| File name: | depends.exe |
| Full analysis: | https://app.any.run/tasks/abacc356-39bb-455f-810b-2de37ad858c5 |
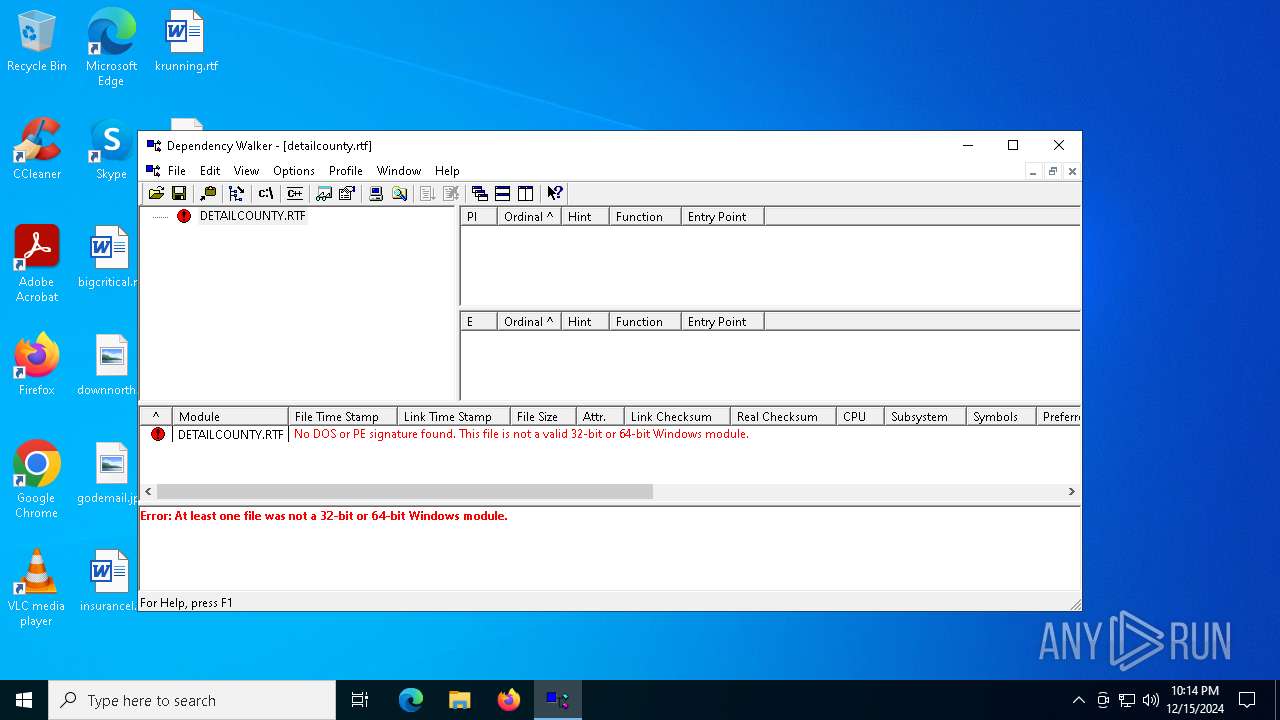
| Verdict: | Malicious activity |
| Analysis date: | December 15, 2024, 22:13:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 (stripped to external PDB), for MS Windows, 12 sections |
| MD5: | C638A62BD2FE7B52788183EDBC85D335 |
| SHA1: | A67299AB73BC6D952A52481BF640167F2F3F5750 |
| SHA256: | FF006C9EDEBCADB8675C6EF17F8D860E59212410E10945ECA1F62EC20812702A |
| SSDEEP: | 24576:bNcX/GwaD/i6Pr/LJlcwkyyygJJJZZtJJJZZMlrc9XfgLrA:bNcX/GdD/i6Pr/LJlAyyygJJJZZtJJJI |
MALICIOUS
No malicious indicators.SUSPICIOUS
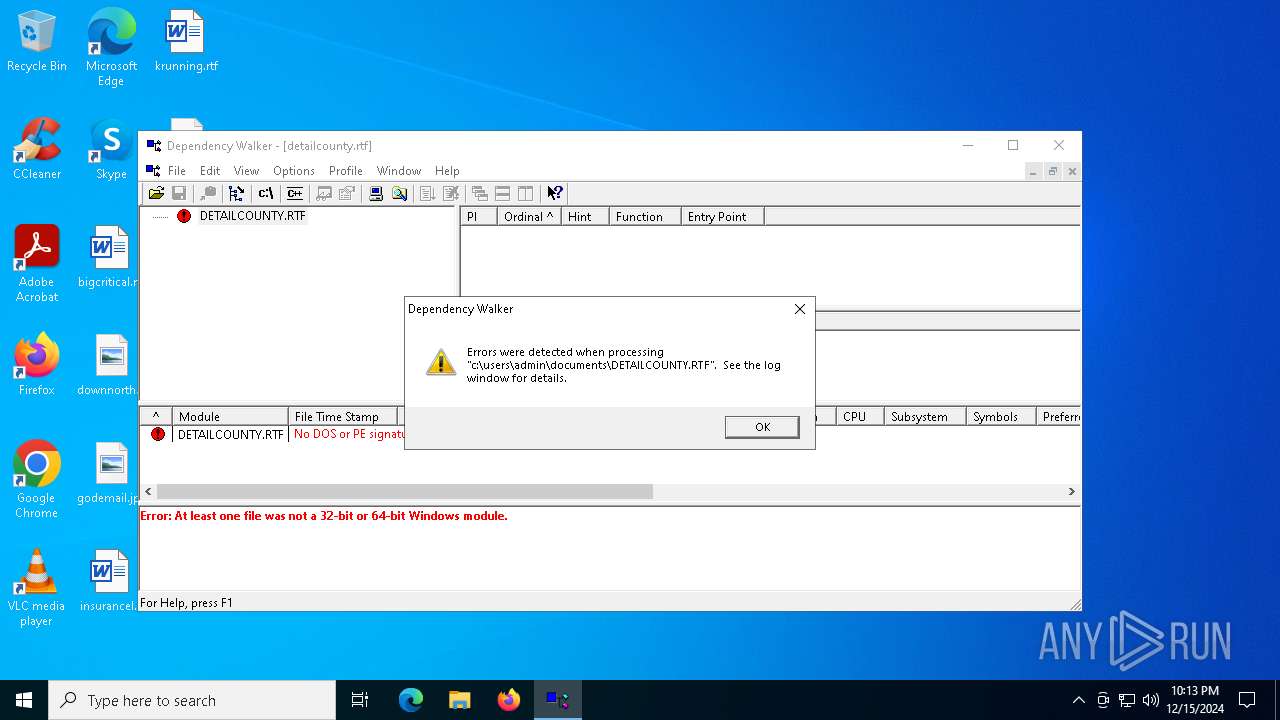
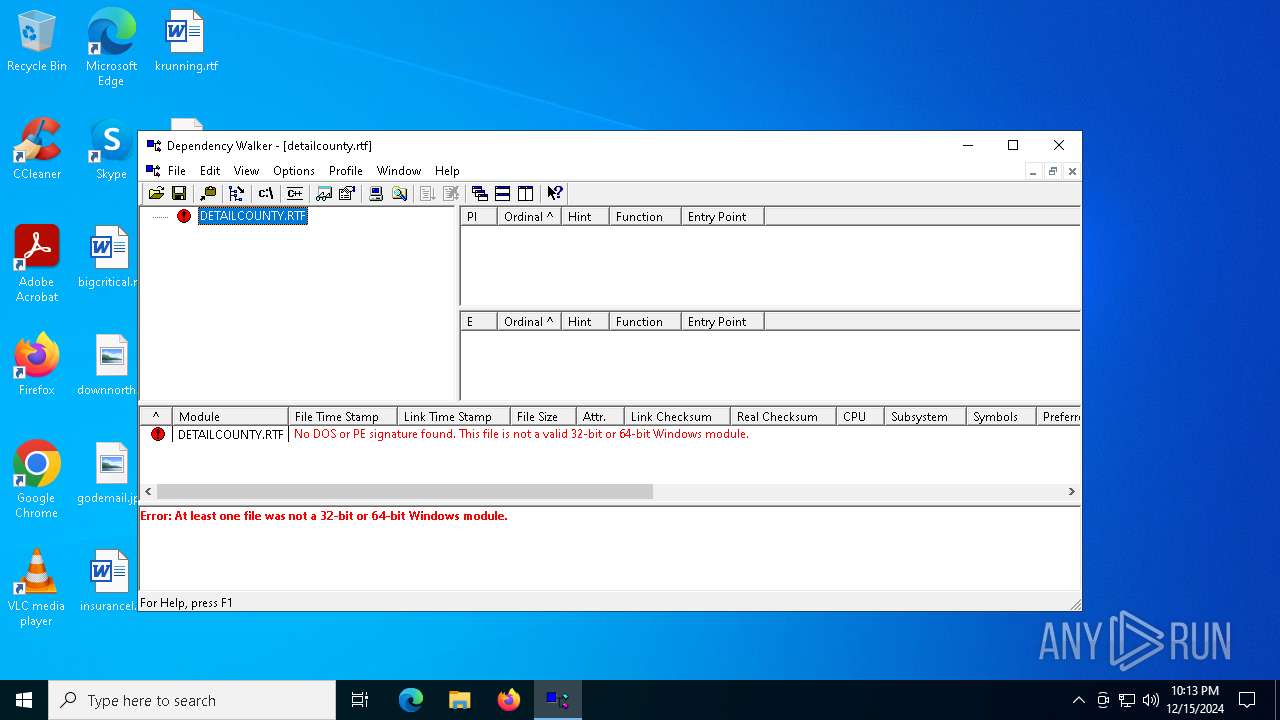
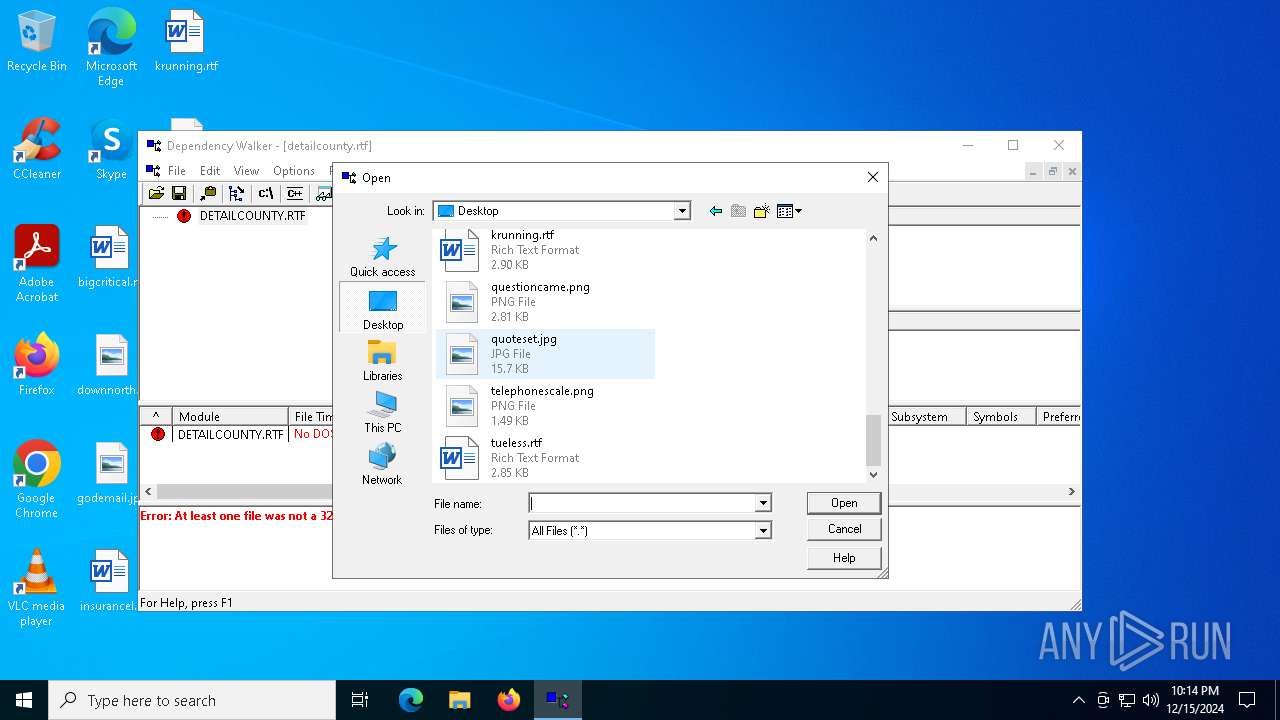
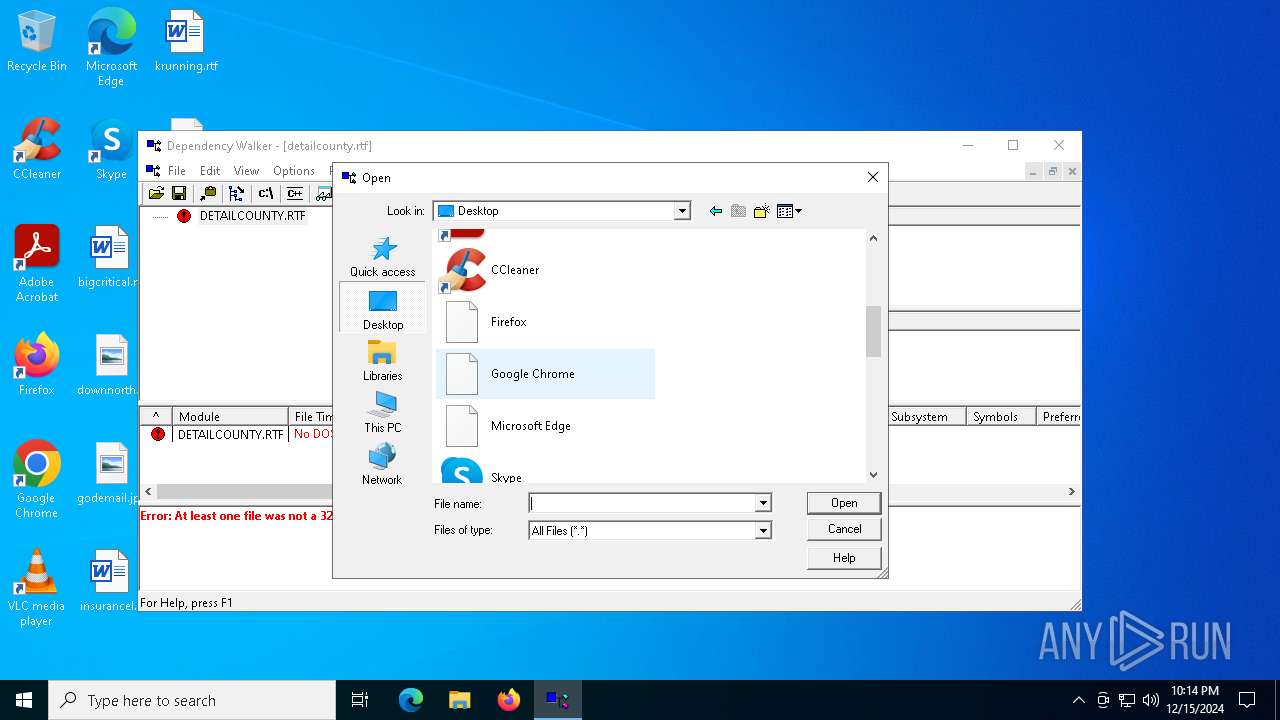
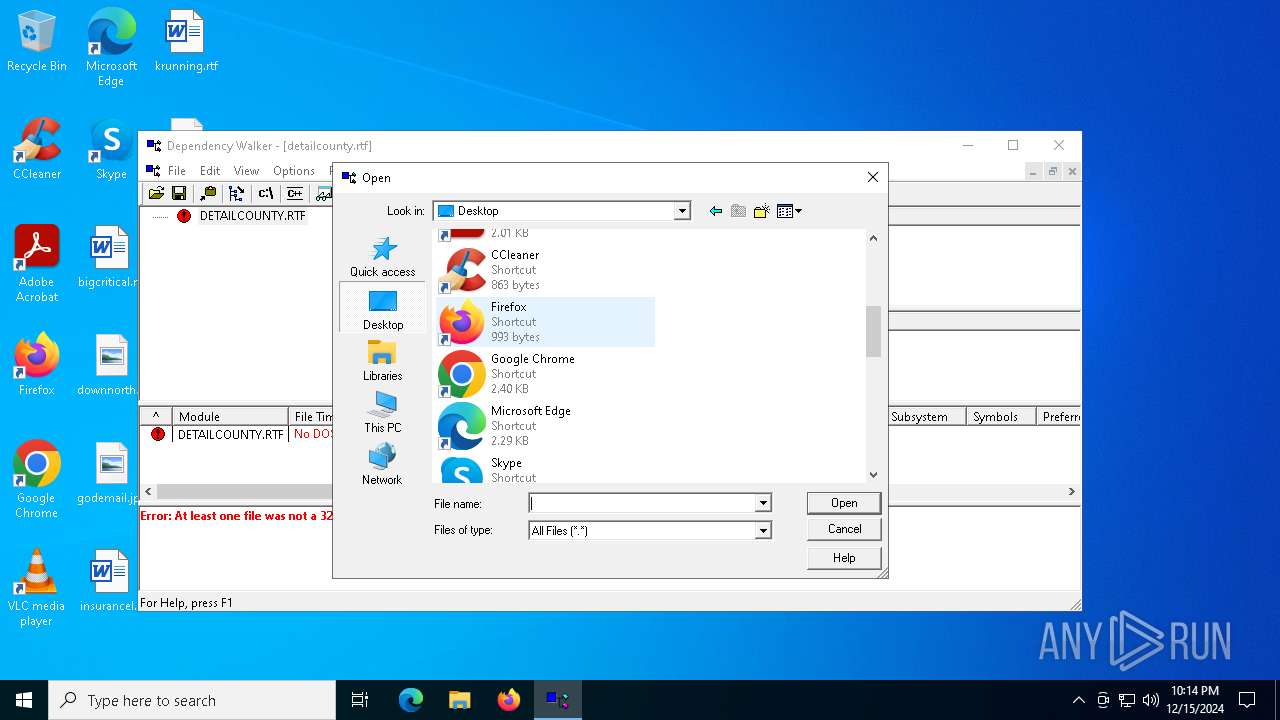
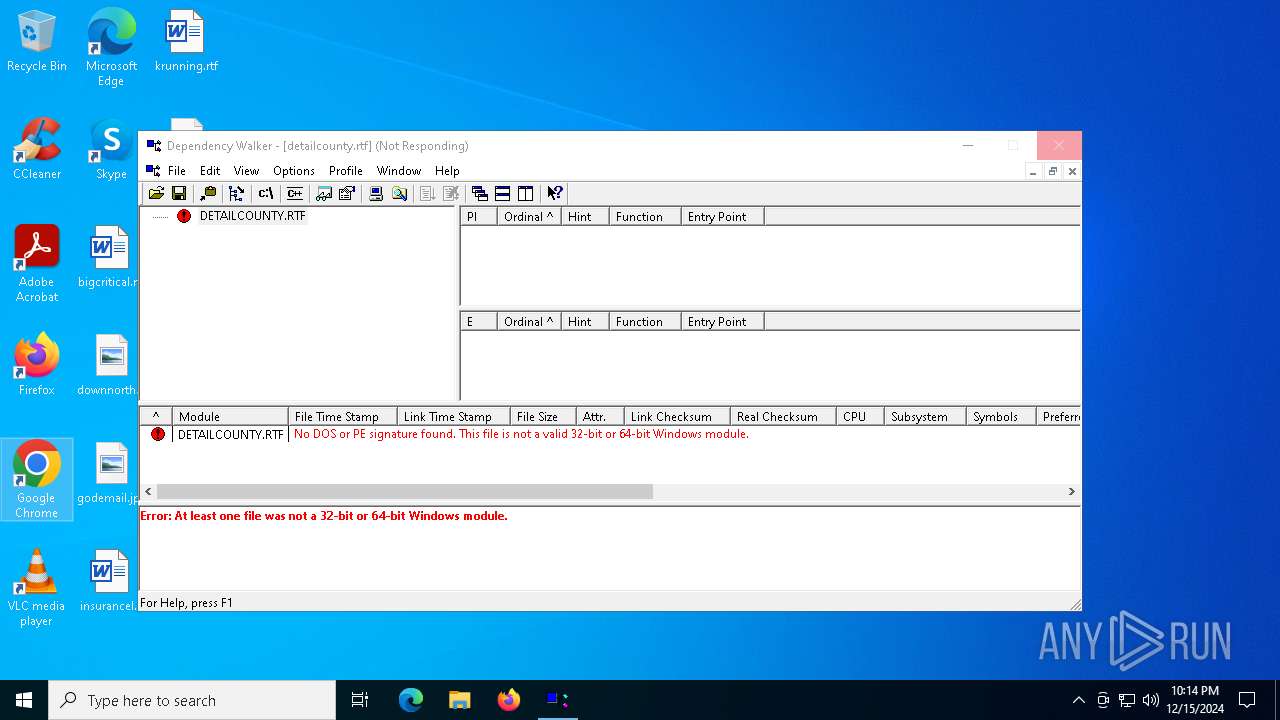
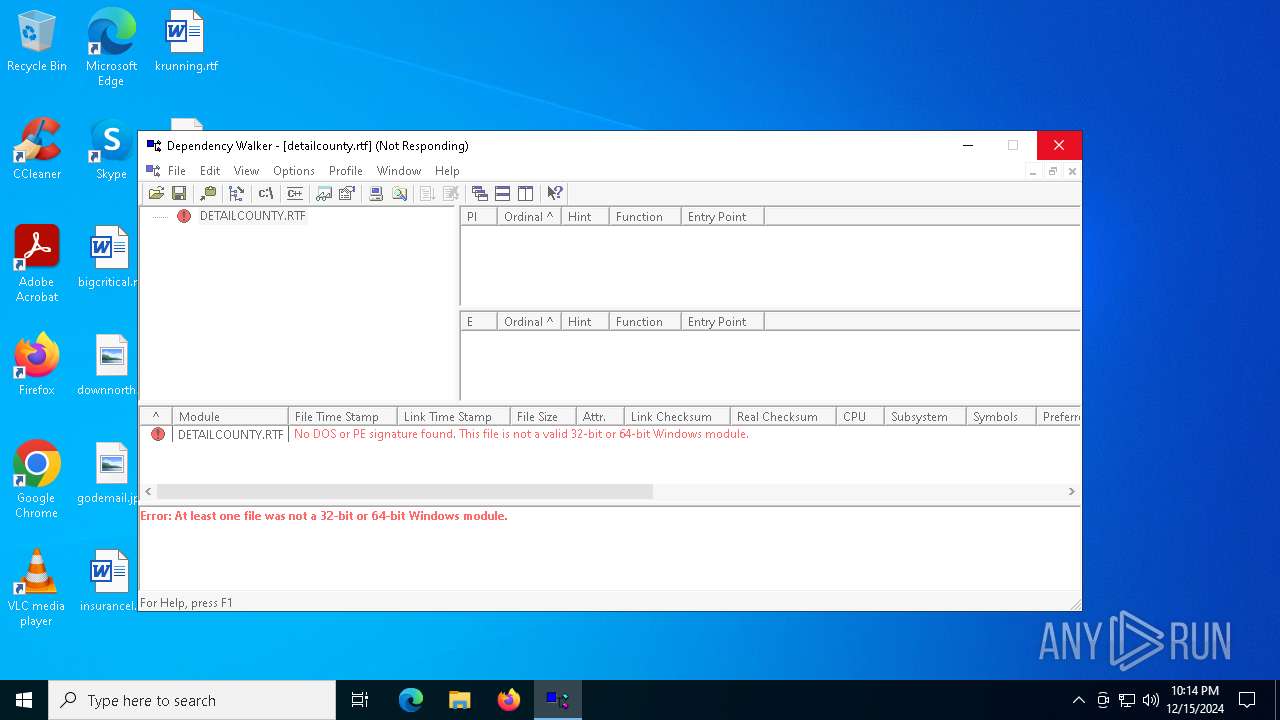
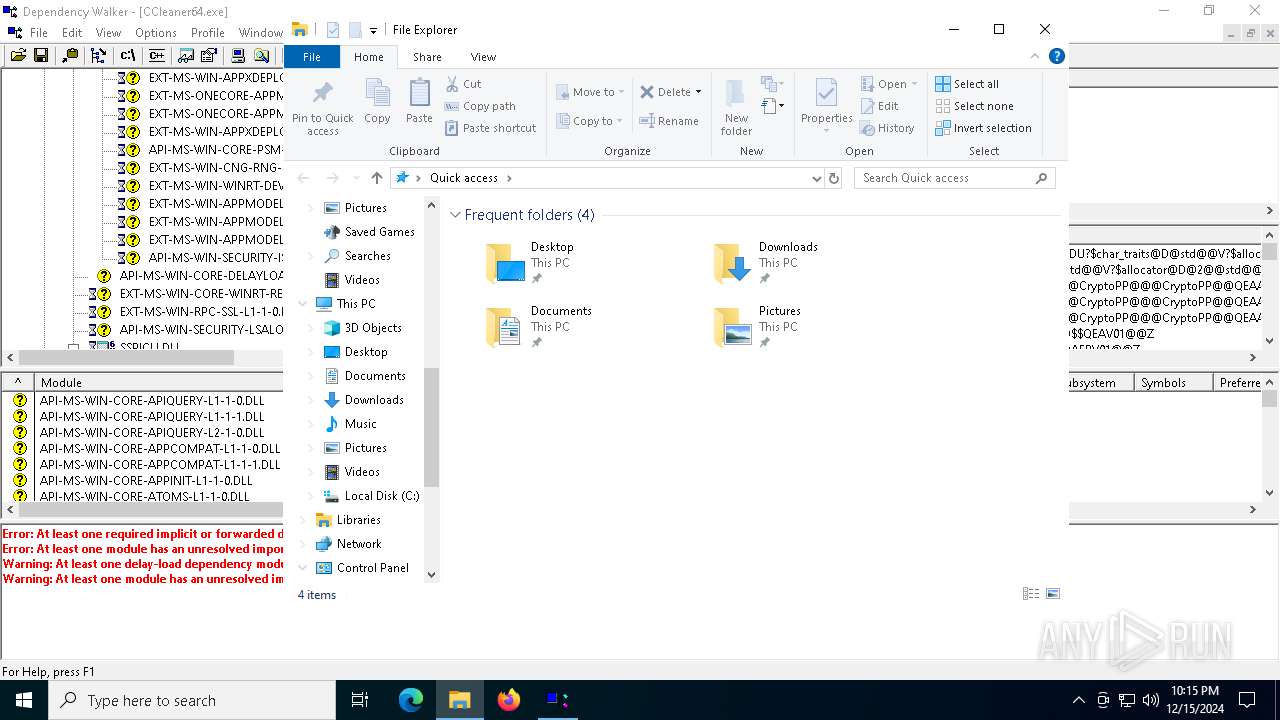
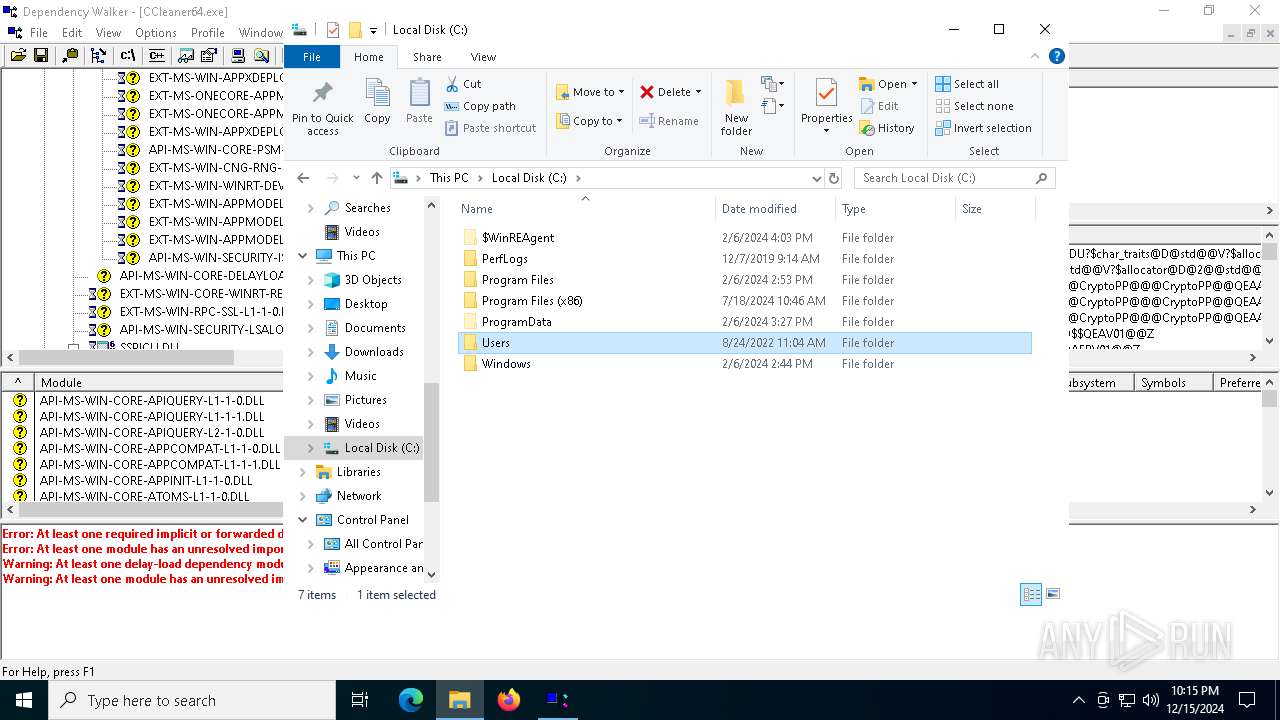
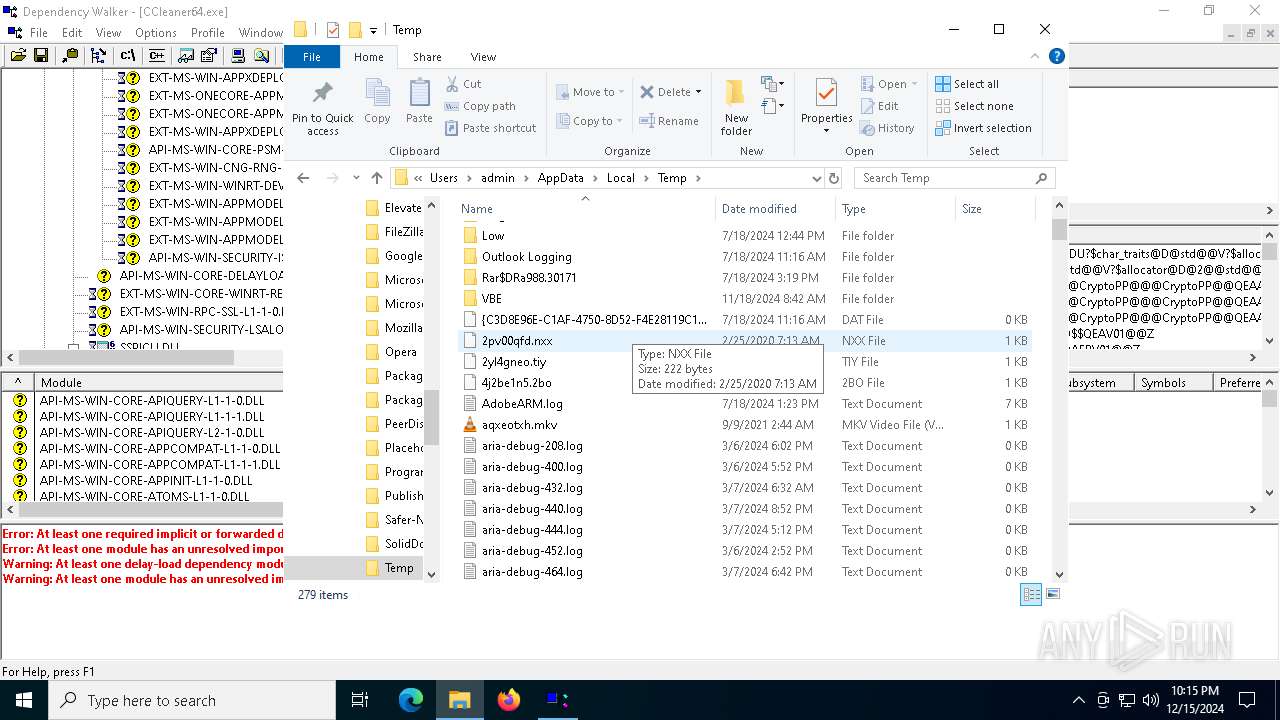
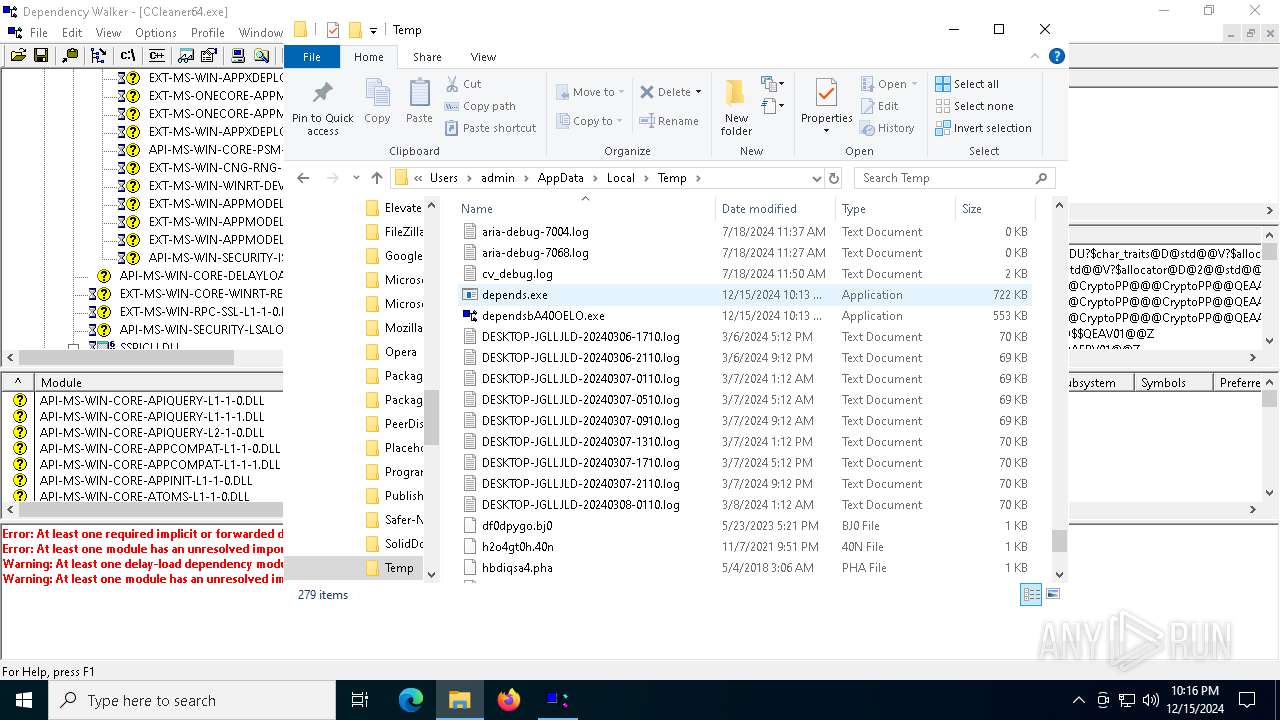
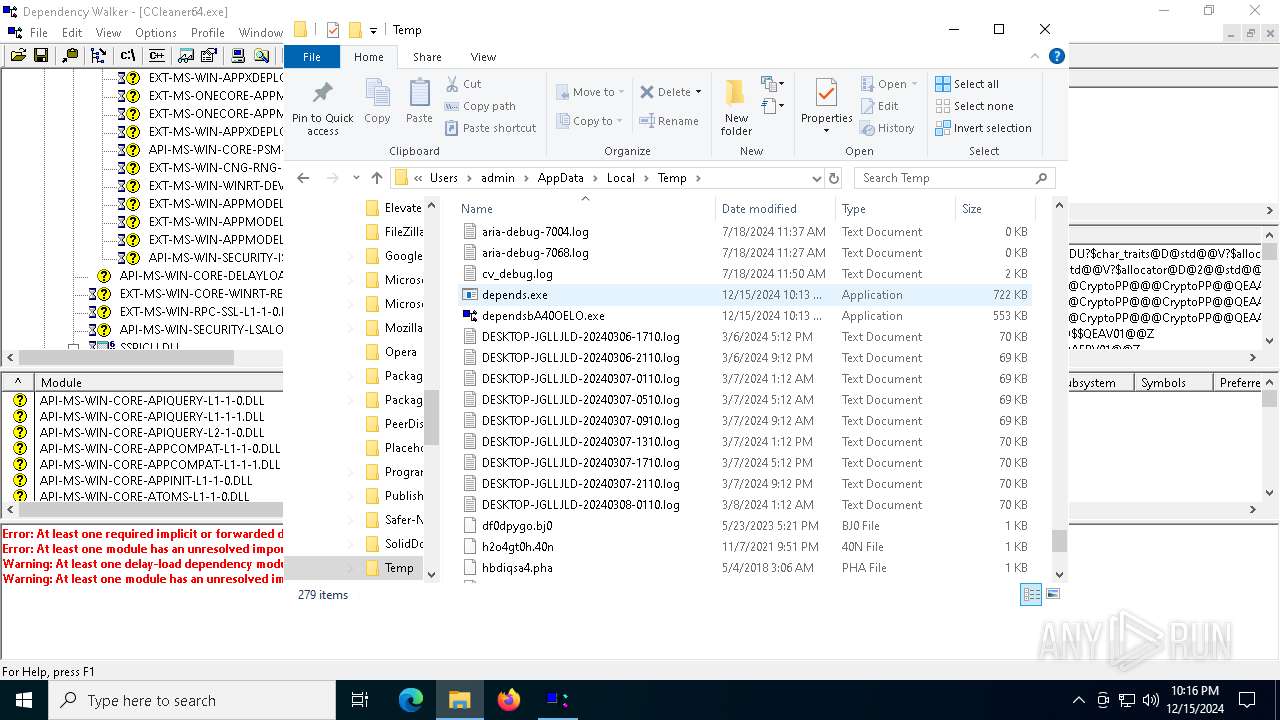
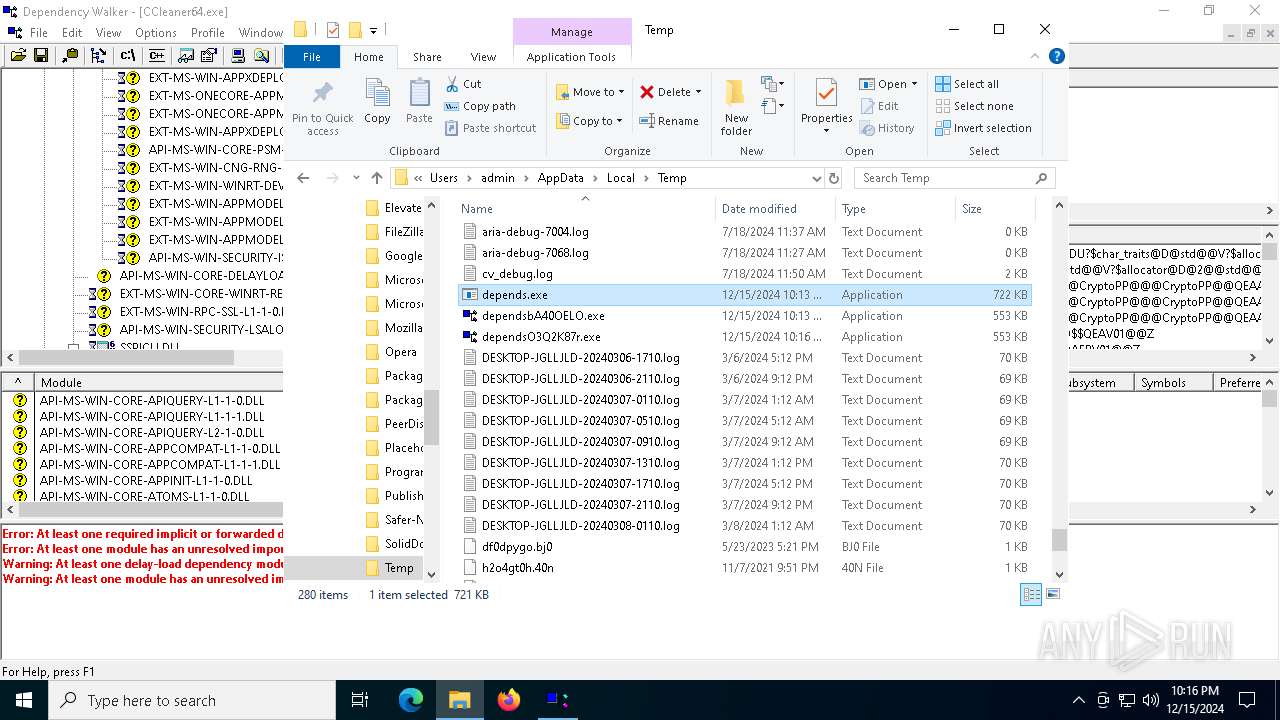
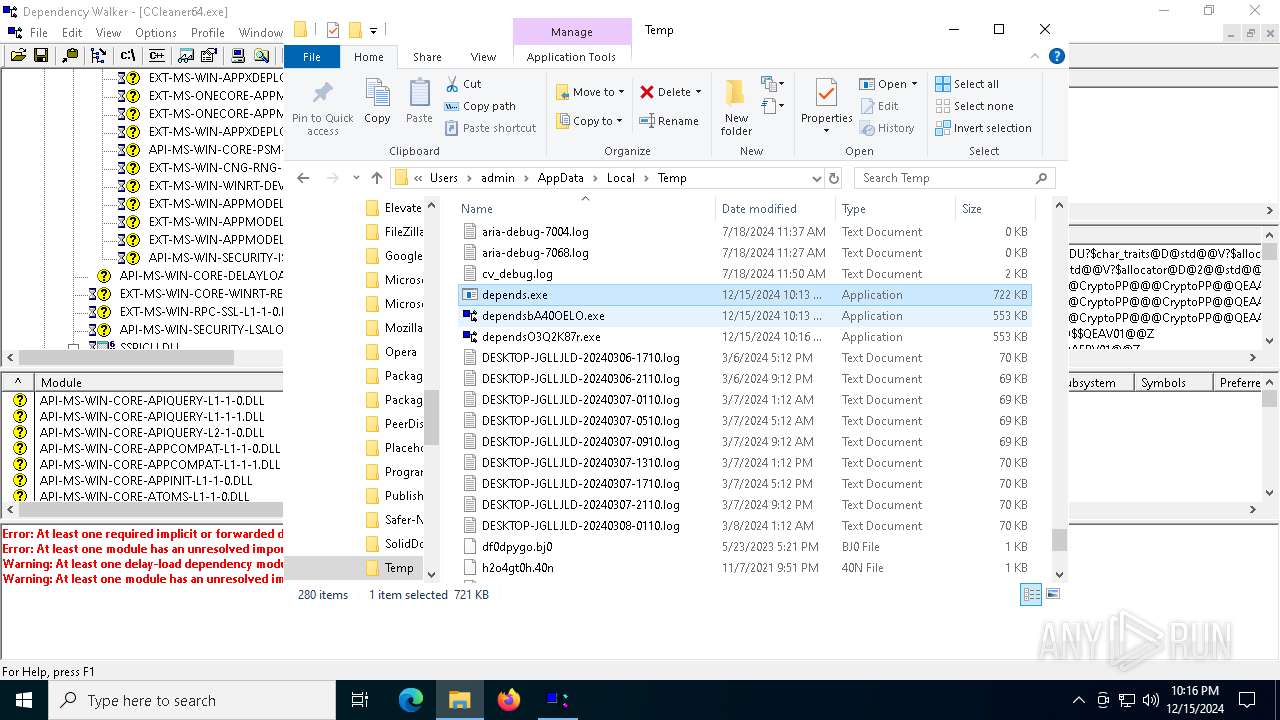
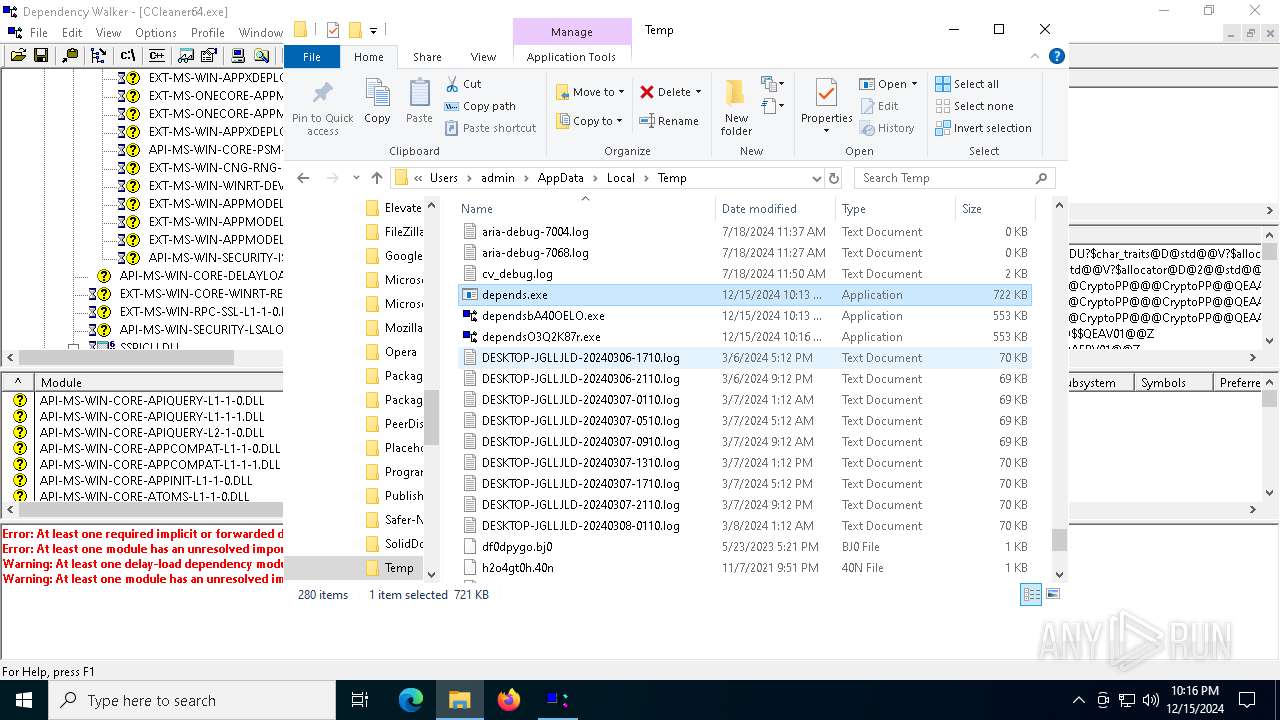
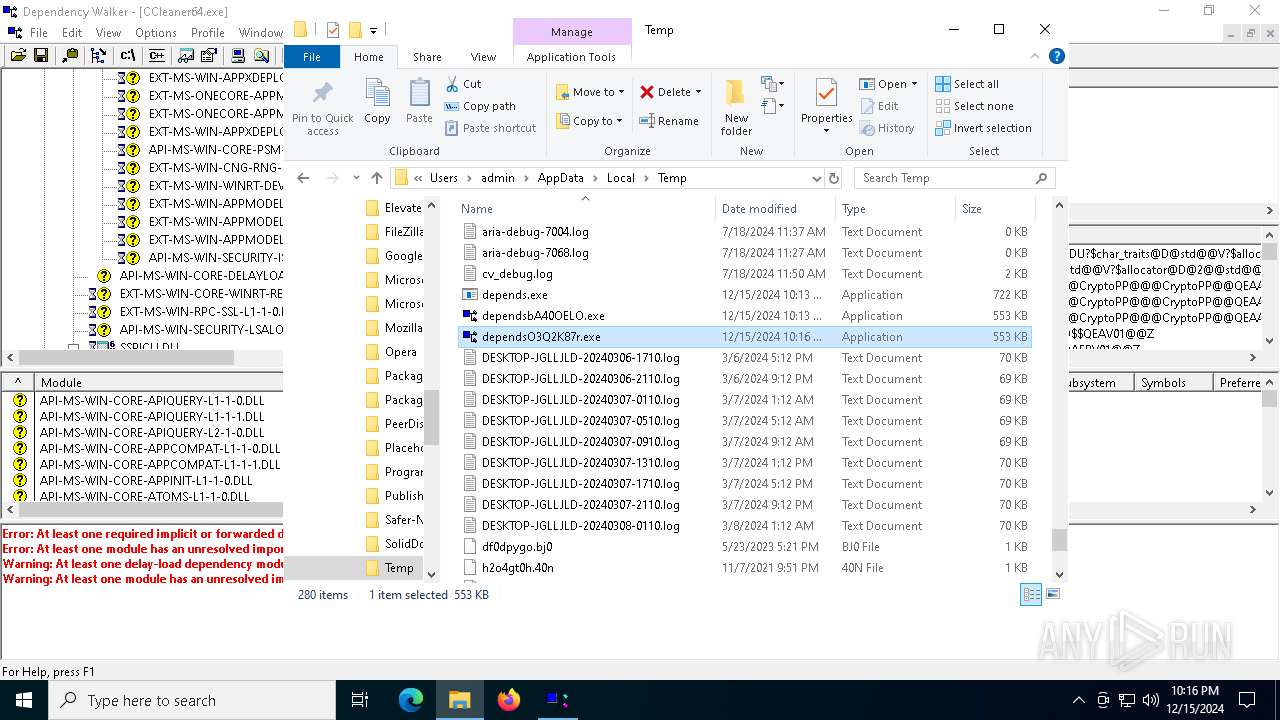
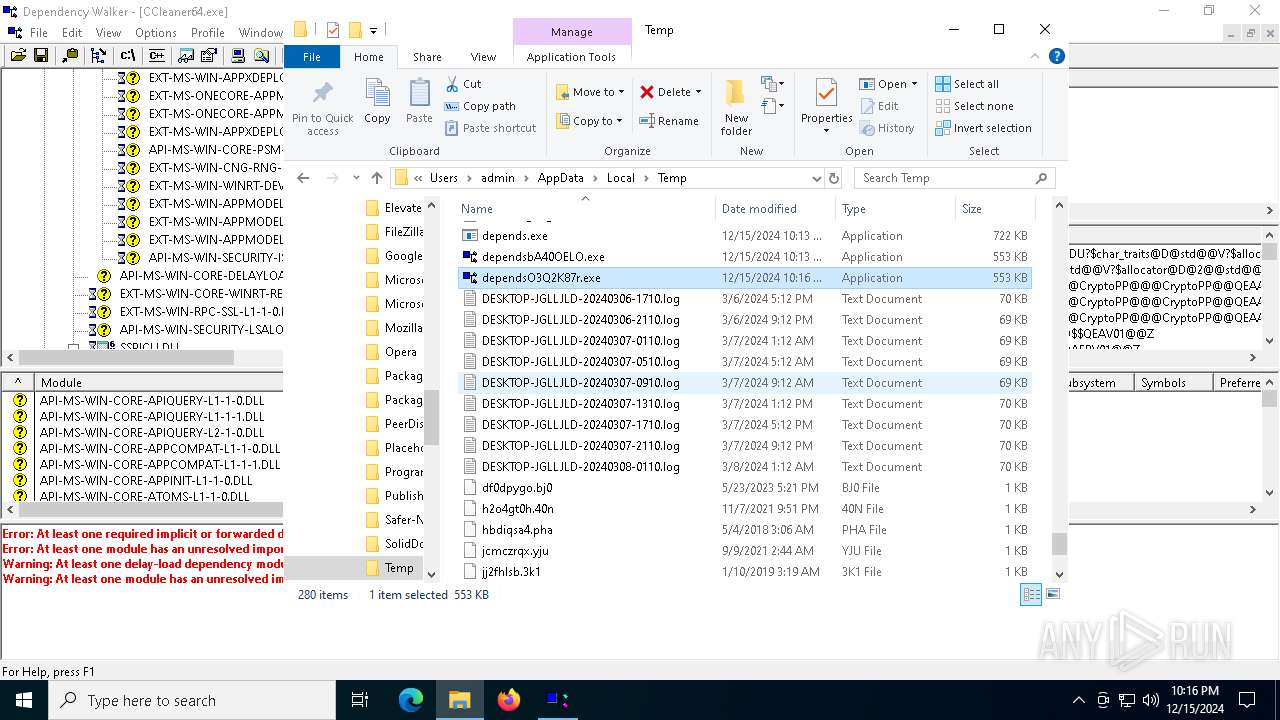
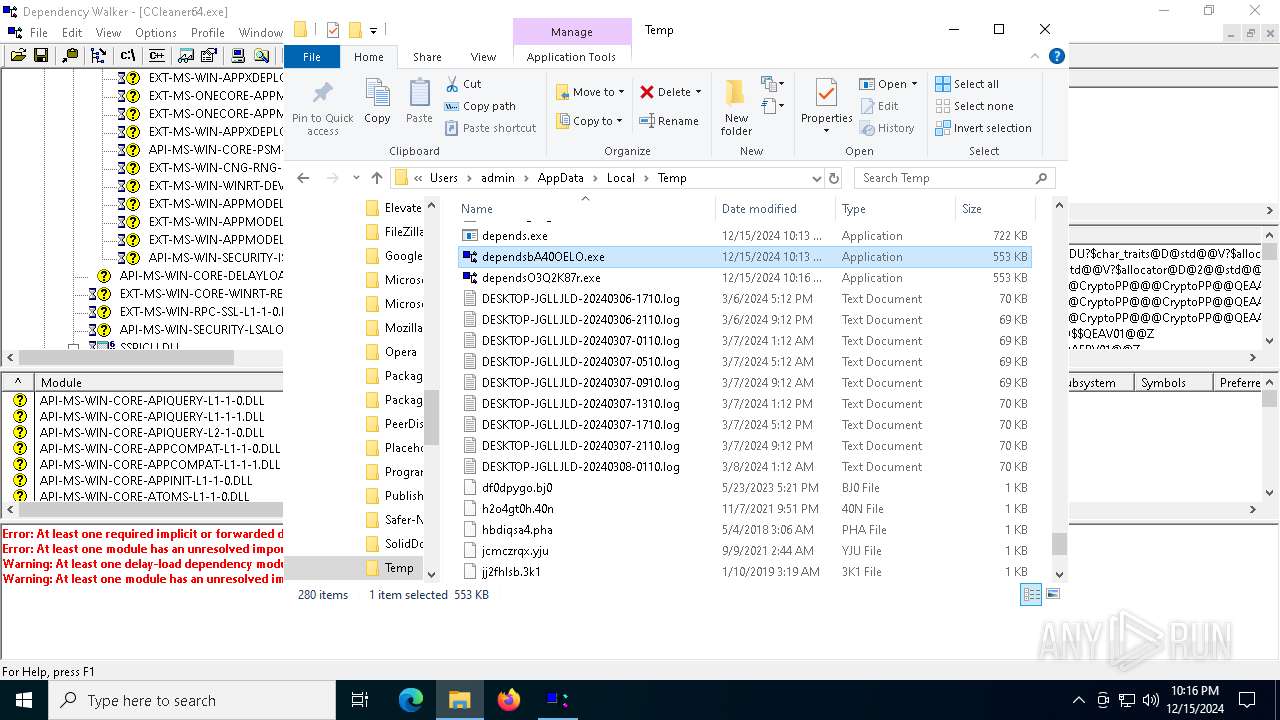
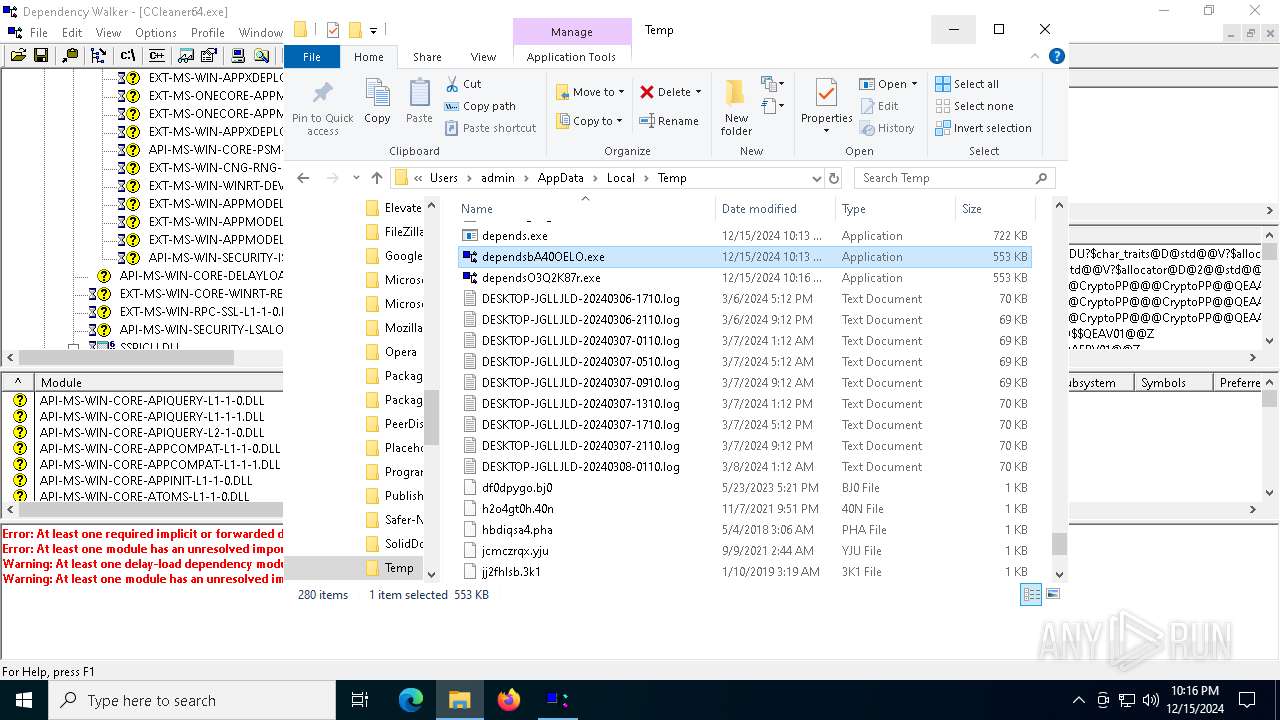
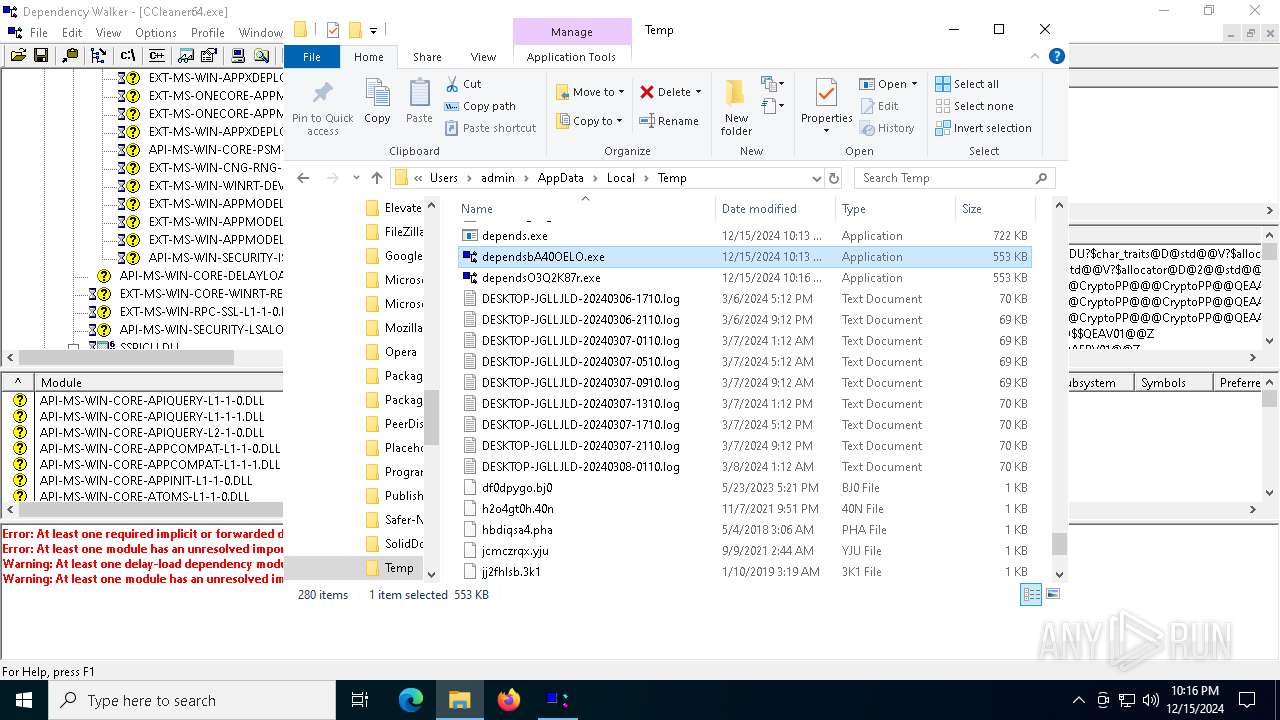
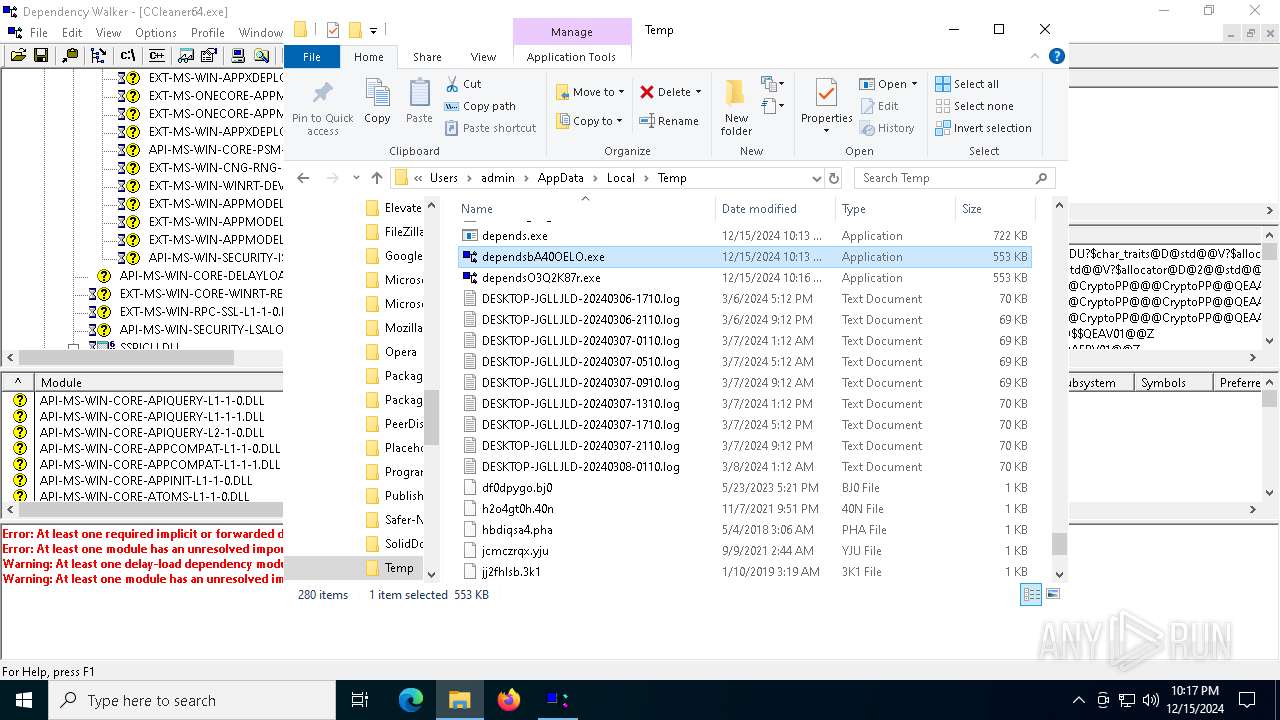
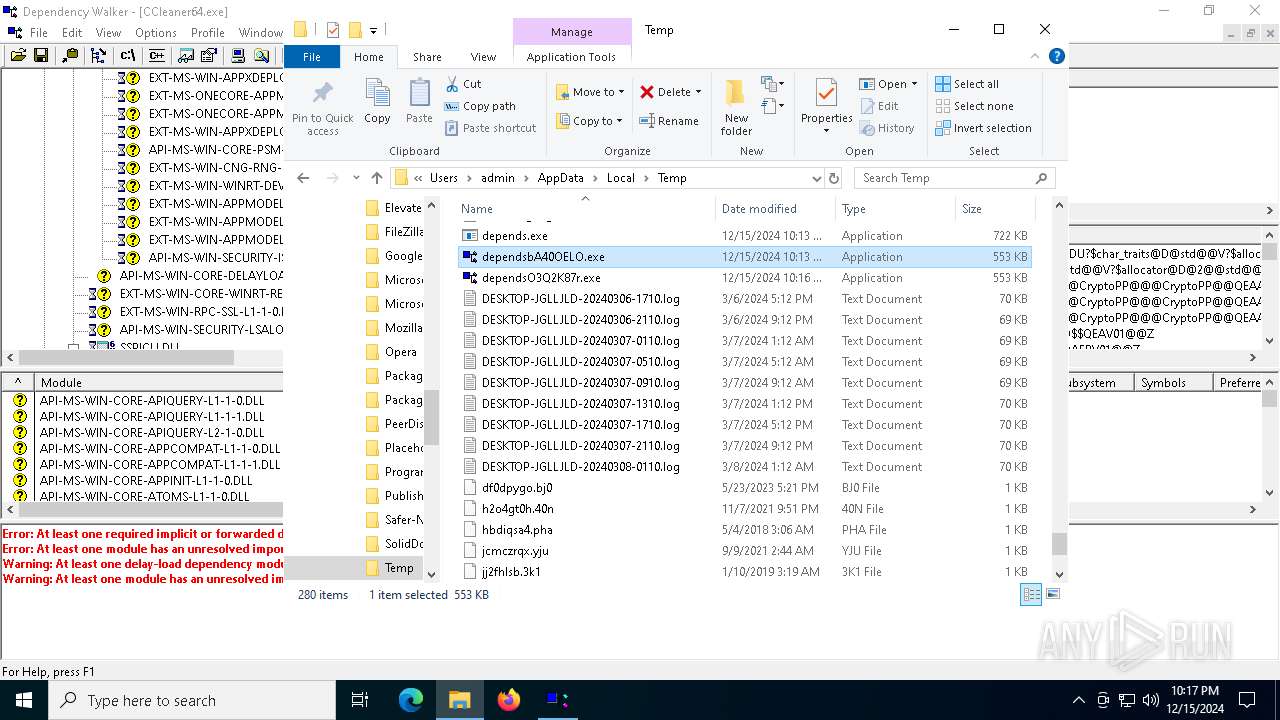
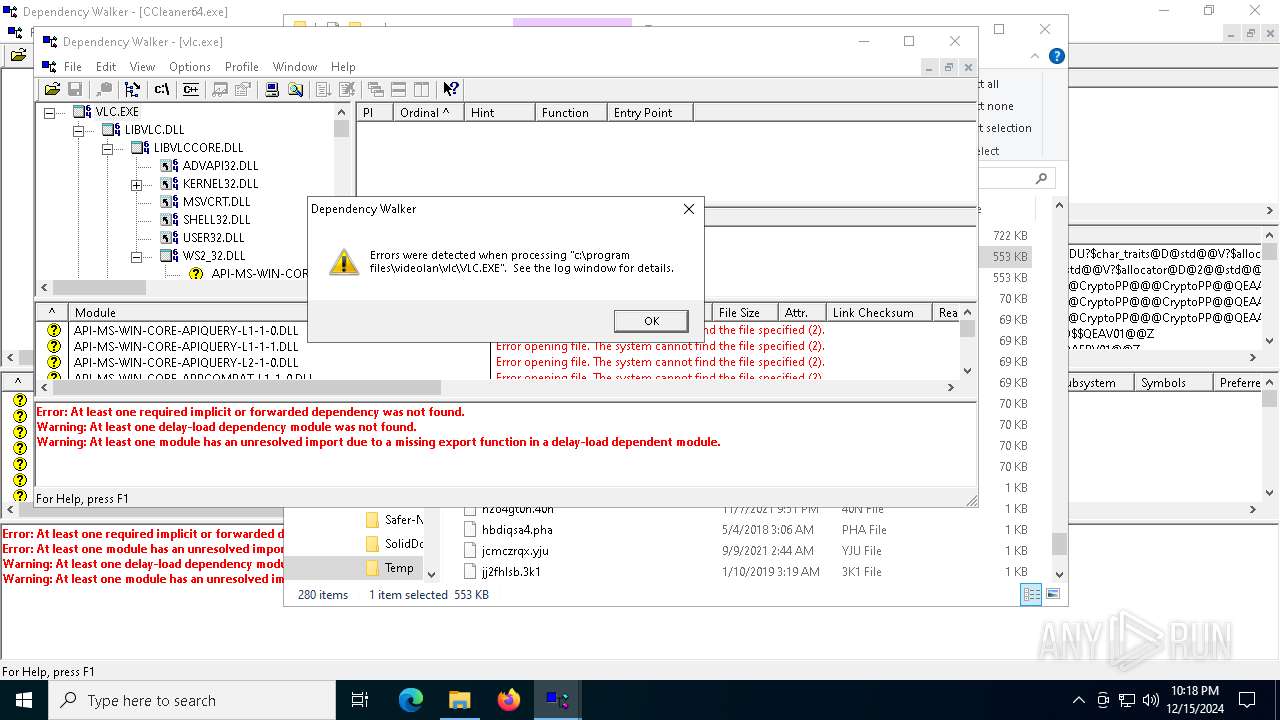
Process drops legitimate windows executable
- depends.exe (PID: 3820)
- depends.exe (PID: 6492)
Executable content was dropped or overwritten
- depends.exe (PID: 3820)
- depends.exe (PID: 6492)
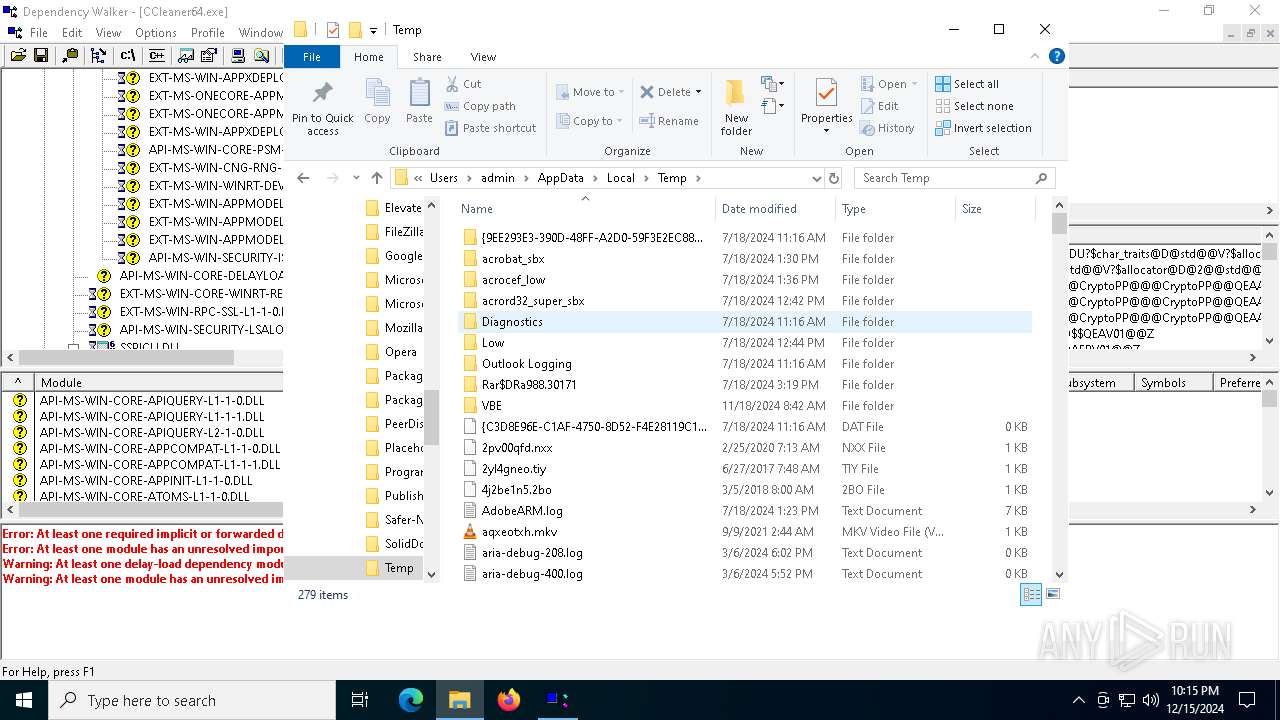
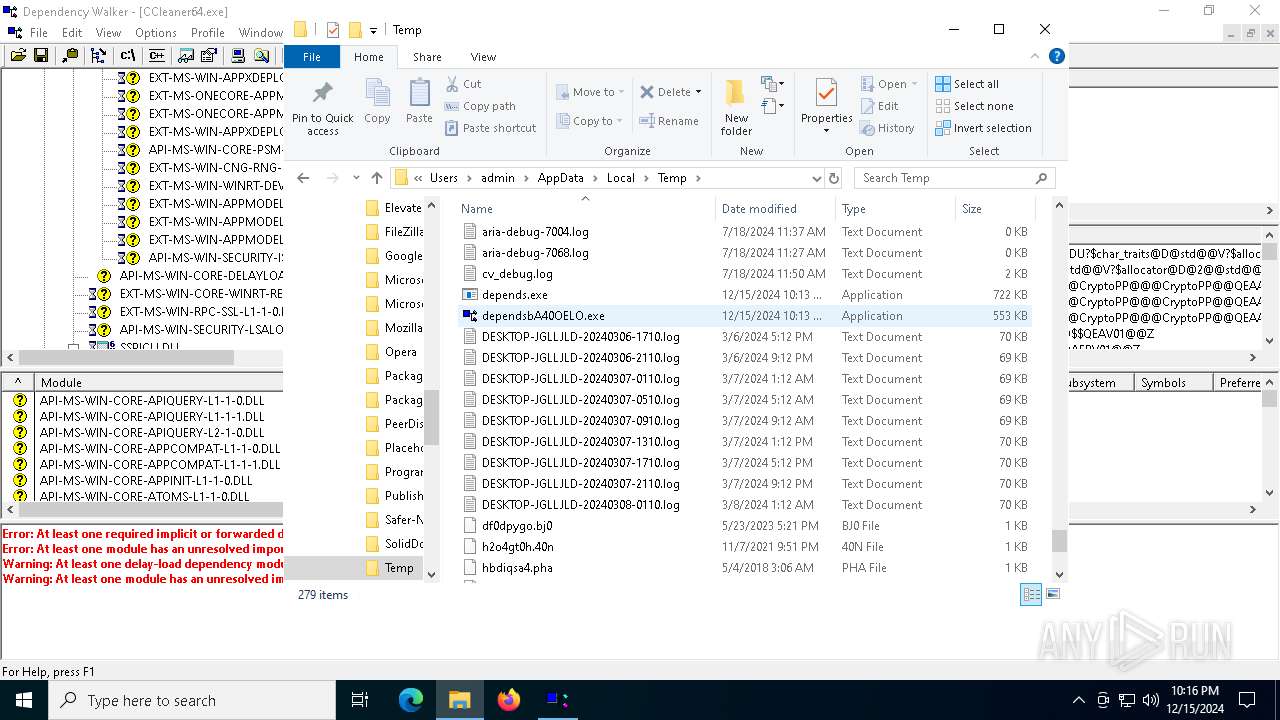
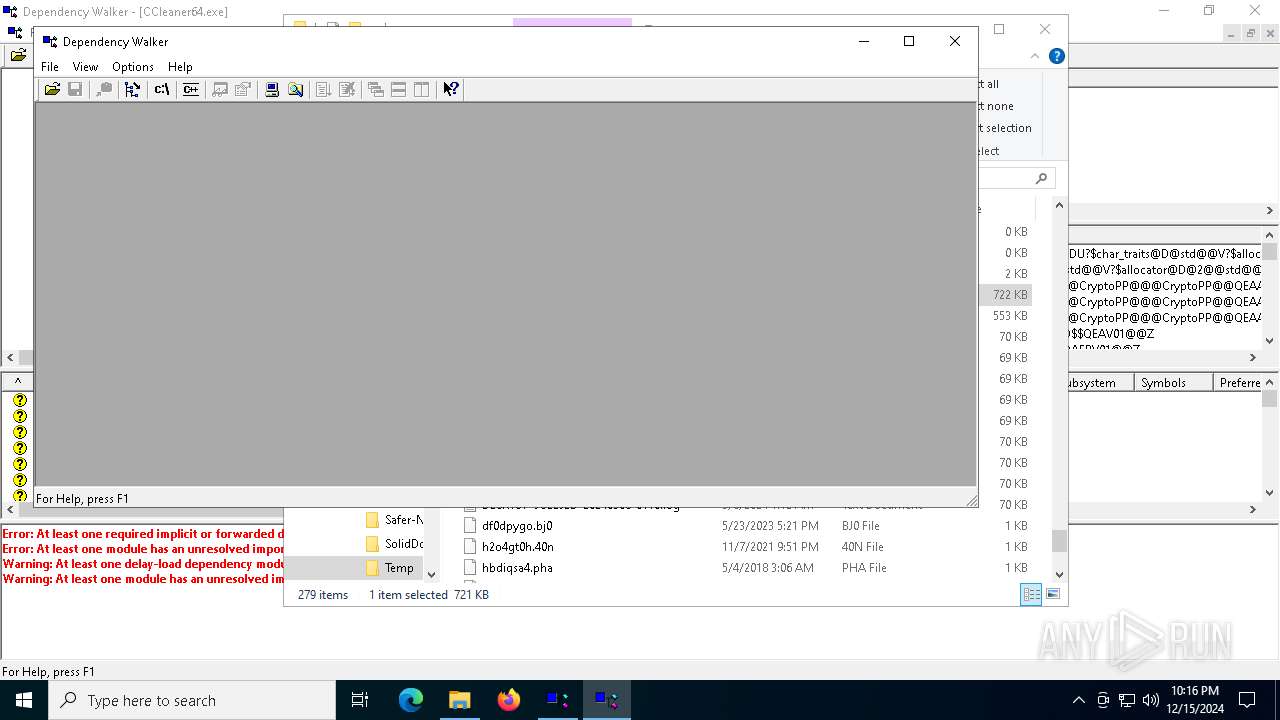
Starts a Microsoft application from unusual location
- dependsbA40OELO.exe (PID: 1200)
- dependsO3Q2K87r.exe (PID: 6612)
- dependsO3Q2K87r.exe (PID: 4536)
- dependsbA40OELO.exe (PID: 4980)
- dependsbA40OELO.exe (PID: 132)
Reads security settings of Internet Explorer
- dependsbA40OELO.exe (PID: 1200)
INFO
Checks supported languages
- depends.exe (PID: 3820)
- dependsbA40OELO.exe (PID: 1200)
- depends.exe (PID: 6492)
- dependsO3Q2K87r.exe (PID: 6612)
- dependsO3Q2K87r.exe (PID: 4536)
- dependsbA40OELO.exe (PID: 4980)
- dependsbA40OELO.exe (PID: 132)
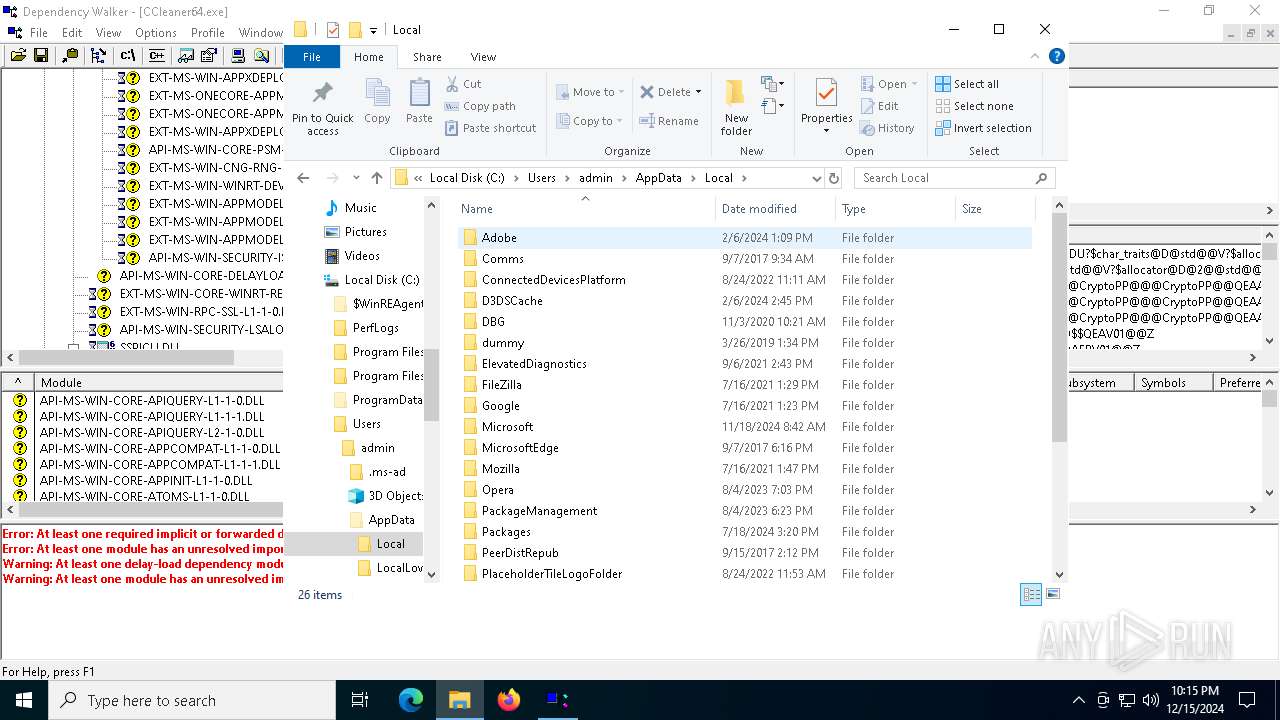
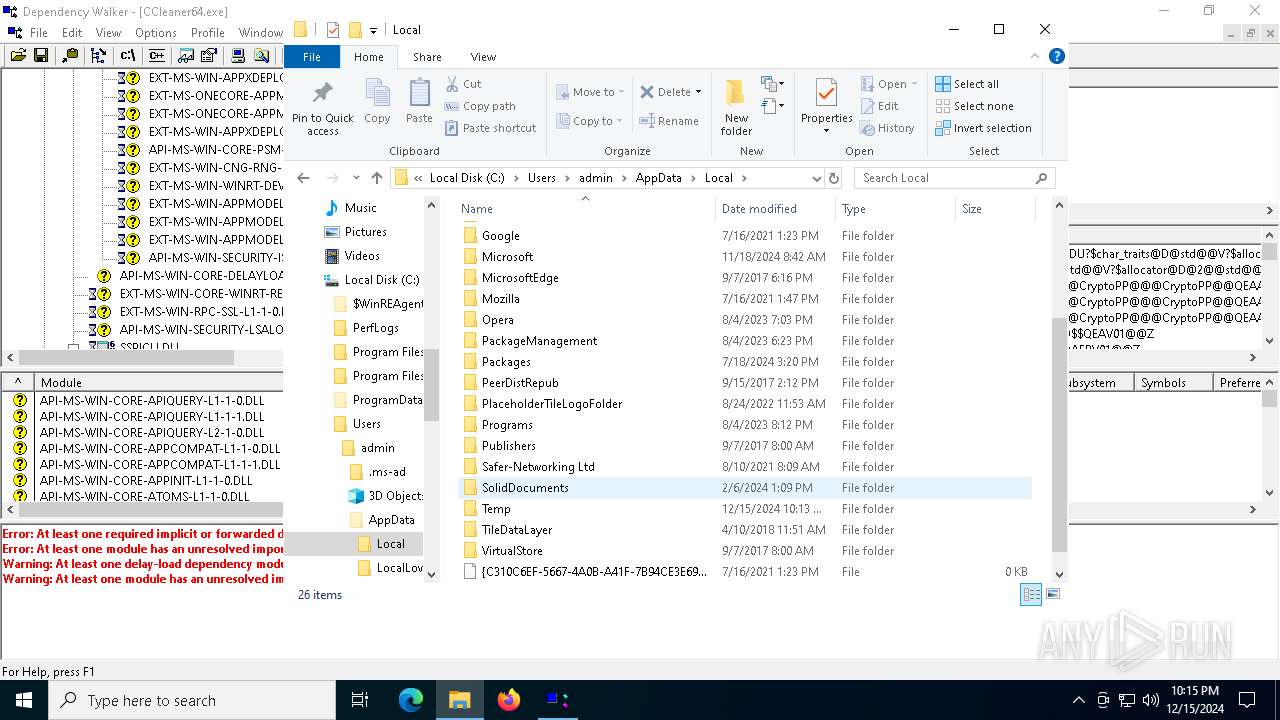
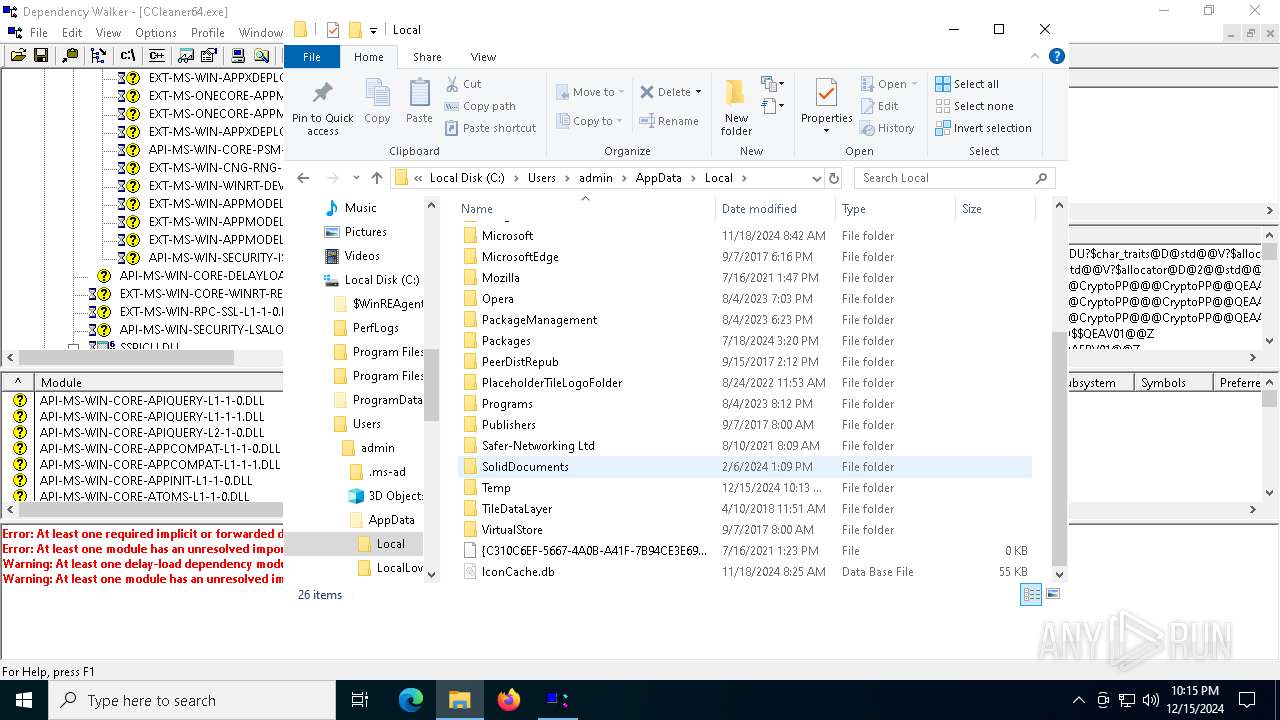
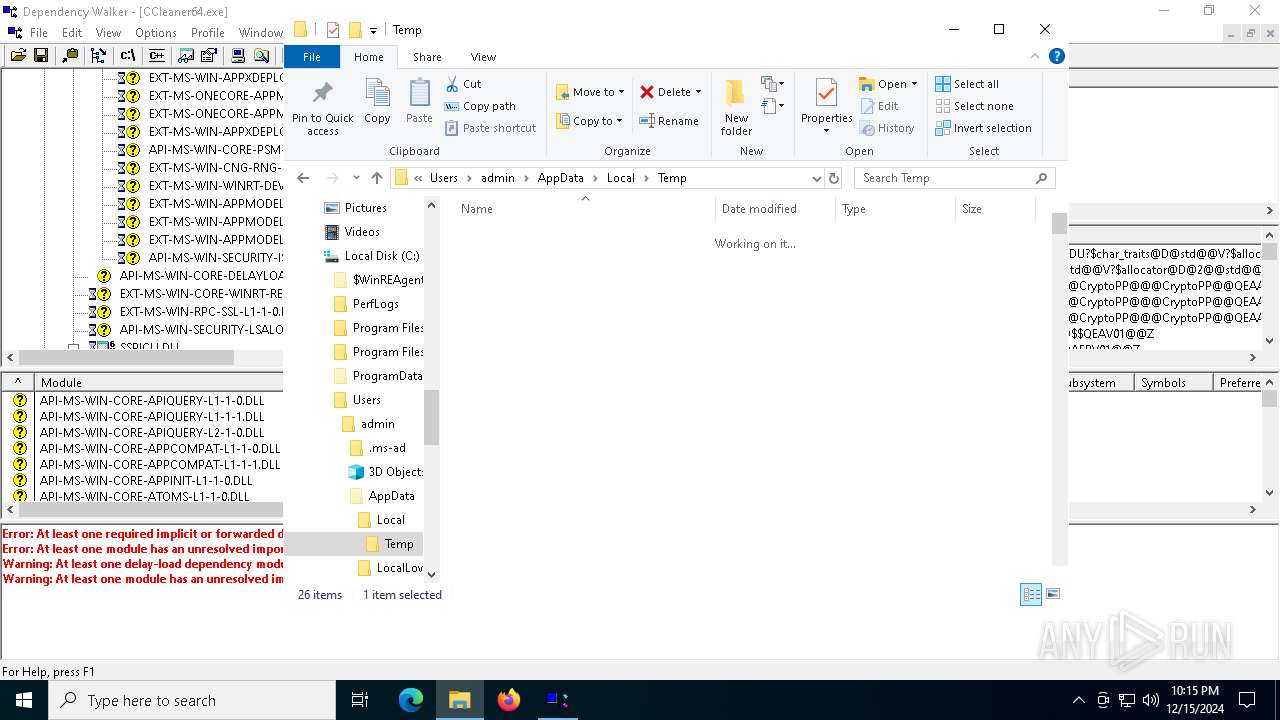
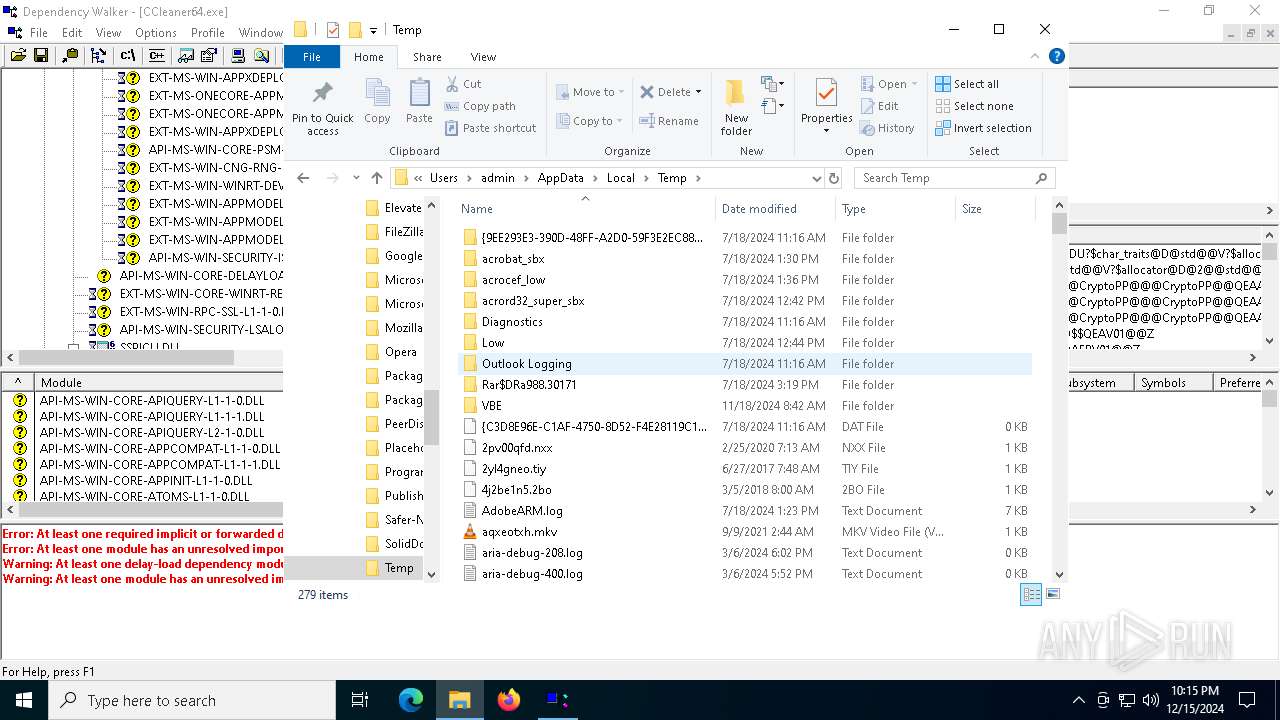
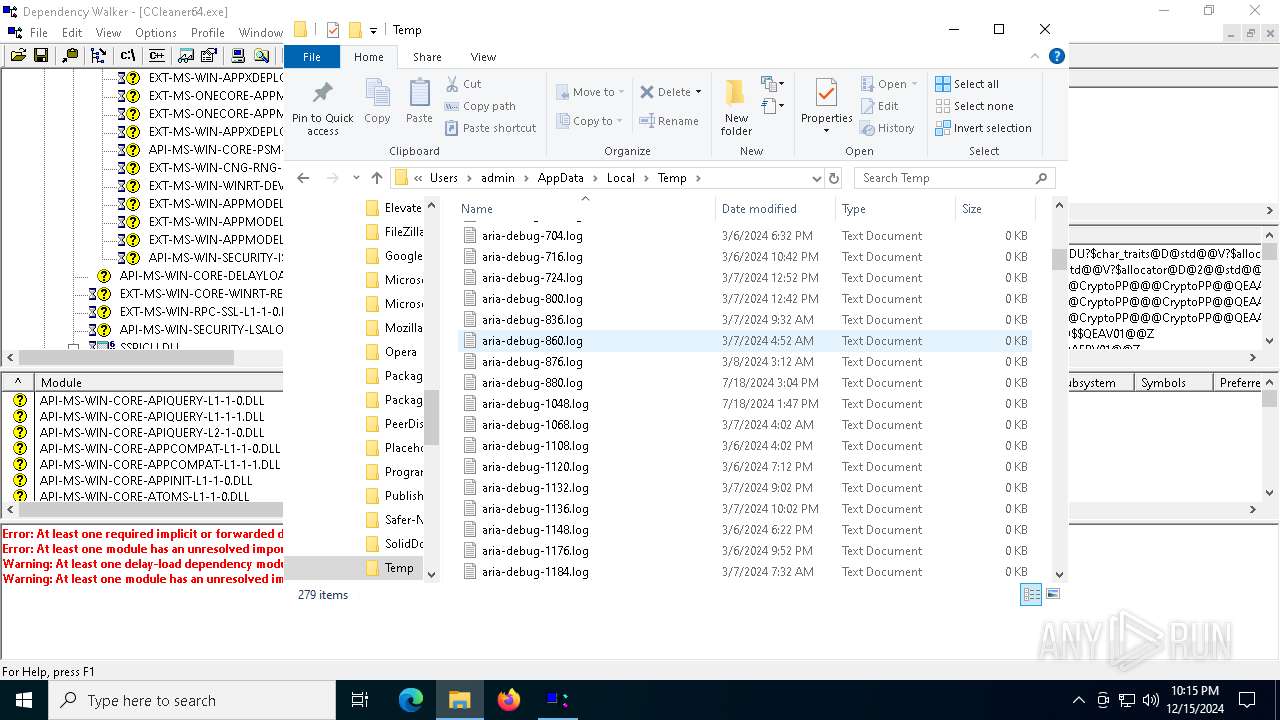
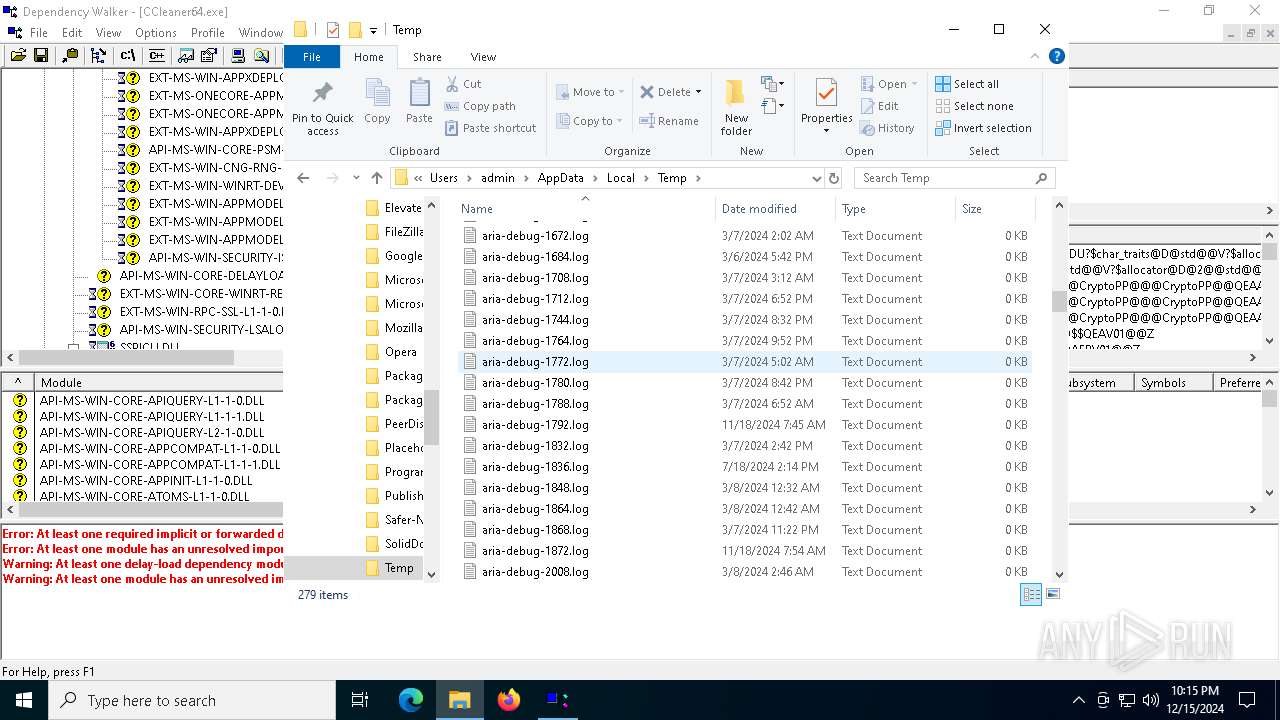
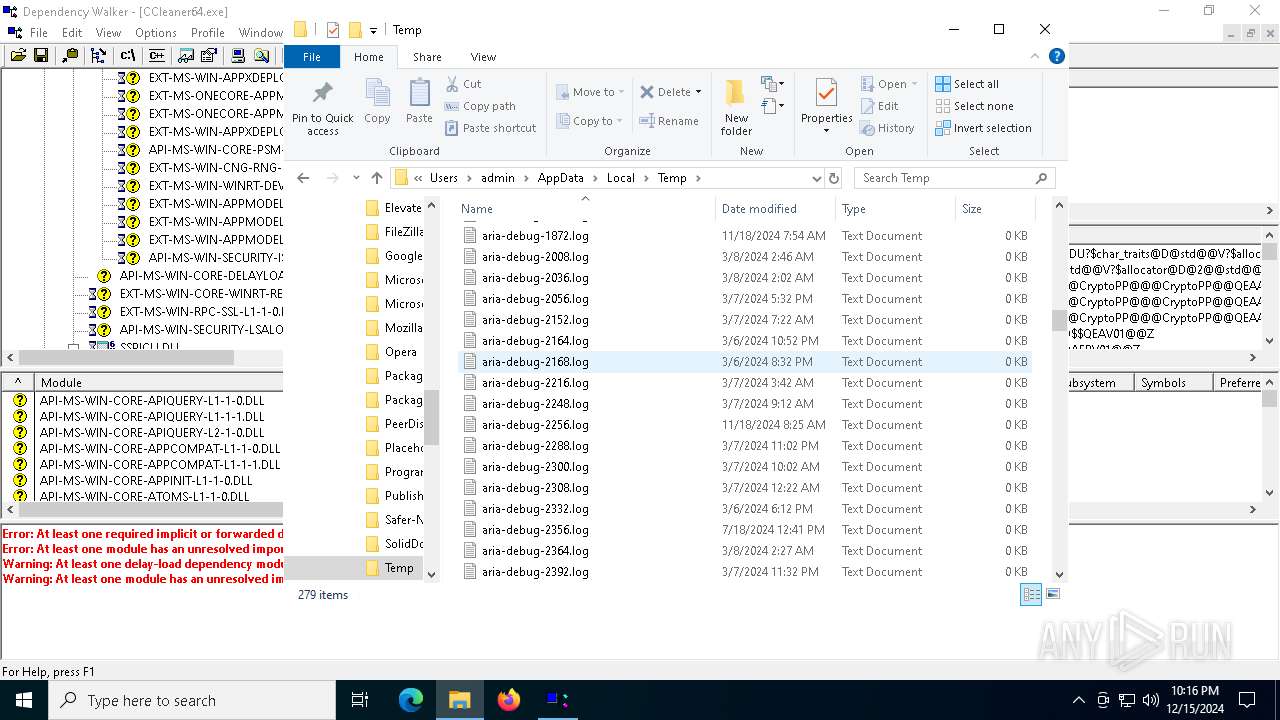
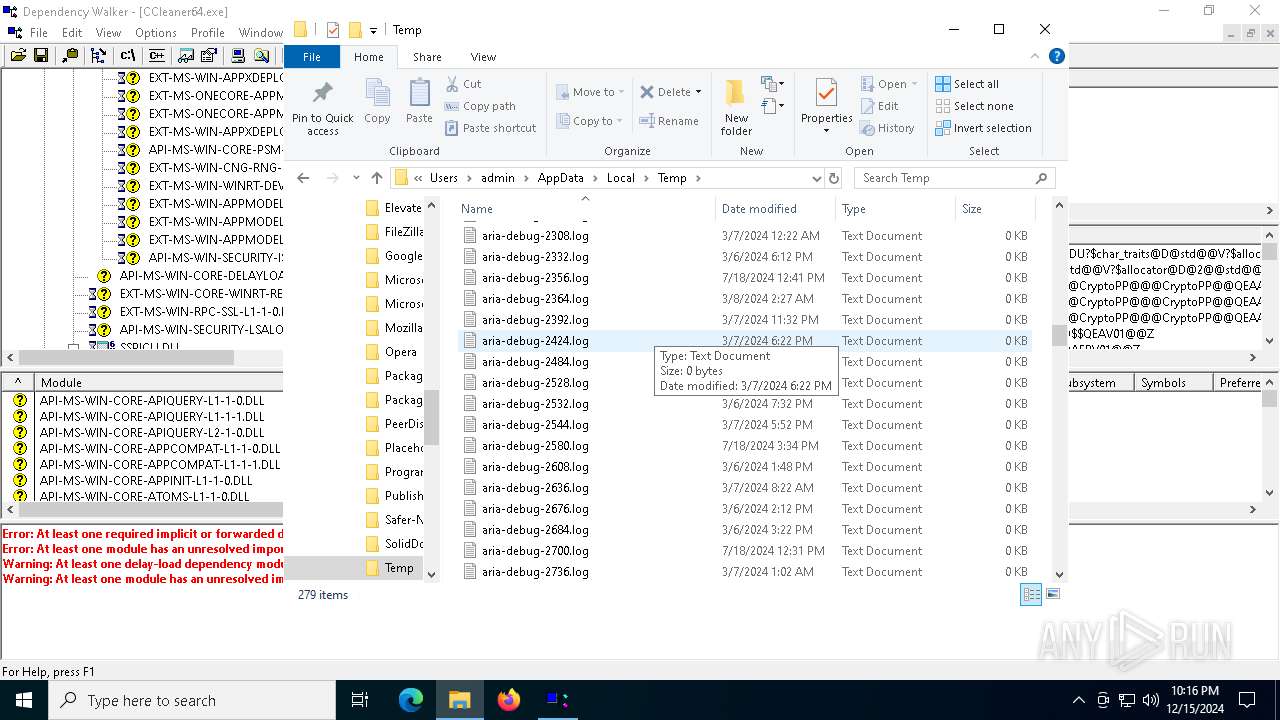
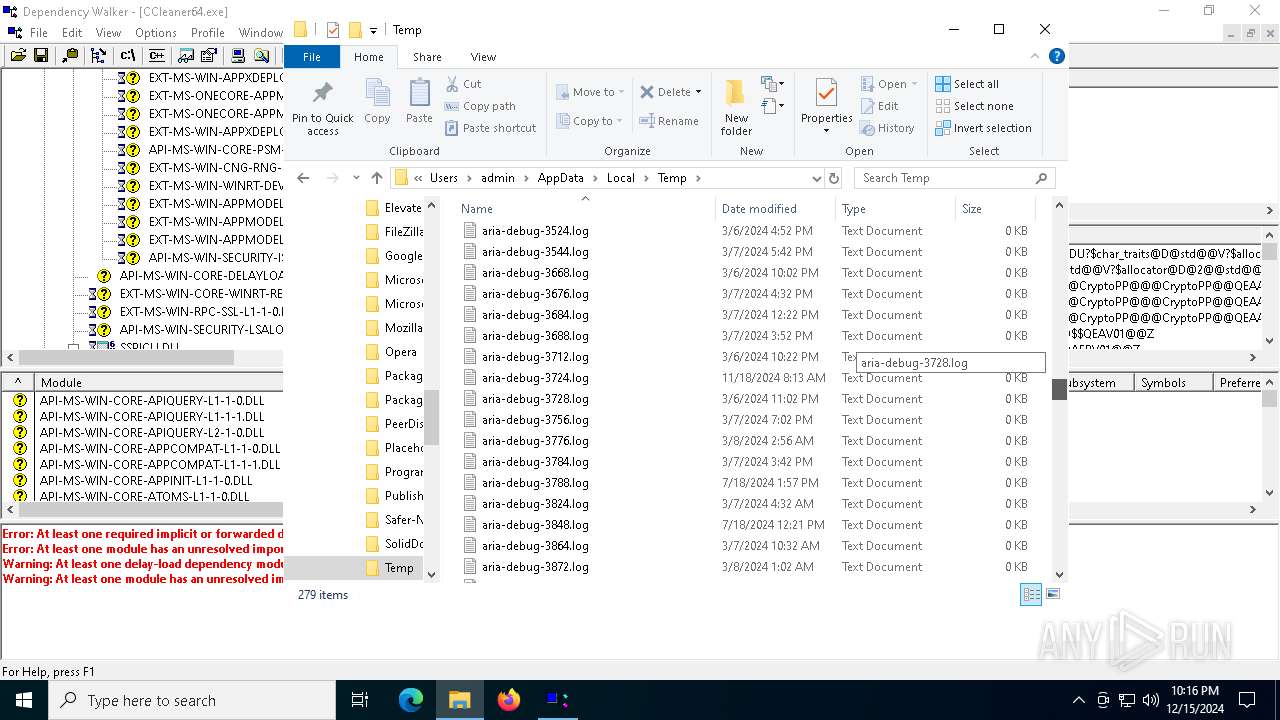
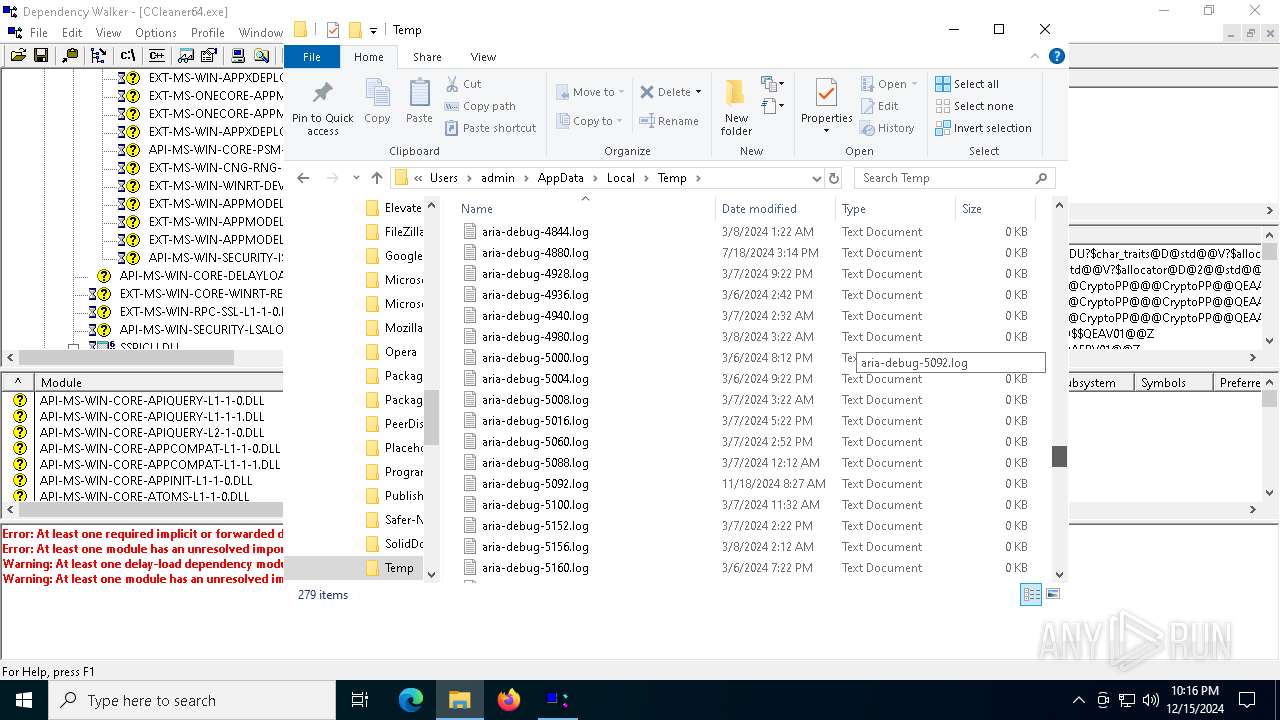
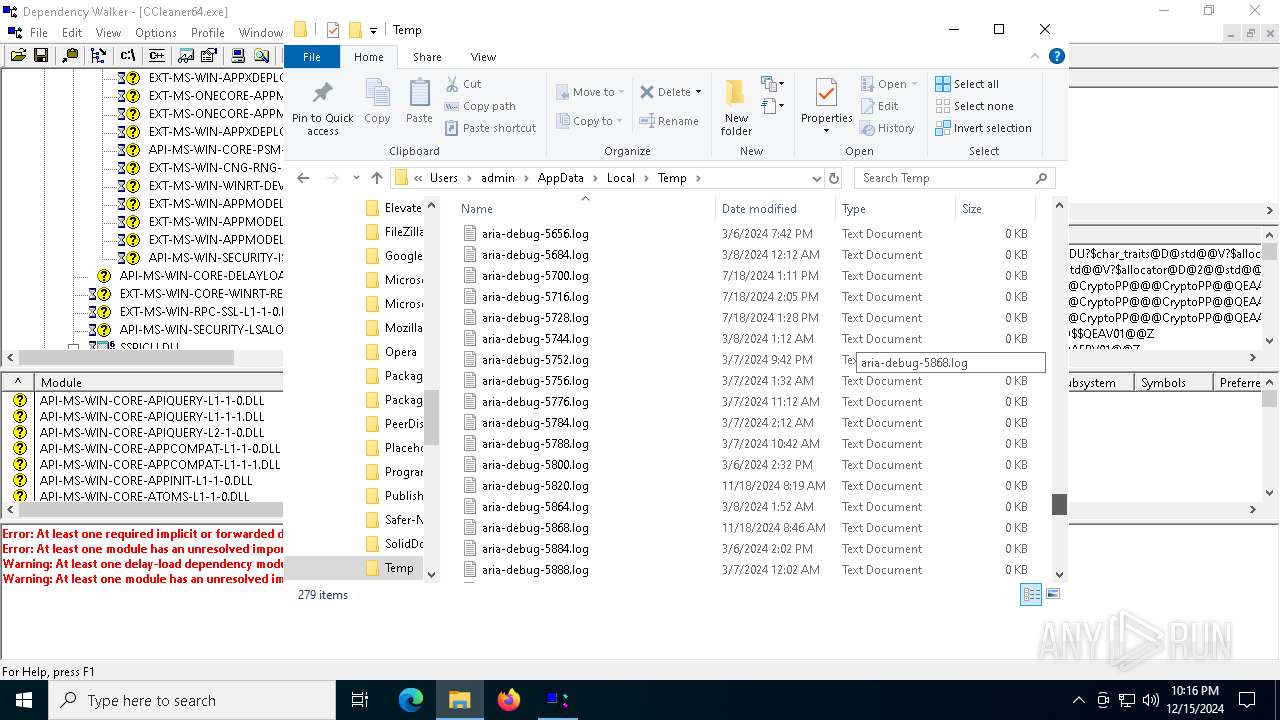
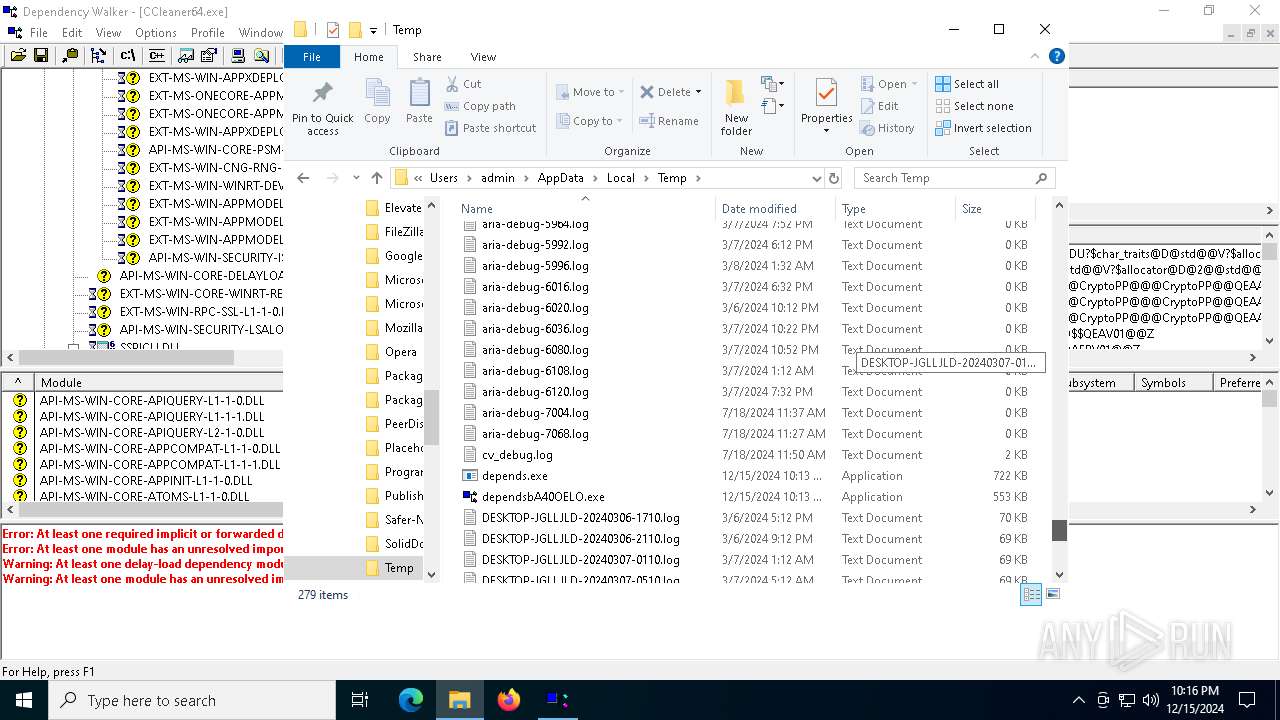
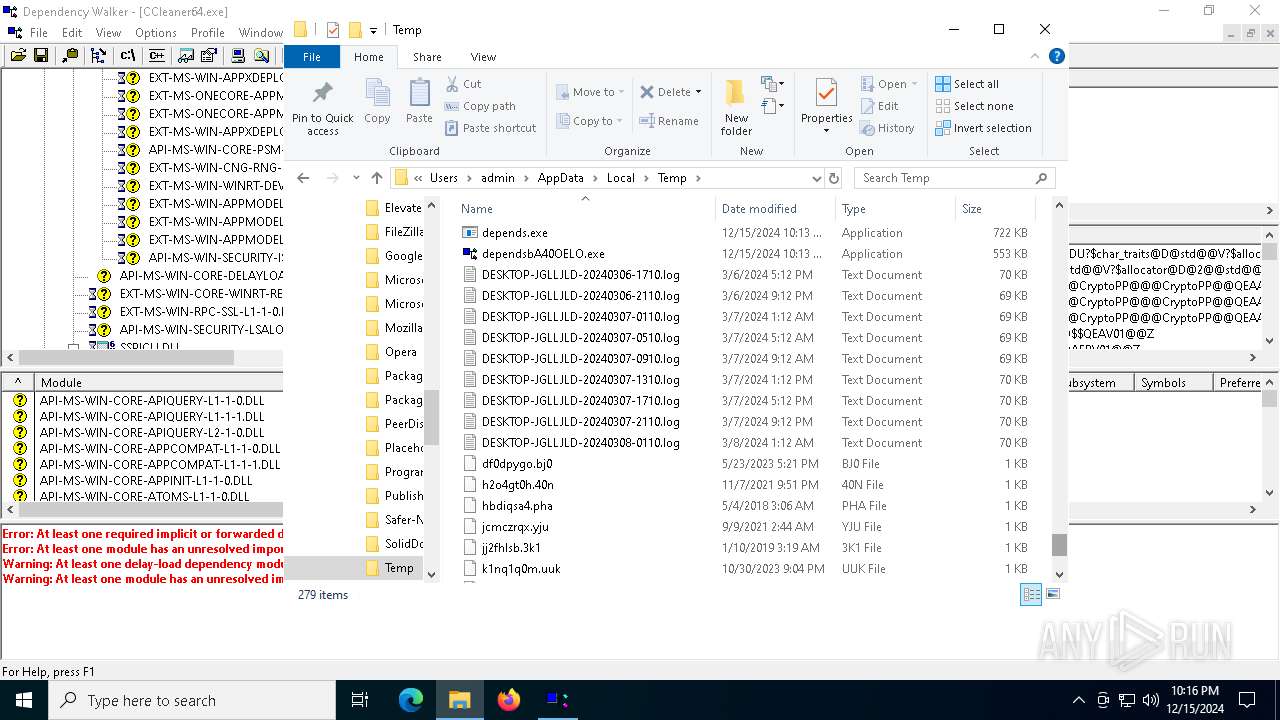
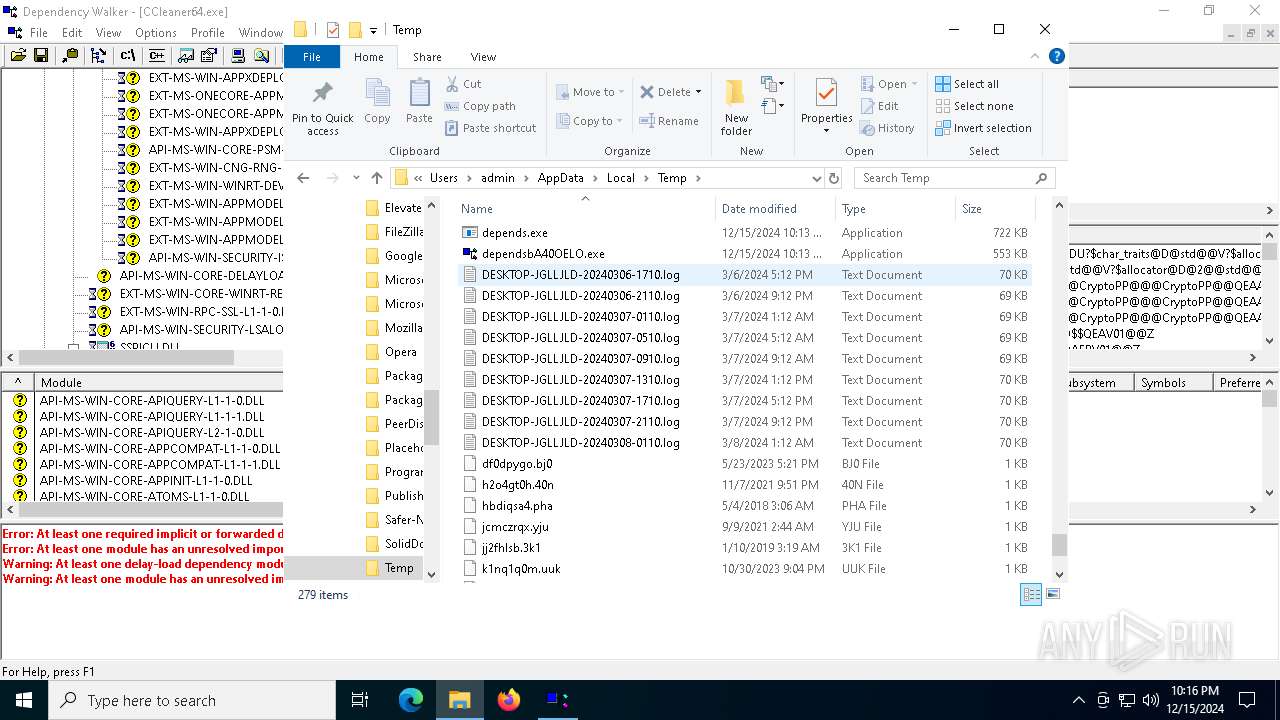
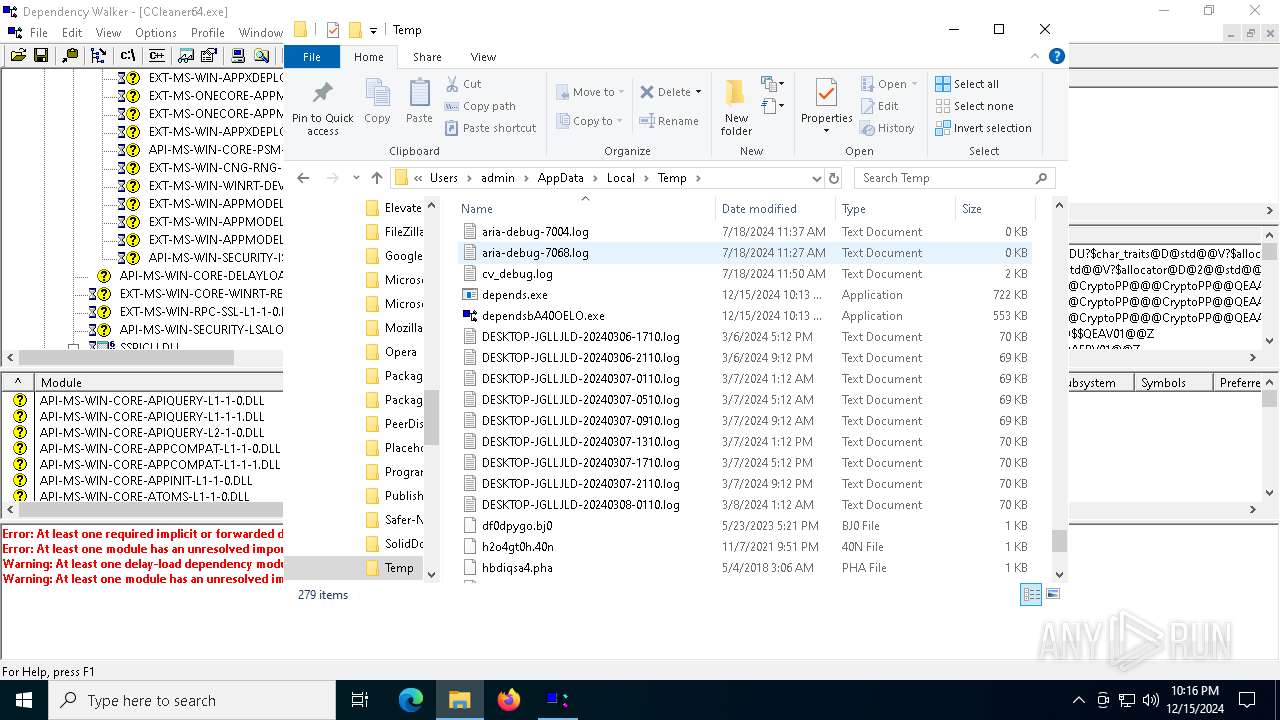
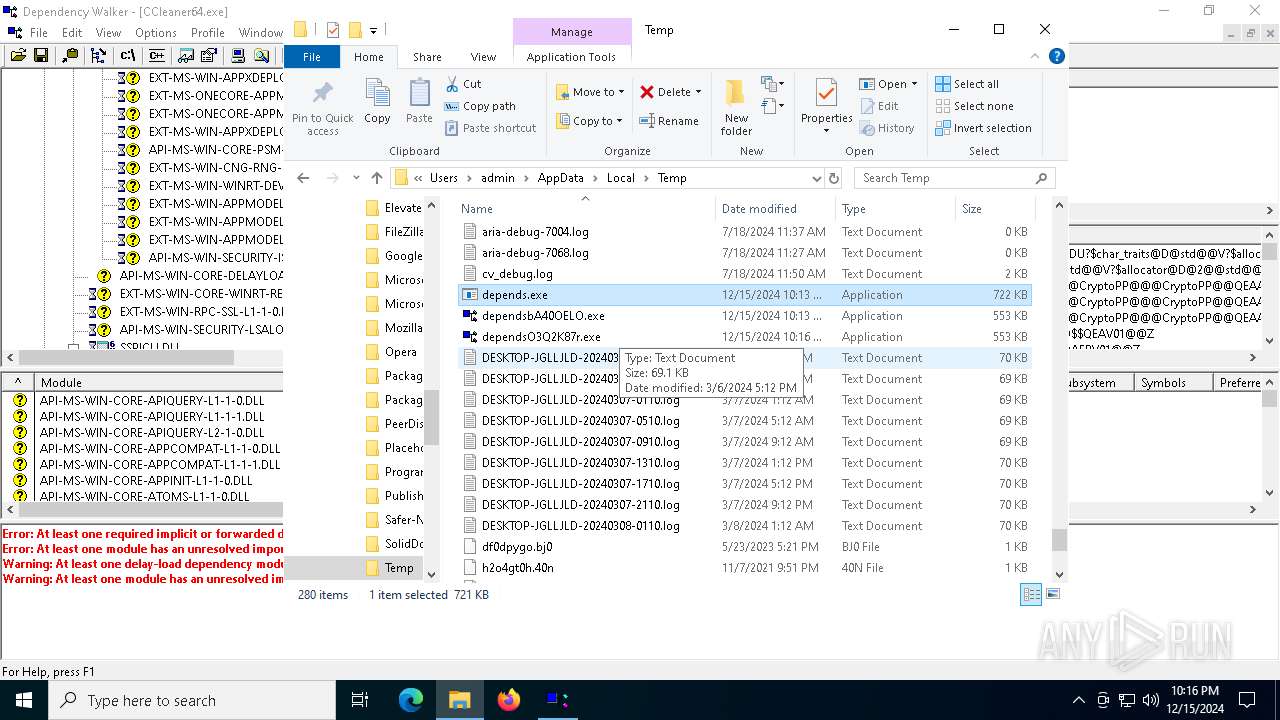
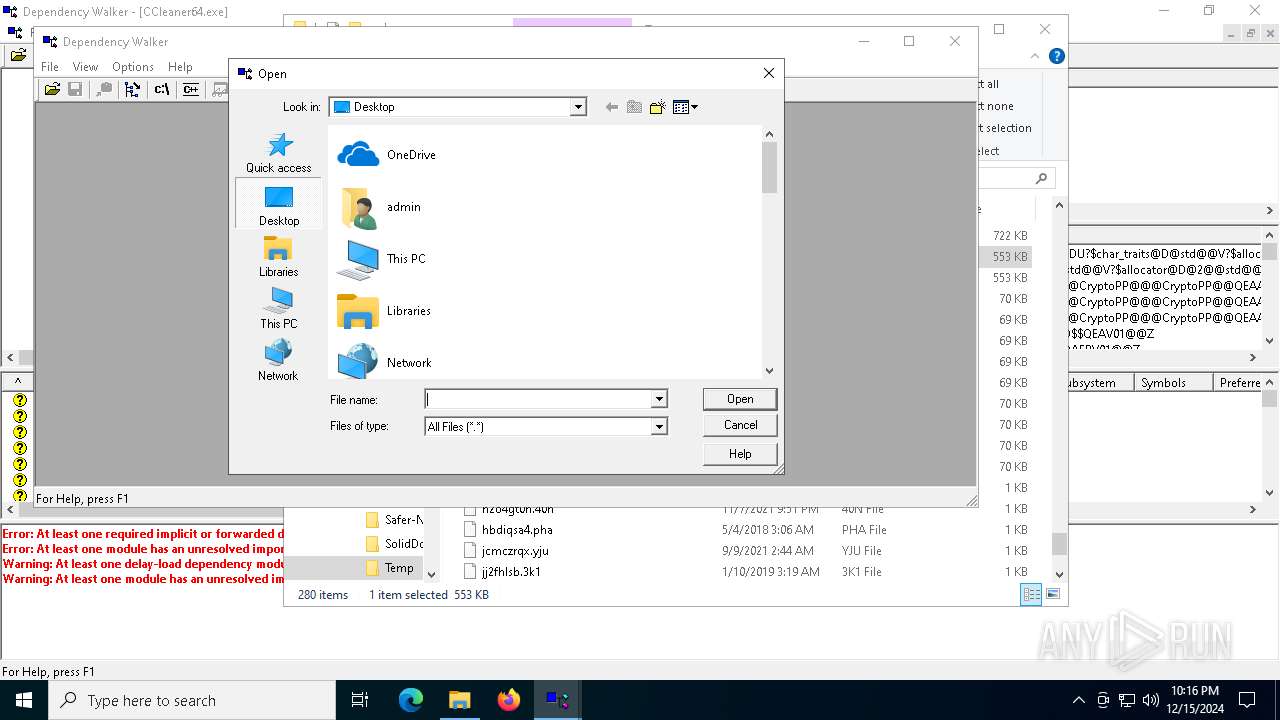
Create files in a temporary directory
- depends.exe (PID: 3820)
- depends.exe (PID: 6492)
Reads the computer name
- dependsbA40OELO.exe (PID: 1200)
- dependsO3Q2K87r.exe (PID: 6612)
- dependsO3Q2K87r.exe (PID: 4536)
- dependsbA40OELO.exe (PID: 132)
- dependsbA40OELO.exe (PID: 4980)
The sample compiled with english language support
- depends.exe (PID: 3820)
- depends.exe (PID: 6492)
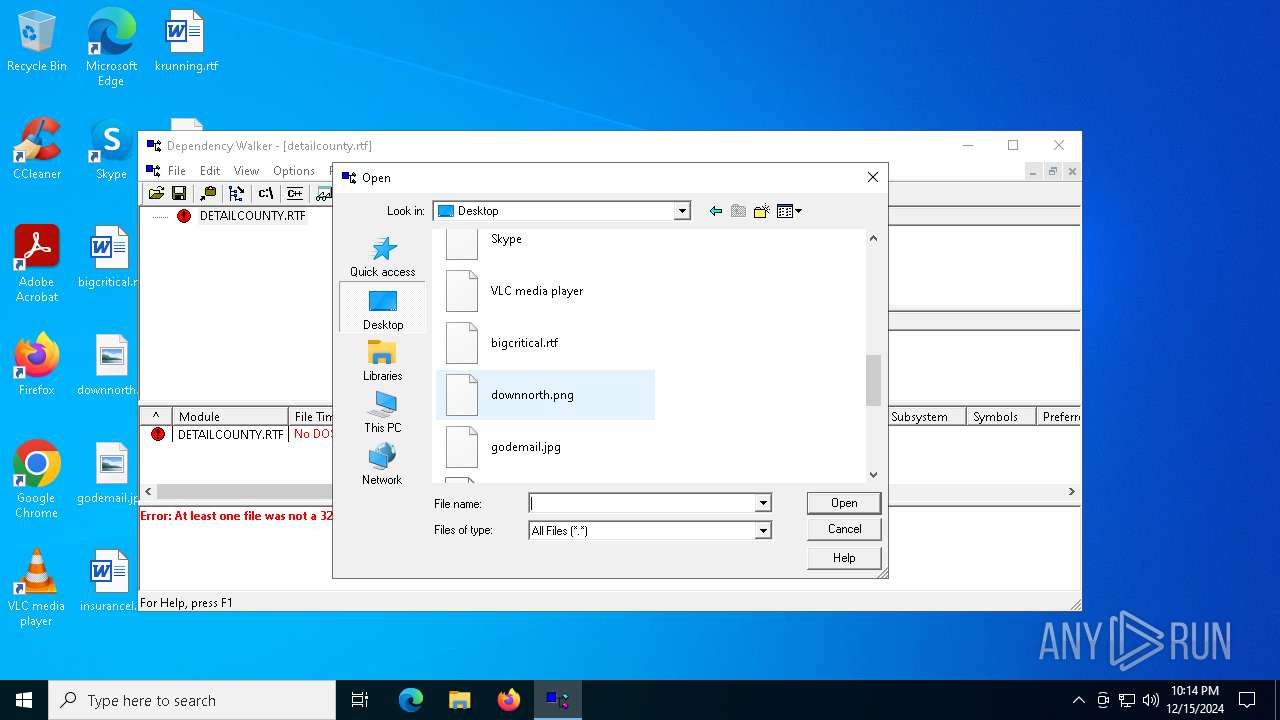
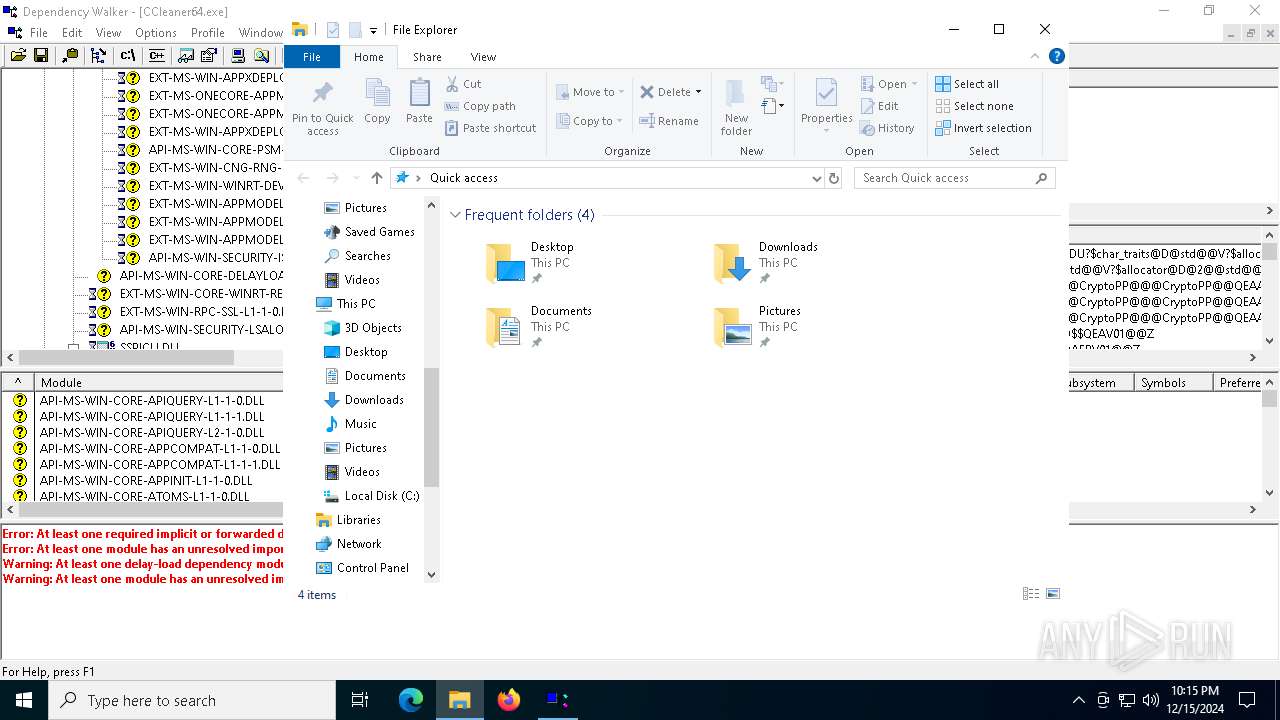
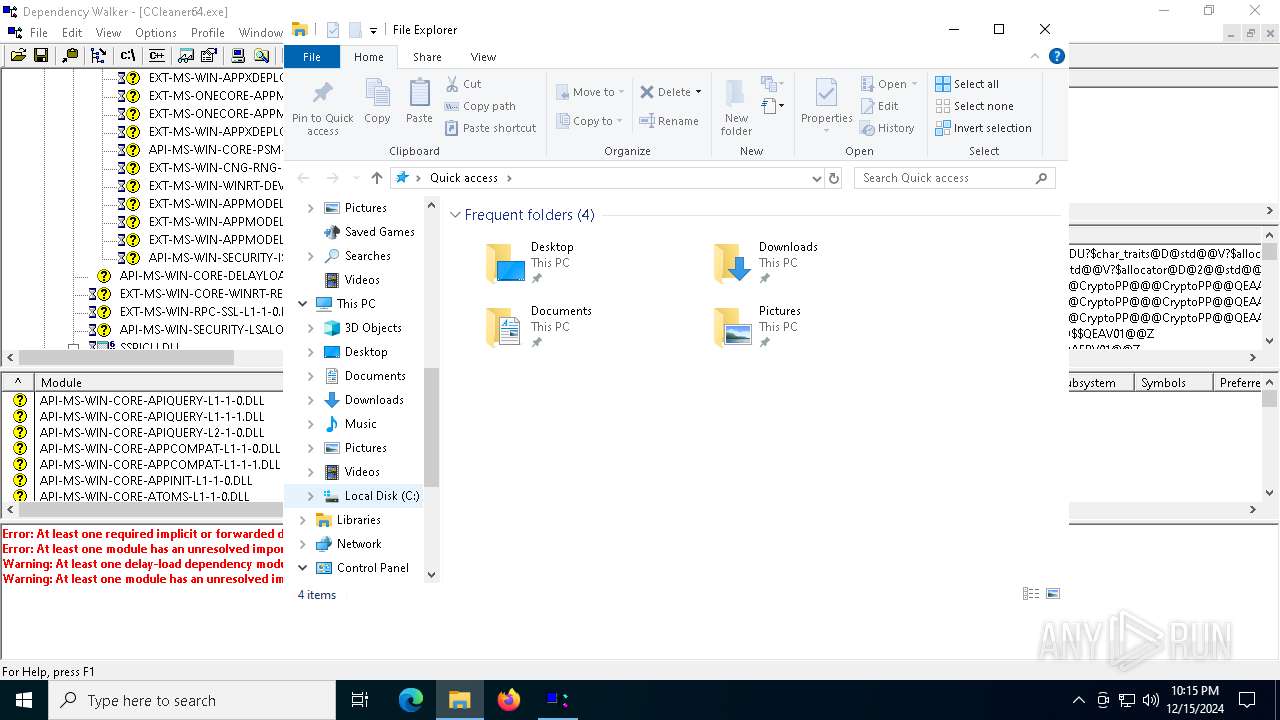
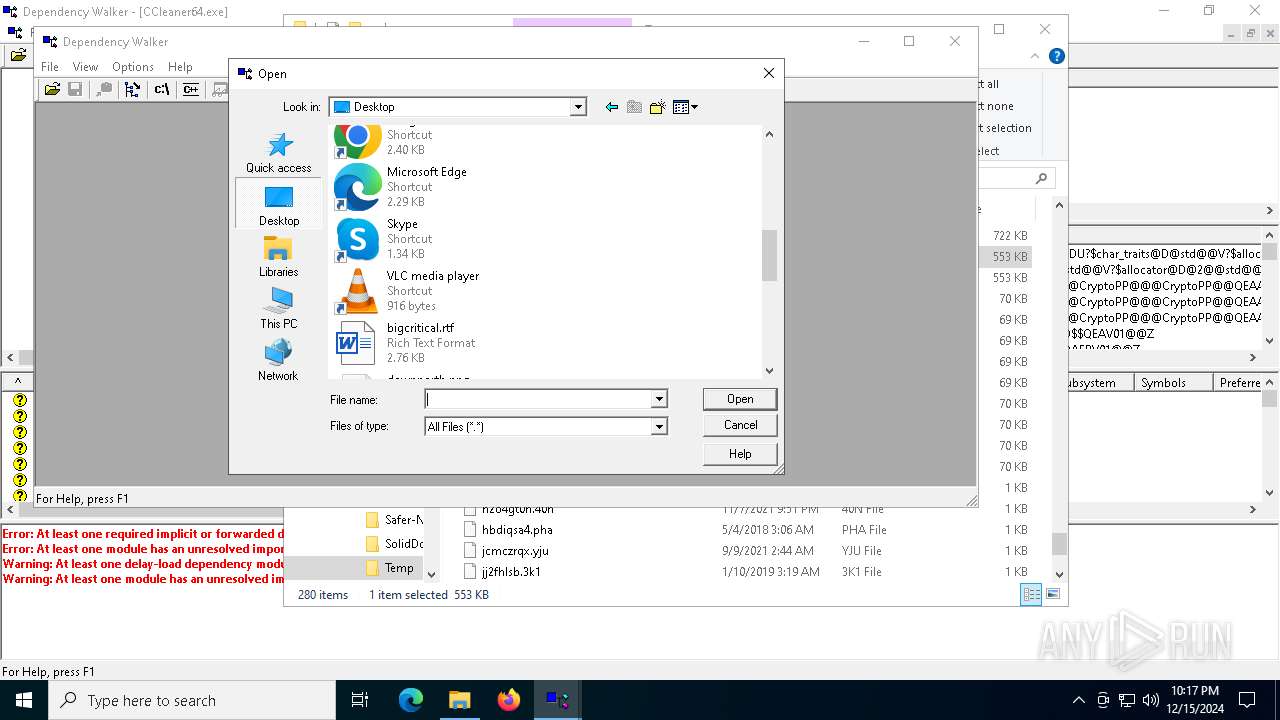
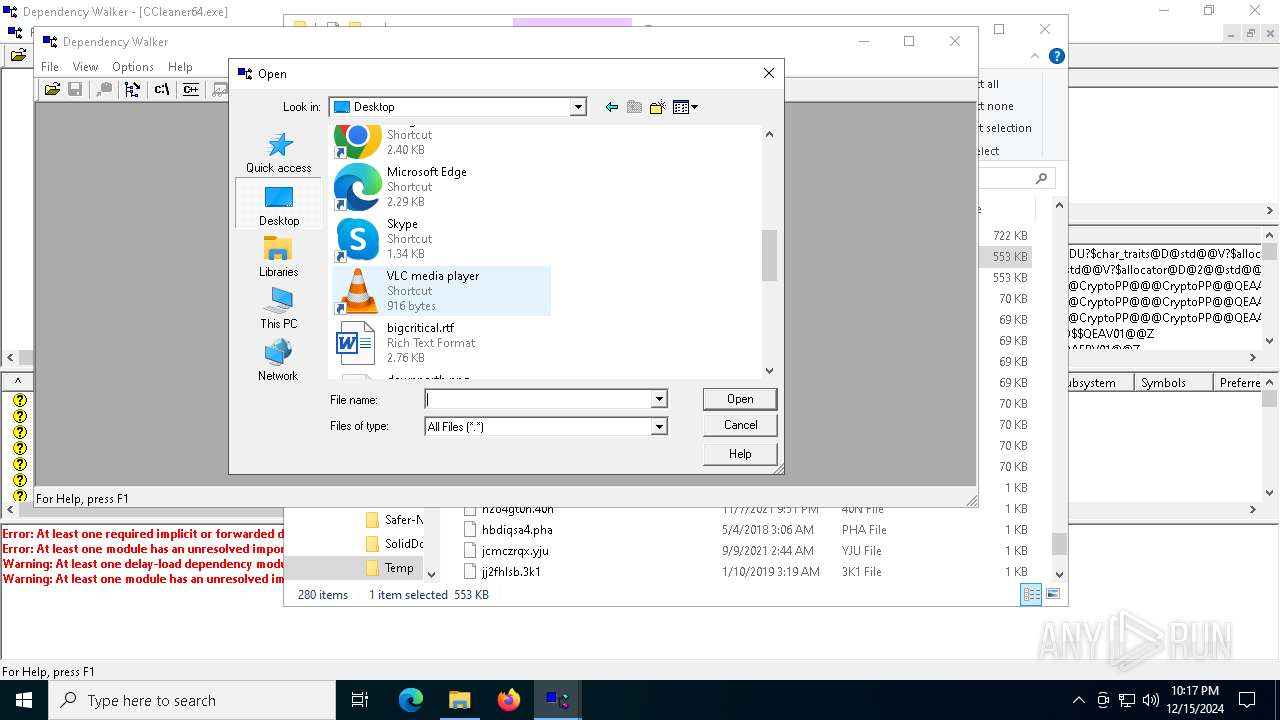
Manual execution by a user
- depends.exe (PID: 6492)
- dependsO3Q2K87r.exe (PID: 4536)
- dependsbA40OELO.exe (PID: 4980)
- dependsbA40OELO.exe (PID: 132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:12:10 11:38:55+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 2.36 |
| CodeSize: | 129024 |
| InitializedDataSize: | 737792 |
| UninitializedDataSize: | 4096 |
| EntryPoint: | 0x1125 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
Total processes
136
Monitored processes
8
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
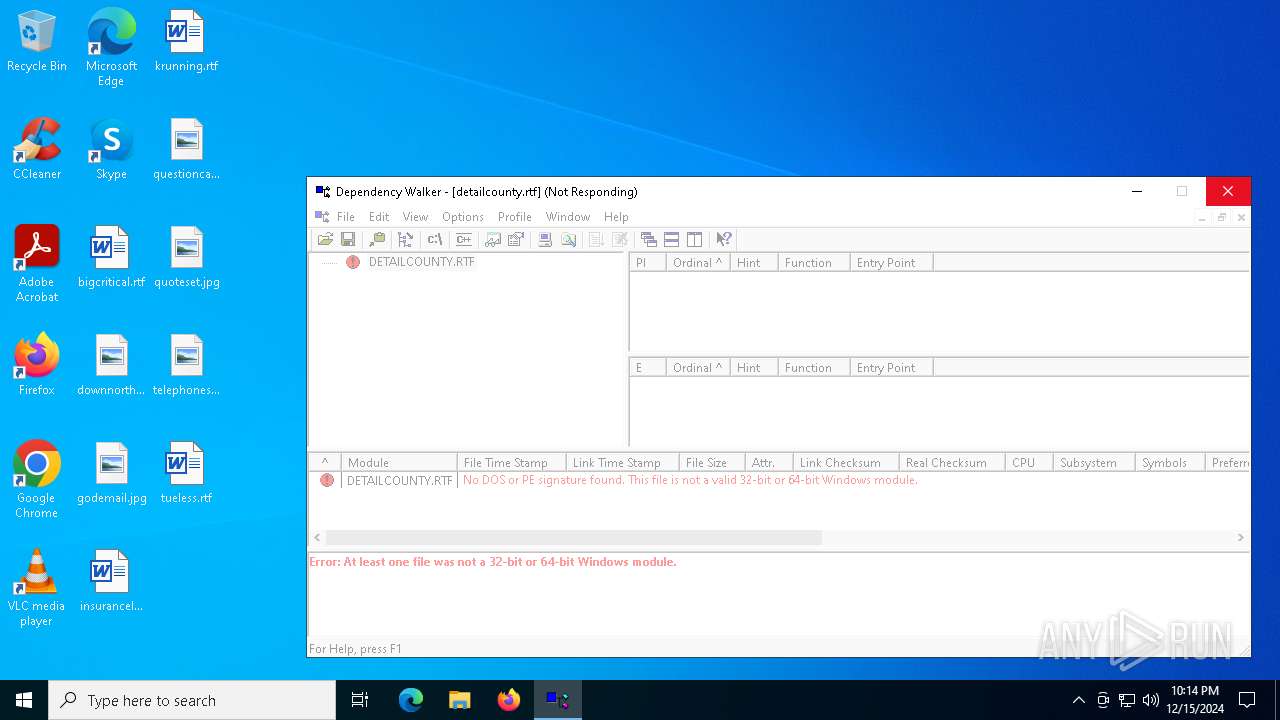
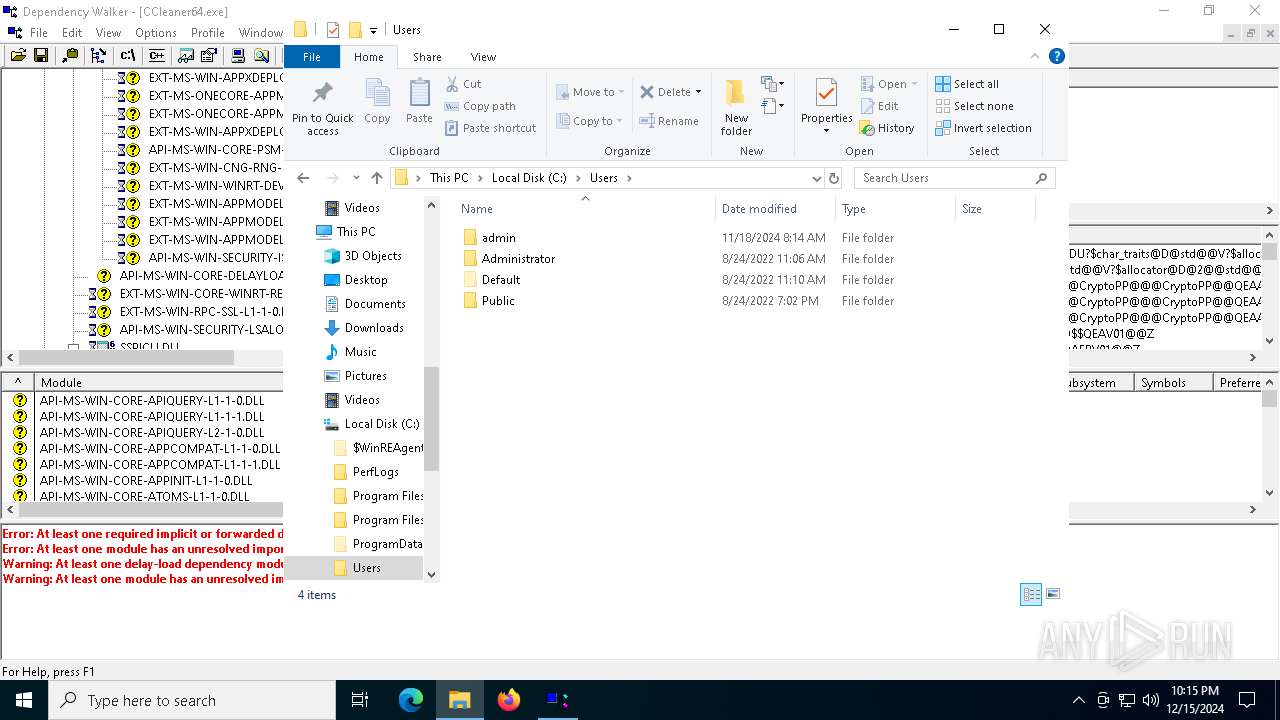
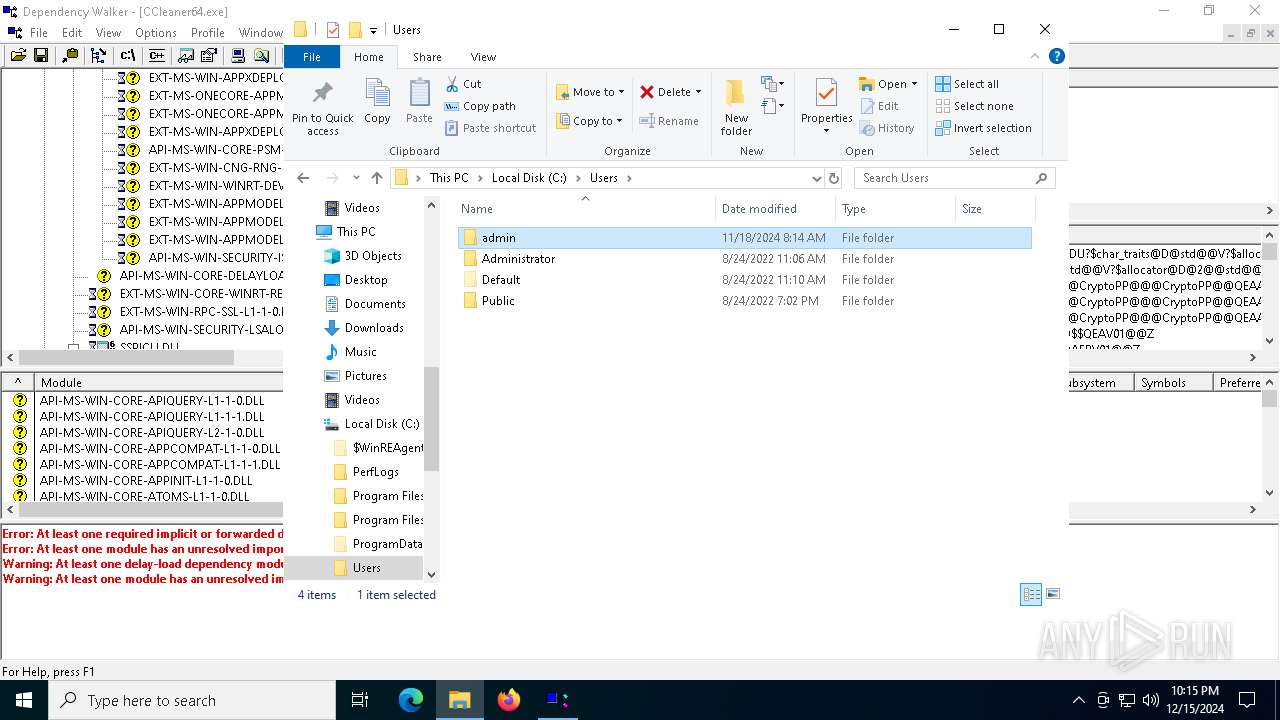
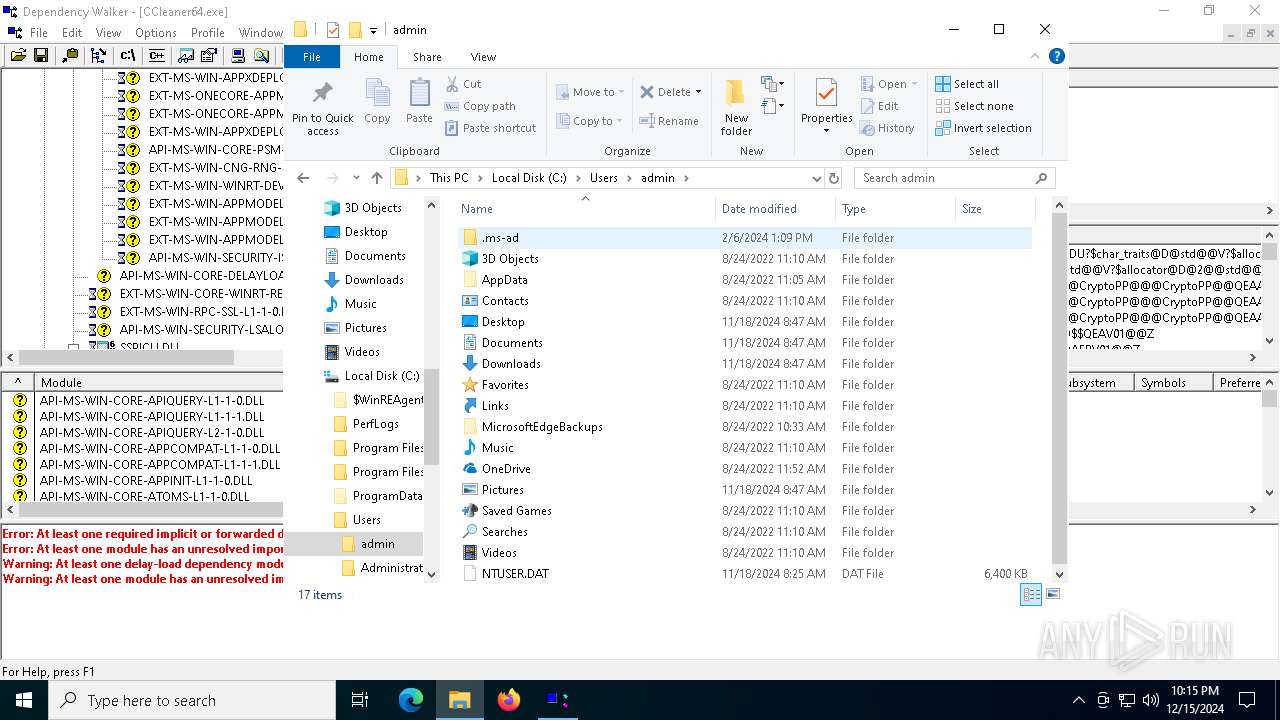
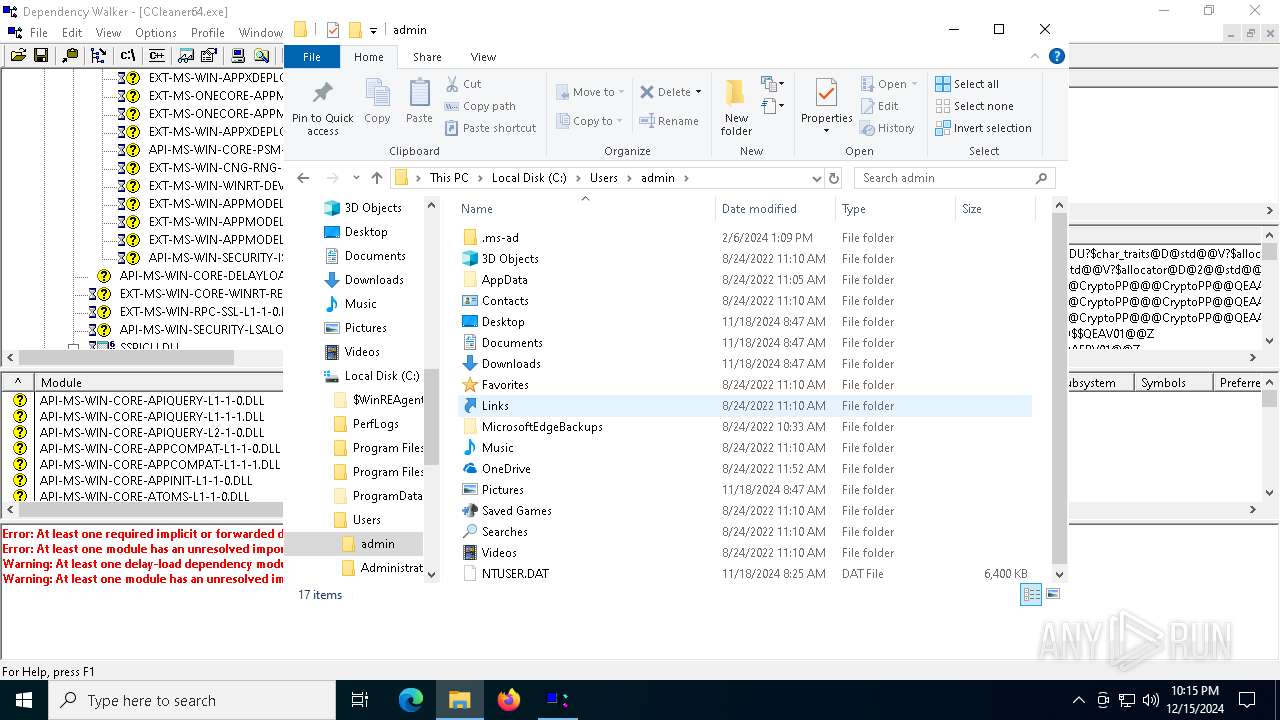
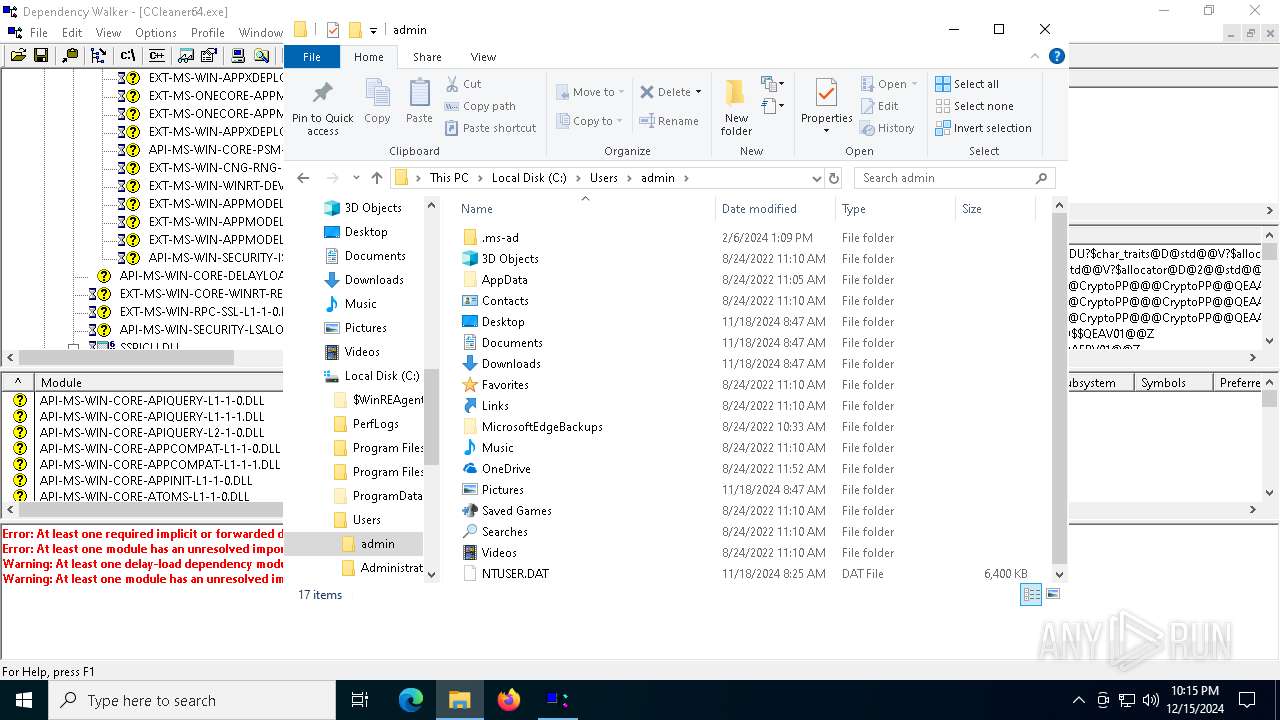
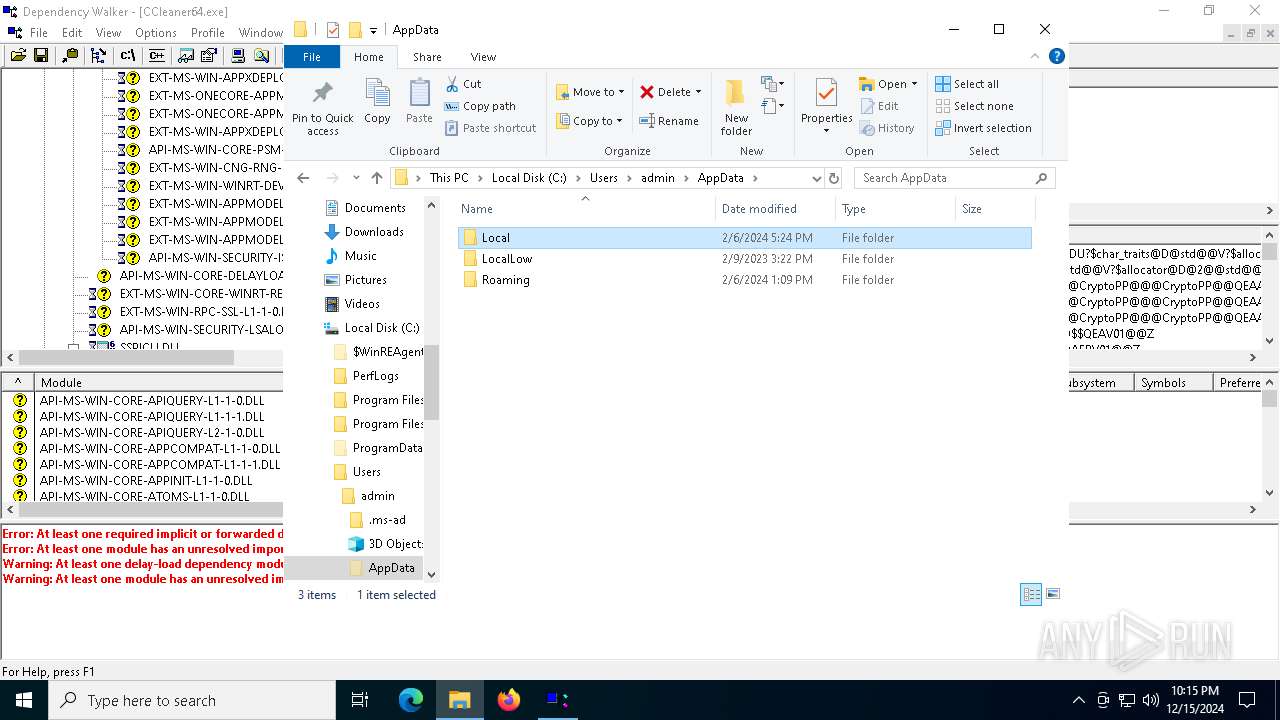
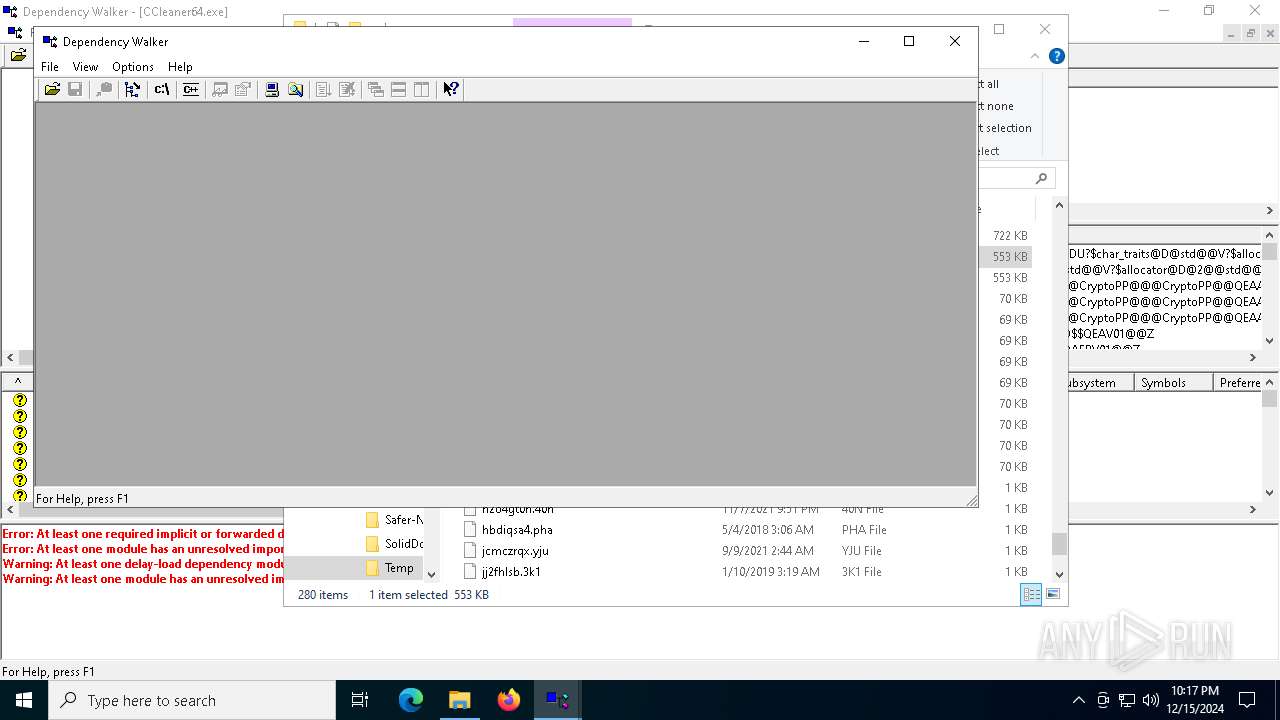
| 132 | "C:\Users\admin\AppData\Local\Temp\dependsbA40OELO.exe" | C:\Users\admin\AppData\Local\Temp\dependsbA40OELO.exe | — | explorer.exe | |||||||||||
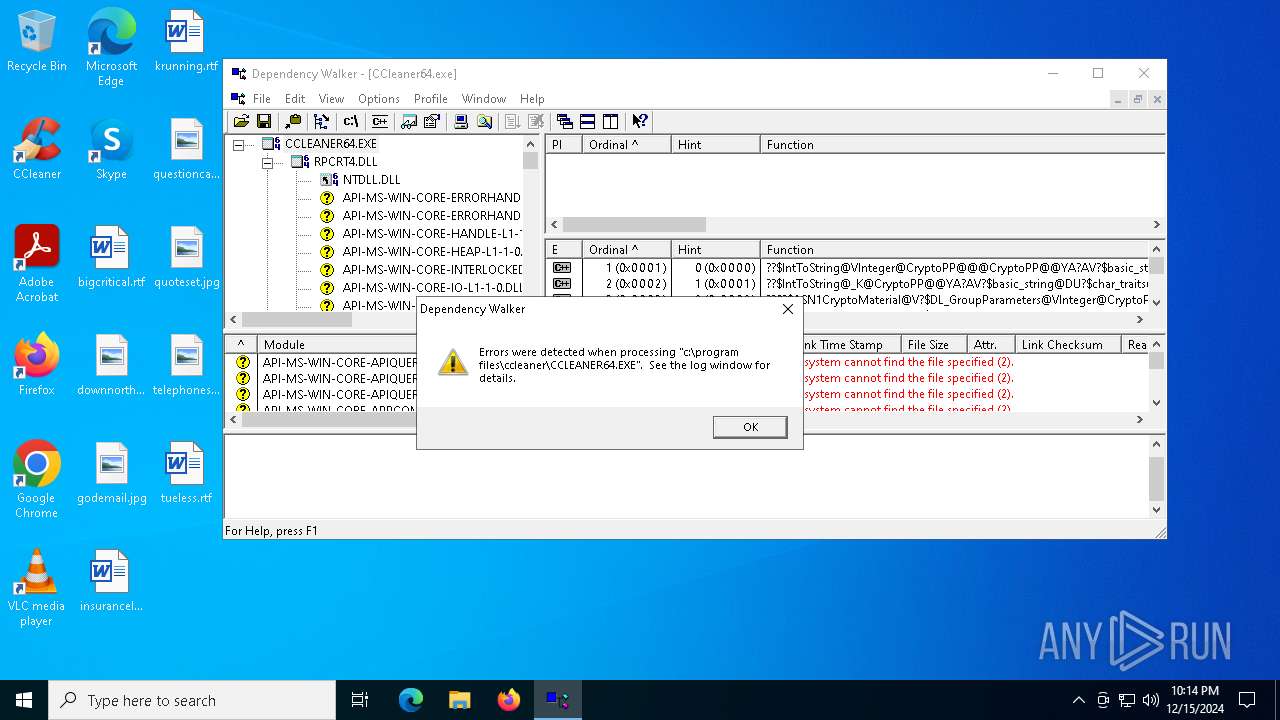
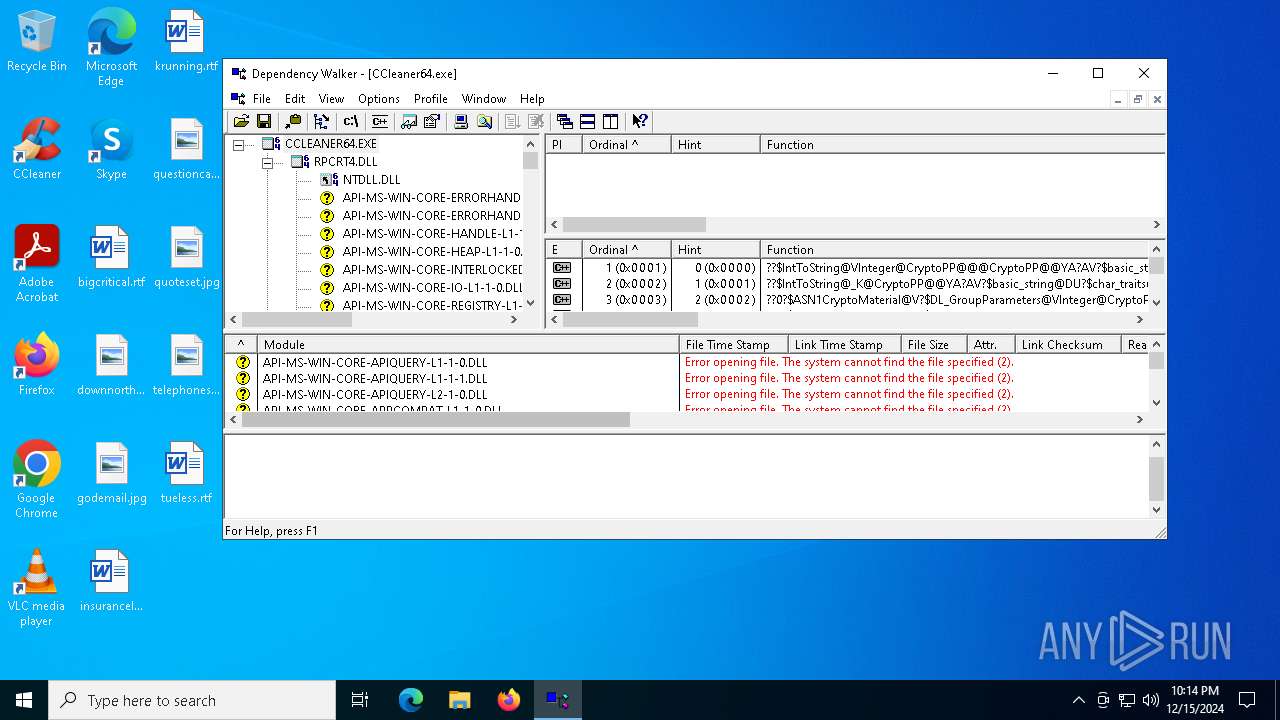
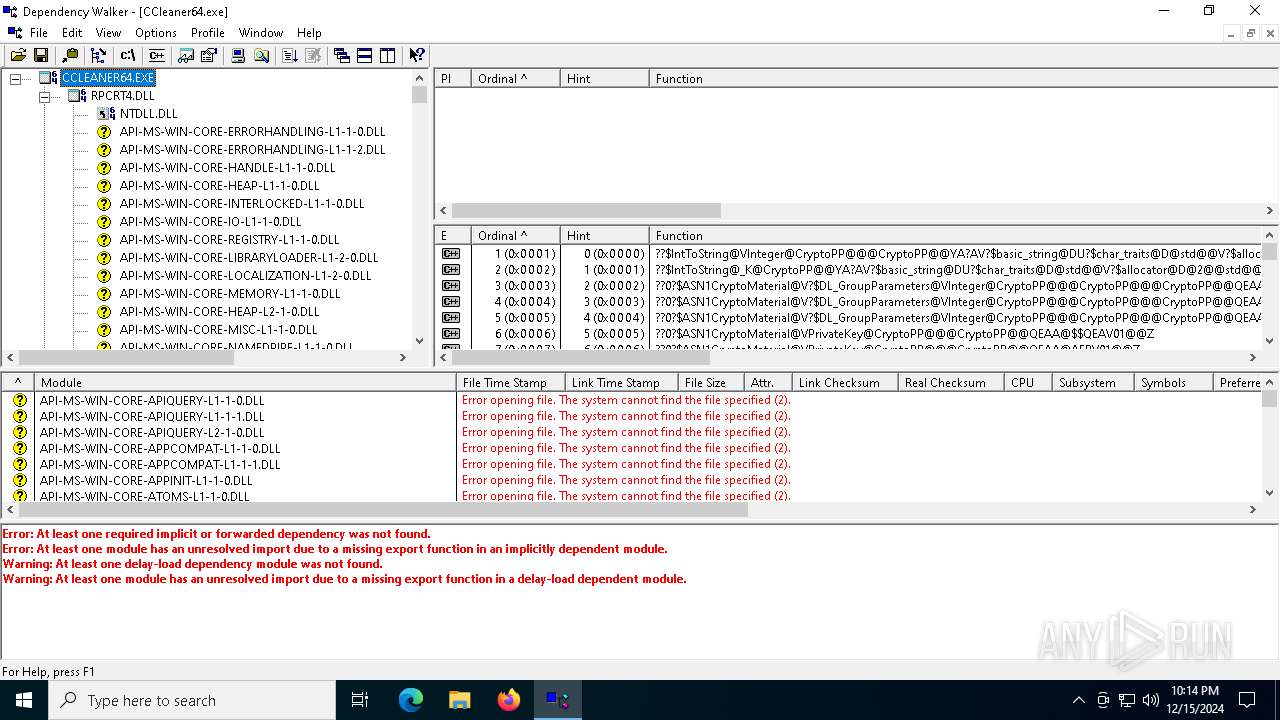
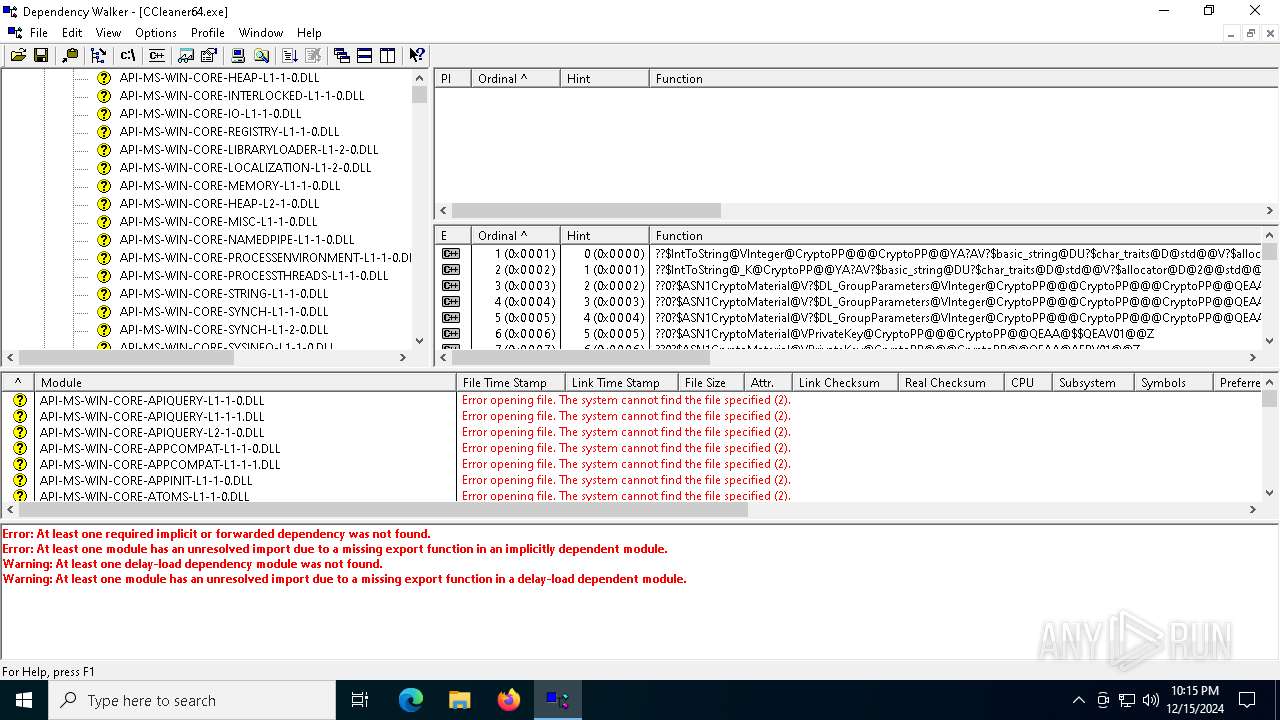
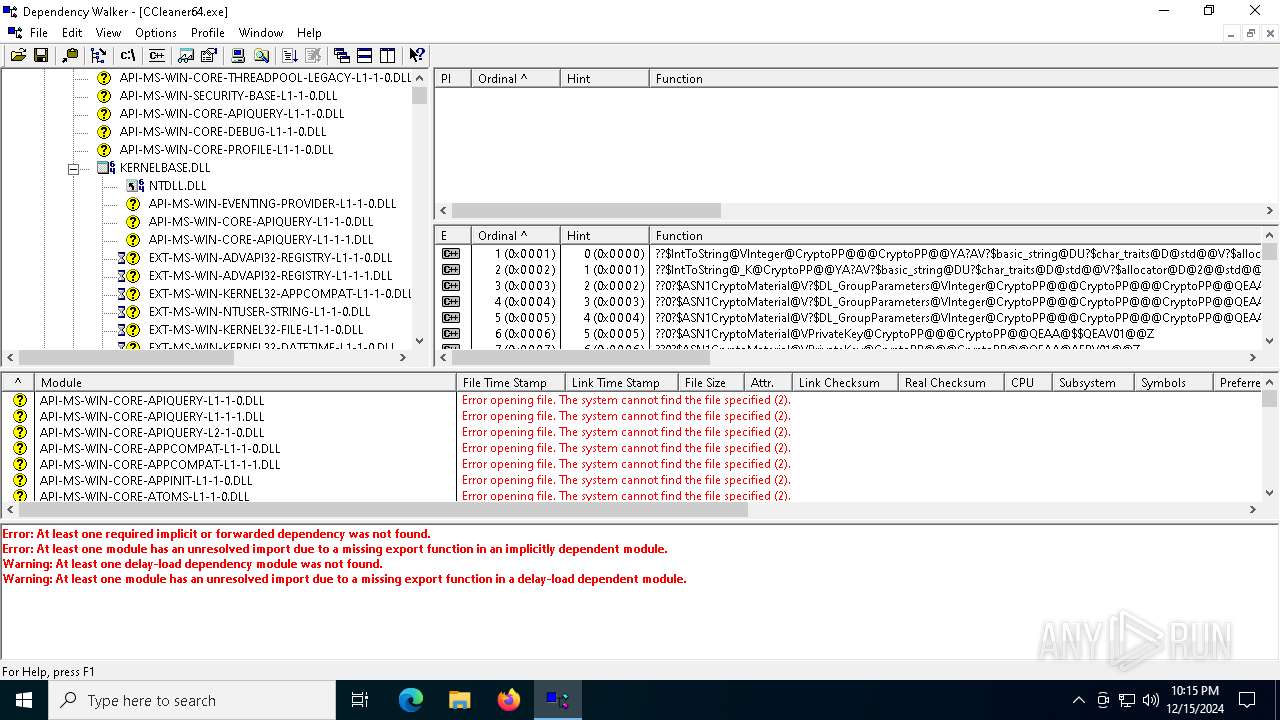
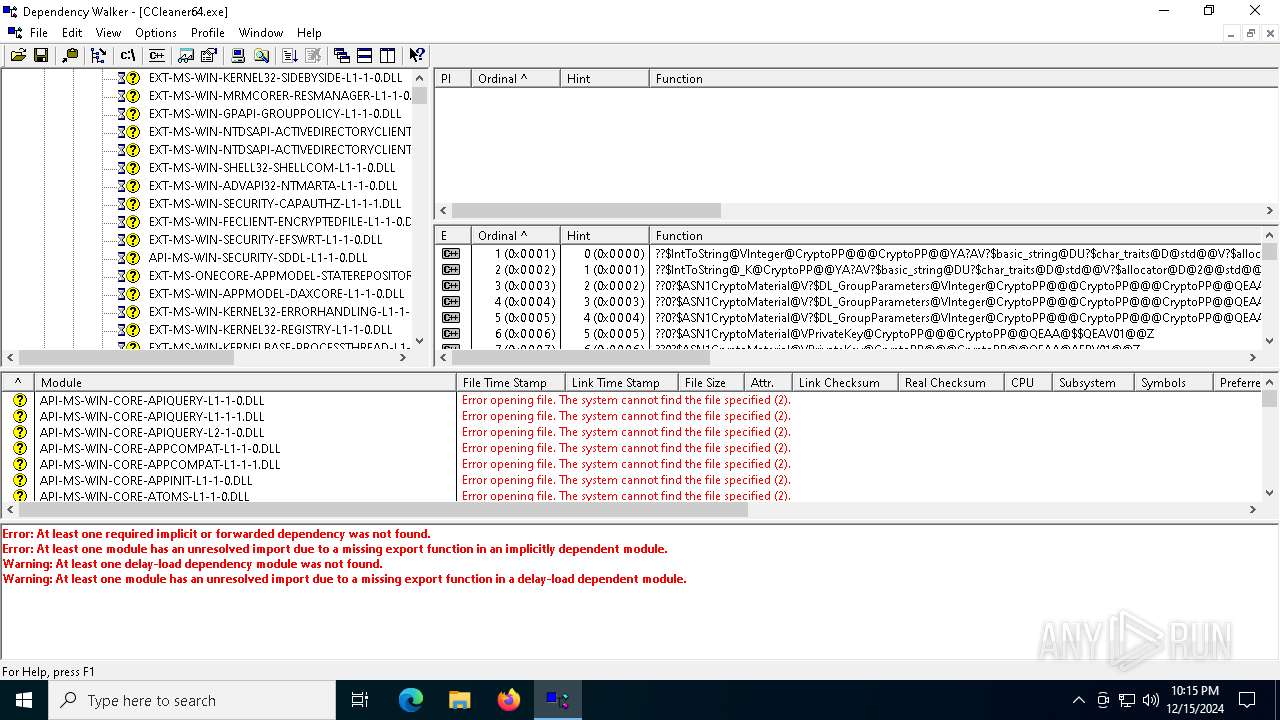
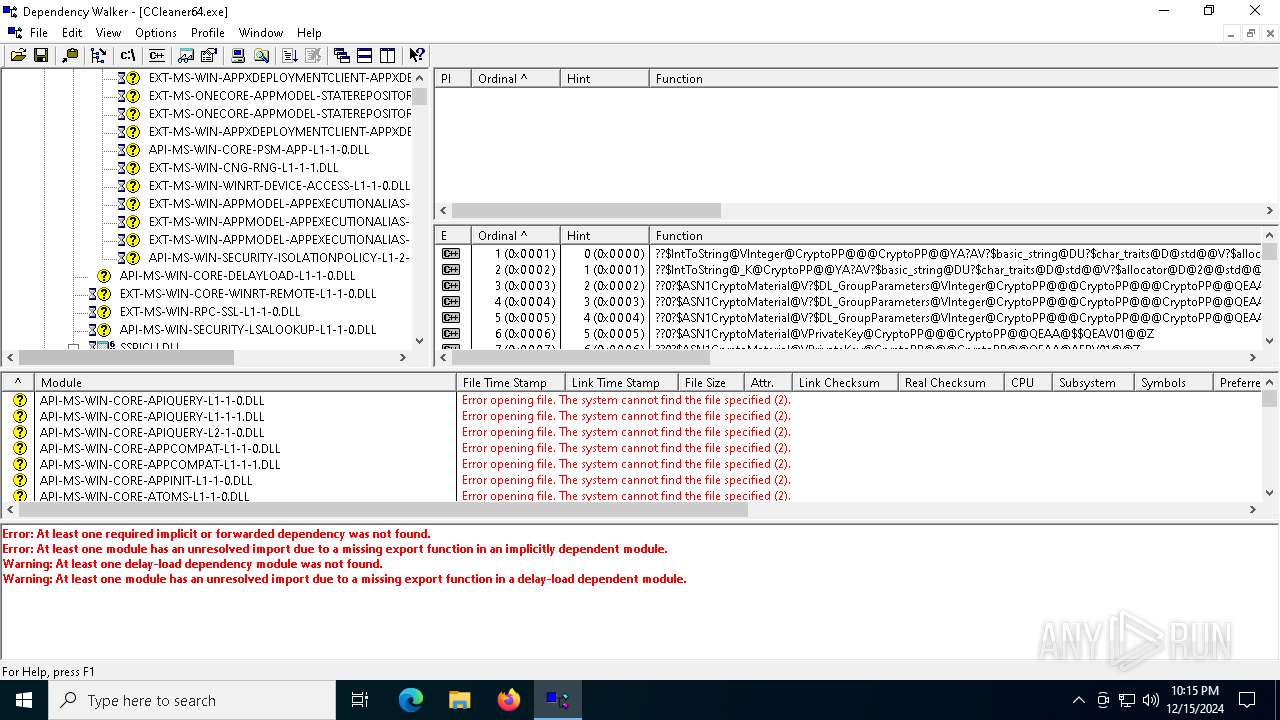
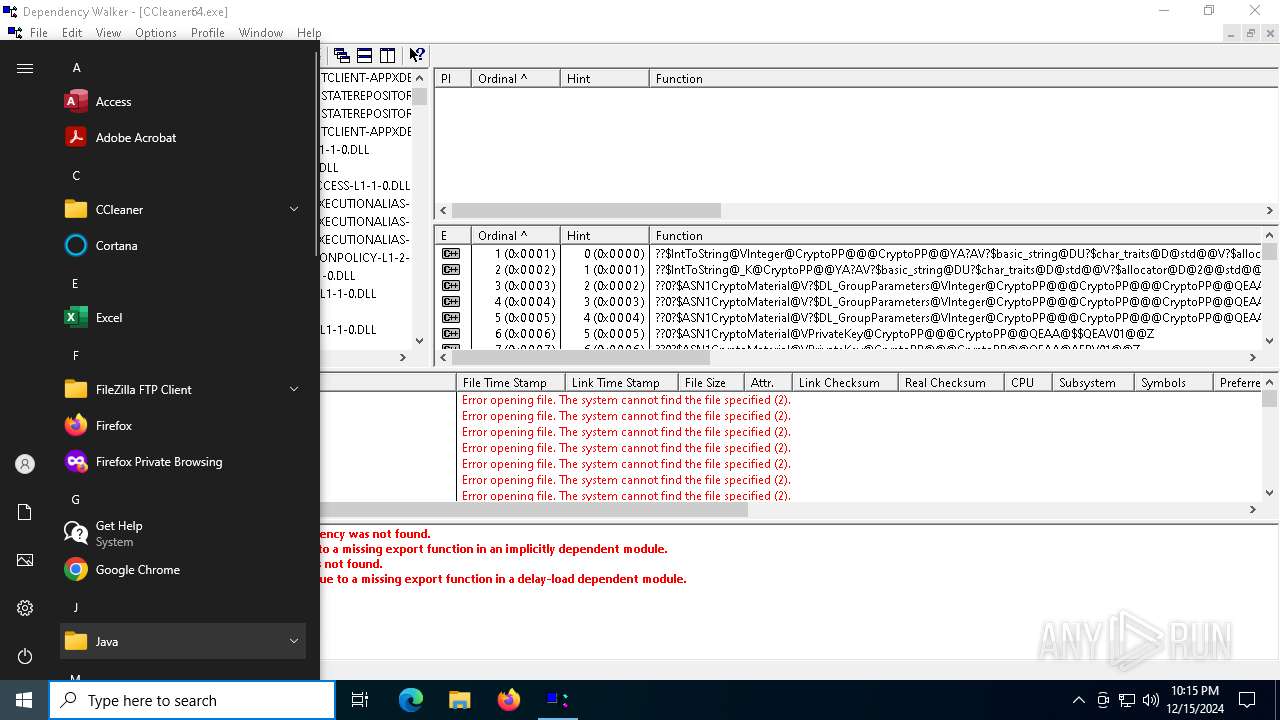
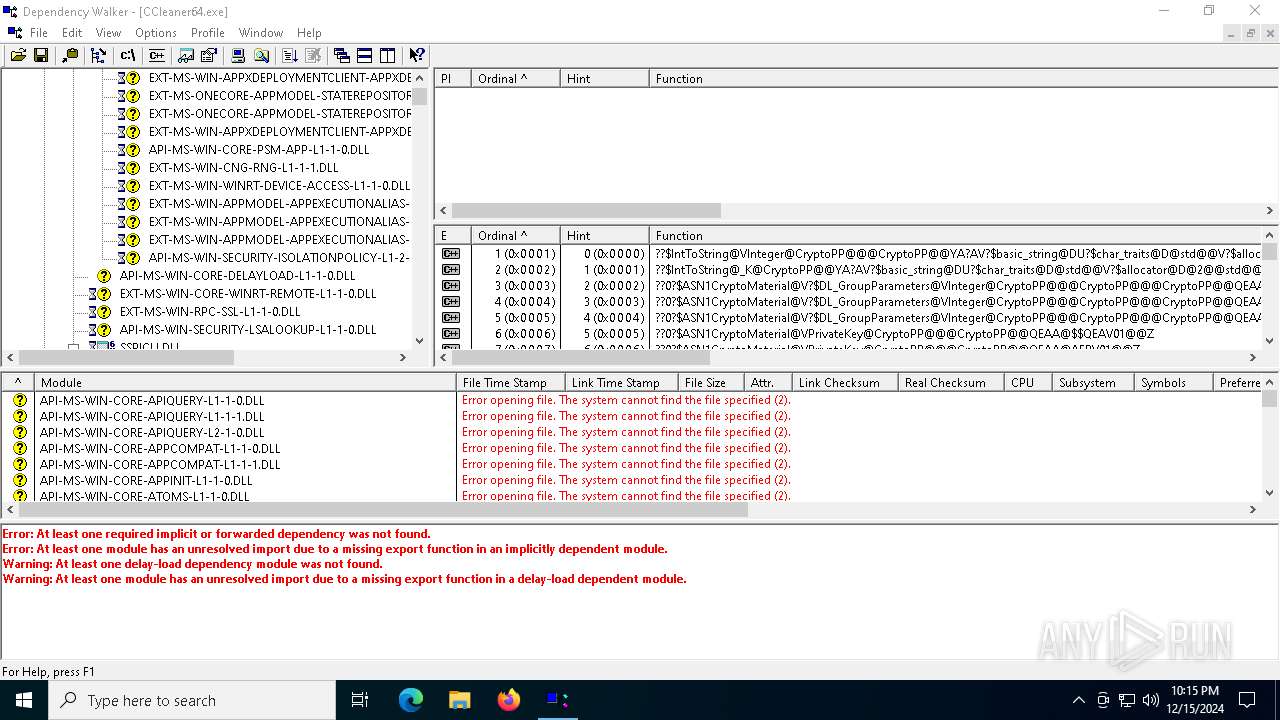
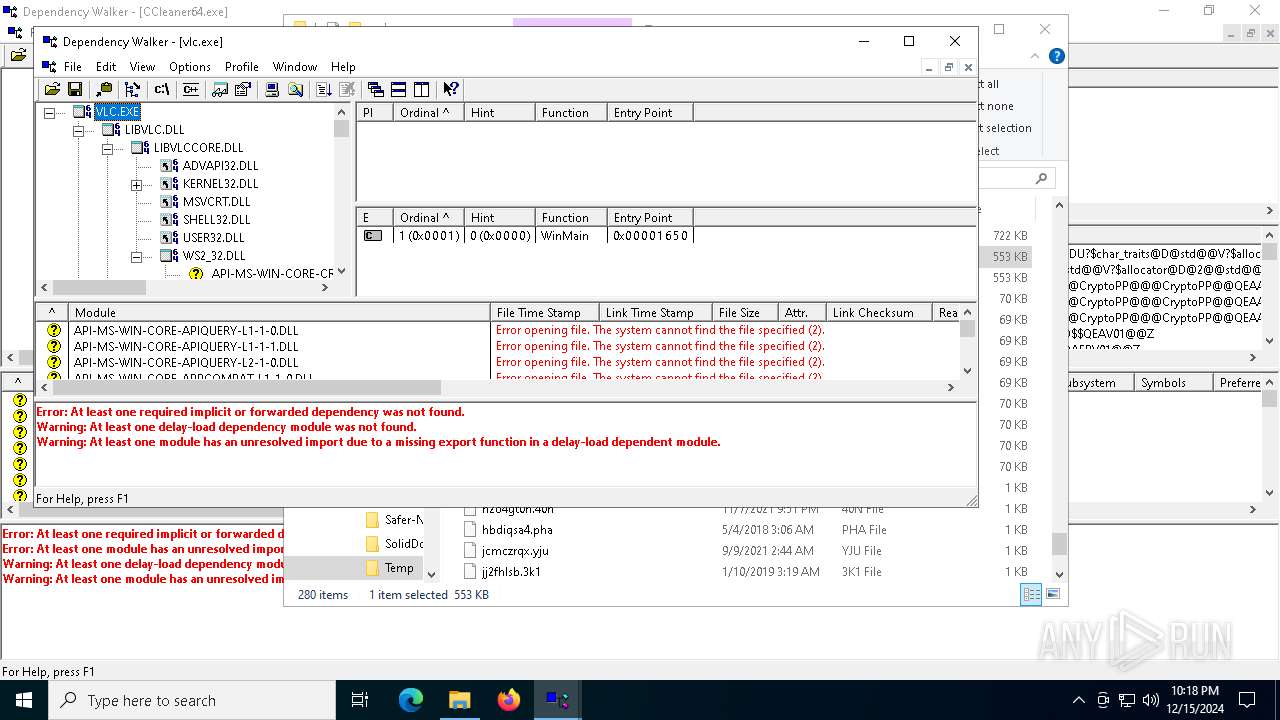
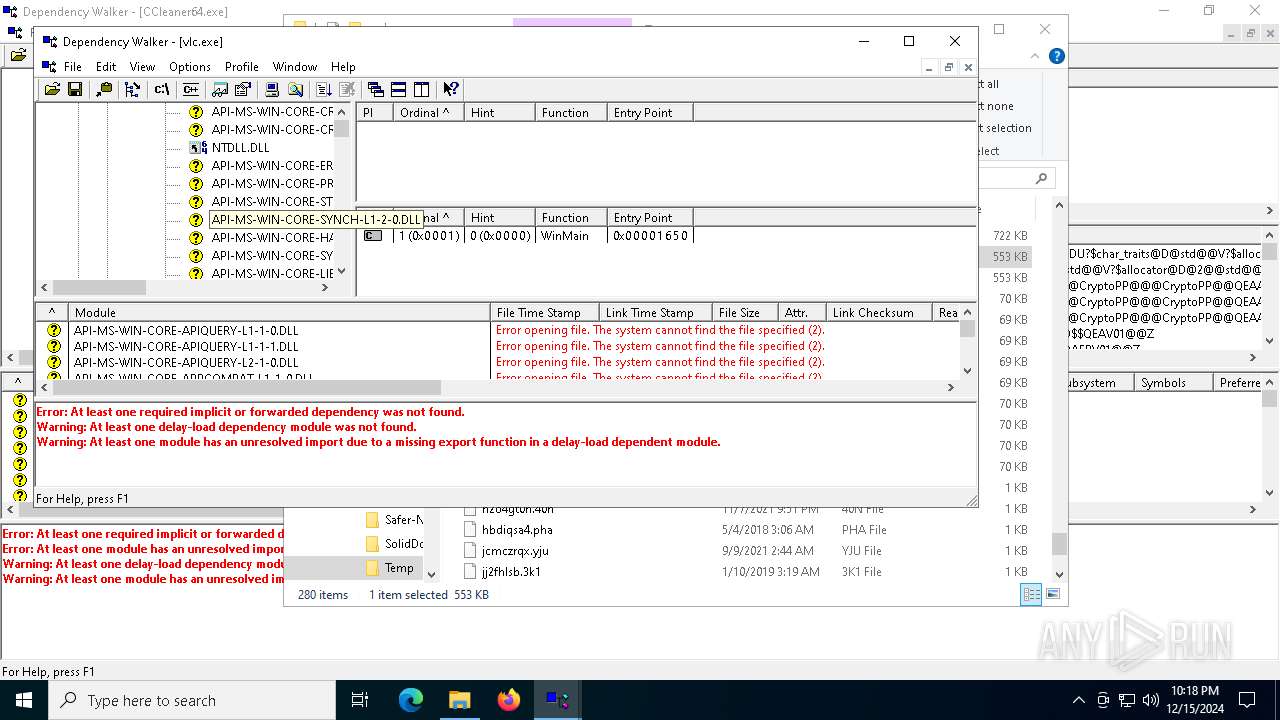
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dependency Walker for Win64 (x64) Exit code: 0 Version: 2.2.6000 Modules
| |||||||||||||||
| 1200 | C:\Users\admin\AppData\Local\Temp\dependsbA40OELO.exe | C:\Users\admin\AppData\Local\Temp\dependsbA40OELO.exe | — | depends.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dependency Walker for Win64 (x64) Version: 2.2.6000 Modules
| |||||||||||||||
| 3420 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3820 | "C:\Users\admin\AppData\Local\Temp\depends.exe" | C:\Users\admin\AppData\Local\Temp\depends.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4536 | "C:\Users\admin\AppData\Local\Temp\dependsO3Q2K87r.exe" | C:\Users\admin\AppData\Local\Temp\dependsO3Q2K87r.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dependency Walker for Win64 (x64) Exit code: 0 Version: 2.2.6000 Modules
| |||||||||||||||
| 4980 | "C:\Users\admin\AppData\Local\Temp\dependsbA40OELO.exe" | C:\Users\admin\AppData\Local\Temp\dependsbA40OELO.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dependency Walker for Win64 (x64) Version: 2.2.6000 Modules
| |||||||||||||||
| 6492 | "C:\Users\admin\AppData\Local\Temp\depends.exe" | C:\Users\admin\AppData\Local\Temp\depends.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6612 | C:\Users\admin\AppData\Local\Temp\dependsO3Q2K87r.exe | C:\Users\admin\AppData\Local\Temp\dependsO3Q2K87r.exe | — | depends.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Dependency Walker for Win64 (x64) Exit code: 0 Version: 2.2.6000 Modules
| |||||||||||||||
Total events
6 754
Read events
6 586
Write events
157
Delete events
11
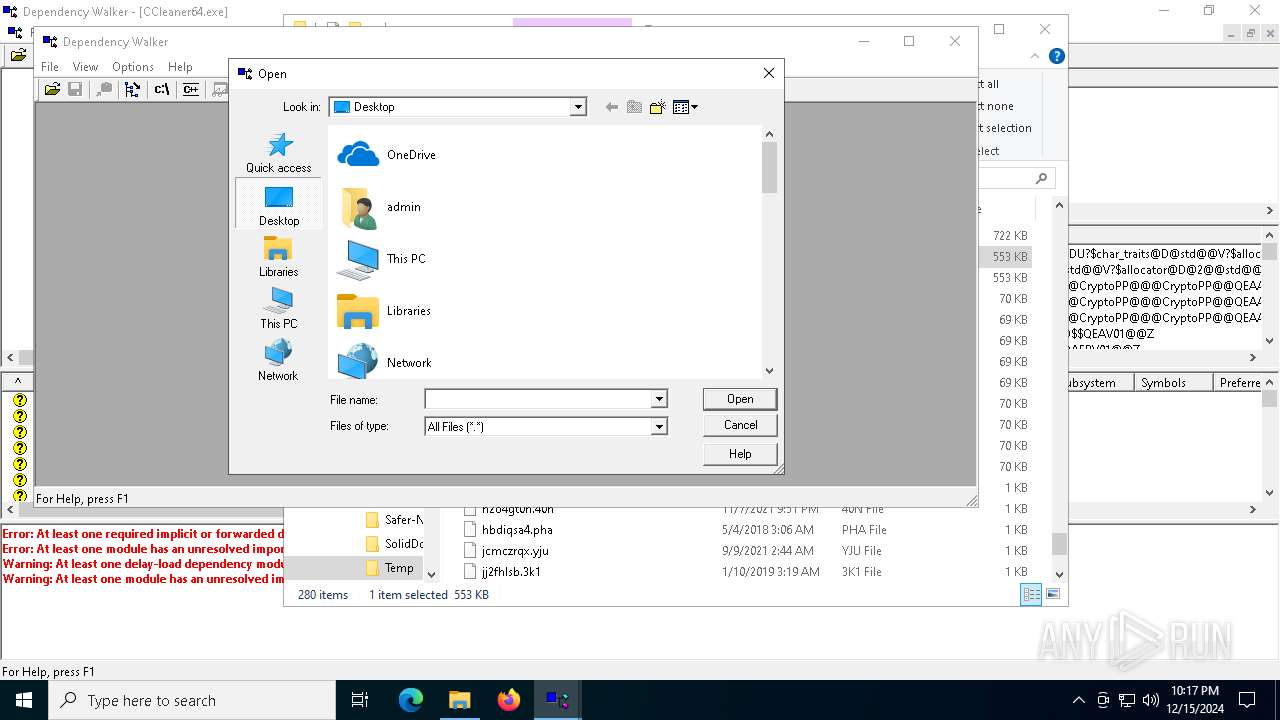
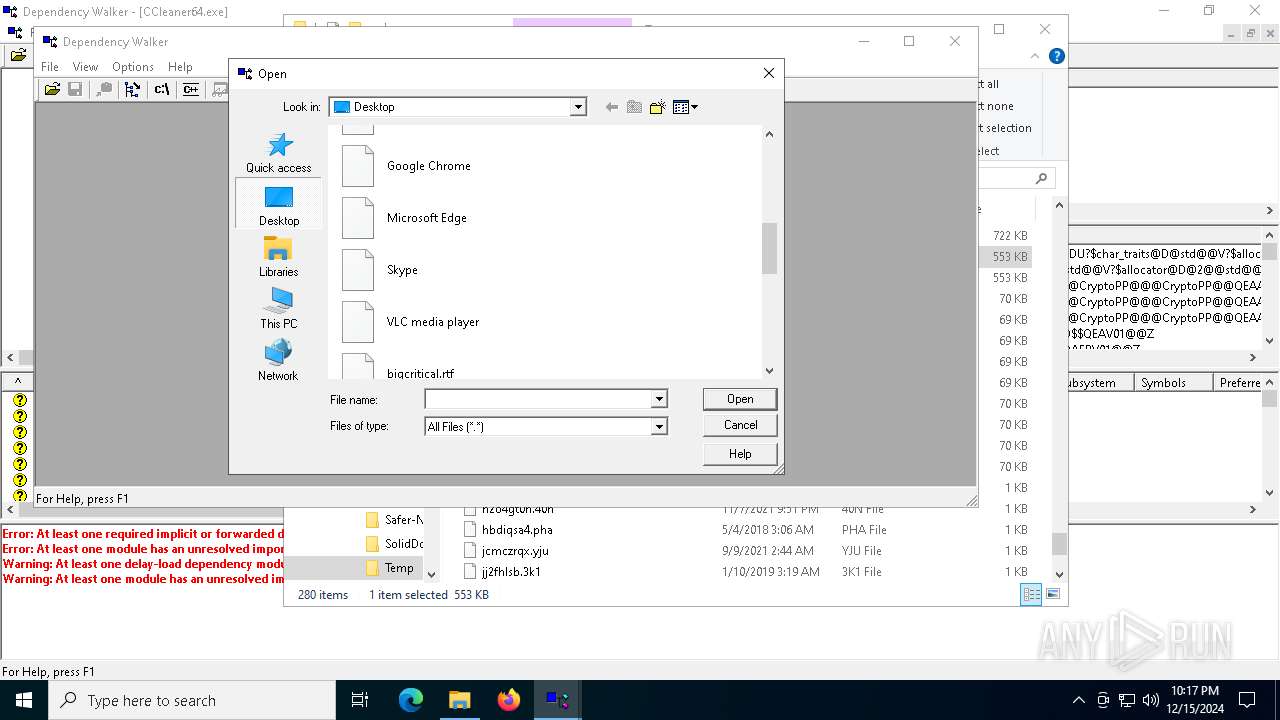
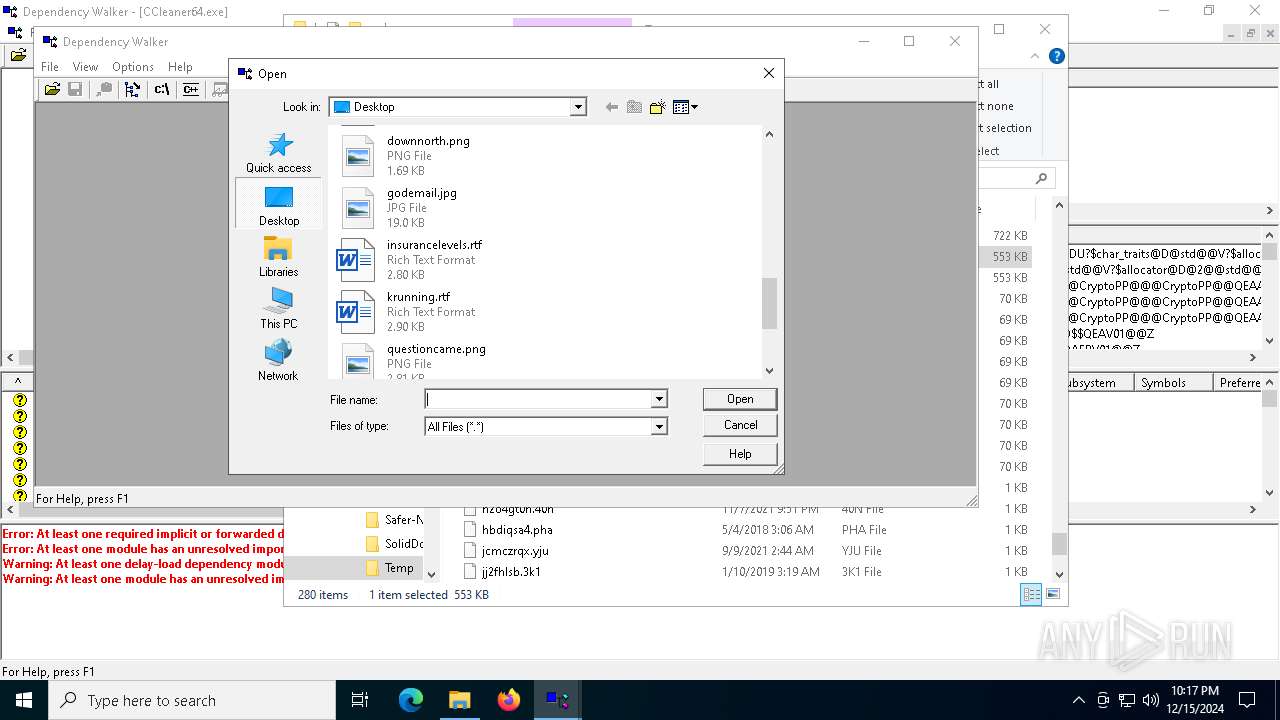
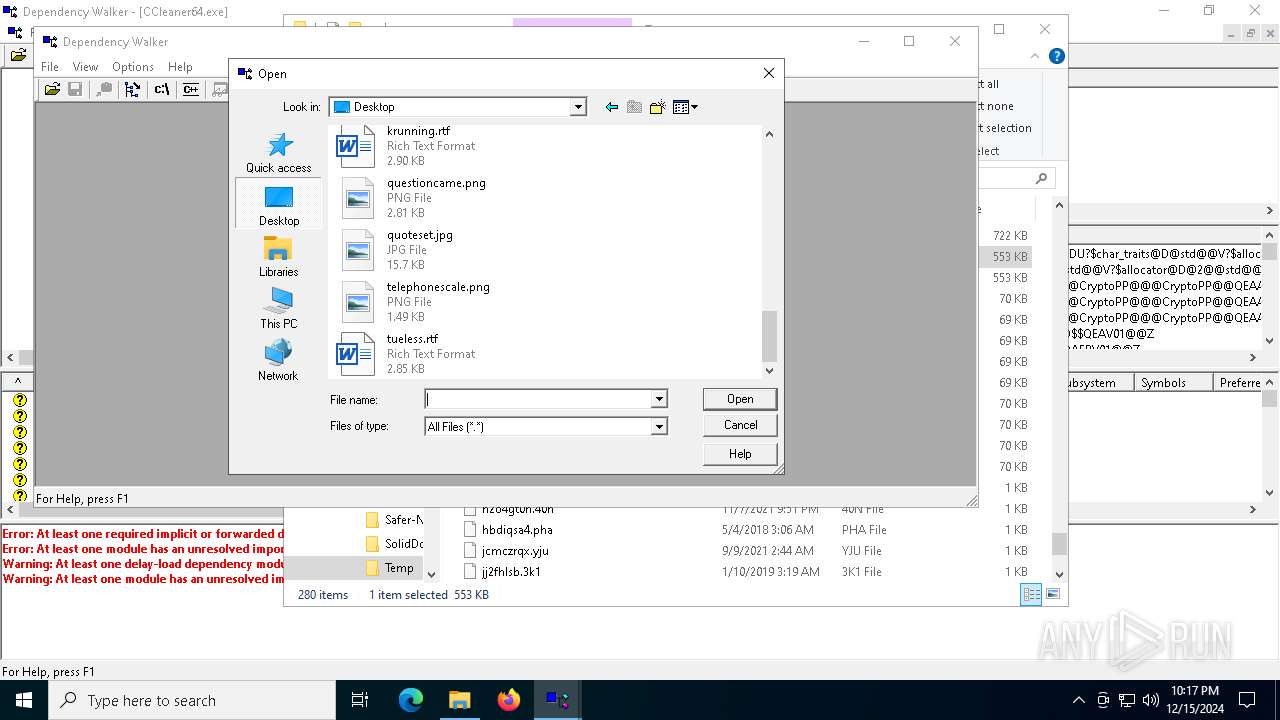
Modification events
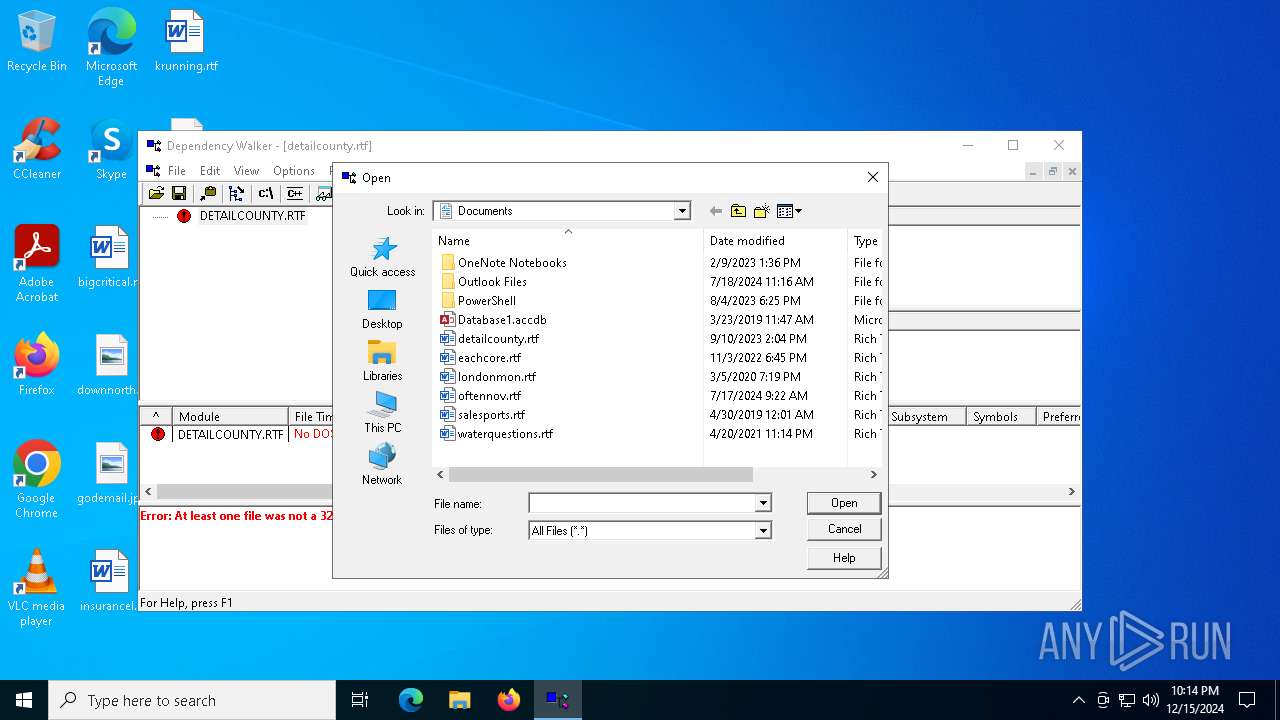
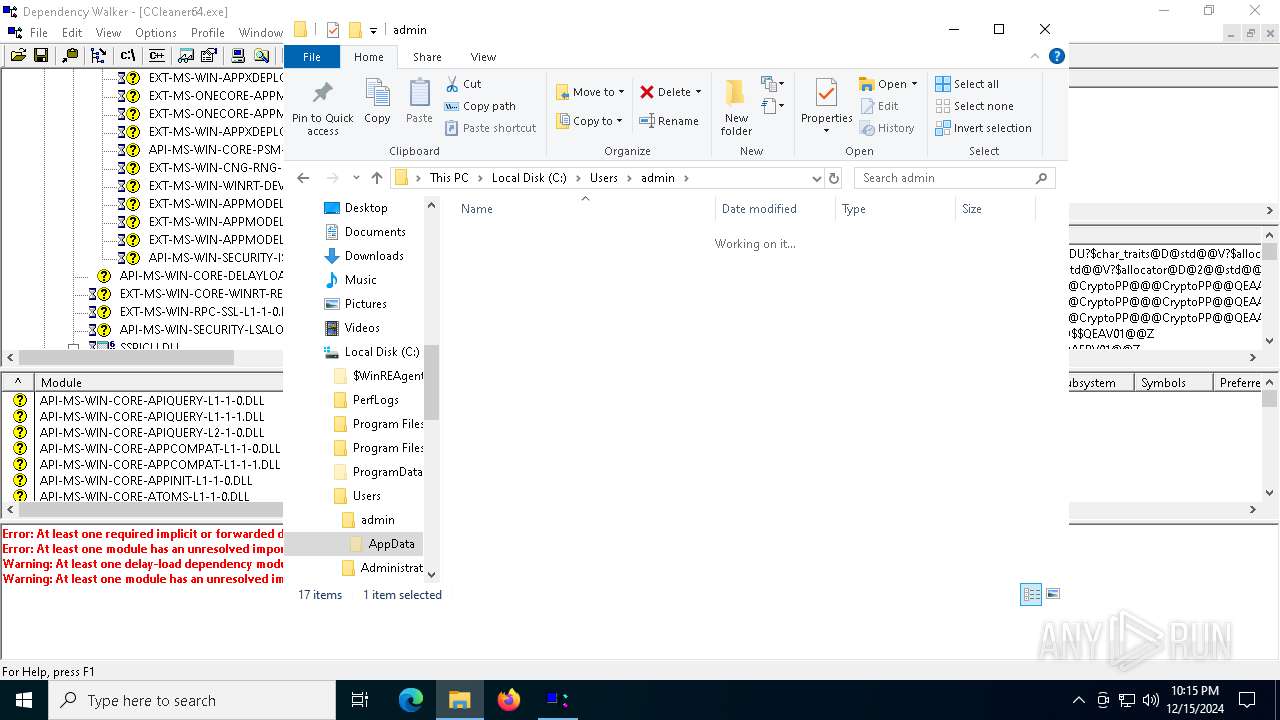
| (PID) Process: | (1200) dependsbA40OELO.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (1200) dependsbA40OELO.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000E0000000300000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (1200) dependsbA40OELO.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 040000000000000005000000020000000100000003000000FFFFFFFF | |||
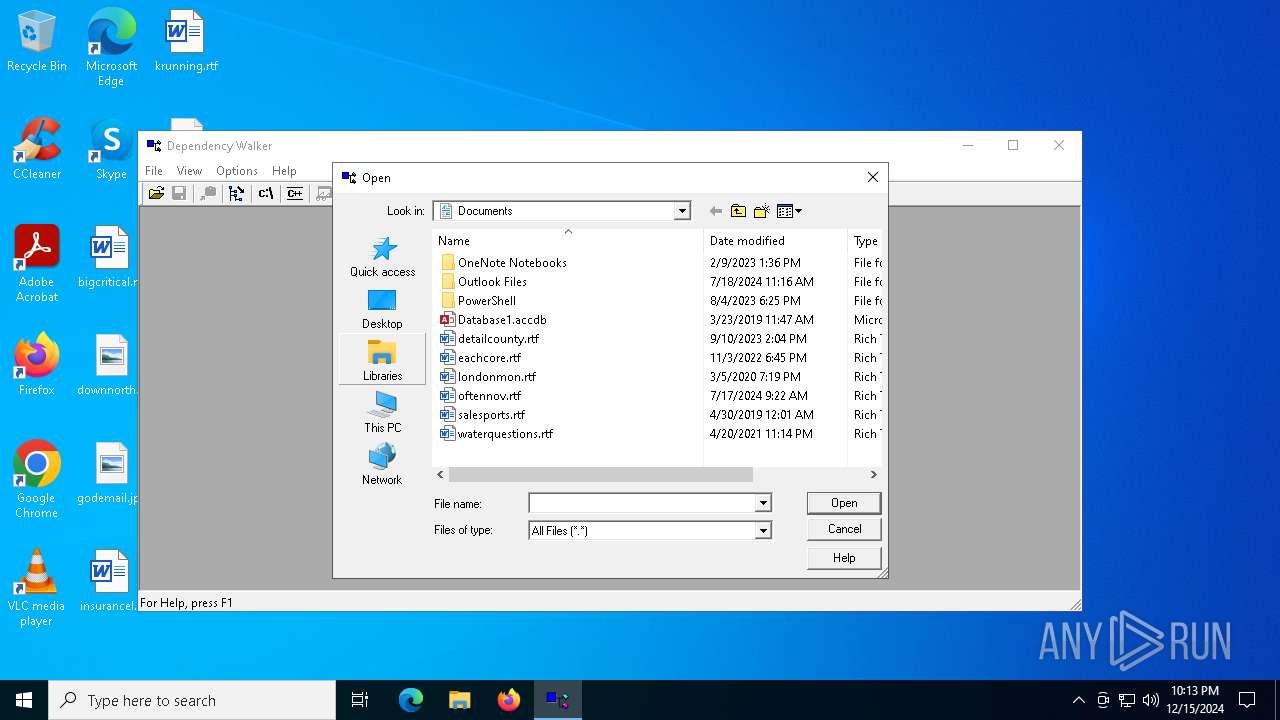
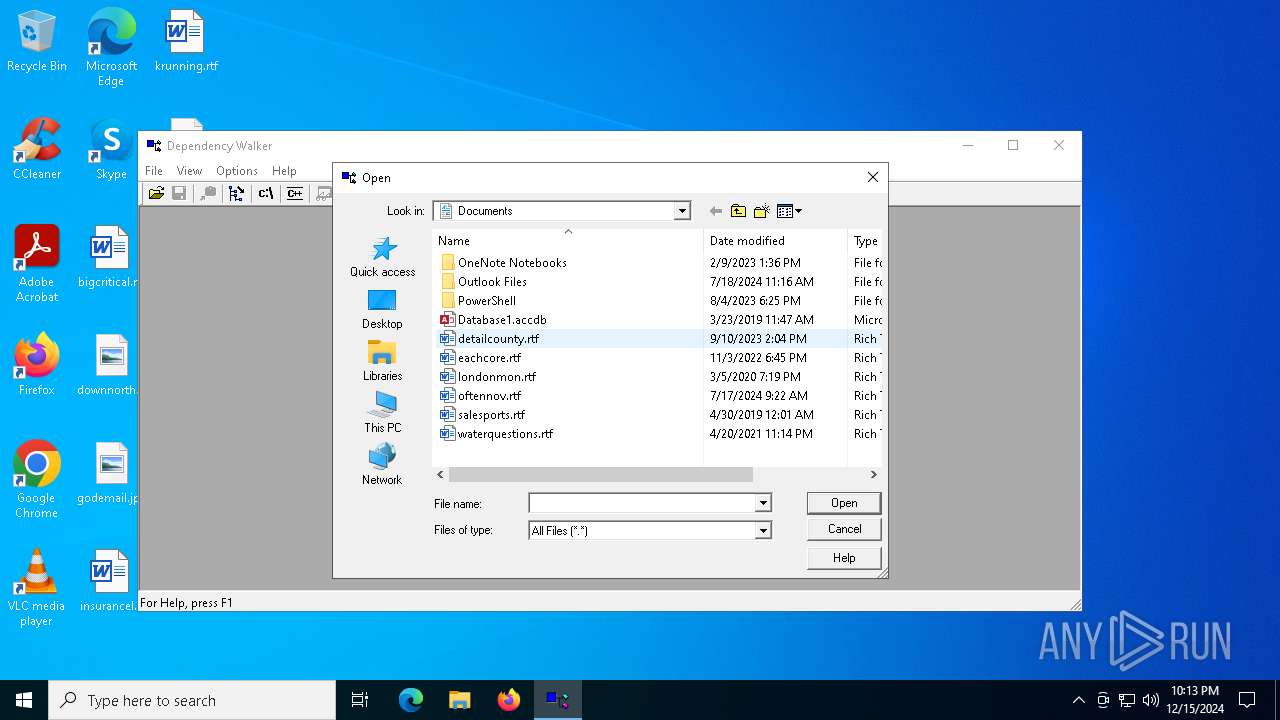
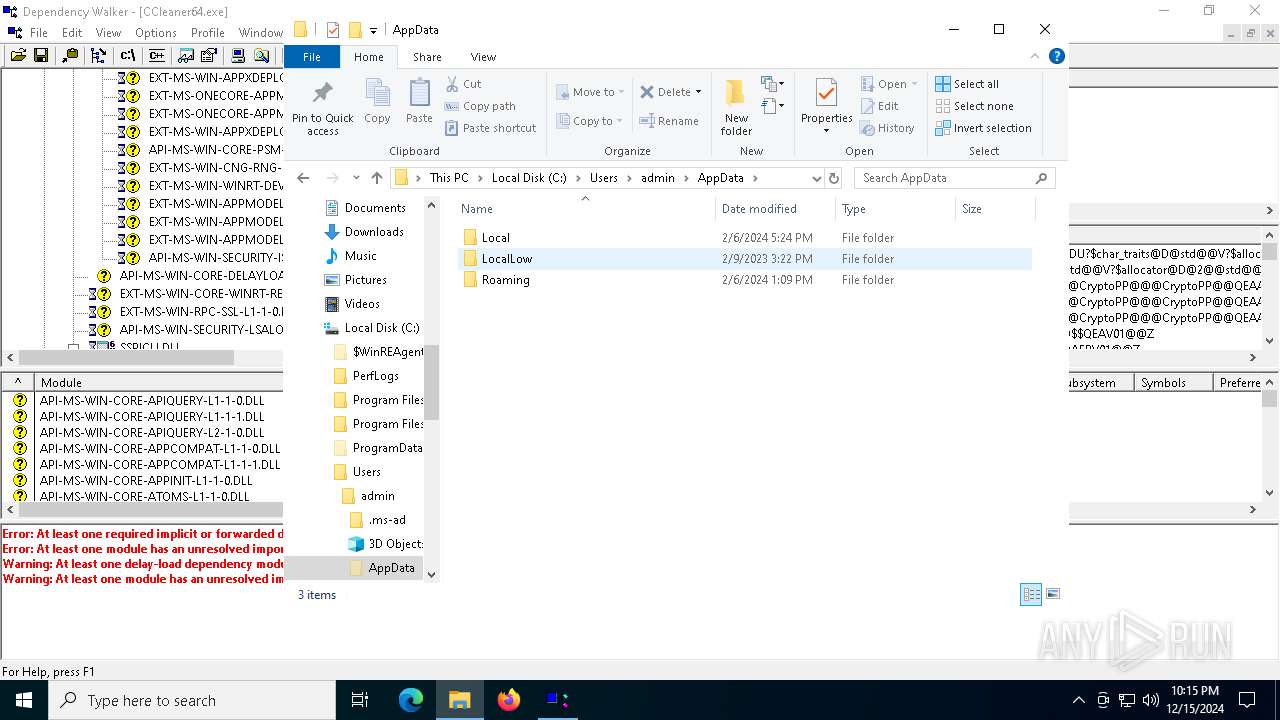
| (PID) Process: | (1200) dependsbA40OELO.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Documents | |||
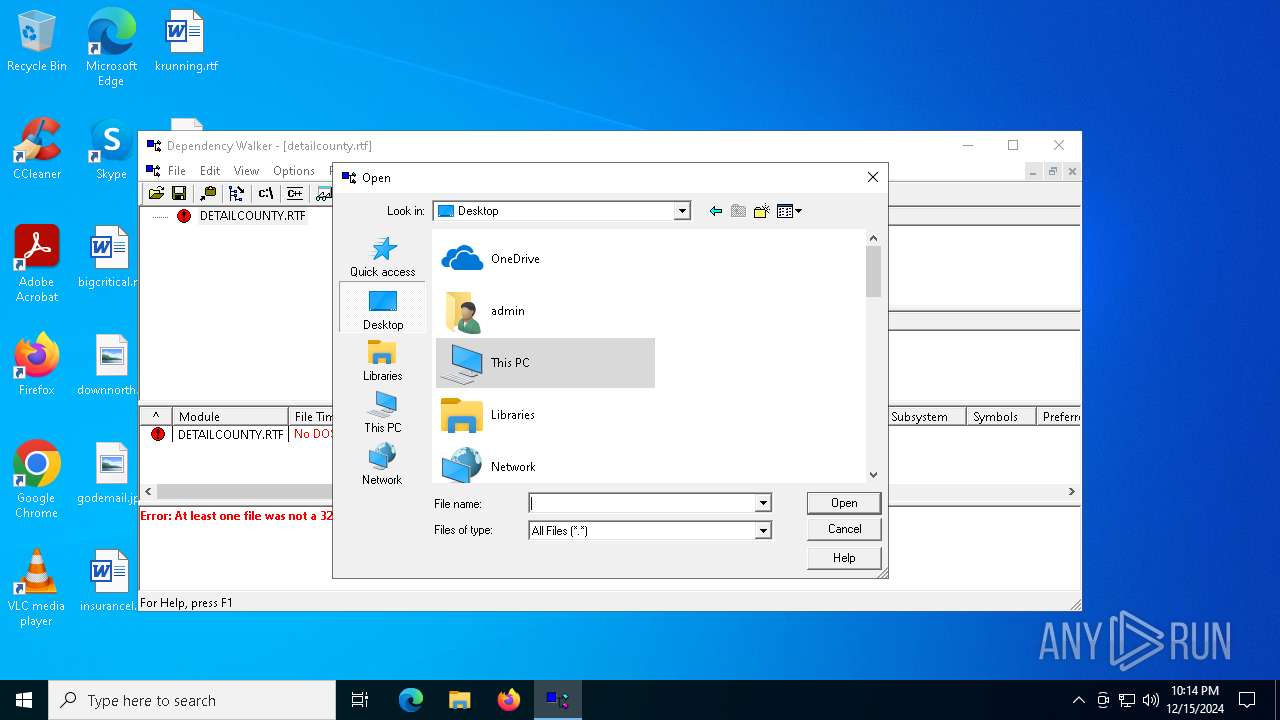
| (PID) Process: | (1200) dependsbA40OELO.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 9E545F6700000000 | |||
| (PID) Process: | (1200) dependsbA40OELO.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 105 | |||
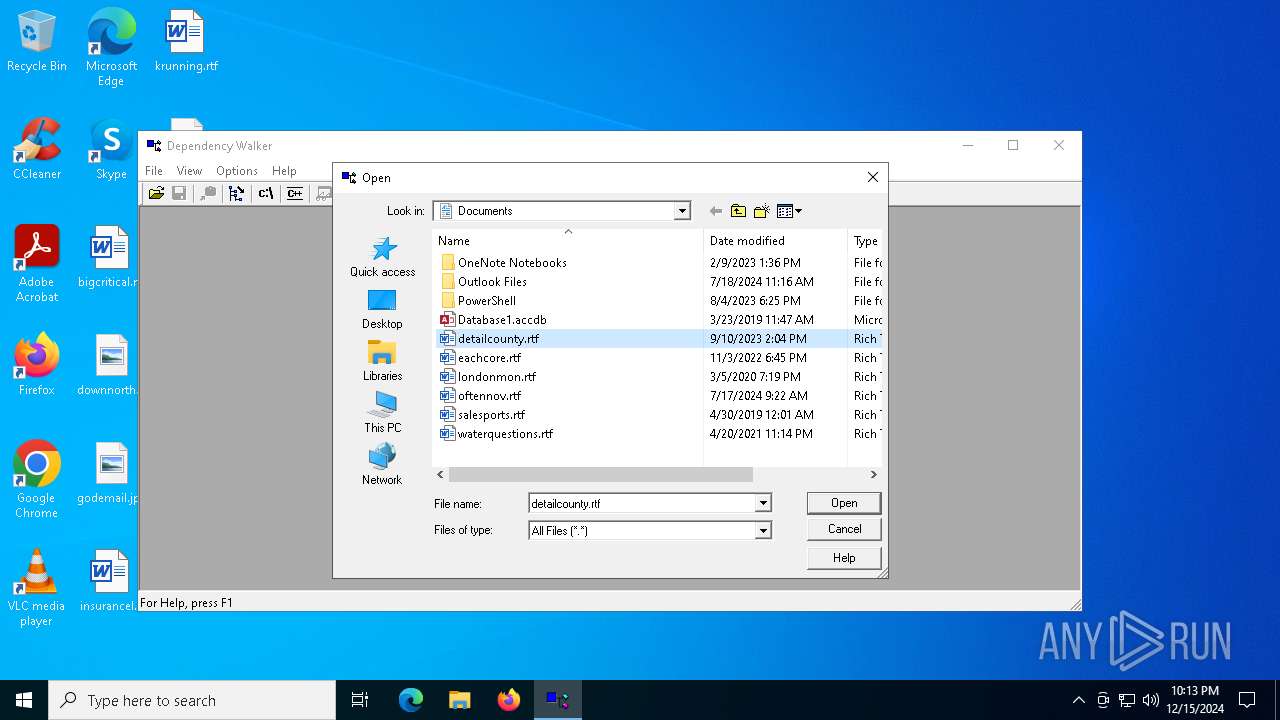
| (PID) Process: | (1200) dependsbA40OELO.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRULegacy |
| Operation: | write | Name: | 0 |
Value: 64006500700065006E006400730062004100340030004F0045004C004F002E00650078006500000014001F50E04FD020EA3A6910A2D808002B30309D14002E80922B16D365937A46956B92703ACA08AF0000 | |||
| (PID) Process: | (1200) dependsbA40OELO.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRULegacy |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (1200) dependsbA40OELO.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\ComDlgLegacy\{7D49D726-3C21-4F05-99AA-FDC2C9474656} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (1200) dependsbA40OELO.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\ComDlgLegacy\{7D49D726-3C21-4F05-99AA-FDC2C9474656} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
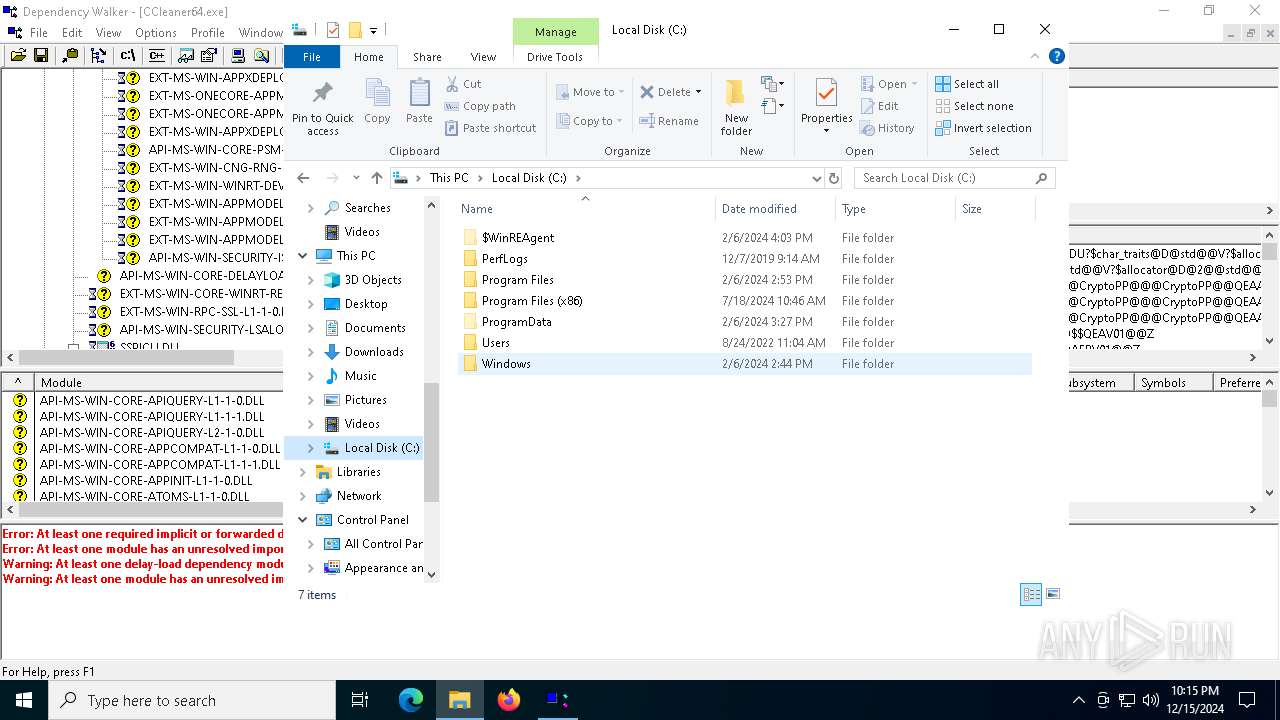
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6492 | depends.exe | C:\Users\admin\AppData\Local\Temp\dependsO3Q2K87r.exe | executable | |
MD5:FC9015FC4596D90BFE0547AB96CB21B3 | SHA256:57C483DC985A9757501993E969C2A7043C26517F97FD49A42B33D2D6A4193D8B | |||
| 3820 | depends.exe | C:\Users\admin\AppData\Local\Temp\dependsbA40OELO.exe | executable | |
MD5:FC9015FC4596D90BFE0547AB96CB21B3 | SHA256:57C483DC985A9757501993E969C2A7043C26517F97FD49A42B33D2D6A4193D8B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
39
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.24.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3688 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3688 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7048 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7048 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 184.24.77.35:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 104.126.37.176:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1076 | svchost.exe | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |