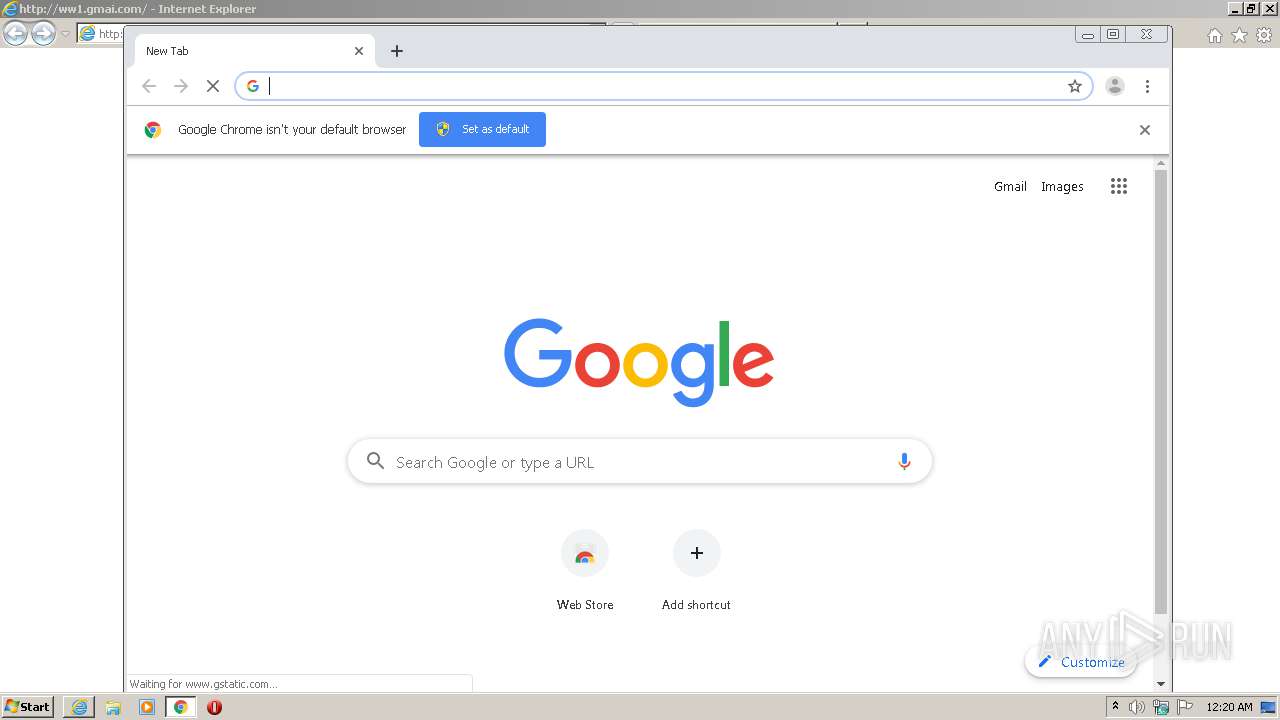
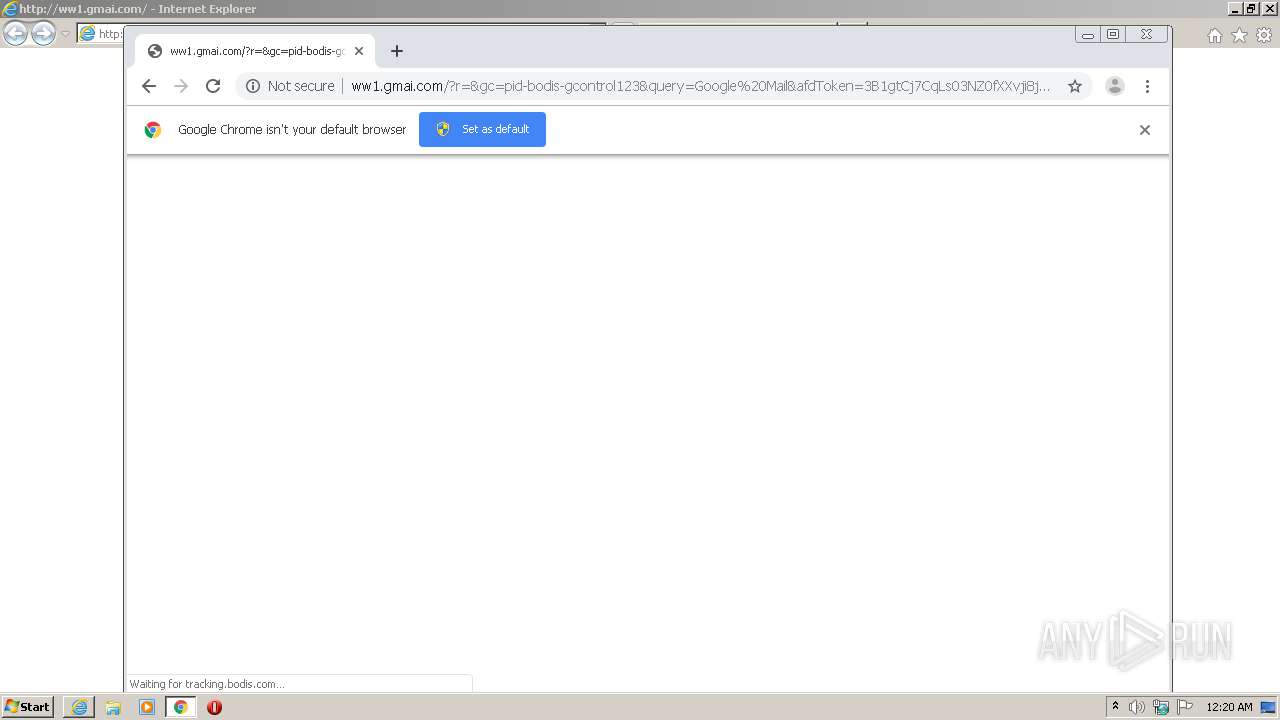
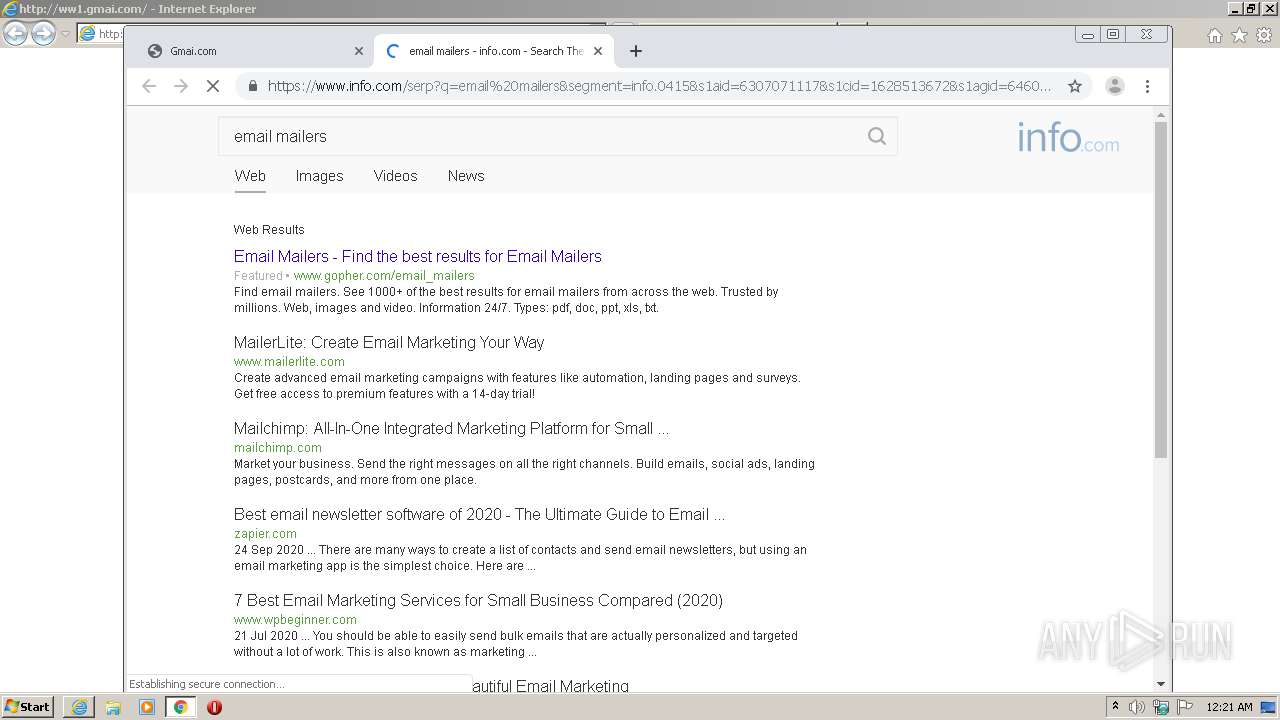
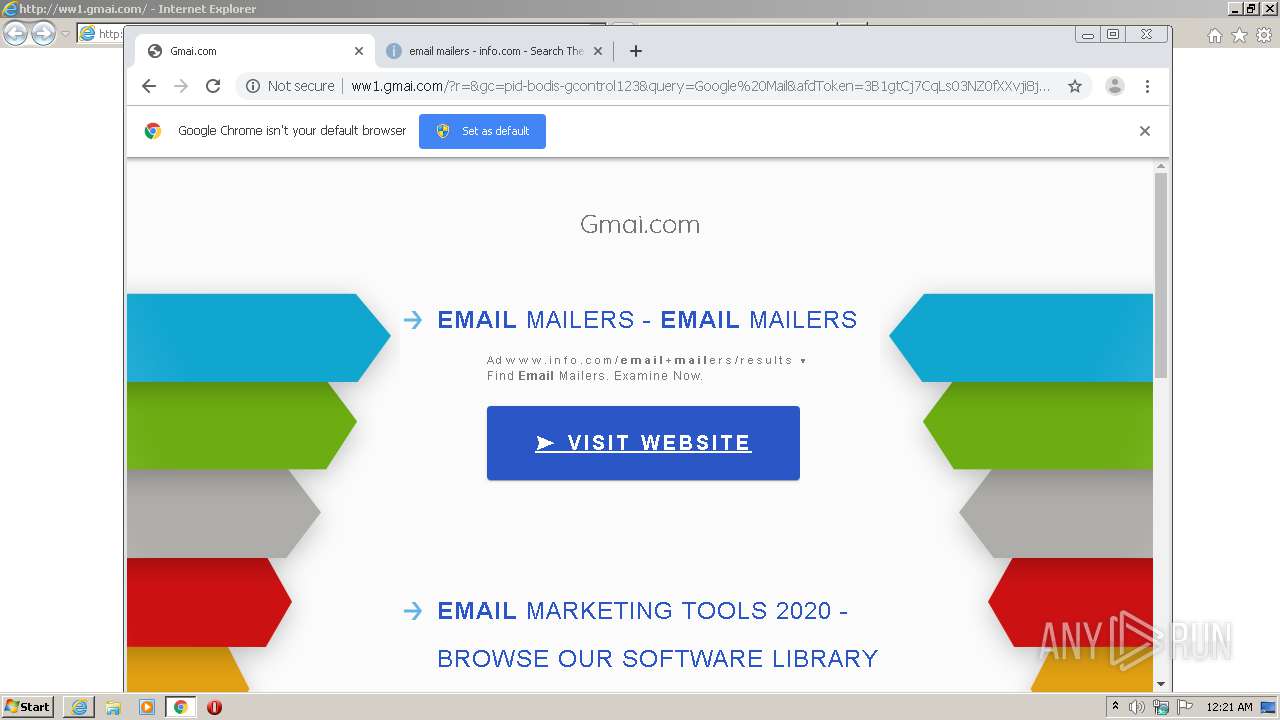
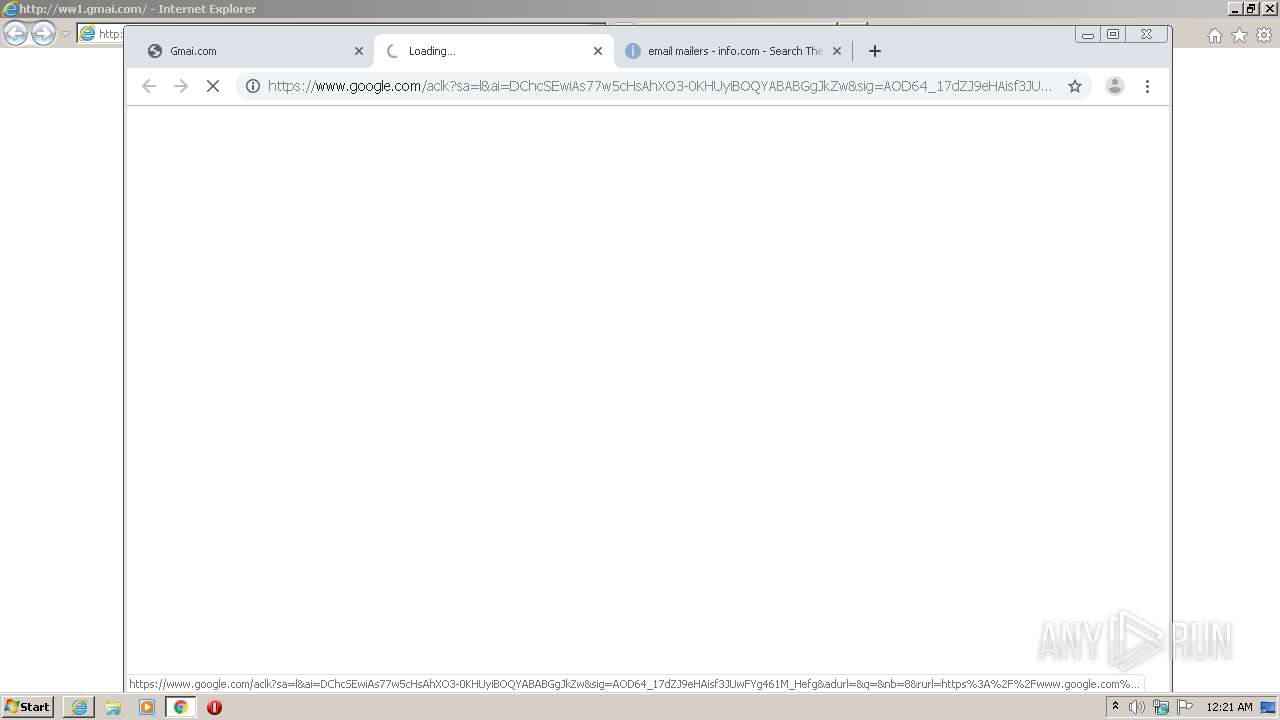
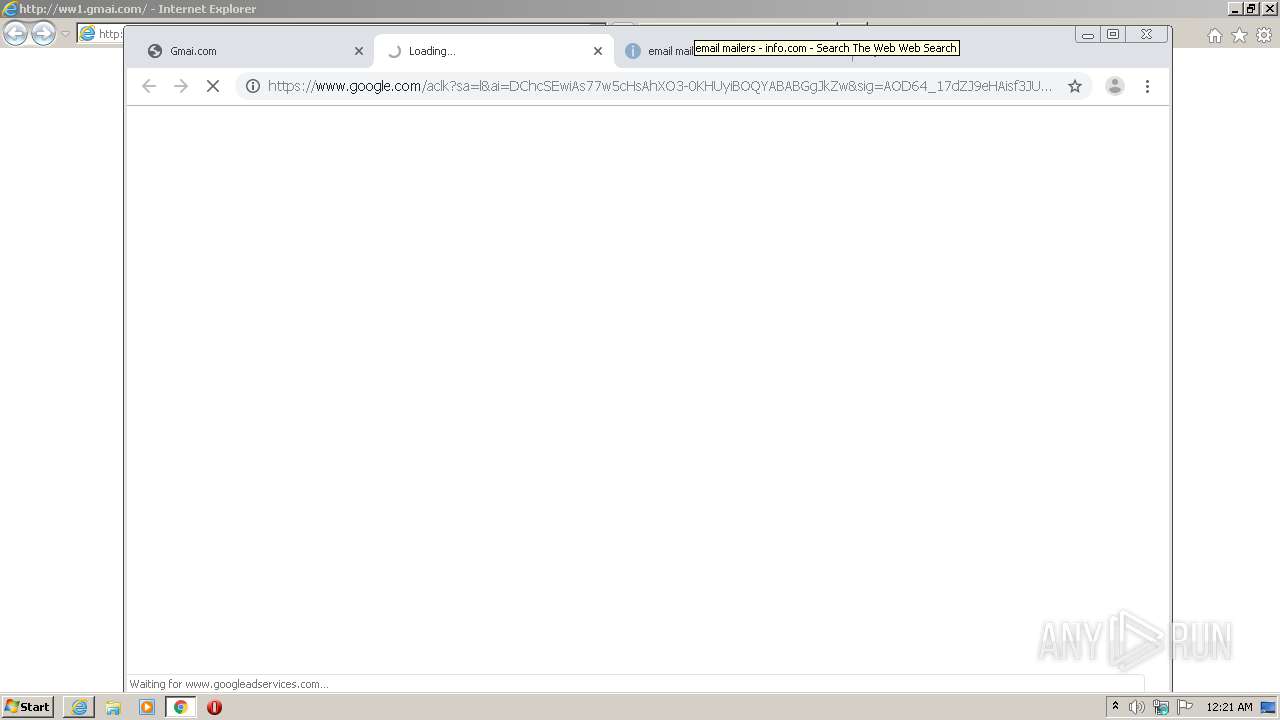
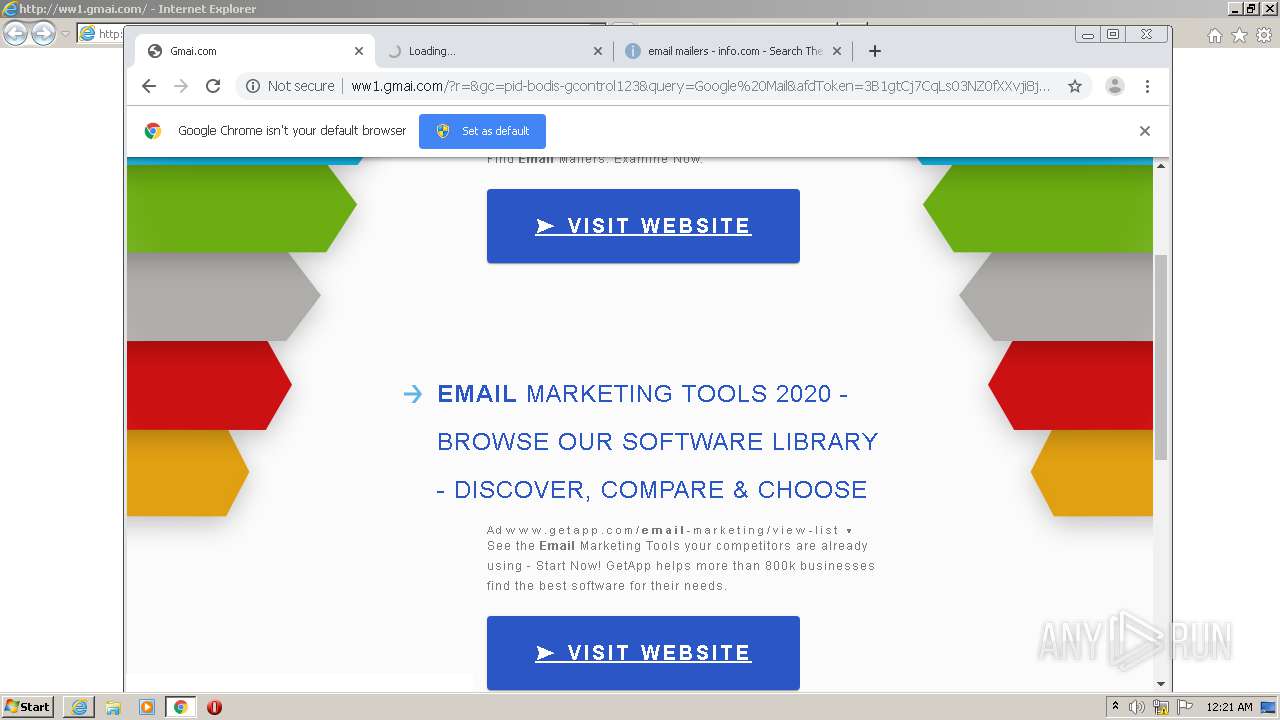
| URL: | http://ww1.gmai.com |
| Full analysis: | https://app.any.run/tasks/3f96ca74-5158-49a5-a5c2-a79e0d434678 |
| Verdict: | Malicious activity |
| Analysis date: | October 19, 2020, 23:20:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AA54C4B955E5FA05546978F9E4E4E5A4 |
| SHA1: | 15E9DD44E5163607B76FCBAE10CC5F210C629AA5 |
| SHA256: | FF3AB79CE06BD280FF11EEB0D9FE88403ED6AAF18712D61CE9C9C6206C13899B |
| SSDEEP: | 3:N1KJSx+In:Ccx3n |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
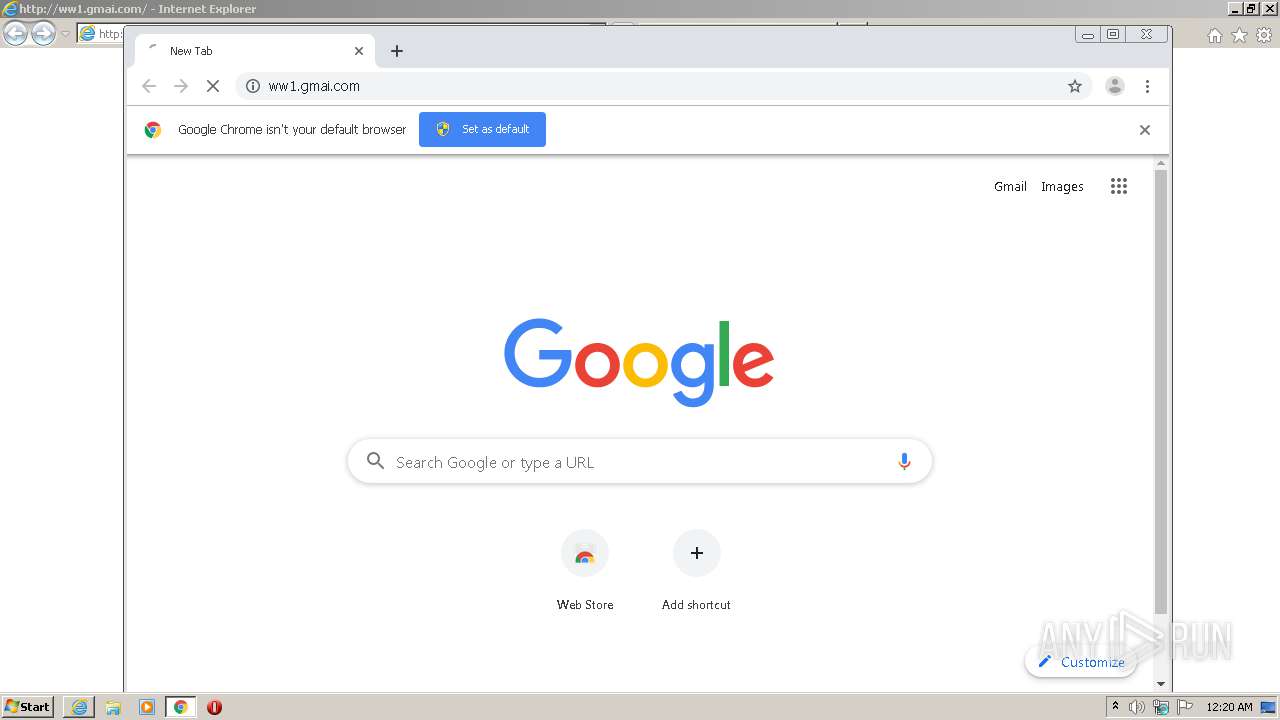
Reads Internet Cache Settings
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 3060)
Application launched itself
- chrome.exe (PID: 3316)
- iexplore.exe (PID: 3060)
Reads internet explorer settings
- iexplore.exe (PID: 2748)
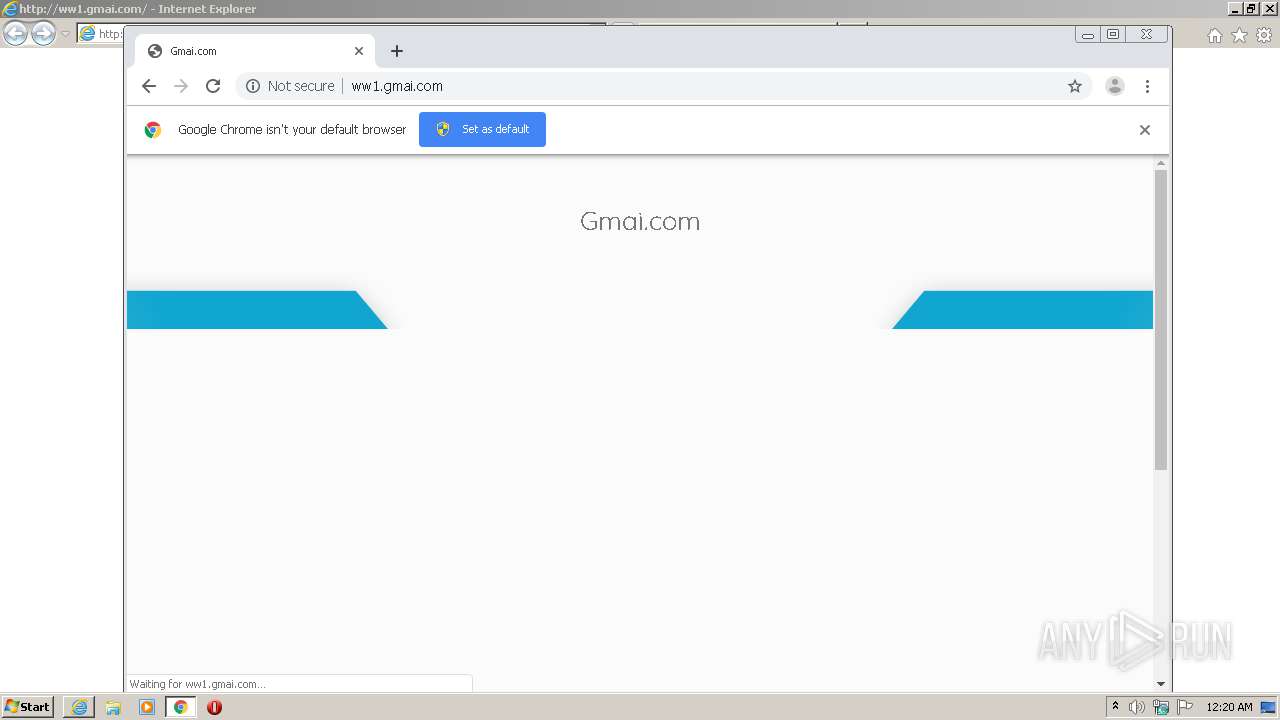
Reads the hosts file
- chrome.exe (PID: 3316)
- chrome.exe (PID: 3348)
Changes settings of System certificates
- iexplore.exe (PID: 3060)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3060)
Manual execution by user
- chrome.exe (PID: 3316)
Reads settings of System Certificates
- chrome.exe (PID: 3348)
- iexplore.exe (PID: 3060)
Changes internet zones settings
- iexplore.exe (PID: 3060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
21
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,4577580729768062482,7278160804838050602,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=10659118843286829300 --mojo-platform-channel-handle=3856 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,4577580729768062482,7278160804838050602,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5340957012920937911 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f06a9d0,0x6f06a9e0,0x6f06a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,4577580729768062482,7278160804838050602,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8846703599629284326 --mojo-platform-channel-handle=3416 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,4577580729768062482,7278160804838050602,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3576839093207718458 --mojo-platform-channel-handle=3388 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,4577580729768062482,7278160804838050602,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16243644701867668077 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3060 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,4577580729768062482,7278160804838050602,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=234506343202875660 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3660 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3060 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://ww1.gmai.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,4577580729768062482,7278160804838050602,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6991775531199684464 --mojo-platform-channel-handle=1064 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
949
Read events
768
Write events
175
Delete events
6
Modification events
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2197149554 | |||
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30844526 | |||
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
47
Text files
79
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3060 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8E1F55-CF4.pma | — | |
MD5:— | SHA256:— | |||
| 2748 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\EO739WQY.htm | html | |
MD5:— | SHA256:— | |||
| 2748 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
| 2748 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\N9ZOJ63I.htm | html | |
MD5:— | SHA256:— | |||
| 3316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3ff5036e-cb29-4d7a-8c66-e1a27a7ddfd2.tmp | — | |
MD5:— | SHA256:— | |||
| 3316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169f42.TMP | text | |
MD5:— | SHA256:— | |||
| 3316 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169f61.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
50
DNS requests
33
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
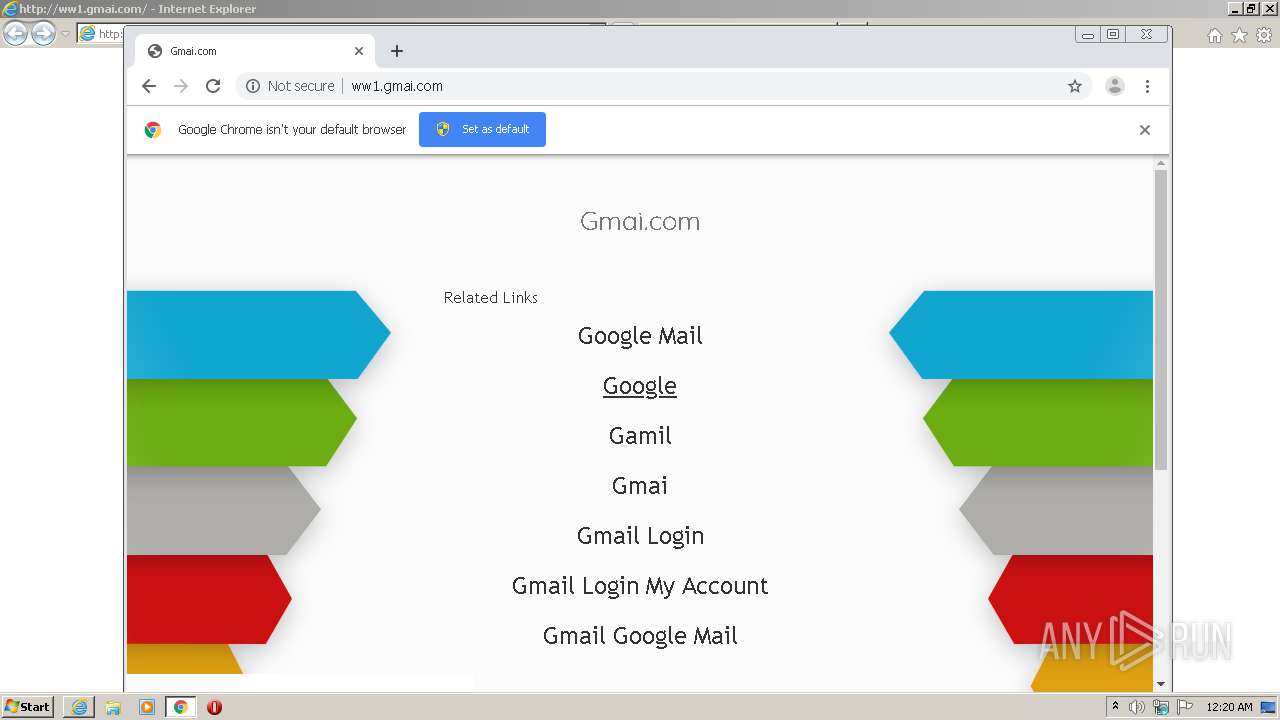
3060 | iexplore.exe | GET | — | 199.59.242.153:80 | http://ww1.gmai.com/favicon.ico | US | — | — | malicious |
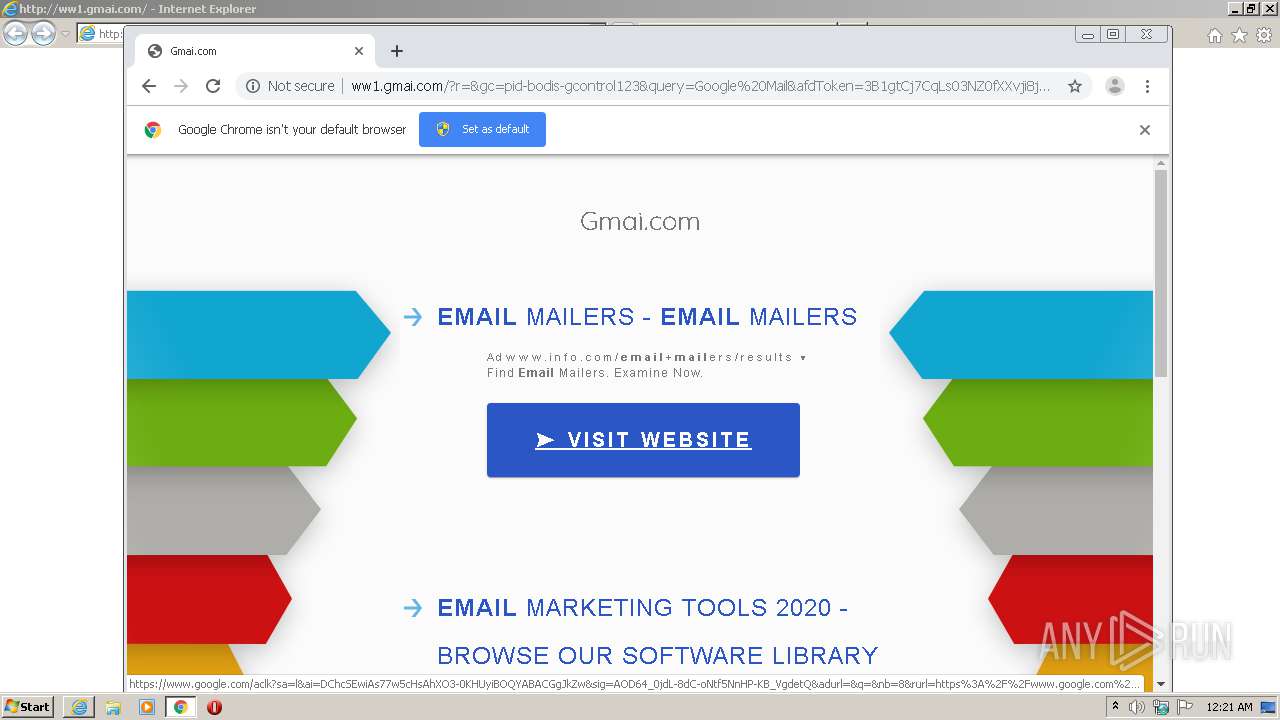
3348 | chrome.exe | GET | 200 | 199.59.242.155:80 | http://tracking.bodis.com/tlpv?d=eyJkb21haW5fbmFtZSI6ImdtYWkuY29tIiwic2VydmVyIjo5MSwidGVybXMiOltdLCJVUkwiOiJodHRwOlwvXC93dzEuZ21haS5jb21cLyIsInJlZmVycmVyIjoiIiwiZHciOjEwNDIsImRoIjo1MzksInJ3IjoxMjgwLCJyaCI6NzIwfQ&t=1603149657&abp=0 | US | — | — | whitelisted |
2748 | iexplore.exe | GET | 200 | 199.59.242.153:80 | http://ww1.gmai.com/ | US | html | 3.99 Kb | malicious |
2748 | iexplore.exe | GET | 200 | 199.59.242.153:80 | http://ww1.gmai.com/ | US | html | 3.99 Kb | malicious |
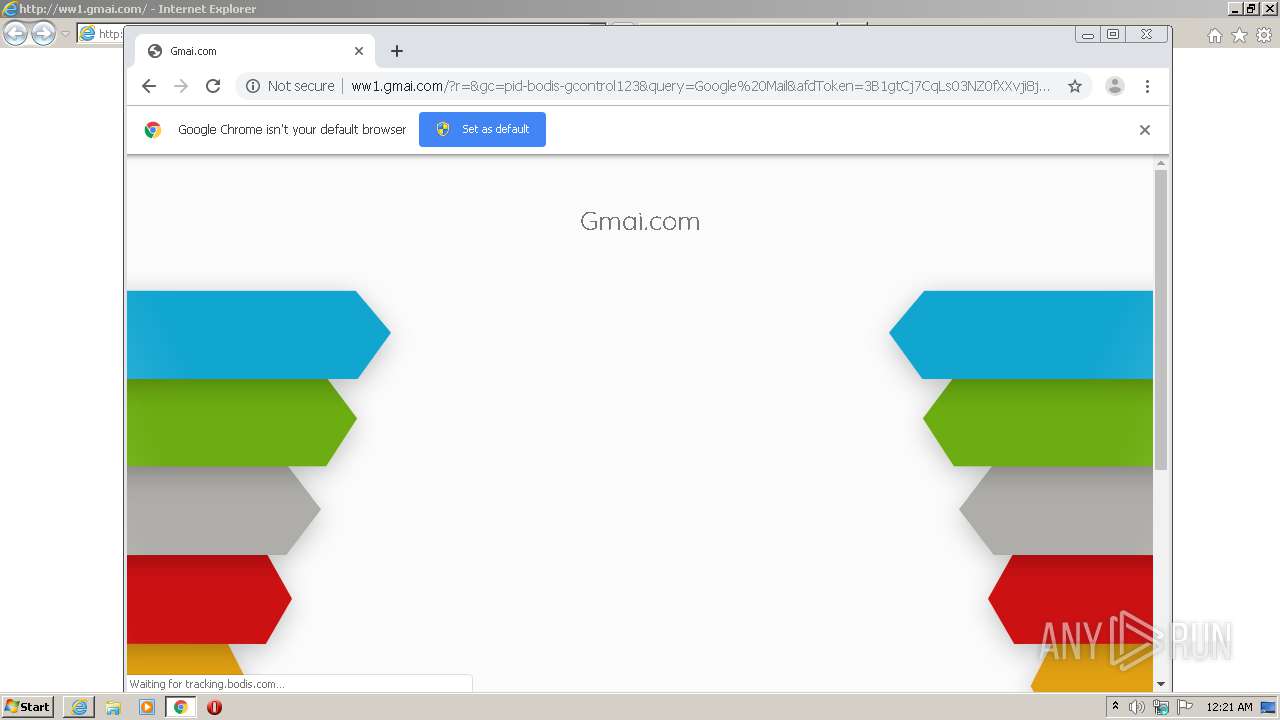
3348 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww1.gmai.com/public/legacy/10353/resources/arrows-bg-ext.png | US | image | 1.12 Kb | malicious |
3348 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww1.gmai.com/?r=&gc=pid-bodis-gcontrol123&query=Google%20Mail&afdToken=3B1gtCj7CqLs03NZ0fXXvji8jZ5B9YcDrAo_92RPVck_zvH3TKd8EL2khS97LzsROWnvvKwPWai0nLVN0apBXEyCwXJfBdeHXJZOse6EUGzaNWLY | US | html | 3.99 Kb | malicious |
3348 | chrome.exe | GET | 200 | 199.59.242.153:80 | http://ww1.gmai.com/ | US | html | 3.99 Kb | malicious |
2748 | iexplore.exe | GET | 200 | 199.59.242.153:80 | http://ww1.gmai.com/px.gif?ch=1&rn=9.233160316297585 | US | image | 42 b | malicious |
2748 | iexplore.exe | GET | 200 | 199.59.242.153:80 | http://ww1.gmai.com/px.gif?ch=1&rn=6.156837064270679 | US | image | 42 b | malicious |
3060 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2748 | iexplore.exe | 199.59.242.153:80 | ww1.gmai.com | Bodis, LLC | US | malicious |
3060 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
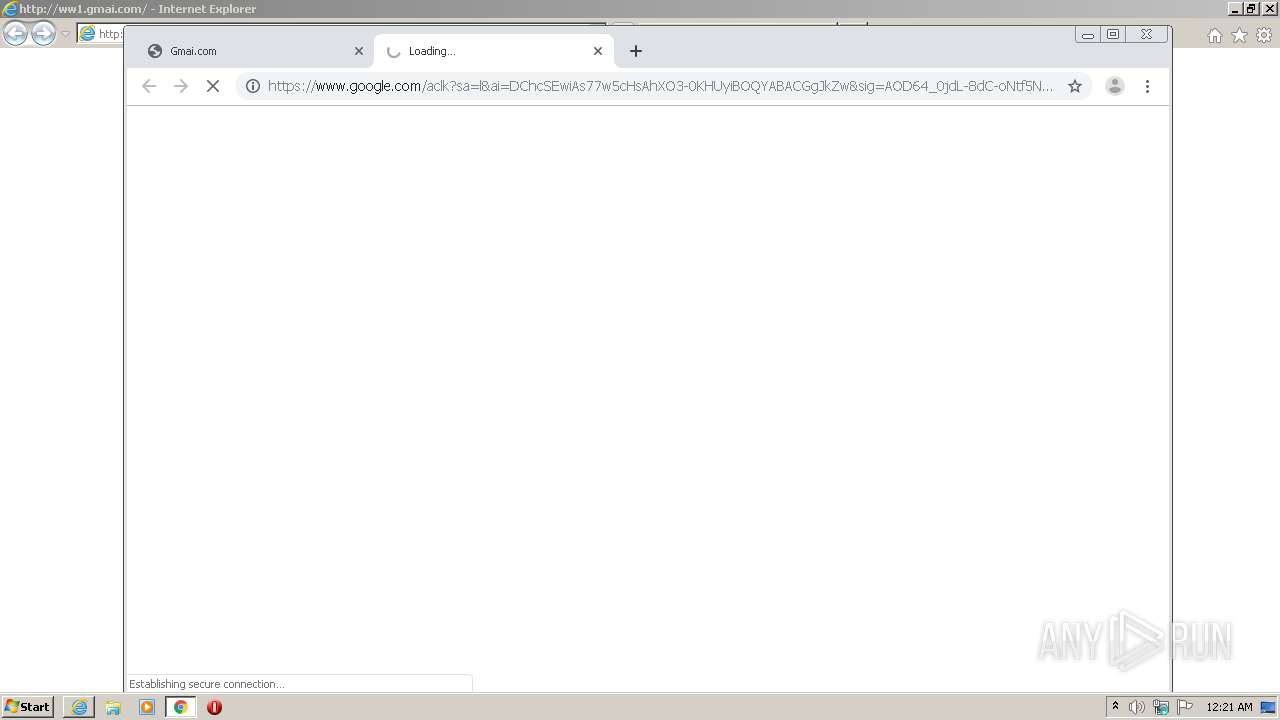
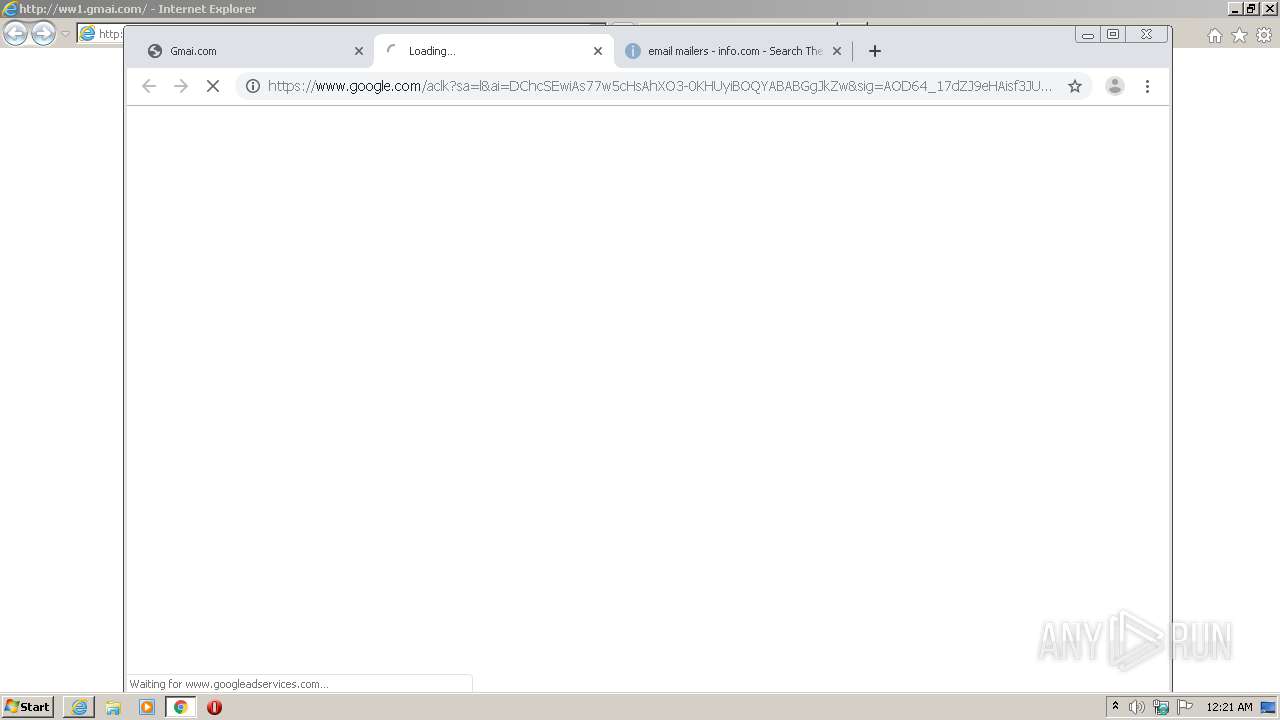
3348 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
3348 | chrome.exe | 216.58.207.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3348 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3348 | chrome.exe | 199.59.242.153:80 | ww1.gmai.com | Bodis, LLC | US | malicious |
3348 | chrome.exe | 172.217.22.78:443 | ogs.google.com | Google Inc. | US | whitelisted |
3348 | chrome.exe | 172.217.18.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
3348 | chrome.exe | 216.58.207.33:443 | afs.googleusercontent.com | Google Inc. | US | whitelisted |
3348 | chrome.exe | 199.59.242.155:443 | tracking.bodis.com | Bodis, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ww1.gmai.com |
| malicious |
www.google.com |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3348 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |
3348 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |