| File name: | SophosConnect_2.3.1_IPsec_and_SSLVPN.msi |
| Full analysis: | https://app.any.run/tasks/3b881363-7081-4e67-90a3-3b5e0726e274 |
| Verdict: | Malicious activity |
| Analysis date: | October 01, 2024, 17:06:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Sophos Connect , Author: Sophos Ltd, Keywords: Installer, Comments: This installer database contains the logic and data required to install Sophos Connect., Create Time/Date: Wed Jun 19 12:18:50 2024, Name of Creating Application: Windows Installer XML Toolset (3.11.2.4516), Security: 2, Template: Intel;1033, Last Saved By: Intel;1033, Revision Number: {50D2FD97-066F-49AF-971A-7446F4109EFD}2.3.1.0619;{46F8AD9B-F154-47D2-898B-CBE125645E85}2.3.1.0619;{5A9E3376-BF41-425C-B0E8-318388686A58}, Number of Pages: 200, Number of Characters: 0 |
| MD5: | D7F92AED61EB6DAF53B3B97F28997F54 |
| SHA1: | BC0260578A567011EF984097A375C6E1ECBD1A41 |
| SHA256: | FF523A9F1D6566A88626741E802D8C161A7C125F8B7FD7B2E11E8C8699DC57C7 |
| SSDEEP: | 98304:Y6IdjRfW0ScsUB/Ct4soIOet/aDcaseiV73ejh2ORJ4BjJFwtFmVTmcWplctoS7a:LuuWbyHmC8Ybnt5DVok1v7tF |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process verifies whether the antivirus software is installed
- msiexec.exe (PID: 376)
Uses TASKKILL.EXE to kill process
- msiexec.exe (PID: 5736)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 3396)
- drvinst.exe (PID: 400)
- drvinst.exe (PID: 2804)
Executable content was dropped or overwritten
- drvinst.exe (PID: 400)
- drvinst.exe (PID: 2804)
Executes as Windows Service
- charon-svc.exe (PID: 7016)
- VSSVC.exe (PID: 4056)
- openvpnserv.exe (PID: 4596)
- scvpn.exe (PID: 7132)
The process drops C-runtime libraries
- msiexec.exe (PID: 3396)
Process drops legitimate windows executable
- msiexec.exe (PID: 3396)
INFO
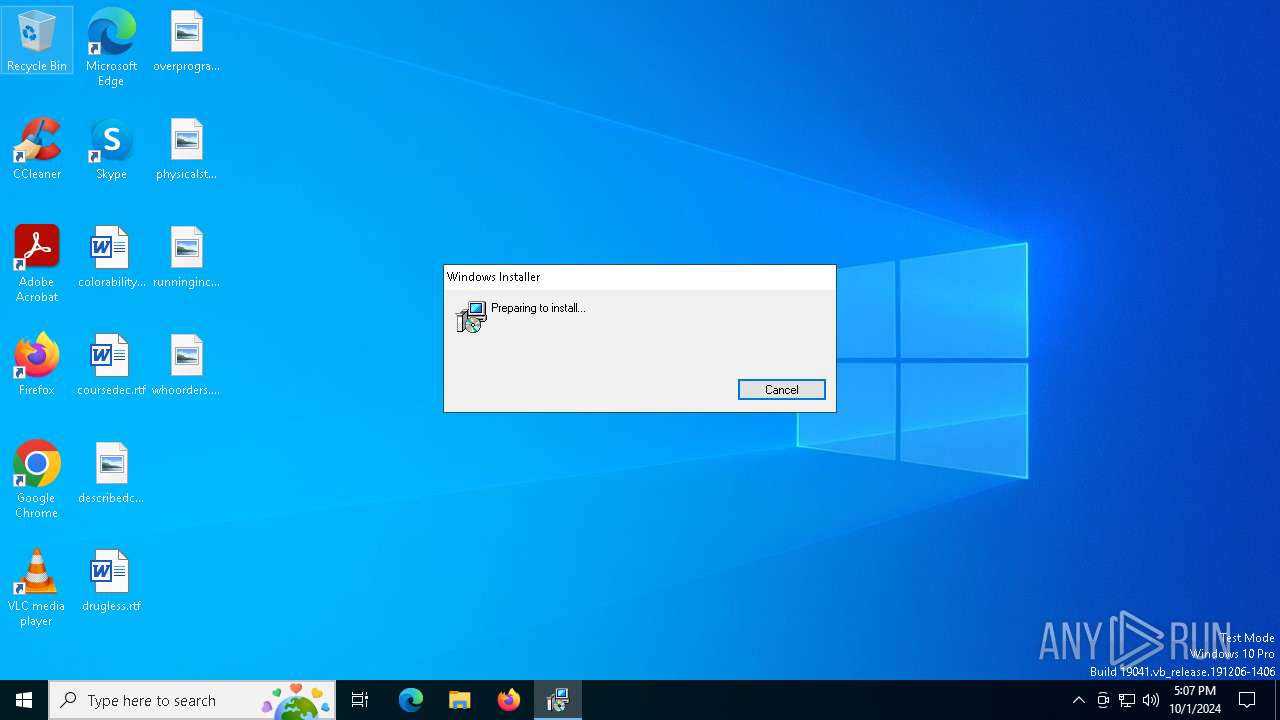
An automatically generated document
- msiexec.exe (PID: 376)
Create files in a temporary directory
- msiexec.exe (PID: 376)
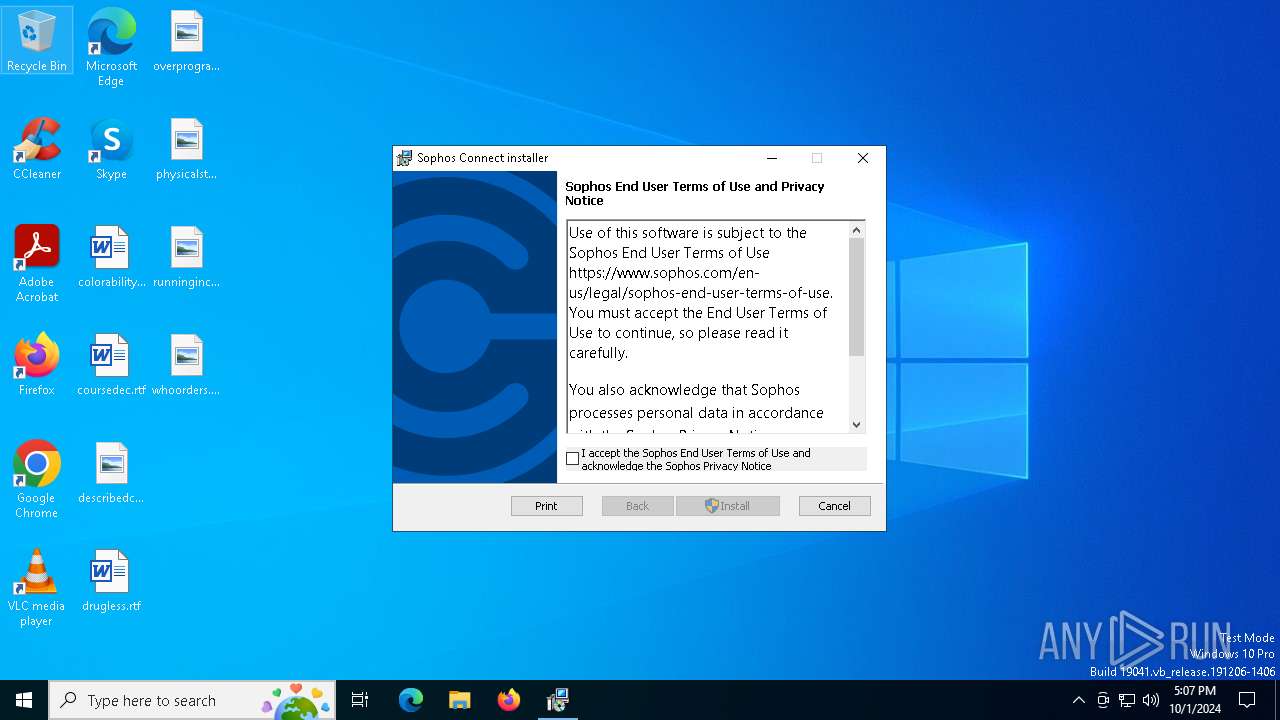
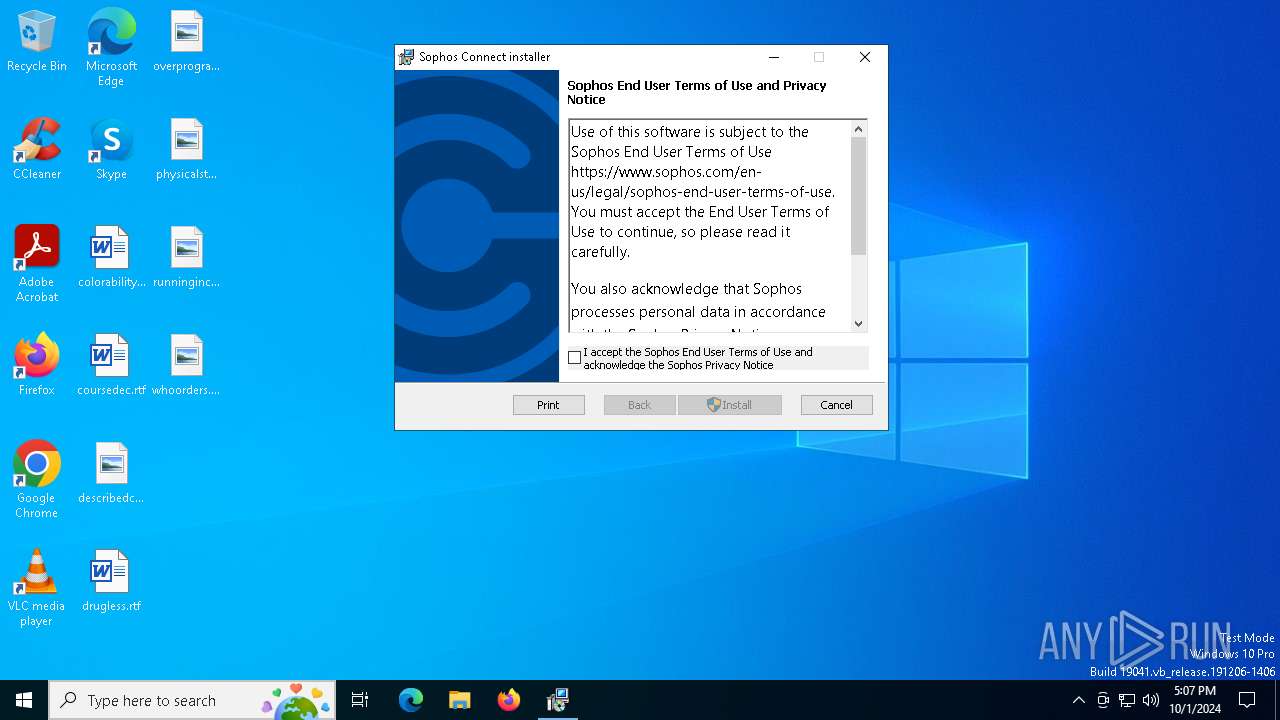
Reads the software policy settings
- msiexec.exe (PID: 376)
Creates files or folders in the user directory
- msiexec.exe (PID: 376)
Manages system restore points
- SrTasks.exe (PID: 2248)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 376)
Checks proxy server information
- msiexec.exe (PID: 376)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3396)
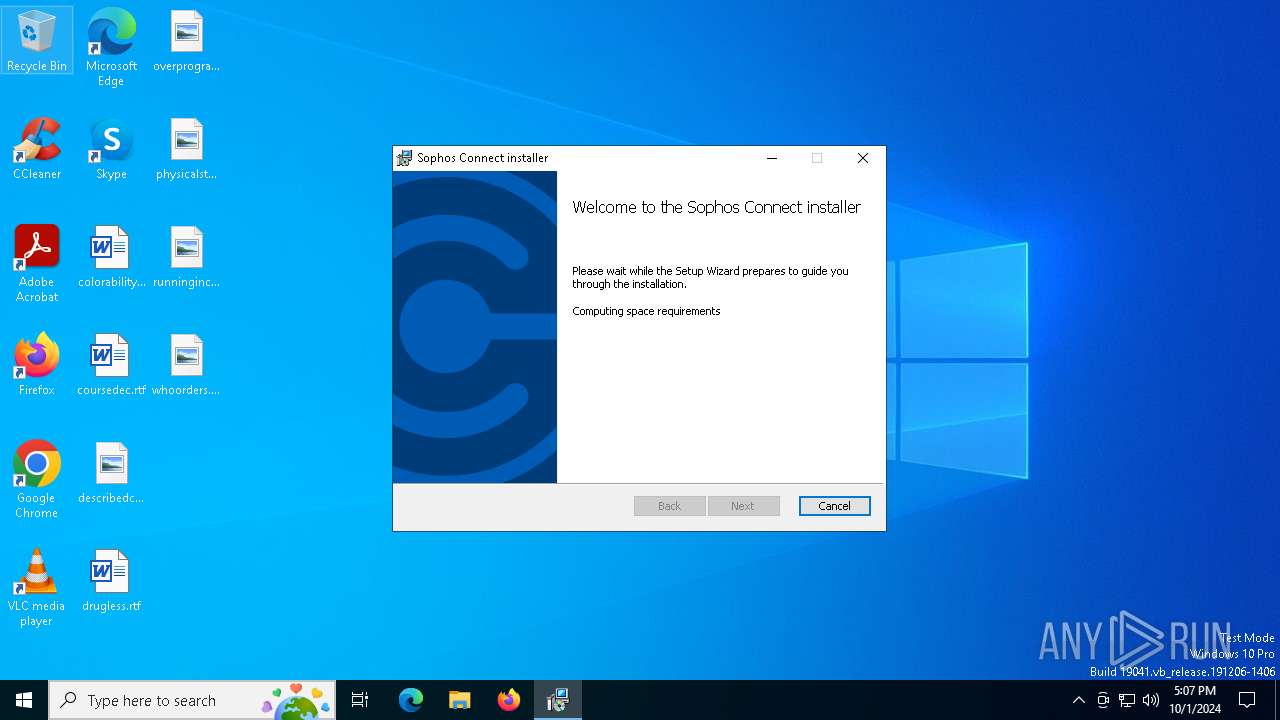
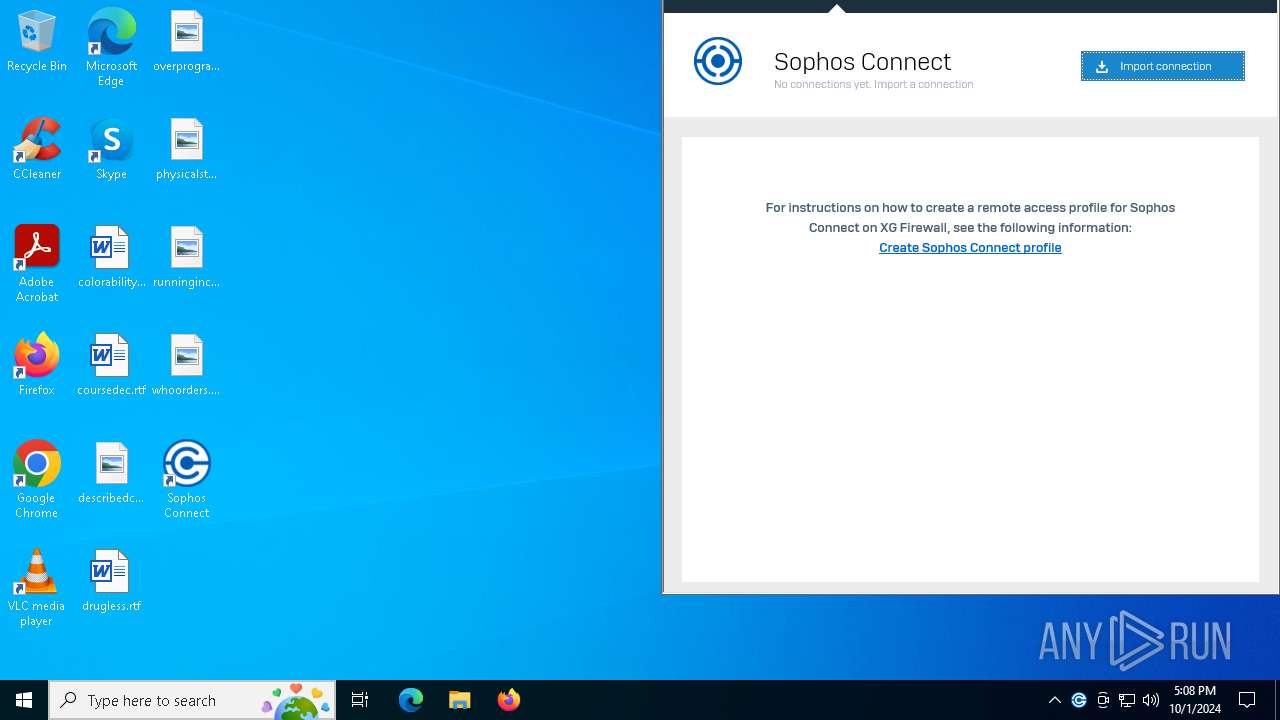
Manual execution by a user
- scgui.exe (PID: 7068)
- scgui.exe (PID: 440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Sophos Connect Installer |
| Author: | Sophos Ltd |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Sophos Connect. |
| RevisionNumber: | {3C07877A-6FE3-4DD2-9DE1-FA9608B3771E} |
| CreateDate: | 2024:06:19 12:17:54 |
| ModifyDate: | 2024:06:19 12:17:54 |
| Pages: | 200 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.2.4516) |
| Security: | Read-only recommended |
| Template: | Intel;1033,1031,1034,1036,1040,1041,1042,1046,2052,1028 |
| LastModifiedBy: | Intel;1033 |
| Characters: | - |
Total processes
157
Monitored processes
22
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\SophosConnect_2.3.1_IPsec_and_SSLVPN.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 400 | DrvInst.exe "4" "1" "c:\program files (x86)\sophos\connect\tapdriver\win10amd64\oemvista.inf" "9" "4da5a64bf" "00000000000001E0" "WinSta0\Default" "00000000000001C8" "208" "c:\program files (x86)\sophos\connect\tapdriver\win10amd64" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
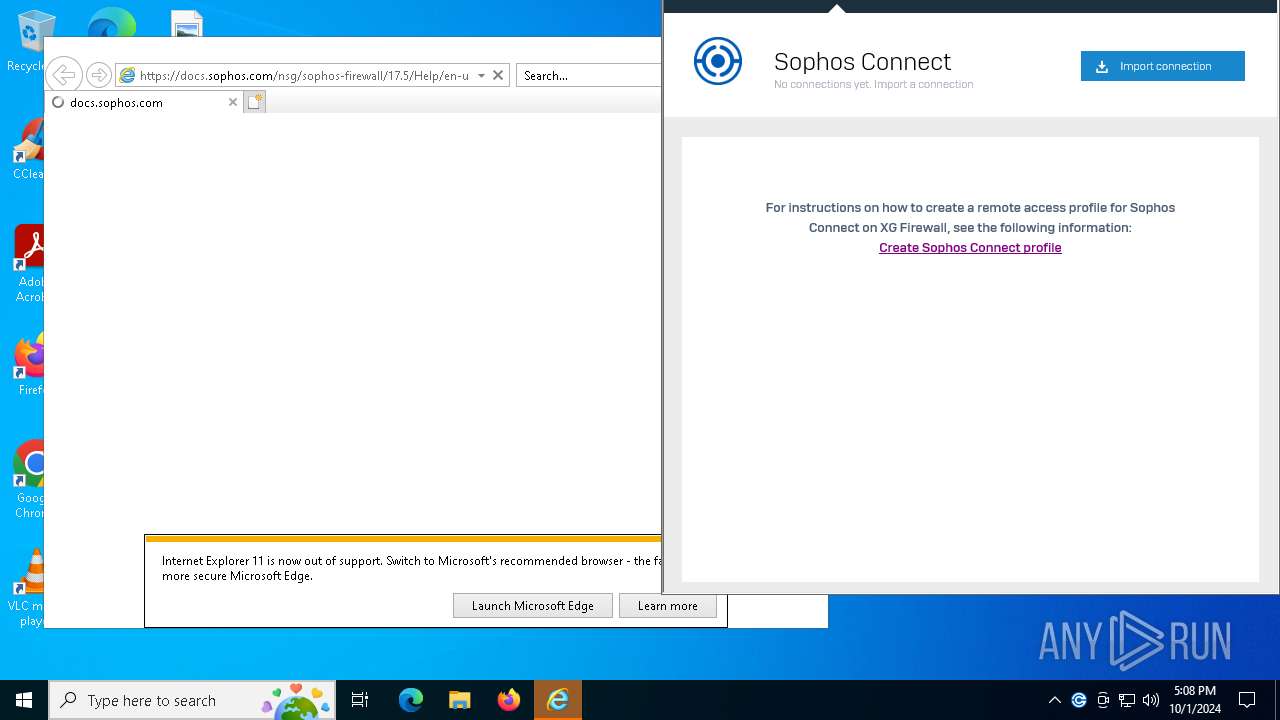
| 420 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:1556 CREDAT:9480 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 440 | "C:\Program Files (x86)\Sophos\Connect\GUI\scgui.exe" | C:\Program Files (x86)\Sophos\Connect\GUI\scgui.exe | — | explorer.exe | |||||||||||
User: admin Company: Sophos Integrity Level: MEDIUM Description: Sophos Connect GUI Version: 2.3.1.0619 Modules
| |||||||||||||||
| 752 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:1556 CREDAT:9474 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
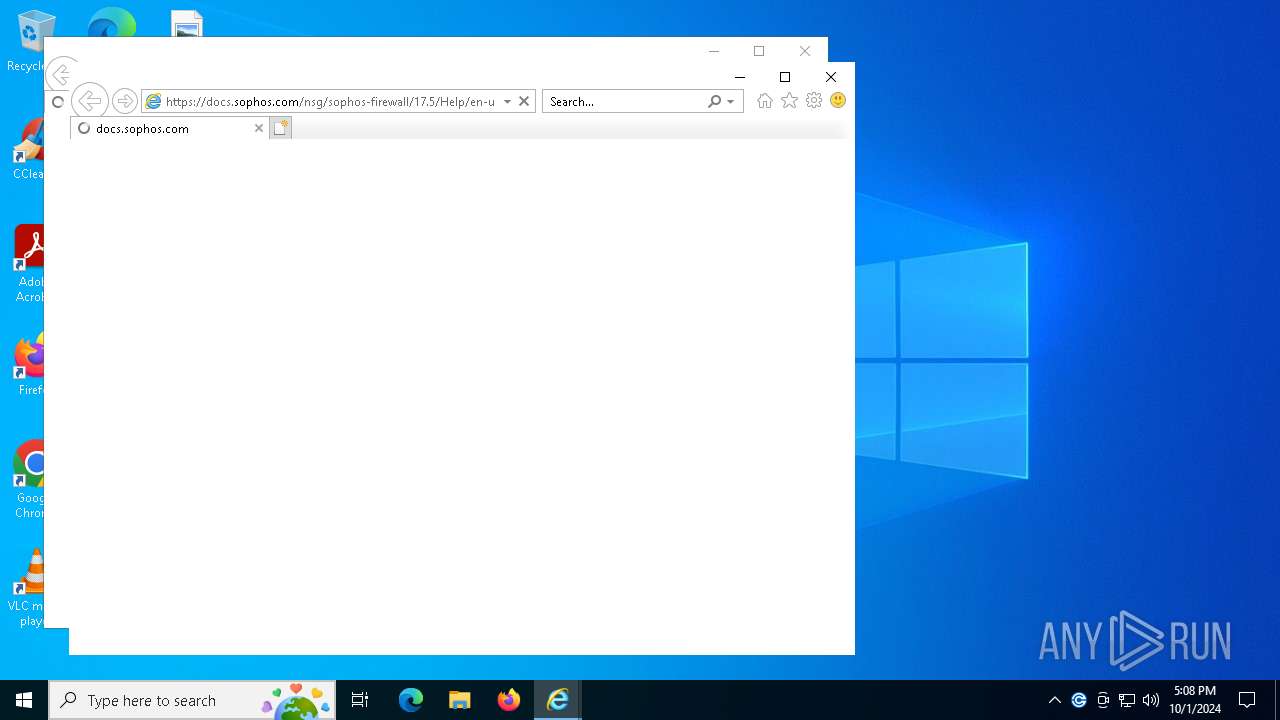
| 1556 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2224 | C:\Windows\syswow64\MsiExec.exe -Embedding E976B009479FB0D2F0B787224FCFDCE2 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2248 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2488 | "C:\Program Files (x86)\Sophos\Connect\TapDriver\win10amd64\tapinstall.exe" install "C:\Program Files (x86)\Sophos\Connect\TapDriver\win10amd64\OemVista.inf" tapSophos | C:\Program Files (x86)\Sophos\Connect\TapDriver\win10amd64\tapinstall.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Setup API Exit code: 0 Version: 6.1.7600.16385 (win7_wdk.100208-1538) Modules
| |||||||||||||||
| 2804 | DrvInst.exe "2" "211" "ROOT\NET\0000" "C:\WINDOWS\INF\oem1.inf" "oem1.inf:3beb73aff103cc24:tapSophos.ndi:1.0.0.0:tapsophos," "4da5a64bf" "00000000000001E0" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
29 374
Read events
28 838
Write events
504
Delete events
32
Modification events
| (PID) Process: | (3396) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000E9E5BD612414DB01440D00000C080000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3396) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000E9E5BD612414DB01440D00000C080000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3396) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000FCA10C622414DB01440D00000C080000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3396) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000004CF30E622414DB01440D00000C080000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3396) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000004CF30E622414DB01440D00000C080000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3396) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000B2B913622414DB01440D00000C080000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3396) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (3396) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 480000000000000008097F622414DB01440D00000C080000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3396) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000A1D083622414DB01440D0000A0080000E8030000010000000000000000000000CA23BA6BA323BA409A13711AEEED9BDF00000000000000000000000000000000 | |||
| (PID) Process: | (4056) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000A35F8D622414DB01D80F000084000000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
29
Suspicious files
96
Text files
74
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3396 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3396 | msiexec.exe | C:\Windows\Installer\3fdbd6.msi | — | |
MD5:— | SHA256:— | |||
| 3396 | msiexec.exe | C:\Windows\Temp\~DF6058931F8F073A14.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 3396 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:21848B198A35C3431BB408401F3F99D2 | SHA256:3553D8A18977153F477C91EBD7AFC940004B67351D434A731F0A4C853631C3FE | |||
| 376 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EC9B1D0ABBD7F98B401D425828828CE_BD99E049BBF0D523D53FBF6DBA488755 | binary | |
MD5:6C1528B5CC354F3A13A83BF301B06BEF | SHA256:F22C723C6FF264996C7B39FF7B9E6CB3274935A69C5B44E24F50CA04AD87377F | |||
| 3396 | msiexec.exe | C:\Windows\Installer\MSIE1D2.tmp | executable | |
MD5:A3AE5D86ECF38DB9427359EA37A5F646 | SHA256:C8D190D5BE1EFD2D52F72A72AE9DFA3940AB3FACEB626405959349654FE18B74 | |||
| 376 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EC9B1D0ABBD7F98B401D425828828CE_BD99E049BBF0D523D53FBF6DBA488755 | der | |
MD5:45CD0C5A4A7E9FF6754CD94C9B9F0404 | SHA256:84C85AC0FB8CA6CA0606683D5FD38DC164D1C22F11C4A0F0BD876913487589FD | |||
| 3396 | msiexec.exe | C:\Windows\Installer\MSIE638.tmp | binary | |
MD5:69FDE2DD3865A3351DFDC89C07321774 | SHA256:43F571FB0647FFB5307DD66F0F41B24507266F49D3274EDF5EC3EC43B6E3591A | |||
| 3396 | msiexec.exe | C:\Program Files (x86)\Sophos\Connect\davici.dll | executable | |
MD5:5285965A38C393FEDD9976E847AAFD5C | SHA256:D009589BE8741A364C077C11605656DE6D67785C0F3470325B5875D7E2FA227D | |||
| 3396 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{6bba23ca-23a3-40ba-9a13-711aeeed9bdf}_OnDiskSnapshotProp | binary | |
MD5:21848B198A35C3431BB408401F3F99D2 | SHA256:3553D8A18977153F477C91EBD7AFC940004B67351D434A731F0A4C853631C3FE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
97
DNS requests
36
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
376 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
376 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
376 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAcFTiM6sUruh9Hy26bb9vo%3D | unknown | — | — | whitelisted |
2064 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7132 | scvpn.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
752 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDQHuXxad%2F5c1K2Rl1mo%3D | unknown | — | — | whitelisted |
752 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
7132 | scvpn.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAcFTiM6sUruh9Hy26bb9vo%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6796 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
376 | msiexec.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4324 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2064 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2064 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
Process | Message |
|---|---|
charon-svc.exe | Invalid parameter passed to C runtime function.
|