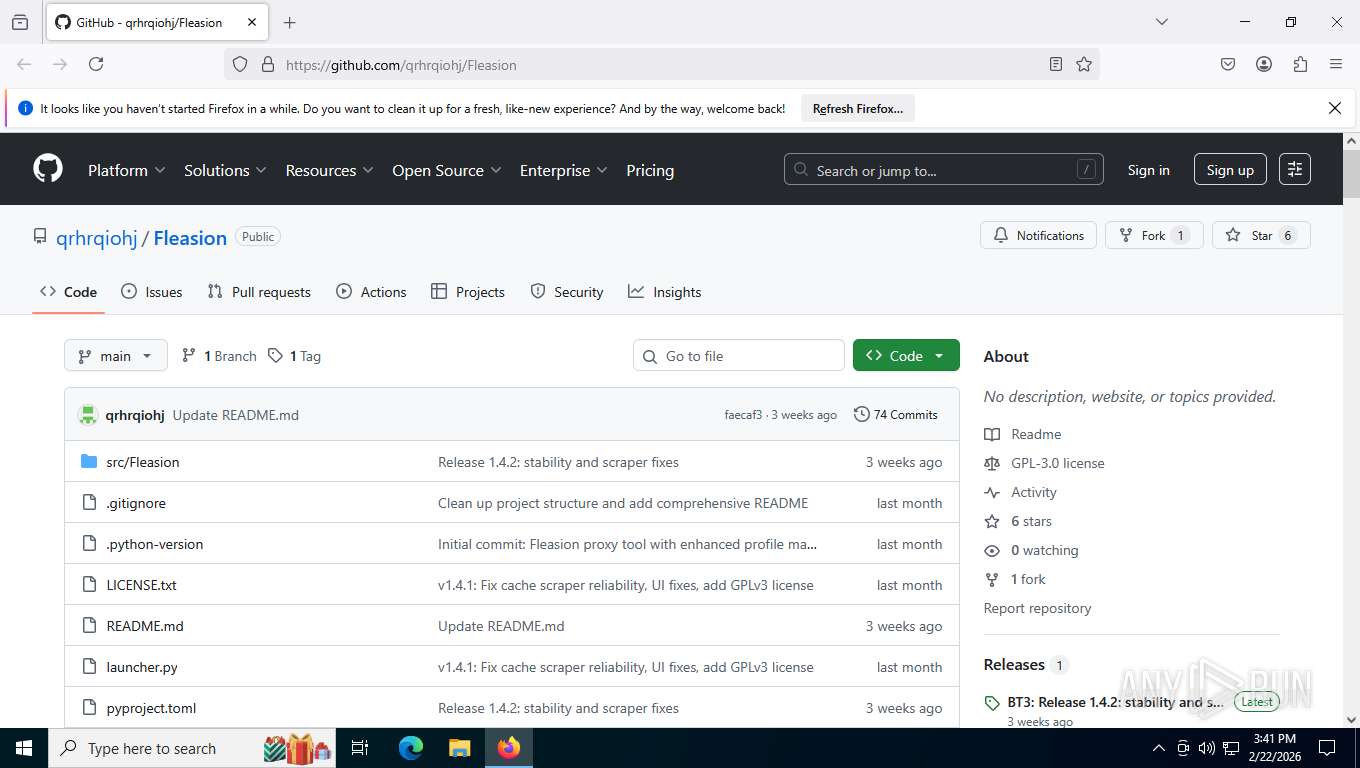
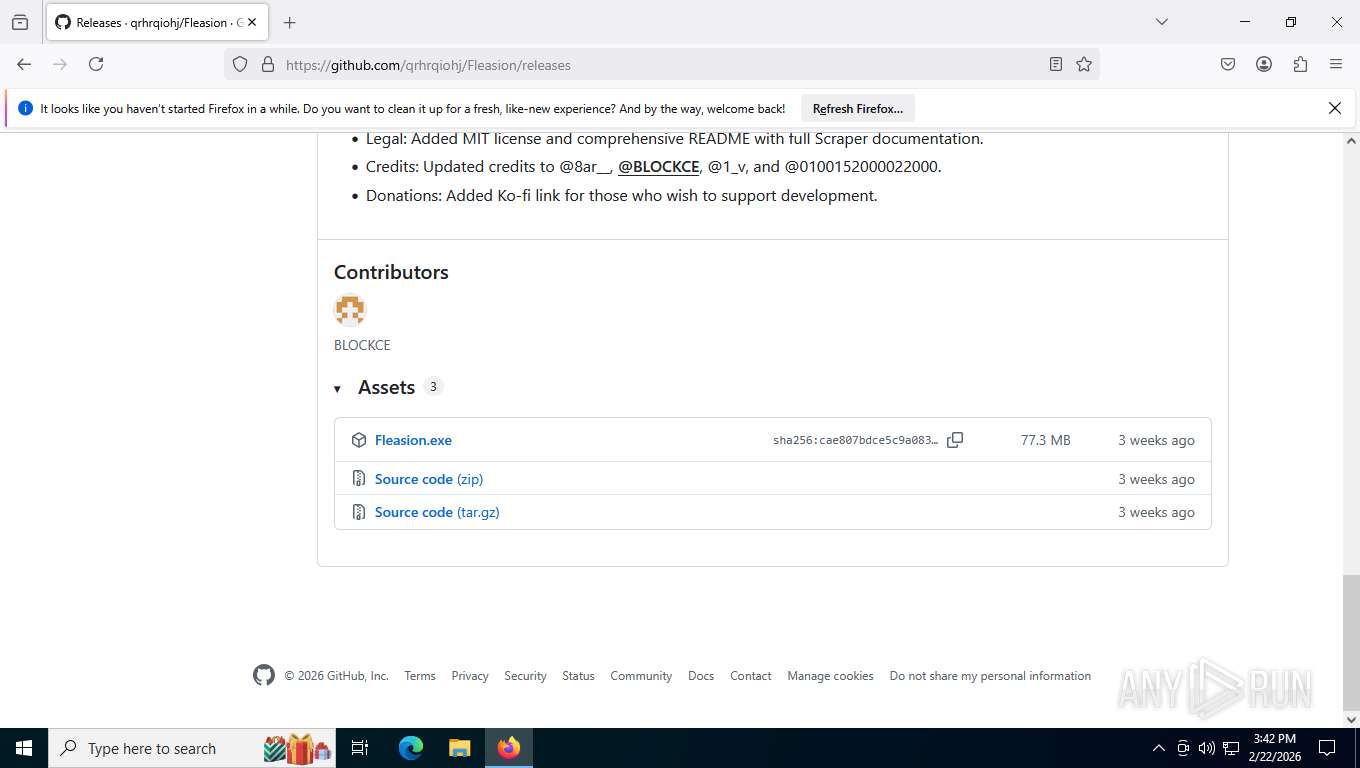
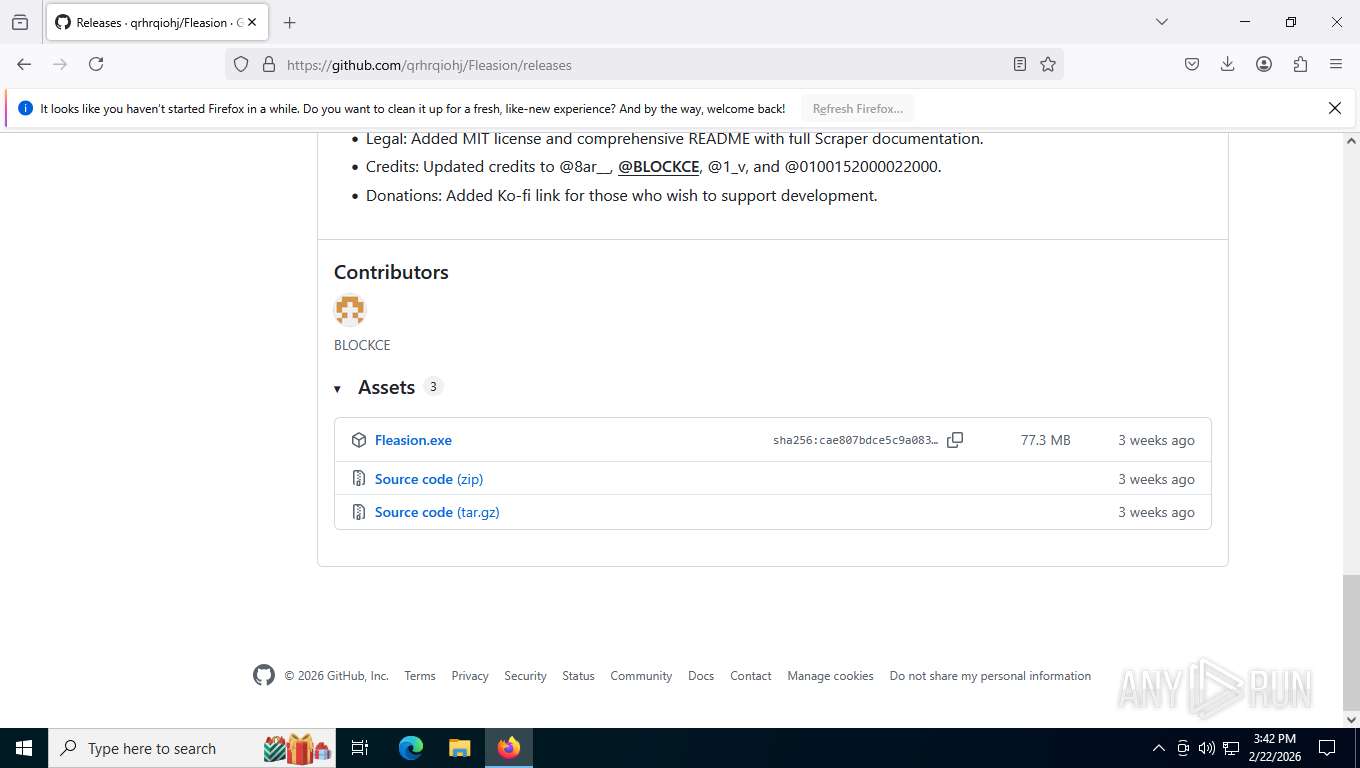
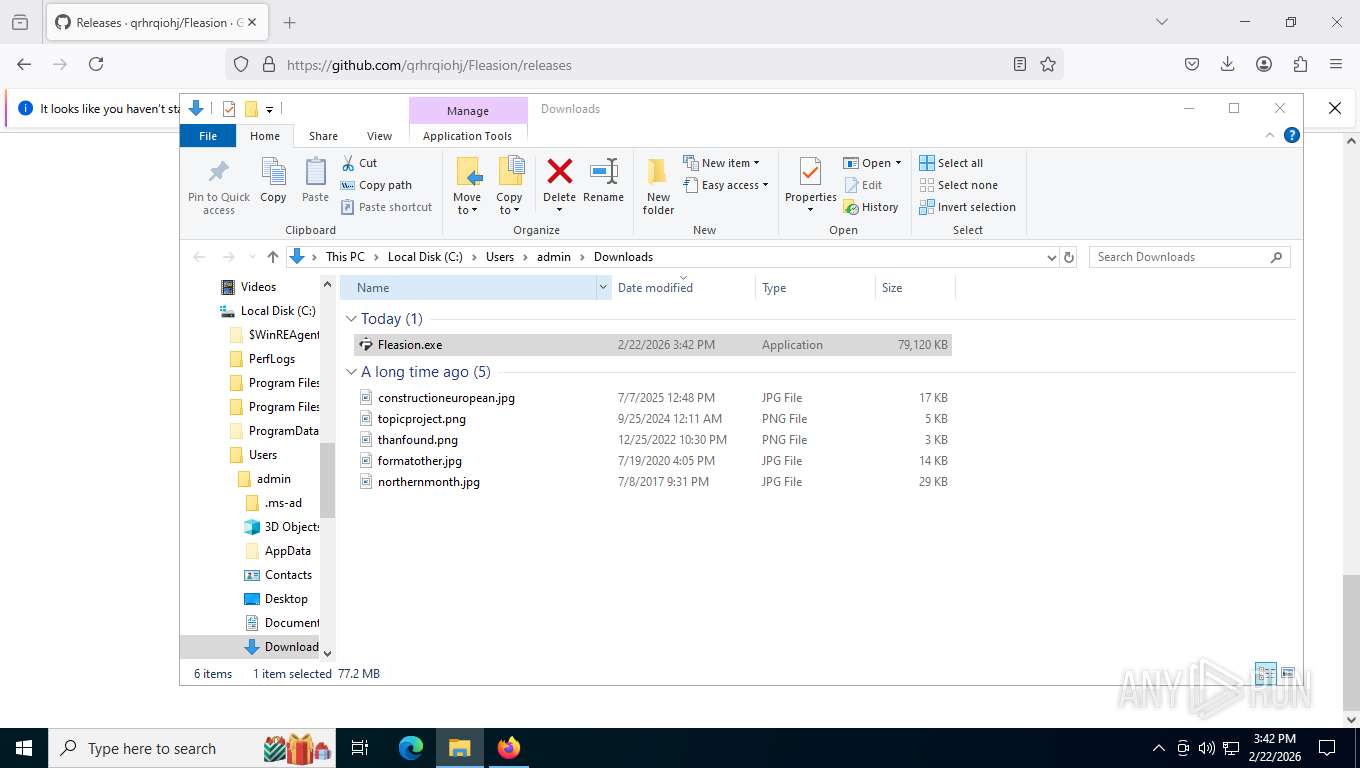
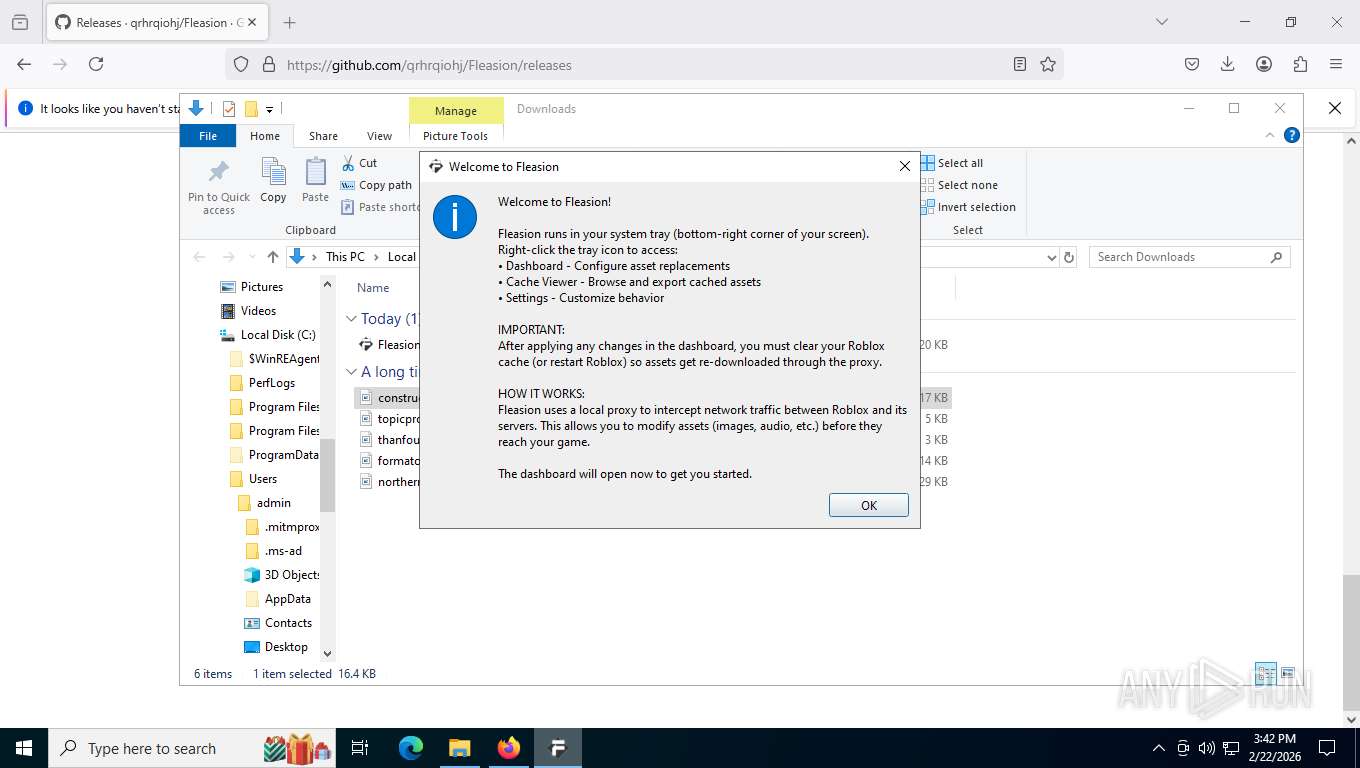
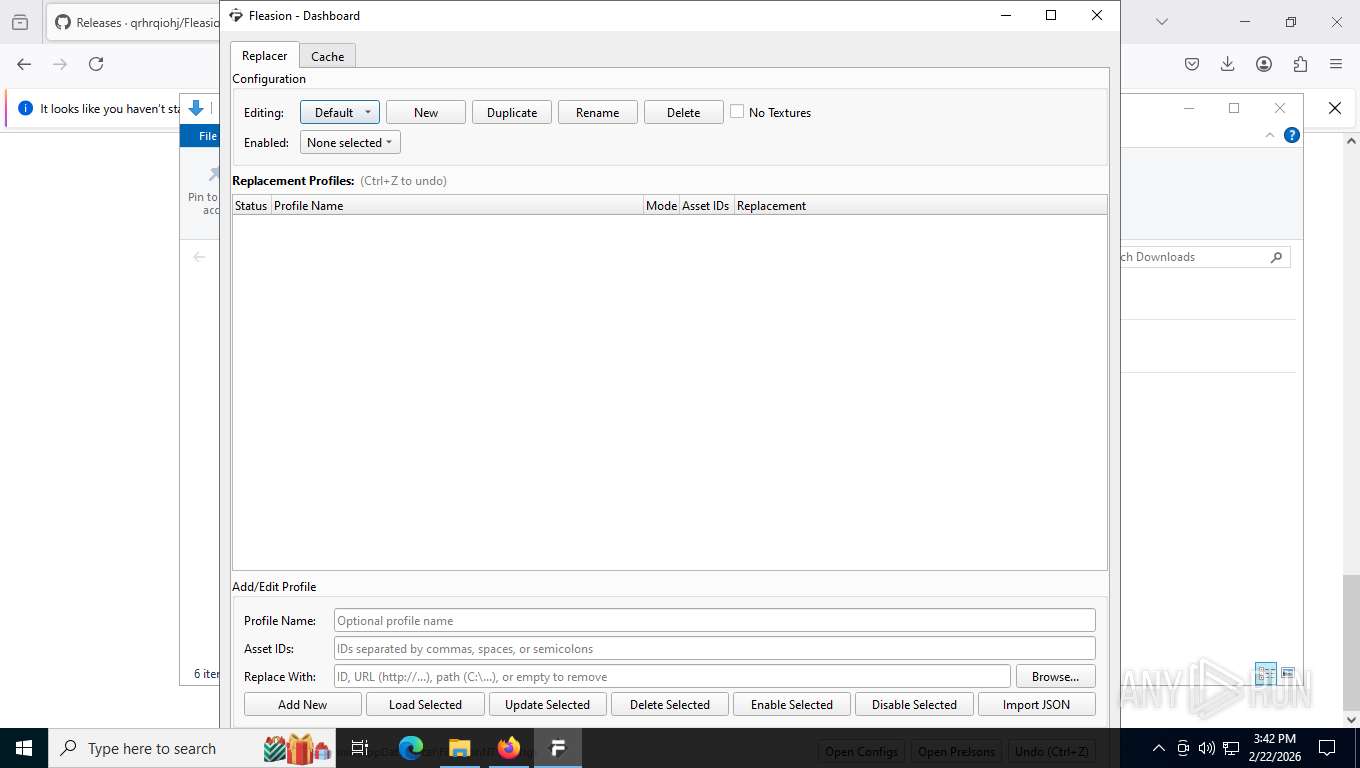
| URL: | https://github.com/qrhrqiohj/Fleasion |
| Full analysis: | https://app.any.run/tasks/c92042f1-e7f1-4f63-82f0-fd20c3297b5b |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2026, 20:41:47 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2D2B8CF64708CA658E5175FFA105F7A6 |
| SHA1: | 94A3D1619EBD9D336613618782D2D56C6F22E756 |
| SHA256: | FEDC0076B1987FECCD2D41AF9BE9A994B0BF34CB23C6A86555C86F4BD2FFC612 |
| SSDEEP: | 3:N8tEdkVULDLn:2uy6Ln |
MALICIOUS
GENERIC has been found (auto)
- Fleasion.exe (PID: 8360)
- Fleasion.exe (PID: 3624)
Malicious driver has been detected
- Fleasion.exe (PID: 8360)
- Fleasion.exe (PID: 8360)
- Fleasion.exe (PID: 3624)
- Fleasion.exe (PID: 3624)
SUSPICIOUS
Process drops python dynamic module
- Fleasion.exe (PID: 8360)
- Fleasion.exe (PID: 3624)
Drops a system driver (possible attempt to evade defenses)
- Fleasion.exe (PID: 8360)
- Fleasion.exe (PID: 3624)
Application launched itself
- Fleasion.exe (PID: 8360)
Get information on the list of running processes
- Fleasion.exe (PID: 476)
Reads the date of Windows installation
- Fleasion.exe (PID: 476)
Named pipe usage
- windows-redirector.exe (PID: 4040)
INFO
Checks supported languages
- Fleasion.exe (PID: 8360)
- Fleasion.exe (PID: 476)
- Fleasion.exe (PID: 3624)
- windows-redirector.exe (PID: 4040)
Reads the computer name
- Fleasion.exe (PID: 8360)
- Fleasion.exe (PID: 476)
- windows-redirector.exe (PID: 4040)
- Fleasion.exe (PID: 3624)
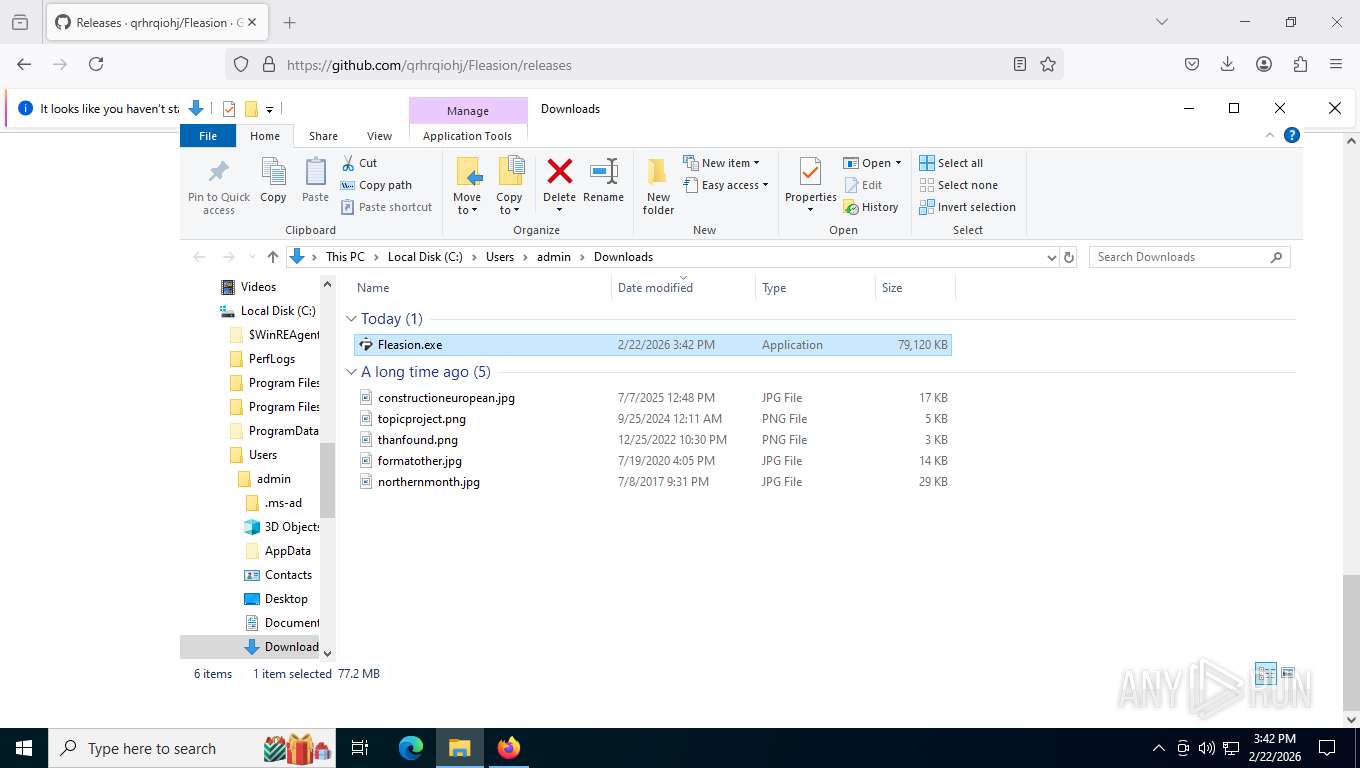
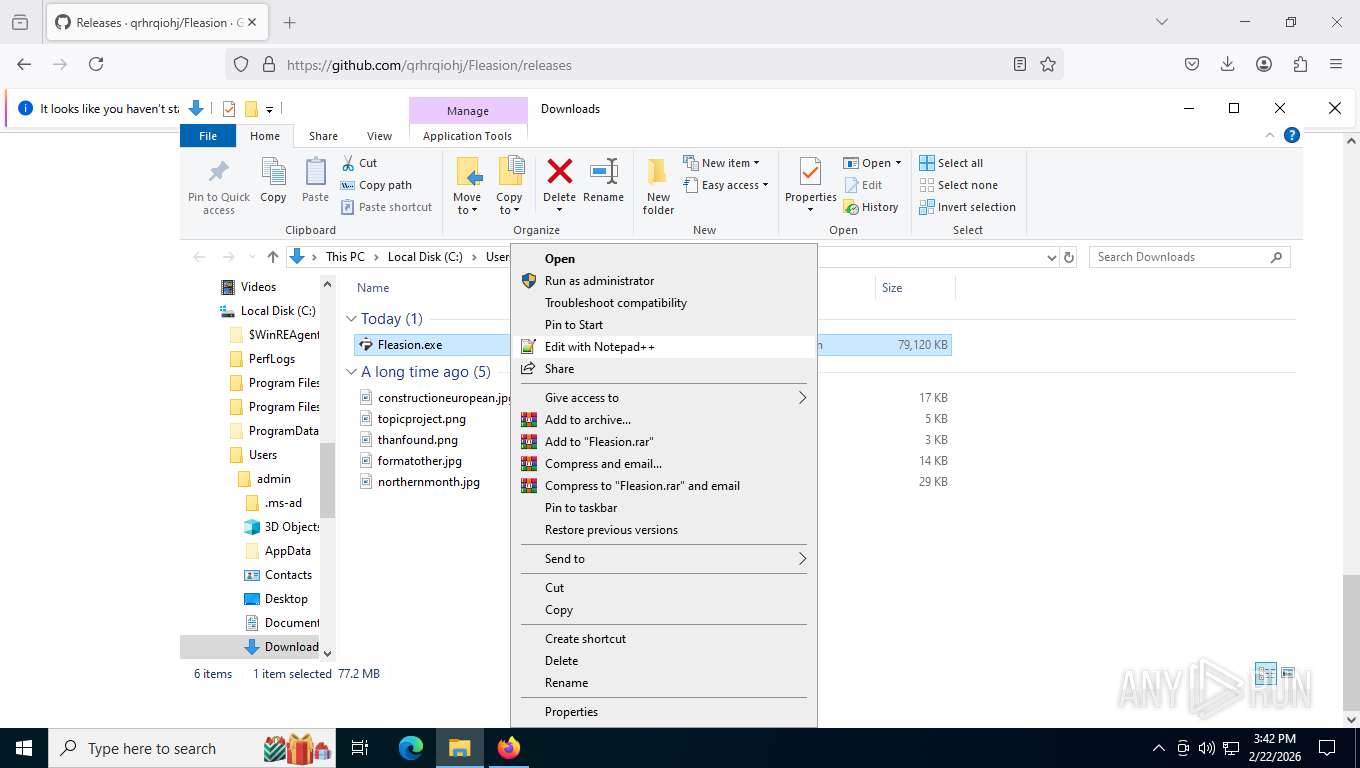
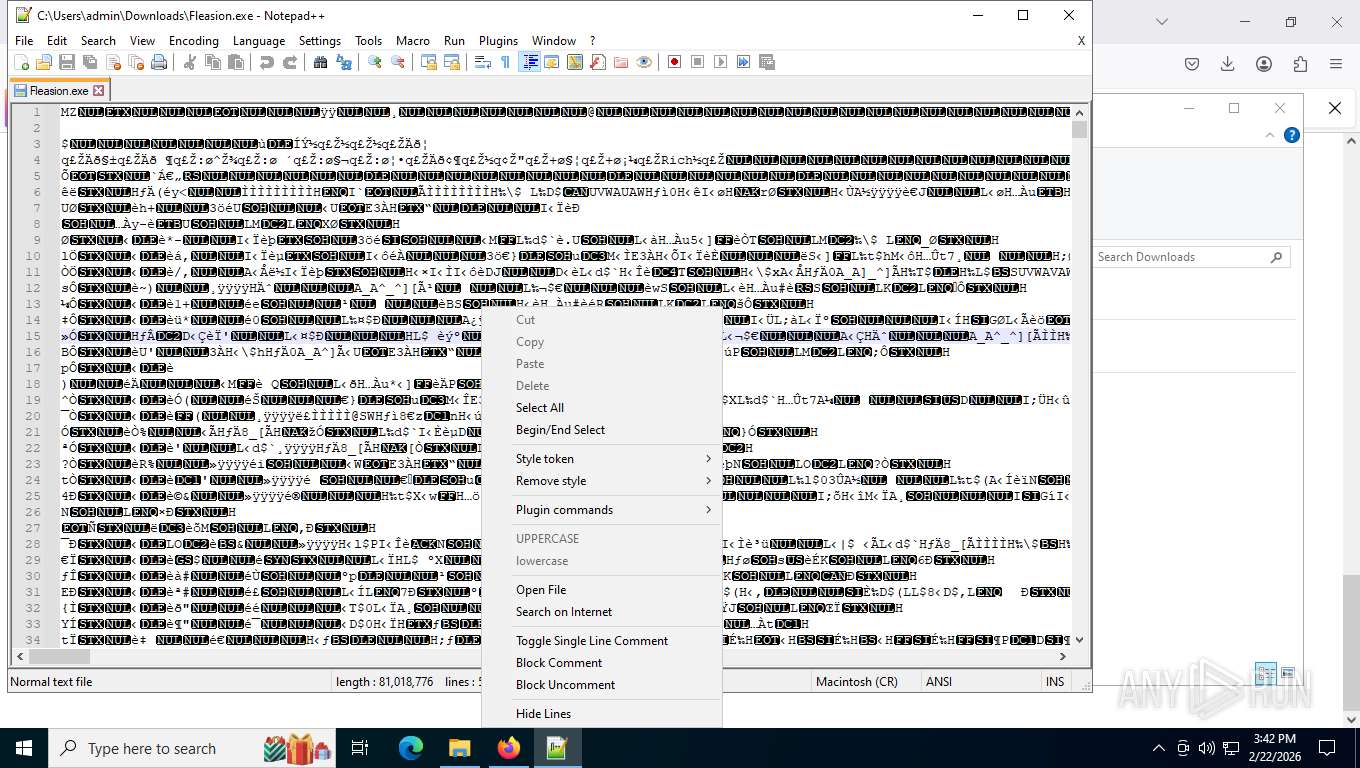
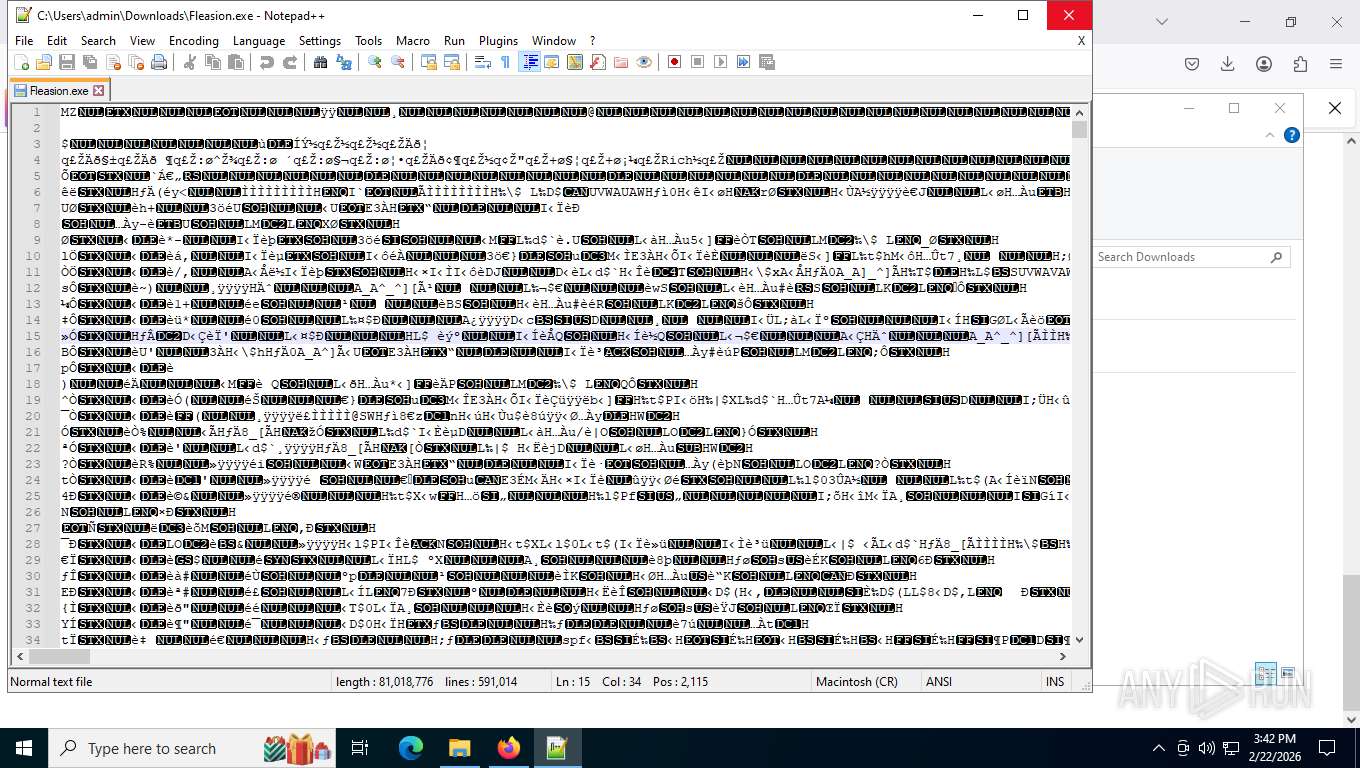
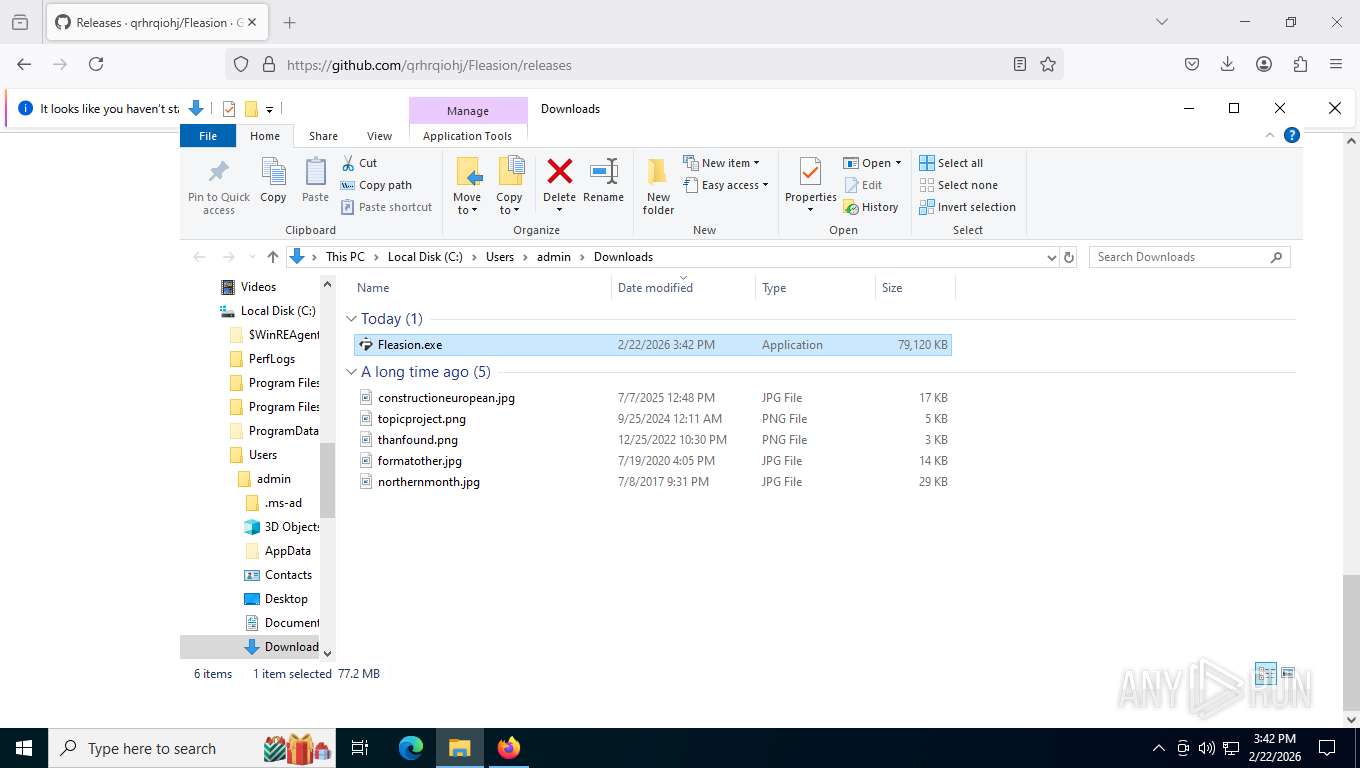
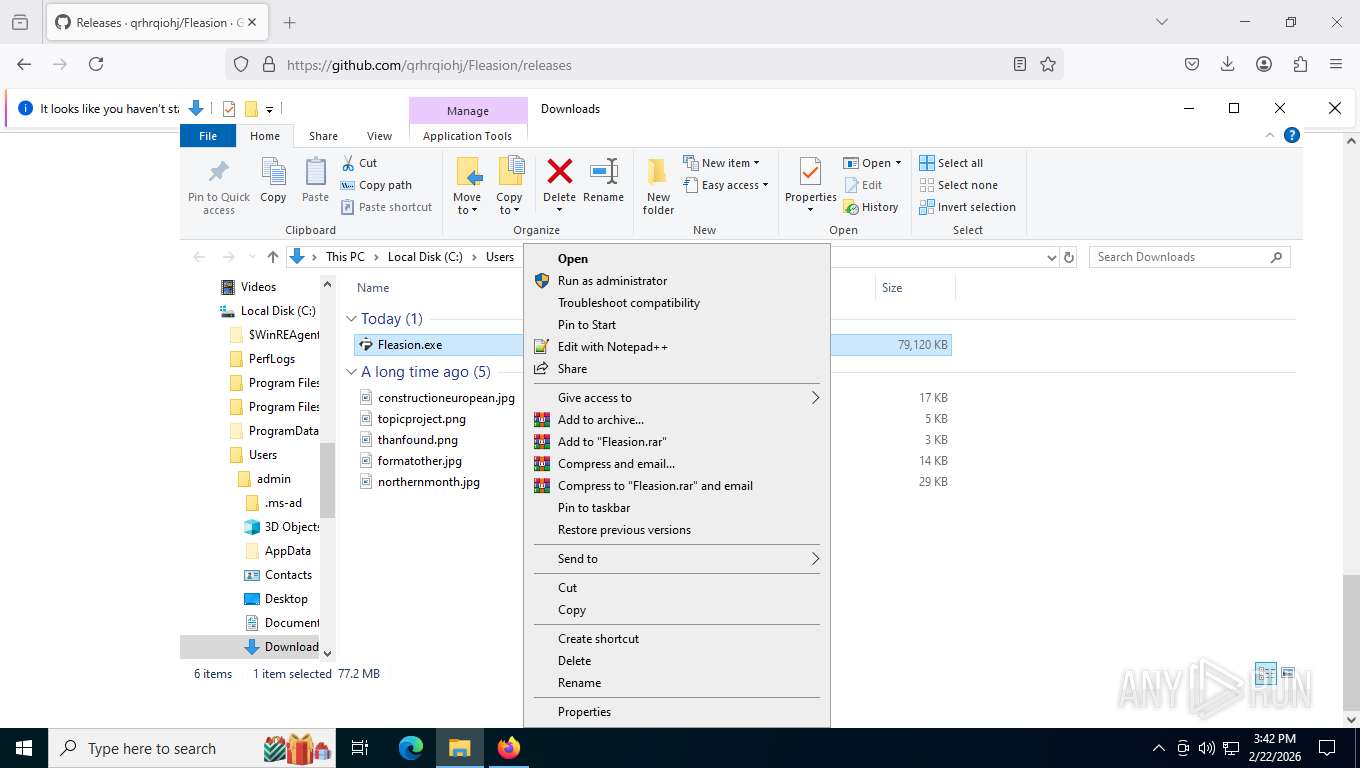
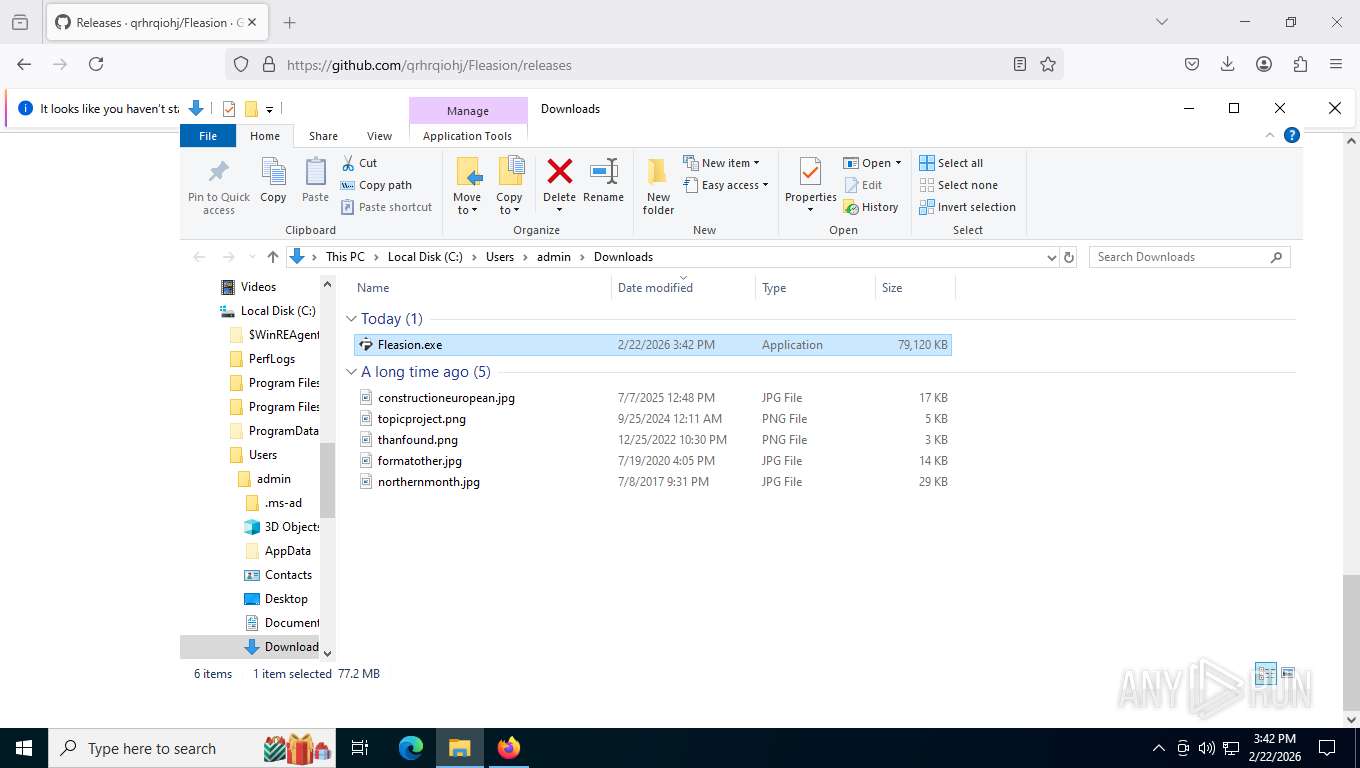
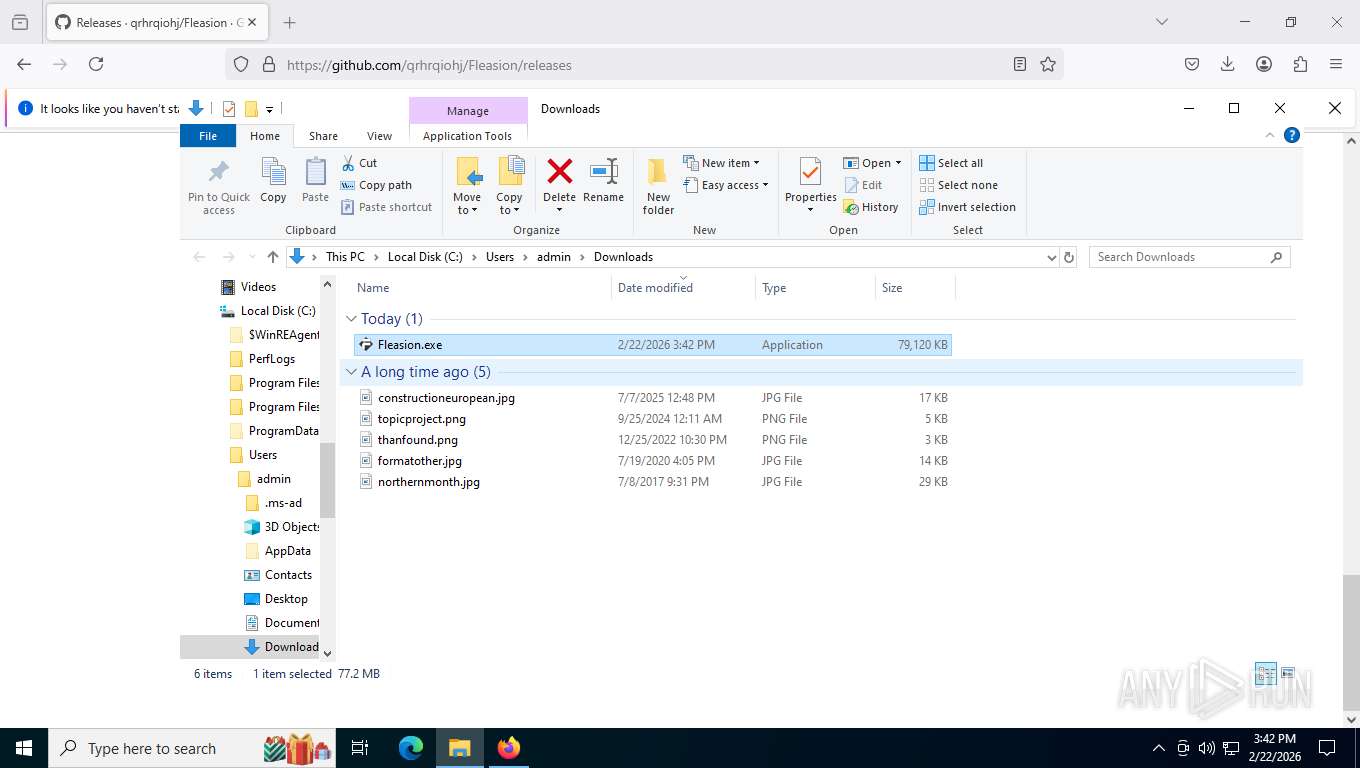
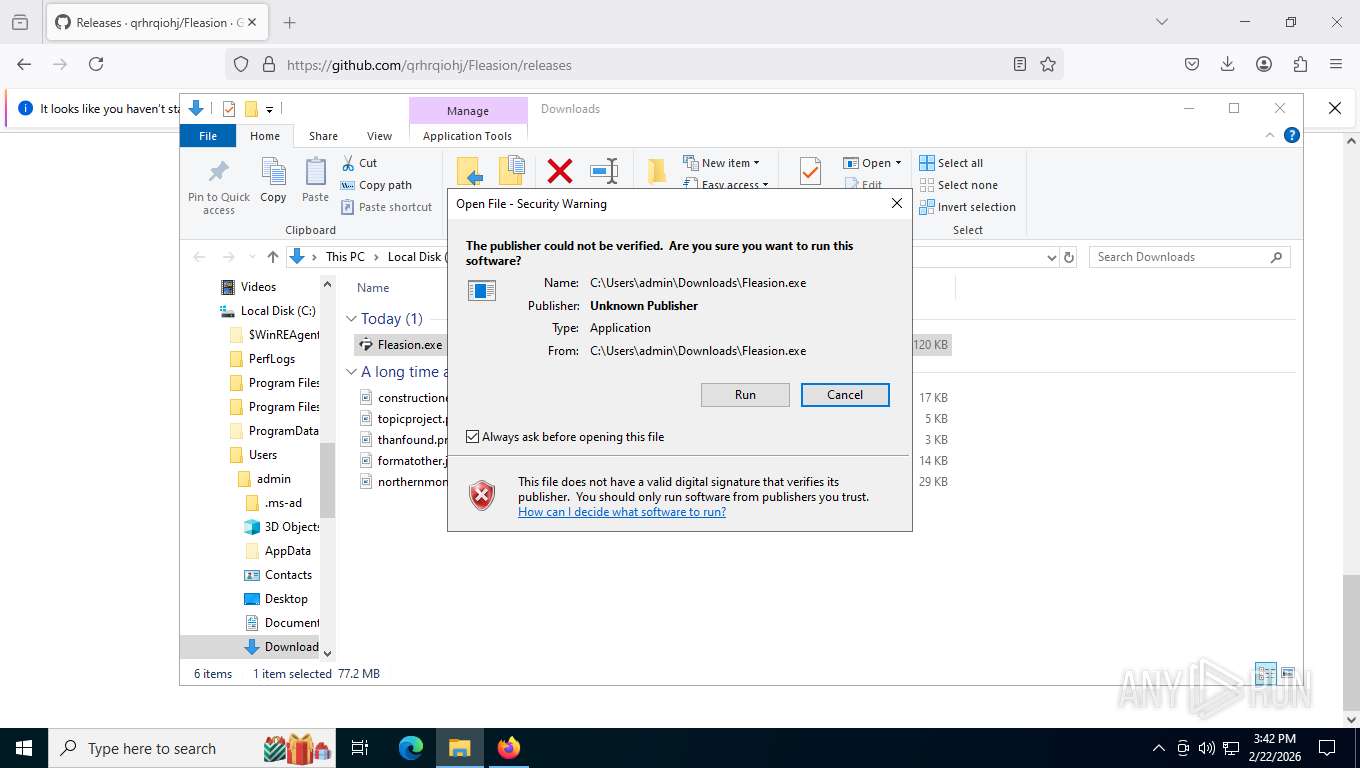
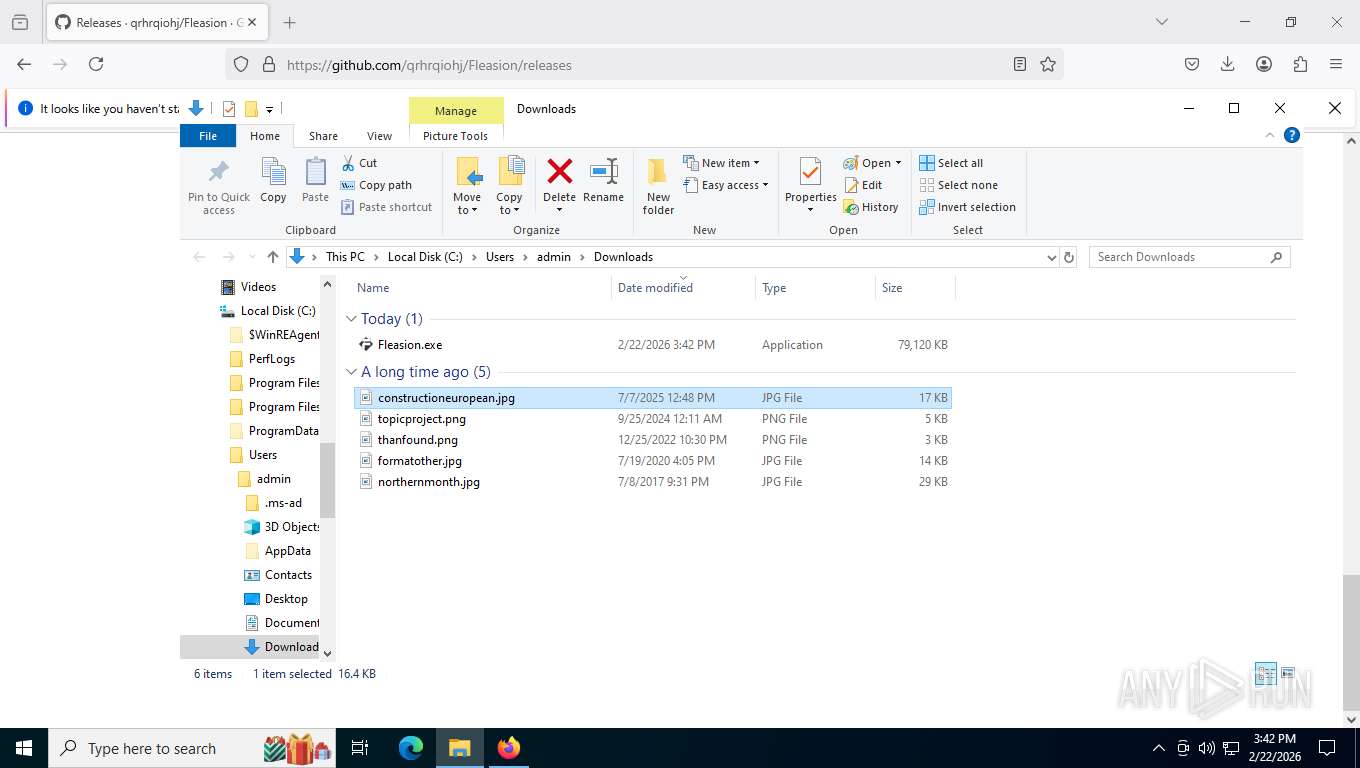
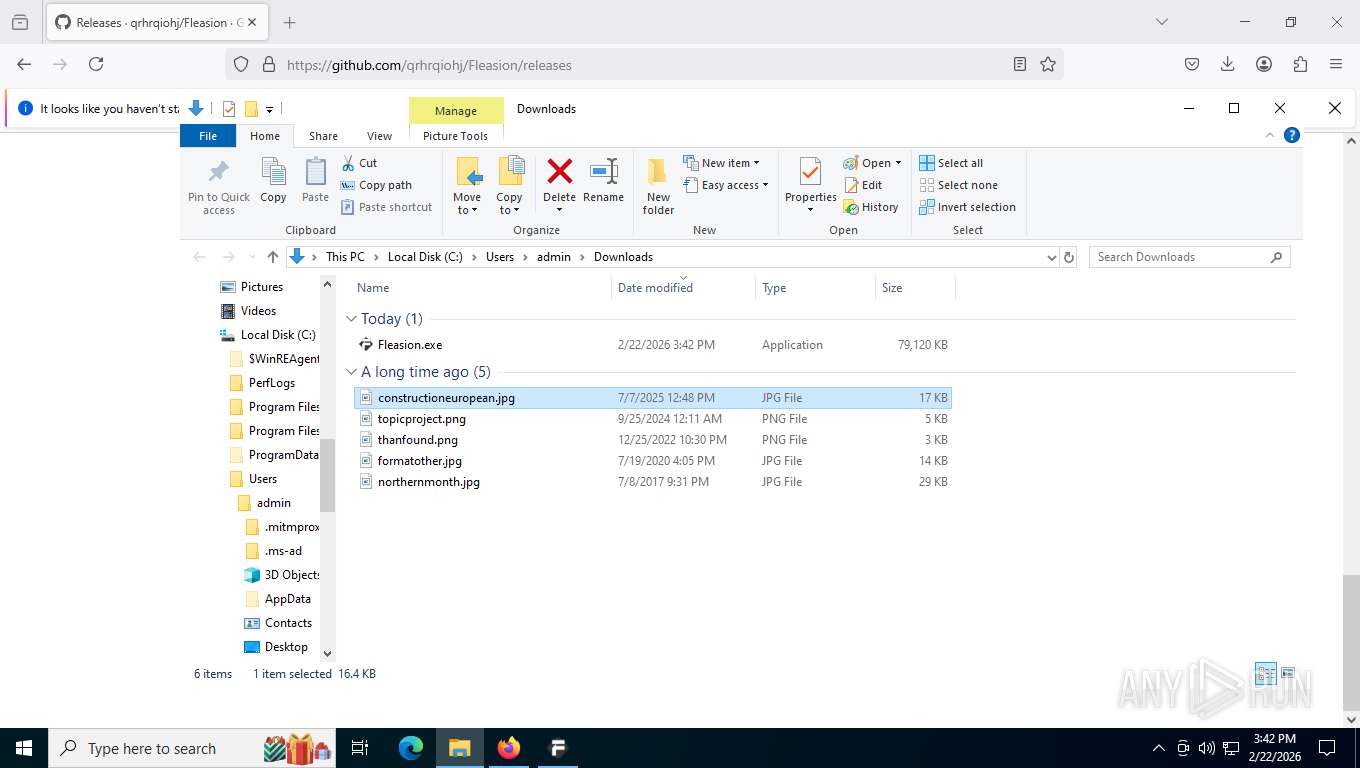
Manual execution by a user
- Fleasion.exe (PID: 8360)
- notepad++.exe (PID: 1672)
- Fleasion.exe (PID: 3624)
- mspaint.exe (PID: 4516)
Drops script file
- Fleasion.exe (PID: 8360)
- firefox.exe (PID: 5080)
- Fleasion.exe (PID: 476)
- Fleasion.exe (PID: 3624)
Application launched itself
- firefox.exe (PID: 1840)
- firefox.exe (PID: 5080)
Create files in a temporary directory
- Fleasion.exe (PID: 8360)
- Fleasion.exe (PID: 3624)
Reads security settings of Internet Explorer
- Fleasion.exe (PID: 476)
Creates files or folders in the user directory
- Fleasion.exe (PID: 476)
Checks proxy server information
- Fleasion.exe (PID: 476)
Reads the machine GUID from the registry
- Fleasion.exe (PID: 476)
Process checks computer location settings
- Fleasion.exe (PID: 476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
180
Monitored processes
32
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 476 | "C:\Users\admin\Downloads\Fleasion.exe" | C:\Users\admin\Downloads\Fleasion.exe | Fleasion.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1352 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tasklist.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Downloads\Fleasion.exe" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://github.com/qrhrqiohj/Fleasion | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 1856 | tasklist /FI "IMAGENAME eq RobloxPlayerBeta.exe" | C:\Windows\System32\tasklist.exe | — | Fleasion.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4776 -prefsLen 39330 -prefMapHandle 4768 -prefMapSize 272981 -jsInitHandle 4812 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4920 -initialChannelId {6ab03207-f477-47d5-9037-7d36c02a7cc5} -parentPid 5080 -crashReporter "\\.\pipe\gecko-crash-server-pipe.5080" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 8 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 2748 | tasklist /FI "IMAGENAME eq RobloxPlayerBeta.exe" | C:\Windows\System32\tasklist.exe | — | Fleasion.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3624 | "C:\Users\admin\Downloads\Fleasion.exe" | C:\Users\admin\Downloads\Fleasion.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4040 | "C:\Users\admin\AppData\Local\Temp\_MEI83602\mitmproxy_windows\windows-redirector.exe" \\.\pipe\mitmproxy-transparent-proxy-476 | C:\Users\admin\AppData\Local\Temp\_MEI83602\mitmproxy_windows\windows-redirector.exe | — | Fleasion.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 4516 | "C:\WINDOWS\system32\mspaint.exe" "C:\Users\admin\Downloads\constructioneuropean.jpg" | C:\Windows\System32\mspaint.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Paint Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 320
Read events
5 285
Write events
34
Delete events
1
Modification events
| (PID) Process: | (476) Fleasion.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\DirectSound\Speaker Configuration |
| Operation: | write | Name: | Speaker Configuration |
Value: 4 | |||
| (PID) Process: | (4516) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | GridExtent |
Value: 1 | |||
| (PID) Process: | (4516) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\Ribbon |
| Operation: | write | Name: | QatItems |
Value: <siq:customUI xmlns:siq="http://schemas.microsoft.com/windows/2009/ribbon/qat"><siq:ribbon minimized="false"><siq:qat position="0"><siq:sharedControls><siq:control idQ="siq:20002" visible="false" argument="0"/><siq:control idQ="siq:20003" visible="false" argument="0"/><siq:control idQ="siq:20004" visible="true" argument="0"/><siq:control idQ="siq:20014" visible="false" argument="0"/><siq:control idQ="siq:20017" visible="false" argument="0"/><siq:control idQ="siq:20019" visible="false" argument="0"/><siq:control idQ="siq:31001" visible="true" argument="0"/><siq:control idQ="siq:31002" visible="true" argument="0"/></siq:sharedControls></siq:qat></siq:ribbon></siq:customUI> | |||
| (PID) Process: | (4516) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\Recent File List |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4516) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\Recent File List |
| Operation: | write | Name: | File1 |
Value: C:\Users\admin\Downloads\constructioneuropean.jpg | |||
| (PID) Process: | (4040) windows-redirector.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\System\WinDivert |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Users\admin\AppData\Local\Temp\_MEI83602\mitmproxy_windows\WinDivert64.sys | |||
| (PID) Process: | (4040) windows-redirector.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\EventLog\System\WinDivert |
| Operation: | write | Name: | TypesSupported |
Value: 7 | |||
| (PID) Process: | (4516) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | WindowPlacement |
Value: 2C00000000000000010000000000000000000000FFFFFFFFFFFFFFFF870000004C000000C7040000B2020000 | |||
| (PID) Process: | (4516) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ShowThumbnail |
Value: 0 | |||
| (PID) Process: | (4516) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | BMPWidth |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
1 701
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5080 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 5080 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5080 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:16E941D6905EF179B1F0A343AEC762EC | SHA256:D120D6EEF9CDEA96D156B8FA666D3C1DDF512CC3785B2E56E955D05414DA7B54 | |||
| 5080 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:3134ED3F12E4F4F8643DB90043B0FD7B | SHA256:26E4F122034D7A03F6DA0E707799B09CBEEBDAF8D7A3133A1F7BD894AC72EEA1 | |||
| 5080 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | binary | |
MD5:CEC7BB1C0286EEA4A6588CD28277B121 | SHA256:D5273EF16FC181EE84F693A9465E9AA05C68331546592A97B8028A9115F9EF7A | |||
| 5080 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5080 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5080 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5080 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5080 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
187
TCP/UDP connections
80
DNS requests
108
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5080 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | binary | 8 b | unknown |
5080 | firefox.exe | GET | 101 | 34.107.243.93:443 | https://push.services.mozilla.com/ | US | — | — | unknown |
5080 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | binary | 90 b | unknown |
5080 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | US | binary | 281 b | whitelisted |
5080 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | US | binary | 281 b | whitelisted |
5080 | firefox.exe | POST | 200 | 142.251.141.131:80 | http://o.pki.goog/we2 | US | binary | 279 b | whitelisted |
5080 | firefox.exe | GET | 200 | 151.101.193.91:443 | https://firefox.settings.services.mozilla.com/v1/ | US | binary | 1.20 Kb | unknown |
5080 | firefox.exe | GET | 200 | 151.101.193.91:443 | https://firefox.settings.services.mozilla.com/v1/buckets/monitor/collections/changes/changeset?collection=url-parser-default-unknown-schemes-interventions&bucket=main&_expected=0 | US | binary | 274 b | unknown |
5080 | firefox.exe | GET | 200 | 151.101.193.91:443 | https://firefox.settings.services.mozilla.com/v1/buckets/main/collections/hijack-blocklists?_expected=1605801189258 | US | binary | 1.68 Kb | unknown |
5080 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | binary | 8 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
1324 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2860 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5080 | firefox.exe | 151.101.193.91:443 | firefox.settings.services.mozilla.com | FASTLY | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5080 | firefox.exe | 140.82.114.4:443 | github.com | GITHUB | US | whitelisted |
5080 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
5080 | firefox.exe | 151.101.1.91:443 | firefox.settings.services.mozilla.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
mozilla.map.fastly.net |
| whitelisted |
github.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |
1324 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
5080 | firefox.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
5080 | firefox.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
5080 | firefox.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|