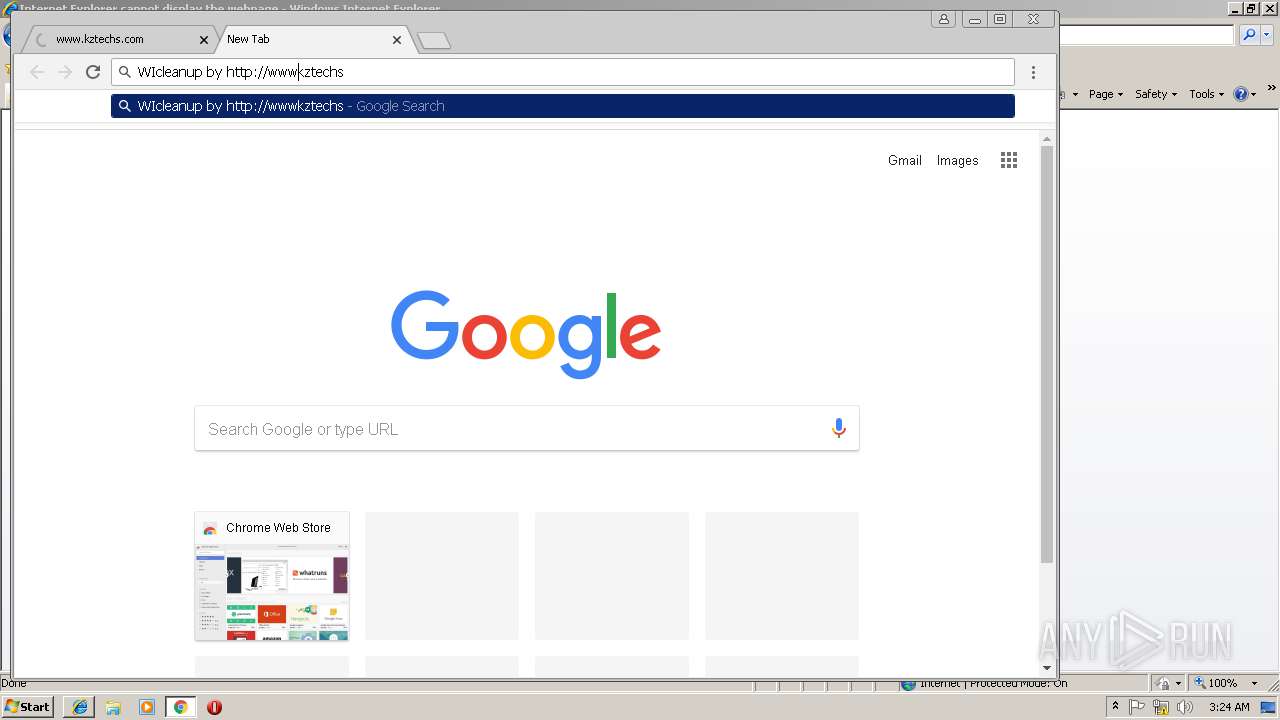
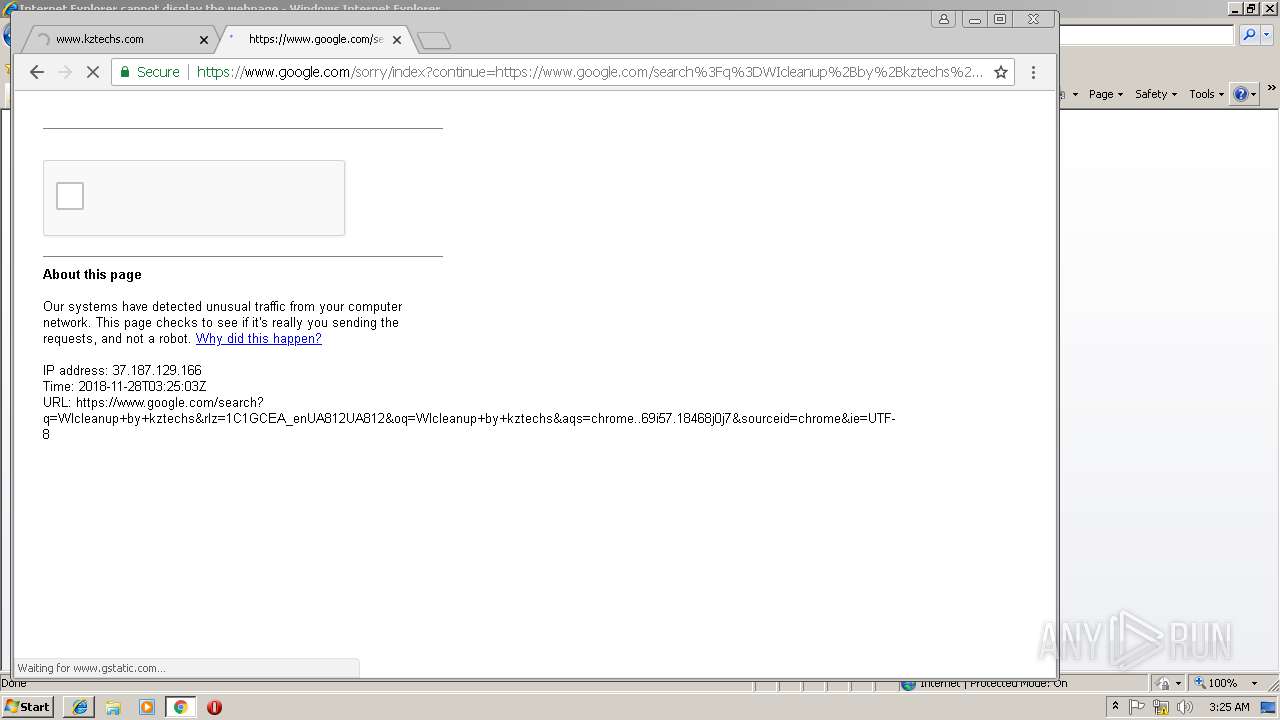
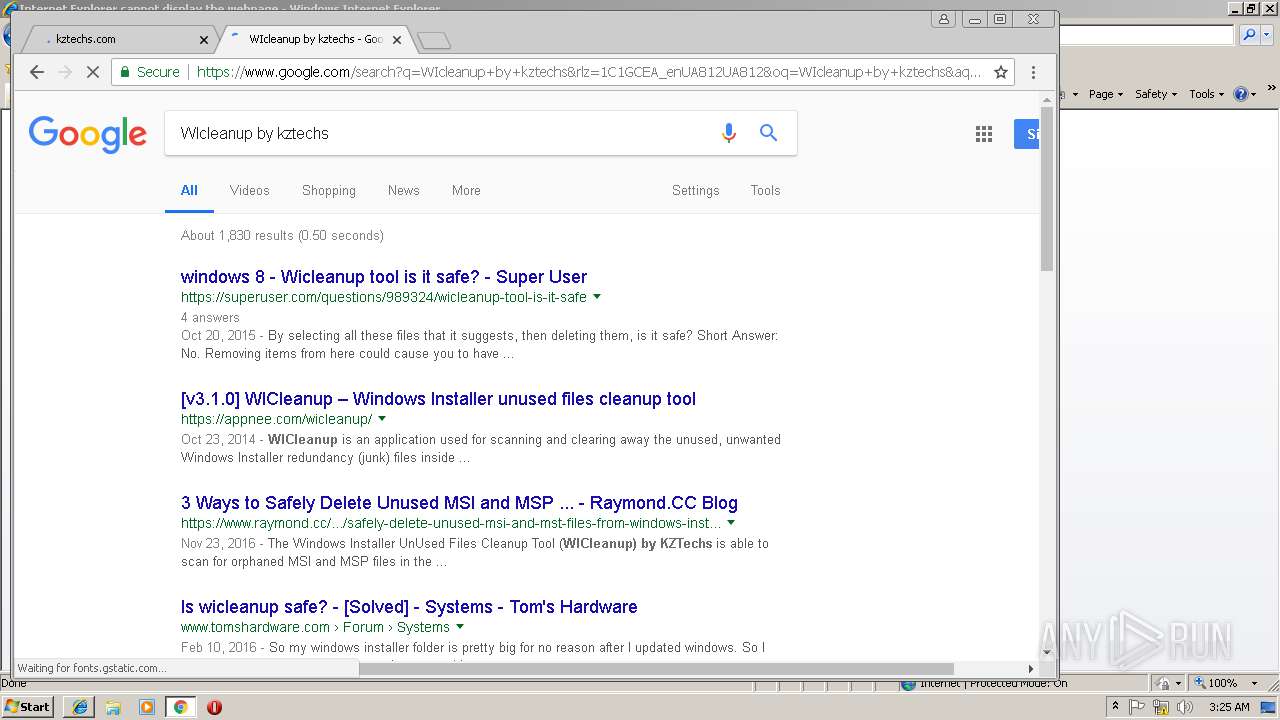
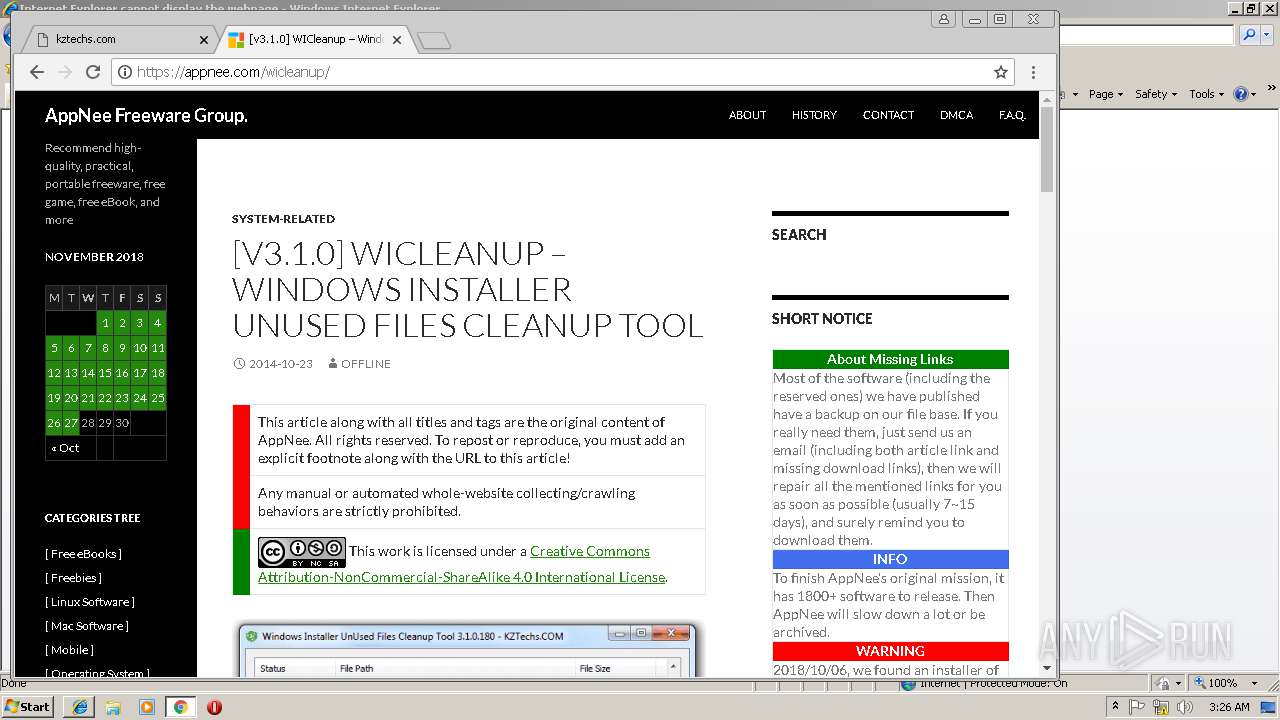
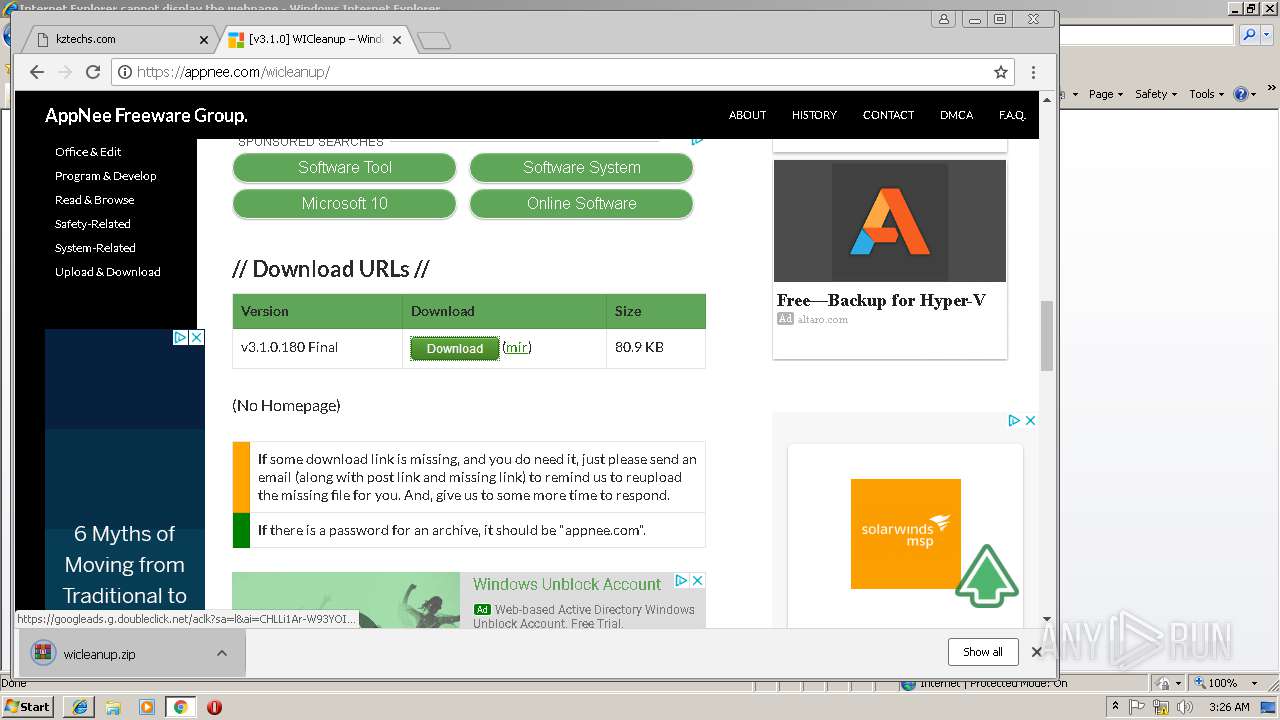
| URL: | http://www.kztechs.com/wicleanup |
| Full analysis: | https://app.any.run/tasks/9203e9de-0230-413a-87e6-376686a218cb |
| Verdict: | Malicious activity |
| Analysis date: | November 28, 2018, 03:23:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 07685CC940AADF130291CC6E48CDEA85 |
| SHA1: | 78515430239167E06E0326EC12D40AB4A8F1C68A |
| SHA256: | FF09F0A5B2A8CCB6EF551CFF0D4B4A728002E8375AC324E2277293E84DE83331 |
| SSDEEP: | 3:N1KJS4JdtSMeAELAn:Cc4JypA5 |
MALICIOUS
Application was dropped or rewritten from another process
- WICleanupUI.EXE (PID: 556)
- WICleanupC.EXE (PID: 3732)
- WICleanupUI.EXE (PID: 1476)
- WICleanupC.EXE (PID: 1852)
SUSPICIOUS
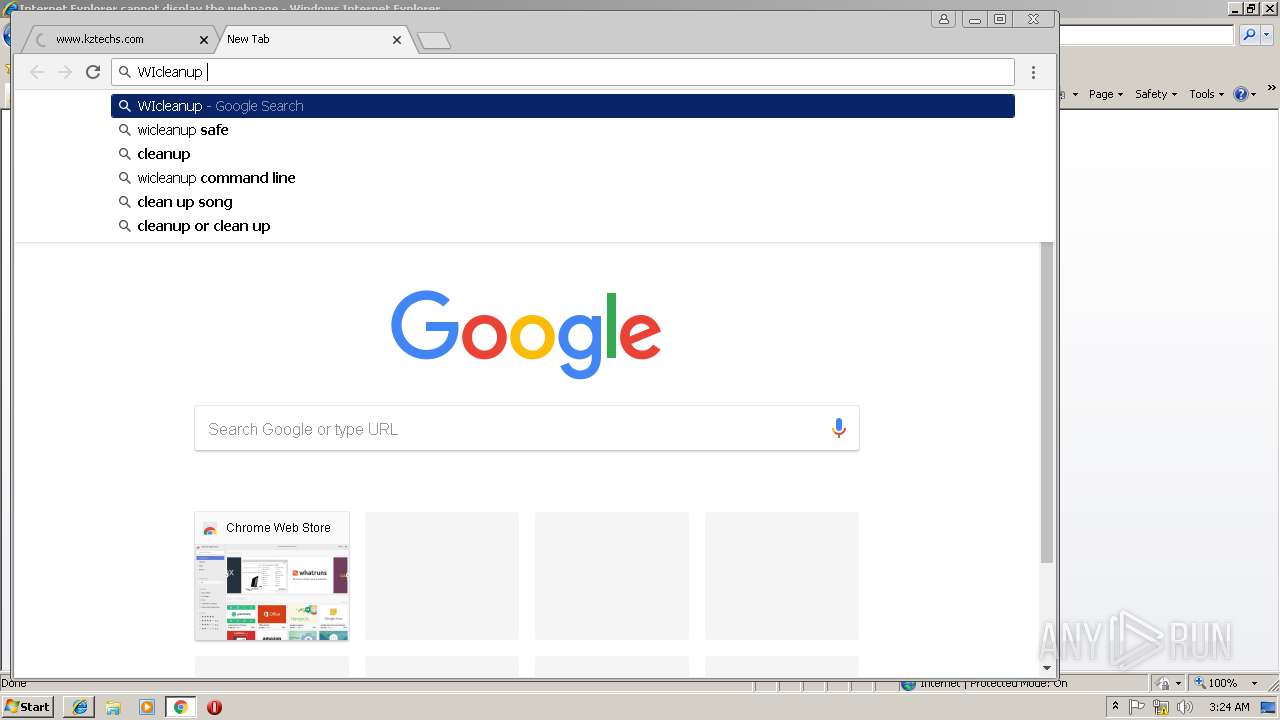
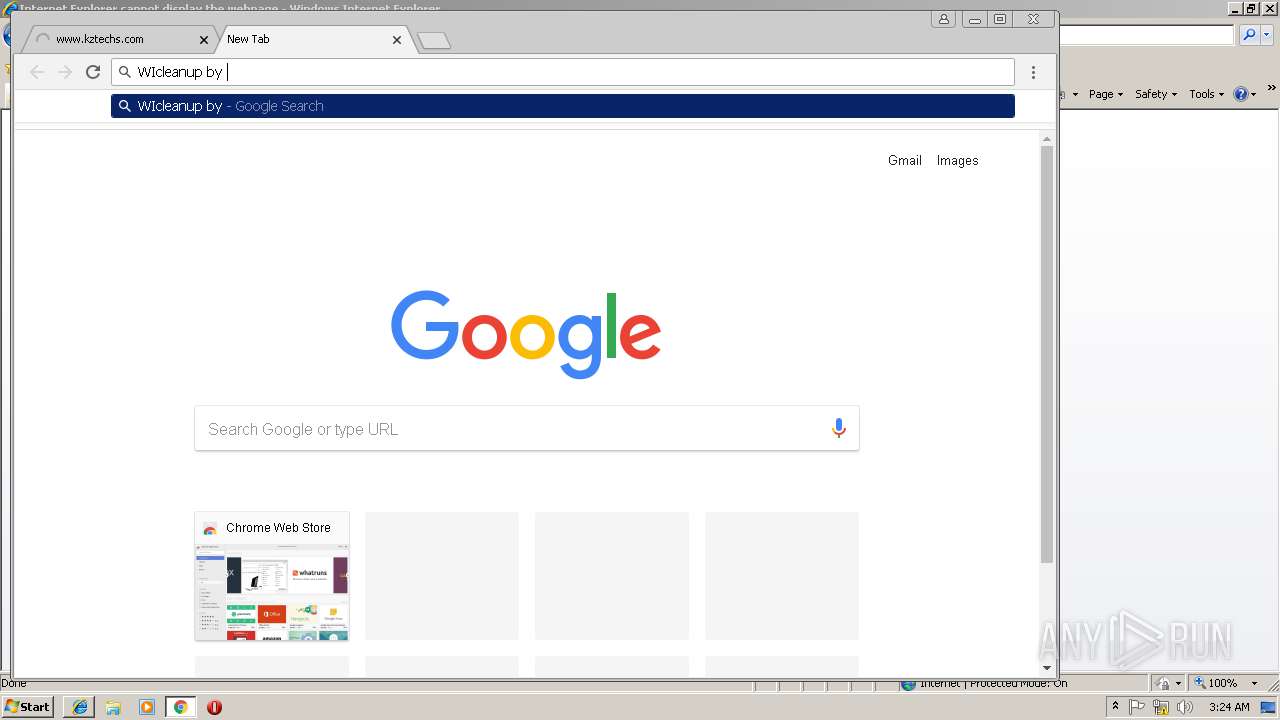
Reads internet explorer settings
- WICleanupUI.EXE (PID: 1476)
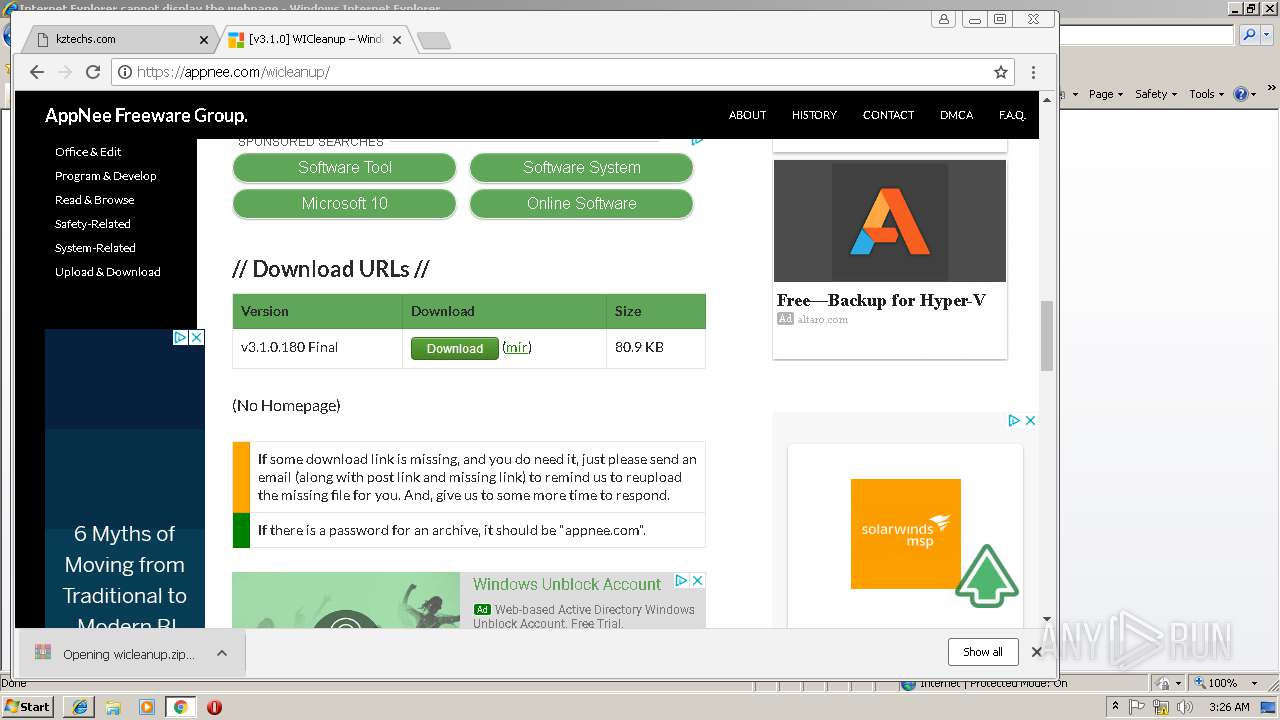
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1684)
INFO
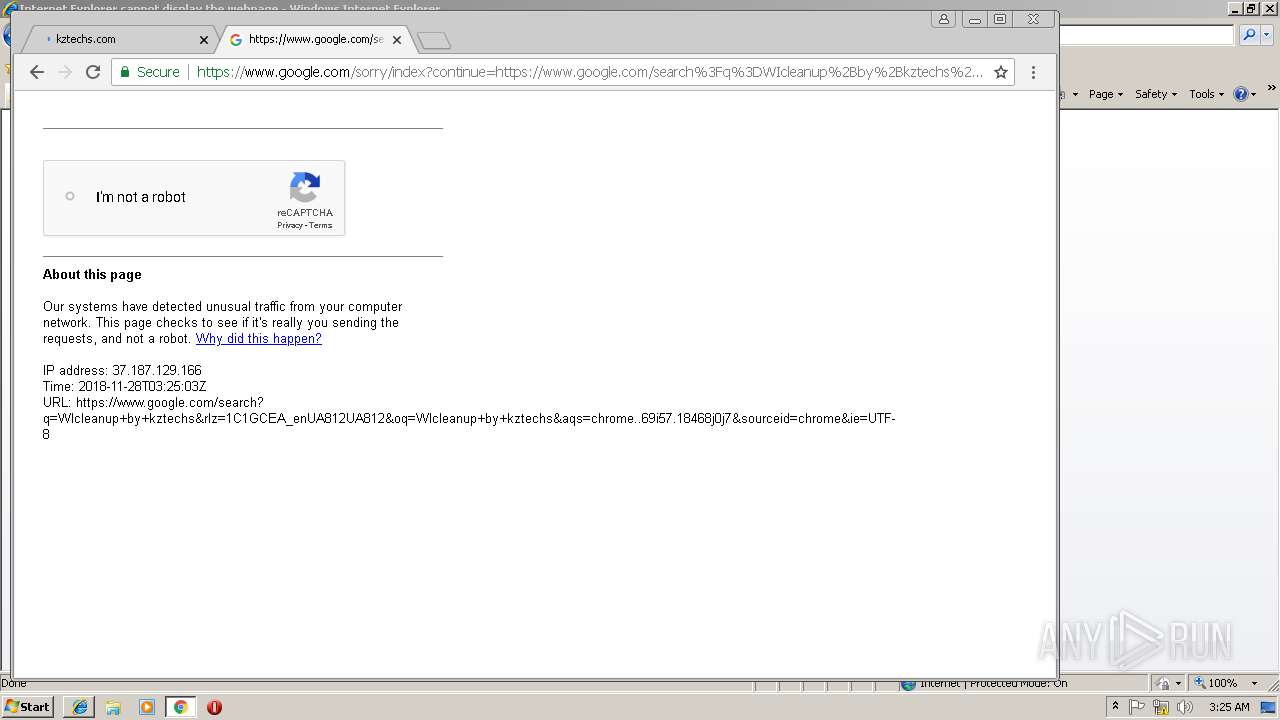
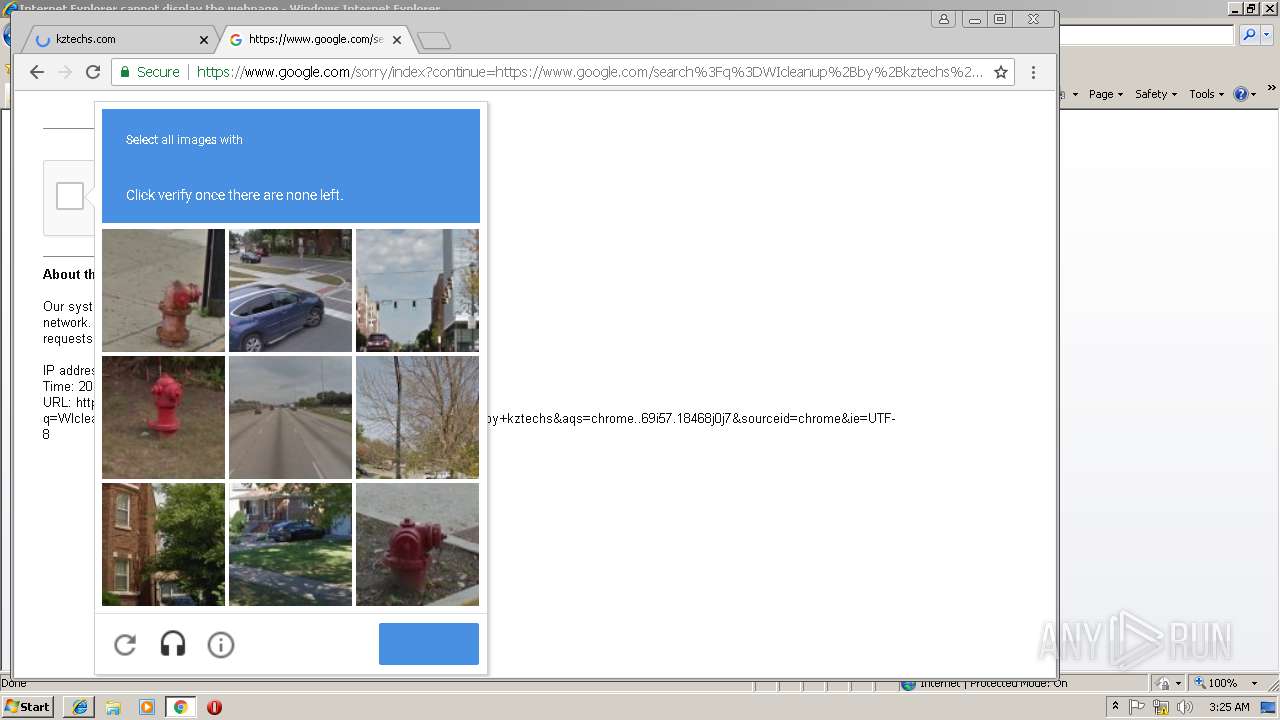
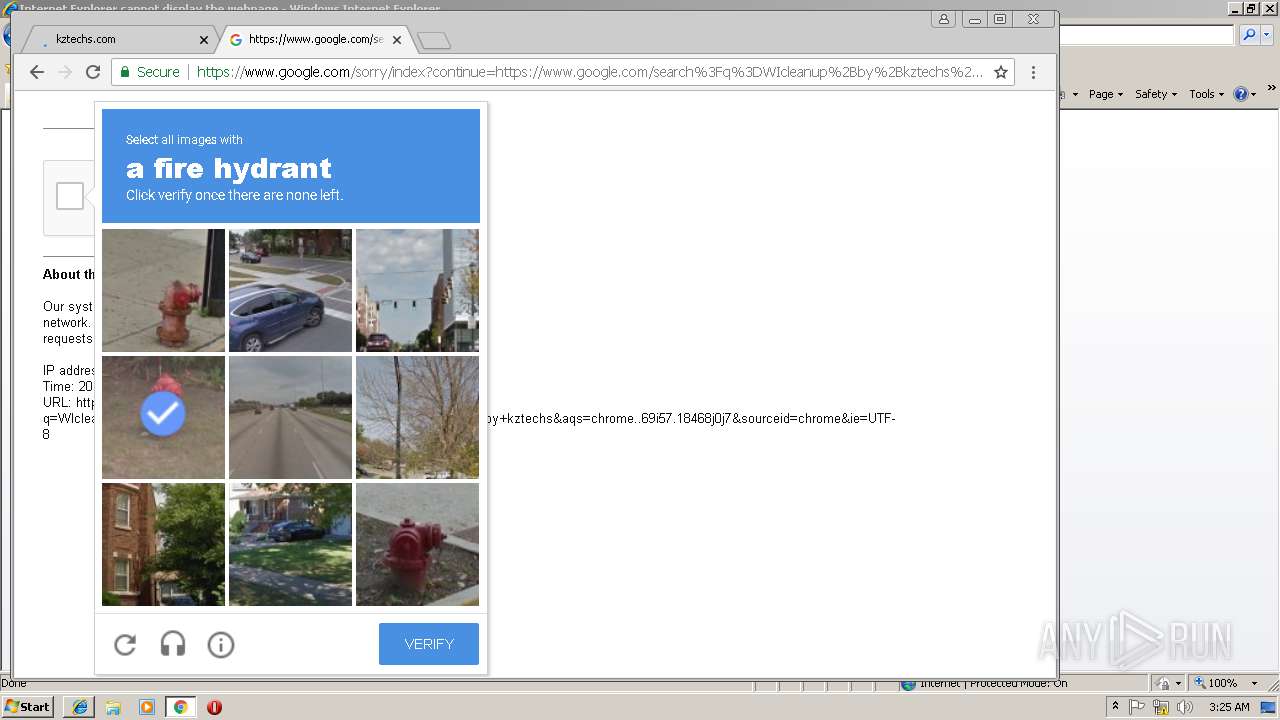
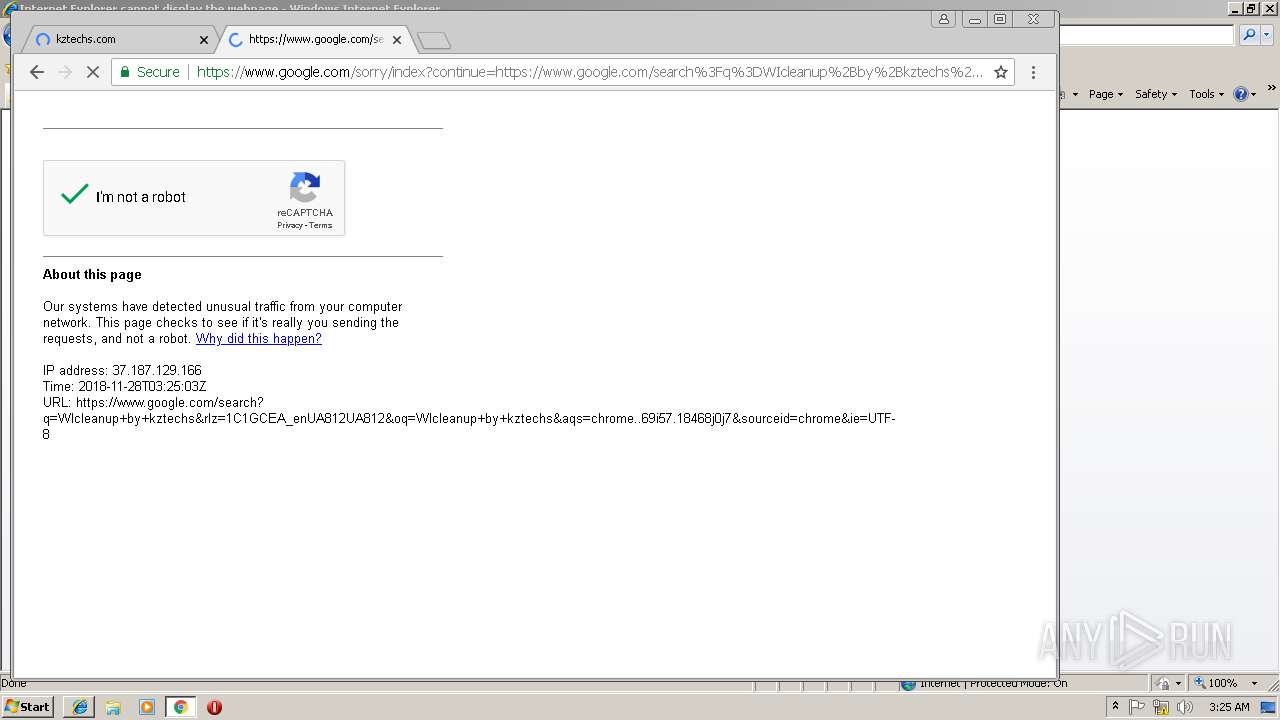
Changes internet zones settings
- iexplore.exe (PID: 3504)
Application launched itself
- iexplore.exe (PID: 3504)
- chrome.exe (PID: 3036)
Reads Internet Cache Settings
- iexplore.exe (PID: 3784)
- chrome.exe (PID: 3036)
Reads internet explorer settings
- iexplore.exe (PID: 3784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
24
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
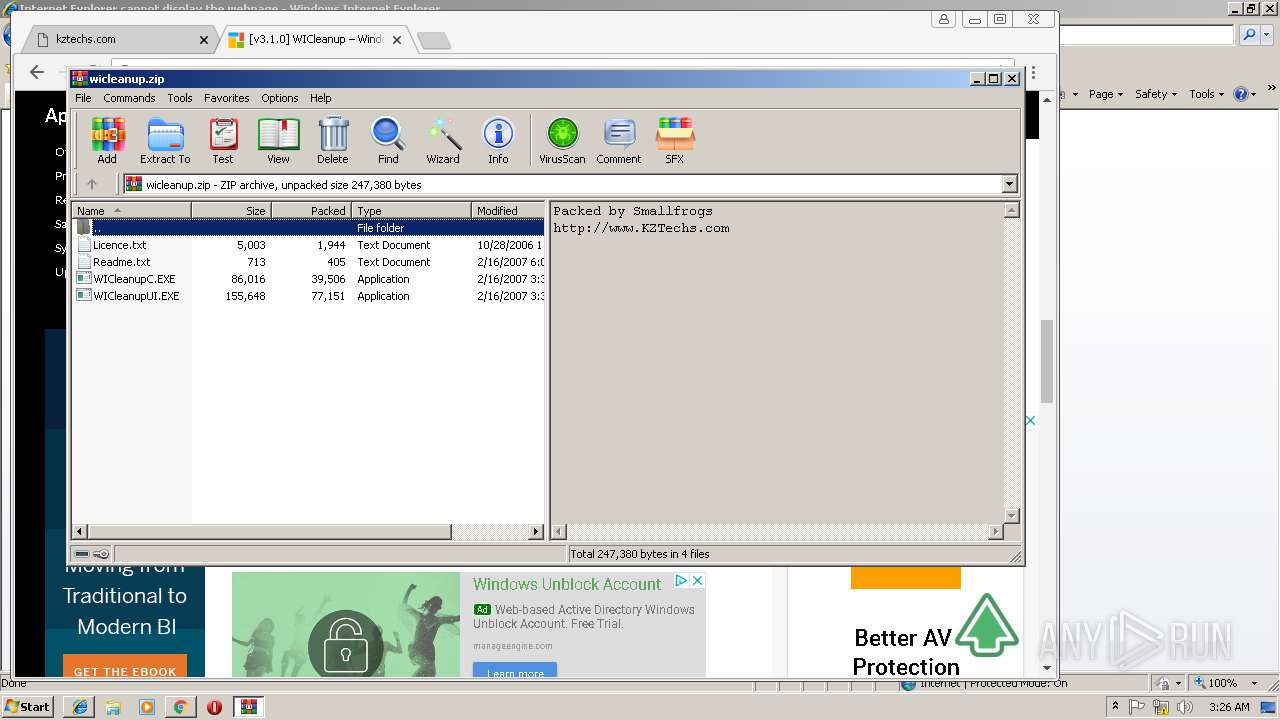
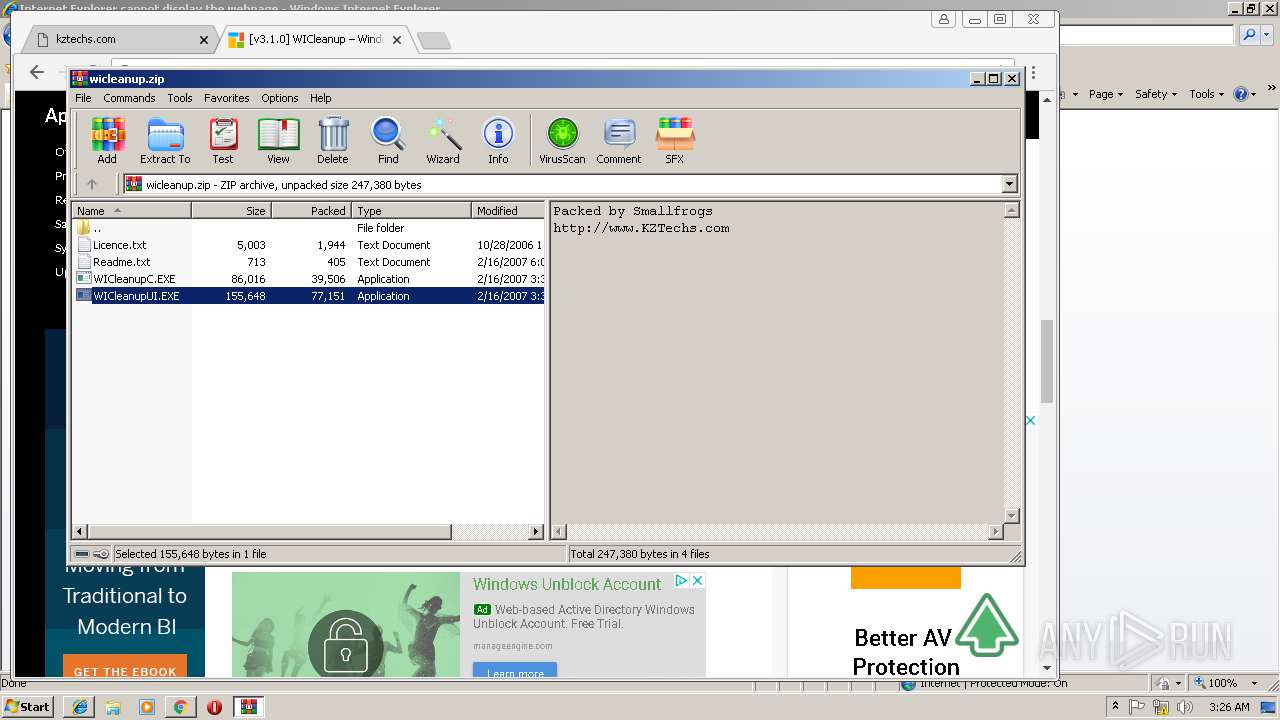
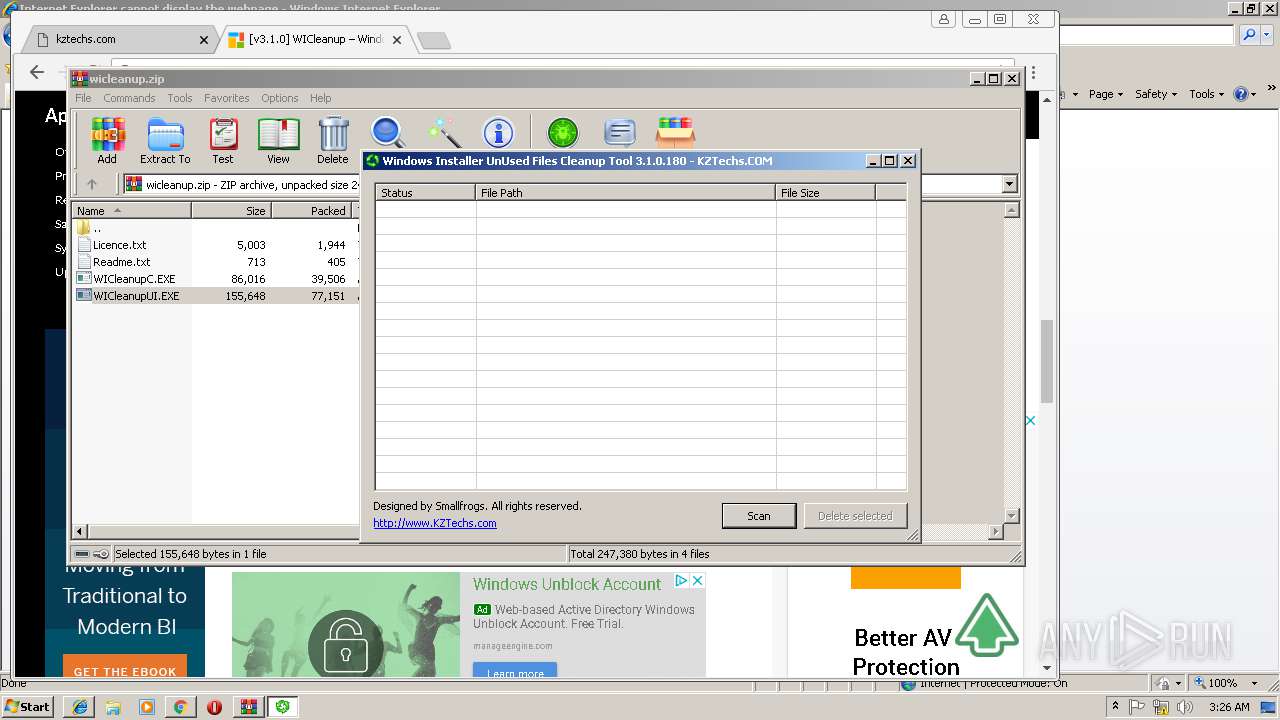
| 556 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1684.10177\WICleanupUI.EXE" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1684.10177\WICleanupUI.EXE | — | WinRAR.exe | |||||||||||
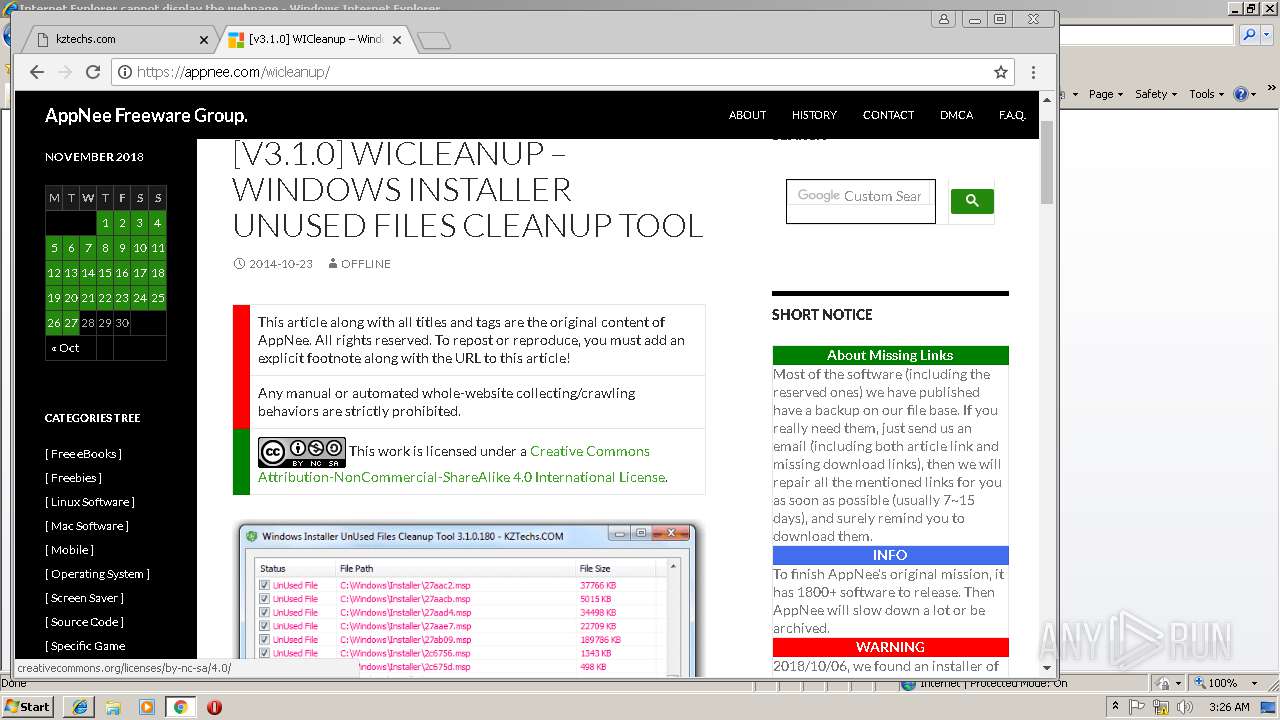
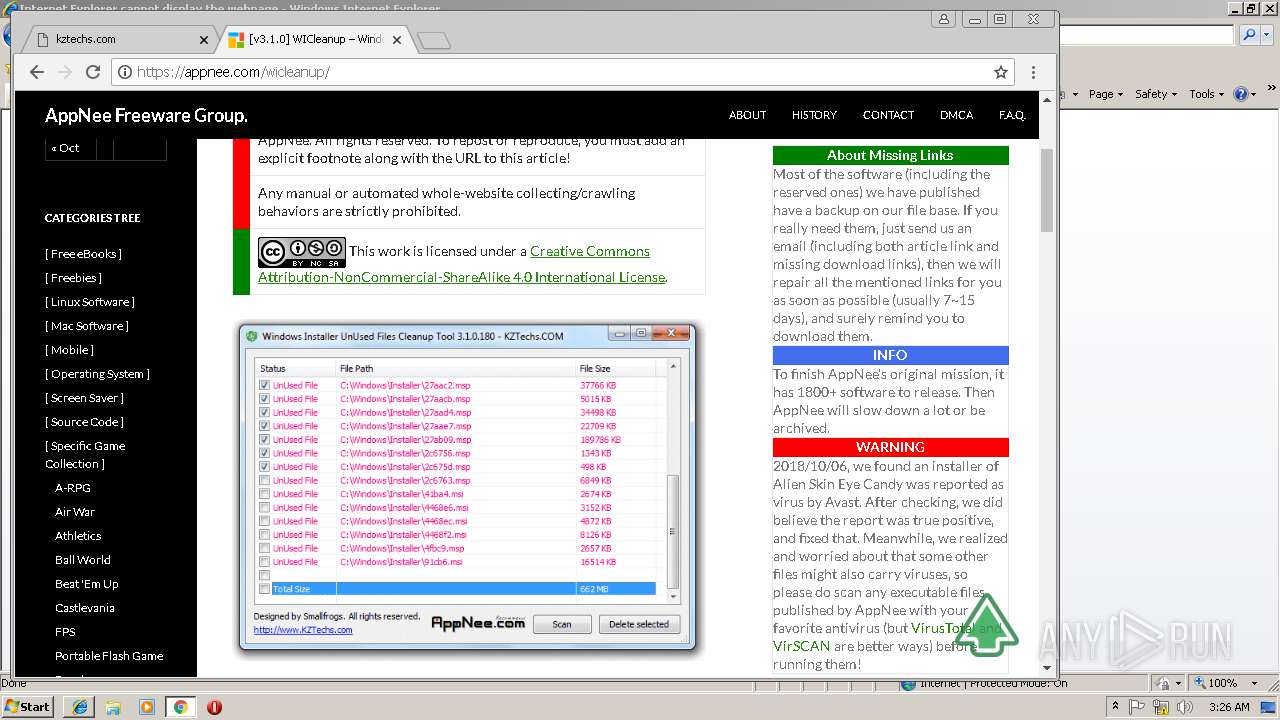
User: admin Company: Smallfrogs Studio Integrity Level: MEDIUM Description: Windows Installer UnUsed Files Cleanup Tool Exit code: 3221226540 Version: 3, 1, 0, 180 Modules
| |||||||||||||||
| 904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,3109898549533116112,5505573986152939345,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=B3111DCCECC0C8A6E8DDA3329662954F --mojo-platform-channel-handle=4620 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,3109898549533116112,5505573986152939345,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=D57B0C4493E5C067970D49BCC149E39D --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=D57B0C4493E5C067970D49BCC149E39D --renderer-client-id=15 --mojo-platform-channel-handle=3488 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1476 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1684.10177\WICleanupUI.EXE" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1684.10177\WICleanupUI.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Smallfrogs Studio Integrity Level: HIGH Description: Windows Installer UnUsed Files Cleanup Tool Exit code: 0 Version: 3, 1, 0, 180 Modules
| |||||||||||||||
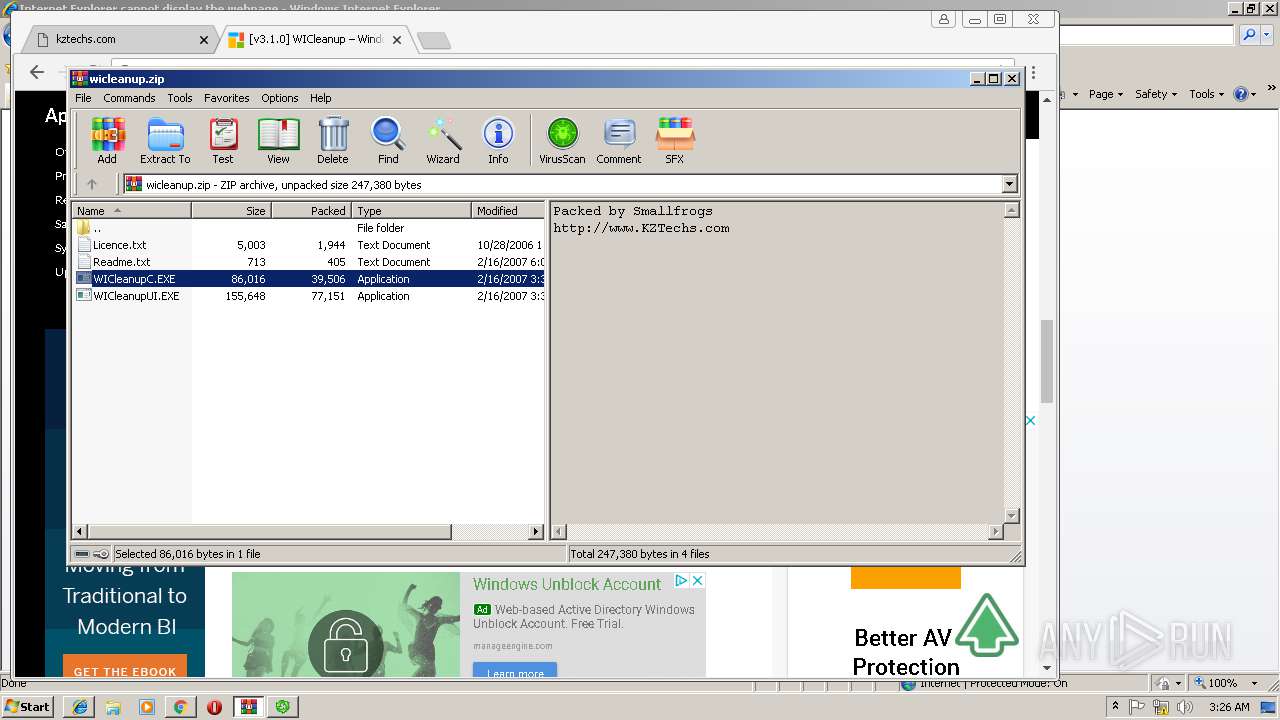
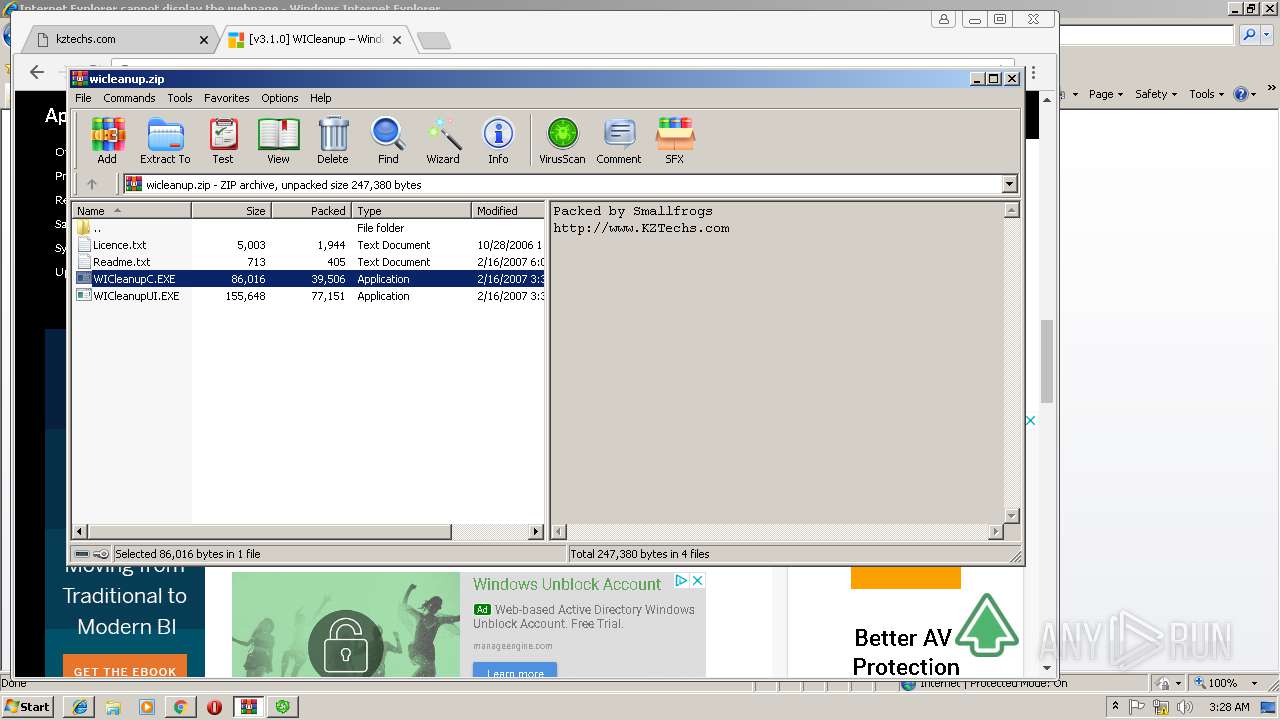
| 1684 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\wicleanup.zip" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1852 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1684.11299\WICleanupC.EXE" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1684.11299\WICleanupC.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Smallfrogs Studio Integrity Level: MEDIUM Description: Windows Installer UnUsed Files Cleanup Tool Exit code: 3221226540 Version: 3, 1, 0, 180 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3044 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,3109898549533116112,5505573986152939345,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=D63024330B3ECE5F9CAD52D8A767FA17 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=D63024330B3ECE5F9CAD52D8A767FA17 --renderer-client-id=7 --mojo-platform-channel-handle=3608 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,3109898549533116112,5505573986152939345,131072 --enable-features=PasswordImport --service-pipe-token=E5498AB97E5560FF7383C4FDD47ED2A7 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E5498AB97E5560FF7383C4FDD47ED2A7 --renderer-client-id=3 --mojo-platform-channel-handle=2036 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=968,3109898549533116112,5505573986152939345,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=52AB6836FAB287CF5DDAD92A3BBD375A --mojo-platform-channel-handle=1028 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 788
Read events
1 616
Write events
168
Delete events
4
Modification events
| (PID) Process: | (3504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {00C249D9-F2BD-11E8-834A-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3504) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070B0003001C00030017002A002E02 | |||
Executable files
4
Suspicious files
126
Text files
162
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3504 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3504 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3504 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 3784 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\httpErrorPagesScripts[1] | text | |
MD5:E7CA76A3C9EE0564471671D500E3F0F3 | SHA256:58268CA71A28973B756A48BBD7C9DC2F6B87B62AE343E582CE067C725275B63C | |||
| 3784 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\info_48[1] | image | |
MD5:49E0EF03E74704089A60C437085DB89E | SHA256:CAA140523BA00994536B33618654E379216261BABAAE726164A0F74157BB11FF | |||
| 3784 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\http_404[1] | html | |
MD5:4CD84A1B063BF6DEA53E06755EF9E24D | SHA256:988CC4B451673F847D823C9D9BA14AD50D3CA1141BC1E17C6415B8F64B6E1C22 | |||
| 3784 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\bullet[1] | image | |
MD5:0C4C086DD852704E8EEB8FF83E3B73D1 | SHA256:1CB3B6EA56C5B5DECF5E1D487AD51DBB2F62E6A6C78F23C1C81FDA1B64F8DB16 | |||
| 3784 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\ErrorPageTemplate[1] | text | |
MD5:F4FE1CB77E758E1BA56B8A8EC20417C5 | SHA256:8D018639281B33DA8EB3CE0B21D11E1D414E59024C3689F92BE8904EB5779B5F | |||
| 3784 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\errorPageStrings[1] | text | |
MD5:1A0563F7FB85A678771450B131ED66FD | SHA256:EB5678DE9D8F29CA6893D4E6CA79BD5AB4F312813820FE4997B009A2B1A1654C | |||
| 3784 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\down[1] | image | |
MD5:555E83CE7F5D280D7454AF334571FB25 | SHA256:70F316A5492848BB8242D49539468830B353DDAA850964DB4E60A6D2D7DB4880 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
92
DNS requests
49
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
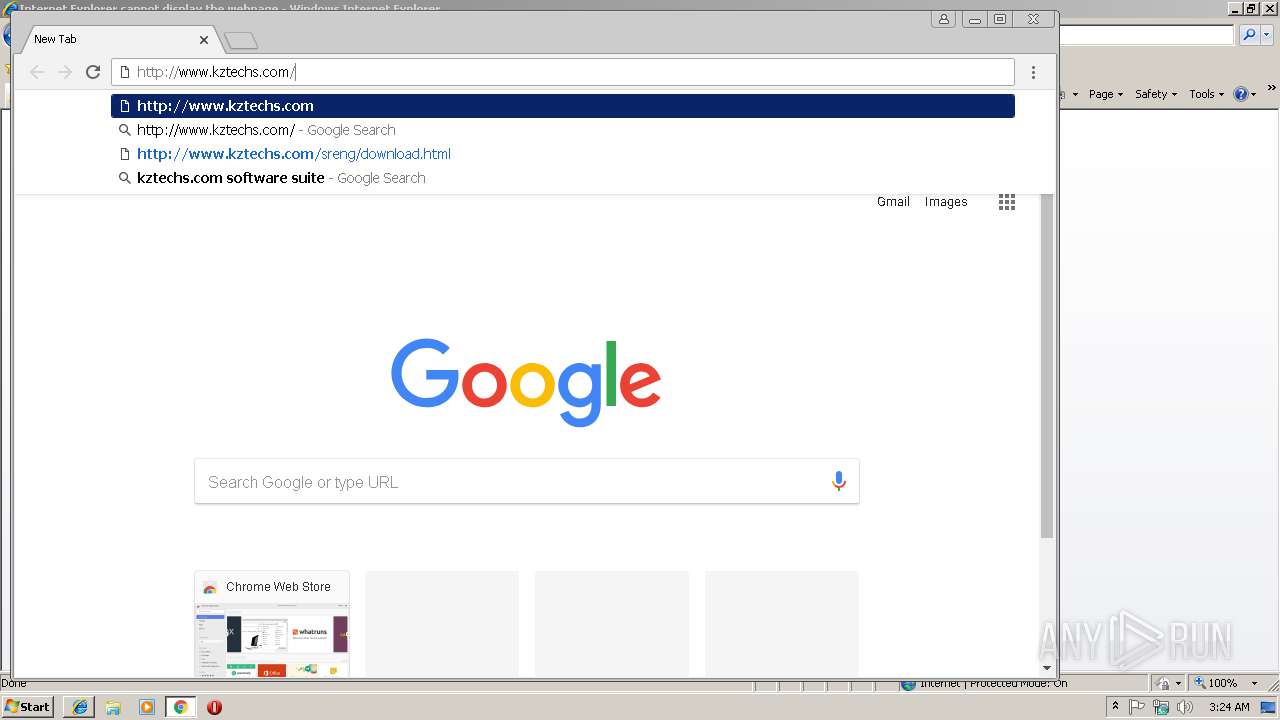
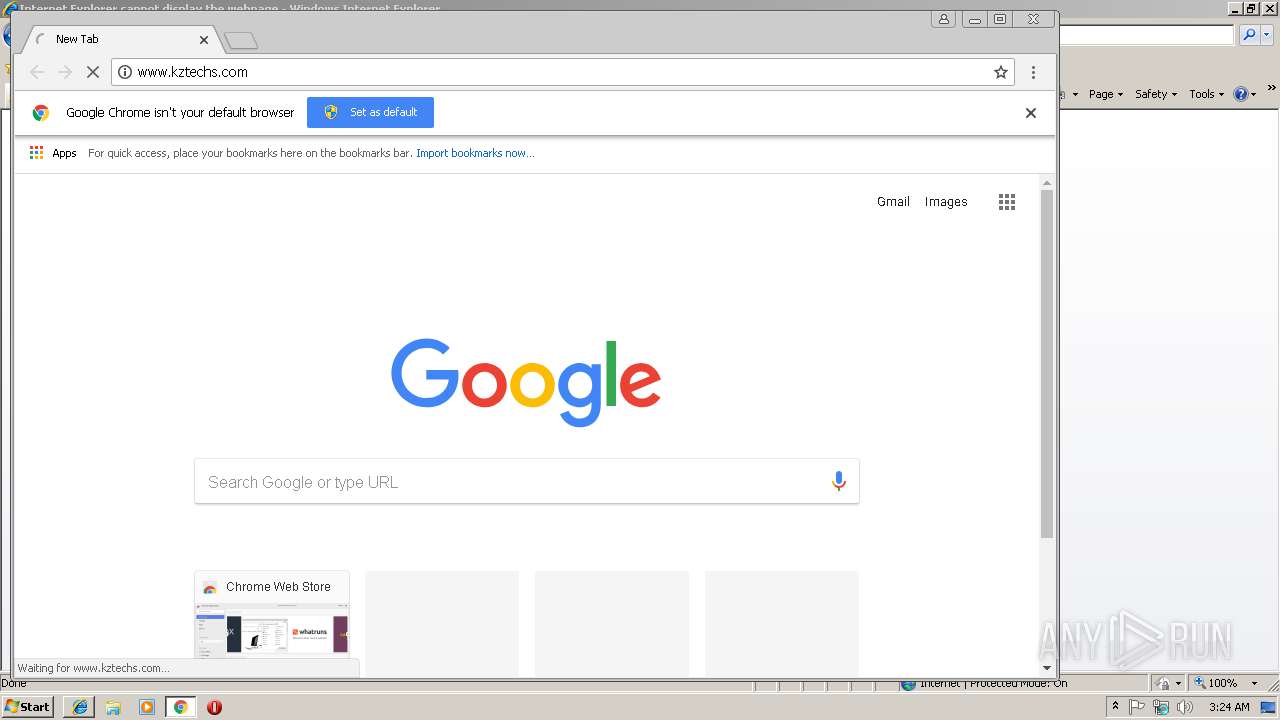
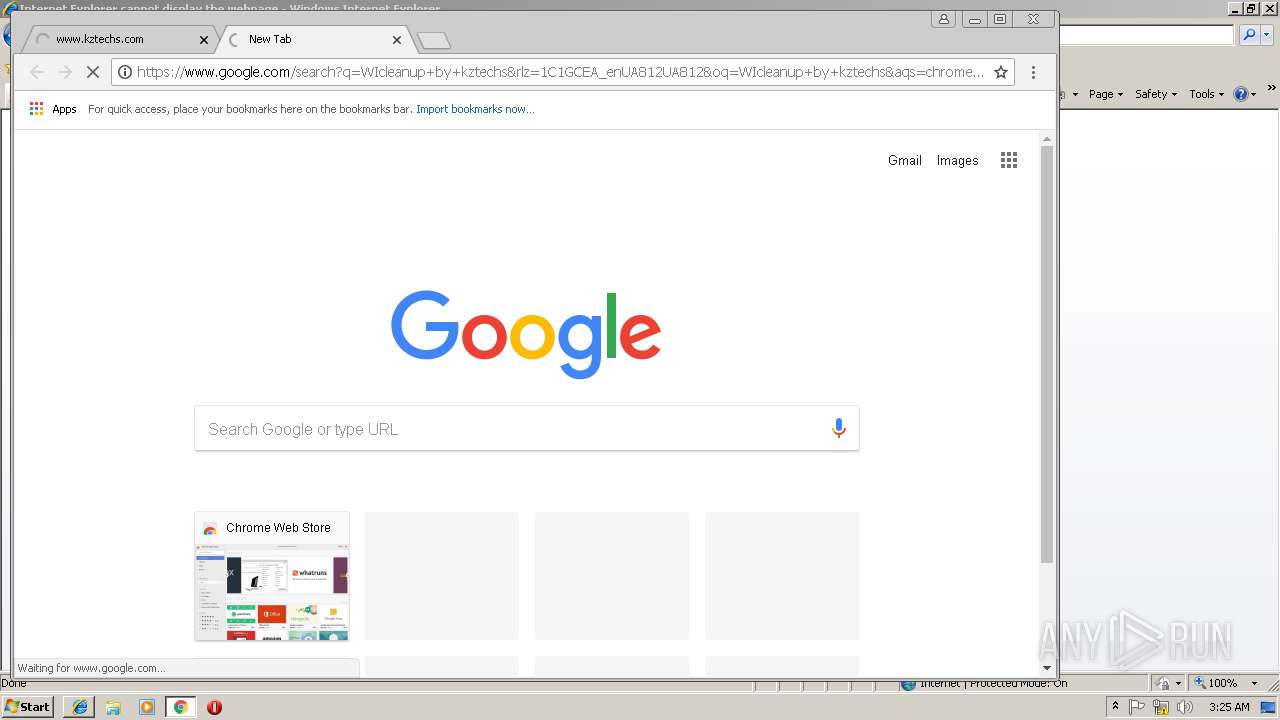
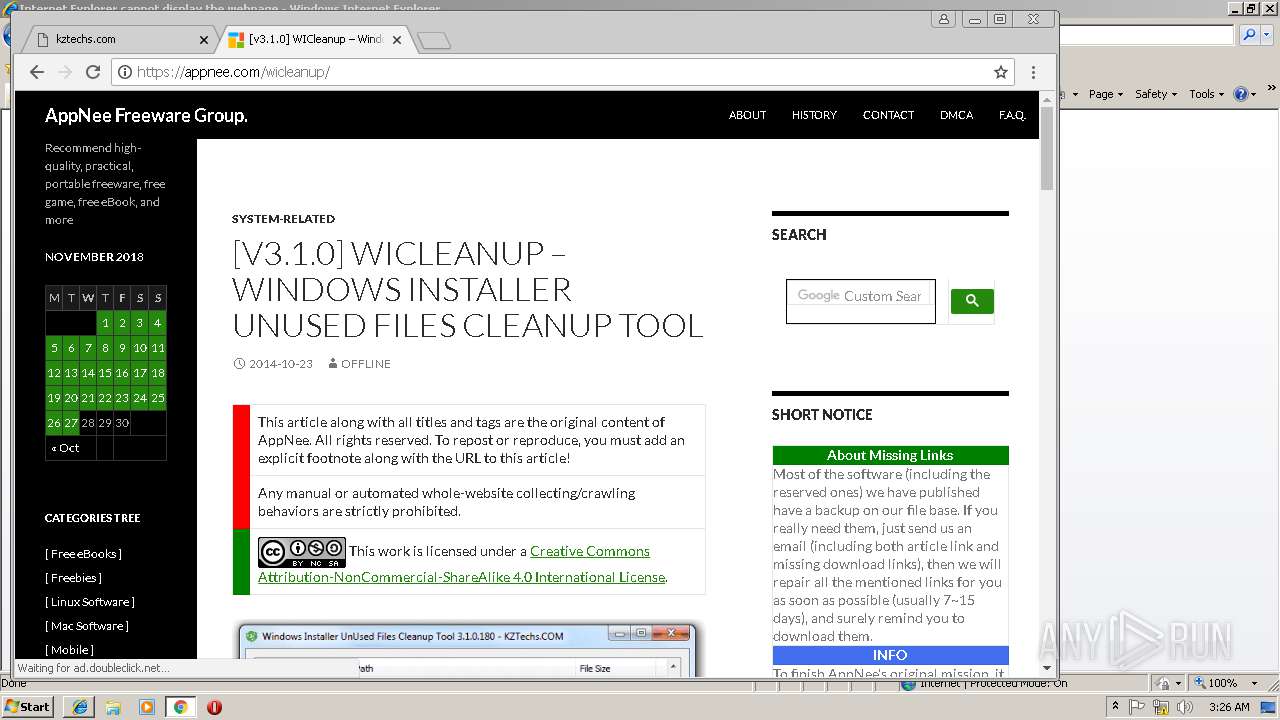
3784 | iexplore.exe | GET | — | 184.168.221.48:80 | http://www.kztechs.com/wicleanup | US | — | — | whitelisted |
3784 | iexplore.exe | GET | — | 184.168.221.48:80 | http://www.kztechs.com/ | US | — | — | whitelisted |
3784 | iexplore.exe | GET | — | 184.168.221.48:80 | http://www.kztechs.com/NpVoZ/wicleanup | US | — | — | whitelisted |
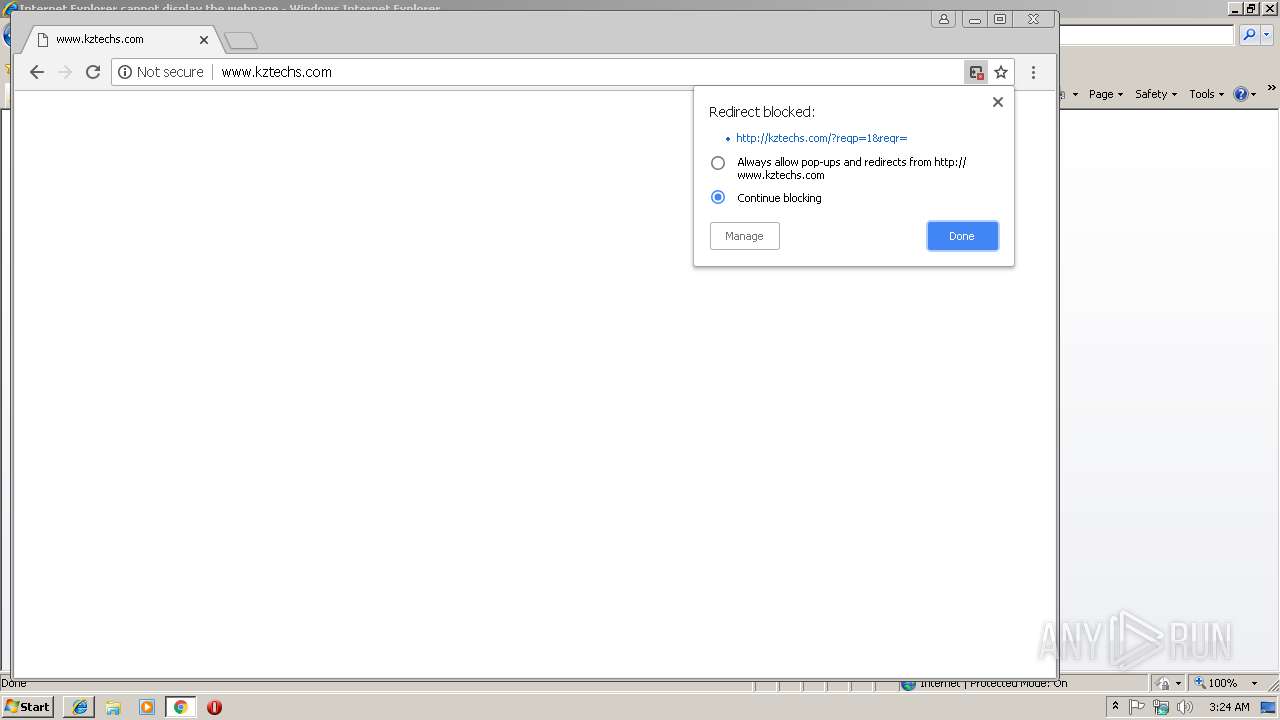
3036 | chrome.exe | GET | — | 184.168.221.48:80 | http://www.kztechs.com/ | US | — | — | whitelisted |
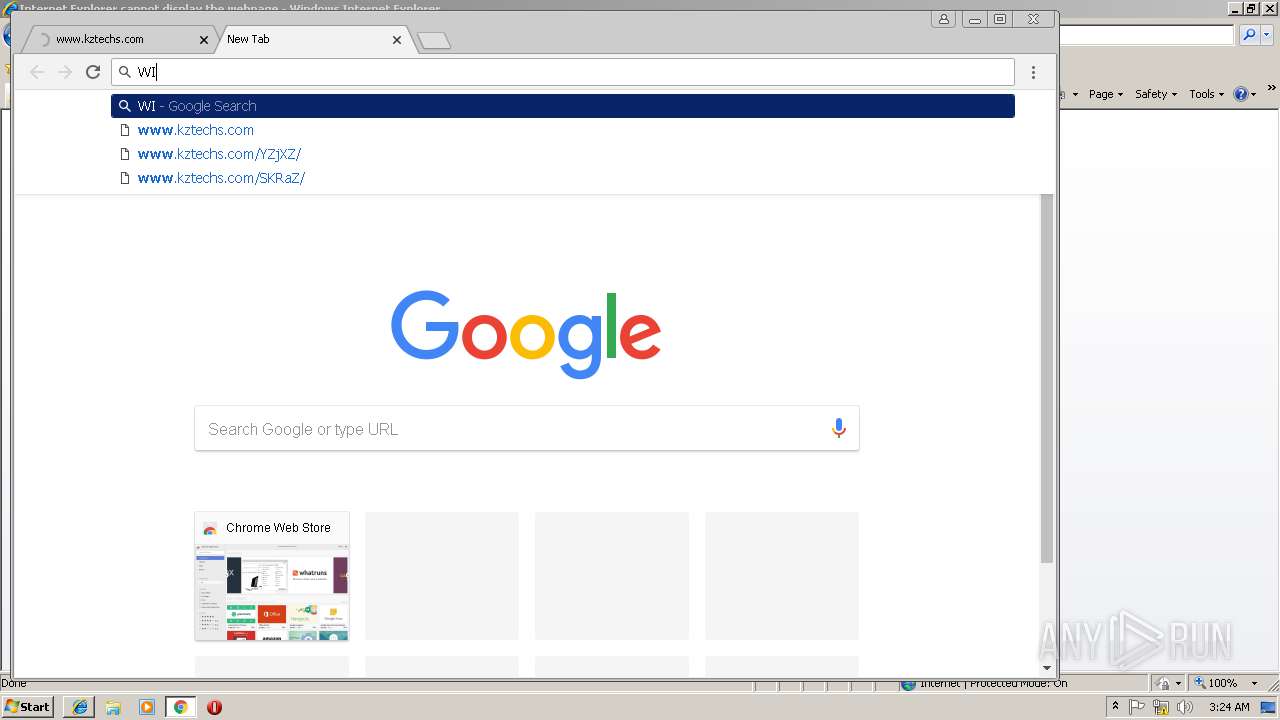
3036 | chrome.exe | GET | — | 184.168.221.48:80 | http://www.kztechs.com/YZjXZ/ | US | — | — | whitelisted |
3036 | chrome.exe | GET | — | 50.63.202.45:80 | http://kztechs.com/?reqp=1&reqr= | US | — | — | whitelisted |
3036 | chrome.exe | GET | — | 50.63.202.45:80 | http://kztechs.com/XbhiZ/?reqp=1&reqr= | US | — | — | whitelisted |
3036 | chrome.exe | GET | 200 | 184.168.131.213:80 | http://mcc.godaddy.com/park/rT1apaO1Mv5jLab= | US | html | 183 b | whitelisted |
3036 | chrome.exe | GET | 200 | 184.168.221.48:80 | http://www.kztechs.com/ | US | html | 374 b | whitelisted |
3036 | chrome.exe | GET | 200 | 95.100.252.51:80 | http://ak2.imgaft.com/images/new_logo_GDTrans.png | unknown | image | 3.72 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3504 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3784 | iexplore.exe | 184.168.221.48:80 | www.kztechs.com | GoDaddy.com, LLC | US | malicious |
3036 | chrome.exe | 172.217.19.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3036 | chrome.exe | 184.168.221.48:80 | www.kztechs.com | GoDaddy.com, LLC | US | malicious |
3036 | chrome.exe | 172.217.168.196:443 | www.google.com | Google Inc. | US | whitelisted |
3036 | chrome.exe | 172.217.19.206:443 | apis.google.com | Google Inc. | US | whitelisted |
3036 | chrome.exe | 172.217.19.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3036 | chrome.exe | 184.168.131.213:80 | mcc.godaddy.com | GoDaddy.com, LLC | US | unknown |
3036 | chrome.exe | 50.63.202.45:80 | kztechs.com | GoDaddy.com, LLC | US | malicious |
3036 | chrome.exe | 23.217.186.149:443 | www.godaddy.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.kztechs.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1476 | WICleanupUI.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Zbot Generic URI/Header Struct .bin |
1476 | WICleanupUI.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Zbot Generic URI/Header Struct .bin |
1476 | WICleanupUI.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Zbot Generic URI/Header Struct .bin |