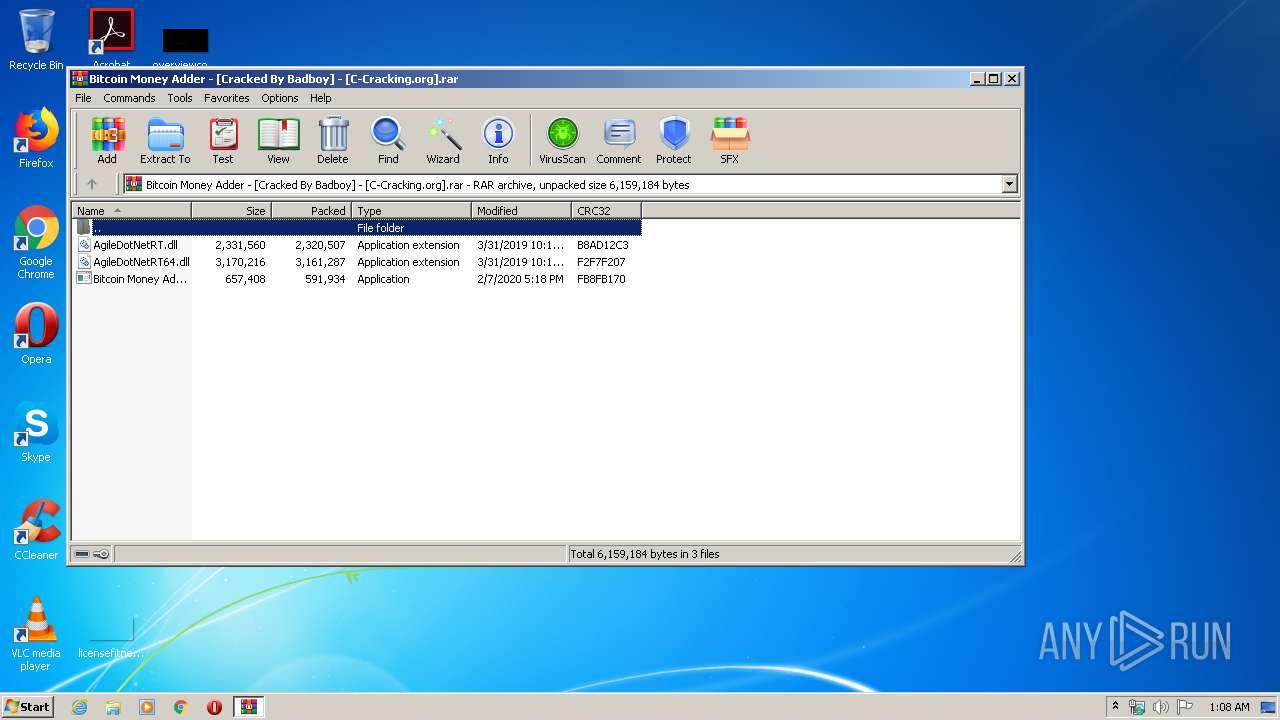
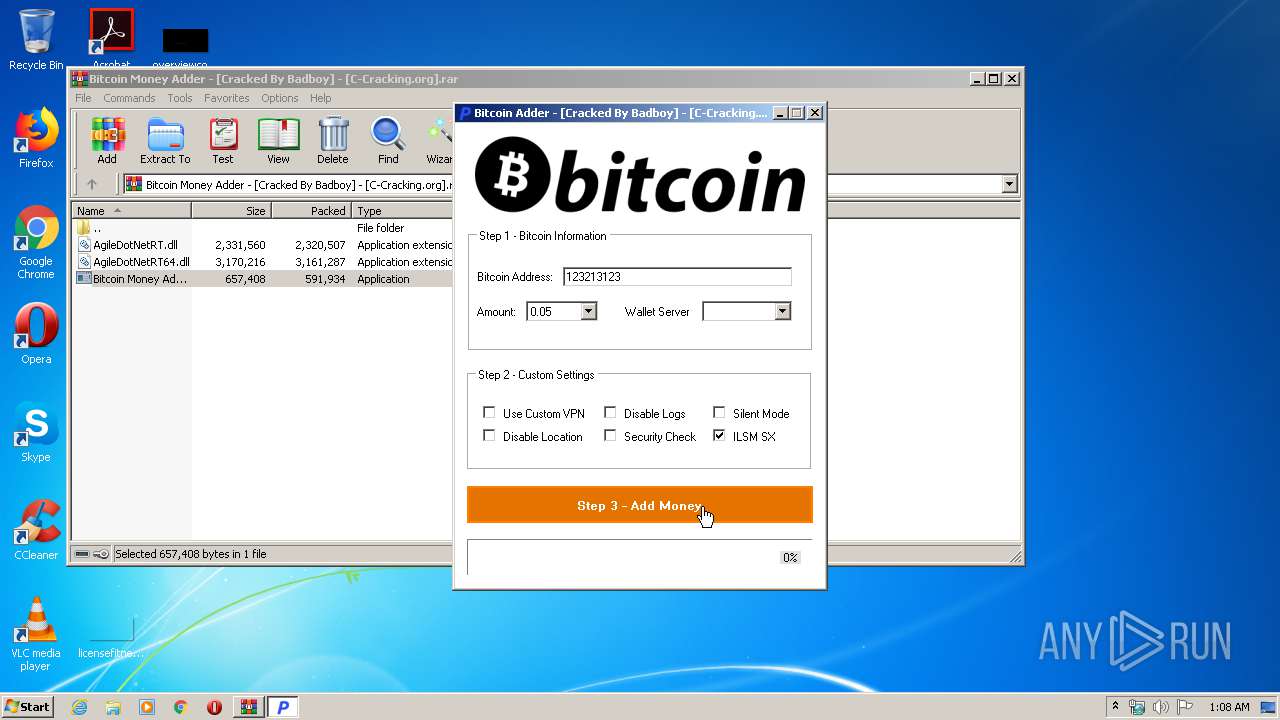
| File name: | Bitcoin Money Adder - [Cracked By Badboy] - [C-Cracking.org].rar |
| Full analysis: | https://app.any.run/tasks/67ffd6cc-d3fc-444c-b79f-1fc278da5525 |
| Verdict: | No threats detected |
| Analysis date: | March 23, 2020, 01:08:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 160F70C8ECD3230657392BE61FB41ECA |
| SHA1: | B04931304DAF3ED03B5D33E5D44D8E9F7B1AA535 |
| SHA256: | FF1398AF237FFDC96744BDEC79DA631D0A5BDA69A2A4FFFE60F4872163CA066B |
| SSDEEP: | 98304:za80/cinED4X0LqsngcOFfJGCAhYhf7J/YdV0QMCgd0i0+Bfqz:zTmcOfMt5OxJGCAh8TJai0F |
MALICIOUS
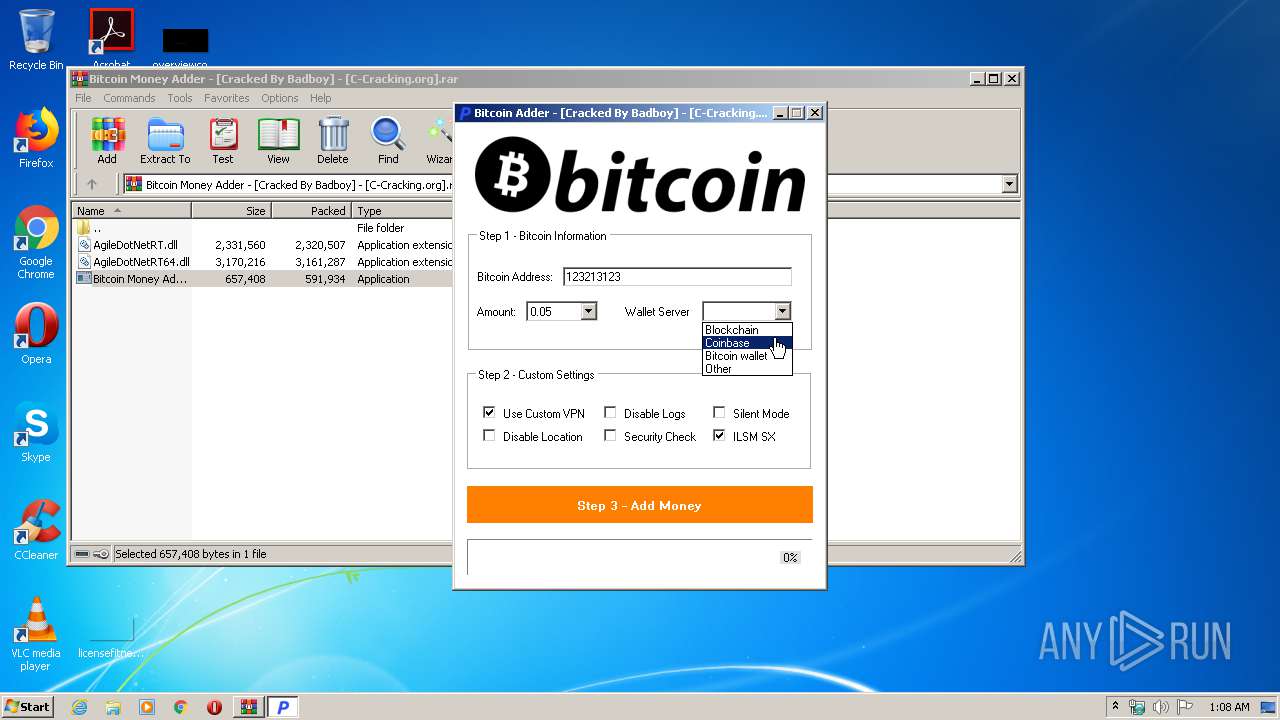
Loads dropped or rewritten executable
- Bitcoin Money Adder - [Cracked By Badboy] - [C-Cracking.org].exe (PID: 3512)
Application was dropped or rewritten from another process
- Bitcoin Money Adder - [Cracked By Badboy] - [C-Cracking.org].exe (PID: 3512)
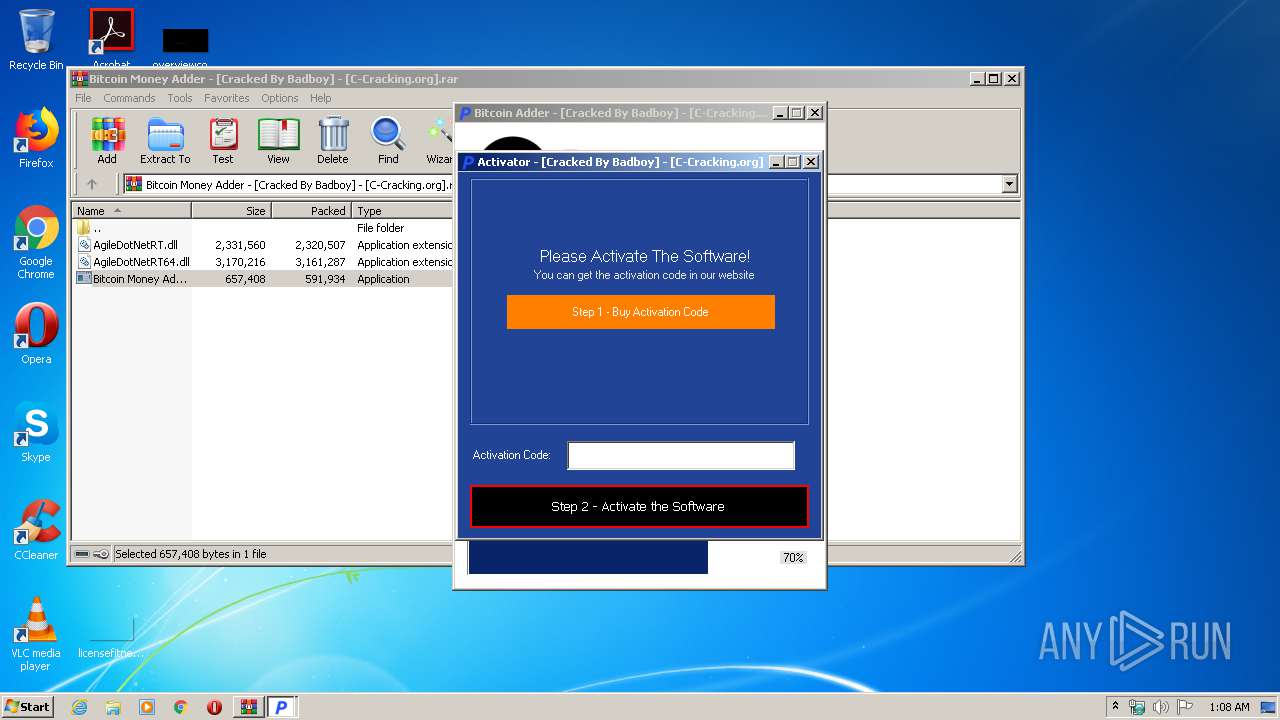
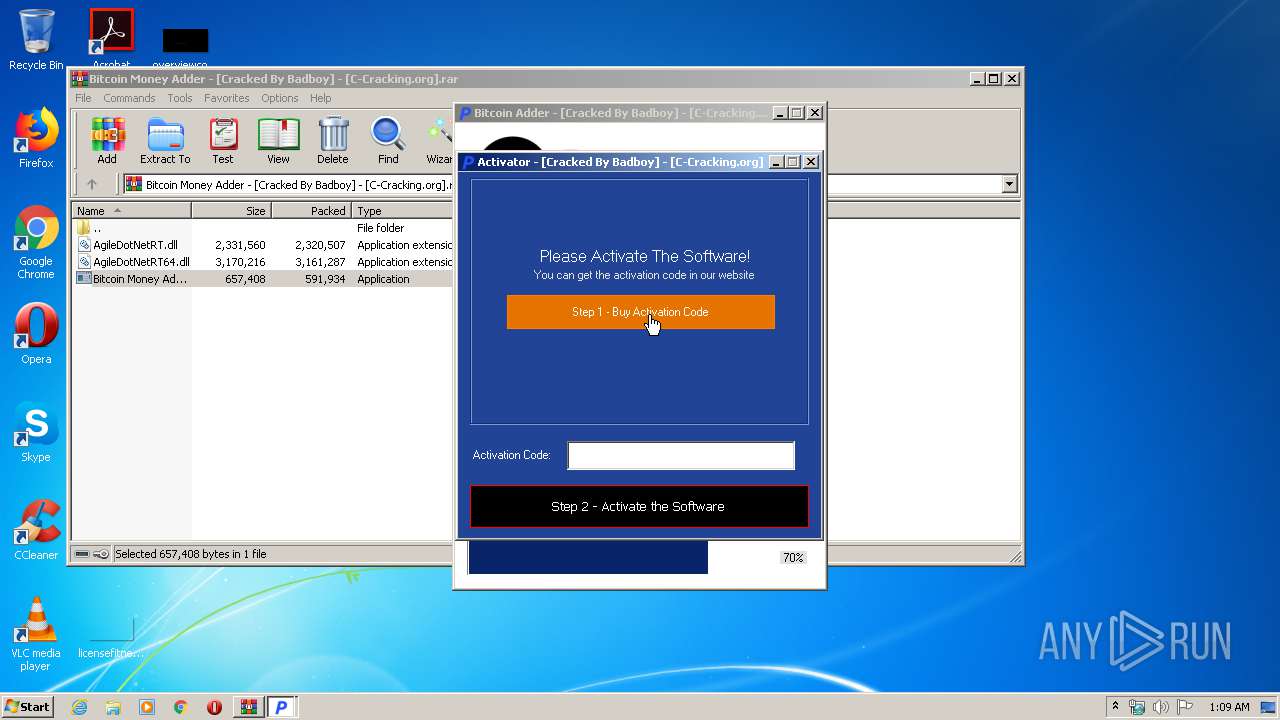
SUSPICIOUS
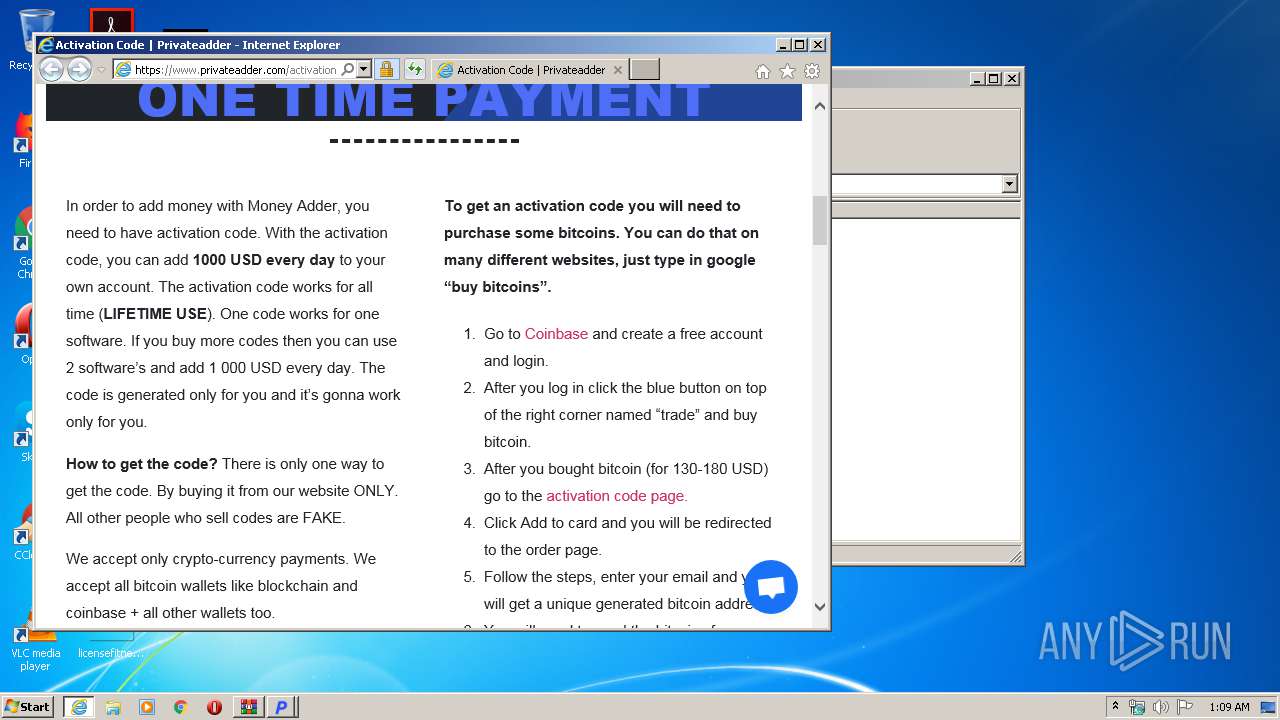
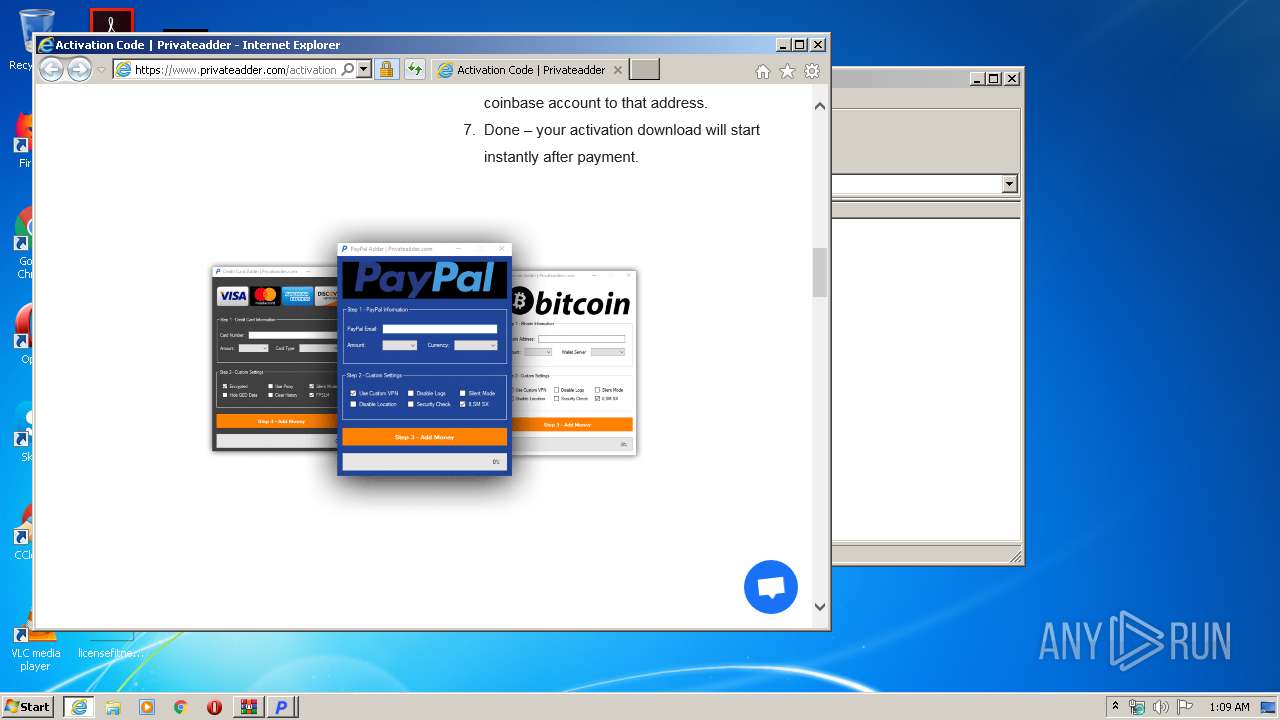
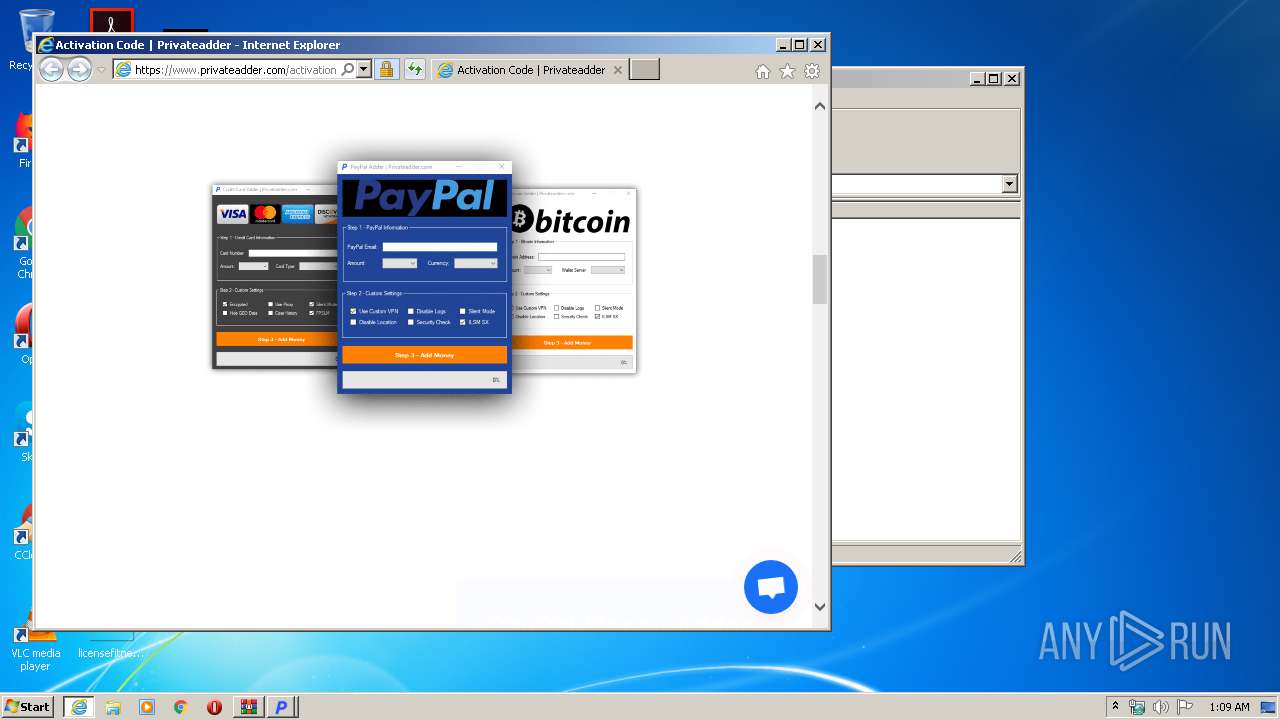
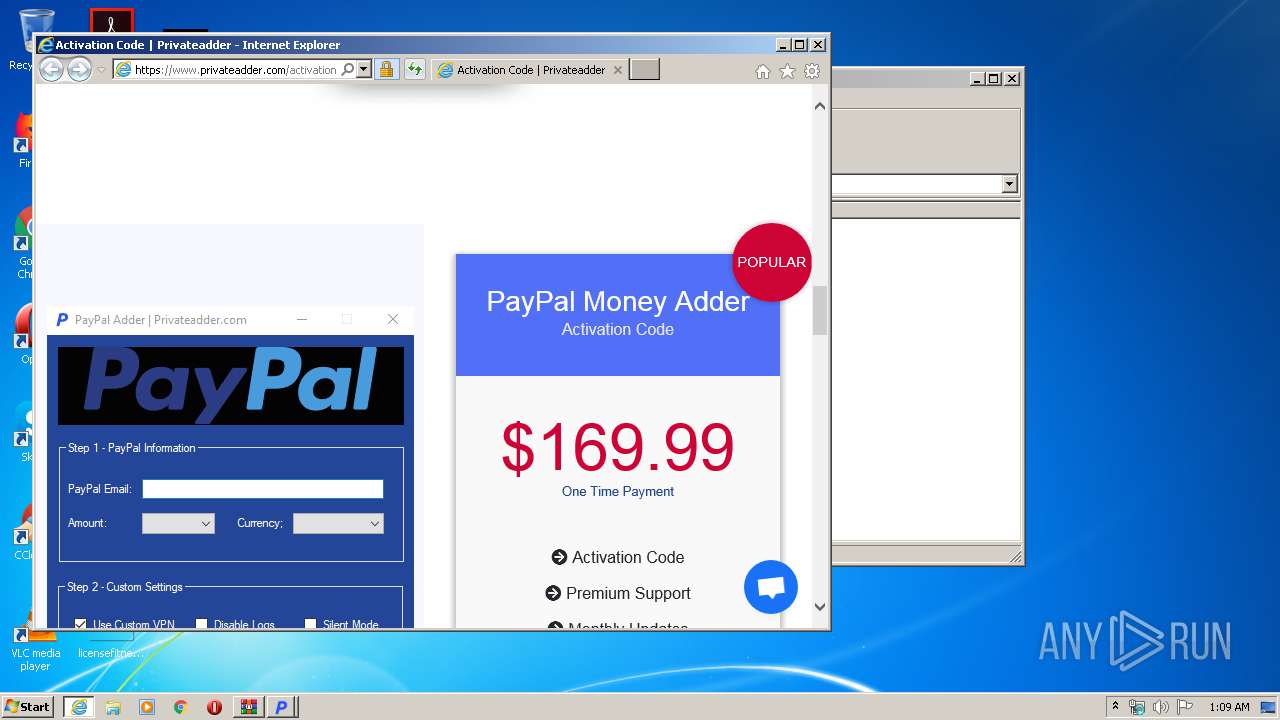
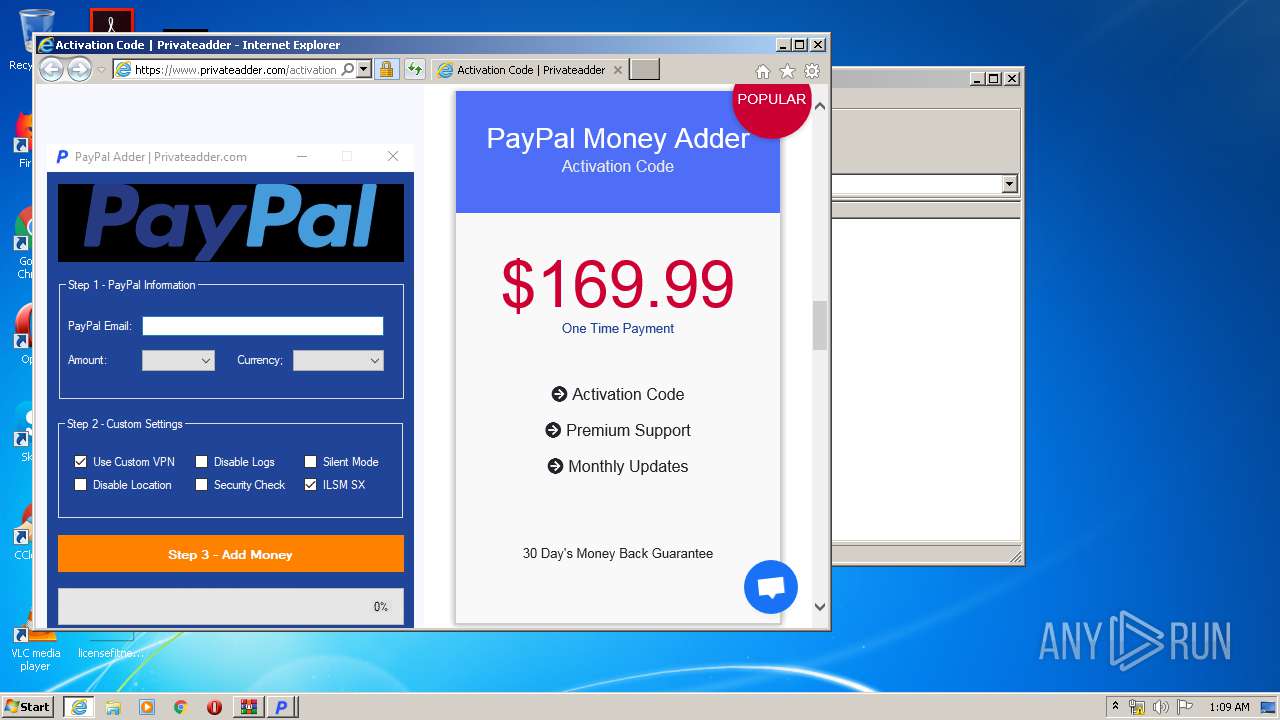
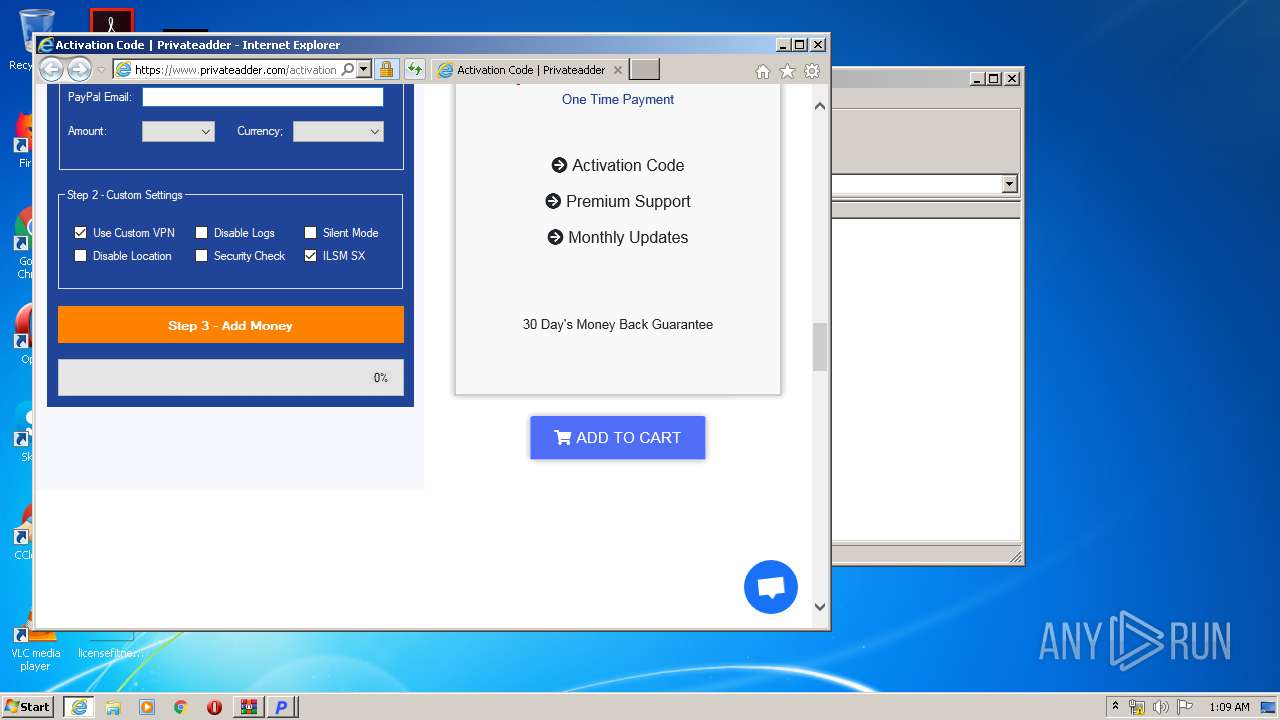
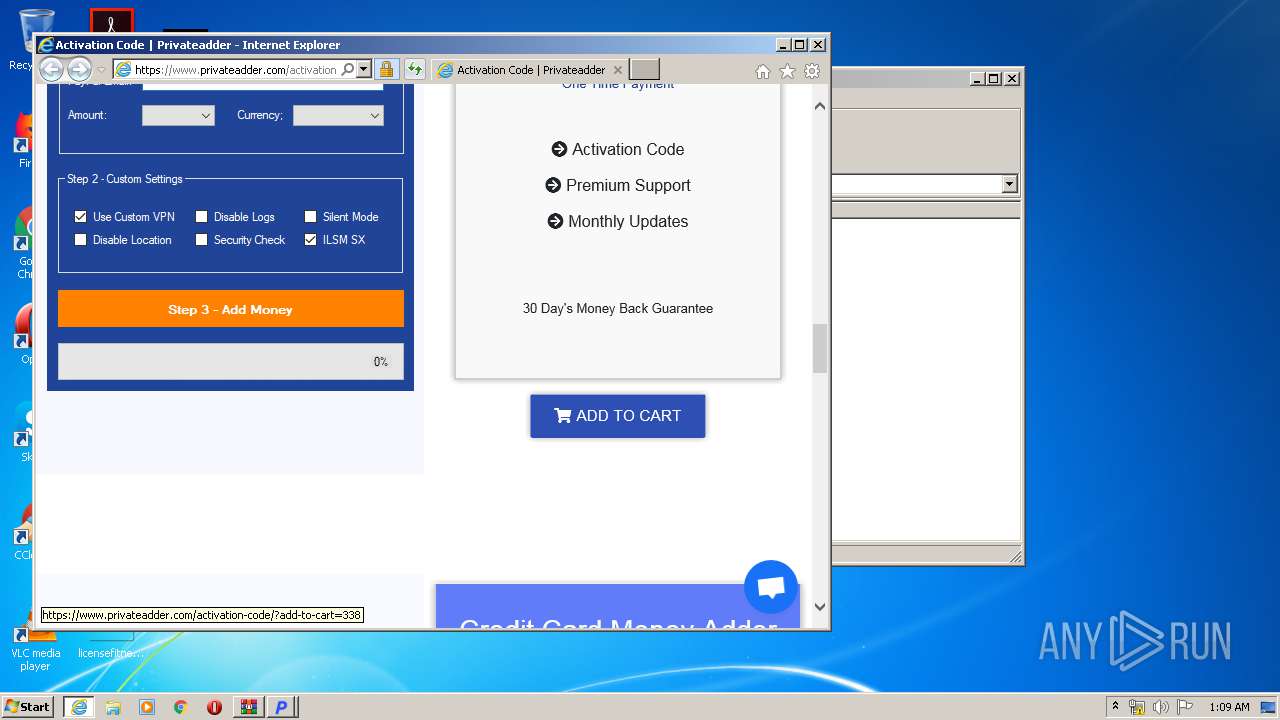
Starts Internet Explorer
- Bitcoin Money Adder - [Cracked By Badboy] - [C-Cracking.org].exe (PID: 3512)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3984)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3336)
Creates files in the user directory
- iexplore.exe (PID: 2772)
Application launched itself
- iexplore.exe (PID: 3336)
Reads internet explorer settings
- iexplore.exe (PID: 2772)
Reads Internet Cache Settings
- iexplore.exe (PID: 3336)
- iexplore.exe (PID: 2772)
Reads settings of System Certificates
- iexplore.exe (PID: 2772)
- iexplore.exe (PID: 3336)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3336)
Changes settings of System certificates
- iexplore.exe (PID: 3336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
38
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2772 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3336 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
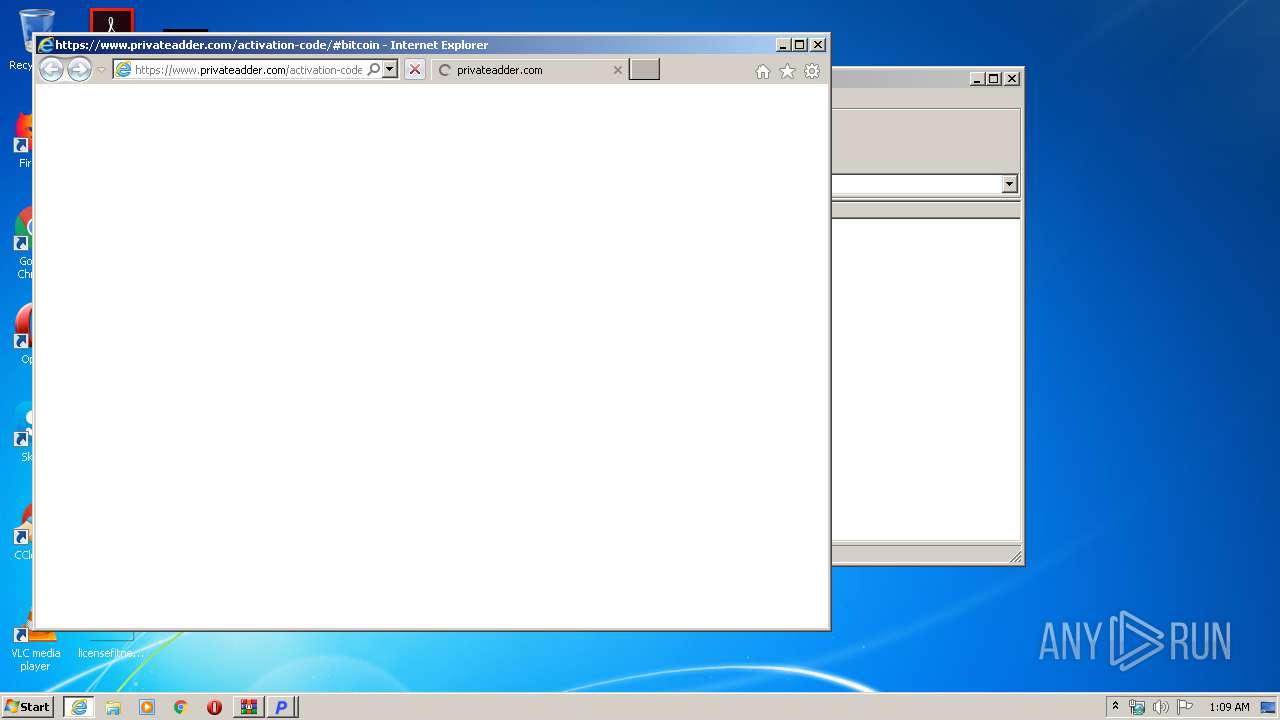
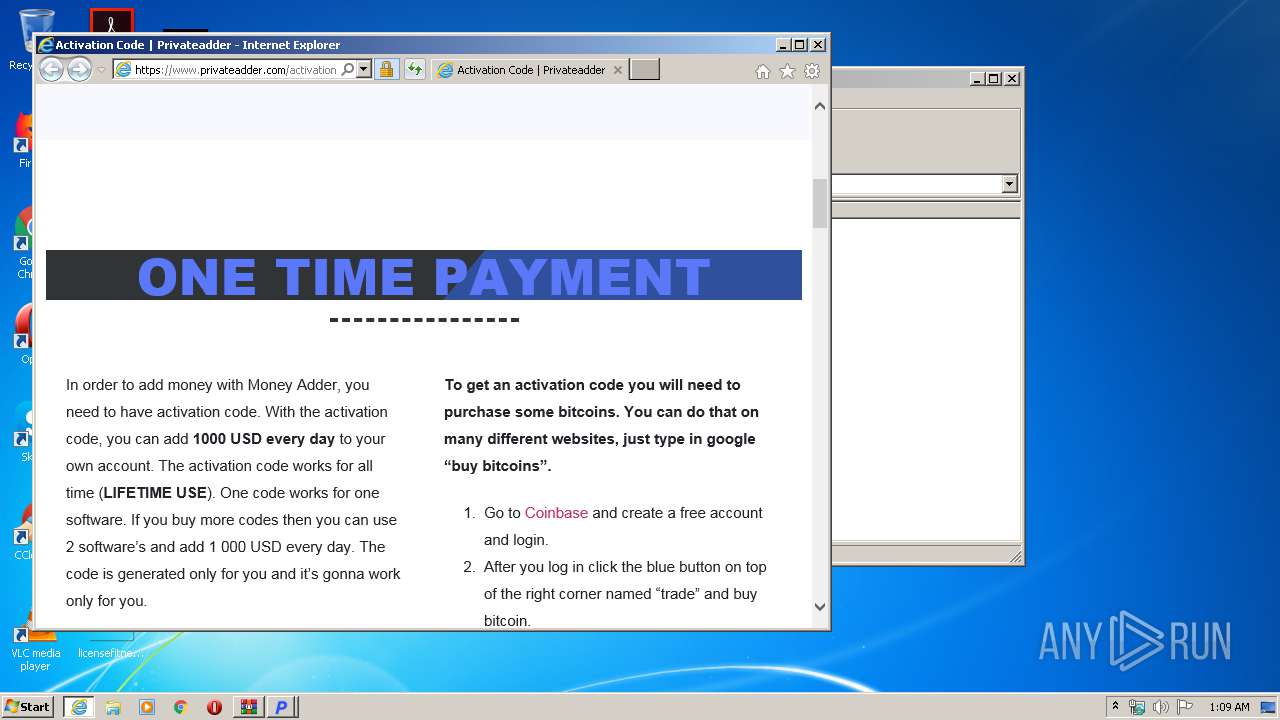
| 3336 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.privateadder.com/activation-code/#bitcoin | C:\Program Files\Internet Explorer\iexplore.exe | Bitcoin Money Adder - [Cracked By Badboy] - [C-Cracking.org].exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
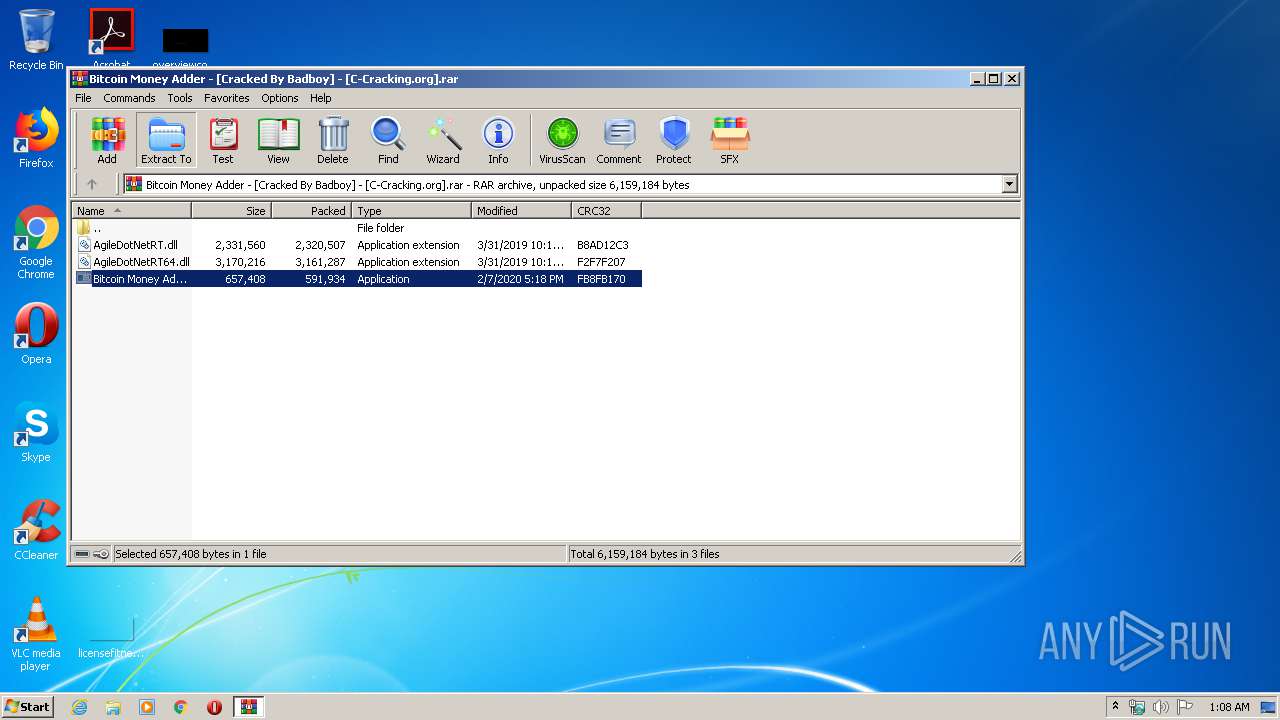
| 3512 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3984.3528\Bitcoin Money Adder - [Cracked By Badboy] - [C-Cracking.org].exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3984.3528\Bitcoin Money Adder - [Cracked By Badboy] - [C-Cracking.org].exe | — | WinRAR.exe | |||||||||||
User: admin Company: privateadder.com Integrity Level: MEDIUM Description: Bitcoin Money Adder Exit code: 0 Version: 4.0.0.0 Modules
| |||||||||||||||
| 3984 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Bitcoin Money Adder - [Cracked By Badboy] - [C-Cracking.org].rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
5 671
Read events
1 238
Write events
2 977
Delete events
1 456
Modification events
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Bitcoin Money Adder - [Cracked By Badboy] - [C-Cracking.org].rar | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
3
Suspicious files
39
Text files
28
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2772 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar189D.tmp | — | |
MD5:— | SHA256:— | |||
| 2772 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C1B3CC7FF1466C71640A202F8258105B_B4D464F572EA722672286FD2855D5C8D | binary | |
MD5:— | SHA256:— | |||
| 2772 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | der | |
MD5:— | SHA256:— | |||
| 2772 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C1B3CC7FF1466C71640A202F8258105B_B4D464F572EA722672286FD2855D5C8D | der | |
MD5:— | SHA256:— | |||
| 2772 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_74167E25E5476CCA2A5946AAA61BF9E1 | binary | |
MD5:— | SHA256:— | |||
| 2772 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\9XCGNBSH.txt | text | |
MD5:— | SHA256:— | |||
| 2772 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\activation-code[1].htm | html | |
MD5:— | SHA256:— | |||
| 2772 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5457A8CE4B2A7499F8299A013B6E1C7C_CE50F893881D43DC0C815E4D80FAF2B4 | der | |
MD5:— | SHA256:— | |||
| 2772 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5457A8CE4B2A7499F8299A013B6E1C7C_CE50F893881D43DC0C815E4D80FAF2B4 | binary | |
MD5:— | SHA256:— | |||
| 2772 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\671c44d6797e6dd9ce76d1681300bed3[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
34
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2772 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCECsuburZdTZsFIpu26N8jAc%3D | US | der | 727 b | whitelisted |
2772 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | US | der | 471 b | whitelisted |
2772 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
2772 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
2772 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEAUJOHw%2BEvvE86TwUxVW25c%3D | US | der | 279 b | whitelisted |
2772 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrBBNpPfHTPX6Jy6BVzyBPnBWMnQQUPnQtH89FdQR%2BP8Cihz5MQ4NRE8YCEAUJOHw%2BEvvE86TwUxVW25c%3D | US | der | 279 b | whitelisted |
2772 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | US | der | 471 b | whitelisted |
2772 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCECdm7lbrSfOOq9dwovyE3iI%3D | US | der | 471 b | whitelisted |
2772 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCECsuburZdTZsFIpu26N8jAc%3D | US | der | 727 b | whitelisted |
2772 | iexplore.exe | GET | 304 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCECsuburZdTZsFIpu26N8jAc%3D | US | der | 727 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2772 | iexplore.exe | 104.18.61.73:443 | www.privateadder.com | Cloudflare Inc | US | shared |
2772 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2772 | iexplore.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2772 | iexplore.exe | 104.20.37.161:443 | client.crisp.chat | Cloudflare Inc | US | shared |
2772 | iexplore.exe | 104.20.36.161:443 | client.crisp.chat | Cloudflare Inc | US | shared |
— | — | 104.20.37.161:443 | client.crisp.chat | Cloudflare Inc | US | shared |
3336 | iexplore.exe | 104.18.61.73:443 | www.privateadder.com | Cloudflare Inc | US | shared |
3336 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2772 | iexplore.exe | 104.248.10.131:443 | client.relay.crisp.chat | — | US | unknown |
2772 | iexplore.exe | 13.226.159.41:443 | ik.imagekit.io | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.privateadder.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
ik.imagekit.io |
| shared |
ocsp.usertrust.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
client.crisp.chat |
| whitelisted |
settings.crisp.chat |
| whitelisted |
client.relay.crisp.chat |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |