| File name: | Patch7.0.exe |
| Full analysis: | https://app.any.run/tasks/58e5baa3-9d6d-4edb-99f0-923dc67208d4 |
| Verdict: | Malicious activity |
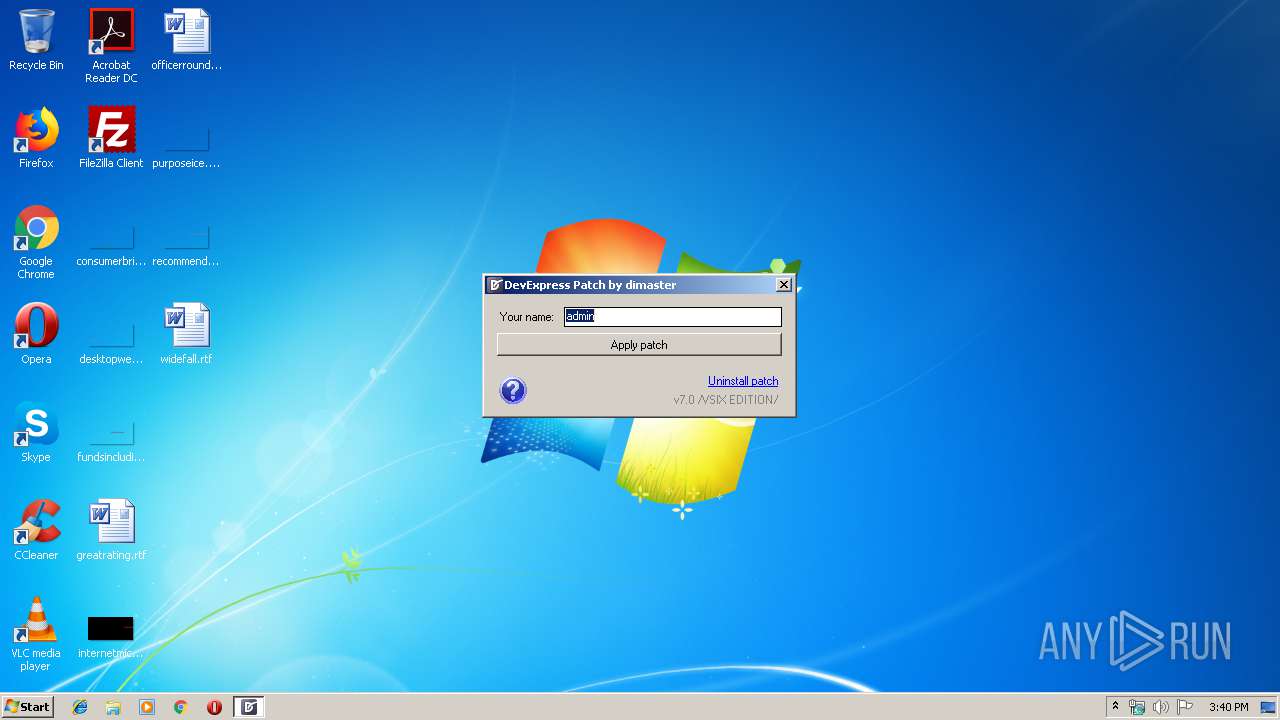
| Analysis date: | January 17, 2020, 15:40:30 |
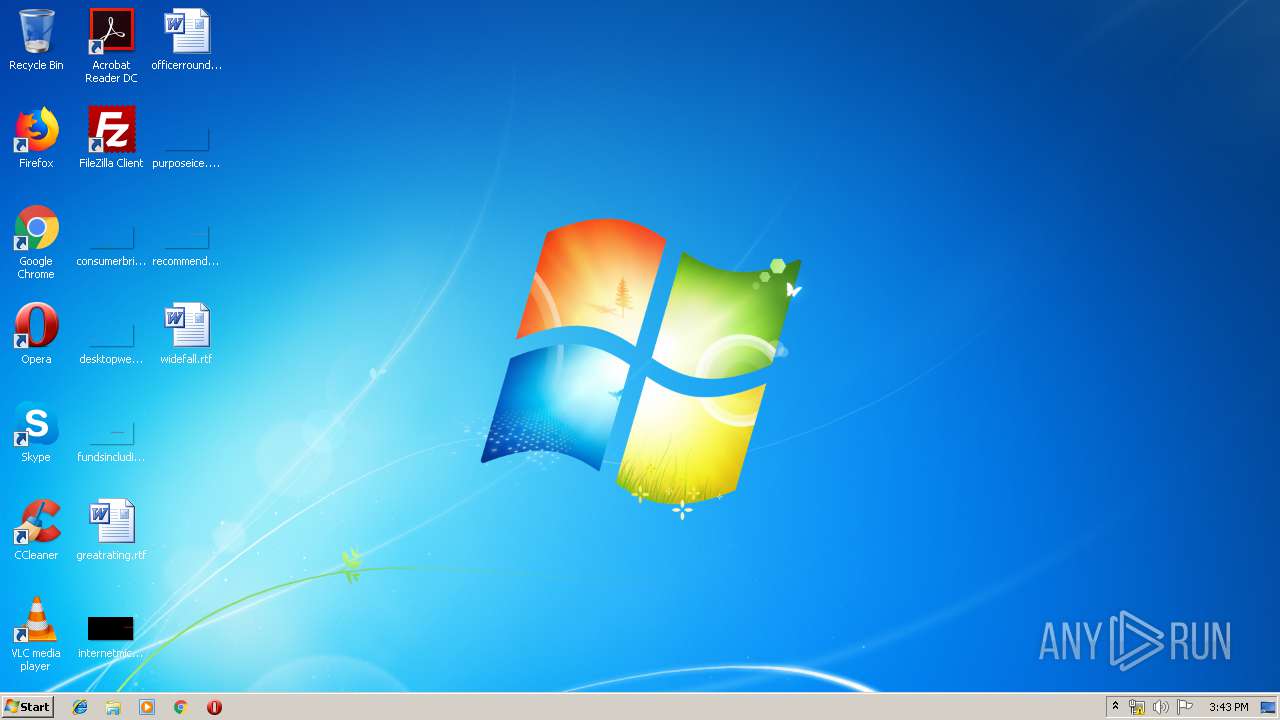
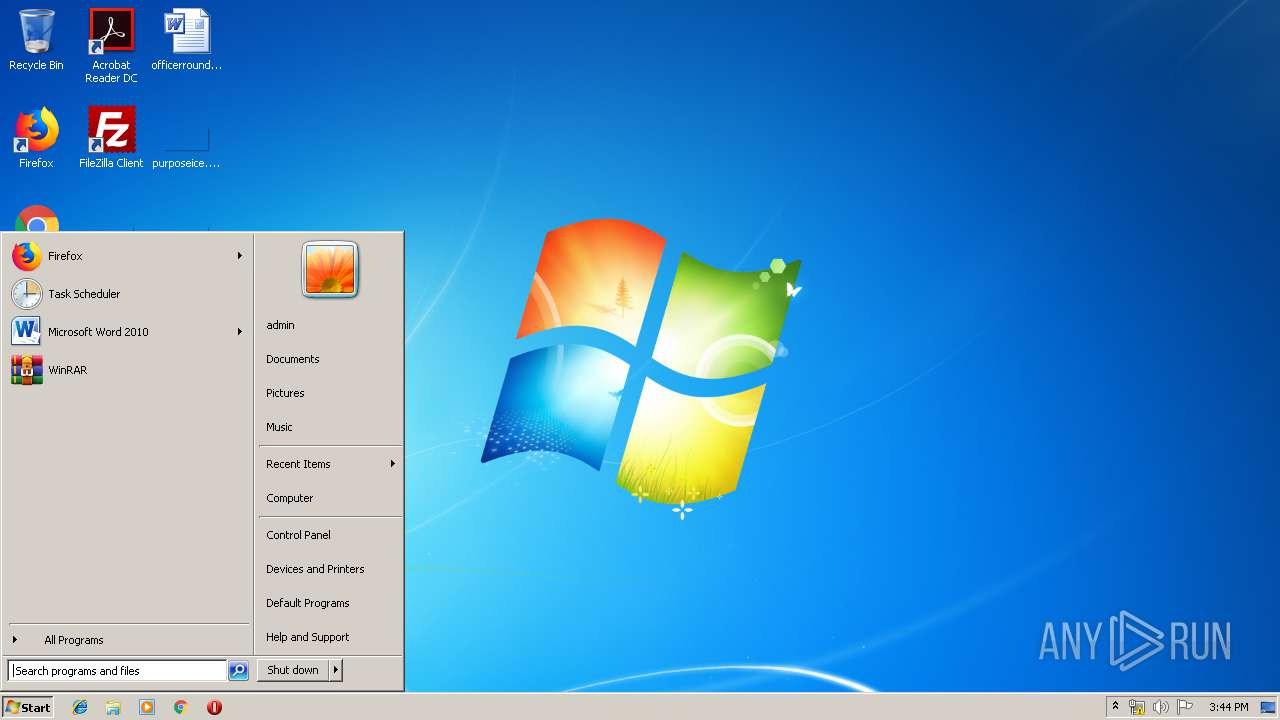
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 5962A7FAC8DE78EEFDE8E448C268274E |
| SHA1: | 2E7B54DA66F05797C21B0E5B1B44E50BD59C6A61 |
| SHA256: | FF4B7F0C60CE0554D893C02246D34656F2C3AAABE7149A11BC119D8899F06DFC |
| SSDEEP: | 12288:P23VZ1X3wSIqWe2rz3MeHqOVuFiD5Cwp3n+1VYpU:P0WJbM8VND5Cwxn+1VYpU |
MALICIOUS
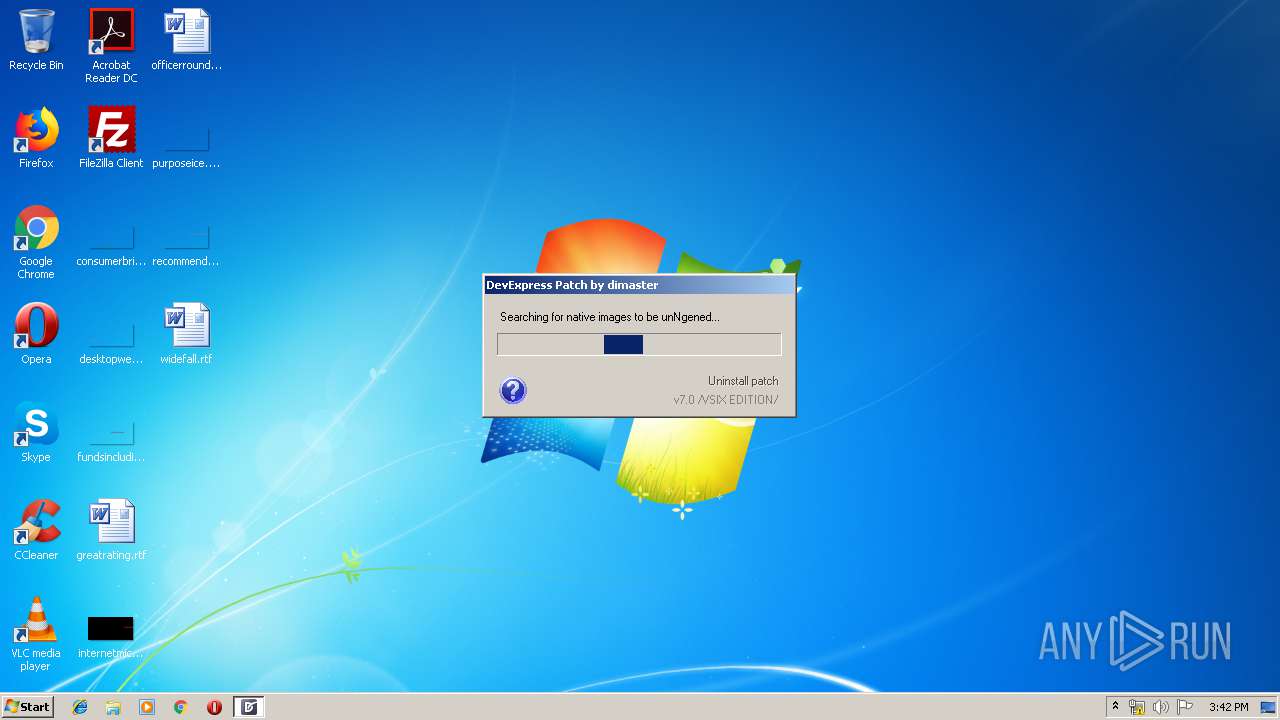
Loads dropped or rewritten executable
- Patch7.0.exe (PID: 4080)
SUSPICIOUS
Creates files in the Windows directory
- Patch7.0.exe (PID: 4080)
- ngen.exe (PID: 3368)
Executable content was dropped or overwritten
- Patch7.0.exe (PID: 4080)
Reads internet explorer settings
- Patch7.0.exe (PID: 4080)
Removes files from Windows directory
- Patch7.0.exe (PID: 4080)
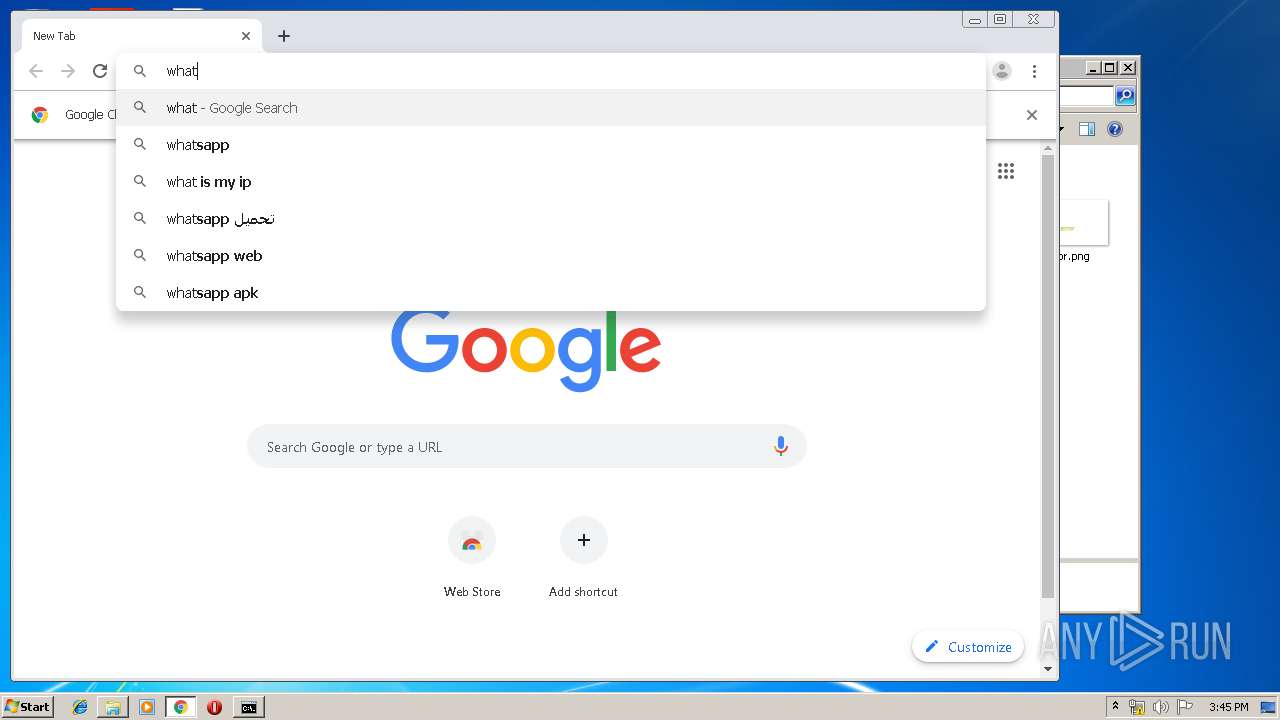
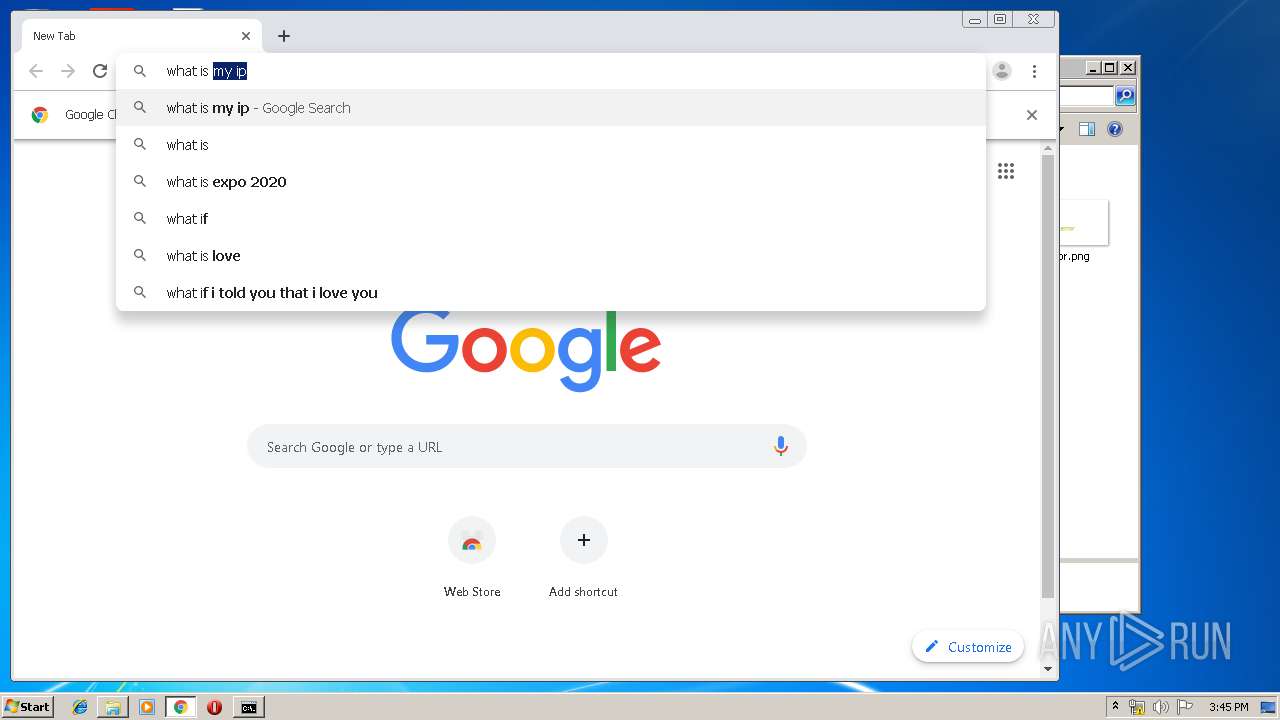
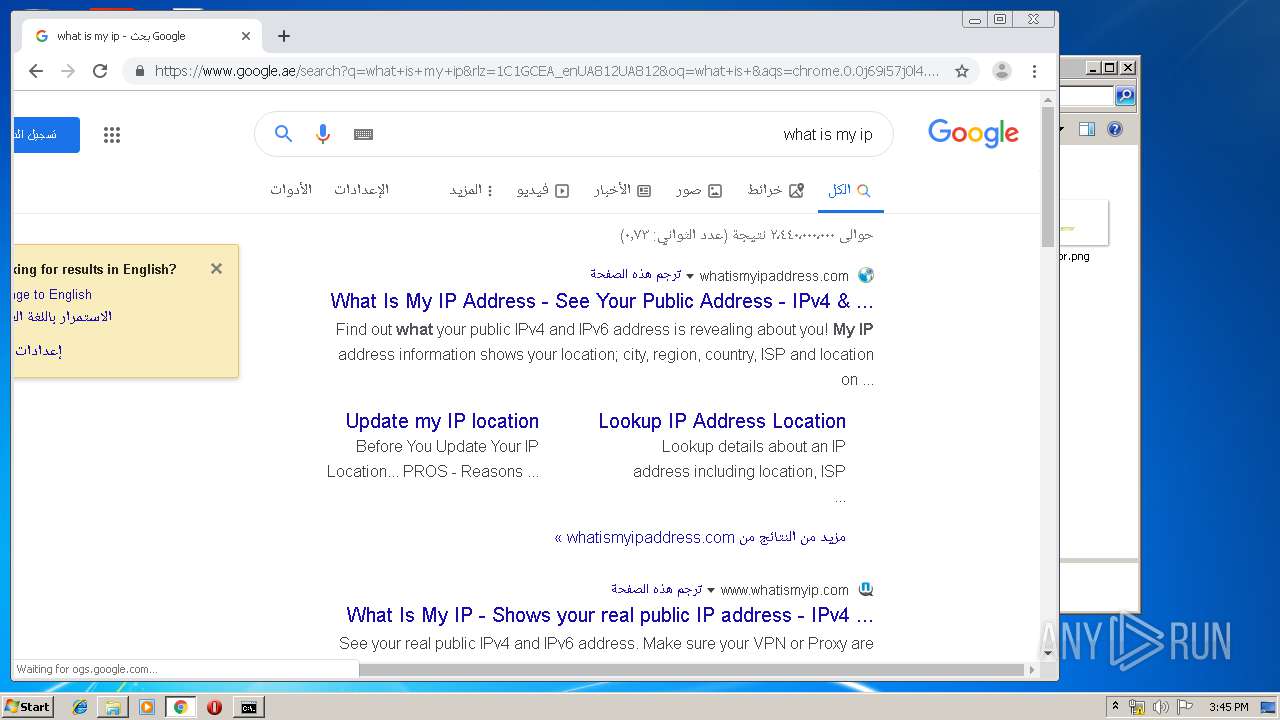
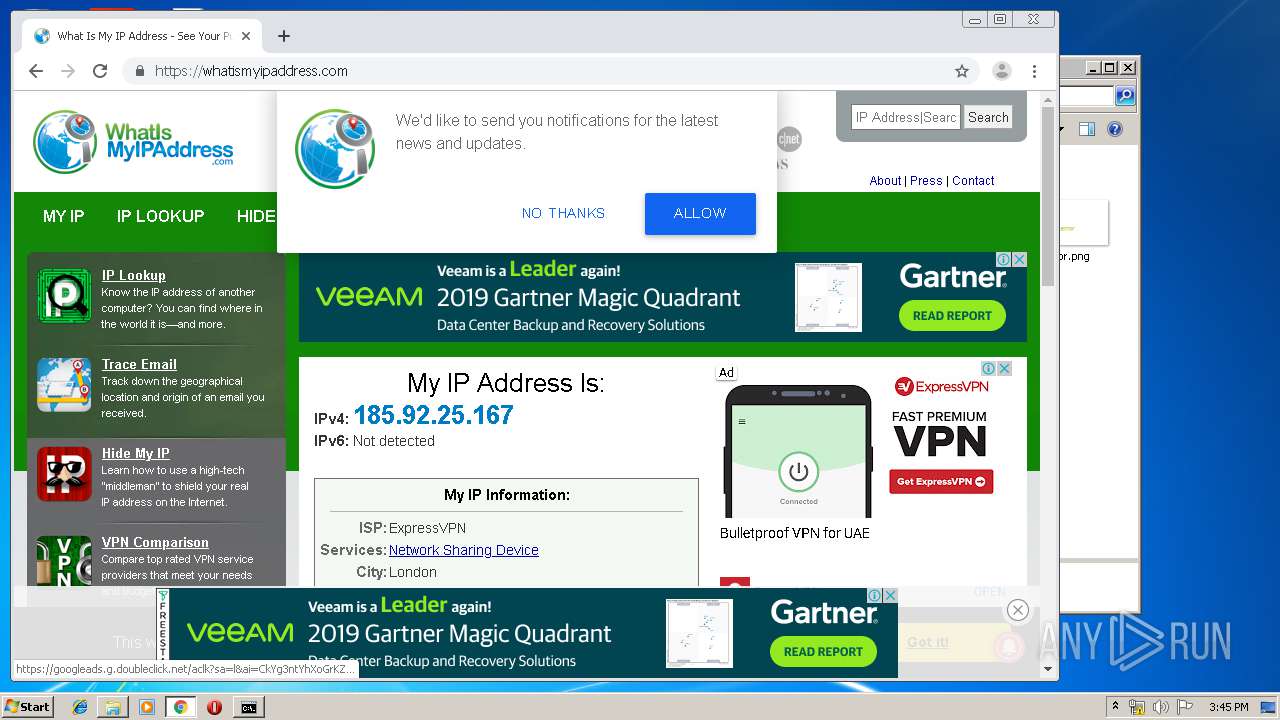
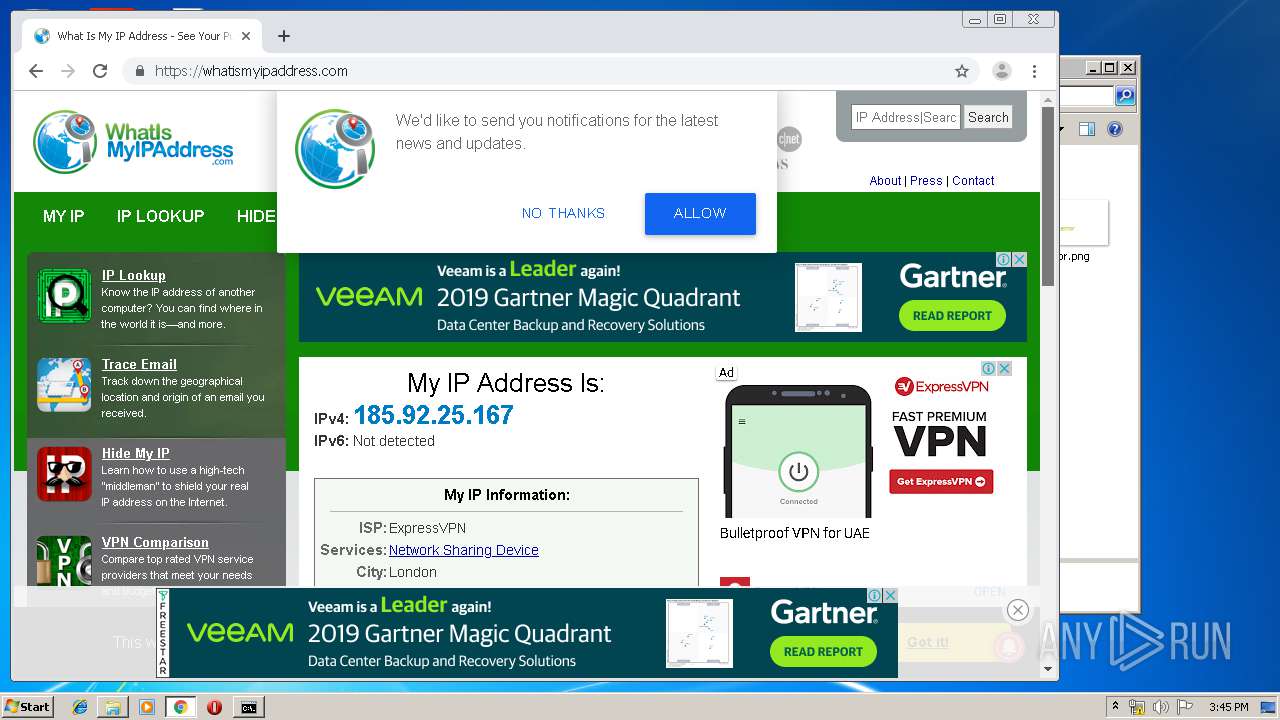
Uses IPCONFIG.EXE to discover IP address
- cmd.exe (PID: 3128)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3832)
INFO
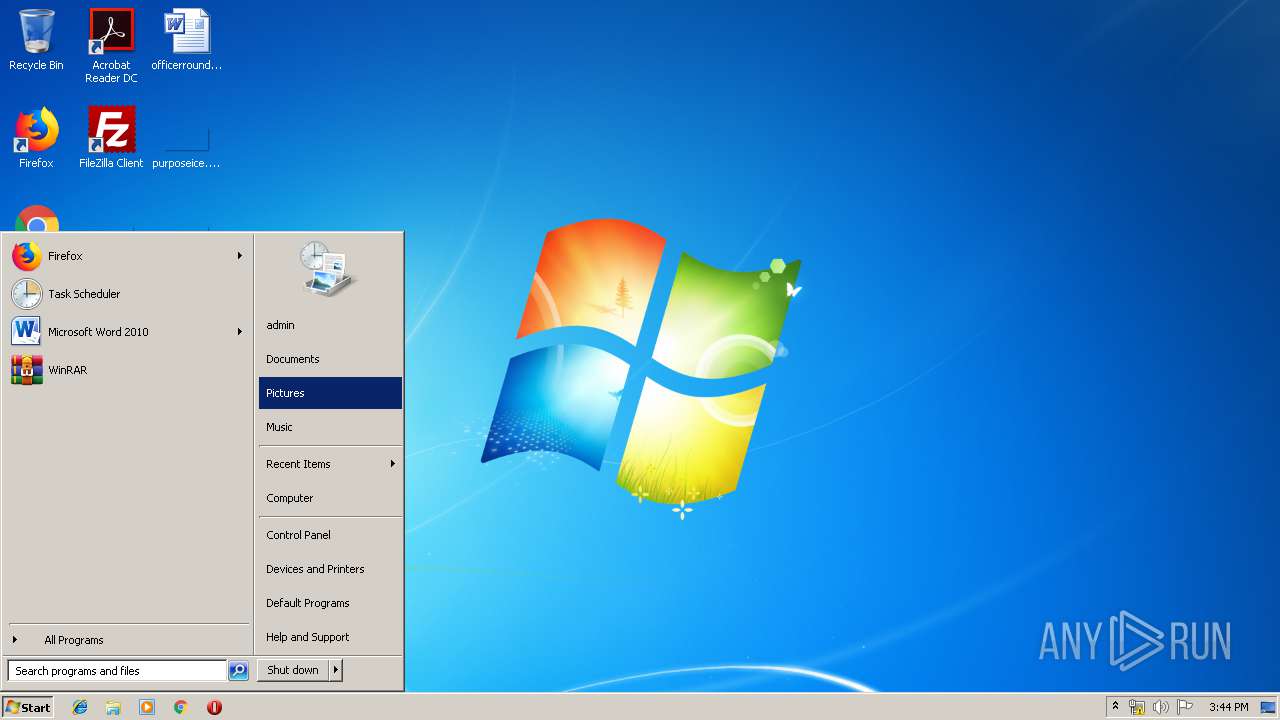
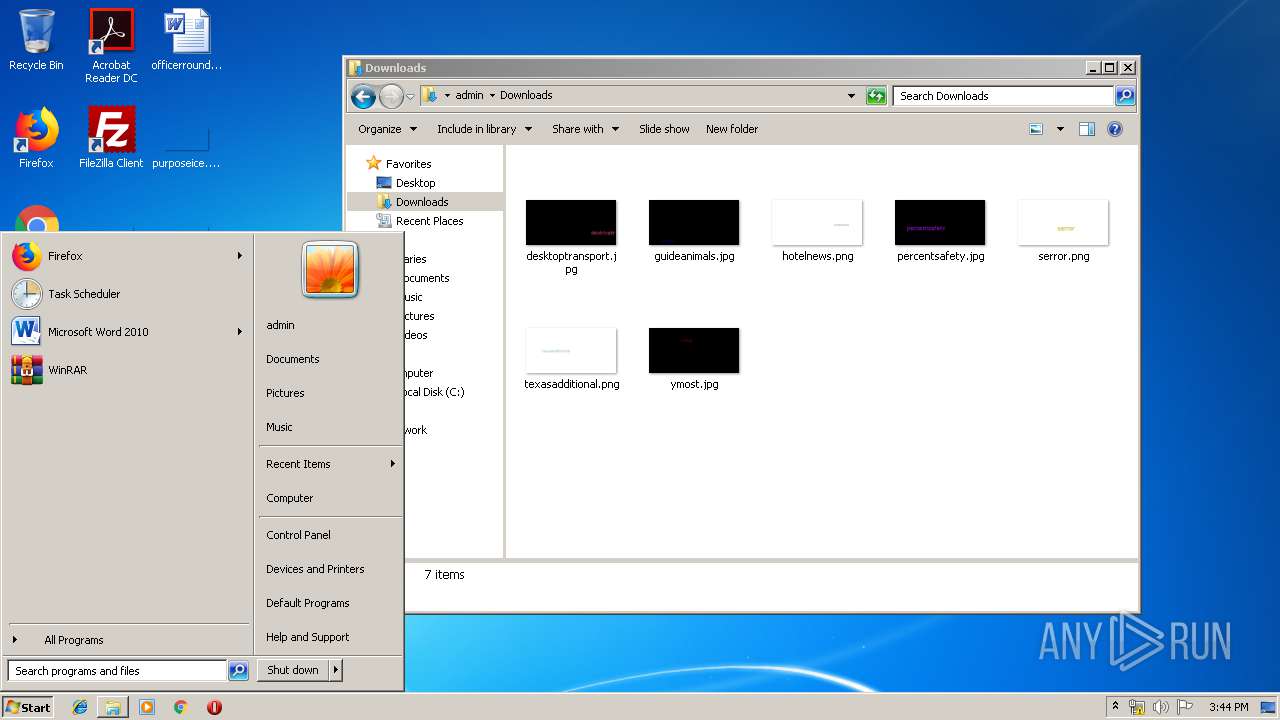
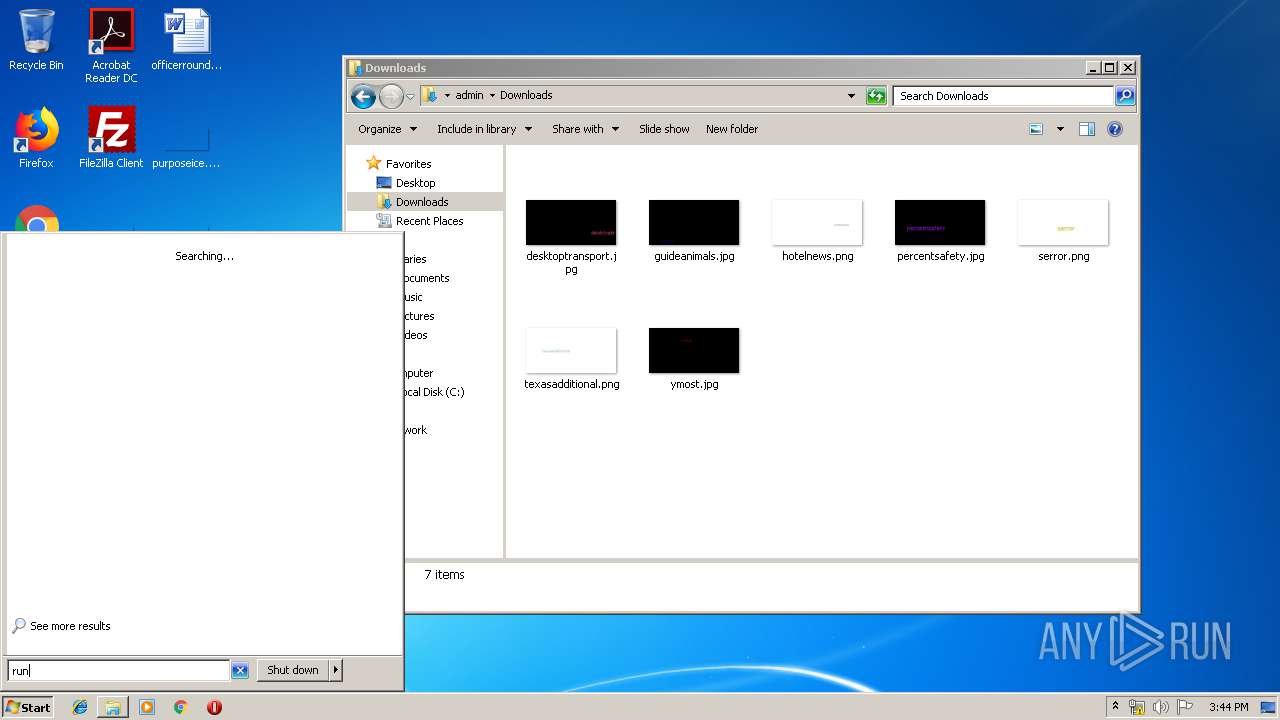
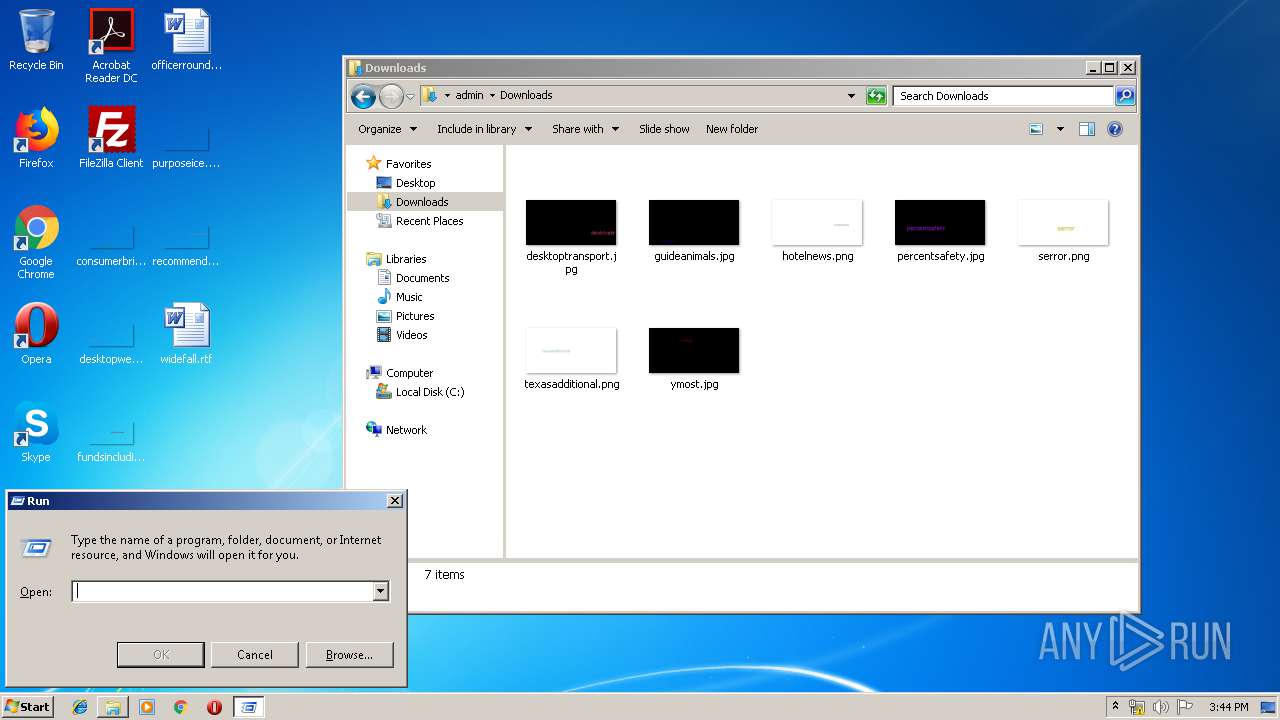
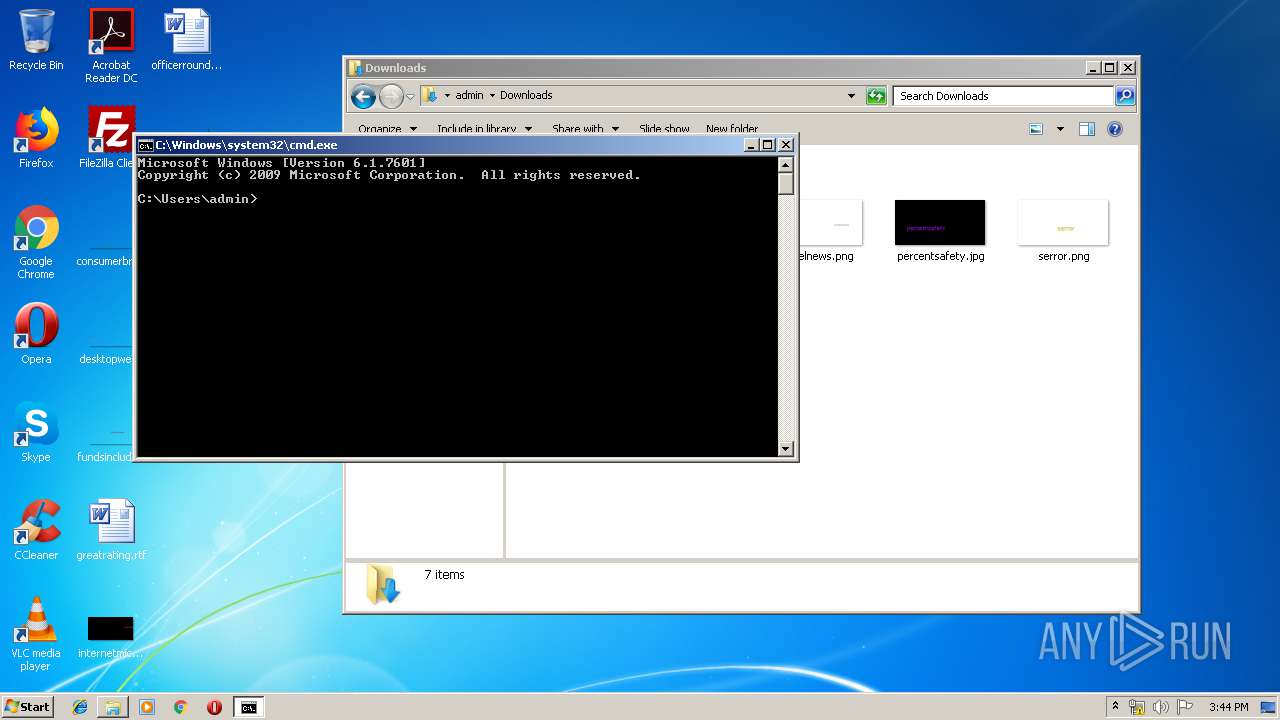
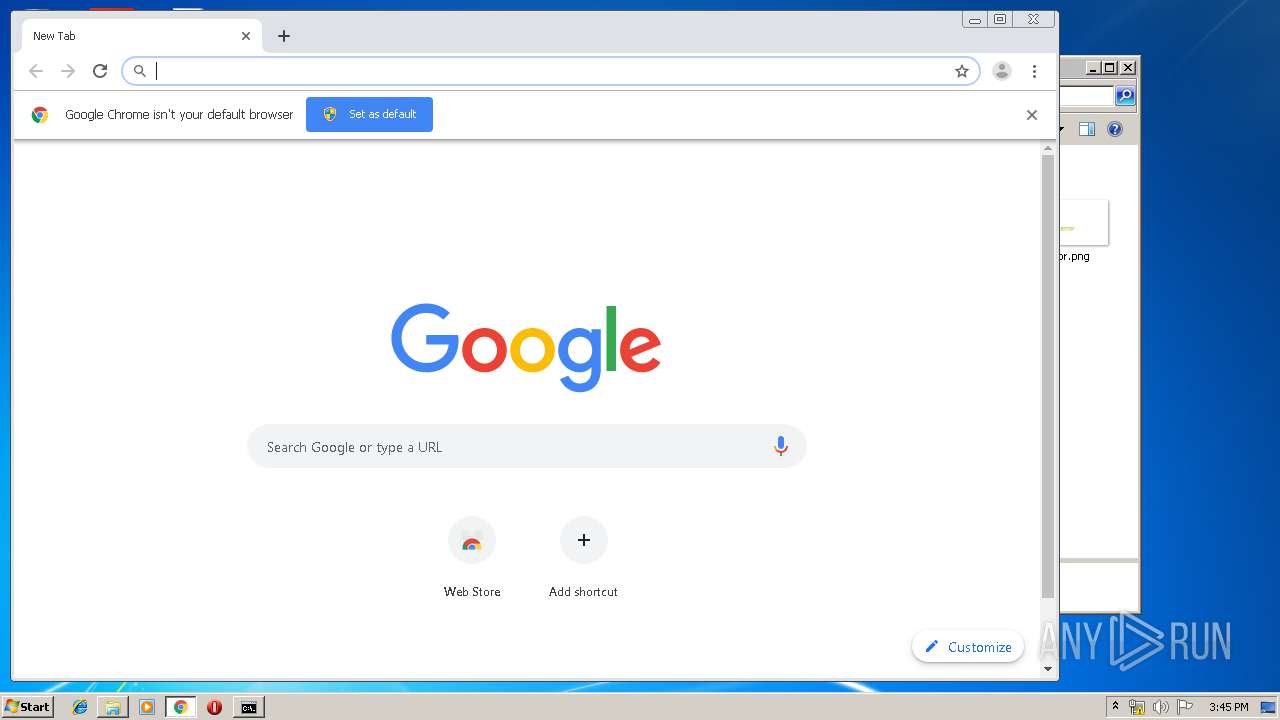
Manual execution by user
- cmd.exe (PID: 3128)
- chrome.exe (PID: 3832)
Reads the hosts file
- chrome.exe (PID: 3832)
- chrome.exe (PID: 2572)
Application launched itself
- chrome.exe (PID: 3832)
Reads settings of System Certificates
- chrome.exe (PID: 2572)
Changes settings of System certificates
- chrome.exe (PID: 2572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:08:14 11:08:40+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 470528 |
| InitializedDataSize: | 20480 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x74dde |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.0.0.0 |
| ProductVersionNumber: | 7.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | dimaster |
| FileDescription: | DevExpress.Patch |
| FileVersion: | 7.0.0.0 |
| InternalName: | DevExpress.Patch.exe |
| LegalCopyright: | Copyright © dimaster 2015 |
| LegalTrademarks: | - |
| OriginalFileName: | DevExpress.Patch.exe |
| ProductName: | DevExpress 2015 Universal Patch by dimaster |
| ProductVersion: | 7.0.0.0 |
| AssemblyVersion: | 7.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Aug-2015 09:08:40 |
| Comments: | - |
| CompanyName: | dimaster |
| FileDescription: | DevExpress.Patch |
| FileVersion: | 7.0.0.0 |
| InternalName: | DevExpress.Patch.exe |
| LegalCopyright: | Copyright © dimaster 2015 |
| LegalTrademarks: | - |
| OriginalFilename: | DevExpress.Patch.exe |
| ProductName: | DevExpress 2015 Universal Patch by dimaster |
| ProductVersion: | 7.0.0.0 |
| Assembly Version: | 7.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 14-Aug-2015 09:08:40 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00072DE4 | 0x00072E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.90417 |
.rsrc | 0x00076000 | 0x00004D00 | 0x00004E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.8401 |
.reloc | 0x0007C000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.42965 | 3312 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.50497 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.35361 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.45849 | 48 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
107
Monitored processes
65
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,3336348749294107158,7637144826095271056,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15395262223507445735 --mojo-platform-channel-handle=3584 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,3336348749294107158,7637144826095271056,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6240428930225035593 --mojo-platform-channel-handle=4528 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3336348749294107158,7637144826095271056,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2688415458508491977 --renderer-client-id=46 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4772 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3336348749294107158,7637144826095271056,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9131016391453634714 --renderer-client-id=49 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4388 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 616 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe" display | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | Patch7.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,3336348749294107158,7637144826095271056,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16402044553068347973 --mojo-platform-channel-handle=4100 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,3336348749294107158,7637144826095271056,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14973814152650218757 --mojo-platform-channel-handle=4092 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,3336348749294107158,7637144826095271056,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1388047008618953688 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,3336348749294107158,7637144826095271056,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6983806033897789234 --mojo-platform-channel-handle=3592 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,3336348749294107158,7637144826095271056,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5361061224648062485 --mojo-platform-channel-handle=3340 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 229
Read events
1 898
Write events
326
Delete events
5
Modification events
| (PID) Process: | (4080) Patch7.0.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application |
| Operation: | write | Name: | AutoBackupLogFiles |
Value: 0 | |||
| (PID) Process: | (4080) Patch7.0.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\COM+ SOAP Services |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Windows\Microsoft.NET\Framework\v4.0.30319\EventLogMessages.dll | |||
| (PID) Process: | (4080) Patch7.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fusion\GACChangeNotification\Default |
| Operation: | write | Name: | StoreChangeID |
Value: 783 | |||
| (PID) Process: | (4080) Patch7.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fusion\GACChangeNotification\Default |
| Operation: | write | Name: | StoreChangeIDFor64BitProcesses |
Value: 274 | |||
| (PID) Process: | (4080) Patch7.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fusion\GACChangeNotification\Default |
| Operation: | write | Name: | StoreChangeIDFor32BitProcesses |
Value: 783 | |||
| (PID) Process: | (4080) Patch7.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fusion\GACChangeNotification\Default |
| Operation: | write | Name: | DevExpress.Patch.Common,7.0.0.0,,7fc7bfca2443de66,MSIL |
Value: EC5140C74CCDD501 | |||
| (PID) Process: | (4080) Patch7.0.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4080) Patch7.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Licenses\0378852d-d597-4a32-b6d9-680a16a3cda6 |
| Operation: | write | Name: | 70 |
Value: HWCXMLODStqqYg9MI6kBvtiGhc7tLZNJ7+DJ4Y+JDMaK2/ISQtqrux0zNXOOHj7TmOGuN3eSTJcKsBqh6bwkTsO8OKSoRLtCI8Z0QQGYvxPJEL/MRL4kEoNaB79H2+WwW63Smg==AAAAAAAAAAAAAAAAAAAAAAAAAAA3MCw1Mzg2NzQ3OTc5Nzc1OSw1Mzg2NzQ3OTc5Nzc1OSxhZG1pbiwxLDEsMQ== | |||
| (PID) Process: | (4080) Patch7.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Licenses\6F0F8269-1516-44C6-BD30-0E90BE27871C |
| Operation: | write | Name: | 70 |
Value: 1309 | |||
| (PID) Process: | (4080) Patch7.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Licenses\0378852d-d597-4a32-b6d9-680a16a3cda6 |
| Operation: | write | Name: | 71 |
Value: JPHi9fDc1+9VjLSSYPZ+Kd7BL3OgqZJcwmq10/d+2j1gACqoFayTNyUQVPiIJPIgeZQb0+yKAvq+n5C4Tq05PVsZtpnnr5yLdD+eagJj4usFM42ZQ8sEs6knx4EMT3TUwFlyeA==AAAAAAAAAAAAAAAAAAAAAAAAAAA3MSw1Mzg2NzQ3OTc5Nzc1OSw1Mzg2NzQ3OTc5Nzc1OSxhZG1pbiwxLDEsMQ== | |||
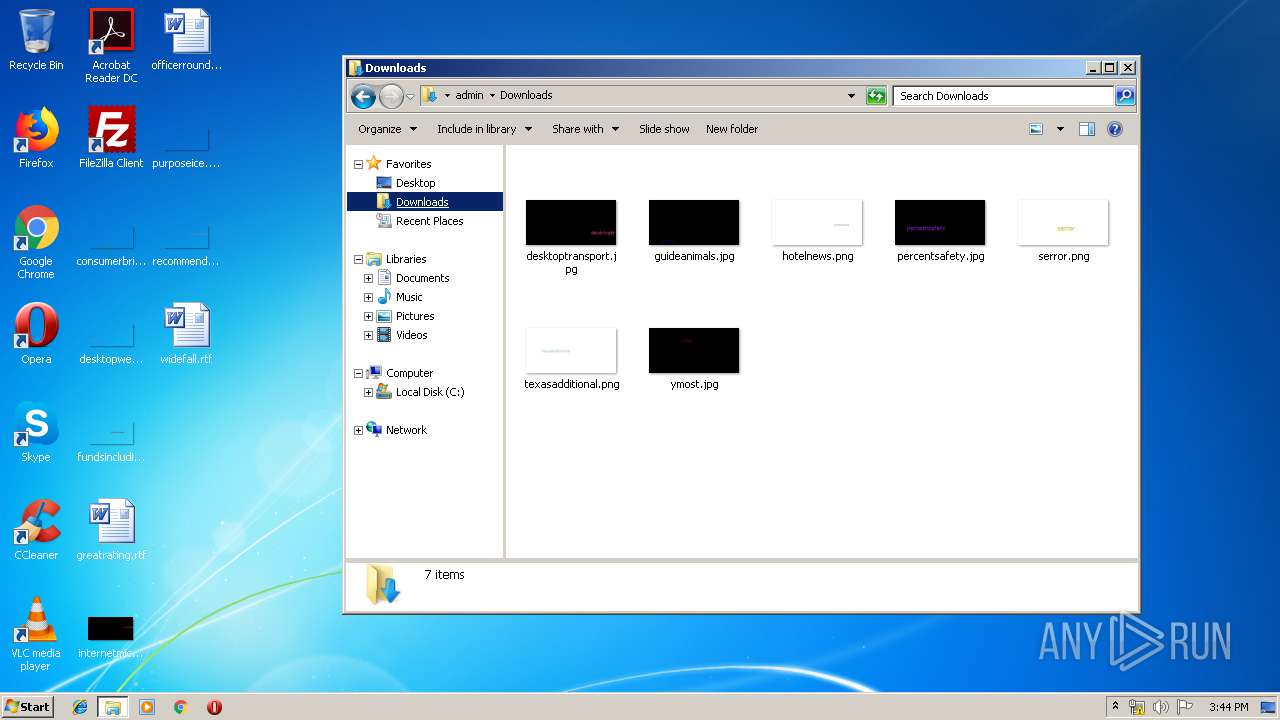
Executable files
4
Suspicious files
123
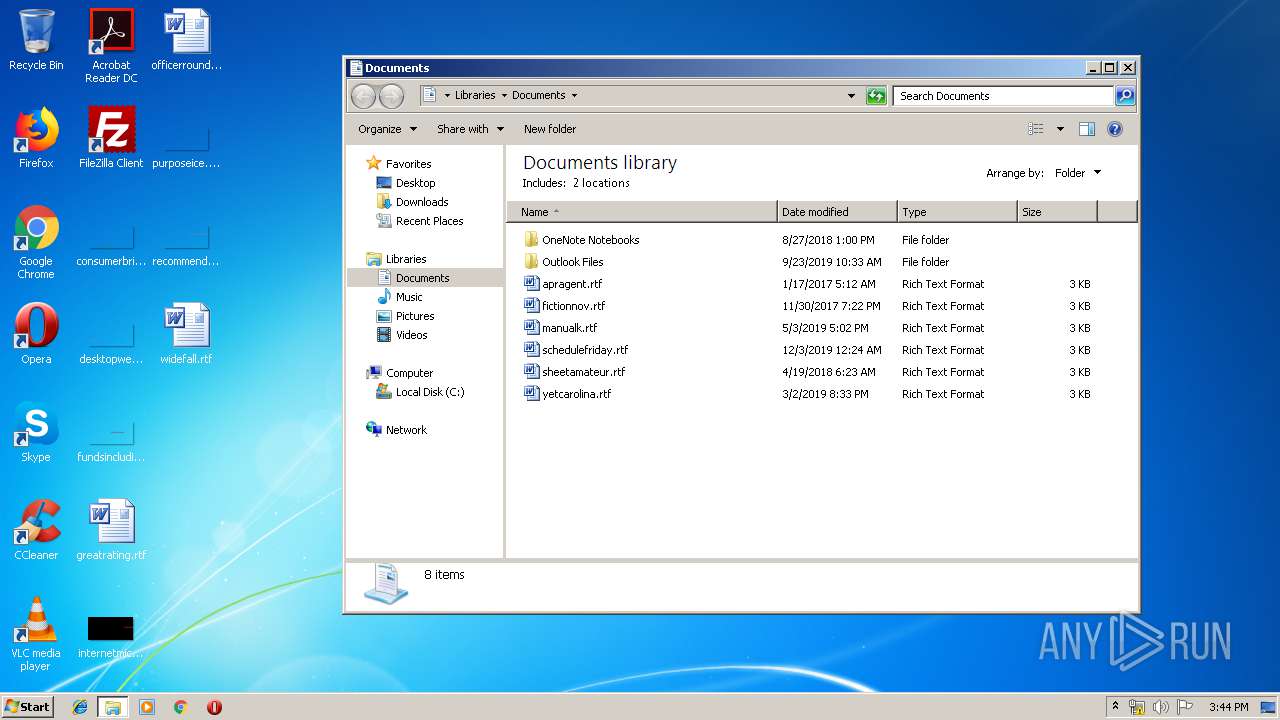
Text files
293
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4080 | Patch7.0.exe | C:\Windows\tfadxp70.txt | — | |
MD5:— | SHA256:— | |||
| 4080 | Patch7.0.exe | C:\Windows\assembly\tmp\DXAKWY1Y\DevExpress.Patch.Common.dll | — | |
MD5:— | SHA256:— | |||
| 4080 | Patch7.0.exe | C:\Windows\assembly\GAC_MSIL\DevExpress.Patch.Common\7.0.0.0__7fc7bfca2443de66 | — | |
MD5:— | SHA256:— | |||
| 3832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\79194a86-4bd2-44fb-ab6e-fbf8a179e1f7.tmp | — | |
MD5:— | SHA256:— | |||
| 3832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF3d85b1.TMP | text | |
MD5:— | SHA256:— | |||
| 3368 | ngen.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.log | text | |
MD5:— | SHA256:— | |||
| 3832 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF3d85b1.TMP | text | |
MD5:— | SHA256:— | |||
| 4080 | Patch7.0.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.log | text | |
MD5:— | SHA256:— | |||
| 616 | ngen.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.log | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
184
DNS requests
139
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2572 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
2572 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
2572 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
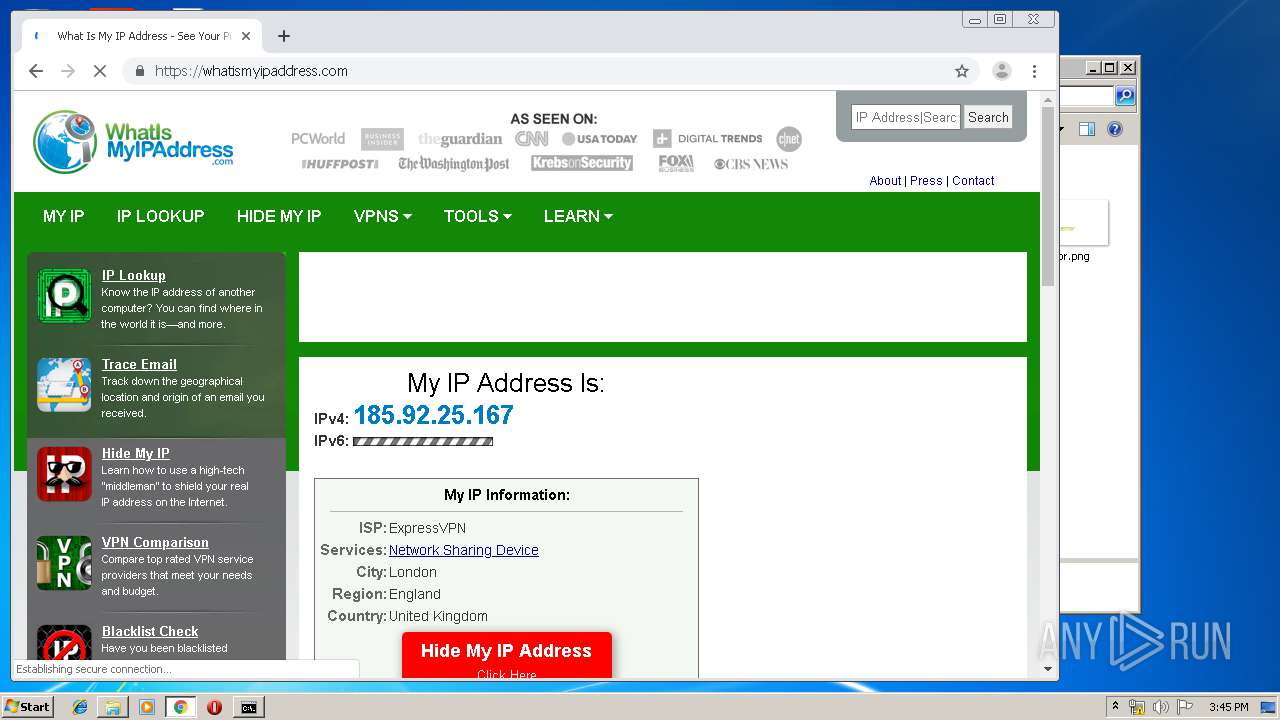
2572 | chrome.exe | GET | 200 | 74.125.4.168:80 | http://r3---sn-aigzrne7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.92.25.167&mm=28&mn=sn-aigzrne7&ms=nvh&mt=1579275803&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2572 | chrome.exe | GET | 200 | 173.194.138.200:80 | http://r3---sn-aigzrn7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.92.25.167&mm=28&mn=sn-aigzrn7d&ms=nvh&mt=1579275803&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
2572 | chrome.exe | GET | 200 | 204.13.202.71:80 | http://ssl.trustwave.com/issuers/STCA.crt | US | der | 956 b | whitelisted |
2572 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.comodoca.com/COMODORSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
2572 | chrome.exe | GET | 200 | 8.253.207.121:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
2572 | chrome.exe | GET | 200 | 52.222.168.106:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2572 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2572 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2572 | chrome.exe | 172.217.23.163:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2572 | chrome.exe | 172.217.22.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
2572 | chrome.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2572 | chrome.exe | 172.217.16.129:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2572 | chrome.exe | 172.217.23.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2572 | chrome.exe | 173.194.138.200:80 | r3---sn-aigzrn7d.gvt1.com | Google Inc. | US | whitelisted |
2572 | chrome.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
2572 | chrome.exe | 172.217.22.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
clients2.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r3---sn-aigzrn7d.gvt1.com |
| whitelisted |
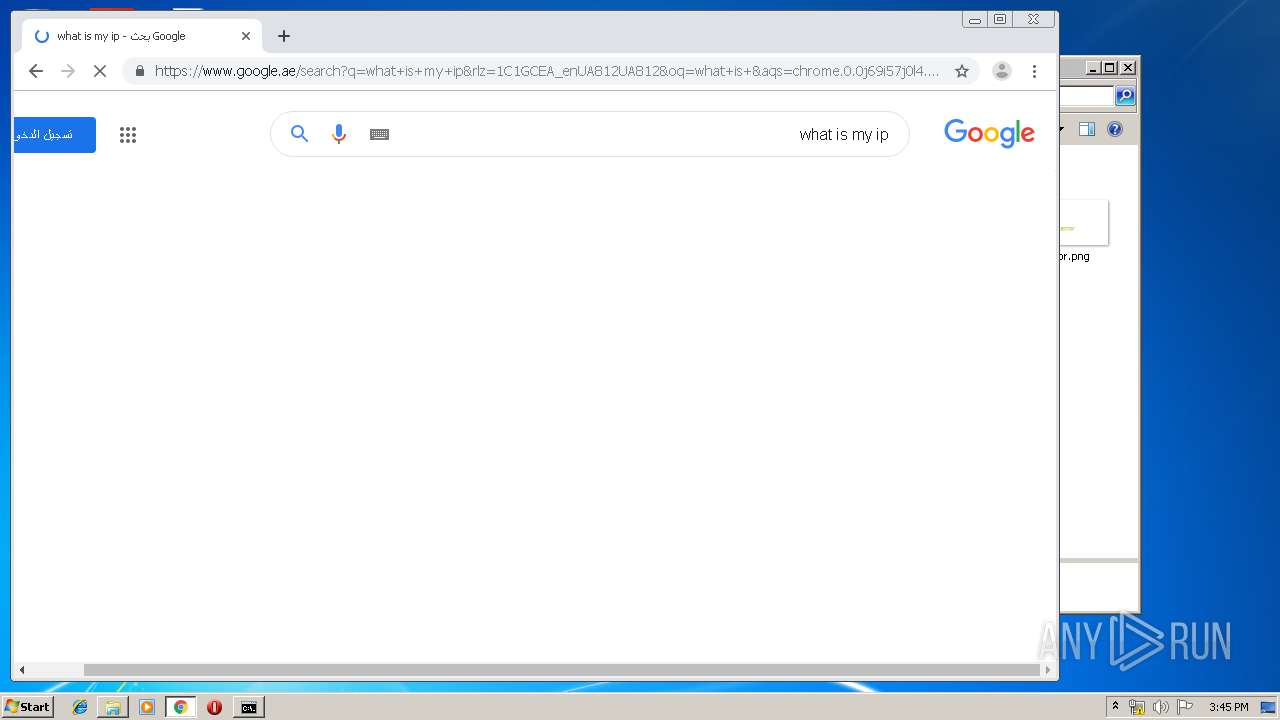
Threats
PID | Process | Class | Message |
|---|---|---|---|
2572 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Known External IP Lookup Service Domain in SNI |
2572 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Known External IP Lookup Service Domain in SNI |
2572 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Known External IP Lookup Service Domain in SNI |