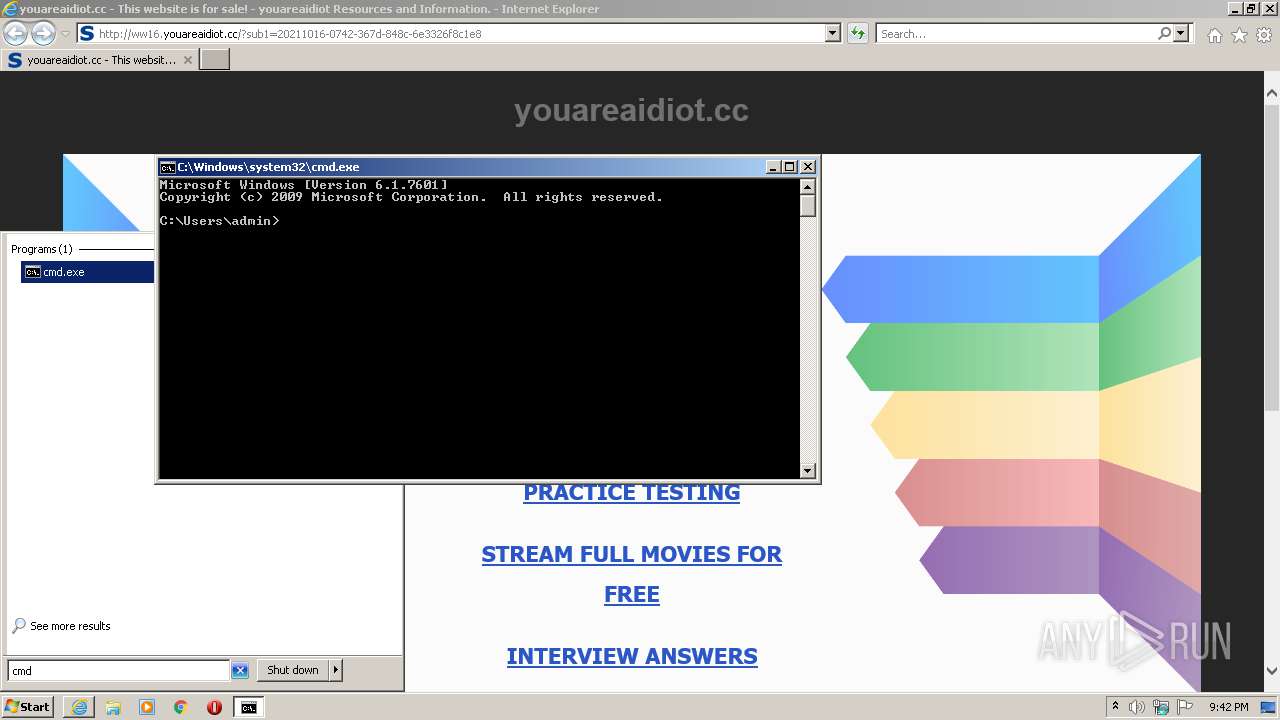
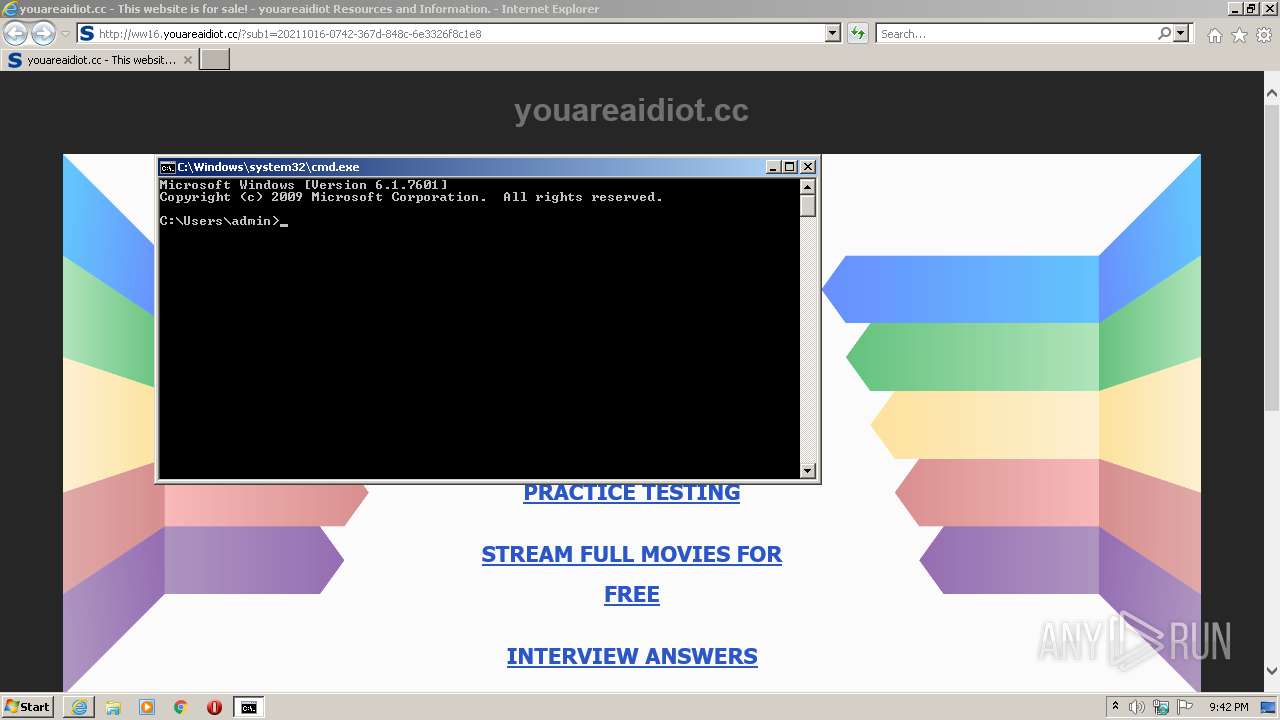
| URL: | https://youareaidiot.cc |
| Full analysis: | https://app.any.run/tasks/9c68eafe-f85b-44c1-bd52-f31a87c02a23 |
| Verdict: | Malicious activity |
| Analysis date: | October 15, 2021, 20:42:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0C9324D2E60D7681036F7669EC492A9E |
| SHA1: | 298E334782A23C9AD4035A9AC6E7D5E7D9EBF465 |
| SHA256: | FEFB7CEBA17FDE519FBBA867A43D715B694A249899BF6C71ACD5C269814FAD27 |
| SSDEEP: | 3:N8uN6TG:2uN1 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3432)
Checks supported languages
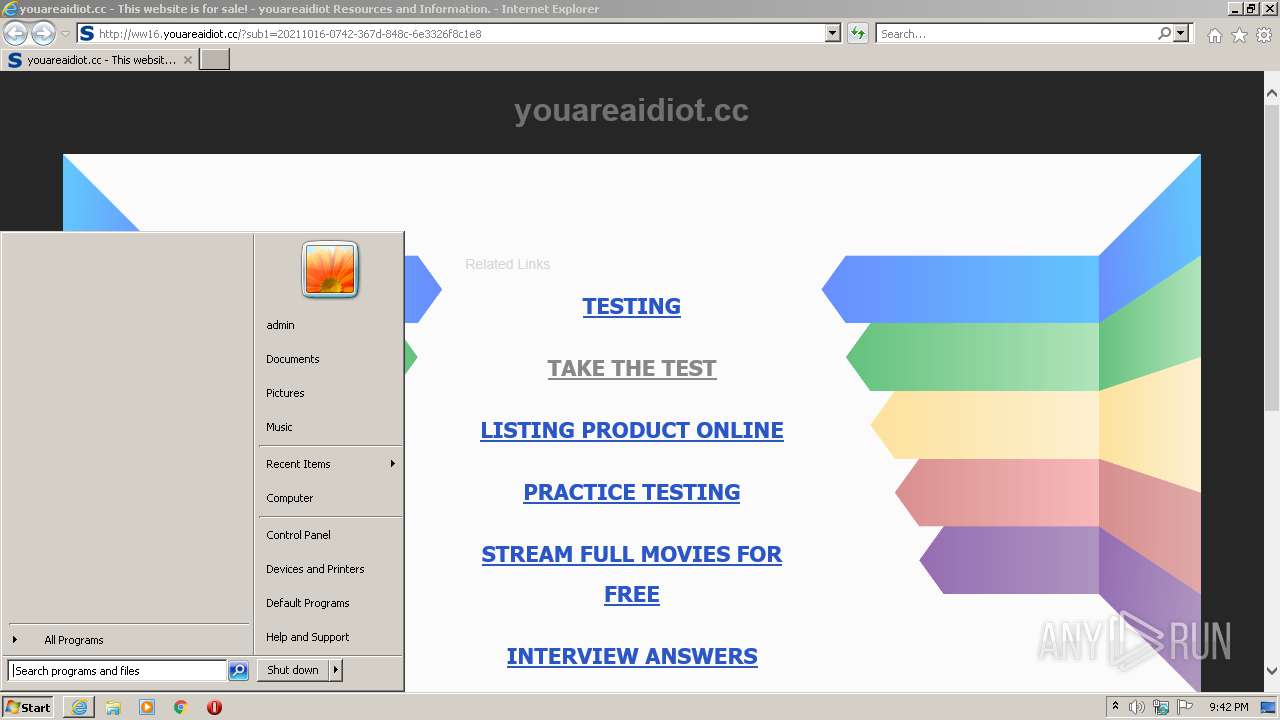
- cmd.exe (PID: 2916)
INFO
Reads the computer name
- iexplore.exe (PID: 320)
- iexplore.exe (PID: 3432)
Checks supported languages
- iexplore.exe (PID: 3432)
- iexplore.exe (PID: 320)
Changes internet zones settings
- iexplore.exe (PID: 320)
Application launched itself
- iexplore.exe (PID: 320)
Checks Windows Trust Settings
- iexplore.exe (PID: 3432)
- iexplore.exe (PID: 320)
Reads settings of System Certificates
- iexplore.exe (PID: 3432)
- iexplore.exe (PID: 320)
Creates files in the user directory
- iexplore.exe (PID: 3432)
Reads internet explorer settings
- iexplore.exe (PID: 3432)
Manual execution by user
- cmd.exe (PID: 2916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://youareaidiot.cc" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2916 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3432 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:320 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
13 783
Read events
13 668
Write events
115
Delete events
0
Modification events
| (PID) Process: | (320) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (320) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 781296000 | |||
| (PID) Process: | (320) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30917125 | |||
| (PID) Process: | (320) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (320) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30917125 | |||
| (PID) Process: | (320) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (320) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (320) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (320) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (320) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
15
Text files
14
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab2118.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2119.tmp | cat | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2108.tmp | cat | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7835C1E7B7D9E2E80DA29B85911CC82C | binary | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\Y9ACFIVF.txt | text | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab2107.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7835C1E7B7D9E2E80DA29B85911CC82C | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
25
DNS requests
17
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
320 | iexplore.exe | GET | 304 | 8.253.207.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6d2dd2fcbb1e6ebe | US | — | — | whitelisted |
3432 | iexplore.exe | GET | 200 | 2.16.186.33:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgTRoVatBr7mjCYmVNG0yqdjaw%3D%3D | unknown | der | 503 b | shared |
3432 | iexplore.exe | GET | 200 | 91.195.240.112:80 | http://ww16.youareaidiot.cc/?sub1=20211016-0742-367d-848c-6e3326f8c1e8 | DE | html | 7.44 Kb | unknown |
3432 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3432 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCECRXdf7EU7SwCgAAAAD%2FZgs%3D | US | der | 471 b | whitelisted |
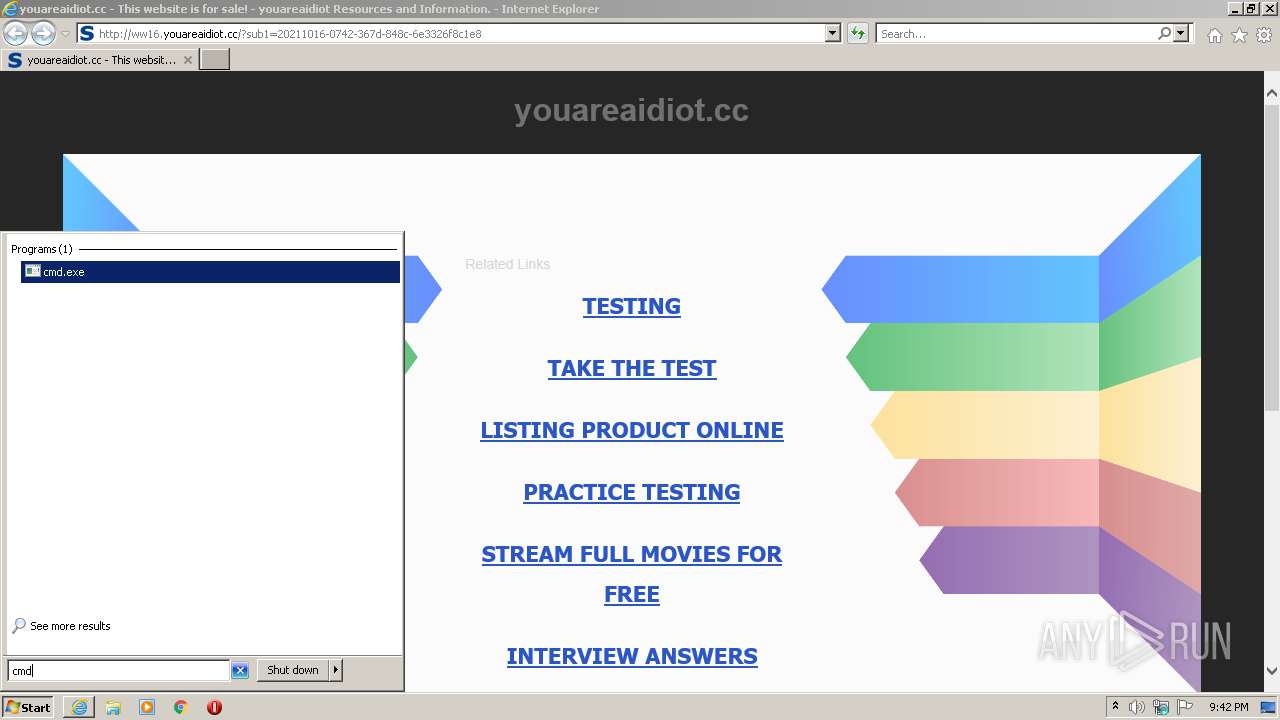
3432 | iexplore.exe | GET | 200 | 142.250.186.68:80 | http://www.google.com/adsense/domains/caf.js | US | text | 56.9 Kb | malicious |
3432 | iexplore.exe | GET | 200 | 91.195.240.112:80 | http://ww16.youareaidiot.cc/search/tsc.php?200=MzYyNDM1MzEw&21=MTg1LjE5OC4yNDMuMjA5&681=MTYzNDMzMDU1NzQ4ZTBjOTQ3ZTc2MjZiMTJkMjkzZTQ2YThmMzRlN2E3&crc=c479f39cf5bccb4779b030190f4d6cafb831ab77&cv=1 | DE | compressed | 7.44 Kb | unknown |
3432 | iexplore.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3432 | iexplore.exe | GET | 200 | 8.253.207.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?a2954d12c382145c | US | compressed | 59.7 Kb | whitelisted |
320 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3432 | iexplore.exe | 103.224.182.242:443 | youareaidiot.cc | Trellian Pty. Limited | AU | malicious |
3432 | iexplore.exe | 142.250.184.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3432 | iexplore.exe | 142.250.186.68:443 | www.google.com | Google Inc. | US | whitelisted |
320 | iexplore.exe | 205.234.175.175:80 | img.sedoparking.com | CacheNetworks, Inc. | US | suspicious |
320 | iexplore.exe | 8.253.207.120:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
320 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
320 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
320 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
320 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3432 | iexplore.exe | 91.195.240.112:80 | ww16.youareaidiot.cc | SEDO GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
youareaidiot.cc |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
ww16.youareaidiot.cc |
| unknown |
www.google.com |
| malicious |
img.sedoparking.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .cc TLD |