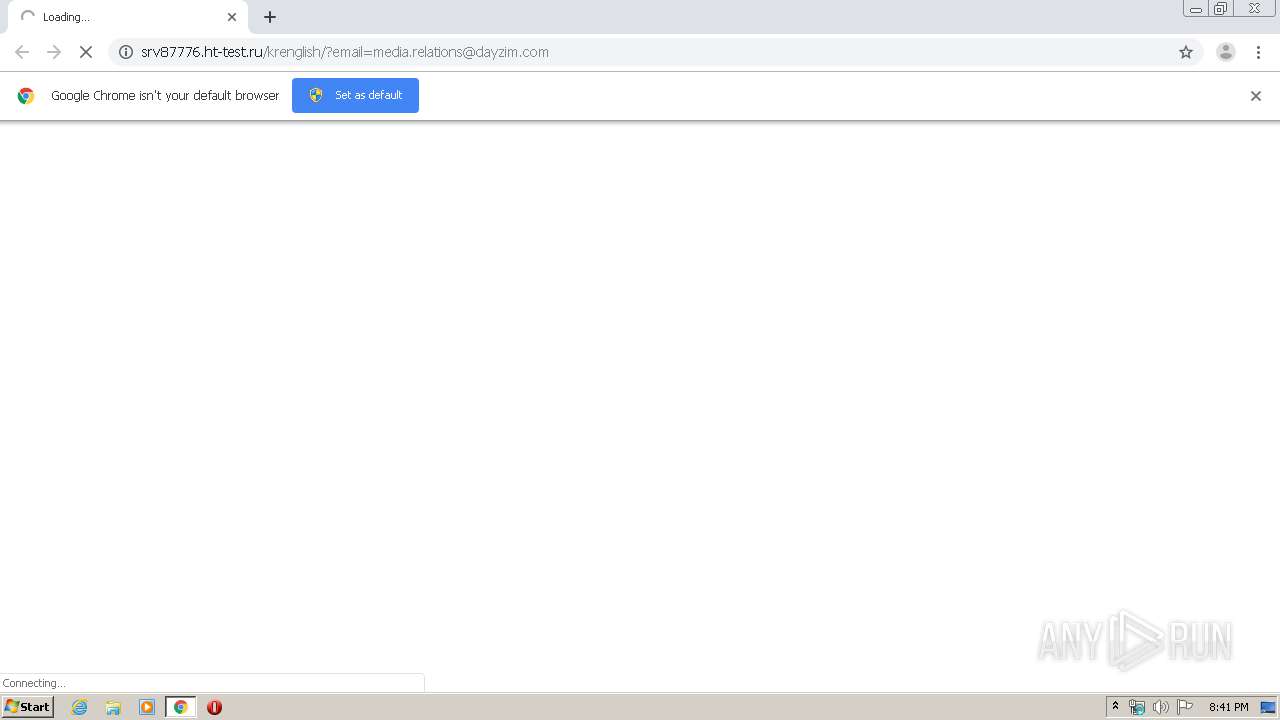
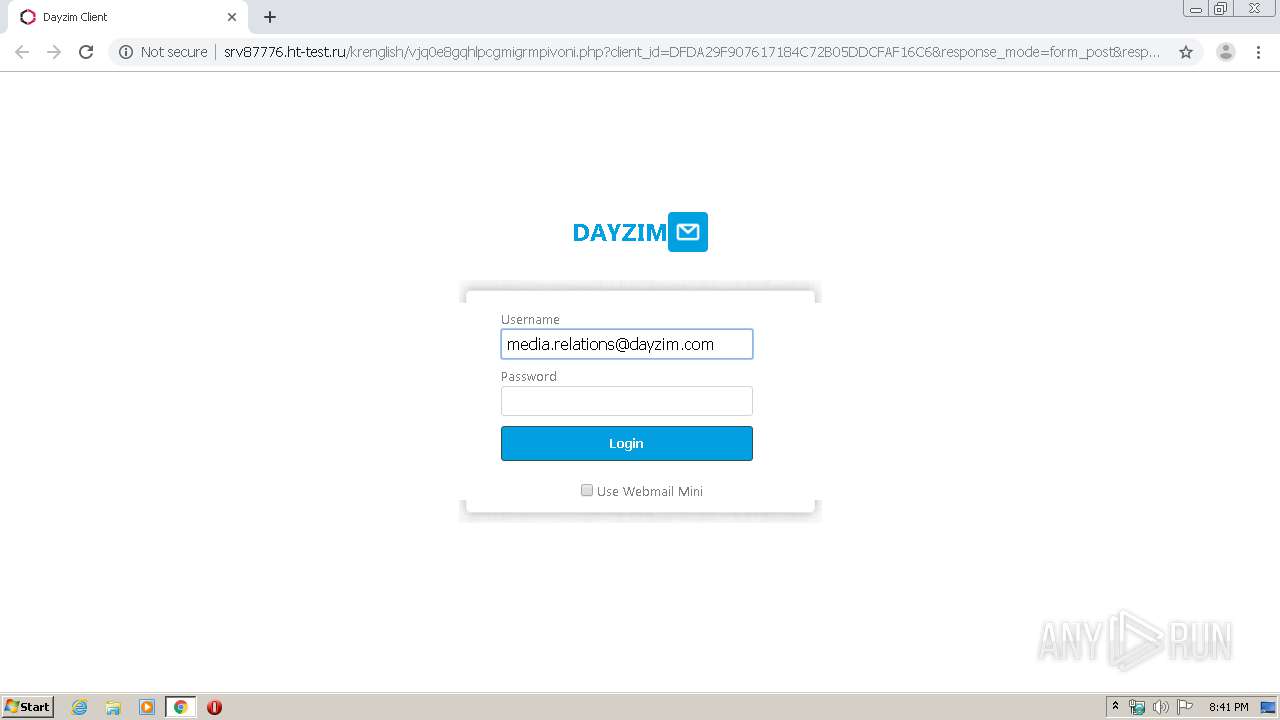
| URL: | http://srv87776.ht-test.ru/krenglish/?email=media.relations@dayzim.com |
| Full analysis: | https://app.any.run/tasks/41d82adc-a092-4e7c-9409-d6f23d2b4ac0 |
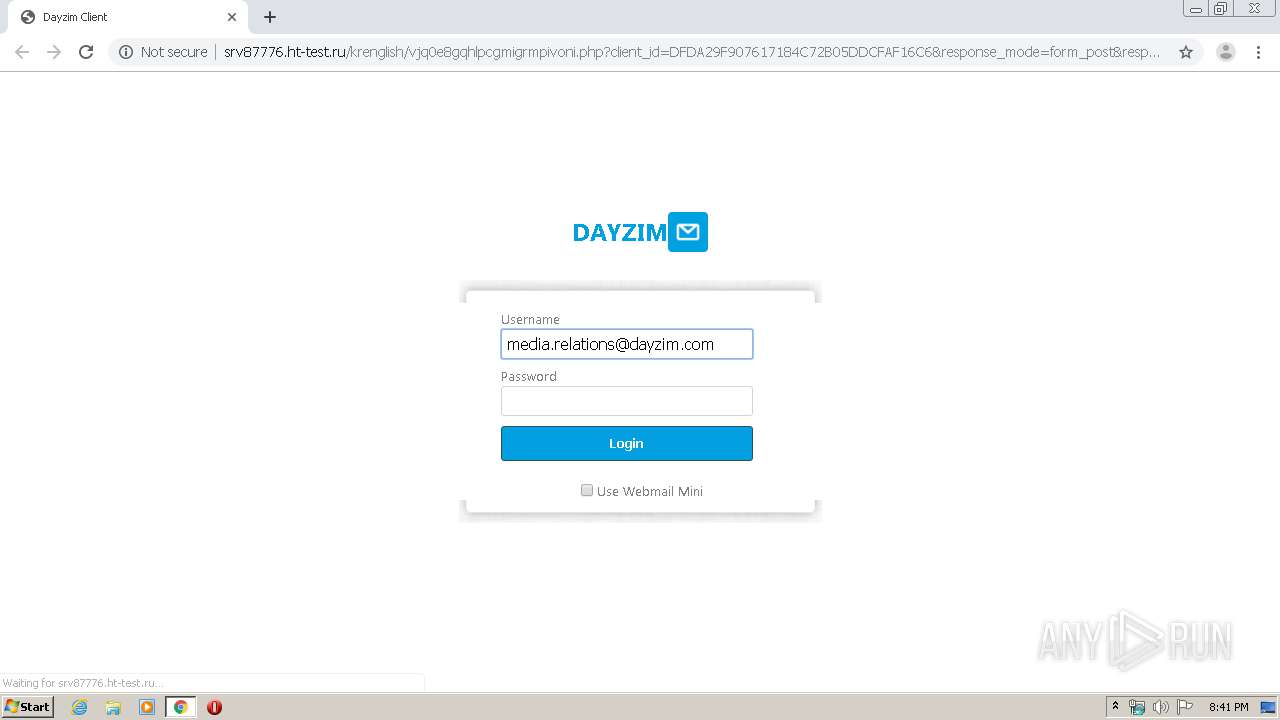
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 19:41:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D122EC1C1103C3E7C78AEEE52DEC0300 |
| SHA1: | 75CB8FBF2E5A898BA3D234060F831EDF7FB723E7 |
| SHA256: | FF2E2702CE75234A1A4C6A64F11D6D819A10AB52F0E77A203FB30A05A9711641 |
| SSDEEP: | 3:N1KNXRETwhR9KBtTlFELXlqKilyD5:CXR9KBdhDgt |
MALICIOUS
WebMail phishing page detected
- chrome.exe (PID: 3600)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3028)
INFO
Reads the hosts file
- chrome.exe (PID: 3028)
- chrome.exe (PID: 3600)
Application launched itself
- chrome.exe (PID: 3028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
28
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11783766316990740779 --mojo-platform-channel-handle=3080 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=505002427682020716 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4004 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14009728553901089372 --mojo-platform-channel-handle=3040 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16168330679529612092 --mojo-platform-channel-handle=3820 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8964099395621351429 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2120 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1045992950330205633 --mojo-platform-channel-handle=3900 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa8a9d0,0x6fa8a9e0,0x6fa8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=221079689848501072 --mojo-platform-channel-handle=2604 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,14134417760950761469,12088534520466632996,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15690350705082306493 --mojo-platform-channel-handle=3428 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://srv87776.ht-test.ru/krenglish/?email=media.relations@dayzim.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
611
Read events
526
Write events
80
Delete events
5
Modification events
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3028-13230070882090125 |
Value: 259 | |||
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3028) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
18
Text files
234
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E824B62-BD4.pma | — | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7b8d1f37-4b08-4901-9380-8ae7d2f7d90a.tmp | — | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66c5e.TMP | text | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3028 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66e81.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
33
DNS requests
16
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3600 | chrome.exe | GET | 302 | 8.10.192.121:80 | http://dayzim.com/favicon.ico | US | — | — | unknown |
3600 | chrome.exe | GET | 301 | 104.17.120.180:80 | http://www.dayzim.com/favicon.ico | US | — | — | suspicious |
3600 | chrome.exe | GET | 302 | 78.110.50.131:80 | http://srv87776.ht-test.ru/krenglish/?email=media.relations@dayzim.com | RU | — | — | malicious |
3600 | chrome.exe | GET | 200 | 78.110.50.131:80 | http://srv87776.ht-test.ru/krenglish/vjq0e8gqhlpcgmigrmpivoni.php?client_id=DFDA29F907617184C72B05DDCFAF16C6&response_mode=form_post&response_type=code+id_token&scope=openid+profile&email=media.relations@dayzim.com&Connect_Authentication_Properties&&nonce=698686651dfda29f907617184c72b05ddcfaf16c6&redirect_uri=&ui_locales=en-US&mkt=en-US | RU | html | 2.72 Kb | malicious |
3600 | chrome.exe | GET | 404 | 78.110.50.131:80 | http://srv87776.ht-test.ru/krenglish/login_files/img/middle.png | RU | html | 344 b | malicious |
3600 | chrome.exe | GET | 404 | 78.110.50.131:80 | http://srv87776.ht-test.ru/krenglish/login_files/img/background.png | RU | html | 348 b | malicious |
3600 | chrome.exe | GET | 200 | 104.17.244.204:80 | http://cdn2.hubspot.net/hub/208537/file-30361289-ico/favicon.ico | US | image | 1.12 Kb | whitelisted |
3600 | chrome.exe | GET | 302 | 172.217.23.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 522 b | whitelisted |
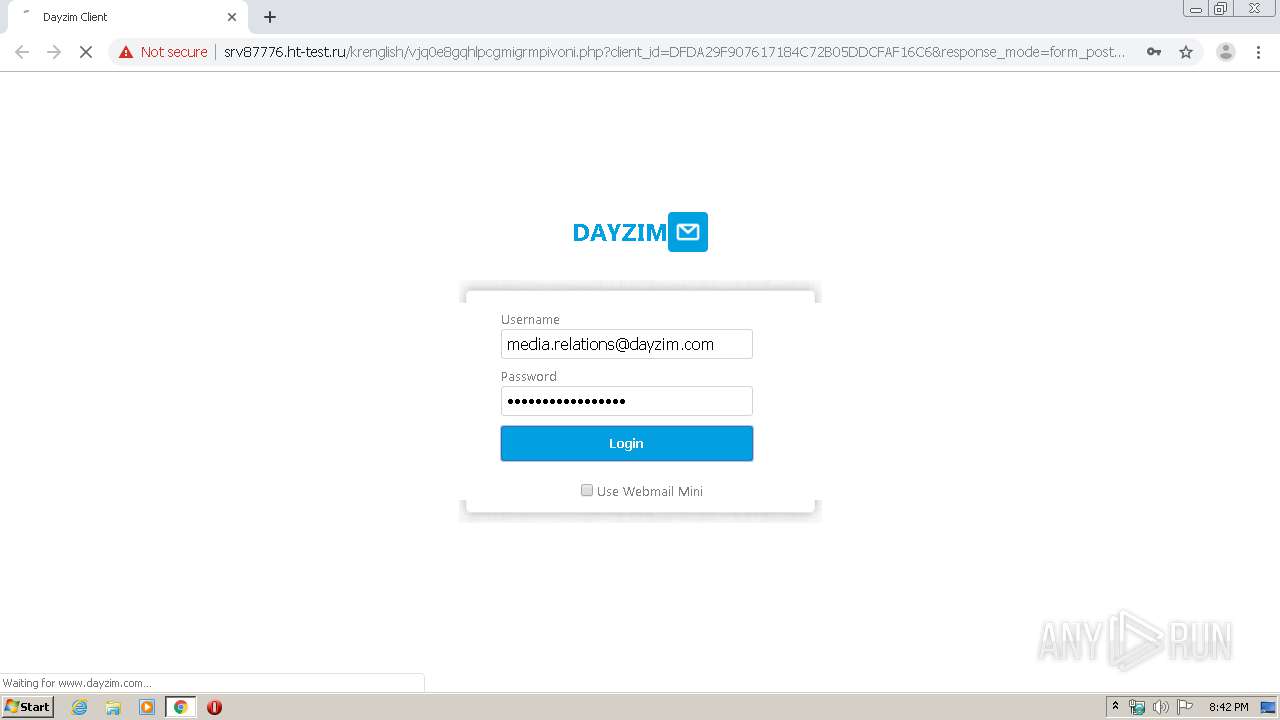
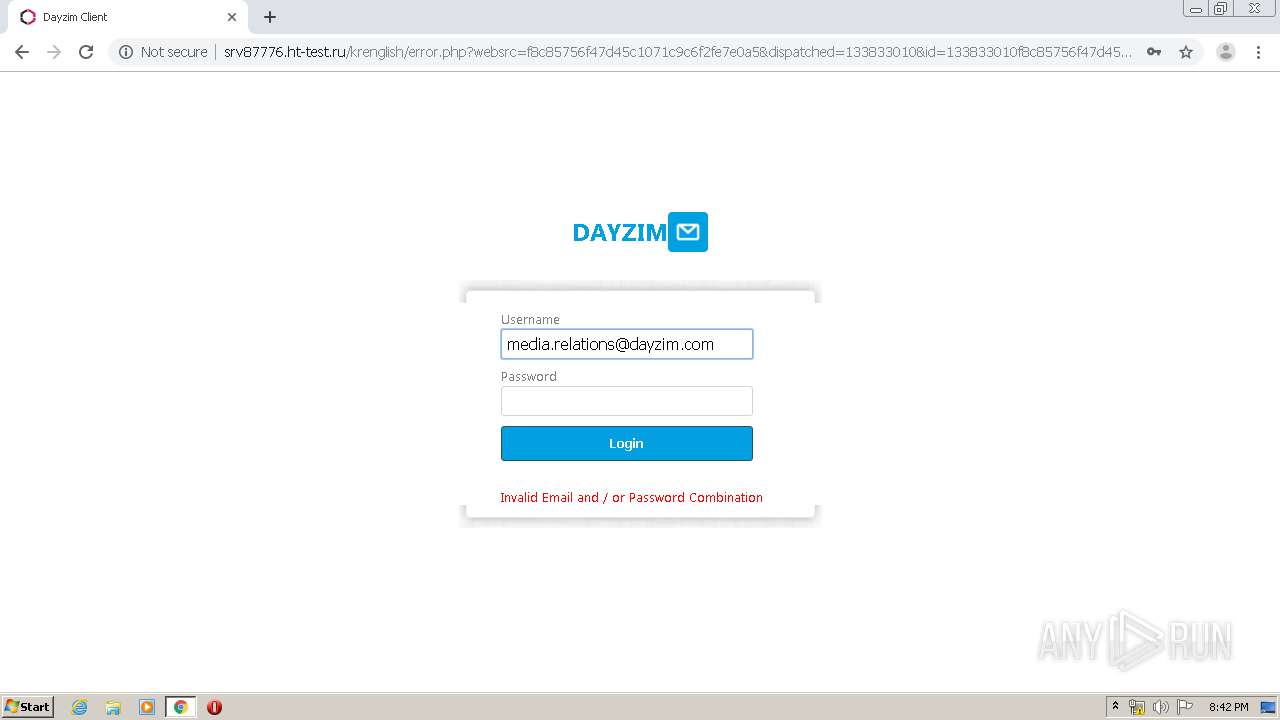
3600 | chrome.exe | POST | 302 | 78.110.50.131:80 | http://srv87776.ht-test.ru/krenglish/login.php | RU | — | — | malicious |
3600 | chrome.exe | GET | 200 | 78.110.50.131:80 | http://srv87776.ht-test.ru/krenglish/login_files/top.png | RU | image | 1.67 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3600 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3600 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3600 | chrome.exe | 104.17.120.180:80 | www.dayzim.com | Cloudflare Inc | US | shared |
3600 | chrome.exe | 104.17.120.180:443 | www.dayzim.com | Cloudflare Inc | US | shared |
3600 | chrome.exe | 216.58.208.42:443 | www.googleapis.com | Google Inc. | US | whitelisted |
3600 | chrome.exe | 8.10.192.121:80 | dayzim.com | The Day & Zimmermann Group, Inc. | US | unknown |
3600 | chrome.exe | 172.217.23.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
— | — | 172.217.23.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3600 | chrome.exe | 173.194.151.74:80 | r4---sn-4g5e6nes.gvt1.com | Google Inc. | US | whitelisted |
3600 | chrome.exe | 172.217.23.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
srv87776.ht-test.ru |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
dayzim.com |
| unknown |
www.dayzim.com |
| suspicious |
cdn2.hubspot.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3600 | chrome.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible Microsoft Account Phishing |
3 ETPRO signatures available at the full report