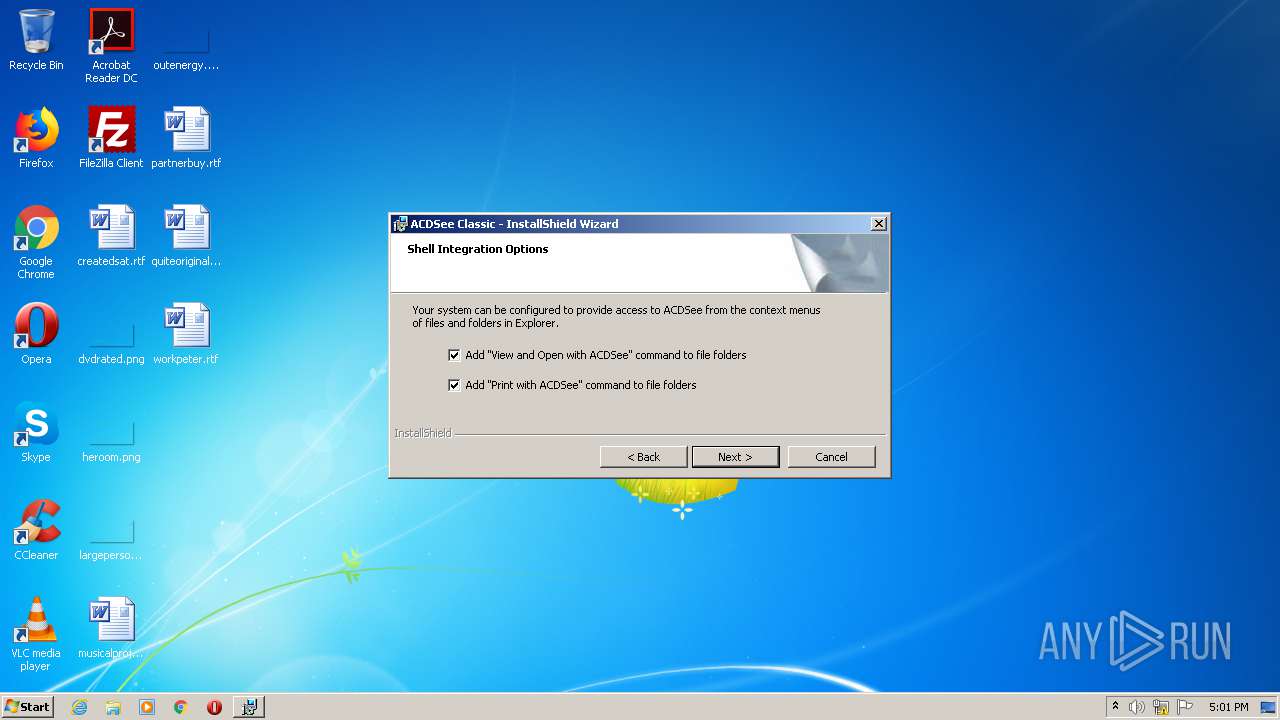
Modifies the open verb of a shell class
- MsiExec.exe (PID: 2776)
Creates files in the program directory
- MSI8AD.tmp (PID: 2544)
- vboxm.dll (PID: 1092)
Application launched itself
- RUNDLL32.exe (PID: 1936)
Uses RUNDLL32.EXE to load library
- vboxm.dll (PID: 1092)
- RUNDLL32.exe (PID: 1936)
Reads Internet Cache Settings
- 2.44 Classic_acdsee244.exe (PID: 3208)
Starts application with an unusual extension
- ACDSee32.exe (PID: 2876)
- ACDSee32.exe (PID: 3052)
INFO
Application launched itself
- msiexec.exe (PID: 2136)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3536)
Creates a software uninstall entry
- msiexec.exe (PID: 2136)
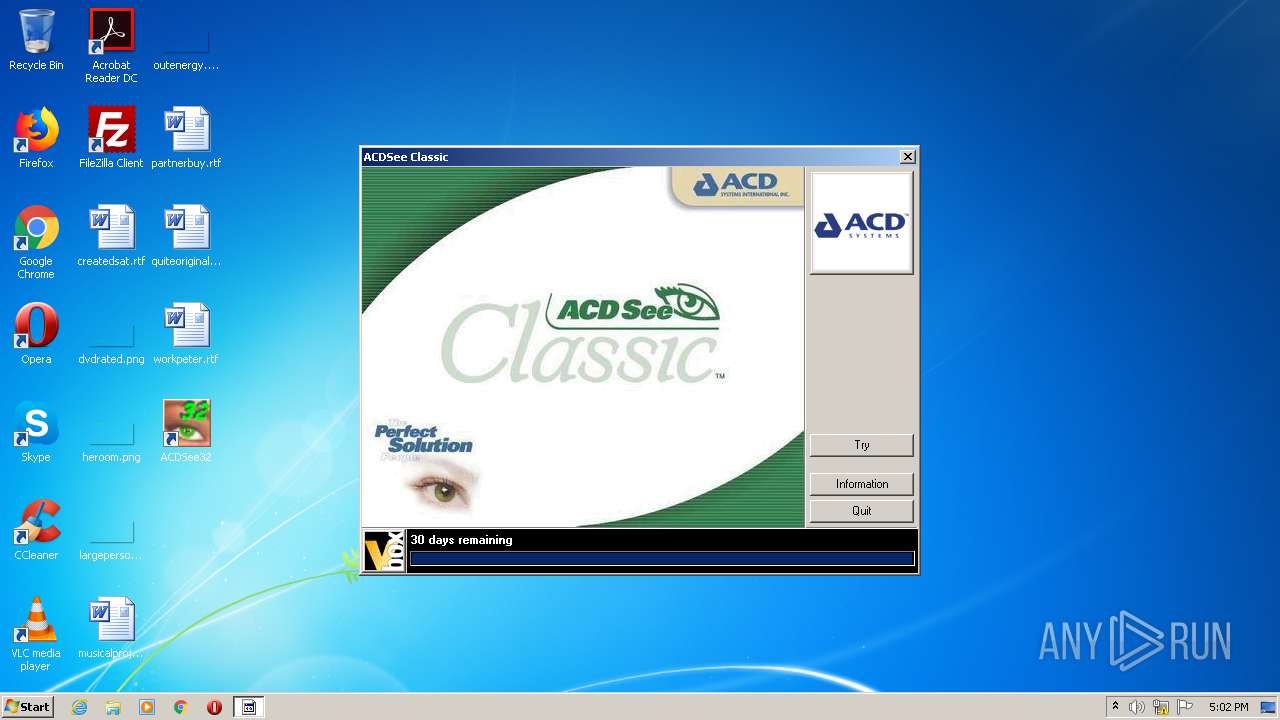
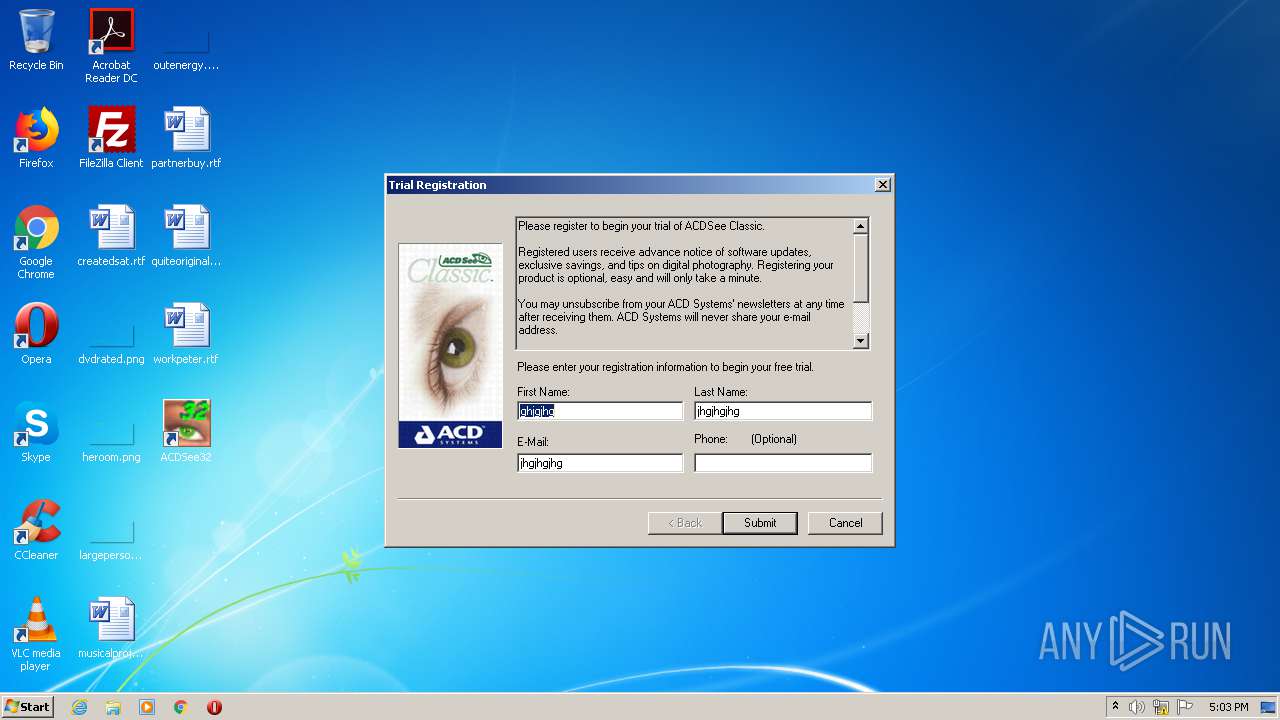
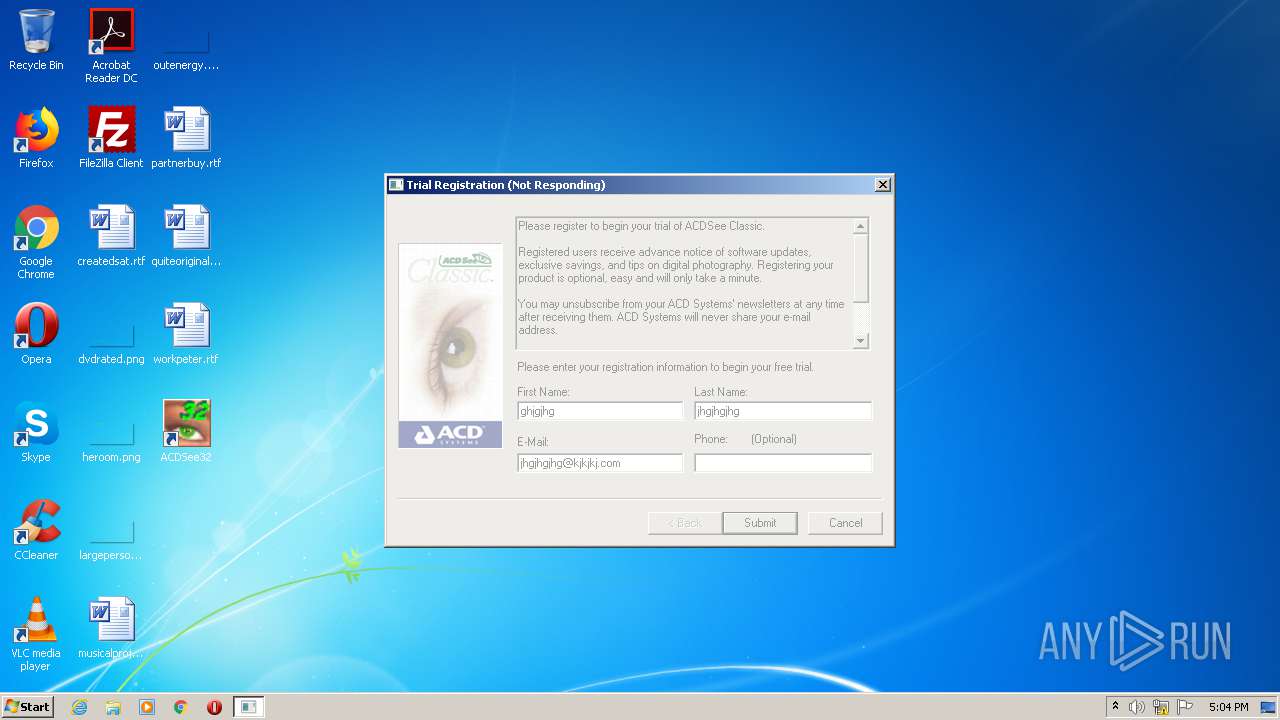
Manual execution by user
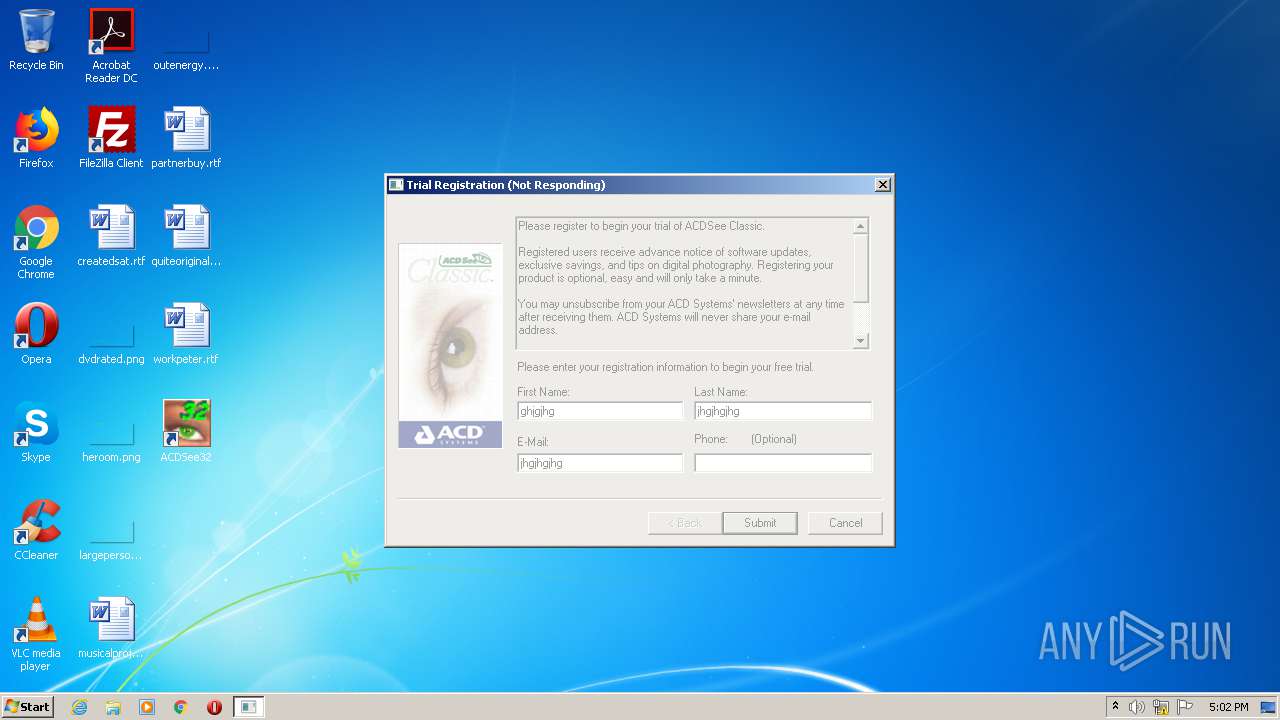
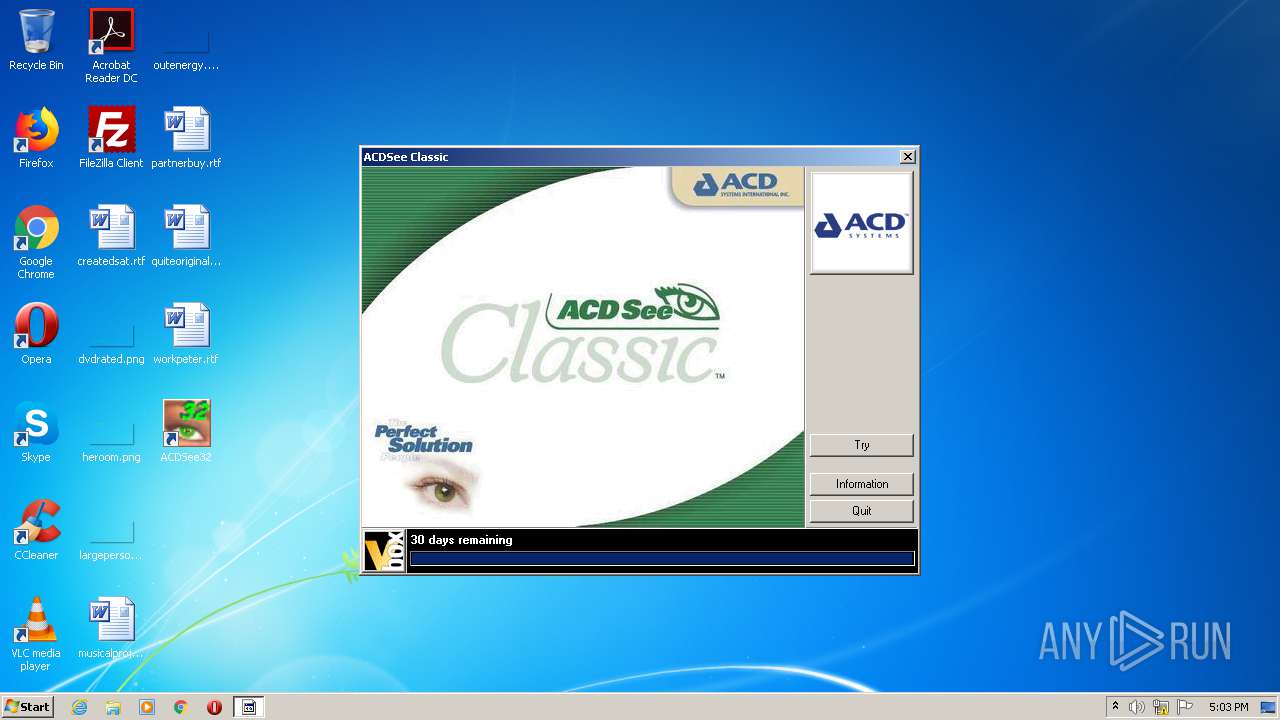
- ACDSee32.exe (PID: 3052)
Creates files in the program directory
- msiexec.exe (PID: 2136)
Dropped object may contain Bitcoin addresses
- vboxm.dll (PID: 1092)
- vboxm.dll (PID: 2480)
Searches for installed software
- msiexec.exe (PID: 2136)
Starts application with an unusual extension
- msiexec.exe (PID: 2136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2003:03:06 00:13:56+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 139264 |
| InitializedDataSize: | 102400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x188dc |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.1.160.0 |
| ProductVersionNumber: | 8.1.0.0 |
| FileFlagsMask: | 0x0002 |
| FileFlags: | Pre-release |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | |
| CompanyName: | ACD Systems Ltd. |
| FileDescription: | Setup Launcher |
| FileVersion: | 2.0.44 |
| InternalName: | setup.exe |
| OriginalFileName: | setup.exe |
| LegalCopyright: | Copyright (C) 2003 InstallShield Software Corp. |
| ProductName: | ACDSee Classic |
| ProductVersion: | 2.0.44 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Mar-2003 23:13:56 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | ACD Systems Ltd. |
| FileDescription: | Setup Launcher |
| FileVersion: | 2.0.44 |
| InternalName: | setup.exe |
| OriginalFilename: | setup.exe |
| LegalCopyright: | Copyright (C) 2003 InstallShield Software Corp. |
| ProductName: | ACDSee Classic |
| ProductVersion: | 2.0.44 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 05-Mar-2003 23:13:56 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002121E | 0x00022000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48366 |
.rdata | 0x00023000 | 0x00003DE8 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.19235 |
.data | 0x00027000 | 0x000091F8 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.12203 |
.rsrc | 0x00031000 | 0x0000A2E0 | 0x0000B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.23936 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.87924 | 666 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 6.39652 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 3.9625 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 6.7616 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 2.48972 | 308 | UNKNOWN | English - United States | RT_CURSOR |
69 | 2.47806 | 110 | UNKNOWN | English - United States | RT_STRING |
72 | 2.32551 | 110 | UNKNOWN | English - United States | RT_STRING |
73 | 2.76648 | 204 | UNKNOWN | English - United States | RT_STRING |
100 | 2.64576 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.01924 | 20 | UNKNOWN | English - United States | RT_GROUP_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
55
Monitored processes
17
Malicious processes
11
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 872 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Common Files\Vbox\Common\vboxm.dll" -PF0FE218FCC7DA301 | C:\Program Files\Common Files\Vbox\Common\vboxm.dll | ACDSee32.exe | ||||||||||||
User: admin Company: Preview Systems, Inc. Integrity Level: MEDIUM Description: Vbox Trial Client DLL Exit code: 0 Version: 4,6,1,32 Modules
| |||||||||||||||
| 1936 | RUNDLL32 C:\PROGRA~1\COMMON~1\Vbox\Common\vboxr.dll,PowerPL /M | C:\Windows\system32\RUNDLL32.exe | — | vboxm.dll | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2136 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Common Files\Vbox\Common\vboxm.dll" -PF0FE218FCC7DA301 | C:\Program Files\Common Files\Vbox\Common\vboxm.dll | ACDSee32.exe | ||||||||||||
User: admin Company: Preview Systems, Inc. Integrity Level: MEDIUM Description: Vbox Trial Client DLL Exit code: 0 Version: 4,6,1,32 Modules
| |||||||||||||||
| 2544 | "C:\Windows\Installer\MSI8AD.tmp" | C:\Windows\Installer\MSI8AD.tmp | msiexec.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2656 | C:\Windows\system32\RUNDLL32.exe C:\PROGRA~1\COMMON~1\Vbox\Common\vboxr.dll,PowerPL /R00000790 | C:\Windows\system32\RUNDLL32.exe | — | RUNDLL32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2700 | C:\Windows\System32\svchost.exe -k WerSvcGroup | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2776 | C:\Windows\system32\MsiExec.exe -Embedding CF89E9E156DCC09959DF32220596BB6E | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 520
Read events
1 689
Write events
814
Delete events
17
Modification events
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\2.44 Pynffvp_npqfrr244.rkr |
Value: 000000000000000000000000350C0000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000680000009C0000008B1C46001000000033000000218616007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000000000000A0E57600FFFFFFFF70DB3A00FFFFFFFF70599D7500000000000000003CE57600857599750004000000000000A0E57600FFFFFFFF70DB3A00FFFFFFFFD0333B00D4343B0068DB3A006CE576002FB14E7680B08176ACF27600381E4F7614634F76A0173800A0E57600B87A390070000000BD0EB51780E57600BE6A4F76A0173800A0E5760000000000ACE776006F624F76A0173800A0E5760000000400000000807C624F76A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E00670011000000483D3800403D380073006F00660074005C00690064E600002D0EB51768E60000D50DB5171CE6760082914F7668E67600E4080000C90DB51730E67600B69C4F76E80823024C06000048E6760011000000483D3800403D38000000000040B0817648E6760078042302B8E60000810DB51768E6760082914F76B8E676006CE6760027954F7600000000E408230294E67600CD944F76E408230240E7760058042302E1944F76000000005804230240E776009CE676001000000033000000218616007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000000000000A0E57600FFFFFFFF70DB3A00FFFFFFFF70599D7500000000000000003CE57600857599750004000000000000A0E57600FFFFFFFF70DB3A00FFFFFFFFD0333B00D4343B0068DB3A006CE576002FB14E7680B08176ACF27600381E4F7614634F76A0173800A0E57600B87A390070000000BD0EB51780E57600BE6A4F76A0173800A0E5760000000000ACE776006F624F76A0173800A0E5760000000400000000807C624F76A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E00670011000000483D3800403D380073006F00660074005C00690064E600002D0EB51768E60000D50DB5171CE6760082914F7668E67600E4080000C90DB51730E67600B69C4F76E80823024C06000048E6760011000000483D3800403D38000000000040B0817648E6760078042302B8E60000810DB51768E6760082914F76B8E676006CE6760027954F7600000000E408230294E67600CD944F76E408230240E7760058042302E1944F76000000005804230240E776009CE676001000000033000000218616007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000000000000A0E57600FFFFFFFF70DB3A00FFFFFFFF70599D7500000000000000003CE57600857599750004000000000000A0E57600FFFFFFFF70DB3A00FFFFFFFFD0333B00D4343B0068DB3A006CE576002FB14E7680B08176ACF27600381E4F7614634F76A0173800A0E57600B87A390070000000BD0EB51780E57600BE6A4F76A0173800A0E5760000000000ACE776006F624F76A0173800A0E5760000000400000000807C624F76A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E00670011000000483D3800403D380073006F00660074005C00690064E600002D0EB51768E60000D50DB5171CE6760082914F7668E67600E4080000C90DB51730E67600B69C4F76E80823024C06000048E6760011000000483D3800403D38000000000040B0817648E6760078042302B8E60000810DB51768E6760082914F76B8E676006CE6760027954F7600000000E408230294E67600CD944F76E408230240E7760058042302E1944F76000000005804230240E776009CE67600 | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | Zvpebfbsg.Jvaqbjf.JvaqbjfVafgnyyre |
Value: 000000000000000000000000DF020000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (392) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000680000009C000000D41D46001000000033000000218616007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000000000000A0E57600FFFFFFFF70DB3A00FFFFFFFF70599D7500000000000000003CE57600857599750004000000000000A0E57600FFFFFFFF70DB3A00FFFFFFFFD0333B00D4343B0068DB3A006CE576002FB14E7680B08176ACF27600381E4F7614634F76A0173800A0E57600B87A390070000000BD0EB51780E57600BE6A4F76A0173800A0E5760000000000ACE776006F624F76A0173800A0E5760000000400000000807C624F76A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E00670011000000483D3800403D380073006F00660074005C00690064E600002D0EB51768E60000D50DB5171CE6760082914F7668E67600E4080000C90DB51730E67600B69C4F76E80823024C06000048E6760011000000483D3800403D38000000000040B0817648E6760078042302B8E60000810DB51768E6760082914F76B8E676006CE6760027954F7600000000E408230294E67600CD944F76E408230240E7760058042302E1944F76000000005804230240E776009CE676001000000033000000218616007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000000000000A0E57600FFFFFFFF70DB3A00FFFFFFFF70599D7500000000000000003CE57600857599750004000000000000A0E57600FFFFFFFF70DB3A00FFFFFFFFD0333B00D4343B0068DB3A006CE576002FB14E7680B08176ACF27600381E4F7614634F76A0173800A0E57600B87A390070000000BD0EB51780E57600BE6A4F76A0173800A0E5760000000000ACE776006F624F76A0173800A0E5760000000400000000807C624F76A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E00670011000000483D3800403D380073006F00660074005C00690064E600002D0EB51768E60000D50DB5171CE6760082914F7668E67600E4080000C90DB51730E67600B69C4F76E80823024C06000048E6760011000000483D3800403D38000000000040B0817648E6760078042302B8E60000810DB51768E6760082914F76B8E676006CE6760027954F7600000000E408230294E67600CD944F76E408230240E7760058042302E1944F76000000005804230240E776009CE676001000000033000000218616007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E00650078006500000000000000A0E57600FFFFFFFF70DB3A00FFFFFFFF70599D7500000000000000003CE57600857599750004000000000000A0E57600FFFFFFFF70DB3A00FFFFFFFFD0333B00D4343B0068DB3A006CE576002FB14E7680B08176ACF27600381E4F7614634F76A0173800A0E57600B87A390070000000BD0EB51780E57600BE6A4F76A0173800A0E5760000000000ACE776006F624F76A0173800A0E5760000000400000000807C624F76A017380063003A005C00750073006500720073005C00610064006D0069006E005C0061007000700064006100740061005C0072006F0061006D0069006E00670011000000483D3800403D380073006F00660074005C00690064E600002D0EB51768E60000D50DB5171CE6760082914F7668E67600E4080000C90DB51730E67600B69C4F76E80823024C06000048E6760011000000483D3800403D38000000000040B0817648E6760078042302B8E60000810DB51768E6760082914F76B8E676006CE6760027954F7600000000E408230294E67600CD944F76E408230240E7760058042302E1944F76000000005804230240E776009CE67600 | |||
| (PID) Process: | (2136) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000B236A87BC3A7D60158080000640C0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2136) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000B236A87BC3A7D60158080000640C0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2136) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 43 | |||
| (PID) Process: | (2136) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000004CE4F67BC3A7D60158080000640C0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2136) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000A646F97BC3A7D60158080000F00A0000E80300000100000000000000000000006B10A102C5A66A44905746966CA1008C0000000000000000 | |||
| (PID) Process: | (872) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\WMI Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D0BB0E7CC3A7D601680300009C0B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
13
Suspicious files
11
Text files
15
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3208 | 2.44 Classic_acdsee244.exe | C:\Users\admin\AppData\Local\Temp\~41D0.tmp | — | |
MD5:— | SHA256:— | |||
| 2136 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2136 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF79B6CA5A7D1BB0B0.TMP | — | |
MD5:— | SHA256:— | |||
| 3536 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 2136 | msiexec.exe | C:\Windows\Installer\MSI8AD.tmp | — | |
MD5:— | SHA256:— | |||
| 872 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 3208 | 2.44 Classic_acdsee244.exe | C:\Users\admin\AppData\Local\Temp\_is41E1\_ISMSIDEL.INI | text | |
MD5:— | SHA256:— | |||
| 2544 | MSI8AD.tmp | C:\Program Files\Common Files\Vbox\Licenses\ACDSee Classic_2.44_B5E3.lic | text | |
MD5:— | SHA256:— | |||
| 2136 | msiexec.exe | C:\Windows\Installer\2dfb5c.msi | executable | |
MD5:— | SHA256:— | |||
| 2544 | MSI8AD.tmp | C:\Program Files\Common Files\Vbox\Common\vboxm.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
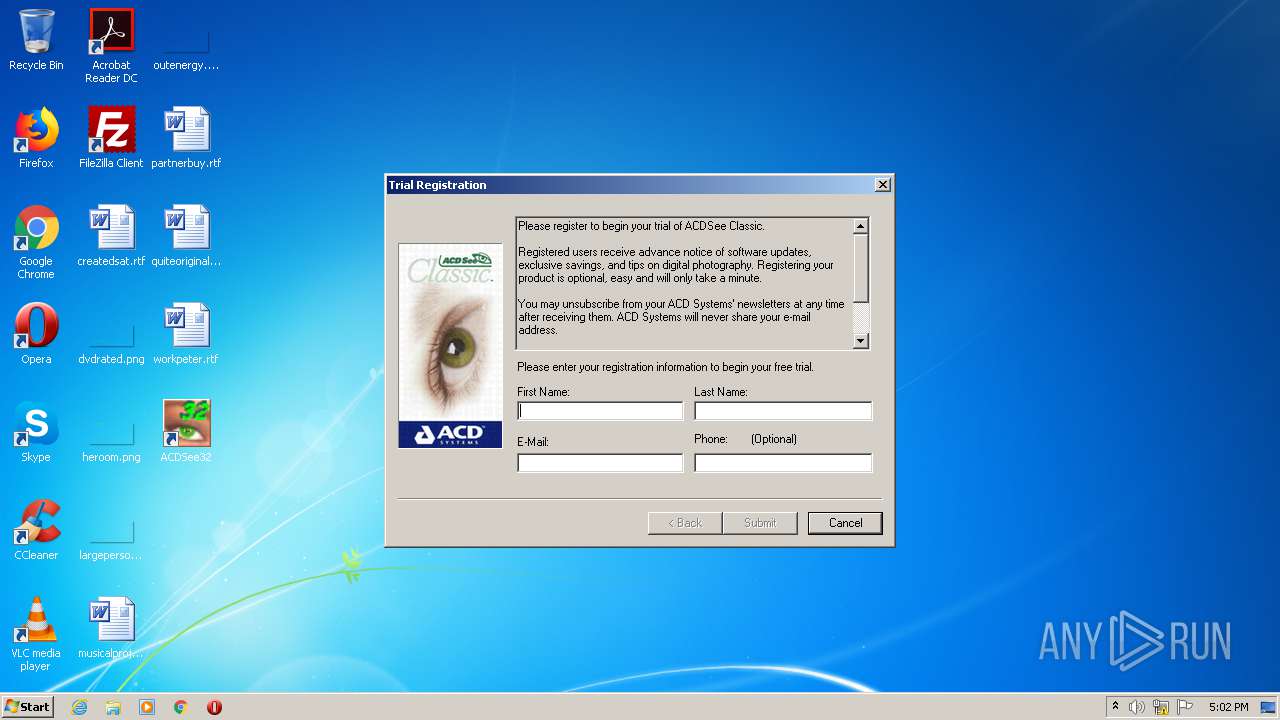
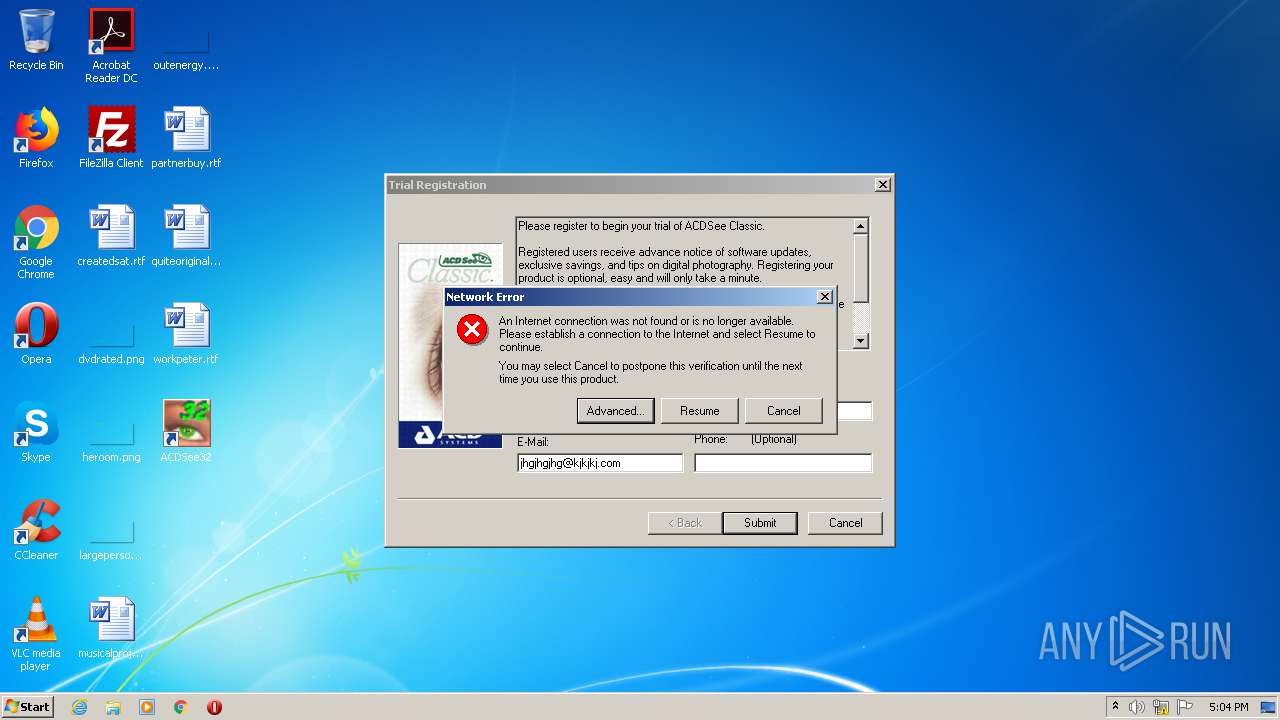
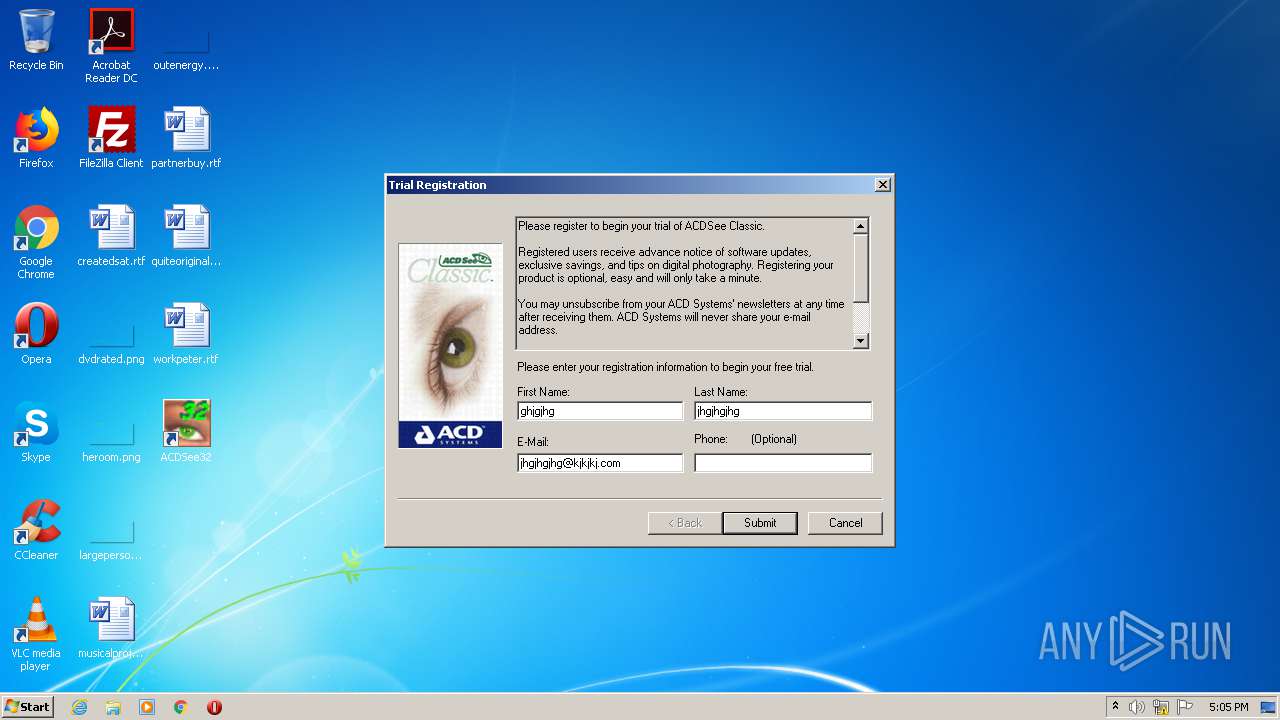
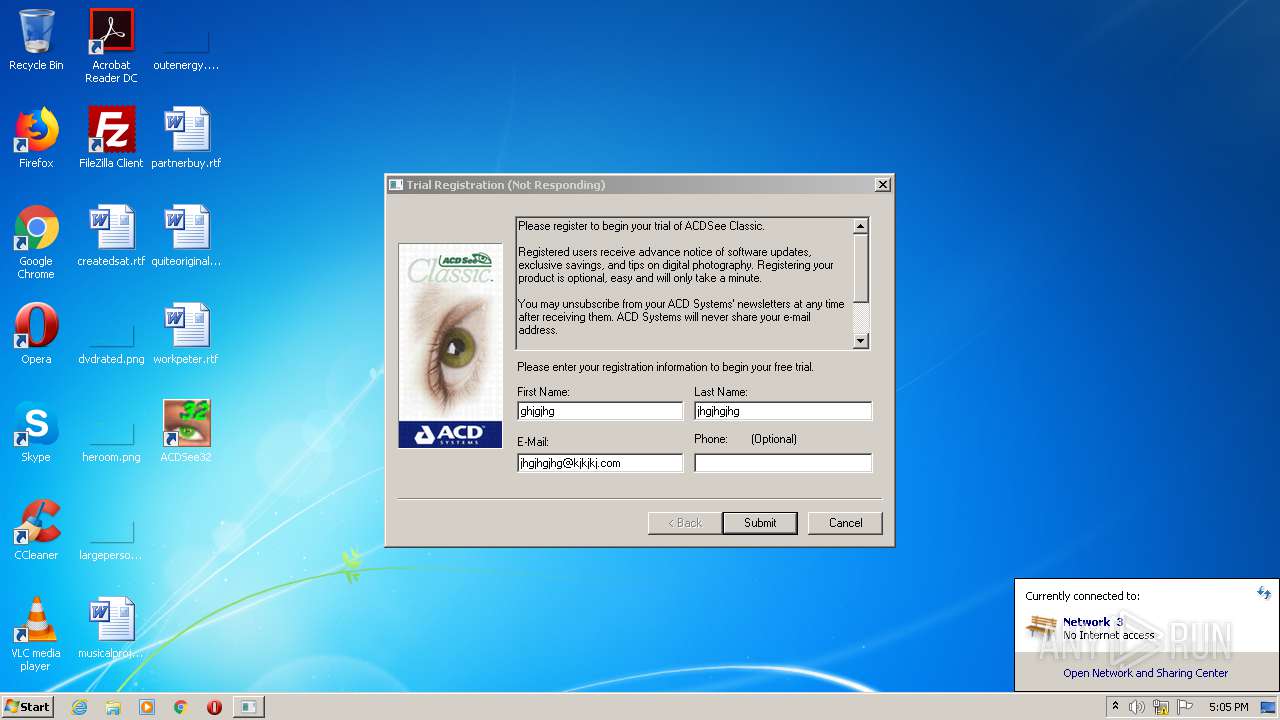
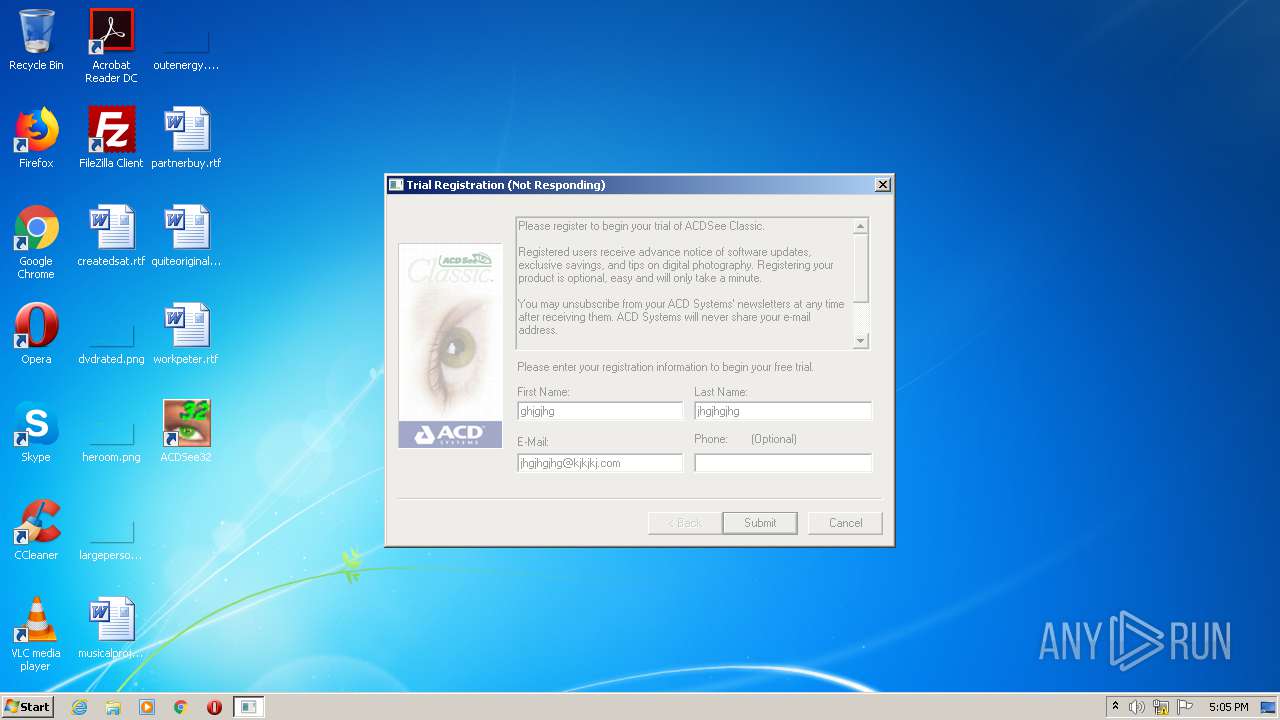
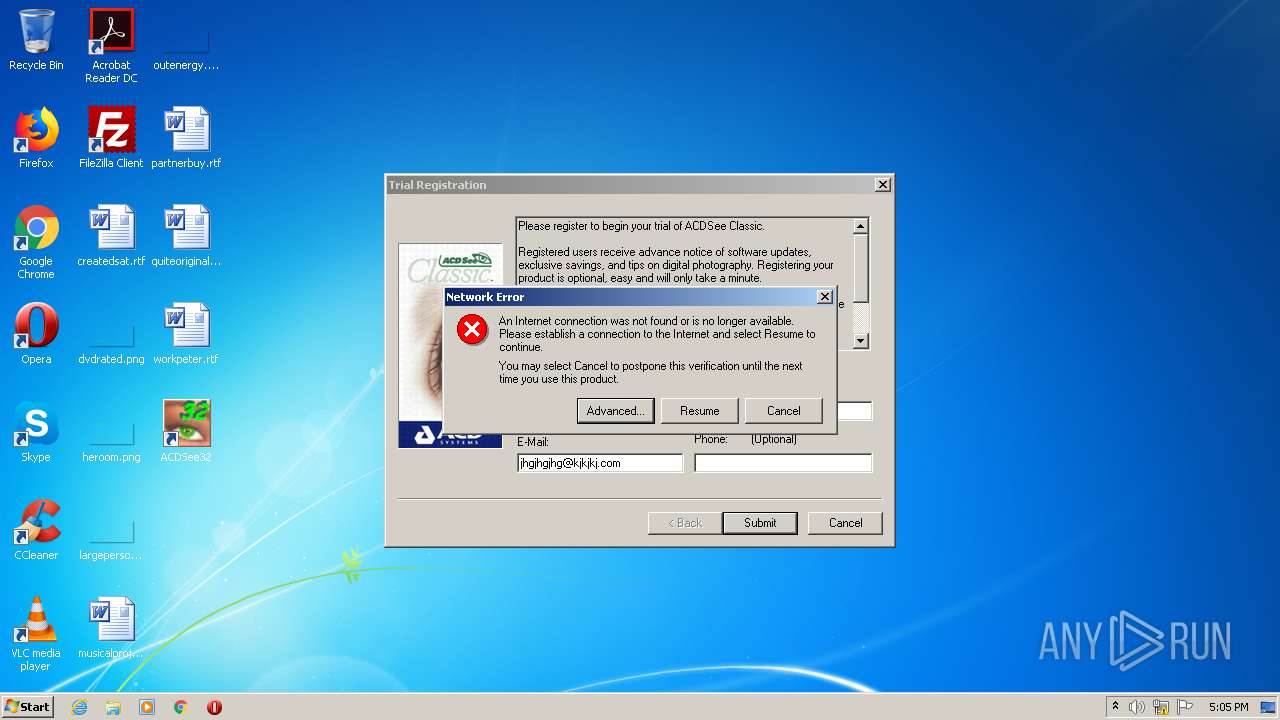
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2480 | vboxm.dll | POST | — | 198.107.2.175:80 | http://198.107.2.175:80/trial_reg/trial_reg.pl | US | — | — | unknown |
1092 | vboxm.dll | POST | — | 198.107.2.175:80 | http://198.107.2.175:80/trial_reg/trial_reg.pl | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1092 | vboxm.dll | 198.107.2.175:80 | — | NTT America, Inc. | US | unknown |
2480 | vboxm.dll | 198.107.2.175:80 | — | NTT America, Inc. | US | unknown |