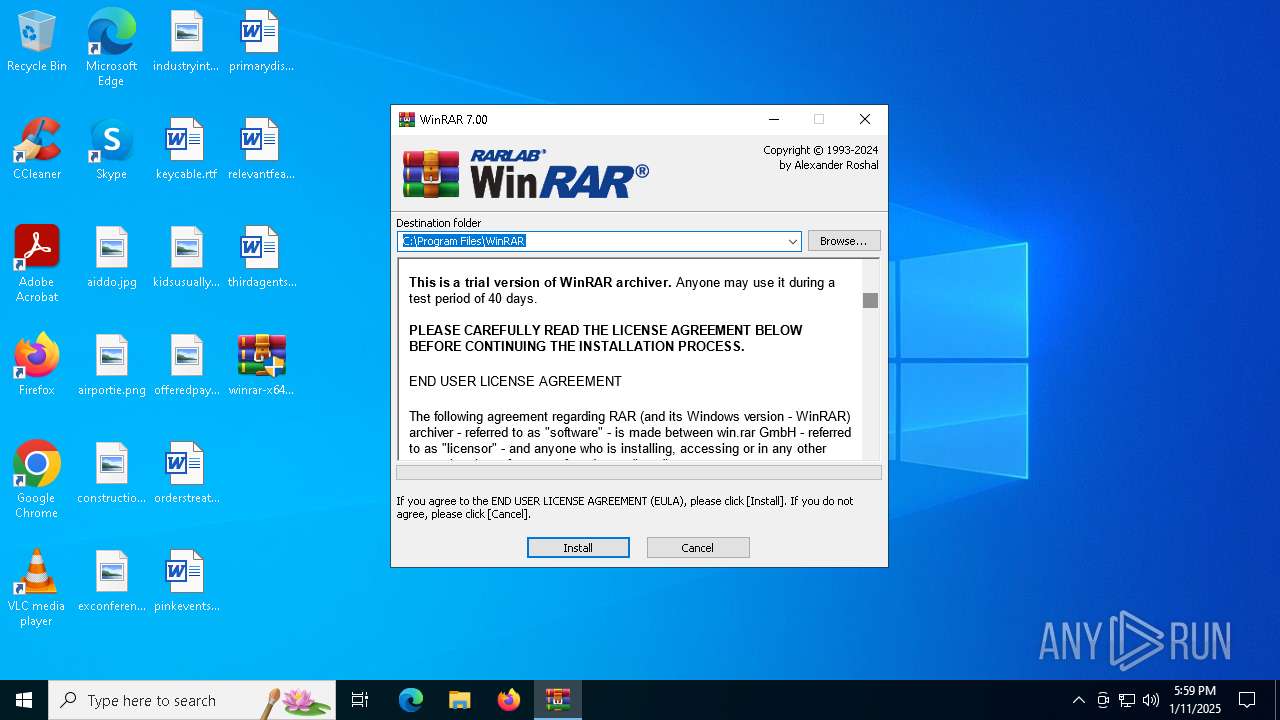
| File name: | winrar-x64-700.exe |
| Full analysis: | https://app.any.run/tasks/9a3eefd7-425e-4add-8d33-b644f7b41bc5 |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2025, 17:59:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 8 sections |
| MD5: | 48DEABFACB5C8E88B81C7165ED4E3B0B |
| SHA1: | DE3DAB0E9258F9FF3C93AB6738818C6EC399E6A4 |
| SHA256: | FF309D1430FC97FCCAA9CB82DDF3D23CE9AFDF62DCF8C69512DE40820DF15E24 |
| SSDEEP: | 98304:4dg3yw2pZkMJ5YWzIeKx+8gEgHjLzOcWlnExcE8zhL8V04bgR6w3gyEnfY1AY6mS:0QNVUyg |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- winrar-x64-700.exe (PID: 3812)
- Uninstall.exe (PID: 2324)
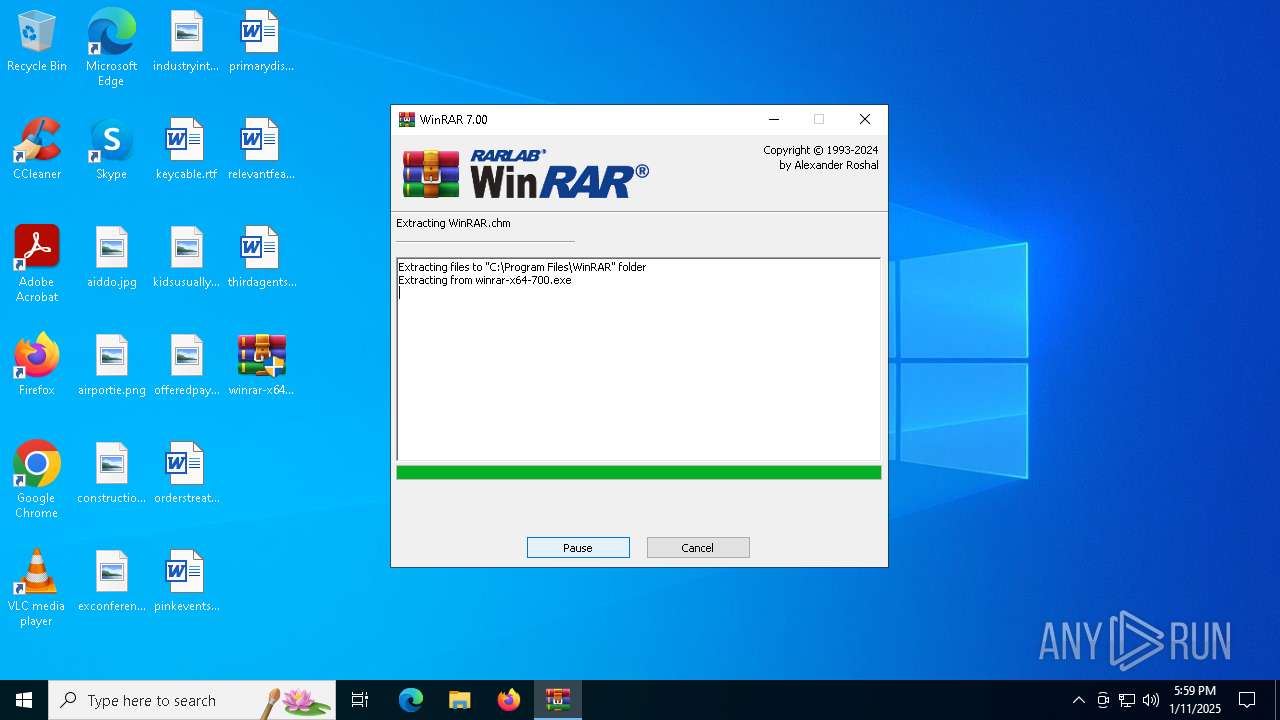
Executable content was dropped or overwritten
- winrar-x64-700.exe (PID: 3812)
Reads Microsoft Outlook installation path
- winrar-x64-700.exe (PID: 3812)
Reads the date of Windows installation
- winrar-x64-700.exe (PID: 3812)
- Uninstall.exe (PID: 2324)
Reads Internet Explorer settings
- winrar-x64-700.exe (PID: 3812)
Drops 7-zip archiver for unpacking
- winrar-x64-700.exe (PID: 3812)
Creates/Modifies COM task schedule object
- Uninstall.exe (PID: 2324)
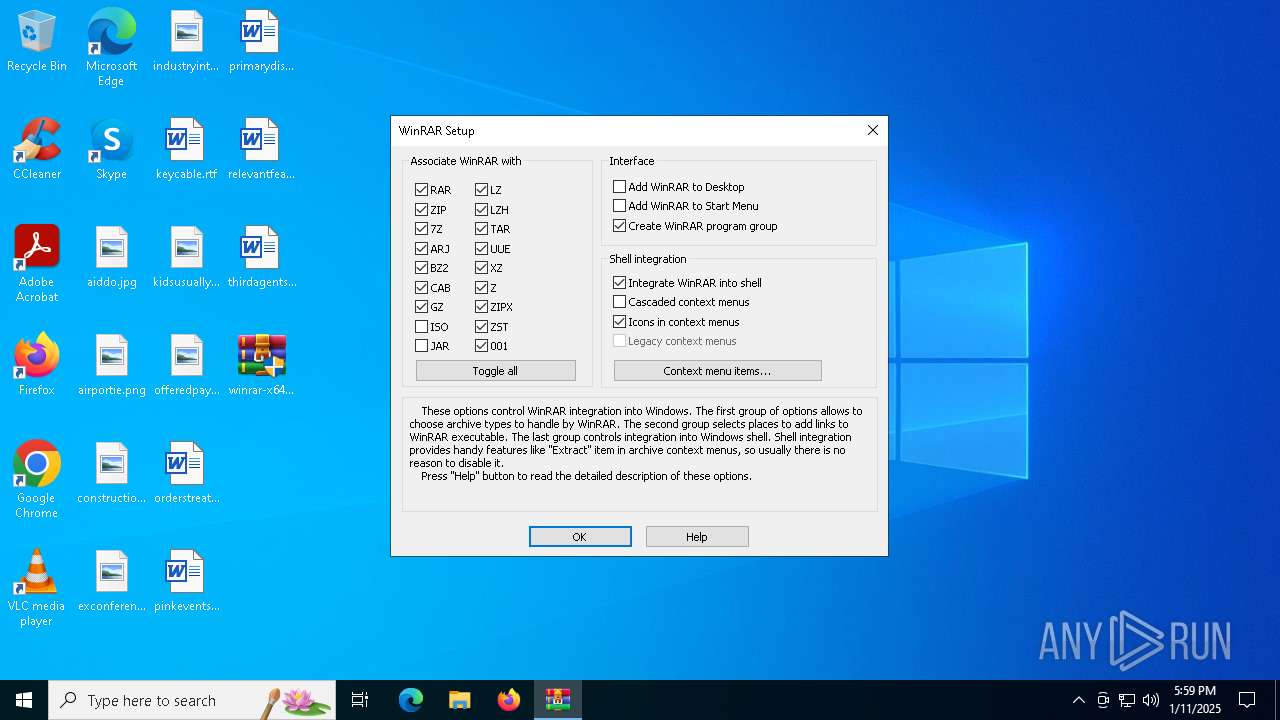
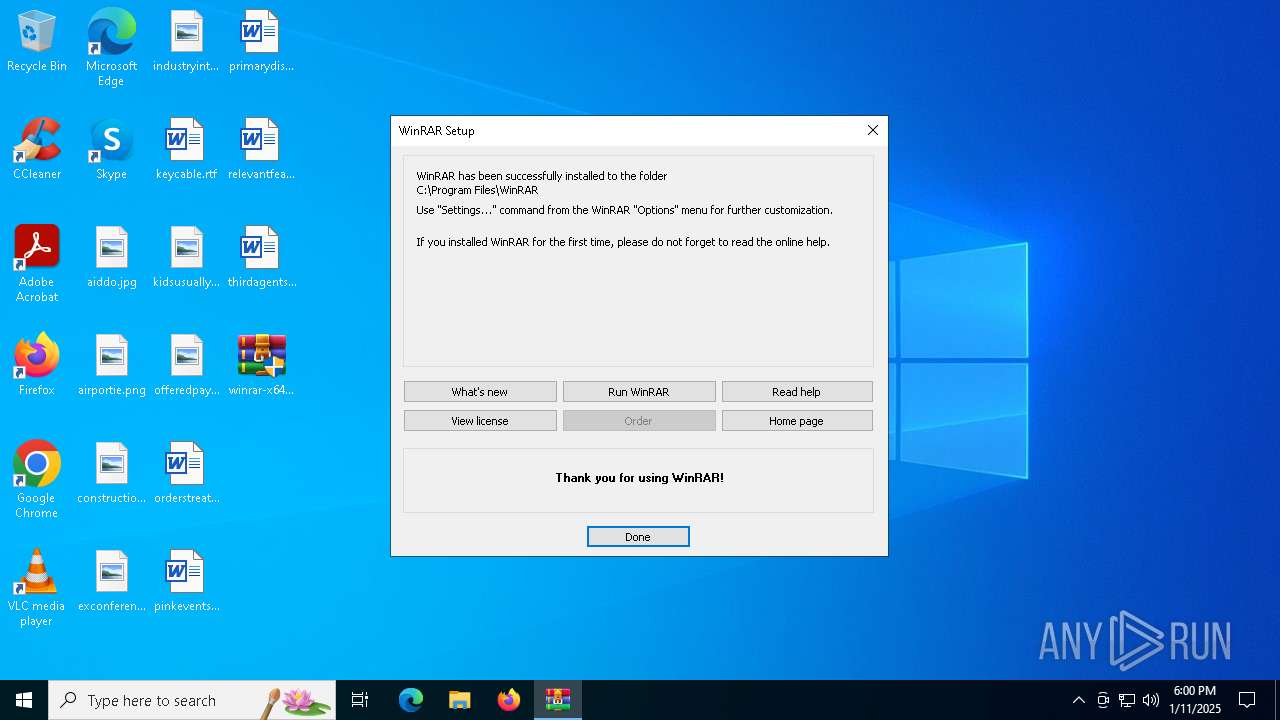
Creates a software uninstall entry
- Uninstall.exe (PID: 2324)
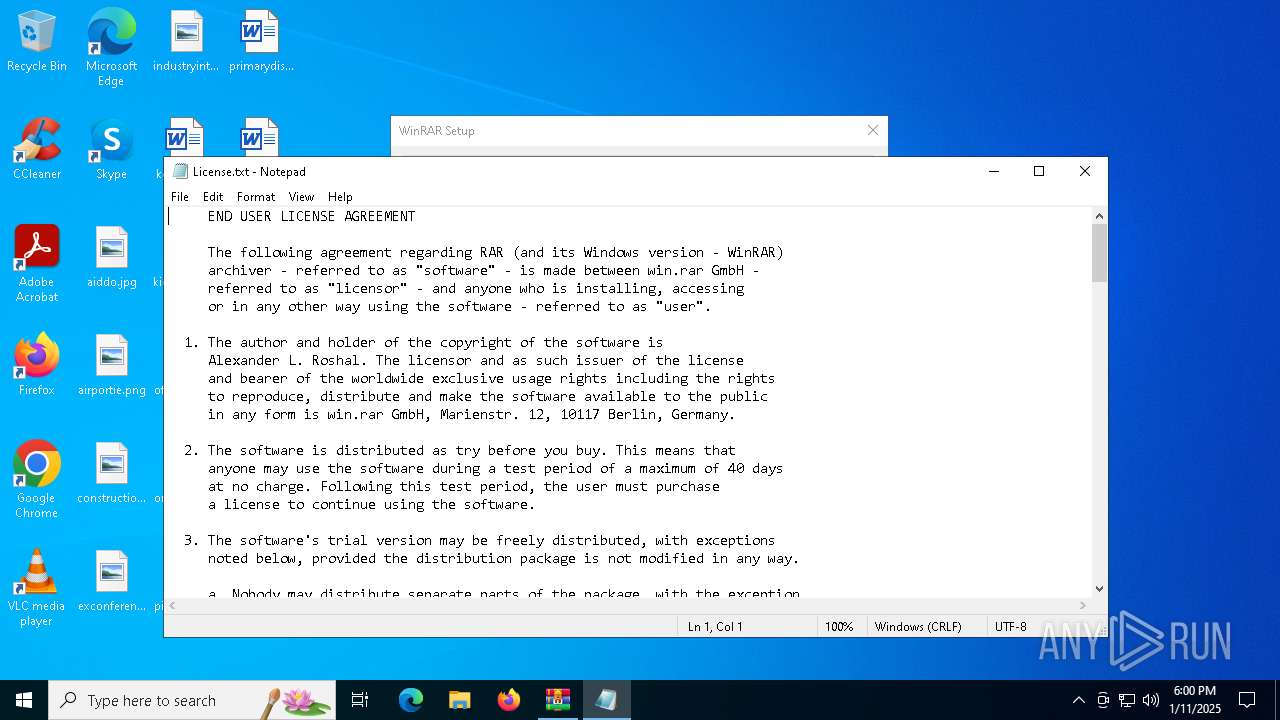
Start notepad (likely ransomware note)
- Uninstall.exe (PID: 2324)
Searches for installed software
- Uninstall.exe (PID: 2324)
INFO
Reads the computer name
- winrar-x64-700.exe (PID: 3812)
- Uninstall.exe (PID: 2324)
The sample compiled with english language support
- winrar-x64-700.exe (PID: 3812)
Creates files in the program directory
- winrar-x64-700.exe (PID: 3812)
- Uninstall.exe (PID: 2324)
The process uses the downloaded file
- winrar-x64-700.exe (PID: 3812)
- Uninstall.exe (PID: 2324)
The sample compiled with russian language support
- winrar-x64-700.exe (PID: 3812)
Checks proxy server information
- winrar-x64-700.exe (PID: 3812)
Process checks computer location settings
- winrar-x64-700.exe (PID: 3812)
- Uninstall.exe (PID: 2324)
Checks supported languages
- Uninstall.exe (PID: 2324)
- winrar-x64-700.exe (PID: 3812)
Creates files or folders in the user directory
- Uninstall.exe (PID: 2324)
Reads Microsoft Office registry keys
- Uninstall.exe (PID: 2324)
Reads security settings of Internet Explorer
- notepad.exe (PID: 1868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:02:26 09:02:06+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.33 |
| CodeSize: | 270848 |
| InitializedDataSize: | 309760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x29e60 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.0.0.0 |
| ProductVersionNumber: | 7.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| ProductName: | WinRAR |
| CompanyName: | Alexander Roshal |
| FileDescription: | WinRAR |
| FileVersion: | 7.0.0 |
| ProductVersion: | 7.0.0 |
| InternalName: | WinRAR |
| LegalCopyright: | Copyright © Alexander Roshal 1993-2024 |
| OriginalFileName: | WinRAR.exe |
Total processes
121
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1868 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Program Files\WinRAR\License.txt | C:\Windows\System32\notepad.exe | — | Uninstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2324 | "C:\Program Files\WinRAR\uninstall.exe" /setup | C:\Program Files\WinRAR\Uninstall.exe | — | winrar-x64-700.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: Uninstall WinRAR Version: 7.0.0 Modules
| |||||||||||||||
| 2744 | "C:\Users\admin\Desktop\winrar-x64-700.exe" | C:\Users\admin\Desktop\winrar-x64-700.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR Exit code: 3221226540 Version: 7.0.0 Modules
| |||||||||||||||
| 3812 | "C:\Users\admin\Desktop\winrar-x64-700.exe" | C:\Users\admin\Desktop\winrar-x64-700.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: WinRAR Exit code: 0 Version: 7.0.0 Modules
| |||||||||||||||
Total events
1 661
Read events
1 574
Write events
83
Delete events
4
Modification events
| (PID) Process: | (3812) winrar-x64-700.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3812) winrar-x64-700.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3812) winrar-x64-700.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3812) winrar-x64-700.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFavoritesInitialSelection |
Value: | |||
| (PID) Process: | (3812) winrar-x64-700.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFeedsInitialSelection |
Value: | |||
| (PID) Process: | (3812) winrar-x64-700.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR SFX |
| Operation: | write | Name: | C%%Program Files%WinRAR |
Value: C:\Program Files\WinRAR | |||
| (PID) Process: | (2324) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.rar |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (2324) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.zip |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (2324) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.cab |
| Operation: | write | Name: | Set |
Value: 1 | |||
| (PID) Process: | (2324) Uninstall.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Setup\.arj |
| Operation: | write | Name: | Set |
Value: 1 | |||
Executable files
13
Suspicious files
11
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3812 | winrar-x64-700.exe | — | ||
MD5:— | SHA256:— | |||
| 3812 | winrar-x64-700.exe | C:\Program Files\WinRAR\Rar.txt | text | |
MD5:FC13E375F3144A55ADFB46F342778447 | SHA256:7511C100DAA946175EFC18082D1923518BF1BFC8C1A80EA0252AF585FBE295B5 | |||
| 3812 | winrar-x64-700.exe | C:\Program Files\WinRAR\Descript.ion | text | |
MD5:84846ABC52DC17020E4E934D3C94B4E6 | SHA256:3449FD40D054C96285FAB92011E732174C7CD000EDA67470376F26F0D431F1F2 | |||
| 3812 | winrar-x64-700.exe | C:\Program Files\WinRAR\Uninstall.lst | text | |
MD5:6EEEFCB85673C14201D024B6E6AC6258 | SHA256:B75FDEE208D2834AB147DACB51F4E7D70E44457C8B639048FE67B252B8D61F1F | |||
| 3812 | winrar-x64-700.exe | C:\Program Files\WinRAR\ReadMe.txt | text | |
MD5:00D0A57A6D64EE3DE8F4D5529D6C6447 | SHA256:FCD13E1B97AF47B8B923BA97AE15E9731C66093609667C3171D5DD24A6F7F2E6 | |||
| 3812 | winrar-x64-700.exe | C:\Program Files\WinRAR\RarExt.dll | executable | |
MD5:3068EC5DC5FC098D27E2270366A7C4F6 | SHA256:FA913A43D99FD0AF75959A176C08A6041004A511329D608510AE6EBD75C7EA8E | |||
| 3812 | winrar-x64-700.exe | C:\Program Files\WinRAR\Order.htm | html | |
MD5:5C336DE3B3D794322AD9E5915E3A509F | SHA256:BCE29EF3B95306CB7B304FB8C3039BE7157356D9F9D4E7E1C6BFBF02A117F48F | |||
| 3812 | winrar-x64-700.exe | C:\Program Files\WinRAR\Default32.SFX | executable | |
MD5:7D8EA28F68D0959DBBDD901B9752B966 | SHA256:2E46177284A0F1D8AAC4CD247AF024320C3914DFA37C052C8D6D49B0BDB62725 | |||
| 3812 | winrar-x64-700.exe | C:\Program Files\WinRAR\UnRAR.exe | executable | |
MD5:0100DAD675575734961F4C7BD2DA5628 | SHA256:D95BBA20F04687B0B821D4FC0A17137DB8B9EDA5FE3FB34DA319ABEFC45FE0D1 | |||
| 3812 | winrar-x64-700.exe | C:\Program Files\WinRAR\Resources.pri | binary | |
MD5:43CB15C1F1CC705305AEBA33B0A9EE73 | SHA256:A7BB097441D9F06DD7A8D08874D70E7495626760C05284CA1AE3A208C11B52F0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
20
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
640 | svchost.exe | GET | 200 | 2.19.198.194:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
640 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.19.198.194:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
640 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 104.126.37.147:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
640 | svchost.exe | 2.19.198.194:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.19.198.194:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
640 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |