| File name: | prova.ppsx |
| Full analysis: | https://app.any.run/tasks/f440c142-e8ab-4761-8ab0-24473a670166 |
| Verdict: | Suspicious activity |
| Analysis date: | September 03, 2020, 07:08:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
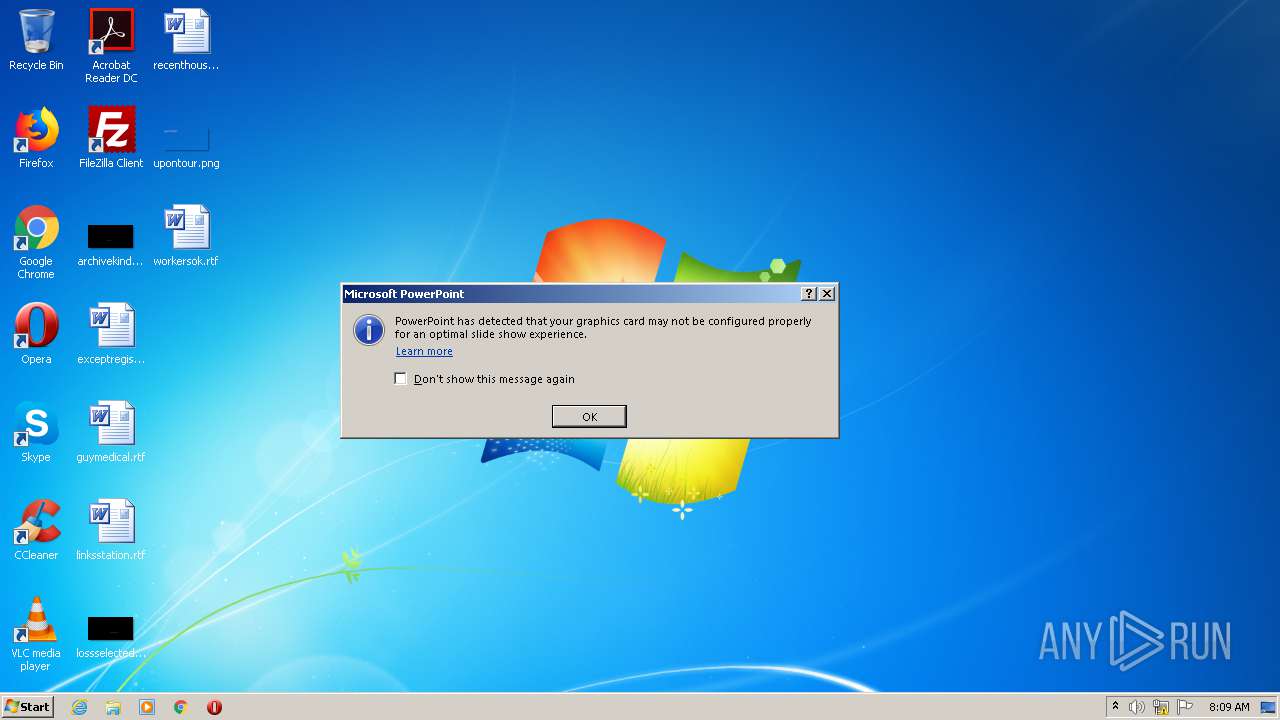
| MIME: | application/vnd.openxmlformats-officedocument.presentationml.presentation |
| File info: | Microsoft PowerPoint 2007+ |
| MD5: | C1D73CE5BF0559A86BAE0F9045A82E0A |
| SHA1: | 4537D7FC4188403484BA5AC865EDF51E1733F909 |
| SHA256: | FF301B3295959A3AC5F3D0A5EA0D9F0AEDCD8DA7C4207B18F4BBB6DDAA0CDF22 |
| SSDEEP: | 6144:WGw90n0pM0WTxL6qGlLsMnQfQ+ztaf0r/XP:WH9Y0KVJCDlGta+ |
MALICIOUS
Requests a remote executable file from MS Office
- POWERPNT.EXE (PID: 2900)
SUSPICIOUS
Checks supported languages
- POWERPNT.EXE (PID: 2900)
INFO
Reads Microsoft Office registry keys
- POWERPNT.EXE (PID: 2900)
Reads Internet Cache Settings
- POWERPNT.EXE (PID: 2900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .pptx | | | PowerPoint Microsoft Office Open XML Format document (87) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (10.5) |
| .zip | | | ZIP compressed archive (2.4) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x1159853c |
| ZipCompressedSize: | 606 |
| ZipUncompressedSize: | 4423 |
| ZipFileName: | [Content_Types].xml |
XMP
| Title: | PowerPoint Presentation |
|---|---|
| Creator: | Windows User |
XML
| LastModifiedBy: | Windows User |
|---|---|
| RevisionNumber: | 11 |
| CreateDate: | 2017:10:23 00:57:05Z |
| ModifyDate: | 2020:07:24 06:47:35Z |
| Template: | Equity |
| TotalEditTime: | 25 minutes |
| Words: | 1082 |
| Application: | Microsoft Office PowerPoint |
| PresentationFormat: | On-screen Show (4:3) |
| Paragraphs: | 22 |
| Slides: | 7 |
| Notes: | 1 |
| HiddenSlides: | - |
| MMClips: | - |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 12 |
Total processes
37
Monitored processes
1
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2900 | "C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE" /s "C:\Users\admin\AppData\Local\Temp\prova.ppsx" | C:\Program Files\Microsoft Office\Office14\POWERPNT.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft PowerPoint Exit code: 0 Version: 14.0.6009.1000 Modules
| |||||||||||||||
Total events
686
Read events
640
Write events
44
Delete events
2
Modification events
| (PID) Process: | (2900) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\Resiliency\StartupItems |
| Operation: | write | Name: | r0 |
Value: 72302000540B0000010000000000000000000000 | |||
| (PID) Process: | (2900) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2900) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2900) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2900) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2900) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2900) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2900) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2900) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2900) POWERPNT.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
24
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2900 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\CVR931.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2900 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\{A66F1D6A-F716-4256-A6E2-EAC397C3523A} | — | |
MD5:— | SHA256:— | |||
| 2900 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\{63895320-F3D9-4BB4-BEEB-A90E8184FCB6} | — | |
MD5:— | SHA256:— | |||
| 2900 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Temp\~DFABB92FBB4EB79499.TMP | — | |
MD5:— | SHA256:— | |||
| 2900 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-CNRY.FSD | binary | |
MD5:— | SHA256:— | |||
| 2900 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\LocalCacheFileEditManager\FSD-CNRY.FSD | binary | |
MD5:— | SHA256:— | |||
| 2900 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSF-CTBL.FSF | binary | |
MD5:— | SHA256:— | |||
| 2900 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\LocalCacheFileEditManager\FSD-{07596D7D-A941-4480-8358-2806FD758E0B}.FSD | binary | |
MD5:— | SHA256:— | |||
| 2900 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\LocalCacheFileEditManager\FSF-{0E1EEE64-E8C6-4E2A-9759-63CF07FD8988}.FSF | binary | |
MD5:— | SHA256:— | |||
| 2900 | POWERPNT.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-{0305F303-D005-4A79-80E4-75C3F79C7B35}.FSD | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
0
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2900 | POWERPNT.EXE | GET | — | 118.99.13.4:1234 | http://118.99.13.4:1234/qqqzqa | HK | — | — | suspicious |
2900 | POWERPNT.EXE | GET | — | 118.99.13.4:8099 | http://118.99.13.4:8099/file.dll | HK | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2900 | POWERPNT.EXE | 118.99.13.4:1234 | — | Forewin Telecom Group Limited, ISP at | HK | suspicious |
2900 | POWERPNT.EXE | 118.99.13.4:8099 | — | Forewin Telecom Group Limited, ISP at | HK | suspicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2900 | POWERPNT.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Malicious Windows SCT Download MSXMLHTTP M2 |