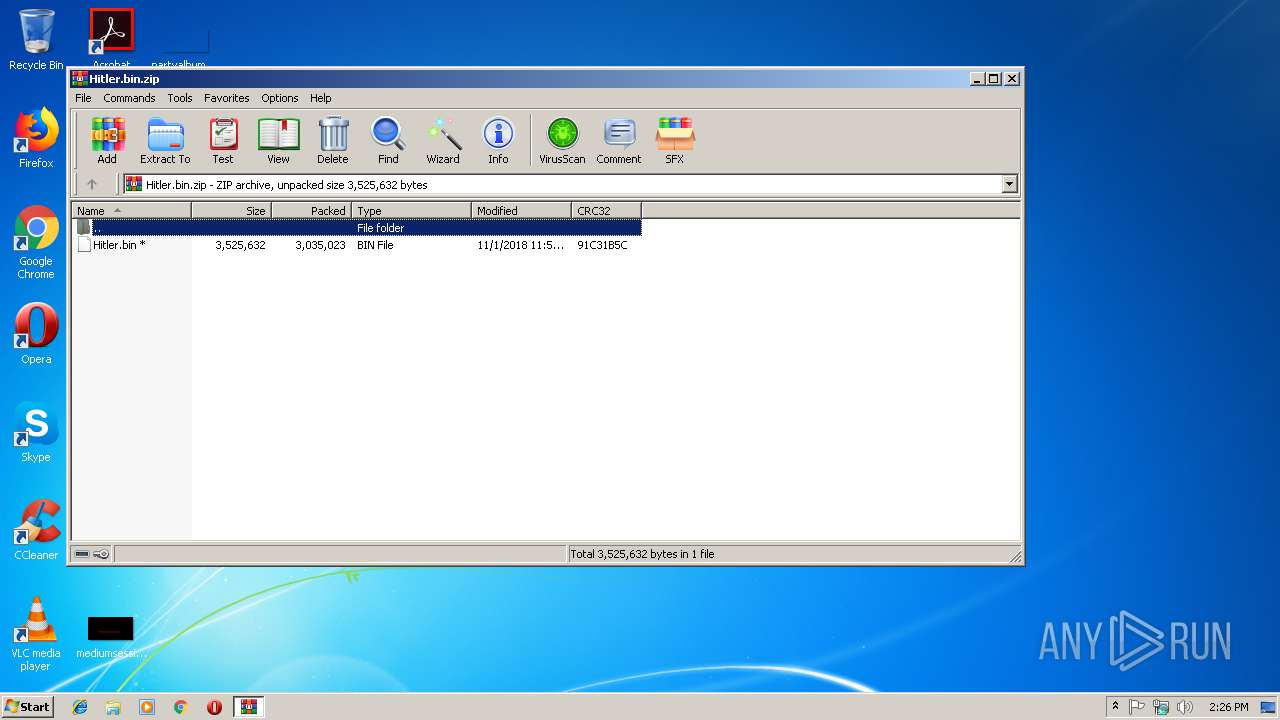
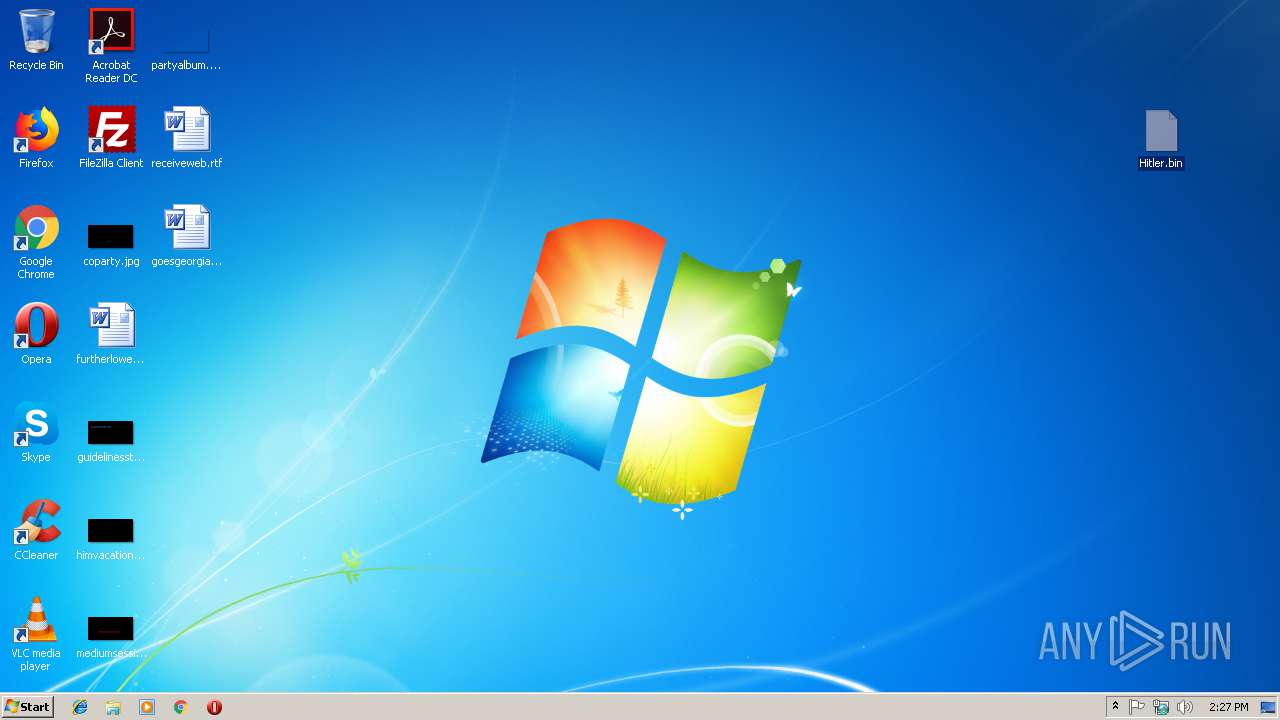
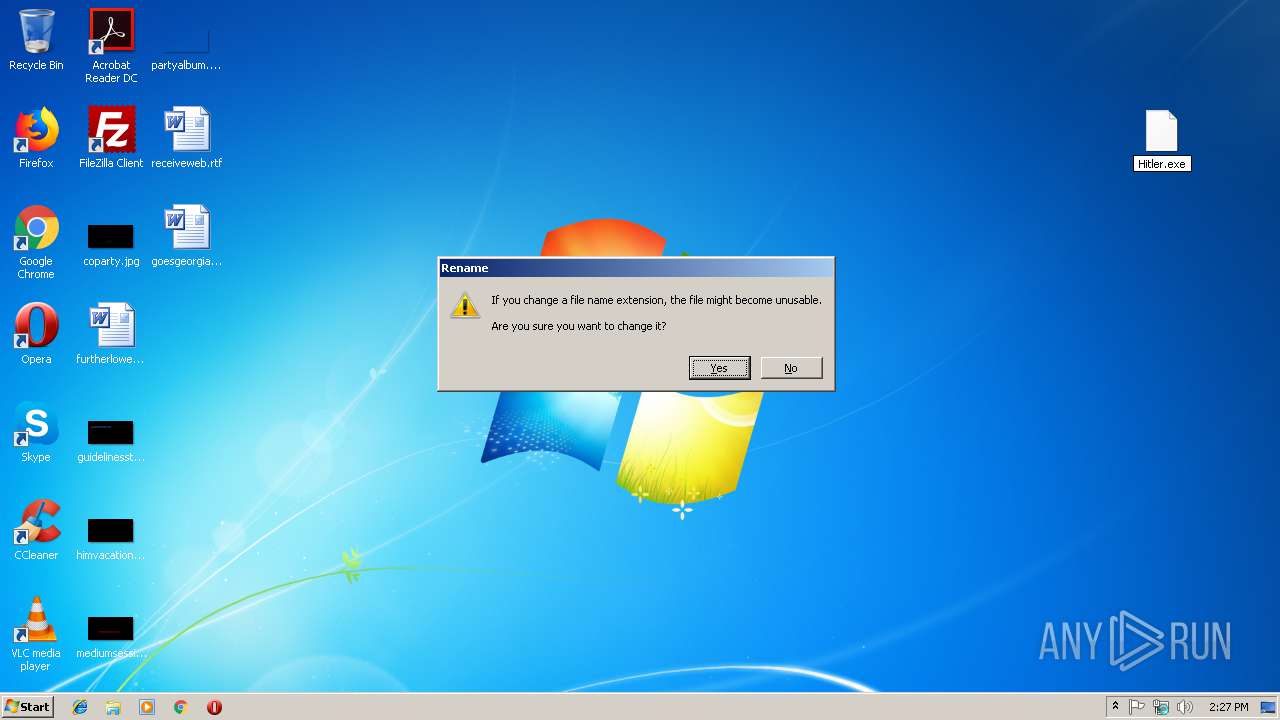
| File name: | Hitler.bin.zip |
| Full analysis: | https://app.any.run/tasks/6467c1b4-7dce-465e-90a5-1034976c2587 |
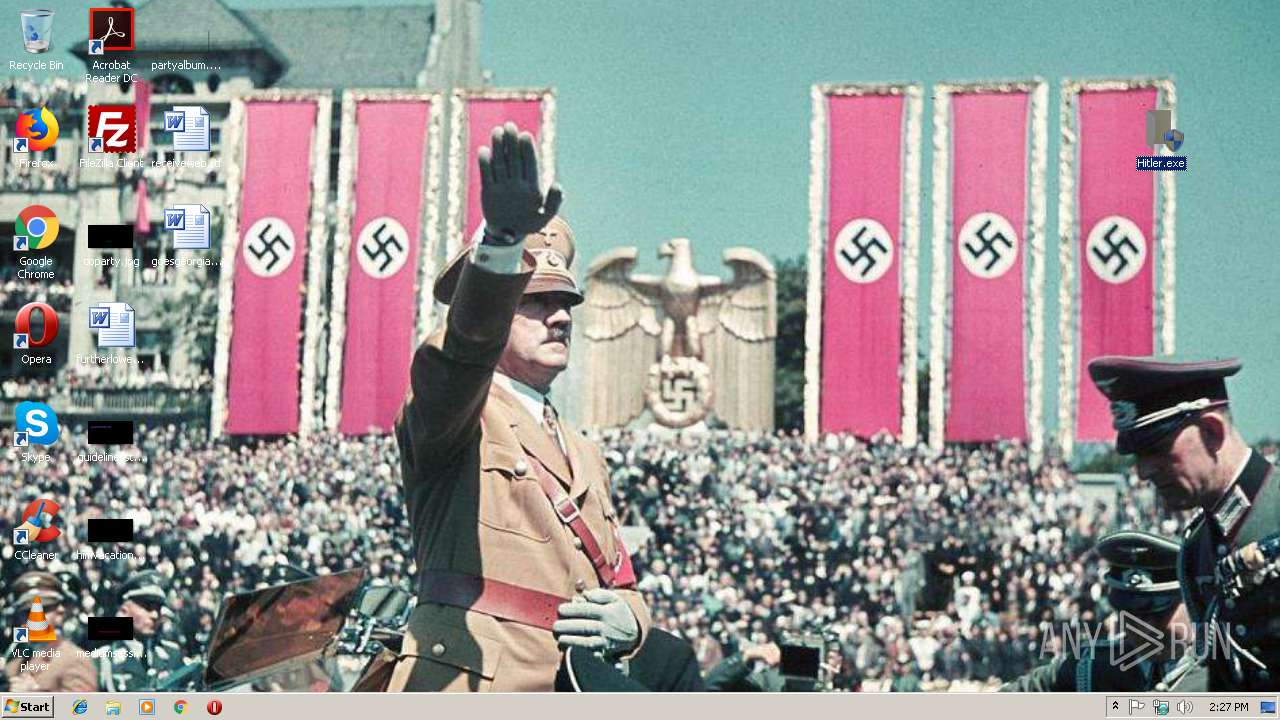
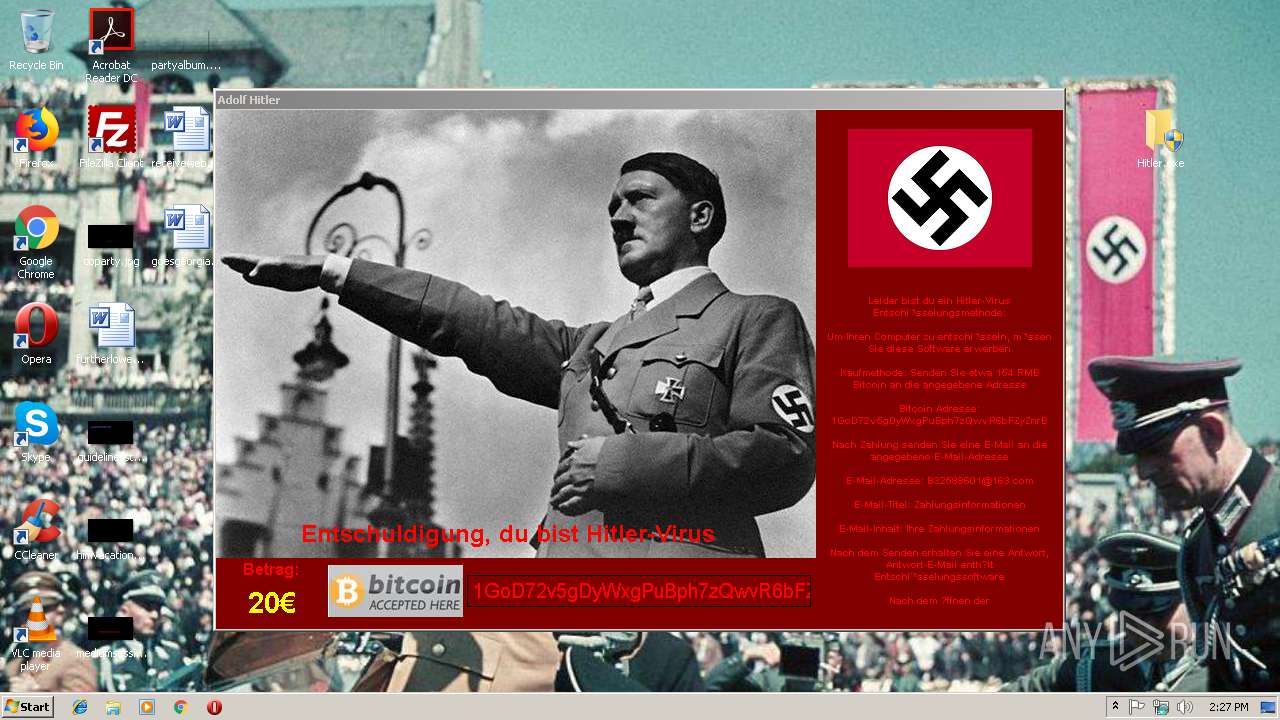
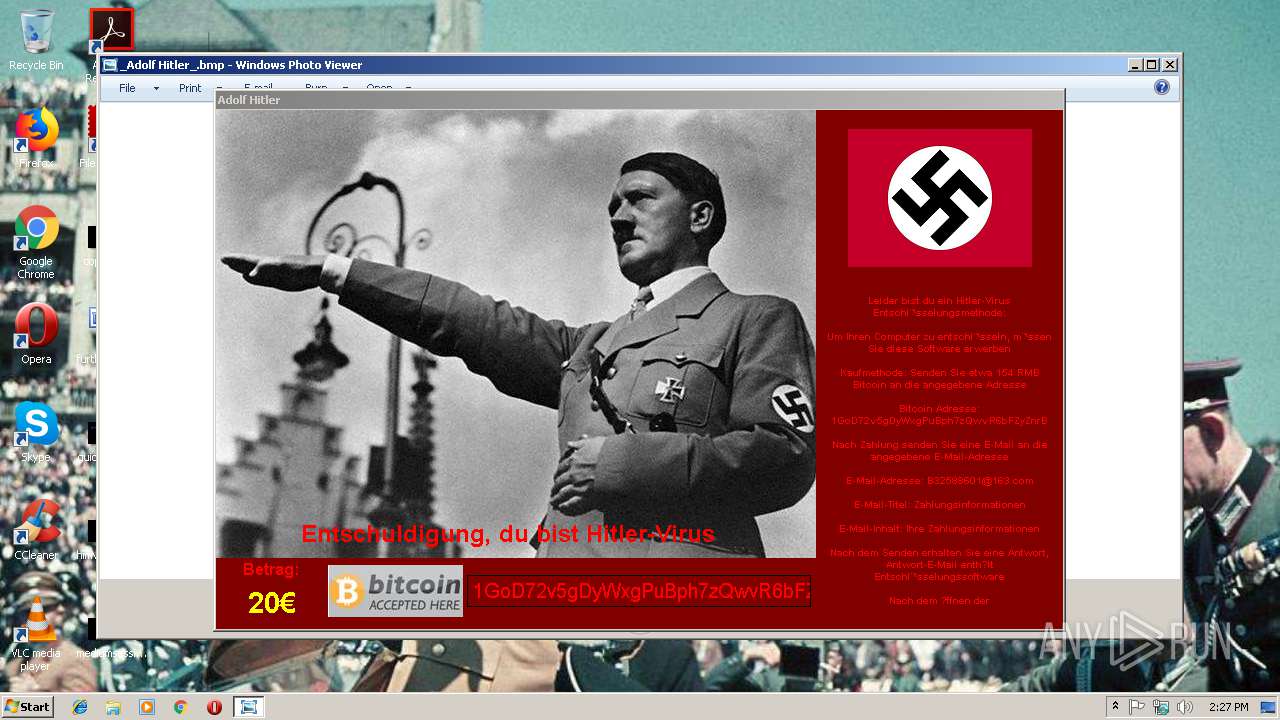
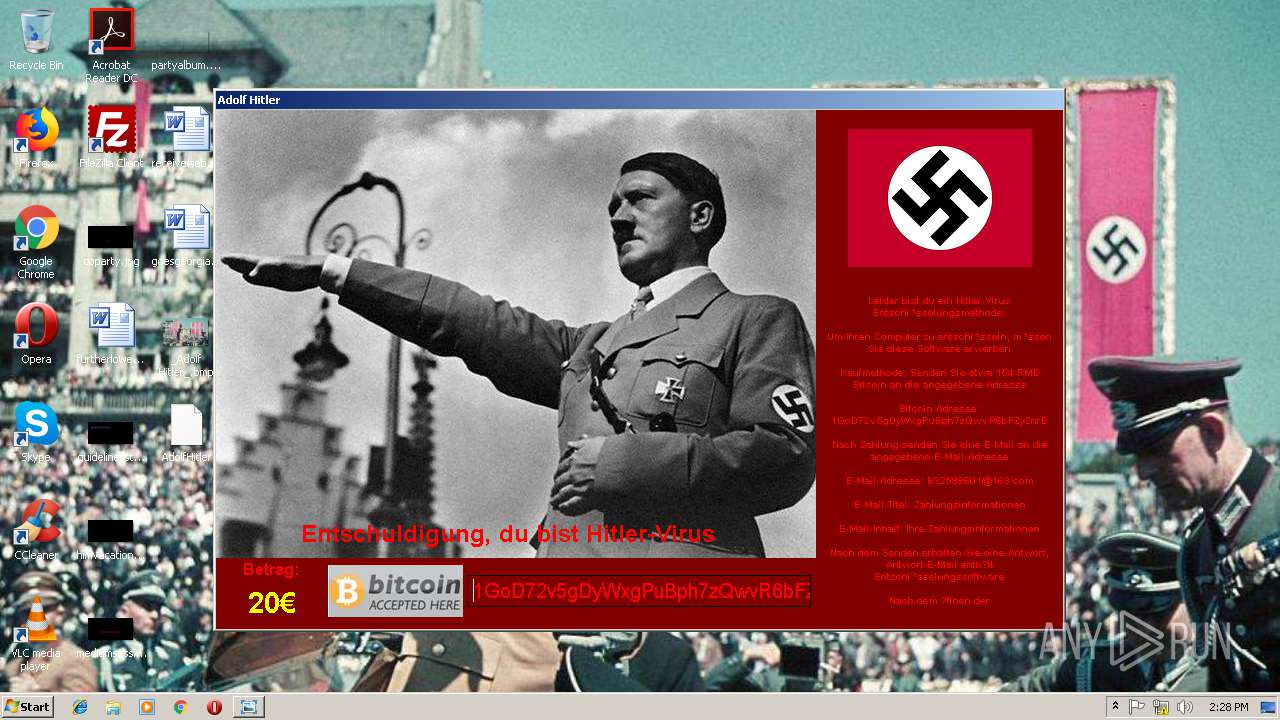
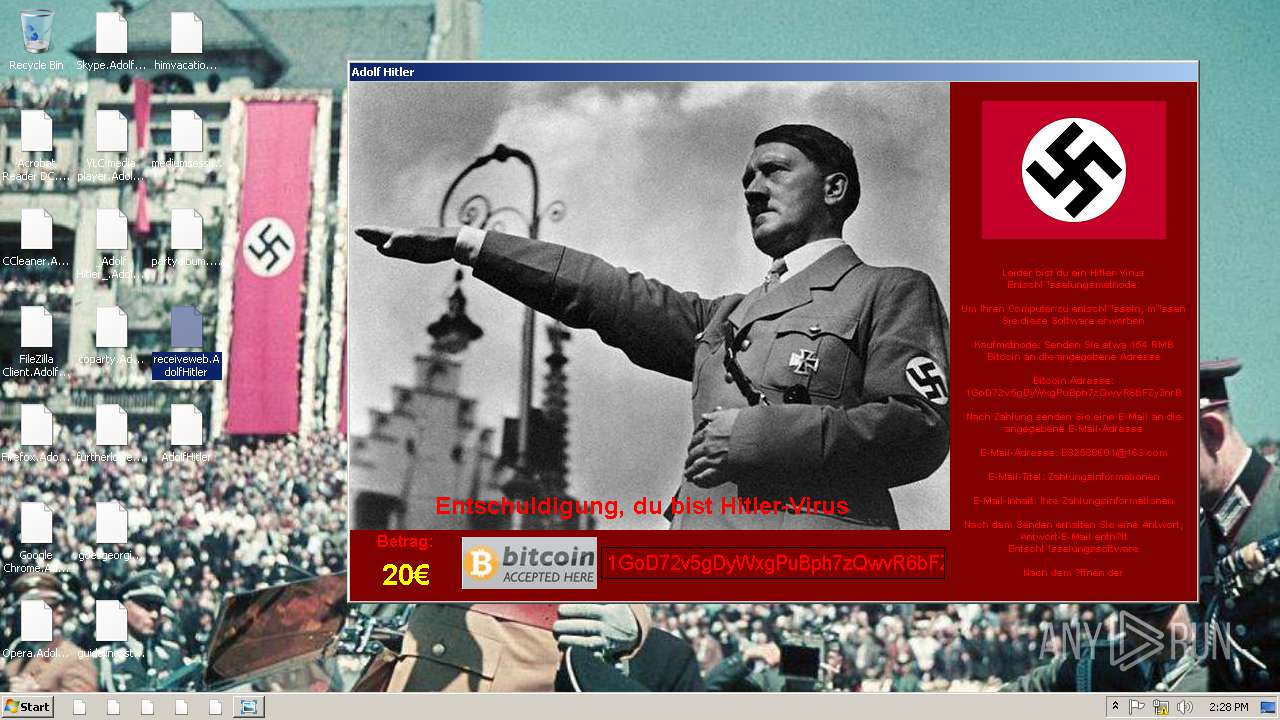
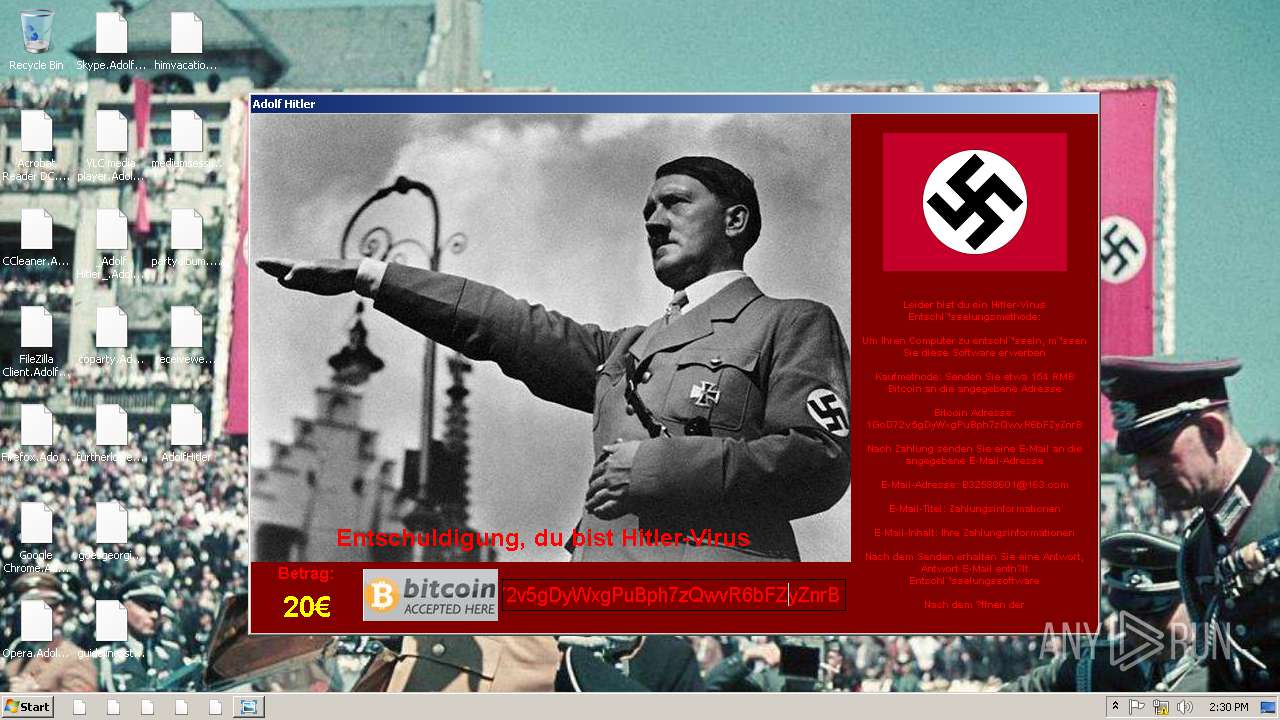
| Verdict: | Malicious activity |
| Analysis date: | February 07, 2019, 14:26:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 4989F13EC0868FD9C323B5918B1133BF |
| SHA1: | 0FD88C54372BC4C2B5561A7D099A731A46E05228 |
| SHA256: | FEFFAC4729D31A9A6F4C4734F82FD622F639378E3786E6B66601CE1E015D2BF9 |
| SSDEEP: | 49152:HEjouADIdgcsM22j8occ2e+rWrothFnG25Yanp0X7T+fHC1gJpmcKmYhzZGTLd/R:HEjQmgcsM22j8lc2eaAGTm/7Ii1QK1ED |
MALICIOUS
Application was dropped or rewritten from another process
- Hitler.exe (PID: 3912)
- Hitler.exe (PID: 2800)
Deletes shadow copies
- cmd.exe (PID: 3828)
Changes the autorun value in the registry
- Hitler.exe (PID: 2800)
UAC/LUA settings modification
- Hitler.exe (PID: 2800)
Starts BCDEDIT.EXE to disable recovery
- cmd.exe (PID: 3828)
Loads the Task Scheduler COM API
- wbengine.exe (PID: 3488)
Actions looks like stealing of personal data
- Hitler.exe (PID: 2800)
Modifies files in Chrome extension folder
- Hitler.exe (PID: 2800)
SUSPICIOUS
Uses ICACLS.EXE to modify access control list
- Hitler.exe (PID: 2800)
Creates files in the Windows directory
- Hitler.exe (PID: 2800)
- wbadmin.exe (PID: 4080)
- SearchIndexer.exe (PID: 2388)
Starts CMD.EXE for commands execution
- Hitler.exe (PID: 2800)
Creates files in the user directory
- Hitler.exe (PID: 2800)
Reads Internet Cache Settings
- Hitler.exe (PID: 2800)
Connects to SMTP port
- Hitler.exe (PID: 2800)
Low-level read access rights to disk partition
- wbengine.exe (PID: 3488)
- vds.exe (PID: 3072)
Writes to a desktop.ini file (may be used to cloak folders)
- Hitler.exe (PID: 2800)
- SearchProtocolHost.exe (PID: 3960)
Creates files in the program directory
- Hitler.exe (PID: 2800)
- SearchProtocolHost.exe (PID: 2168)
- SearchIndexer.exe (PID: 2696)
- SearchIndexer.exe (PID: 2388)
Executable content was dropped or overwritten
- Hitler.exe (PID: 2800)
INFO
Dropped object may contain Bitcoin addresses
- Hitler.exe (PID: 2800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:11:02 00:55:14 |
| ZipCRC: | 0x91c31b5c |
| ZipCompressedSize: | 3035023 |
| ZipUncompressedSize: | 3525632 |
| ZipFileName: | Hitler.bin |
Total processes
65
Monitored processes
20
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2168 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe1_ Global\UsGthrCtrlFltPipeMssGthrPipe1 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2204 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2388 | C:\Windows\system32\SearchIndexer.exe /Embedding | C:\Windows\system32\SearchIndexer.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Indexer Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2628 | "C:\Windows\system32\SearchFilterHost.exe" 0 516 520 528 65536 524 | C:\Windows\system32\SearchFilterHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Filter Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2696 | C:\Windows\system32\SearchIndexer.exe /Embedding | C:\Windows\system32\SearchIndexer.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Indexer Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2800 | "C:\Users\admin\Desktop\Hitler.exe" | C:\Users\admin\Desktop\Hitler.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2872 | wmic shadowcopy delete | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2996 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Hitler.bin.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3072 | C:\Windows\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3208 | bcdedit /set {default} boostatuspolicy ignoreallfailures | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
3 916
Read events
2 245
Write events
1 464
Delete events
207
Modification events
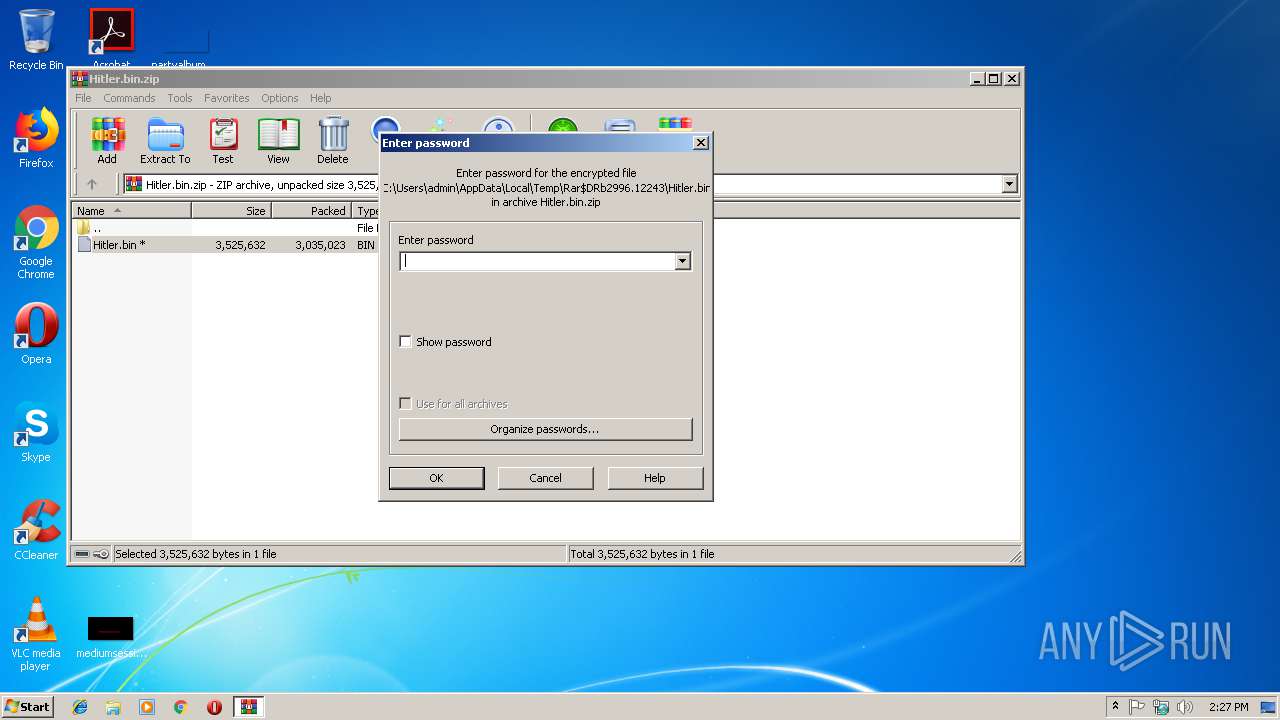
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Hitler.bin.zip | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2996) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
579
Suspicious files
15 805
Text files
260
Unknown types
336
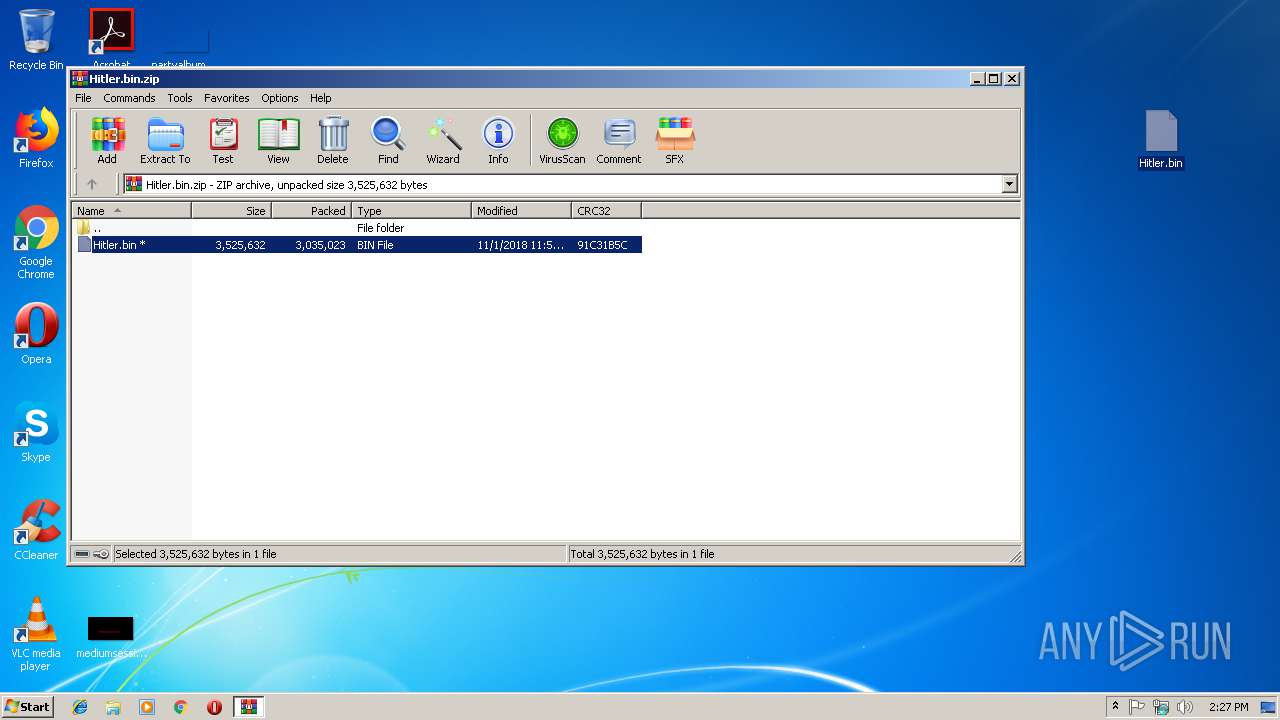
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2996 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2996.12243\Hitler.bin | — | |
MD5:— | SHA256:— | |||
| 2800 | Hitler.exe | C:\autoexec.bat | — | |
MD5:— | SHA256:— | |||
| 2800 | Hitler.exe | C:\config.sys | — | |
MD5:— | SHA256:— | |||
| 2800 | Hitler.exe | C:\MSOCache\All Users\{90140000-0016-0409-0000-0000000FF1CE}-C\ExcelLR.cab | — | |
MD5:— | SHA256:— | |||
| 2800 | Hitler.exe | C:\MSOCache\All Users\{90140000-0016-0409-0000-0000000FF1CE}-C\ExcelMUI.msi | — | |
MD5:— | SHA256:— | |||
| 2800 | Hitler.exe | C:\MSOCache\All Users\{90140000-0016-0409-0000-0000000FF1CE}-C\Setup.xml | — | |
MD5:— | SHA256:— | |||
| 2800 | Hitler.exe | C:\MSOCache\All Users\{90140000-0018-0409-0000-0000000FF1CE}-C\PowerPointMUI.msi | — | |
MD5:— | SHA256:— | |||
| 2800 | Hitler.exe | C:\MSOCache\All Users\{90140000-0018-0409-0000-0000000FF1CE}-C\PptLR.cab | — | |
MD5:— | SHA256:— | |||
| 2800 | Hitler.exe | C:\MSOCache\All Users\{90140000-0018-0409-0000-0000000FF1CE}-C\Setup.xml | — | |
MD5:— | SHA256:— | |||
| 2800 | Hitler.exe | C:\MSOCache\All Users\{90140000-0019-0409-0000-0000000FF1CE}-C\PublisherMUI.msi | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
5
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2800 | Hitler.exe | GET | 200 | 103.235.46.39:80 | http://www.baidu.com/ | HK | html | 149 Kb | whitelisted |
2800 | Hitler.exe | GET | 200 | 125.77.198.152:80 | http://2019.ip138.com/ic.asp | CN | html | 215 b | suspicious |
2800 | Hitler.exe | GET | 200 | 163.171.128.148:80 | http://www.ip138.com/ | US | html | 19.2 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2800 | Hitler.exe | 103.235.46.39:80 | www.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | unknown |
2800 | Hitler.exe | 163.171.128.148:80 | www.ip138.com | — | US | malicious |
2800 | Hitler.exe | 125.77.198.152:80 | 2019.ip138.com | Xiamen | CN | suspicious |
2800 | Hitler.exe | 123.125.50.135:25 | smtp.163.com | China Unicom Beijing Province Network | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.baidu.com |
| whitelisted |
smtp.163.com |
| shared |
www.ip138.com |
| suspicious |
2019.ip138.com |
| unknown |
Threats
1 ETPRO signatures available at the full report