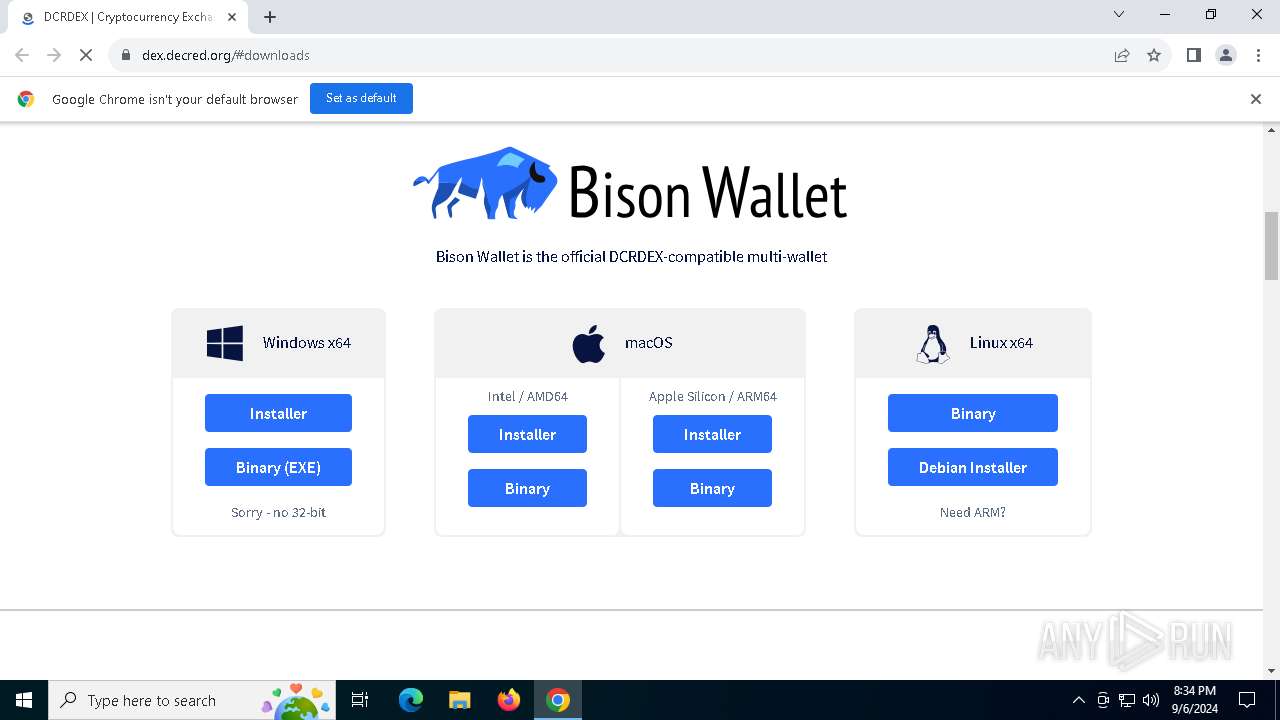
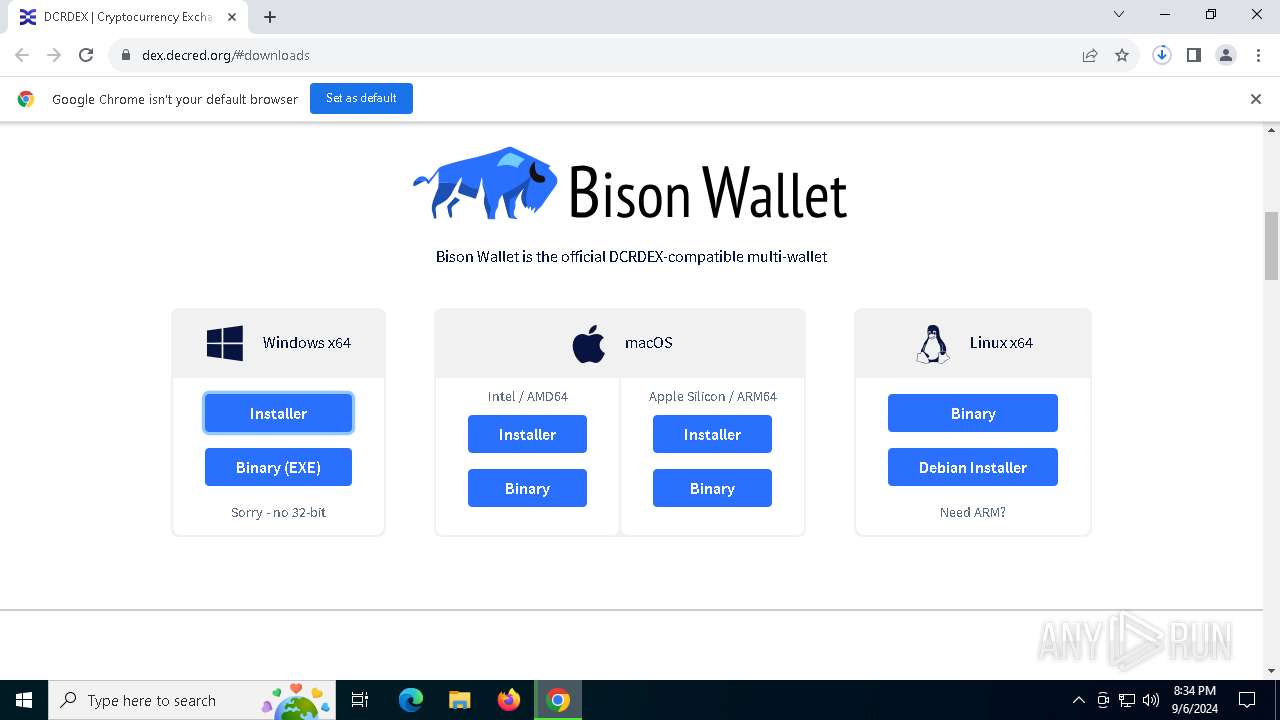
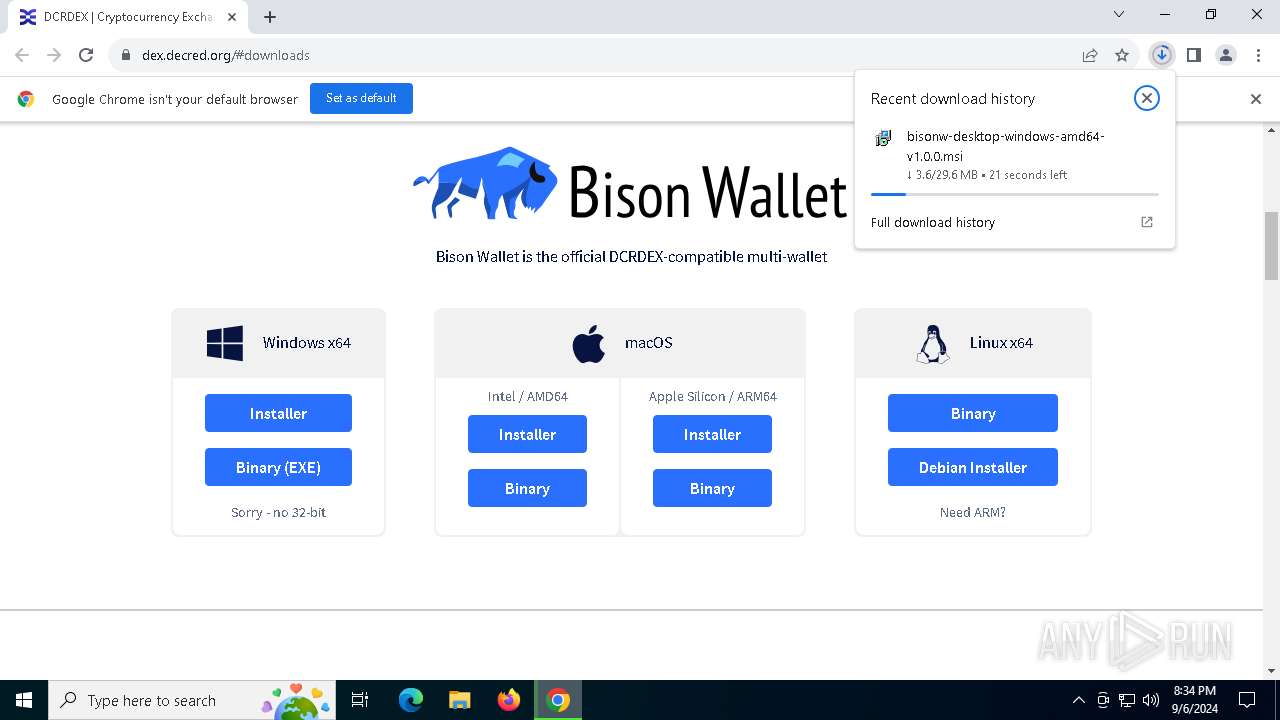
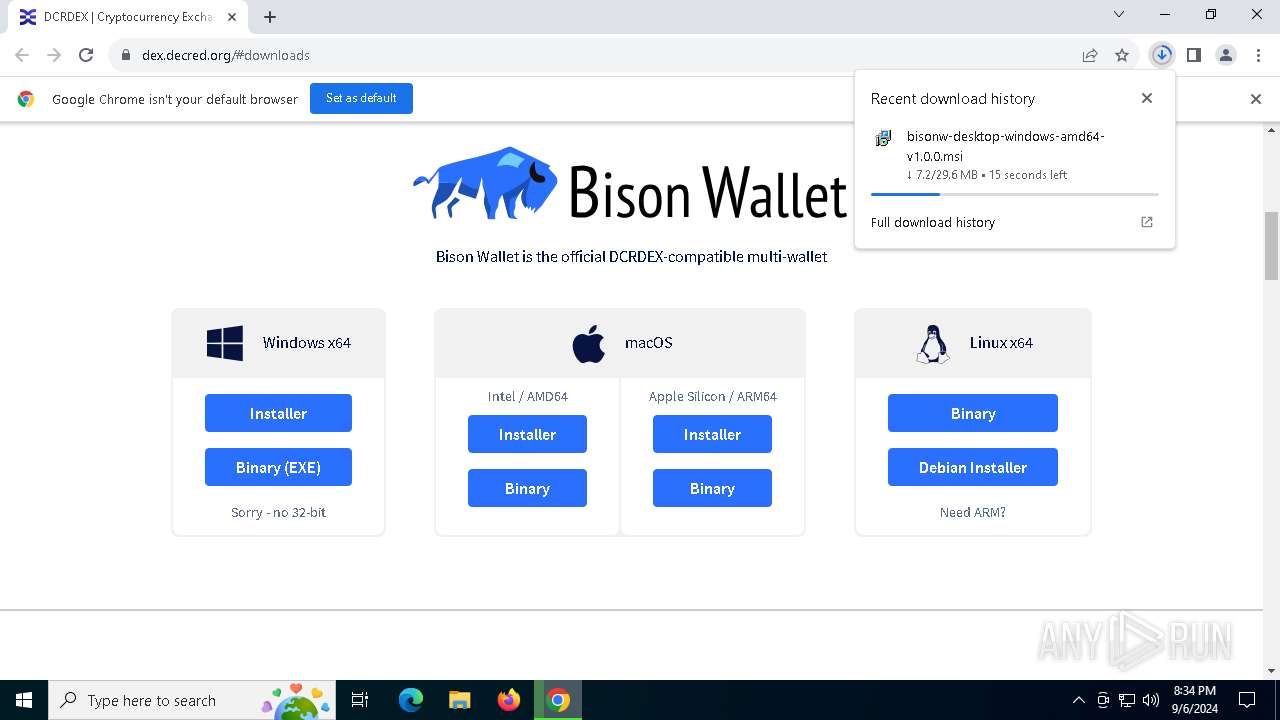
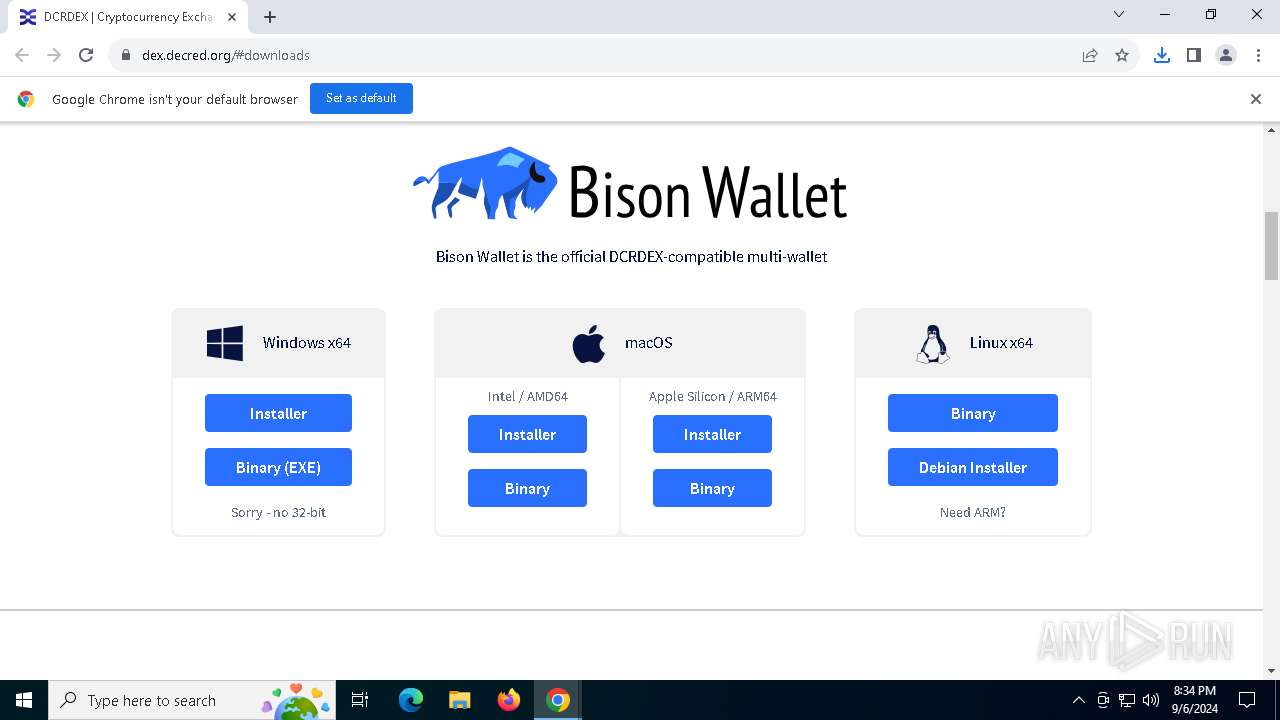
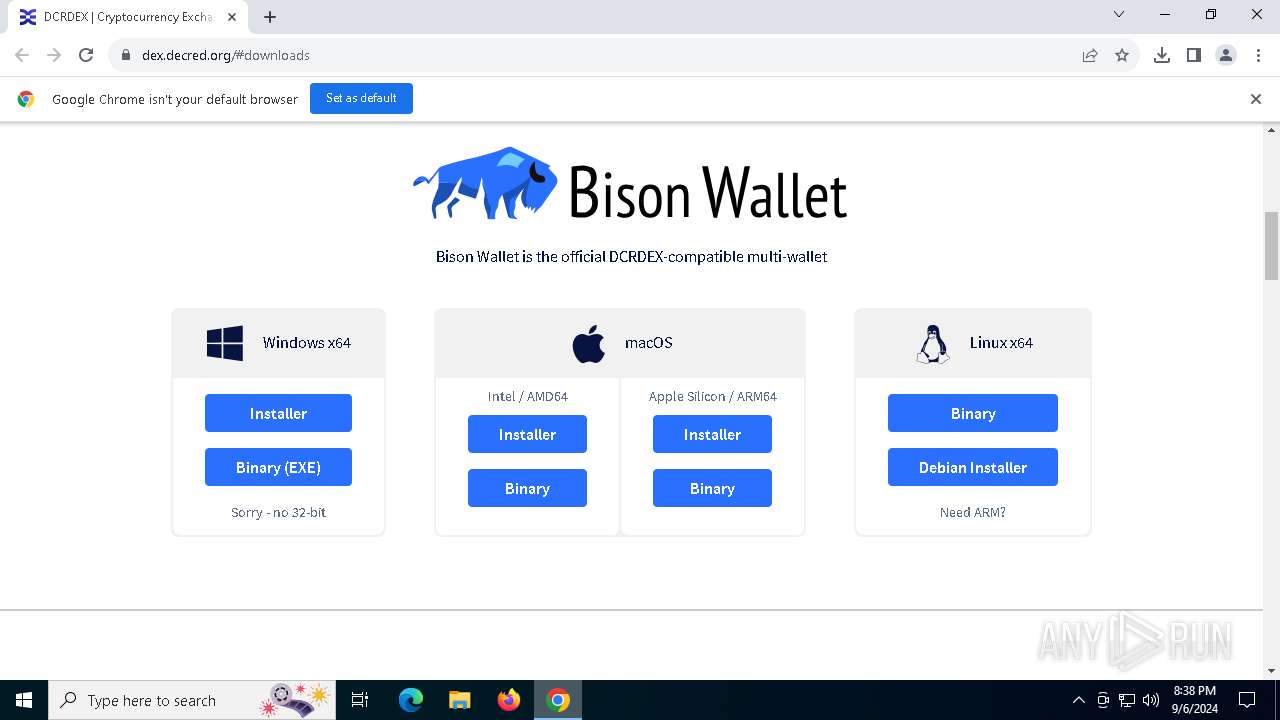
| URL: | https://dex.decred.org/#downloads |
| Full analysis: | https://app.any.run/tasks/85043d92-e859-4ba0-a953-0ad6408cd6bd |
| Verdict: | Malicious activity |
| Analysis date: | September 06, 2024, 20:34:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | B1F391A9EE287509594CBF087E3C2B3E |
| SHA1: | 0C96D902BAEA0F69E249D0984A5BAFF70388AC9D |
| SHA256: | FF7FE0EA3416E488A574248B158FDC976B59EADB0FFB7AD676D1AA611EE4FE3D |
| SSDEEP: | 3:N8Y4Ak+sFJ4n:2Y4AJsk |
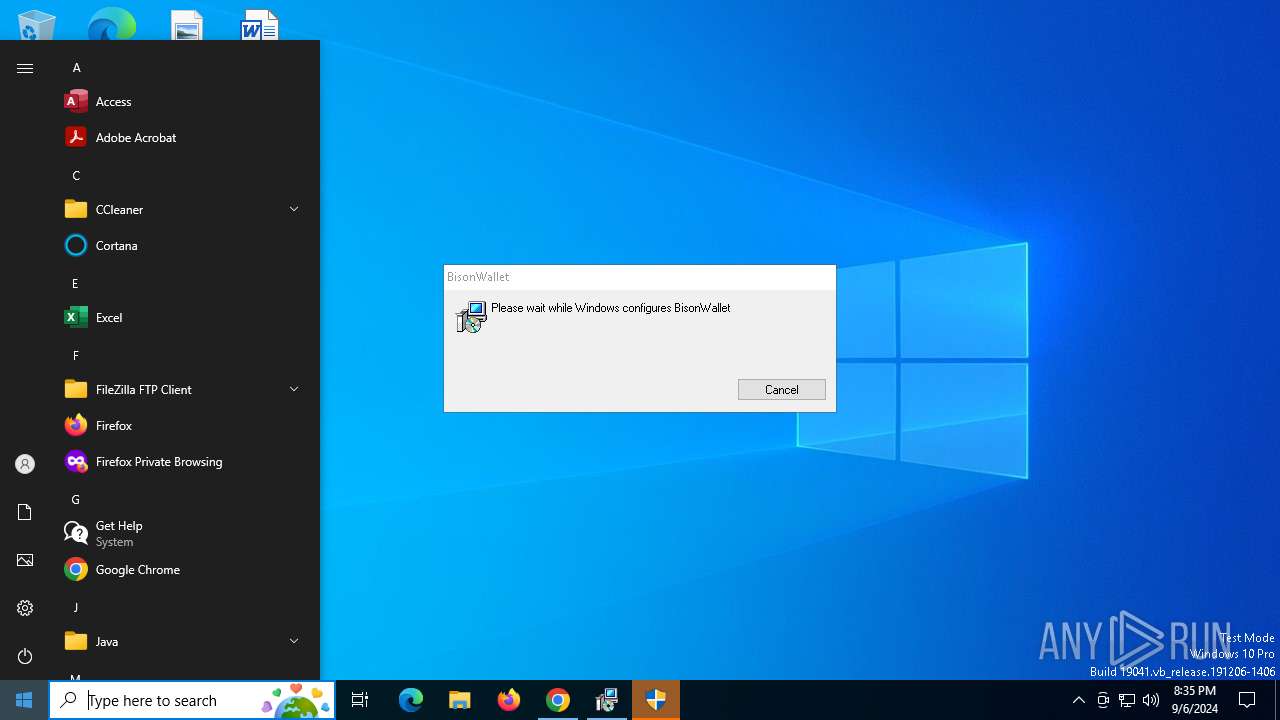
MALICIOUS
No malicious indicators.SUSPICIOUS
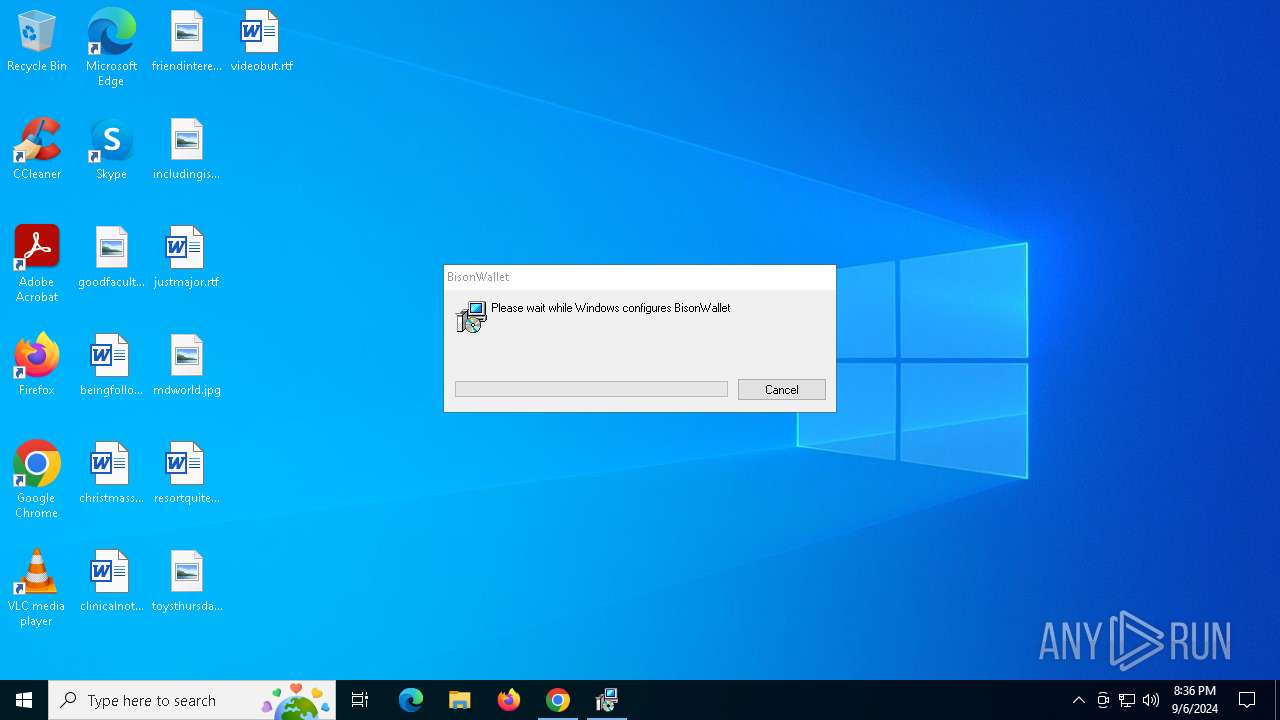
Executes as Windows Service
- VSSVC.exe (PID: 5172)
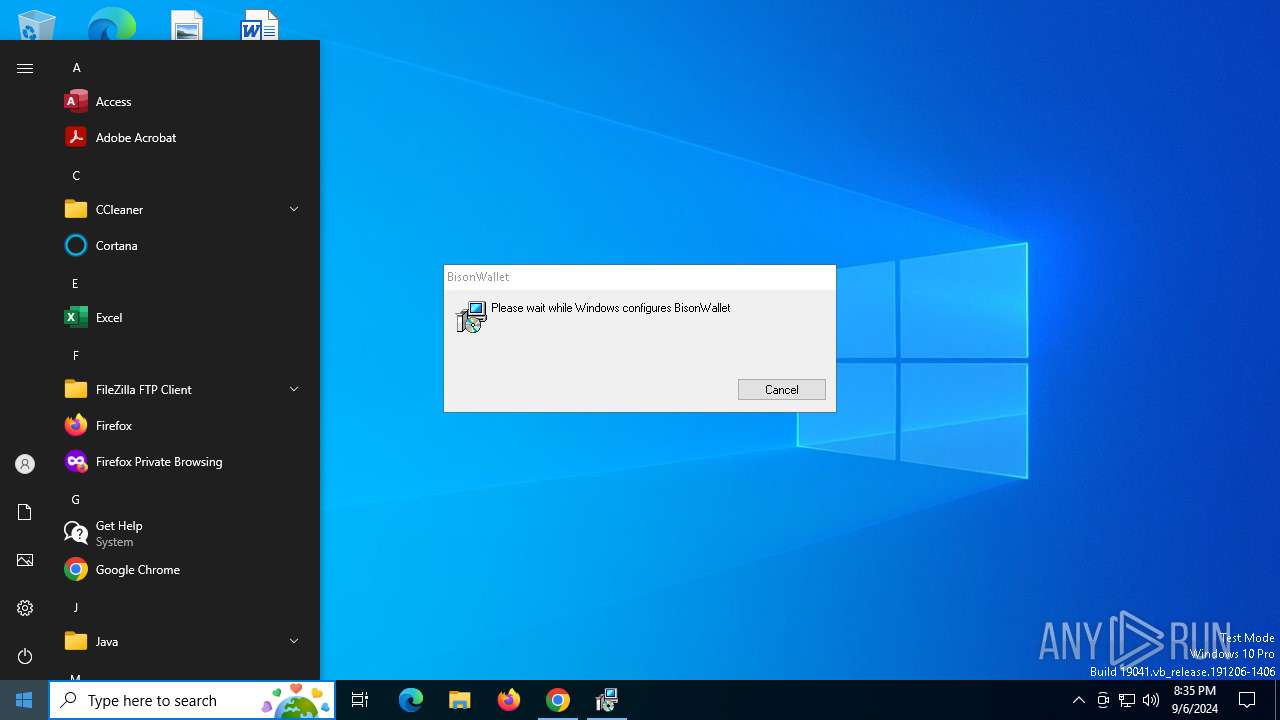
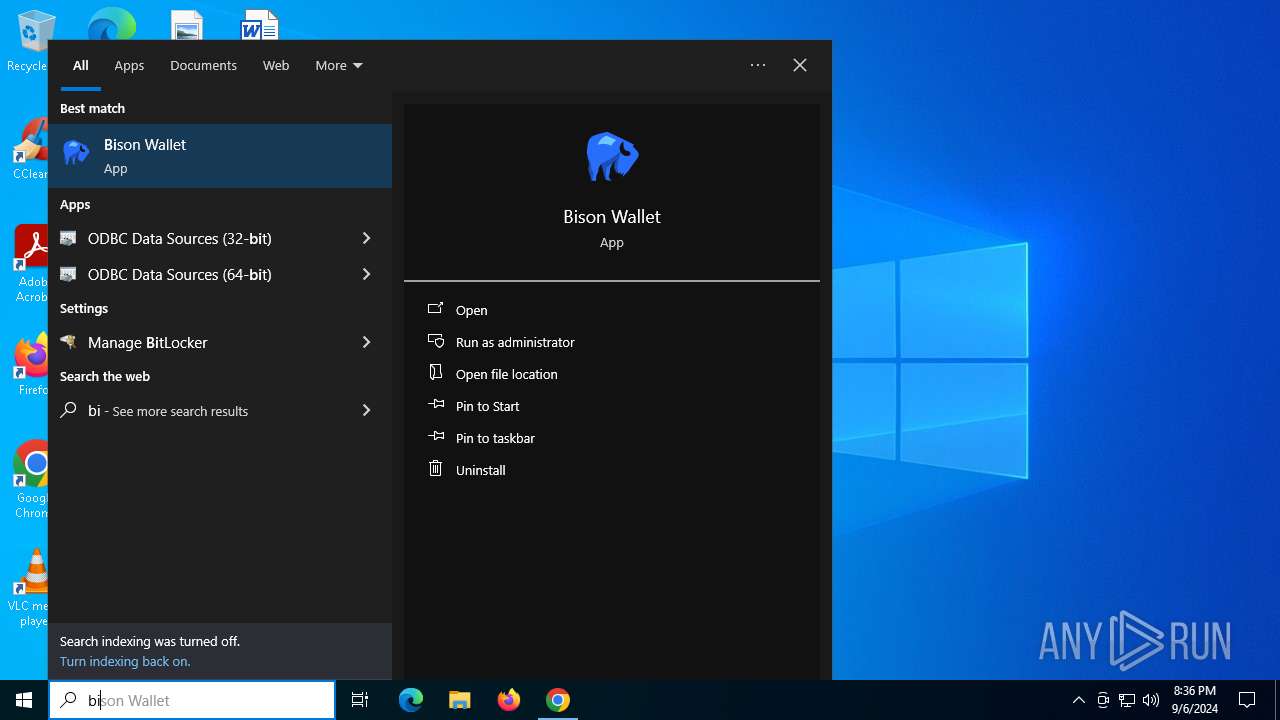
Starts POWERSHELL.EXE for commands execution
- Bisonw-desktop.exe (PID: 4164)
- Bisonw-desktop.exe (PID: 7020)
- Bisonw-desktop.exe (PID: 4344)
- Bisonw-desktop.exe (PID: 2680)
Reads the Windows owner or organization settings
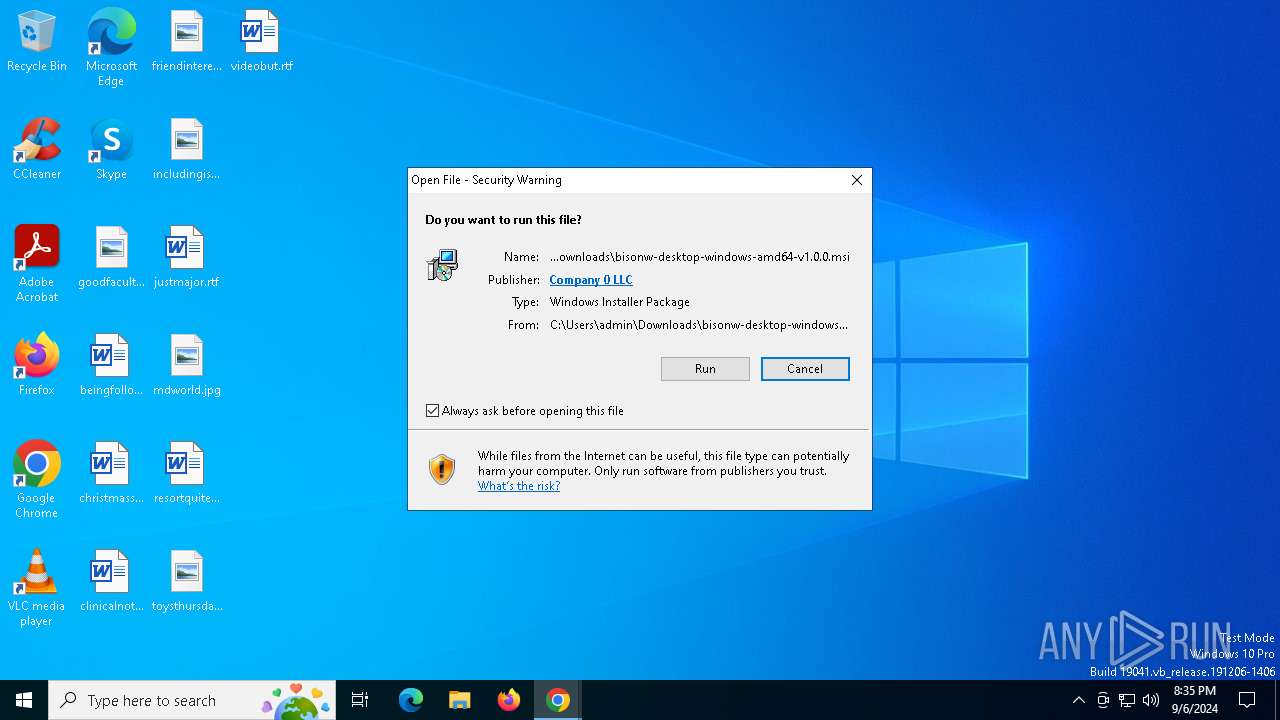
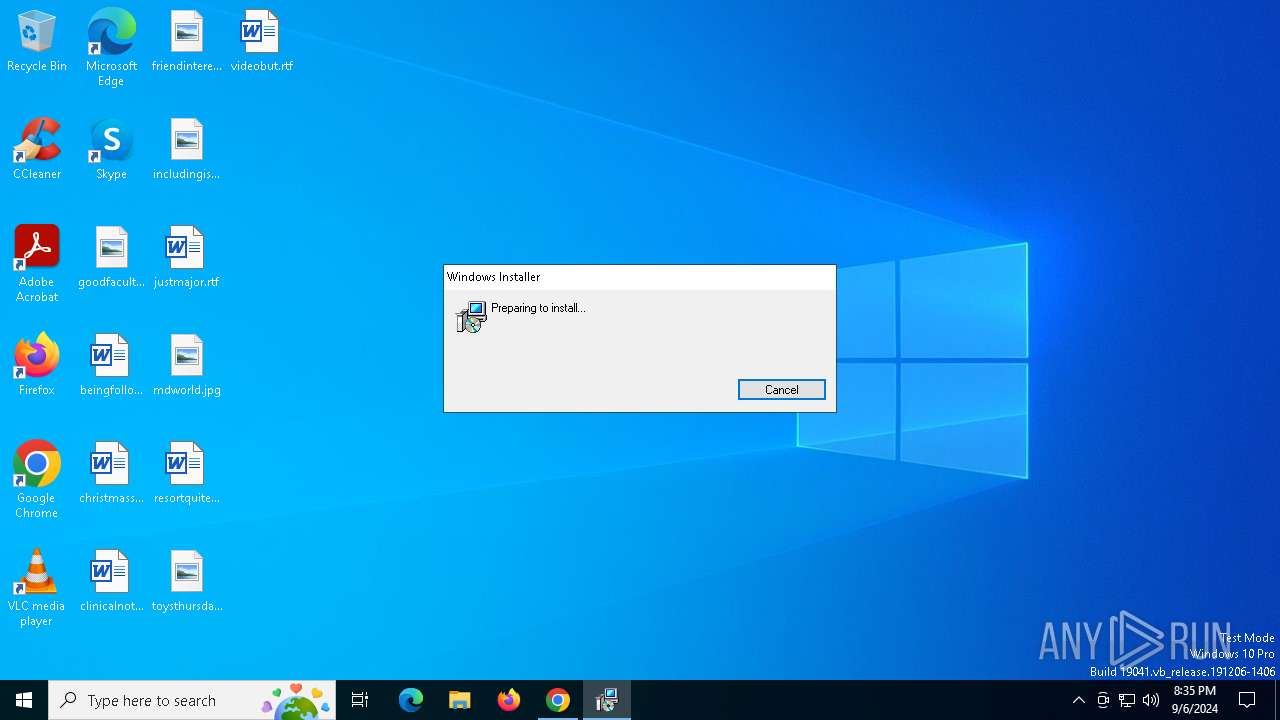
- msiexec.exe (PID: 7008)
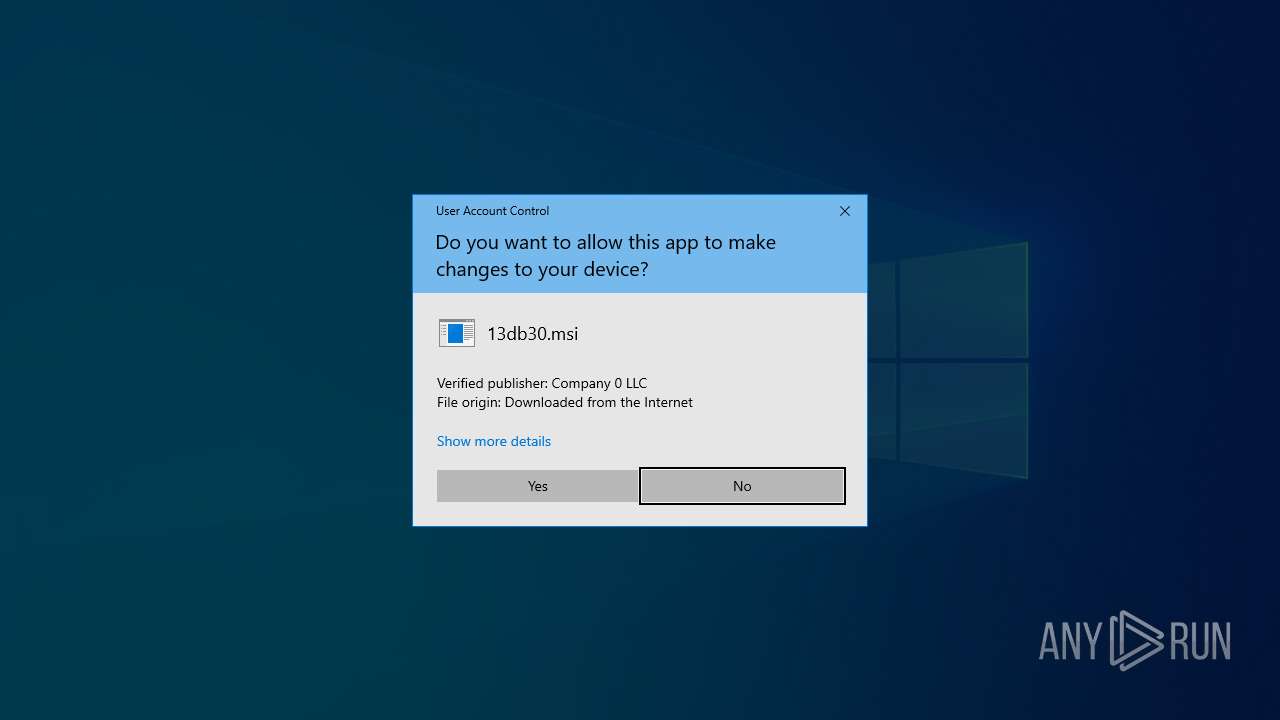
Process drops legitimate windows executable
- msiexec.exe (PID: 7008)
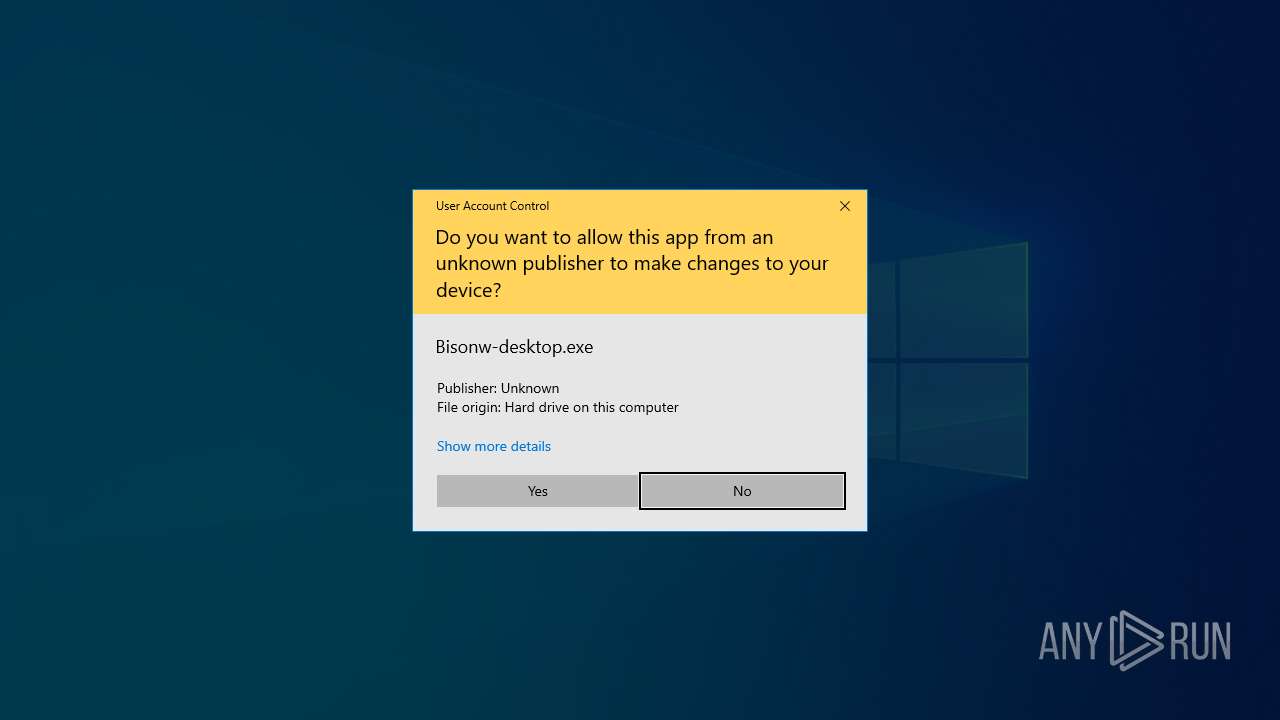
Checks Windows Trust Settings
- msiexec.exe (PID: 7008)
The process bypasses the loading of PowerShell profile settings
- Bisonw-desktop.exe (PID: 4164)
- Bisonw-desktop.exe (PID: 4344)
- Bisonw-desktop.exe (PID: 7020)
- Bisonw-desktop.exe (PID: 2680)
Application launched itself
- Bisonw-desktop.exe (PID: 7020)
- Bisonw-desktop.exe (PID: 4164)
Adds/modifies Windows certificates
- Bisonw-desktop.exe (PID: 7020)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 872)
INFO
Reads Microsoft Office registry keys
- chrome.exe (PID: 1480)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6504)
The process uses the downloaded file
- chrome.exe (PID: 1480)
- chrome.exe (PID: 6992)
Checks supported languages
- msiexec.exe (PID: 7008)
- Bisonw-desktop.exe (PID: 4164)
- Bisonw-desktop.exe (PID: 7020)
- Bisonw-desktop.exe (PID: 2680)
- Bisonw-desktop.exe (PID: 4344)
- ShellExperienceHost.exe (PID: 872)
Reads the computer name
- msiexec.exe (PID: 7008)
- Bisonw-desktop.exe (PID: 4164)
- Bisonw-desktop.exe (PID: 4344)
- Bisonw-desktop.exe (PID: 7020)
- ShellExperienceHost.exe (PID: 872)
- Bisonw-desktop.exe (PID: 2680)
Reads the software policy settings
- msiexec.exe (PID: 6504)
- msiexec.exe (PID: 7008)
- slui.exe (PID: 5816)
- slui.exe (PID: 7052)
- Bisonw-desktop.exe (PID: 7020)
- Bisonw-desktop.exe (PID: 4164)
Create files in a temporary directory
- Bisonw-desktop.exe (PID: 4164)
- Bisonw-desktop.exe (PID: 7020)
Creates files or folders in the user directory
- Bisonw-desktop.exe (PID: 4164)
Reads the machine GUID from the registry
- msiexec.exe (PID: 7008)
- Bisonw-desktop.exe (PID: 7020)
- Bisonw-desktop.exe (PID: 4164)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7008)
Creates a software uninstall entry
- msiexec.exe (PID: 7008)
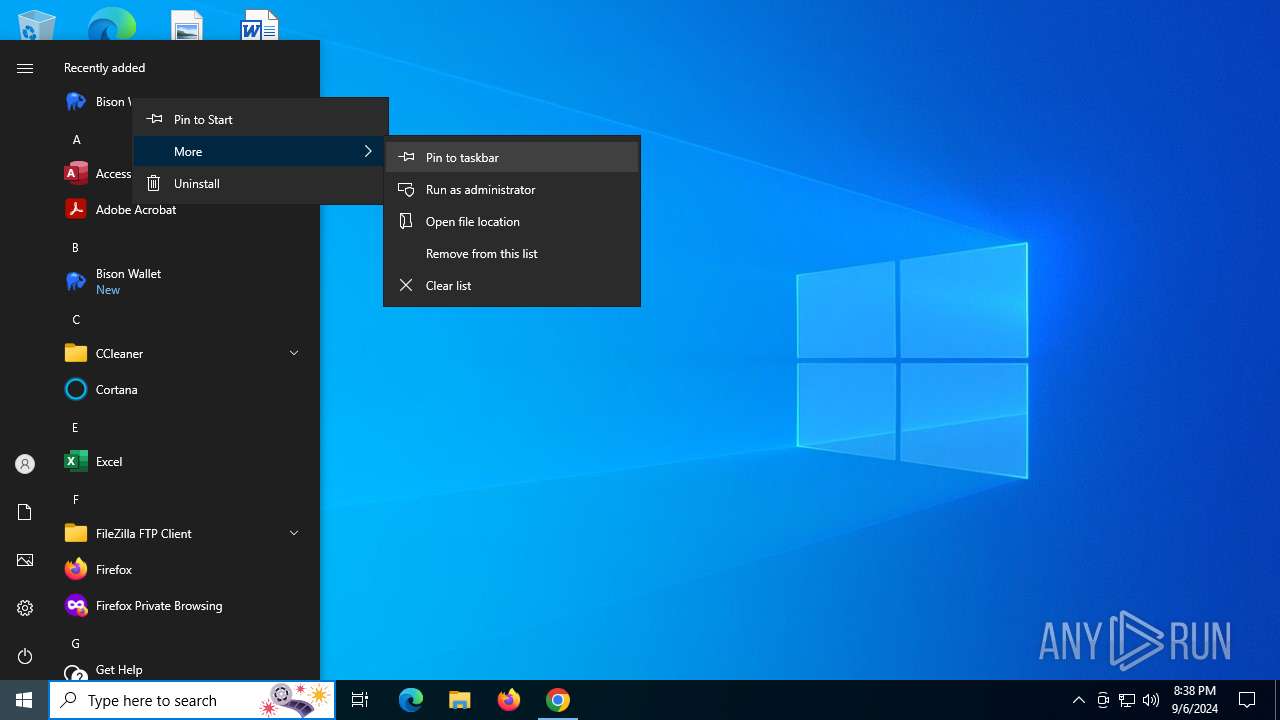
Manual execution by a user
- Bisonw-desktop.exe (PID: 4164)
- Bisonw-desktop.exe (PID: 7020)
Application launched itself
- chrome.exe (PID: 1480)
Sends debugging messages
- Bisonw-desktop.exe (PID: 4344)
- Bisonw-desktop.exe (PID: 2680)
Checks proxy server information
- slui.exe (PID: 7052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
179
Monitored processes
40
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 400 | powershell -NoProfile Get-StartApps | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Bisonw-desktop.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5868 --field-trial-handle=1876,i,3659043625320357759,13859090568897881318,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2116 --field-trial-handle=1876,i,3659043625320357759,13859090568897881318,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://dex.decred.org/#downloads" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1492 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1700 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=4560 --field-trial-handle=1876,i,3659043625320357759,13859090568897881318,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5712 --field-trial-handle=1876,i,3659043625320357759,13859090568897881318,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Decred\Bisonw-desktop.exe" --webview http://127.0.0.1:5758 | C:\Program Files\Decred\Bisonw-desktop.exe | Bisonw-desktop.exe | ||||||||||||
User: admin Company: Decred Integrity Level: HIGH Description: The Decred DEX Client (WebView version) Exit code: 2 Version: 0.7.0 Modules
| |||||||||||||||
Total events
57 804
Read events
57 255
Write events
523
Delete events
26
Modification events
| (PID) Process: | (1480) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1480) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1480) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1480) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1480) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6992) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000002F0E0C3B9C00DB01 | |||
| (PID) Process: | (1480) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.msi\OpenWithProgids |
| Operation: | write | Name: | Msi.Package |
Value: | |||
| (PID) Process: | (7008) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000076F9FD3F9C00DB01601B00008C040000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7008) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000076F9FD3F9C00DB01601B00008C040000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7008) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000028D353409C00DB01601B00008C040000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
2
Suspicious files
245
Text files
66
Unknown types
235
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF130969.TMP | — | |
MD5:— | SHA256:— | |||
| 1480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF130979.TMP | — | |
MD5:— | SHA256:— | |||
| 1480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4d44fd4a-c28d-4961-bd80-0d46bdd7421f.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1480 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:723783C35EAEEE1492EDB30847AE6750 | SHA256:C29323F784CF873BF34992E7A2B4630B19641BF42980109E31D5AF2D487DF6F8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
77
DNS requests
46
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6652 | svchost.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 304 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4276 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3716 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6796 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aczuxlmyjmlqjqkw3f2ydnakdekq_9092/hfnkpimlhhgieaddgfemjhofmfblmnib_9092_all_cidjajoypo47ffrtyhcvgjopym.crx3 | unknown | — | — | whitelisted |
1480 | chrome.exe | GET | 200 | 100.24.223.135:80 | http://ocsps.ssl.com/MEkwRzBFMEMwQTAJBgUrDgMCGgUABBQMDtATfnJO6JAXDQoHl8pAaJdhTQQU3QQJB6L1en1SUxKSle44gCUNplkCCGQzUdPHOJ8I | unknown | — | — | whitelisted |
4276 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6796 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aczuxlmyjmlqjqkw3f2ydnakdekq_9092/hfnkpimlhhgieaddgfemjhofmfblmnib_9092_all_cidjajoypo47ffrtyhcvgjopym.crx3 | unknown | — | — | whitelisted |
1480 | chrome.exe | GET | 200 | 54.230.228.50:80 | http://crls.ssl.com/SSLcom-SubCA-CodeSigning-RSA-4096-R1.crl | unknown | — | — | whitelisted |
6796 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aczuxlmyjmlqjqkw3f2ydnakdekq_9092/hfnkpimlhhgieaddgfemjhofmfblmnib_9092_all_cidjajoypo47ffrtyhcvgjopym.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 52.167.17.97:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6652 | svchost.exe | 23.32.185.131:80 | www.microsoft.com | AKAMAI-AS | BR | whitelisted |
2120 | MoUsoCoreWorker.exe | 23.32.185.131:80 | www.microsoft.com | AKAMAI-AS | BR | whitelisted |
— | — | 20.10.31.115:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3716 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3716 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1480 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1344 | chrome.exe | 108.177.119.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
dex.decred.org |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
github.com |
| shared |
Threats
Process | Message |
|---|---|
Bisonw-desktop.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
Bisonw-desktop.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
Bisonw-desktop.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
Bisonw-desktop.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|