| File name: | 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader |
| Full analysis: | https://app.any.run/tasks/a3dfe0e9-694b-4835-b00a-132539709aaf |
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2025, 05:14:02 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 98D2693CA6BEA8C7D5809BB6AB4EC07D |
| SHA1: | E9FB89460685FD16C2820636CE45E219D9030903 |
| SHA256: | FF1911EEB0BAD6C45C6C8B5D3D381BA710A4CDE5D2093ABD3B89D70763A0A5B8 |
| SSDEEP: | 98304:iefUuZuKAuf5jTFnkOefUuZuKAuf5jTFrkHVrGDYwOwjefUuZuKAuf5jTFPkOefj:WEdC15gY |
MALICIOUS
Executing a file with an untrusted certificate
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 4180)
Starts NET.EXE for service management
- cmd.exe (PID: 5640)
- cmd.exe (PID: 1072)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 728)
- cmd.exe (PID: 5868)
- net.exe (PID: 1852)
- net.exe (PID: 5204)
- net.exe (PID: 5508)
- net.exe (PID: 5436)
- net.exe (PID: 2392)
Changes the autorun value in the registry
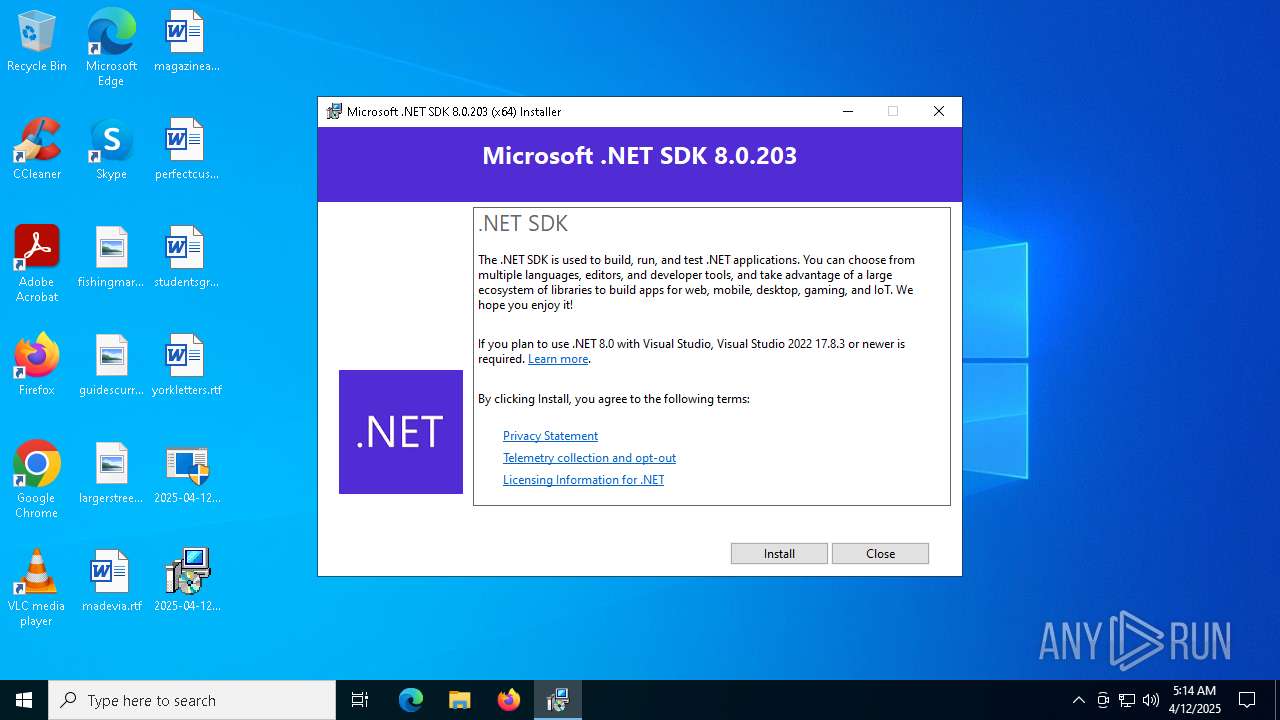
- dotnet-sdk-8.0.203-win-x64.exe (PID: 6824)
Uses NET.EXE to stop Windows Security Center service
- cmd.exe (PID: 1072)
- net.exe (PID: 1852)
Uses NET.EXE to stop Windows Update service
- cmd.exe (PID: 5640)
- net.exe (PID: 2392)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 6988)
- net.exe (PID: 5960)
Starts NET.EXE to view/change users localgroup
- cmd.exe (PID: 2236)
- net.exe (PID: 4464)
SUSPICIOUS
Process drops legitimate windows executable
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5892)
- UpdatAuto.exe (PID: 7152)
Starts a Microsoft application from unusual location
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 864)
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 4180)
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5892)
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 1244)
- dotnet-sdk-8.0.203-win-x64.exe (PID: 6824)
Executable content was dropped or overwritten
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5892)
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 4180)
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 1244)
- UpdatAuto.exe (PID: 7152)
- dotnet-sdk-8.0.203-win-x64.exe (PID: 6824)
Executing commands from a ".bat" file
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5892)
- UpdatAuto.exe (PID: 7152)
Starts CMD.EXE for commands execution
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5892)
- UpdatAuto.exe (PID: 7152)
Creates file in the systems drive root
- UpdatAuto.exe (PID: 7152)
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5892)
Starts itself from another location
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 4180)
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 1244)
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5892)
Searches for installed software
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 1244)
Reads security settings of Internet Explorer
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 1244)
Windows service management via SC.EXE
- sc.exe (PID: 3240)
- sc.exe (PID: 4188)
- sc.exe (PID: 2552)
- sc.exe (PID: 2984)
- sc.exe (PID: 5400)
Creates a software uninstall entry
- dotnet-sdk-8.0.203-win-x64.exe (PID: 6824)
INFO
Create files in a temporary directory
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5892)
- UpdatAuto.exe (PID: 7152)
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 1244)
The sample compiled with chinese language support
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5892)
- UpdatAuto.exe (PID: 7152)
Checks supported languages
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 4180)
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5892)
- UpdatAuto.exe (PID: 7152)
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 1244)
- dotnet-sdk-8.0.203-win-x64.exe (PID: 6824)
Creates files in the program directory
- UpdatAuto.exe (PID: 7152)
- dotnet-sdk-8.0.203-win-x64.exe (PID: 6824)
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe (PID: 5892)
The sample compiled with english language support
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 1244)
Reads the computer name
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 1244)
- dotnet-sdk-8.0.203-win-x64.exe (PID: 6824)
- UpdatAuto.exe (PID: 7152)
Process checks computer location settings
- 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe (PID: 1244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (24.9) |
|---|---|---|
| .exe | | | InstallShield setup (13) |
| .exe | | | Win32 EXE PECompact compressed (generic) (12.6) |
| .exe | | | Win32 Executable MS Visual C++ (generic) (9.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:03:12 04:30:52+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 102400 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x27dc |
| OSVersion: | 4 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.1.0.0 |
| ProductVersionNumber: | 6.1.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| Comments: | Windows Update Manager for NT |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Windows Update Manager for NT |
| LegalCopyright: | Copyright (C) Microsoft Corp. 1981-1999 |
| ProductName: | Microsoft(R) Windows (R) 2000 Operating System |
| FileVersion: | 6.01 |
| ProductVersion: | 6.01 |
| InternalName: | INCUBUS |
| OriginalFileName: | INCUBUS.exe |
Total processes
170
Monitored processes
49
Malicious processes
7
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | cmd.exe /c net stop srservice | C:\Windows\SysWOW64\cmd.exe | — | 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | "C:\Users\admin\Desktop\2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe" | C:\Users\admin\Desktop\2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Manager for NT Exit code: 3221226540 Version: 6.01 Modules
| |||||||||||||||
| 900 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | C:\WINDOWS\system32\net1 stop wuauserv | C:\Windows\SysWOW64\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | cmd.exe /c net stop wscsvc | C:\Windows\SysWOW64\cmd.exe | — | 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | C:\WINDOWS\system32\cmd.exe /c C:\WINDOWS\system32\Option.bat | C:\Windows\SysWOW64\cmd.exe | — | 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 041
Read events
1 008
Write events
26
Delete events
7
Modification events
| (PID) Process: | (6824) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | write | Name: | BundleCachePath |
Value: C:\ProgramData\Package Cache\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9}\dotnet-sdk-8.0.203-win-x64.exe | |||
| (PID) Process: | (6824) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | write | Name: | BundleUpgradeCode |
Value: {2F768D97-5DB1-633B-DA88-37AFC81A605E} | |||
| (PID) Process: | (6824) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | write | Name: | BundleAddonCode |
Value: | |||
| (PID) Process: | (6824) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | write | Name: | BundleDetectCode |
Value: | |||
| (PID) Process: | (6824) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | write | Name: | BundlePatchCode |
Value: | |||
| (PID) Process: | (6824) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | write | Name: | BundleVersion |
Value: 8.2.324.15524 | |||
| (PID) Process: | (6824) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | write | Name: | VersionMajor |
Value: 8 | |||
| (PID) Process: | (6824) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | write | Name: | VersionMinor |
Value: 2 | |||
| (PID) Process: | (6824) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | write | Name: | BundleProviderKey |
Value: {1b7b7e0b-adb5-40cf-af56-2586842b5ca9} | |||
| (PID) Process: | (6824) dotnet-sdk-8.0.203-win-x64.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{1b7b7e0b-adb5-40cf-af56-2586842b5ca9} |
| Operation: | write | Name: | BundleTag |
Value: | |||
Executable files
17
Suspicious files
2
Text files
21
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5892 | 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader.exe | C:\Windows\SysWOW64\Option.bat | text | |
MD5:1D04ABF39E9DF55EED1D04430CC21EB8 | SHA256:0BC485263CF8A962E64DB0B88F156F2A9AF1B81ECFDB1CF9111D497E85DF70F3 | |||
| 1244 | 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | C:\Windows\Temp\{A8F45D1C-0CBE-4683-B4EF-C741EA705150}\.ba\thm.xml | xml | |
MD5:BC4C1B302D6C87C4026508120E167C95 | SHA256:C9E7E37D46601196E0DDA5D42FDF80C533DAB4CDF09D68E5A7C9A86C05795E00 | |||
| 1244 | 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | C:\Windows\Temp\{A8F45D1C-0CBE-4683-B4EF-C741EA705150}\.ba\1041\thm.wxl | xml | |
MD5:C94D1C2454375B72D458EFF51F54FD48 | SHA256:DAB0F9BAE96057C7C819571E40122BF1CA4A39834627B617A73DD071B2437423 | |||
| 1244 | 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | C:\Windows\Temp\{A8F45D1C-0CBE-4683-B4EF-C741EA705150}\.ba\bg.png | image | |
MD5:9EB0320DFBF2BD541E6A55C01DDC9F20 | SHA256:9095BF7B6BAA0107B40A4A6D727215BE077133A190F4CA9BD89A176842141E79 | |||
| 1244 | 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | C:\Windows\Temp\{A8F45D1C-0CBE-4683-B4EF-C741EA705150}\.ba\wixstdba.dll | executable | |
MD5:AA531C5359EBFB8204C12E774C7EF280 | SHA256:44B362B78639BACCD5C83F0B224A206730B1276FAB849C77FD1FB17DB2F07014 | |||
| 1244 | 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | C:\Windows\Temp\{A8F45D1C-0CBE-4683-B4EF-C741EA705150}\.ba\1031\thm.wxl | xml | |
MD5:D9F3E60B1262A4140991C47BC9D2E37F | SHA256:6B37D837535CA6AB6D46703EADF9CD87965DE6DA66F034F0053F52971150FC43 | |||
| 1244 | 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | C:\Windows\Temp\{A8F45D1C-0CBE-4683-B4EF-C741EA705150}\.ba\thm.wxl | xml | |
MD5:4479C9AAAAE17F8009392786F0910789 | SHA256:34919F9197533A6BA636941A91E33E57338FB86A821FA02BF586CB80E9EEBDB2 | |||
| 1244 | 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | C:\Windows\Temp\{A8F45D1C-0CBE-4683-B4EF-C741EA705150}\.ba\1040\thm.wxl | xml | |
MD5:29AECDE585E557A812B86141F0656043 | SHA256:04FAD78A493E7123CABCFD4E0A405AF3FD2175CF24AD4CE93B30539029FEC5C3 | |||
| 1244 | 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | C:\Windows\Temp\{A8F45D1C-0CBE-4683-B4EF-C741EA705150}\.ba\1029\thm.wxl | xml | |
MD5:9128B2606544FB6446F43B030C212E46 | SHA256:ACD0958C0C2187F766BA87C7F84A2AE3BA1BF7F3E9DD5D874C37C3D7C6FBF5E3 | |||
| 1244 | 2025-04-12_98d2693ca6bea8c7d5809bb6ab4ec07d_black-basta_elex_hijackloader_luca-stealer_rhadamanthys_smoke-loader~4.exe | C:\Windows\Temp\{A8F45D1C-0CBE-4683-B4EF-C741EA705150}\.ba\1033\thm.wxl | xml | |
MD5:4479C9AAAAE17F8009392786F0910789 | SHA256:34919F9197533A6BA636941A91E33E57338FB86A821FA02BF586CB80E9EEBDB2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
38
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 304 | 4.175.87.197:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
7396 | SIHClient.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
7396 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7396 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7396 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 40.69.42.241:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
— | — | GET | 304 | 4.175.87.197:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 304 | 4.175.87.197:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
7396 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6544 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7396 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |