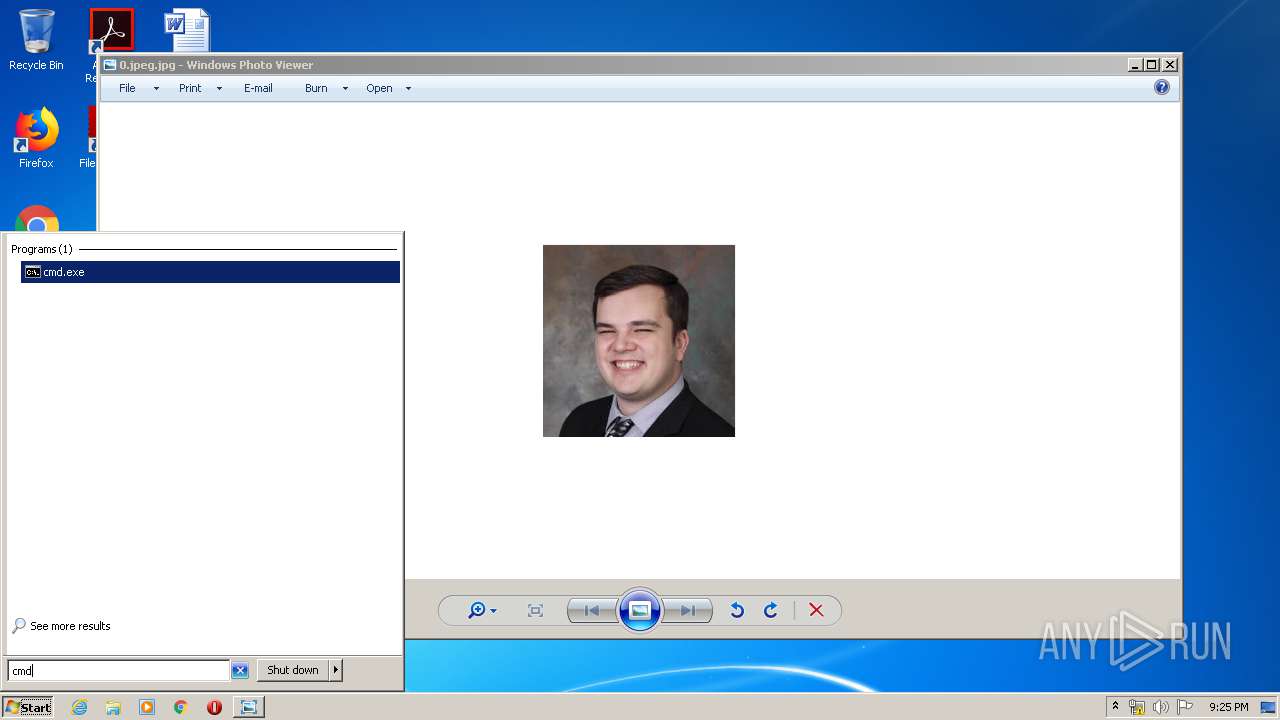
| File name: | 0.jpeg |
| Full analysis: | https://app.any.run/tasks/d47b4466-a38a-4045-8a20-5a4eceaadd63 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 20:21:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | image/jpeg |
| File info: | JPEG image data, JFIF standard 1.01, aspect ratio, density 1x1, segment length 16, baseline, precision 8, 193x193, frames 3 |
| MD5: | E36A2CB45C8544CB690F3A19A5B56B9B |
| SHA1: | 370D5A3ED2A64DCD83C6AF1215FCFCAE33EDC20E |
| SHA256: | FEB3B34430D1920F34911A9DE45BCB0651CBFD8367BD32E6752CF34ACF05BAEC |
| SSDEEP: | 192:7MfBV9lfbaqmG0D6AvQ4DddJ31HFEGcoHuULKb7jju3F:QfBzlfLmhms7J315rOULy7vu1 |
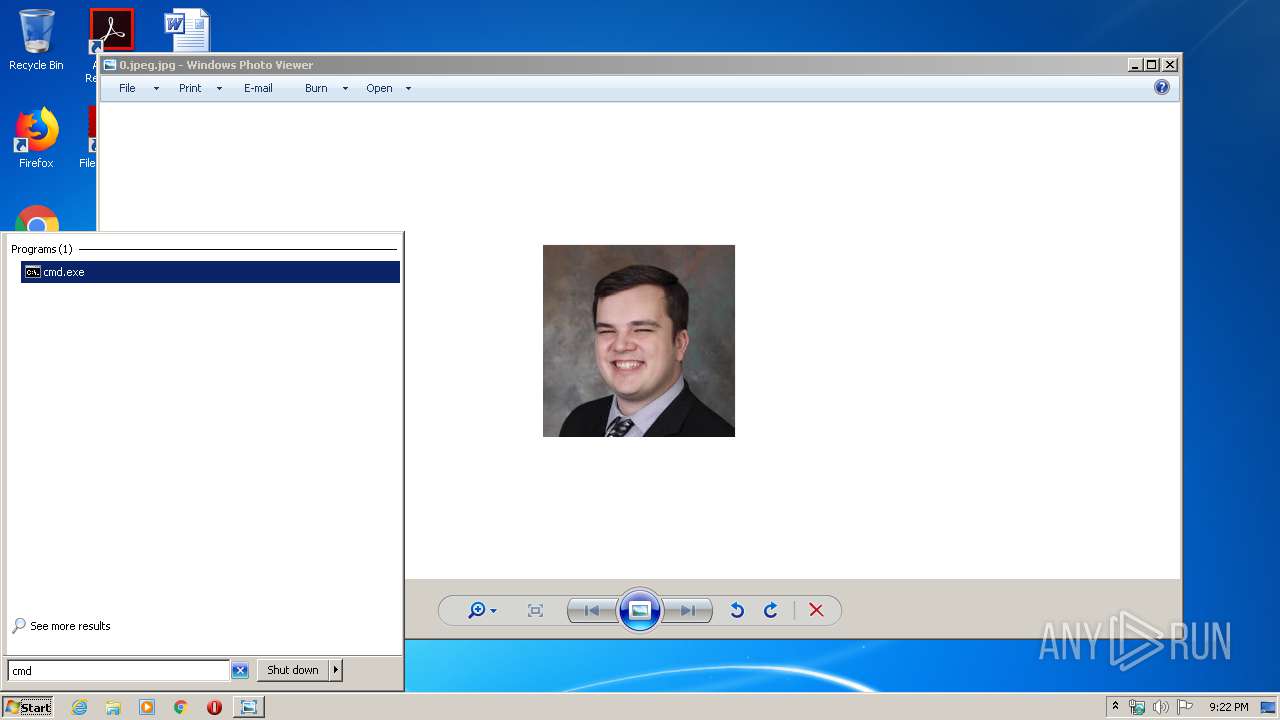
MALICIOUS
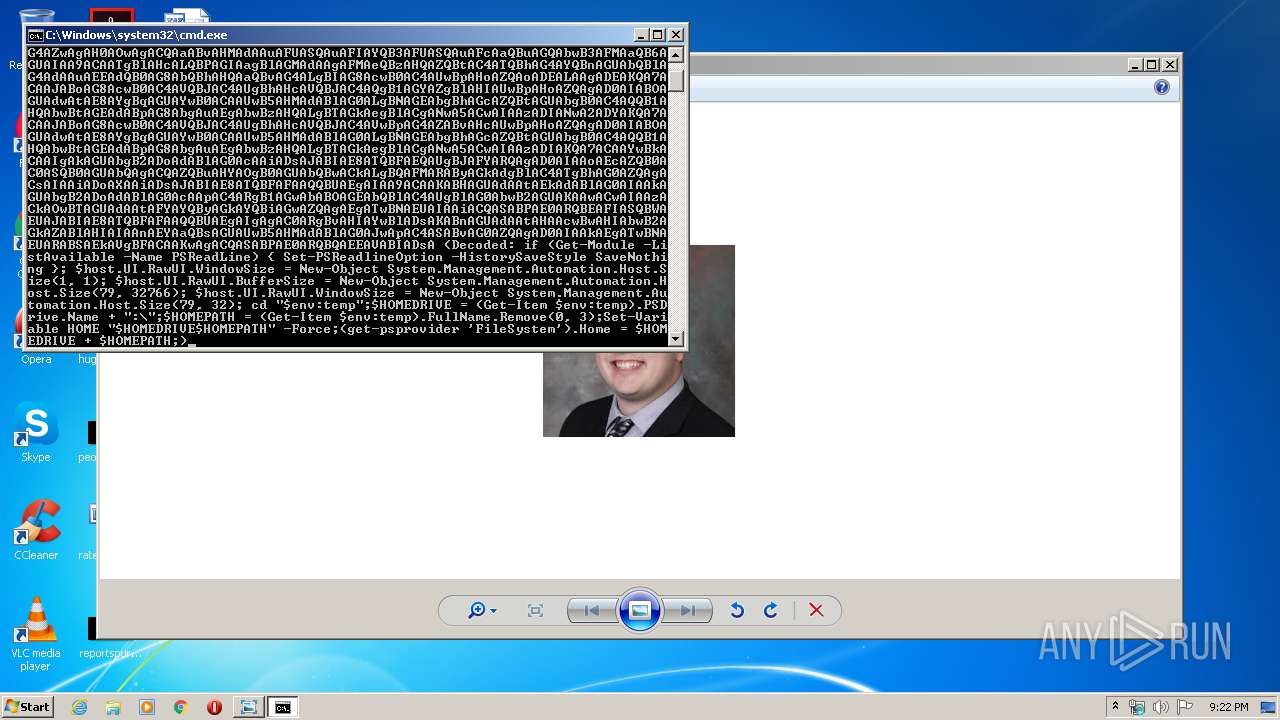
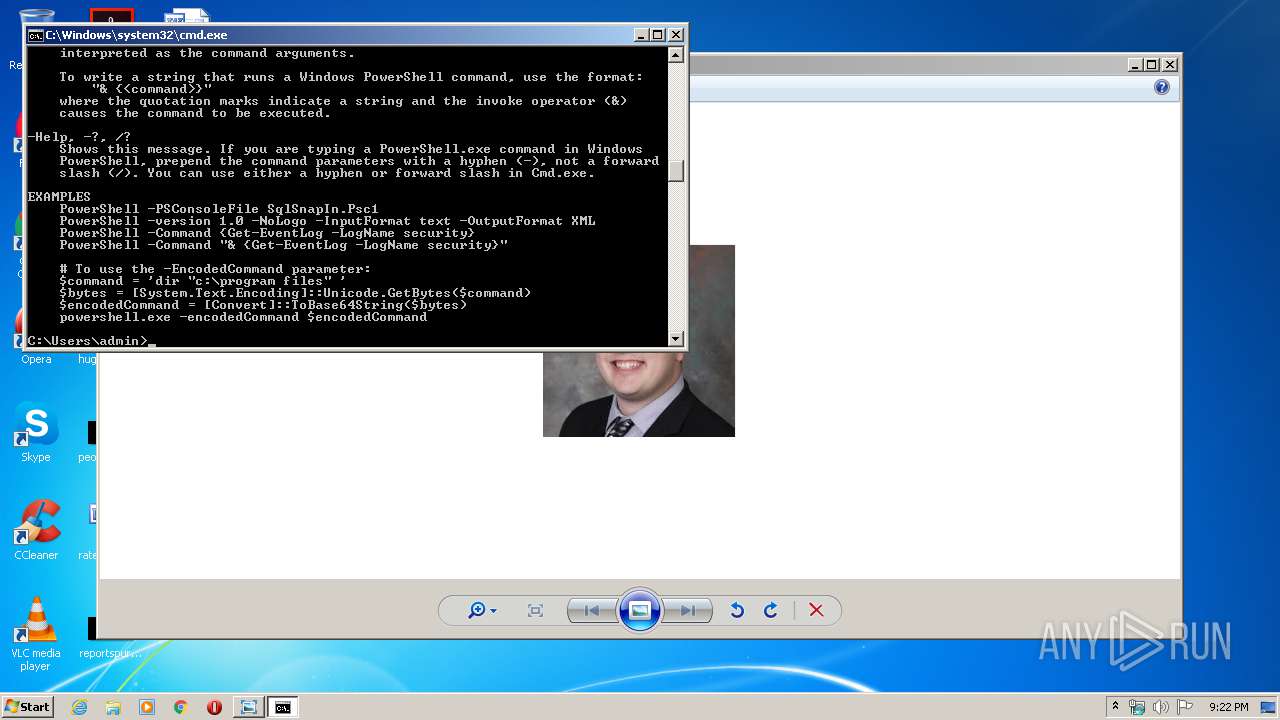
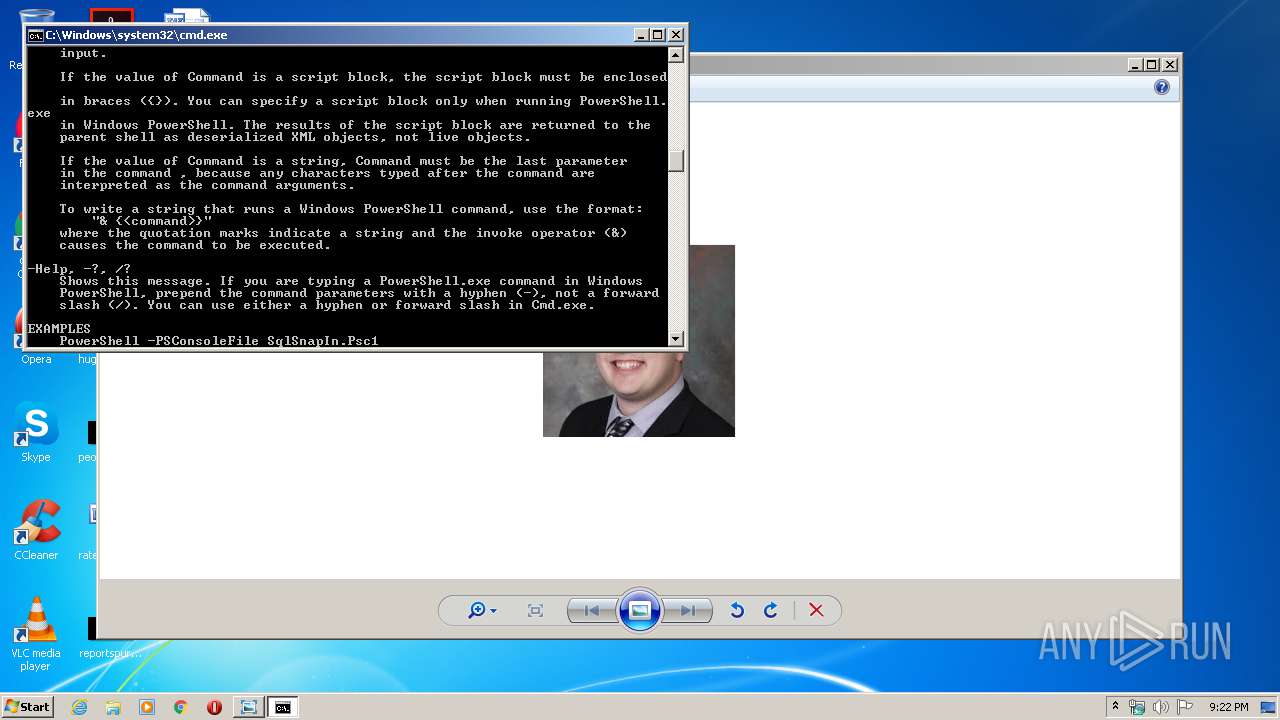
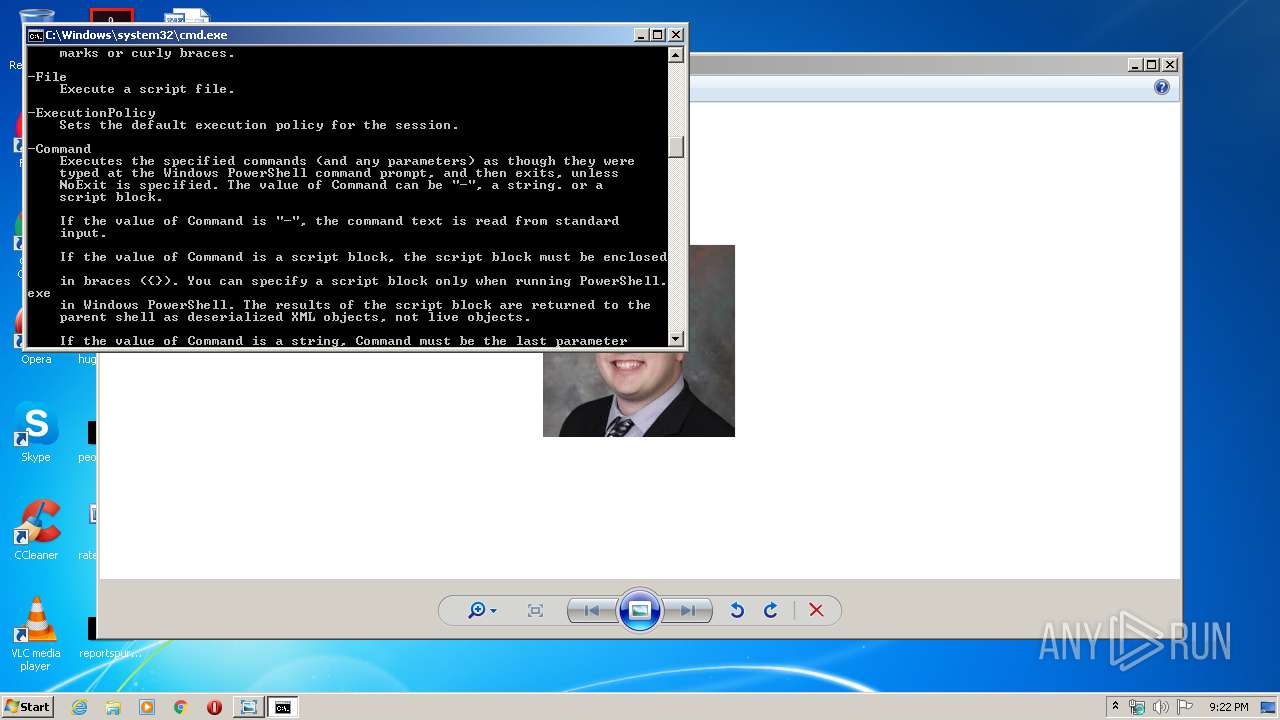
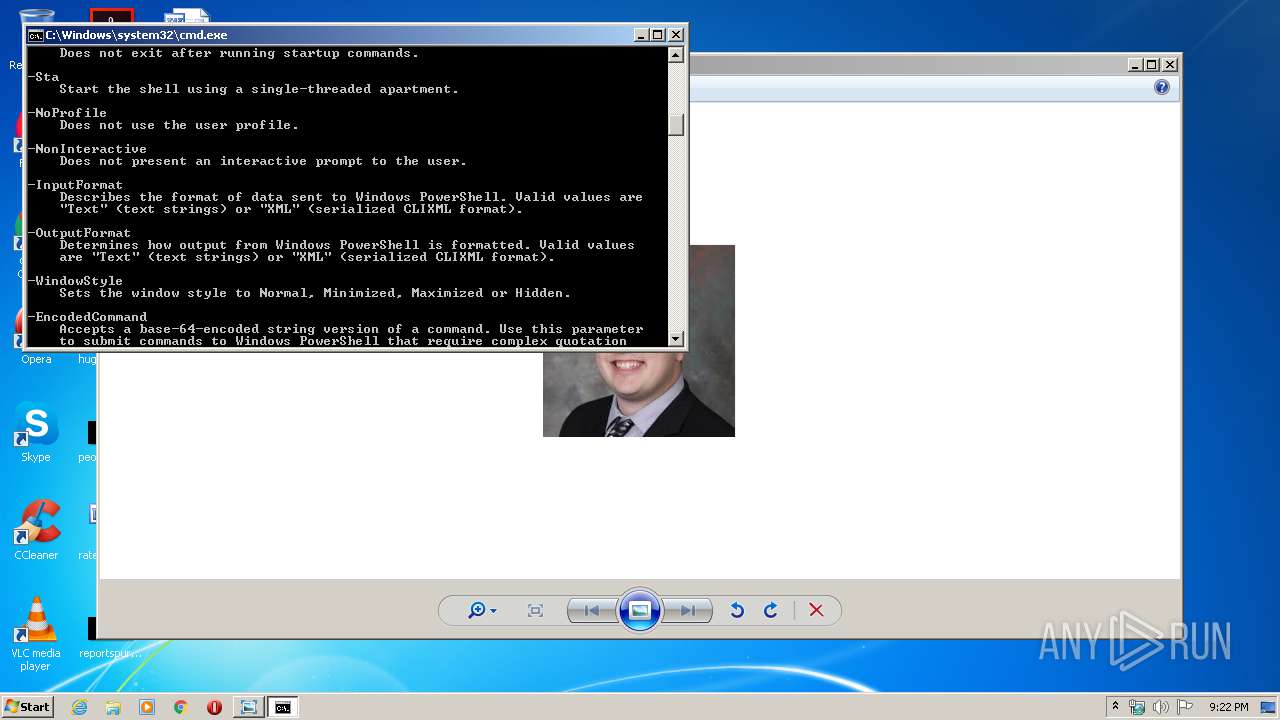
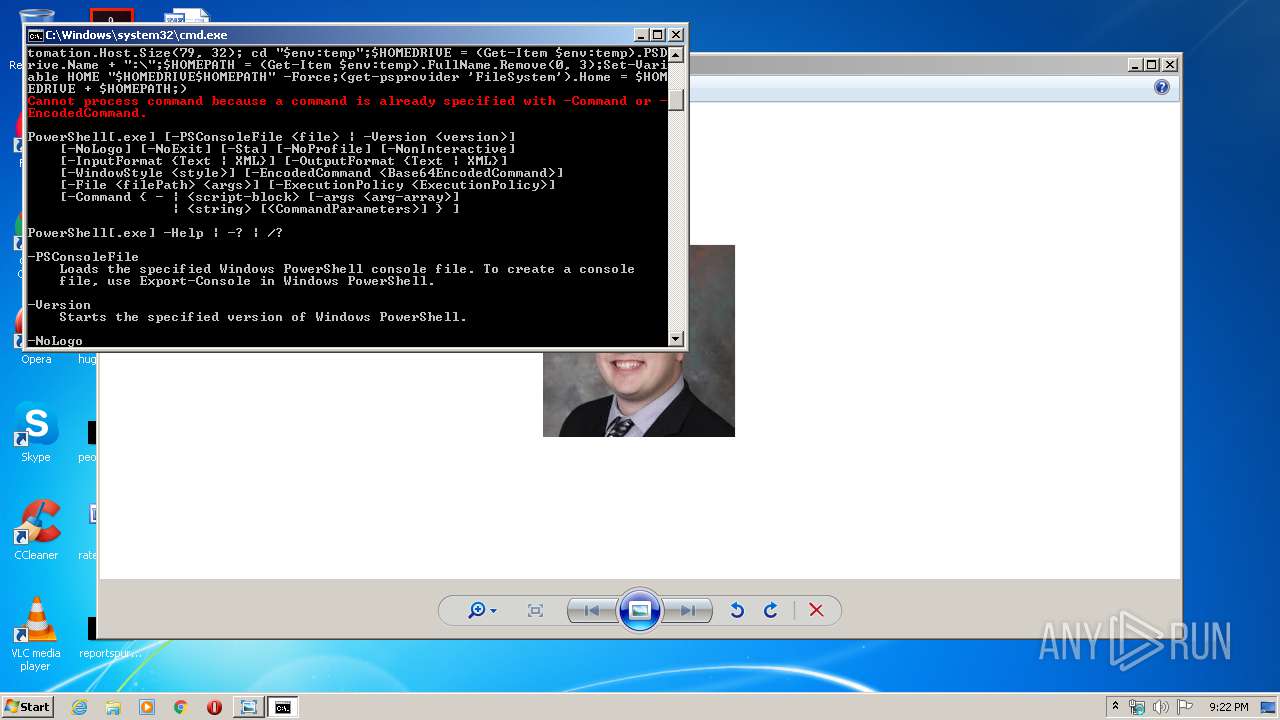
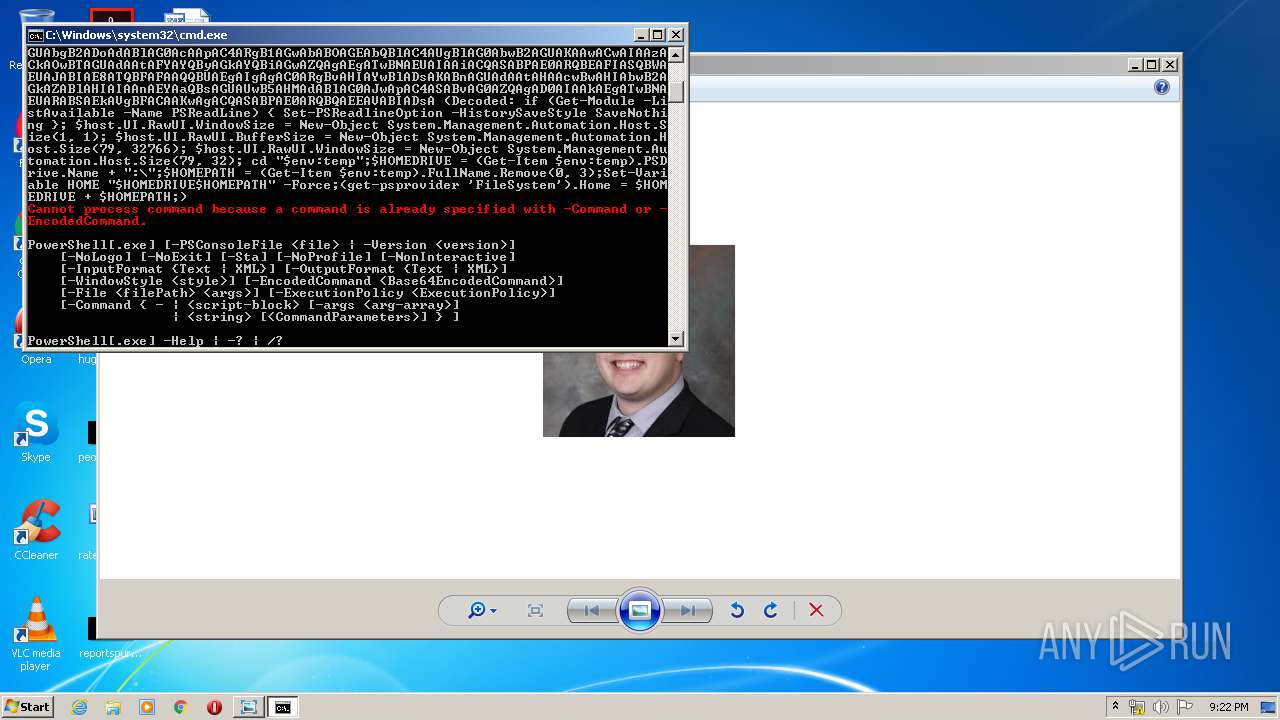
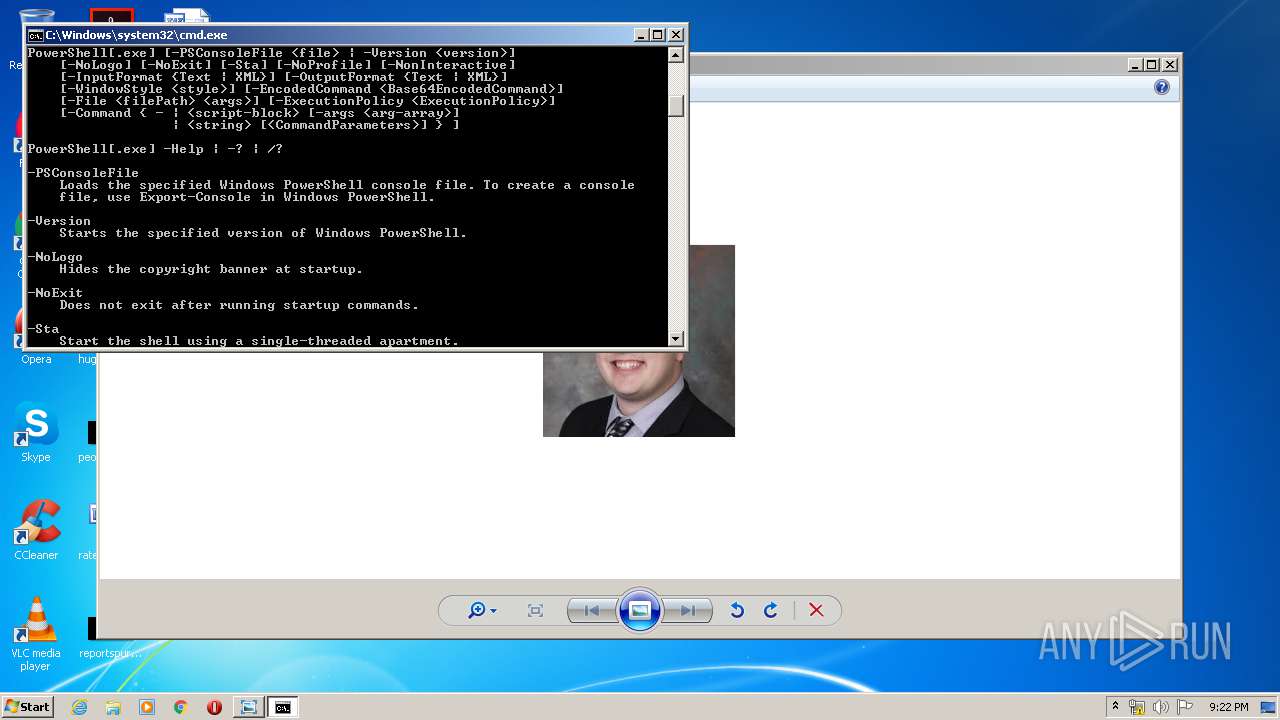
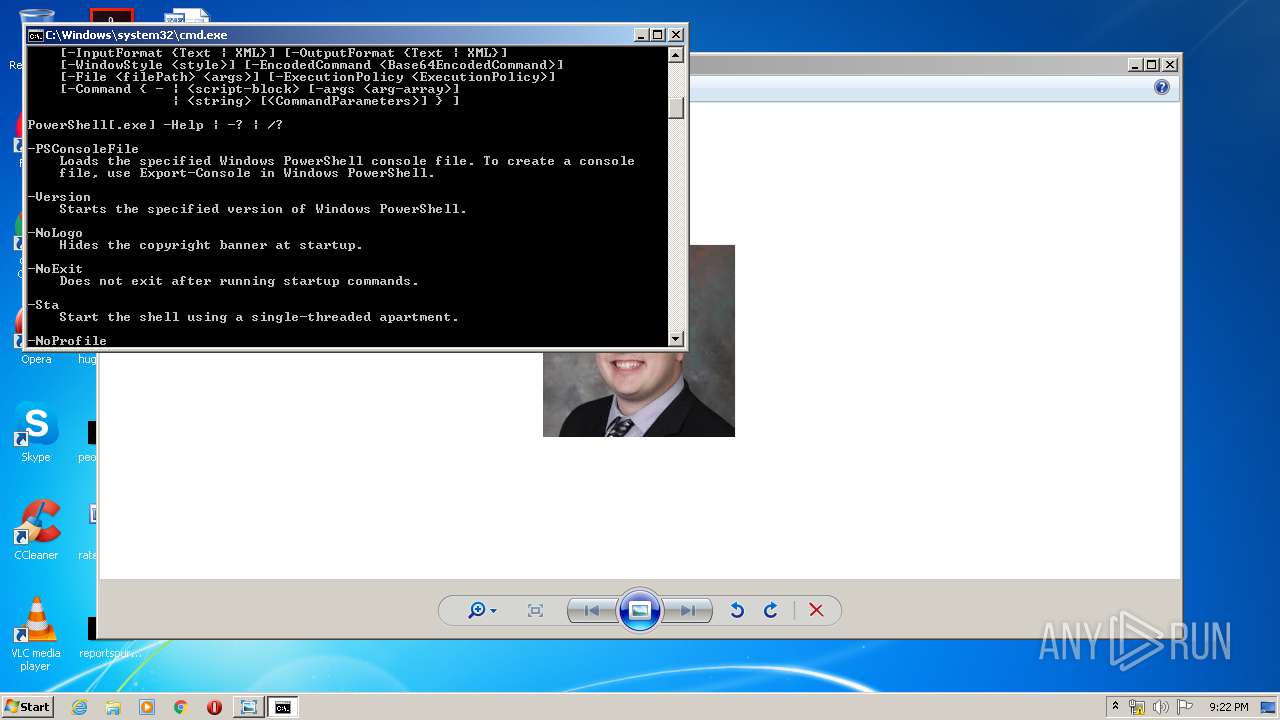
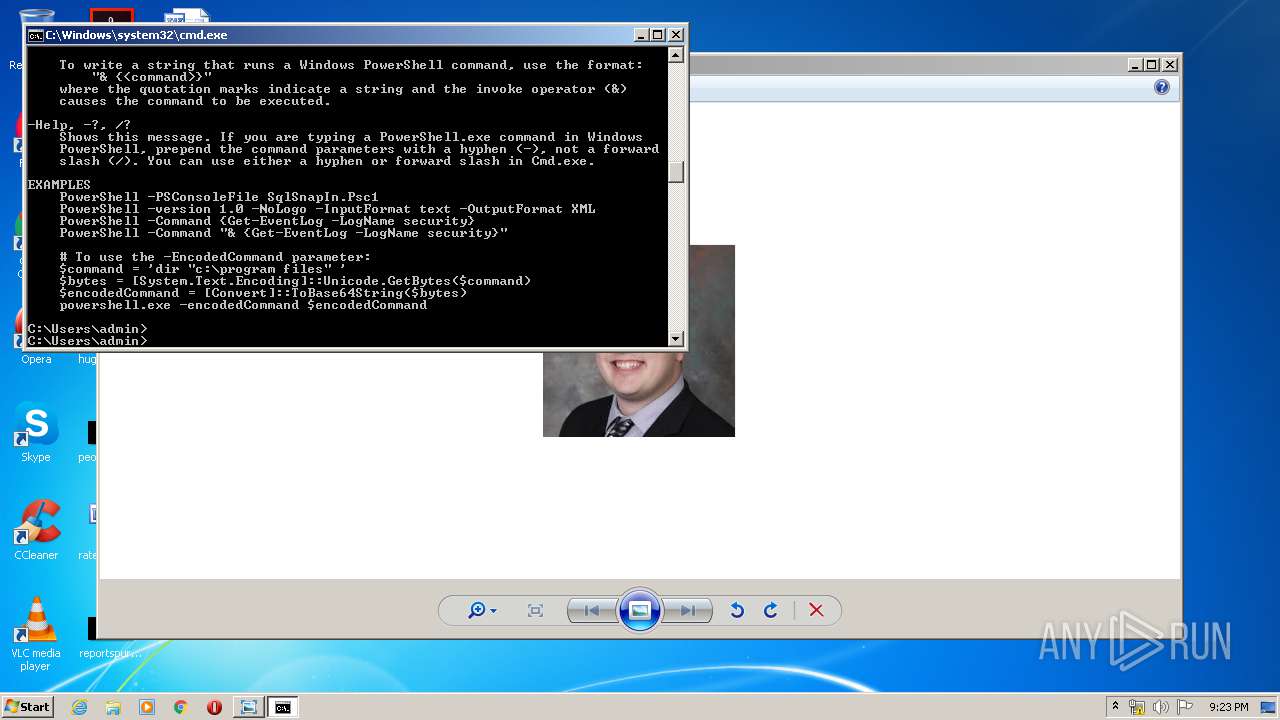
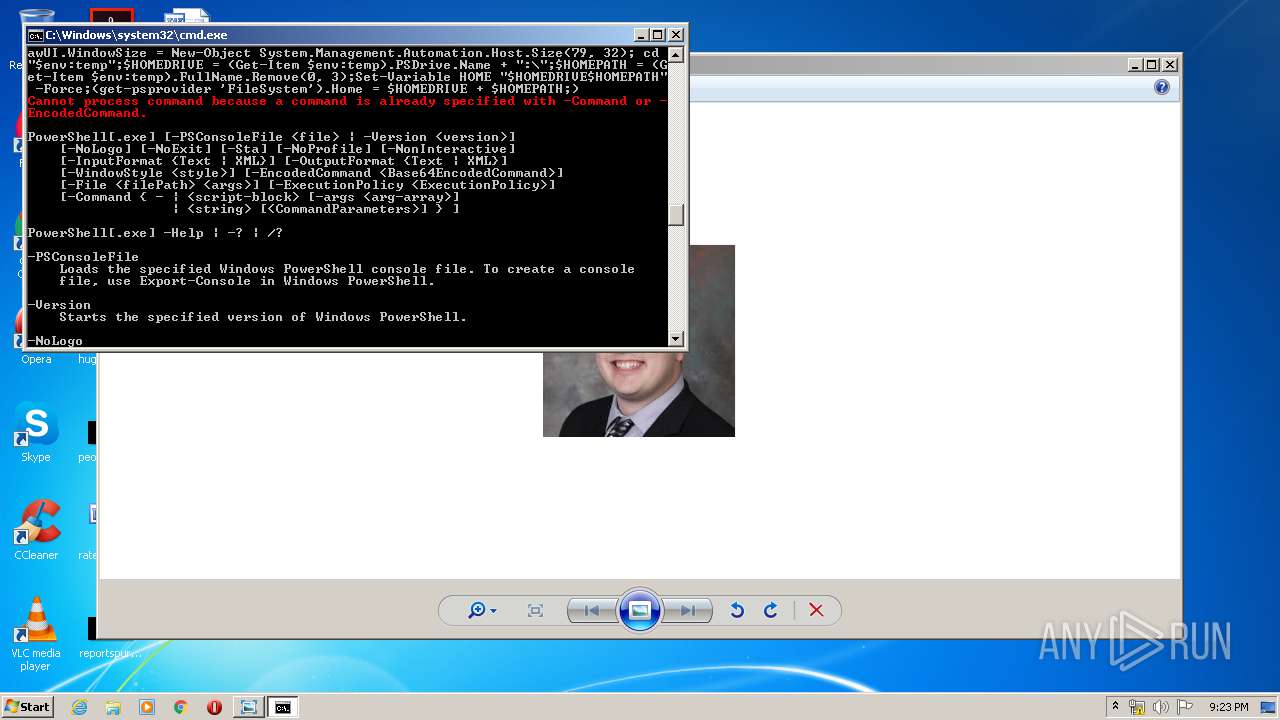
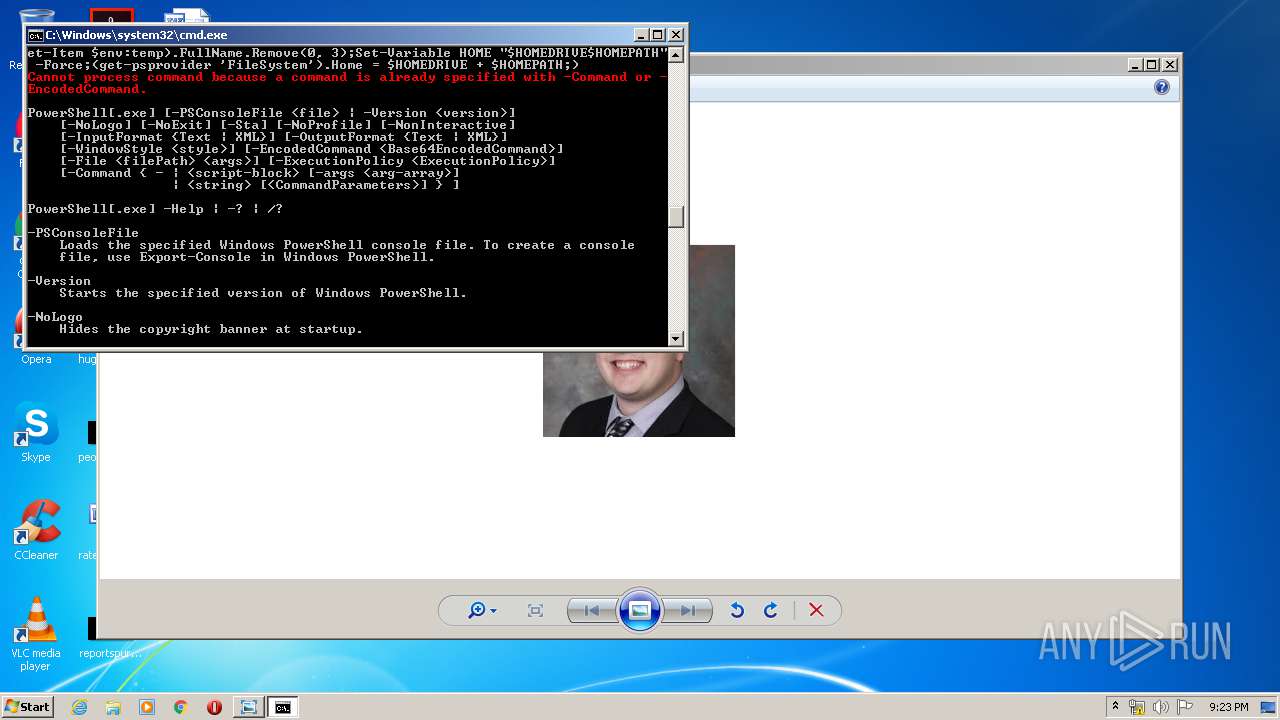
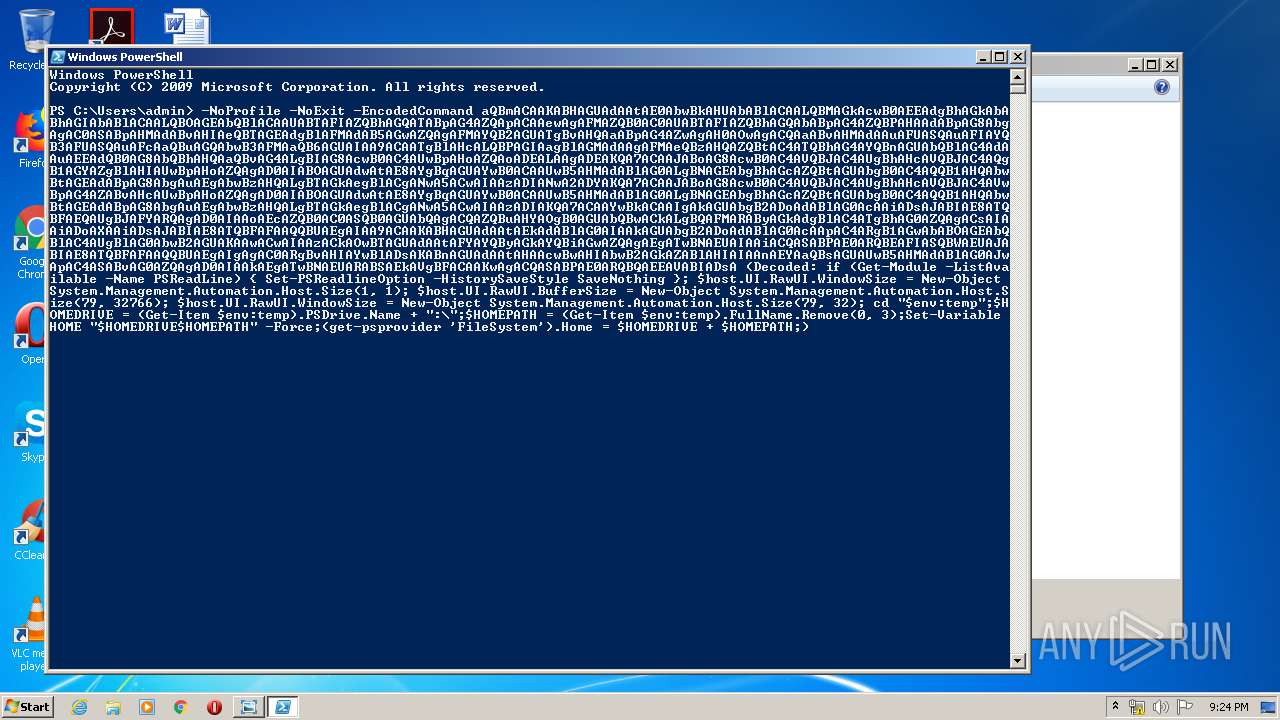
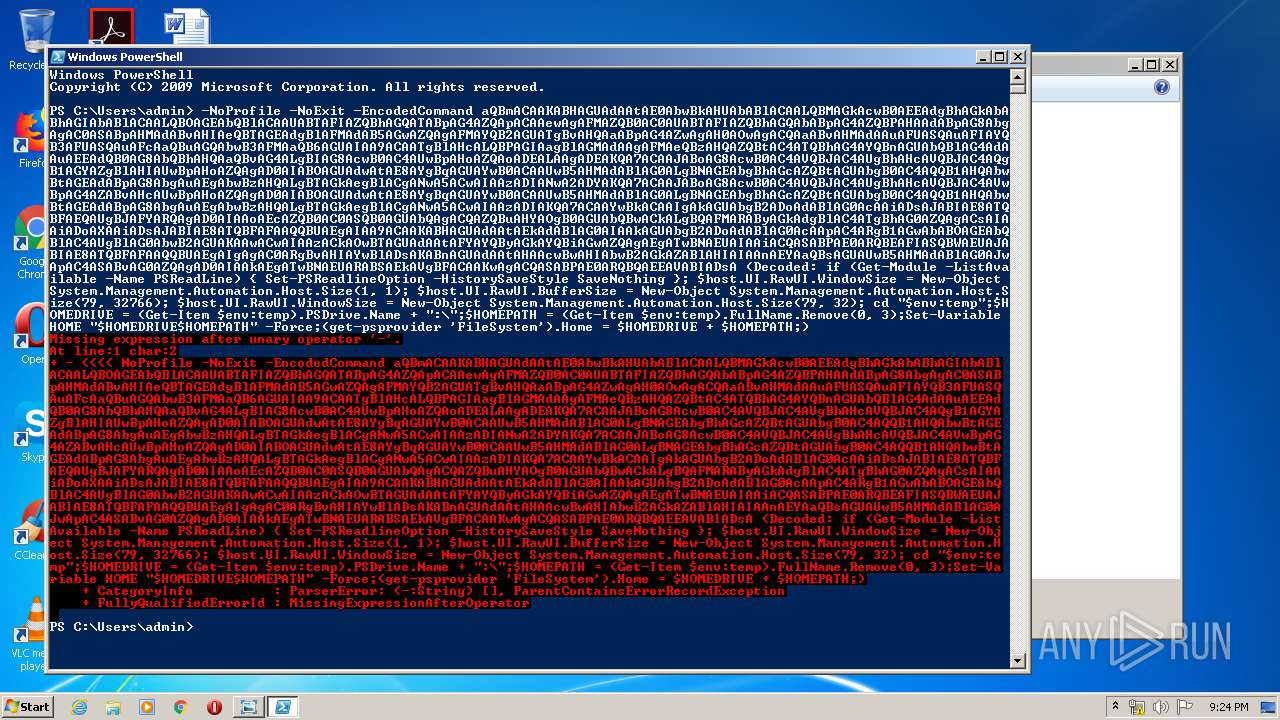
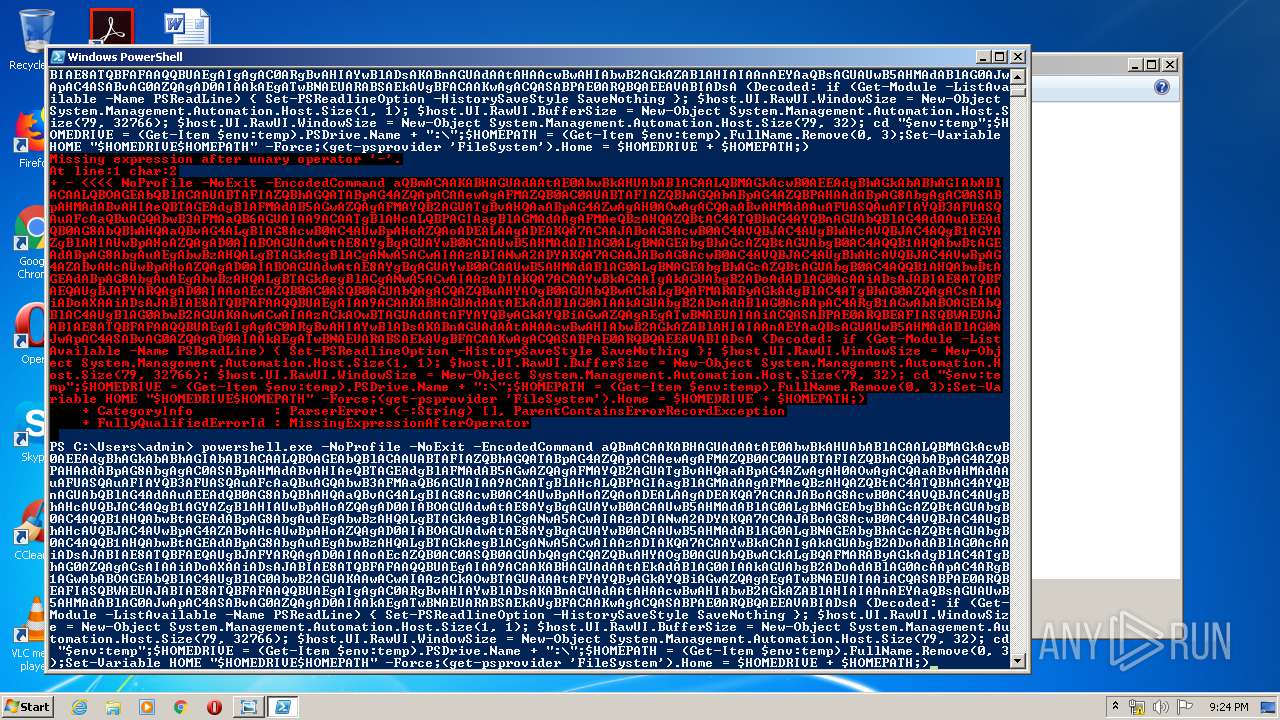
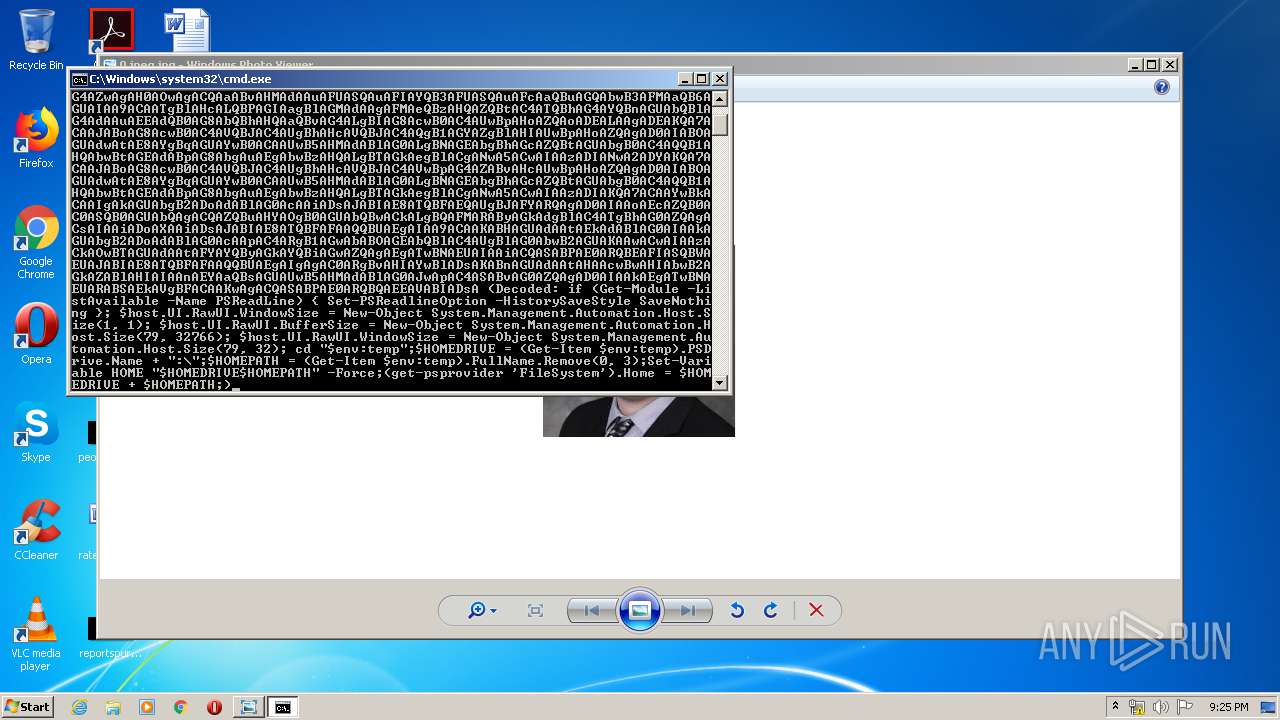
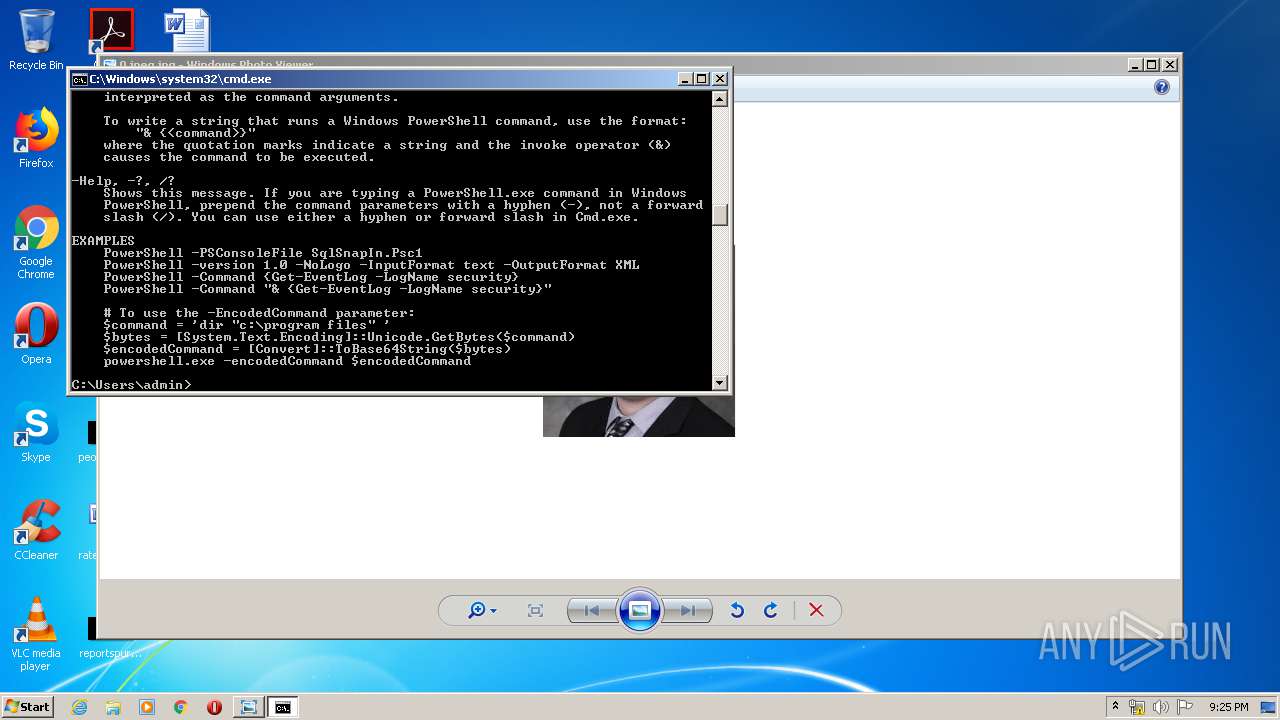
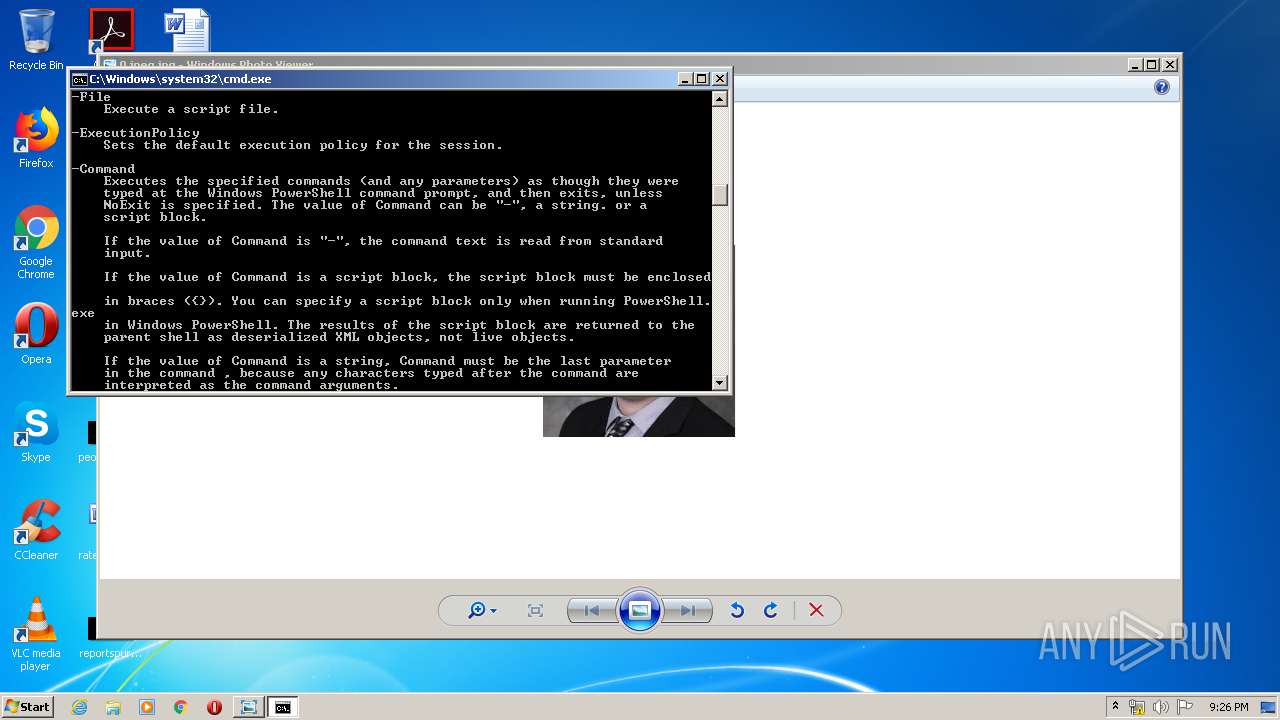
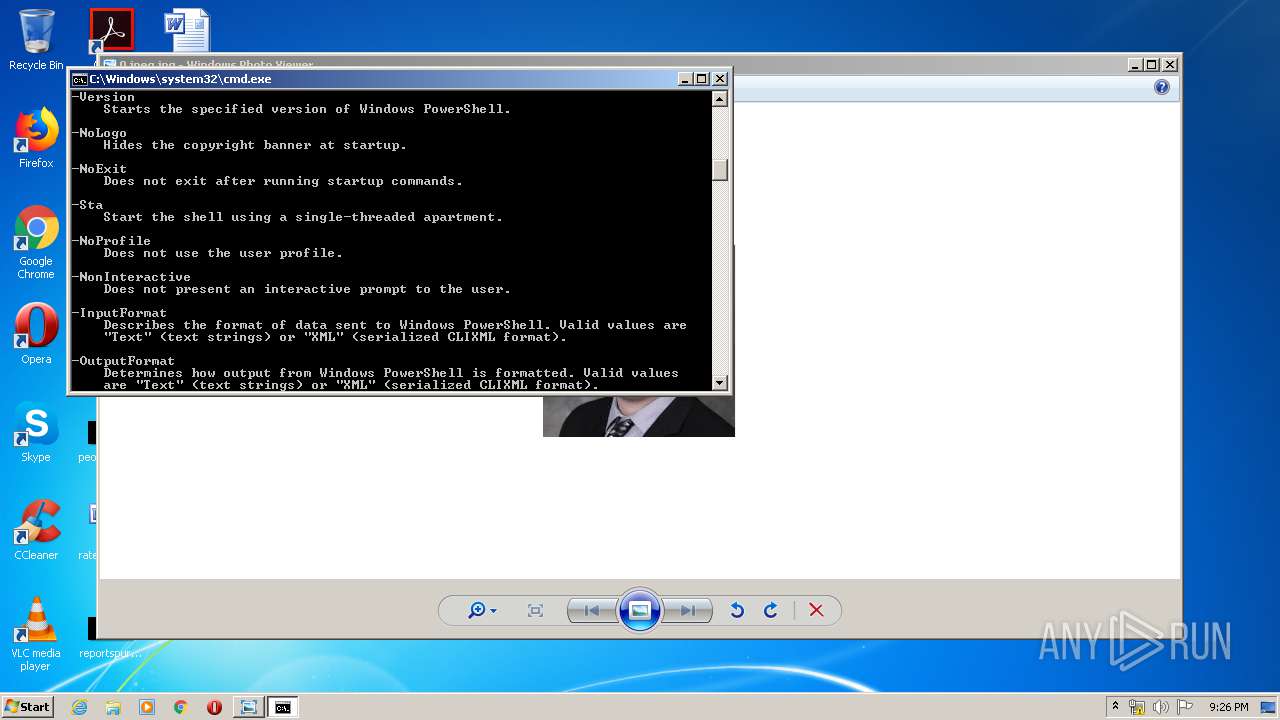
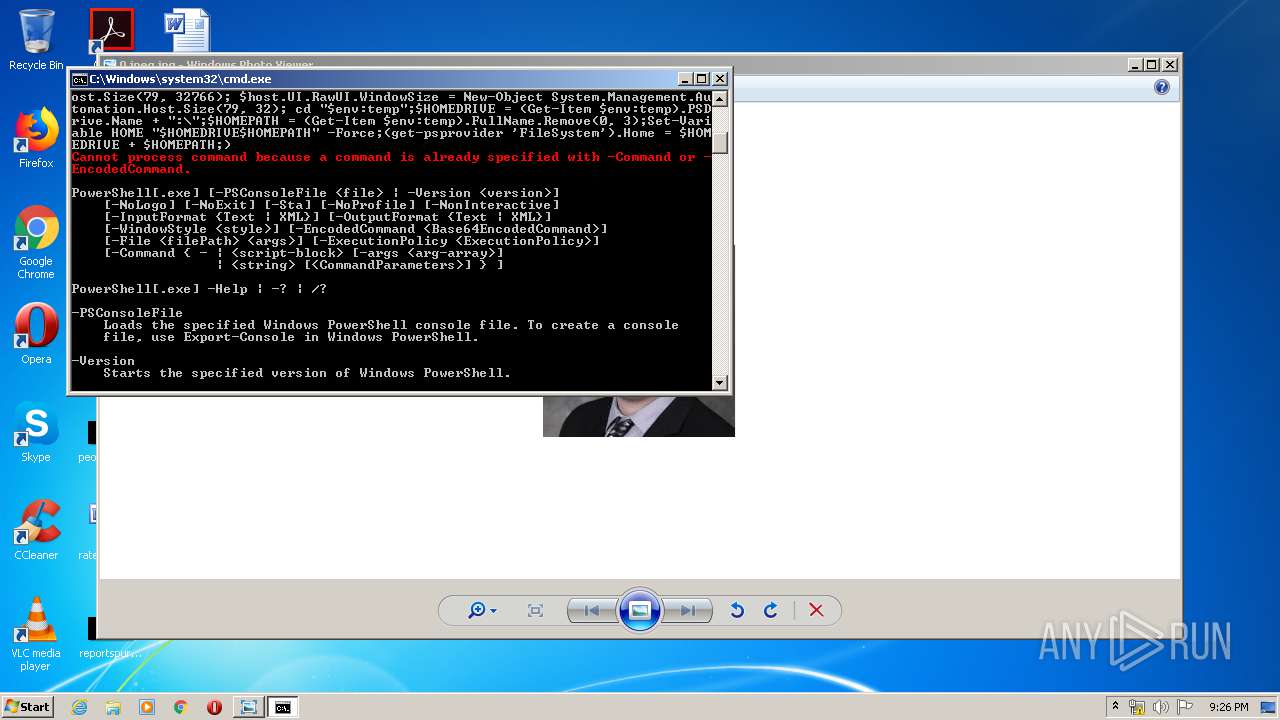
Executes PowerShell scripts
- cmd.exe (PID: 3684)
- cmd.exe (PID: 3464)
- cmd.exe (PID: 2932)
SUSPICIOUS
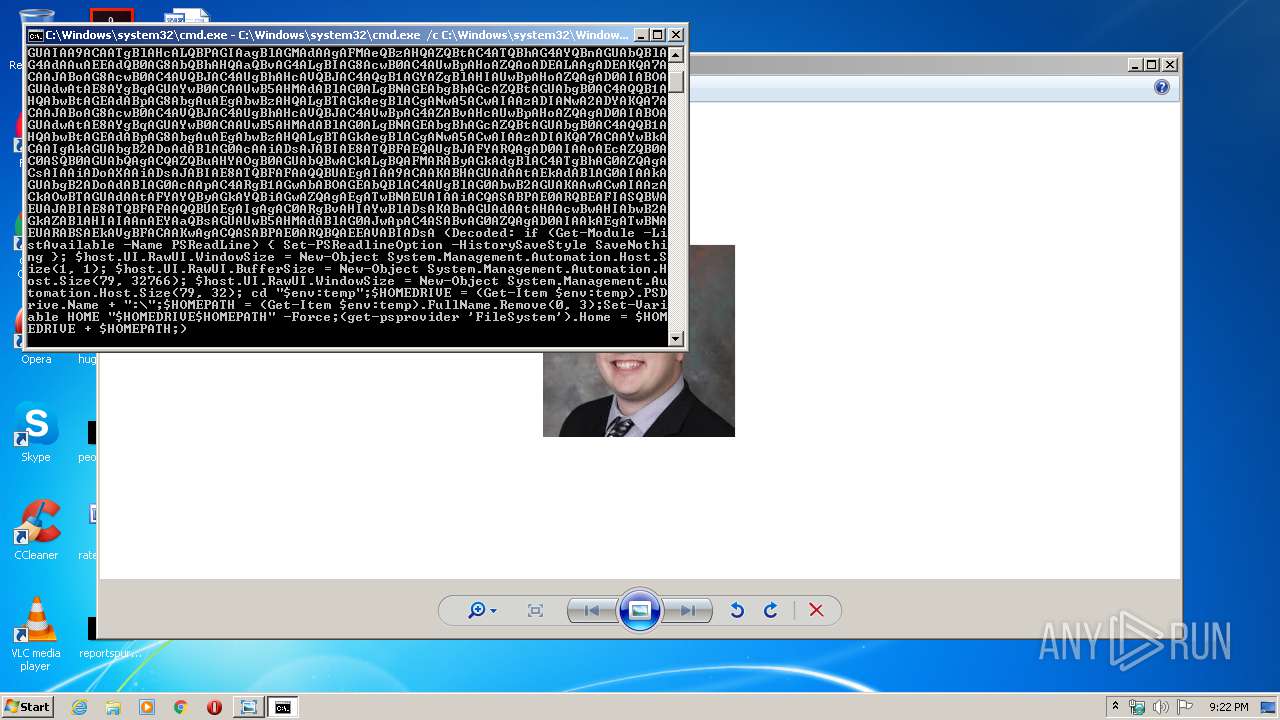
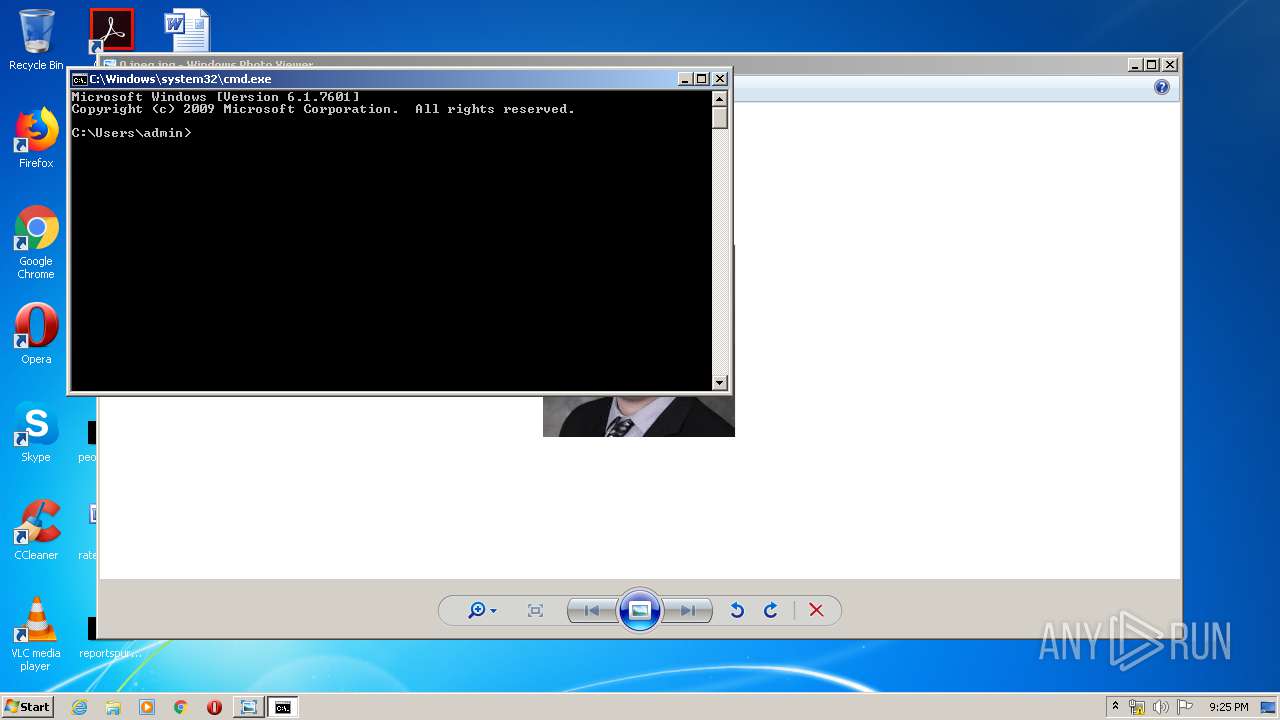
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3464)
- cmd.exe (PID: 3524)
Application launched itself
- cmd.exe (PID: 3464)
- cmd.exe (PID: 3524)
Creates files in the user directory
- powershell.exe (PID: 1928)
- powershell.exe (PID: 1696)
- powershell.exe (PID: 2156)
- powershell.exe (PID: 3848)
PowerShell script executed
- powershell.exe (PID: 1696)
INFO
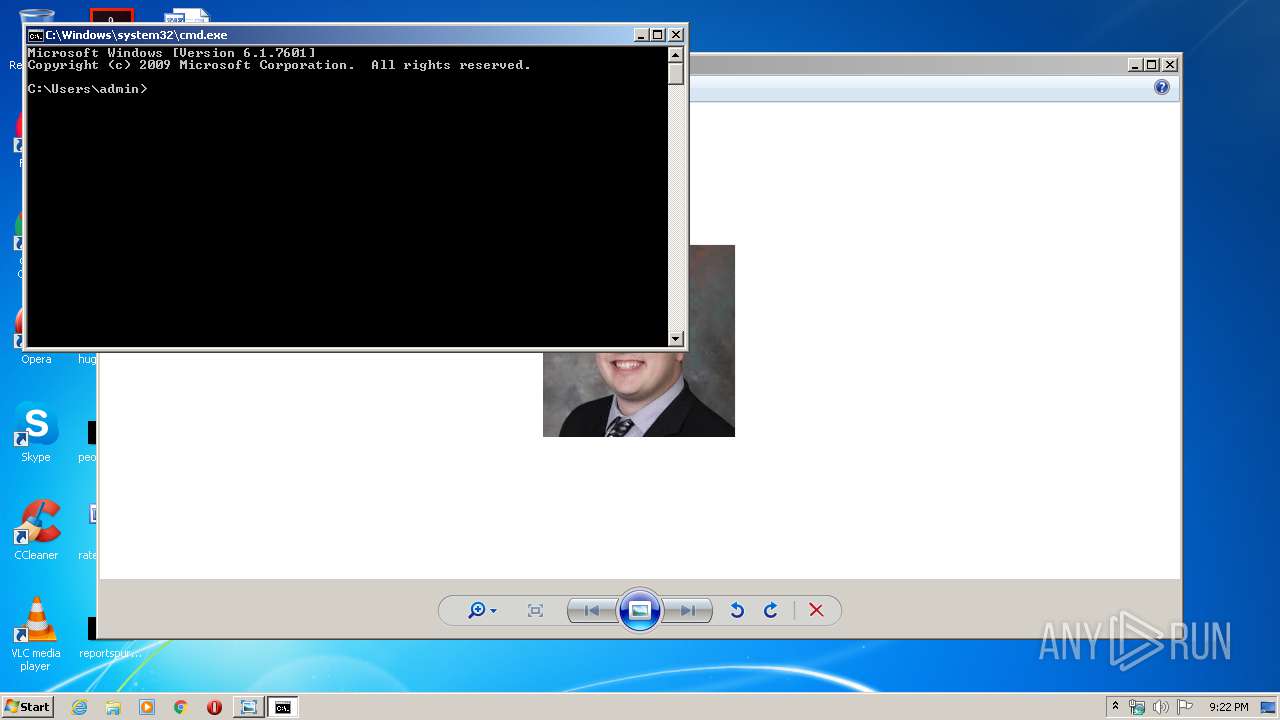
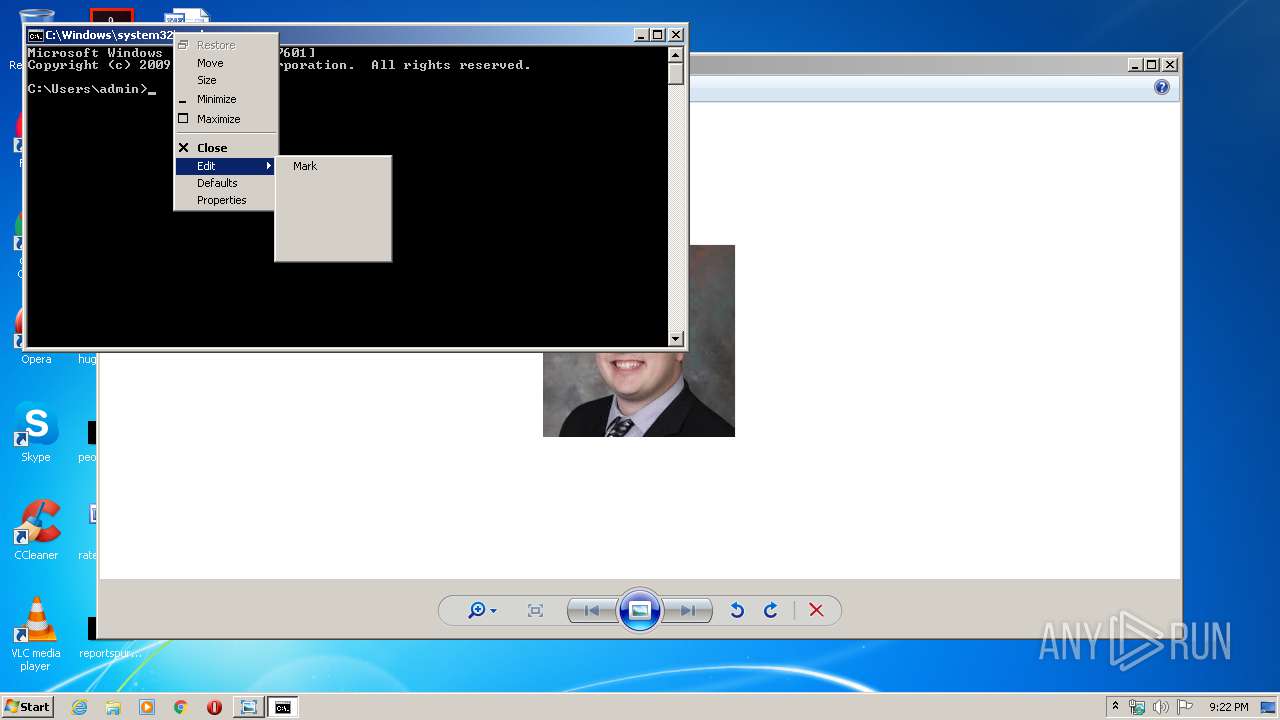
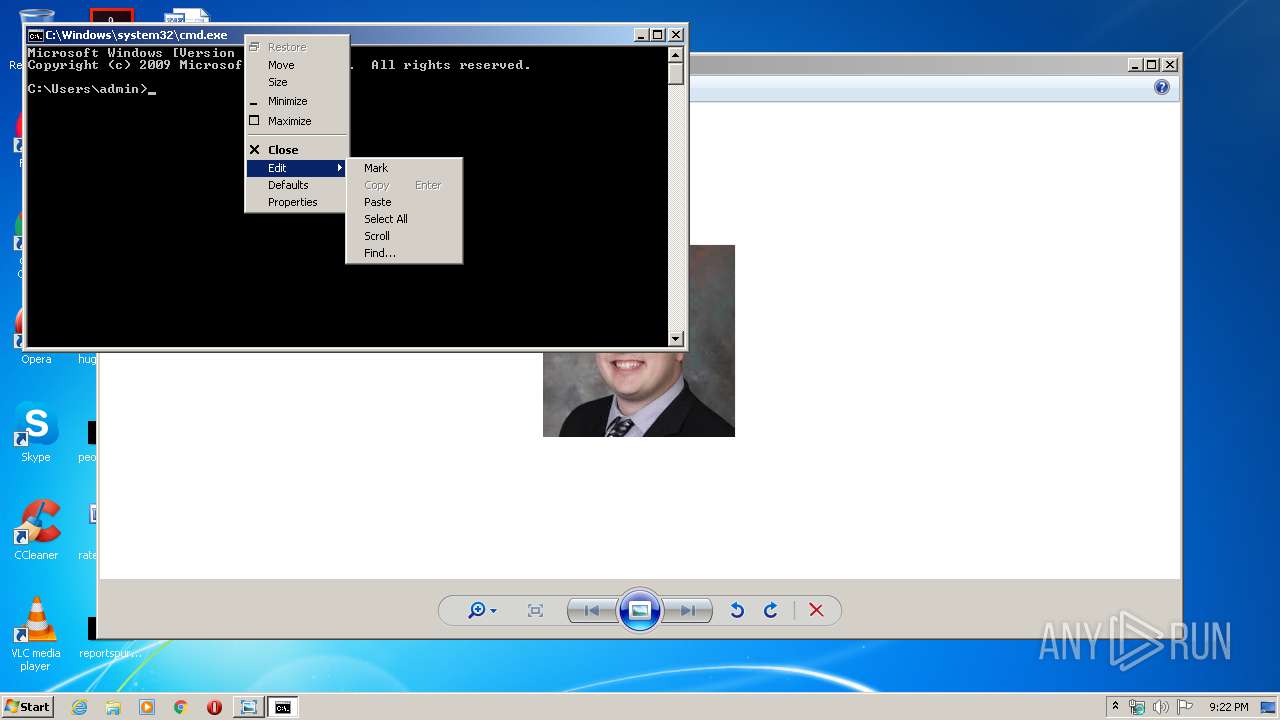
Manual execution by user
- cmd.exe (PID: 3464)
- powershell.exe (PID: 1696)
- cmd.exe (PID: 3524)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jpg | | | JFIF JPEG bitmap (50) |
|---|---|---|
| .jpg | | | JPEG bitmap (37.4) |
| .mp3 | | | MP3 audio (12.4) |
EXIF
JFIF
| JFIFVersion: | 1.01 |
|---|---|
| ResolutionUnit: | None |
| XResolution: | 1 |
| YResolution: | 1 |
Composite
| ImageSize: | 193x193 |
|---|---|
| Megapixels: | 0.037 |
Total processes
45
Monitored processes
9
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1696 | "C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe" | C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
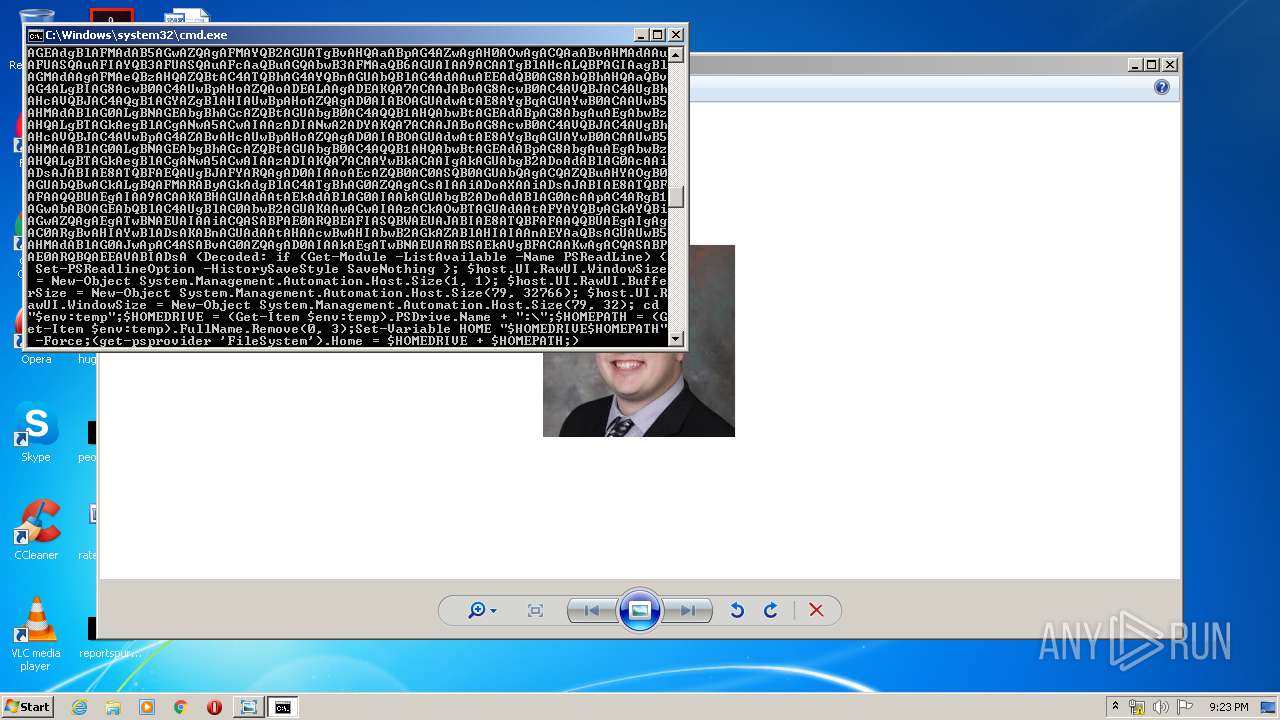
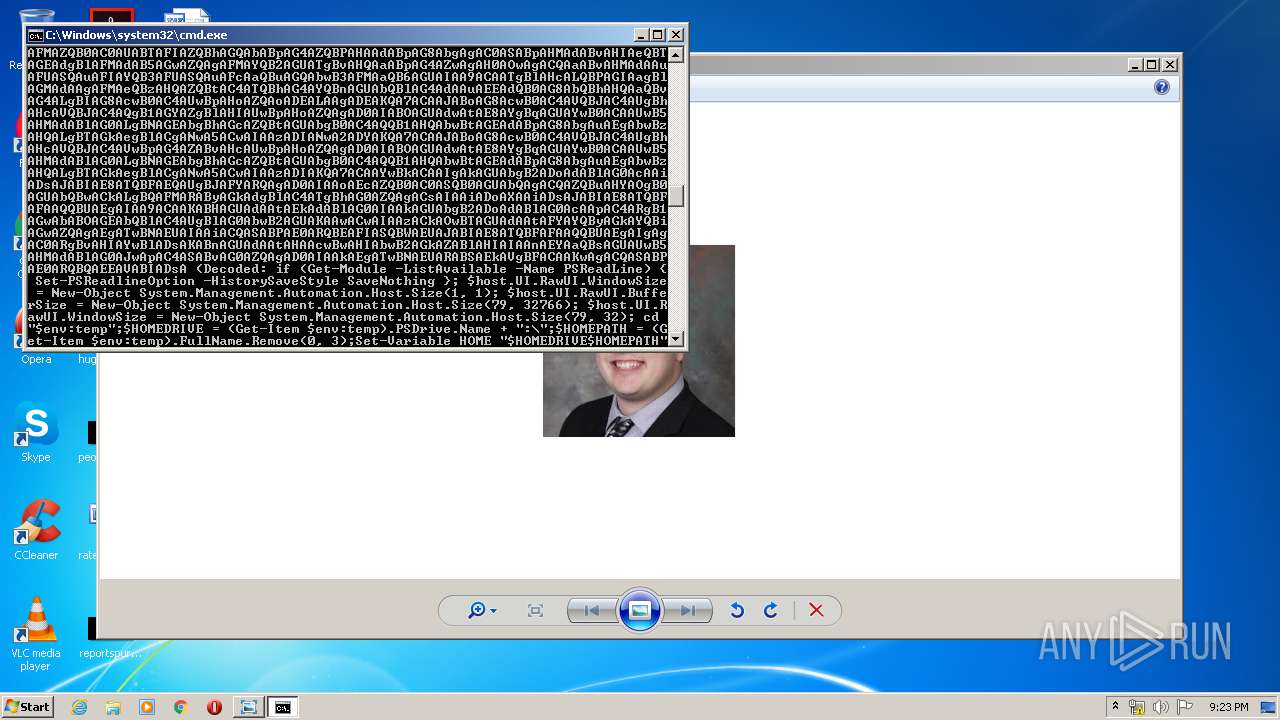
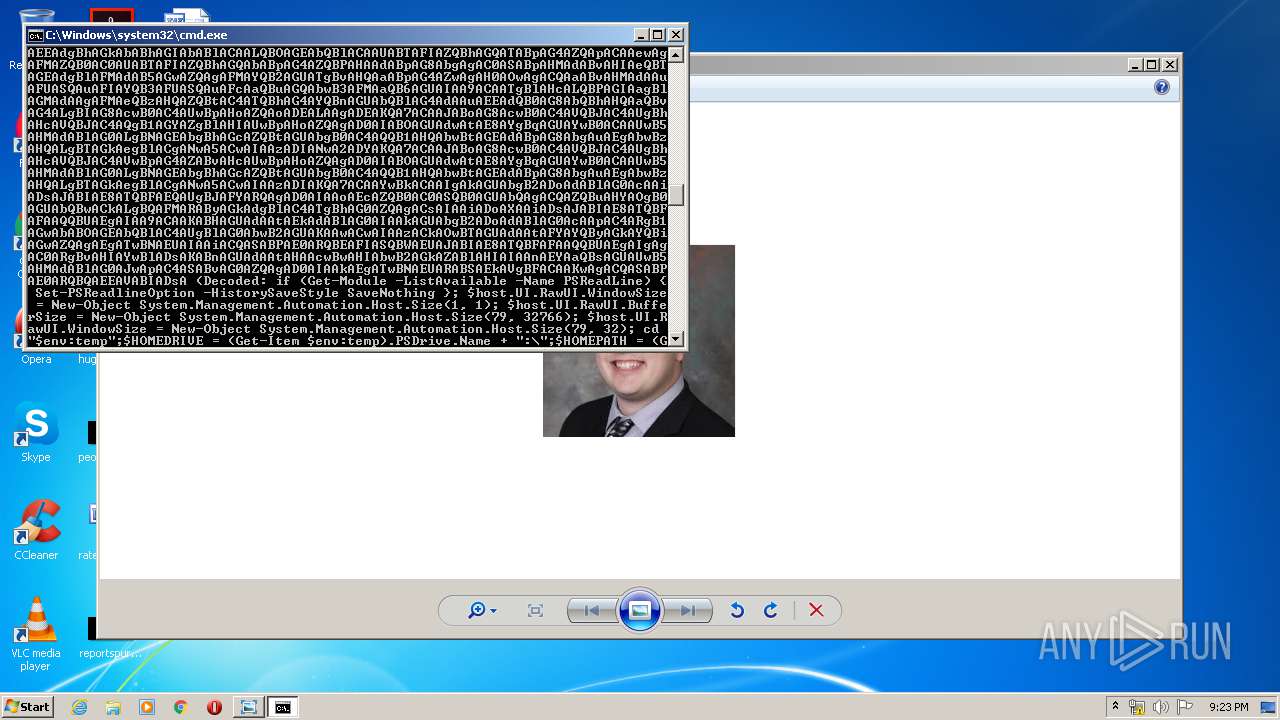
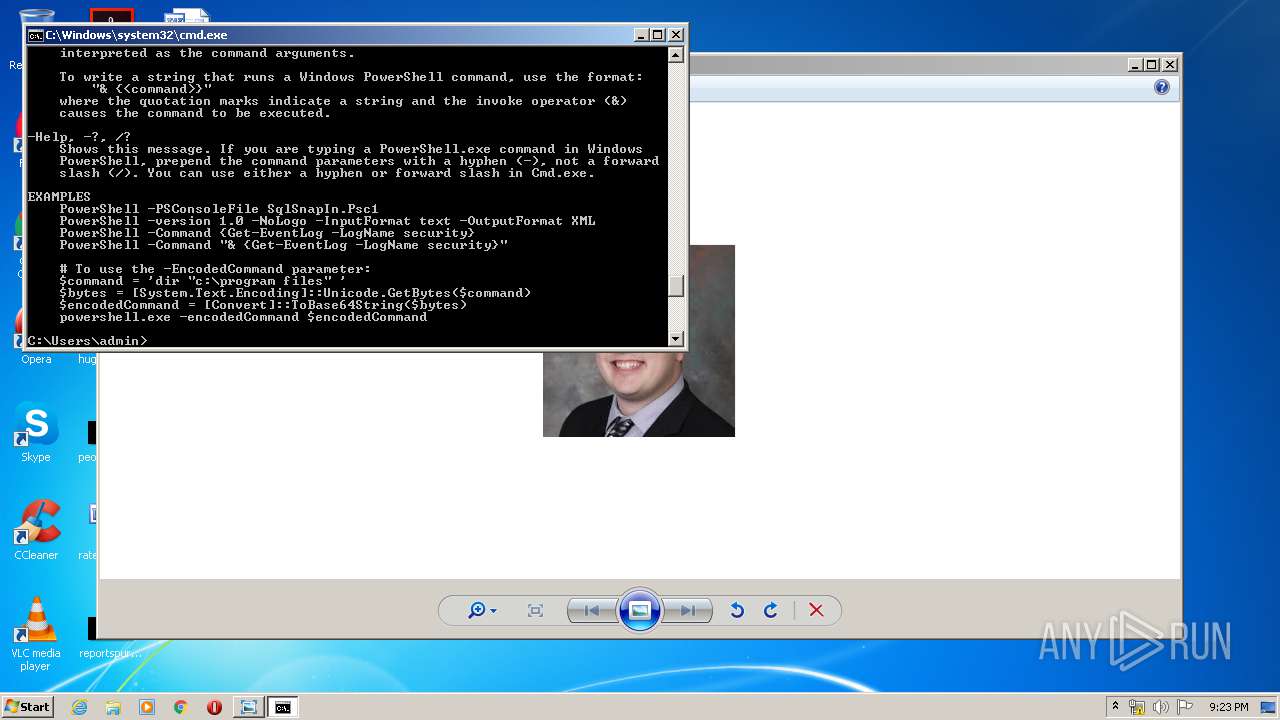
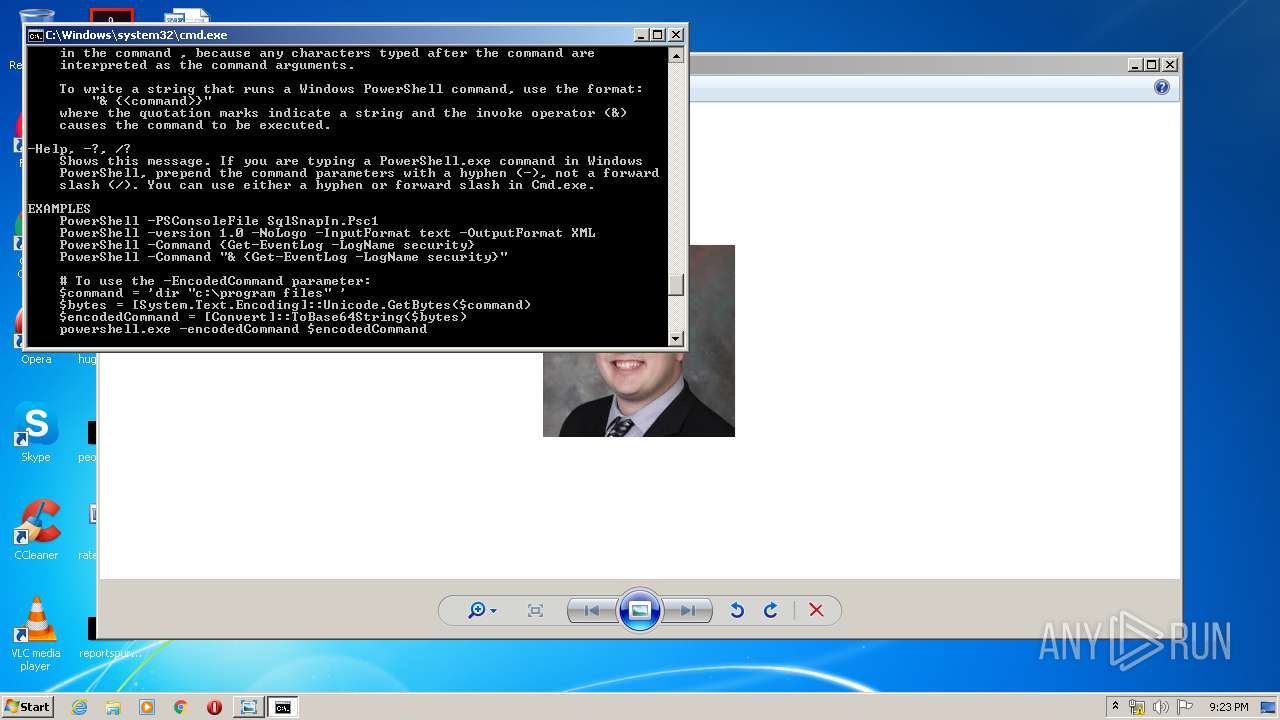
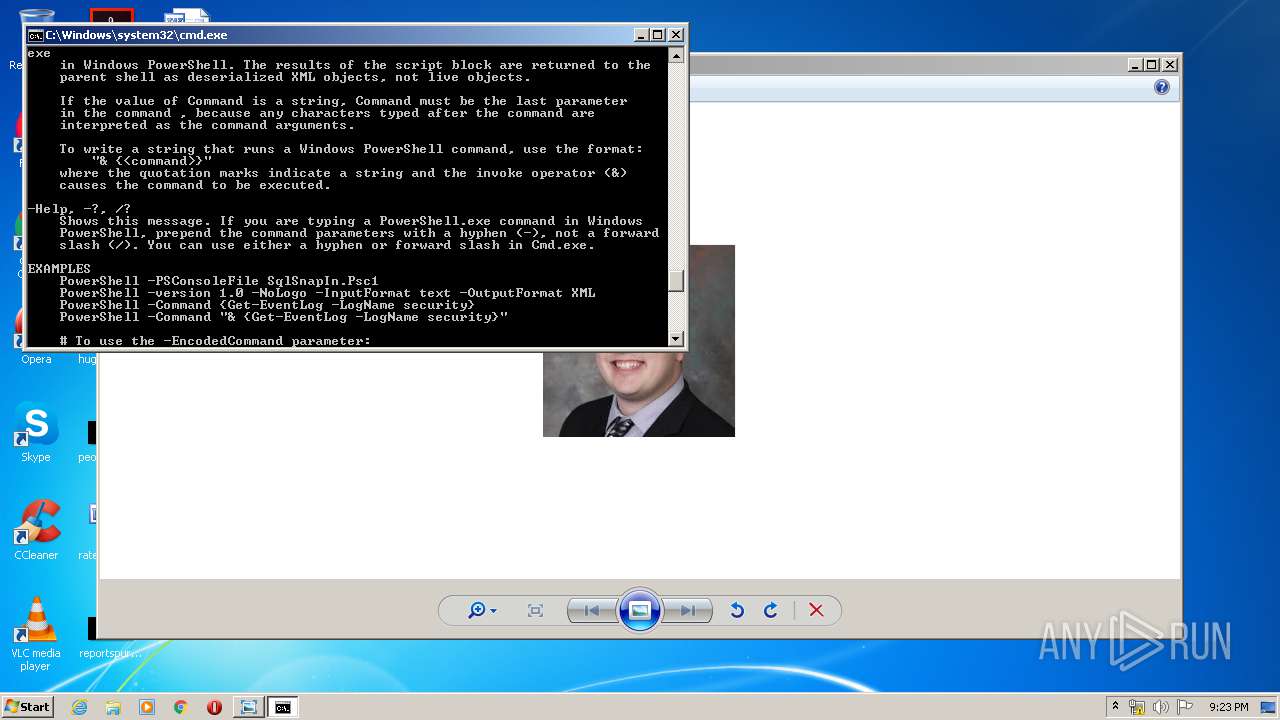
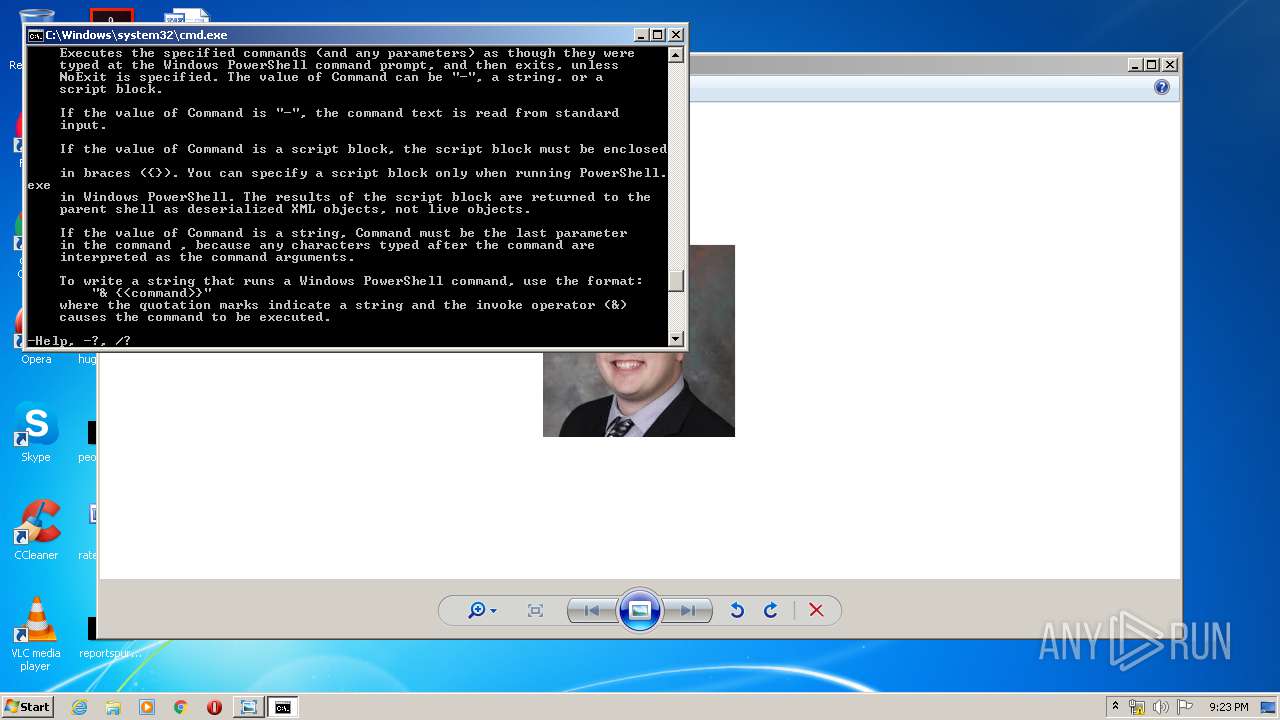
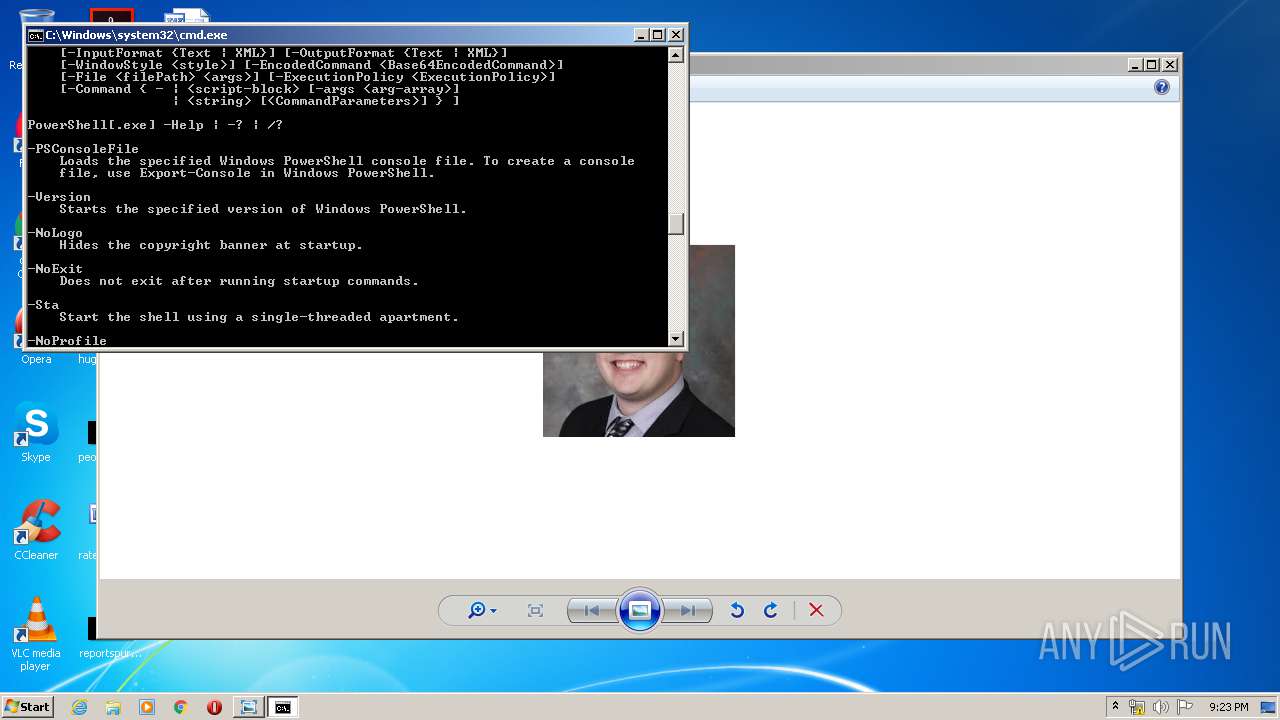
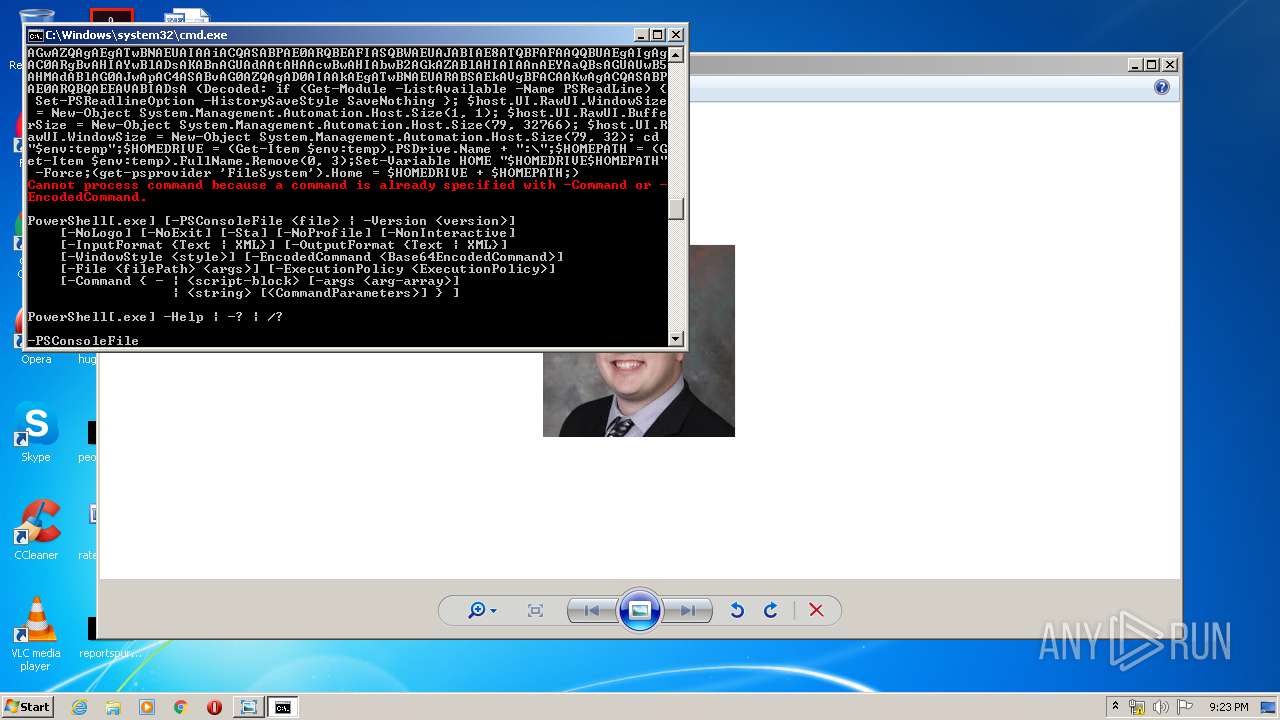
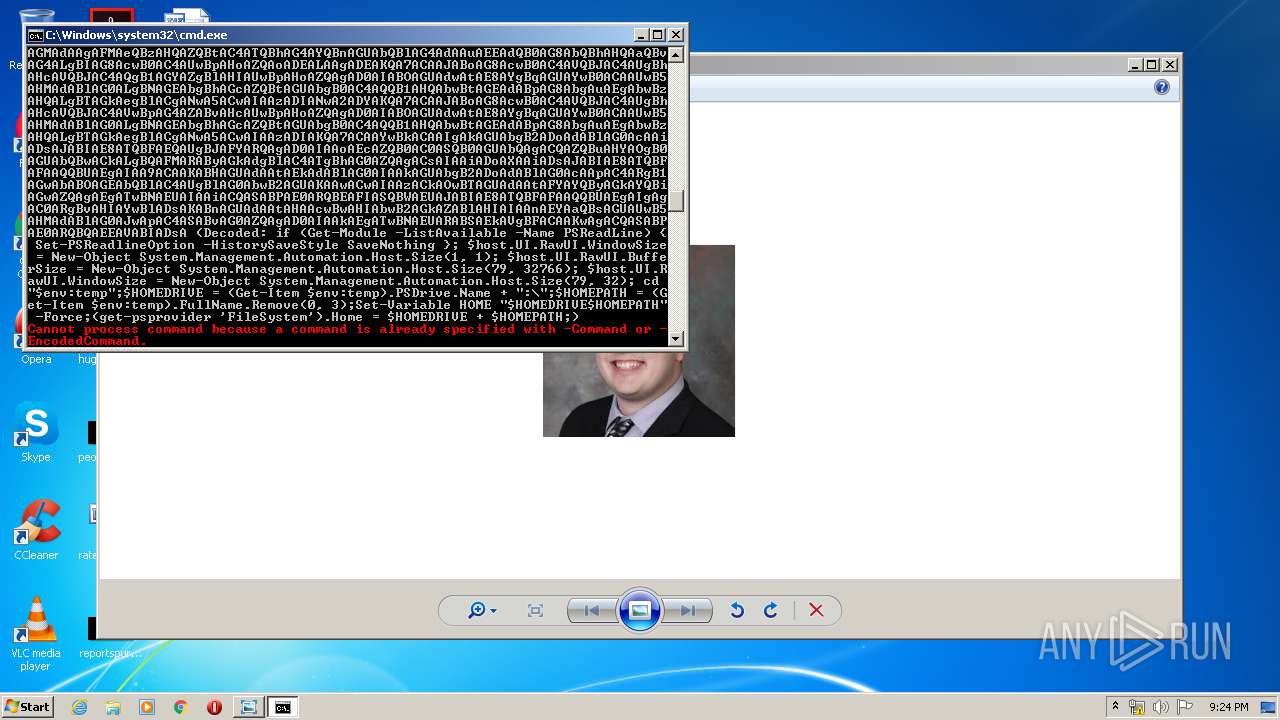
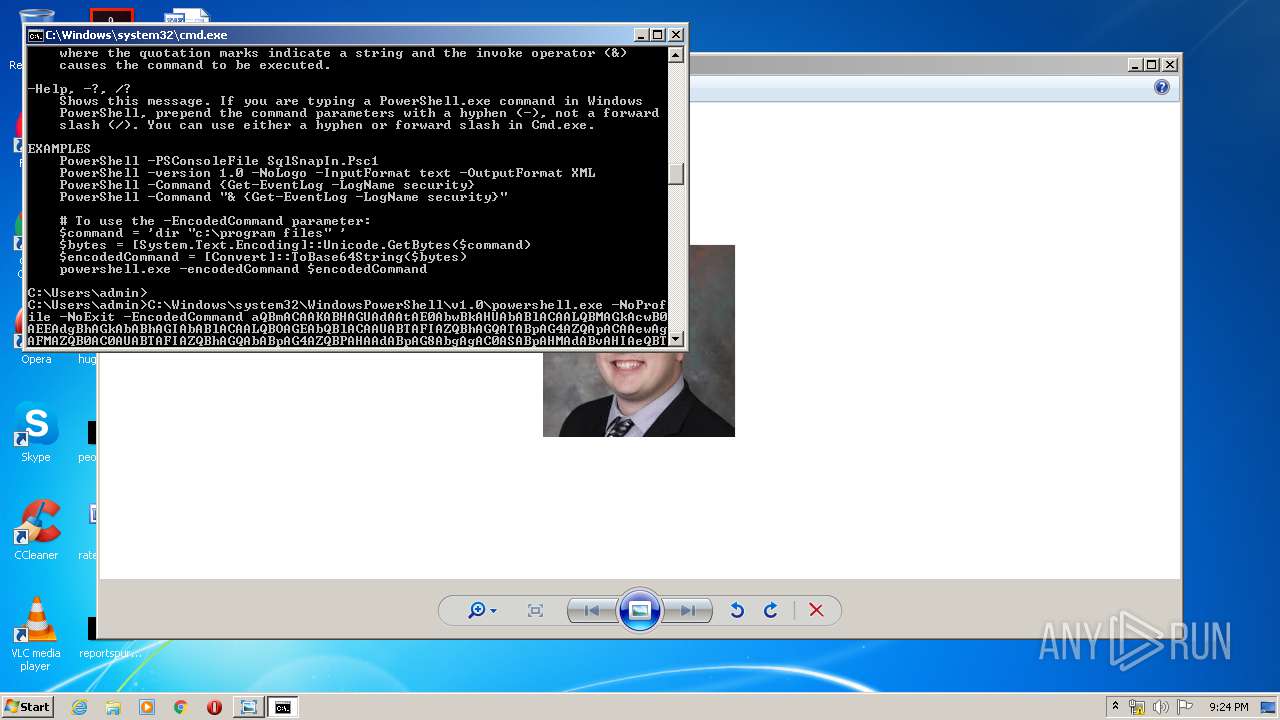
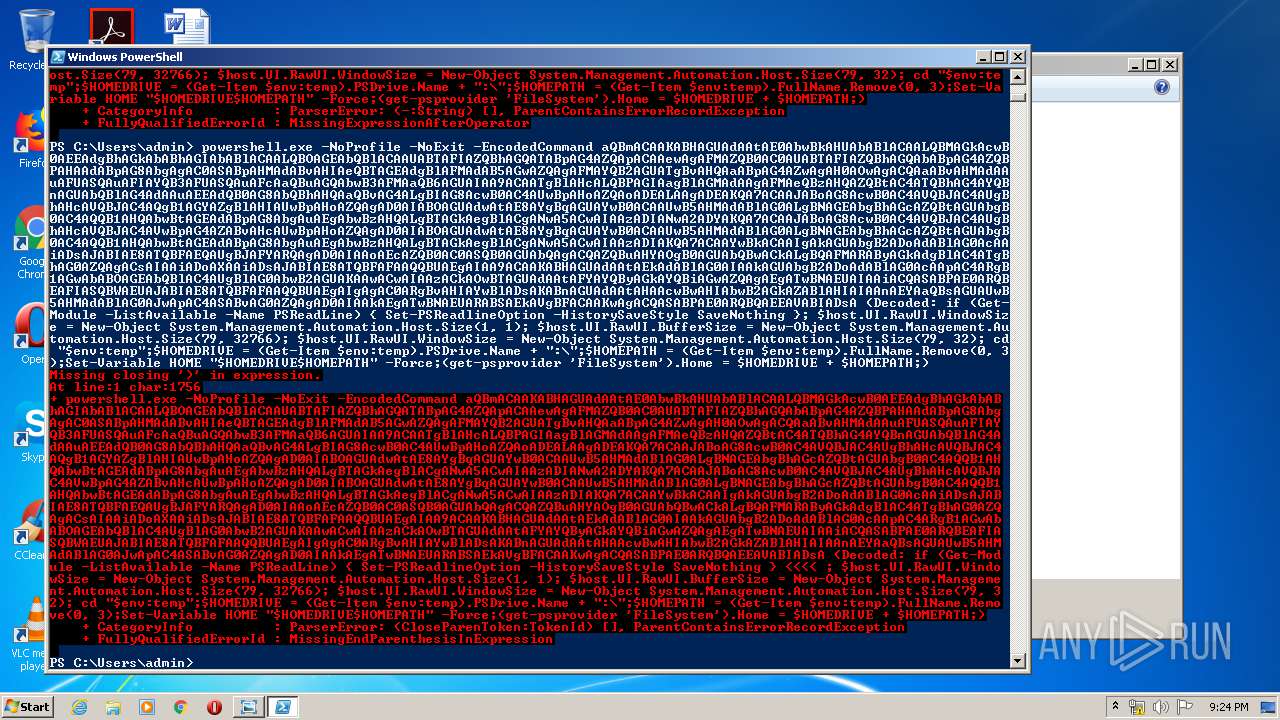
| 1928 | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NoExit -EncodedCommand aQBmACAAKABHAGUAdAAtAE0AbwBkAHUAbABlACAALQBMAGkAcwB0AEEAdgBhAGkAbABhAGIAbABlACAALQBOAGEAbQBlACAAUABTAFIAZQBhAGQATABpAG4AZQApACAAewAgAFMAZQB0AC0AUABTAFIAZQBhAGQAbABpAG4AZQBPAHAAdABpAG8AbgAgAC0ASABpAHMAdABvAHIAeQBTAGEAdgBlAFMAdAB5AGwAZQAgAFMAYQB2AGUATgBvAHQAaABpAG4AZwAgAH0AOwAgACQAaABvAHMAdAAuAFUASQAuAFIAYQB3AFUASQAuAFcAaQBuAGQAbwB3AFMAaQB6AGUAIAA9ACAATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ATQBhAG4AYQBnAGUAbQBlAG4AdAAuAEEAdQB0AG8AbQBhAHQAaQBvAG4ALgBIAG8AcwB0AC4AUwBpAHoAZQAoADEALAAgADEAKQA7ACAAJABoAG8AcwB0AC4AVQBJAC4AUgBhAHcAVQBJAC4AQgB1AGYAZgBlAHIAUwBpAHoAZQAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBNAGEAbgBhAGcAZQBtAGUAbgB0AC4AQQB1AHQAbwBtAGEAdABpAG8AbgAuAEgAbwBzAHQALgBTAGkAegBlACgANwA5ACwAIAAzADIANwA2ADYAKQA7ACAAJABoAG8AcwB0AC4AVQBJAC4AUgBhAHcAVQBJAC4AVwBpAG4AZABvAHcAUwBpAHoAZQAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBNAGEAbgBhAGcAZQBtAGUAbgB0AC4AQQB1AHQAbwBtAGEAdABpAG8AbgAuAEgAbwBzAHQALgBTAGkAegBlACgANwA5ACwAIAAzADIAKQA7ACAAYwBkACAAIgAkAGUAbgB2ADoAdABlAG0AcAAiADsAJABIAE8ATQBFAEQAUgBJAFYARQAgAD0AIAAoAEcAZQB0AC0ASQB0AGUAbQAgACQAZQBuAHYAOgB0AGUAbQBwACkALgBQAFMARAByAGkAdgBlAC4ATgBhAG0AZQAgACsAIAAiADoAXAAiADsAJABIAE8ATQBFAFAAQQBUAEgAIAA9ACAAKABHAGUAdAAtAEkAdABlAG0AIAAkAGUAbgB2ADoAdABlAG0AcAApAC4ARgB1AGwAbABOAGEAbQBlAC4AUgBlAG0AbwB2AGUAKAAwACwAIAAzACkAOwBTAGUAdAAtAFYAYQByAGkAYQBiAGwAZQAgAEgATwBNAEUAIAAiACQASABPAE0ARQBEAFIASQBWAEUAJABIAE8ATQBFAFAAQQBUAEgAIgAgAC0ARgBvAHIAYwBlADsAKABnAGUAdAAtAHAAcwBwAHIAbwB2AGkAZABlAHIAIAAnAEYAaQBsAGUAUwB5AHMAdABlAG0AJwApAC4ASABvAG0AZQAgAD0AIAAkAEgATwBNAEUARABSAEkAVgBFACAAKwAgACQASABPAE0ARQBQAEEAVABIADsA (Decoded: if (Get-Module -ListAvailable -Name PSReadLine) { Set-PSReadlineOption -HistorySaveStyle SaveNothing }; $host.UI.RawUI.WindowSize = New-Object System.Management.Automation.Host.Size(1, 1); $host.UI.RawUI.BufferSize = New-Object System.Management.Automation.Host.Size(79, 32766); $host.UI.RawUI.WindowSize = New-Object System.Management.Automation.Host.Size(79, 32); cd "$env:temp";$HOMEDRIVE = (Get-Item $env:temp).PSDrive.Name + ":\";$HOMEPATH = (Get-Item $env:temp).FullName.Remove(0, 3);Set-Variable HOME "$HOMEDRIVE$HOMEPATH" -Force;(get-psprovider 'FileSystem').Home = $HOMEDRIVE + $HOMEPATH;) | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 4294770688 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2156 | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NoExit -EncodedCommand aQBmACAAKABHAGUAdAAtAE0AbwBkAHUAbABlACAALQBMAGkAcwB0AEEAdgBhAGkAbABhAGIAbABlACAALQBOAGEAbQBlACAAUABTAFIAZQBhAGQATABpAG4AZQApACAAewAgAFMAZQB0AC0AUABTAFIAZQBhAGQAbABpAG4AZQBPAHAAdABpAG8AbgAgAC0ASABpAHMAdABvAHIAeQBTAGEAdgBlAFMAdAB5AGwAZQAgAFMAYQB2AGUATgBvAHQAaABpAG4AZwAgAH0AOwAgACQAaABvAHMAdAAuAFUASQAuAFIAYQB3AFUASQAuAFcAaQBuAGQAbwB3AFMAaQB6AGUAIAA9ACAATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ATQBhAG4AYQBnAGUAbQBlAG4AdAAuAEEAdQB0AG8AbQBhAHQAaQBvAG4ALgBIAG8AcwB0AC4AUwBpAHoAZQAoADEALAAgADEAKQA7ACAAJABoAG8AcwB0AC4AVQBJAC4AUgBhAHcAVQBJAC4AQgB1AGYAZgBlAHIAUwBpAHoAZQAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBNAGEAbgBhAGcAZQBtAGUAbgB0AC4AQQB1AHQAbwBtAGEAdABpAG8AbgAuAEgAbwBzAHQALgBTAGkAegBlACgANwA5ACwAIAAzADIANwA2ADYAKQA7ACAAJABoAG8AcwB0AC4AVQBJAC4AUgBhAHcAVQBJAC4AVwBpAG4AZABvAHcAUwBpAHoAZQAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBNAGEAbgBhAGcAZQBtAGUAbgB0AC4AQQB1AHQAbwBtAGEAdABpAG8AbgAuAEgAbwBzAHQALgBTAGkAegBlACgANwA5ACwAIAAzADIAKQA7ACAAYwBkACAAIgAkAGUAbgB2ADoAdABlAG0AcAAiADsAJABIAE8ATQBFAEQAUgBJAFYARQAgAD0AIAAoAEcAZQB0AC0ASQB0AGUAbQAgACQAZQBuAHYAOgB0AGUAbQBwACkALgBQAFMARAByAGkAdgBlAC4ATgBhAG0AZQAgACsAIAAiADoAXAAiADsAJABIAE8ATQBFAFAAQQBUAEgAIAA9ACAAKABHAGUAdAAtAEkAdABlAG0AIAAkAGUAbgB2ADoAdABlAG0AcAApAC4ARgB1AGwAbABOAGEAbQBlAC4AUgBlAG0AbwB2AGUAKAAwACwAIAAzACkAOwBTAGUAdAAtAFYAYQByAGkAYQBiAGwAZQAgAEgATwBNAEUAIAAiACQASABPAE0ARQBEAFIASQBWAEUAJABIAE8ATQBFAFAAQQBUAEgAIgAgAC0ARgBvAHIAYwBlADsAKABnAGUAdAAtAHAAcwBwAHIAbwB2AGkAZABlAHIAIAAnAEYAaQBsAGUAUwB5AHMAdABlAG0AJwApAC4ASABvAG0AZQAgAD0AIAAkAEgATwBNAEUARABSAEkAVgBFACAAKwAgACQASABPAE0ARQBQAEEAVABIADsA (Decoded: if (Get-Module -ListAvailable -Name PSReadLine) { Set-PSReadlineOption -HistorySaveStyle SaveNothing }; $host.UI.RawUI.WindowSize = New-Object System.Management.Automation.Host.Size(1, 1); $host.UI.RawUI.BufferSize = New-Object System.Management.Automation.Host.Size(79, 32766); $host.UI.RawUI.WindowSize = New-Object System.Management.Automation.Host.Size(79, 32); cd "$env:temp";$HOMEDRIVE = (Get-Item $env:temp).PSDrive.Name + ":\";$HOMEPATH = (Get-Item $env:temp).FullName.Remove(0, 3);Set-Variable HOME "$HOMEDRIVE$HOMEPATH" -Force;(get-psprovider 'FileSystem').Home = $HOMEDRIVE + $HOMEPATH;) | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 4294770688 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2932 | C:\Windows\system32\cmd.exe /c C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NoExit -EncodedCommand aQBmACAAKABHAGUAdAAtAE0AbwBkAHUAbABlACAALQBMAGkAcwB0AEEAdgBhAGkAbABhAGIAbABlACAALQBOAGEAbQBlACAAUABTAFIAZQBhAGQATABpAG4AZQApACAAewAgAFMAZQB0AC0AUABTAFIAZQBhAGQAbABpAG4AZQBPAHAAdABpAG8AbgAgAC0ASABpAHMAdABvAHIAeQBTAGEAdgBlAFMAdAB5AGwAZQAgAFMAYQB2AGUATgBvAHQAaABpAG4AZwAgAH0AOwAgACQAaABvAHMAdAAuAFUASQAuAFIAYQB3AFUASQAuAFcAaQBuAGQAbwB3AFMAaQB6AGUAIAA9ACAATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ATQBhAG4AYQBnAGUAbQBlAG4AdAAuAEEAdQB0AG8AbQBhAHQAaQBvAG4ALgBIAG8AcwB0AC4AUwBpAHoAZQAoADEALAAgADEAKQA7ACAAJABoAG8AcwB0AC4AVQBJAC4AUgBhAHcAVQBJAC4AQgB1AGYAZgBlAHIAUwBpAHoAZQAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBNAGEAbgBhAGcAZQBtAGUAbgB0AC4AQQB1AHQAbwBtAGEAdABpAG8AbgAuAEgAbwBzAHQALgBTAGkAegBlACgANwA5ACwAIAAzADIANwA2ADYAKQA7ACAAJABoAG8AcwB0AC4AVQBJAC4AUgBhAHcAVQBJAC4AVwBpAG4AZABvAHcAUwBpAHoAZQAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBNAGEAbgBhAGcAZQBtAGUAbgB0AC4AQQB1AHQAbwBtAGEAdABpAG8AbgAuAEgAbwBzAHQALgBTAGkAegBlACgANwA5ACwAIAAzADIAKQA7ACAAYwBkACAAIgAkAGUAbgB2ADoAdABlAG0AcAAiADsAJABIAE8ATQBFAEQAUgBJAFYARQAgAD0AIAAoAEcAZQB0AC0ASQB0AGUAbQAgACQAZQBuAHYAOgB0AGUAbQBwACkALgBQAFMARAByAGkAdgBlAC4ATgBhAG0AZQAgACsAIAAiADoAXAAiADsAJABIAE8ATQBFAFAAQQBUAEgAIAA9ACAAKABHAGUAdAAtAEkAdABlAG0AIAAkAGUAbgB2ADoAdABlAG0AcAApAC4ARgB1AGwAbABOAGEAbQBlAC4AUgBlAG0AbwB2AGUAKAAwACwAIAAzACkAOwBTAGUAdAAtAFYAYQByAGkAYQBiAGwAZQAgAEgATwBNAEUAIAAiACQASABPAE0ARQBEAFIASQBWAEUAJABIAE8ATQBFAFAAQQBUAEgAIgAgAC0ARgBvAHIAYwBlADsAKABnAGUAdAAtAHAAcwBwAHIAbwB2AGkAZABlAHIAIAAnAEYAaQBsAGUAUwB5AHMAdABlAG0AJwApAC4ASABvAG0AZQAgAD0AIAAkAEgATwBNAEUARABSAEkAVgBFACAAKwAgACQASABPAE0ARQBQAEEAVABIADsA (Decoded: if (Get-Module -ListAvailable -Name PSReadLine) { Set-PSReadlineOption -HistorySaveStyle SaveNothing }; $host.UI.RawUI.WindowSize = New-Object System.Management.Automation.Host.Size(1, 1); $host.UI.RawUI.BufferSize = New-Object System.Management.Automation.Host.Size(79, 32766); $host.UI.RawUI.WindowSize = New-Object System.Management.Automation.Host.Size(79, 32); cd "$env:temp";$HOMEDRIVE = (Get-Item $env:temp).PSDrive.Name + ":\";$HOMEPATH = (Get-Item $env:temp).FullName.Remove(0, 3);Set-Variable HOME "$HOMEDRIVE$HOMEPATH" -Force;(get-psprovider 'FileSystem').Home = $HOMEDRIVE + $HOMEPATH;) | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4294770688 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
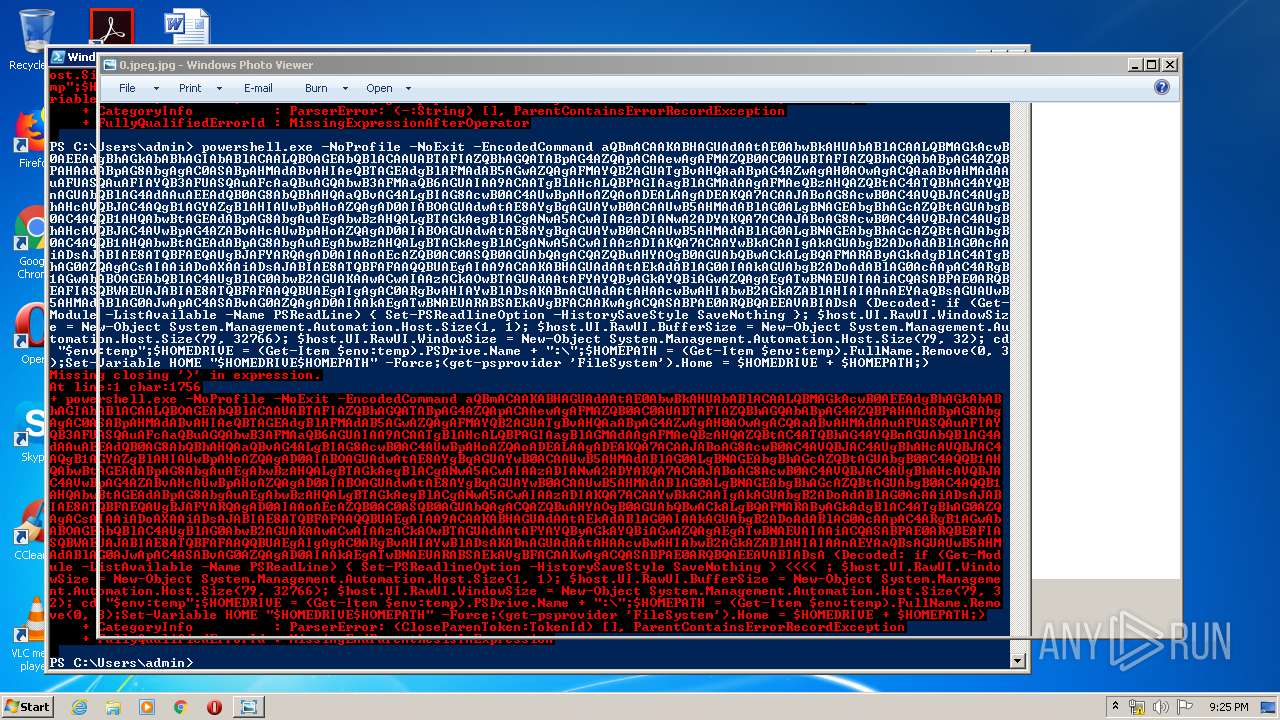
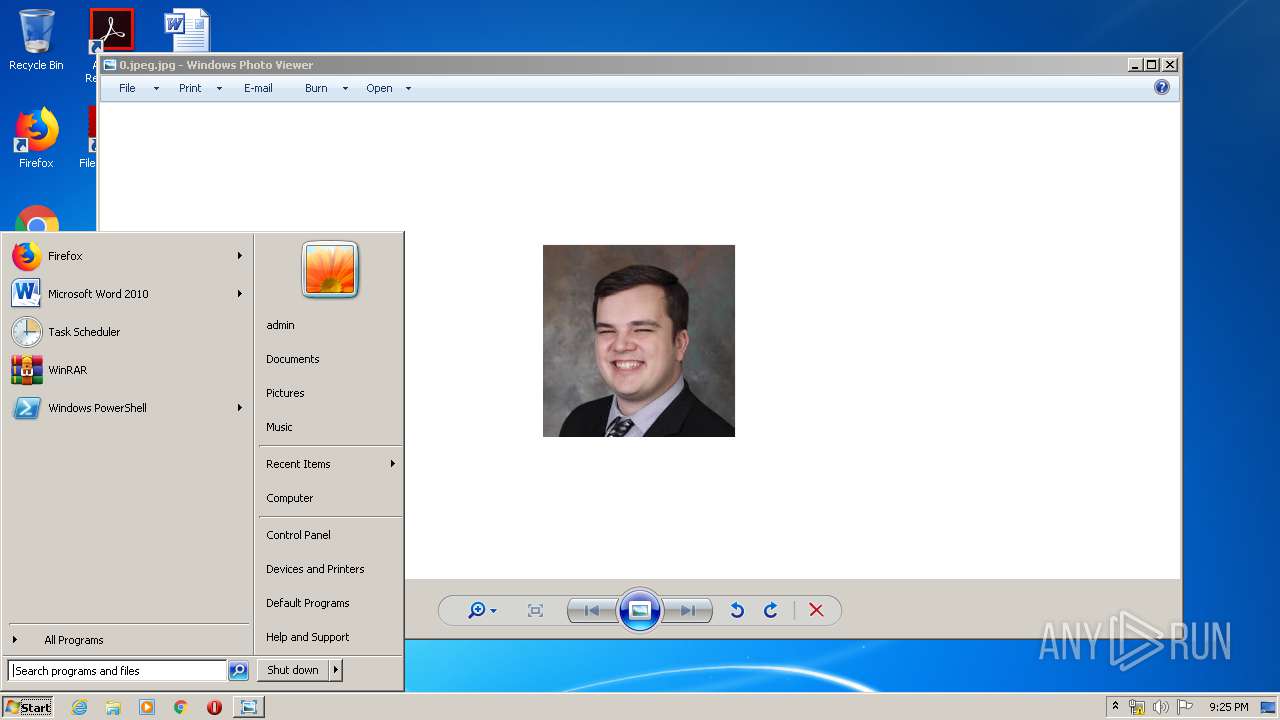
| 3052 | "C:\Windows\System32\rundll32.exe" "C:\Program Files\Windows Photo Viewer\PhotoViewer.dll", ImageView_Fullscreen C:\Users\admin\AppData\Local\Temp\0.jpeg.jpg | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3464 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3524 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3684 | C:\Windows\system32\cmd.exe /c C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NoExit -EncodedCommand aQBmACAAKABHAGUAdAAtAE0AbwBkAHUAbABlACAALQBMAGkAcwB0AEEAdgBhAGkAbABhAGIAbABlACAALQBOAGEAbQBlACAAUABTAFIAZQBhAGQATABpAG4AZQApACAAewAgAFMAZQB0AC0AUABTAFIAZQBhAGQAbABpAG4AZQBPAHAAdABpAG8AbgAgAC0ASABpAHMAdABvAHIAeQBTAGEAdgBlAFMAdAB5AGwAZQAgAFMAYQB2AGUATgBvAHQAaABpAG4AZwAgAH0AOwAgACQAaABvAHMAdAAuAFUASQAuAFIAYQB3AFUASQAuAFcAaQBuAGQAbwB3AFMAaQB6AGUAIAA9ACAATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ATQBhAG4AYQBnAGUAbQBlAG4AdAAuAEEAdQB0AG8AbQBhAHQAaQBvAG4ALgBIAG8AcwB0AC4AUwBpAHoAZQAoADEALAAgADEAKQA7ACAAJABoAG8AcwB0AC4AVQBJAC4AUgBhAHcAVQBJAC4AQgB1AGYAZgBlAHIAUwBpAHoAZQAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBNAGEAbgBhAGcAZQBtAGUAbgB0AC4AQQB1AHQAbwBtAGEAdABpAG8AbgAuAEgAbwBzAHQALgBTAGkAegBlACgANwA5ACwAIAAzADIANwA2ADYAKQA7ACAAJABoAG8AcwB0AC4AVQBJAC4AUgBhAHcAVQBJAC4AVwBpAG4AZABvAHcAUwBpAHoAZQAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBNAGEAbgBhAGcAZQBtAGUAbgB0AC4AQQB1AHQAbwBtAGEAdABpAG8AbgAuAEgAbwBzAHQALgBTAGkAegBlACgANwA5ACwAIAAzADIAKQA7ACAAYwBkACAAIgAkAGUAbgB2ADoAdABlAG0AcAAiADsAJABIAE8ATQBFAEQAUgBJAFYARQAgAD0AIAAoAEcAZQB0AC0ASQB0AGUAbQAgACQAZQBuAHYAOgB0AGUAbQBwACkALgBQAFMARAByAGkAdgBlAC4ATgBhAG0AZQAgACsAIAAiADoAXAAiADsAJABIAE8ATQBFAFAAQQBUAEgAIAA9ACAAKABHAGUAdAAtAEkAdABlAG0AIAAkAGUAbgB2ADoAdABlAG0AcAApAC4ARgB1AGwAbABOAGEAbQBlAC4AUgBlAG0AbwB2AGUAKAAwACwAIAAzACkAOwBTAGUAdAAtAFYAYQByAGkAYQBiAGwAZQAgAEgATwBNAEUAIAAiACQASABPAE0ARQBEAFIASQBWAEUAJABIAE8ATQBFAFAAQQBUAEgAIgAgAC0ARgBvAHIAYwBlADsAKABnAGUAdAAtAHAAcwBwAHIAbwB2AGkAZABlAHIAIAAnAEYAaQBsAGUAUwB5AHMAdABlAG0AJwApAC4ASABvAG0AZQAgAD0AIAAkAEgATwBNAEUARABSAEkAVgBFACAAKwAgACQASABPAE0ARQBQAEEAVABIADsA (Decoded: if (Get-Module -ListAvailable -Name PSReadLine) { Set-PSReadlineOption -HistorySaveStyle SaveNothing }; $host.UI.RawUI.WindowSize = New-Object System.Management.Automation.Host.Size(1, 1); $host.UI.RawUI.BufferSize = New-Object System.Management.Automation.Host.Size(79, 32766); $host.UI.RawUI.WindowSize = New-Object System.Management.Automation.Host.Size(79, 32); cd "$env:temp";$HOMEDRIVE = (Get-Item $env:temp).PSDrive.Name + ":\";$HOMEPATH = (Get-Item $env:temp).FullName.Remove(0, 3);Set-Variable HOME "$HOMEDRIVE$HOMEPATH" -Force;(get-psprovider 'FileSystem').Home = $HOMEDRIVE + $HOMEPATH;) | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4294770688 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3848 | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NoExit -EncodedCommand aQBmACAAKABHAGUAdAAtAE0AbwBkAHUAbABlACAALQBMAGkAcwB0AEEAdgBhAGkAbABhAGIAbABlACAALQBOAGEAbQBlACAAUABTAFIAZQBhAGQATABpAG4AZQApACAAewAgAFMAZQB0AC0AUABTAFIAZQBhAGQAbABpAG4AZQBPAHAAdABpAG8AbgAgAC0ASABpAHMAdABvAHIAeQBTAGEAdgBlAFMAdAB5AGwAZQAgAFMAYQB2AGUATgBvAHQAaABpAG4AZwAgAH0AOwAgACQAaABvAHMAdAAuAFUASQAuAFIAYQB3AFUASQAuAFcAaQBuAGQAbwB3AFMAaQB6AGUAIAA9ACAATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ATQBhAG4AYQBnAGUAbQBlAG4AdAAuAEEAdQB0AG8AbQBhAHQAaQBvAG4ALgBIAG8AcwB0AC4AUwBpAHoAZQAoADEALAAgADEAKQA7ACAAJABoAG8AcwB0AC4AVQBJAC4AUgBhAHcAVQBJAC4AQgB1AGYAZgBlAHIAUwBpAHoAZQAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBNAGEAbgBhAGcAZQBtAGUAbgB0AC4AQQB1AHQAbwBtAGEAdABpAG8AbgAuAEgAbwBzAHQALgBTAGkAegBlACgANwA5ACwAIAAzADIANwA2ADYAKQA7ACAAJABoAG8AcwB0AC4AVQBJAC4AUgBhAHcAVQBJAC4AVwBpAG4AZABvAHcAUwBpAHoAZQAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBNAGEAbgBhAGcAZQBtAGUAbgB0AC4AQQB1AHQAbwBtAGEAdABpAG8AbgAuAEgAbwBzAHQALgBTAGkAegBlACgANwA5ACwAIAAzADIAKQA7ACAAYwBkACAAIgAkAGUAbgB2ADoAdABlAG0AcAAiADsAJABIAE8ATQBFAEQAUgBJAFYARQAgAD0AIAAoAEcAZQB0AC0ASQB0AGUAbQAgACQAZQBuAHYAOgB0AGUAbQBwACkALgBQAFMARAByAGkAdgBlAC4ATgBhAG0AZQAgACsAIAAiADoAXAAiADsAJABIAE8ATQBFAFAAQQBUAEgAIAA9ACAAKABHAGUAdAAtAEkAdABlAG0AIAAkAGUAbgB2ADoAdABlAG0AcAApAC4ARgB1AGwAbABOAGEAbQBlAC4AUgBlAG0AbwB2AGUAKAAwACwAIAAzACkAOwBTAGUAdAAtAFYAYQByAGkAYQBiAGwAZQAgAEgATwBNAEUAIAAiACQASABPAE0ARQBEAFIASQBWAEUAJABIAE8ATQBFAFAAQQBUAEgAIgAgAC0ARgBvAHIAYwBlADsAKABnAGUAdAAtAHAAcwBwAHIAbwB2AGkAZABlAHIAIAAnAEYAaQBsAGUAUwB5AHMAdABlAG0AJwApAC4ASABvAG0AZQAgAD0AIAAkAEgATwBNAEUARABSAEkAVgBFACAAKwAgACQASABPAE0ARQBQAEEAVABIADsA (Decoded: if (Get-Module -ListAvailable -Name PSReadLine) { Set-PSReadlineOption -HistorySaveStyle SaveNothing }; $host.UI.RawUI.WindowSize = New-Object System.Management.Automation.Host.Size(1, 1); $host.UI.RawUI.BufferSize = New-Object System.Management.Automation.Host.Size(79, 32766); $host.UI.RawUI.WindowSize = New-Object System.Management.Automation.Host.Size(79, 32); cd "$env:temp";$HOMEDRIVE = (Get-Item $env:temp).PSDrive.Name + ":\";$HOMEPATH = (Get-Item $env:temp).FullName.Remove(0, 3);Set-Variable HOME "$HOMEDRIVE$HOMEPATH" -Force;(get-psprovider 'FileSystem').Home = $HOMEDRIVE + $HOMEPATH;) | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 4294770688 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
838
Read events
618
Write events
220
Delete events
0
Modification events
| (PID) Process: | (3052) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: rundll32.exe | |||
| (PID) Process: | (1928) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2156) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1696) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3848) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
8
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1928 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4I57XZKGTK14WJNTZQCP.temp | — | |
MD5:— | SHA256:— | |||
| 2156 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\AEIM3P3TNR8P7TWHGOJS.temp | — | |
MD5:— | SHA256:— | |||
| 1696 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\E5T8BKTFN48ZT0HS1L61.temp | — | |
MD5:— | SHA256:— | |||
| 3848 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PGQSSHN428MVLASMJPQ1.temp | — | |
MD5:— | SHA256:— | |||
| 1928 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFa71d20.TMP | binary | |
MD5:— | SHA256:— | |||
| 1928 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1696 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFa8bb5f.TMP | binary | |
MD5:— | SHA256:— | |||
| 3848 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFa9e7d9.TMP | binary | |
MD5:— | SHA256:— | |||
| 2156 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1696 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report