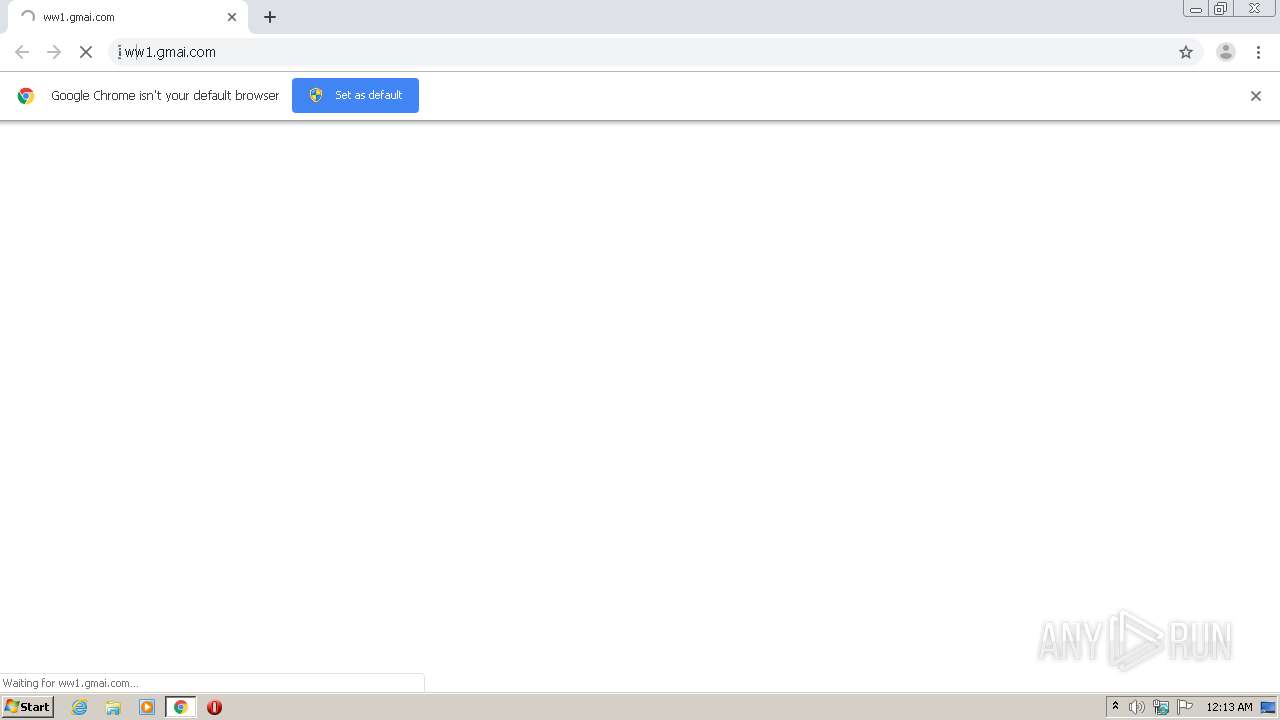
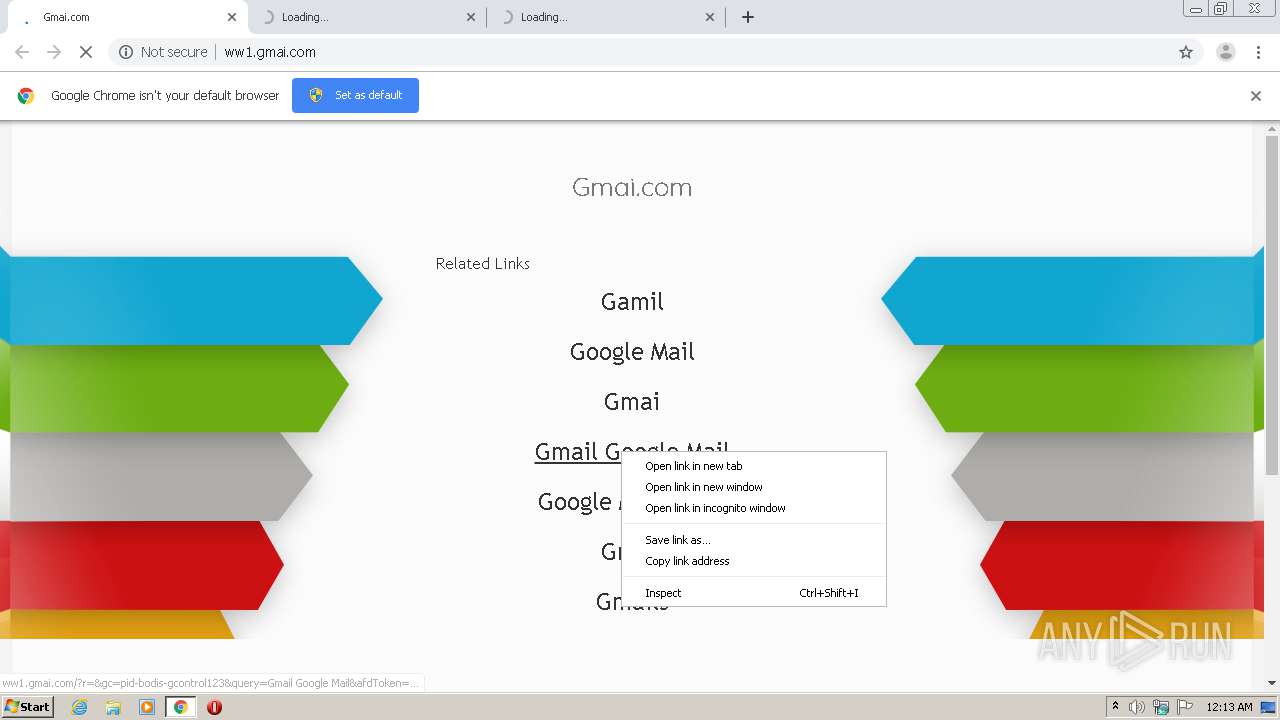
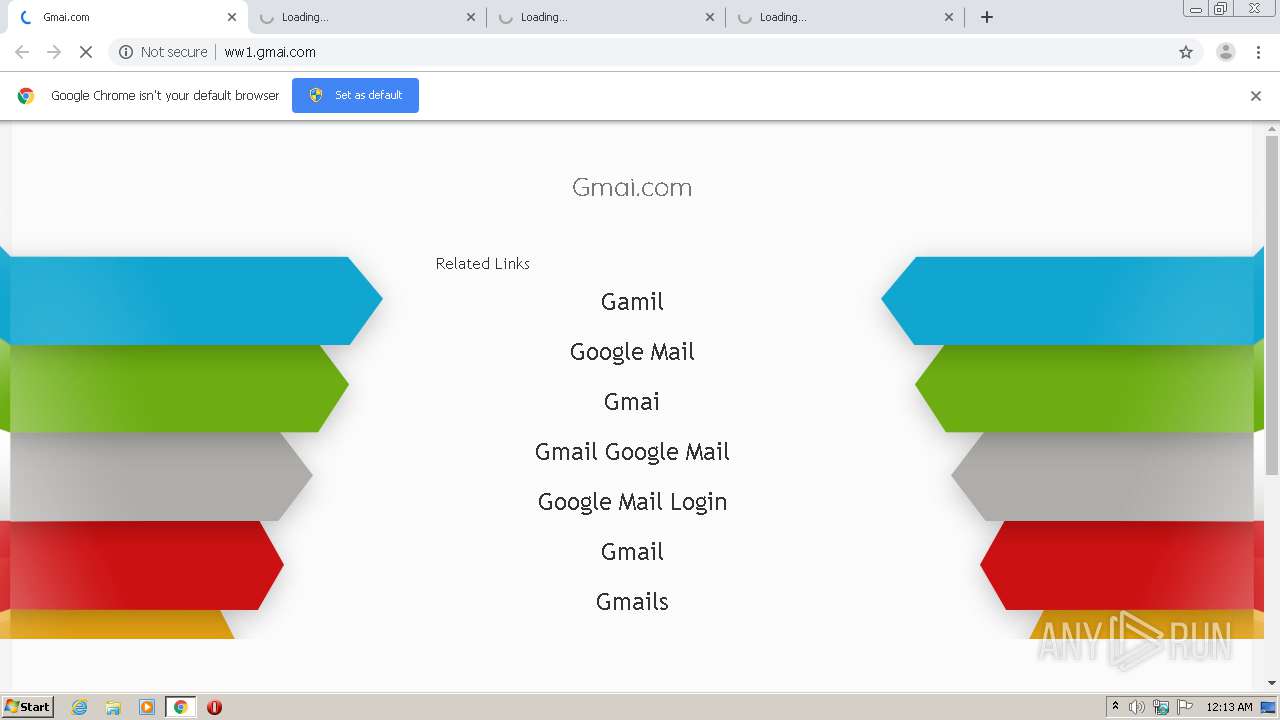
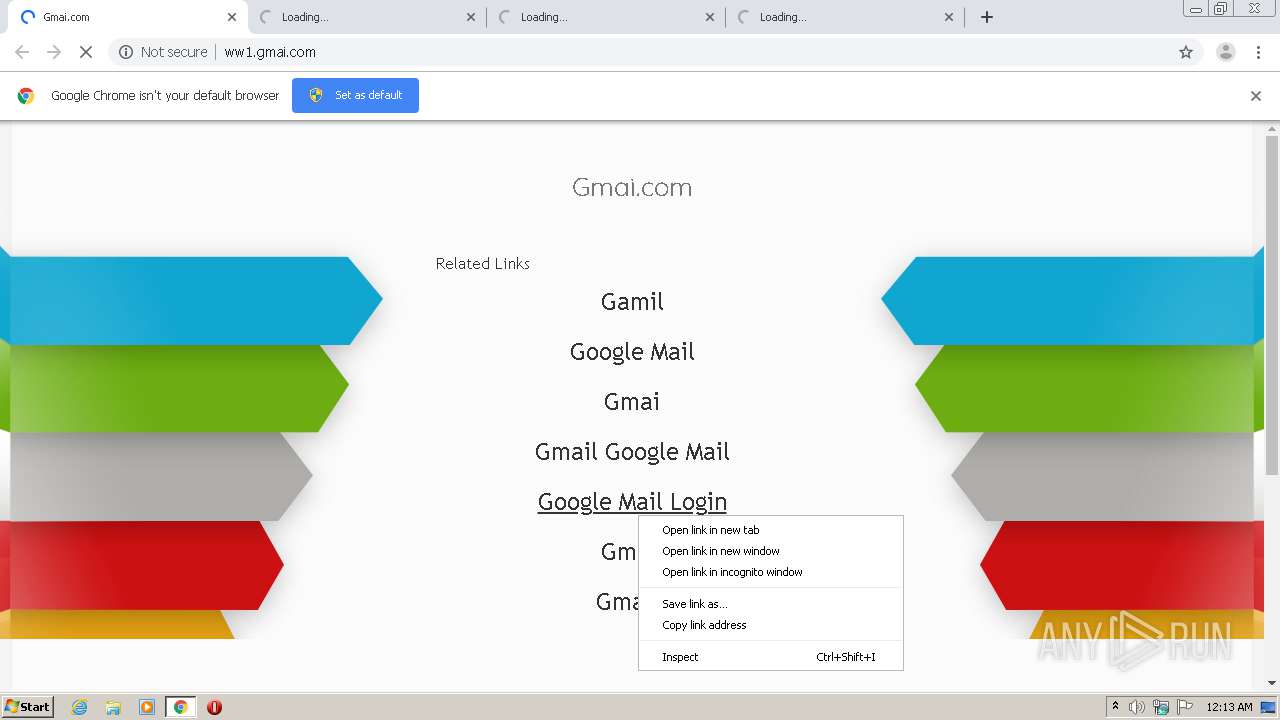
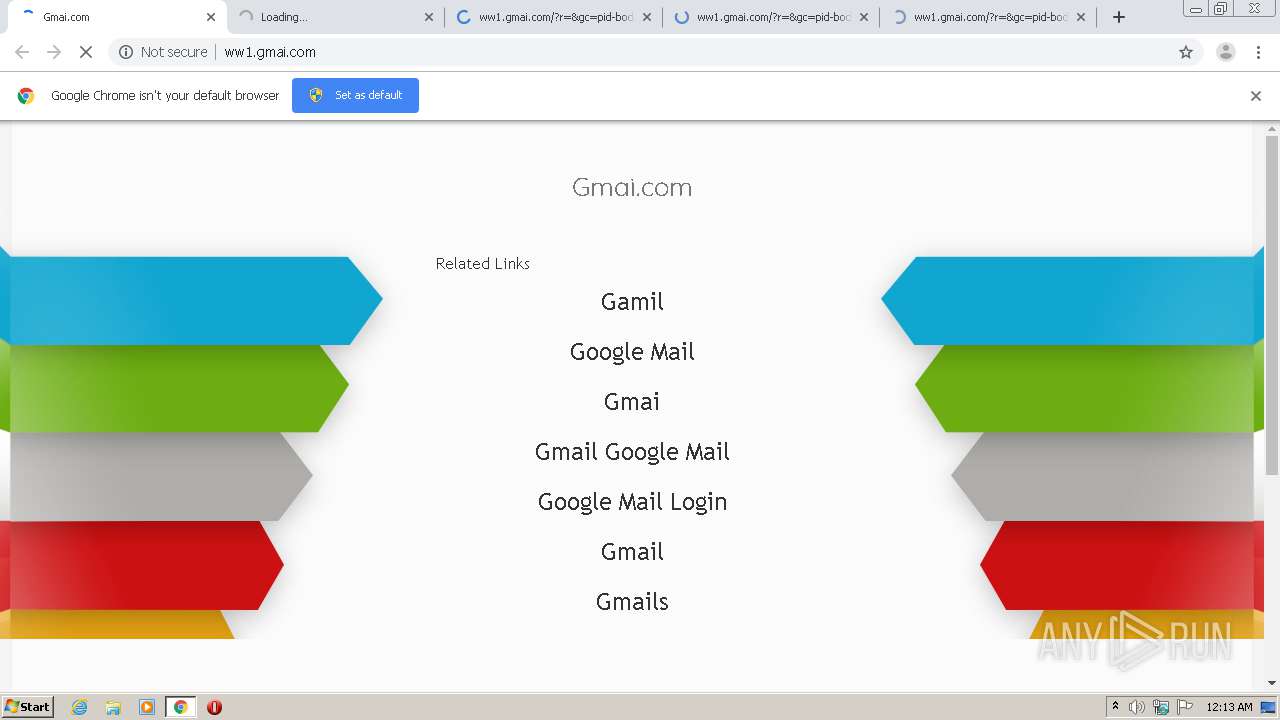
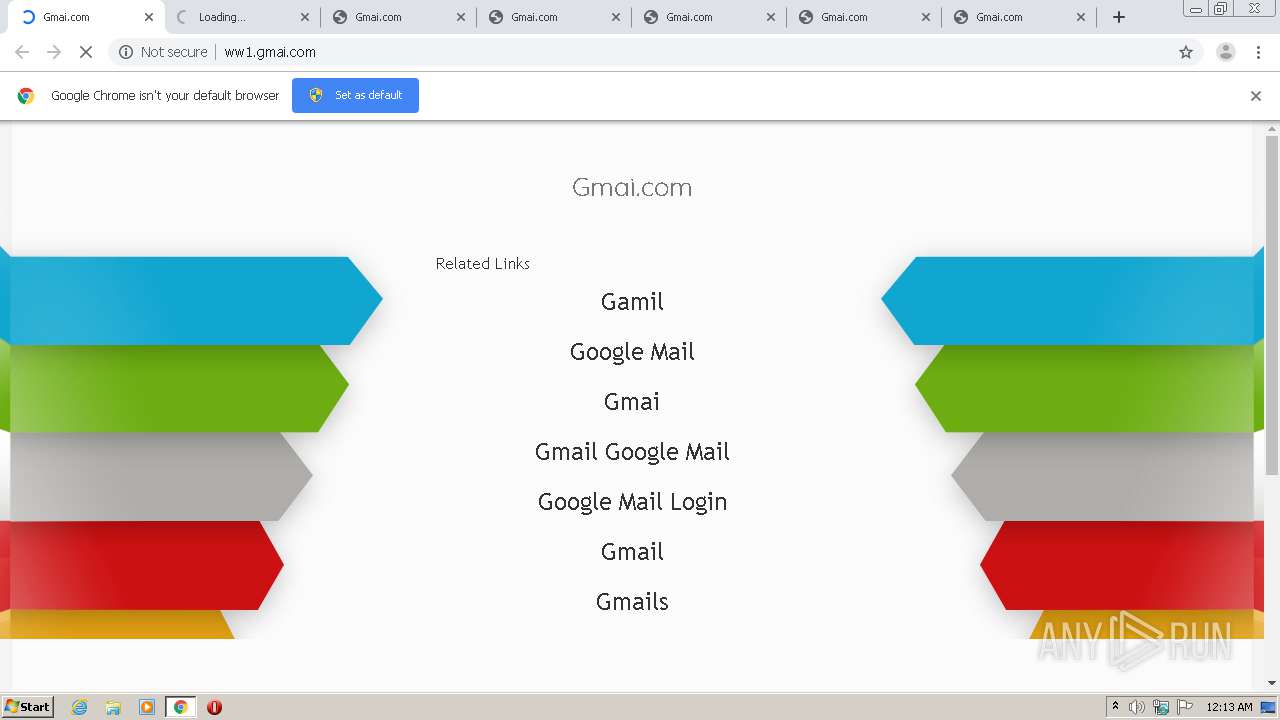
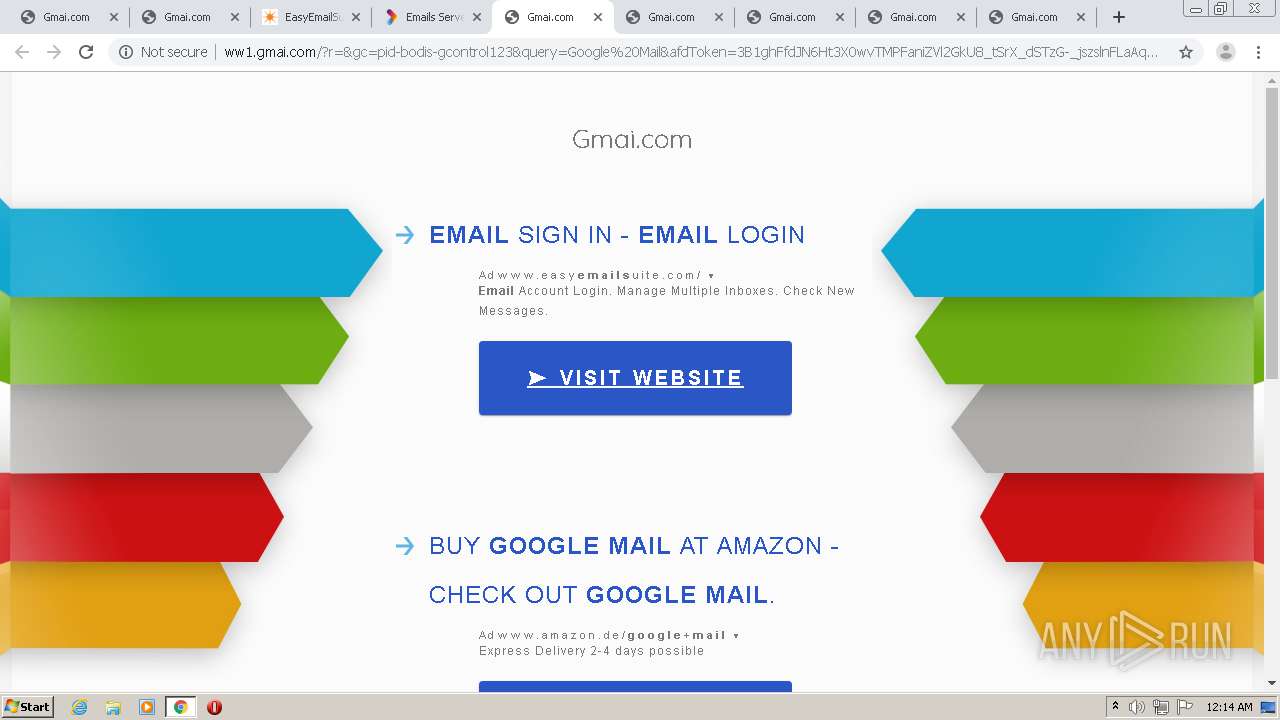
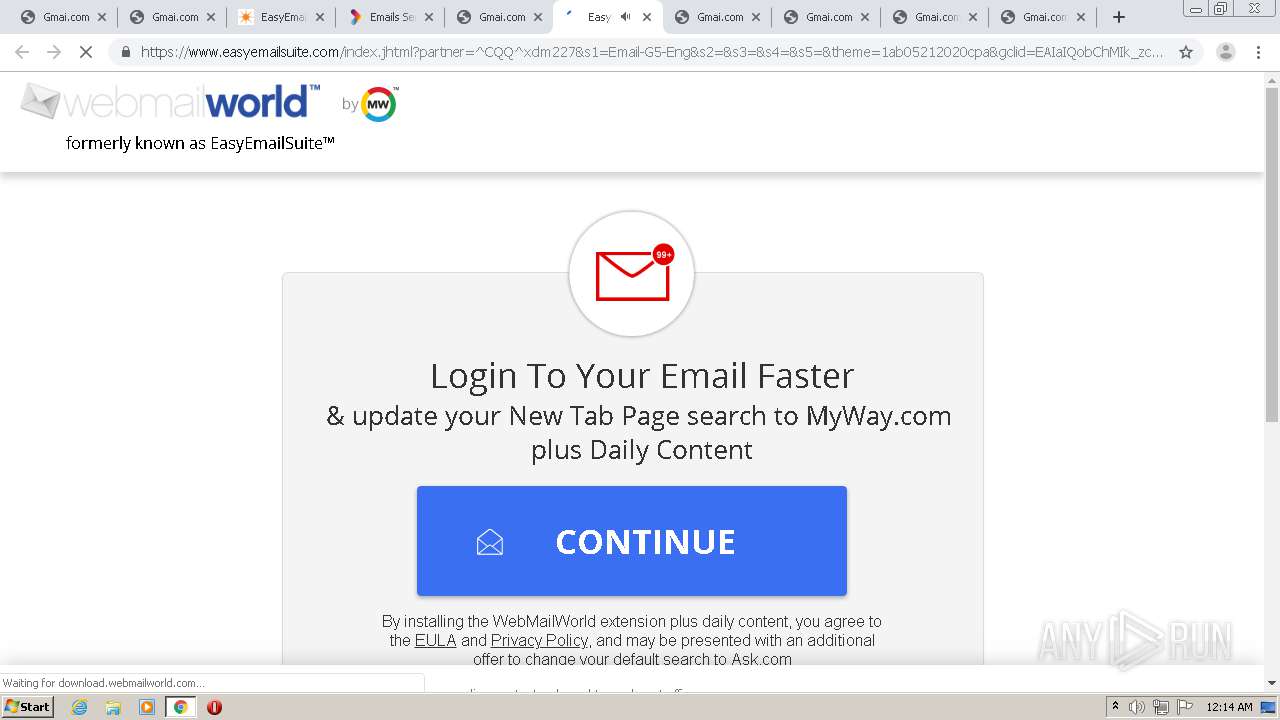
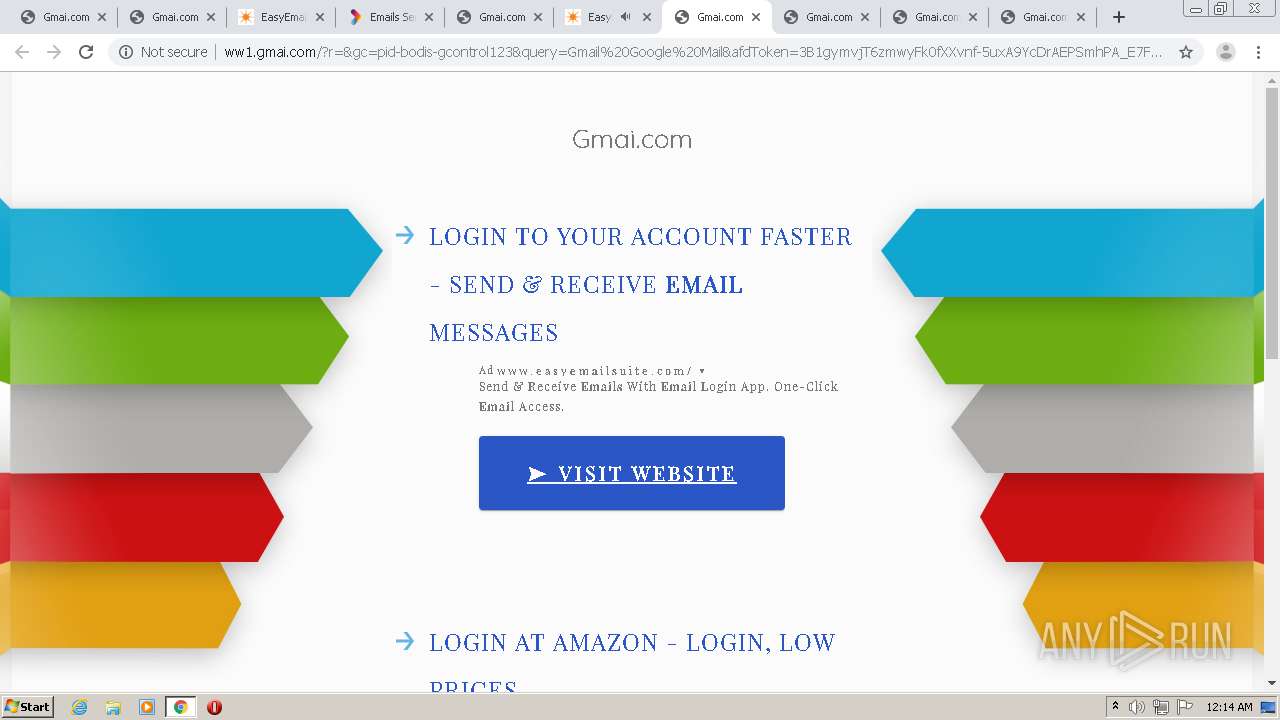
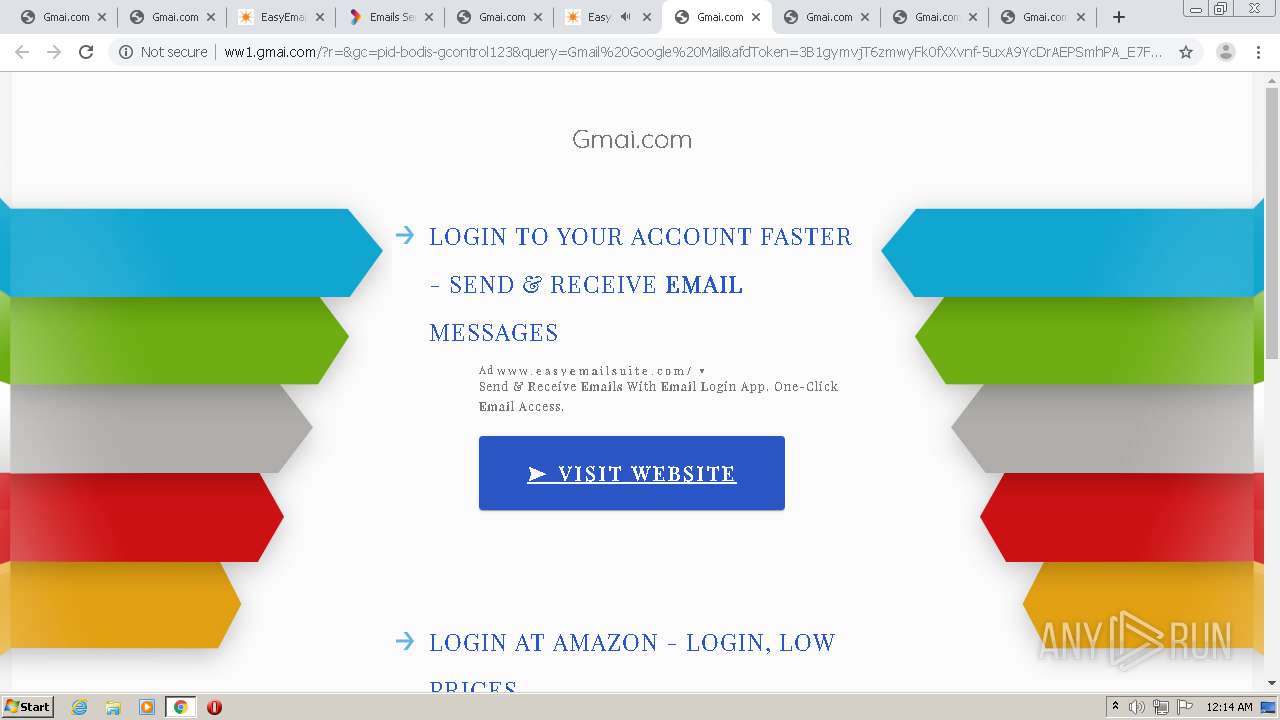
| URL: | http://ww1.gmai.com |
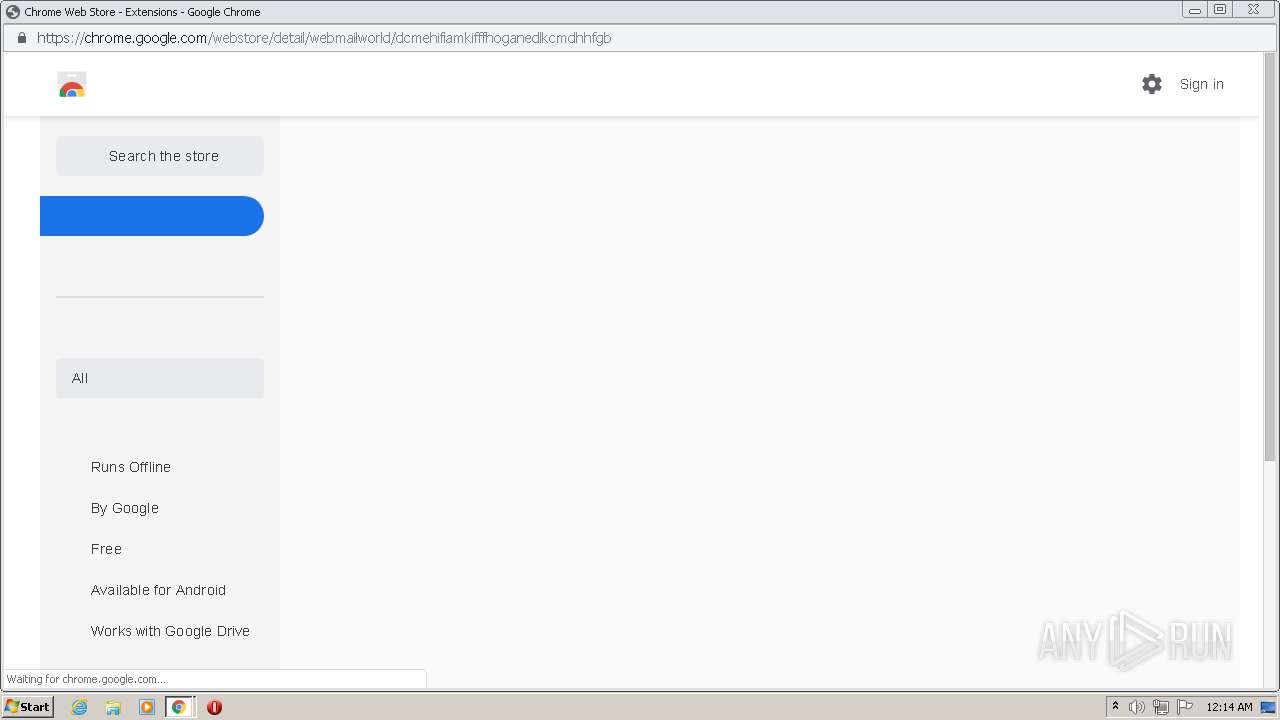
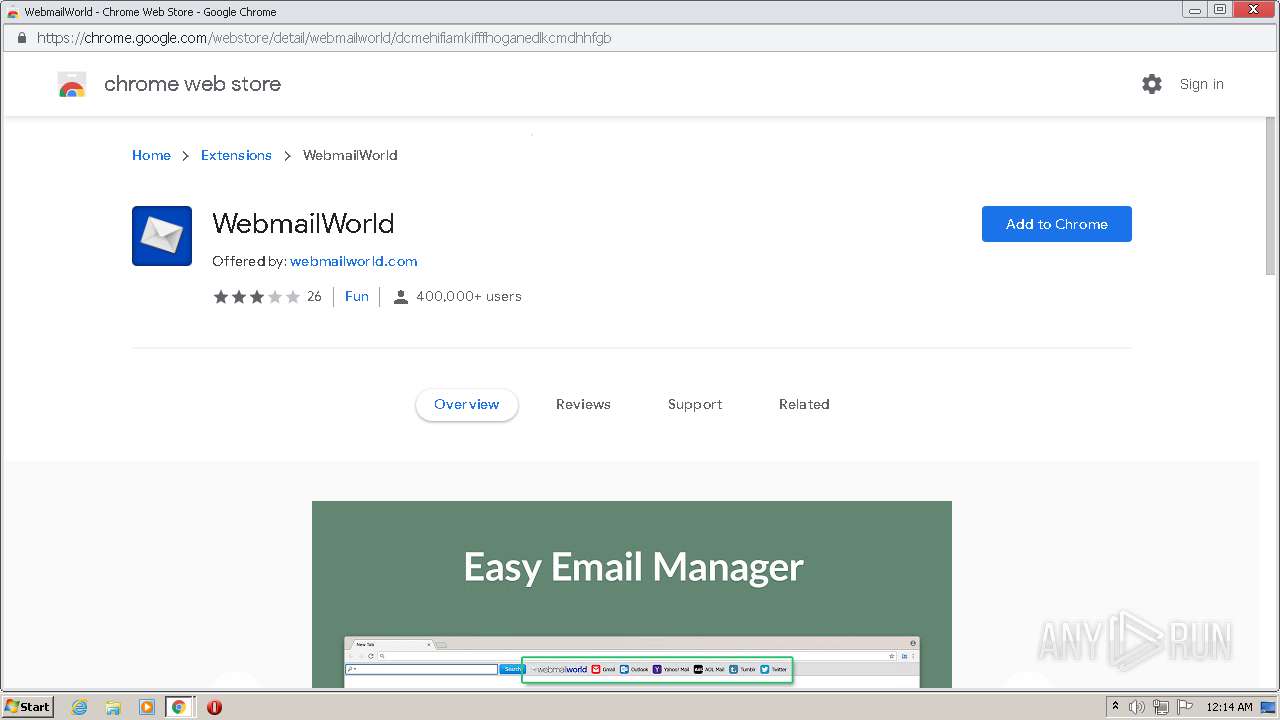
| Full analysis: | https://app.any.run/tasks/4924a888-0e49-43f0-ac98-bba0b020fba6 |
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2020, 23:13:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AA54C4B955E5FA05546978F9E4E4E5A4 |
| SHA1: | 15E9DD44E5163607B76FCBAE10CC5F210C629AA5 |
| SHA256: | FF3AB79CE06BD280FF11EEB0D9FE88403ED6AAF18712D61CE9C9C6206C13899B |
| SSDEEP: | 3:N1KJSx+In:Ccx3n |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2564)
- chrome.exe (PID: 576)
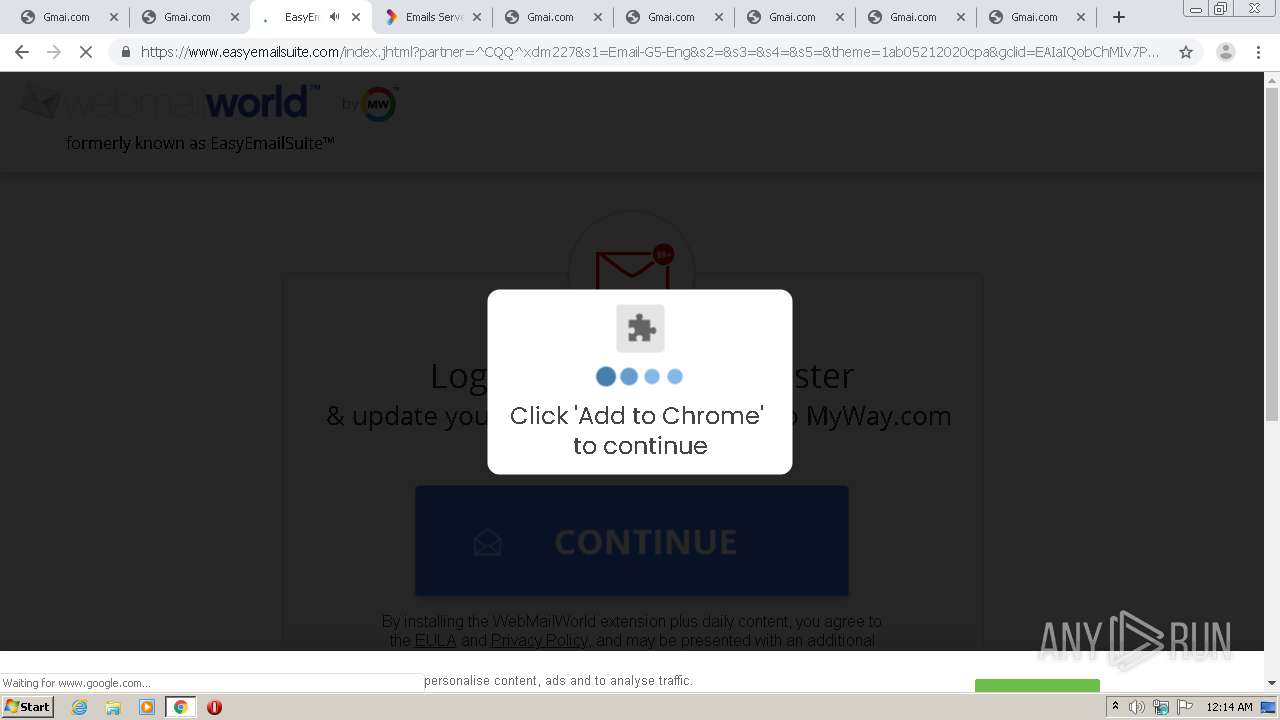
Application launched itself
- chrome.exe (PID: 2564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
31
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13303407557918279023,16310817576681642504,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16939045572303061841 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2524 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13303407557918279023,16310817576681642504,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=1046220816062201582 --mojo-platform-channel-handle=1560 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13303407557918279023,16310817576681642504,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15866187392920711742 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4920 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13303407557918279023,16310817576681642504,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11912398015596602757 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13303407557918279023,16310817576681642504,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7577538886508564727 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2204 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13303407557918279023,16310817576681642504,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15971327776609877969 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4816 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13303407557918279023,16310817576681642504,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=12926330321861838758 --mojo-platform-channel-handle=5244 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13303407557918279023,16310817576681642504,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17872848736691634087 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4016 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13303407557918279023,16310817576681642504,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4632162925442444056 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4820 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2724 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
677
Read events
567
Write events
106
Delete events
4
Modification events
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2564-13247622815841750 |
Value: 259 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
70
Text files
89
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8E1DA0-A04.pma | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e7b1873f-5281-416a-9e6a-9e0ced8ec471.tmp | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2d41f0.TMP | text | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF2d41f0.TMP | text | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF2d422e.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
82
DNS requests
53
Threats
61
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
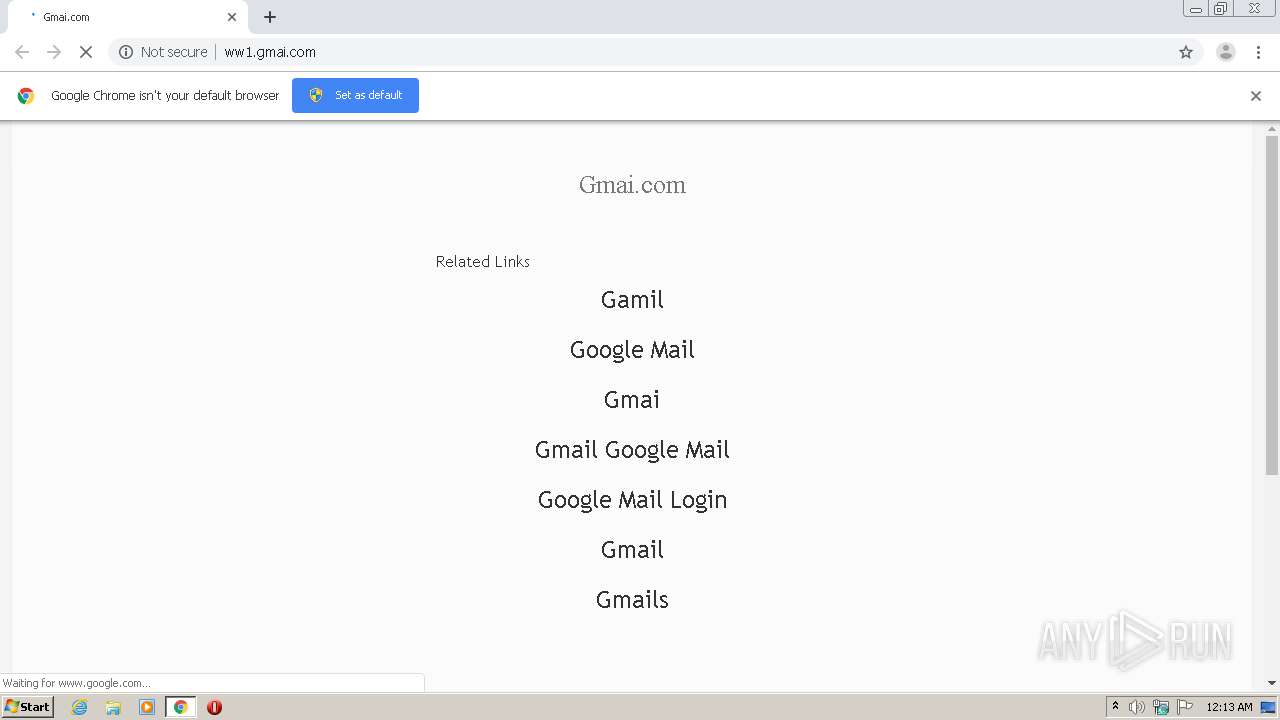
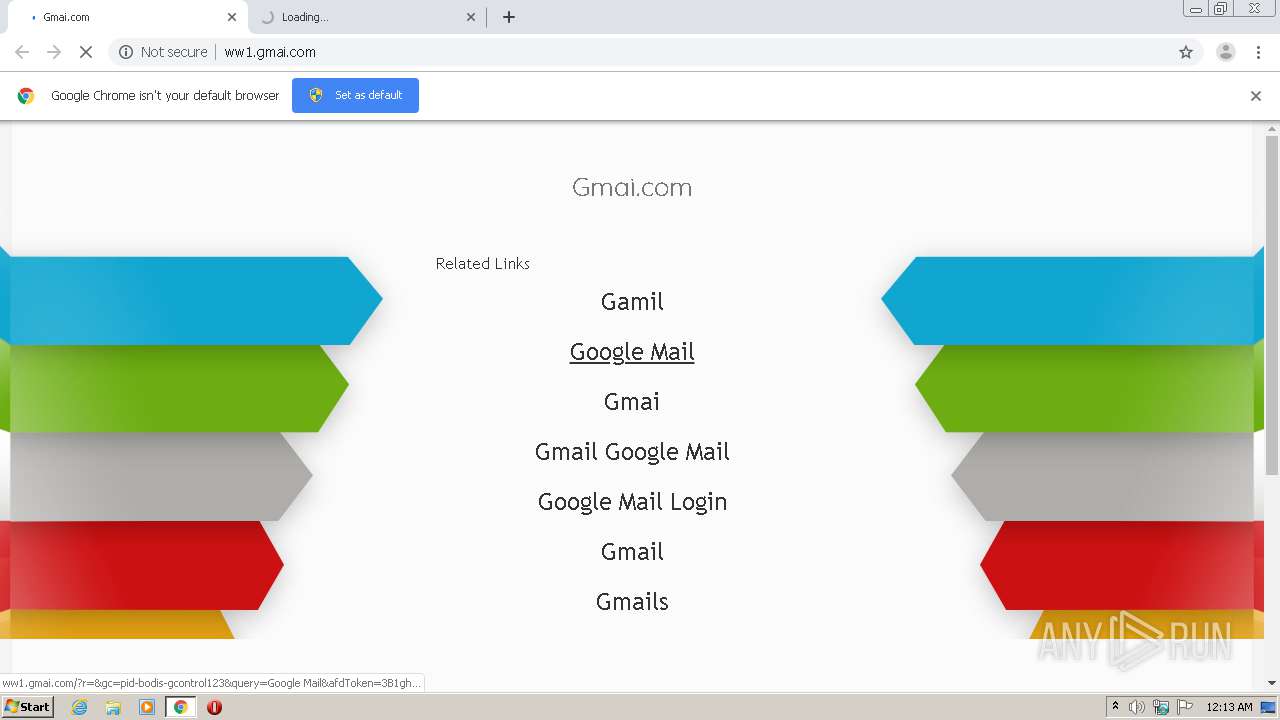
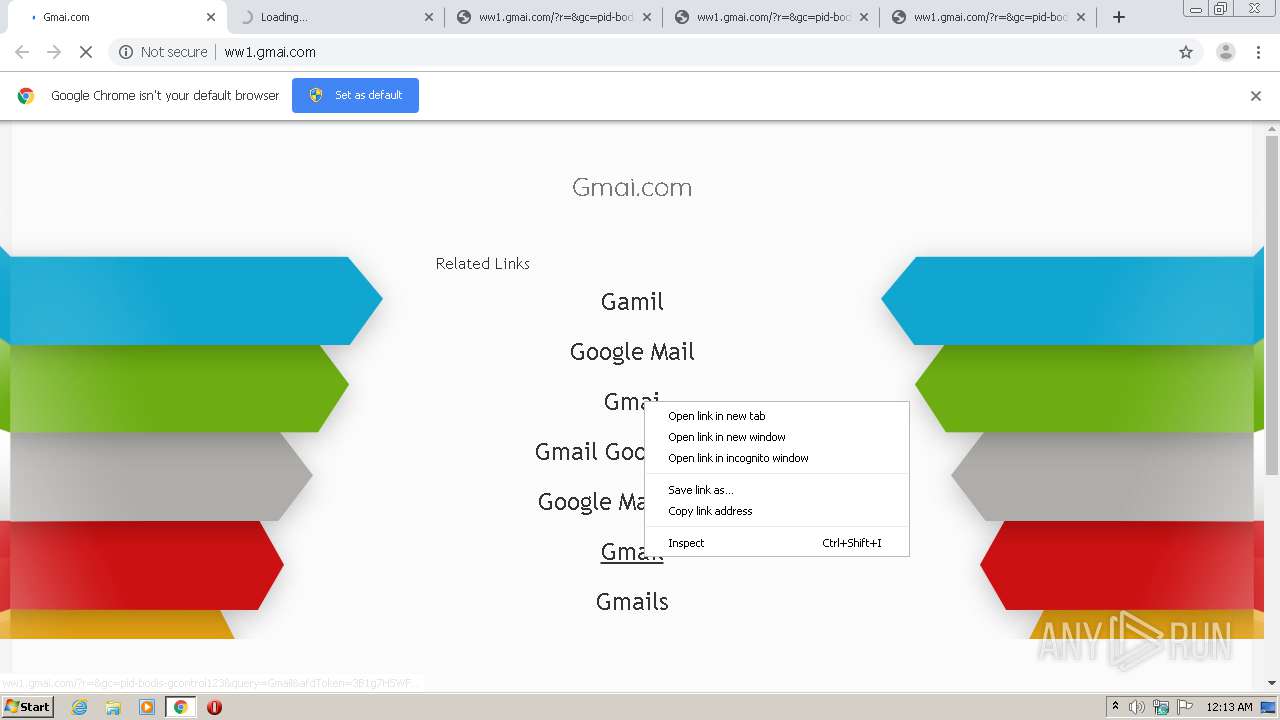
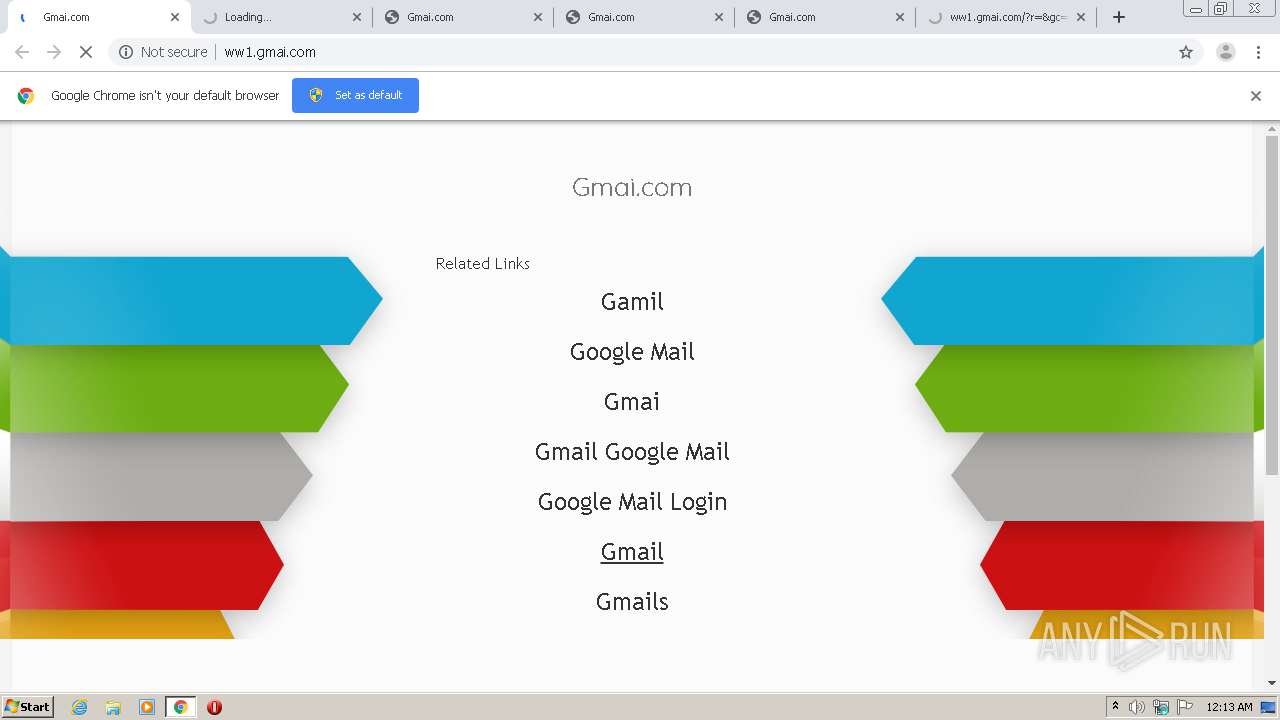
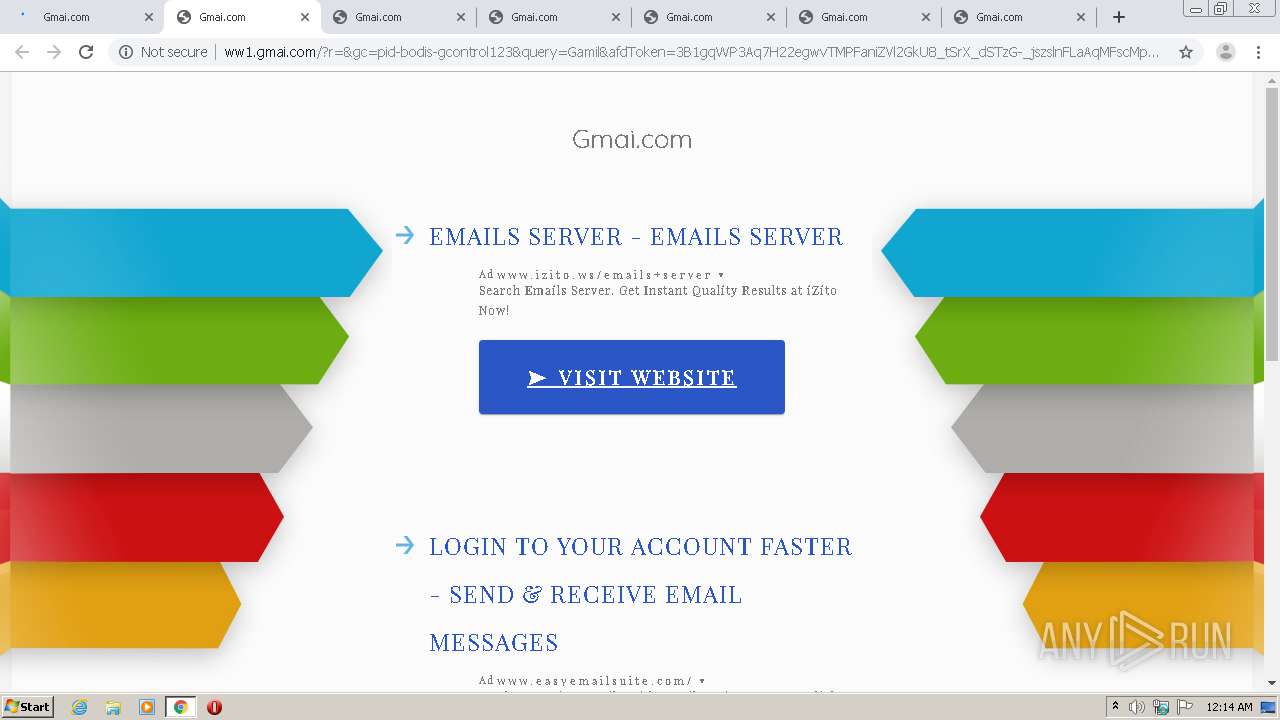
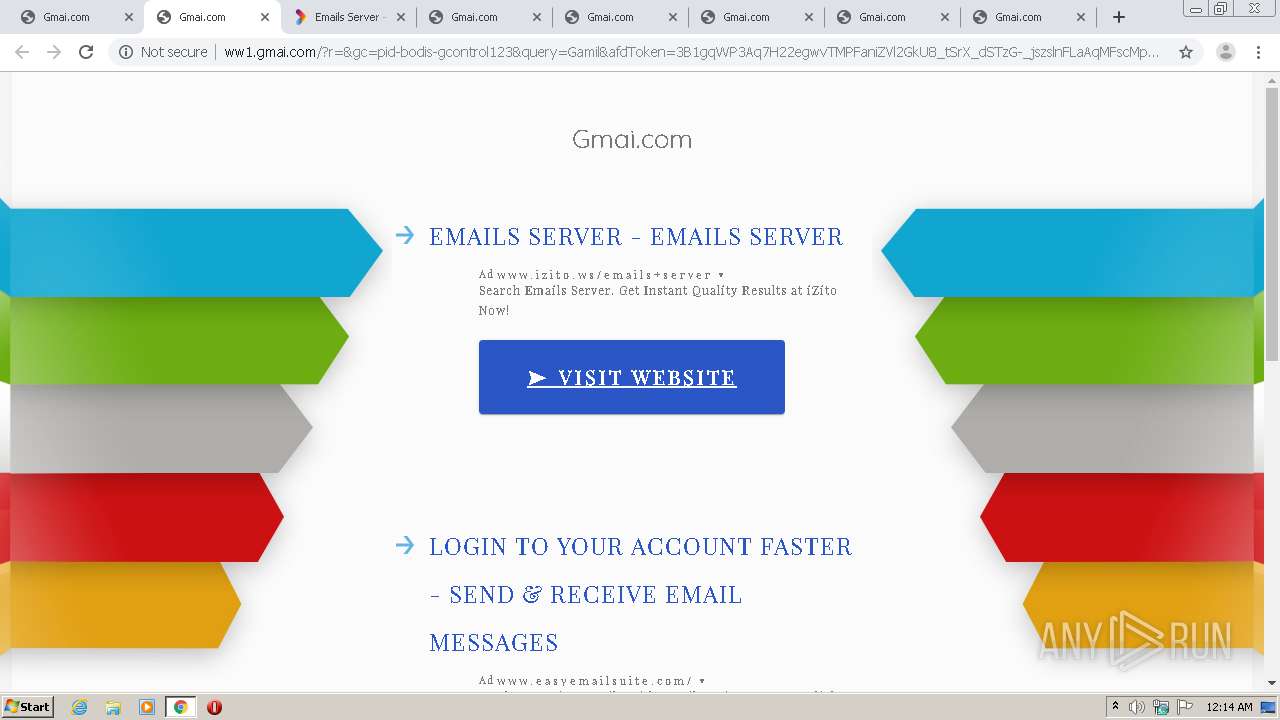
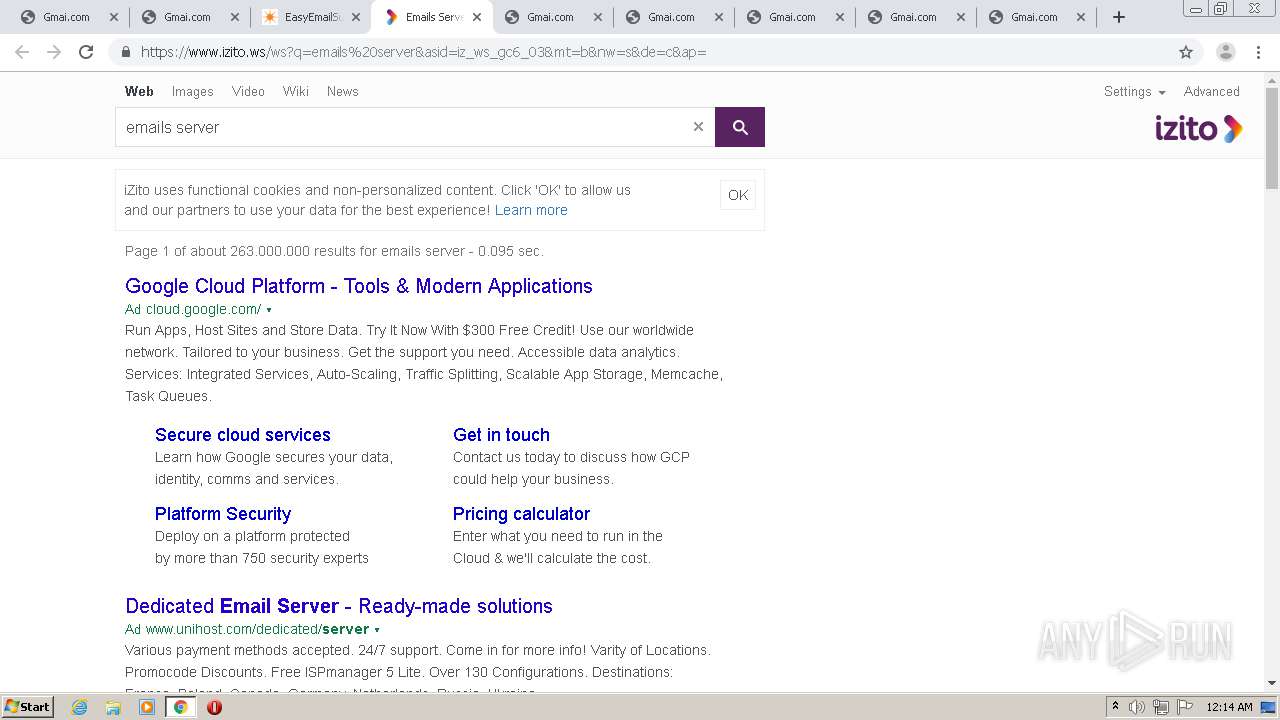
576 | chrome.exe | GET | — | 199.59.242.153:80 | http://ww1.gmai.com/?r=&gc=pid-bodis-gcontrol123&query=Gamil&afdToken=3B1gqWP3Aq7H22egwvTMPFaniZVl2GkU8_tSrX_dSTzG-_jszslnFLaAqMFscMp8Y3J9oFn2XhmWvrsMycgc6ju1_tZAUPaZFIAR3RLFETWCVQM | US | — | — | malicious |
576 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww1.gmai.com/ | US | html | 3.99 Kb | malicious |
576 | chrome.exe | GET | 404 | 199.59.242.153:80 | http://ww1.gmai.com/favicon.ico | US | html | 3.99 Kb | malicious |
576 | chrome.exe | GET | 404 | 199.59.242.153:80 | http://ww1.gmai.com/favicon.ico | US | html | 3.99 Kb | malicious |
576 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww1.gmai.com/glp?r=&u=http%3A%2F%2Fww1.gmai.com%2F&gc=pid-bodis-gcontrol123&sq=Gmail%20Google%20Mail&rw=1280&rh=720&ww=1280&wh=572 | US | text | 9.83 Kb | malicious |
576 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww1.gmai.com/?r=&gc=pid-bodis-gcontrol123&query=Google%20Mail%20Login&afdToken=3B1gsmHhBurYiy2kwvTMPFaniZVl2GkU8_tSrX_dSTzG-_jszslnFLaAqMFscMp8Y3J9oFn2XhmWvrsMycgc6ju1_o8LRfGpRJ45_hLFFTWCVQM | US | html | 3.99 Kb | malicious |
576 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww1.gmai.com/?r=&gc=pid-bodis-gcontrol123&query=Gmail%20Google%20Mail&afdToken=3B1gymvjT6zmwyFk0fXXvnf-5uxA9YcDrAEPSmhPA_E7FPH3TOg-e8-lhS97LzAhhGXv6pQLg6i0nLVN0apBXEyCz3J0RpfpJL1Mtd2EUGnaNWLY | US | html | 3.99 Kb | malicious |
576 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww1.gmai.com/?r=&gc=pid-bodis-gcontrol123&query=Google%20Mail&afdToken=3B1ghFfdJN6Ht3X0wvTMPFaniZVl2GkU8_tSrX_dSTzG-_jszslnFLaAqMFscMp8Y3J9oFn2XhmWvrsMycgc6ju1_sQRM-WSd-MLhhLFEjWCVQM | US | html | 3.99 Kb | malicious |
576 | chrome.exe | GET | — | 199.59.242.153:80 | http://ww1.gmai.com/public/legacy/10353/resources/arrows-bg.jpg | US | — | — | malicious |
576 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww1.gmai.com/px.gif?ch=2&rn=10.095485617957765 | US | image | 42 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
576 | chrome.exe | 199.59.242.153:80 | ww1.gmai.com | Bodis, LLC | US | malicious |
576 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
576 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
576 | chrome.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
576 | chrome.exe | 216.58.208.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
576 | chrome.exe | 142.250.74.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
576 | chrome.exe | 199.59.242.155:443 | tracking.bodis.com | Bodis, LLC | US | suspicious |
576 | chrome.exe | 172.217.22.33:443 | afs.googleusercontent.com | Google Inc. | US | whitelisted |
576 | chrome.exe | 172.217.16.130:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
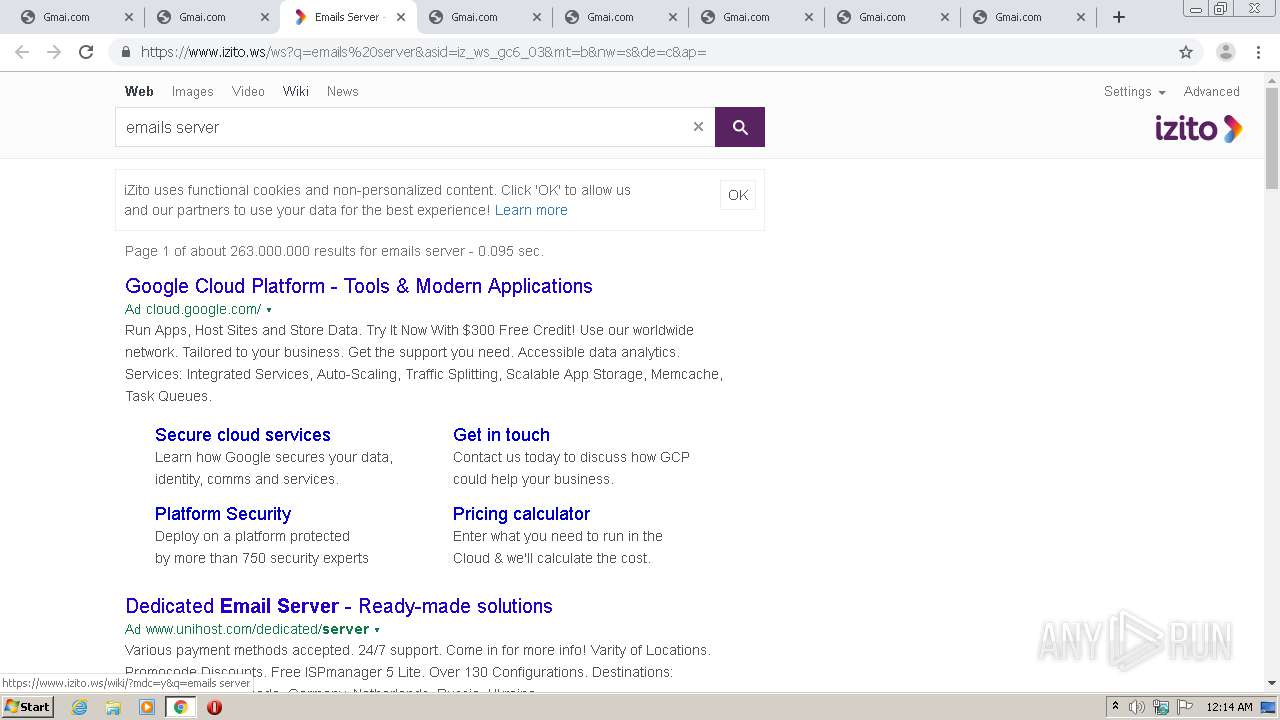
576 | chrome.exe | 212.100.243.81:443 | www.izito.ws | Rackspace Ltd. | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ww1.gmai.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
tracking.bodis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
afs.googleusercontent.com |
| whitelisted |
www.googleadservices.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
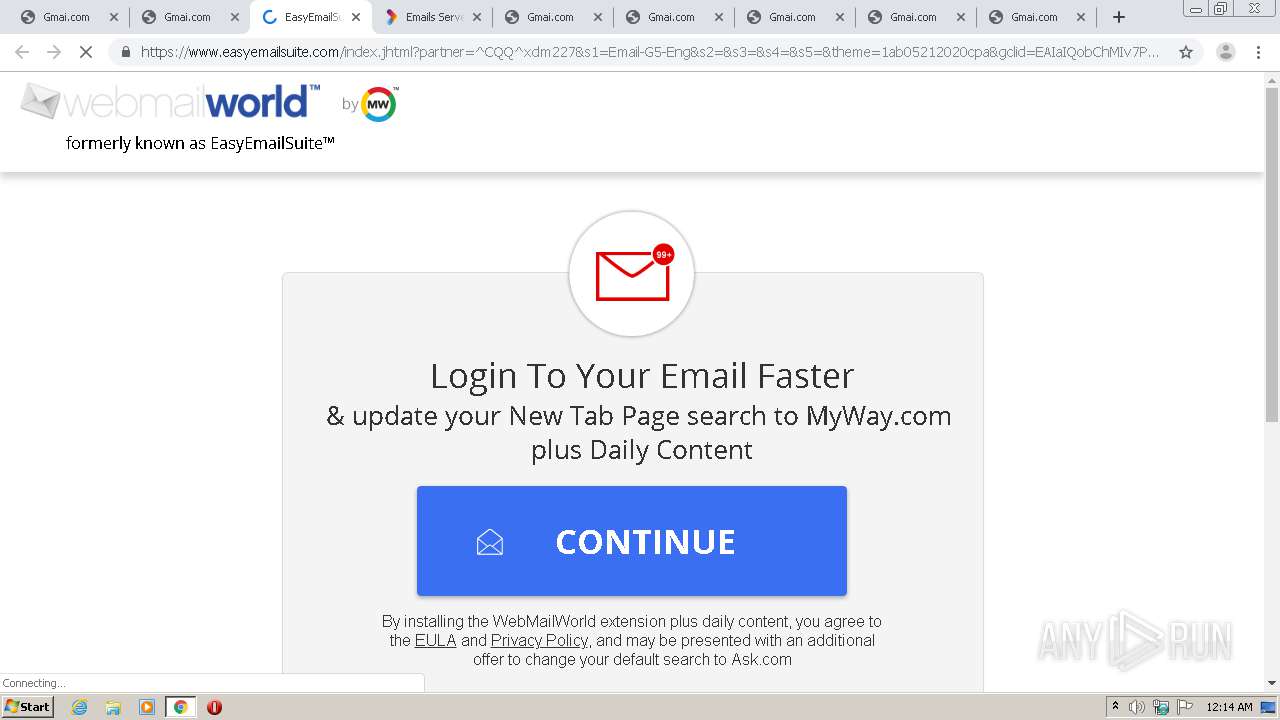
576 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |
576 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |
576 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |
576 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |
576 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |
576 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |
576 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |
576 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |