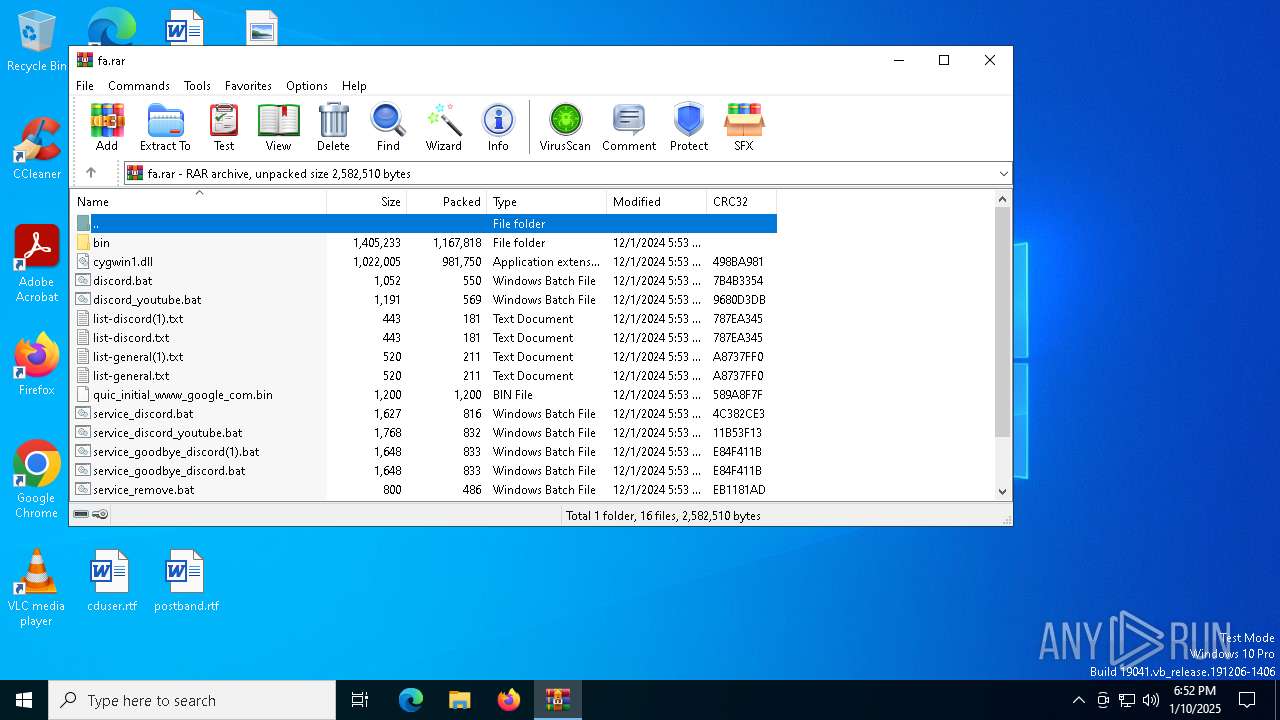
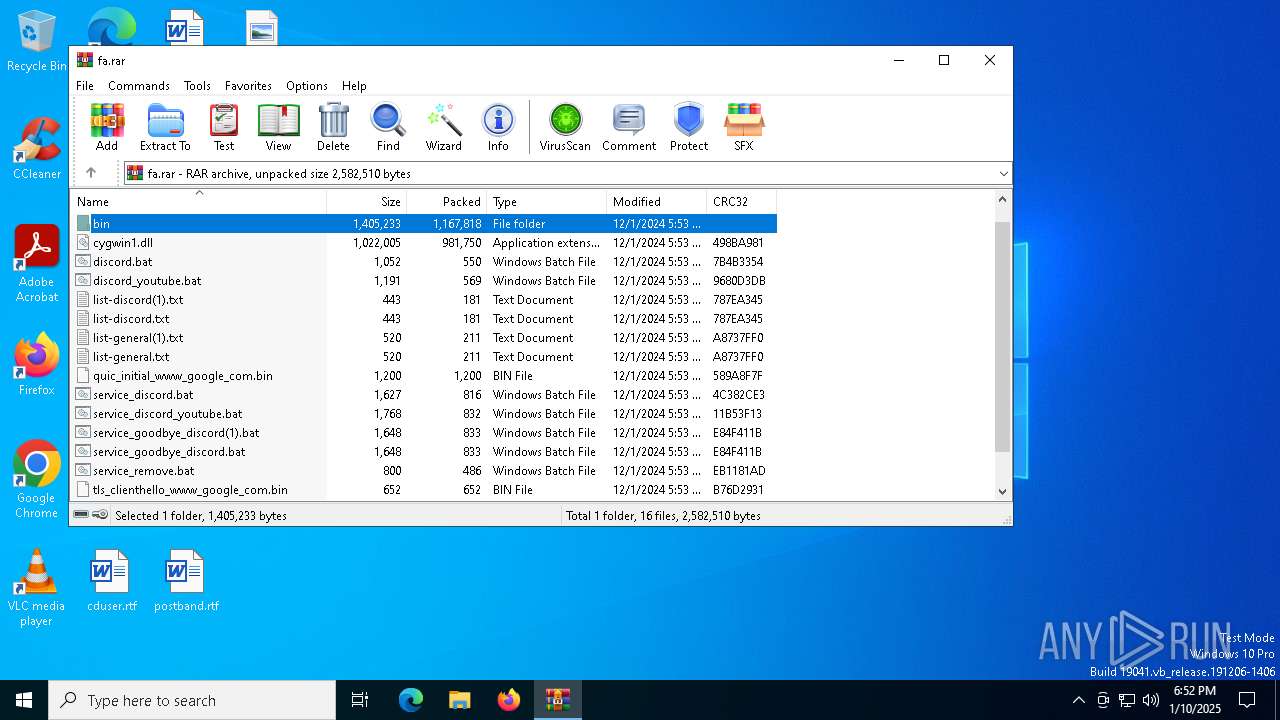
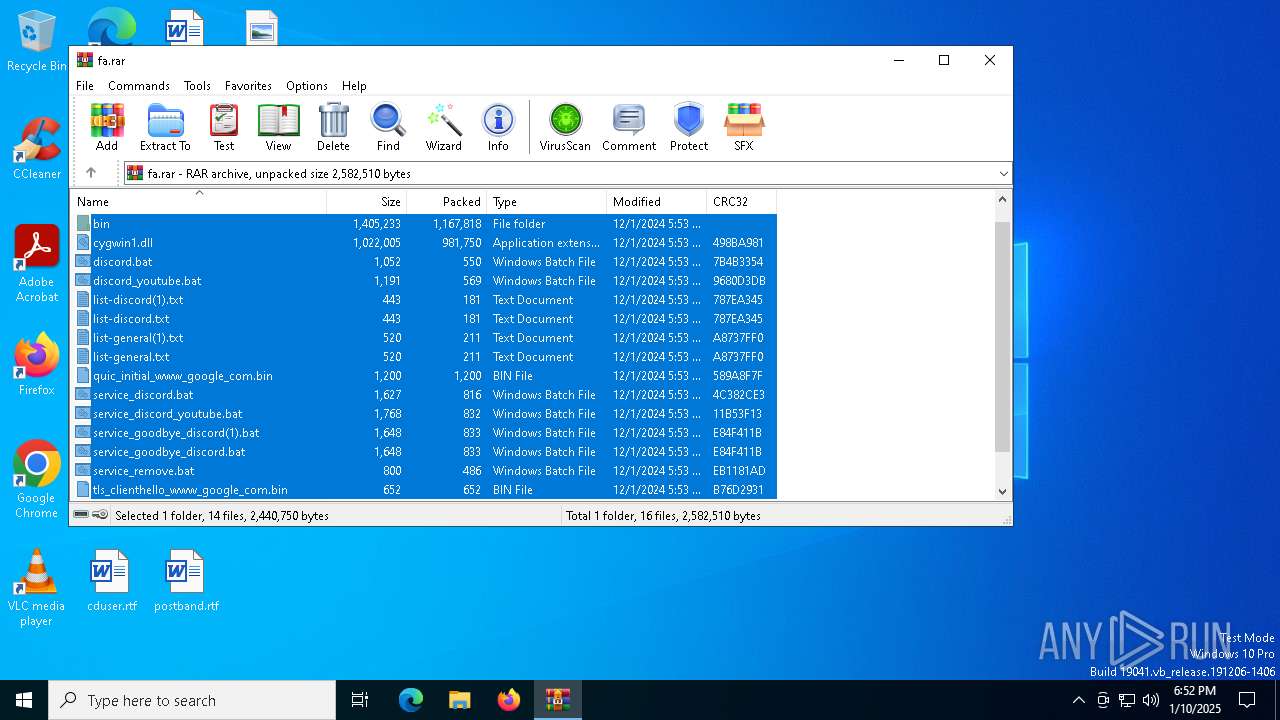
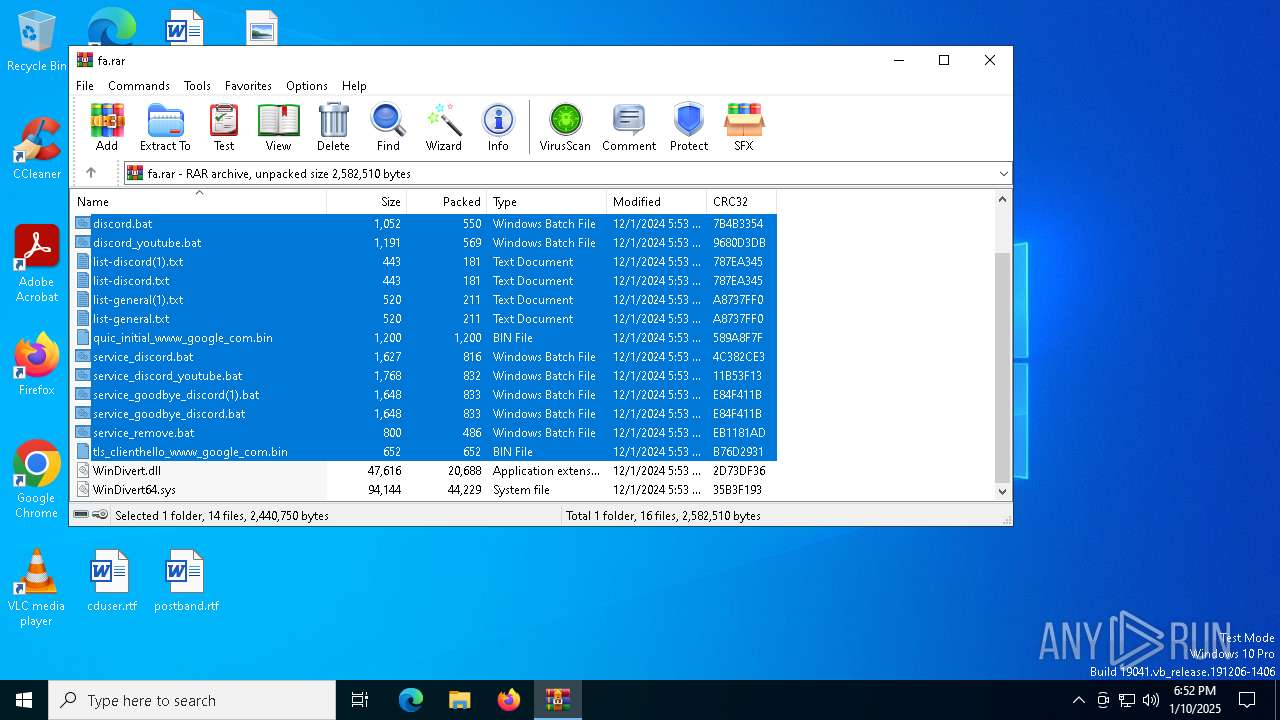
| File name: | fa.rar |
| Full analysis: | https://app.any.run/tasks/60ff8baa-b101-45cd-8a90-d1a3c857411b |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2025, 18:52:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 43D4D3BC5DFAE661A070D427BFABC82A |
| SHA1: | 7C9BBA2370E672102A82DC323B93D0B05ACB9639 |
| SHA256: | FF3B2F9ABF032794E4740D601FF09E1FBB0B78CEF17020A4D0CEF782FED62A6C |
| SSDEEP: | 98304:4zSlamsJKKg/kzPvXuaoAd66PRJcWh/7UswxfKYiEkcm6codVpGU7xWG0jIWvXXi:4meo+kb |
MALICIOUS
Detects Cygwin installation
- WinRAR.exe (PID: 5464)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 5464)
Starts application with an unusual extension
- cmd.exe (PID: 6880)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 5464)
The process uses the downloaded file
- WinRAR.exe (PID: 5464)
Changes the display of characters in the console
- cmd.exe (PID: 6880)
Manual execution by a user
- cmd.exe (PID: 6880)
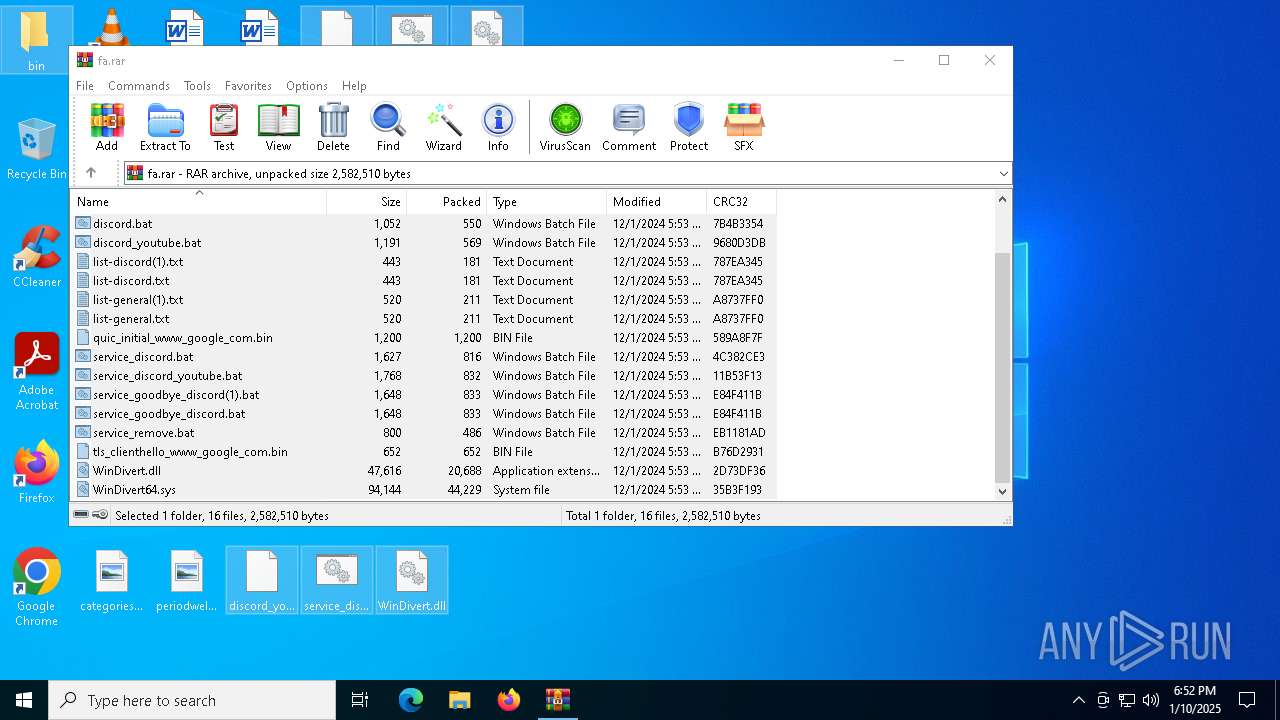
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5464)
Checks supported languages
- chcp.com (PID: 6940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 550 |
| UncompressedSize: | 1052 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | discord.bat |
Total processes
135
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5464 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\fa.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6880 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\discord_youtube.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6888 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6940 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6960 | "C:\Users\admin\Desktop\bin\winws.exe" --wf-tcp=80,443 --wf-udp=443,50000-65535 --filter-udp=443 --hostlist="C:\Users\admin\Desktop\list-general.txt" --dpi-desync=fake --dpi-desync-udplen-increment=10 --dpi-desync-repeats=6 --dpi-desync-udplen-pattern=0xDEADBEEF --dpi-desync-fake-quic="C:\Users\admin\Desktop\bin\quic_initial_www_google_com.bin" --new --filter-udp=50000-65535 --dpi-desync=fake,tamper --dpi-desync-any-protocol --dpi-desync-fake-quic="C:\Users\admin\Desktop\bin\quic_initial_www_google_com.bin" --new --filter-tcp=80 --hostlist="C:\Users\admin\Desktop\list-general.txt" --dpi-desync=fake,split2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig --new --filter-tcp=443 --hostlist="C:\Users\admin\Desktop\list-general.txt" --dpi-desync=fake,split2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig --dpi-desync-fake-tls="C:\Users\admin\Desktop\bin\tls_clienthello_www_google_com.bin" | C:\Users\admin\Desktop\bin\winws.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 6992 | "C:\Users\admin\Desktop\bin\winws.exe" --wf-tcp=80,443 --wf-udp=443,50000-65535 --filter-udp=443 --hostlist="C:\Users\admin\Desktop\list-general.txt" --dpi-desync=fake --dpi-desync-udplen-increment=10 --dpi-desync-repeats=6 --dpi-desync-udplen-pattern=0xDEADBEEF --dpi-desync-fake-quic="C:\Users\admin\Desktop\bin\quic_initial_www_google_com.bin" --new --filter-udp=50000-65535 --dpi-desync=fake,tamper --dpi-desync-any-protocol --dpi-desync-fake-quic="C:\Users\admin\Desktop\bin\quic_initial_www_google_com.bin" --new --filter-tcp=80 --hostlist="C:\Users\admin\Desktop\list-general.txt" --dpi-desync=fake,split2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig --new --filter-tcp=443 --hostlist="C:\Users\admin\Desktop\list-general.txt" --dpi-desync=fake,split2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig --dpi-desync-fake-tls="C:\Users\admin\Desktop\bin\tls_clienthello_www_google_com.bin" | C:\Users\admin\Desktop\bin\winws.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 7044 | "C:\Users\admin\Desktop\bin\winws.exe" --wf-tcp=80,443 --wf-udp=443,50000-65535 --filter-udp=443 --hostlist="C:\Users\admin\Desktop\list-general.txt" --dpi-desync=fake --dpi-desync-udplen-increment=10 --dpi-desync-repeats=6 --dpi-desync-udplen-pattern=0xDEADBEEF --dpi-desync-fake-quic="C:\Users\admin\Desktop\bin\quic_initial_www_google_com.bin" --new --filter-udp=50000-65535 --dpi-desync=fake,tamper --dpi-desync-any-protocol --dpi-desync-fake-quic="C:\Users\admin\Desktop\bin\quic_initial_www_google_com.bin" --new --filter-tcp=80 --hostlist="C:\Users\admin\Desktop\list-general.txt" --dpi-desync=fake,split2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig --new --filter-tcp=443 --hostlist="C:\Users\admin\Desktop\list-general.txt" --dpi-desync=fake,split2 --dpi-desync-autottl=2 --dpi-desync-fooling=md5sig --dpi-desync-fake-tls="C:\Users\admin\Desktop\bin\tls_clienthello_www_google_com.bin" | C:\Users\admin\Desktop\bin\winws.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 7056 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | winws.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 121
Read events
2 100
Write events
21
Delete events
0
Modification events
| (PID) Process: | (5464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\fa.rar | |||
| (PID) Process: | (5464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (5464) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
7
Suspicious files
4
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5464.47174\discord.bat | text | |
MD5:45690B45382641FBF75F75CBBB259817 | SHA256:8B08C005E87F890346366925312F448D5CDD65B9FEBC2922E9DF29F8B01B17FF | |||
| 5464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5464.47174\quic_initial_www_google_com.bin | binary | |
MD5:312526D39958D89B1F8AB67789AB985F | SHA256:F4589C57749F956BB30538197A521D7005F8B0A8723B4707E72405E51DDAC50A | |||
| 5464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5464.47174\list-discord(1).txt | text | |
MD5:6B11A60838A26A7B78F366036AC5E945 | SHA256:3A7B6AAEDEF1ACD96281546214593ACEAEE30084DDC712C4EE125FCD51E27935 | |||
| 5464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5464.47174\service_goodbye_discord.bat | text | |
MD5:50DD66C2196F7D8518140C3EB2B204EB | SHA256:A04E7FC4DBECC3617663A418CF2DE30A2D1528F88A32AC5019EB8F0F9704C12F | |||
| 5464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5464.47174\list-general(1).txt | text | |
MD5:973CE9FD99CE984A7C4ED77D41ACAF3B | SHA256:FE37729CF2C925668251FE19951EDDB31FBEBA069112410109851AB7ACF69ABE | |||
| 5464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5464.47174\service_discord.bat | text | |
MD5:8ACA9A7FA70CA4FBF815467209BFAD44 | SHA256:14ACA13DBEEA50E24B0FA2E3E7DEFCC8962E055DDA038939567CFA5CBED35987 | |||
| 5464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5464.47174\discord_youtube.bat | text | |
MD5:A86EE199DF14377CC62001FE47CE9EC3 | SHA256:B1F1FFC91EB71C40FBADA38A9E9067DFEAFCD97051B1CE8FEB8ADC49364F3725 | |||
| 5464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5464.47174\service_goodbye_discord(1).bat | text | |
MD5:50DD66C2196F7D8518140C3EB2B204EB | SHA256:A04E7FC4DBECC3617663A418CF2DE30A2D1528F88A32AC5019EB8F0F9704C12F | |||
| 5464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5464.47174\list-discord.txt | text | |
MD5:6B11A60838A26A7B78F366036AC5E945 | SHA256:3A7B6AAEDEF1ACD96281546214593ACEAEE30084DDC712C4EE125FCD51E27935 | |||
| 5464 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5464.47174\list-general.txt | text | |
MD5:973CE9FD99CE984A7C4ED77D41ACAF3B | SHA256:FE37729CF2C925668251FE19951EDDB31FBEBA069112410109851AB7ACF69ABE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
31
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.169:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6276 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4 | System | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4 | System | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2040 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 2.16.204.148:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 23.48.23.169:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |