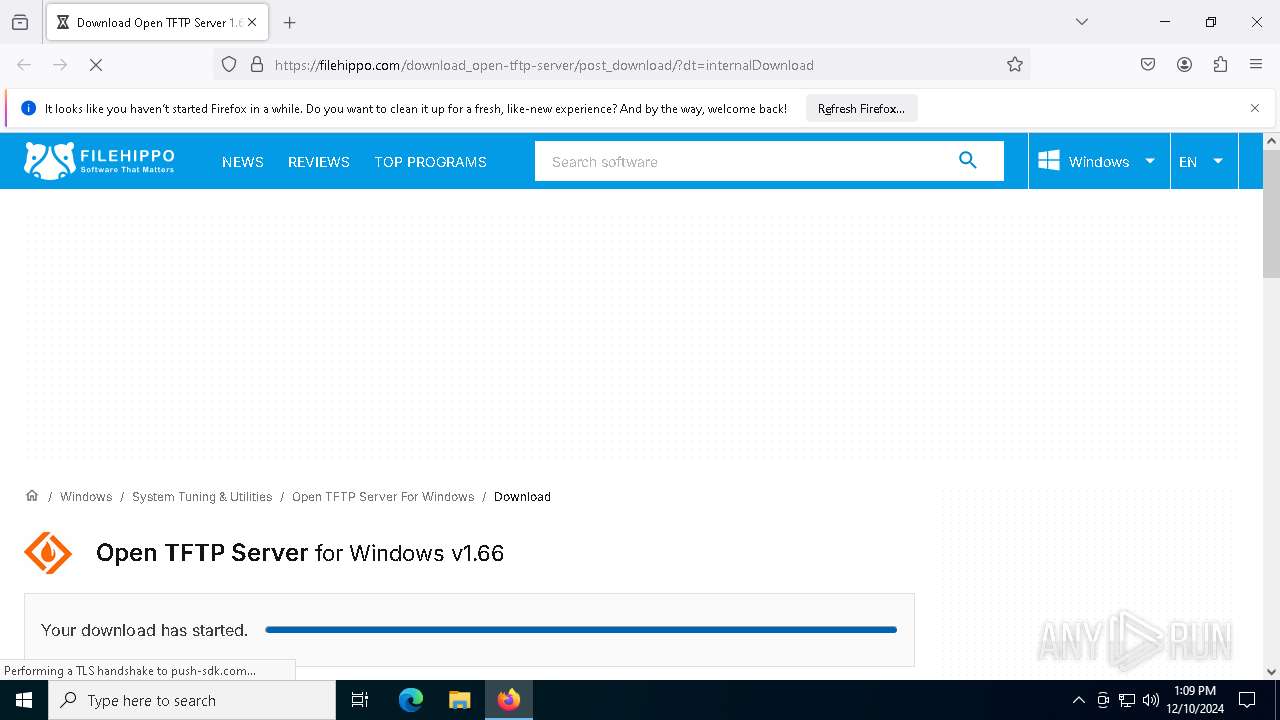
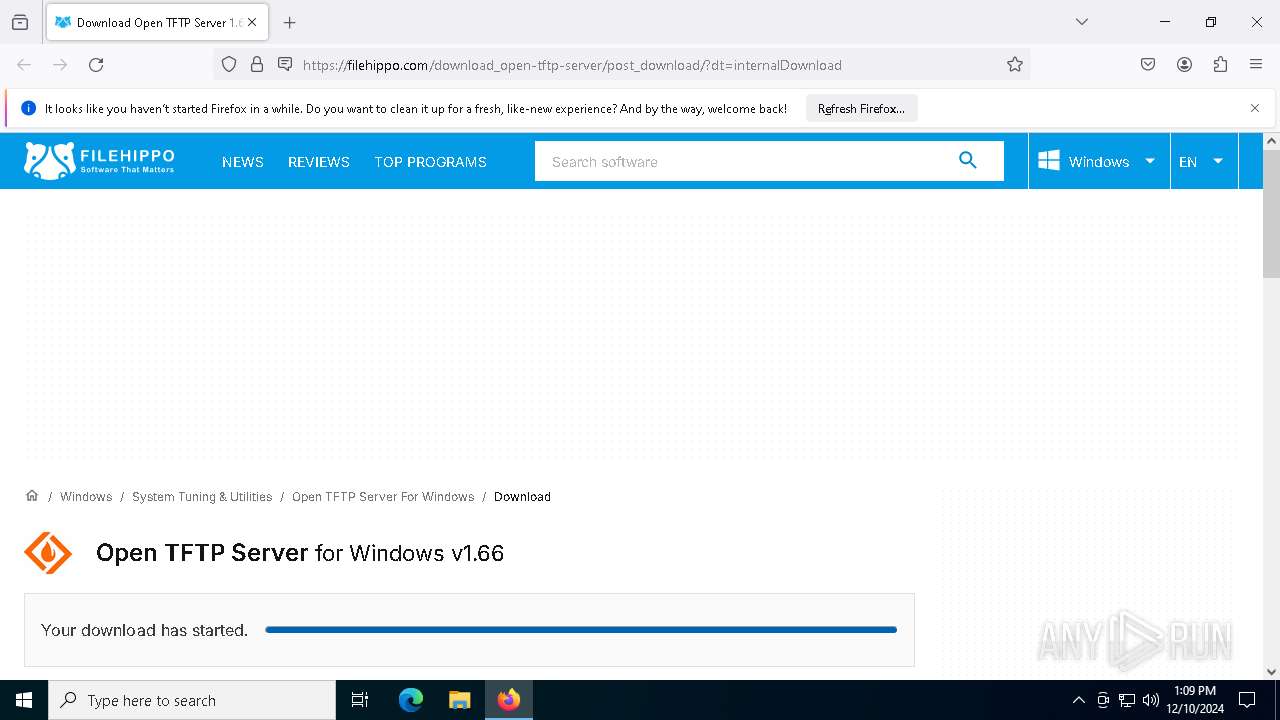
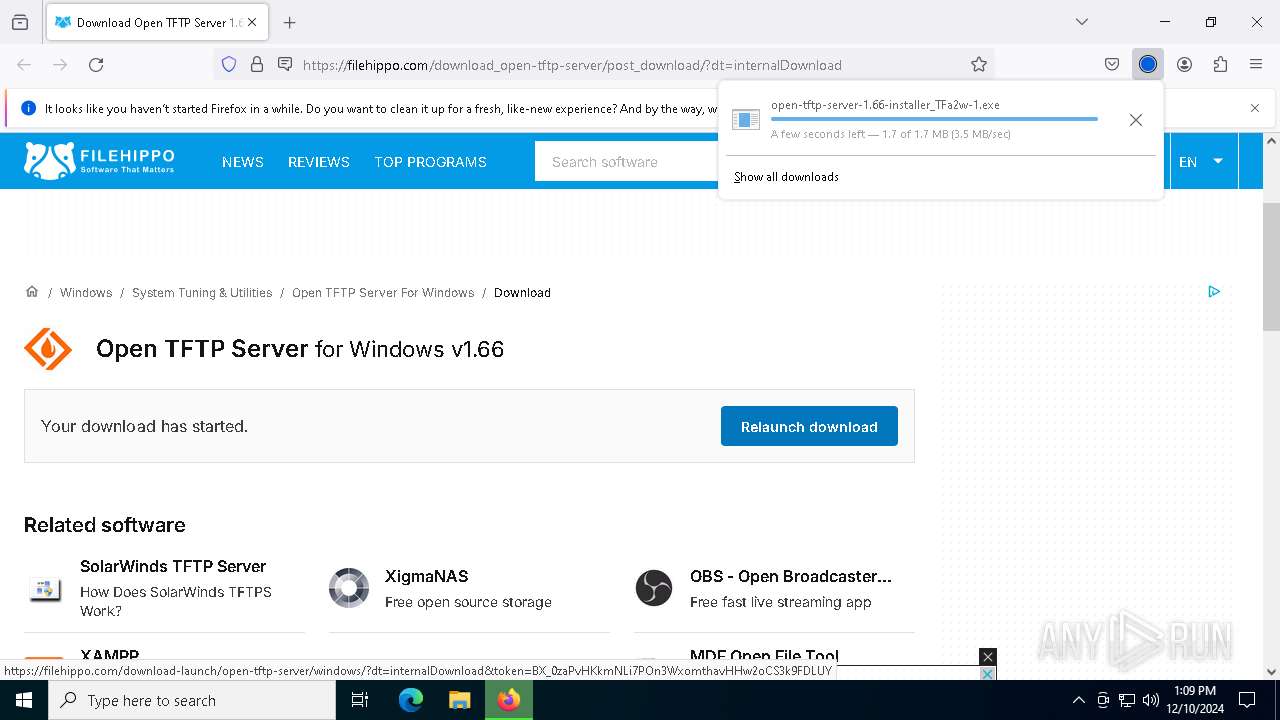
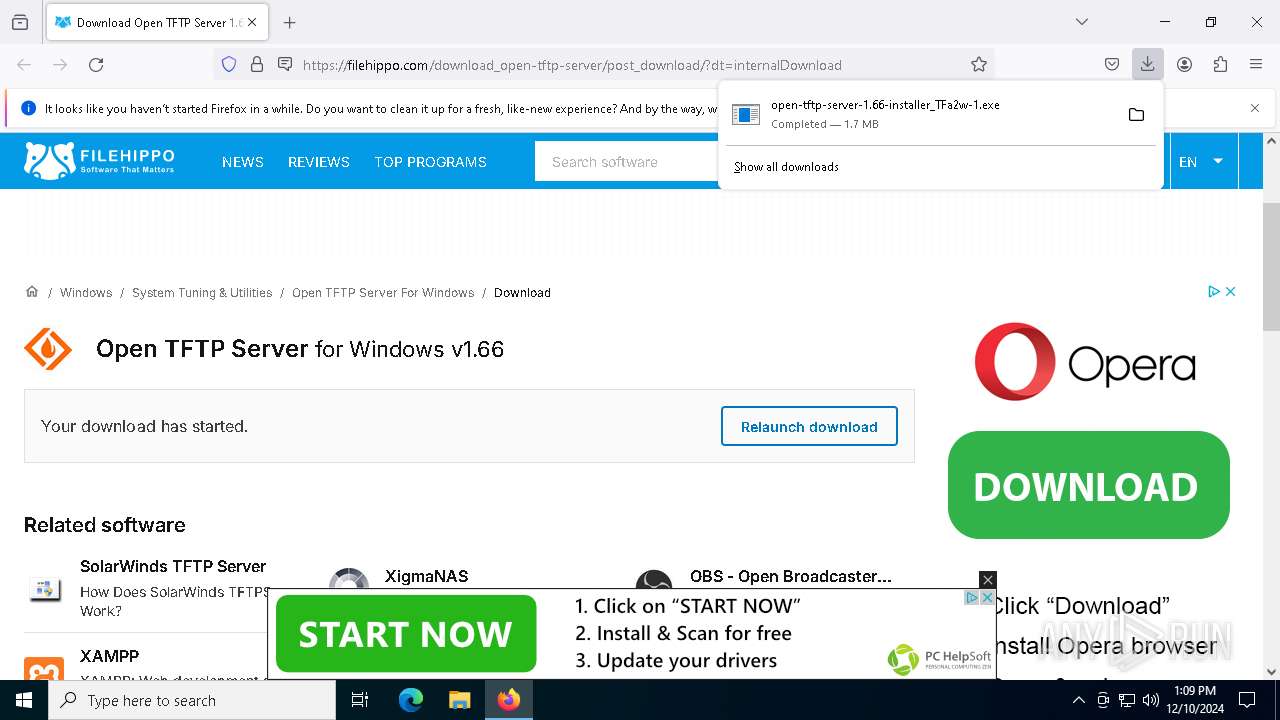
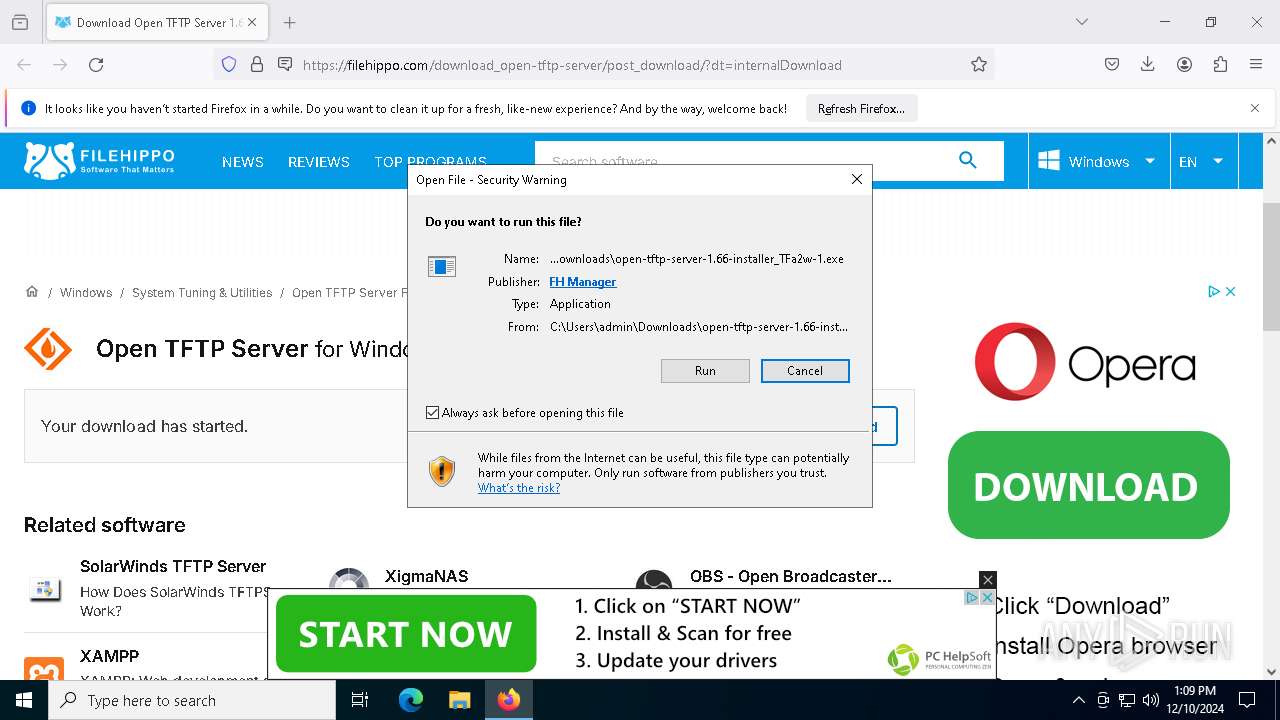
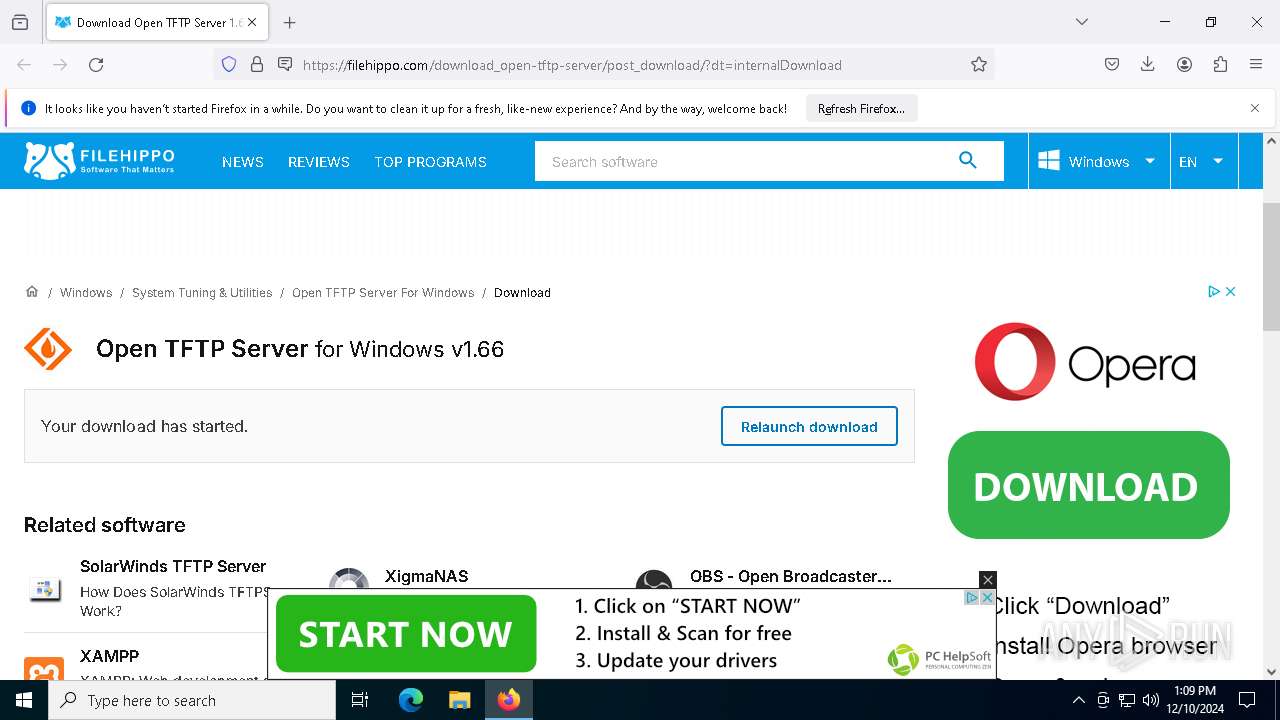
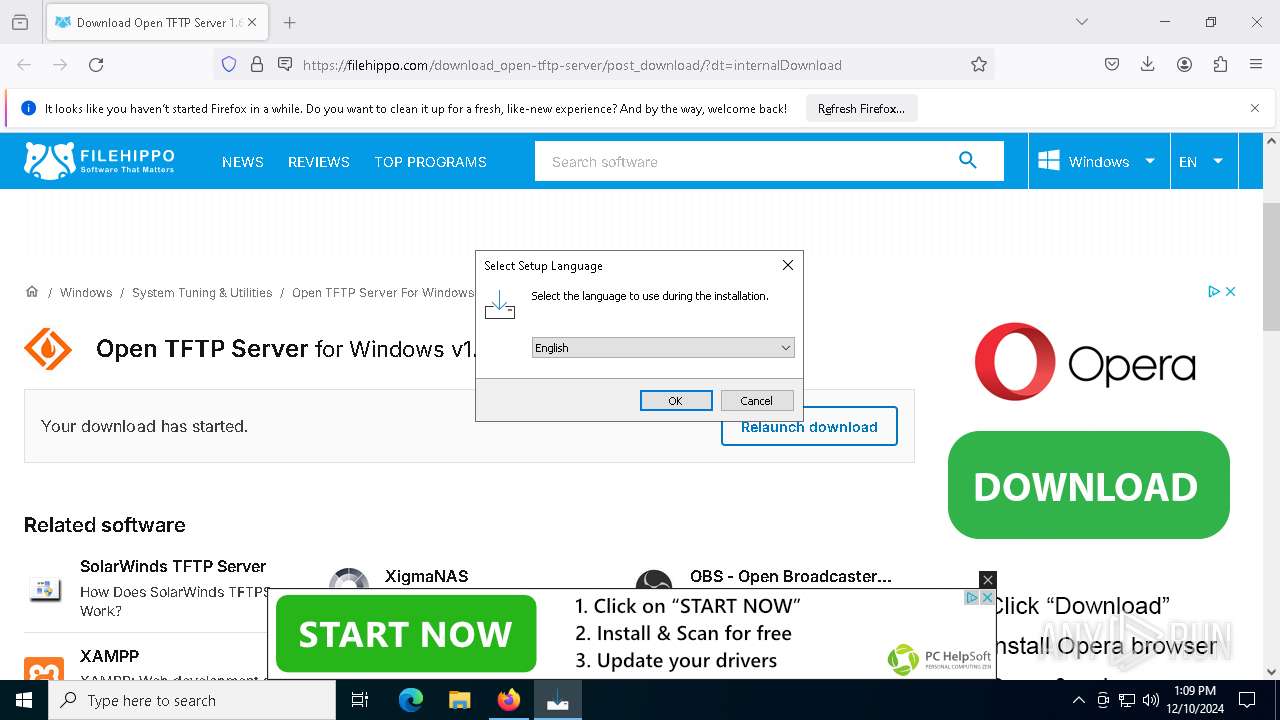
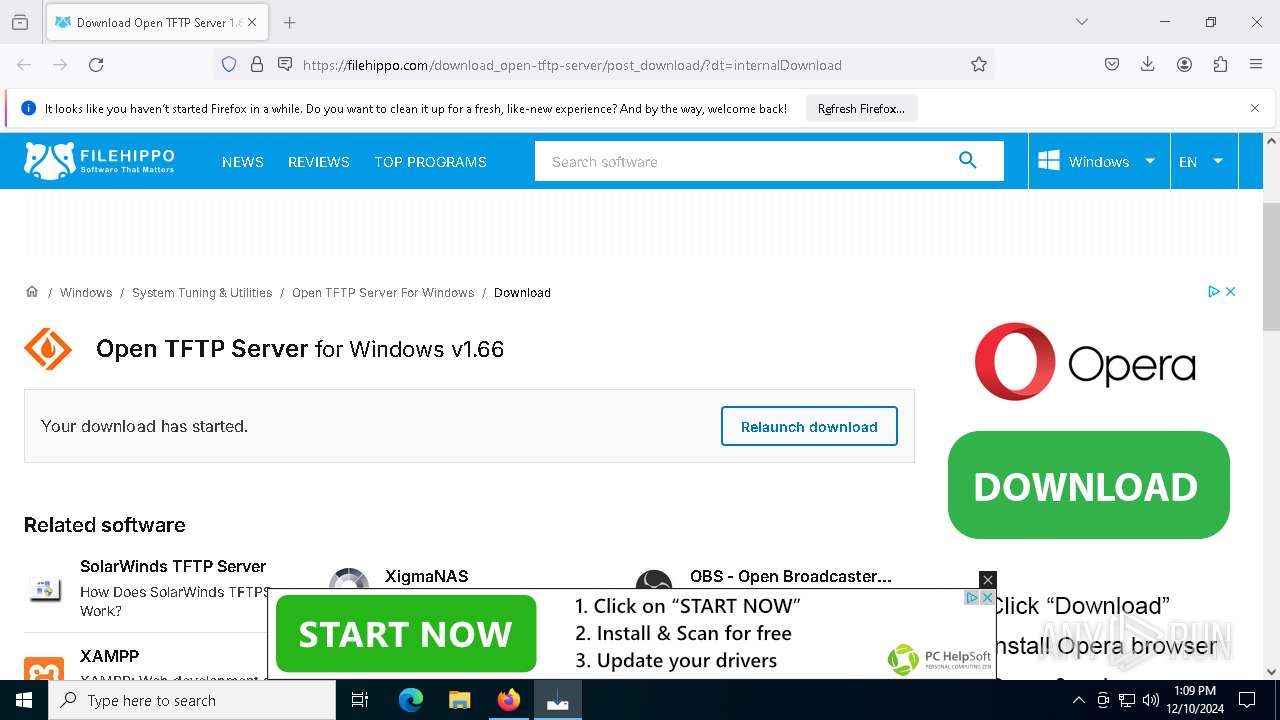
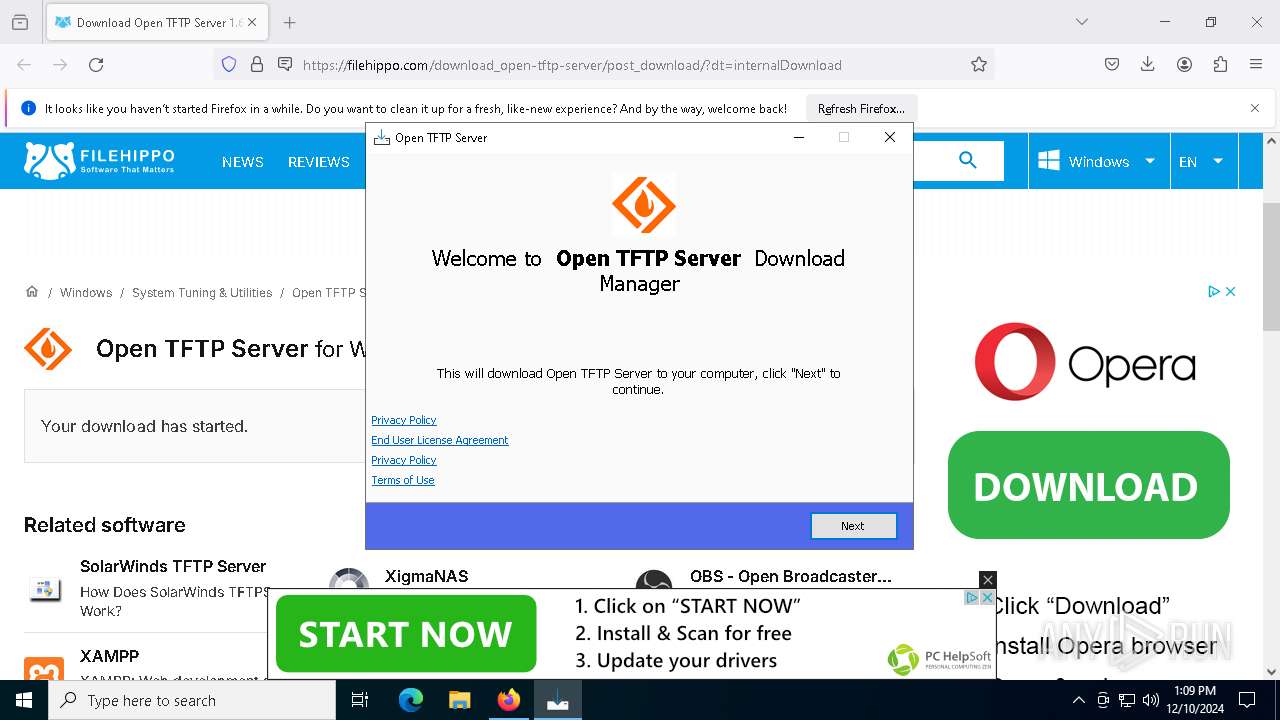
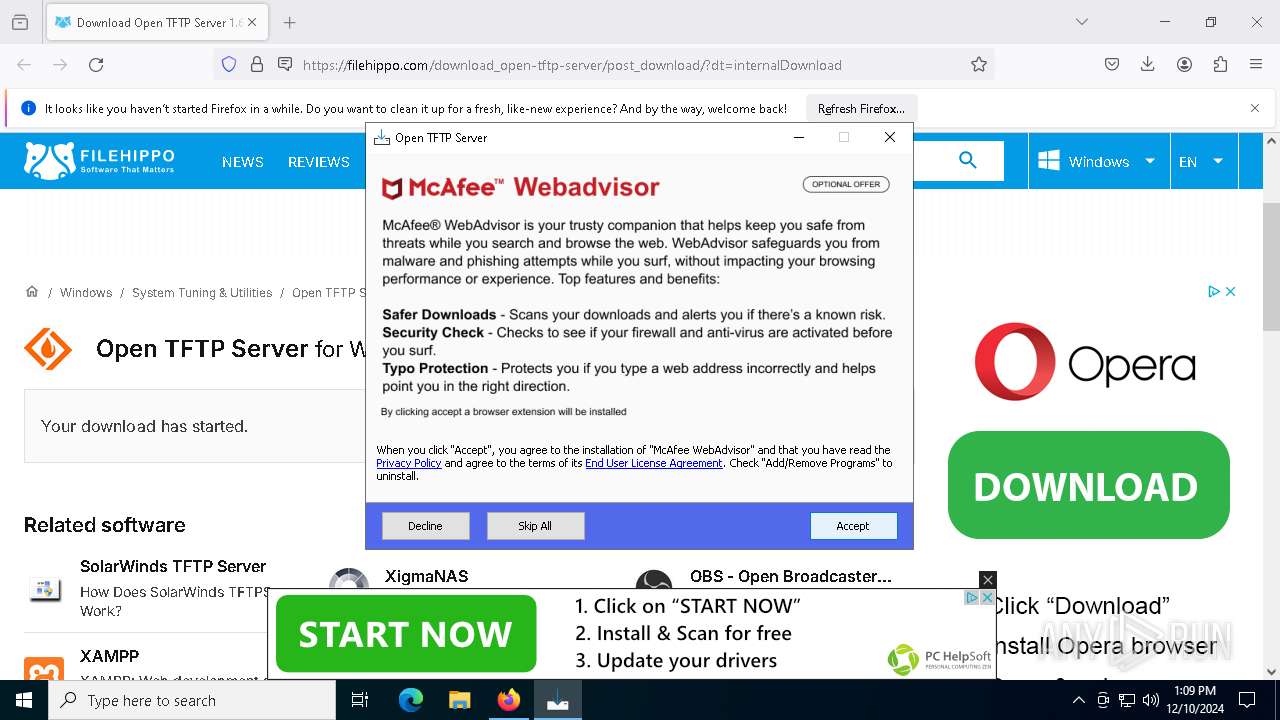
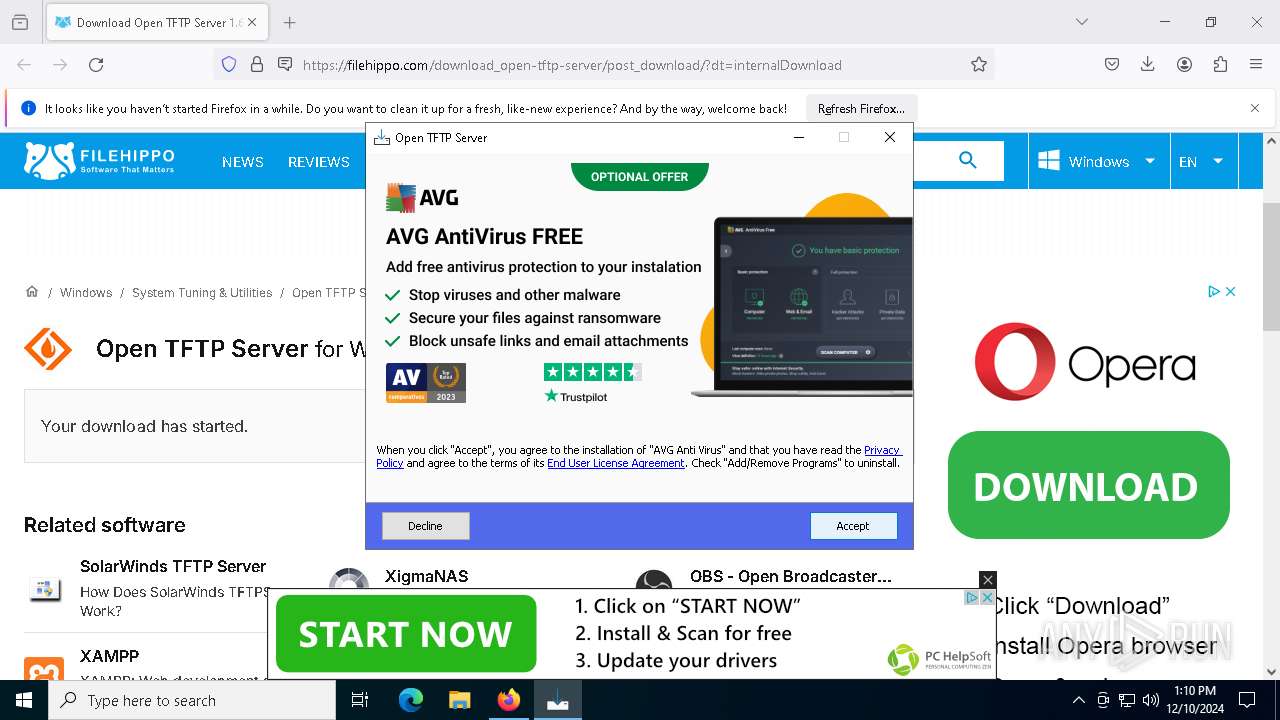
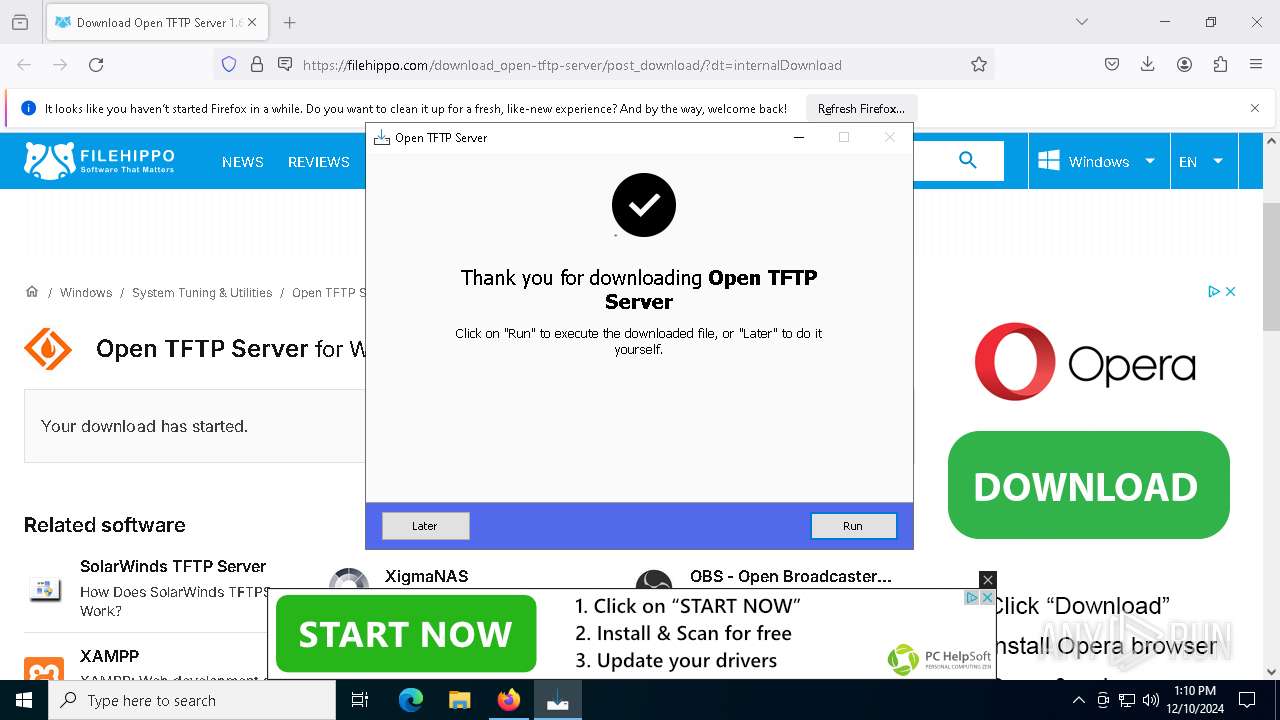
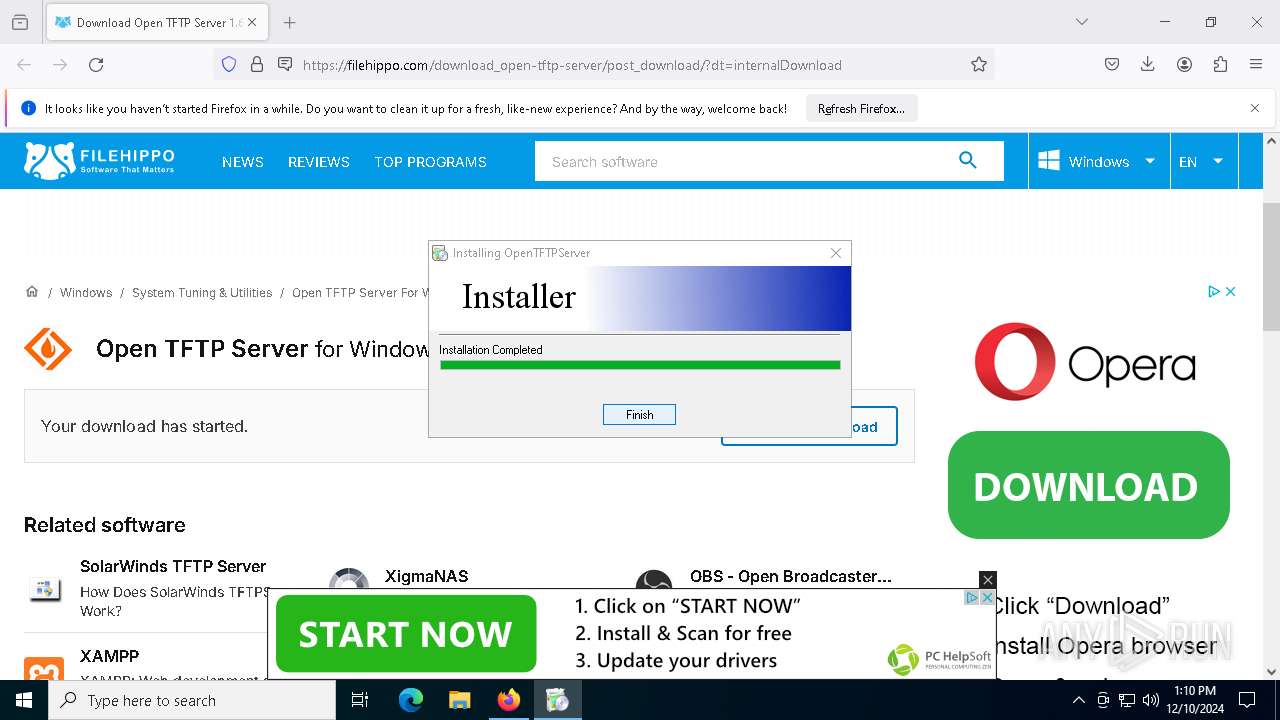
| URL: | https://filehippo.com/download_open-tftp-server/post_download/?dt=internalDownload |
| Full analysis: | https://app.any.run/tasks/79dafce3-c5b2-4031-bc9b-ed02d8928907 |
| Verdict: | Malicious activity |
| Analysis date: | December 10, 2024, 13:09:32 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F0F51A494494D4DE2F77F13DBD39C8FA |
| SHA1: | 8A0A6BBB2CD5B4C0FBCF8EBF3513BD7DFFC8593B |
| SHA256: | FF9125856E6A3342C8908B92A42A514E2B47A7277C1FEDDEFF3ABAF47274D499 |
| SSDEEP: | 3:N8KpKM7vANK6Wx4maThJLJfB:2KkMrAzWStThzfB |
MALICIOUS
No malicious indicators.SUSPICIOUS
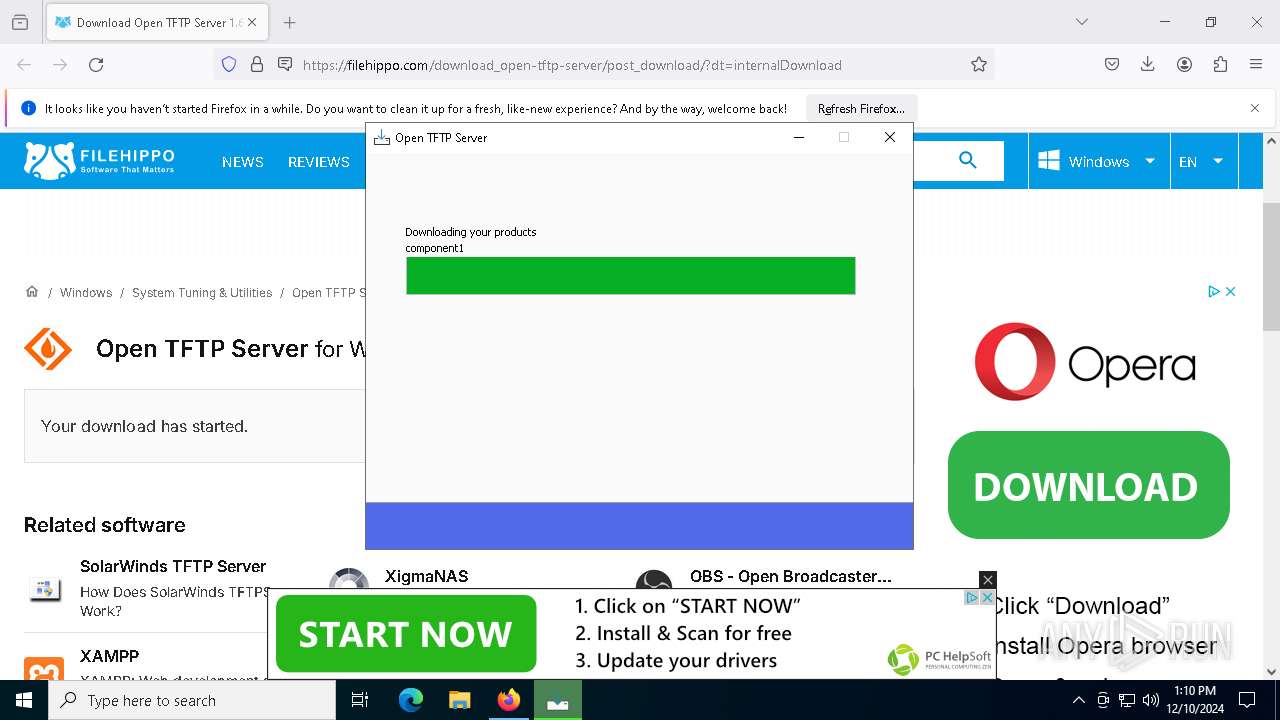
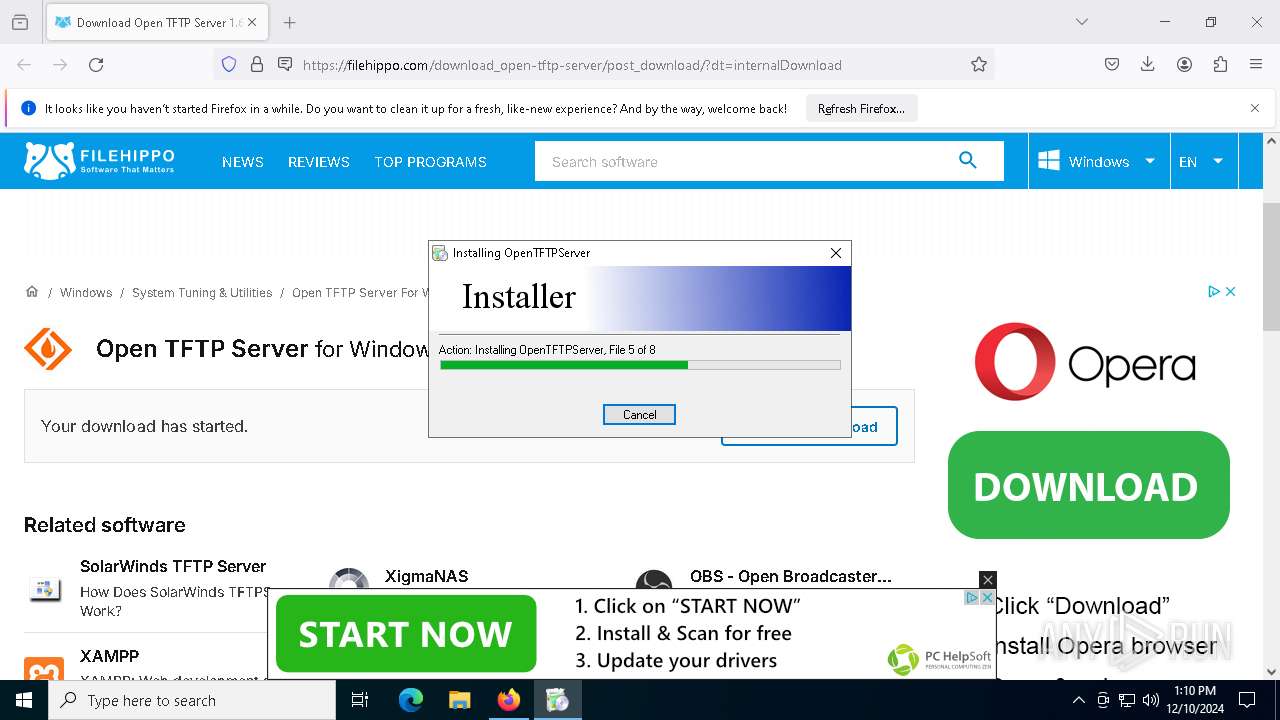
Executable content was dropped or overwritten
- open-tftp-server-1.66-installer_TFa2w-1.exe (PID: 3928)
- open-tftp-server-1.66-installer_TFa2w-1.exe (PID: 7224)
- open-tftp-server-1.66-installer_TFa2w-1.tmp (PID: 7364)
- open-tftp-server-1.66-installer.exe (PID: 5556)
- icarus.exe (PID: 4592)
- saBSI.exe (PID: 7268)
- avg_antivirus_free_setup.exe (PID: 440)
- avg_antivirus_free_online_setup.exe (PID: 7896)
- icarus.exe (PID: 2220)
- installer.exe (PID: 7400)
- installer.exe (PID: 5972)
Reads security settings of Internet Explorer
- open-tftp-server-1.66-installer_TFa2w-1.tmp (PID: 7264)
- open-tftp-server-1.66-installer_TFa2w-1.tmp (PID: 7364)
- installer.exe (PID: 7400)
Starts itself from another location
- icarus.exe (PID: 4592)
Executes application which crashes
- open-tftp-server-1.66-installer_TFa2w-1.tmp (PID: 7364)
Checks Windows Trust Settings
- installer.exe (PID: 7400)
Process drops legitimate windows executable
- icarus.exe (PID: 2220)
The process drops C-runtime libraries
- icarus.exe (PID: 2220)
Creates/Modifies COM task schedule object
- installer.exe (PID: 7400)
INFO
Process checks computer location settings
- open-tftp-server-1.66-installer_TFa2w-1.tmp (PID: 7264)
Application launched itself
- firefox.exe (PID: 6436)
- firefox.exe (PID: 6364)
Checks supported languages
- open-tftp-server-1.66-installer_TFa2w-1.tmp (PID: 7364)
- OpenTFTPServerMTInstallService.exe (PID: 5000)
- icarus.exe (PID: 3280)
- open-tftp-server-1.66-installer_TFa2w-1.tmp (PID: 7264)
The sample compiled with english language support
- open-tftp-server-1.66-installer_TFa2w-1.tmp (PID: 7364)
- saBSI.exe (PID: 7268)
- icarus.exe (PID: 4592)
- avg_antivirus_free_setup.exe (PID: 440)
- avg_antivirus_free_online_setup.exe (PID: 7896)
- icarus.exe (PID: 2220)
- installer.exe (PID: 7400)
- installer.exe (PID: 5972)
Reads the software policy settings
- open-tftp-server-1.66-installer_TFa2w-1.tmp (PID: 7364)
Reads the machine GUID from the registry
- saBSI.exe (PID: 7268)
- icarus.exe (PID: 4592)
- installer.exe (PID: 7400)
Sends debugging messages
- saBSI.exe (PID: 7268)
- installer.exe (PID: 7400)
Reads the computer name
- icarus.exe (PID: 3280)
Reads CPU info
- icarus.exe (PID: 3280)
Executable content was dropped or overwritten
- firefox.exe (PID: 6436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
162
Monitored processes
32
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Users\admin\AppData\Local\Temp\is-HU53N.tmp\component1_extract\avg_antivirus_free_setup.exe" /silent /ws /psh:92pTu5hwB2YIiy0fyEE6ldULU0Qm7w2f5ooou3M2ZSWOuq6sopKQdRLY0Jkk1ytdDCEx5jlM1GSQtc | C:\Users\admin\AppData\Local\Temp\is-HU53N.tmp\component1_extract\avg_antivirus_free_setup.exe | open-tftp-server-1.66-installer_TFa2w-1.tmp | ||||||||||||
User: admin Company: AVG Technologies CZ, s.r.o. Integrity Level: HIGH Description: AVG Installer Version: 2.1.99.0 Modules
| |||||||||||||||
| 2220 | C:\WINDOWS\Temp\asw-ecd8e808-3816-4d61-a2f6-ac4e23dfba2c\avg-av\icarus.exe /silent /ws /psh:92pTu5hwB2YIiy0fyEE6ldULU0Qm7w2f5ooou3M2ZSWOuq6sopKQdRLY0Jkk1ytdDCEx5jlM1GSQtc /cookie:mmm_irs_ppi_902_451_o /edat_dir:C:\WINDOWS\Temp\asw.06801671035523a9 /track-guid:339878fe-4ce5-4b20-a355-595e7c2ecc2c /er_master:master_ep_ad242a4c-a8b4-4db3-a6c2-444c91c95336 /er_ui:ui_ep_5052c3bc-6674-4786-80c8-ae530881f99a /er_slave:avg-av_slave_ep_1abd7e8d-f1a3-45a2-9b7a-29bfe84cb510 /slave:avg-av | C:\Windows\Temp\asw-ecd8e808-3816-4d61-a2f6-ac4e23dfba2c\avg-av\icarus.exe | icarus.exe | ||||||||||||
User: admin Company: Gen Digital Inc. Integrity Level: HIGH Description: AVG Installer Version: 24.12.8365.0 Modules
| |||||||||||||||
| 3060 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | OpenTFTPServerMTInstallService.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3080 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6360 -childID 10 -isForBrowser -prefsHandle 3980 -prefMapHandle 6400 -prefsLen 31197 -prefMapSize 244583 -jsInitHandle 1308 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {0a8a04a2-7d1d-4993-a7bc-d59eab01751f} 6436 "\\.\pipe\gecko-crash-server-pipe.6436" 24008a26310 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 3280 | C:\WINDOWS\Temp\asw-ecd8e808-3816-4d61-a2f6-ac4e23dfba2c\avg-av-vps\icarus.exe /silent /ws /psh:92pTu5hwB2YIiy0fyEE6ldULU0Qm7w2f5ooou3M2ZSWOuq6sopKQdRLY0Jkk1ytdDCEx5jlM1GSQtc /cookie:mmm_irs_ppi_902_451_o /edat_dir:C:\WINDOWS\Temp\asw.06801671035523a9 /track-guid:339878fe-4ce5-4b20-a355-595e7c2ecc2c /er_master:master_ep_ad242a4c-a8b4-4db3-a6c2-444c91c95336 /er_ui:ui_ep_5052c3bc-6674-4786-80c8-ae530881f99a /er_slave:avg-av-vps_slave_ep_53b8b002-610e-44ef-b05c-911477965019 /slave:avg-av-vps | C:\Windows\Temp\asw-ecd8e808-3816-4d61-a2f6-ac4e23dfba2c\avg-av-vps\icarus.exe | — | icarus.exe | |||||||||||
User: admin Company: Gen Digital Inc. Integrity Level: HIGH Description: AVG Installer Version: 24.12.8365.0 Modules
| |||||||||||||||
| 3928 | "C:\Users\admin\Downloads\open-tftp-server-1.66-installer_TFa2w-1.exe" | C:\Users\admin\Downloads\open-tftp-server-1.66-installer_TFa2w-1.exe | firefox.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: FH Manager Exit code: 3221226525 Version: 12.11.2371.8174 Modules
| |||||||||||||||
| 4592 | C:\WINDOWS\Temp\asw-ecd8e808-3816-4d61-a2f6-ac4e23dfba2c\common\icarus.exe /icarus-info-path:C:\WINDOWS\Temp\asw-ecd8e808-3816-4d61-a2f6-ac4e23dfba2c\icarus-info.xml /install /silent /ws /psh:92pTu5hwB2YIiy0fyEE6ldULU0Qm7w2f5ooou3M2ZSWOuq6sopKQdRLY0Jkk1ytdDCEx5jlM1GSQtc /cookie:mmm_irs_ppi_902_451_o /edat_dir:C:\WINDOWS\Temp\asw.06801671035523a9 /track-guid:339878fe-4ce5-4b20-a355-595e7c2ecc2c | C:\Windows\Temp\asw-ecd8e808-3816-4d61-a2f6-ac4e23dfba2c\common\icarus.exe | avg_antivirus_free_online_setup.exe | ||||||||||||
User: admin Company: Gen Digital Inc. Integrity Level: HIGH Description: AVG Installer Version: 24.12.8365.0 Modules
| |||||||||||||||
| 5000 | C:\OpenTFTPServer\OpenTFTPServerMTInstallService.exe | C:\OpenTFTPServer\OpenTFTPServerMTInstallService.exe | — | open-tftp-server-1.66-installer.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 5556 | "C:\Users\admin\Downloads\open-tftp-server-1.66-installer.exe" | C:\Users\admin\Downloads\open-tftp-server-1.66-installer.exe | open-tftp-server-1.66-installer_TFa2w-1.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 5836 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7364 -s 1008 | C:\Windows\SysWOW64\WerFault.exe | open-tftp-server-1.66-installer_TFa2w-1.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
36 635
Read events
36 576
Write events
54
Delete events
5
Modification events
| (PID) Process: | (6436) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (6436) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (7364) open-tftp-server-1.66-installer_TFa2w-1.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\Component Categories\{56FFCC30-D398-11D0-B2AE-00A0C908FA49}\Enum |
| Operation: | write | Name: | Implementing |
Value: 1C00000001000000E8070C0002000A000D000A000400F000010000001E768127E028094199FEB9D127C57AFE | |||
| (PID) Process: | (7364) open-tftp-server-1.66-installer_TFa2w-1.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 010000000000000020C6C6D3044BDB01 | |||
| (PID) Process: | (7268) saBSI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\McAfee\WebAdvisor |
| Operation: | write | Name: | UUID |
Value: {2AEB6E50-D888-4AED-B0C1-42461C624701} | |||
| (PID) Process: | (7268) saBSI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\McAfee\WebAdvisor |
| Operation: | write | Name: | InstallerFlags |
Value: 1 | |||
| (PID) Process: | (7896) avg_antivirus_free_online_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\1D0EC6DE-4A80-4CC3-A335-E6E41C951198 |
| Operation: | write | Name: | 5FD38555-4B16-40AE-9A09-E2C969CB74AF |
Value: F6D4F52220BB5A3D7246A004278BB23F | |||
| (PID) Process: | (7896) avg_antivirus_free_online_setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\C06AEB9D-8774-46E7-8160-8321BCD14D9F |
| Operation: | write | Name: | 7CCD586D-2ABC-42FF-A23B-3731F4F183D9 |
Value: F6D4F52220BB5A3D7246A004278BB23F | |||
| (PID) Process: | (7268) saBSI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\McAfee\WebAdvisor |
| Operation: | write | Name: | InstallationStatus |
Value: PENDING | |||
| (PID) Process: | (7268) saBSI.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\McAfee\WebAdvisor |
| Operation: | write | Name: | InstallationID |
Value: UNDEFINED | |||
Executable files
289
Suspicious files
338
Text files
908
Unknown types
35
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6436 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 6436 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6436 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 6436 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db-journal | binary | |
MD5:4D03E5CF36568DCD3F1D813F8249317B | SHA256:EA83C8F26DDFAF670964128796F1919387FF522DEE74D95E4186FC5D8795558F | |||
| 6436 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6436 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6436 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6436 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6436 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 6436 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
67
TCP/UDP connections
232
DNS requests
234
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
6436 | firefox.exe | POST | 200 | 142.250.185.99:80 | http://o.pki.goog/wr2 | US | binary | 472 b | whitelisted |
6436 | firefox.exe | POST | 200 | 95.101.54.145:80 | http://r11.o.lencr.org/ | DE | binary | 504 b | whitelisted |
6436 | firefox.exe | POST | 200 | 142.250.185.99:80 | http://o.pki.goog/wr2 | US | binary | 472 b | whitelisted |
6436 | firefox.exe | POST | 200 | 142.250.185.99:80 | http://o.pki.goog/wr2 | US | binary | 472 b | whitelisted |
6436 | firefox.exe | POST | 200 | 2.16.202.120:80 | http://r10.o.lencr.org/ | NL | binary | 504 b | whitelisted |
— | — | GET | 200 | 2.16.164.122:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 314 b | whitelisted |
6436 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | whitelisted |
6436 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1468 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.122:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 2.23.209.183:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6436 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
filehippo.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
Threats
Process | Message |
|---|---|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-HU53N.tmp\component0_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-HU53N.tmp\component0_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-HU53N.tmp\component0_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-HU53N.tmp\component0_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-HU53N.tmp\component0_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-HU53N.tmp\component0_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|