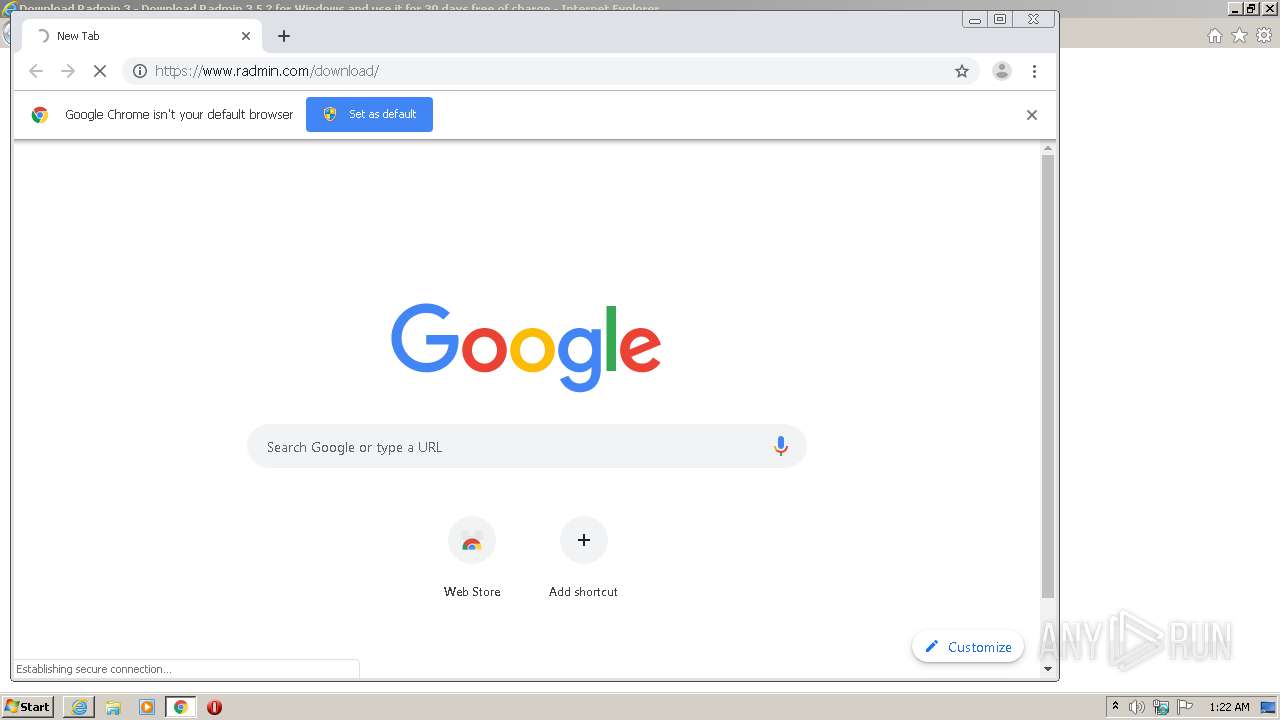
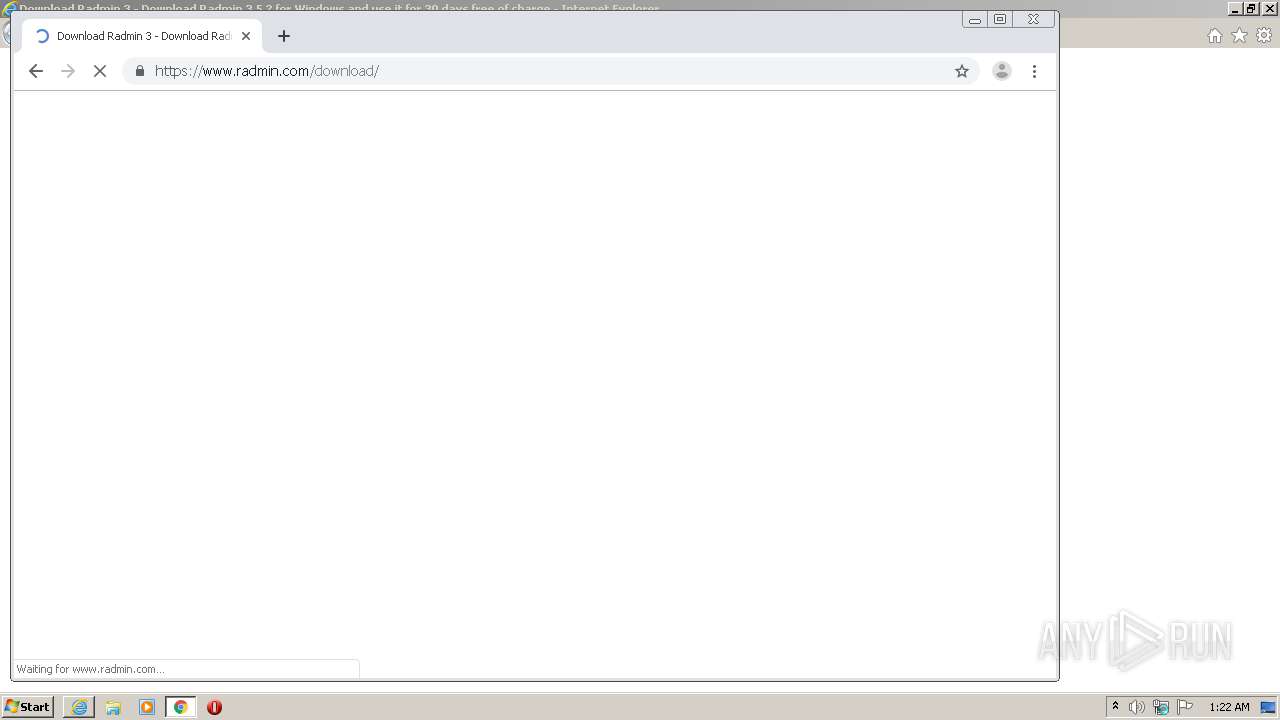
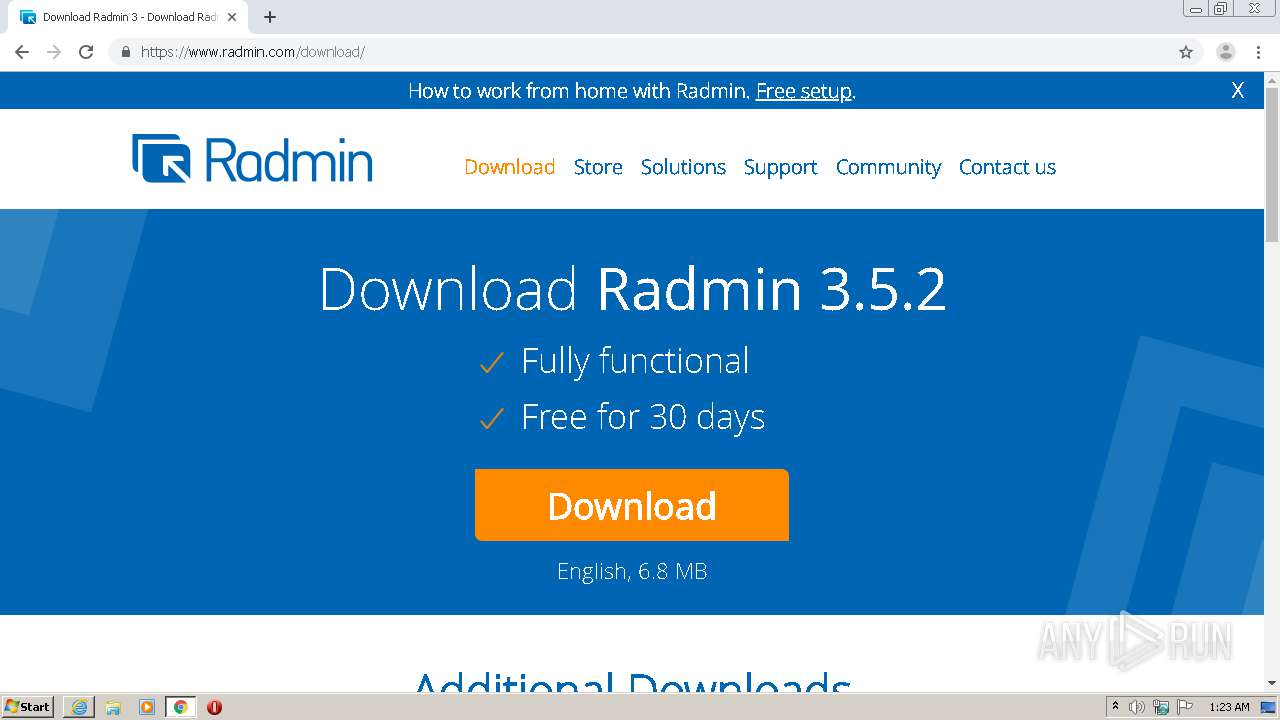
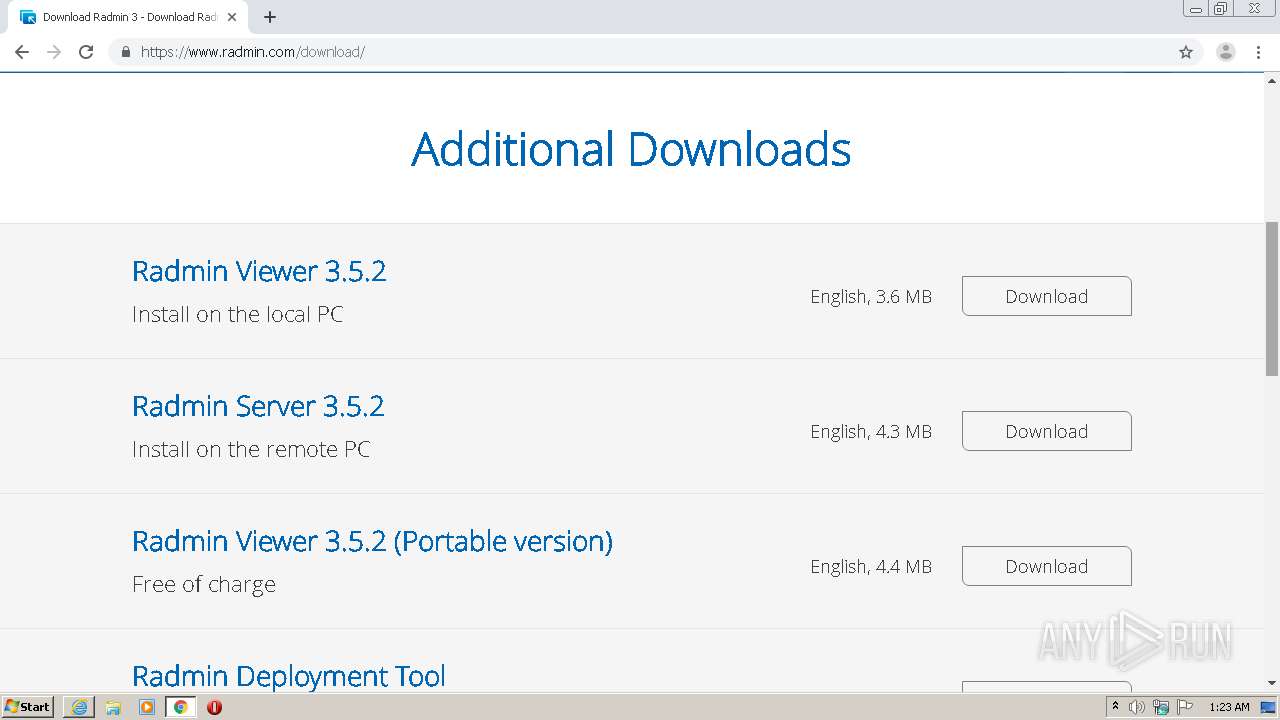
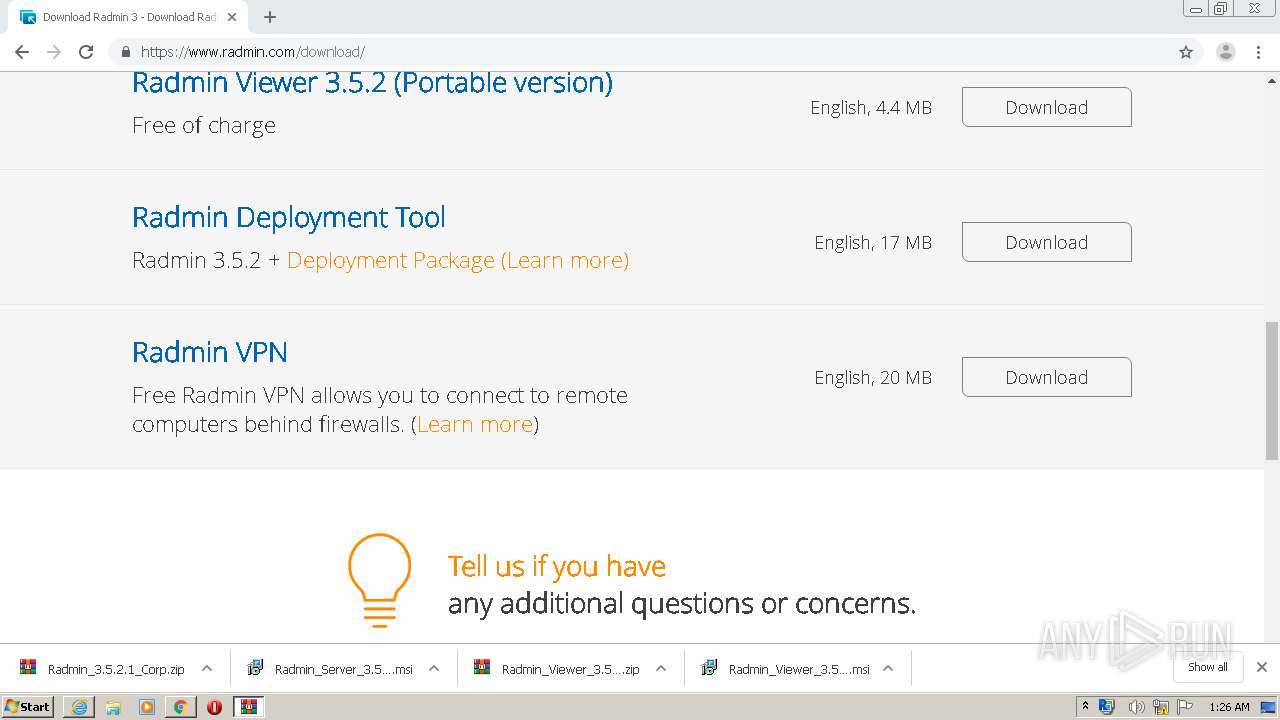
| URL: | https://www.radmin.com/download/ |
| Full analysis: | https://app.any.run/tasks/b2f65fff-e080-47a7-a232-fa66d134a7ee |
| Verdict: | Malicious activity |
| Analysis date: | June 09, 2020, 00:22:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6B90AD54B4C92102EA4A5A2D8258B198 |
| SHA1: | 2A78970AAFCBC07B1421DC2E325C624E0FC1BF5A |
| SHA256: | FEE4190FBED63AEB1224BD236E680FA53AA5D765AD4E10498ACFCF65C43DE9F5 |
| SSDEEP: | 3:N8DSLU+QGWKLn:2OLUmL |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3592)
- RServer3.exe (PID: 672)
- FamItrfc.Exe (PID: 752)
- FamItrfc.Exe (PID: 3356)
Application was dropped or rewritten from another process
- Radmin.exe (PID: 1264)
- rsetup.exe (PID: 1016)
- rsetup.exe (PID: 3484)
- rsetup.exe (PID: 2200)
- RServer3.exe (PID: 672)
- FamItrfc.Exe (PID: 752)
- FamItrfc.Exe (PID: 3356)
- rsl.exe (PID: 2548)
- rserver3.exe (PID: 3368)
- rserver3.exe (PID: 3120)
Changes settings of System certificates
- rsetup.exe (PID: 3484)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2628)
Executable content was dropped or overwritten
- chrome.exe (PID: 2628)
- chrome.exe (PID: 3044)
- msiexec.exe (PID: 2344)
- MsiExec.exe (PID: 2128)
- msiexec.exe (PID: 1156)
- WinRAR.exe (PID: 2292)
- rsetup.exe (PID: 3484)
- DrvInst.exe (PID: 1740)
Creates files in the user directory
- Radmin.exe (PID: 1264)
Starts Microsoft Installer
- chrome.exe (PID: 2628)
Executed as Windows Service
- vssvc.exe (PID: 916)
- RServer3.exe (PID: 672)
Creates files in the Windows directory
- msiexec.exe (PID: 1156)
- DrvInst.exe (PID: 1740)
- RServer3.exe (PID: 672)
- DrvInst.exe (PID: 1604)
Removes files from Windows directory
- DrvInst.exe (PID: 1604)
- DrvInst.exe (PID: 1740)
Executed via COM
- DrvInst.exe (PID: 1740)
- DrvInst.exe (PID: 1604)
Creates files in the driver directory
- DrvInst.exe (PID: 1604)
- DrvInst.exe (PID: 1740)
Uses NETSH.EXE for network configuration
- MsiExec.exe (PID: 856)
Application launched itself
- FamItrfc.Exe (PID: 752)
Adds / modifies Windows certificates
- rsetup.exe (PID: 3484)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 1476)
- chrome.exe (PID: 2628)
- iexplore.exe (PID: 1516)
Creates files in the user directory
- iexplore.exe (PID: 1516)
- iexplore.exe (PID: 1476)
Application launched itself
- iexplore.exe (PID: 1476)
- chrome.exe (PID: 2628)
- msiexec.exe (PID: 1156)
Manual execution by user
- chrome.exe (PID: 2628)
Reads the hosts file
- chrome.exe (PID: 3044)
- chrome.exe (PID: 2628)
Changes internet zones settings
- iexplore.exe (PID: 1476)
Reads internet explorer settings
- iexplore.exe (PID: 1516)
Reads settings of System Certificates
- chrome.exe (PID: 2628)
- msiexec.exe (PID: 1156)
- chrome.exe (PID: 3044)
- iexplore.exe (PID: 1476)
- rsetup.exe (PID: 3484)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2128)
- MsiExec.exe (PID: 856)
- MsiExec.exe (PID: 3996)
Searches for installed software
- msiexec.exe (PID: 1156)
Low-level read access rights to disk partition
- vssvc.exe (PID: 916)
Creates files in the program directory
- msiexec.exe (PID: 1156)
Creates a software uninstall entry
- msiexec.exe (PID: 1156)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1476)
Changes settings of System certificates
- iexplore.exe (PID: 1476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
101
Monitored processes
58
Malicious processes
13
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,2168438777248495283,14865404307217131316,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=749649474846665288 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4132 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,2168438777248495283,14865404307217131316,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1232030545770164409 --mojo-platform-channel-handle=2628 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
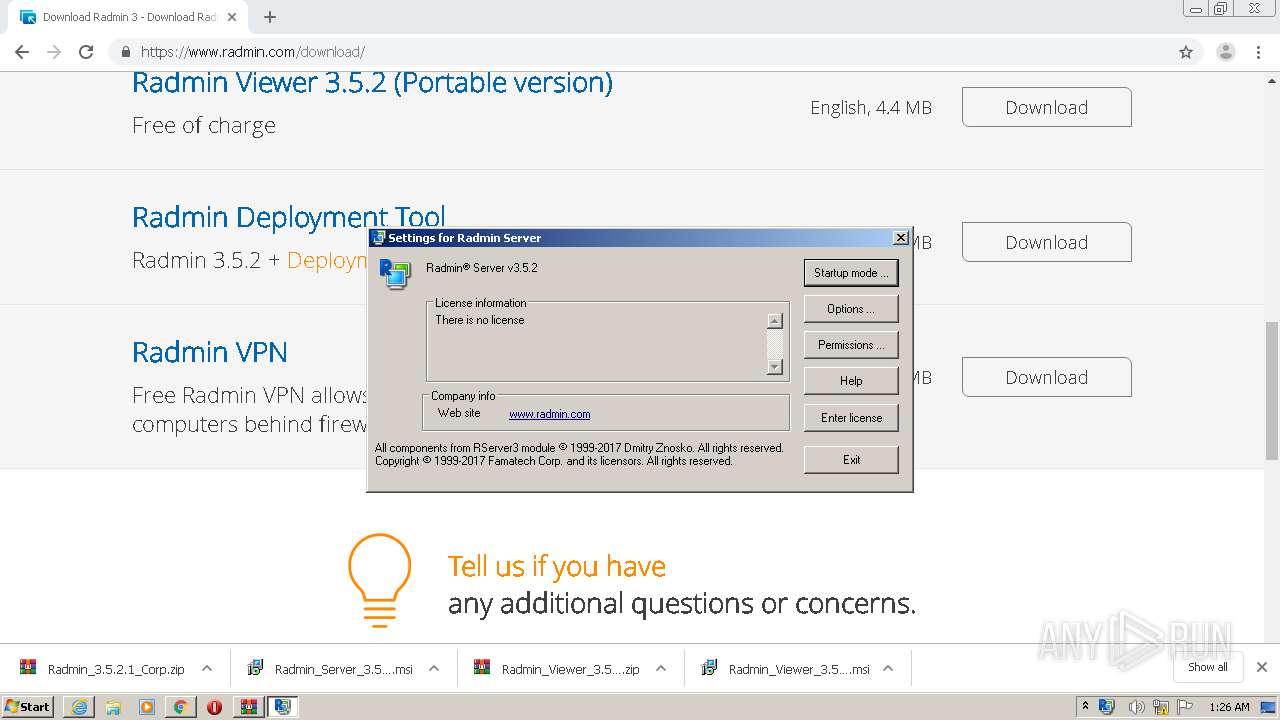
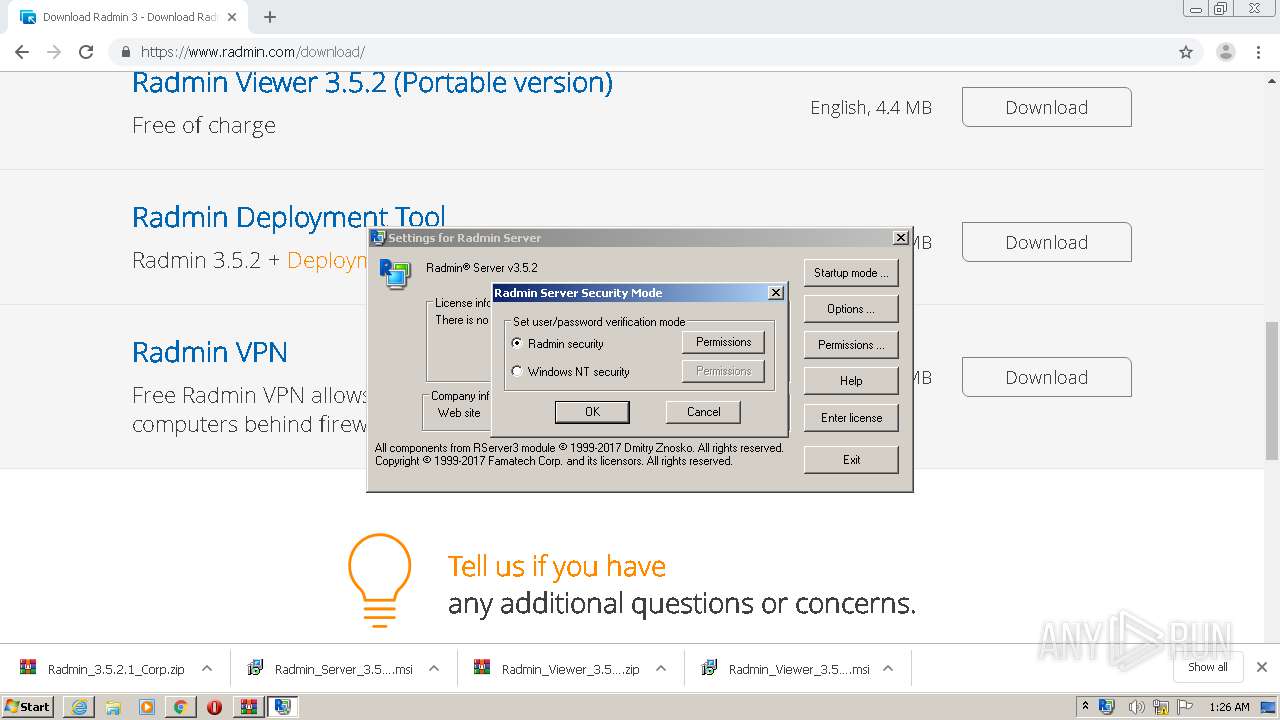
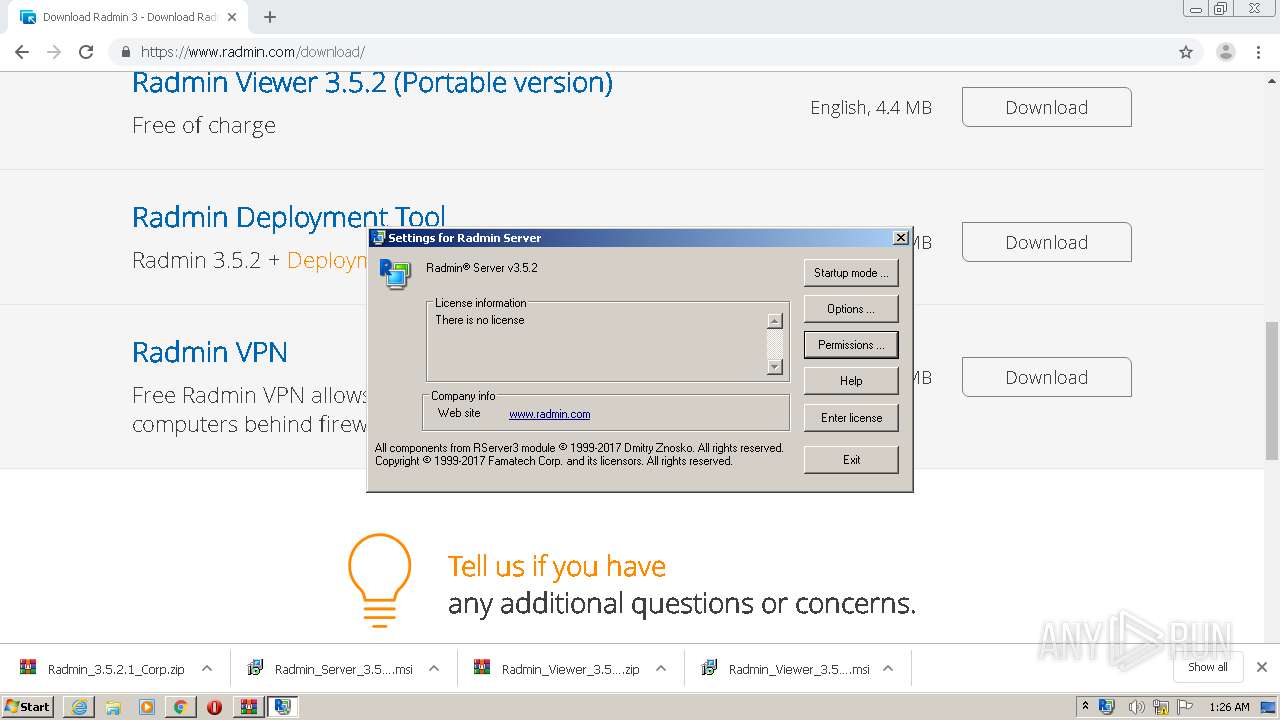
| 672 | "C:\Windows\system32\rserver30\RServer3.exe" /service | C:\Windows\system32\rserver30\RServer3.exe | services.exe | ||||||||||||
User: SYSTEM Company: Famatech Corp. Integrity Level: SYSTEM Description: Radmin Server Exit code: 0 Version: 3, 5, 2, 0 Modules
| |||||||||||||||
| 704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,2168438777248495283,14865404307217131316,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14151317941807048345 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4836 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 752 | "C:\Windows\system32\rserver30\FamItrfc.Exe" | C:\Windows\system32\rserver30\FamItrfc.Exe | — | RServer3.exe | |||||||||||
User: SYSTEM Company: Famatech Corp. Integrity Level: SYSTEM Description: Radmin component Exit code: 0 Version: 3,5,2,1205 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,2168438777248495283,14865404307217131316,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13467805585970113343 --mojo-platform-channel-handle=2140 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 856 | C:\Windows\system32\MsiExec.exe -Embedding D022BBD45222575EC1DDC0DE9E1F8C46 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 916 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1016 | "C:\Users\admin\AppData\Local\Temp\{1B704FD1-C00F-482F-8997-82F2F19E10E7}\rsetup.exe" /stop | C:\Users\admin\AppData\Local\Temp\{1B704FD1-C00F-482F-8997-82F2F19E10E7}\rsetup.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Famatech Corp. Integrity Level: SYSTEM Description: Radmin Setup Helper Exit code: 1 Version: 3, 5, 2, 0 Modules
| |||||||||||||||
| 1156 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
10 748
Read events
3 876
Write events
5 137
Delete events
1 735
Modification events
| (PID) Process: | (1476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 489928370 | |||
| (PID) Process: | (1476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30817780 | |||
| (PID) Process: | (1476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1476) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
80
Suspicious files
144
Text files
365
Unknown types
51
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab8D21.tmp | — | |
MD5:— | SHA256:— | |||
| 1516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar8D22.tmp | — | |
MD5:— | SHA256:— | |||
| 1516 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\AFHQ9EW9.txt | — | |
MD5:— | SHA256:— | |||
| 1516 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\W9B5BZ1N.txt | — | |
MD5:— | SHA256:— | |||
| 1516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | der | |
MD5:ED5A6F0B6B9CE0E483C59F5272265664 | SHA256:387CBFD6BA914237129F111C6CB19583765142FC54D1D122C3F540493D210595 | |||
| 1516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\DD9CD6EC8FB0411C5693C089FB4E41E3 | binary | |
MD5:FA3A48957E1E25C02164A63721B38EDE | SHA256:9374F3756AA3AAE6CA0F78083EC928E8F933FFB9C7D10149D14DE6980464059A | |||
| 1516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | der | |
MD5:17AA2DD7C12A667F392EFDBAF991F39B | SHA256:ACDFB099E176339CFD8800791E56DF6F3C56E50D5FF1B37BA33195FF985FF919 | |||
| 1516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\DD9CD6EC8FB0411C5693C089FB4E41E3 | der | |
MD5:45B0427B2245601059C8B6917BCA67B5 | SHA256:ABDE9726D0649FB4DF3069738EF74AB316E88A2EB7DCBC0390FB3AABE964B352 | |||
| 1516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\download[1].htm | html | |
MD5:733FEAC14C454A6845A78EFFCE001B9B | SHA256:2E6916924DB0F50A19355EE60886087C63ED6E32746D77093F8895801AD4CA79 | |||
| 1516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | binary | |
MD5:5357183C5B36CD42E3402D1A9BCBA408 | SHA256:E037E68A7E8B35B7BB16CBBD370537A27B7A81A592574C78DC42D50002E5F40A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
103
DNS requests
56
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1516 | iexplore.exe | GET | 200 | 2.16.186.35:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
1516 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEkwRzBFMEMwQTAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCBUJraGmcno%2B | US | der | 1.73 Kb | whitelisted |
1516 | iexplore.exe | GET | 200 | 2.16.186.27:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgTg9FXqYQ%2F9QAt9RQXNHGxggw%3D%3D | unknown | der | 527 b | whitelisted |
1516 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBTkIInKBAzXkF0Qh0pel3lfHJ9GPAQU0sSw0pHUTBFxs2HLPaH%2B3ahq1OMCAxvnFQ%3D%3D | US | der | 1.66 Kb | whitelisted |
1516 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
1516 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
1516 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA6O%2BBjVXZc2rpJ%2B516RAgc%3D | US | der | 471 b | whitelisted |
1516 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA6O%2BBjVXZc2rpJ%2B516RAgc%3D | US | der | 471 b | whitelisted |
1476 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1476 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1516 | iexplore.exe | 216.58.212.132:443 | www.google.com | Google Inc. | US | whitelisted |
1516 | iexplore.exe | 172.217.18.106:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
1516 | iexplore.exe | 5.254.23.206:443 | 705167.ssl.1c-bitrix-cdn.ru | — | RO | unknown |
1516 | iexplore.exe | 172.217.16.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1516 | iexplore.exe | 192.124.249.23:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
1516 | iexplore.exe | 172.217.21.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1516 | iexplore.exe | 31.13.92.14:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
1476 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1516 | iexplore.exe | 31.13.92.36:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
1516 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.radmin.com |
| suspicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
www.google-analytics.com |
| whitelisted |
705167.ssl.1c-bitrix-cdn.ru |
| suspicious |
www.google.com |
| malicious |
ajax.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
api.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
RServer3.exe | %n%n%n%n%n%n%n%n%n |
rserver3.exe | %n%n%n%n%n%n%n%n%n |