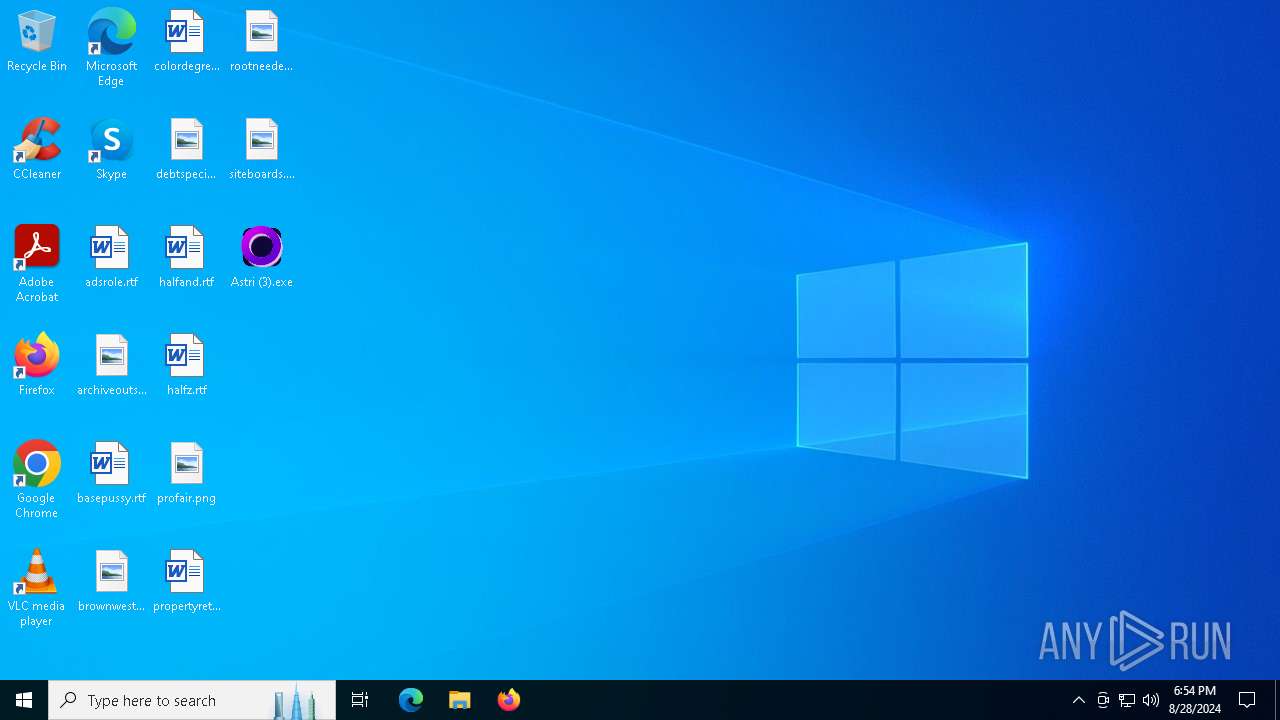
| File name: | Astri (3).exe |
| Full analysis: | https://app.any.run/tasks/3b982290-4491-4ea2-a10f-36e52550d75d |
| Verdict: | Malicious activity |
| Analysis date: | August 28, 2024, 18:53:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64 (stripped to external PDB), for MS Windows |
| MD5: | 5E9172CC34F77200A469F7C1FE0A61E6 |
| SHA1: | 52DFF13A09FA22AEB4F5D28571E5A67B4B1AC91C |
| SHA256: | FEB057C03CB1B4DBB43ABDD58C8416E4D605BD8C28643CDDD00DAA41B78A7385 |
| SSDEEP: | 196608:aPZ1Cu+VDuEvYiKPyAXFVuekA19t+oFmvwZt8IaI+VqCnsIS8JnqnXn64AIkVR1m:u1ClDFETZ1vxmYL8/ZnRaX1k4L |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops the executable file immediately after the start
- Astri (3).exe (PID: 7064)
- Astri (3).exe (PID: 368)
Process drops legitimate windows executable
- Astri (3).exe (PID: 7064)
- Astri (3).exe (PID: 368)
Process drops python dynamic module
- Astri (3).exe (PID: 7064)
- Astri (3).exe (PID: 368)
Executable content was dropped or overwritten
- Astri (3).exe (PID: 7064)
- Astri (3).exe (PID: 368)
The process drops C-runtime libraries
- Astri (3).exe (PID: 7064)
- Astri (3).exe (PID: 368)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 876)
- cmd.exe (PID: 6132)
Starts CMD.EXE for commands execution
- astri.exe (PID: 6396)
- astri.exe (PID: 2520)
Loads Python modules
- astri.exe (PID: 6396)
- astri.exe (PID: 2520)
Hides command output
- cmd.exe (PID: 876)
- cmd.exe (PID: 6132)
Reads security settings of Internet Explorer
- Astri (3).exe (PID: 7064)
- Astri (3).exe (PID: 368)
INFO
Create files in a temporary directory
- Astri (3).exe (PID: 7064)
- Astri (3).exe (PID: 368)
Checks supported languages
- Astri (3).exe (PID: 7064)
- astri.exe (PID: 6396)
- Astri (3).exe (PID: 368)
- astri.exe (PID: 2520)
Reads the machine GUID from the registry
- astri.exe (PID: 6396)
- astri.exe (PID: 2520)
Reads the computer name
- astri.exe (PID: 6396)
- Astri (3).exe (PID: 7064)
- astri.exe (PID: 2520)
- Astri (3).exe (PID: 368)
Checks proxy server information
- astri.exe (PID: 6396)
- astri.exe (PID: 2520)
- slui.exe (PID: 6416)
Reads the software policy settings
- slui.exe (PID: 6912)
- slui.exe (PID: 6416)
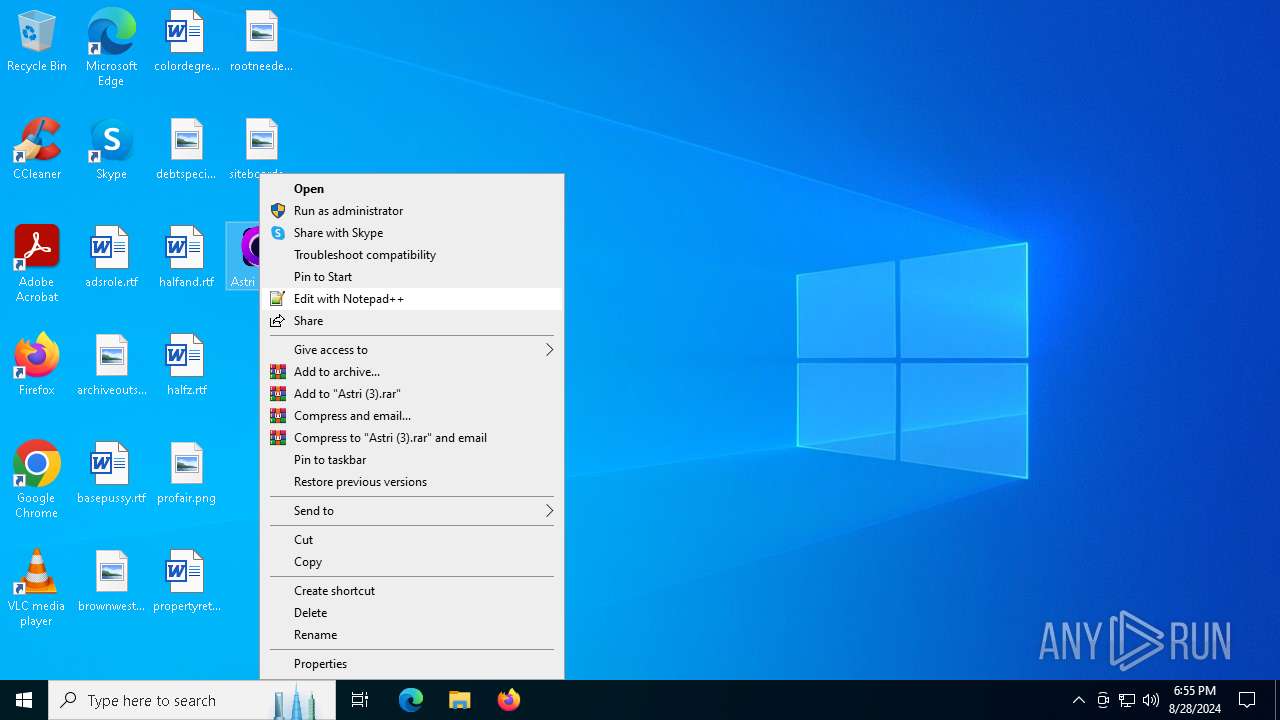
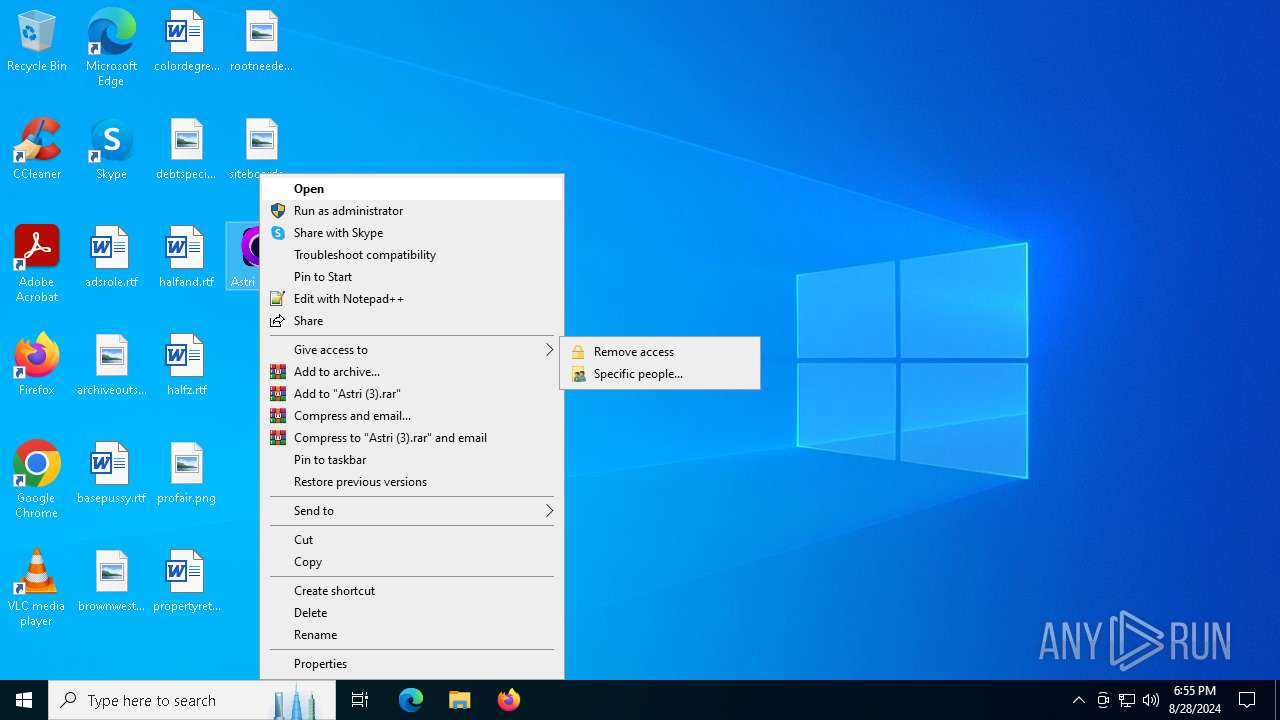
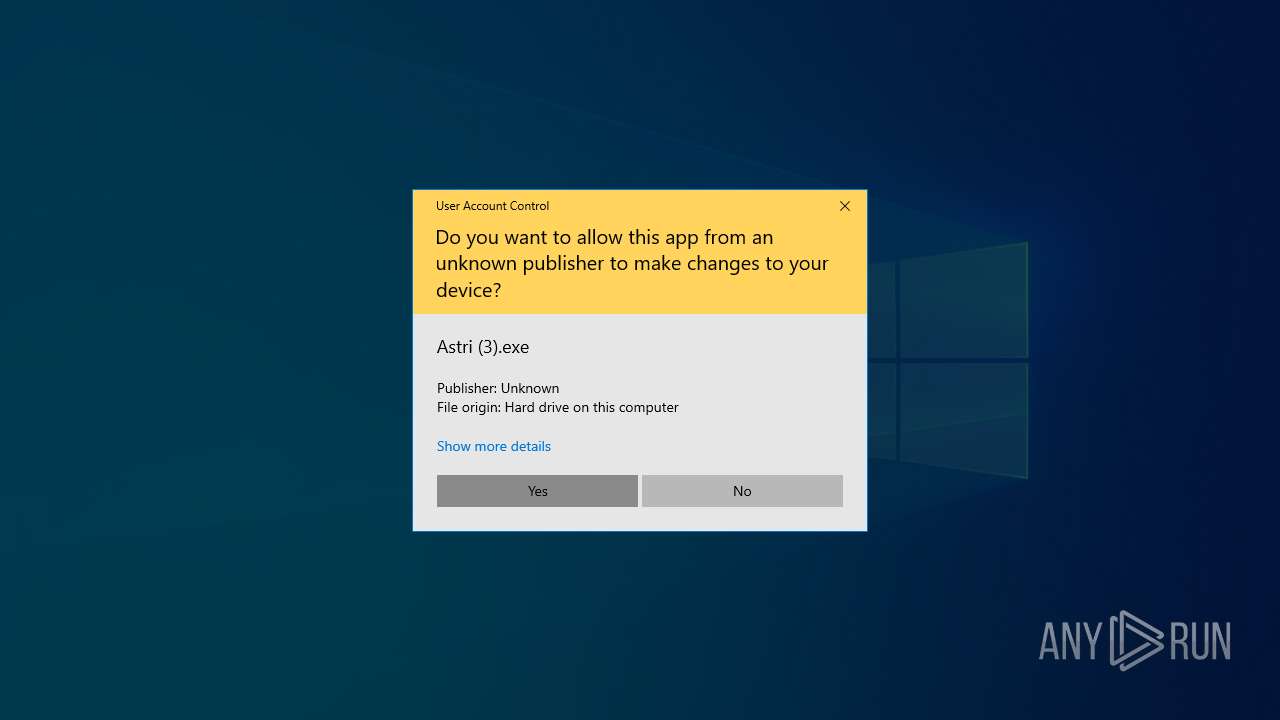
Manual execution by a user
- Astri (3).exe (PID: 368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2023:08:23 20:51:15+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 2.38 |
| CodeSize: | 115200 |
| InitializedDataSize: | 14441472 |
| UninitializedDataSize: | 65024 |
| EntryPoint: | 0x1125 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
148
Monitored processes
17
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 368 | "C:\Users\admin\Desktop\Astri (3).exe" | C:\Users\admin\Desktop\Astri (3).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 876 | C:\WINDOWS\system32\cmd.exe /c taskkill/IM python.exe /F > NUL 2>&1 | C:\Windows\System32\cmd.exe | — | astri.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1168 | taskkill /IM python.exe /F | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1932 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2520 | "C:\Users\admin\Desktop\Astri (3).exe" | C:\Users\admin\AppData\Local\Temp\onefile_368_133693449095359260\astri.exe | Astri (3).exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3672 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Astri (3).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3672 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | astri.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4060 | taskkill /IM python.exe /F | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4820 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | astri.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4820 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Astri (3).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 802
Read events
9 802
Write events
0
Delete events
0
Modification events
Executable files
106
Suspicious files
2
Text files
1 842
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7064 | Astri (3).exe | C:\Users\admin\AppData\Local\Temp\onefile_7064_133693448149869730\_queue.pyd | executable | |
MD5:60DEC90862B996E56AEDAFB2774C3475 | SHA256:9568EF8BAE36EDAE7347B6573407C312CE3B19BBD899713551A1819D6632DA46 | |||
| 7064 | Astri (3).exe | C:\Users\admin\AppData\Local\Temp\onefile_7064_133693448149869730\_ssl.pyd | executable | |
MD5:7C7223F28C0C27C85A979AD222D19288 | SHA256:4EC47BEADC4FD0D38FA39092244C108674012874F3190EE0E484AA988B94F986 | |||
| 7064 | Astri (3).exe | C:\Users\admin\AppData\Local\Temp\onefile_7064_133693448149869730\_socket.pyd | executable | |
MD5:C389430E19F1CD4C2E7B8538E8C52459 | SHA256:A14EFA68D8F7EC018FB867A6BA6C6C290A803B4001FD8C45DB7BDA66FB700067 | |||
| 7064 | Astri (3).exe | C:\Users\admin\AppData\Local\Temp\onefile_7064_133693448149869730\_multiprocessing.pyd | executable | |
MD5:B3C8414BBCAE9BCC3377A4DF72A4AED7 | SHA256:65413D49D81E5B939226A211FD40C9B7C6D61366651639446273988930F4A6FD | |||
| 7064 | Astri (3).exe | C:\Users\admin\AppData\Local\Temp\onefile_7064_133693448149869730\astri.exe | executable | |
MD5:479A9FA623417EE8E33FC3870F767BE6 | SHA256:A3C32E3FE405B79AB527E1E492063519A4F1350DBC1BFC5D9E6358D35D78F319 | |||
| 7064 | Astri (3).exe | C:\Users\admin\AppData\Local\Temp\onefile_7064_133693448149869730\_elementtree.pyd | executable | |
MD5:9C4DFF1C5B5EA7EC18DA13C4B219A62C | SHA256:18EC7D16E01158FF8FDADC370DD8D32EC32600A3485C813F4E983C4C0F77B2DE | |||
| 7064 | Astri (3).exe | C:\Users\admin\AppData\Local\Temp\onefile_7064_133693448149869730\_cffi_backend.pyd | executable | |
MD5:6F1B90884343F717C5DC14F94EF5ACEA | SHA256:2093E7E4F5359B38F0819BDEF8314FDA332A1427F22E09AFC416E1EDD5910FE1 | |||
| 7064 | Astri (3).exe | C:\Users\admin\AppData\Local\Temp\onefile_7064_133693448149869730\_bz2.pyd | executable | |
MD5:56203038756826A0A683D5750EE04093 | SHA256:31C2F21ADF27CA77FA746C0FDA9C7D7734587AB123B95F2310725AAF4BF4FF3C | |||
| 7064 | Astri (3).exe | C:\Users\admin\AppData\Local\Temp\onefile_7064_133693448149869730\_ctypes.pyd | executable | |
MD5:462FD515CA586048459B9D90A660CB93 | SHA256:BF017767AC650420487CA3225B3077445D24260BF1A33E75F7361B0C6D3E96B4 | |||
| 7064 | Astri (3).exe | C:\Users\admin\AppData\Local\Temp\onefile_7064_133693448149869730\_hashlib.pyd | executable | |
MD5:7A74284813386818ADA7BF55C8D8ACF9 | SHA256:21A1819013DE423BB3B9B682D0B3506C6EF57EE88C61EDF4BA12D8D5F589C9C2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
49
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1404 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6952 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6952 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6252 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7072 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7072 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1404 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1404 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6952 | SIHClient.exe | 52.165.165.26:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |