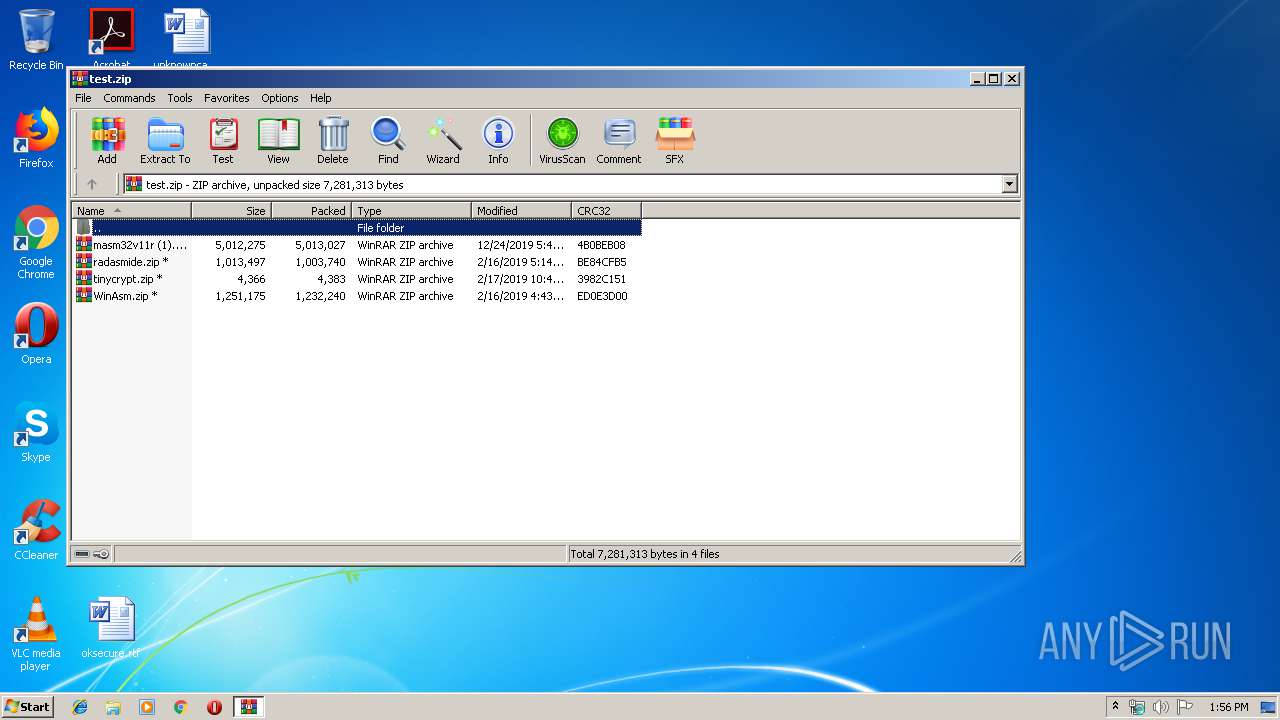
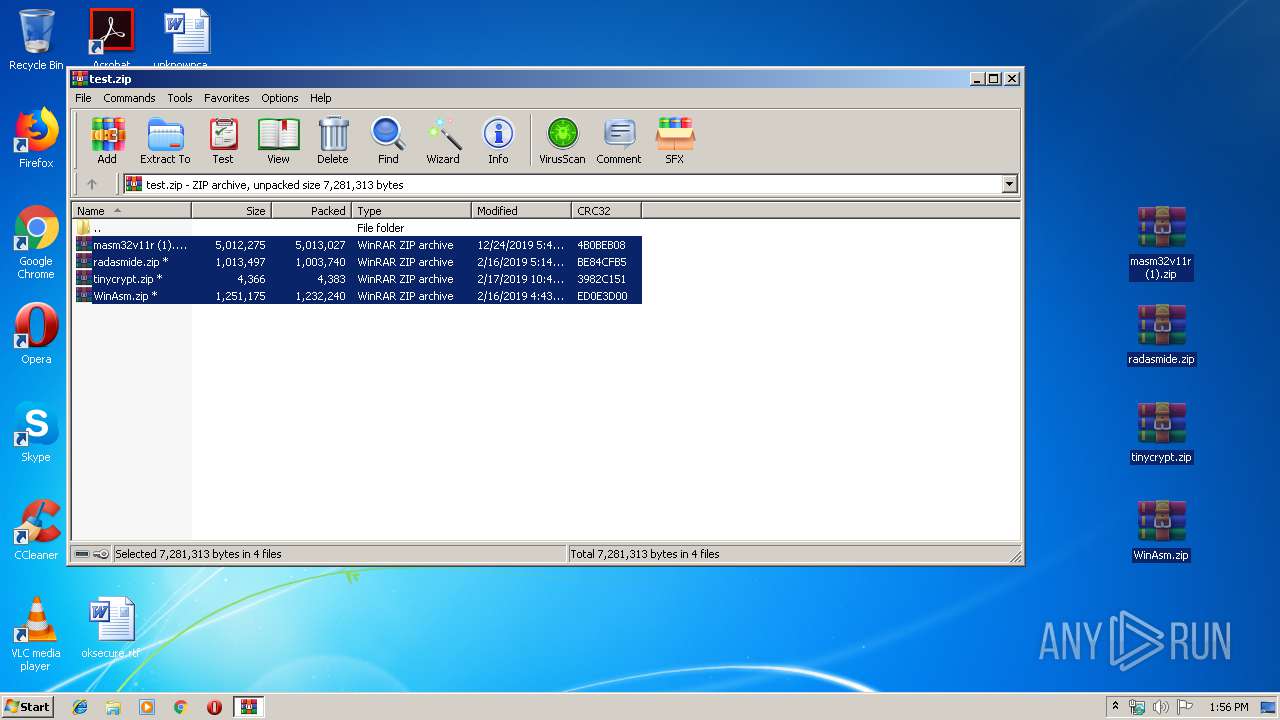
| File name: | test.zip |
| Full analysis: | https://app.any.run/tasks/1188fbbc-58a0-421f-893e-b1d2b0be14d0 |
| Verdict: | Malicious activity |
| Analysis date: | December 25, 2019, 13:55:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 9C5A03357498805EBE2099B4AAC58CE3 |
| SHA1: | AFC8909B5D8D06AD6A5F40DF888332F0FF780D49 |
| SHA256: | FF85BC9AF4DDFA0C9269A848358FD9F4325CF794843CA95EAC9CB7D884A424CC |
| SSDEEP: | 98304:IEO/RNulwWJHdZ2o4yf/+1wiUN1rhJ6qsTirdb7yvbld4Ez997TrVTyQVVeyWlEN:IEcIrayfMwxDJpgxd1p9TxyakvE1q8w2 |
MALICIOUS
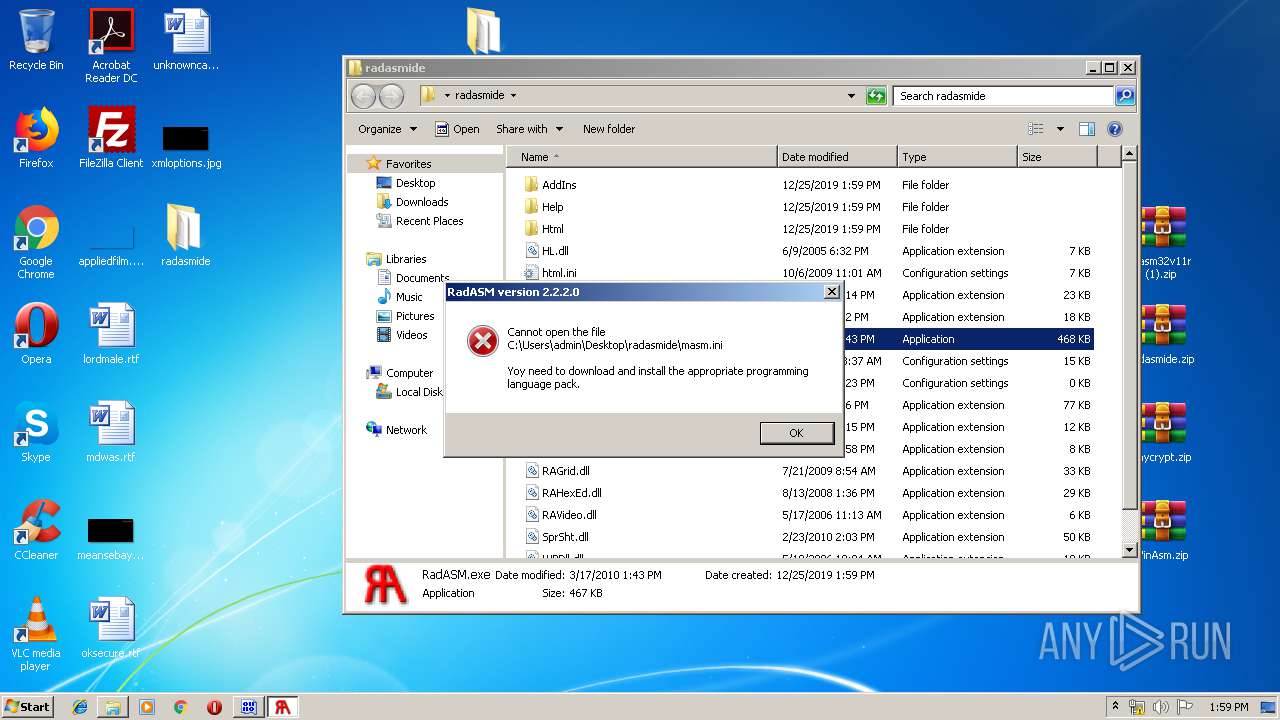
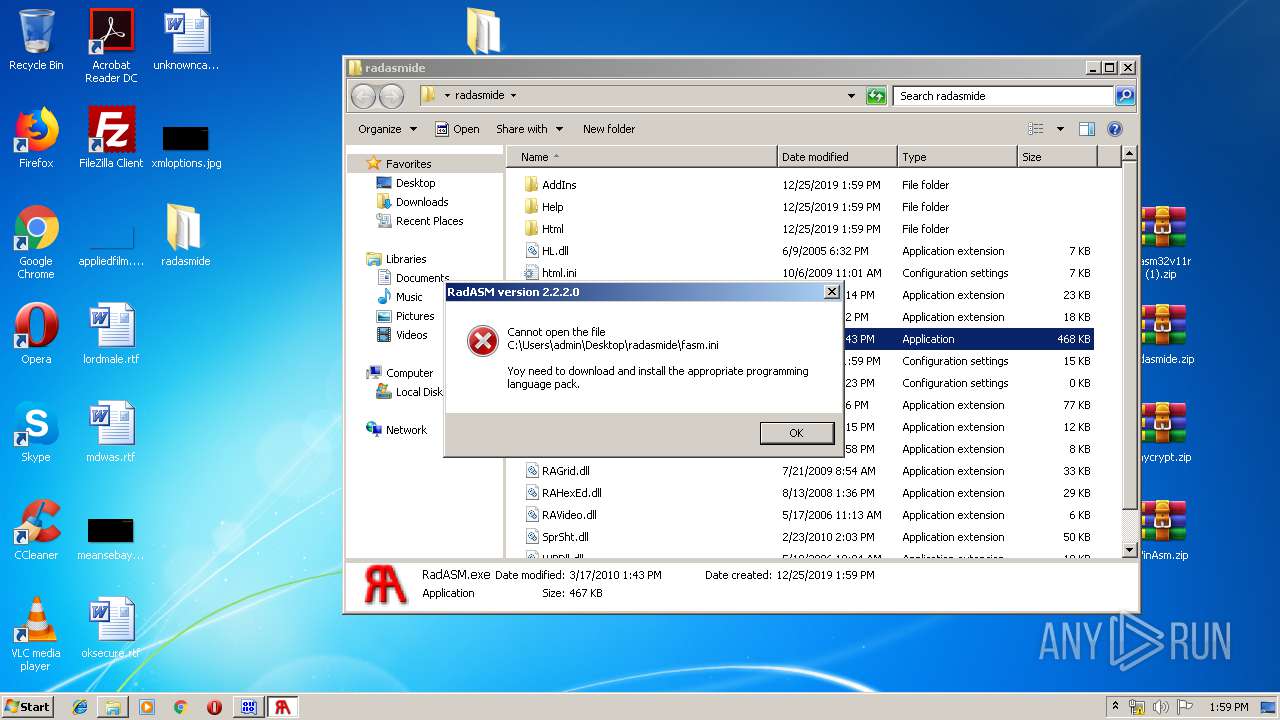
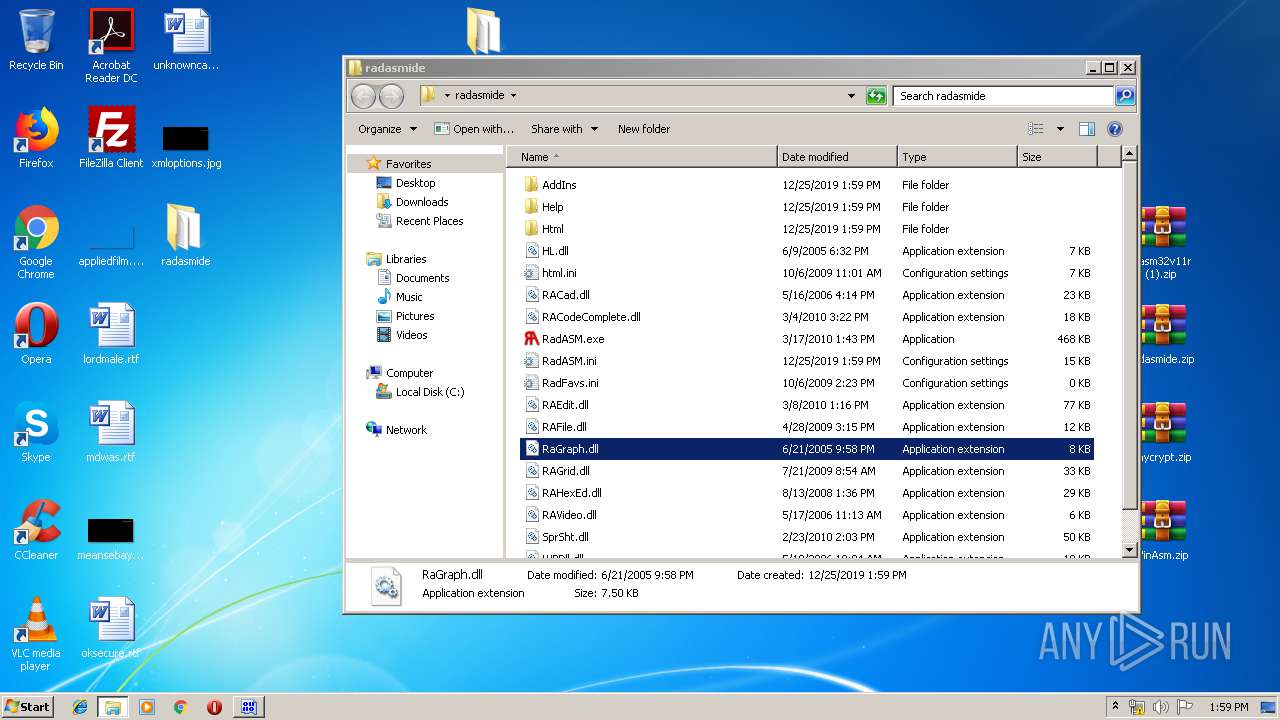
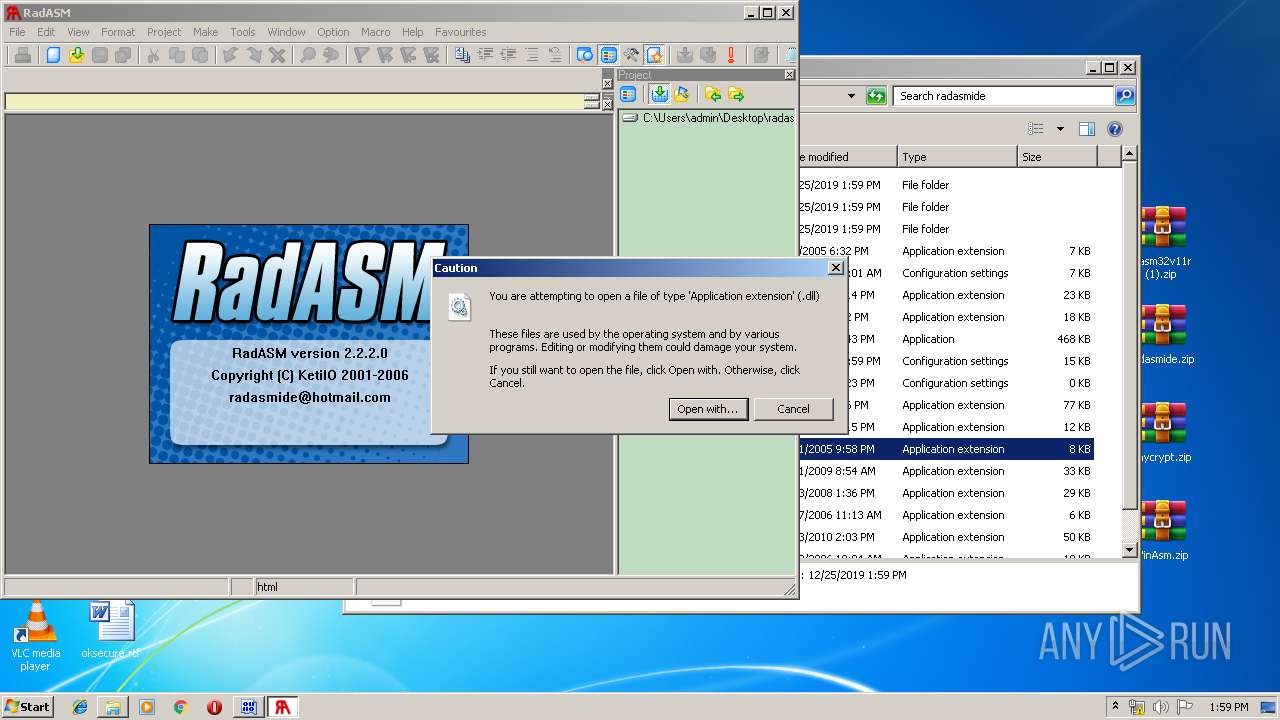
Application was dropped or rewritten from another process
- RadASM.exe (PID: 1712)
- tstexe.exe (PID: 3820)
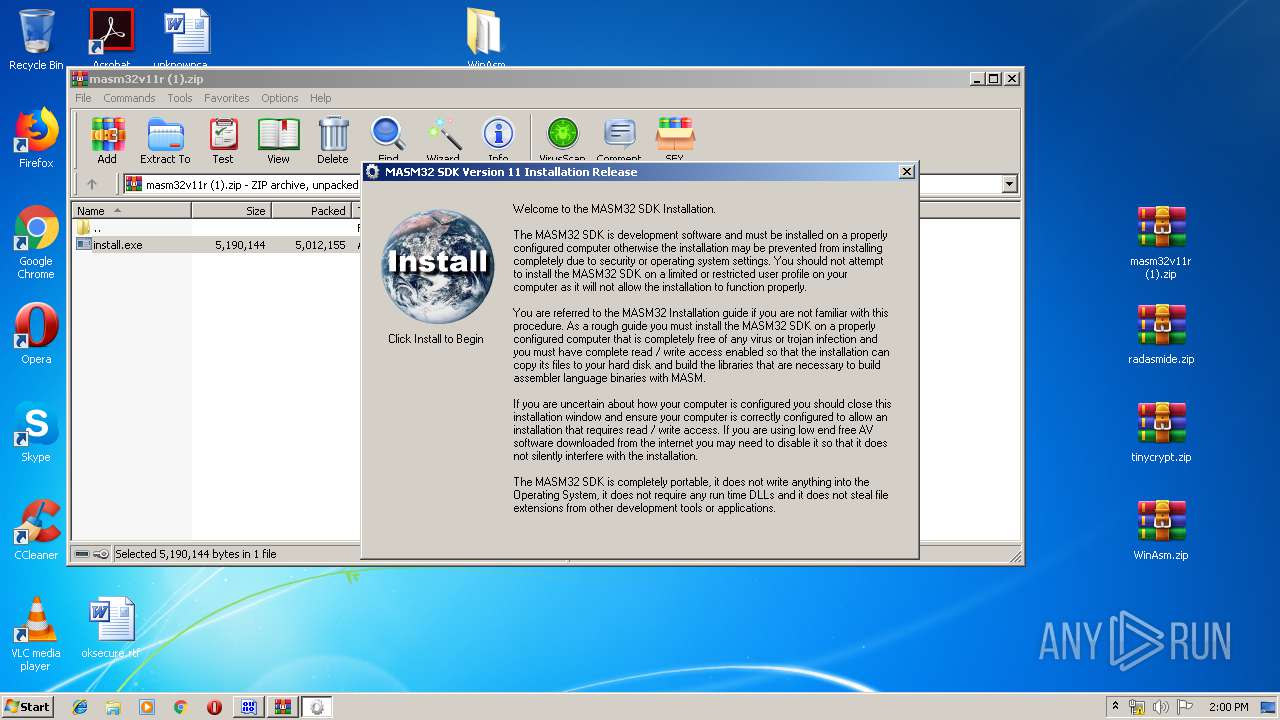
- install.exe (PID: 388)
- masm32ci.exe (PID: 2952)
- install.exe (PID: 3564)
- inc2l.exe (PID: 1708)
- inc2l.exe (PID: 3056)
- inc2l.exe (PID: 940)
- inc2l.exe (PID: 996)
- inc2l.exe (PID: 2188)
- inc2l.exe (PID: 2348)
- inc2l.exe (PID: 2356)
- inc2l.exe (PID: 444)
- inc2l.exe (PID: 3480)
- inc2l.exe (PID: 1036)
- inc2l.exe (PID: 776)
- inc2l.exe (PID: 2308)
- inc2l.exe (PID: 2692)
- inc2l.exe (PID: 4004)
- inc2l.exe (PID: 3168)
- inc2l.exe (PID: 3008)
- inc2l.exe (PID: 2276)
- inc2l.exe (PID: 2584)
- inc2l.exe (PID: 1648)
- inc2l.exe (PID: 3704)
- inc2l.exe (PID: 2244)
- inc2l.exe (PID: 3980)
- inc2l.exe (PID: 1152)
- inc2l.exe (PID: 3868)
- inc2l.exe (PID: 3824)
- Link.exe (PID: 1560)
- Link.exe (PID: 2684)
- inc2l.exe (PID: 2092)
- Link.exe (PID: 4020)
- Link.exe (PID: 2488)
- Link.exe (PID: 2928)
- Link.exe (PID: 3572)
- Link.exe (PID: 3344)
- Link.exe (PID: 3568)
- Link.exe (PID: 1072)
- Link.exe (PID: 2028)
- Link.exe (PID: 2552)
- Link.exe (PID: 1488)
- inc2l.exe (PID: 656)
- inc2l.exe (PID: 3056)
- Link.exe (PID: 2176)
- Link.exe (PID: 3108)
- Link.exe (PID: 2820)
- Link.exe (PID: 2092)
- Link.exe (PID: 600)
- Link.exe (PID: 2808)
- Link.exe (PID: 3308)
- Link.exe (PID: 496)
- Link.exe (PID: 3824)
- Link.exe (PID: 3416)
- Link.exe (PID: 2260)
- Link.exe (PID: 3856)
- Link.exe (PID: 516)
- Link.exe (PID: 3016)
- Link.exe (PID: 2888)
- Link.exe (PID: 1268)
- Link.exe (PID: 2920)
- Link.exe (PID: 2628)
- Link.exe (PID: 2492)
- Link.exe (PID: 3984)
- Link.exe (PID: 2564)
- Link.exe (PID: 4064)
- Link.exe (PID: 1024)
- Link.exe (PID: 940)
- Link.exe (PID: 4060)
- Link.exe (PID: 1648)
- Link.exe (PID: 2820)
- Link.exe (PID: 3236)
- Link.exe (PID: 2500)
- Link.exe (PID: 3336)
- Link.exe (PID: 3640)
- Link.exe (PID: 3496)
- Link.exe (PID: 3296)
- Link.exe (PID: 564)
- Link.exe (PID: 996)
- Link.exe (PID: 2476)
- Link.exe (PID: 3484)
- Link.exe (PID: 2488)
- Link.exe (PID: 2976)
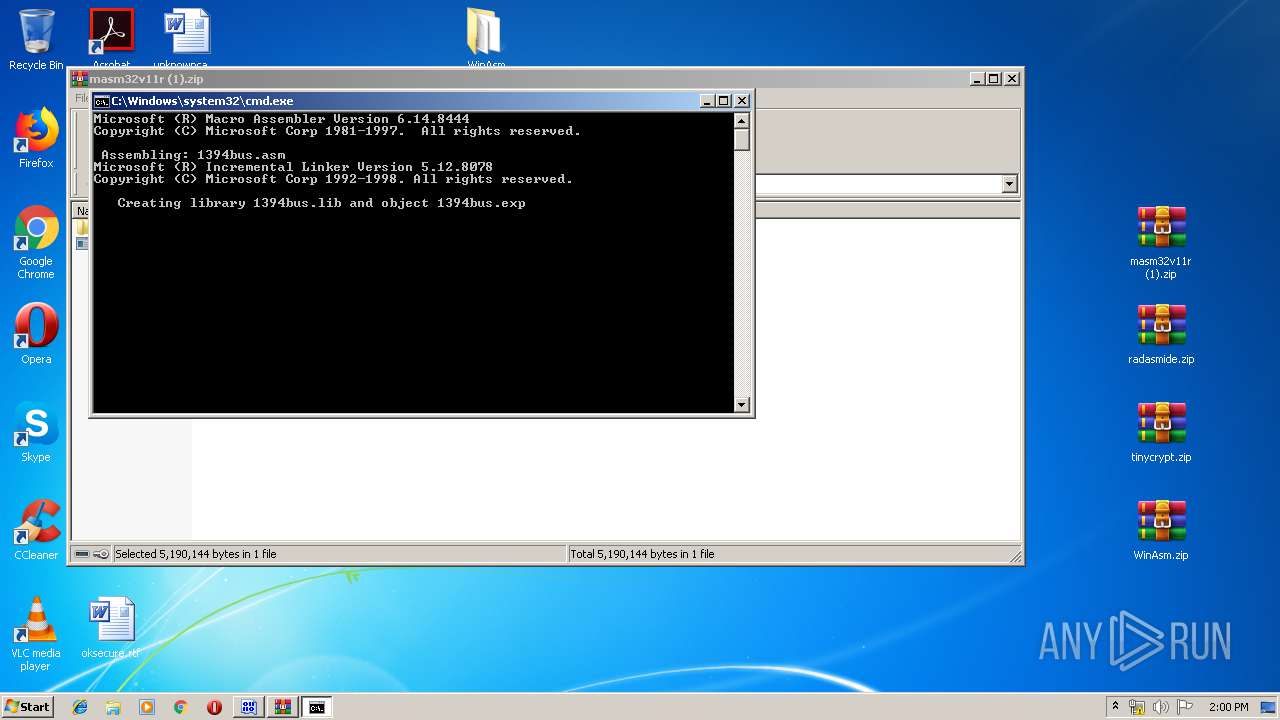
- ml.exe (PID: 1072)
- Link.exe (PID: 2524)
- ml.exe (PID: 3228)
- ml.exe (PID: 1488)
- ml.exe (PID: 1520)
- ml.exe (PID: 2524)
- ml.exe (PID: 3040)
- ml.exe (PID: 3700)
- ml.exe (PID: 504)
- ml.exe (PID: 2760)
- ml.exe (PID: 3776)
- ml.exe (PID: 2648)
- ml.exe (PID: 3548)
- ml.exe (PID: 2468)
- ml.exe (PID: 3260)
- ml.exe (PID: 3308)
- ml.exe (PID: 2612)
- ml.exe (PID: 2232)
- ml.exe (PID: 2028)
- ml.exe (PID: 2844)
- ml.exe (PID: 1216)
- ml.exe (PID: 2628)
- ml.exe (PID: 2844)
- ml.exe (PID: 1792)
- ml.exe (PID: 1848)
- ml.exe (PID: 2104)
- ml.exe (PID: 3244)
- Link.exe (PID: 2696)
- ml.exe (PID: 3940)
- Link.exe (PID: 3152)
- Link.exe (PID: 1520)
- ml.exe (PID: 3560)
Loads dropped or rewritten executable
- RadASM.exe (PID: 1712)
- explorer.exe (PID: 352)
- SearchProtocolHost.exe (PID: 3148)
- Link.exe (PID: 3572)
- Link.exe (PID: 2696)
- Link.exe (PID: 1072)
- Link.exe (PID: 2176)
- Link.exe (PID: 1560)
- Link.exe (PID: 1488)
- Link.exe (PID: 3568)
- Link.exe (PID: 2928)
- Link.exe (PID: 3344)
- Link.exe (PID: 2488)
- Link.exe (PID: 2684)
- Link.exe (PID: 4020)
- Link.exe (PID: 2028)
- Link.exe (PID: 3108)
- Link.exe (PID: 2092)
- Link.exe (PID: 2552)
- Link.exe (PID: 2820)
- Link.exe (PID: 600)
- Link.exe (PID: 496)
- Link.exe (PID: 3824)
- Link.exe (PID: 2888)
- Link.exe (PID: 3416)
- Link.exe (PID: 2260)
- Link.exe (PID: 1268)
- Link.exe (PID: 516)
- Link.exe (PID: 3016)
- Link.exe (PID: 2920)
- Link.exe (PID: 2564)
- Link.exe (PID: 2628)
- Link.exe (PID: 2492)
- Link.exe (PID: 3984)
- Link.exe (PID: 1024)
- Link.exe (PID: 940)
- Link.exe (PID: 4060)
- Link.exe (PID: 4064)
- Link.exe (PID: 2500)
- Link.exe (PID: 2820)
- Link.exe (PID: 3296)
- Link.exe (PID: 1648)
- Link.exe (PID: 3640)
- Link.exe (PID: 996)
- Link.exe (PID: 3496)
- Link.exe (PID: 3336)
- Link.exe (PID: 3236)
- Link.exe (PID: 2476)
- Link.exe (PID: 2488)
- Link.exe (PID: 564)
- Link.exe (PID: 3484)
- Link.exe (PID: 1520)
- Link.exe (PID: 3152)
- Link.exe (PID: 2976)
- Link.exe (PID: 3308)
- Link.exe (PID: 2808)
- Link.exe (PID: 3856)
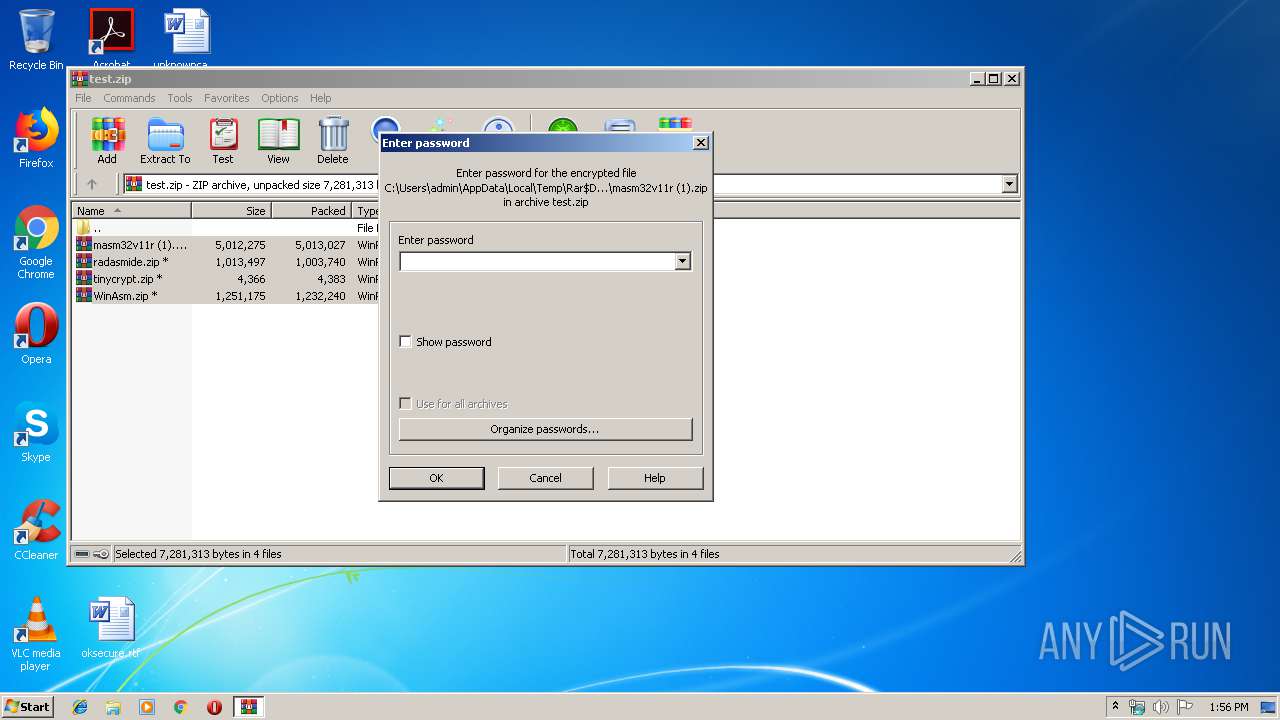
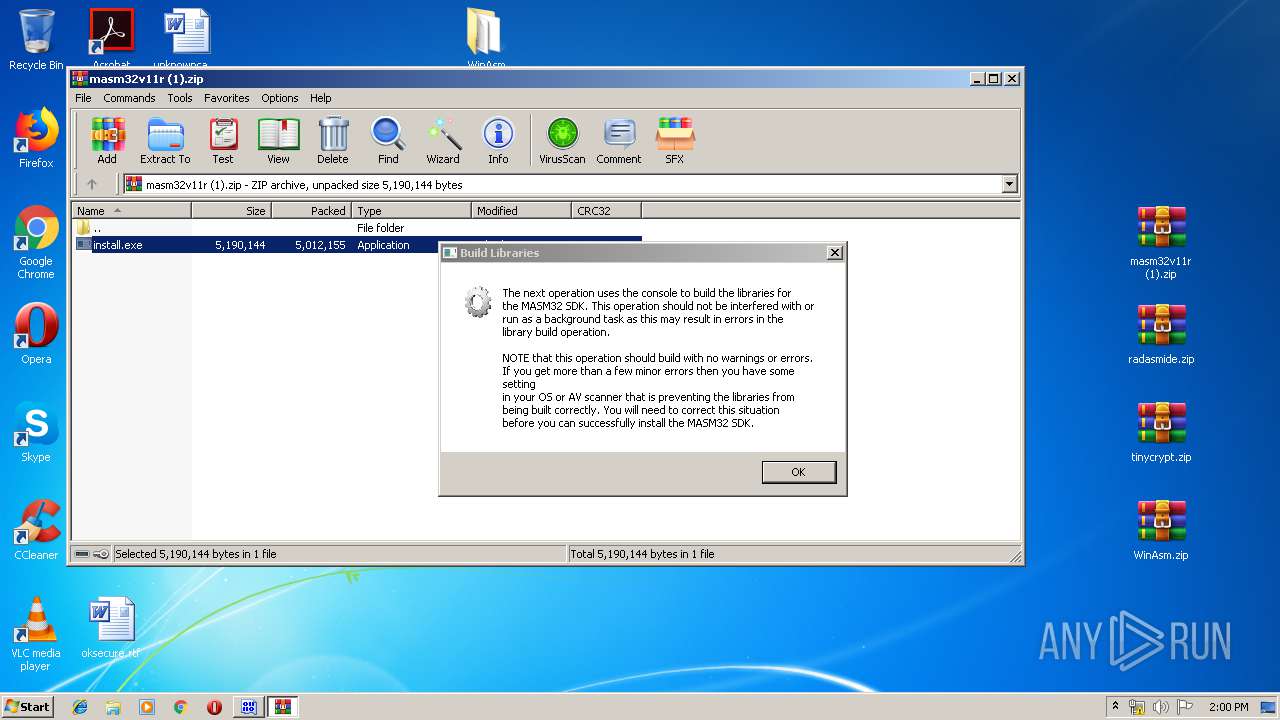
SUSPICIOUS
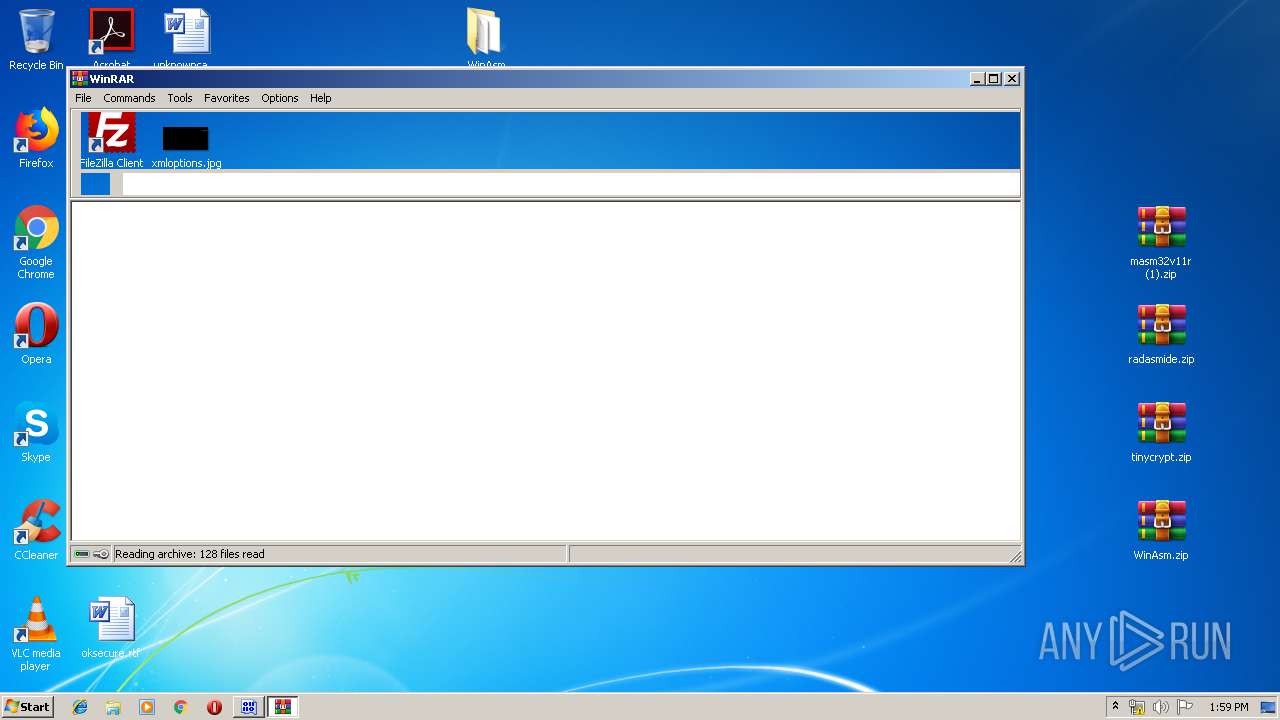
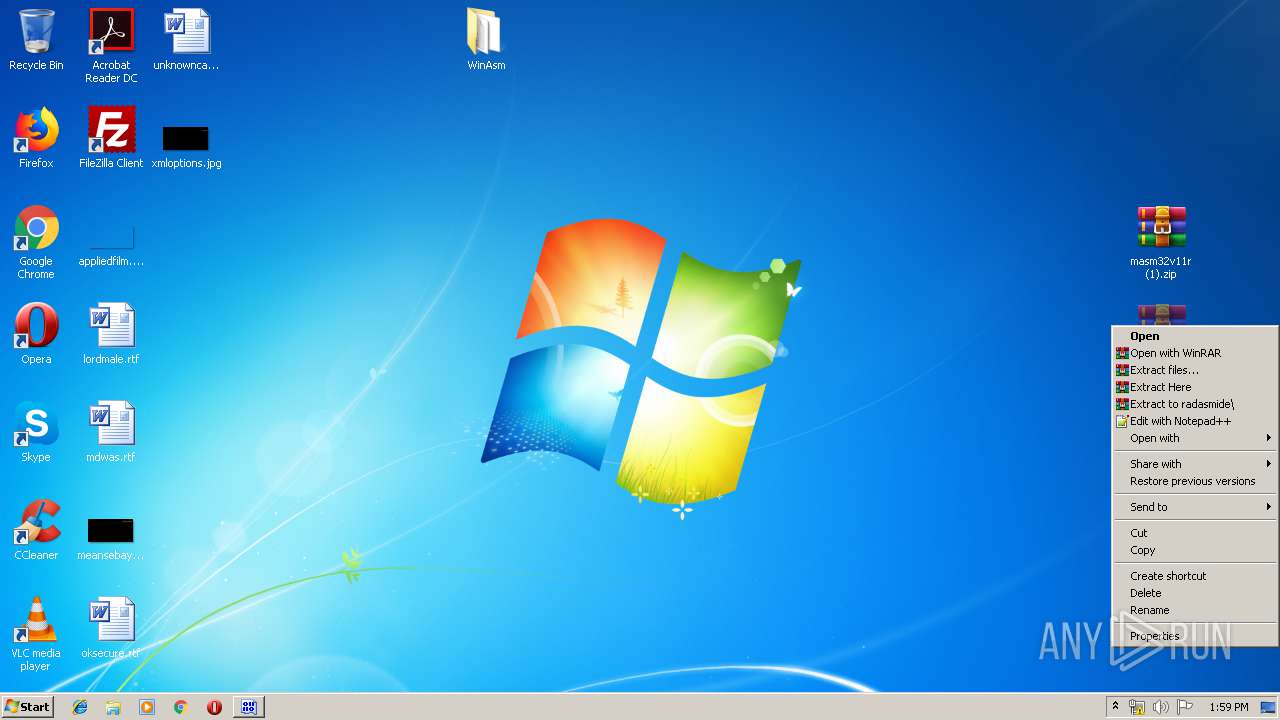
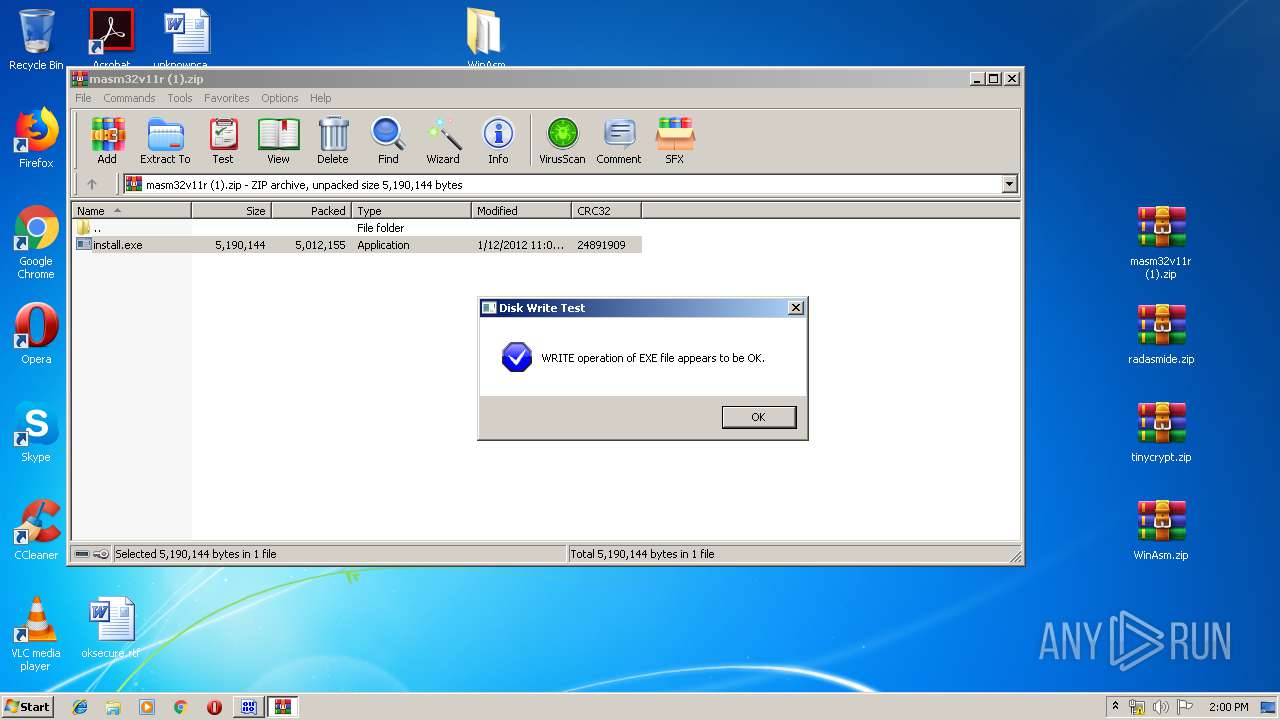
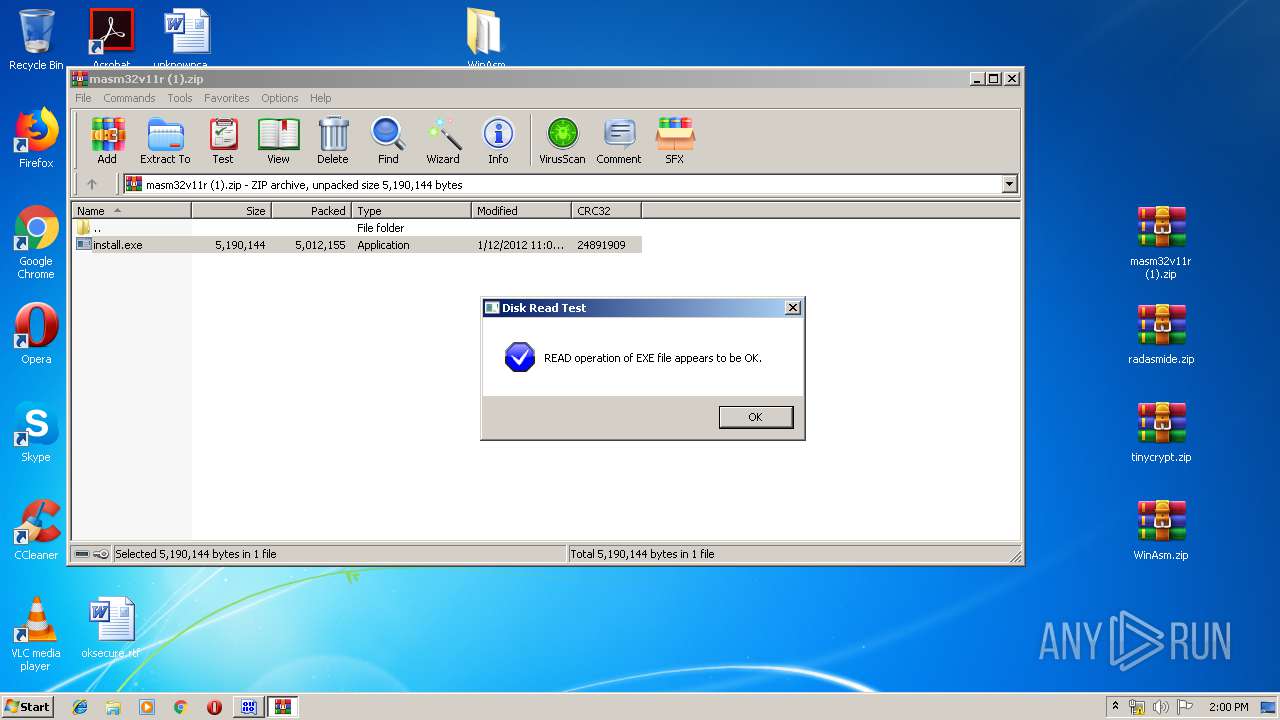
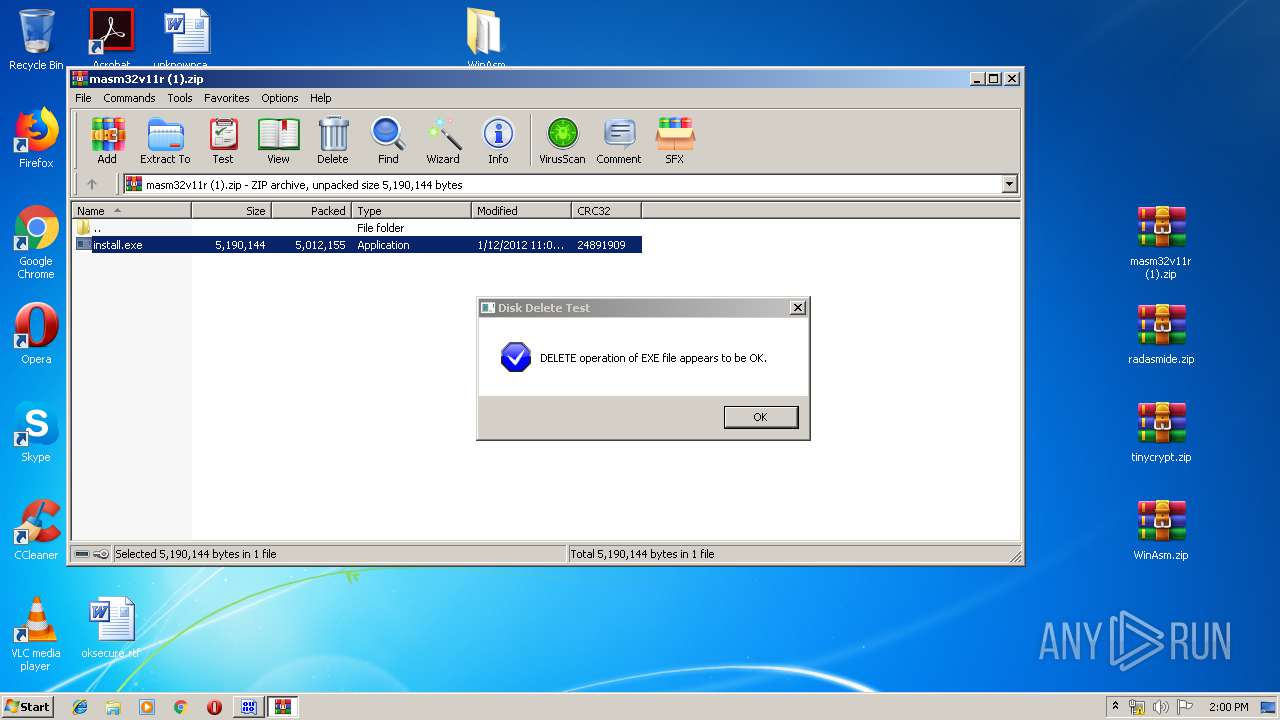
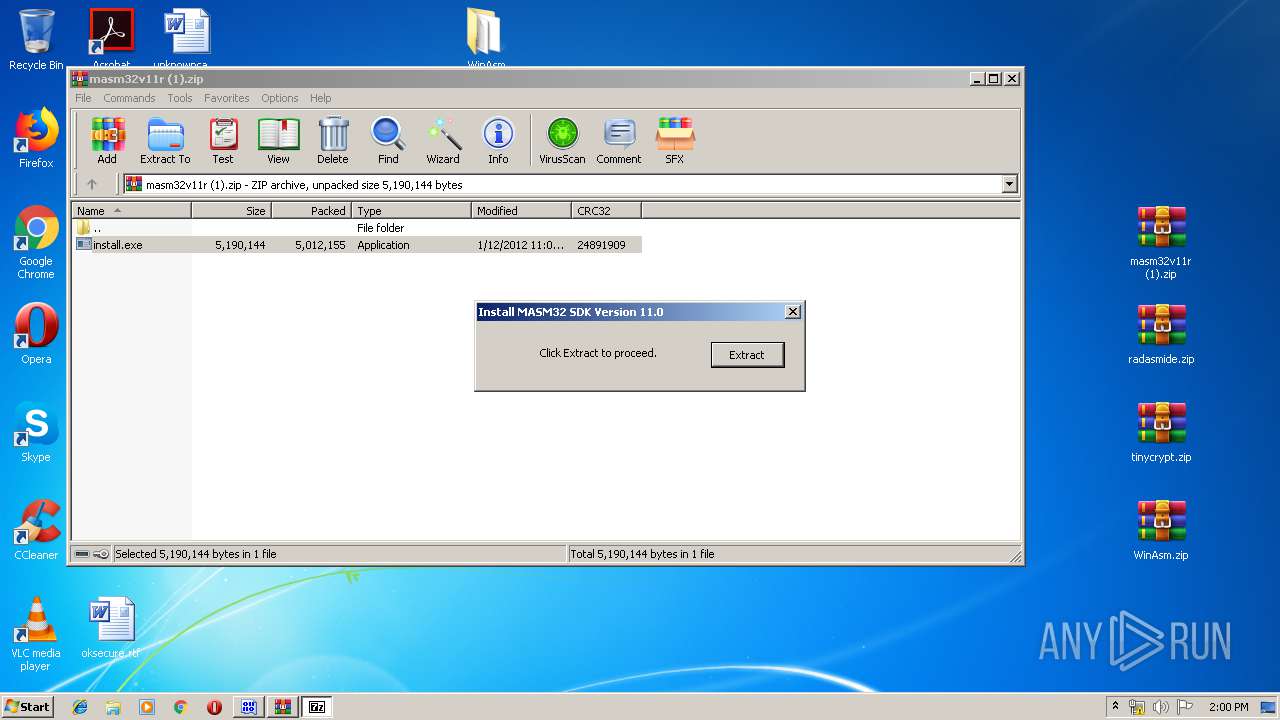
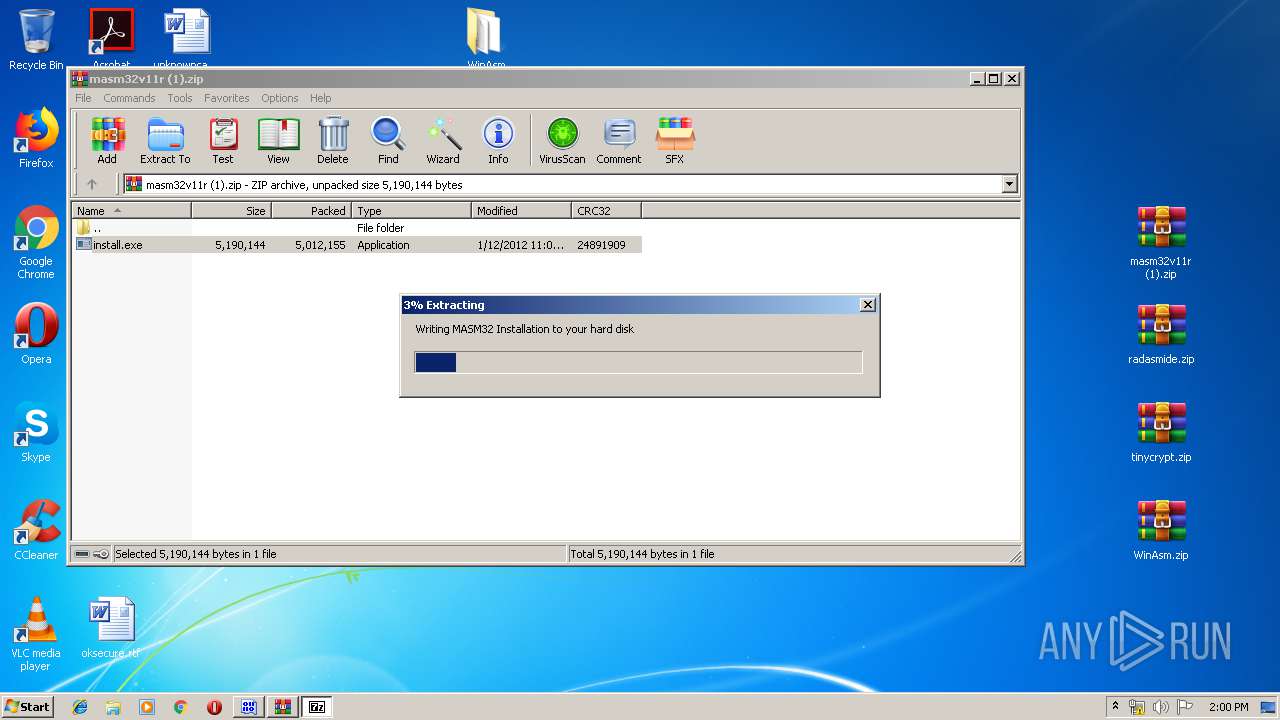
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3200)
- WinRAR.exe (PID: 3400)
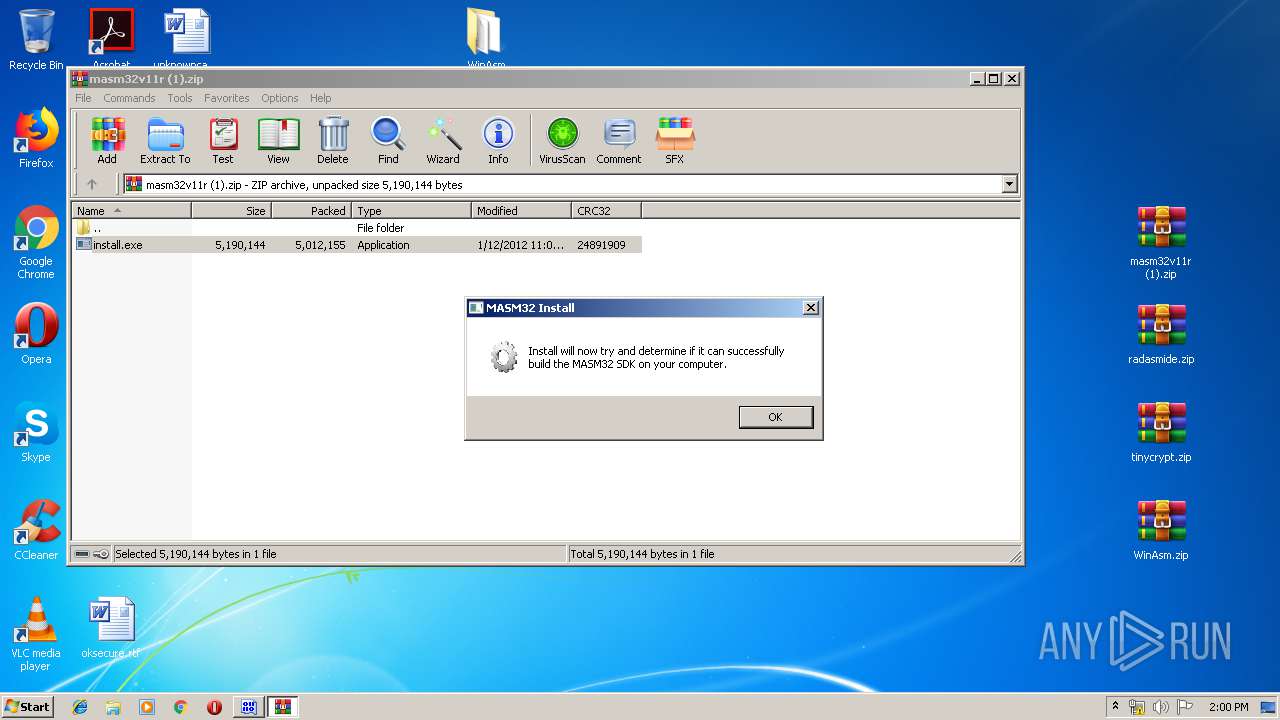
- install.exe (PID: 3564)
- Link.exe (PID: 1560)
- masm32ci.exe (PID: 2952)
Reads Internet Cache Settings
- explorer.exe (PID: 352)
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 352)
Creates files in the user directory
- explorer.exe (PID: 352)
Application launched itself
- Link.exe (PID: 1024)
- Link.exe (PID: 940)
- Link.exe (PID: 2500)
- Link.exe (PID: 1648)
- Link.exe (PID: 3640)
- Link.exe (PID: 3496)
- Link.exe (PID: 3484)
- Link.exe (PID: 2524)
- Link.exe (PID: 2928)
- Link.exe (PID: 2488)
- Link.exe (PID: 1520)
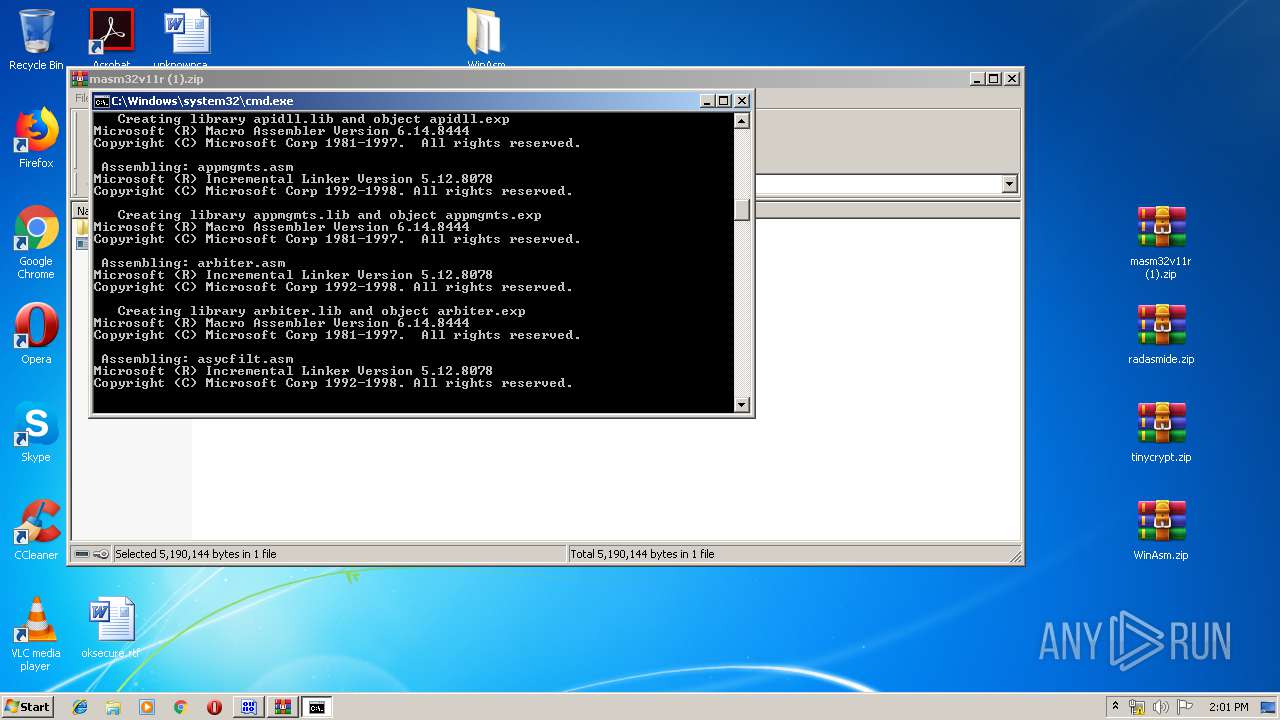
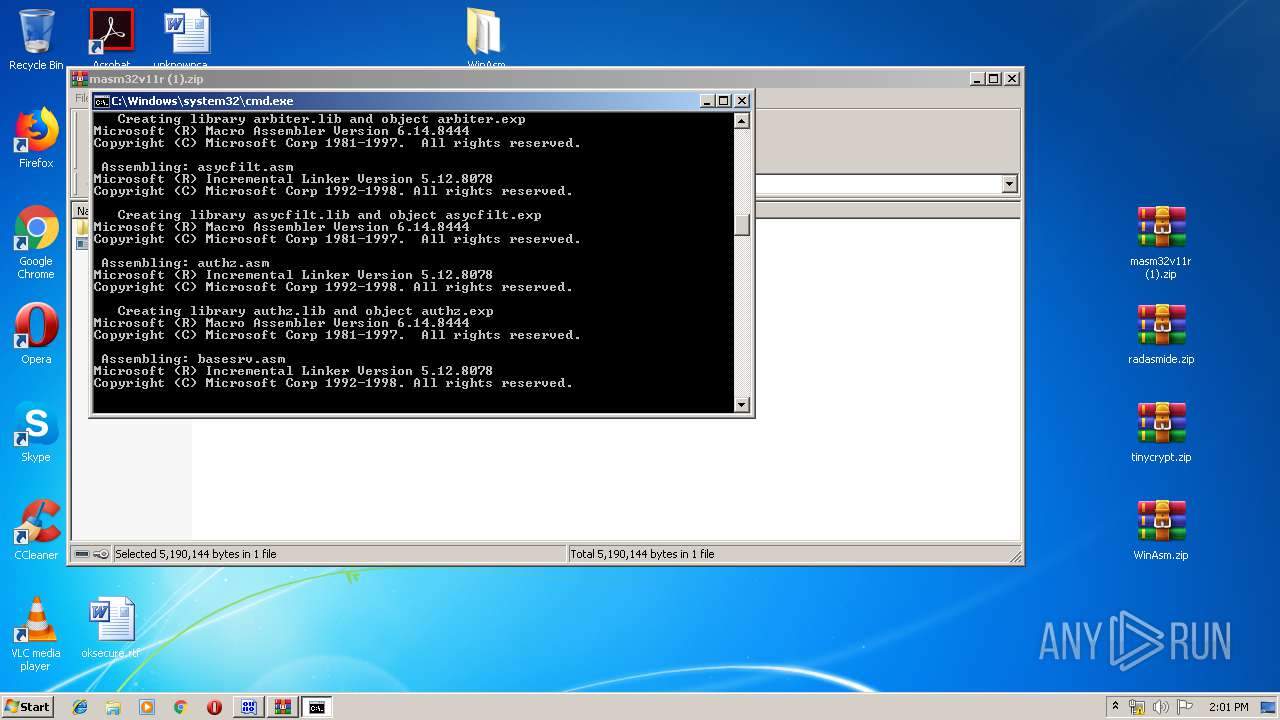
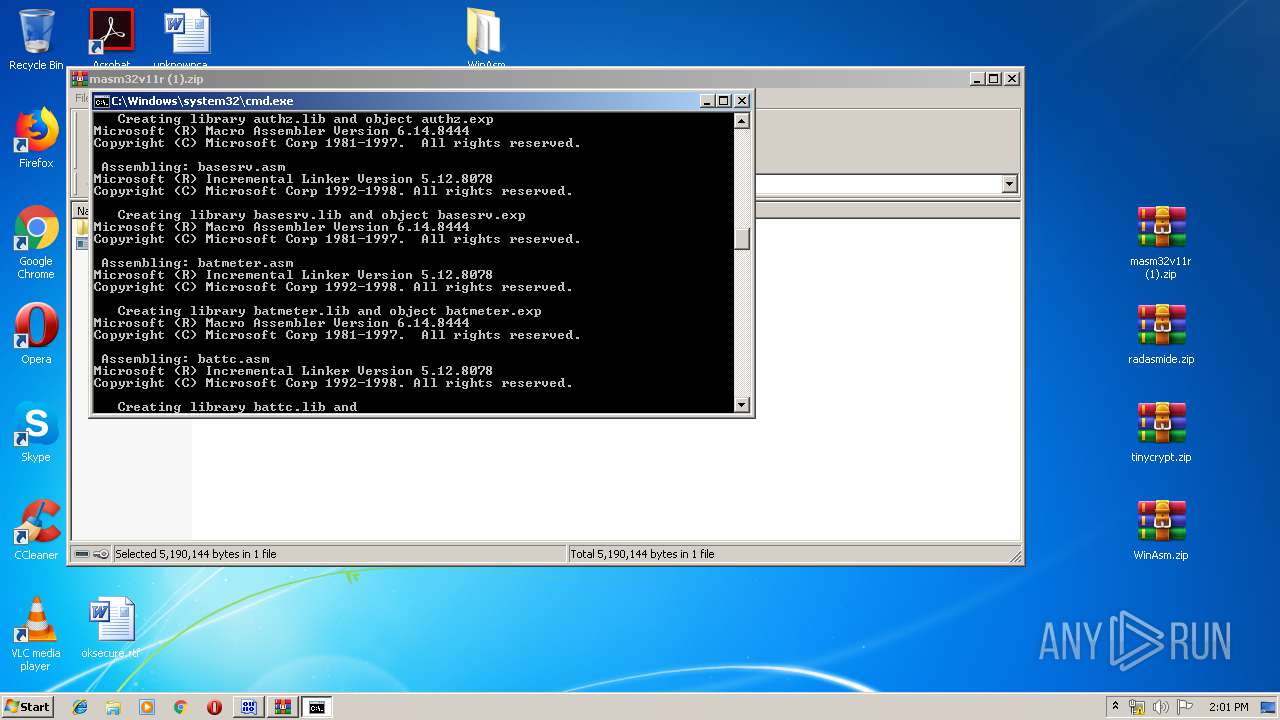
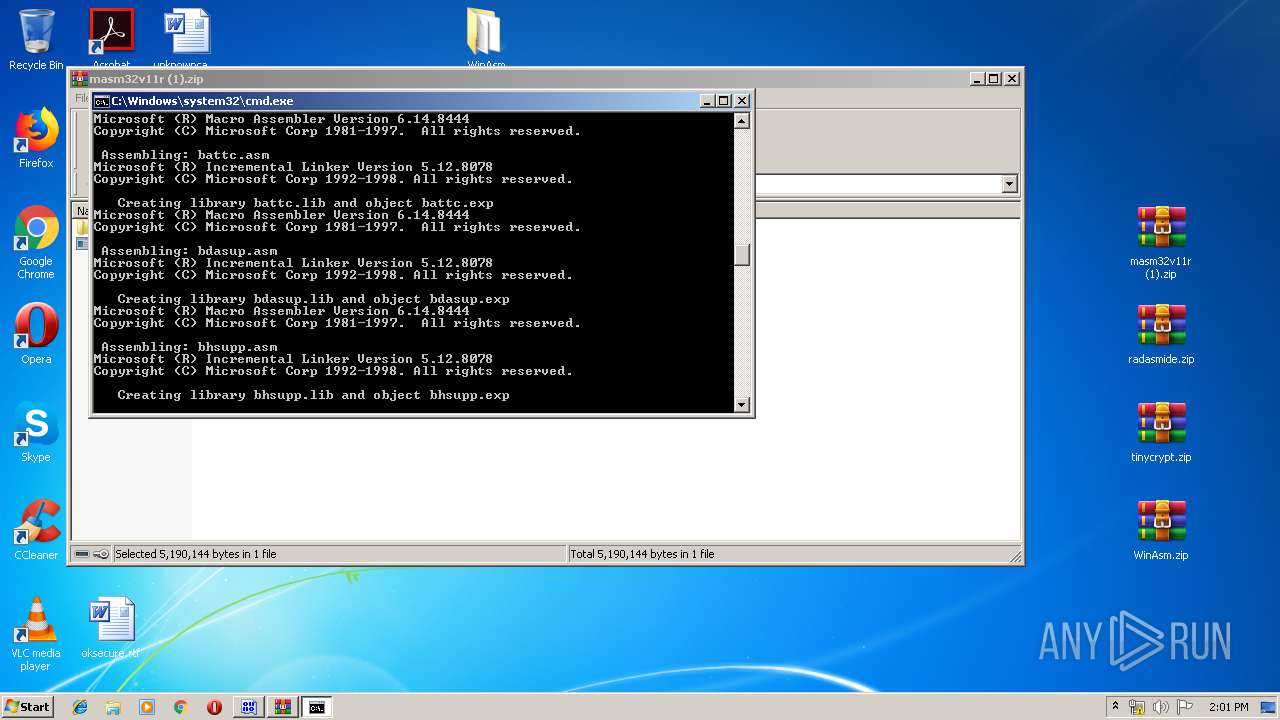
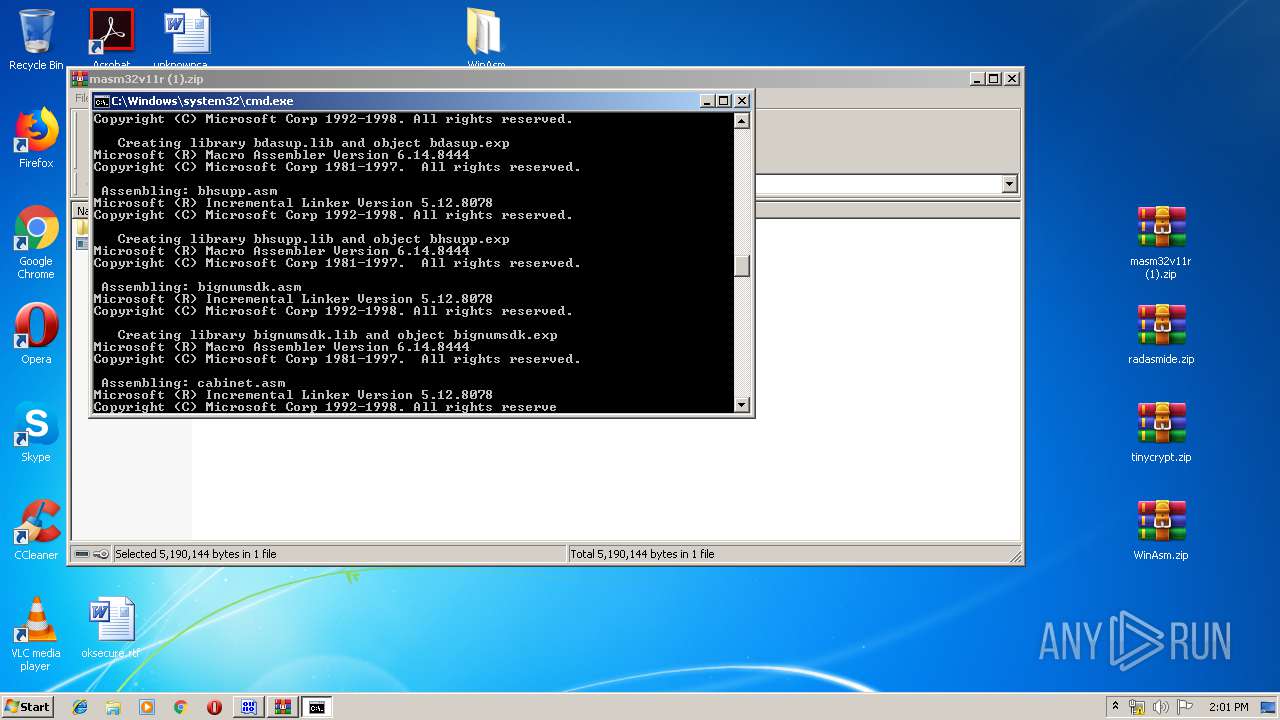
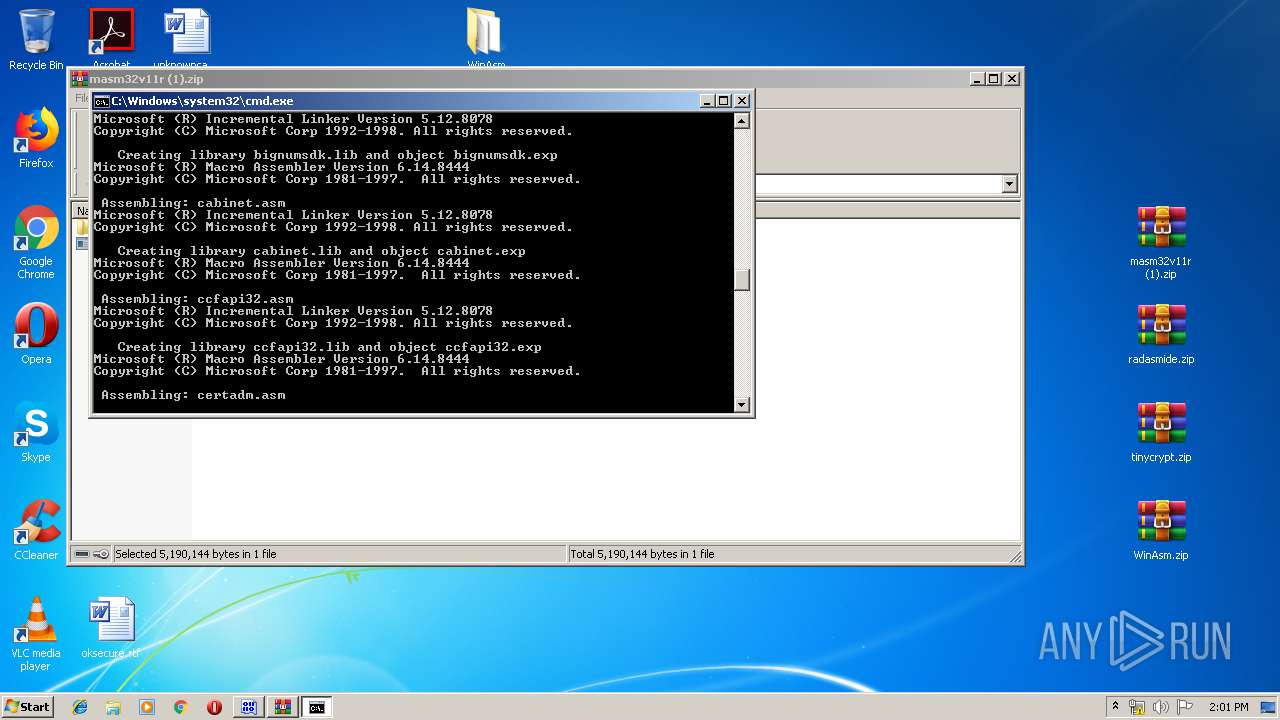
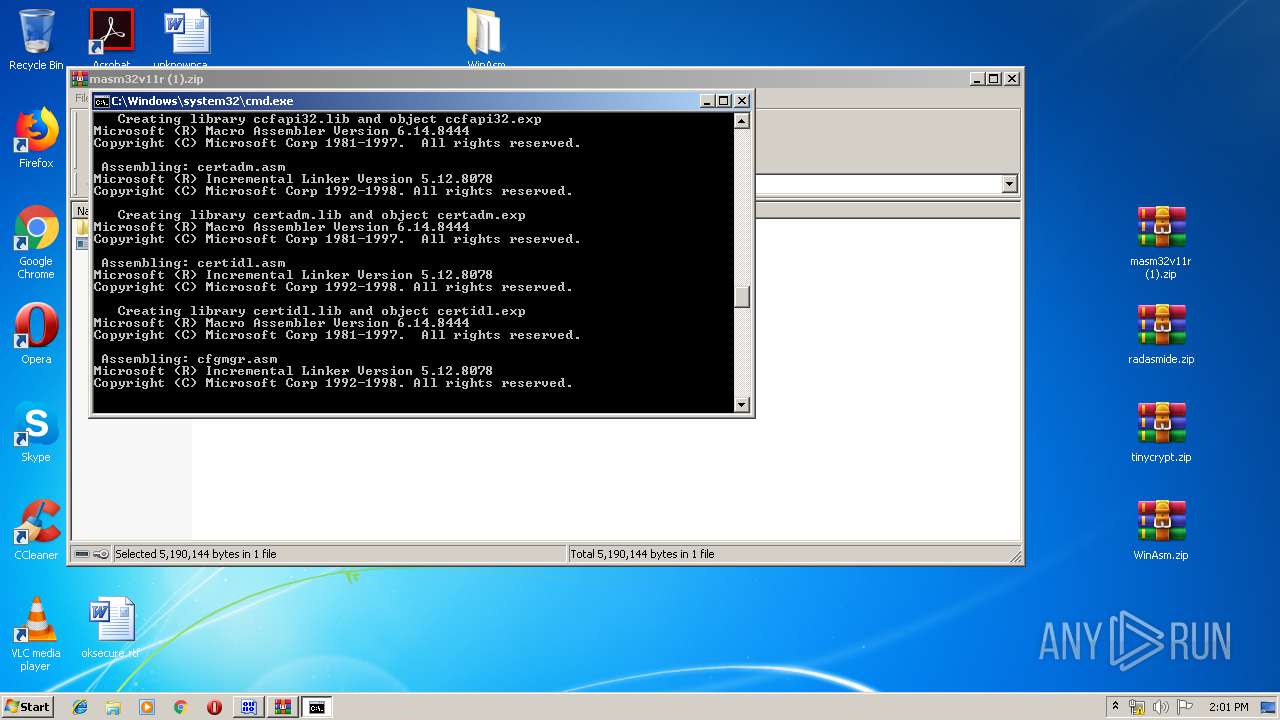
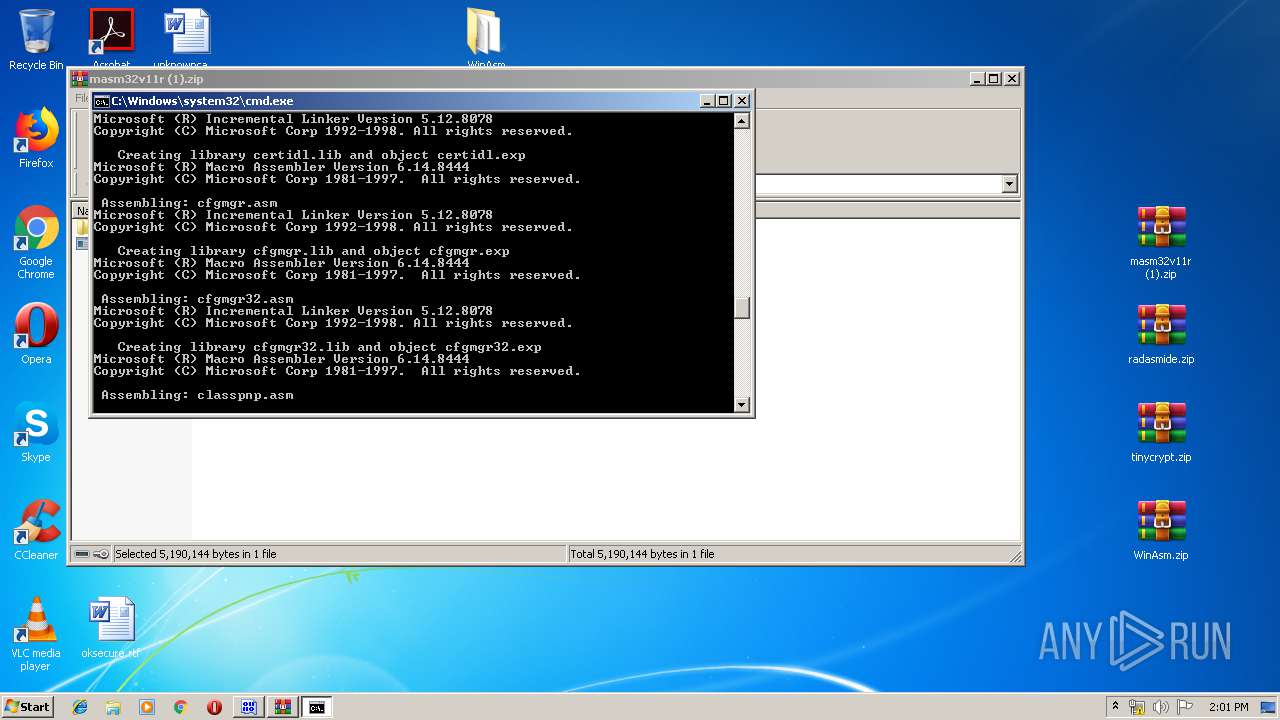
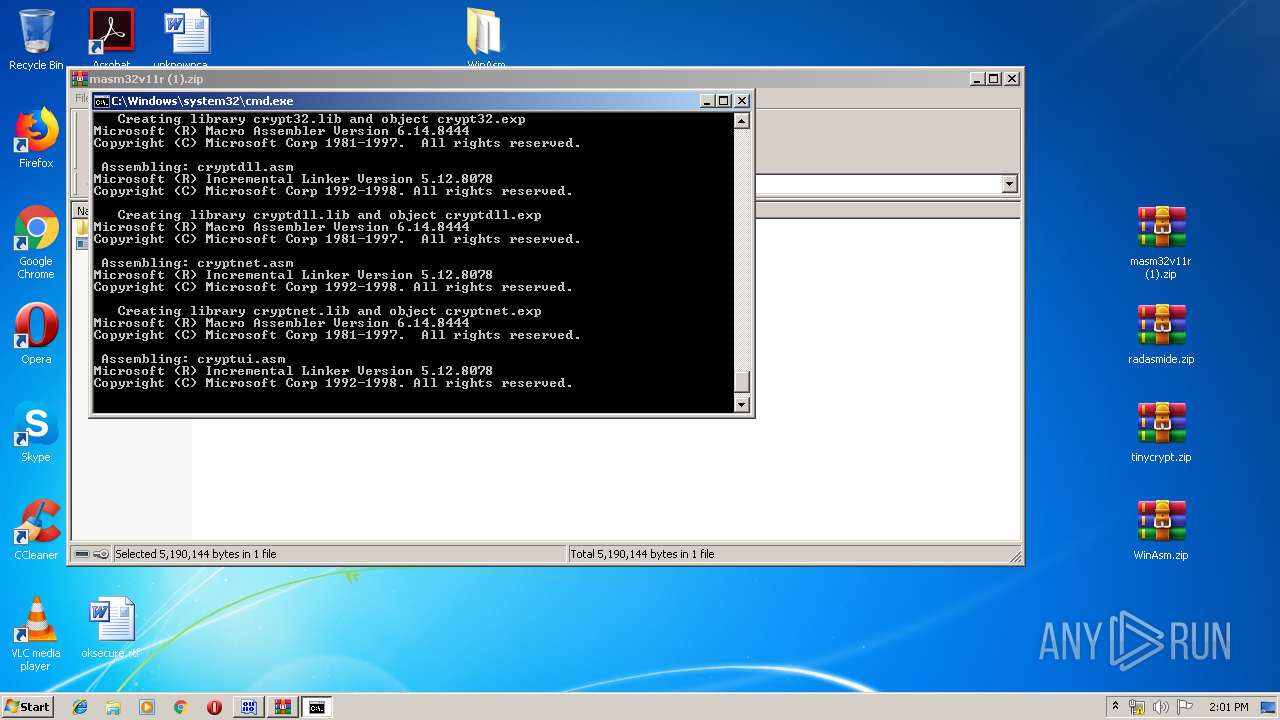
Starts CMD.EXE for commands execution
- install.exe (PID: 3564)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3200)
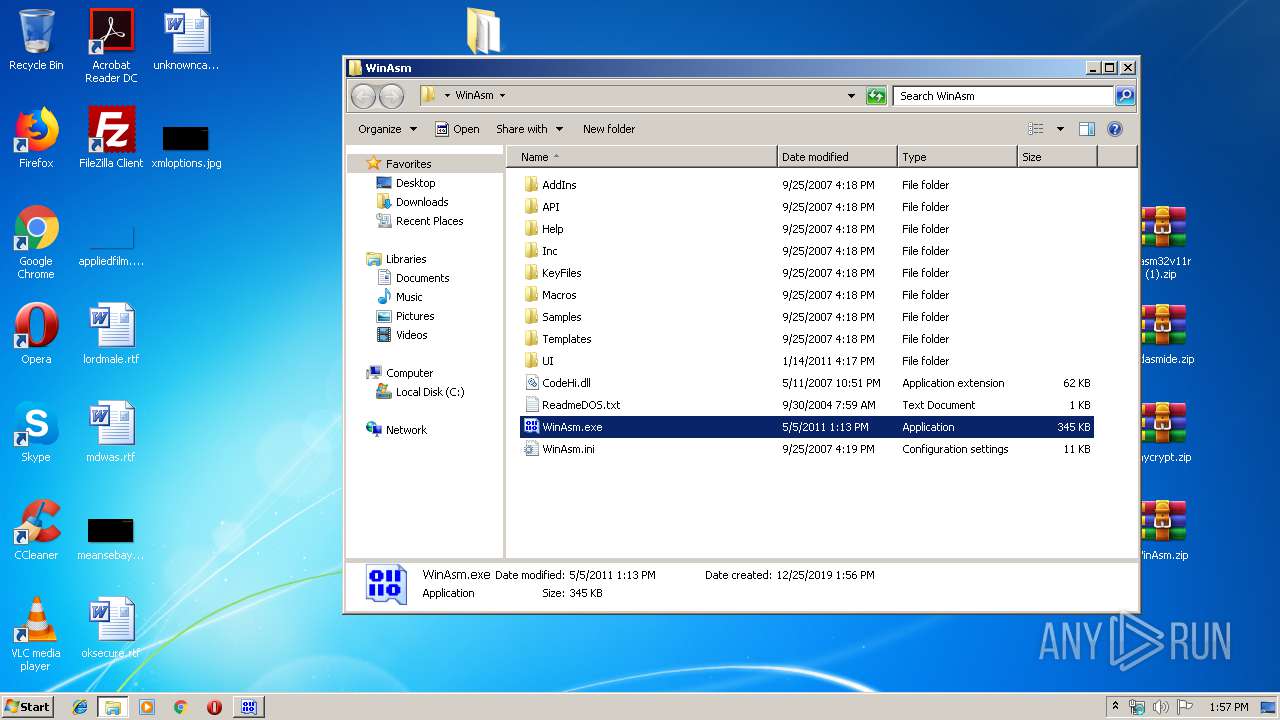
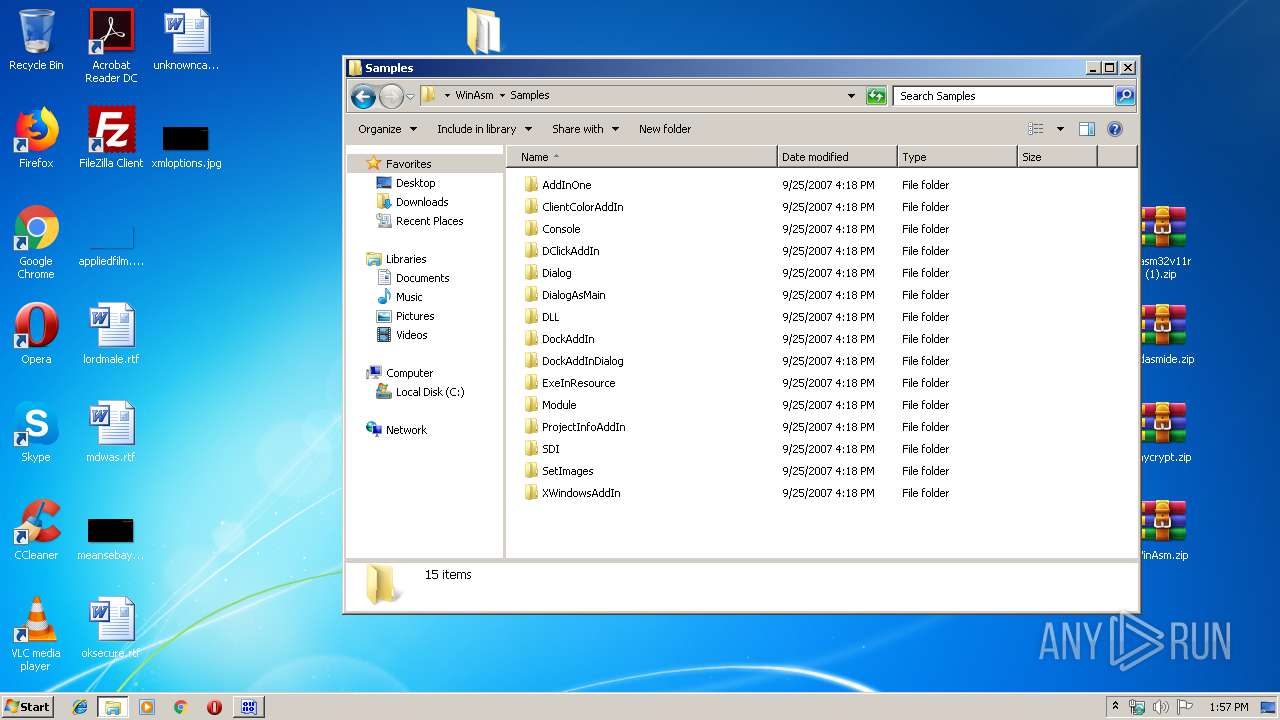
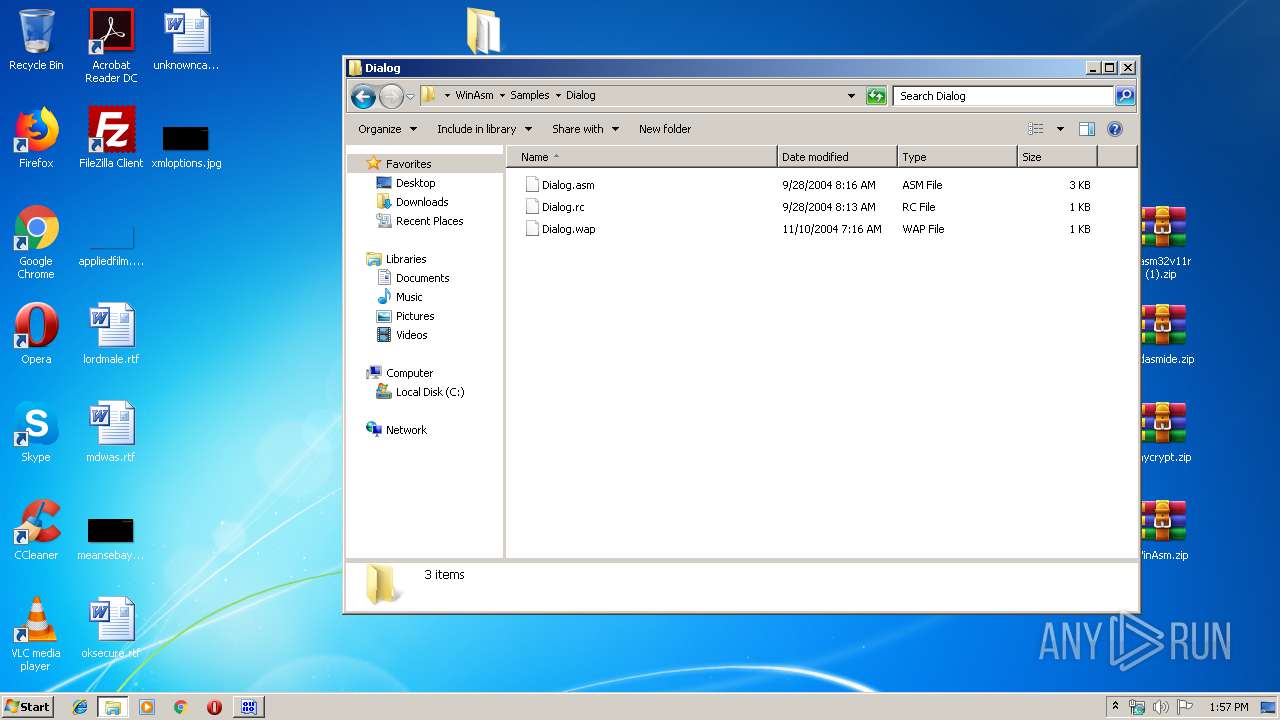
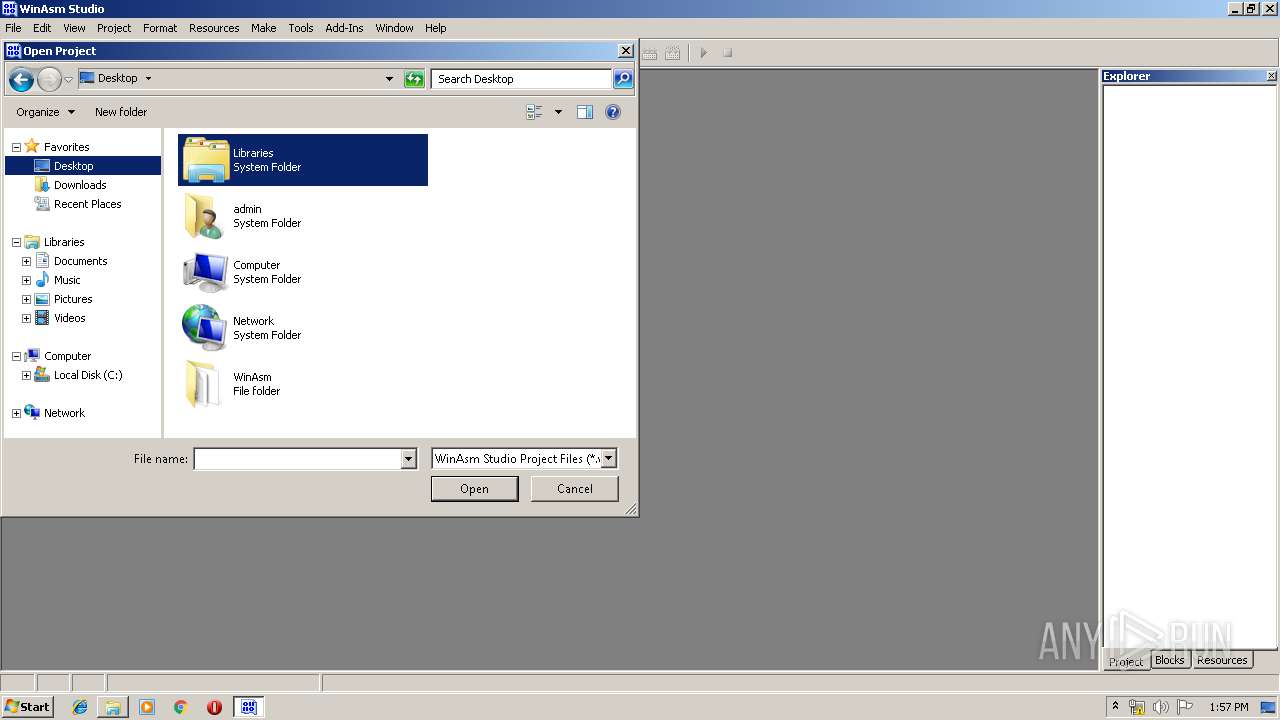
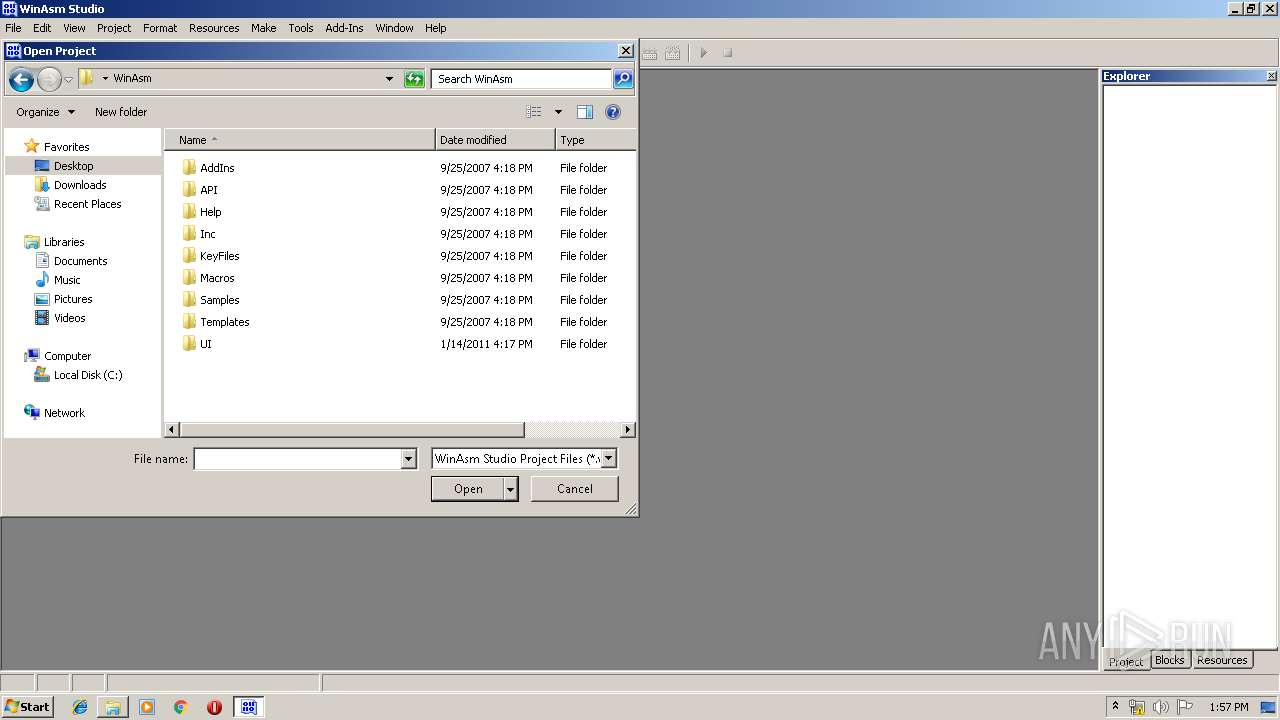
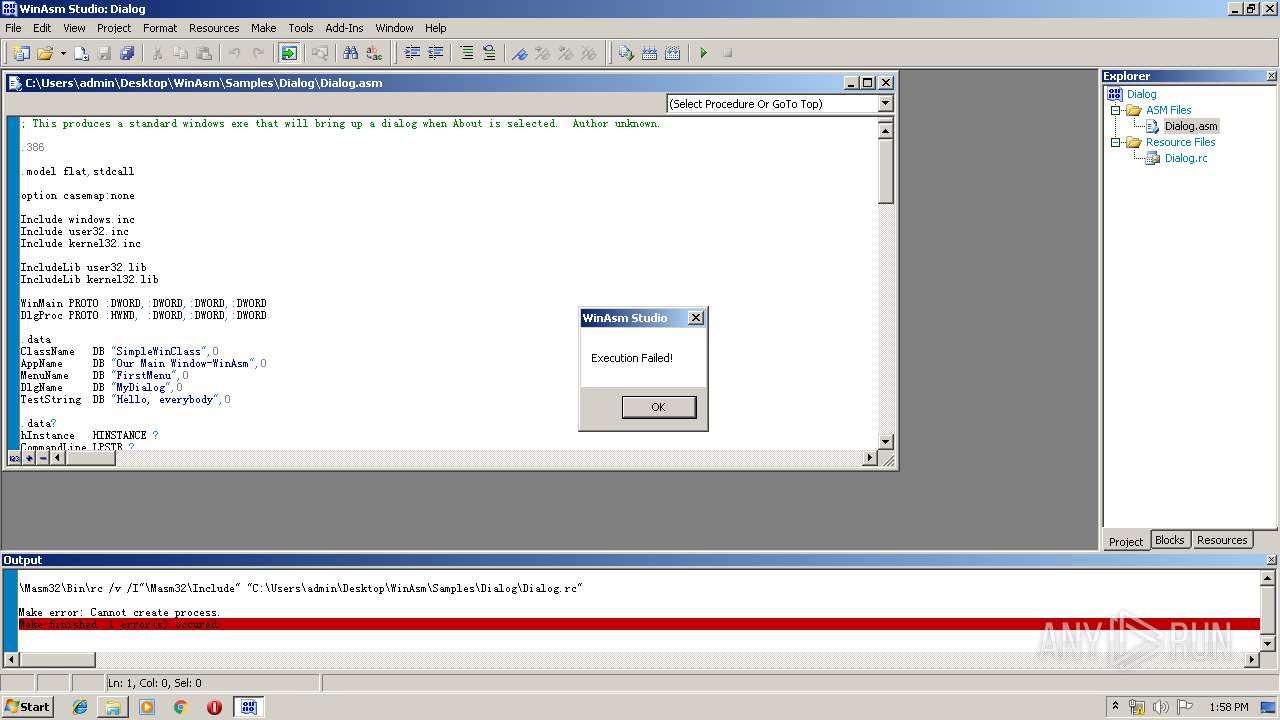
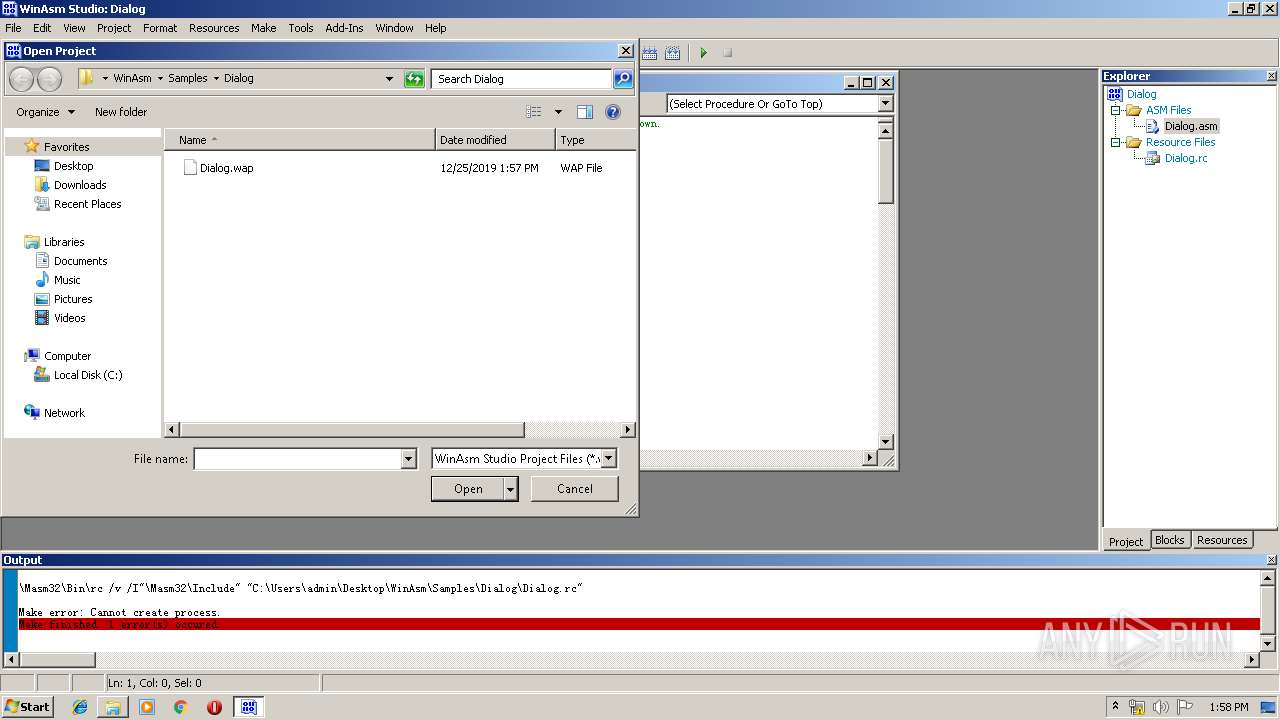
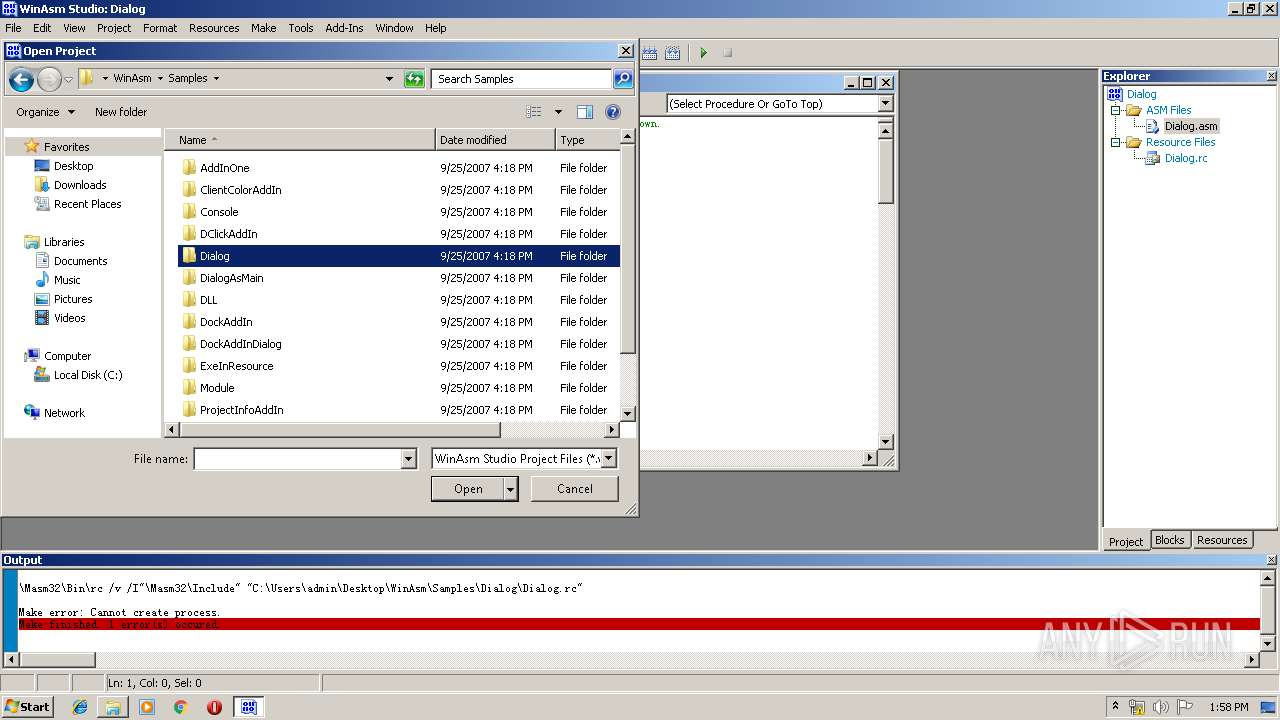
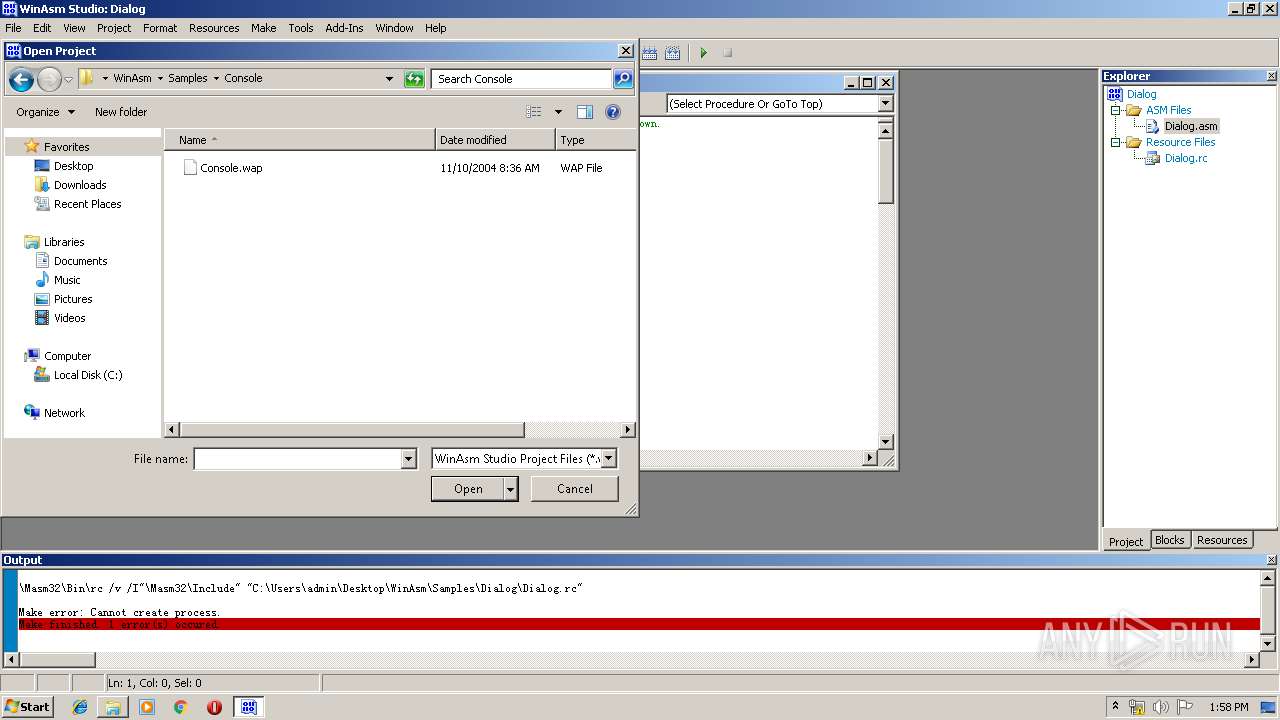
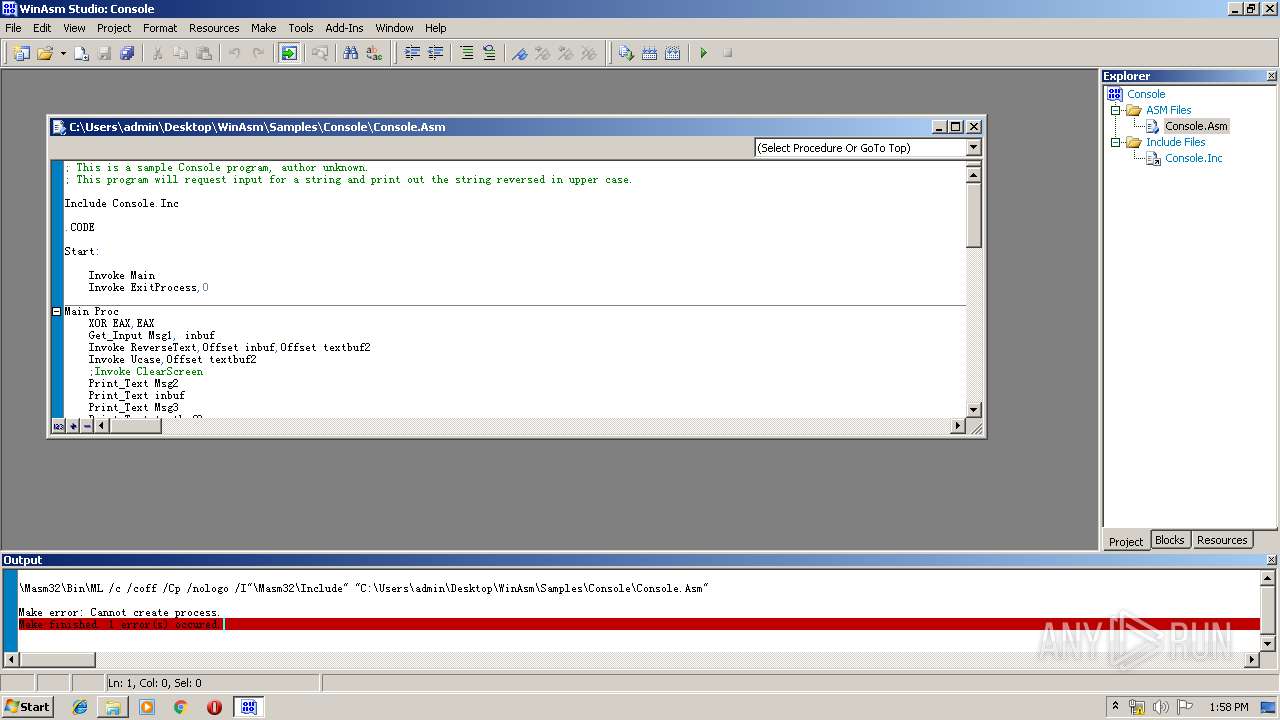
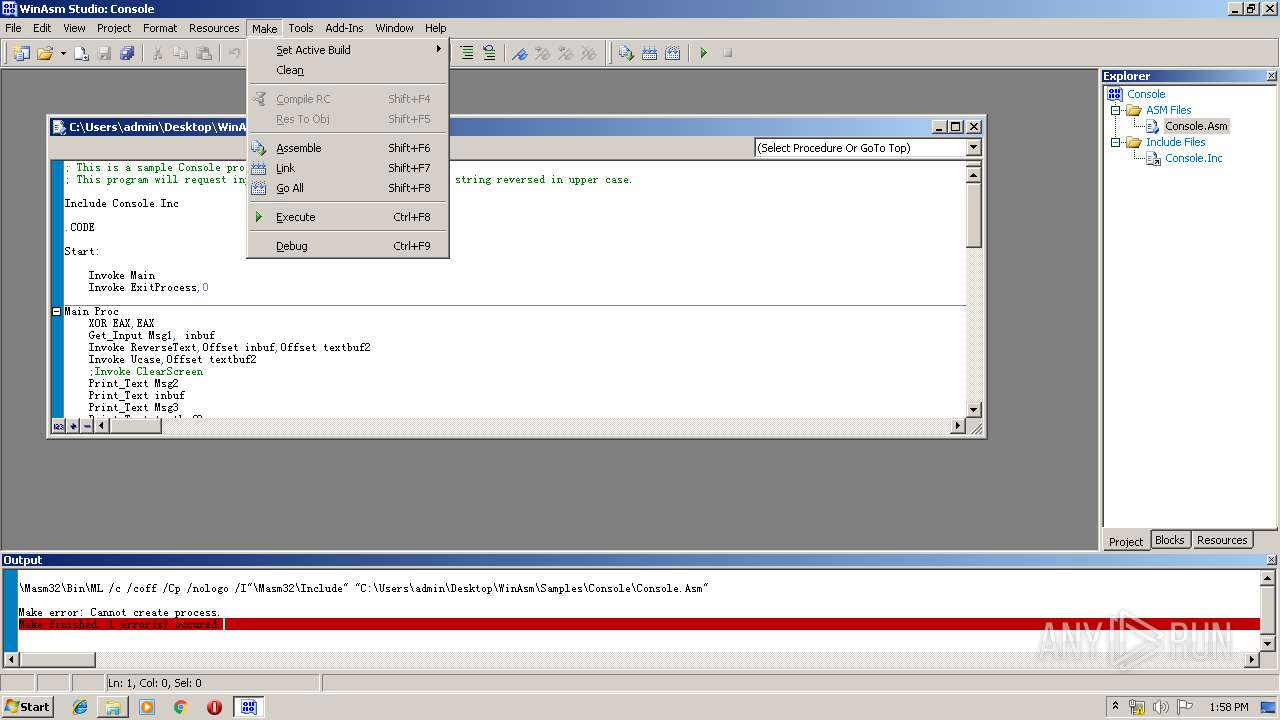
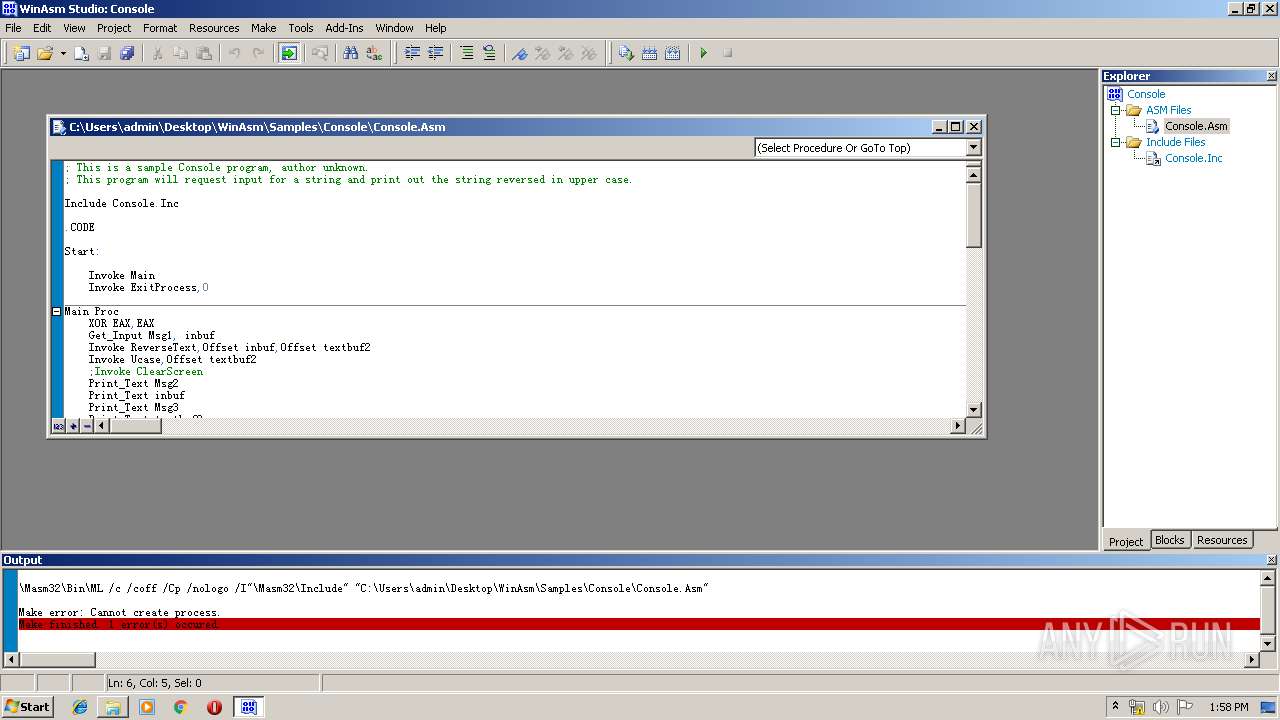
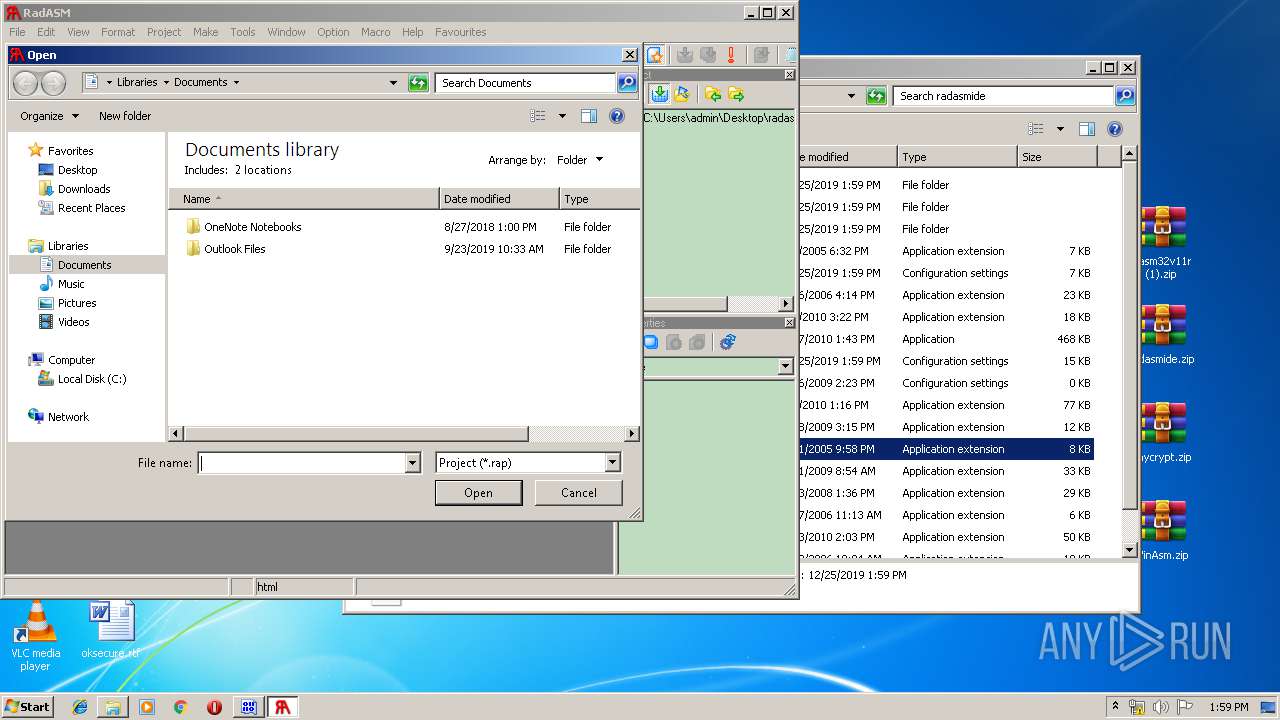
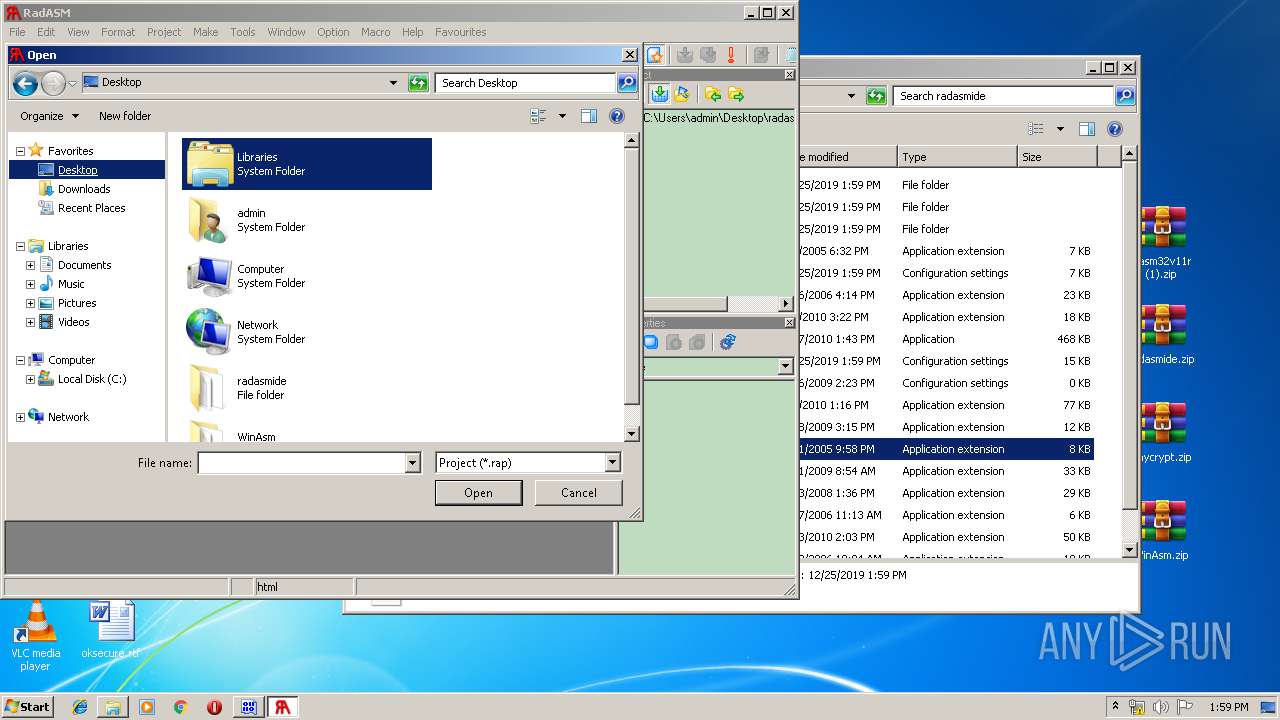
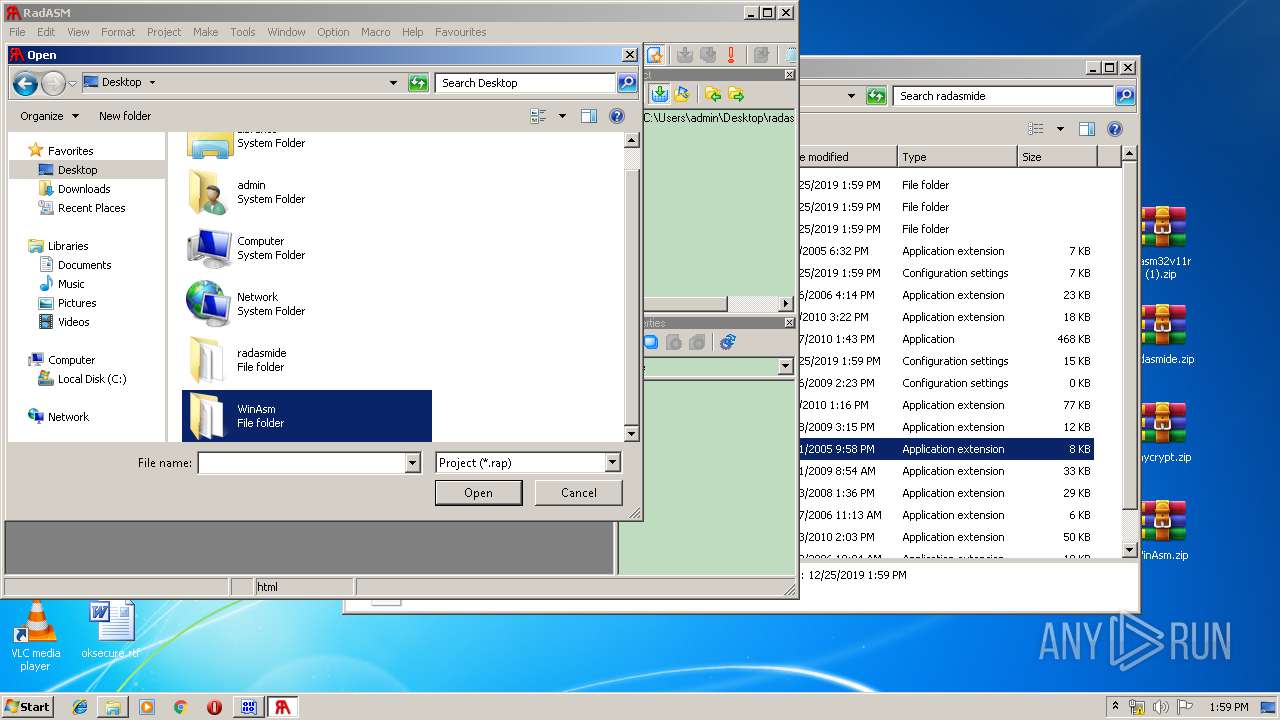
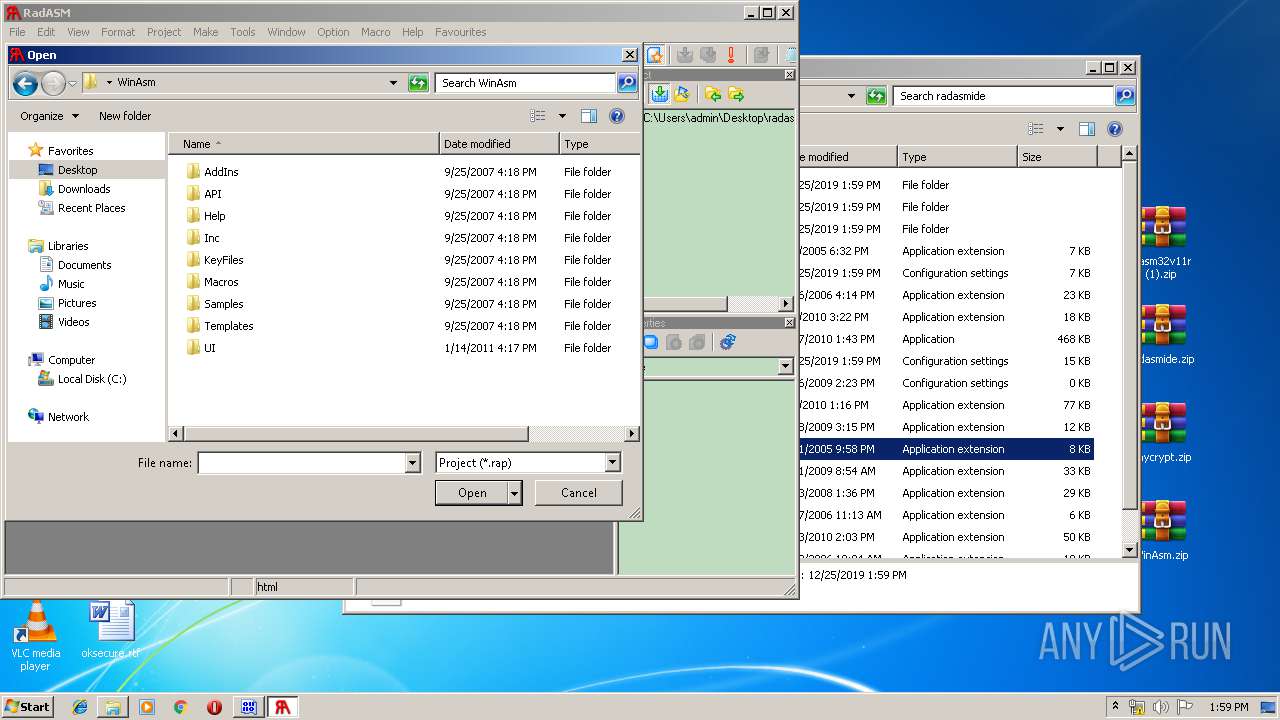
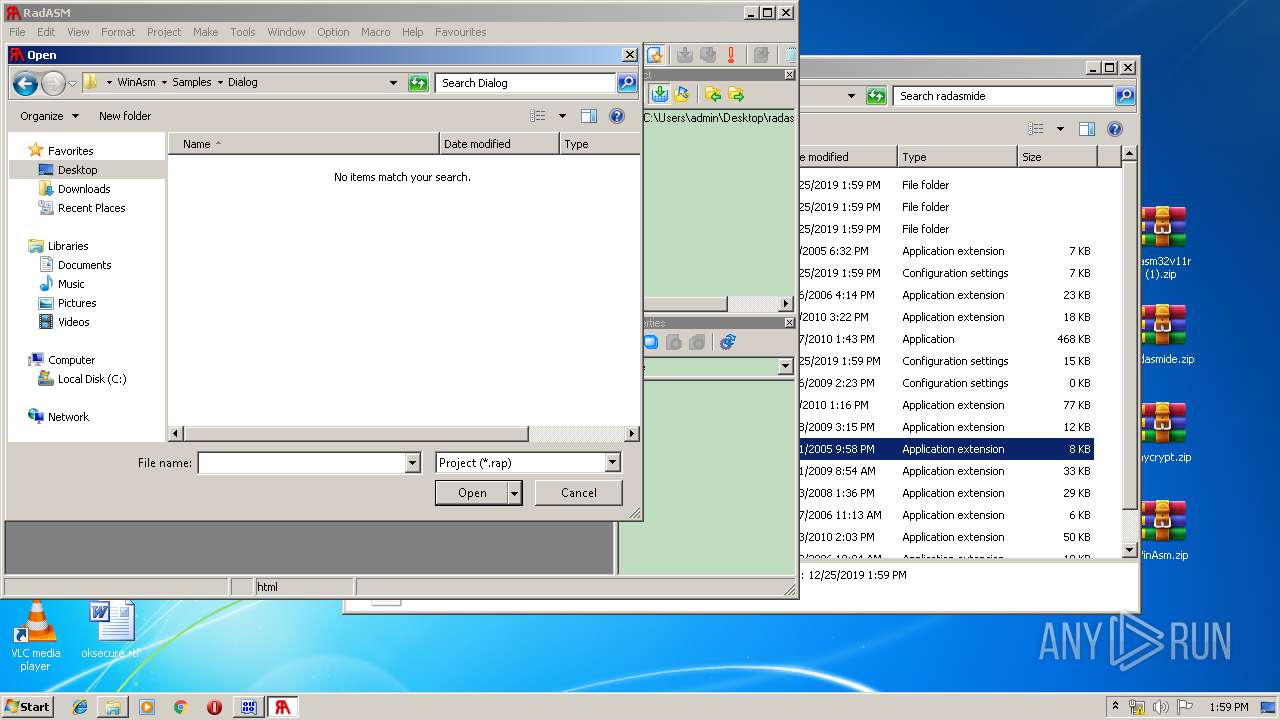
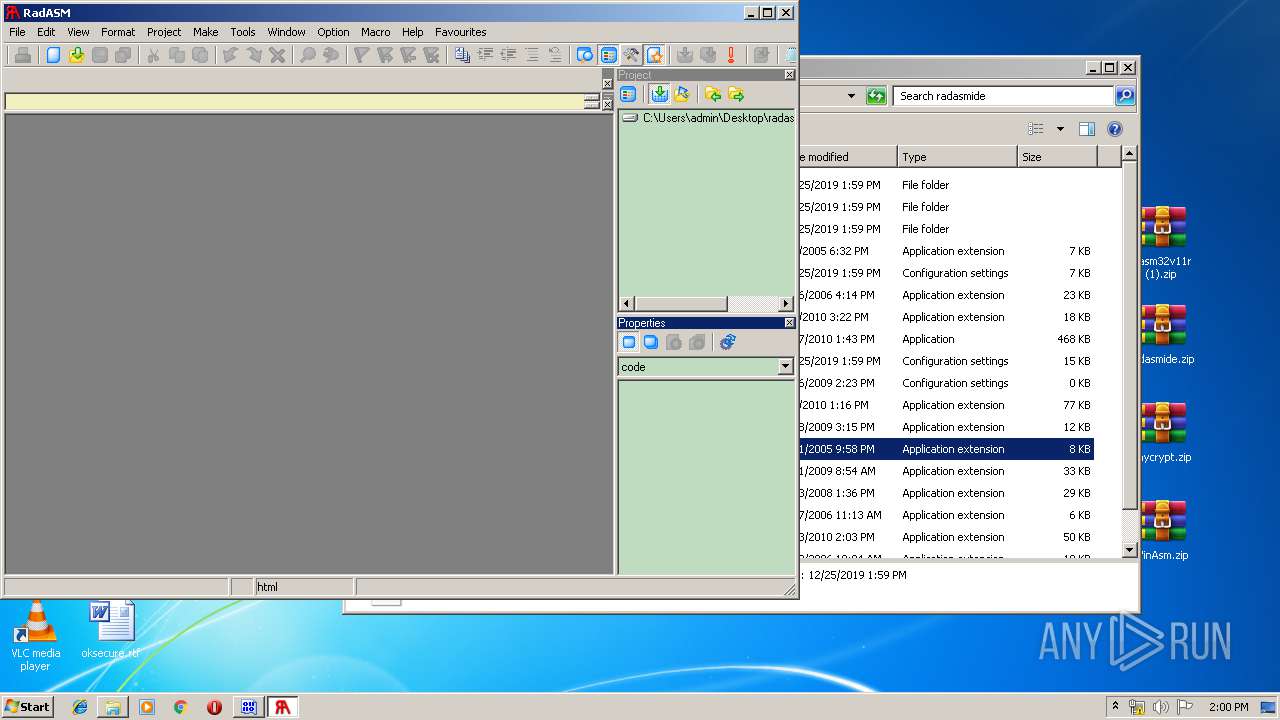
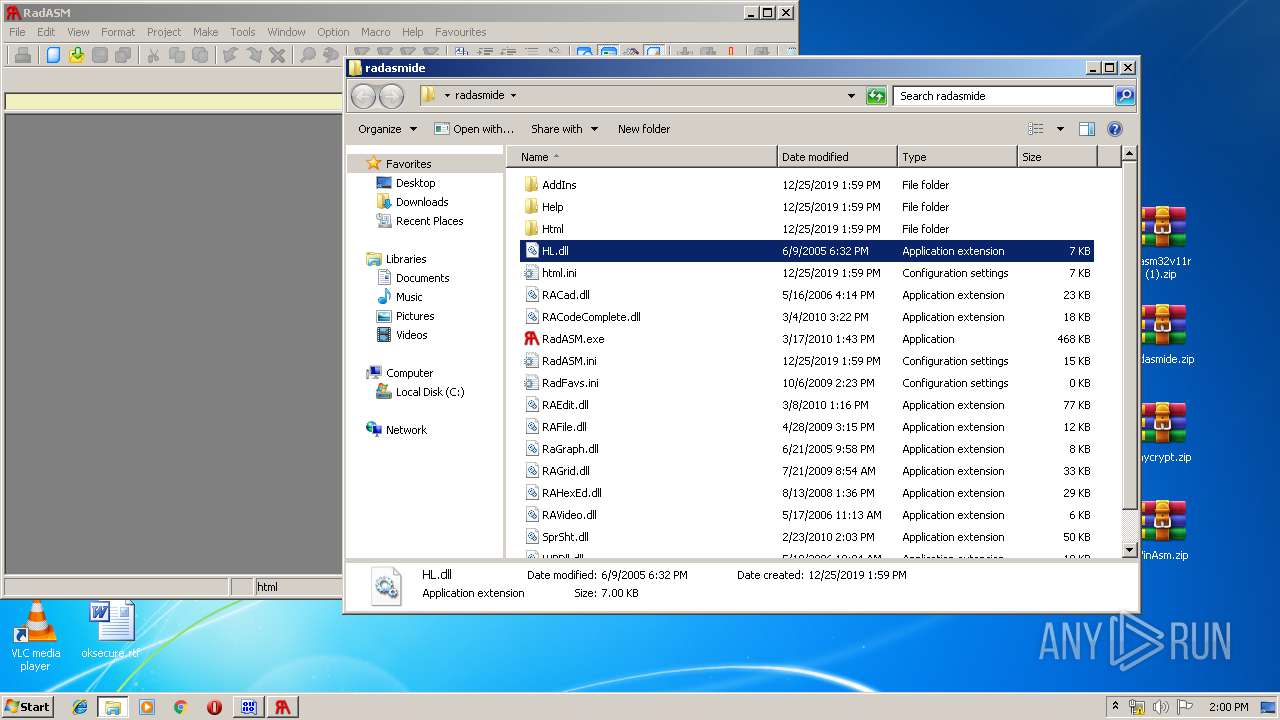
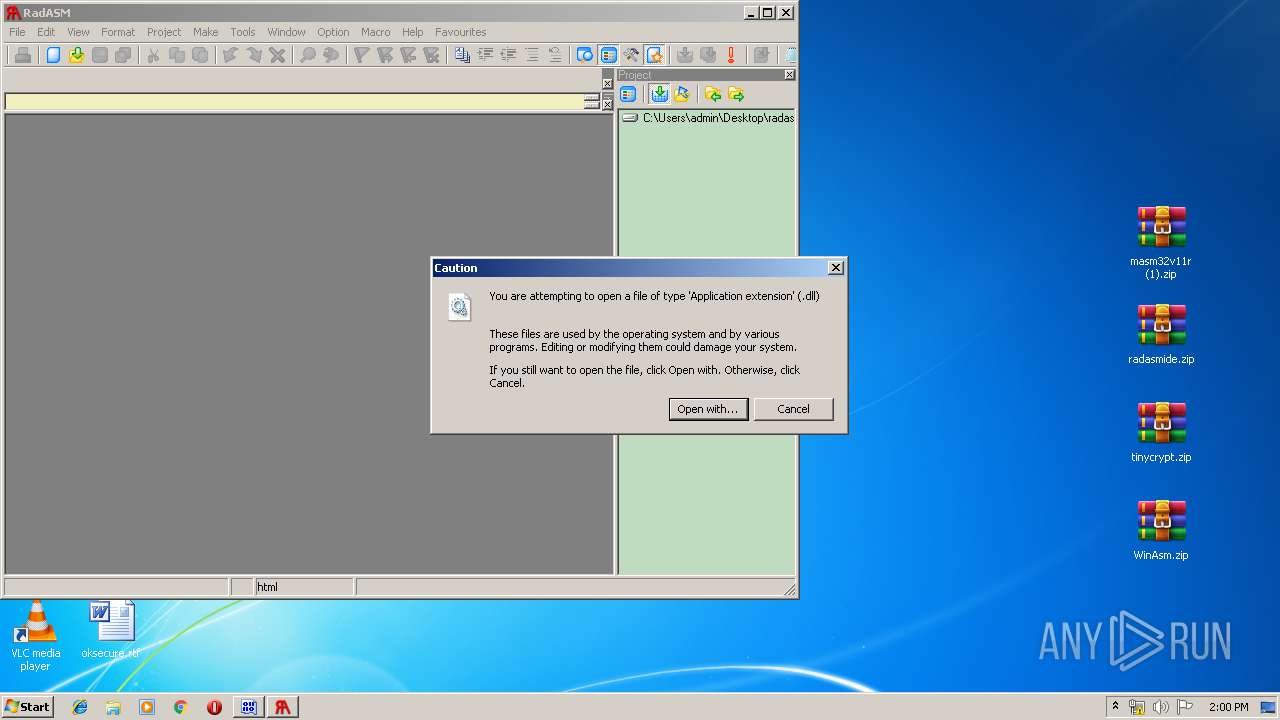
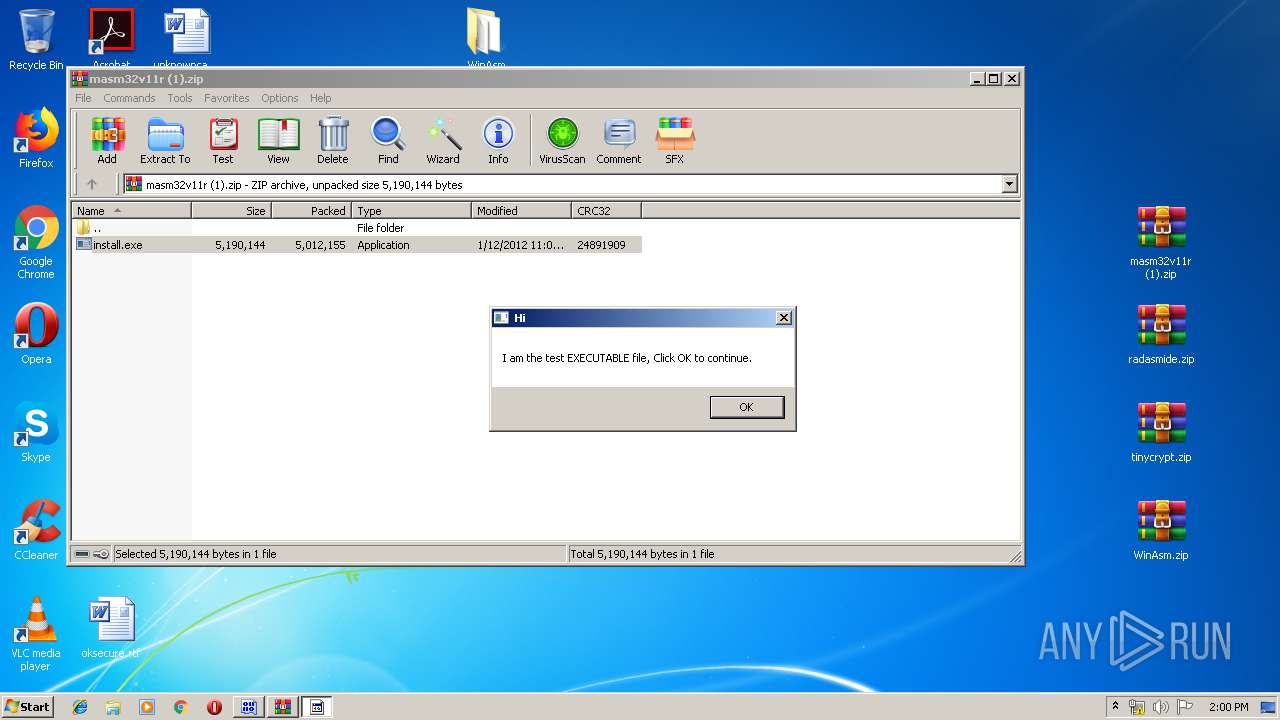
Manual execution by user
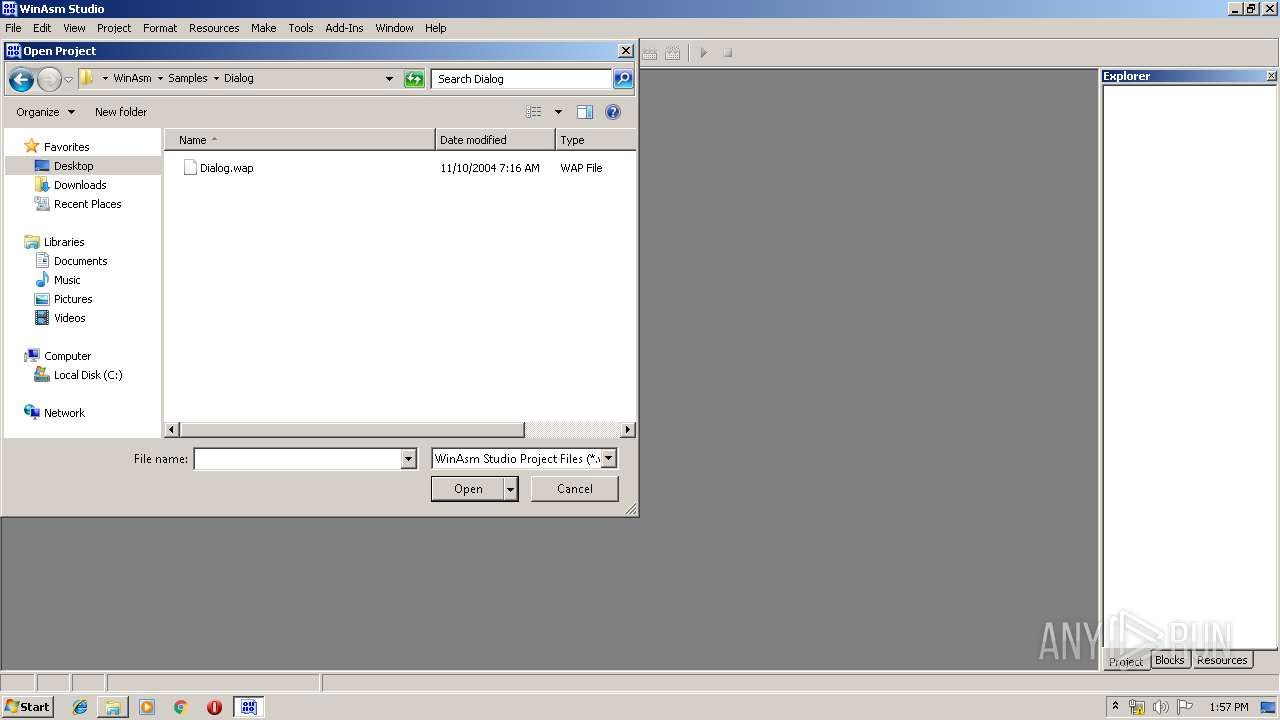
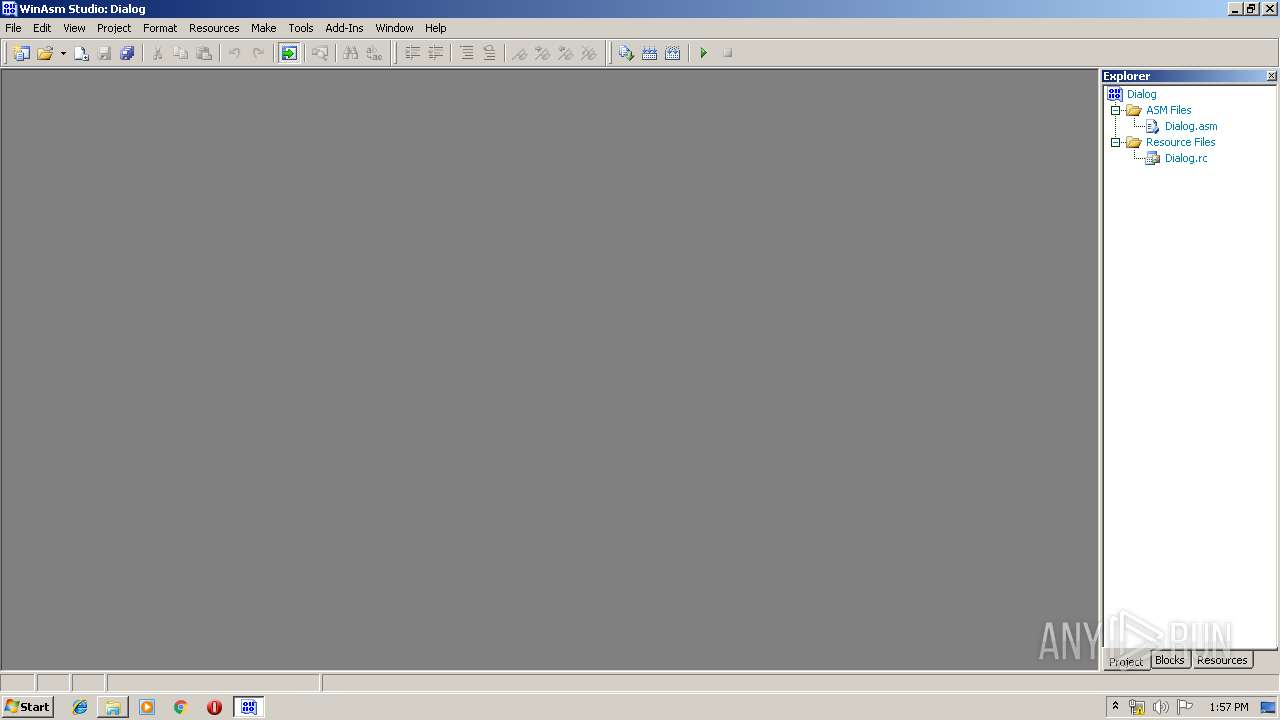
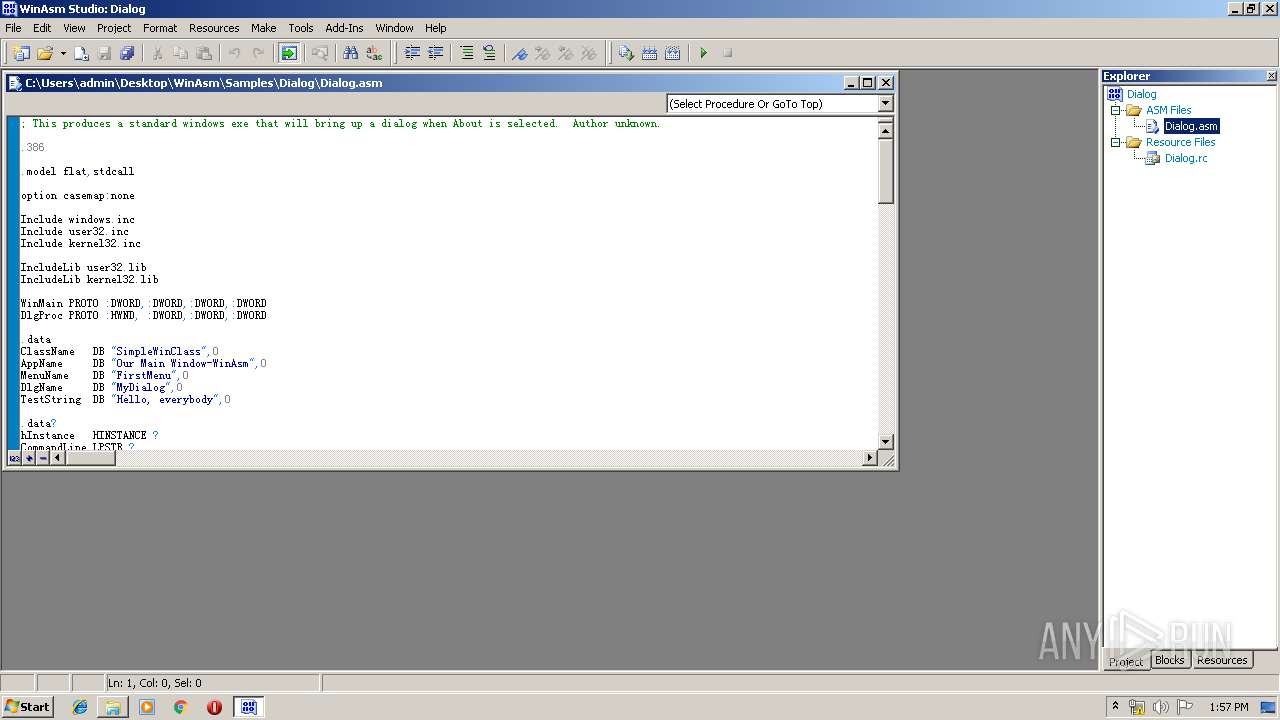
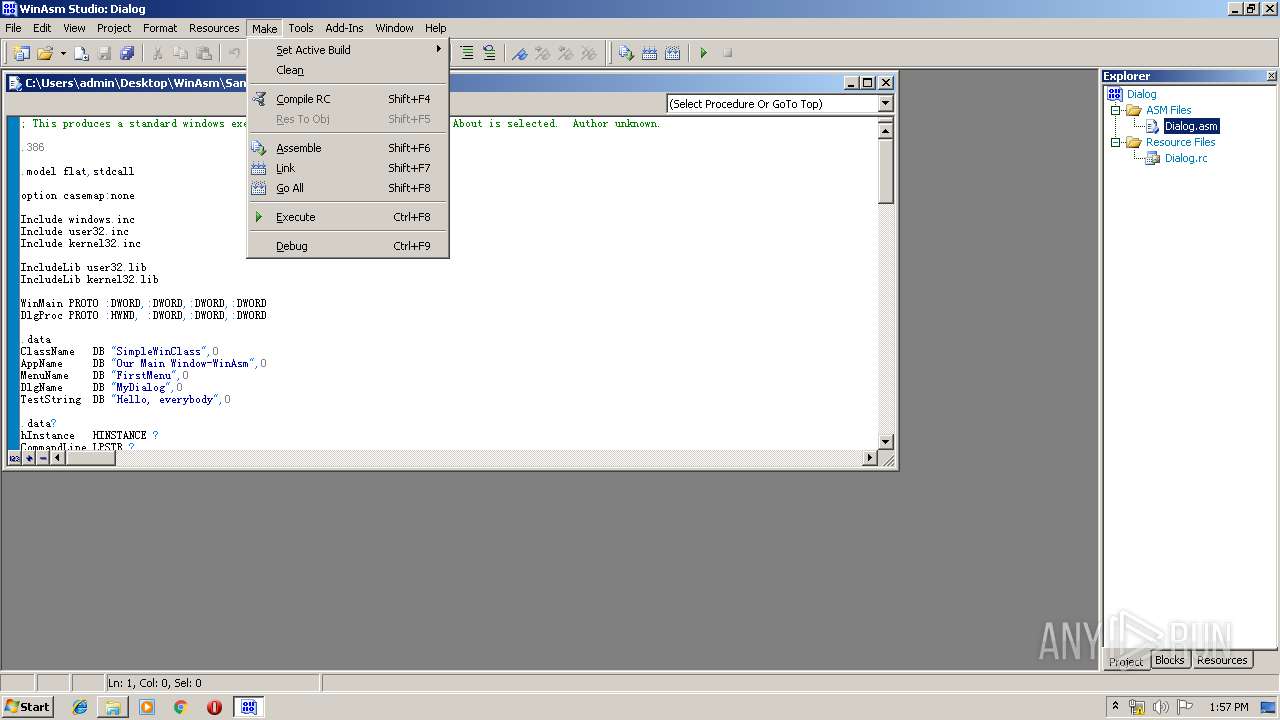
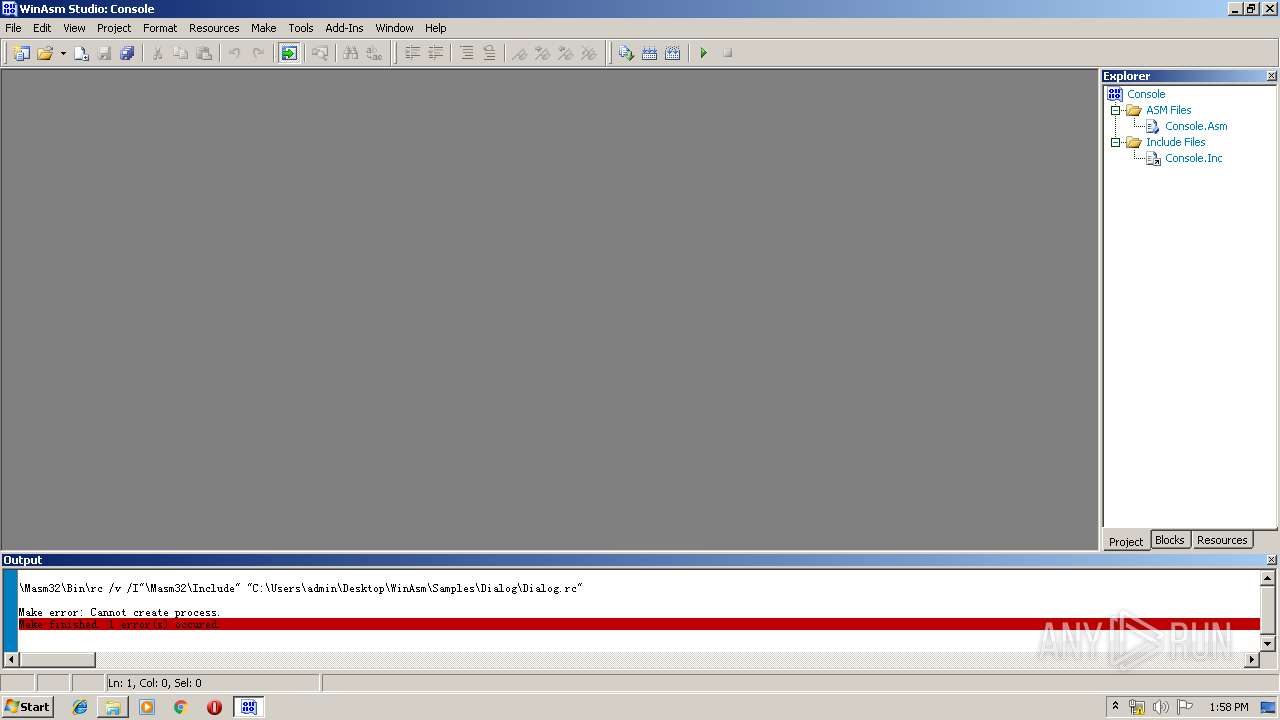
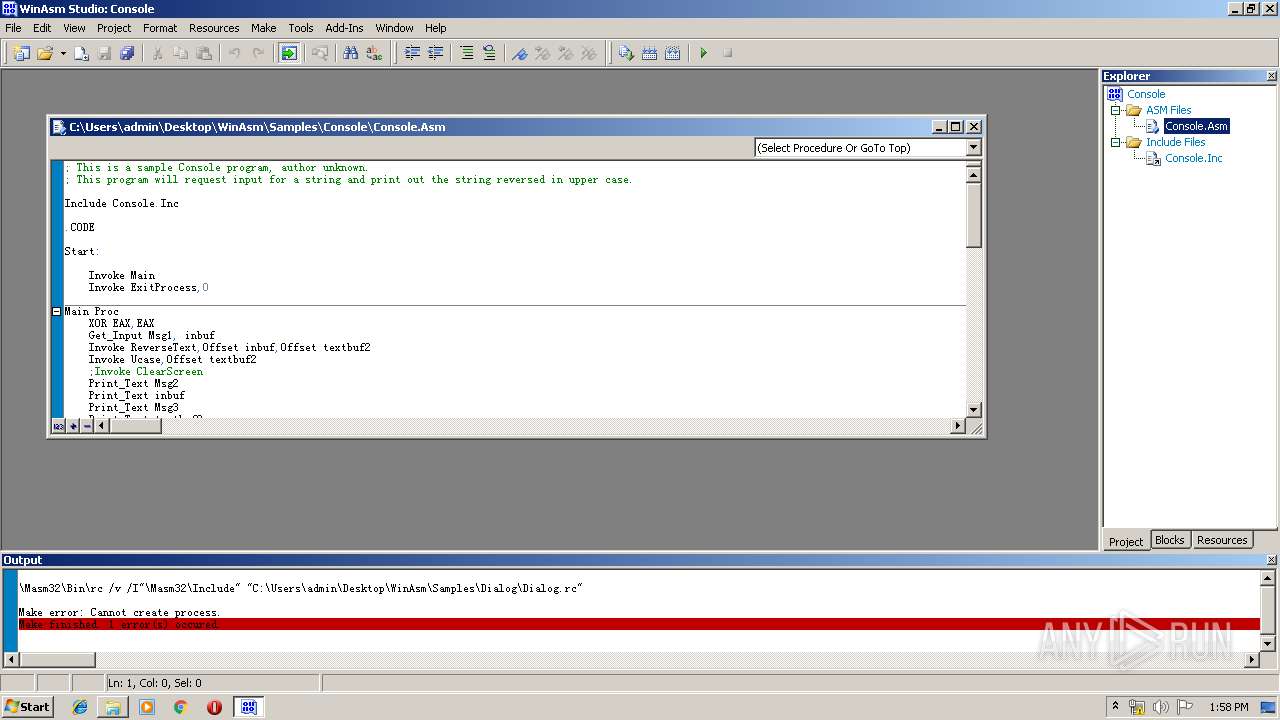
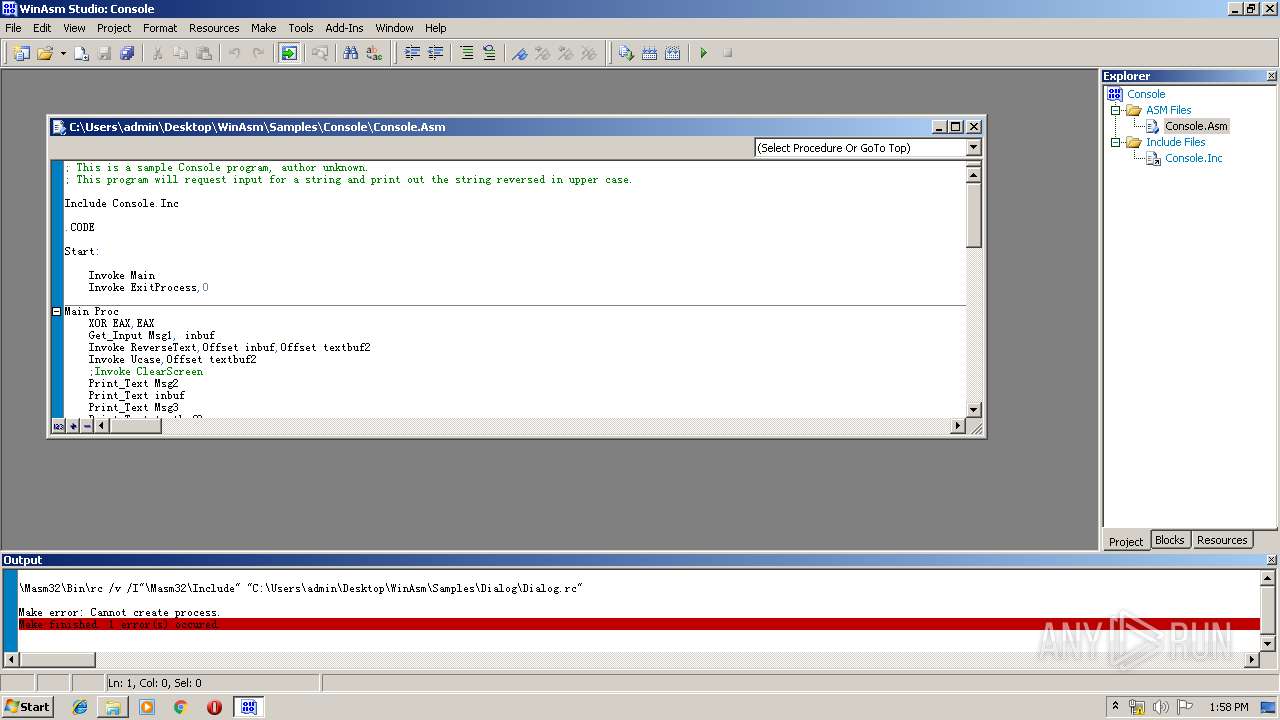
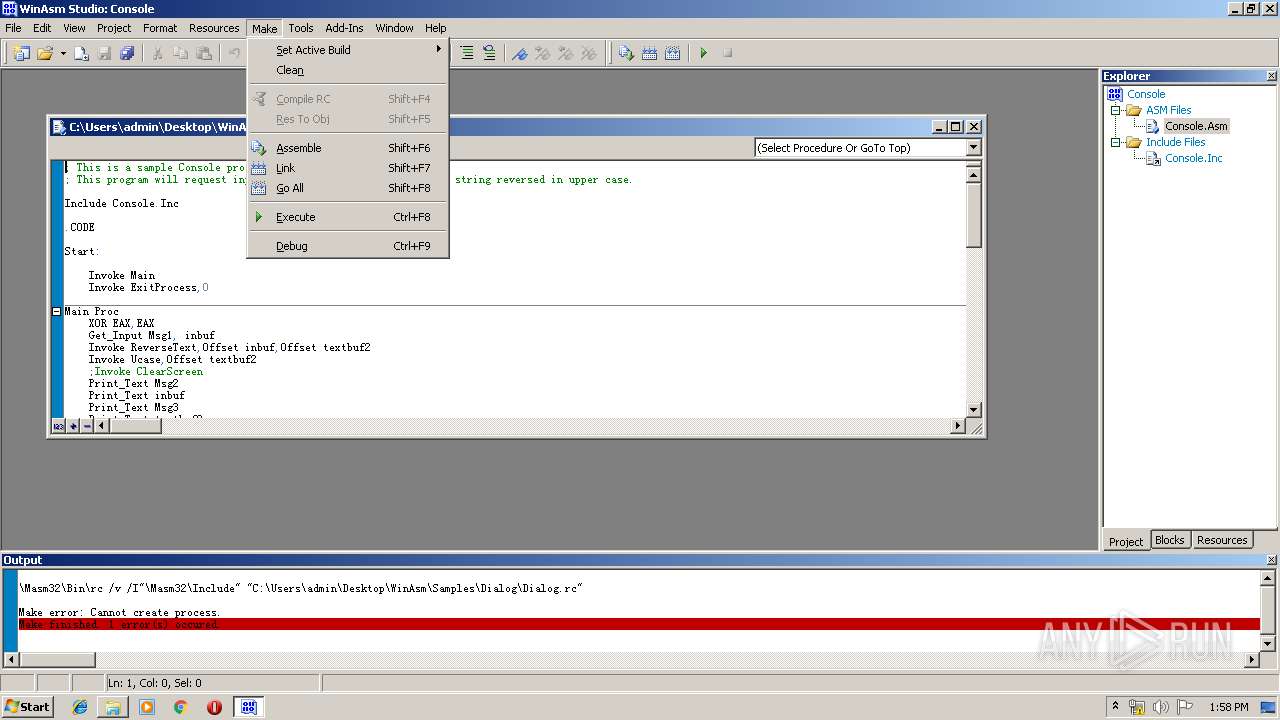
- WinRAR.exe (PID: 3808)
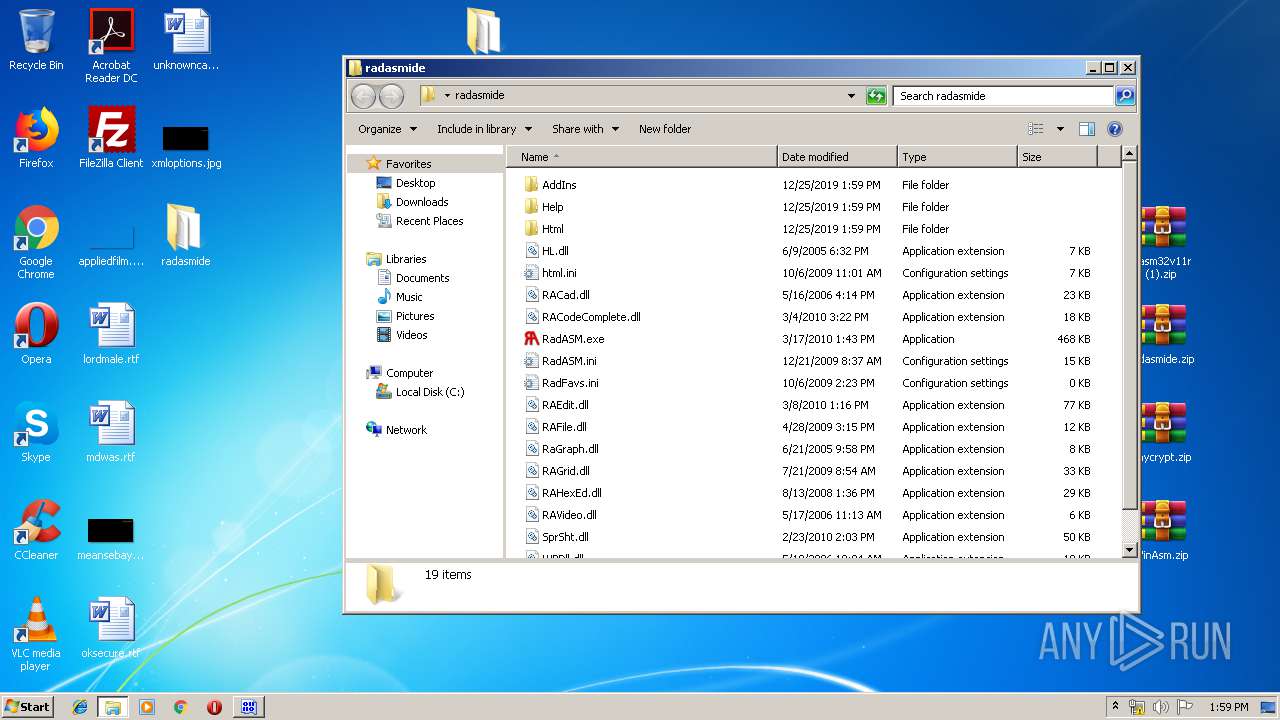
- WinAsm.exe (PID: 2532)
- rundll32.exe (PID: 2968)
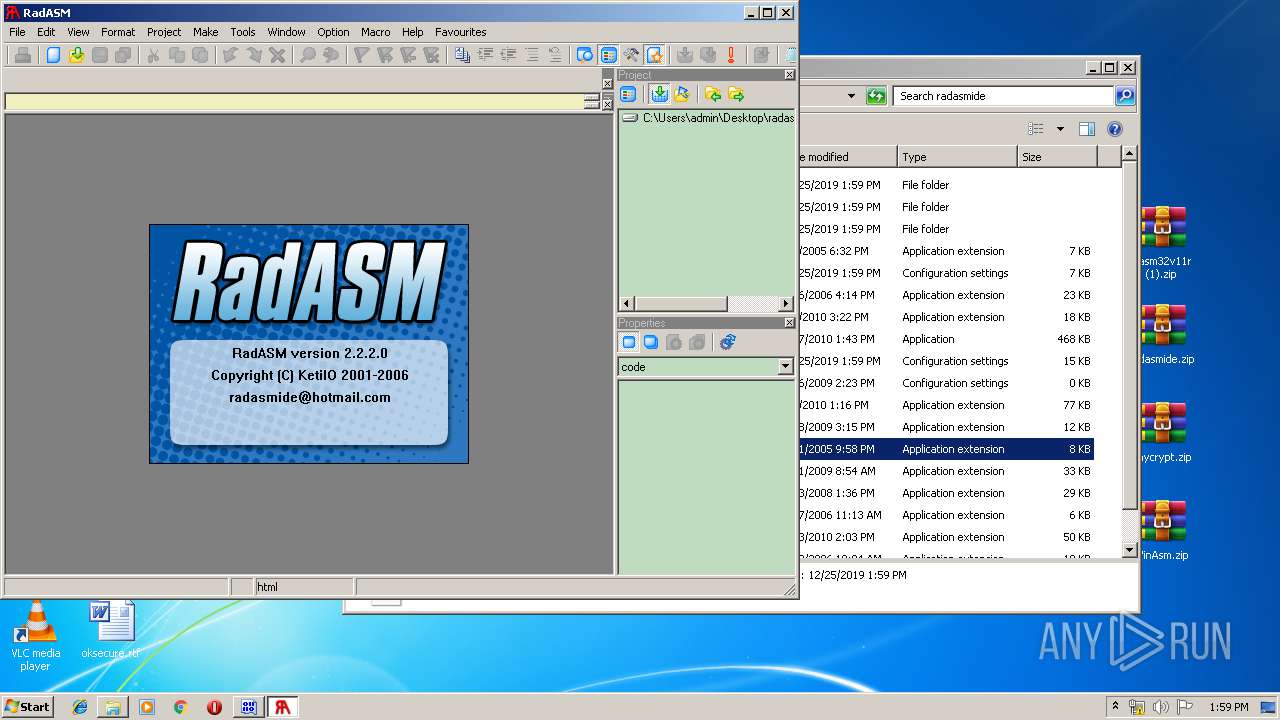
- RadASM.exe (PID: 1712)
- rundll32.exe (PID: 2460)
- WinRAR.exe (PID: 3200)
- WinRAR.exe (PID: 1012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:12:24 21:41:14 |
| ZipCRC: | 0x4b0beb08 |
| ZipCompressedSize: | 5013027 |
| ZipUncompressedSize: | 5012275 |
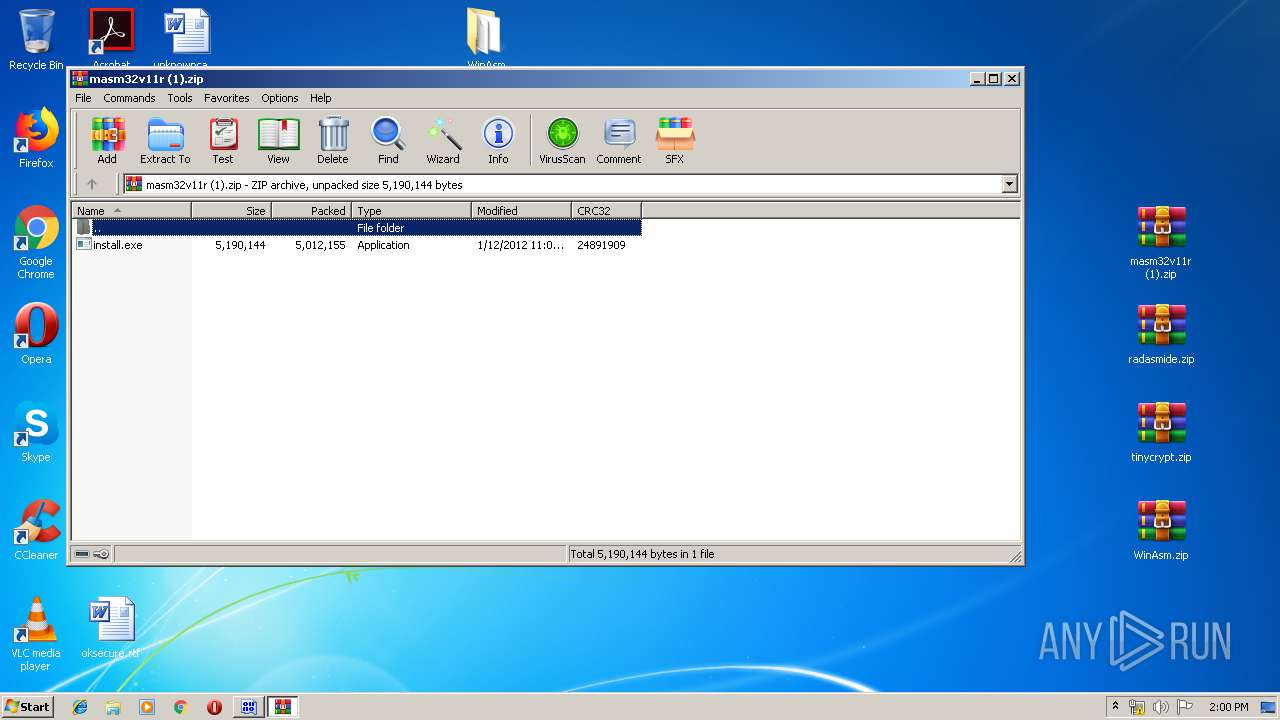
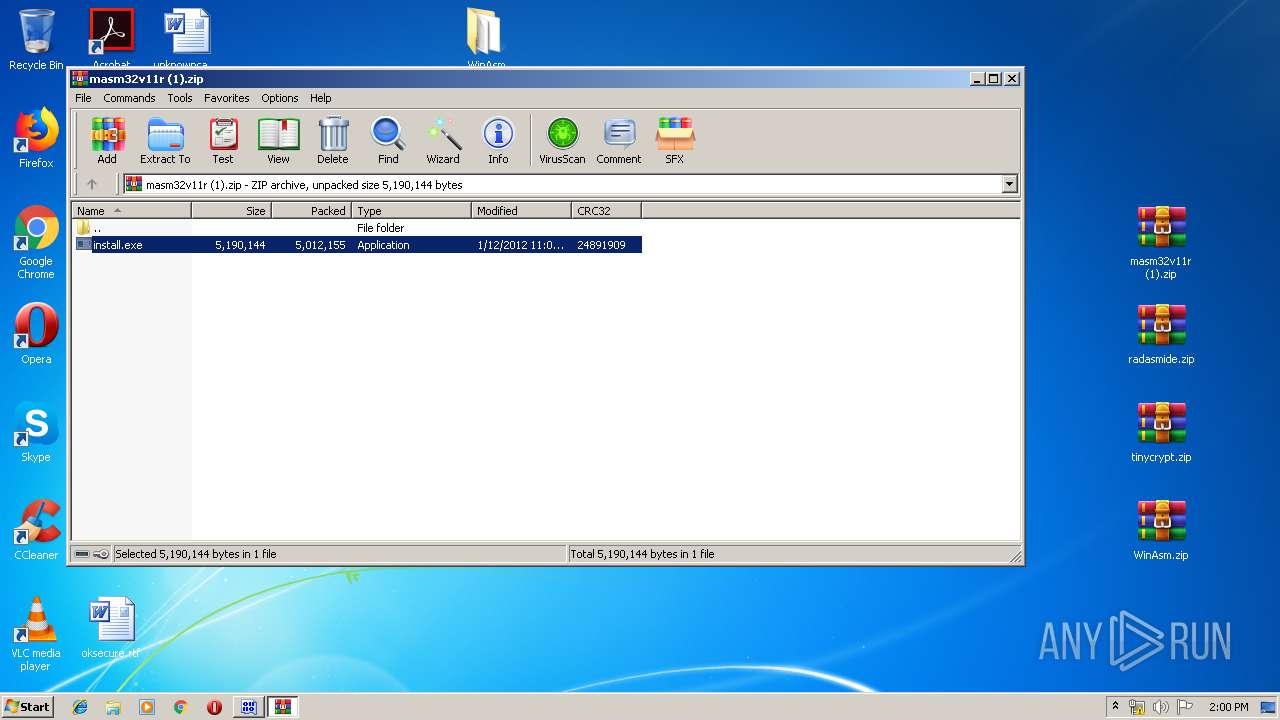
| ZipFileName: | masm32v11r (1).zip |
Total processes
173
Monitored processes
131
Malicious processes
20
Suspicious processes
61
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | inc2l comctl32.inc | C:\masm32\include\inc2l.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 | |||||||||||||||
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
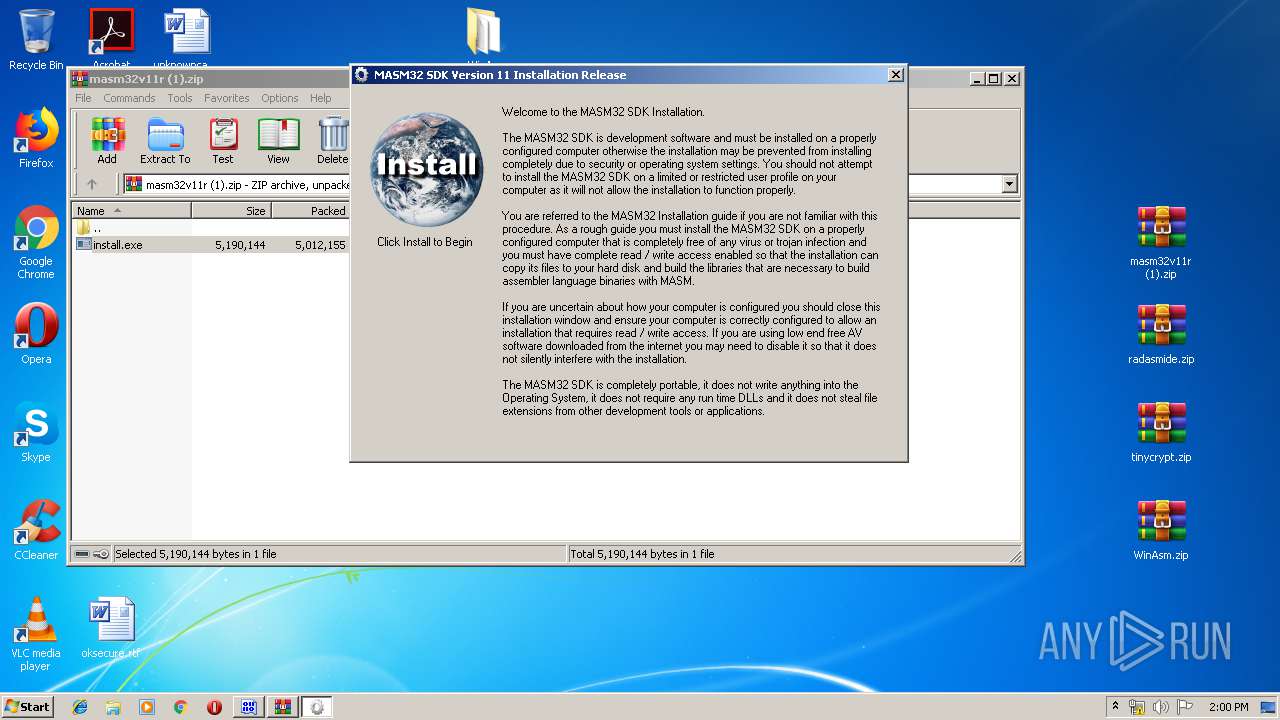
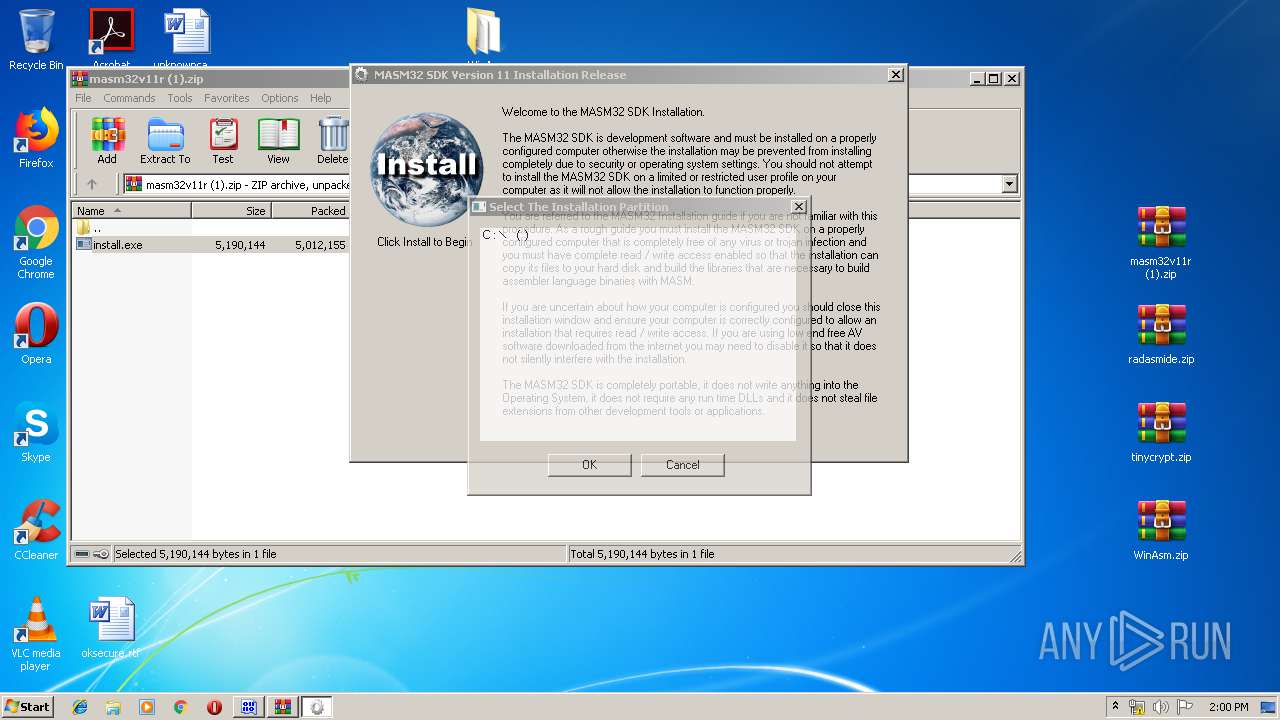
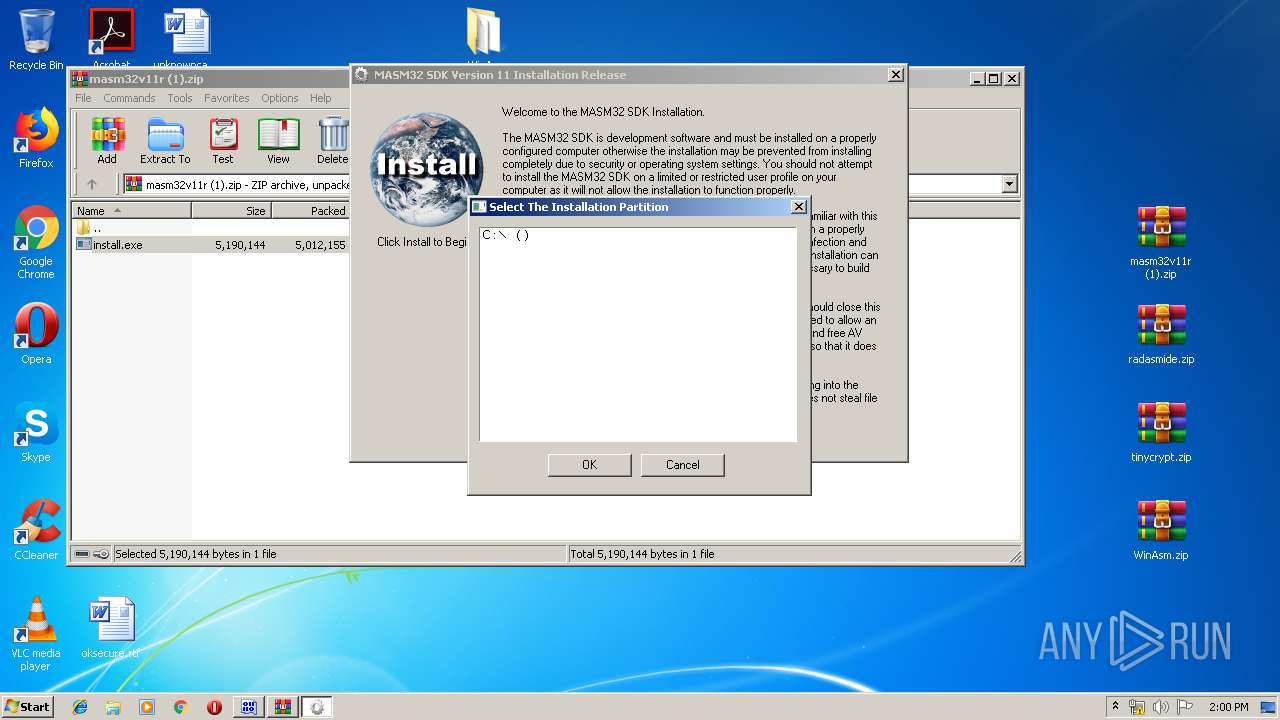
| 388 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3400.42393\install.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3400.42393\install.exe | — | WinRAR.exe | |||||||||||
User: admin Company: The MASM32 SDK Integrity Level: MEDIUM Description: MASM32 Installation Exit code: 3221226540 Version: 11.0 Modules
| |||||||||||||||
| 444 | inc2l advapip.inc | C:\masm32\include\inc2l.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 496 | \masm32\bin\Link /SUBSYSTEM:WINDOWS /DLL /DEF:appmgmts.def appmgmts.obj | C:\masm32\bin\Link.exe | — | inc2l.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) Incremental Linker Exit code: 0 Version: 5.012.8078.0 Modules
| |||||||||||||||
| 504 | \masm32\bin\ml /c /coff advapi32.asm | C:\masm32\bin\ml.exe | — | inc2l.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 516 | \masm32\bin\Link /SUBSYSTEM:WINDOWS /DLL /DEF:arbiter.def arbiter.obj | C:\masm32\bin\Link.exe | — | inc2l.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) Incremental Linker Exit code: 0 Version: 5.012.8078.0 Modules
| |||||||||||||||
| 564 | "C:\masm32\bin\Link.exe" /lib @"C:\Users\admin\AppData\Local\Temp\lah5E53.tmp" | C:\masm32\bin\Link.exe | — | Link.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) Incremental Linker Exit code: 0 Version: 5.012.8078.0 Modules
| |||||||||||||||
| 600 | \masm32\bin\Link /SUBSYSTEM:WINDOWS /DLL /DEF:apidll.def apidll.obj | C:\masm32\bin\Link.exe | — | inc2l.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) Incremental Linker Exit code: 0 Version: 5.012.8078.0 Modules
| |||||||||||||||
| 616 | \masm32\bin\ml /c /coff comctl32.asm | C:\masm32\bin\ml.exe | — | inc2l.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 | |||||||||||||||
Total events
10 672
Read events
9 790
Write events
876
Delete events
6
Modification events
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\test.zip | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3340) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
Executable files
289
Suspicious files
32
Text files
1 924
Unknown types
108
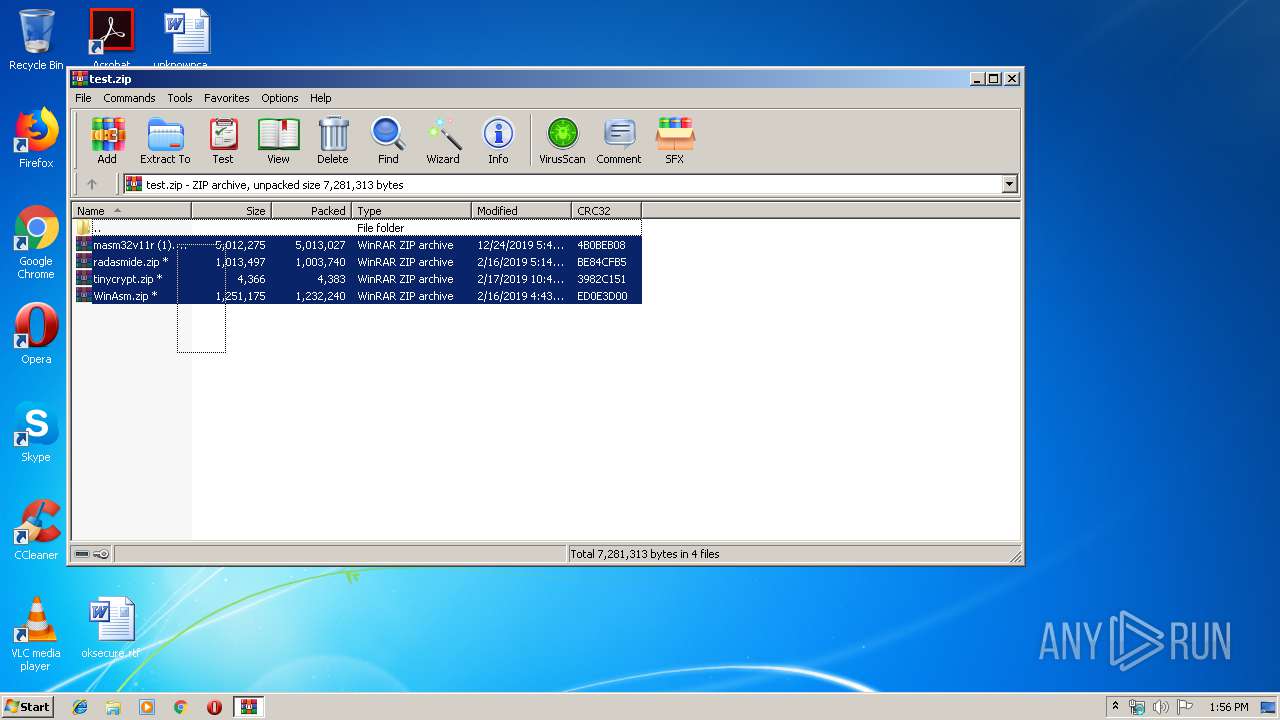
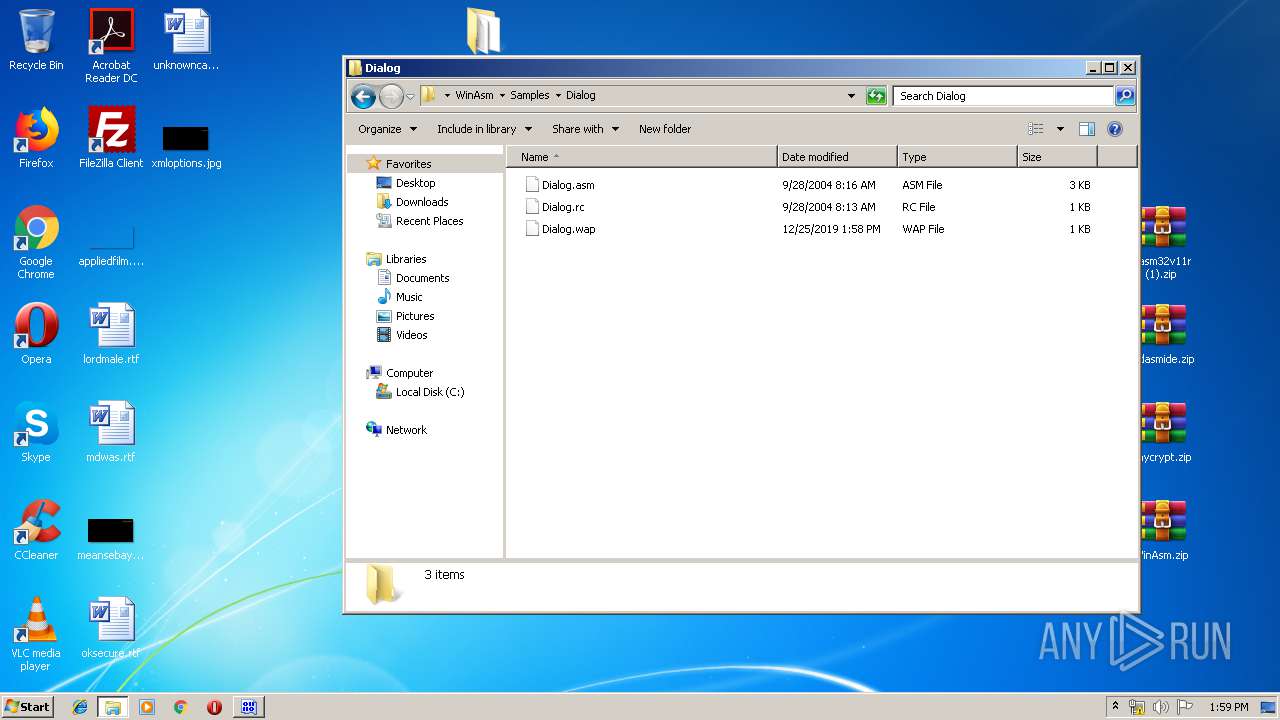
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
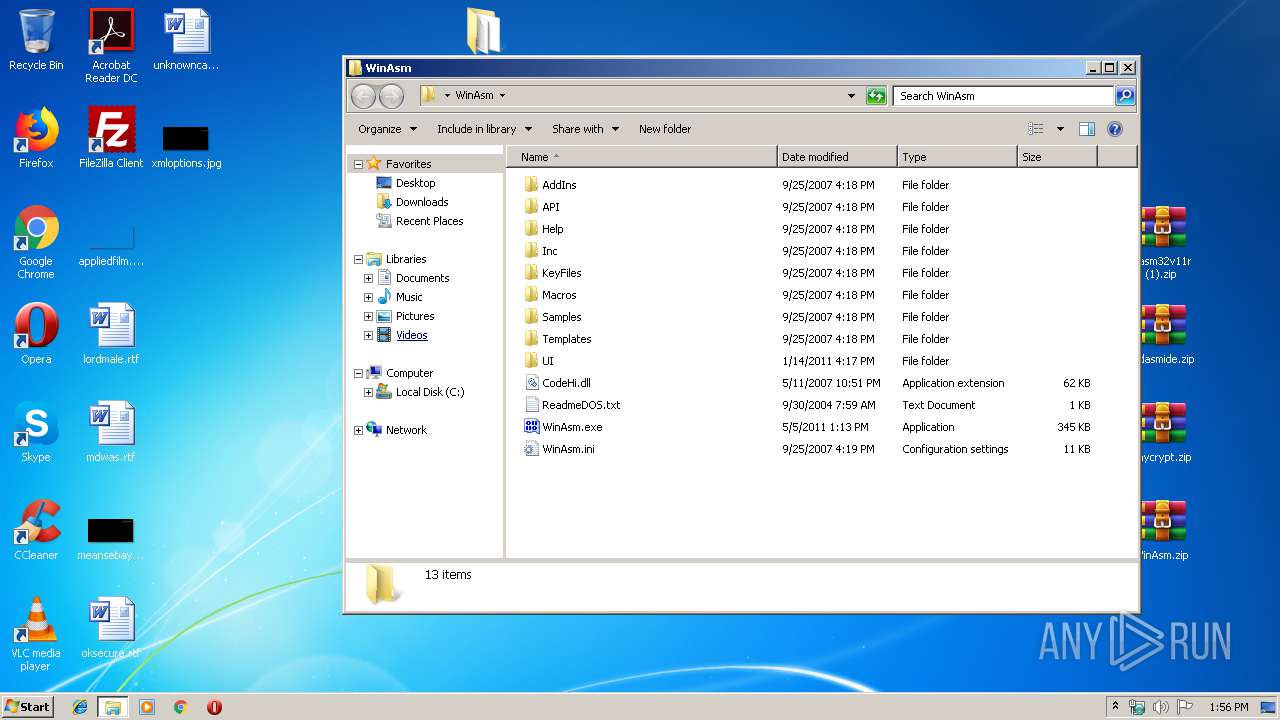
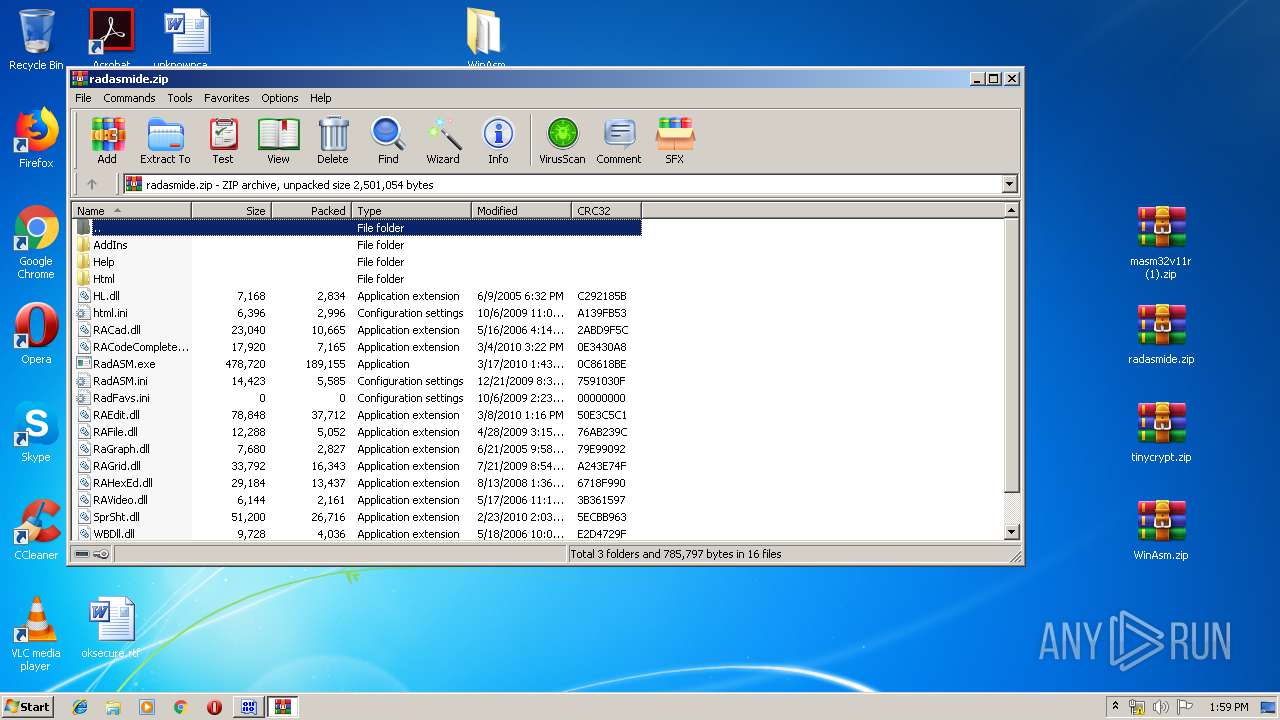
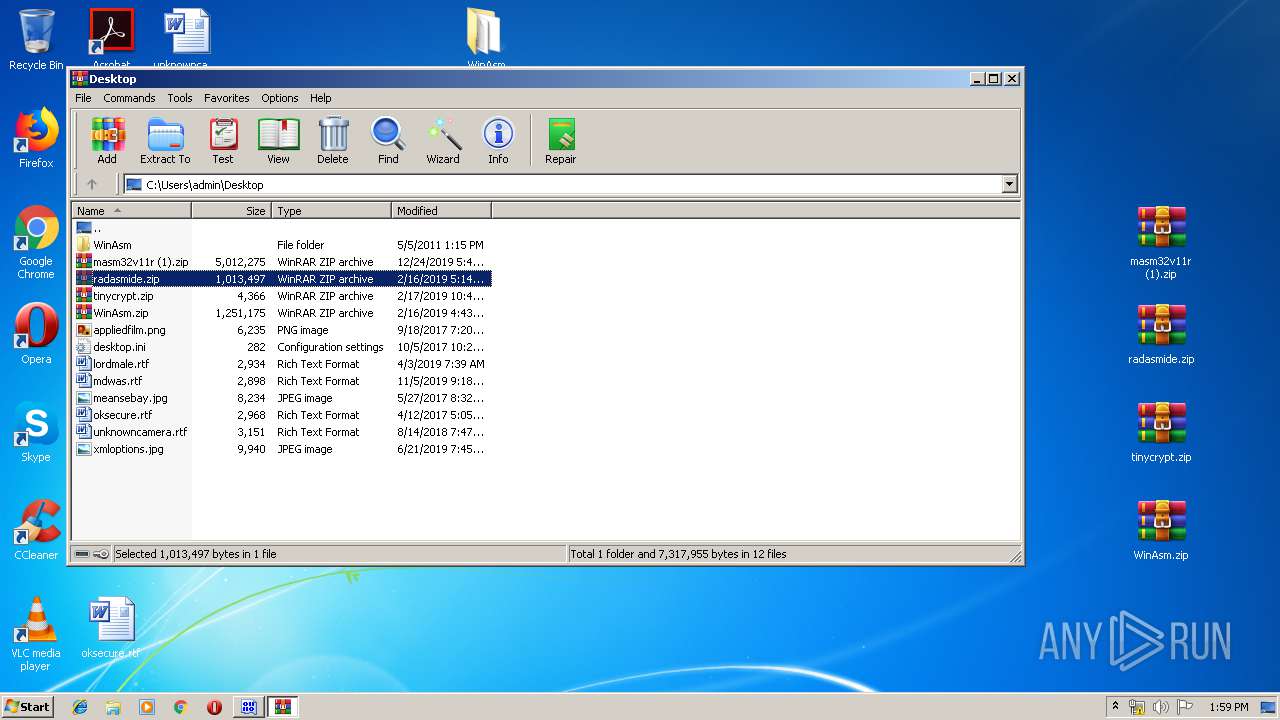
| 3340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3340.19472\masm32v11r (1).zip | — | |
MD5:— | SHA256:— | |||
| 3340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3340.19472\radasmide.zip | — | |
MD5:— | SHA256:— | |||
| 3340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3340.19472\tinycrypt.zip | — | |
MD5:— | SHA256:— | |||
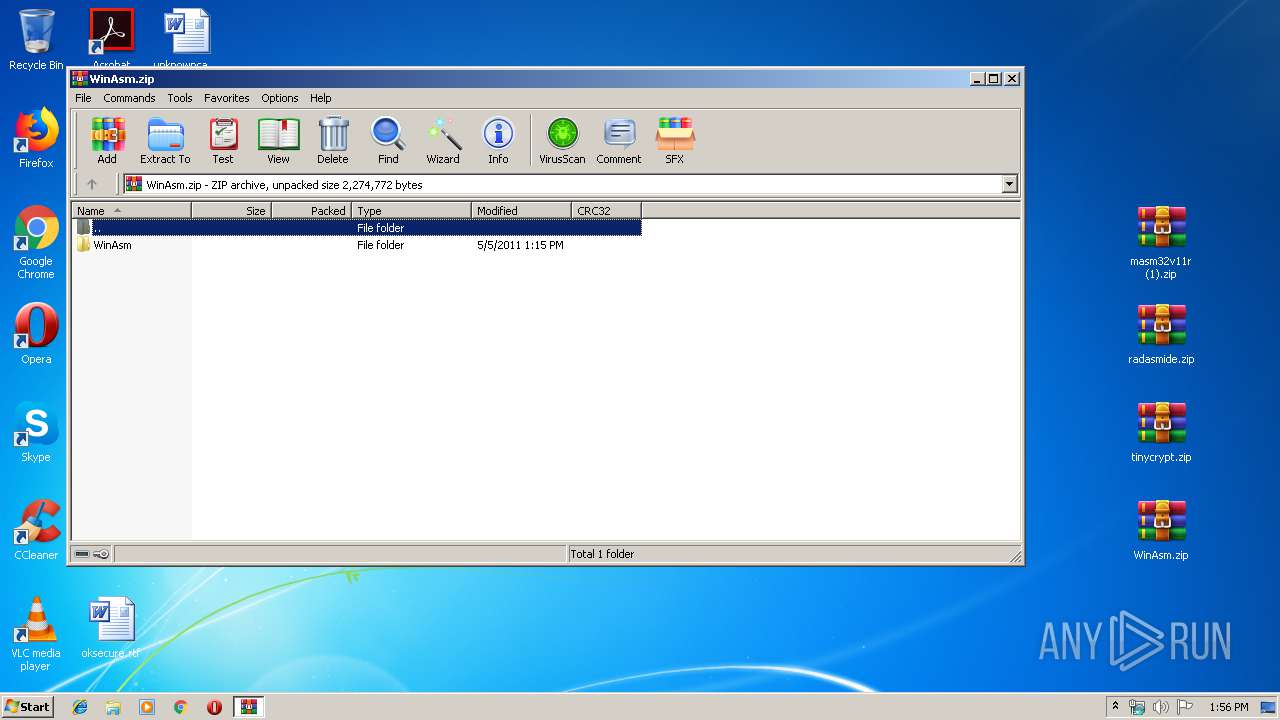
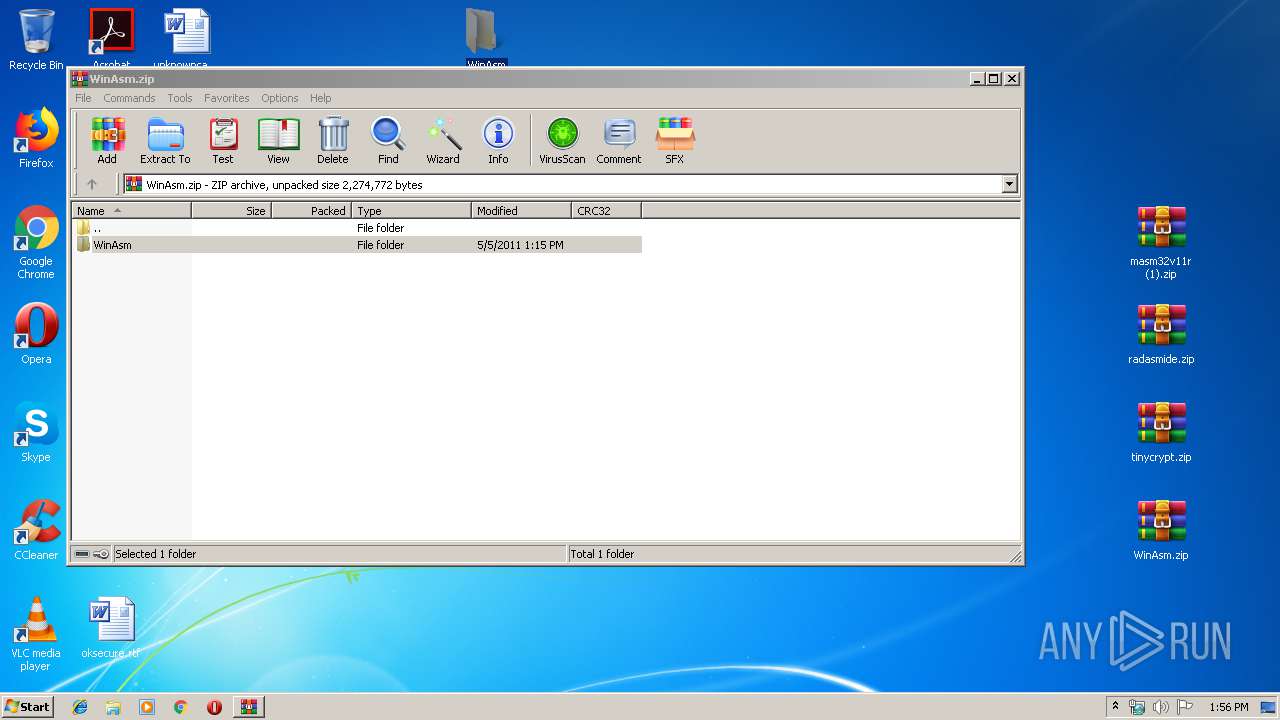
| 3340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3340.19472\WinAsm.zip | — | |
MD5:— | SHA256:— | |||
| 1012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1012.20989\WinAsm\AddIns\ClientColor.dll | — | |
MD5:— | SHA256:— | |||
| 1012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1012.20989\WinAsm\AddIns\MiniDBG.dll | — | |
MD5:— | SHA256:— | |||
| 1012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1012.20989\WinAsm\AddIns\SetImages.dll | — | |
MD5:— | SHA256:— | |||
| 1012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1012.20989\WinAsm\AddIns\XWindows.dll | — | |
MD5:— | SHA256:— | |||
| 1012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1012.20989\WinAsm\API\MasmApiCall.vaa | — | |
MD5:— | SHA256:— | |||
| 1012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1012.20989\WinAsm\API\MasmApiConst.vaa | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report