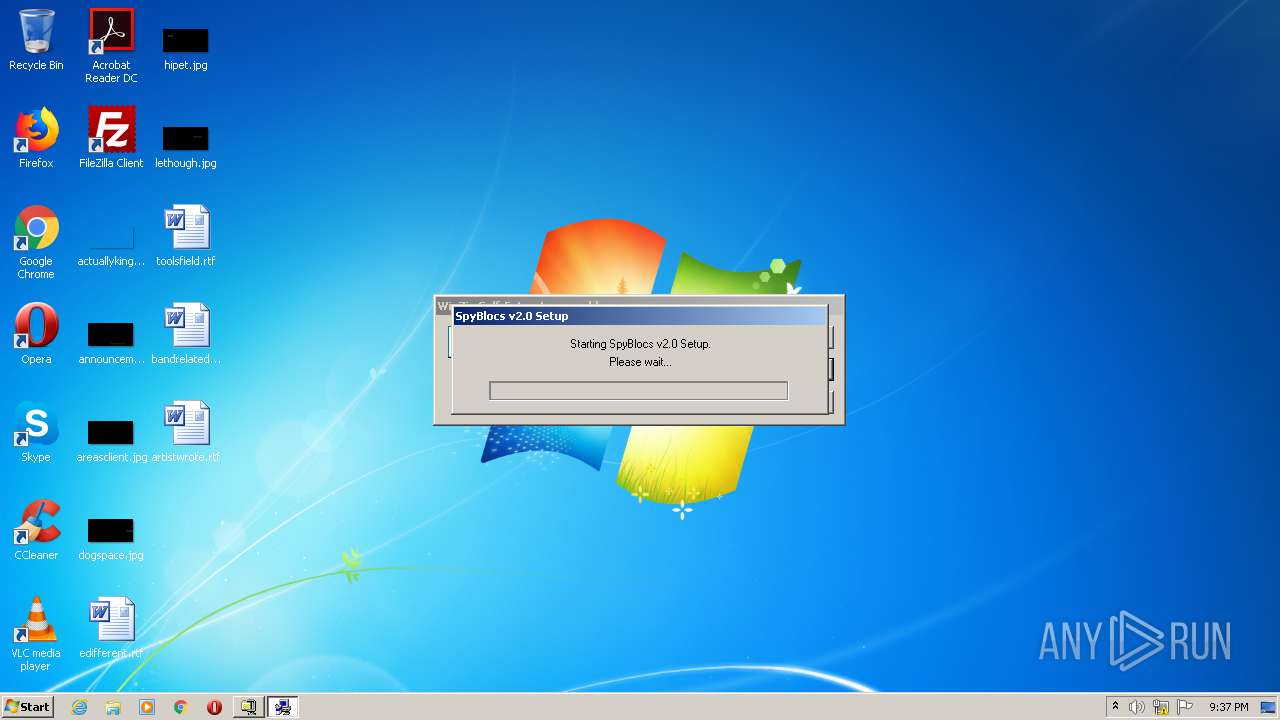
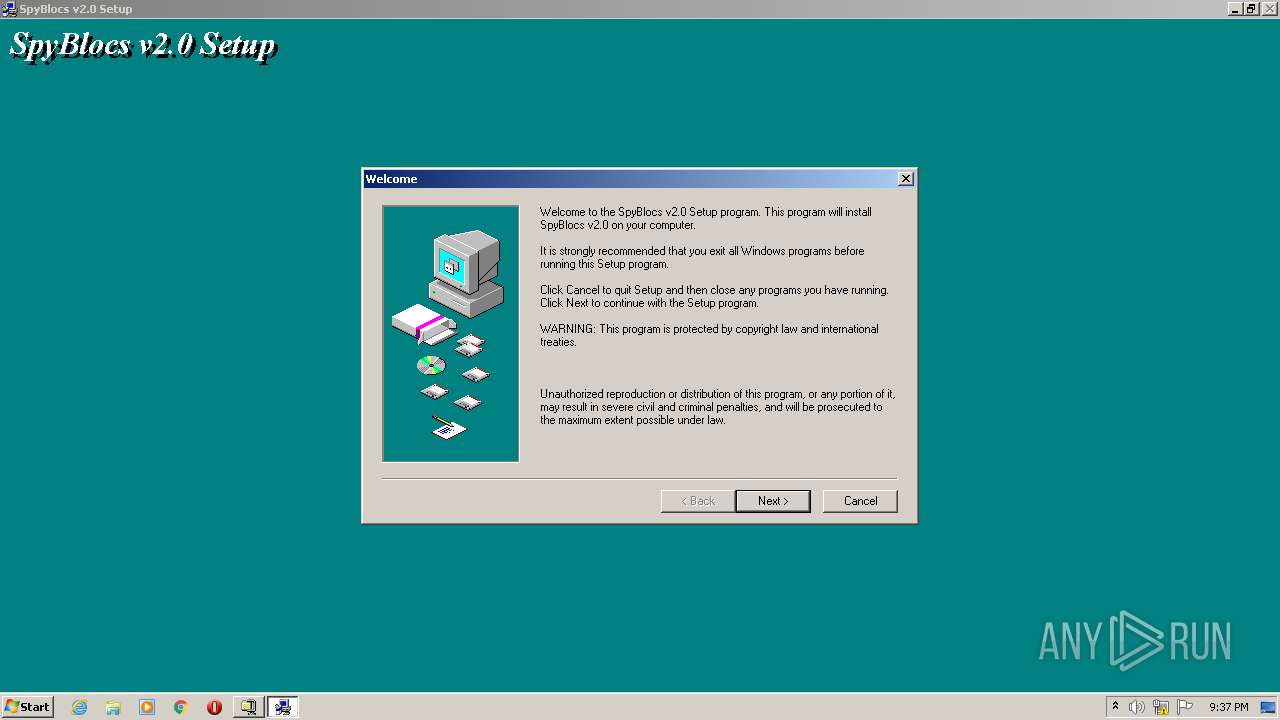
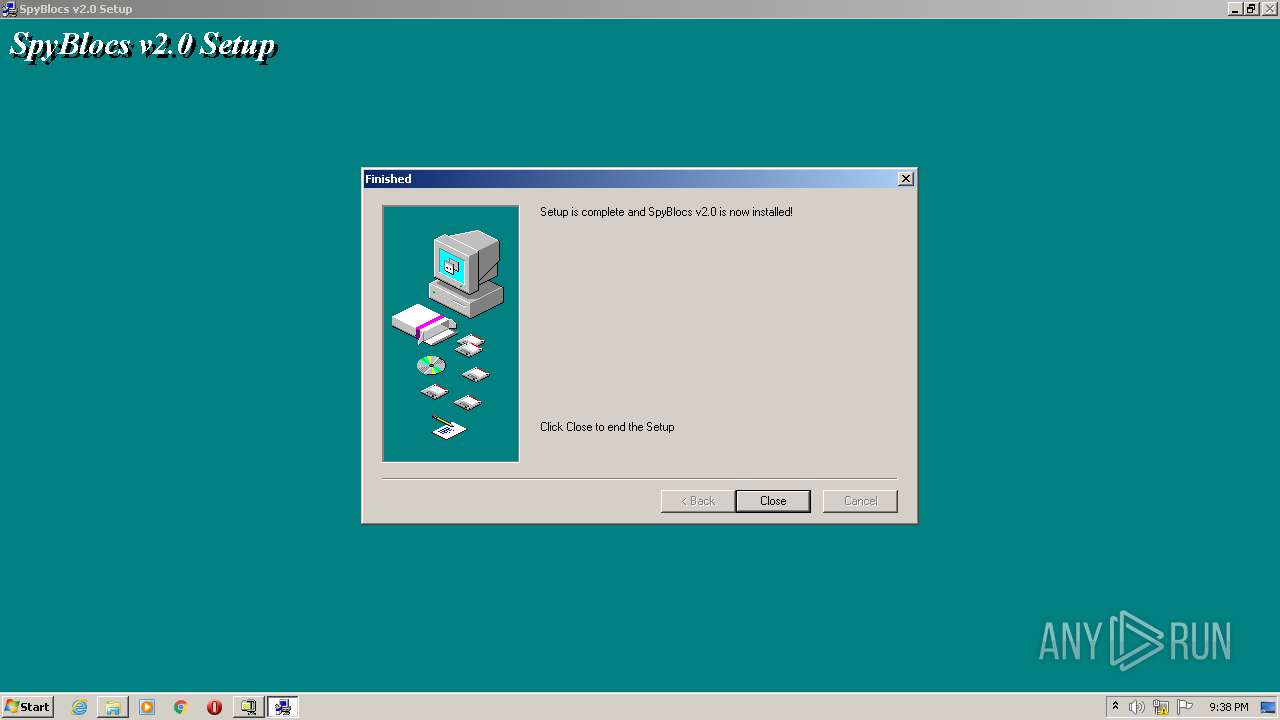
| File name: | spyblocs.exe |
| Full analysis: | https://app.any.run/tasks/74655b2e-33c8-4322-becd-fd28af2cb22a |
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 20:37:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FA66CEF36CAB744E0BBCEA6D7741FC10 |
| SHA1: | 5B7CEA6807FE295728B7070B169570F844C270A8 |
| SHA256: | FEB432DBFE600E42502E4816DA247AE932A244E57BB6BFDADBEDFF652BDCE648 |
| SSDEEP: | 49152:cBoGsinnUoo10MGsejlzqWOuQb6EzFu0x4CiM0qKAkKhGIIMNKQdVL8Dt6DvgdAy:zGsinUXZco1Oi3YKhuMNKQbL94g9C |
MALICIOUS
Loads dropped or rewritten executable
- spyblocs.exe (PID: 2792)
- SpyBlocs.exe (PID: 2568)
Application was dropped or rewritten from another process
- spyblocs.exe (PID: 2792)
- SpyBlocs.exe (PID: 2568)
- unvise32.exe (PID: 3452)
- unvise32.exe (PID: 2056)
Changes the autorun value in the registry
- spyblocs.exe (PID: 2792)
- SpyBlocs.exe (PID: 2568)
SUSPICIOUS
Executable content was dropped or overwritten
- spyblocs.exe (PID: 2792)
- spyblocs.exe (PID: 3652)
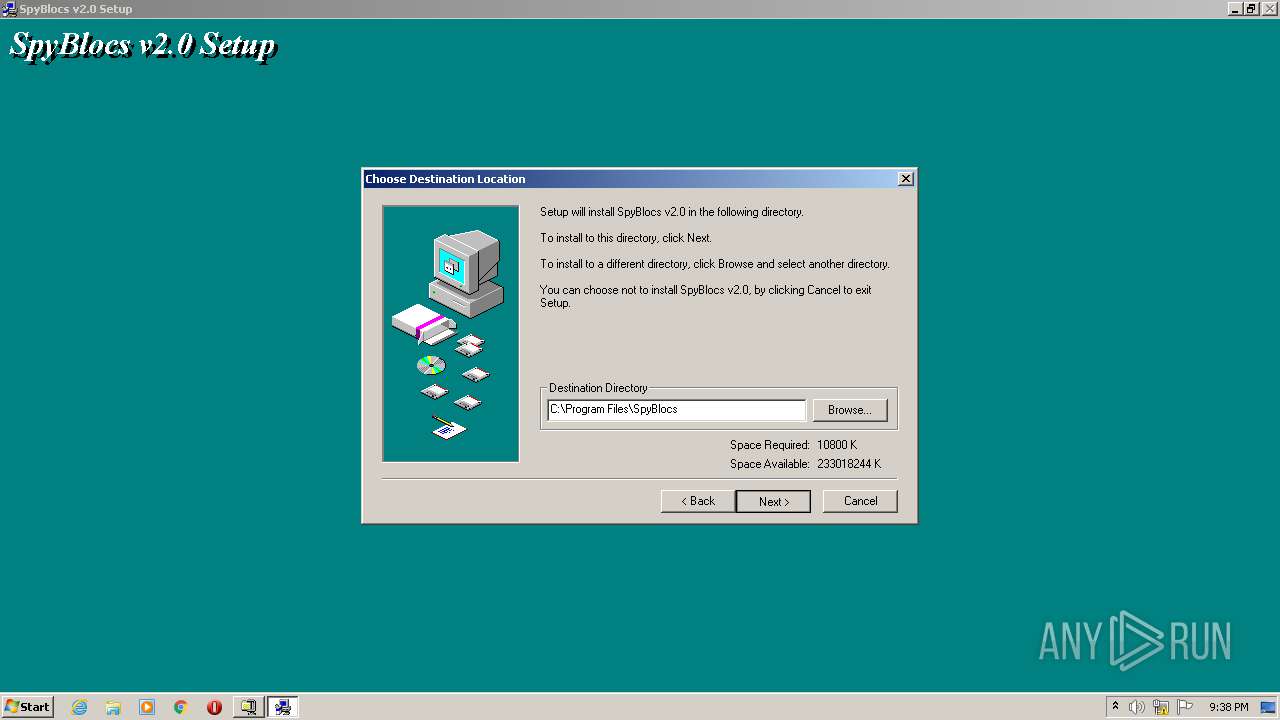
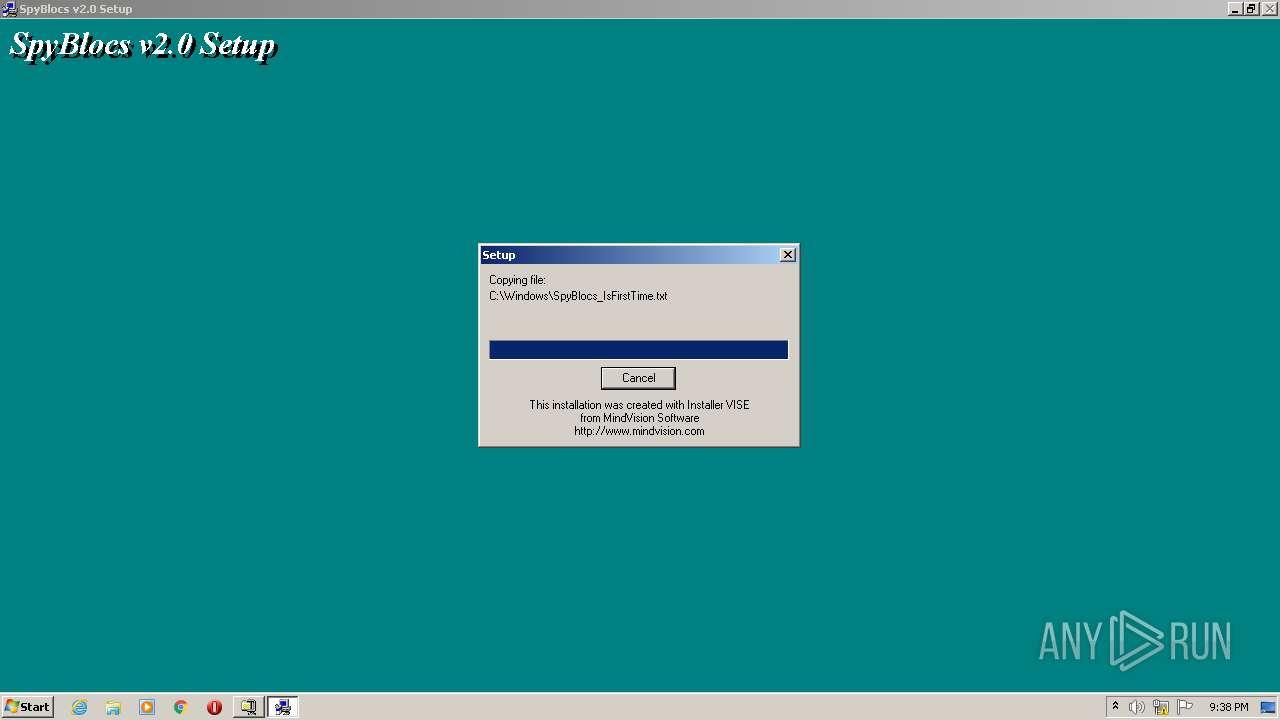
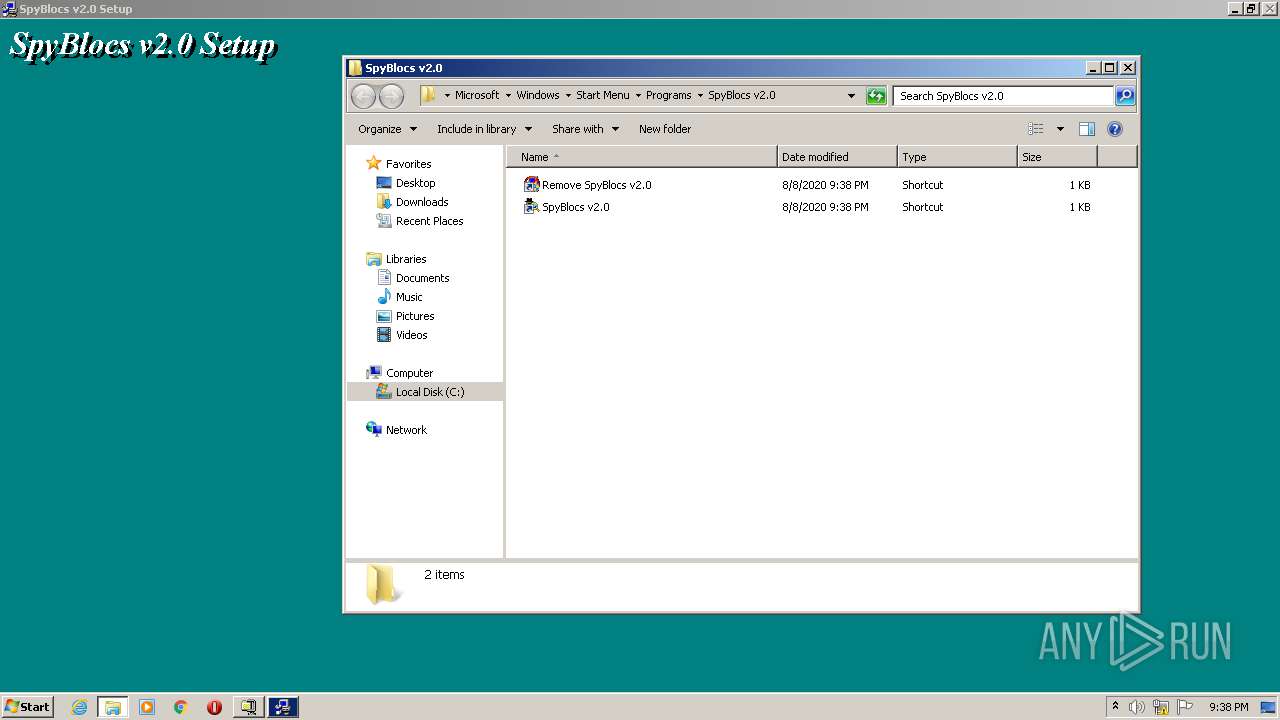
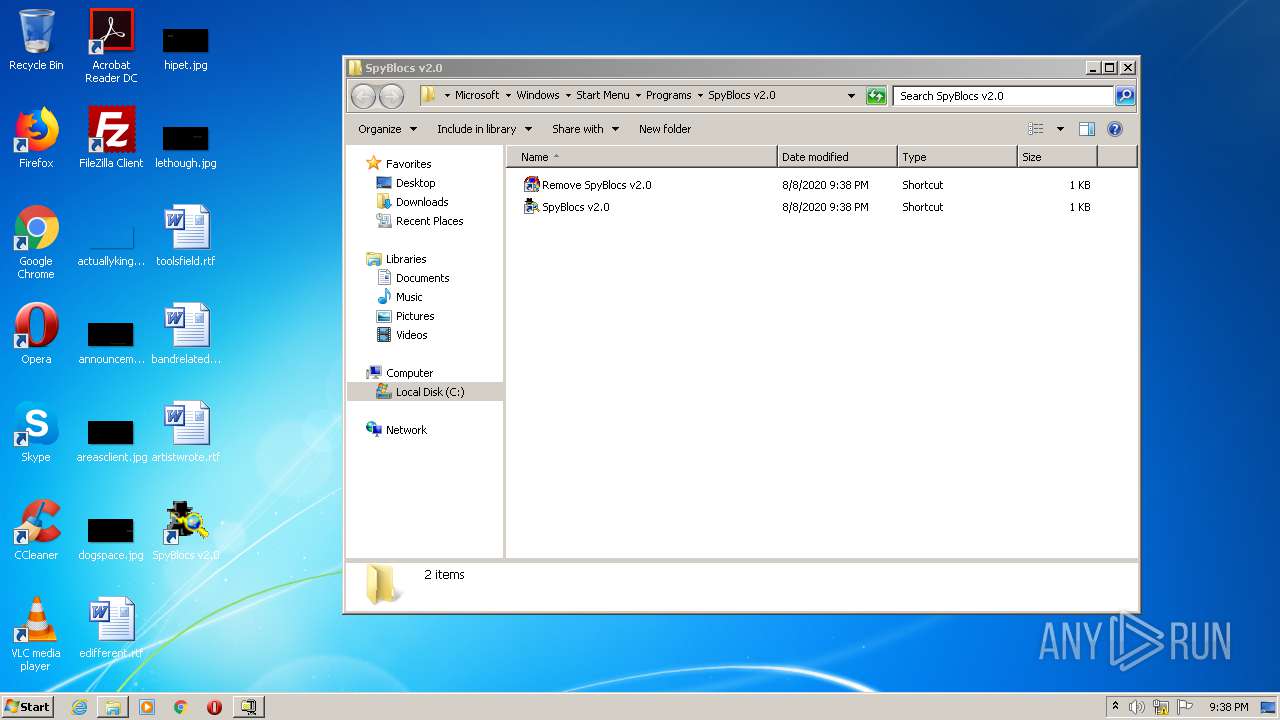
Creates files in the program directory
- spyblocs.exe (PID: 2792)
- SpyBlocs.exe (PID: 2568)
Creates files in the Windows directory
- spyblocs.exe (PID: 2792)
Creates a software uninstall entry
- spyblocs.exe (PID: 2792)
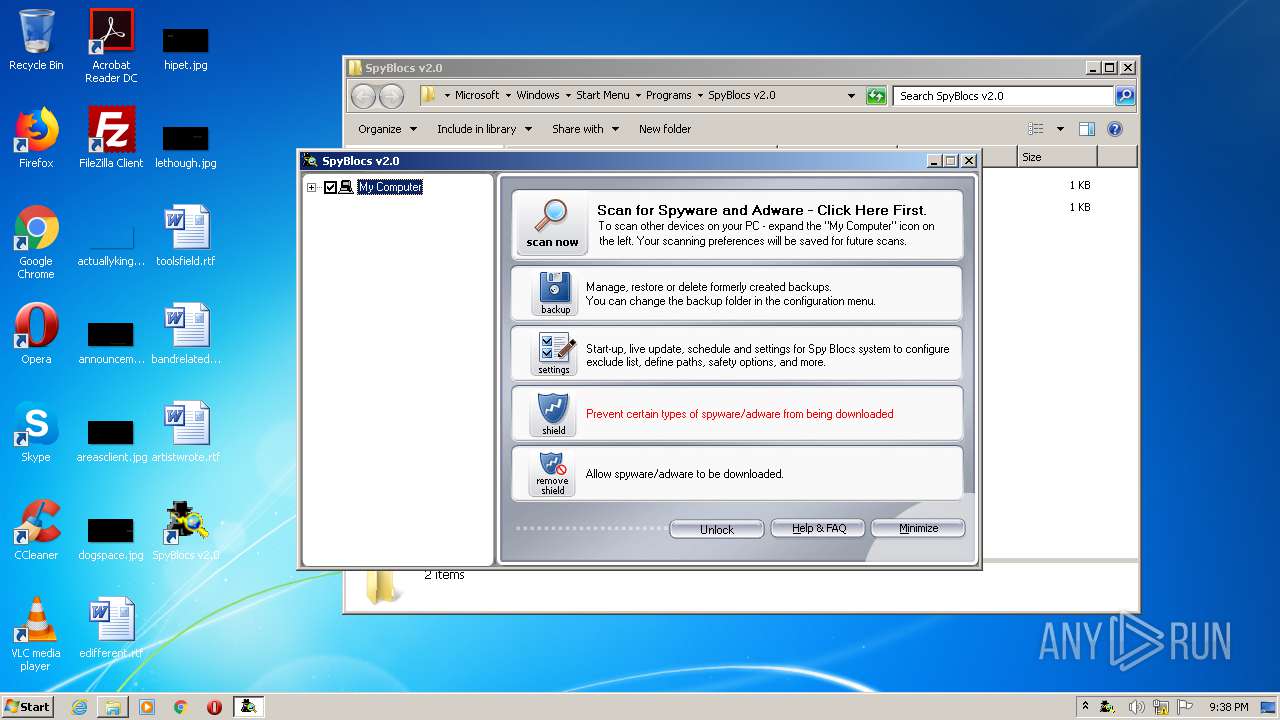
Changes the started page of IE
- SpyBlocs.exe (PID: 2568)
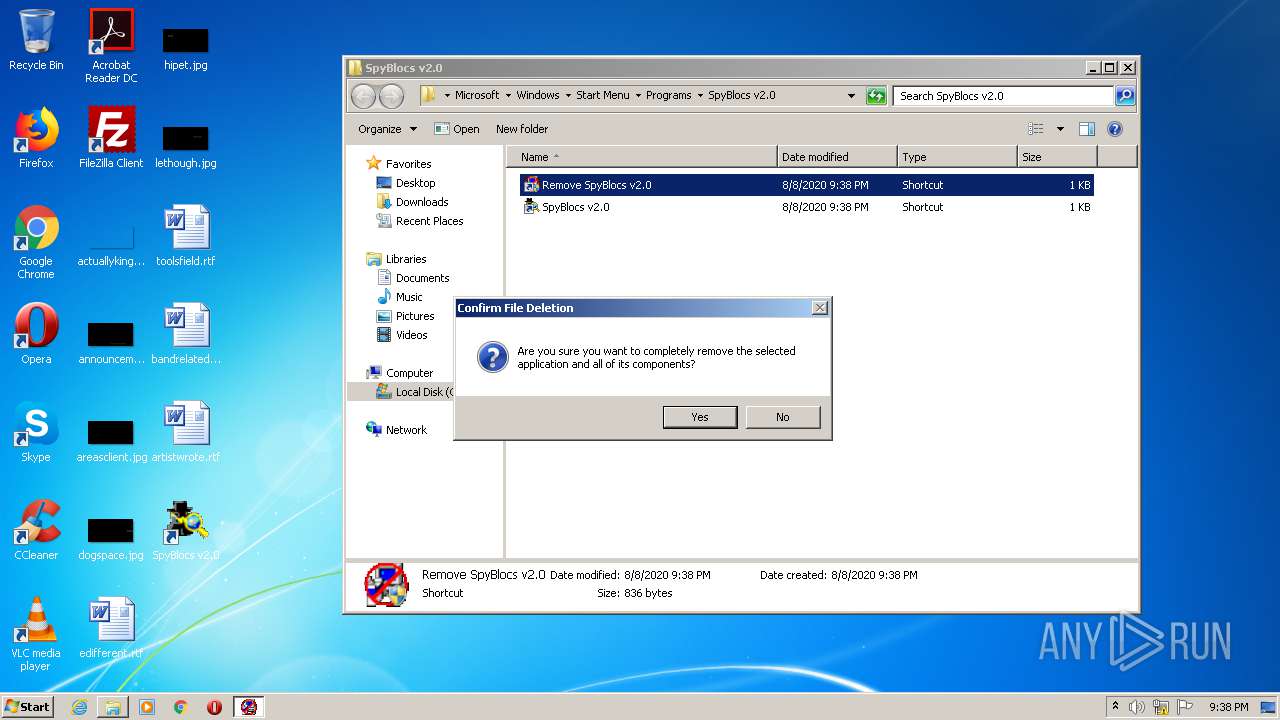
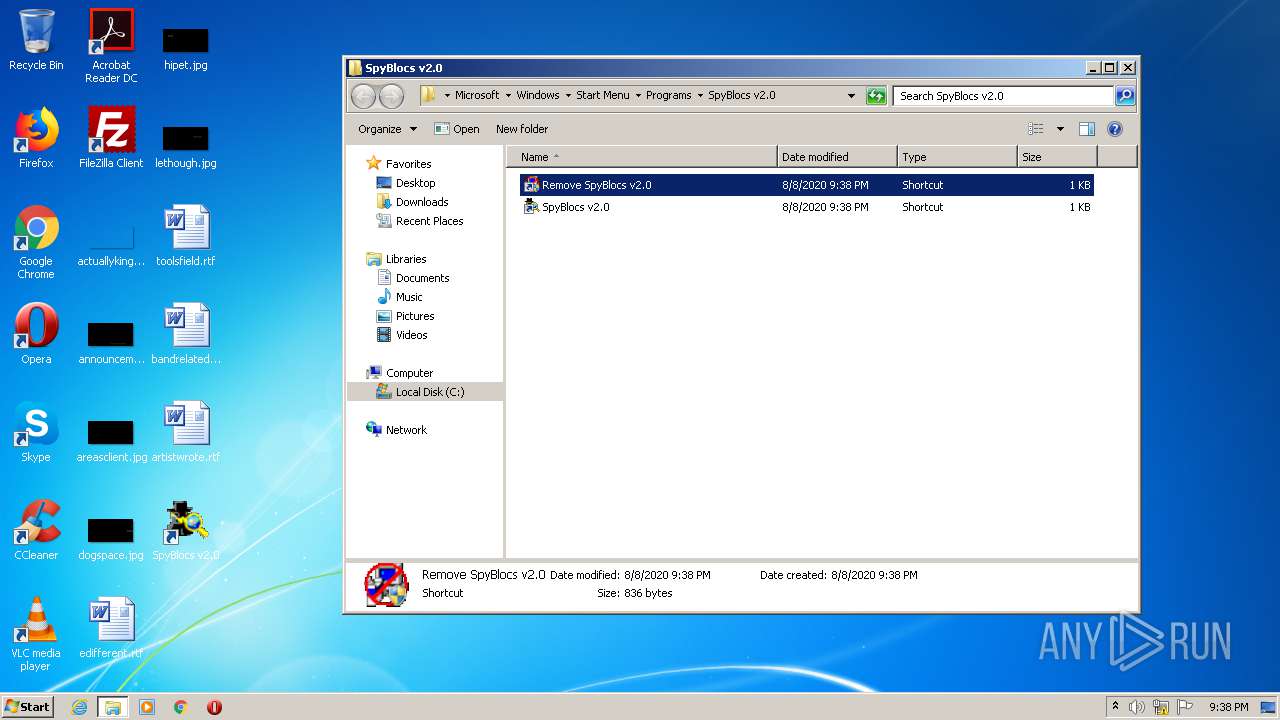
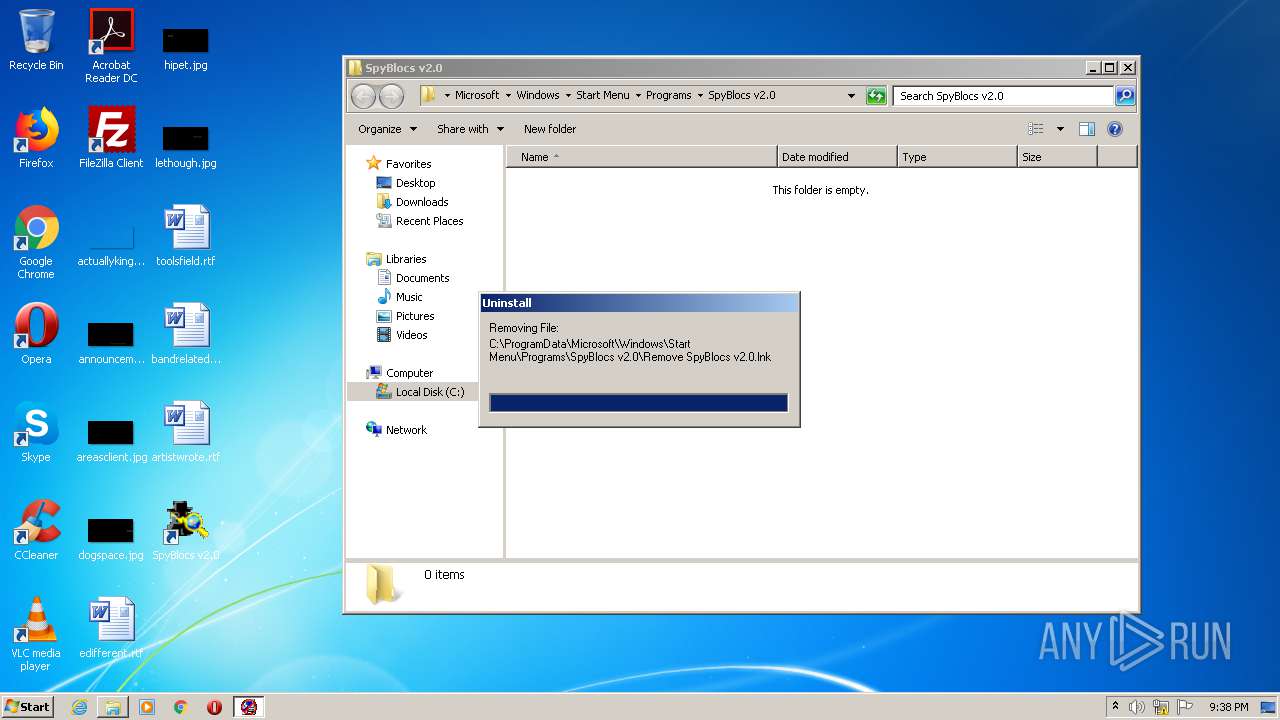
Removes files from Windows directory
- unvise32.exe (PID: 2056)
INFO
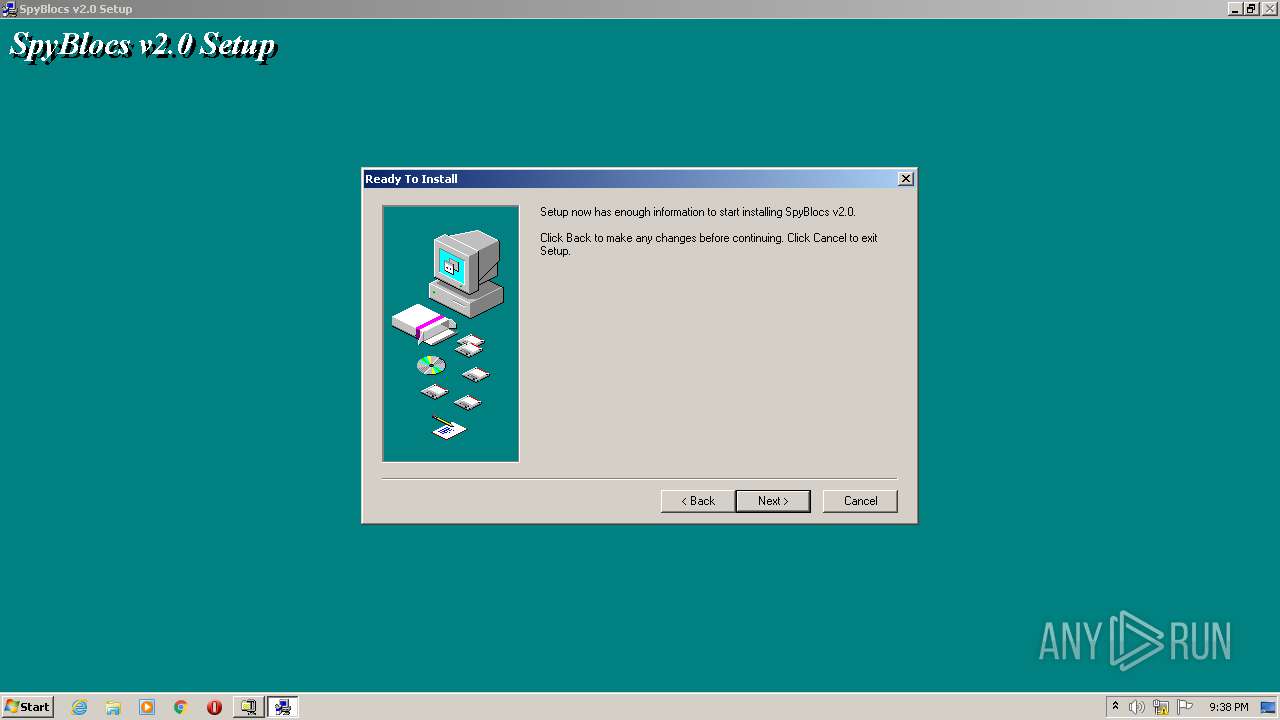
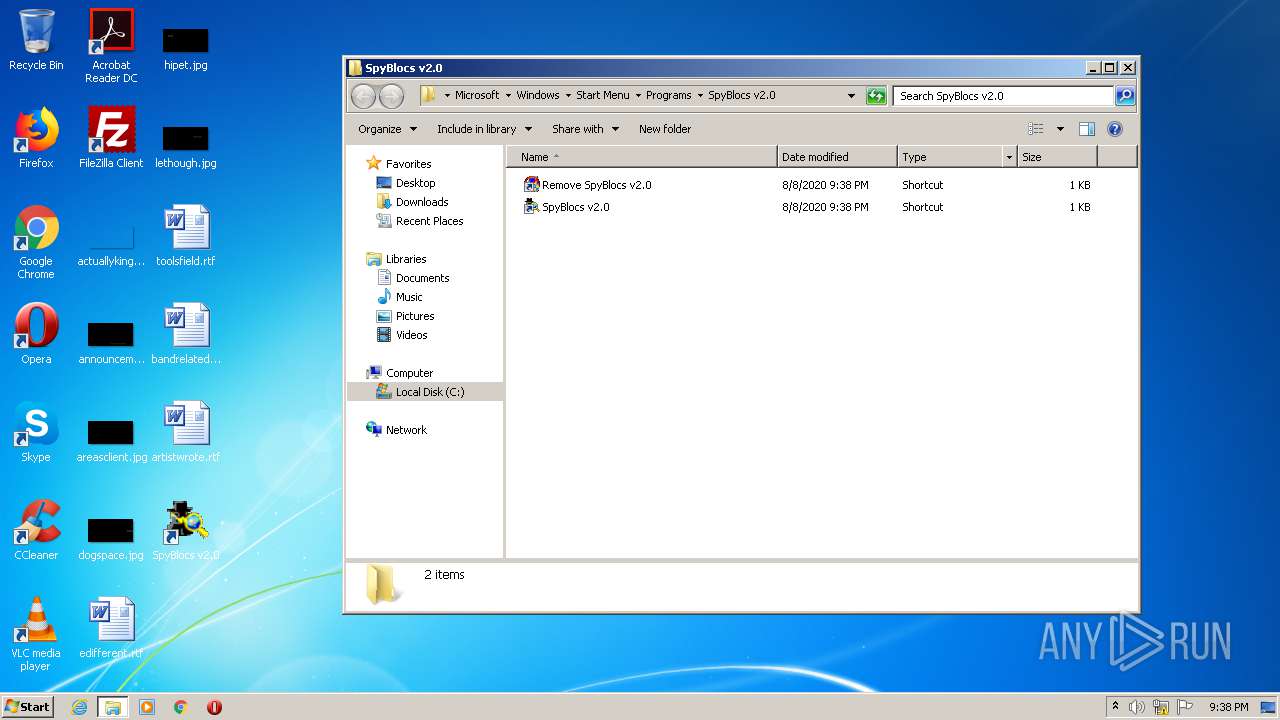
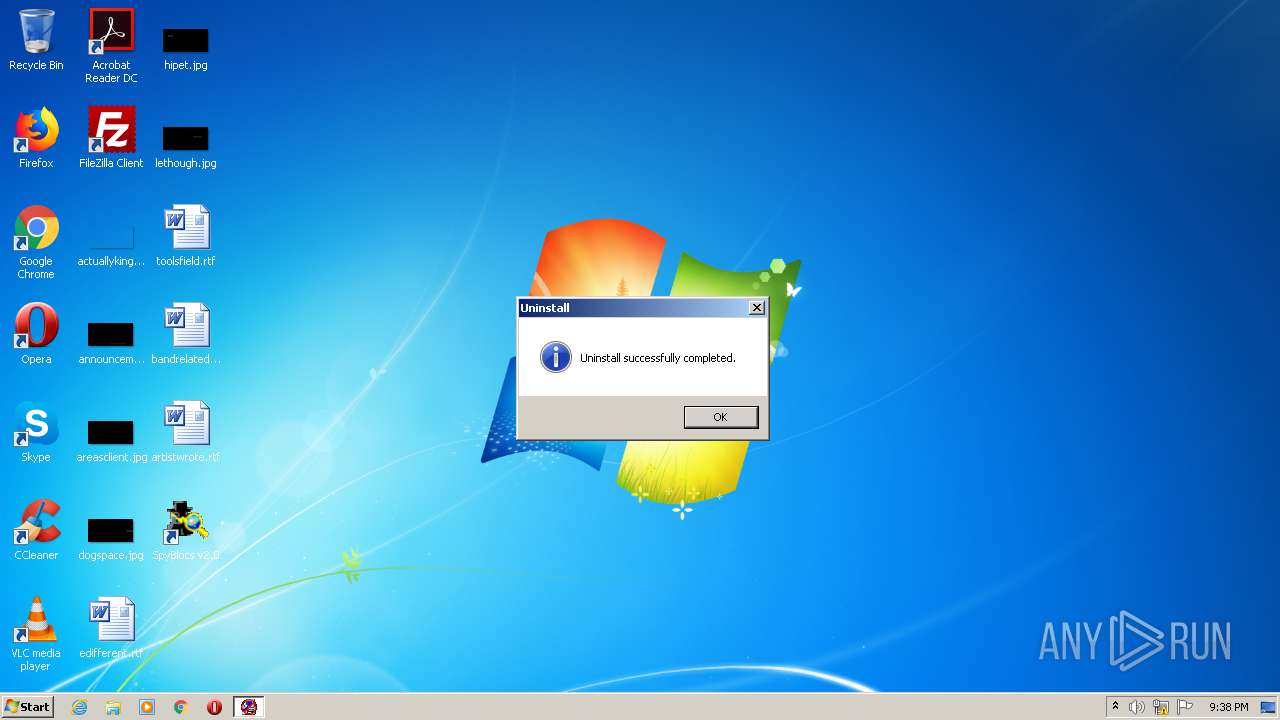
Manual execution by user
- unvise32.exe (PID: 3452)
- unvise32.exe (PID: 2056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (32.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (28.5) |
| .exe | | | Winzip Win32 self-extracting archive (generic) (23.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.7) |
| .exe | | | Win32 Executable (generic) (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2001:01:09 15:09:05+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 5.1 |
| CodeSize: | 22016 |
| InitializedDataSize: | 10752 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3f8f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Jan-2001 14:09:05 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 09-Jan-2001 14:09:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005486 | 0x00005600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45543 |
.rdata | 0x00007000 | 0x00000BD2 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.0843 |
.data | 0x00008000 | 0x00001735 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.88122 |
.rsrc | 0x0000A000 | 0x00000508 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.79764 |
_winzip_ | 0x0000B000 | 0x002B0000 | 0x002AF600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 7.99894 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.37086 | 34 | UNKNOWN | English - United States | RT_GROUP_ICON |
2 | 2.97697 | 296 | UNKNOWN | English - United States | RT_ICON |
Imports
GDI32.dll |
KERNEL32.dll |
USER32.dll |
Total processes
49
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2056 | "C:\Windows\unvise32.exe" C:\PROGRA~1\SpyBlocs\uninstal.log | C:\Windows\unvise32.exe | explorer.exe | ||||||||||||
User: admin Company: MindVision Software Integrity Level: HIGH Description: Uninstall application file Exit code: 0 Version: 3.1.1 Modules
| |||||||||||||||
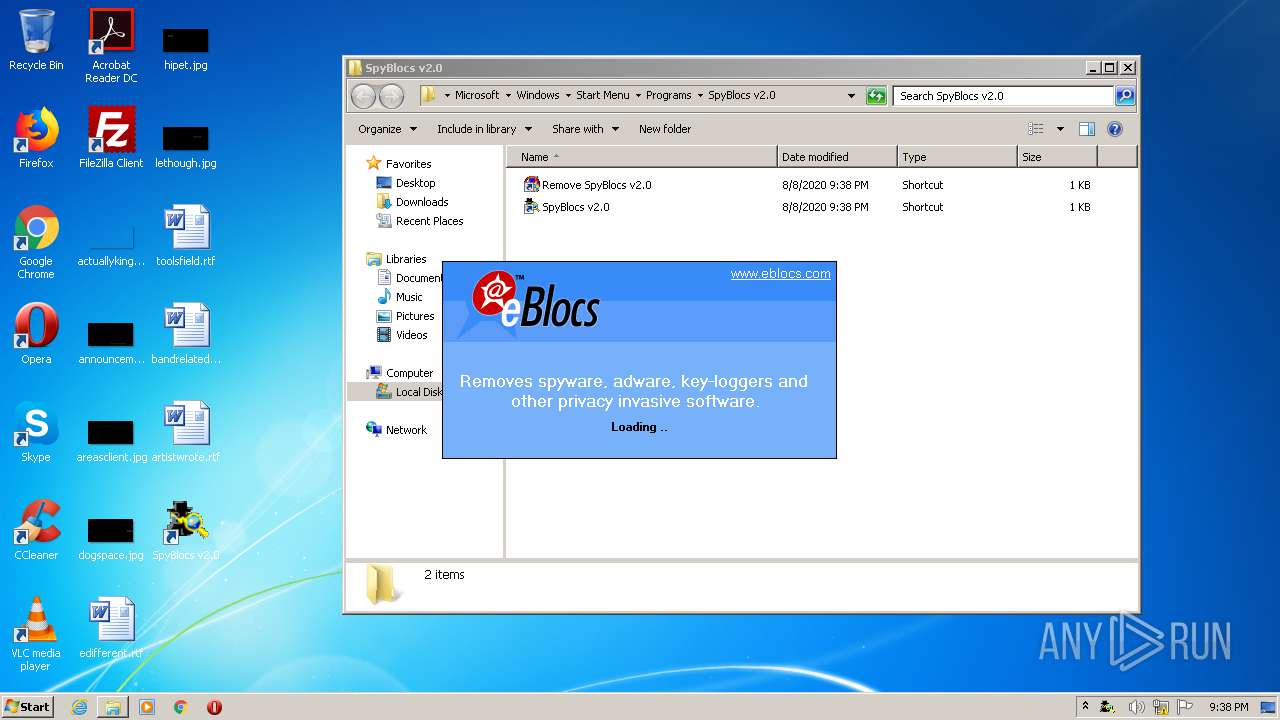
| 2568 | "C:\PROGRA~1\SpyBlocs\SpyBlocs.exe" | C:\PROGRA~1\SpyBlocs\SpyBlocs.exe | spyblocs.exe | ||||||||||||
User: admin Company: www.eblocs.com Integrity Level: HIGH Exit code: 0 Version: 2.00 Modules
| |||||||||||||||
| 2764 | "C:\Users\admin\AppData\Local\Temp\spyblocs.exe" | C:\Users\admin\AppData\Local\Temp\spyblocs.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2792 | .\spyblocs.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\spyblocs.exe | spyblocs.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3452 | "C:\Windows\unvise32.exe" C:\PROGRA~1\SpyBlocs\uninstal.log | C:\Windows\unvise32.exe | — | explorer.exe | |||||||||||
User: admin Company: MindVision Software Integrity Level: MEDIUM Description: Uninstall application file Exit code: 3221226540 Version: 3.1.1 Modules
| |||||||||||||||
| 3652 | "C:\Users\admin\AppData\Local\Temp\spyblocs.exe" | C:\Users\admin\AppData\Local\Temp\spyblocs.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
4 043
Read events
1 467
Write events
2 218
Delete events
358
Modification events
| (PID) Process: | (2792) spyblocs.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2792) spyblocs.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 010000000B0000000000000002000000070000000A000000090000000800000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (2792) spyblocs.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0 |
| Operation: | write | Name: | MRUListEx |
Value: 0400000000000000010000000200000003000000FFFFFFFF | |||
| (PID) Process: | (2792) spyblocs.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\4 |
| Operation: | write | Name: | MRUListEx |
Value: 000000000200000001000000FFFFFFFF | |||
| (PID) Process: | (2792) spyblocs.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\4\0\0\0\0 |
| Operation: | write | Name: | 1 |
Value: 6400310000000000000000001000537079426C6F63732076322E3000480008000400EFBE00000000000000002A0000000000000000000000000000000000000000000000000053007000790042006C006F00630073002000760032002E00300000001C000000 | |||
| (PID) Process: | (2792) spyblocs.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\4\0\0\0\0 |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000FFFFFFFF | |||
| (PID) Process: | (2792) spyblocs.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (2792) spyblocs.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\4\0\0\0\0\1 |
| Operation: | write | Name: | NodeSlot |
Value: 120 | |||
| (PID) Process: | (2792) spyblocs.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\4\0\0\0\0\1 |
| Operation: | write | Name: | MRUListEx |
Value: FFFFFFFF | |||
| (PID) Process: | (2792) spyblocs.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\120\Shell |
| Operation: | write | Name: | KnownFolderDerivedFolderType |
Value: {57807898-8C4F-4462-BB63-71042380B109} | |||
Executable files
11
Suspicious files
2
Text files
118
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2792 | spyblocs.exe | C:\Users\admin\AppData\Local\Temp\~vis0000\miscdata.xyz | — | |
MD5:— | SHA256:— | |||
| 3652 | spyblocs.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\sb_affiliate.ini | text | |
MD5:— | SHA256:— | |||
| 2792 | spyblocs.exe | C:\Users\admin\AppData\Local\Temp\~vis0000\uninstal.log | text | |
MD5:— | SHA256:— | |||
| 3652 | spyblocs.exe | C:\Users\admin\AppData\Local\Temp\WZSE0.TMP\spyblocs.exe | executable | |
MD5:— | SHA256:— | |||
| 2792 | spyblocs.exe | C:\Users\admin\AppData\Local\Temp\~vis0000\rollback.log | text | |
MD5:— | SHA256:— | |||
| 2792 | spyblocs.exe | C:\Program Files\SpyBlocs\RegistrySpylist | text | |
MD5:— | SHA256:— | |||
| 2792 | spyblocs.exe | C:\Program Files\SpyBlocs\spyList | text | |
MD5:— | SHA256:— | |||
| 2792 | spyblocs.exe | C:\Users\admin\AppData\Local\Temp\~vis0000\rebootnt.exe | executable | |
MD5:C459E252866435ED8B928D1509C28DE2 | SHA256:4887FF02F8E45F5E03E351CB5156111659CC1B04FDCA9DAE3BD75CB99381DEDE | |||
| 2792 | spyblocs.exe | C:\Users\admin\AppData\Local\Temp\~vis0000\default.bmp | image | |
MD5:F372B11FF99BFFED4CD279C0155ADEDE | SHA256:D9D5E28EB445E7986BDEF4D409868AF205D525F2F0729427DFE3E33A7251B15D | |||
| 2792 | spyblocs.exe | C:\Users\admin\AppData\Local\Temp\~vis0000\English.vlg | text | |
MD5:707E3B6418526ED6729DEB4A1307F1F2 | SHA256:75081F741B450B8049D3A0106121516745BBA675681FB490E78B7978238258D5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report