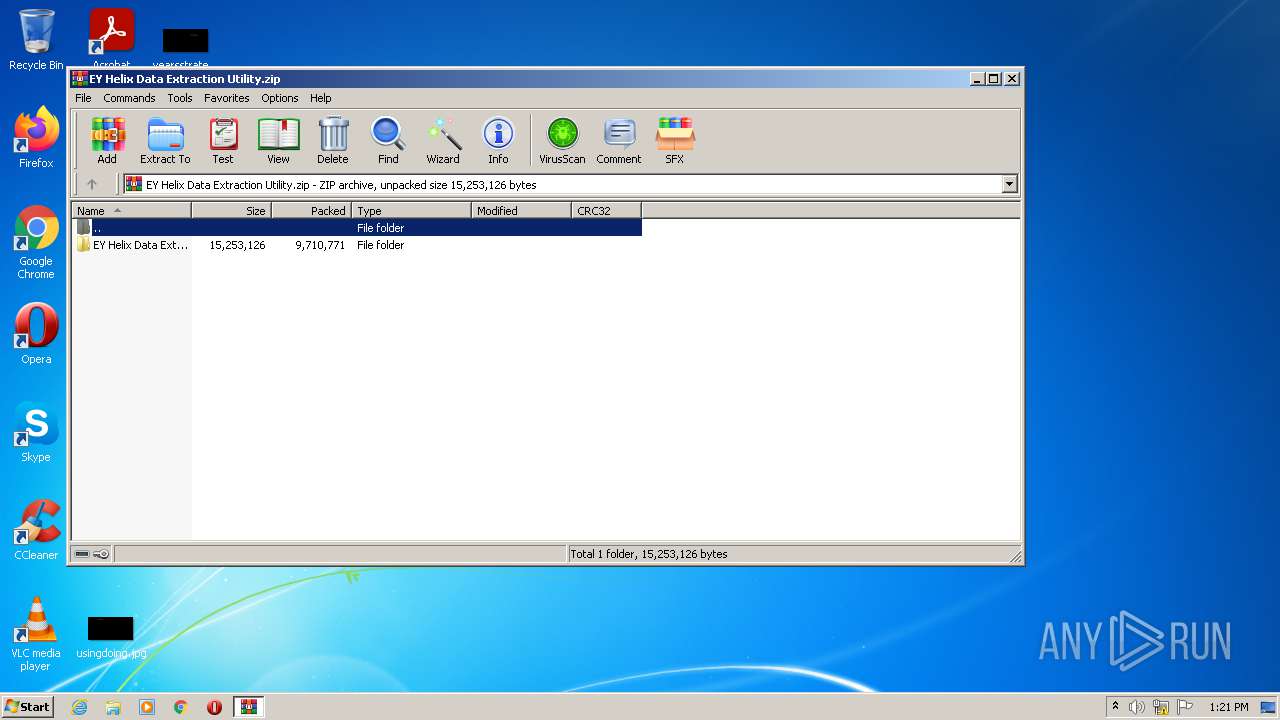
| File name: | EY Helix Data Extraction Utility.zip |
| Full analysis: | https://app.any.run/tasks/692e6573-cfa8-429e-8cd3-67bb8bfb47ce |
| Verdict: | Malicious activity |
| Analysis date: | July 23, 2021, 12:20:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 6770E15EA2A1881E1D63F297F2874818 |
| SHA1: | 46A78FD9E8501F5294EDC9A680694B694584D7DD |
| SHA256: | FF72A0C3F3B663072E259F4FF168F3F7794FF70066BB0A4ED2A6BC5410CF7501 |
| SSDEEP: | 196608:p6BJaCVAp+MJYlRQaWeDhX28HPFpyn32G8tBXB/N60jA+g8UEs92TpmJPS:yJf8iRQMHG3L8t/bA+g8o2Tpsa |
MALICIOUS
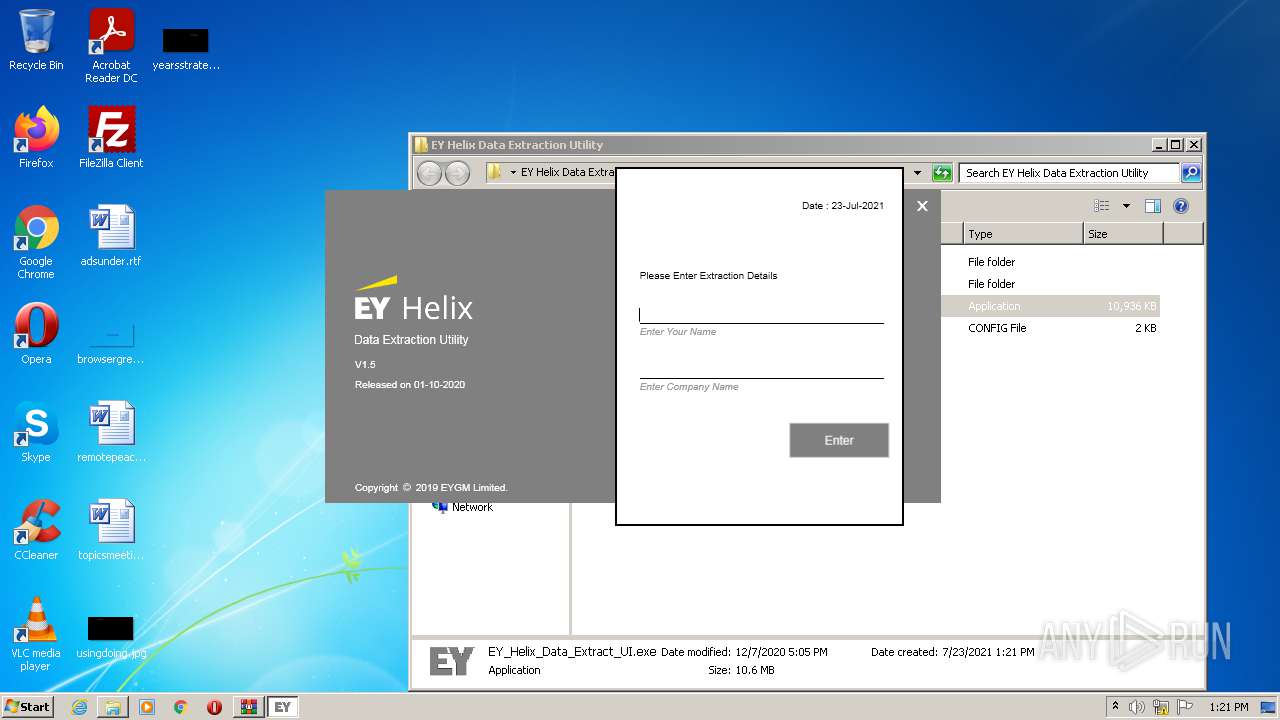
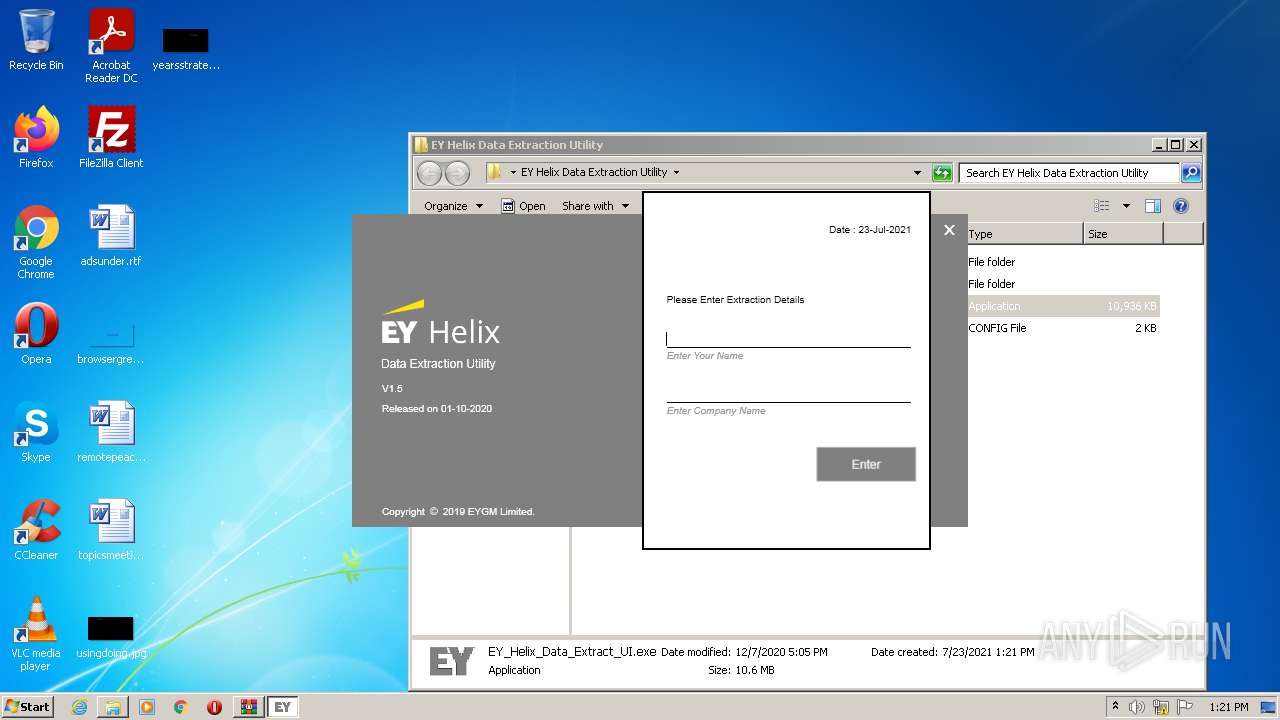
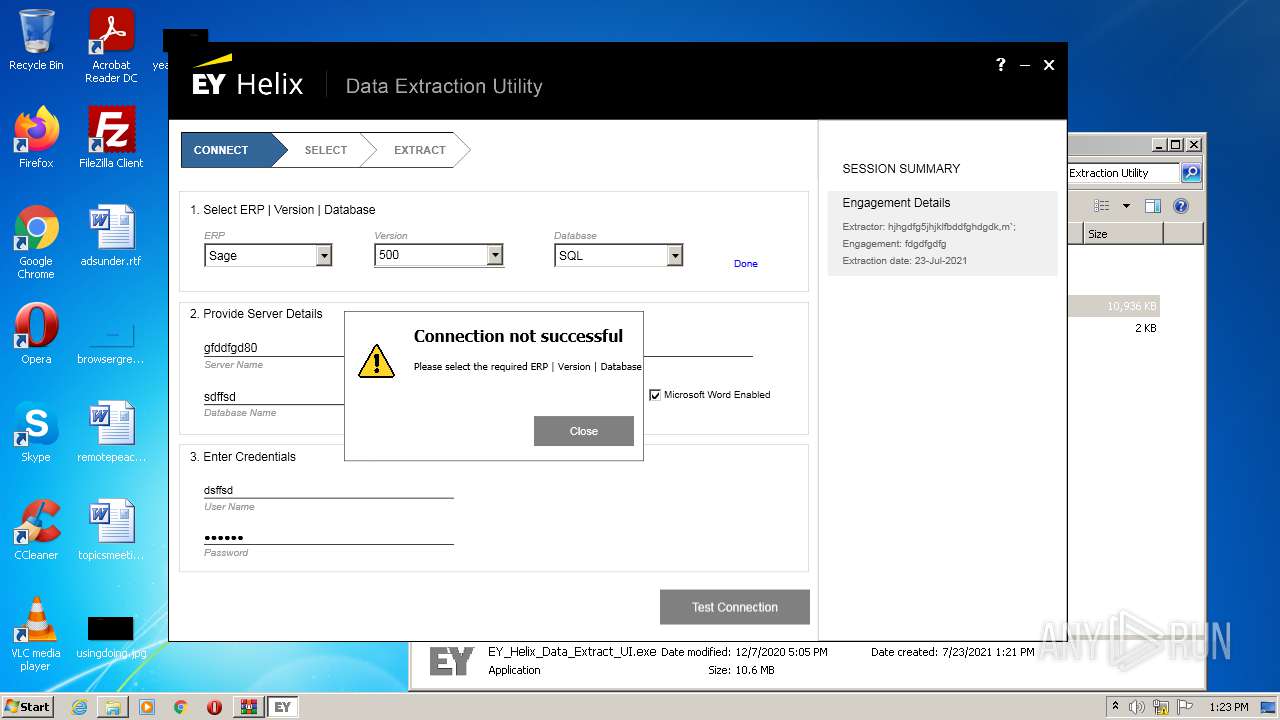
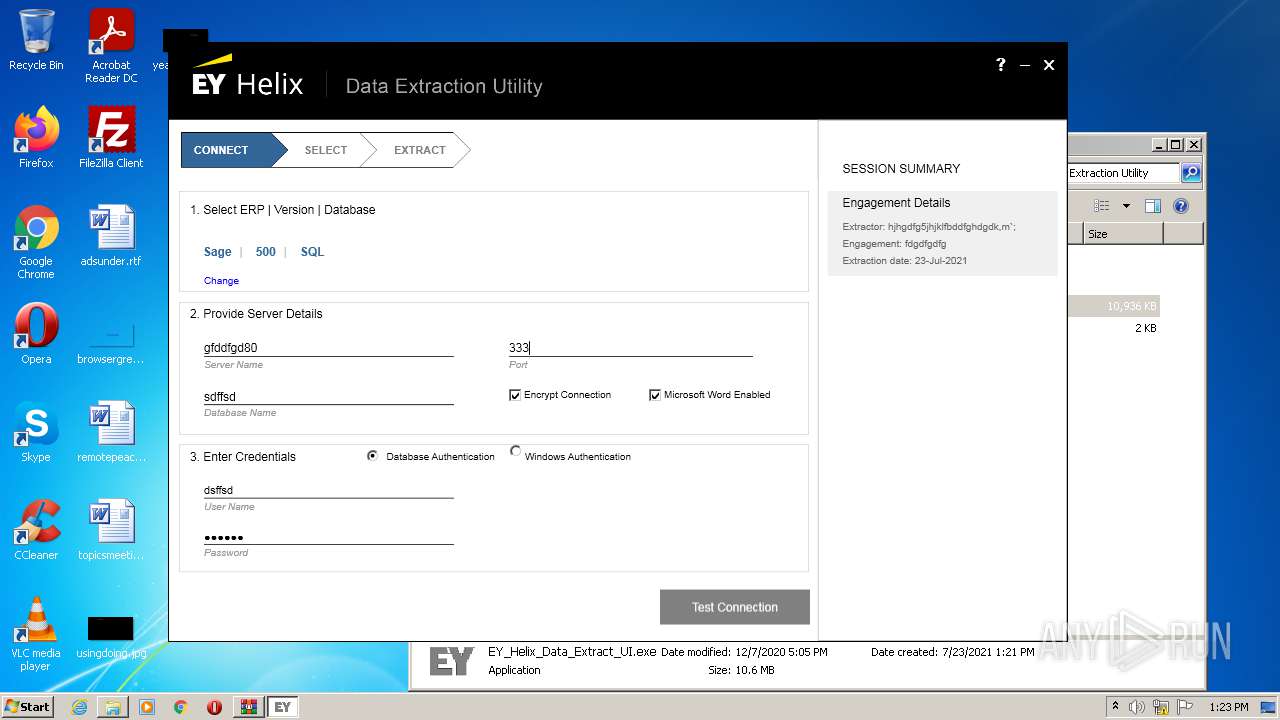
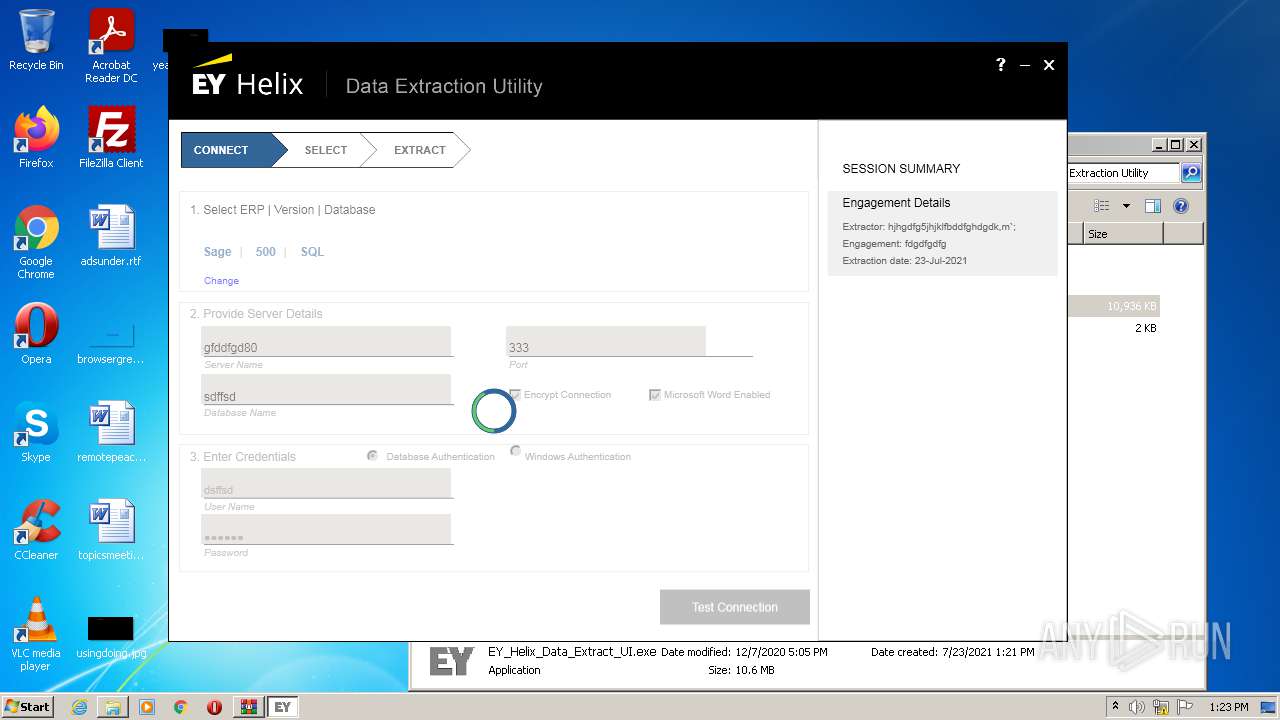
Application was dropped or rewritten from another process
- EY_Helix_Data_Extract_UI.exe (PID: 3776)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 2296)
- EY_Helix_Data_Extract_UI.exe (PID: 3776)
Checks supported languages
- EY_Helix_Data_Extract_UI.exe (PID: 3776)
- WinRAR.exe (PID: 2296)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2296)
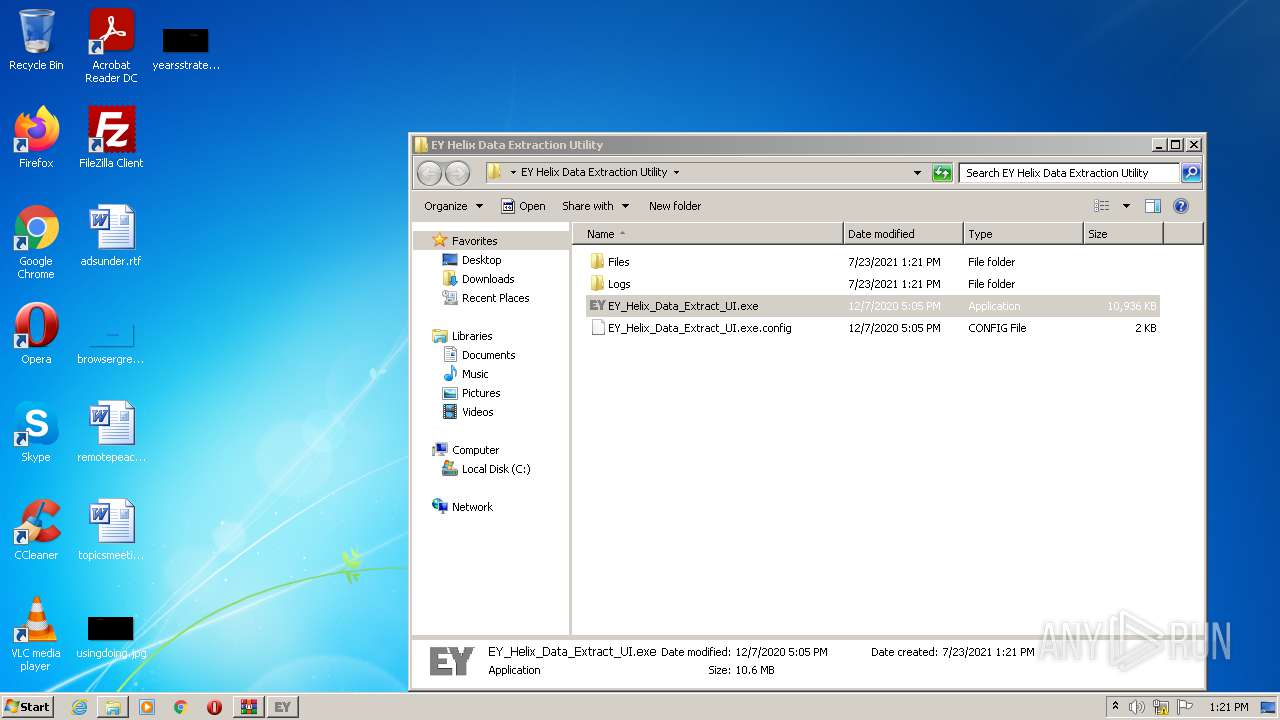
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2296)
INFO
Checks supported languages
- WISPTIS.EXE (PID: 2660)
Reads the computer name
- WISPTIS.EXE (PID: 2660)
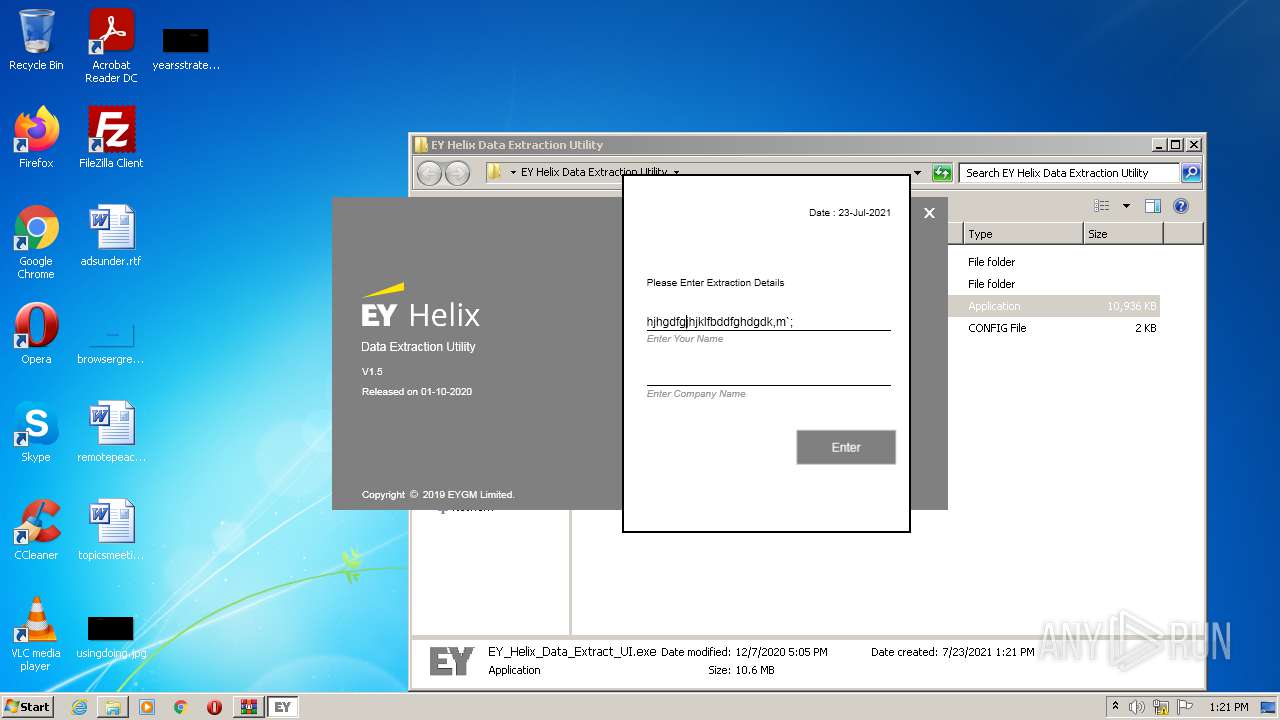
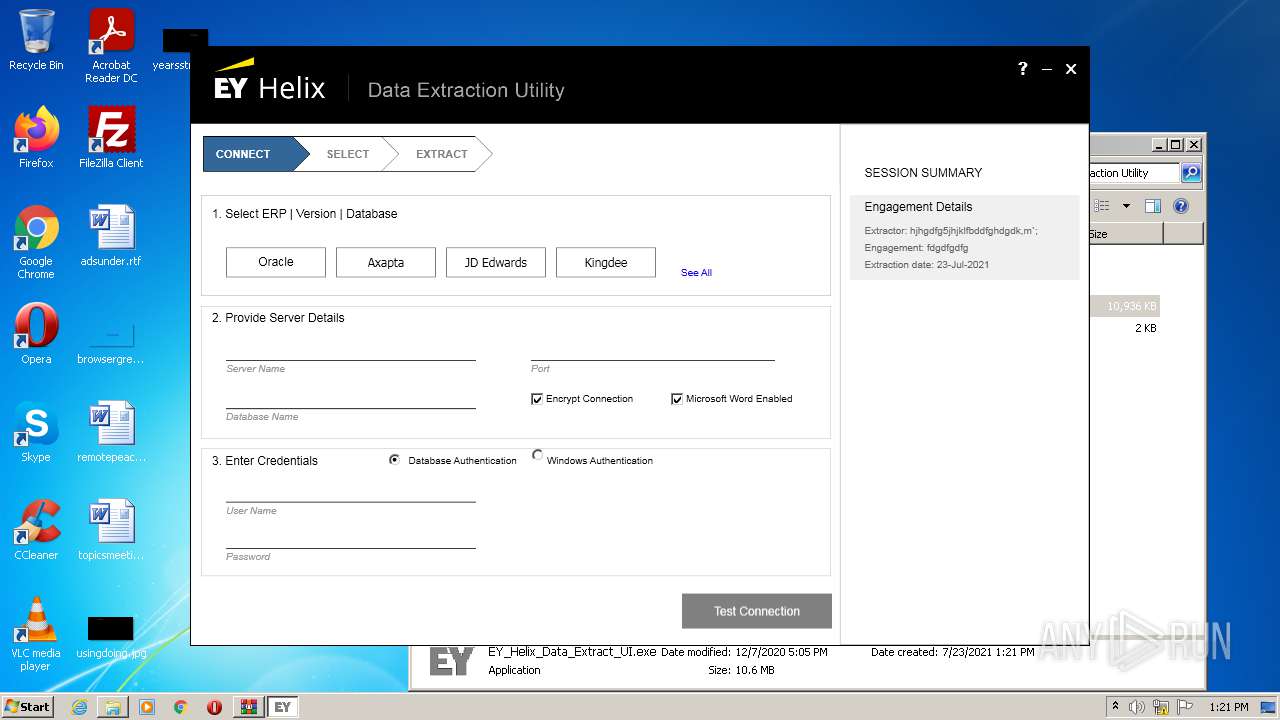
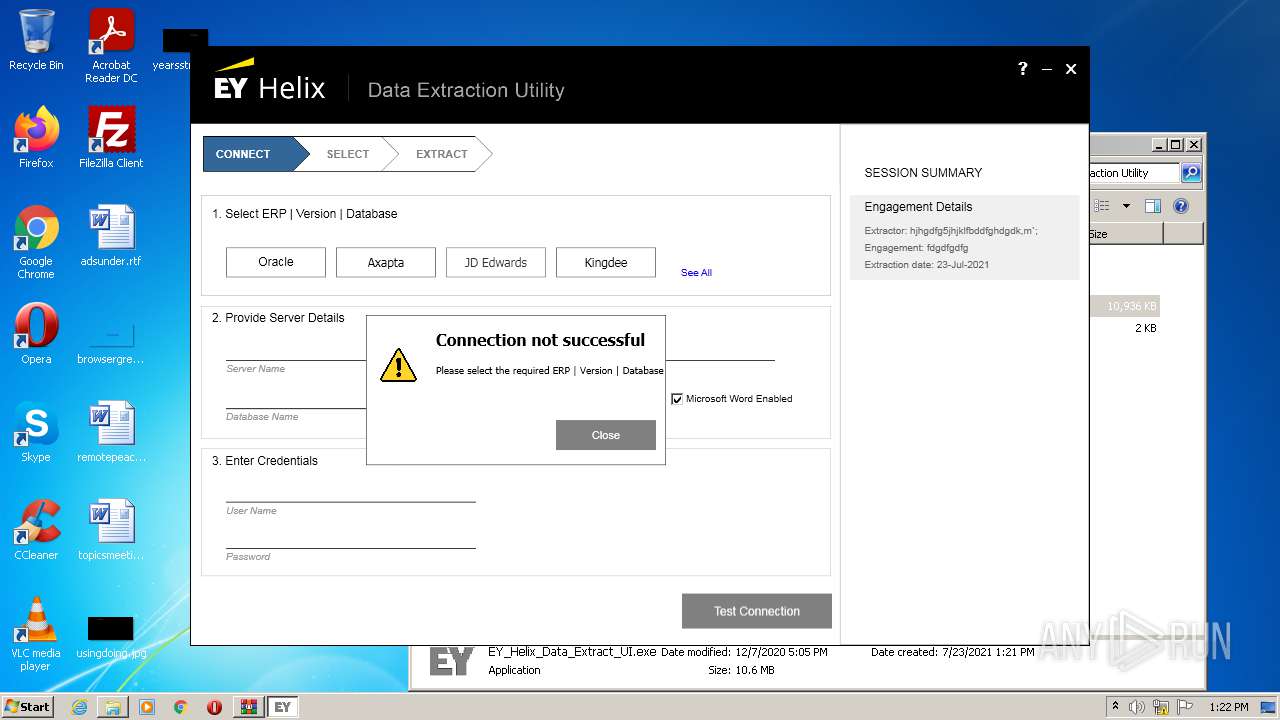
Manual execution by user
- EY_Helix_Data_Extract_UI.exe (PID: 3776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:11:05 17:23:00 |
| ZipCRC: | 0x7370a34c |
| ZipCompressedSize: | 18898 |
| ZipUncompressedSize: | 21039 |
| ZipFileName: | EY Helix Data Extraction Utility/Files/EY_Helix_Data_Extraction_Memo.docx |
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | — | EY_Helix_Data_Extract_UI.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Pen and Touch Input Component Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
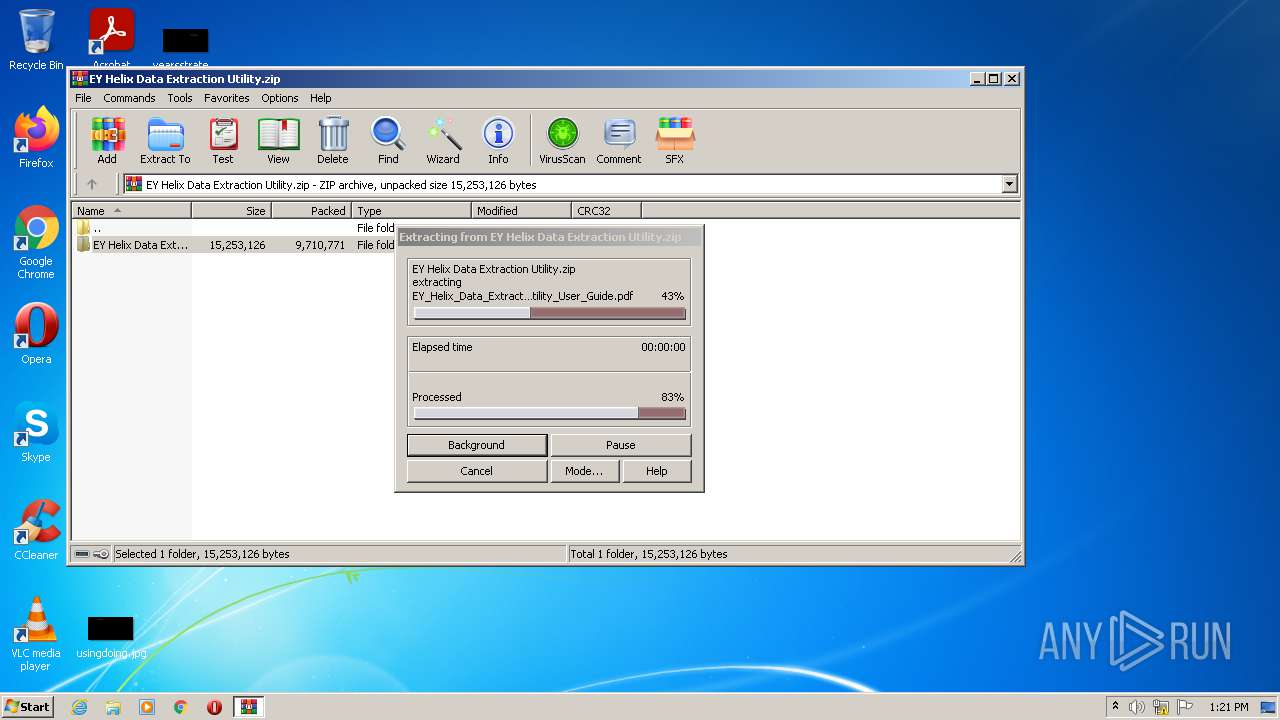
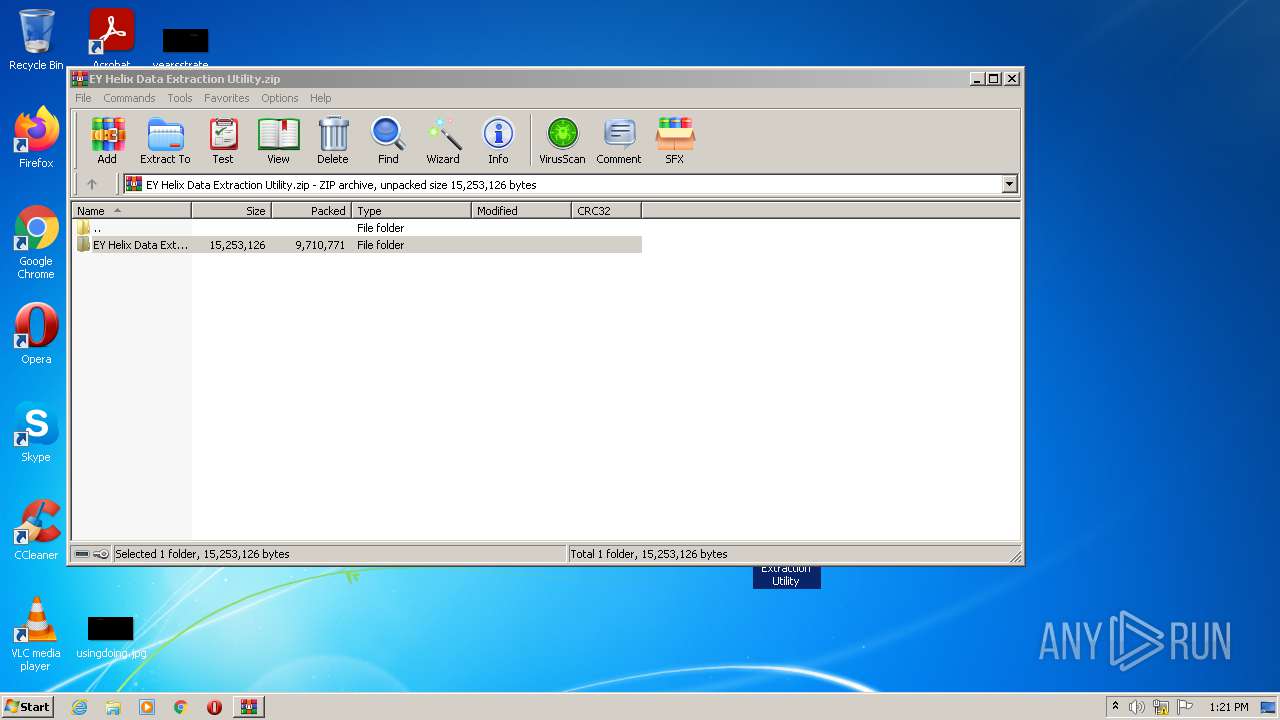
| 2296 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\EY Helix Data Extraction Utility.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2660 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | EY_Helix_Data_Extract_UI.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Pen and Touch Input Component Exit code: 24 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
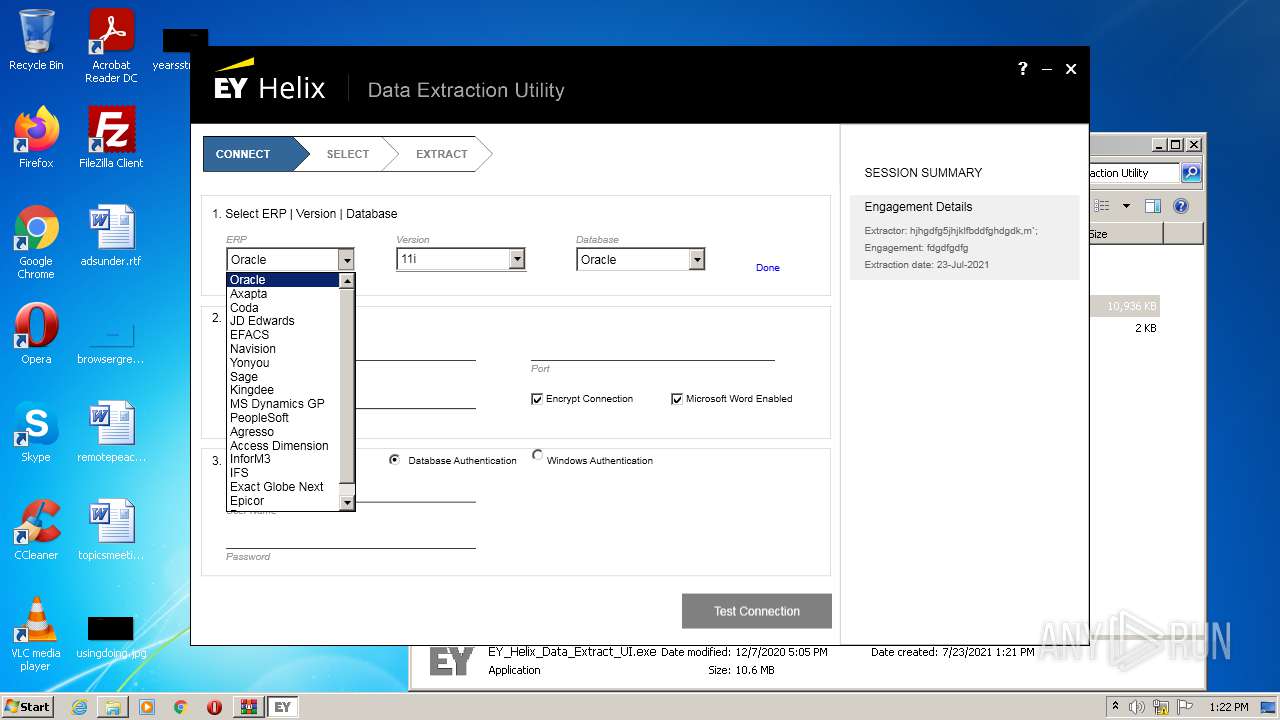
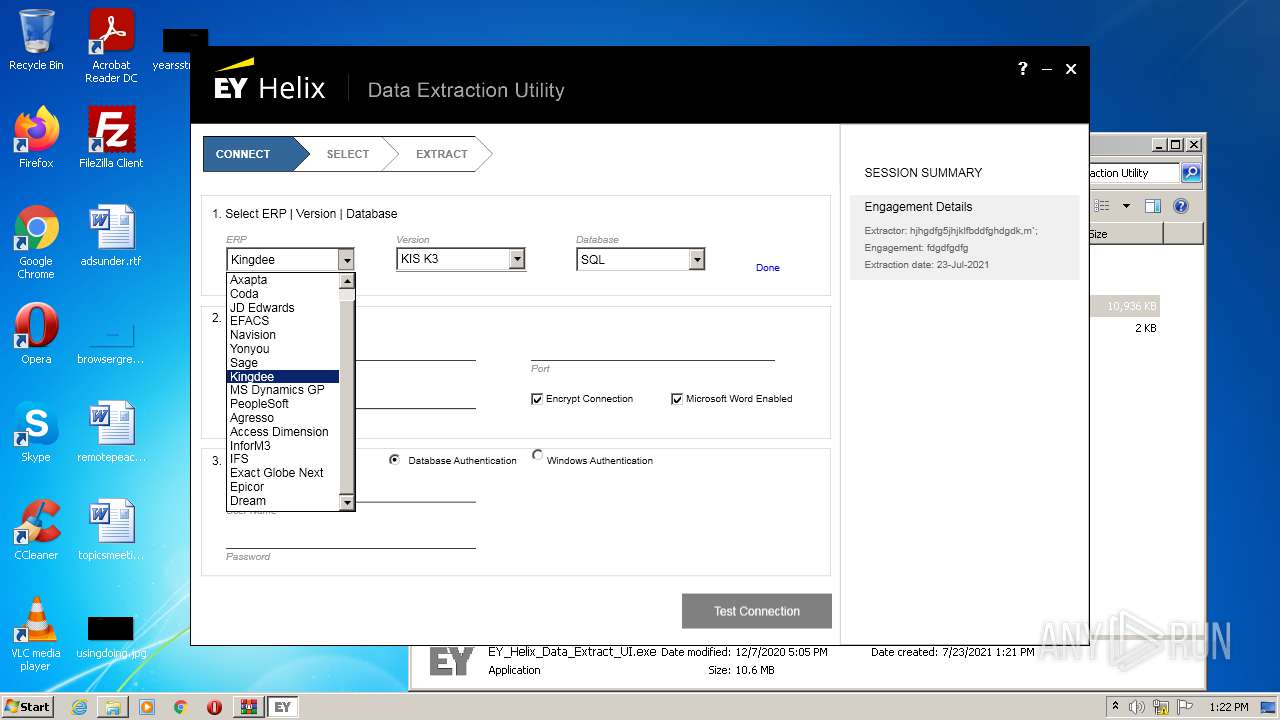
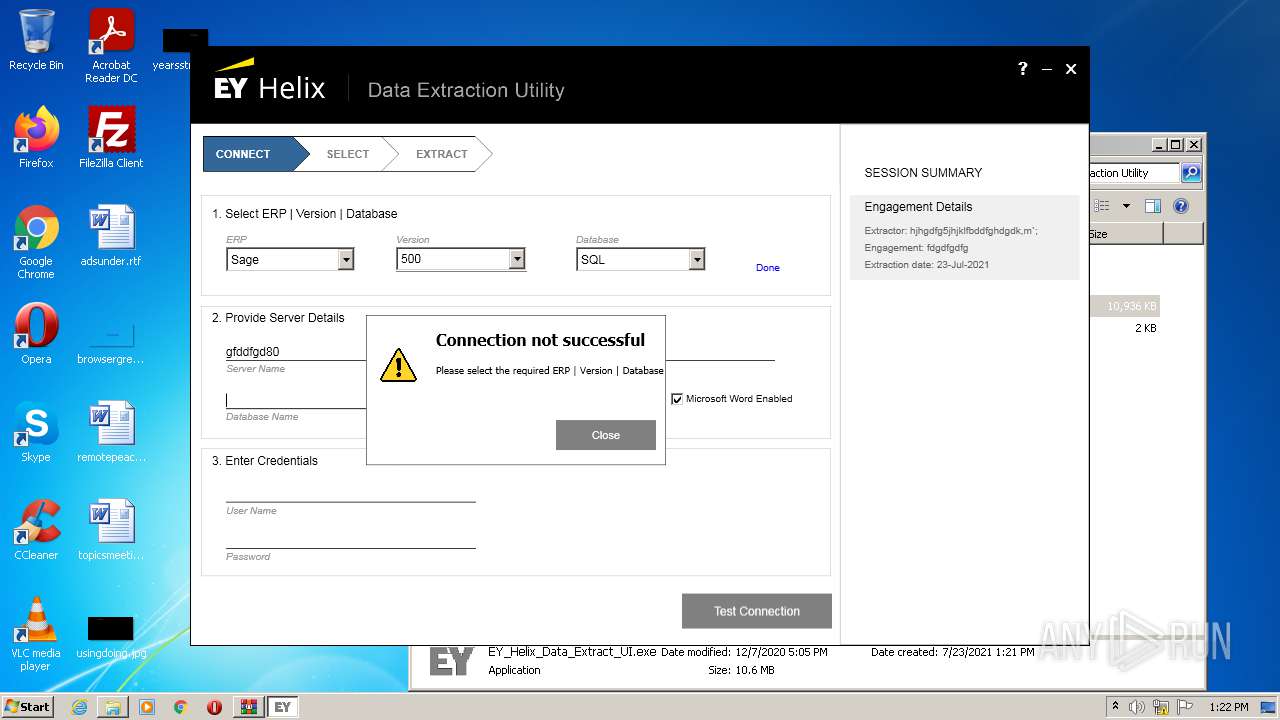
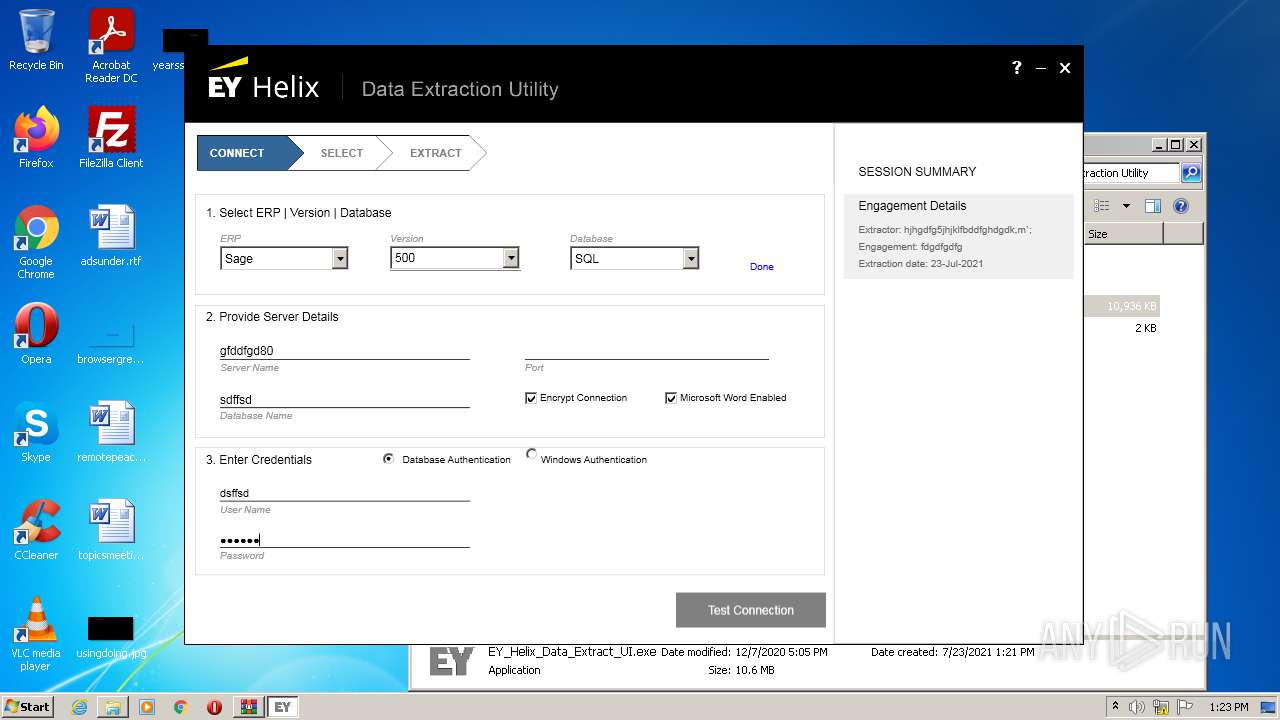
| 3776 | "C:\Users\admin\Desktop\EY Helix Data Extraction Utility\EY_Helix_Data_Extract_UI.exe" | C:\Users\admin\Desktop\EY Helix Data Extraction Utility\EY_Helix_Data_Extract_UI.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: EY_Helix_Data_Extract_UI Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 753
Read events
1 697
Write events
56
Delete events
0
Modification events
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\EY Helix Data Extraction Utility.zip | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2296) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3776) EY_Helix_Data_Extract_UI.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: EY_Helix_Data_Extract_UI.exe | |||
Executable files
1
Suspicious files
58
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
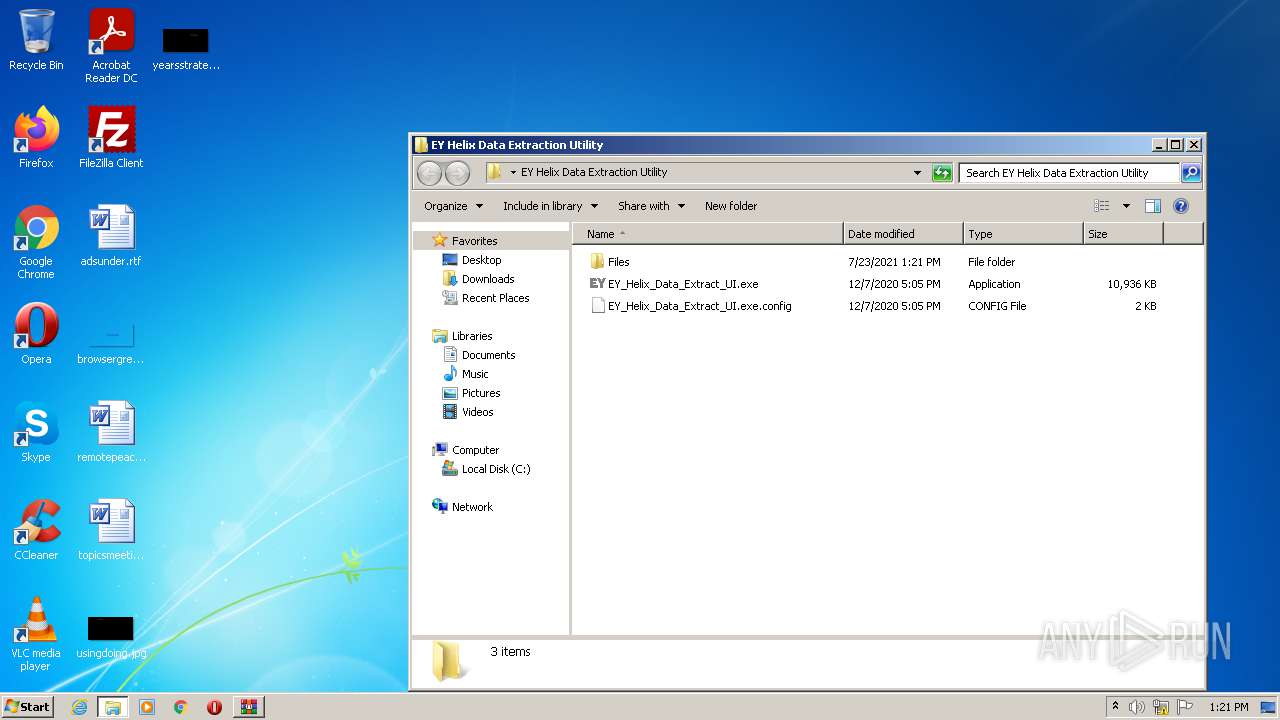
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2296.3255\EY Helix Data Extraction Utility\EY_Helix_Data_Extract_UI.exe | executable | |
MD5:B5BCBFC1BC8F24BED39C109F13B7FCC5 | SHA256:E0386DBF854F034F1D72788C44CE715EEFB736BFE257263278B9A69589D4A735 | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2296.3255\EY Helix Data Extraction Utility\Files\EY_Helix_Data_Extraction_Utility_User_Guide.docx | document | |
MD5:8DE0E51B7FCBECBCB2D9BF9F4CE93611 | SHA256:E59795210413198E3E2E0DA2C1C8196B53C629AA9A69303FC302861A0E057B2A | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2296.3255\EY Helix Data Extraction Utility\Files\Access Dimension_7.1.03_GL.xml | binary | |
MD5:37256575F112B8321ACE83A8632DA9CA | SHA256:7E2452CC33B3F3D296D7AE2B96ED24BB9373547C0E74C986709A3D8AAB4DB22D | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2296.3255\EY Helix Data Extraction Utility\Files\Axapta_AX2009R2_AP.xml | binary | |
MD5:2E8E220EF2AB23A0310877AE0391B9BE | SHA256:20C34E90245BBA157F753785DDA562908E7CDC4350FACCACF787112500B56234 | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2296.3255\EY Helix Data Extraction Utility\EY_Helix_Data_Extract_UI.exe.config | xml | |
MD5:77FC2AF2E85DEDE4C9721C36ECA80DFB | SHA256:847ED20D1724BDA82D164D429ADB395D05AC25EFD4822FA491E78BB53D6B42B6 | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2296.3255\EY Helix Data Extraction Utility\Files\Agresso_Agresso_GL.xml | binary | |
MD5:9AB5F9C98A78D61FD19268C8D7EB341A | SHA256:2BDCF047D1C1C9BCF0BD3D503A3FC260EA6B15DEF489DC6B58C63E1BCDDFFBF8 | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2296.3255\EY Helix Data Extraction Utility\Files\Axapta_AX2.5_GL.xml | binary | |
MD5:6BB8C8FA4DF98F2431A8677148CB2182 | SHA256:4E8280E11131DFD83292F20CC7FEE4EFE45114308FBFD86AD739DD190F3613A4 | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2296.3255\EY Helix Data Extraction Utility\Files\Axapta_AX2.5_AR.xml | binary | |
MD5:C81F9779D23AC0EB33A321841090432F | SHA256:C587B517E6DA480ABDDD7D9E04BD16B756FFE2A5FC0E4E236CD6D75C7811E6F5 | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2296.3255\EY Helix Data Extraction Utility\Files\Axapta_AX2009R2_AR.xml | binary | |
MD5:00DF6E8398B73EDC05F37BE7C2DD722A | SHA256:C6F0BBE45F59CF25ED097BA5DD380B5D72FC4CC9A099FB8782EEC586E04CBAEC | |||
| 2296 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2296.3255\EY Helix Data Extraction Utility\Files\Axapta_AX2009R2_GL.xml | binary | |
MD5:A428E1D9DBC2A232E8A4F805BEDFC4B8 | SHA256:43A4313A9633009D95FB098E2A8B3530E5DAA6EBC7F4D11484D82038BCB2EC4F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report